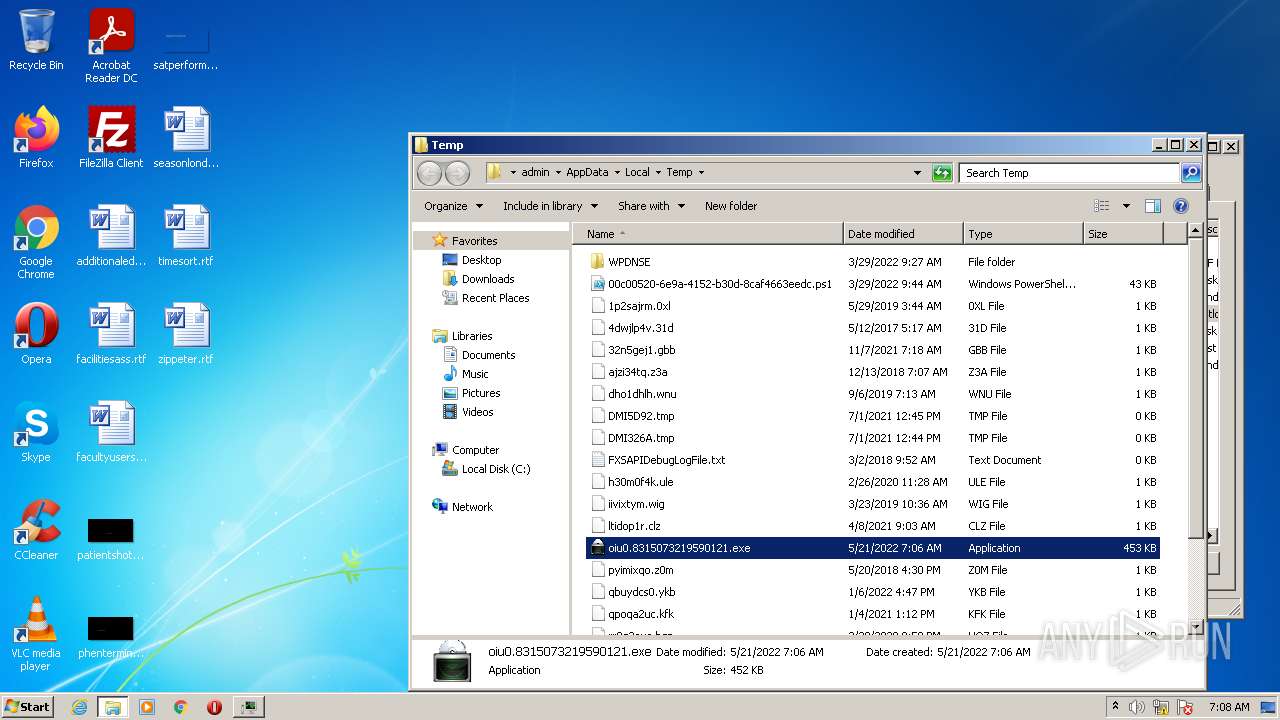
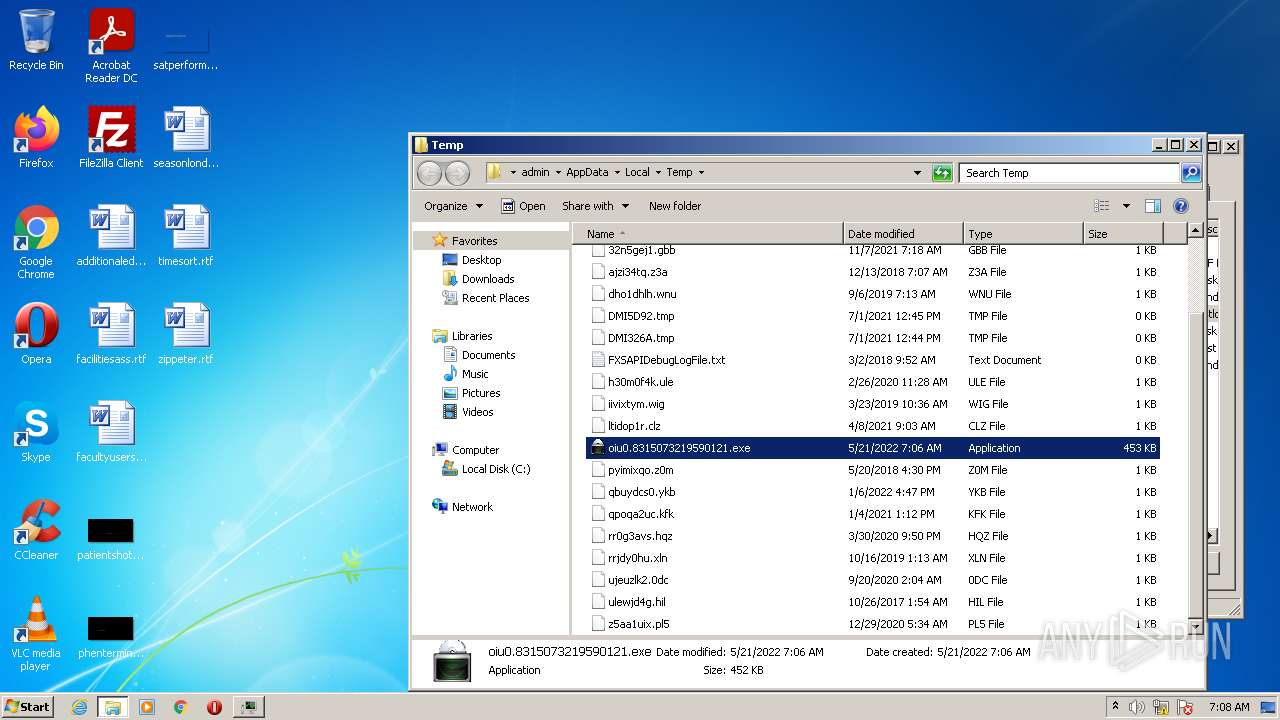
| File name: | C:\Users\admin\Desktop\oiu0.8315073219590121.exe |
| Full analysis: | https://app.any.run/tasks/a2a9cf4b-4f1d-4f8d-ada7-c81f52e569db |
| Verdict: | Malicious activity |
| Analysis date: | May 21, 2022, 06:06:29 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | 981C0D16EEF0B35259EE8232CDC90B1C |
| SHA1: | F380C7FD9AFE826CDC4C0E3D7DD58685B51CE0BE |
| SHA256: | 6560A915088D6F9833F2AE3C533E77373902759F7C581FC4925F6F05E87F6108 |
| SSDEEP: | 12288:bnGxtGknlMLx7BXyst/owVc/Q6hsYTgRf3/J/QLjN:CxMkniCst/owZA51 |
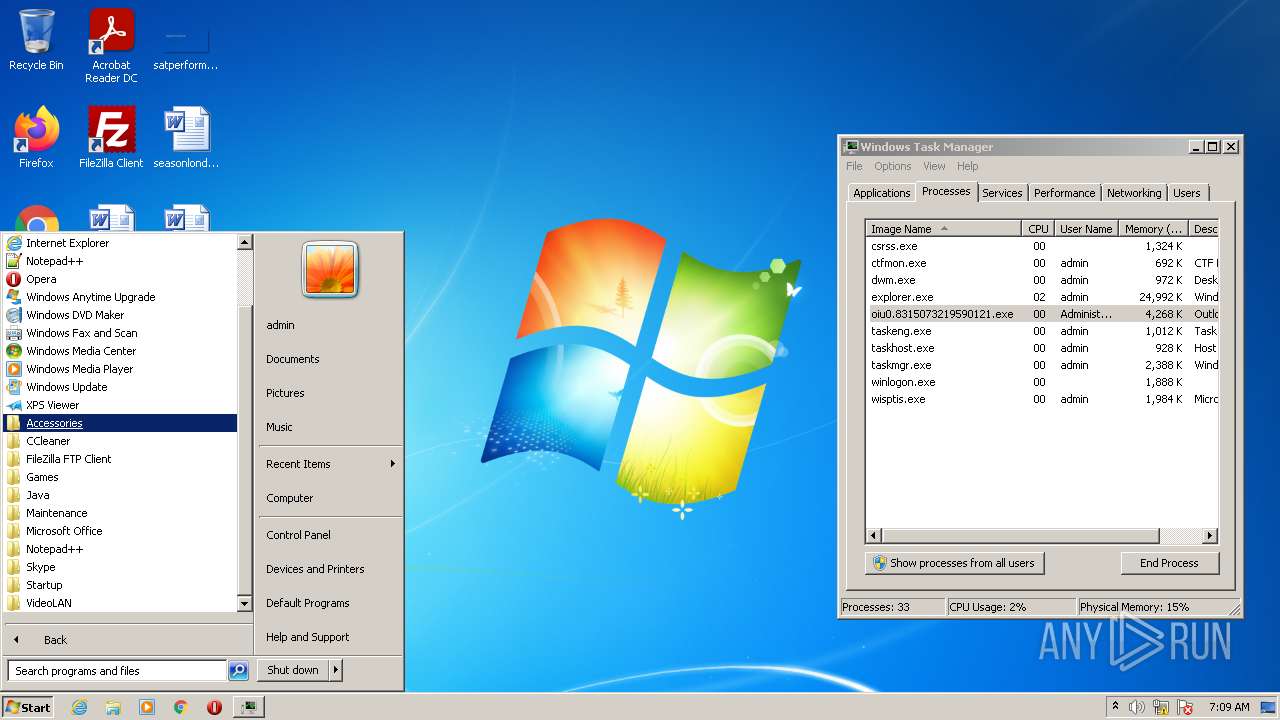
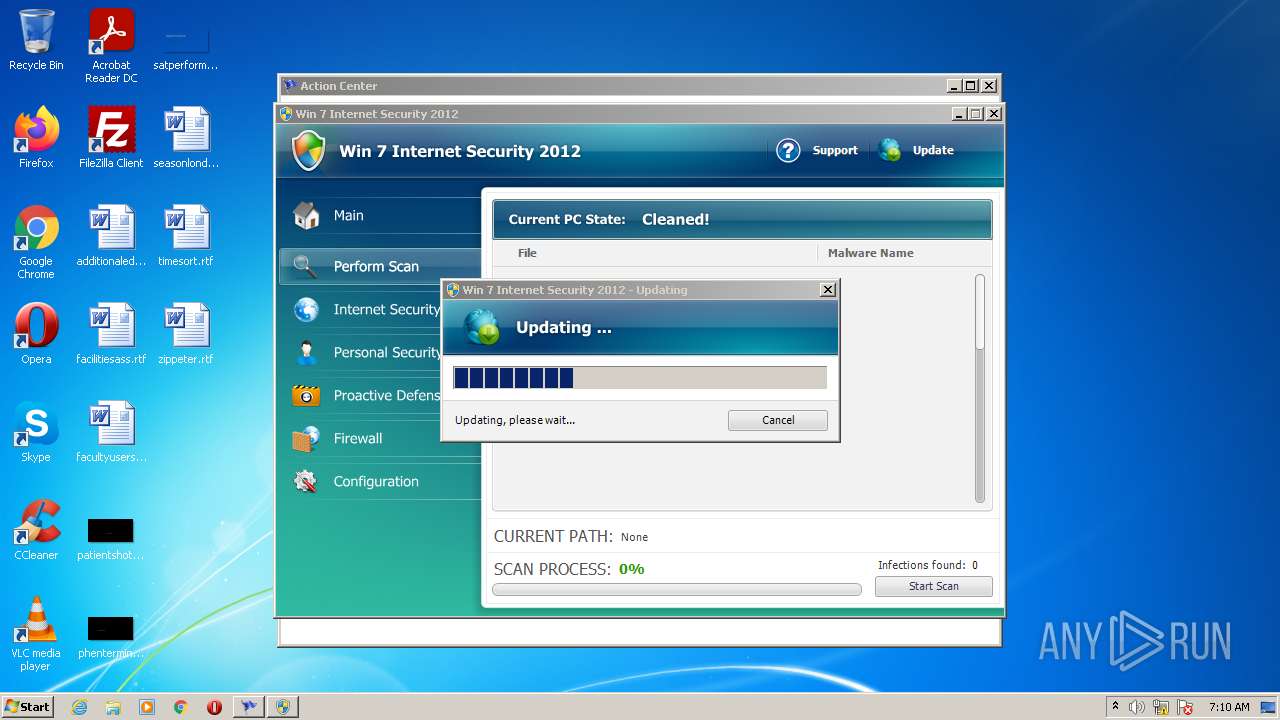
MALICIOUS
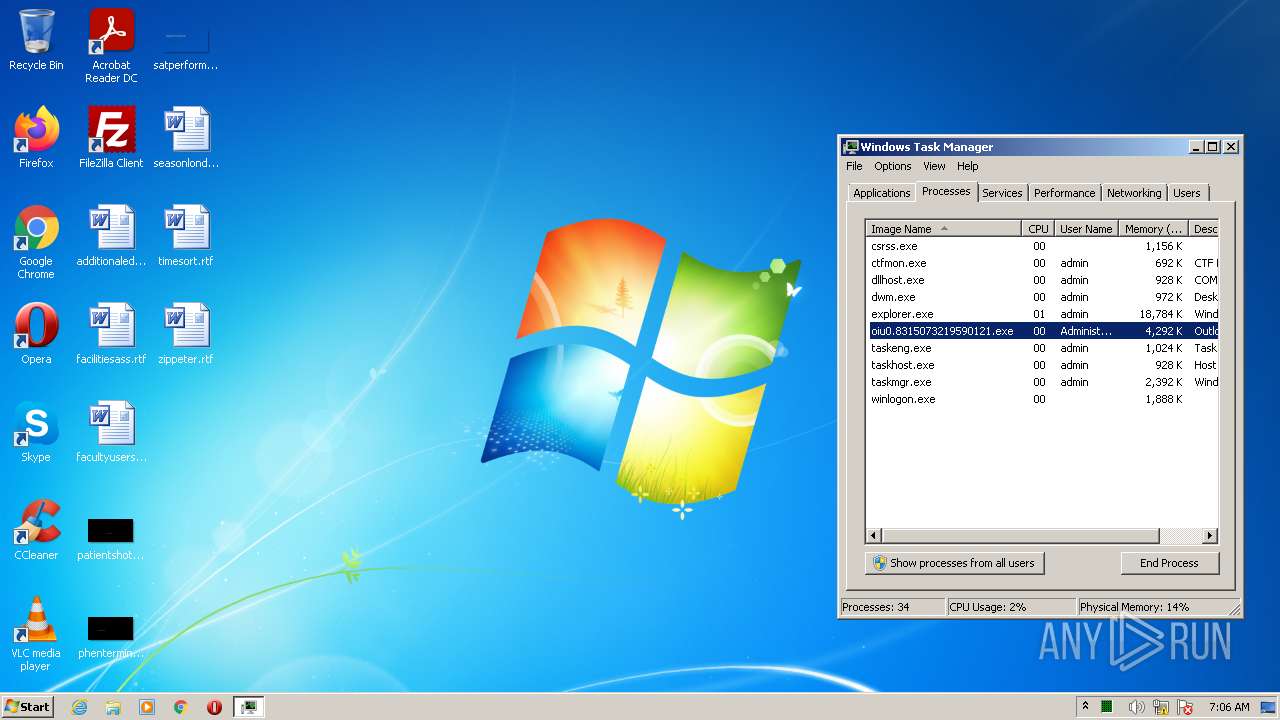
Drops executable file immediately after starts
- oiu0.8315073219590121.exe (PID: 3312)
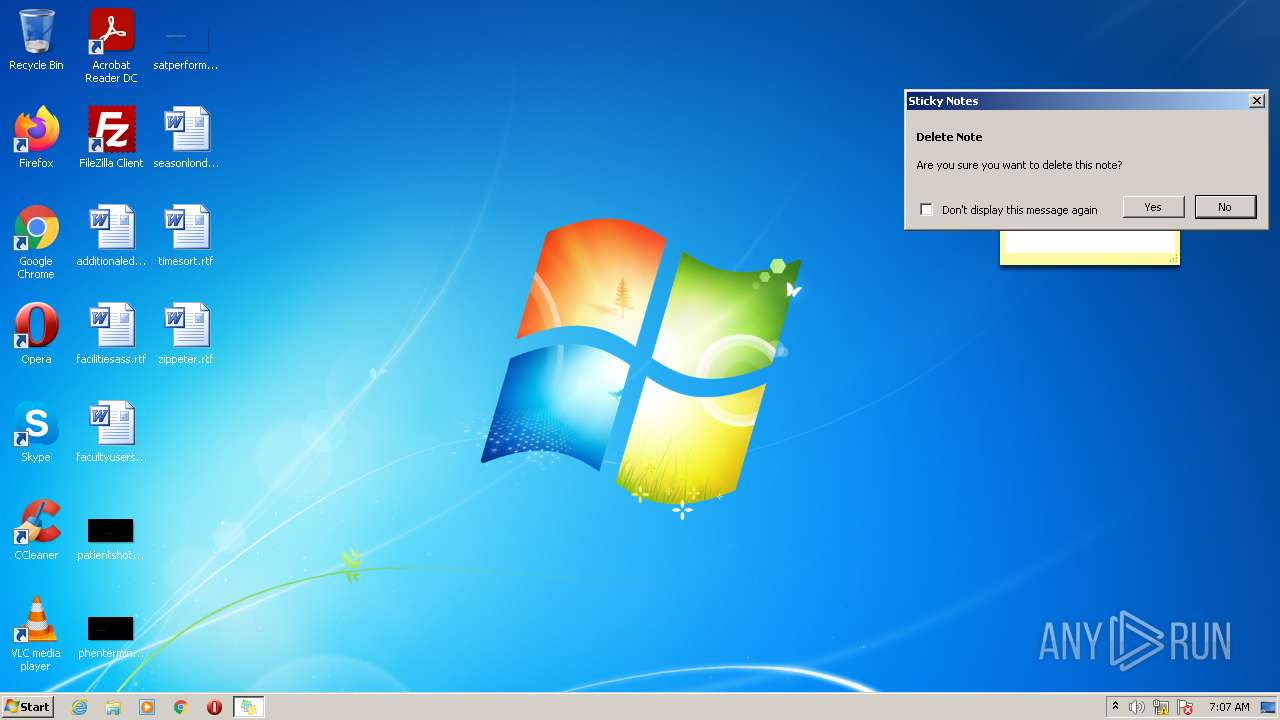
Changes the autorun value in the registry
- StikyNot.exe (PID: 4024)
- oiu0.8315073219590121.exe (PID: 3312)
Loads dropped or rewritten executable
- unsecapp.exe (PID: 3096)
- DllHost.exe (PID: 3916)
- oiu0.8315073219590121.exe (PID: 3312)
SUSPICIOUS
Reads the computer name
- oiu0.8315073219590121.exe (PID: 3312)
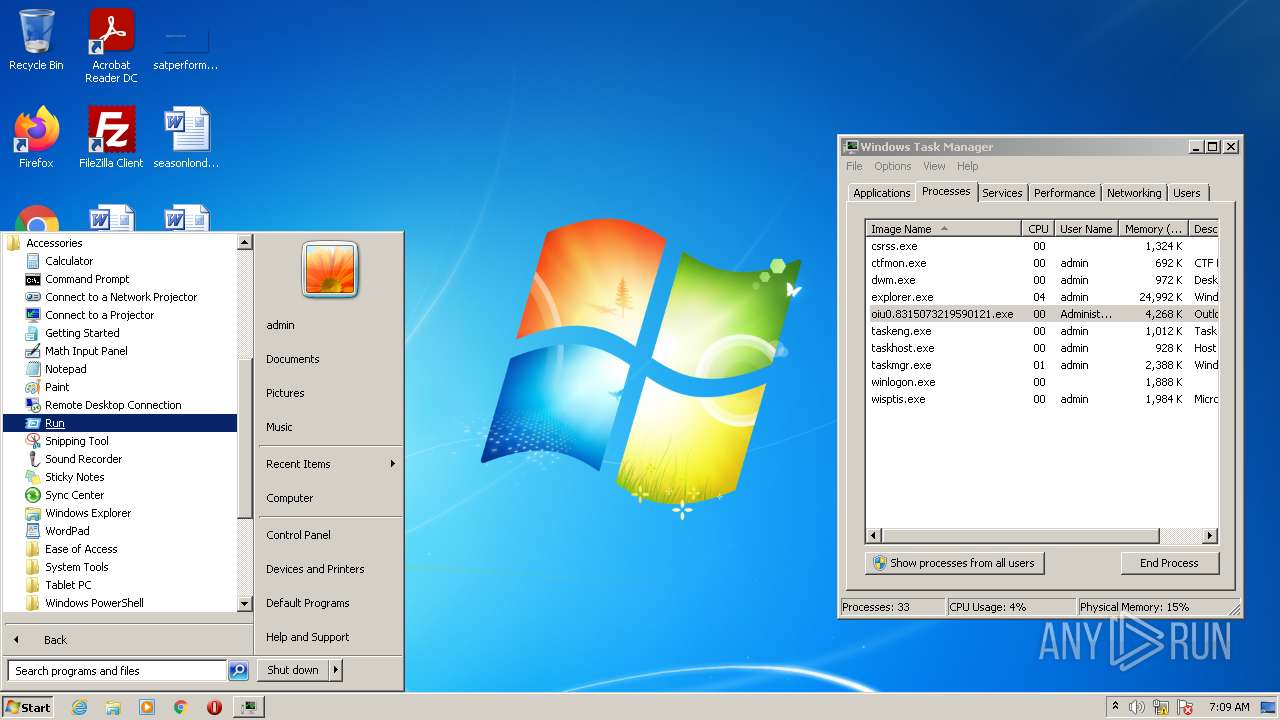
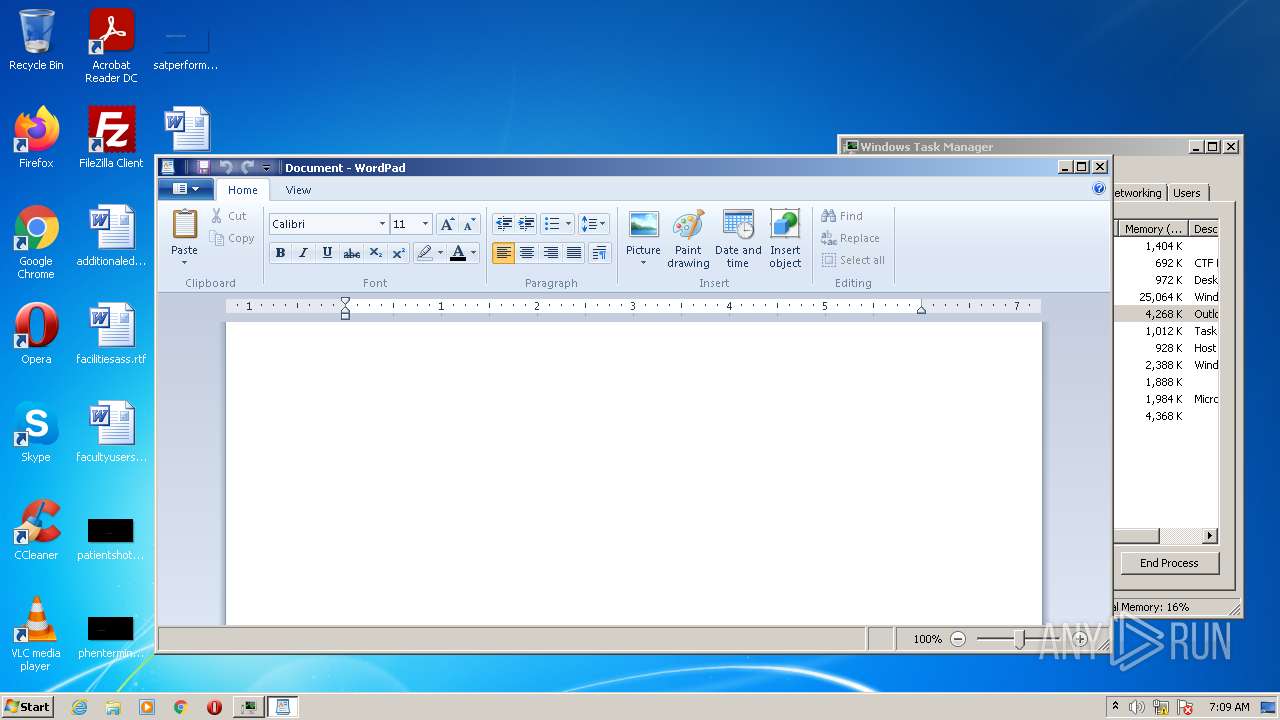
- wordpad.exe (PID: 3428)
- unsecapp.exe (PID: 3096)
Checks supported languages
- oiu0.8315073219590121.exe (PID: 3312)
- wordpad.exe (PID: 3428)
- unsecapp.exe (PID: 3096)
Executable content was dropped or overwritten
- oiu0.8315073219590121.exe (PID: 3312)
Creates files in the program directory
- oiu0.8315073219590121.exe (PID: 3312)
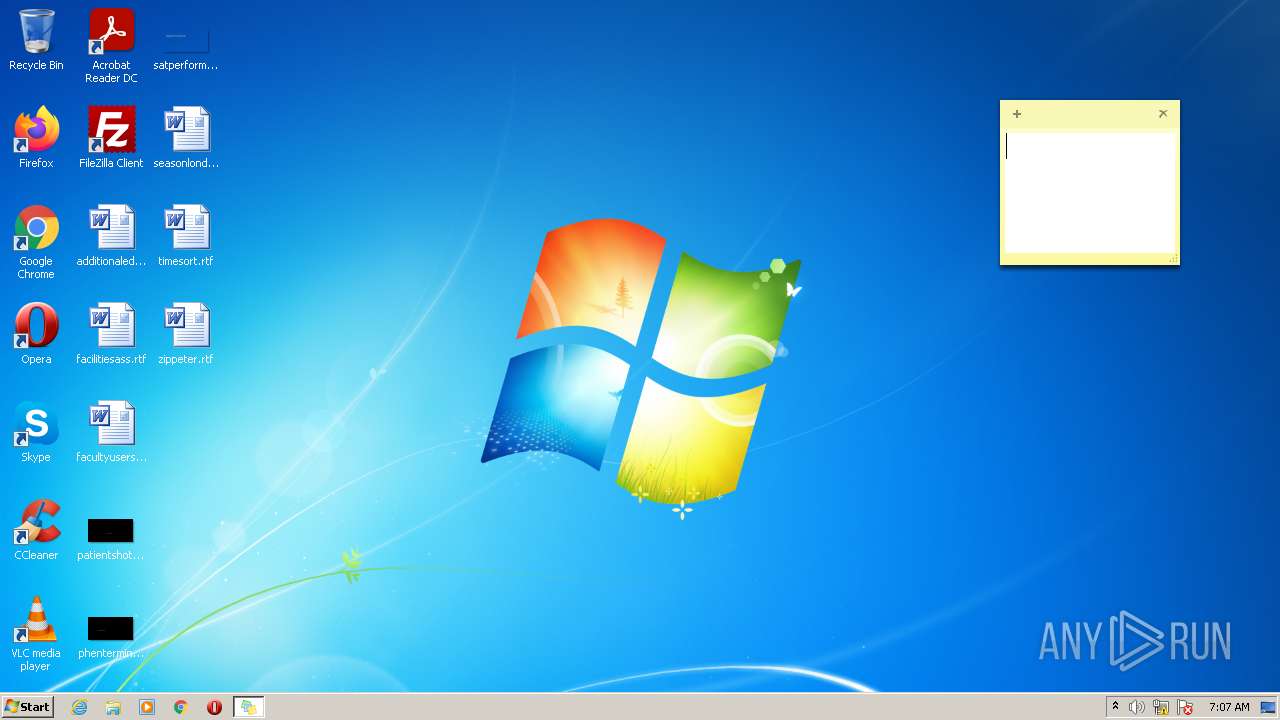
Creates files in the user directory
- StikyNot.exe (PID: 4024)
Reads default file associations for system extensions
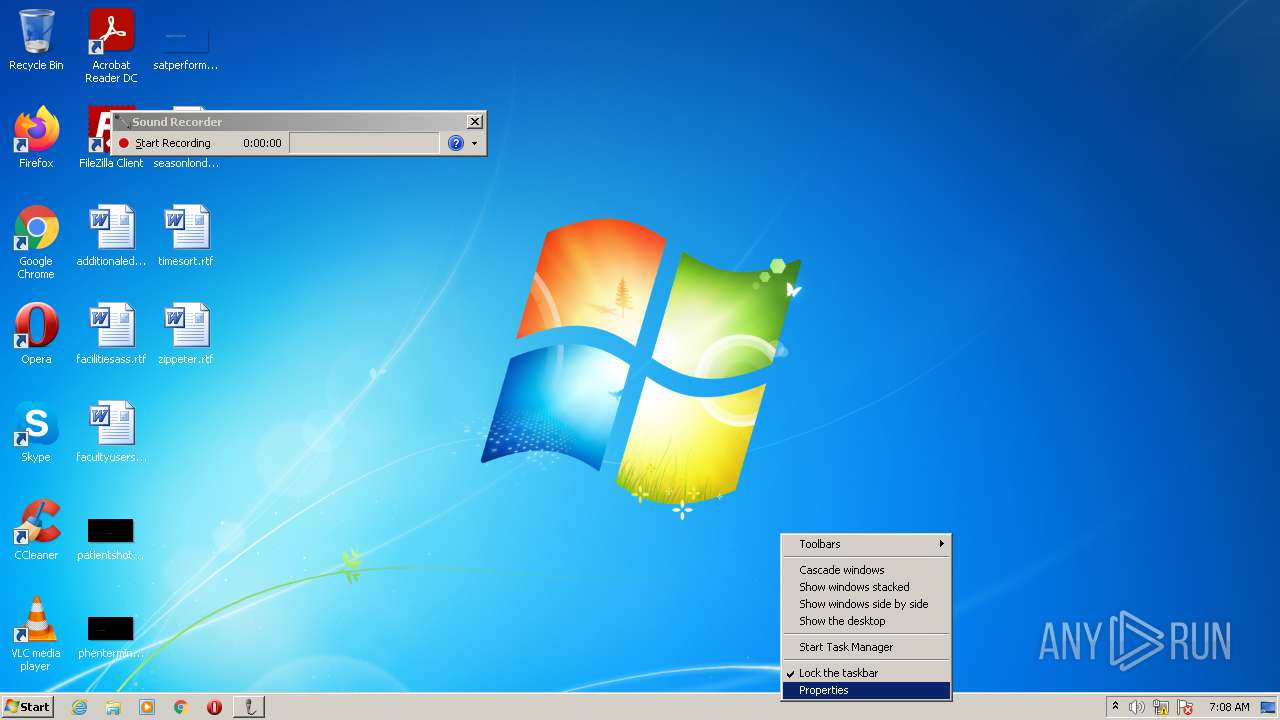
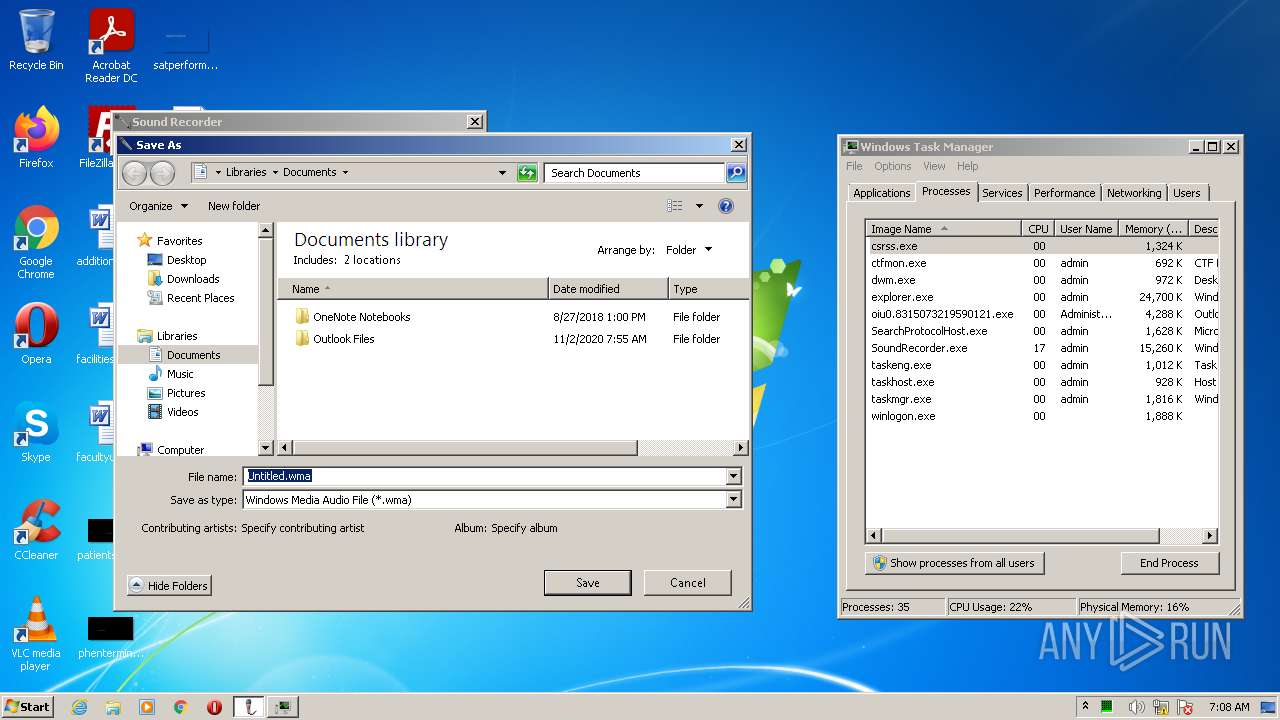
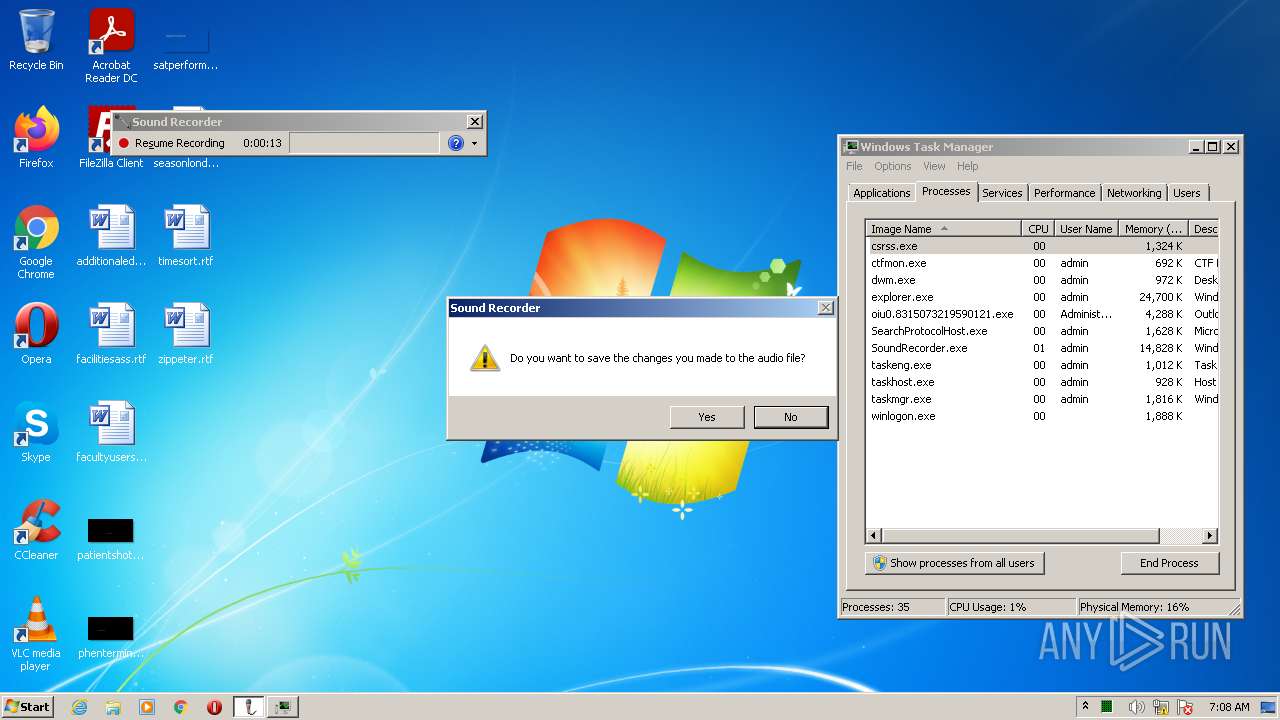
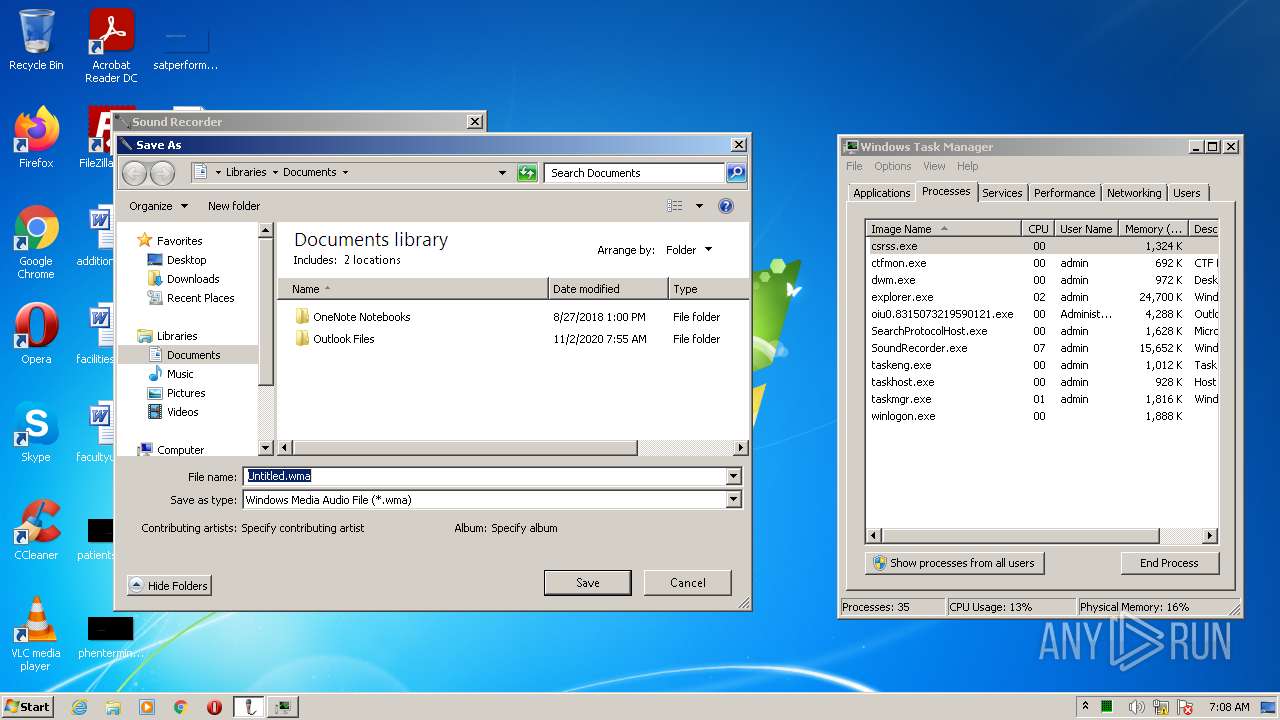
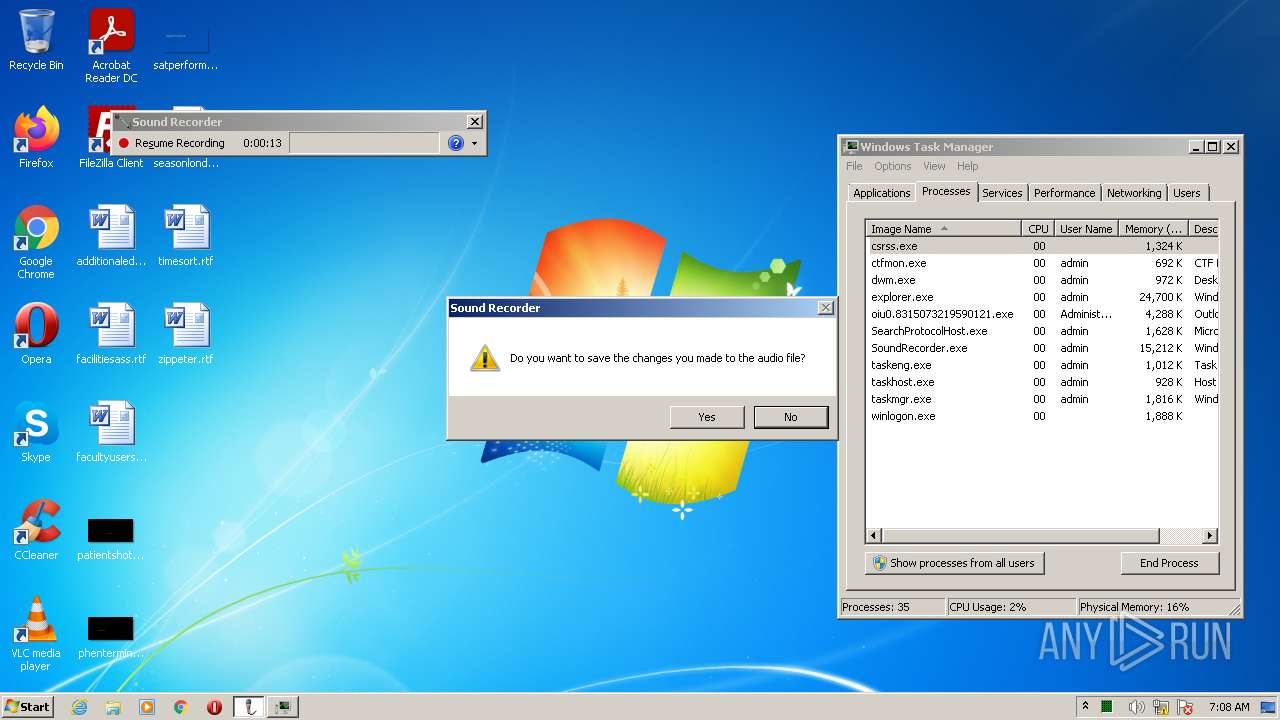
- SoundRecorder.exe (PID: 3548)
Reads Microsoft Outlook installation path
- oiu0.8315073219590121.exe (PID: 3312)
Executed via COM
- unsecapp.exe (PID: 3096)
- DllHost.exe (PID: 3916)
Reads internet explorer settings
- oiu0.8315073219590121.exe (PID: 3312)
Changes default file association
- oiu0.8315073219590121.exe (PID: 3312)
Creates files in the Windows directory
- oiu0.8315073219590121.exe (PID: 3312)
Drops a file with a compile date too recent
- oiu0.8315073219590121.exe (PID: 3312)
INFO
Reads the computer name
- taskmgr.exe (PID: 4064)
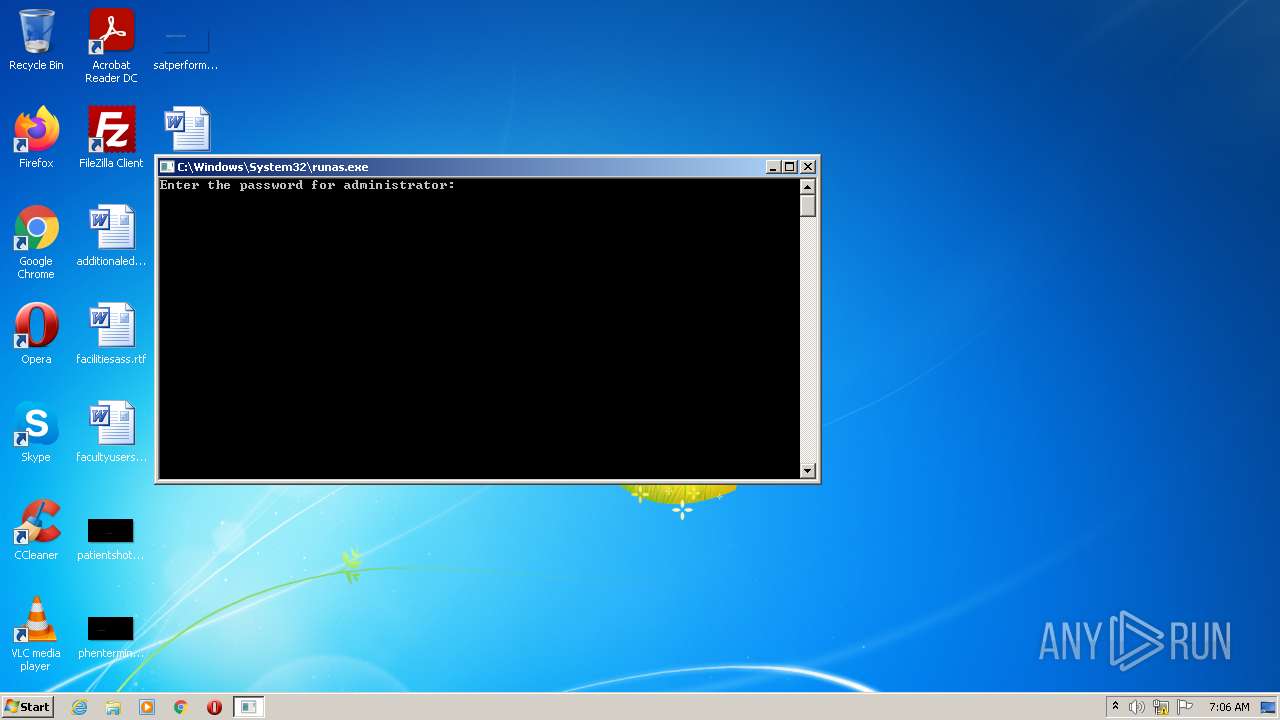
- runas.exe (PID: 2836)
- taskmgr.exe (PID: 3616)
- StikyNot.exe (PID: 4024)
- SoundRecorder.exe (PID: 3548)
- taskmgr.exe (PID: 2448)
- SnippingTool.exe (PID: 1868)
- taskmgr.exe (PID: 2176)
- taskmgr.exe (PID: 2400)
- DllHost.exe (PID: 3916)
- taskmgr.exe (PID: 3868)
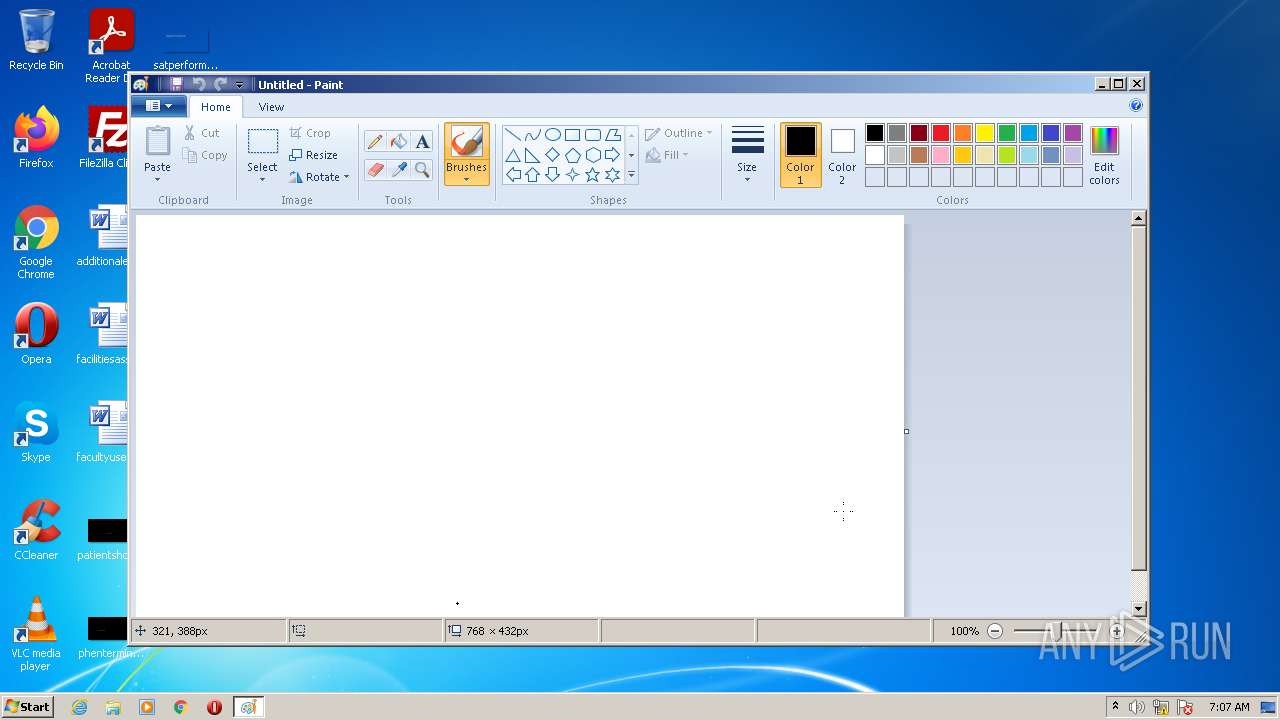
- mspaint.exe (PID: 2724)
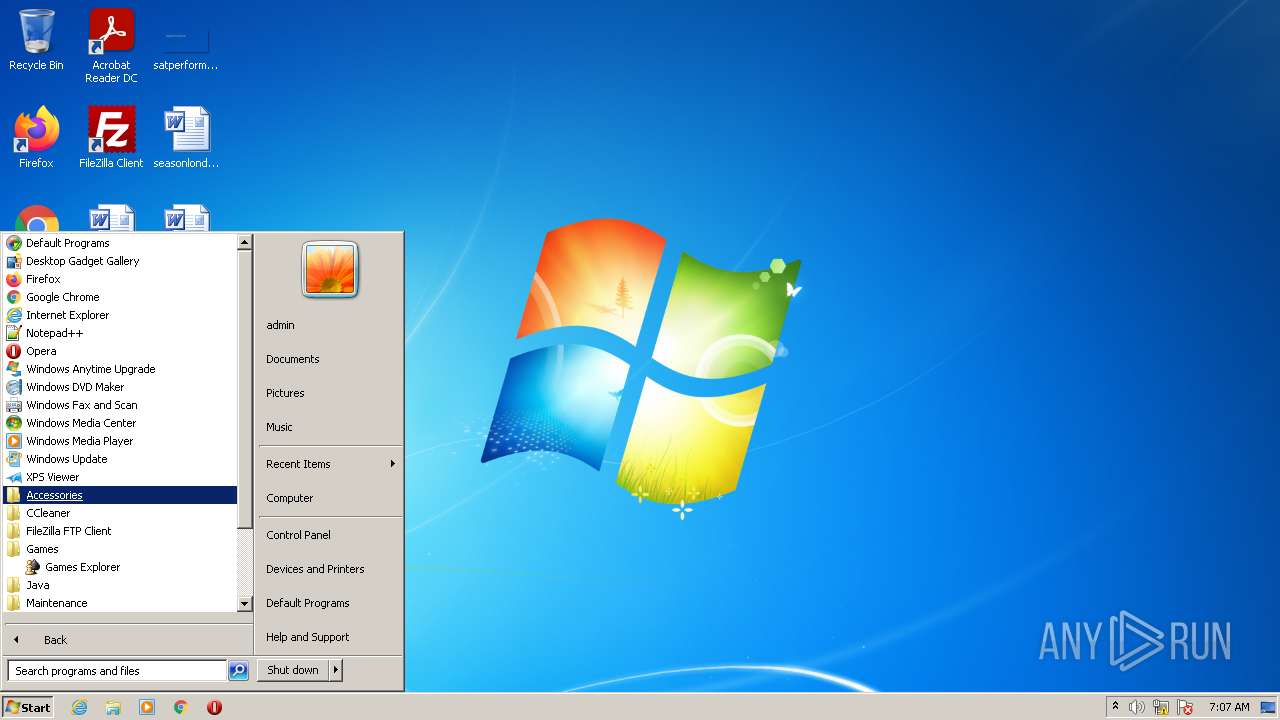
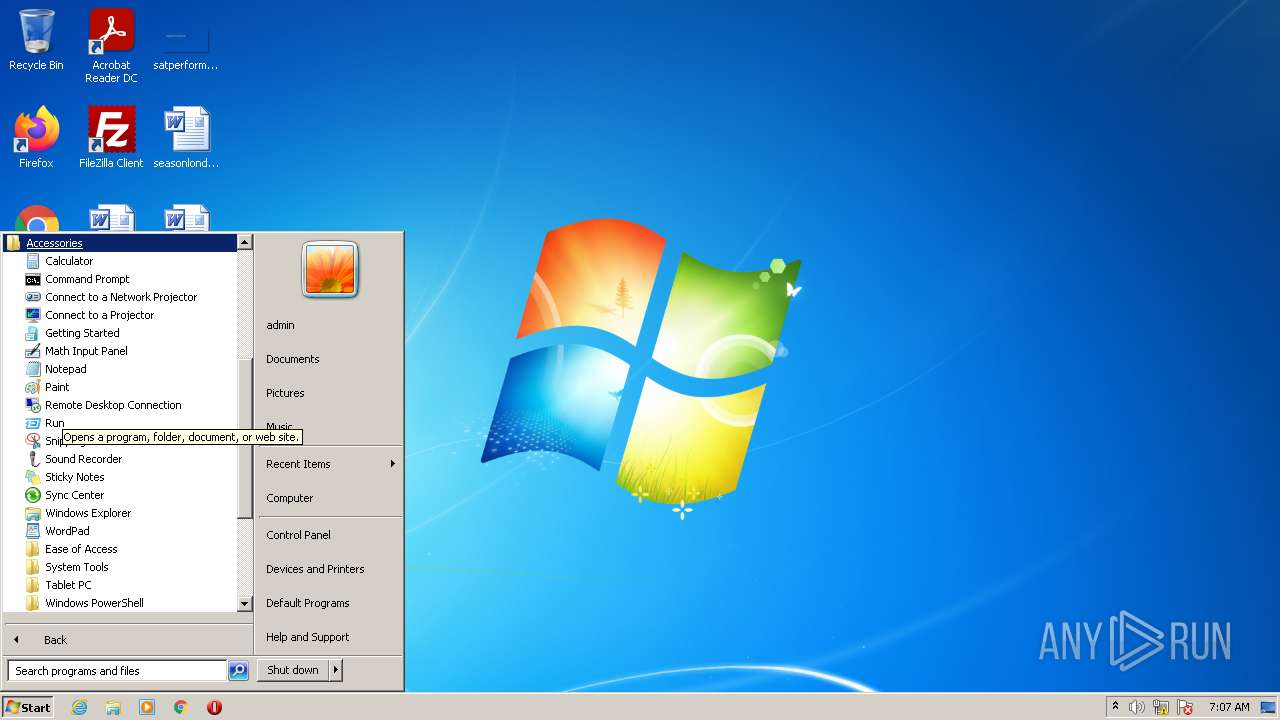
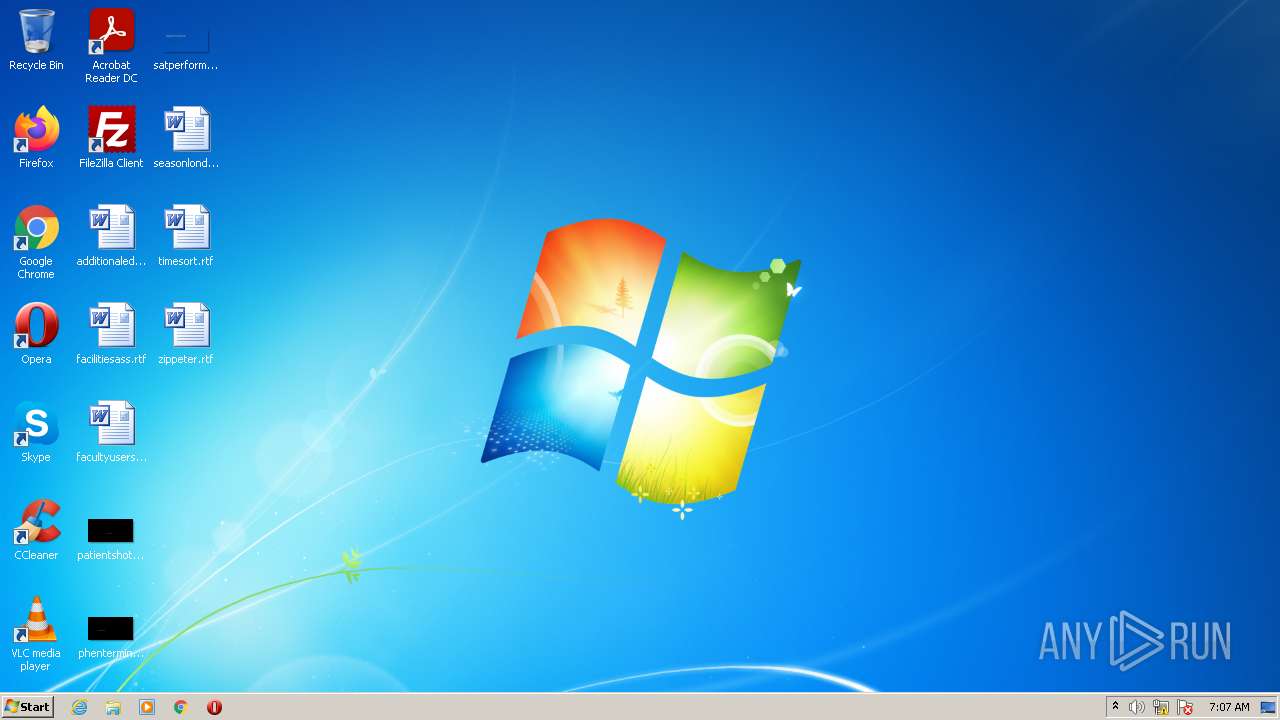
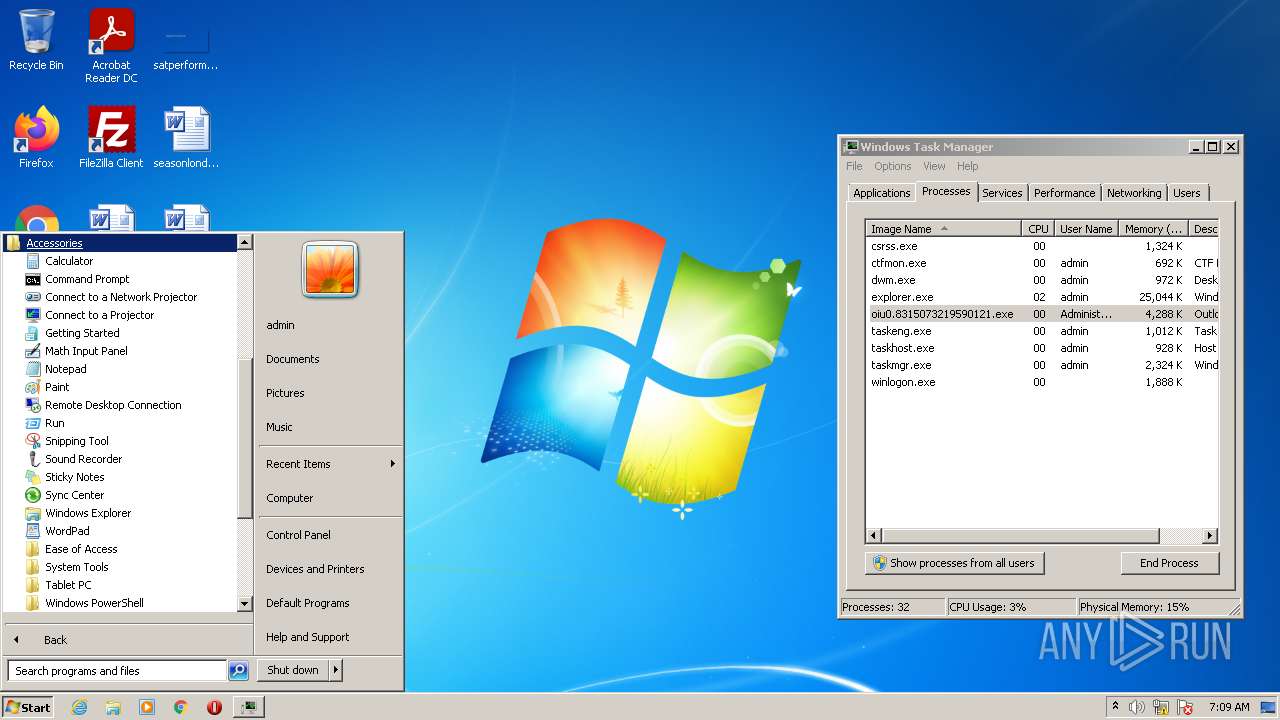
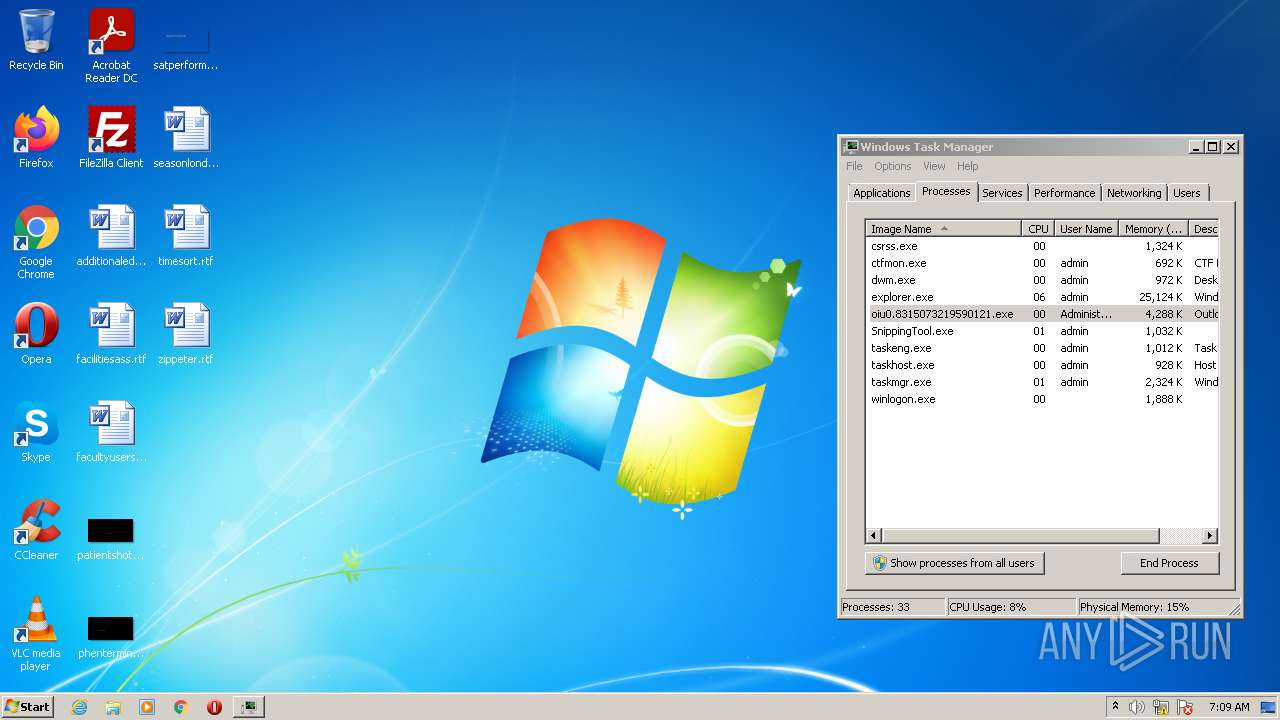
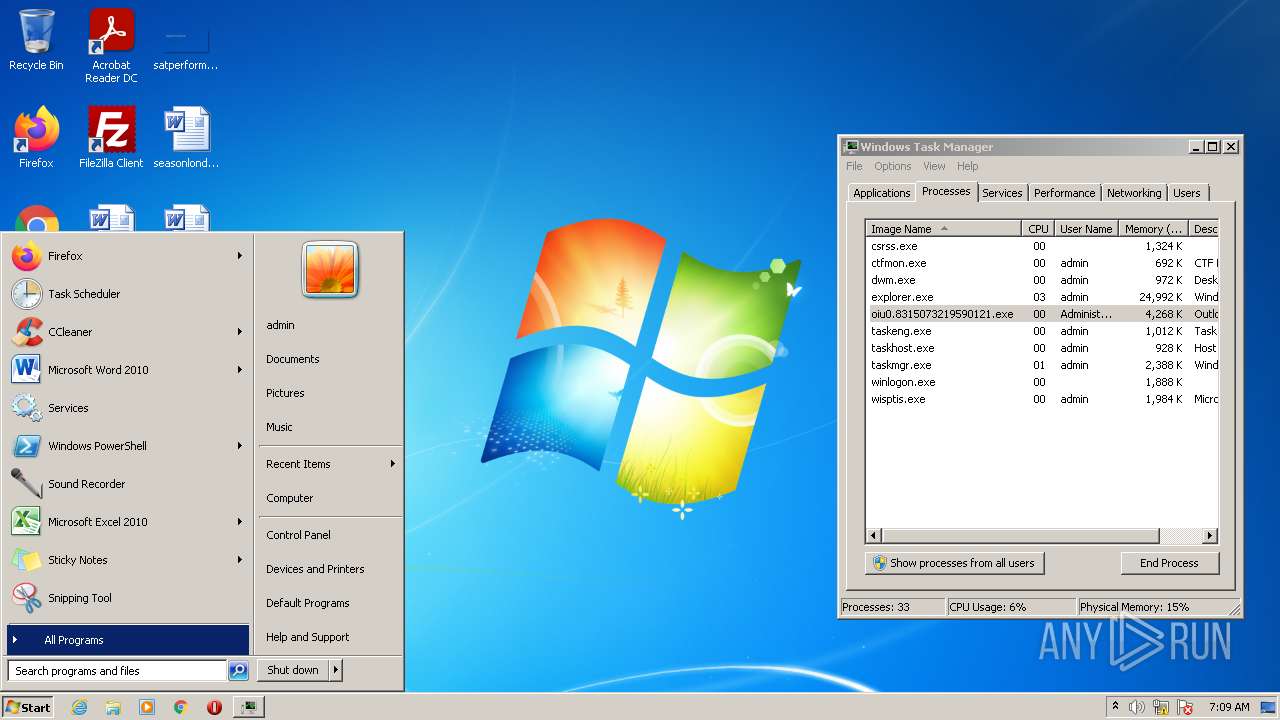
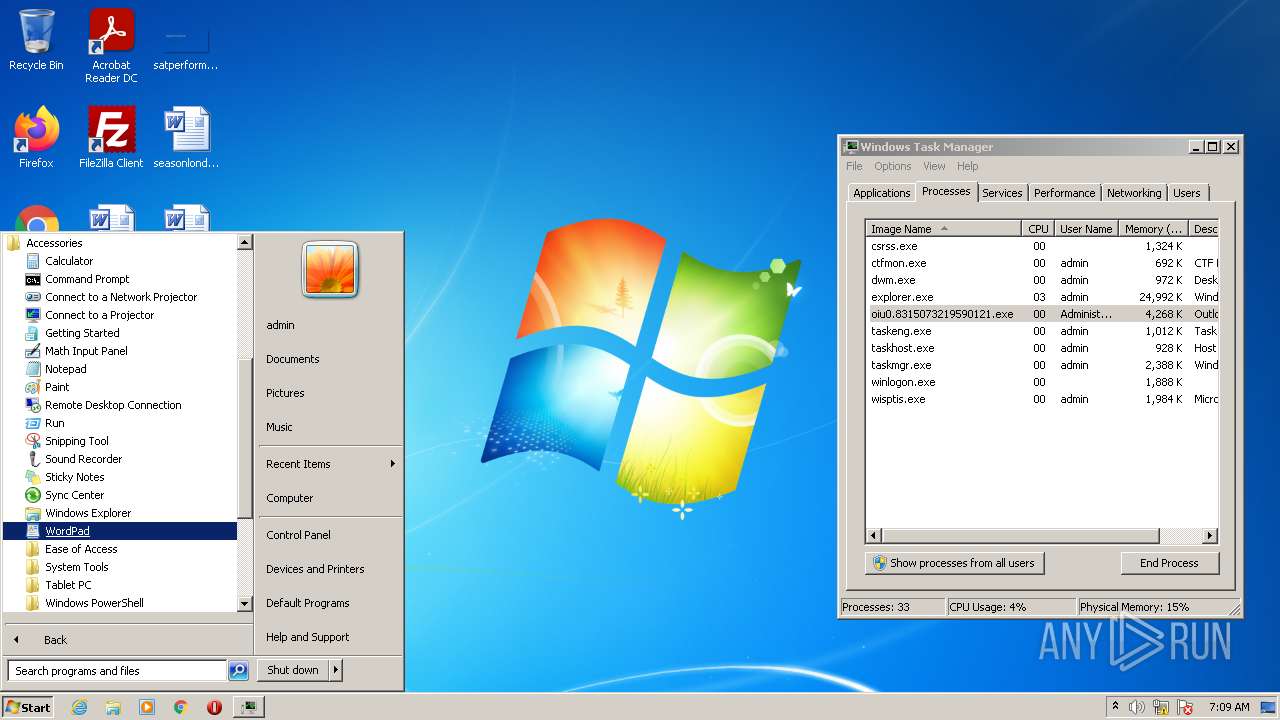
Manual execution by user
- calc.exe (PID: 3648)
- taskmgr.exe (PID: 3616)
- taskmgr.exe (PID: 4064)
- mspaint.exe (PID: 2724)
- StikyNot.exe (PID: 4024)
- SoundRecorder.exe (PID: 3548)
- taskmgr.exe (PID: 2176)
- taskmgr.exe (PID: 2448)
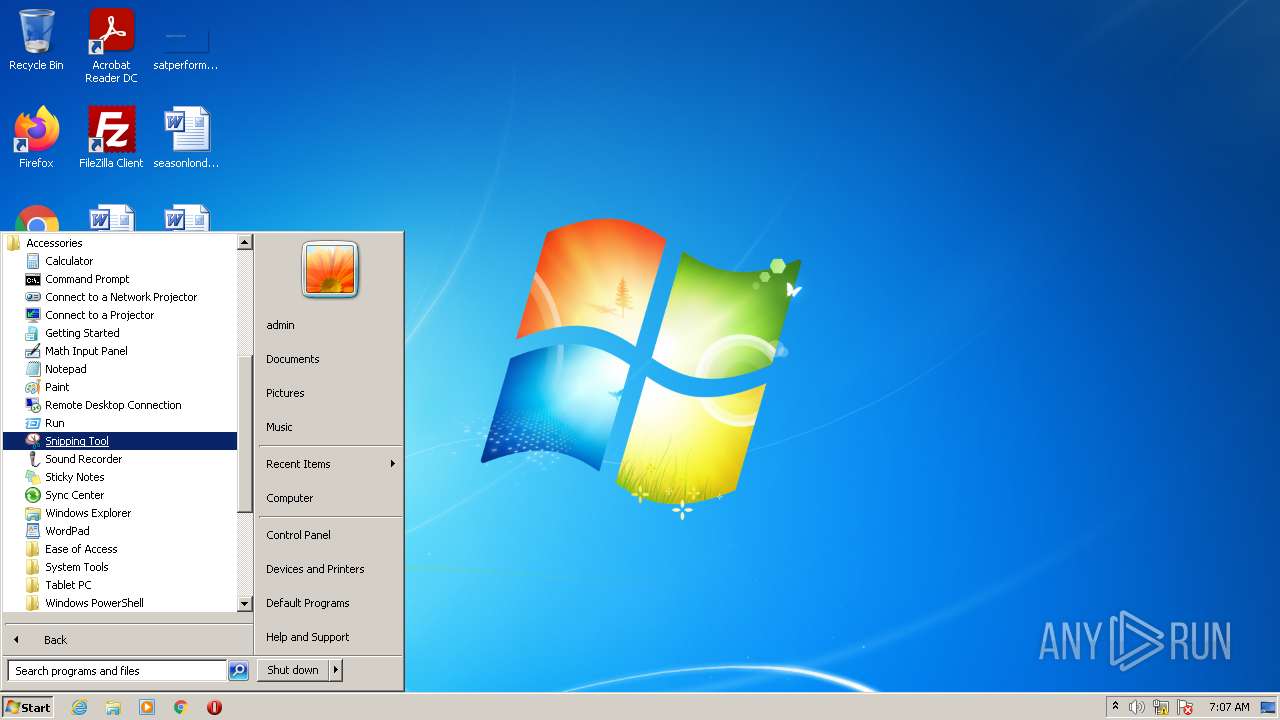
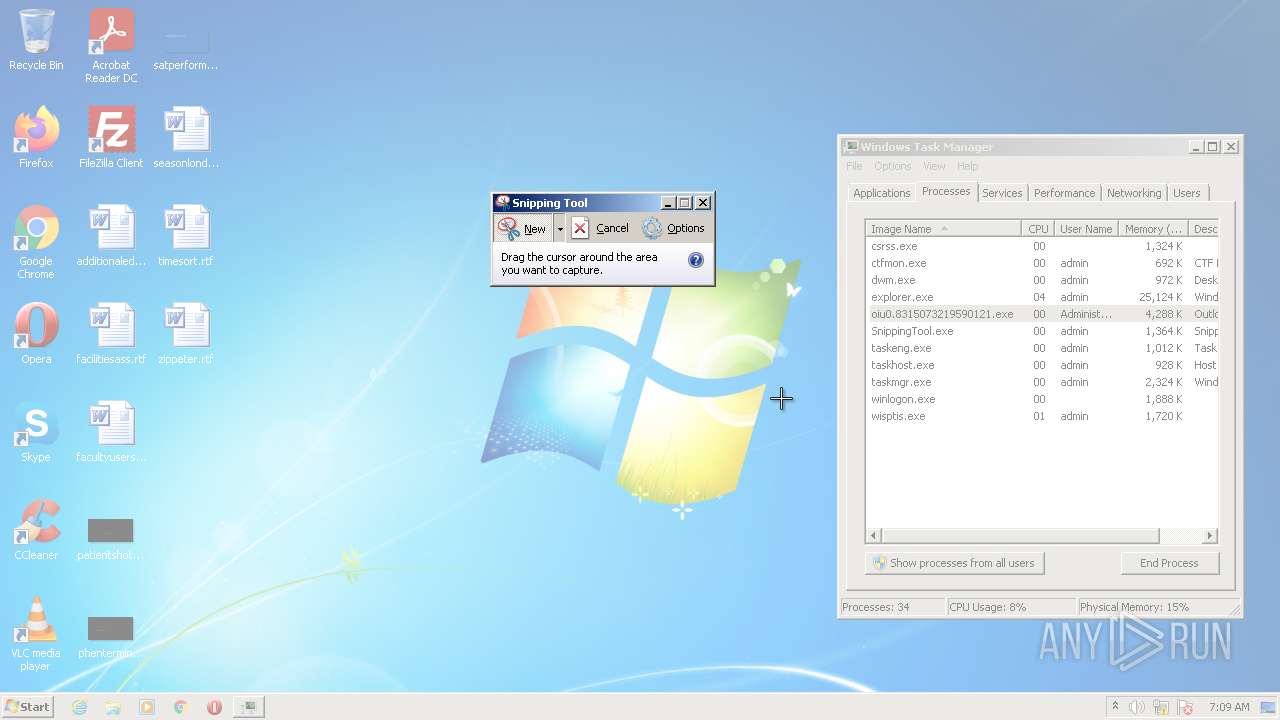
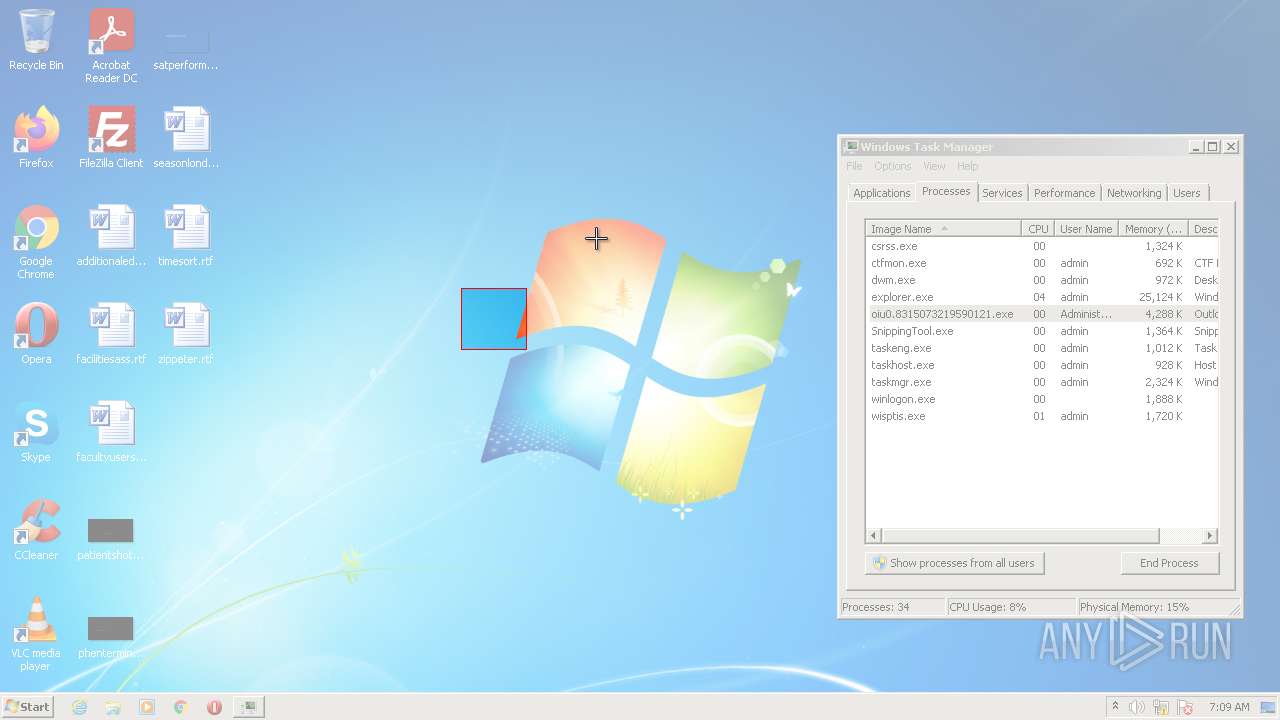
- SnippingTool.exe (PID: 1868)
- wordpad.exe (PID: 3428)
- taskmgr.exe (PID: 2400)
- taskmgr.exe (PID: 3868)
Checks supported languages
- calc.exe (PID: 3648)
- runas.exe (PID: 2836)
- taskmgr.exe (PID: 4064)
- taskmgr.exe (PID: 3616)
- StikyNot.exe (PID: 4024)
- SoundRecorder.exe (PID: 3548)
- taskmgr.exe (PID: 2448)
- SnippingTool.exe (PID: 1868)
- taskmgr.exe (PID: 2400)
- taskmgr.exe (PID: 2176)
- taskmgr.exe (PID: 3868)
- DllHost.exe (PID: 3916)
- mspaint.exe (PID: 2724)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Clipper DOS Executable (33.5) |
|---|---|---|
| .exe | | | Generic Win/DOS Executable (33.2) |
| .exe | | | DOS Executable Generic (33.2) |
EXIF
EXE
| ProductVersion: | 6.00.2900.5931 |
|---|---|
| ProductName: | Microsoft® Windows® Operating System |
| OriginalFileName: | MSOE.DLL |
| LegalCopyright: | © Microsoft Corporation. All rights reserved. |
| InternalName: | MSOE |
| FileVersion: | 6.00.2900.5931 (xpsp_sp3_gdr.100129-1321) |
| FileDescription: | Outlook Express |
| CompanyName: | Microsoft Corporation |
| CharacterSet: | Unicode |
| LanguageCode: | English (U.S.) |
| FileSubtype: | - |
| ObjectFileType: | Dynamic link library |
| FileOS: | Windows NT 32-bit |
| FileFlags: | (none) |
| FileFlagsMask: | 0x003f |
| ProductVersionNumber: | 6.0.2900.5931 |
| FileVersionNumber: | 6.0.2900.5931 |
| Subsystem: | Windows GUI |
| SubsystemVersion: | 4 |
| ImageVersion: | - |
| OSVersion: | 4 |
| EntryPoint: | 0x4e000 |
| UninitializedDataSize: | - |
| InitializedDataSize: | 232656 |
| CodeSize: | 81920 |
| LinkerVersion: | 8 |
| PEType: | PE32 |
| TimeStamp: | 2008:06:24 20:47:18+02:00 |
| MachineType: | Intel 386 or later, and compatibles |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 24-Jun-2008 18:47:18 |
| Detected languages: |
|
| CompanyName: | Microsoft Corporation |
| FileDescription: | Outlook Express |
| FileVersion: | 6.00.2900.5931 (xpsp_sp3_gdr.100129-1321) |
| InternalName: | MSOE |
| LegalCopyright: | © Microsoft Corporation. All rights reserved. |
| OriginalFilename: | MSOE.DLL |
| ProductName: | Microsoft® Windows® Operating System |
| ProductVersion: | 6.00.2900.5931 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000044 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 6 |
| Time date stamp: | 24-Jun-2008 18:47:18 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x00014000 | 0x00013200 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.21508 |
.rdata | 0x00015000 | 0x00027000 | 0x00027000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 7.77987 |
.data | 0x0003C000 | 0x00009000 | 0x00003C00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 2.66041 |
.idata | 0x00045000 | 0x00002DC0 | 0x00002600 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 5.33382 |
.rsrc | 0x00048000 | 0x00005F10 | 0x00005600 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 5.01548 |
.nkh\x07 | 0x0004E000 | 0x00001000 | 0x00000600 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 6.96347 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 3.57065 | 892 | Latin 1 / Western European | English - United States | RT_VERSION |
OBJXPL | 2.58685 | 446 | Latin 1 / Western European | English - United States | XPL |
Imports
ADVAPI32.dll |
GDI32.dll |
KERNEL32.dll |
ODBC32.dll |
OLEACC.dll |
OLEAUT32.dll |
SHELL32.dll |
SHLWAPI.dll |
USER32.dll |
VERSION.dll |
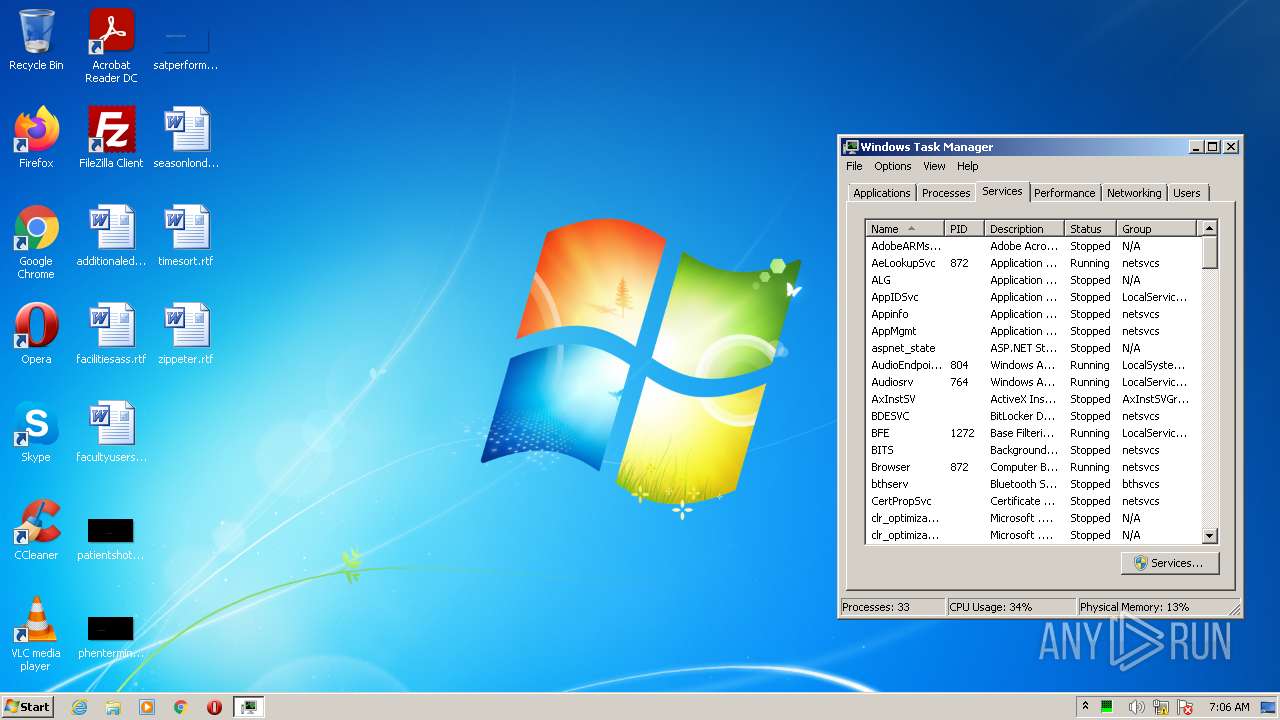
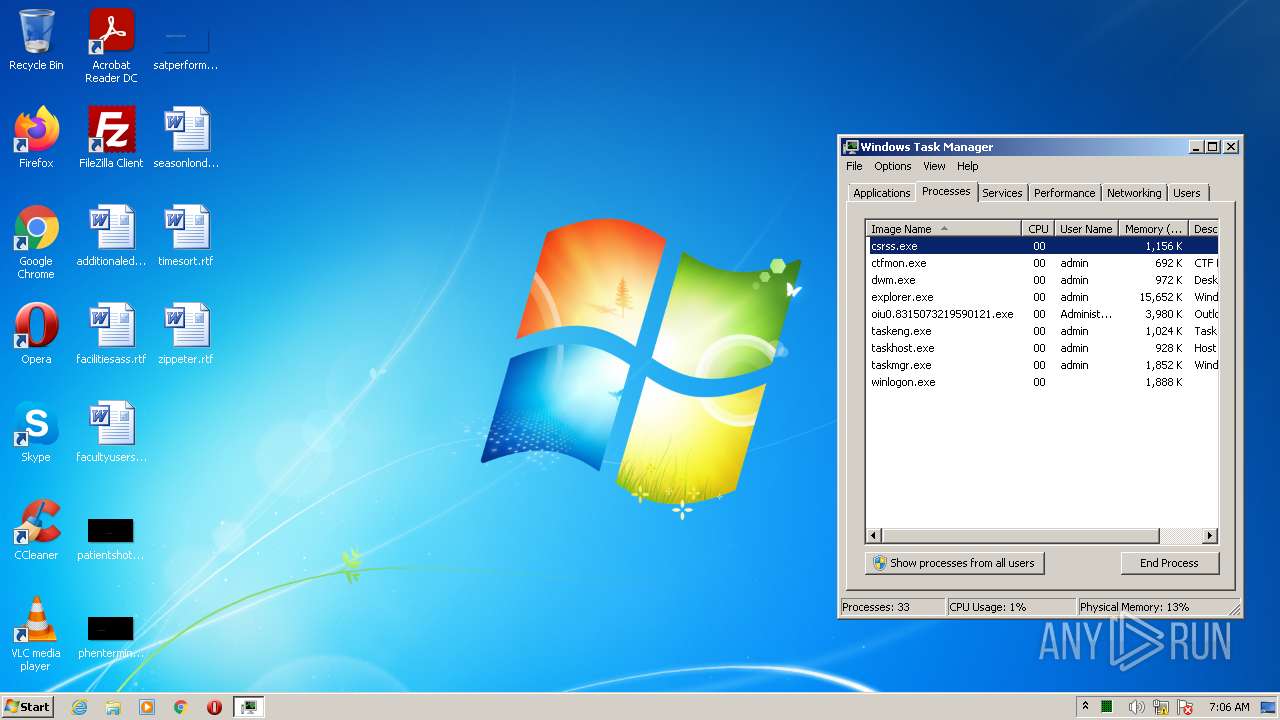
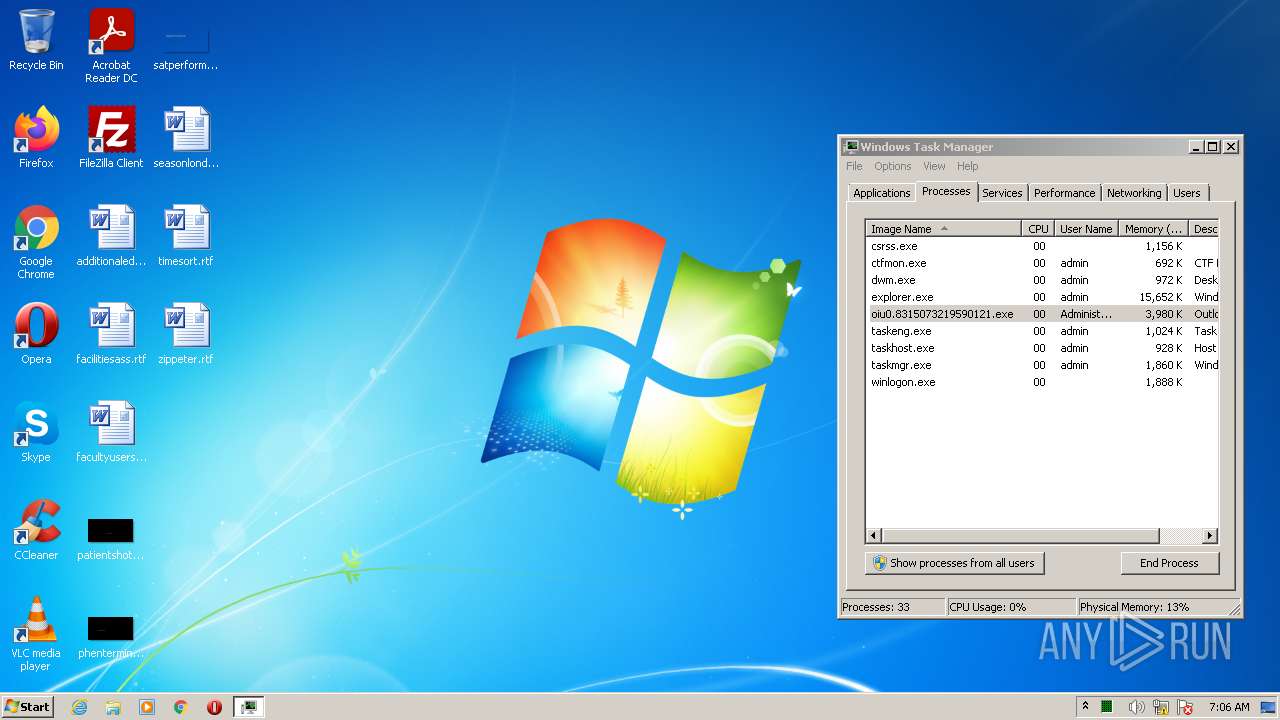
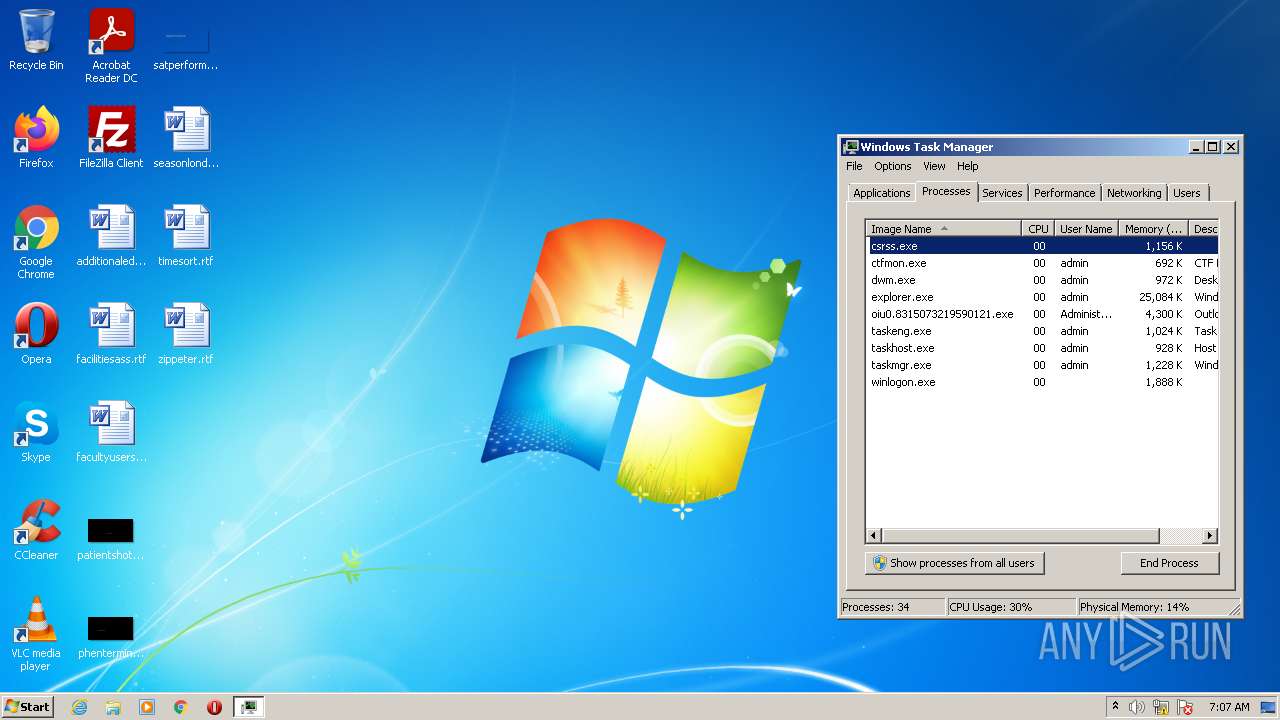
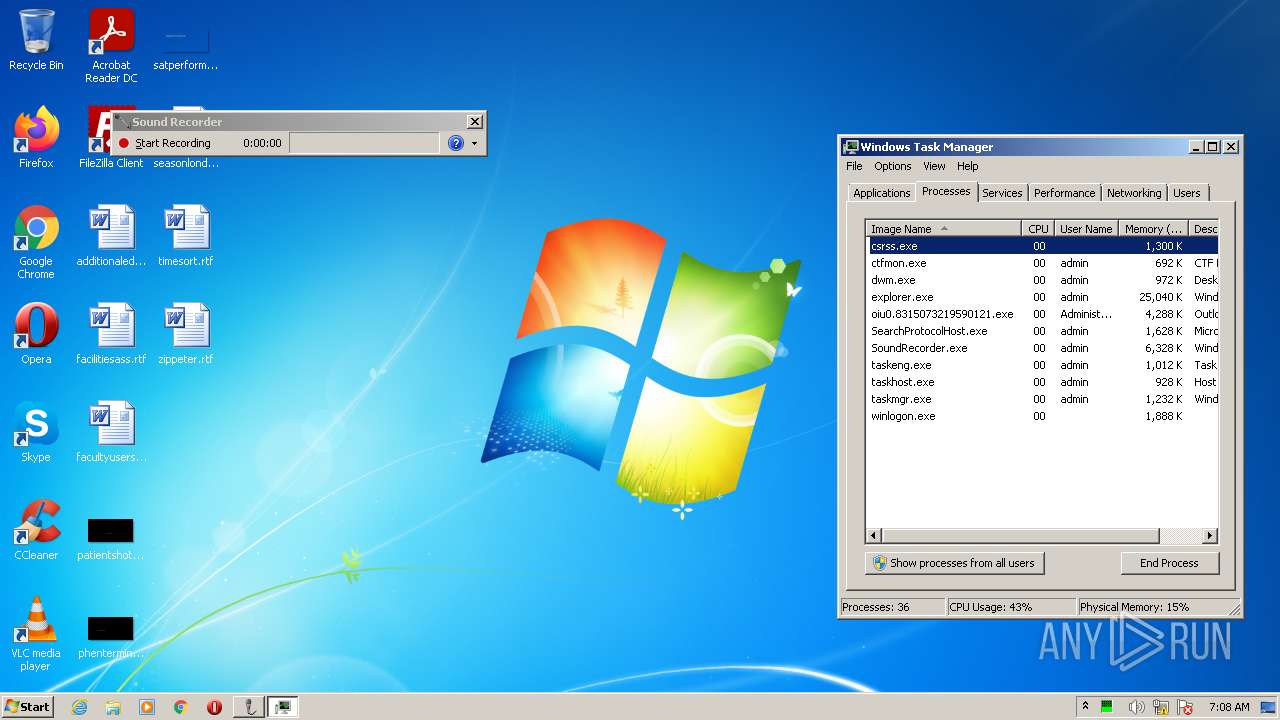
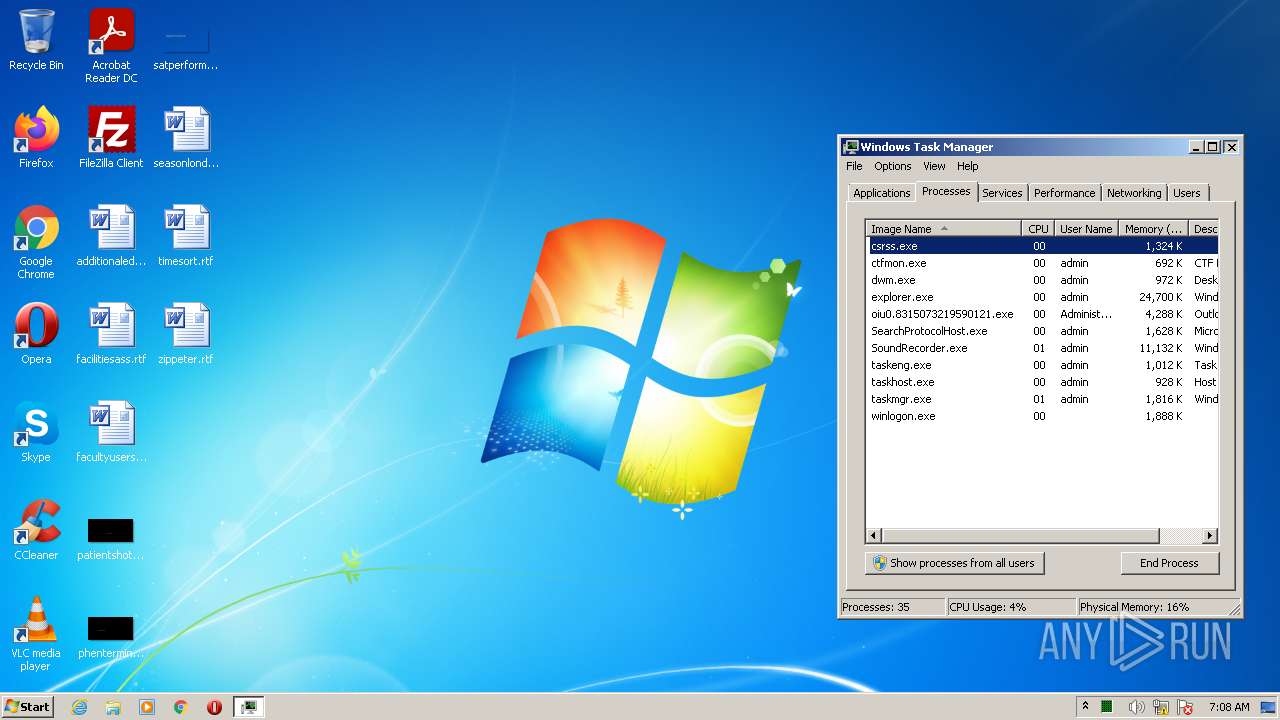
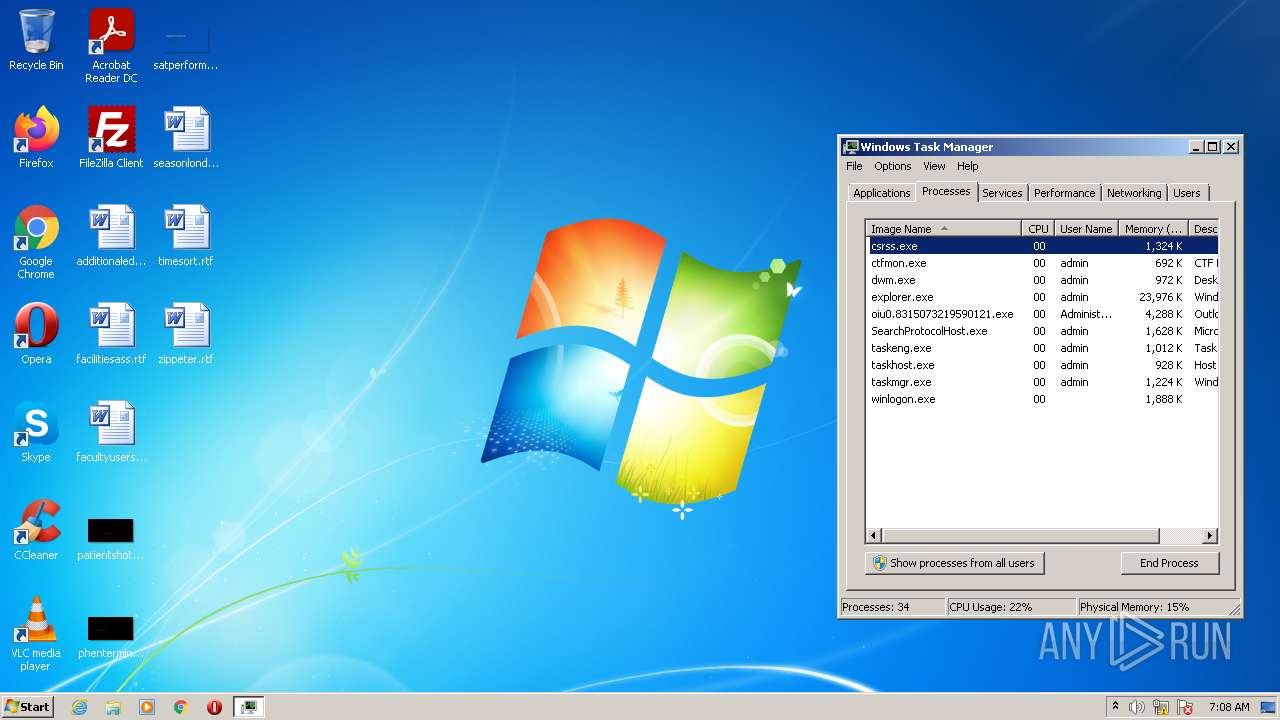
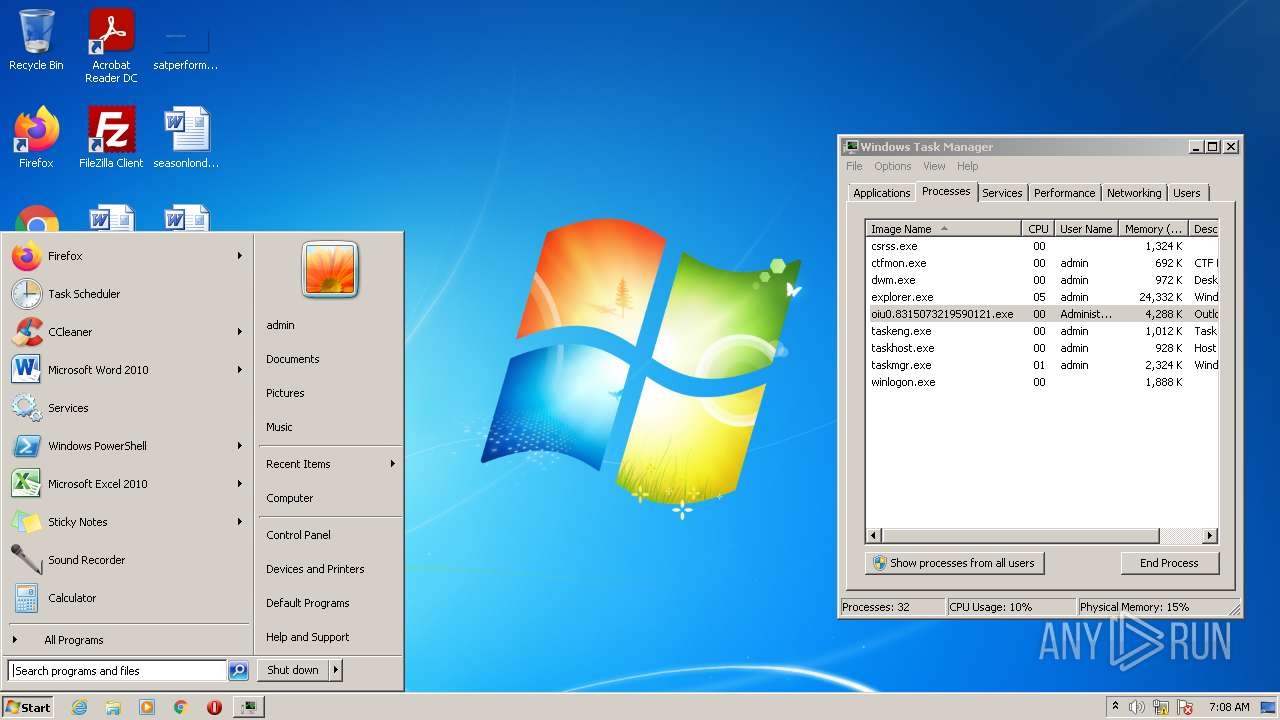
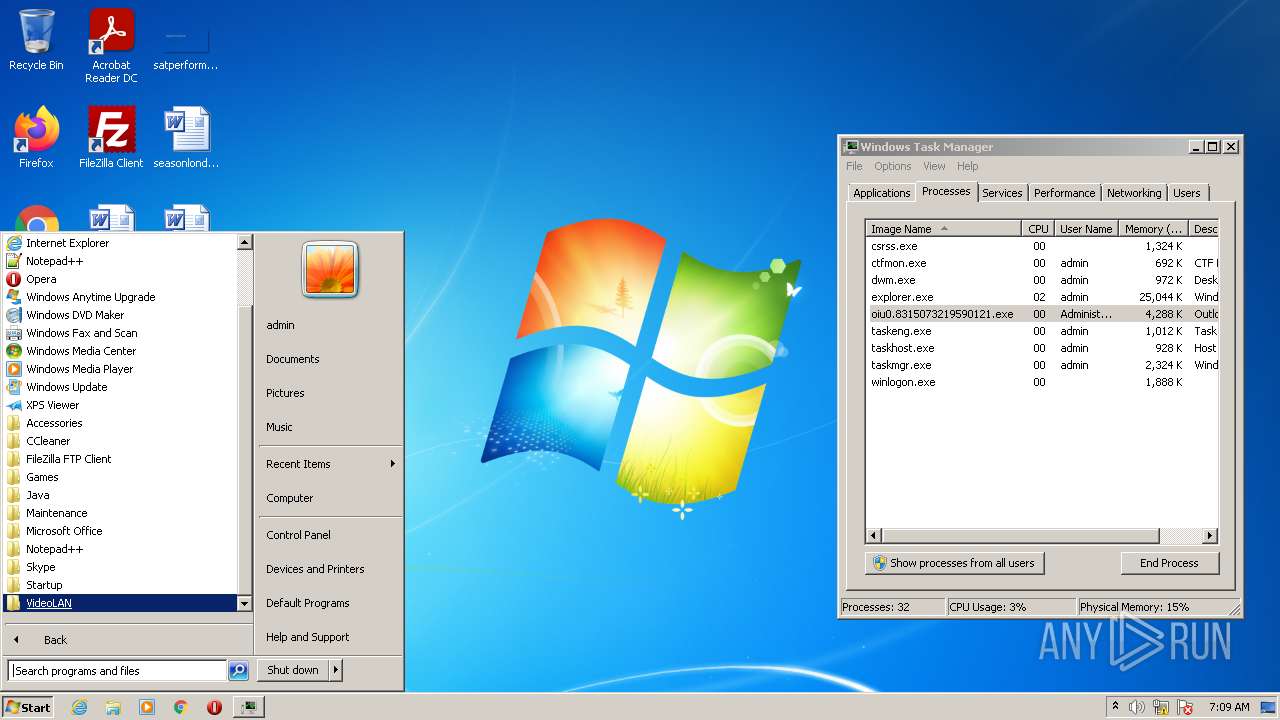
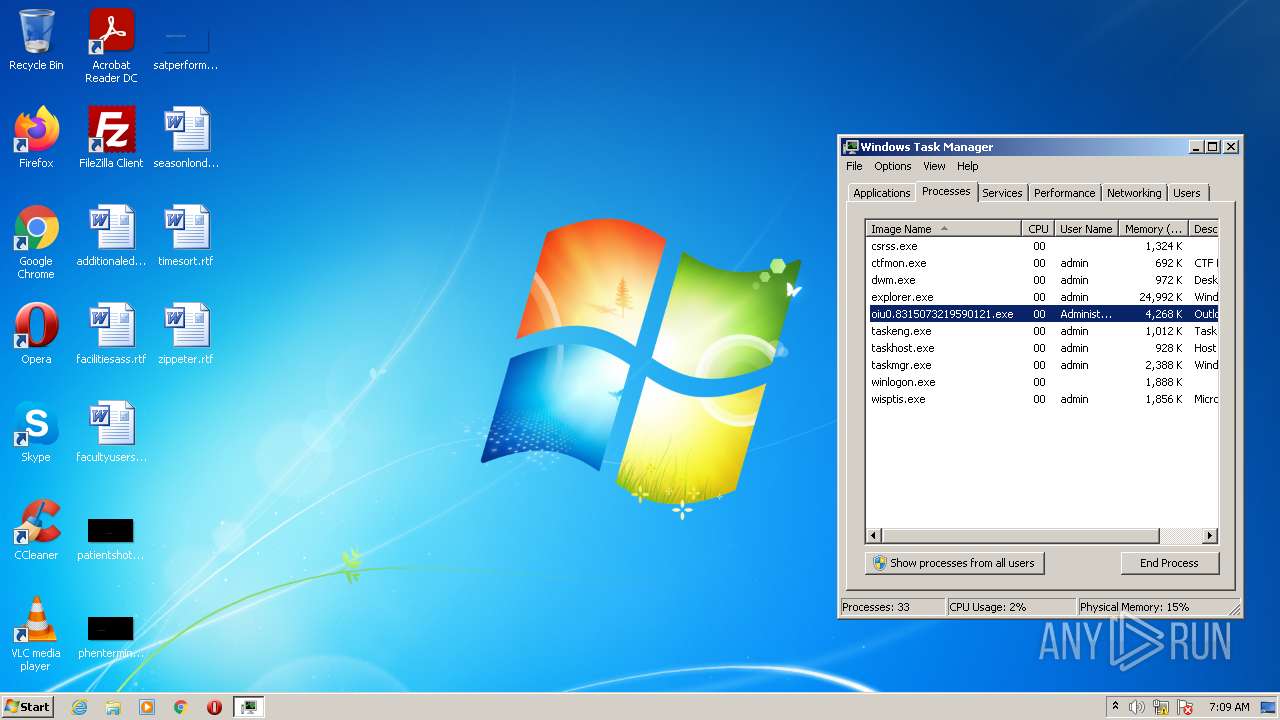
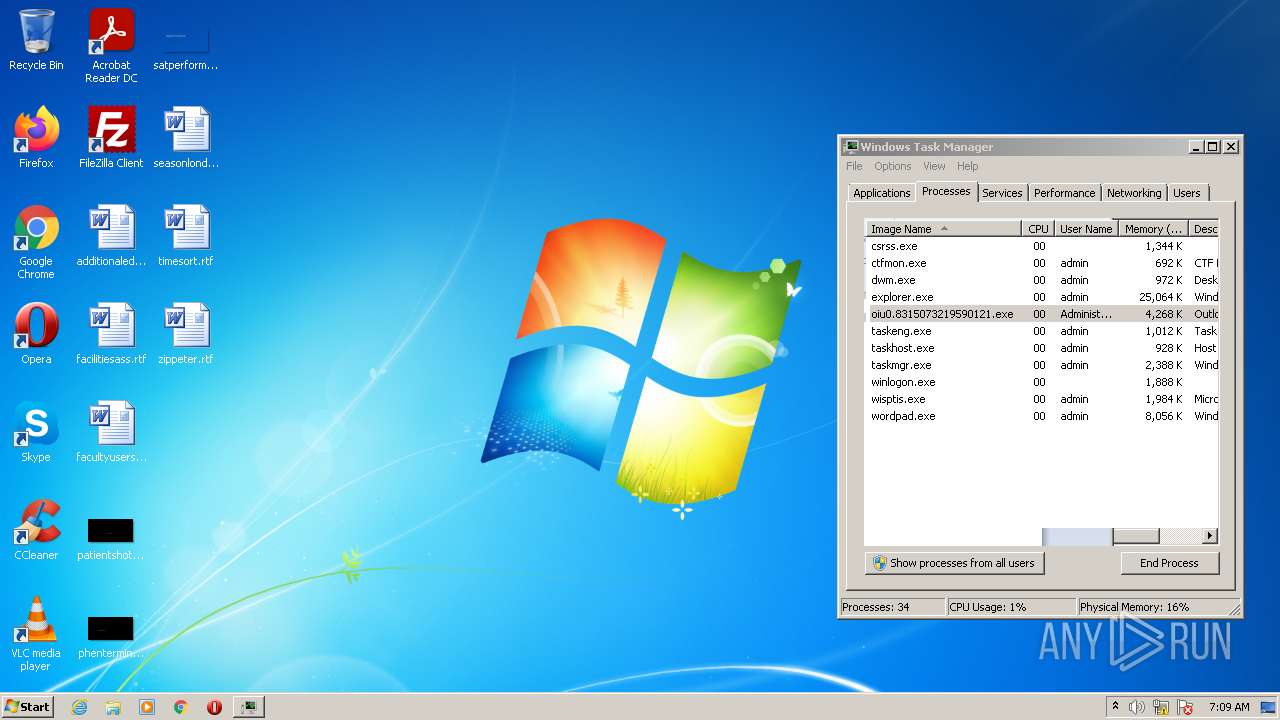
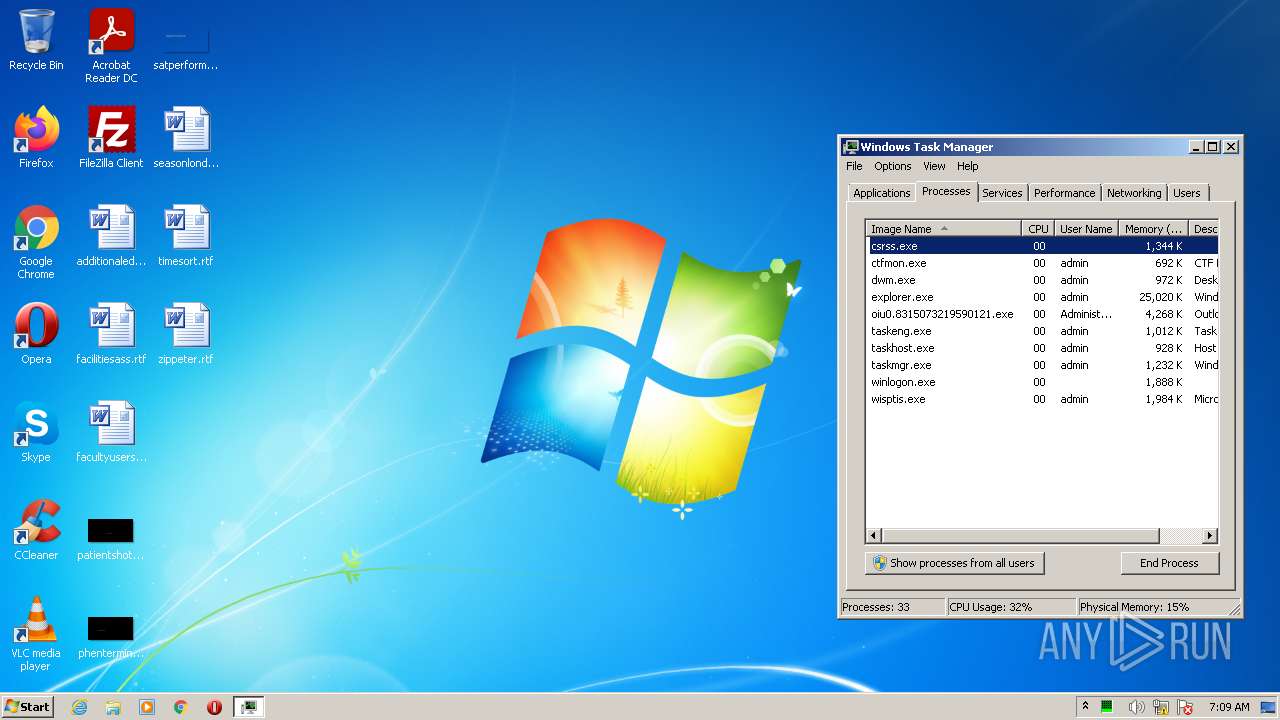
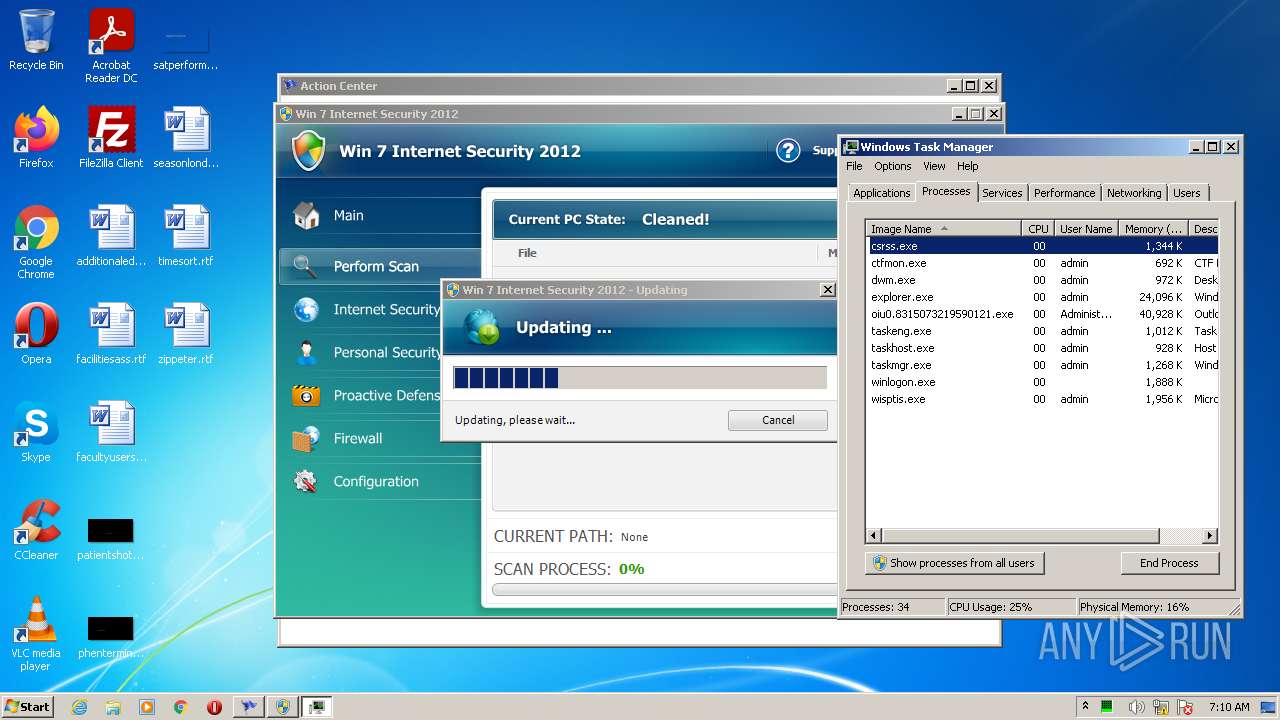
Total processes
57
Monitored processes
16
Malicious processes
2
Suspicious processes
3
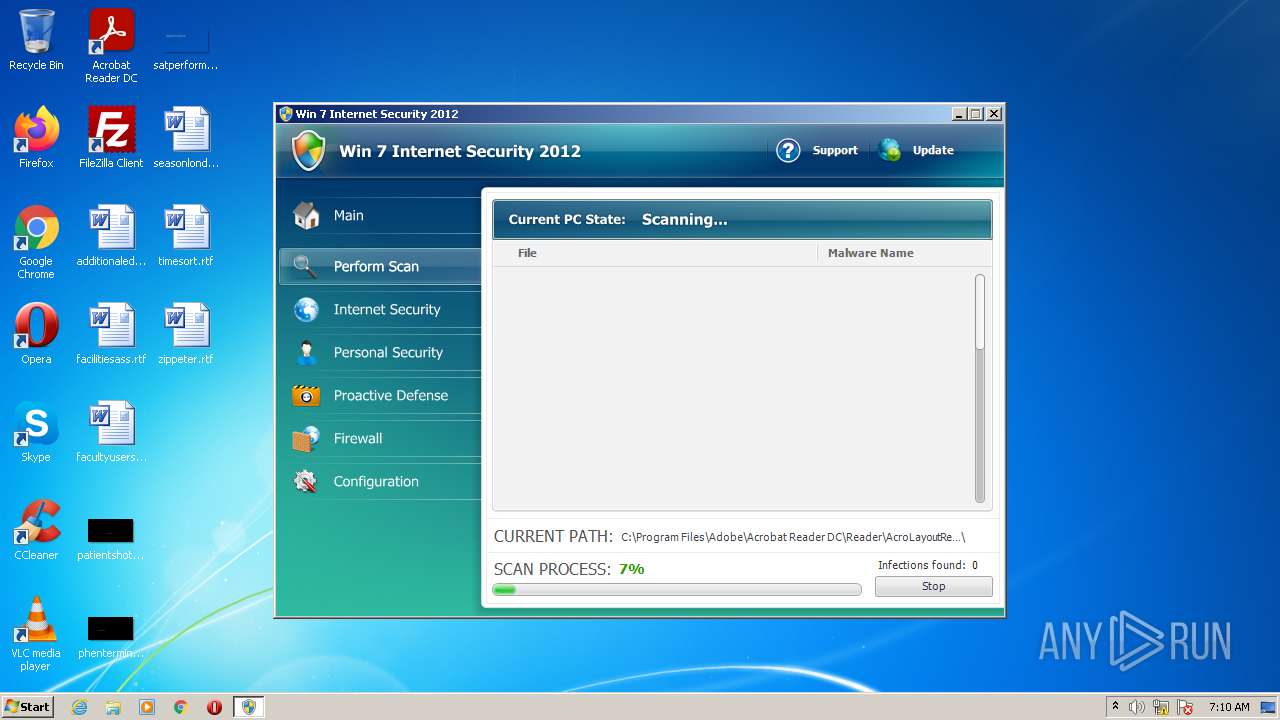
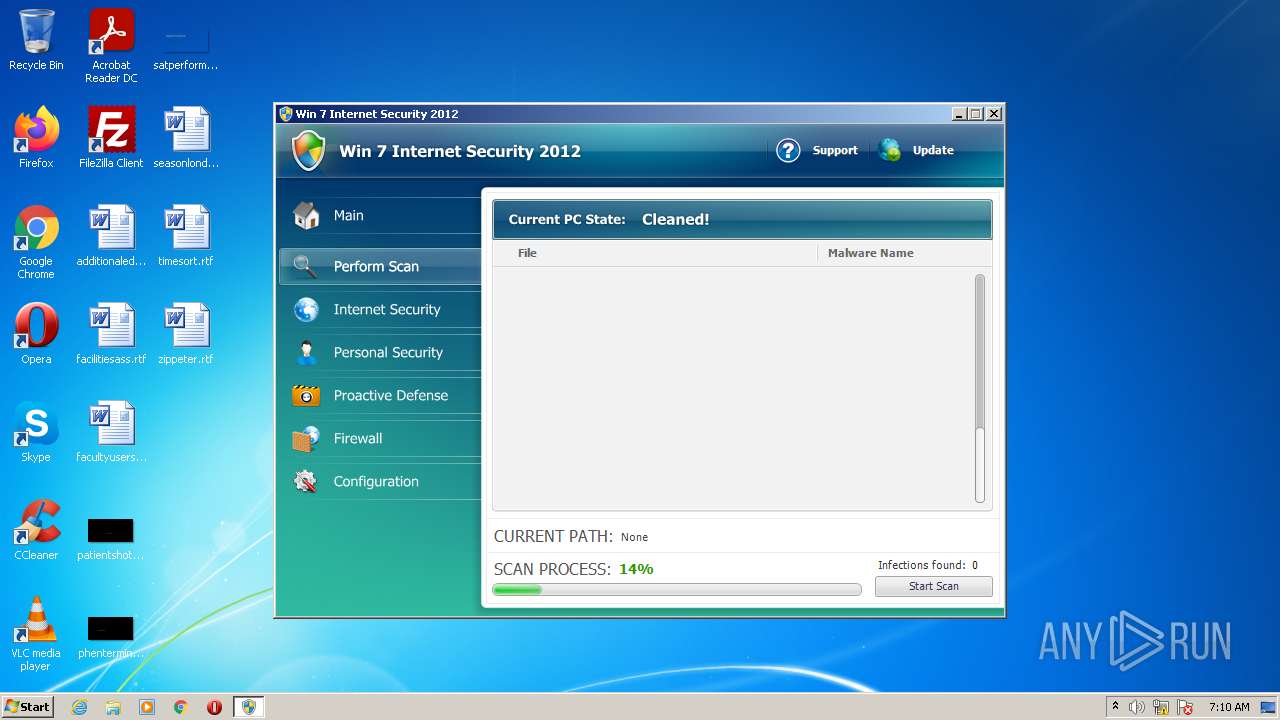
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
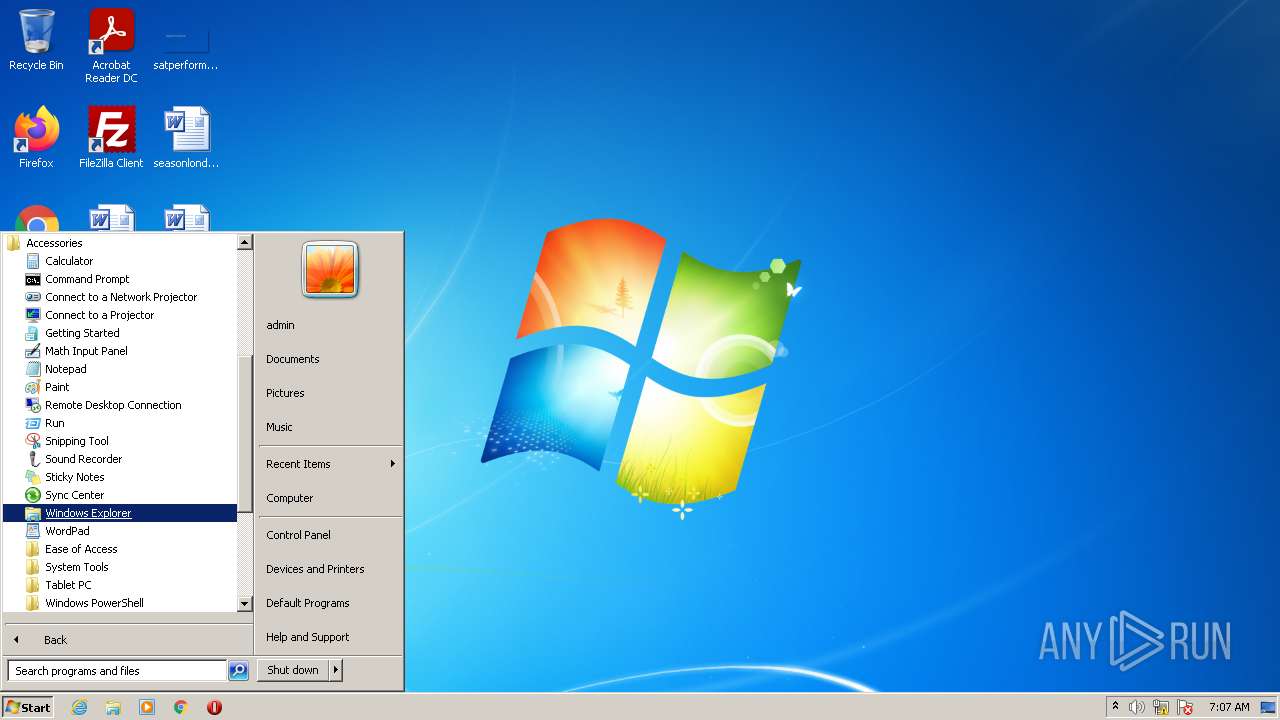
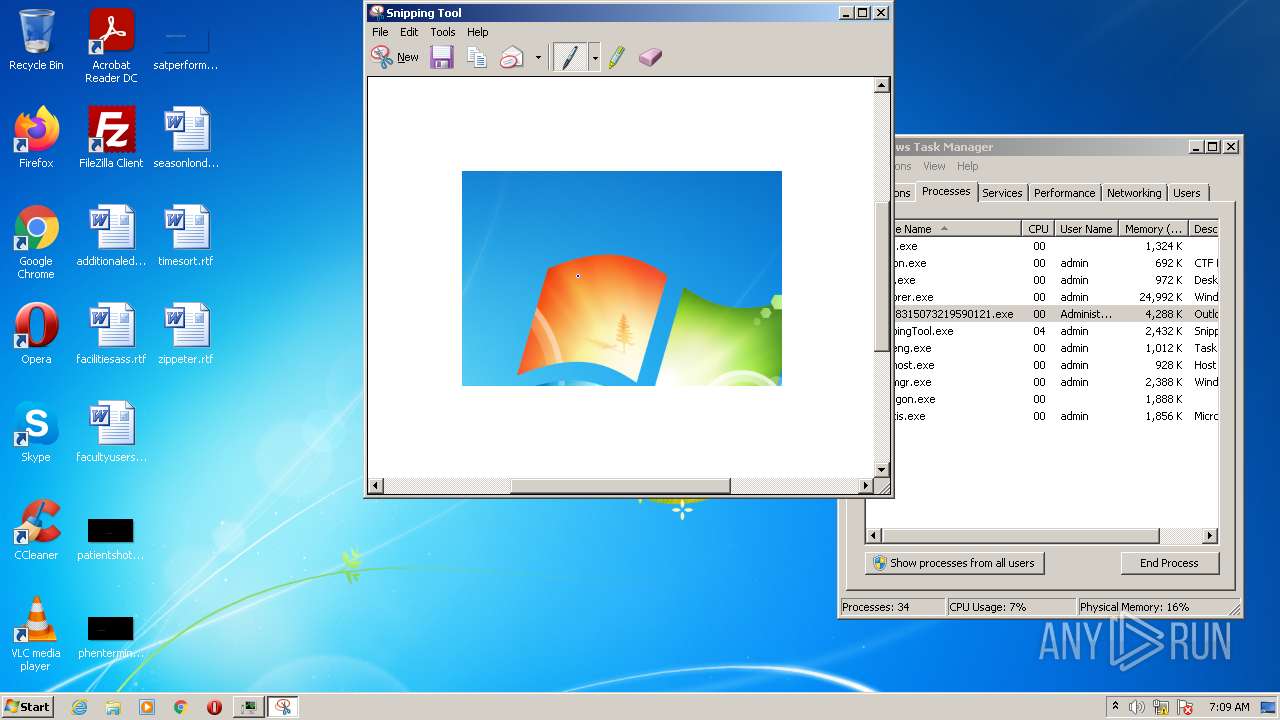
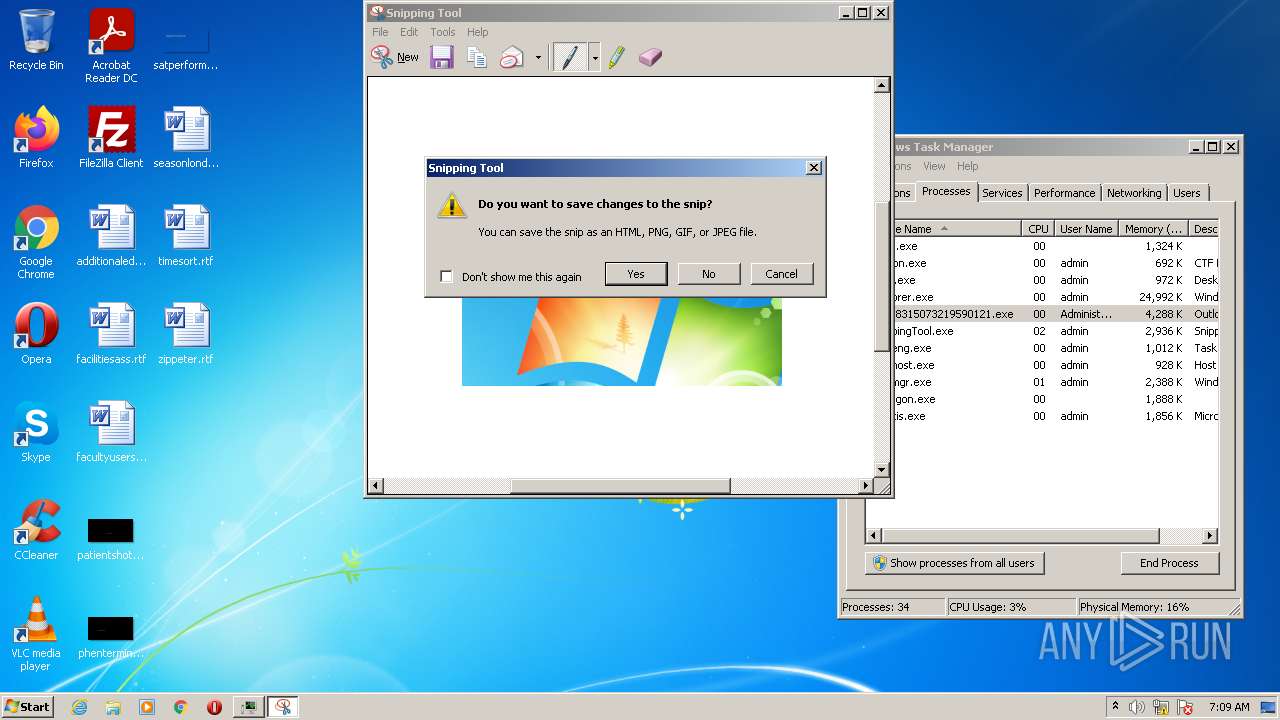
| 1868 | "C:\Windows\system32\SnippingTool.exe" | C:\Windows\system32\SnippingTool.exe | — | Explorer.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Snipping Tool Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2176 | "C:\Windows\system32\taskmgr.exe" /4 | C:\Windows\system32\taskmgr.exe | — | Explorer.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Task Manager Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2400 | "C:\Windows\system32\taskmgr.exe" /4 | C:\Windows\system32\taskmgr.exe | — | Explorer.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Task Manager Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2448 | "C:\Windows\system32\taskmgr.exe" /4 | C:\Windows\system32\taskmgr.exe | — | Explorer.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Task Manager Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2724 | "C:\Windows\system32\mspaint.exe" | C:\Windows\system32\mspaint.exe | — | Explorer.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Paint Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2836 | "C:\Windows\System32\runas.exe" /user:administrator C:\Users\admin\AppData\Local\Temp\oiu0.8315073219590121.exe | C:\Windows\System32\runas.exe | — | Explorer.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Run As Utility Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3096 | C:\Windows\system32\wbem\unsecapp.exe -Embedding | C:\Windows\system32\wbem\unsecapp.exe | — | svchost.exe | |||||||||||
User: Administrator Company: Microsoft Corporation Integrity Level: HIGH Description: Sink to receive asynchronous callbacks for WMI client application Exit code: 0 Version: 10.0.14409.1005 (rs1_srvoob.161208-1155) Modules
| |||||||||||||||
| 3312 | C:\Users\admin\AppData\Local\Temp\oiu0.8315073219590121.exe | C:\Users\admin\AppData\Local\Temp\oiu0.8315073219590121.exe | runas.exe | ||||||||||||
User: Administrator Company: Microsoft Corporation Integrity Level: HIGH Description: Outlook Express Exit code: 0 Version: 6.00.2900.5931 (xpsp_sp3_gdr.100129-1321) Modules
| |||||||||||||||
| 3428 | "C:\Program Files\Windows NT\Accessories\wordpad.exe" | C:\Program Files\Windows NT\Accessories\wordpad.exe | — | Explorer.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Wordpad Application Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3548 | "C:\Windows\system32\SoundRecorder.exe" | C:\Windows\system32\SoundRecorder.exe | — | Explorer.EXE | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Sound Recorder Exit code: 3221225547 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
6 338
Read events
6 103
Write events
225
Delete events
10
Modification events
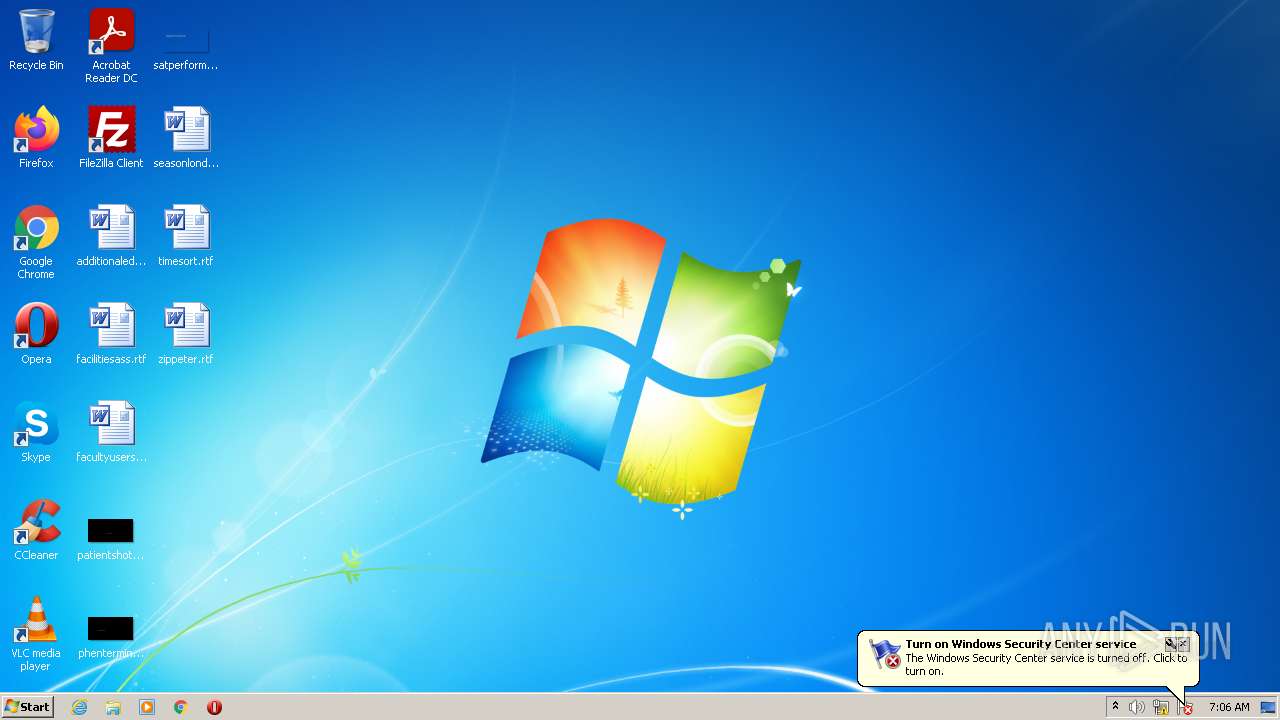
| (PID) Process: | (3312) oiu0.8315073219590121.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Policies\Explorer |
| Operation: | write | Name: | HideSCAHealth |
Value: 1 | |||
| (PID) Process: | (3312) oiu0.8315073219590121.exe | Key: | HKEY_CLASSES_ROOT\.exe |
| Operation: | write | Name: | (default) |
Value: hcf | |||
| (PID) Process: | (3312) oiu0.8315073219590121.exe | Key: | HKEY_CLASSES_ROOT\hcf |
| Operation: | write | Name: | (default) |
Value: Application | |||
| (PID) Process: | (3312) oiu0.8315073219590121.exe | Key: | HKEY_CLASSES_ROOT\hcf |
| Operation: | write | Name: | Content Type |
Value: application/x-msdownload | |||
| (PID) Process: | (3312) oiu0.8315073219590121.exe | Key: | HKEY_CLASSES_ROOT\hcf\DefaultIcon |
| Operation: | write | Name: | (default) |
Value: %1 | |||
| (PID) Process: | (3312) oiu0.8315073219590121.exe | Key: | HKEY_CLASSES_ROOT\hcf\shell\open\command |
| Operation: | write | Name: | (default) |
Value: "C:\Users\Administrator\AppData\Local\gzp.exe" -a "%1" %* | |||
| (PID) Process: | (3312) oiu0.8315073219590121.exe | Key: | HKEY_CLASSES_ROOT\hcf\shell\open\command |
| Operation: | write | Name: | IsolatedCommand |
Value: "%1" %* | |||
| (PID) Process: | (3312) oiu0.8315073219590121.exe | Key: | HKEY_CLASSES_ROOT\hcf\shell\runas\command |
| Operation: | write | Name: | (default) |
Value: "%1" %* | |||
| (PID) Process: | (3312) oiu0.8315073219590121.exe | Key: | HKEY_CLASSES_ROOT\hcf\shell\runas\command |
| Operation: | write | Name: | IsolatedCommand |
Value: "%1" %* | |||
| (PID) Process: | (3312) oiu0.8315073219590121.exe | Key: | HKEY_CLASSES_ROOT\hcf\shell\start\command |
| Operation: | write | Name: | (default) |
Value: "%1" %* | |||
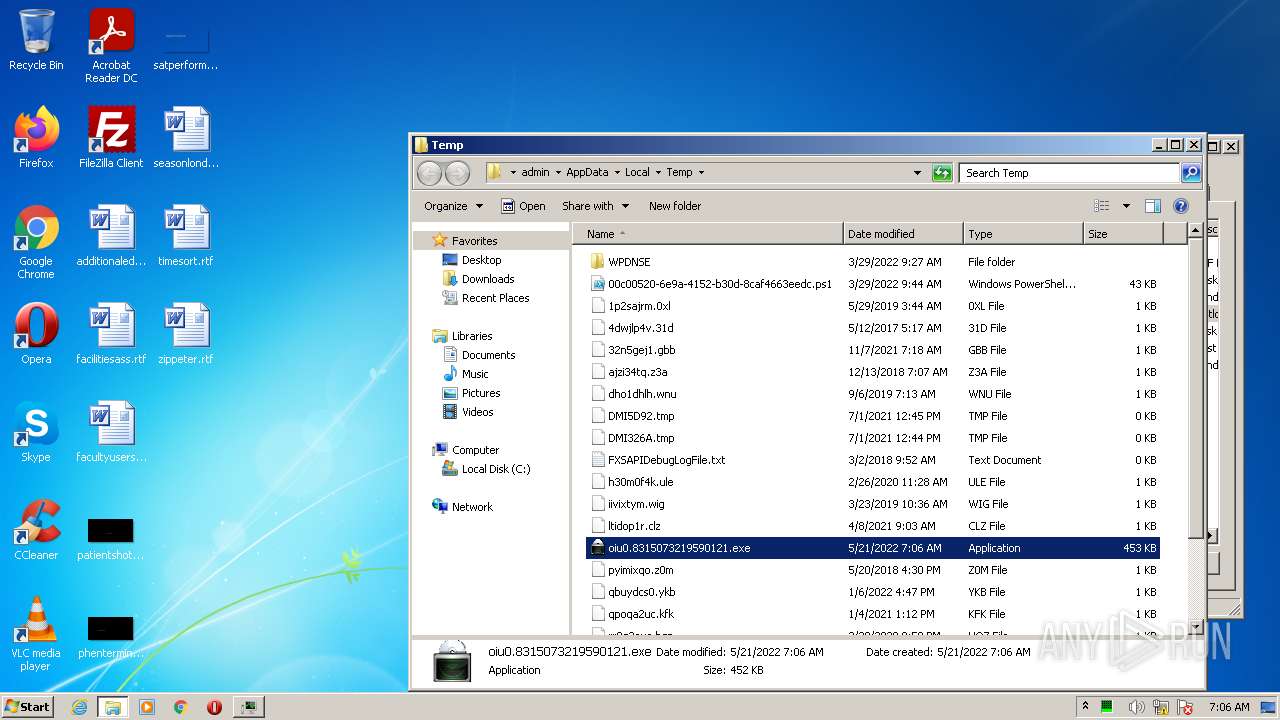
Executable files
2
Suspicious files
7
Text files
10
Unknown types
3
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 4024 | StikyNot.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\G2RE9ASQMHXNW3GUEIKD.temp | binary | |
MD5:— | SHA256:— | |||
| 3916 | DllHost.exe | C:\Users\Administrator\AppData\Local\Microsoft\Windows\WebCache\V01.log | binary | |
MD5:— | SHA256:— | |||
| 4024 | StikyNot.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\337ed59af273c758.customDestinations-ms | binary | |
MD5:— | SHA256:— | |||
| 3312 | oiu0.8315073219590121.exe | C:\Users\Administrator\AppData\Local\gzp.exe | executable | |
MD5:— | SHA256:— | |||
| 3916 | DllHost.exe | C:\Users\Administrator\AppData\Local\Microsoft\Windows\WebCache\V01.chk | binary | |
MD5:— | SHA256:— | |||
| 3916 | DllHost.exe | C:\Users\Administrator\AppData\Local\Microsoft\Windows\WebCache\WebCacheV01.dat | edb | |
MD5:— | SHA256:— | |||
| 3548 | SoundRecorder.exe | C:\Users\admin\AppData\Local\Temp\ARTF412.tmp | wmv | |
MD5:— | SHA256:— | |||
| 3312 | oiu0.8315073219590121.exe | C:\Users\ADMINI~1\AppData\Local\Temp\aib5304.tmp | executable | |
MD5:685F1CBD4AF30A1D0C25F252D399A666 | SHA256:0E478C95A7A07570A69E6061E7C1DA9001BCCAD9CC454F2ED4DA58824A13E0F4 | |||
| 3916 | DllHost.exe | C:\Users\Administrator\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\Q5UI5QUF\NewErrorPageTemplate[1] | text | |
MD5:CDF81E591D9CBFB47A7F97A2BCDB70B9 | SHA256:204D95C6FB161368C795BB63E538FE0B11F9E406494BB5758B3B0D60C5F651BD | |||
| 3916 | DllHost.exe | C:\Users\Administrator\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\Q5UI5QUF\errorPageStrings[1] | text | |
MD5:6B26ECFA58E37D4B5EC861FCDD3F04FA | SHA256:7F7D1069CA8A852C1C8EB36E1D988FE6A9C17ECB8EFF1F66FC5EBFEB5418723A | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
45
DNS requests
73
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3312 | oiu0.8315073219590121.exe | 20.84.181.62:80 | microsoft.com | — | US | suspicious |
3312 | oiu0.8315073219590121.exe | 20.103.85.33:80 | microsoft.com | — | US | suspicious |
— | — | 20.103.85.33:80 | microsoft.com | — | US | suspicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
vuforazaj.com |
| unknown |
fyzybopufanuj.com |
| unknown |
nyzysemadyk.com |
| suspicious |
gavotataran.com |
| unknown |
pubepujiwusiwy.com |
| unknown |
zetofyhecynovu.com |
| unknown |
hypulycyfaqaba.com |
| unknown |
rehudomydefe.com |
| unknown |
vequtycarykeg.com |
| unknown |
sesycifaqago.com |
| unknown |