| URL: | https://surl.me/6f4yf |
| Full analysis: | https://app.any.run/tasks/0fb7ed8f-4885-4dfa-81fb-a1168fea181d |
| Verdict: | Malicious activity |
| Analysis date: | November 29, 2020, 11:08:54 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | EE02AD889FF5EFEACB67B77B7388CF97 |
| SHA1: | F7D3D26791BA0518E350179079F40A9F962E6CEF |
| SHA256: | 6550FEB2A1FF523282F897D63740BC09FEEF6C60EE2B1EBDC89BD485960AFDC1 |
| SSDEEP: | 3:N8dZR+on:2N+o |
MALICIOUS
No malicious indicators.SUSPICIOUS
No suspicious indicators.INFO
Reads internet explorer settings
- iexplore.exe (PID: 2344)
Reads settings of System Certificates
- iexplore.exe (PID: 2388)
- iexplore.exe (PID: 2344)
Application launched itself
- iexplore.exe (PID: 2388)
Changes internet zones settings
- iexplore.exe (PID: 2388)
Adds / modifies Windows certificates
- iexplore.exe (PID: 2388)
Creates files in the user directory
- iexplore.exe (PID: 2388)
Changes settings of System certificates
- iexplore.exe (PID: 2388)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
35
Monitored processes
2
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2344 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:2388 CREDAT:267521 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 2388 | "C:\Program Files\Internet Explorer\iexplore.exe" "https://surl.me/6f4yf" | C:\Program Files\Internet Explorer\iexplore.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
Total events
1 027
Read events
935
Write events
90
Delete events
2
Modification events
| (PID) Process: | (2388) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateLowDateTime |
Value: 559252588 | |||
| (PID) Process: | (2388) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateHighDateTime |
Value: 30852672 | |||
| (PID) Process: | (2388) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (2388) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (2388) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (2388) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (2388) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | write | Name: | ProxyEnable |
Value: 0 | |||
| (PID) Process: | (2388) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Connections |
| Operation: | write | Name: | SavedLegacySettings |
Value: 46000000A5000000010000000000000000000000000000000000000000000000C0E333BBEAB1D301000000000000000000000000020000001700000000000000FE800000000000007D6CB050D9C573F70B000000000000006D00330032005C004D00530049004D004700330032002E0064006C000100000004AA400014AA4000040000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000002000000C0A8016400000000000000000000000000000000000000000800000000000000805D3F00983740000008000002000000000000600000002060040000B8A94000020000008802000060040000B8A9400004000000F8010000B284000088B64000B84B400043003A000000000000000000000000000000000000000000 | |||
| (PID) Process: | (2388) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (2388) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
Executable files
0
Suspicious files
21
Text files
57
Unknown types
10
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2344 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\Low\Cab1B4.tmp | — | |
MD5:— | SHA256:— | |||
| 2344 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\Low\Tar1B5.tmp | — | |
MD5:— | SHA256:— | |||
| 2388 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\Internet Explorer\Services\search_{0633EE93-D776-472f-A0FF-E1416B8B2E3A}.ico | — | |
MD5:— | SHA256:— | |||
| 2344 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\E49827401028F7A0F97B5576C77A26CB_7CE95D8DCA26FE957E7BD7D76F353B08 | der | |
MD5:— | SHA256:— | |||
| 2344 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\YTOWV792\l_DE[1].png | image | |
MD5:— | SHA256:— | |||
| 2344 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\E49827401028F7A0F97B5576C77A26CB_7CE95D8DCA26FE957E7BD7D76F353B08 | binary | |
MD5:— | SHA256:— | |||
| 2344 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\8282537A1700AEC149BE2706B94BE70A | binary | |
MD5:— | SHA256:— | |||
| 2344 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\DY534W2X\l_EN[1].png | image | |
MD5:— | SHA256:— | |||
| 2344 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\MFAQUS6V\sendtofriend[1].htm | html | |
MD5:— | SHA256:— | |||
| 2344 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\DY534W2X\9KKWQS3Q.htm | html | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
69
TCP/UDP connections
76
DNS requests
18
Threats
57
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2388 | iexplore.exe | GET | 302 | 43.243.110.180:80 | http://momomeifu.com/favicon.ico | HK | html | 206 b | unknown |
2344 | iexplore.exe | GET | 200 | 23.55.163.71:80 | http://isrg.trustid.ocsp.identrust.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBRv9GhNQxLSSGKBnMArPUcsHYovpgQUxKexpHsscfrb4UuQdf%2FEFWCFiRACEAoBQUIAAAFThXNqC4Xspwg%3D | US | der | 1.37 Kb | whitelisted |
2344 | iexplore.exe | GET | 302 | 43.243.110.180:80 | http://momomeifu.com/ | HK | html | 206 b | unknown |
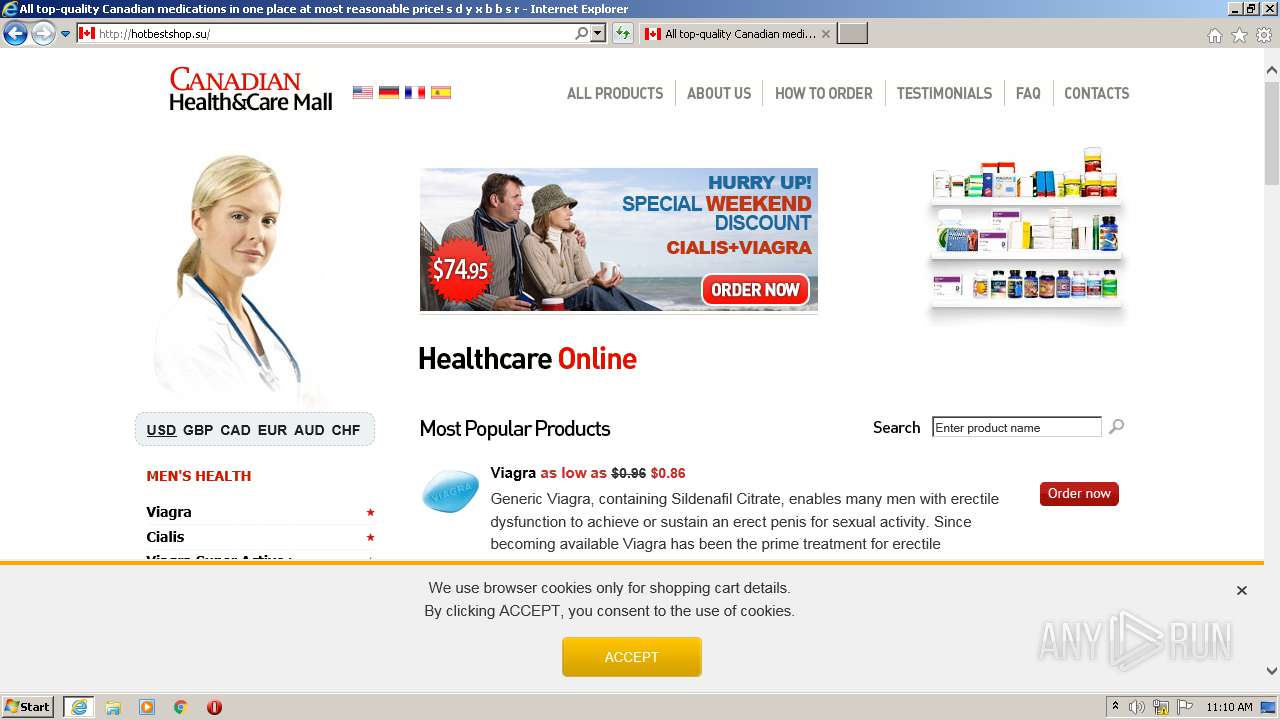
2388 | iexplore.exe | GET | 403 | 85.254.72.9:80 | http://hotbestshop.su/ | LV | html | 168 b | suspicious |
2344 | iexplore.exe | GET | 200 | 85.254.72.9:80 | http://hotbestshop.su/ | LV | html | 9.41 Kb | suspicious |
2344 | iexplore.exe | GET | 200 | 85.254.72.9:80 | http://hotbestshop.su/images/chcm/logo.gif | LV | image | 4.08 Kb | suspicious |
2344 | iexplore.exe | GET | 200 | 85.254.72.9:80 | http://hotbestshop.su/images/chcm/l_EN.png | LV | image | 668 b | suspicious |
2344 | iexplore.exe | GET | 200 | 85.254.72.9:80 | http://hotbestshop.su/images/chcm/l_FR.png | LV | image | 727 b | suspicious |
2344 | iexplore.exe | GET | 200 | 85.254.72.9:80 | http://hotbestshop.su/images/chcm/l_ES.png | LV | image | 647 b | suspicious |
2344 | iexplore.exe | GET | 200 | 85.254.72.9:80 | http://hotbestshop.su/images/chcm/l_DE.png | LV | image | 407 b | suspicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2344 | iexplore.exe | 144.217.15.46:443 | surl.me | OVH SAS | CA | suspicious |
2344 | iexplore.exe | 23.55.163.71:80 | isrg.trustid.ocsp.identrust.com | Akamai International B.V. | US | suspicious |
2344 | iexplore.exe | 23.55.163.48:80 | ocsp.int-x3.letsencrypt.org | Akamai International B.V. | US | unknown |
2344 | iexplore.exe | 23.55.163.68:80 | ocsp.int-x3.letsencrypt.org | Akamai International B.V. | US | suspicious |
2344 | iexplore.exe | 43.243.110.180:80 | momomeifu.com | Sun Network (Hong Kong) Limited - HongKong Backbone | HK | unknown |
2388 | iexplore.exe | 13.107.21.200:80 | www.bing.com | Microsoft Corporation | US | whitelisted |
2388 | iexplore.exe | 43.243.110.180:80 | momomeifu.com | Sun Network (Hong Kong) Limited - HongKong Backbone | HK | unknown |
2388 | iexplore.exe | 85.254.72.9:80 | hotbestshop.su | LATNET SERVISS Ltd. | LV | suspicious |
2344 | iexplore.exe | 85.254.72.9:80 | hotbestshop.su | LATNET SERVISS Ltd. | LV | suspicious |
— | — | 85.254.72.9:80 | hotbestshop.su | LATNET SERVISS Ltd. | LV | suspicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
surl.me |
| suspicious |
isrg.trustid.ocsp.identrust.com |
| whitelisted |
ocsp.int-x3.letsencrypt.org |
| whitelisted |
momomeifu.com |
| unknown |
api.bing.com |
| whitelisted |
www.bing.com |
| whitelisted |
hotbestshop.su |
| suspicious |
iecvlist.microsoft.com |
| whitelisted |
r20swj13mr.microsoft.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
1044 | svchost.exe | Potentially Bad Traffic | ET DNS Query for .su TLD (Soviet Union) Often Malware Related |
2388 | iexplore.exe | Potentially Bad Traffic | ET POLICY HTTP Request to .su TLD (Soviet Union) Often Malware Related |
2344 | iexplore.exe | Potentially Bad Traffic | ET POLICY HTTP Request to .su TLD (Soviet Union) Often Malware Related |
2344 | iexplore.exe | Potentially Bad Traffic | ET POLICY HTTP Request to .su TLD (Soviet Union) Often Malware Related |
2344 | iexplore.exe | Potentially Bad Traffic | ET POLICY HTTP Request to .su TLD (Soviet Union) Often Malware Related |
2344 | iexplore.exe | Potentially Bad Traffic | ET POLICY HTTP Request to .su TLD (Soviet Union) Often Malware Related |
2344 | iexplore.exe | Potentially Bad Traffic | ET POLICY HTTP Request to .su TLD (Soviet Union) Often Malware Related |
2344 | iexplore.exe | Potentially Bad Traffic | ET POLICY HTTP Request to .su TLD (Soviet Union) Often Malware Related |
2344 | iexplore.exe | Potentially Bad Traffic | ET POLICY HTTP Request to .su TLD (Soviet Union) Often Malware Related |
2344 | iexplore.exe | Potentially Bad Traffic | ET POLICY HTTP Request to .su TLD (Soviet Union) Often Malware Related |