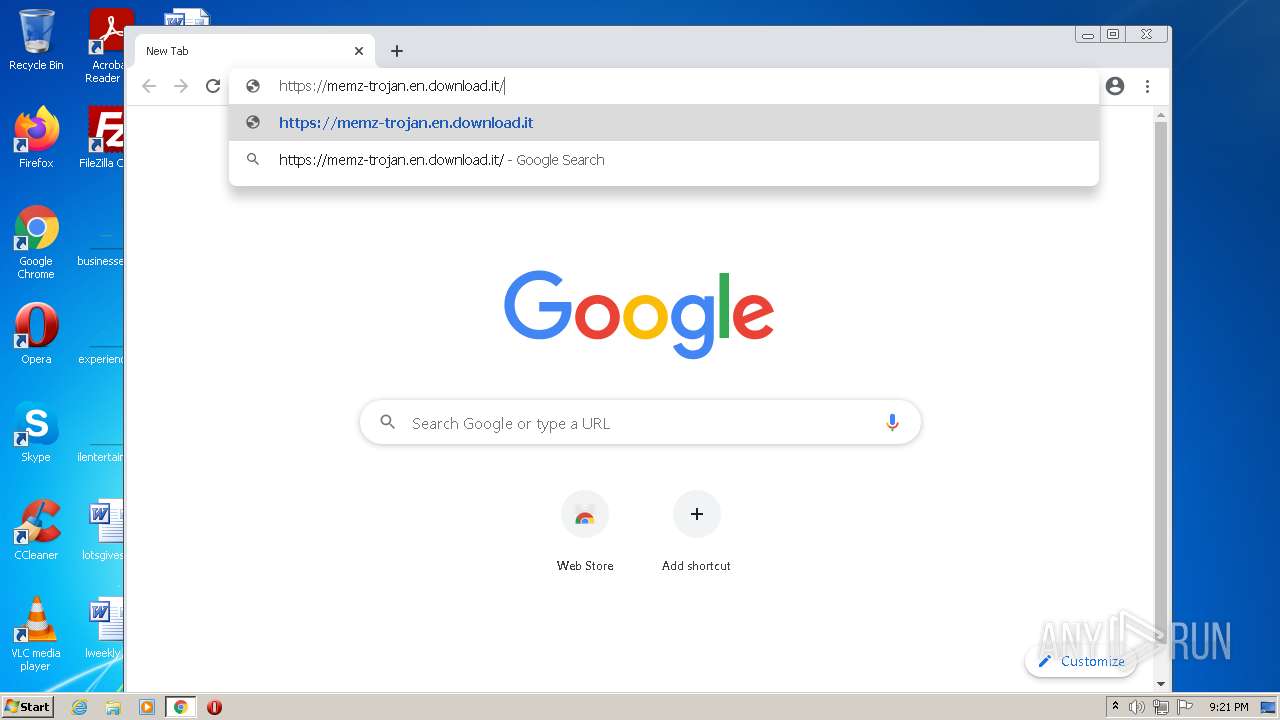
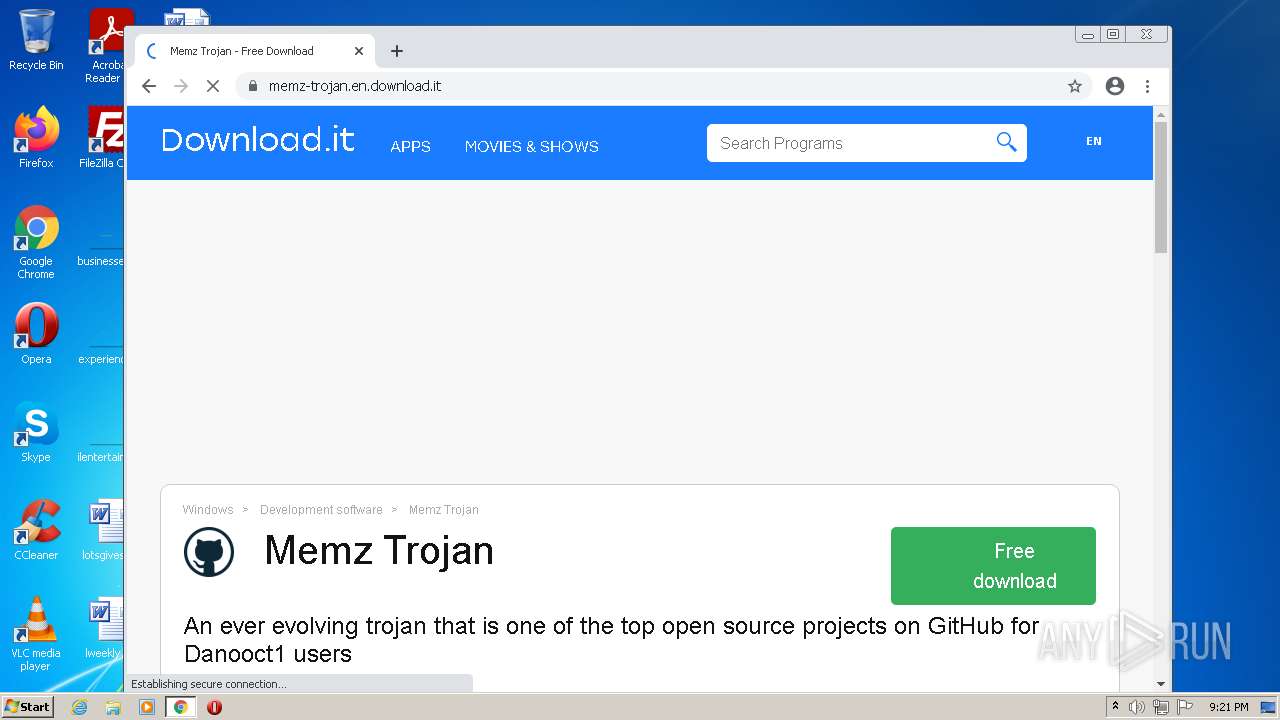
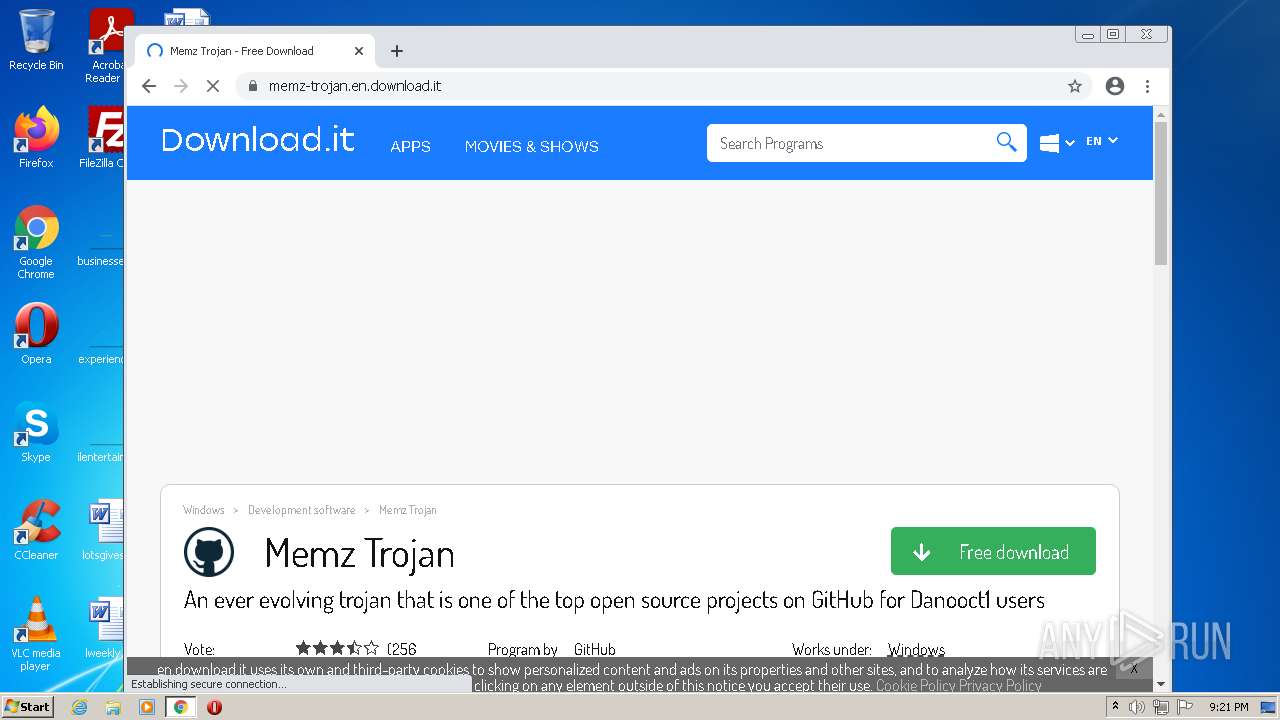
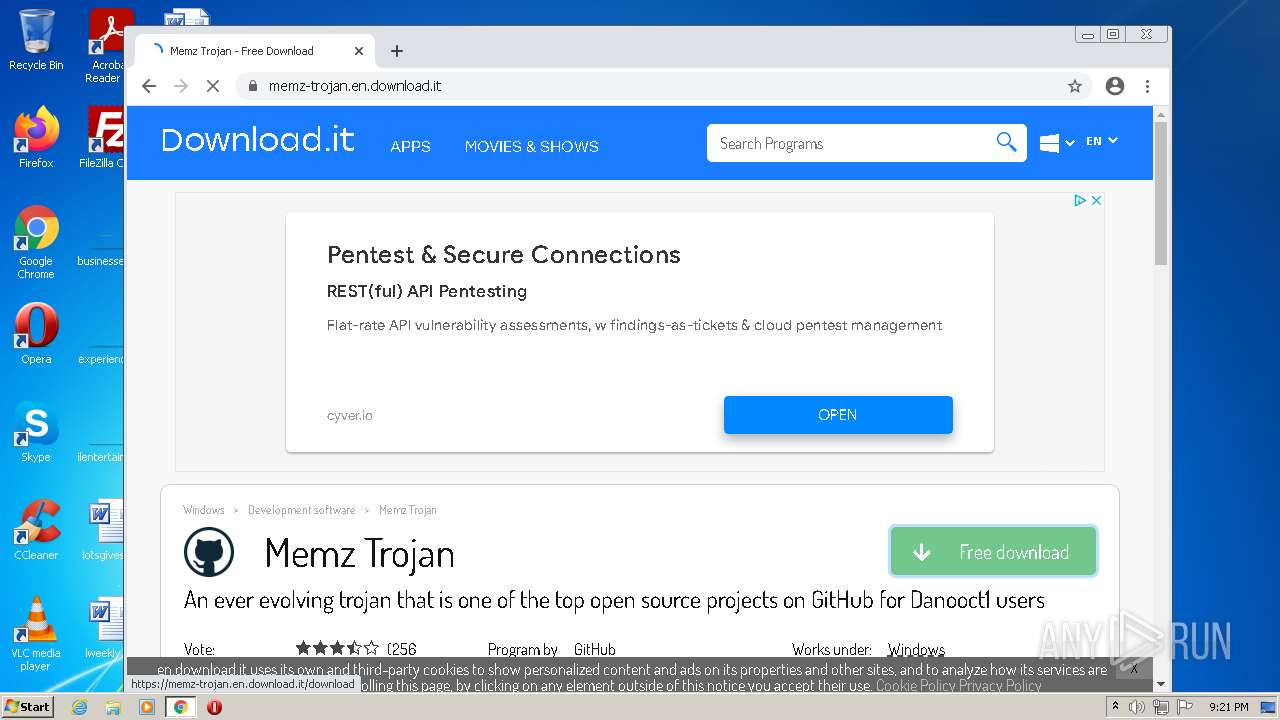
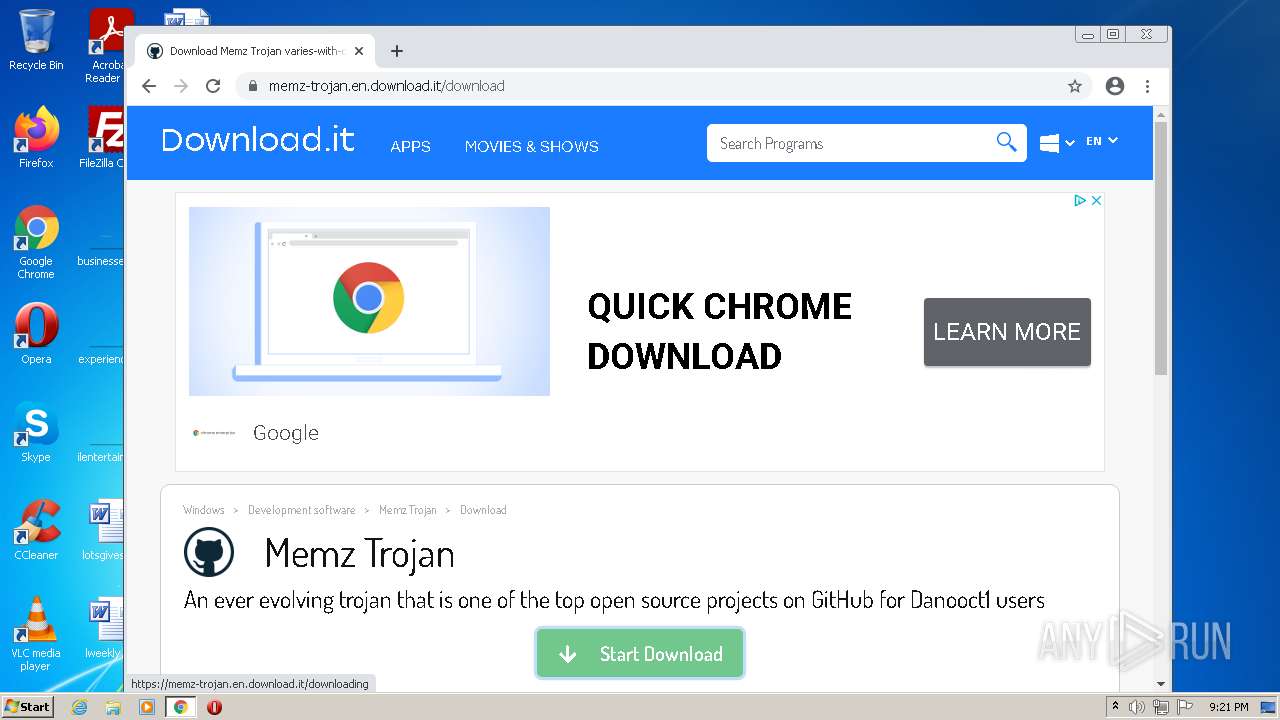
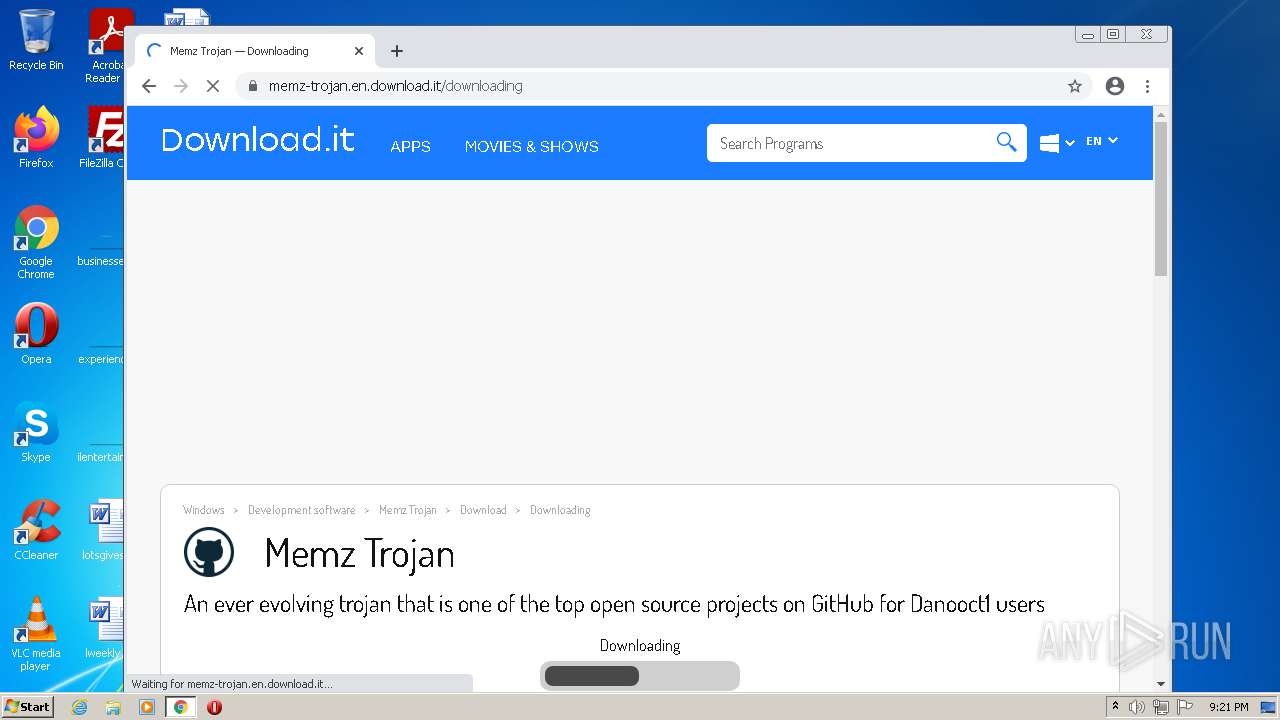
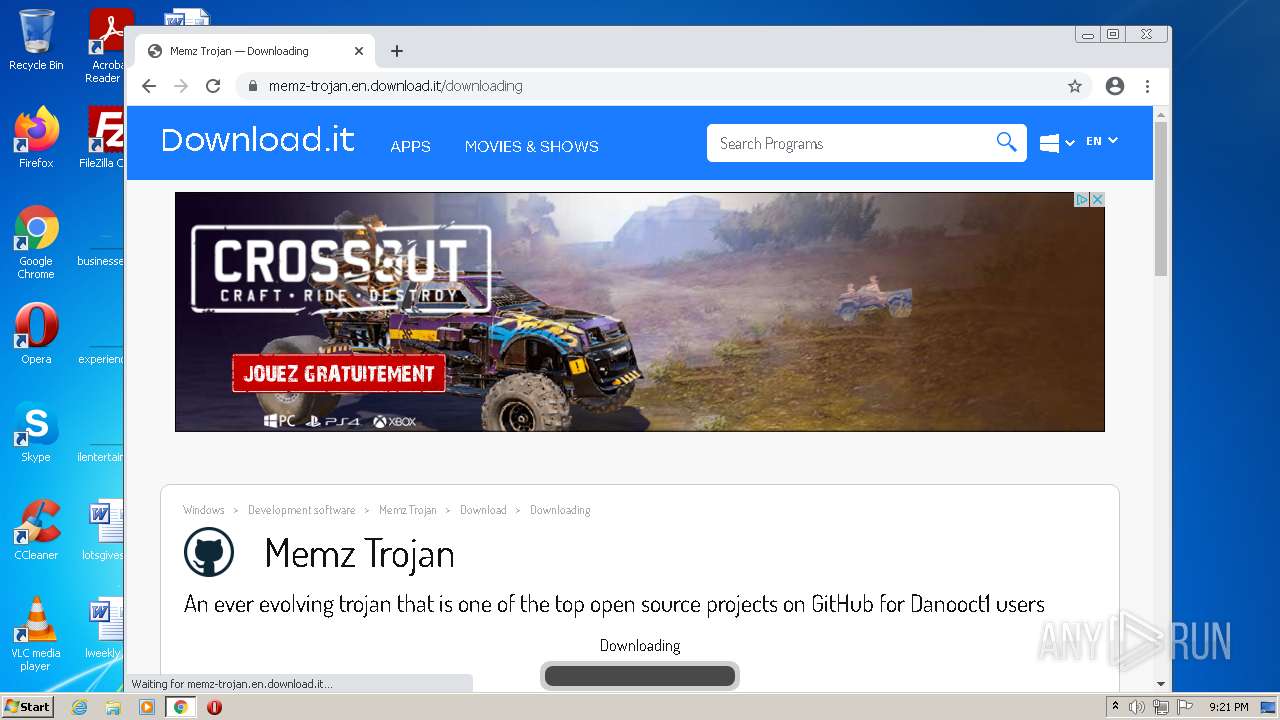
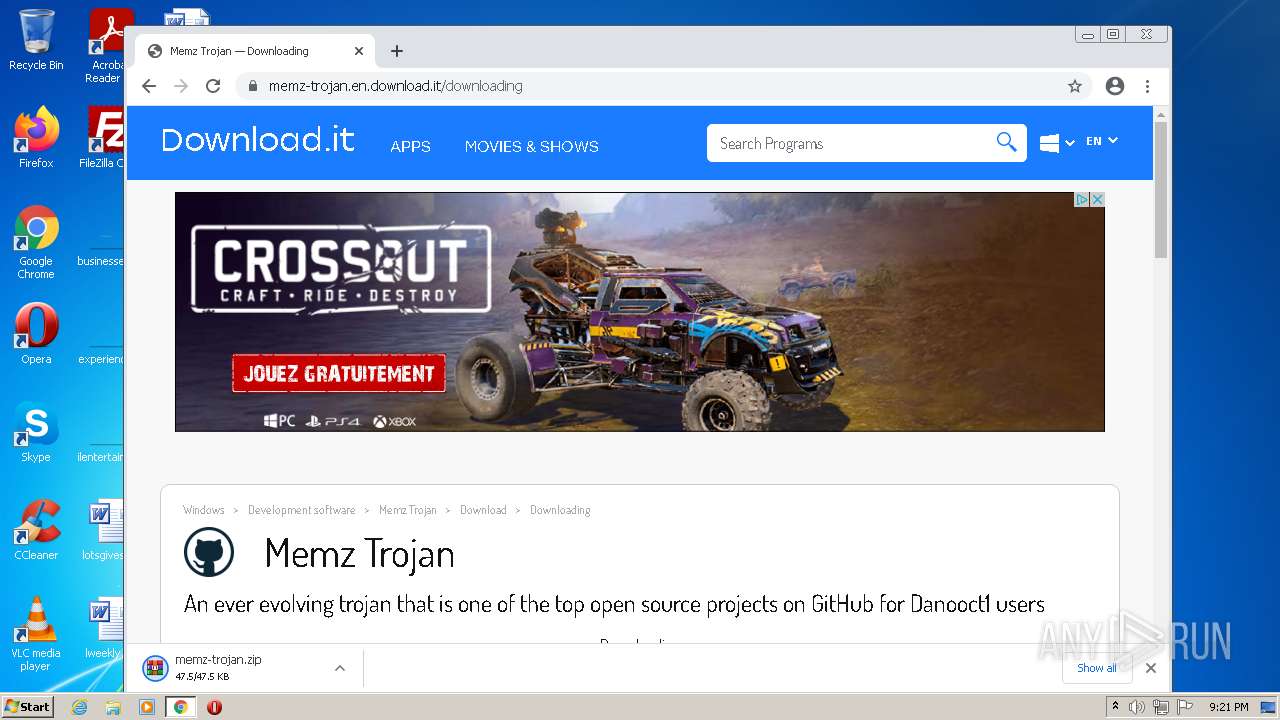
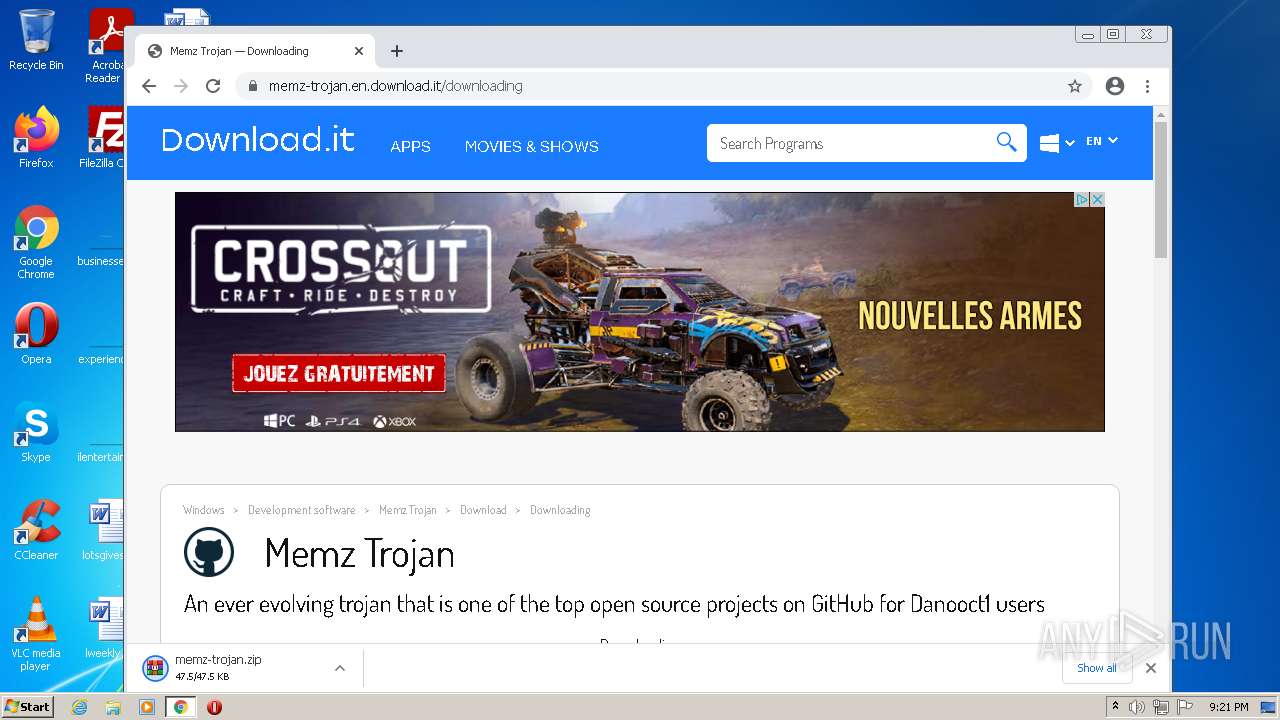
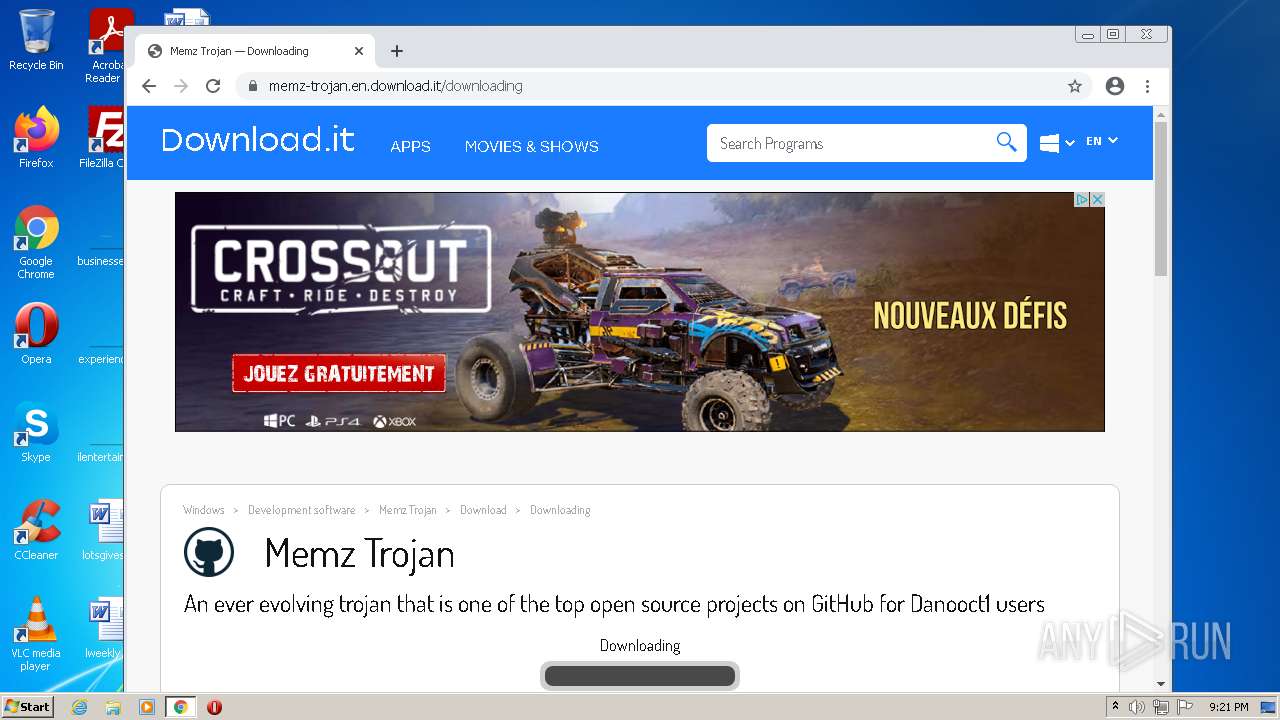
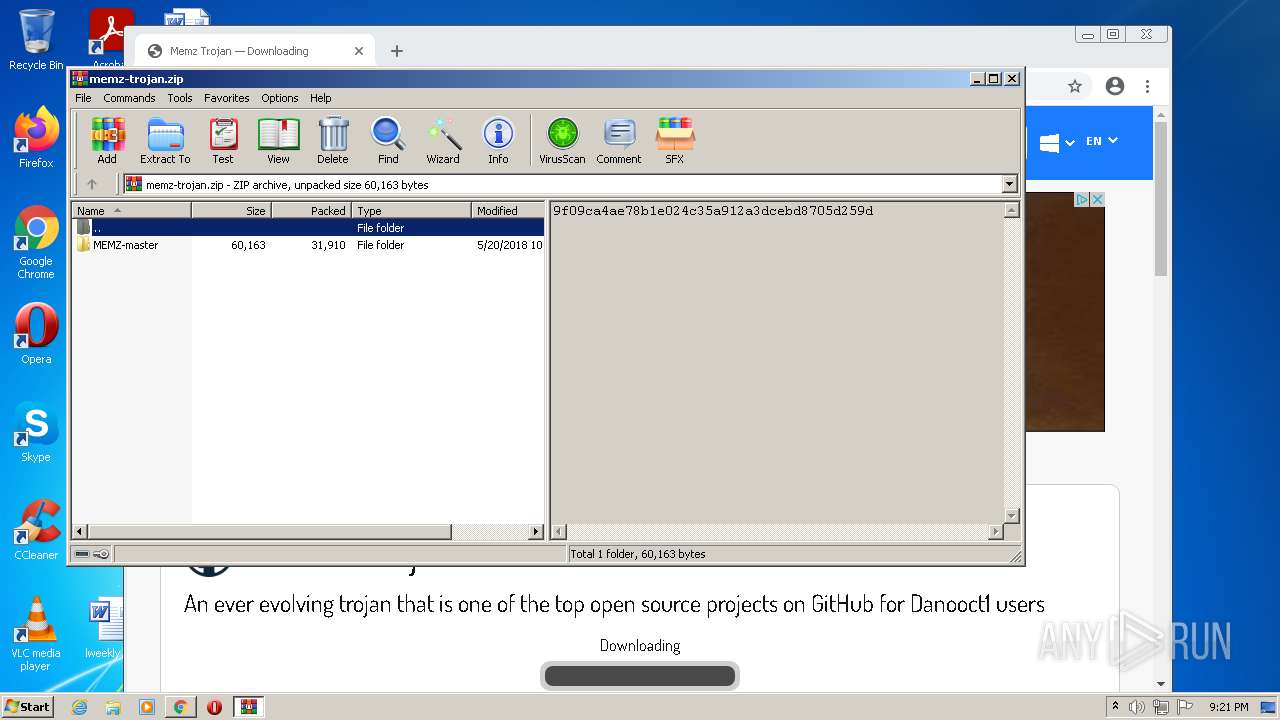
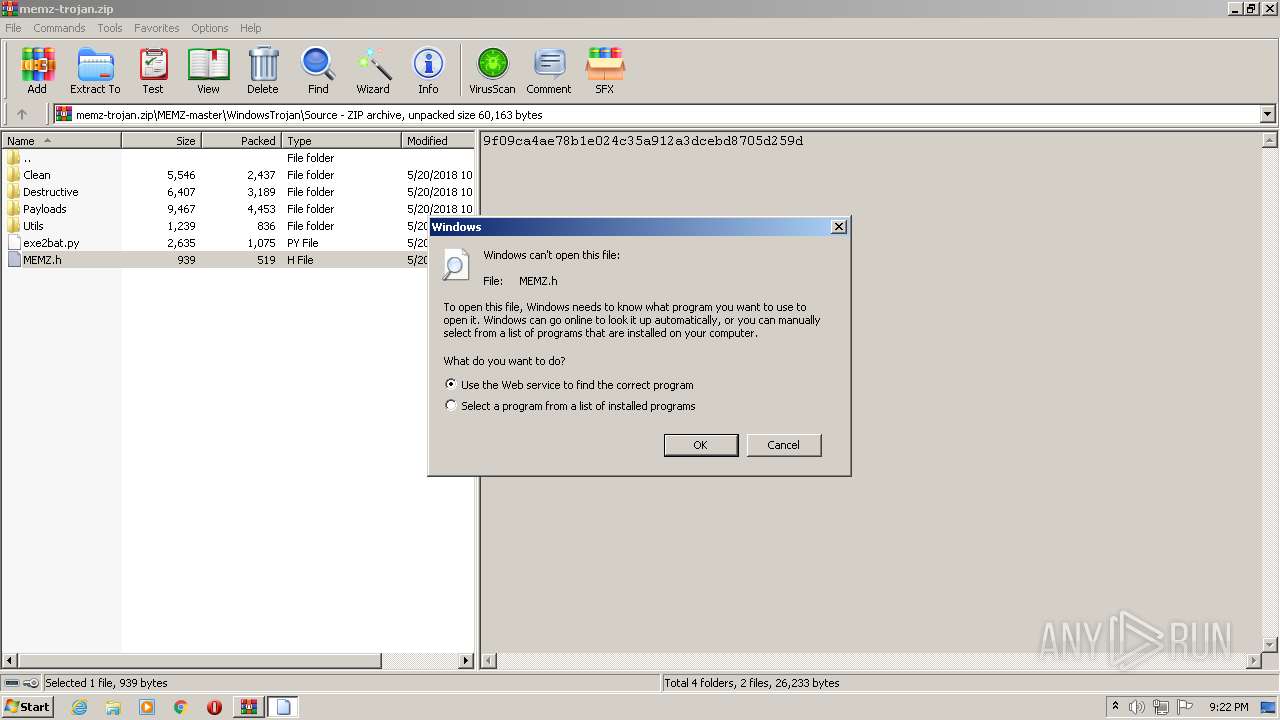
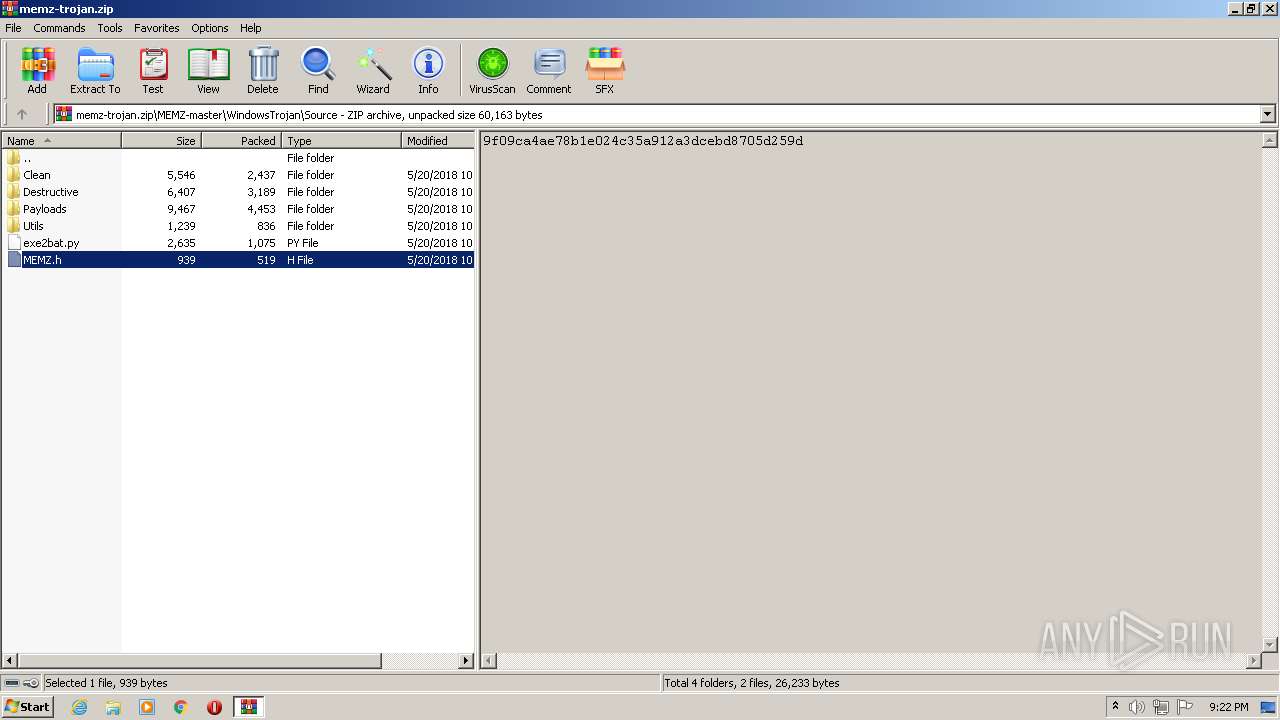
| URL: | https://memz-trojan.en.download.it |
| Full analysis: | https://app.any.run/tasks/d541b7b0-8f4d-4c1d-9218-ac87708eebe5 |
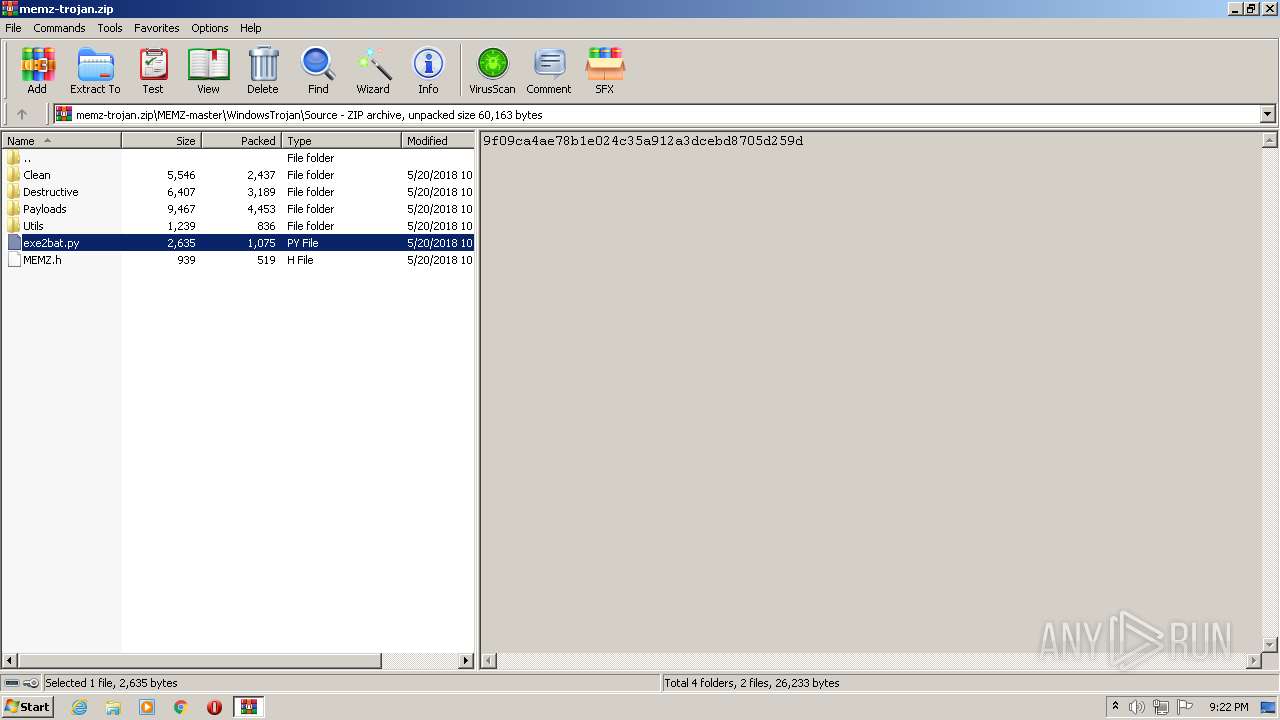
| Verdict: | Malicious activity |
| Analysis date: | January 24, 2022, 21:20:28 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | 083A7A18724A3C8EB738649F3E8910A2 |
| SHA1: | E4A9CEBE63B59C0DAA3D9DE8EFEDA2EBF890BEAA |
| SHA256: | 6538751B373C087AA2630358E7B4AD5FB43CA75B04F95CD50F34B5141967943C |
| SSDEEP: | 3:N8VtIxKWQ:2VqxlQ |
MALICIOUS
Drops executable file immediately after starts
- chrome.exe (PID: 1292)
SUSPICIOUS
Reads Microsoft Outlook installation path
- iexplore.exe (PID: 3316)
- iexplore.exe (PID: 3872)
Modifies files in Chrome extension folder
- chrome.exe (PID: 3836)
Reads the computer name
- WinRAR.exe (PID: 3812)
Uses RUNDLL32.EXE to load library
- WinRAR.exe (PID: 3812)
Checks supported languages
- WinRAR.exe (PID: 3812)
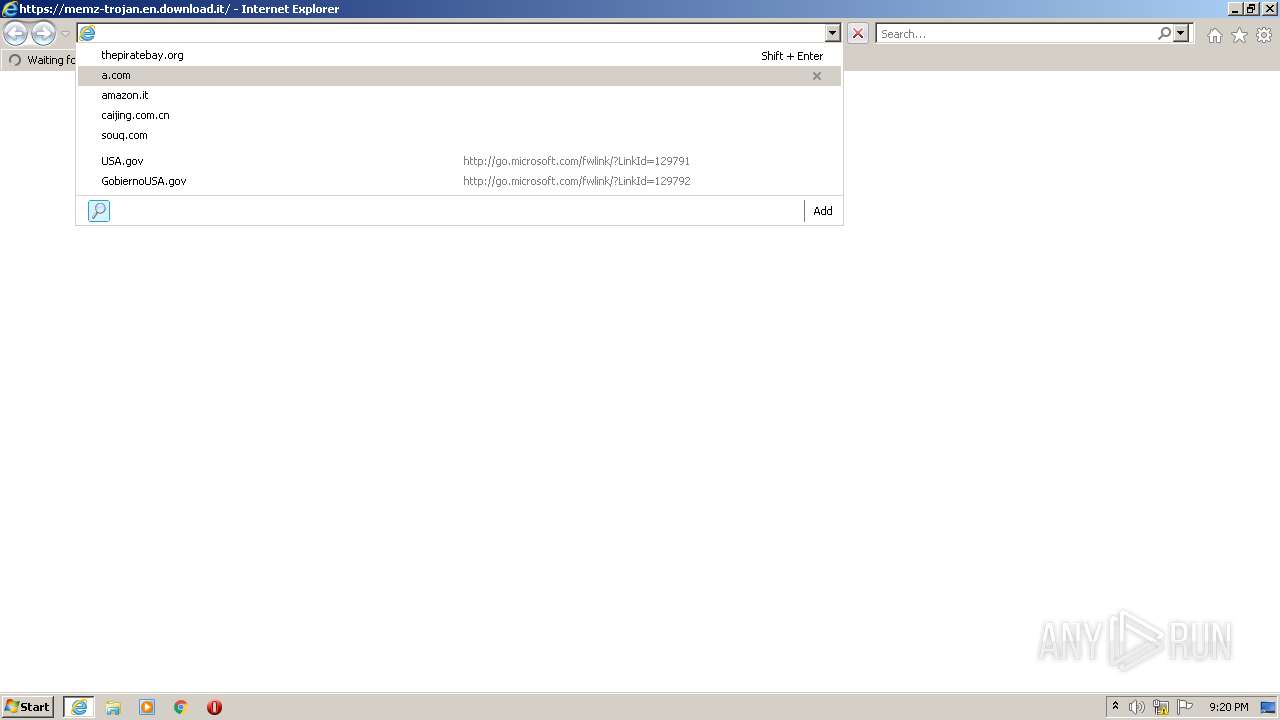
Starts Internet Explorer
- rundll32.exe (PID: 4028)
Executable content was dropped or overwritten
- chrome.exe (PID: 1292)
Drops a file that was compiled in debug mode
- chrome.exe (PID: 1292)
INFO
Checks supported languages
- iexplore.exe (PID: 1536)
- iexplore.exe (PID: 3316)
- chrome.exe (PID: 3836)
- chrome.exe (PID: 3584)
- chrome.exe (PID: 2336)
- chrome.exe (PID: 3556)
- chrome.exe (PID: 2684)
- chrome.exe (PID: 3328)
- chrome.exe (PID: 828)
- chrome.exe (PID: 3968)
- chrome.exe (PID: 3552)
- chrome.exe (PID: 3552)
- chrome.exe (PID: 2084)
- chrome.exe (PID: 968)
- chrome.exe (PID: 2912)
- chrome.exe (PID: 2292)
- chrome.exe (PID: 2608)
- chrome.exe (PID: 3592)
- chrome.exe (PID: 2248)
- chrome.exe (PID: 2464)
- chrome.exe (PID: 4080)
- chrome.exe (PID: 2140)
- chrome.exe (PID: 1248)
- chrome.exe (PID: 3788)
- chrome.exe (PID: 1076)
- chrome.exe (PID: 2572)
- chrome.exe (PID: 2528)
- chrome.exe (PID: 3652)
- chrome.exe (PID: 3476)
- rundll32.exe (PID: 3336)
- rundll32.exe (PID: 4028)
- iexplore.exe (PID: 1160)
- iexplore.exe (PID: 3872)
- rundll32.exe (PID: 3748)
- chrome.exe (PID: 2500)
- chrome.exe (PID: 1748)
- chrome.exe (PID: 3876)
- chrome.exe (PID: 2536)
- chrome.exe (PID: 804)
- chrome.exe (PID: 2504)
- chrome.exe (PID: 272)
- chrome.exe (PID: 2160)
- chrome.exe (PID: 552)
- chrome.exe (PID: 1304)
- chrome.exe (PID: 1644)
- chrome.exe (PID: 3708)
- chrome.exe (PID: 2156)
- chrome.exe (PID: 2480)
- chrome.exe (PID: 776)
- chrome.exe (PID: 3252)
- chrome.exe (PID: 3716)
- chrome.exe (PID: 188)
- chrome.exe (PID: 2416)
- chrome.exe (PID: 2516)
- chrome.exe (PID: 3976)
- chrome.exe (PID: 520)
- chrome.exe (PID: 4092)
- chrome.exe (PID: 3712)
- chrome.exe (PID: 2084)
- chrome.exe (PID: 3928)
- chrome.exe (PID: 1292)
- chrome.exe (PID: 4048)
- chrome.exe (PID: 3468)
Reads the computer name
- iexplore.exe (PID: 3316)
- iexplore.exe (PID: 1536)
- chrome.exe (PID: 3836)
- chrome.exe (PID: 3584)
- chrome.exe (PID: 2336)
- chrome.exe (PID: 828)
- chrome.exe (PID: 3968)
- chrome.exe (PID: 3652)
- chrome.exe (PID: 2572)
- chrome.exe (PID: 3476)
- rundll32.exe (PID: 4028)
- iexplore.exe (PID: 1160)
- iexplore.exe (PID: 3872)
- chrome.exe (PID: 2500)
- chrome.exe (PID: 3876)
- chrome.exe (PID: 2536)
- chrome.exe (PID: 552)
- chrome.exe (PID: 2156)
- chrome.exe (PID: 2480)
- chrome.exe (PID: 776)
- chrome.exe (PID: 3712)
Checks Windows Trust Settings
- iexplore.exe (PID: 1536)
- iexplore.exe (PID: 3872)
- iexplore.exe (PID: 1160)
Reads internet explorer settings
- iexplore.exe (PID: 3316)
- iexplore.exe (PID: 3872)
Reads the date of Windows installation
- iexplore.exe (PID: 1536)
- iexplore.exe (PID: 1160)
- chrome.exe (PID: 776)
Changes internet zones settings
- iexplore.exe (PID: 1536)
- iexplore.exe (PID: 1160)
Application launched itself
- iexplore.exe (PID: 1536)
- chrome.exe (PID: 3836)
- iexplore.exe (PID: 1160)
- chrome.exe (PID: 2500)
Reads settings of System Certificates
- iexplore.exe (PID: 1536)
- chrome.exe (PID: 2336)
- iexplore.exe (PID: 3872)
- iexplore.exe (PID: 1160)
- chrome.exe (PID: 2500)
Manual execution by user
- chrome.exe (PID: 3836)
- chrome.exe (PID: 2500)
Reads the hosts file
- chrome.exe (PID: 3836)
- chrome.exe (PID: 2336)
- chrome.exe (PID: 2500)
- chrome.exe (PID: 2536)
Creates files in the user directory
- iexplore.exe (PID: 3872)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
103
Monitored processes
64
Malicious processes
0
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 188 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --field-trial-handle=1040,15707216960917000307,6506270485253318426,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --mojo-platform-channel-handle=2880 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 272 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1040,15707216960917000307,6506270485253318426,131072 --enable-features=PasswordImport --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=6 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2024 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 520 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --field-trial-handle=1040,15707216960917000307,6506270485253318426,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --mojo-platform-channel-handle=496 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 552 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=1040,15707216960917000307,6506270485253318426,131072 --enable-features=PasswordImport --gpu-preferences=MAAAAAAAAADgAAAwAAAAAAAAAAAAAAAAAABgAAAAAAAQAAAAAAAAAAAAAAAAAAAAKAAAAAQAAAAgAAAAAAAAACgAAAAAAAAAMAAAAAAAAAA4AAAAAAAAABAAAAAAAAAAAAAAAAUAAAAQAAAAAAAAAAAAAAAGAAAAEAAAAAAAAAABAAAABQAAABAAAAAAAAAAAQAAAAYAAAA= --use-gl=swiftshader-webgl --mojo-platform-channel-handle=3000 /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 776 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=chrome.mojom.UtilWin --field-trial-handle=1040,15707216960917000307,6506270485253318426,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=none --mojo-platform-channel-handle=1852 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 804 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=storage.mojom.StorageService --field-trial-handle=1040,15707216960917000307,6506270485253318426,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --mojo-platform-channel-handle=1776 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 828 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=1052,7166919400934522312,12330157875798278777,131072 --enable-features=PasswordImport --gpu-preferences=MAAAAAAAAADgAAAwAAAAAAAAAAAAAAAAAABgAAAAAAAQAAAAAAAAAAAAAAAAAAAAKAAAAAQAAAAgAAAAAAAAACgAAAAAAAAAMAAAAAAAAAA4AAAAAAAAABAAAAAAAAAAAAAAAAUAAAAQAAAAAAAAAAAAAAAGAAAAEAAAAAAAAAABAAAABQAAABAAAAAAAAAAAQAAAAYAAAA= --use-gl=swiftshader-webgl --mojo-platform-channel-handle=1016 /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 968 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1052,7166919400934522312,12330157875798278777,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=16 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2888 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 1076 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1052,7166919400934522312,12330157875798278777,131072 --enable-features=PasswordImport --disable-gpu-compositing --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=22 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3768 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 1160 | "C:\Program Files\Internet Explorer\iexplore.exe" http://go.microsoft.com/fwlink/?LinkId=57426&Ext=py | C:\Program Files\Internet Explorer\iexplore.exe | rundll32.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 1 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
Total events
42 403
Read events
41 949
Write events
442
Delete events
12
Modification events
| (PID) Process: | (1536) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPDaysSinceLastAutoMigration |
Value: 1 | |||
| (PID) Process: | (1536) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPLastLaunchLowDateTime |
Value: 931159392 | |||
| (PID) Process: | (1536) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPLastLaunchHighDateTime |
Value: 30937448 | |||
| (PID) Process: | (1536) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateLowDateTime |
Value: | |||
| (PID) Process: | (1536) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateHighDateTime |
Value: 30937448 | |||
| (PID) Process: | (1536) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (1536) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (1536) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (1536) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (1536) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
Executable files
1
Suspicious files
246
Text files
360
Unknown types
31
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1536 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\57C8EDB95DF3F0AD4EE2DC2B8CFD4157 | binary | |
MD5:— | SHA256:— | |||
| 3836 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\BrowserMetrics\BrowserMetrics-61EF1836-EFC.pma | — | |
MD5:— | SHA256:— | |||
| 1536 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\~DF38924770603E65EC.TMP | gmc | |
MD5:— | SHA256:— | |||
| 1536 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\~DF441441471F2794A4.TMP | gmc | |
MD5:— | SHA256:— | |||
| 1536 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\6BADA8974A10C4BD62CC921D13E43B18_711ED44619924BA6DC33E69F97E7FF63 | binary | |
MD5:— | SHA256:— | |||
| 1536 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Internet Explorer\Recovery\Last Active\{7E8B7A6F-7D5B-11EC-A20C-12A9866C77DE}.dat | binary | |
MD5:— | SHA256:— | |||
| 1536 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\6BADA8974A10C4BD62CC921D13E43B18_711ED44619924BA6DC33E69F97E7FF63 | der | |
MD5:— | SHA256:— | |||
| 1536 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Internet Explorer\Recovery\Last Active\RecoveryStore.{42C873D0-1D90-11EB-BA2C-12A9866C77DE}.dat | binary | |
MD5:— | SHA256:— | |||
| 1536 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Internet Explorer\Recovery\Active\{7525D5B7-7D5B-11EC-A20C-12A9866C77DE}.dat | binary | |
MD5:— | SHA256:— | |||
| 1536 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Internet Explorer\Recovery\Active\{7E8B7A6E-7D5B-11EC-A20C-12A9866C77DE}.dat | binary | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
40
TCP/UDP connections
112
DNS requests
62
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
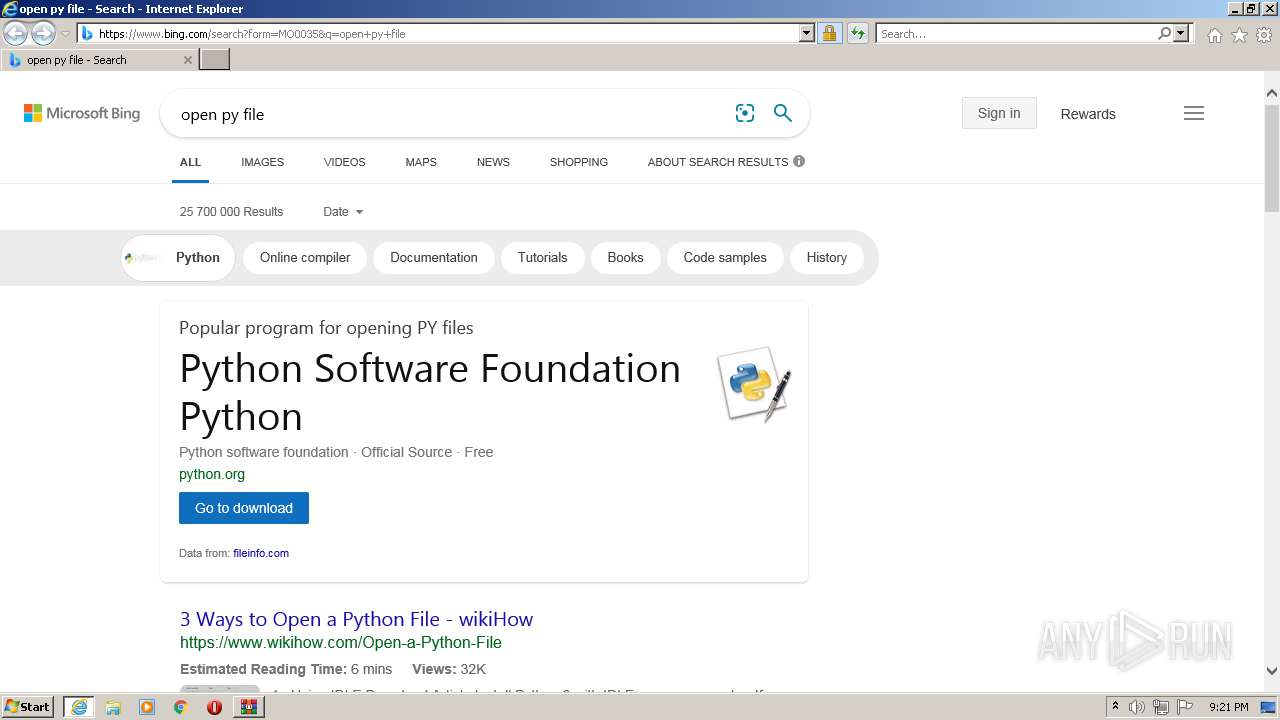
3872 | iexplore.exe | GET | 301 | 2.16.186.27:80 | http://shell.windows.com/fileassoc/fileassoc.asp?Ext=py | unknown | — | — | whitelisted |
924 | svchost.exe | HEAD | 200 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/ji7rr72vshyuysavvoya5i4uvi_2022.1.10.1202/ggkkehgbnfjpeggfpleeakpidbkibbmn_2022.1.10.1202_all_adyj3od2cdlldsmkfhxdxrcy7liq.crx3 | US | — | — | whitelisted |
3872 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | US | der | 471 b | whitelisted |
1536 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTBL0V27RVZ7LBduom%2FnYB45SPUEwQU5Z1ZMIJHWMys%2BghUNoZ7OrUETfACEA8Ull8gIGmZT9XHrHiJQeI%3D | US | der | 1.47 Kb | whitelisted |
924 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/ji7rr72vshyuysavvoya5i4uvi_2022.1.10.1202/ggkkehgbnfjpeggfpleeakpidbkibbmn_2022.1.10.1202_all_adyj3od2cdlldsmkfhxdxrcy7liq.crx3 | US | binary | 3.43 Kb | whitelisted |
924 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/adys6mm2sd23z36ns7e4hcs4hrqq_1.3.36.111/ihnlcenocehgdaegdmhbidjhnhdchfmm_1.3.36.111_win_ac5lwr5427en7czu7myxmee6c7xq.crx3 | US | binary | 43.4 Kb | whitelisted |
924 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/adys6mm2sd23z36ns7e4hcs4hrqq_1.3.36.111/ihnlcenocehgdaegdmhbidjhnhdchfmm_1.3.36.111_win_ac5lwr5427en7czu7myxmee6c7xq.crx3 | US | binary | 719 Kb | whitelisted |
924 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/ji7rr72vshyuysavvoya5i4uvi_2022.1.10.1202/ggkkehgbnfjpeggfpleeakpidbkibbmn_2022.1.10.1202_all_adyj3od2cdlldsmkfhxdxrcy7liq.crx3 | US | binary | 5.62 Kb | whitelisted |
924 | svchost.exe | HEAD | 200 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/adys6mm2sd23z36ns7e4hcs4hrqq_1.3.36.111/ihnlcenocehgdaegdmhbidjhnhdchfmm_1.3.36.111_win_ac5lwr5427en7czu7myxmee6c7xq.crx3 | US | binary | 3.43 Kb | whitelisted |
924 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/adys6mm2sd23z36ns7e4hcs4hrqq_1.3.36.111/ihnlcenocehgdaegdmhbidjhnhdchfmm_1.3.36.111_win_ac5lwr5427en7czu7myxmee6c7xq.crx3 | US | binary | 10.1 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3316 | iexplore.exe | 172.67.75.124:443 | memz-trojan.en.download.it | — | US | unknown |
1536 | iexplore.exe | 204.79.197.200:443 | www.bing.com | Microsoft Corporation | US | whitelisted |
1536 | iexplore.exe | 67.27.233.126:80 | ctldl.windowsupdate.com | Level 3 Communications, Inc. | US | suspicious |
1536 | iexplore.exe | 8.253.95.120:80 | ctldl.windowsupdate.com | Global Crossing | US | suspicious |
1536 | iexplore.exe | 93.184.220.29:80 | ocsp.digicert.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
2336 | chrome.exe | 142.250.186.131:443 | clientservices.googleapis.com | Google Inc. | US | whitelisted |
2336 | chrome.exe | 216.58.212.142:443 | clients2.google.com | Google Inc. | US | whitelisted |
2336 | chrome.exe | 142.250.181.228:443 | www.google.com | Google Inc. | US | whitelisted |
2336 | chrome.exe | 172.217.18.99:443 | update.googleapis.com | Google Inc. | US | whitelisted |
2336 | chrome.exe | 142.250.185.205:443 | accounts.google.com | Google Inc. | US | suspicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
memz-trojan.en.download.it |
| suspicious |
api.bing.com |
| whitelisted |
www.bing.com |
| whitelisted |
ctldl.windowsupdate.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
clientservices.googleapis.com |
| whitelisted |
accounts.google.com |
| shared |
clients2.google.com |
| whitelisted |
www.google.com |
| malicious |
update.googleapis.com |
| whitelisted |