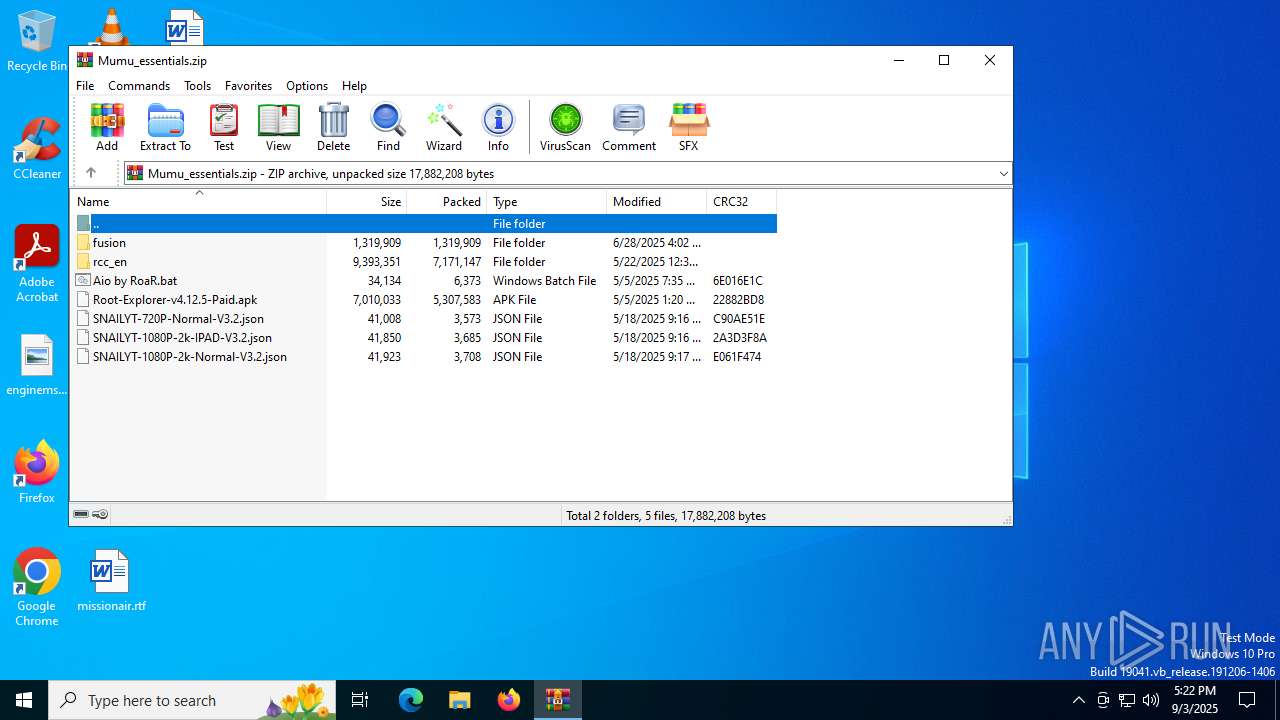
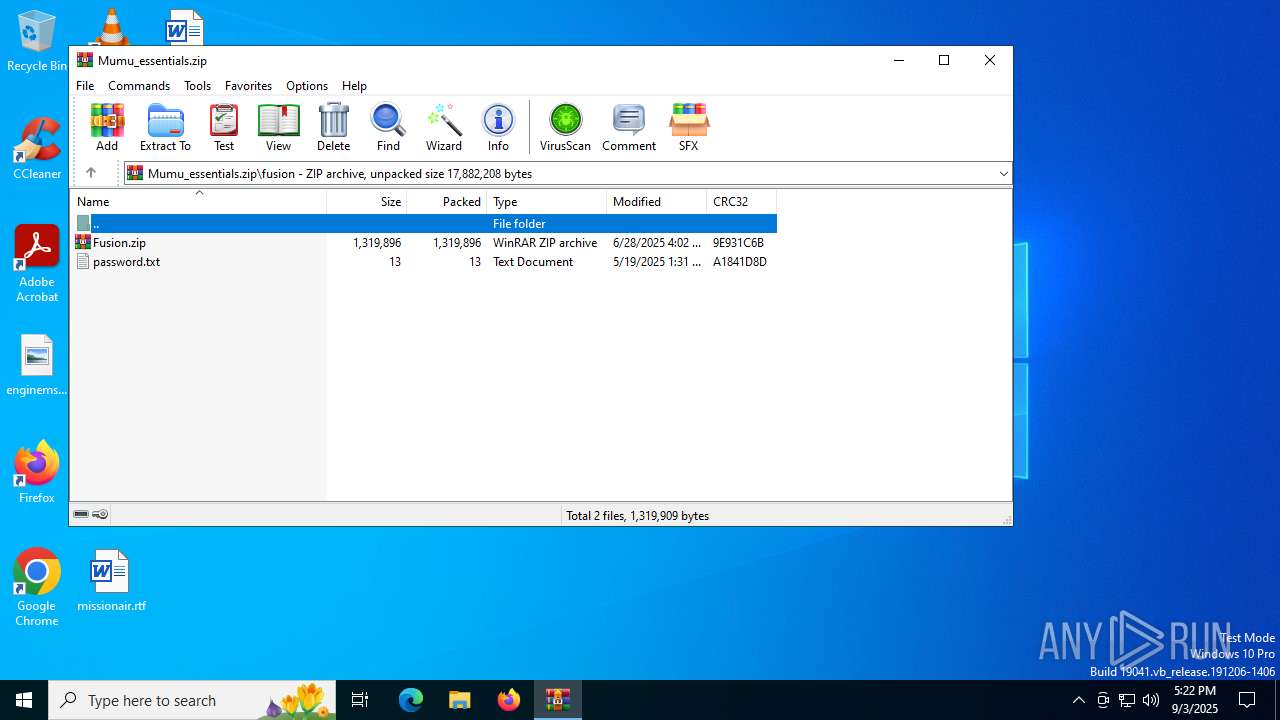
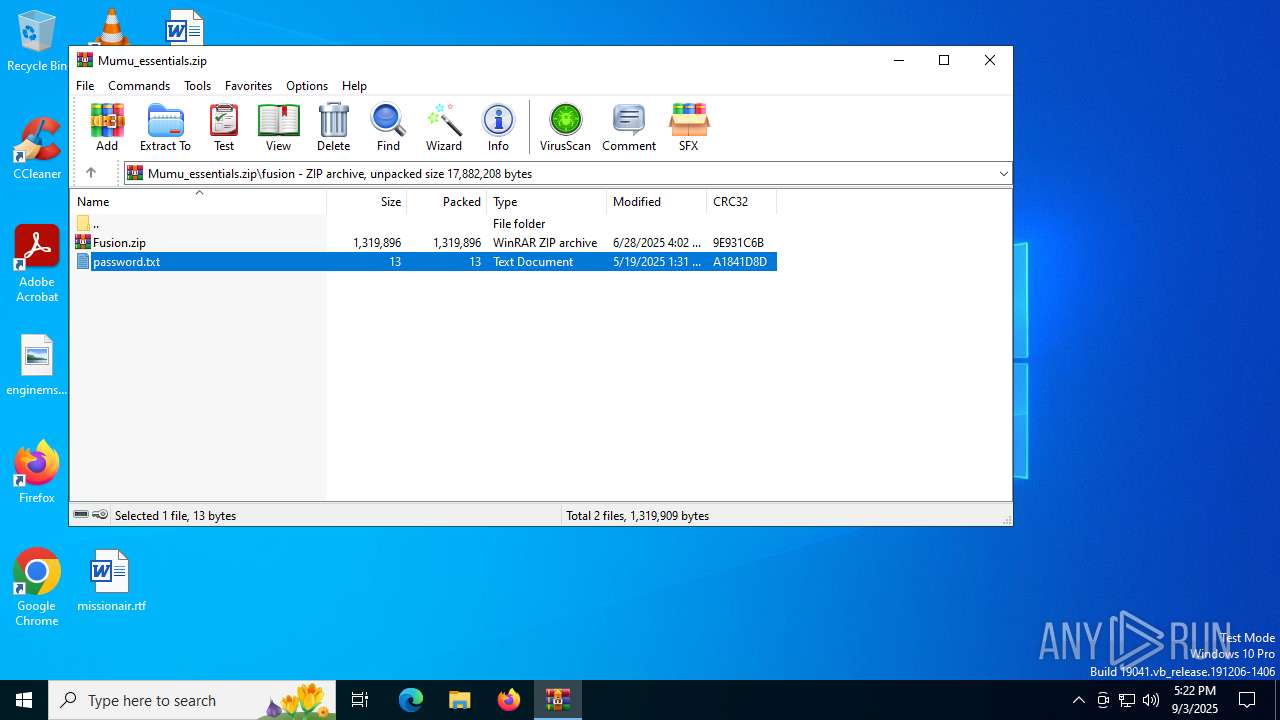
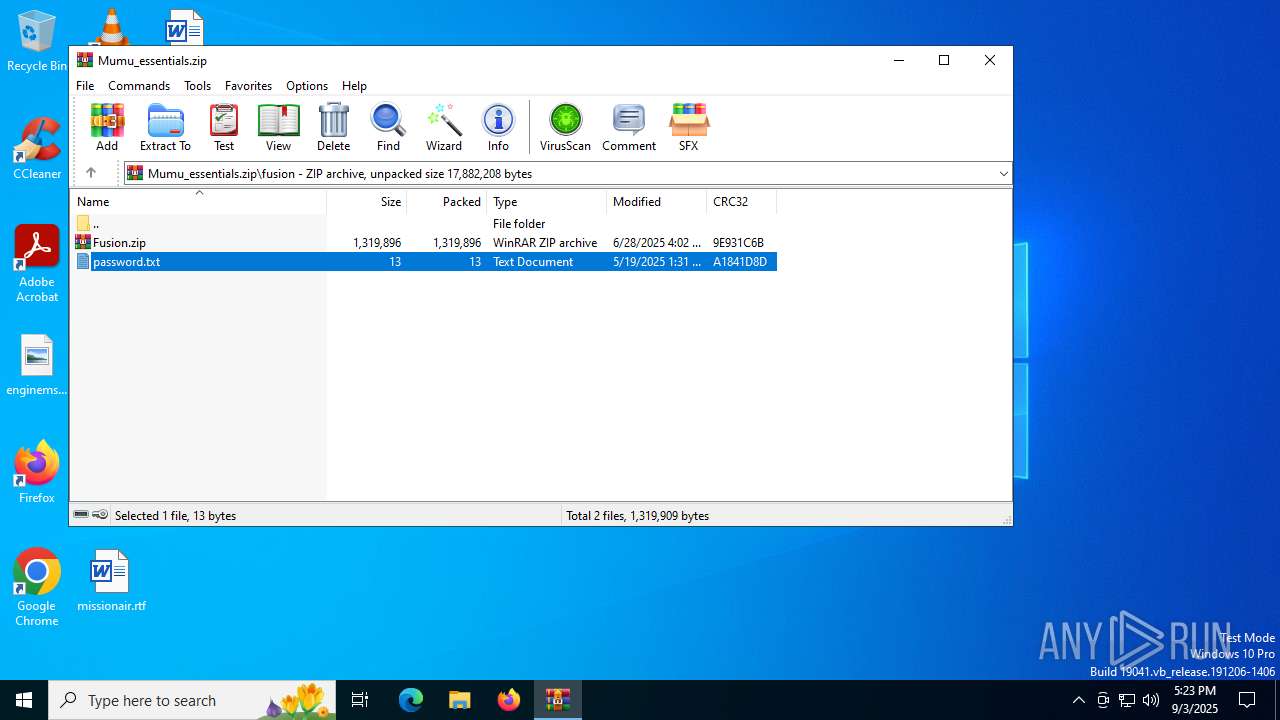
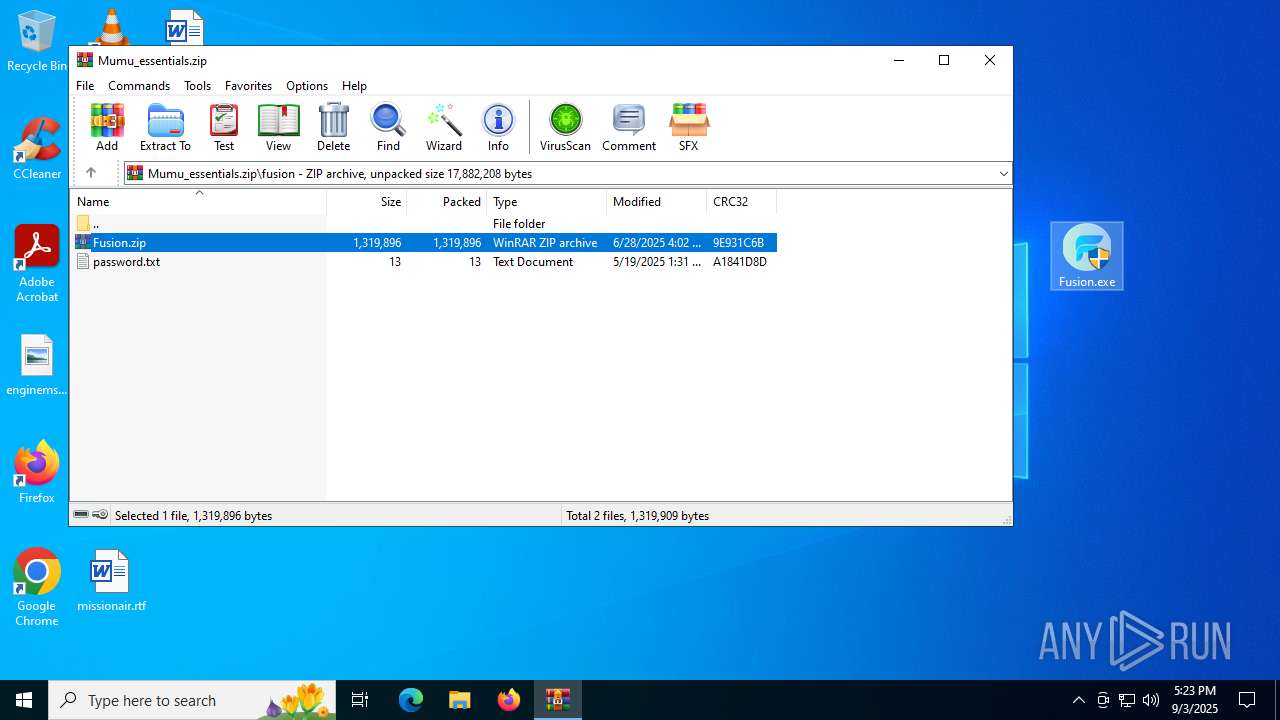
| File name: | Mumu_essentials.zip |
| Full analysis: | https://app.any.run/tasks/13d58699-20c3-48c5-a546-2911ae1ff7d2 |
| Verdict: | Malicious activity |
| Analysis date: | September 03, 2025, 17:22:40 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/zip |
| File info: | Zip archive data, at least v2.0 to extract, compression method=deflate |
| MD5: | 24DC16F9287F55320C1DD4222C25BD3B |
| SHA1: | 1BB99C1651BDF73EC549549D1D147E9D0C336014 |
| SHA256: | 65668FE0F9965A5BCA1AC362658FD09AC51B6FAEF8EF633FCD2E0FC38785ED07 |
| SSDEEP: | 98304:9pAunivpJDY/nePQJVntPZpvv3i1WPrZ96veKiFS0hXezIaGeWr1KLoBkqEXrFgd:0QA4O6sRsYgfXhZHzWBMzOOCmH |
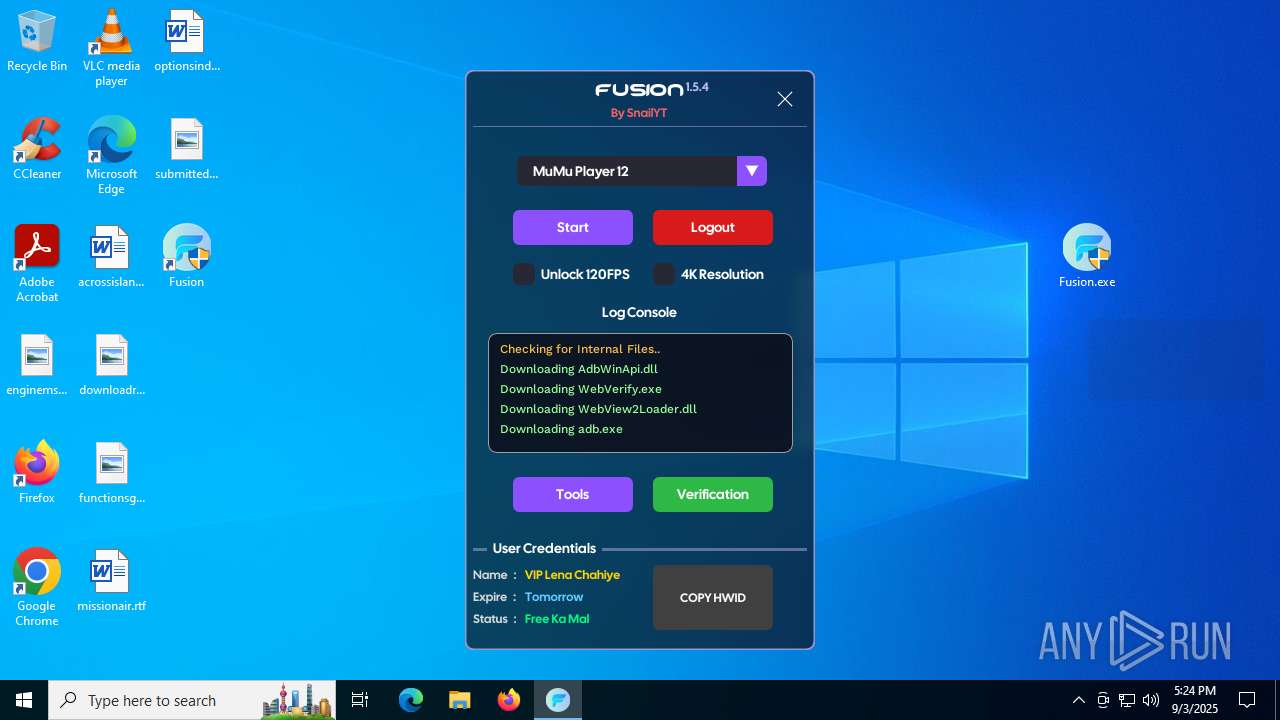
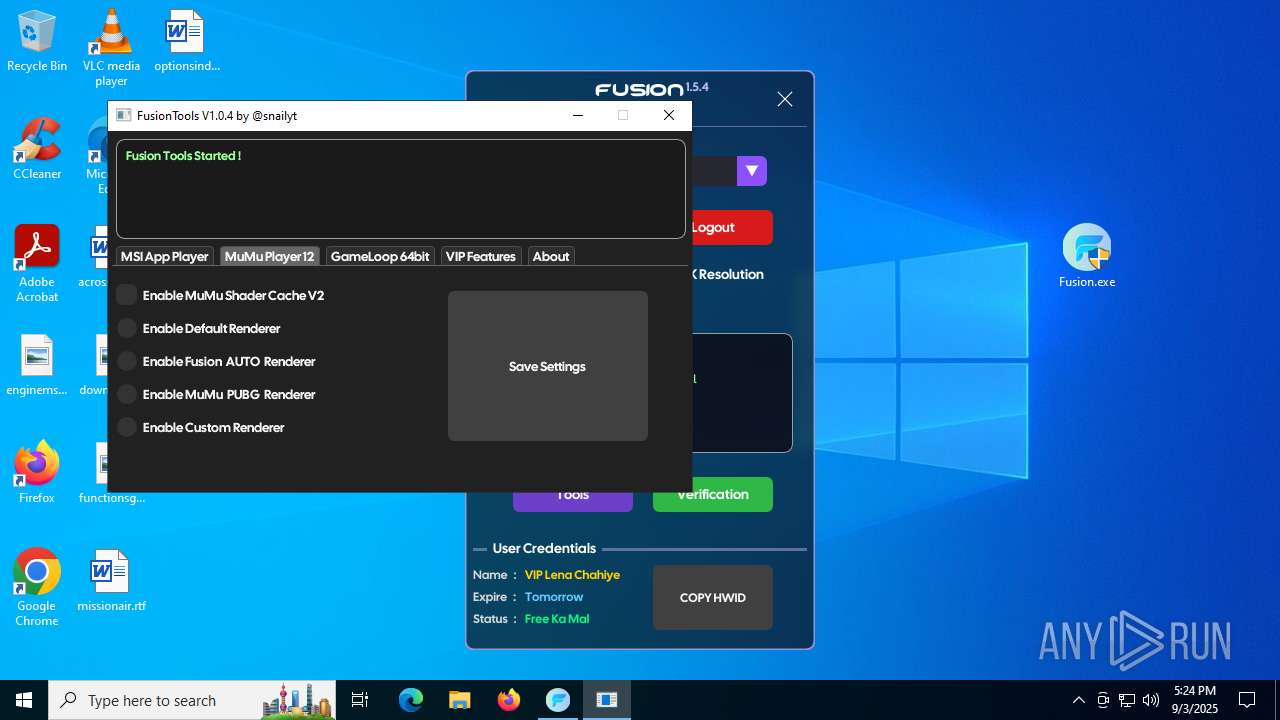
MALICIOUS
Generic archive extractor
- WinRAR.exe (PID: 6680)
SUSPICIOUS
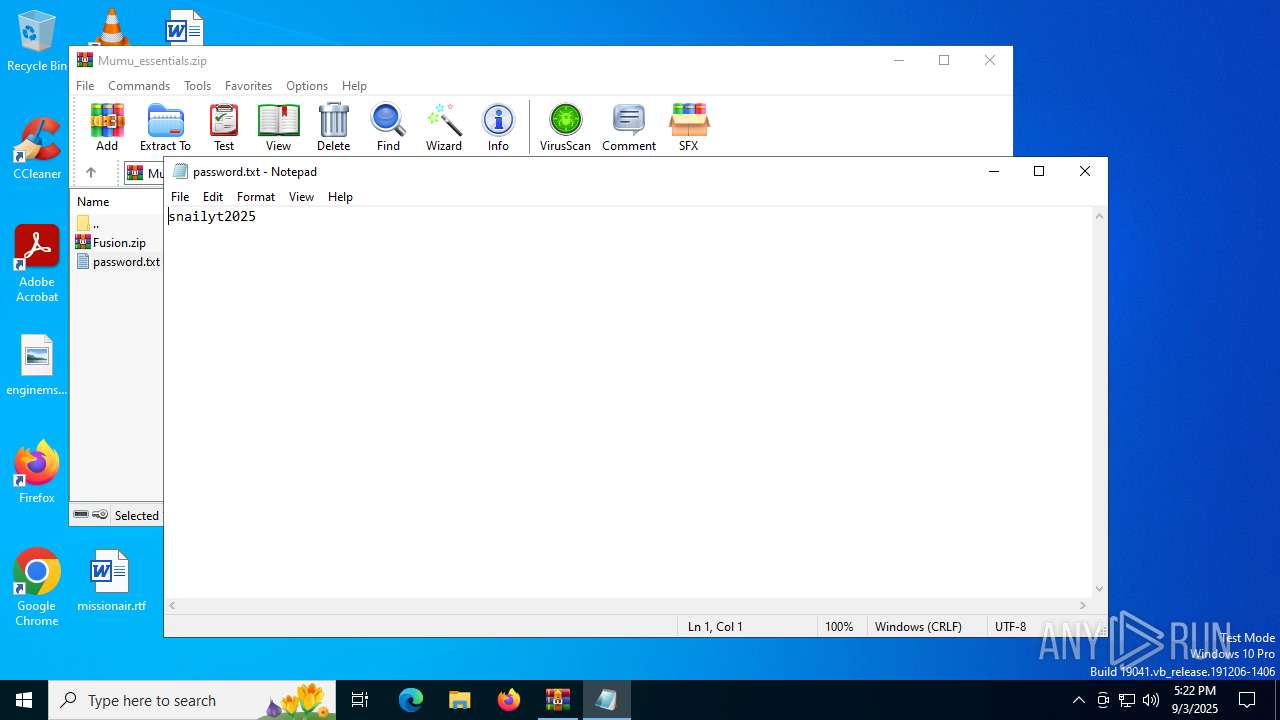
Start notepad (likely ransomware note)
- WinRAR.exe (PID: 6680)
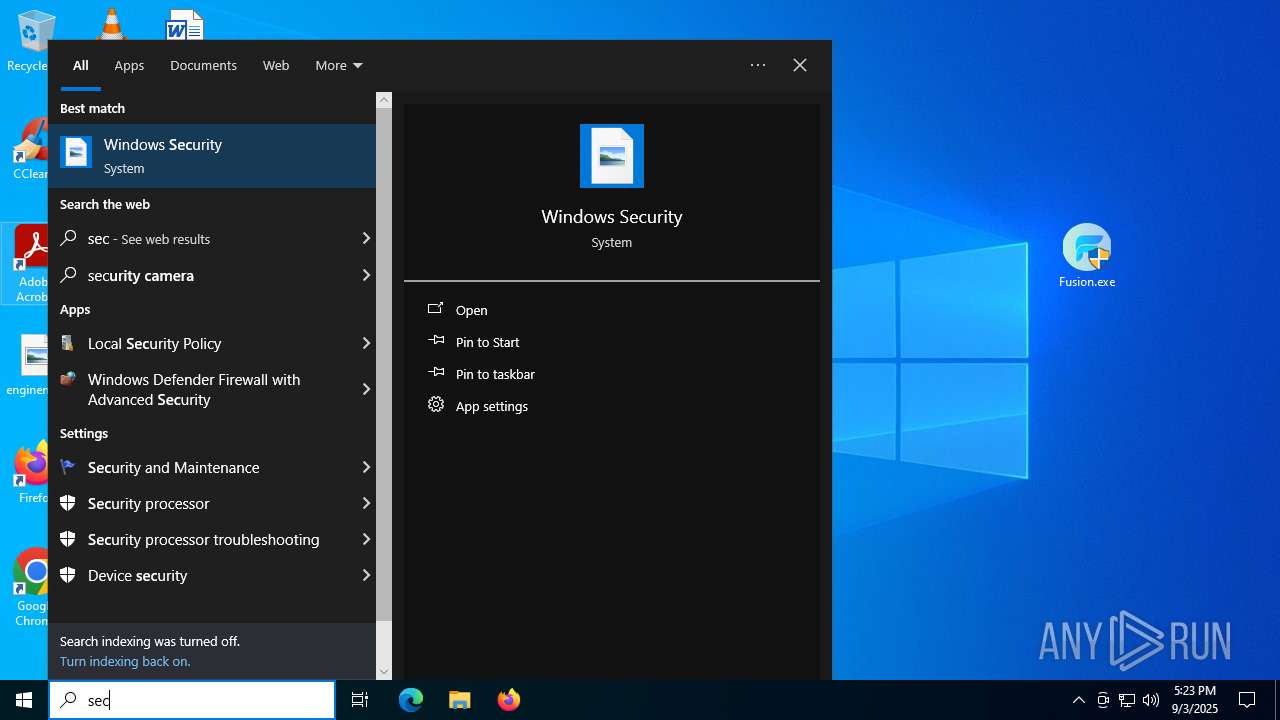
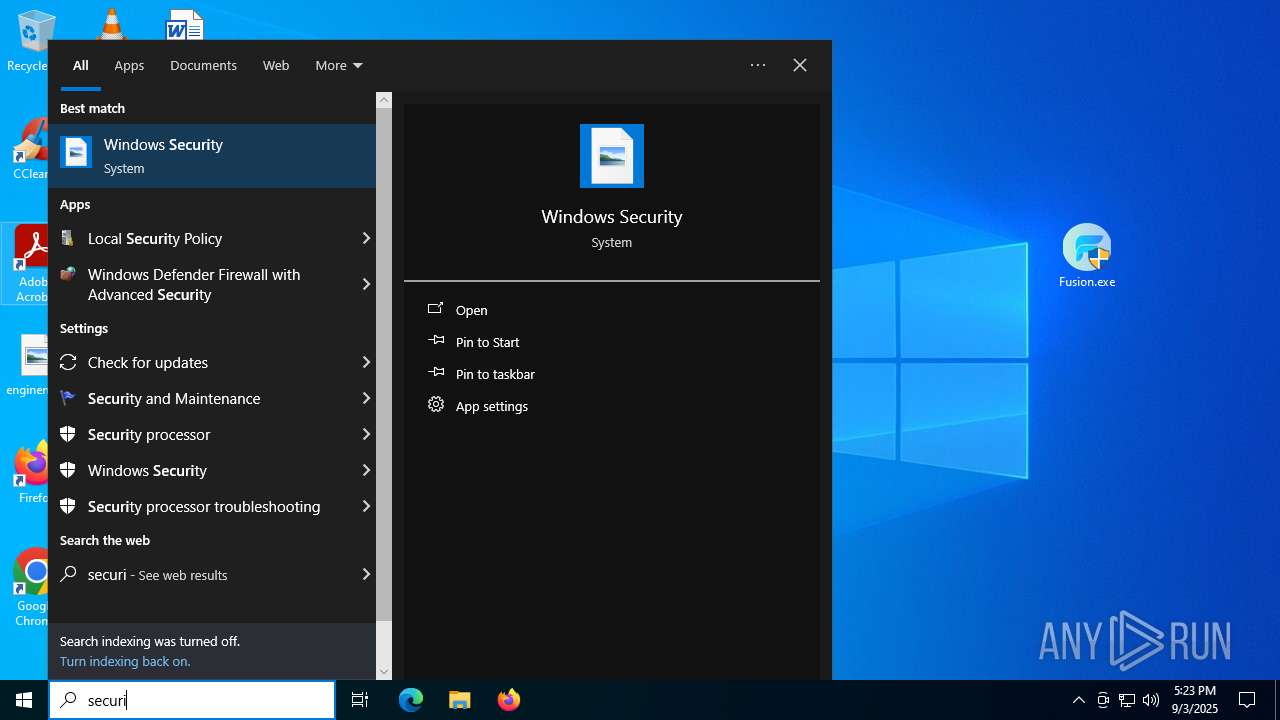
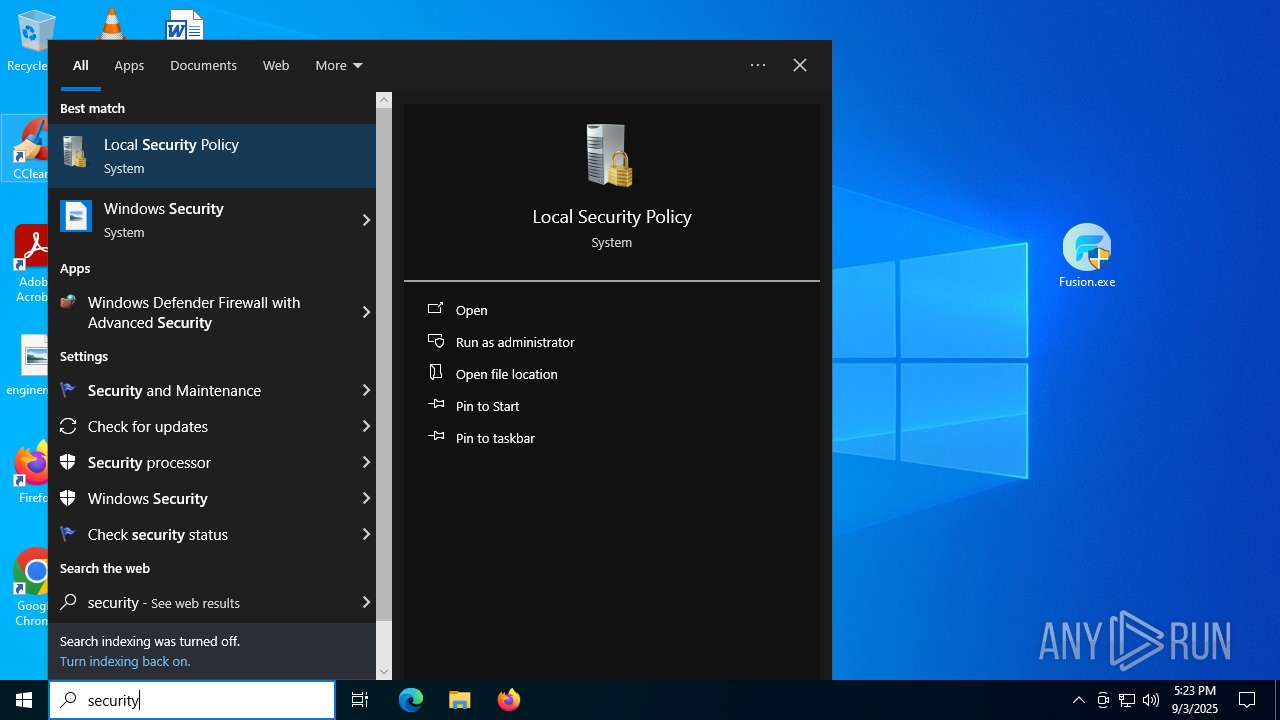
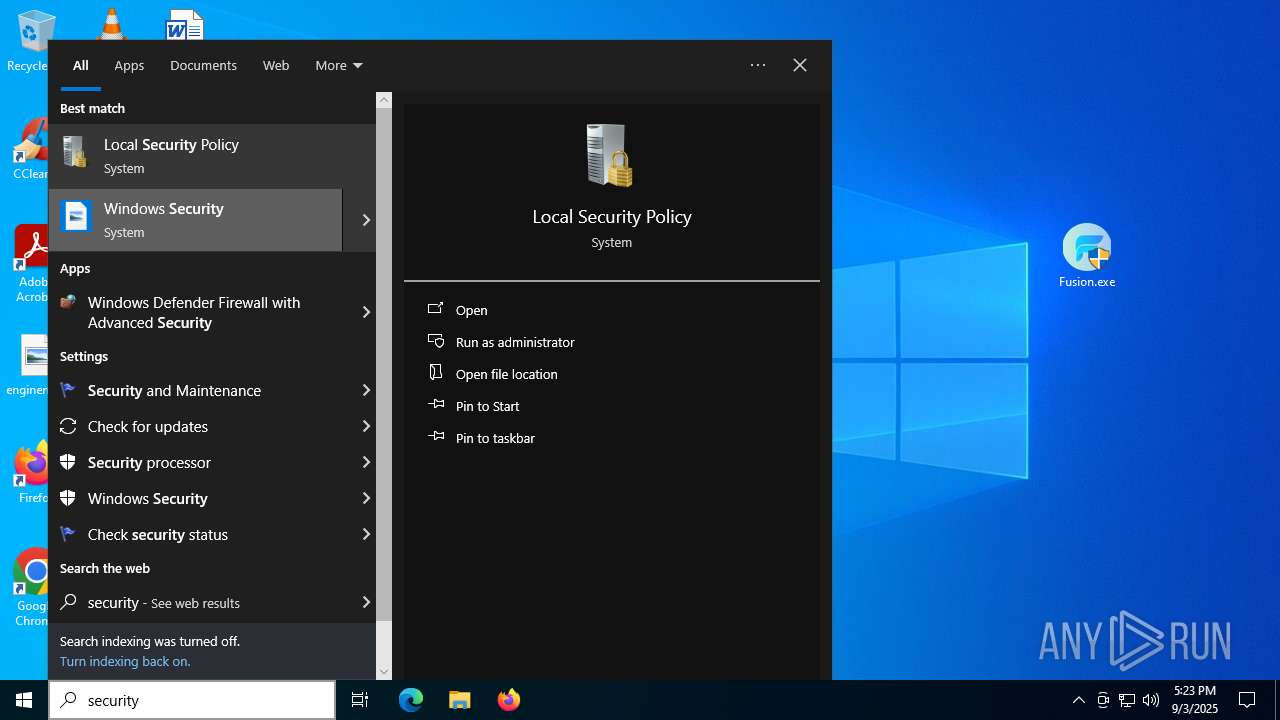
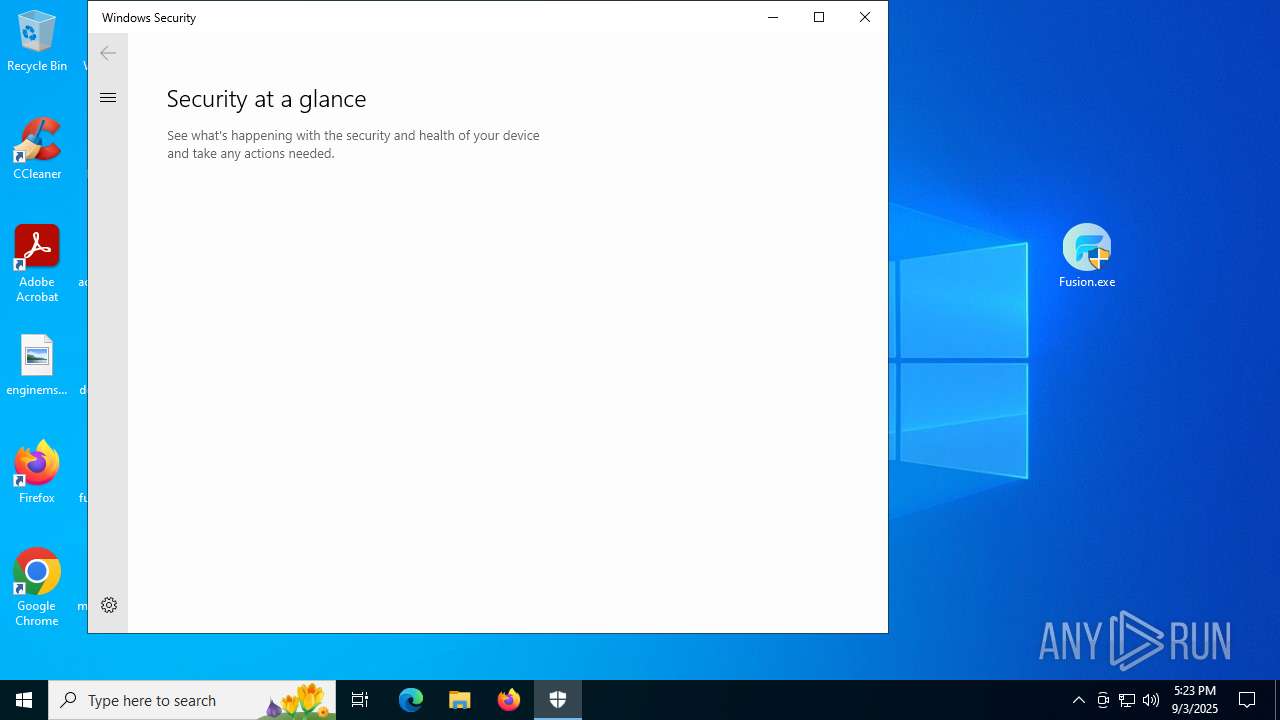
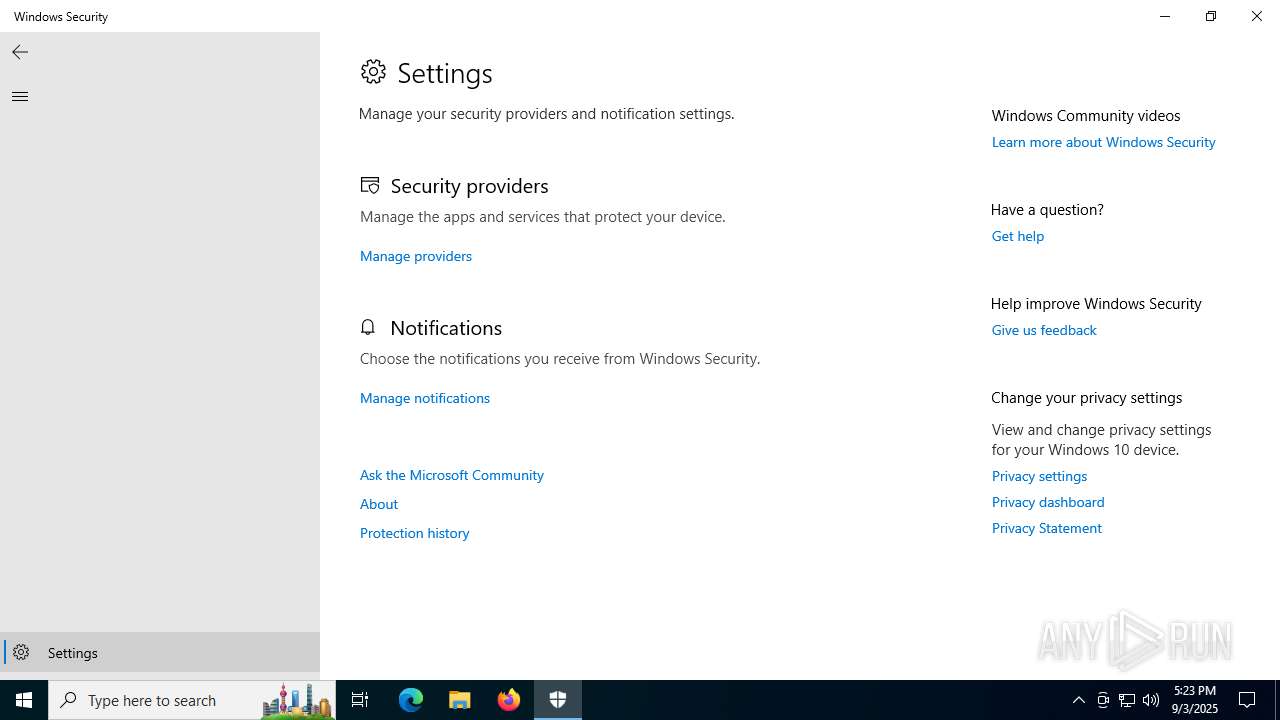
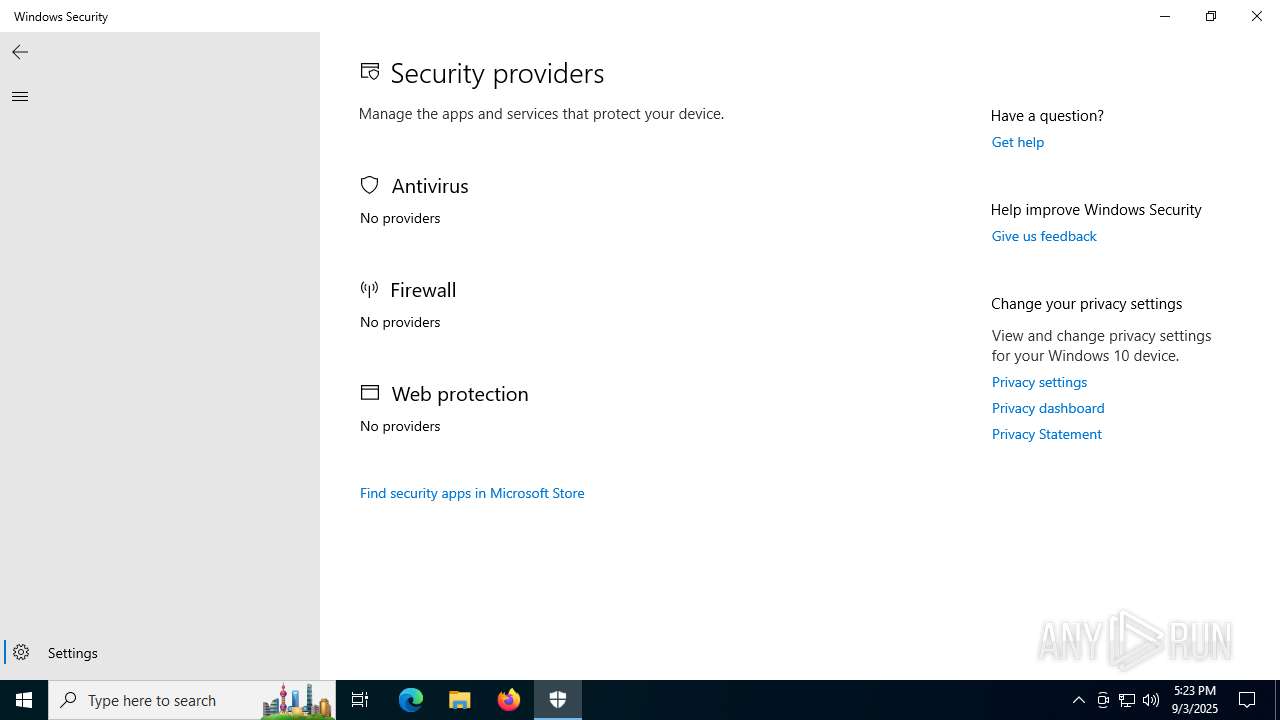
Reads security settings of Internet Explorer
- WinRAR.exe (PID: 6680)
- SecHealthUI.exe (PID: 5780)
- SecHealthUI.exe (PID: 2028)
- Fusion.exe (PID: 4060)
- Fusion.exe (PID: 6648)
- Fusion.exe (PID: 516)
- GameBar.exe (PID: 2064)
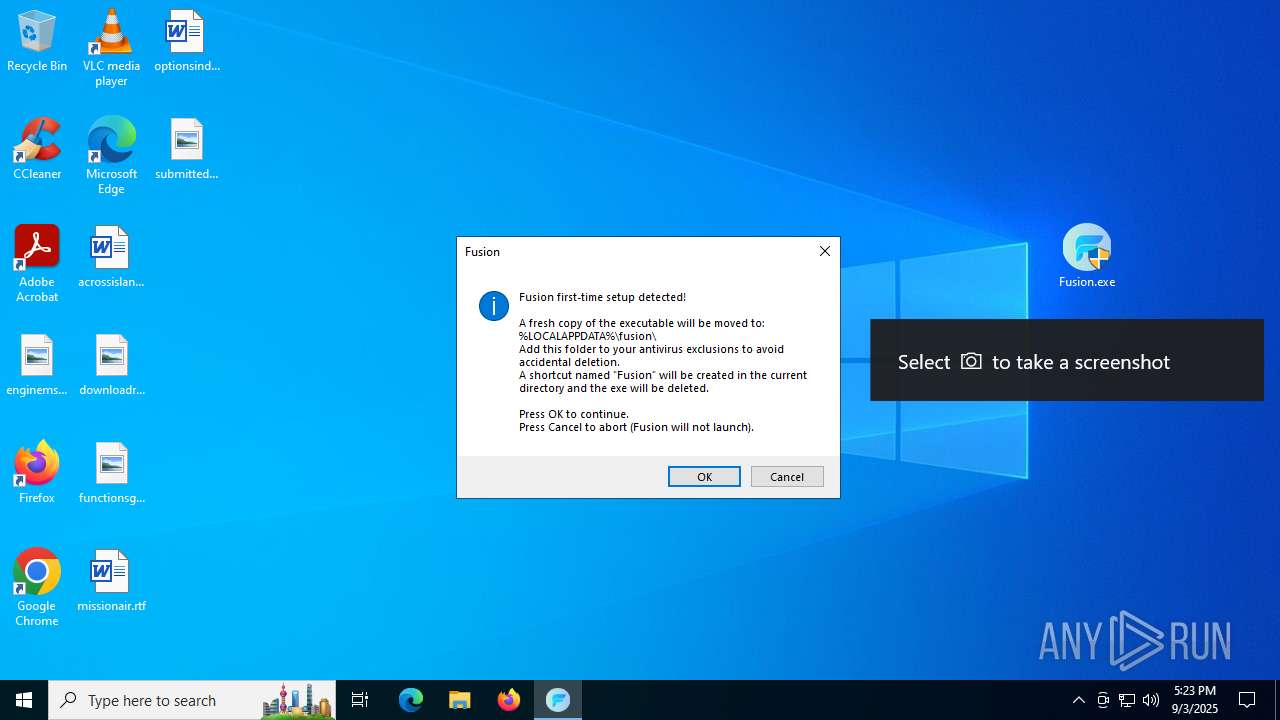
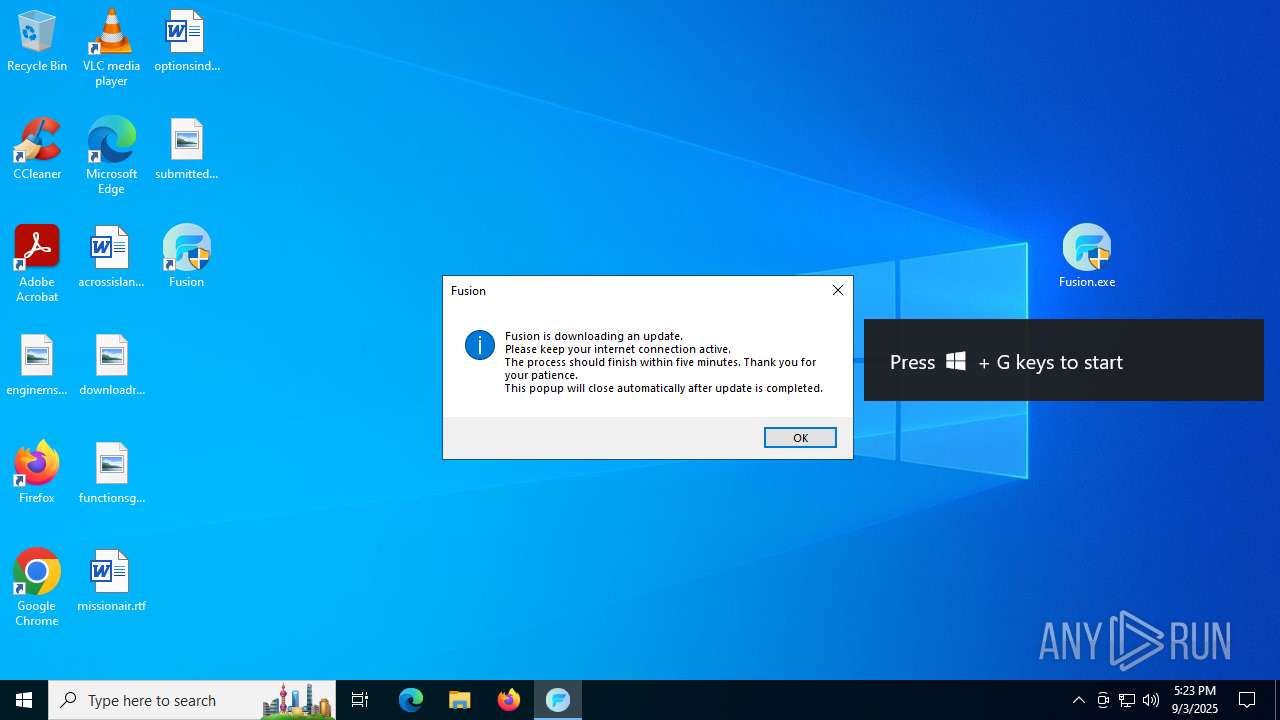
Application launched itself
- WinRAR.exe (PID: 6680)
- Fusion.exe (PID: 2324)
- Fusion.exe (PID: 1472)
- updater.exe (PID: 868)
Starts CMD.EXE for commands execution
- Fusion.exe (PID: 4060)
- Fusion.exe (PID: 6648)
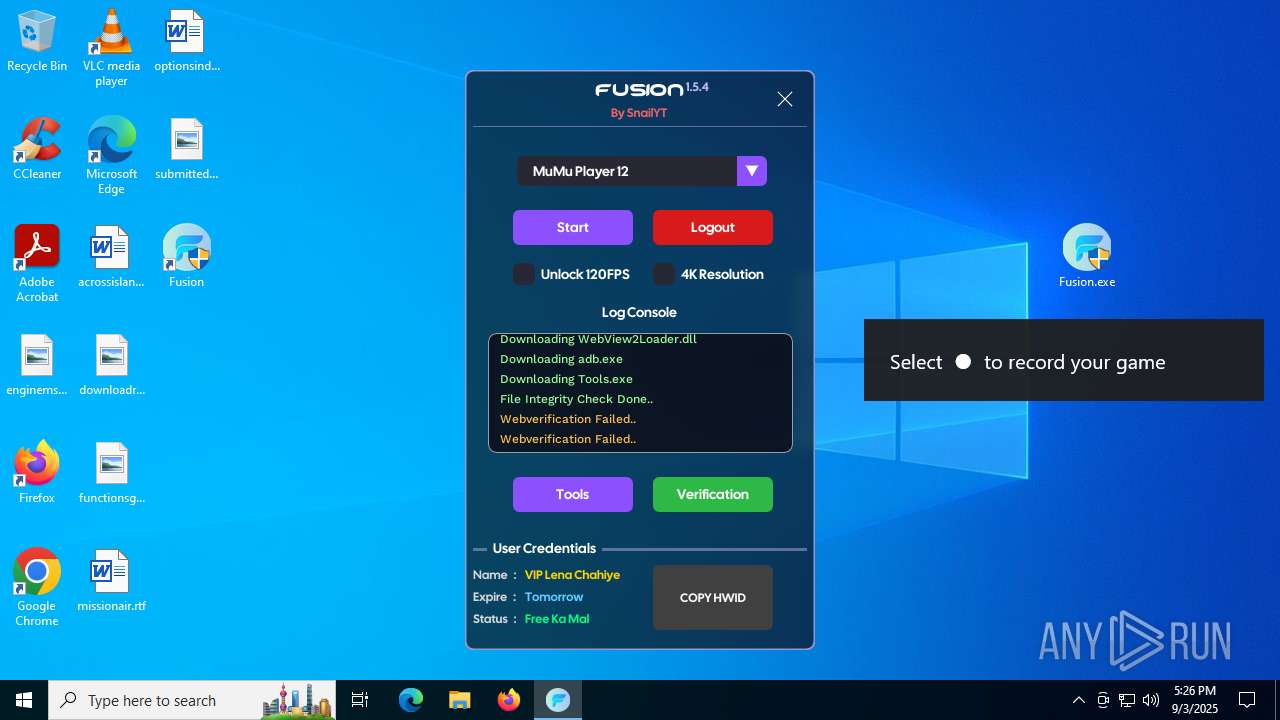
Executable content was dropped or overwritten
- Fusion.exe (PID: 4060)
- Fusion.exe (PID: 6648)
- Fusion.exe (PID: 516)
- cmd.exe (PID: 7064)
Executing commands from a ".bat" file
- Fusion.exe (PID: 4060)
- Fusion.exe (PID: 6648)
The executable file from the user directory is run by the CMD process
- Fusion.exe (PID: 2324)
- Fusion.exe (PID: 1472)
Reads the date of Windows installation
- Fusion.exe (PID: 4060)
- Fusion.exe (PID: 6648)
- Fusion.exe (PID: 516)
Process drops legitimate windows executable
- Fusion.exe (PID: 516)
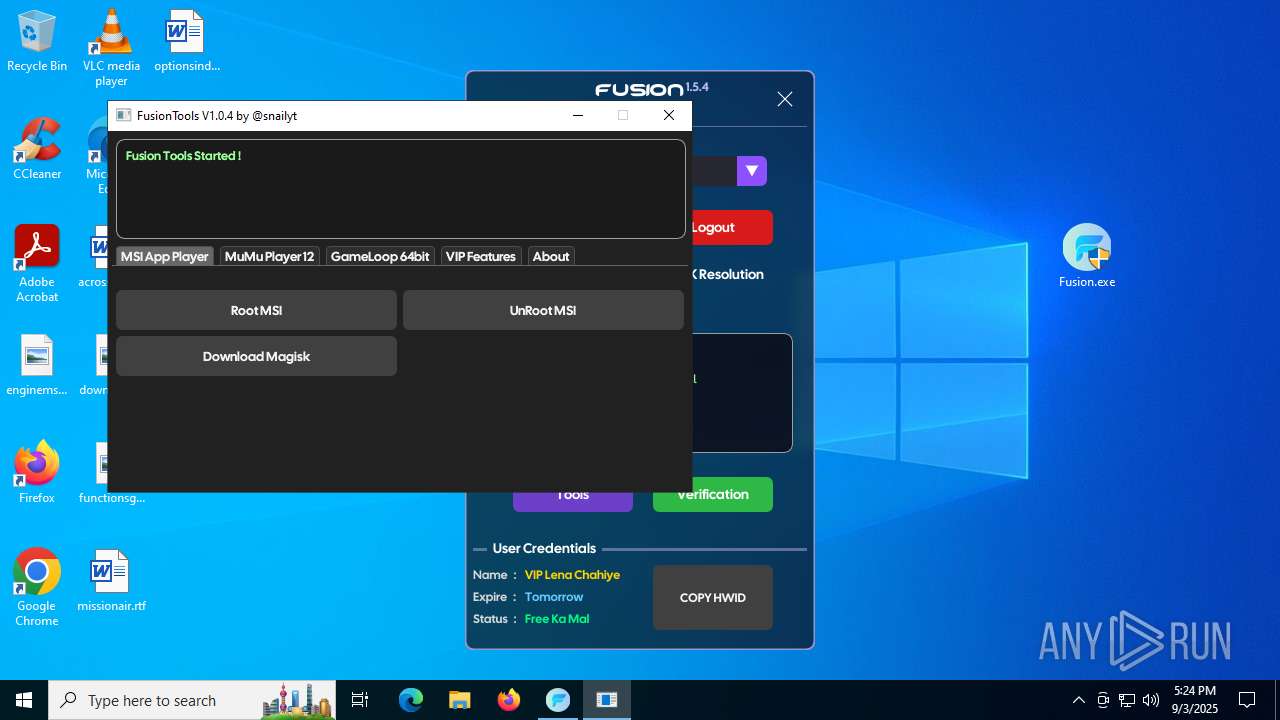
Executes application which crashes
- Tools.exe (PID: 6688)
The process executes via Task Scheduler
- updater.exe (PID: 868)
Uses TASKKILL.EXE to kill process
- cmd.exe (PID: 7064)
INFO
Reads Microsoft Office registry keys
- WinRAR.exe (PID: 6680)
Reads security settings of Internet Explorer
- notepad.exe (PID: 6212)
Reads the computer name
- SecHealthUI.exe (PID: 5780)
- GameBar.exe (PID: 2064)
- SecHealthUI.exe (PID: 2028)
- Fusion.exe (PID: 4060)
- Fusion.exe (PID: 6648)
- Fusion.exe (PID: 516)
- Tools.exe (PID: 6688)
- WebVerify.exe (PID: 5960)
- WebVerify.exe (PID: 1232)
- updater.exe (PID: 868)
- WebVerify.exe (PID: 6208)
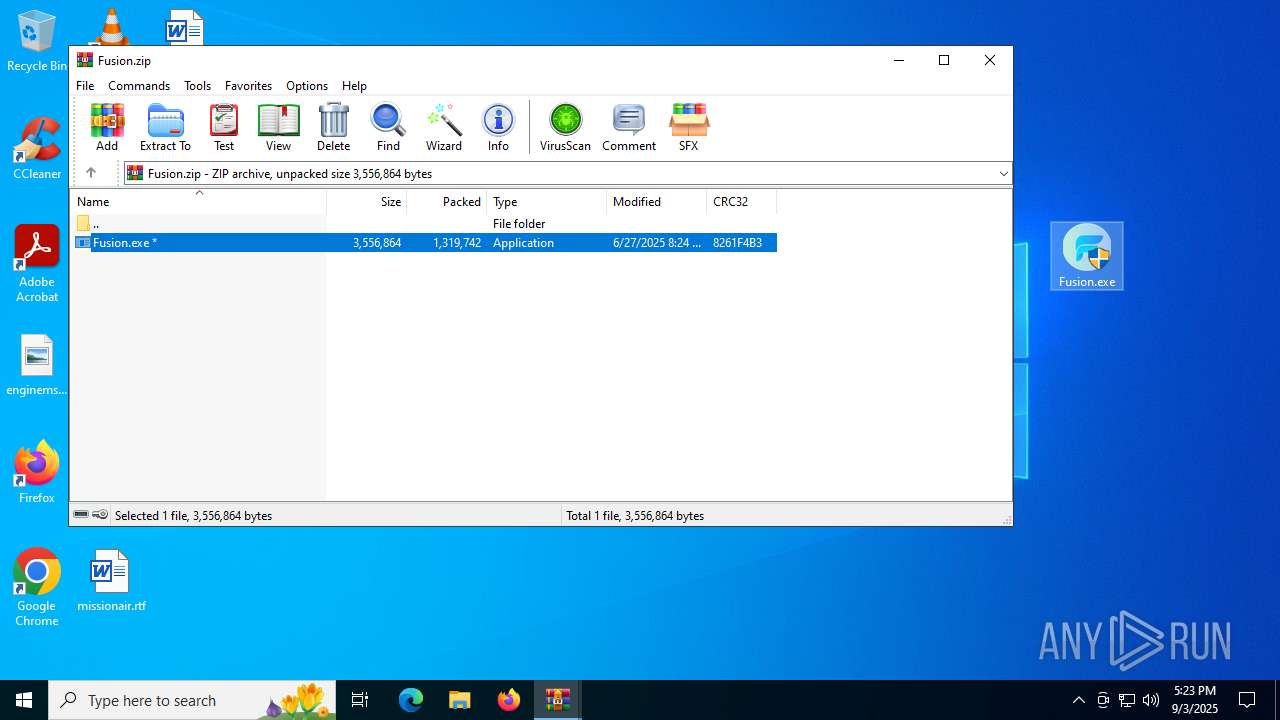
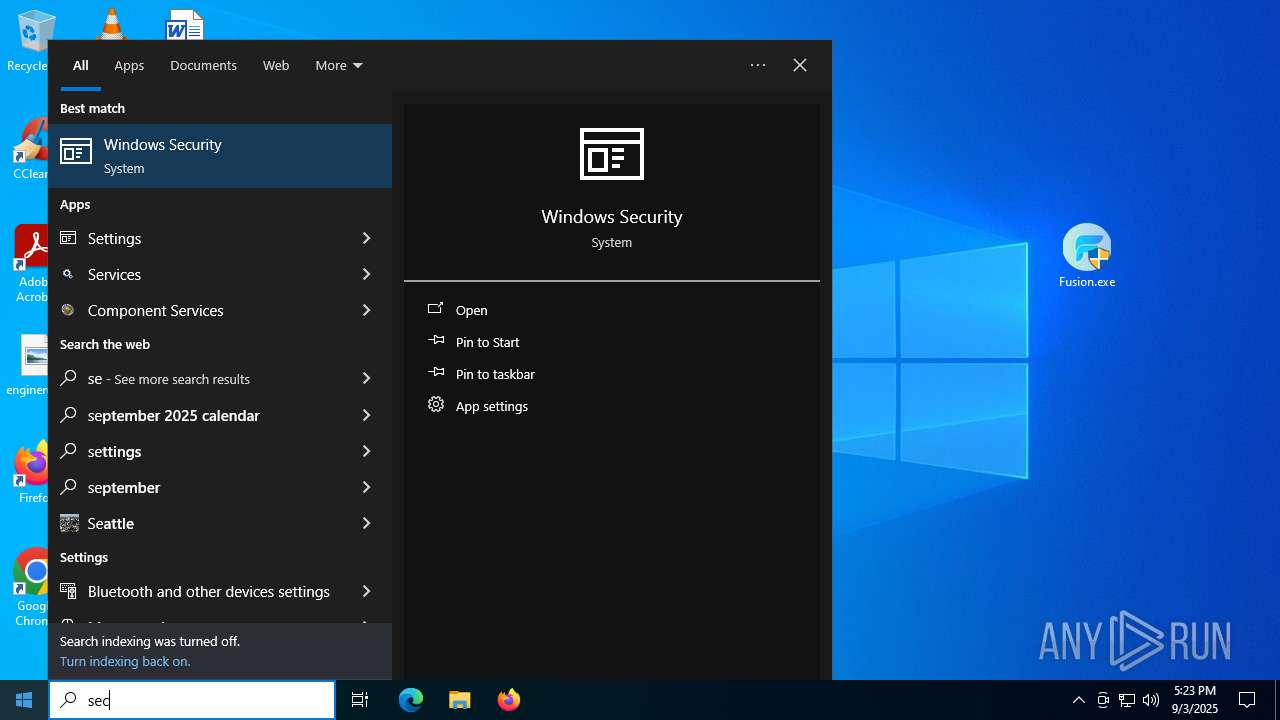
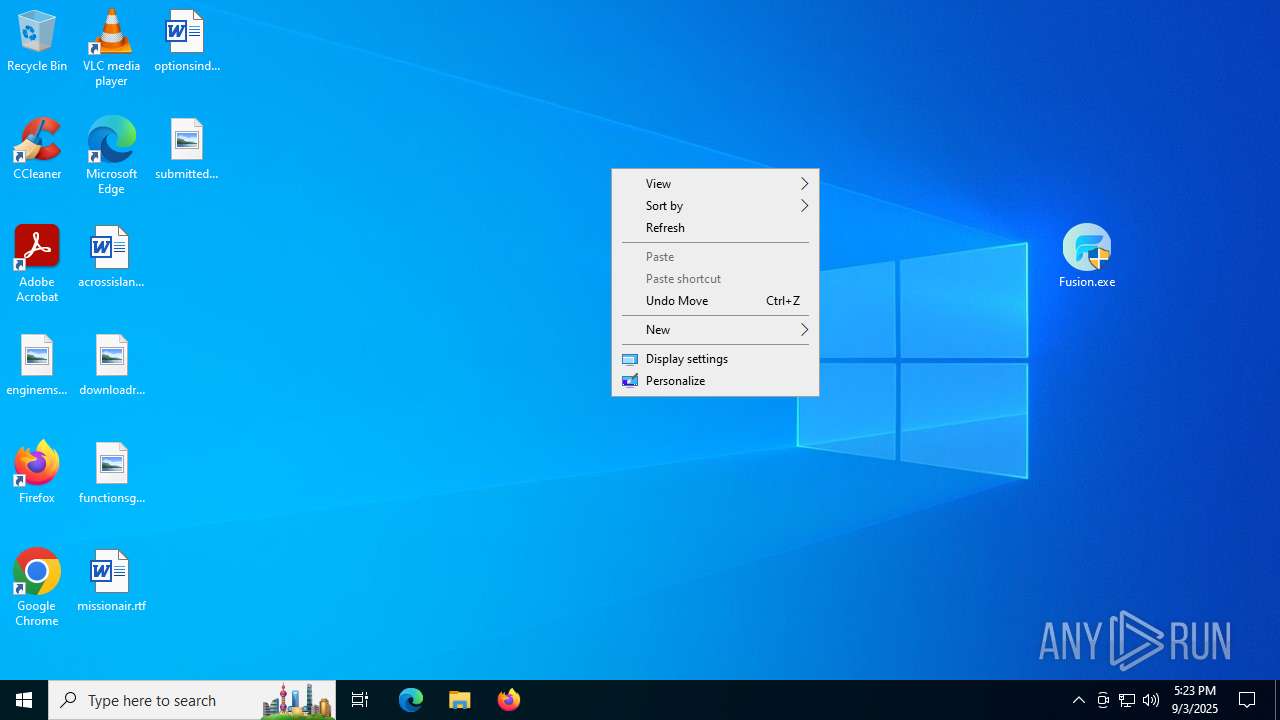
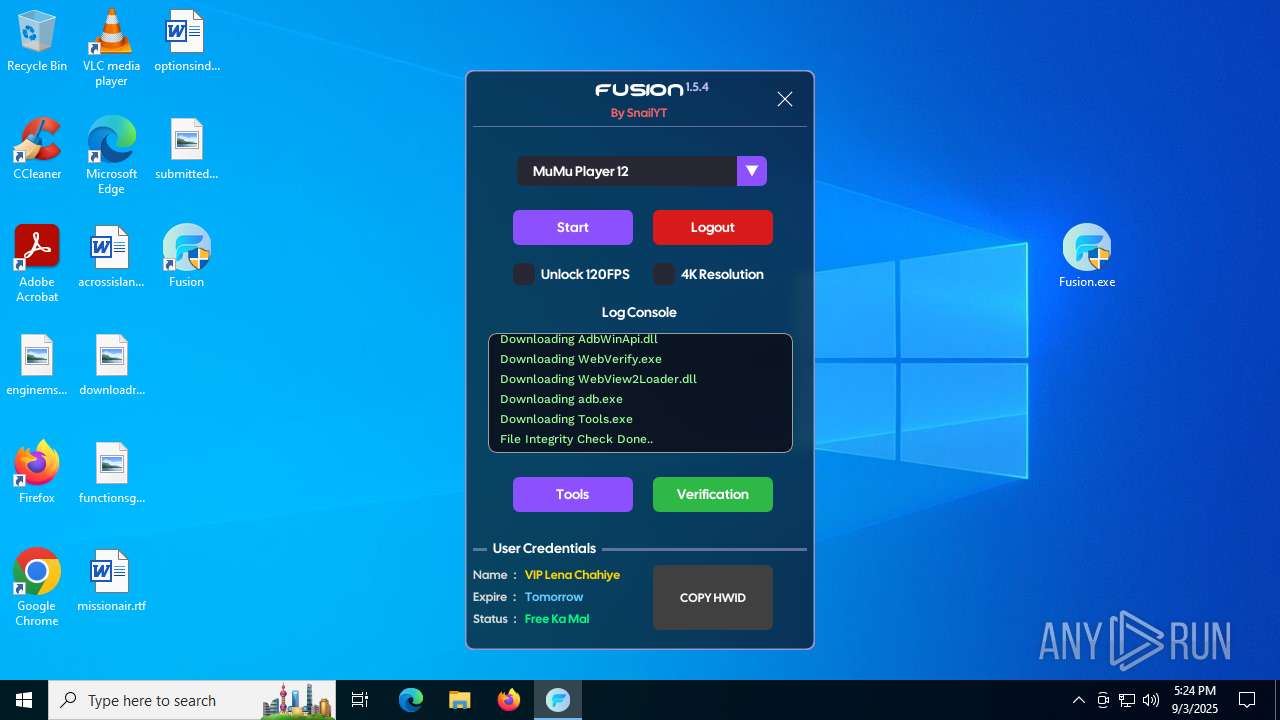
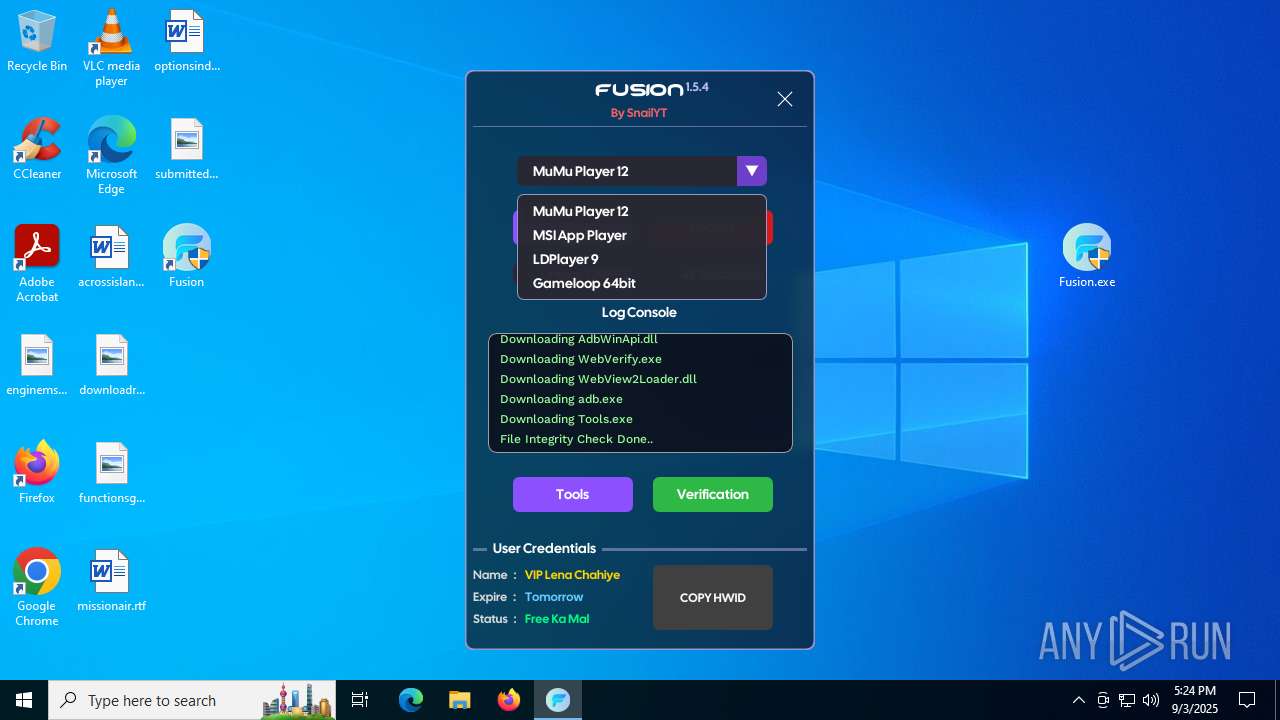
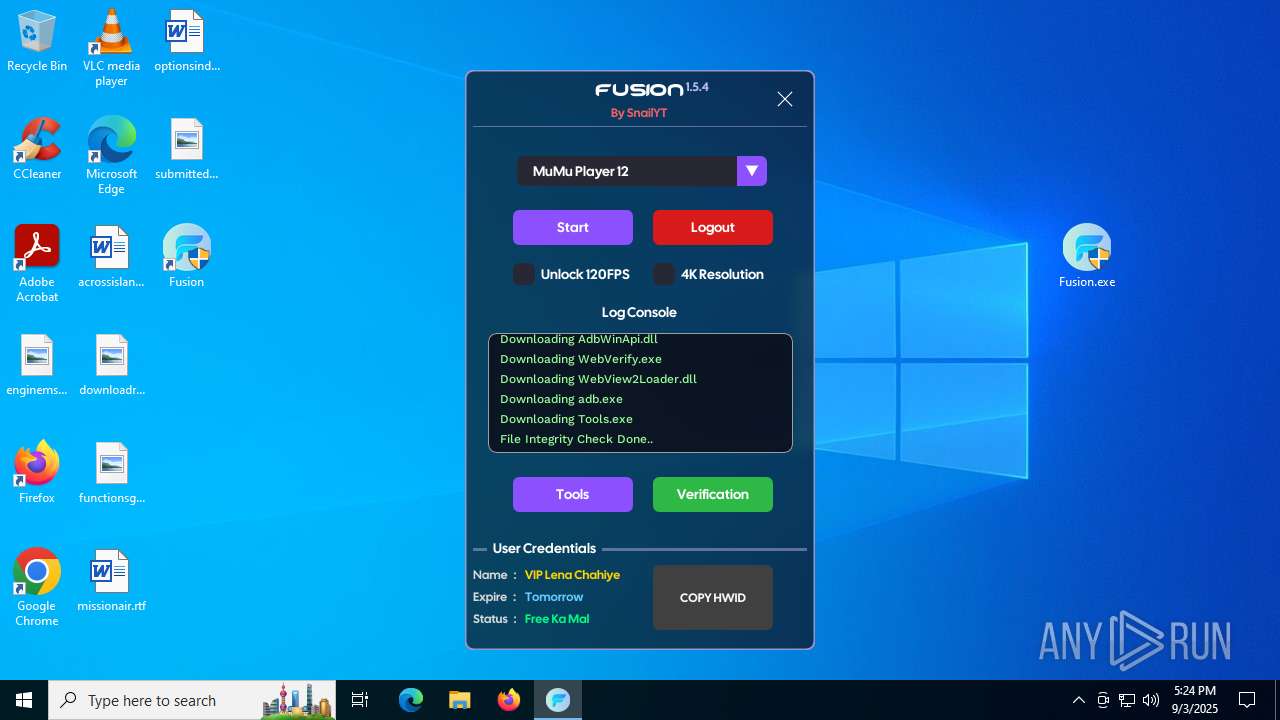
Manual execution by a user
- Fusion.exe (PID: 7124)
- Fusion.exe (PID: 4060)
Create files in a temporary directory
- Fusion.exe (PID: 4060)
Checks supported languages
- SecHealthUI.exe (PID: 2028)
- SecHealthUI.exe (PID: 5780)
- Fusion.exe (PID: 4060)
- GameBar.exe (PID: 2064)
- Fusion.exe (PID: 6648)
- Fusion.exe (PID: 2324)
- Fusion.exe (PID: 1472)
- Fusion.exe (PID: 516)
- Tools.exe (PID: 6688)
- WebVerify.exe (PID: 5960)
- WebVerify.exe (PID: 1232)
- updater.exe (PID: 868)
- updater.exe (PID: 6820)
- WebVerify.exe (PID: 6208)
Executable content was dropped or overwritten
- WinRAR.exe (PID: 828)
Creates files or folders in the user directory
- Fusion.exe (PID: 4060)
- Fusion.exe (PID: 6648)
- Fusion.exe (PID: 516)
- WerFault.exe (PID: 5712)
Process checks computer location settings
- Fusion.exe (PID: 4060)
- Fusion.exe (PID: 516)
- Fusion.exe (PID: 6648)
Reads the software policy settings
- Fusion.exe (PID: 6648)
- Fusion.exe (PID: 516)
- WerFault.exe (PID: 5712)
- slui.exe (PID: 4800)
Reads the machine GUID from the registry
- Fusion.exe (PID: 6648)
- Fusion.exe (PID: 516)
Checks proxy server information
- Fusion.exe (PID: 6648)
- Fusion.exe (PID: 516)
- WerFault.exe (PID: 5712)
- slui.exe (PID: 4800)
The sample compiled with english language support
- Fusion.exe (PID: 516)
Process checks whether UAC notifications are on
- updater.exe (PID: 868)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .zip | | | ZIP compressed archive (100) |
|---|
EXIF
ZIP
| ZipRequiredVersion: | 20 |
|---|---|
| ZipBitFlag: | - |
| ZipCompression: | Deflated |
| ZipModifyDate: | 2025:05:06 01:05:58 |
| ZipCRC: | 0x6e016e1c |
| ZipCompressedSize: | 6373 |
| ZipUncompressedSize: | 34134 |
| ZipFileName: | Aio by RoaR.bat |
Total processes
186
Monitored processes
30
Malicious processes
0
Suspicious processes
5
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 516 | "C:\Users\admin\AppData\Local\fusion\Fusion.exe" | C:\Users\admin\AppData\Local\fusion\Fusion.exe | Fusion.exe | ||||||||||||
User: admin Integrity Level: HIGH Modules
| |||||||||||||||
| 828 | "C:\Program Files\WinRAR\WinRAR.exe" C:\Users\admin\AppData\Local\Temp\Rar$DIa6680.31918\Fusion.zip | C:\Program Files\WinRAR\WinRAR.exe | WinRAR.exe | ||||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.91.0 Modules
| |||||||||||||||
| 868 | "C:\Program Files (x86)\Google\GoogleUpdater\134.0.6985.0\updater.exe" --wake --system | C:\Program Files (x86)\Google\GoogleUpdater\134.0.6985.0\updater.exe | — | svchost.exe | |||||||||||
User: SYSTEM Company: Google LLC Integrity Level: SYSTEM Description: Google Updater Exit code: 0 Version: 134.0.6985.0 Modules
| |||||||||||||||
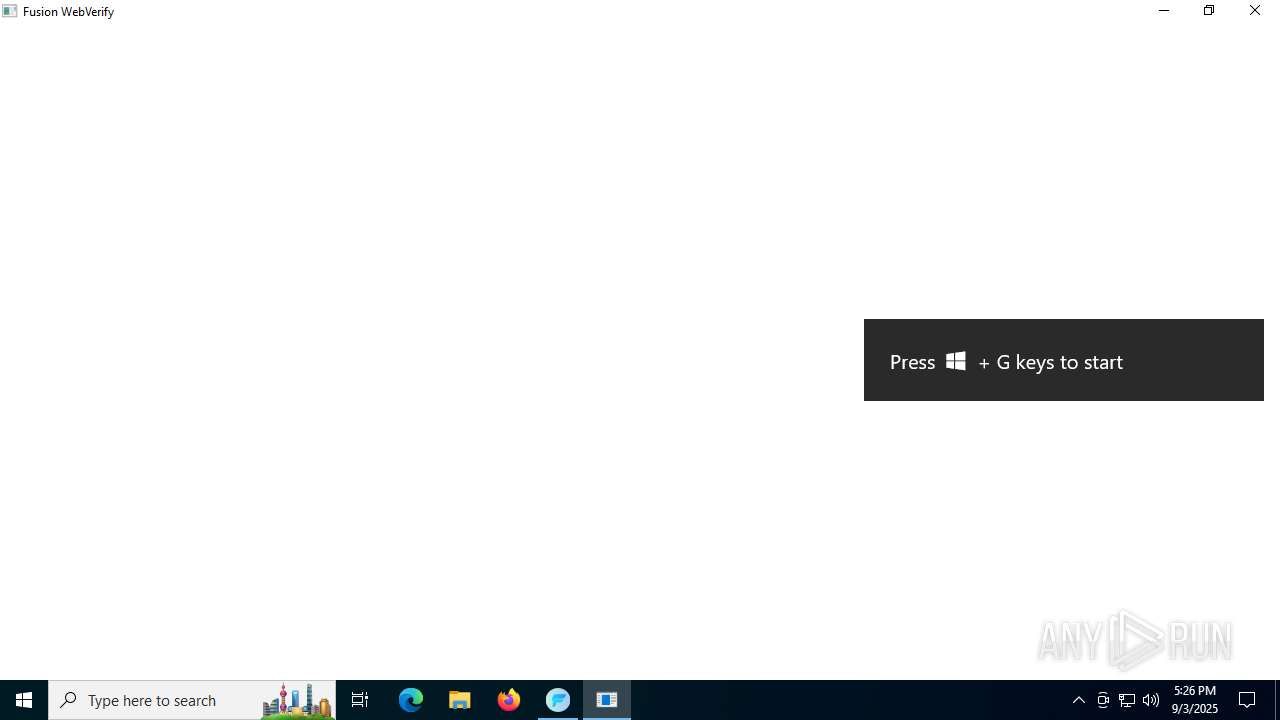
| 1232 | "WebVerify.exe" --ticket=0x33FD7124 | C:\Users\admin\AppData\Local\fusion\WebVerify.exe | Fusion.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 1472 | Fusion.exe | C:\Users\admin\AppData\Local\fusion\Fusion.exe | — | cmd.exe | |||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 1560 | C:\Windows\System32\SecurityHealthHost.exe {E041C90B-68BA-42C9-991E-477B73A75C90} -Embedding | C:\Windows\System32\SecurityHealthHost.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Security Health Host Exit code: 0 Version: 4.18.1907.16384 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2028 | "C:\WINDOWS\SystemApps\Microsoft.Windows.SecHealthUI_cw5n1h2txyewy\SecHealthUI.exe" -ServerName:SecHealthUI.AppXep4x2tbtjws1v9qqs0rmb3hxykvkpqtn.mca | C:\Windows\SystemApps\Microsoft.Windows.SecHealthUI_cw5n1h2txyewy\SecHealthUI.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Defender application Exit code: 1 Version: 10.0.19041.3758 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2064 | "C:\Program Files\WindowsApps\Microsoft.XboxGamingOverlay_2.34.28001.0_x64__8wekyb3d8bbwe\GameBar.exe" -ServerName:App.AppXbdkk0yrkwpcgeaem8zk81k8py1eaahny.mca | C:\Program Files\WindowsApps\Microsoft.XboxGamingOverlay_2.34.28001.0_x64__8wekyb3d8bbwe\GameBar.exe | — | svchost.exe | |||||||||||
User: admin Integrity Level: MEDIUM Modules
| |||||||||||||||
| 2324 | "C:\Users\admin\AppData\Local\fusion\Fusion.exe" | C:\Users\admin\AppData\Local\fusion\Fusion.exe | — | cmd.exe | |||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 3288 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
14 562
Read events
14 467
Write events
92
Delete events
3
Modification events
| (PID) Process: | (6680) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 3 |
Value: C:\Users\admin\Desktop\preferences.zip | |||
| (PID) Process: | (6680) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 2 |
Value: C:\Users\admin\Desktop\chromium_ext.zip | |||
| (PID) Process: | (6680) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 1 |
Value: C:\Users\admin\Desktop\omni_23_10_2024_.zip | |||
| (PID) Process: | (6680) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\Downloads\Mumu_essentials.zip | |||
| (PID) Process: | (6680) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (6680) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (6680) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (6680) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (6680) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Explorer\FileExts\.txt\OpenWithProgids |
| Operation: | write | Name: | txtfile |
Value: | |||
| (PID) Process: | (828) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 3 |
Value: C:\Users\admin\Desktop\chromium_ext.zip | |||
Executable files
9
Suspicious files
17
Text files
6
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 6648 | Fusion.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\07CEF2F654E3ED6050FFC9B6EB844250_3431D4C539FB2CFCB781821E9902850D | binary | |
MD5:6DA2E83CF13E1121527F1C027EFC341C | SHA256:2CB658D6DC7D9C6A4E67AEDD7318FFFF2D24F79405872308031389D967DFC123 | |||
| 6648 | Fusion.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\D9CA54E0FA212456E1DB00704A97658E | binary | |
MD5:4C0B0DE3B4BCAC14E8A5C46EC0C6E8CB | SHA256:4DF15B5B3B166CC1C24C5FD3095625E61622DCF9DC867442D0BEE39F6A22518E | |||
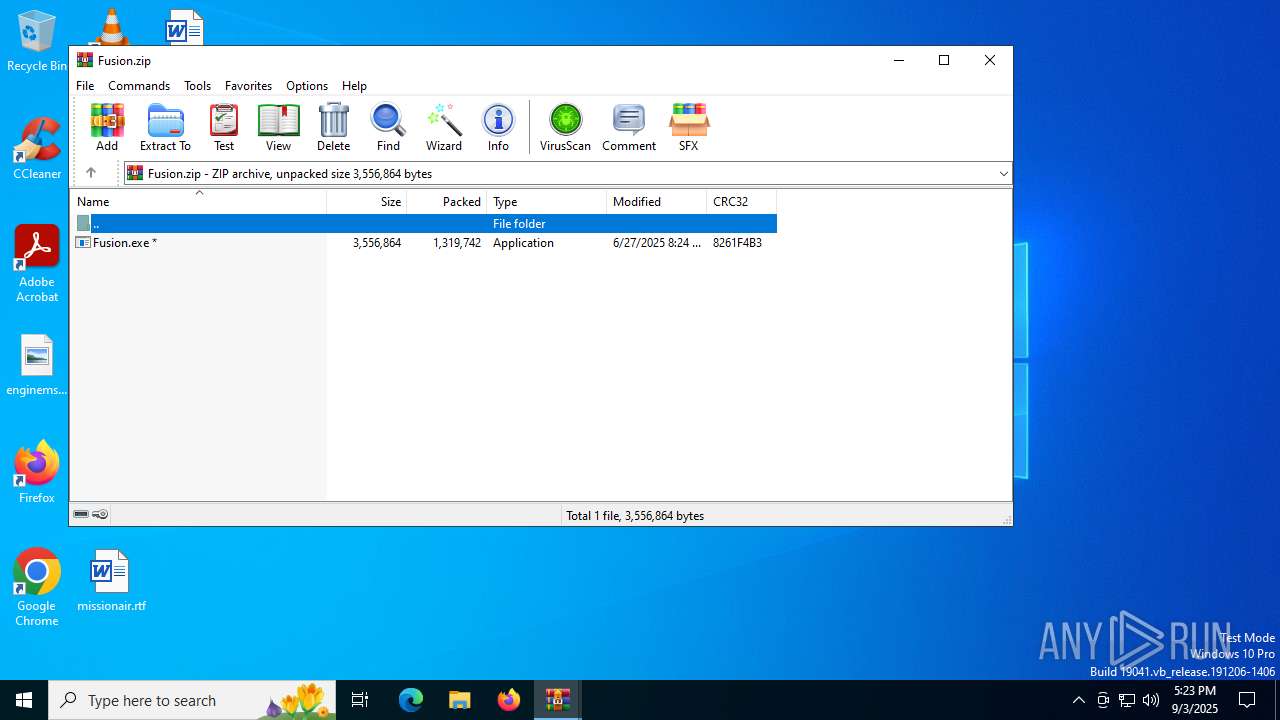
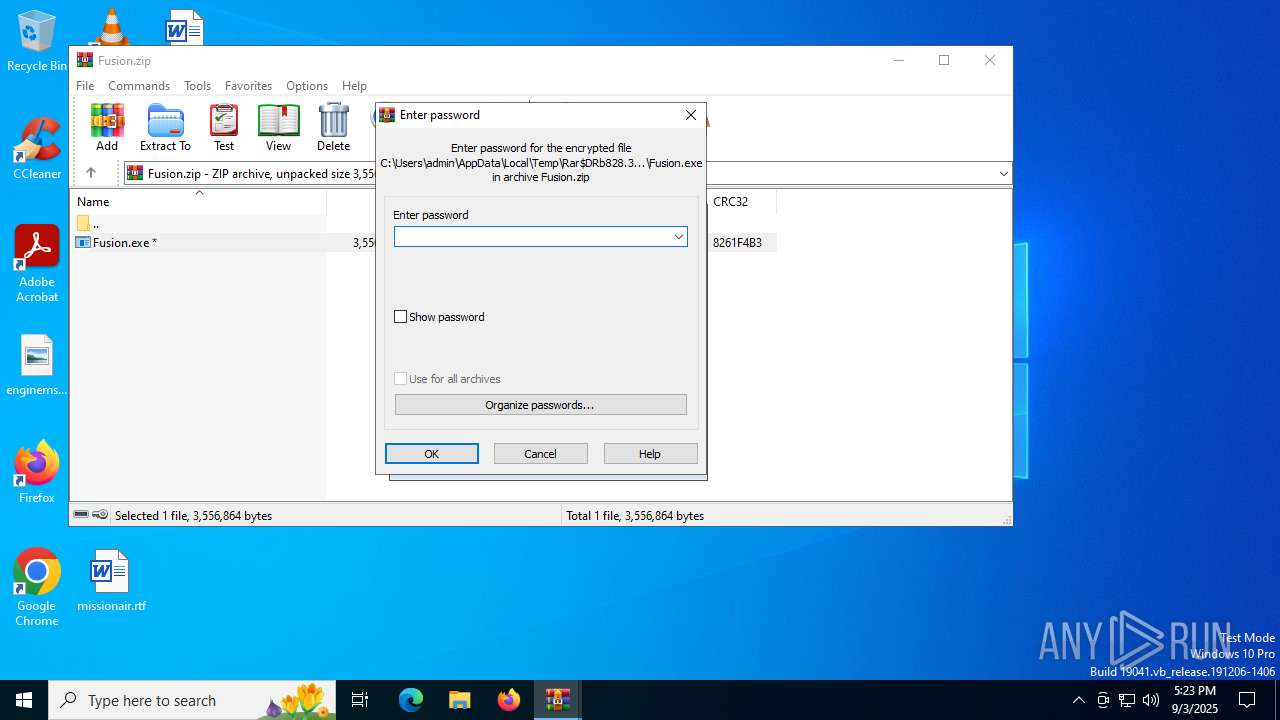
| 6680 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DIa6680.31918\Fusion.zip | compressed | |
MD5:728E900AB6C2D63EFF8CA0D986919E32 | SHA256:D6761C28CF099BE9E53602F4D4F4A6E36E797D76959766C167DD30EEE7E33ABE | |||
| 6648 | Fusion.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\07CEF2F654E3ED6050FFC9B6EB844250_3431D4C539FB2CFCB781821E9902850D | binary | |
MD5:80B36A260B74EEFE0910AC251F1F0240 | SHA256:3EF7201F33C97932E59F490C0CE9155C3B336C642E4A403B74BED4E8A4961FDC | |||
| 4060 | Fusion.exe | C:\Users\admin\AppData\Local\fusion\Fusion.exe | executable | |
MD5:422E4D3B6CCD200F3C0DF013306BE122 | SHA256:4823D20B933C5530BCFA52C9182FFB1C388B7B8472C6F4378B90E855B8E580D6 | |||
| 6648 | Fusion.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\D9CA54E0FA212456E1DB00704A97658E | binary | |
MD5:8EFC6F187521A0AC7A8E14EF15BDA1B3 | SHA256:A9D367C9003ECE05E7524BB91520F6453EE1B541CA957C4A59D9A2319298DC7A | |||
| 6648 | Fusion.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\B2FAF7692FD9FFBD64EDE317E42334BA_89854CA6A0F0936A4D2ECA78845CEA25 | binary | |
MD5:3AA222D7ABCC490F363B4C5245FED18A | SHA256:AE038F3594ABA0202932168D217B415DE9E02C9DE236C5314B423A8ECAD6083C | |||
| 6648 | Fusion.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\D0E1C4B6144E7ECAB3F020E4A19EFC29_B5F77004C894173A10E3A199871D2D90 | binary | |
MD5:39661D64CED47BD8D400CB31890C1951 | SHA256:20D5FD0A36BDB8BEE306A51428D6AC13384DC85EDAFB5000E2A97A65C191DC36 | |||
| 6648 | Fusion.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\B2FAF7692FD9FFBD64EDE317E42334BA_D7393C8F62BDE4D4CB606228BC7A711E | binary | |
MD5:AFD8B771D547B78A7500DC8D0BB560A6 | SHA256:1C8AD6842E2B58671D4FC4A32222A9E82DA50C74D92E277607537A498FE1D95D | |||
| 7064 | cmd.exe | C:\Users\admin\AppData\Local\fusion\Fusion.exe | executable | |
MD5:20081B7867970B6C7C4E6242C9758EC3 | SHA256:D7BAF7971071892D0BDC7E62A53A76C63D32C94AF92D573756467841C56E3125 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
16
TCP/UDP connections
57
DNS requests
38
Threats
2
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
6756 | svchost.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | DE | binary | 471 b | whitelisted |
1268 | svchost.exe | GET | 200 | 2.16.164.114:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | NL | binary | 825 b | whitelisted |
1268 | svchost.exe | GET | 200 | 69.192.161.161:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | DE | binary | 814 b | whitelisted |
6128 | SIHClient.exe | GET | 200 | 69.192.161.161:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | DE | binary | 419 b | whitelisted |
5328 | SearchApp.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAI5PUjXAkJafLQcAAsO18o%3D | DE | binary | 313 b | whitelisted |
5328 | SearchApp.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | DE | binary | 471 b | whitelisted |
6648 | Fusion.exe | GET | 200 | 172.64.149.23:80 | http://ocsp.usertrust.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTNMNJMNDqCqx8FcBWK16EHdimS6QQUU3m%2FWqorSs9UgOHYm8Cd8rIDZssCEH1bUSa0droR23QWC7xTDac%3D | US | binary | 2.18 Kb | whitelisted |
6128 | SIHClient.exe | GET | 200 | 69.192.161.161:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | DE | binary | 407 b | whitelisted |
6648 | Fusion.exe | GET | 200 | 104.18.38.233:80 | http://ocsp.comodoca.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBRTtU9uFqgVGHhJwXZyWCNXmVR5ngQUoBEKIz6W8Qfs4q8p74Klf9AwpLQCEFZnHQTqT5lMbxCBR1nSdZQ%3D | unknown | binary | 1.42 Kb | whitelisted |
5712 | WerFault.exe | GET | 200 | 95.101.149.131:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | NL | binary | 814 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
5944 | MoUsoCoreWorker.exe | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
1268 | svchost.exe | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
5968 | RUXIMICS.exe | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
6756 | svchost.exe | 40.126.32.133:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
6756 | svchost.exe | 2.17.190.73:80 | ocsp.digicert.com | AKAMAI-AS | DE | whitelisted |
1268 | svchost.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
1268 | svchost.exe | 2.16.164.114:80 | crl.microsoft.com | Akamai International B.V. | NL | whitelisted |
1268 | svchost.exe | 69.192.161.161:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
slscr.update.microsoft.com |
| whitelisted |
www.bing.com |
| whitelisted |
fe3cr.delivery.mp.microsoft.com |
| whitelisted |
fp.msedge.net |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2200 | svchost.exe | Not Suspicious Traffic | INFO [ANY.RUN] Attempting to access raw user content on GitHub |
2200 | svchost.exe | Not Suspicious Traffic | INFO [ANY.RUN] Attempting to access release user assets on GitHub |
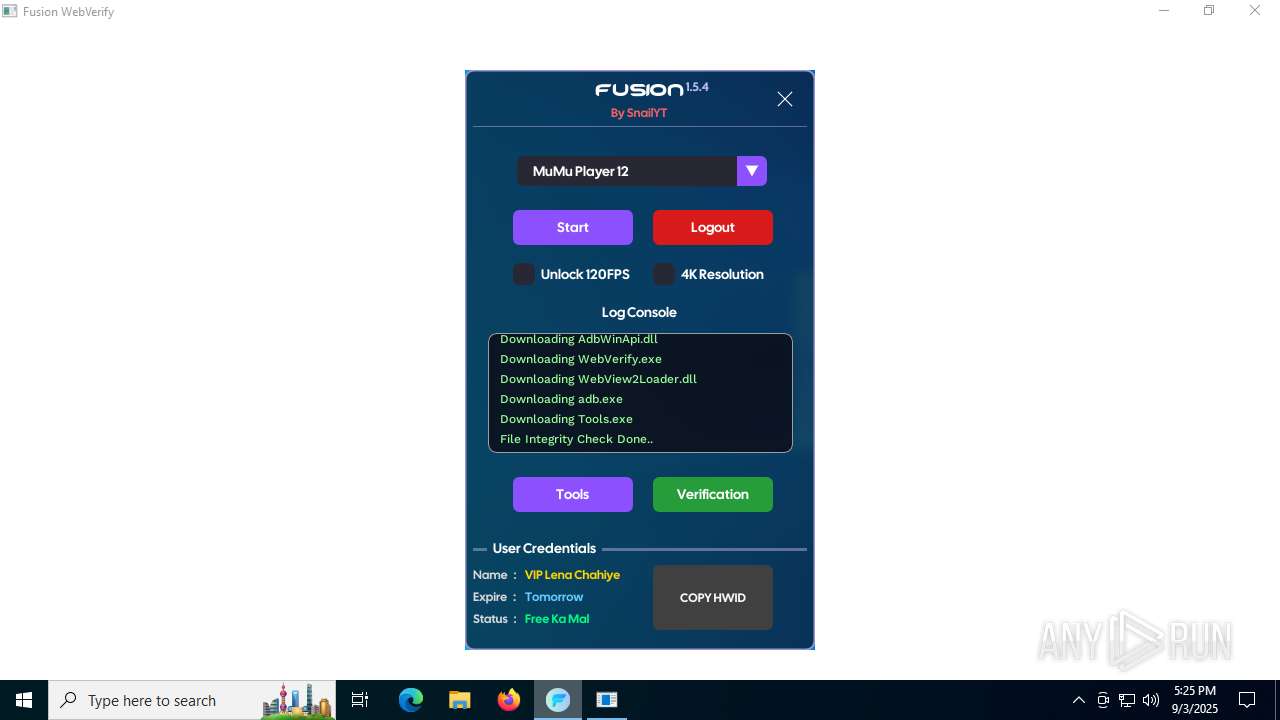
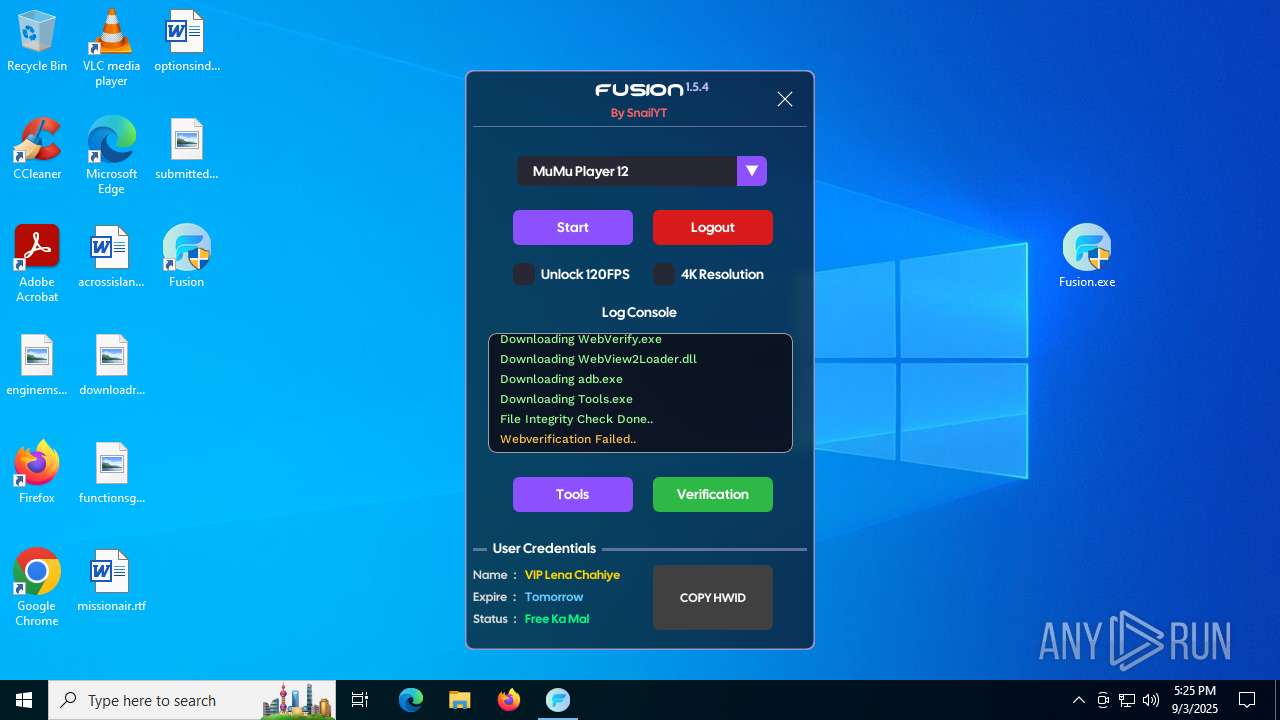
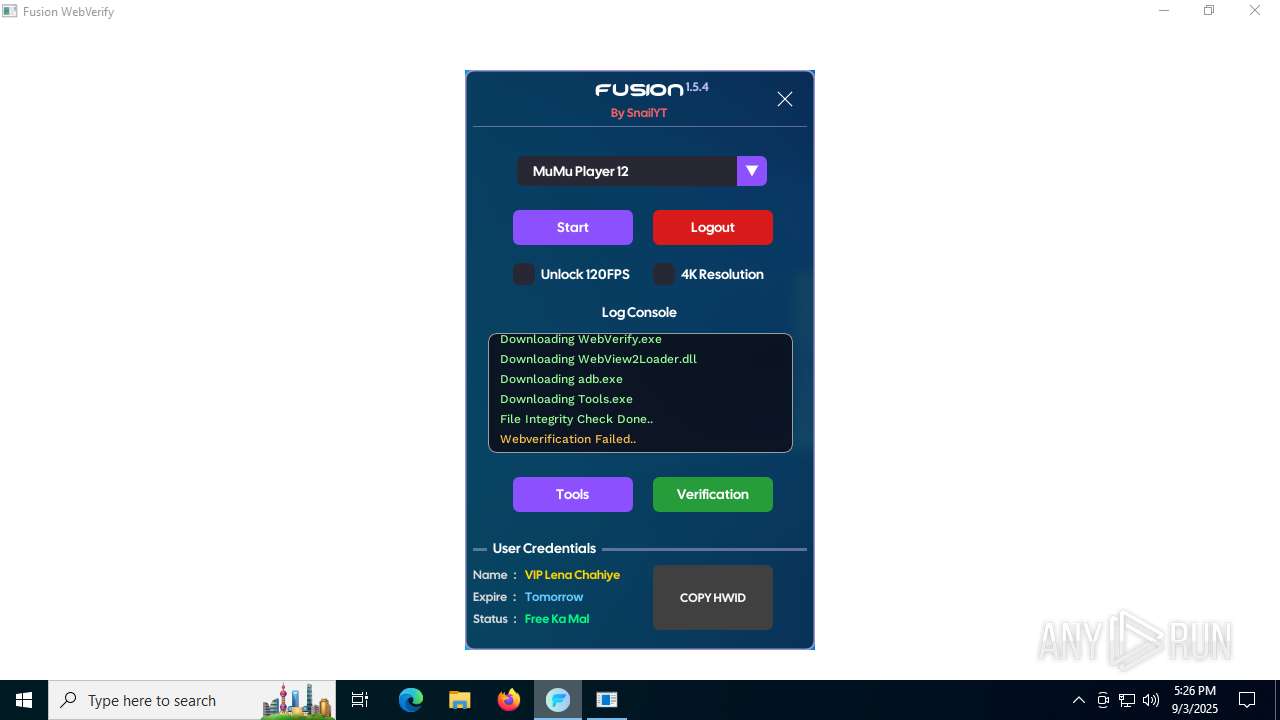
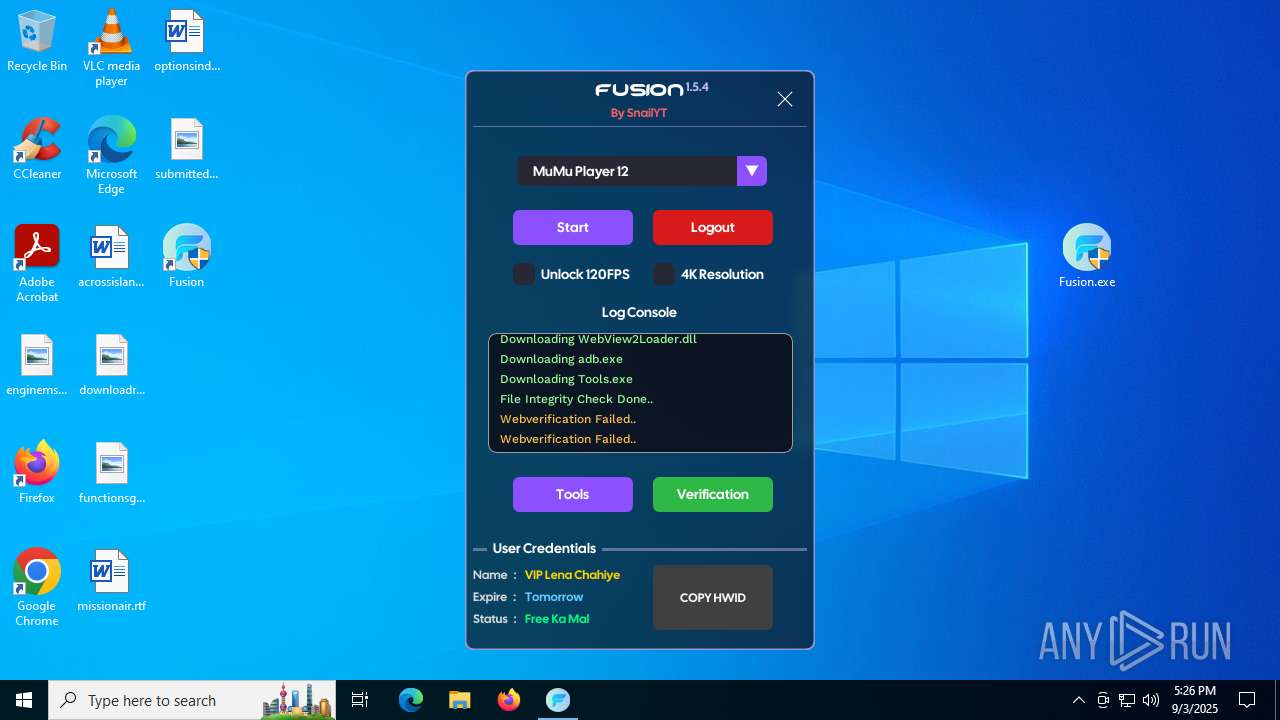
Process | Message |
|---|---|
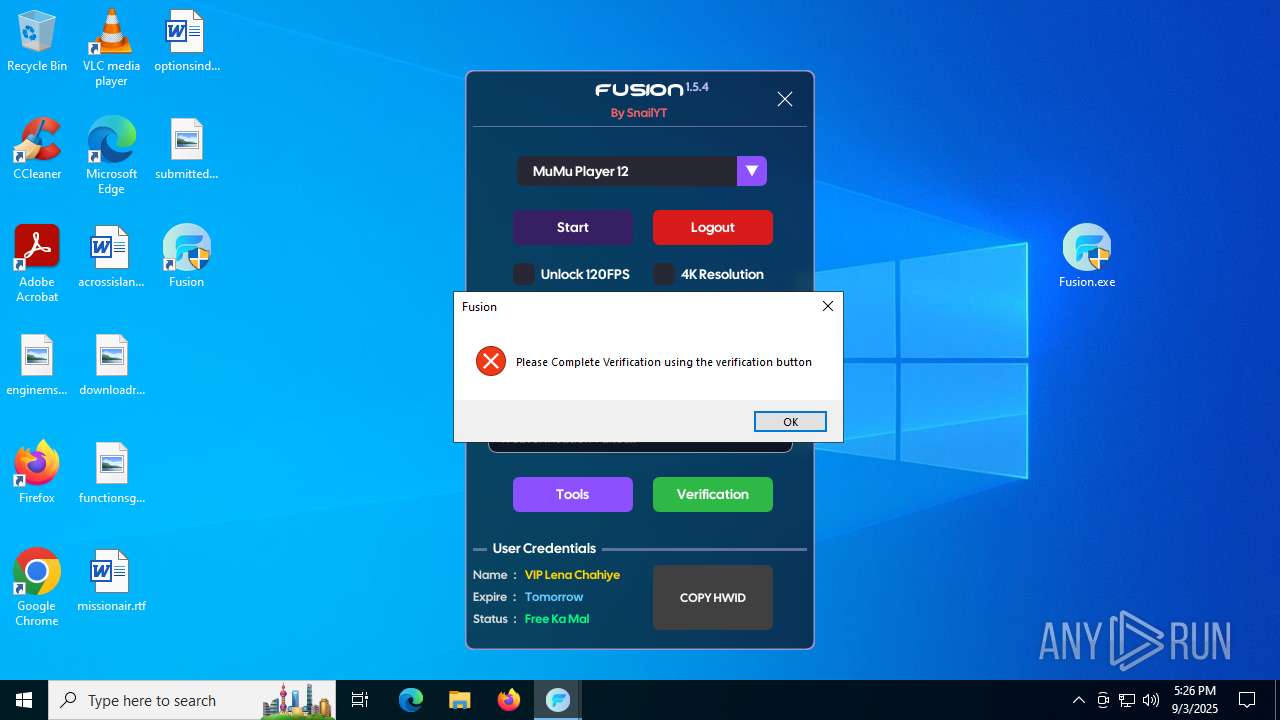
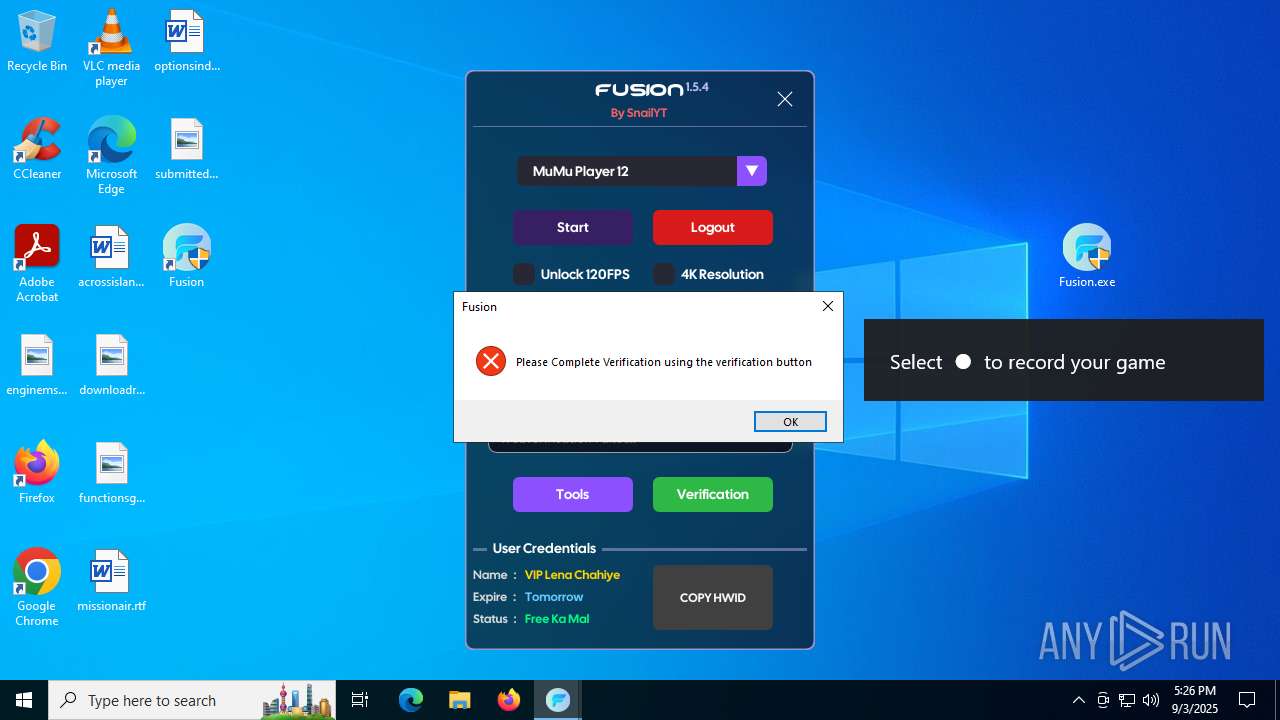
WebVerify.exe | WebView2: Failed to find an installed WebView2 runtime or non-stable Microsoft Edge installation.
|
WebVerify.exe | WebView2: Failed to find an installed WebView2 runtime or non-stable Microsoft Edge installation.
|
WebVerify.exe | WebView2: Failed to find an installed WebView2 runtime or non-stable Microsoft Edge installation.
|
WebVerify.exe | WebView2: Failed to find an installed WebView2 runtime or non-stable Microsoft Edge installation.
|
WebVerify.exe | WebView2: Failed to find an installed WebView2 runtime or non-stable Microsoft Edge installation.
|
WebVerify.exe | WebView2: Failed to find an installed WebView2 runtime or non-stable Microsoft Edge installation.
|