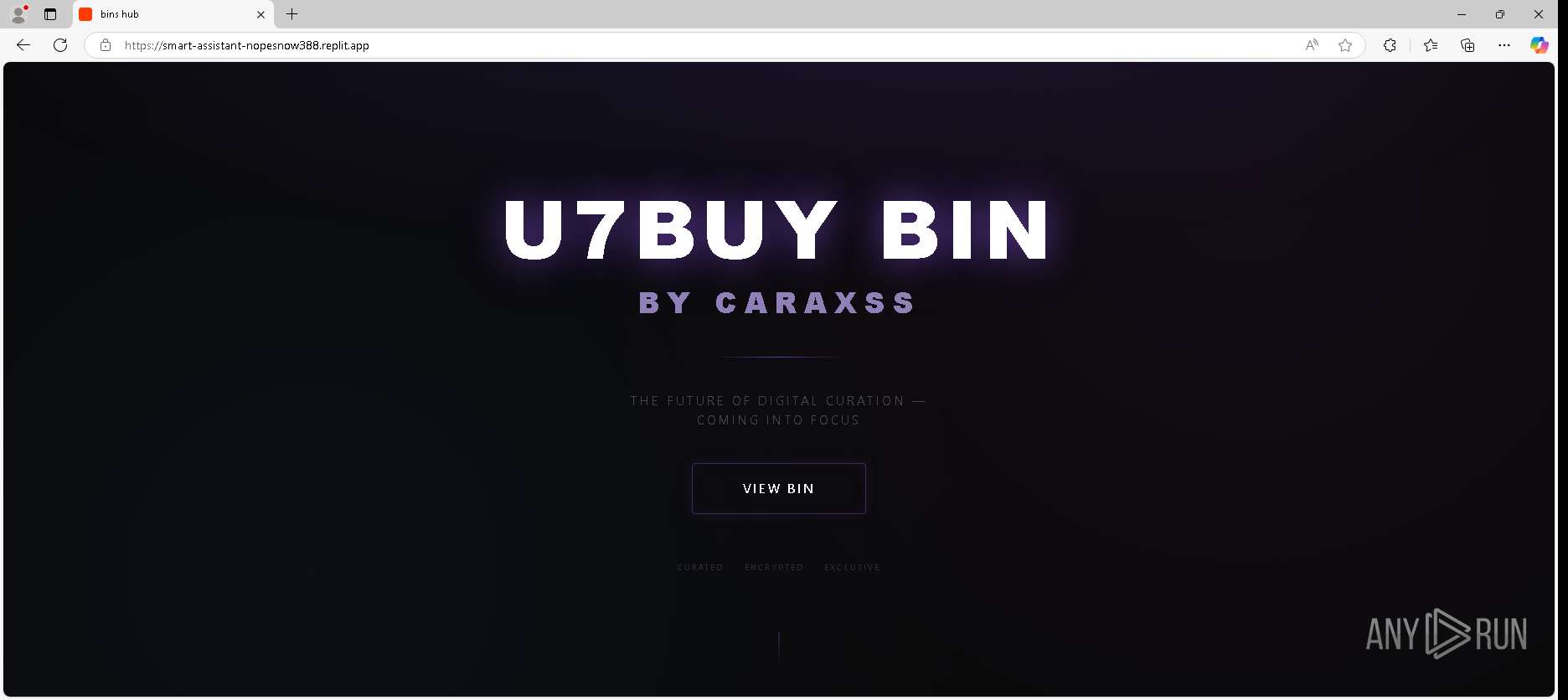
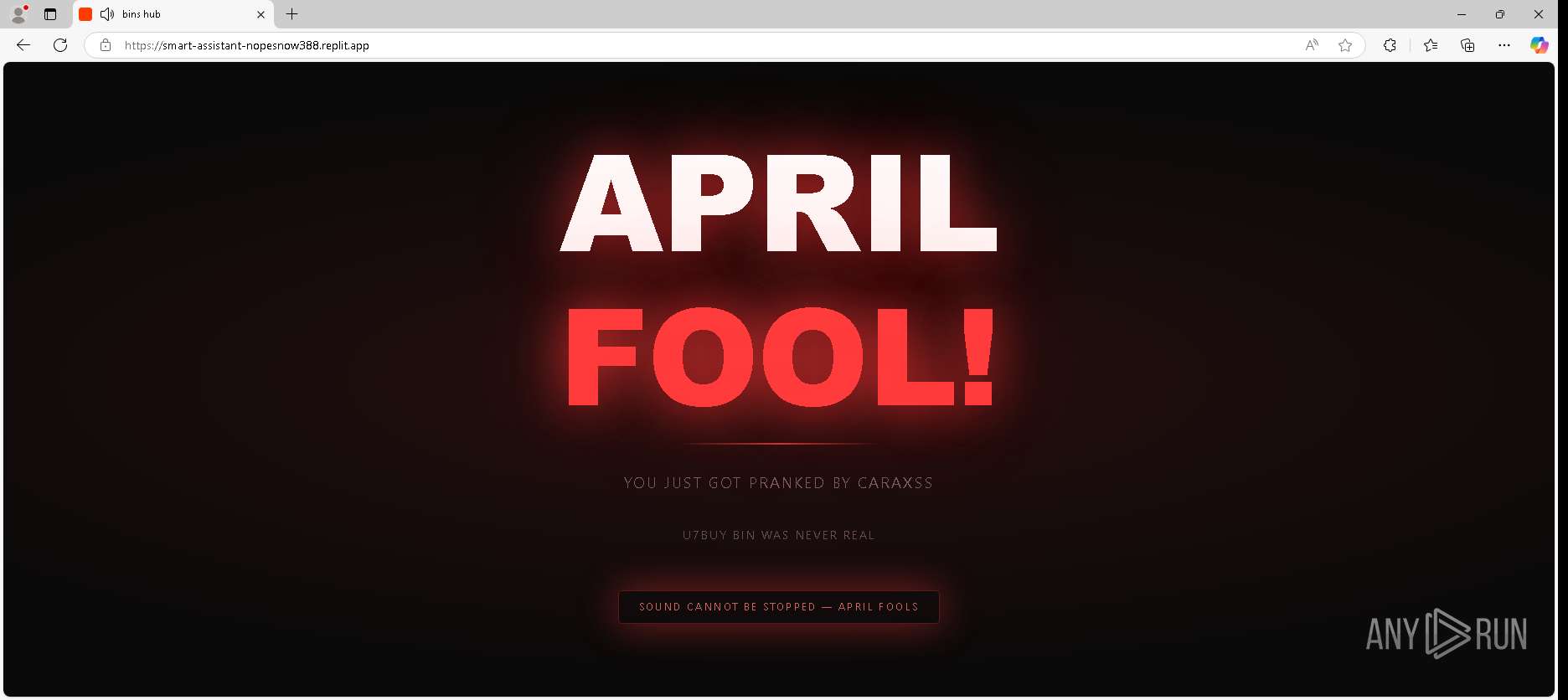
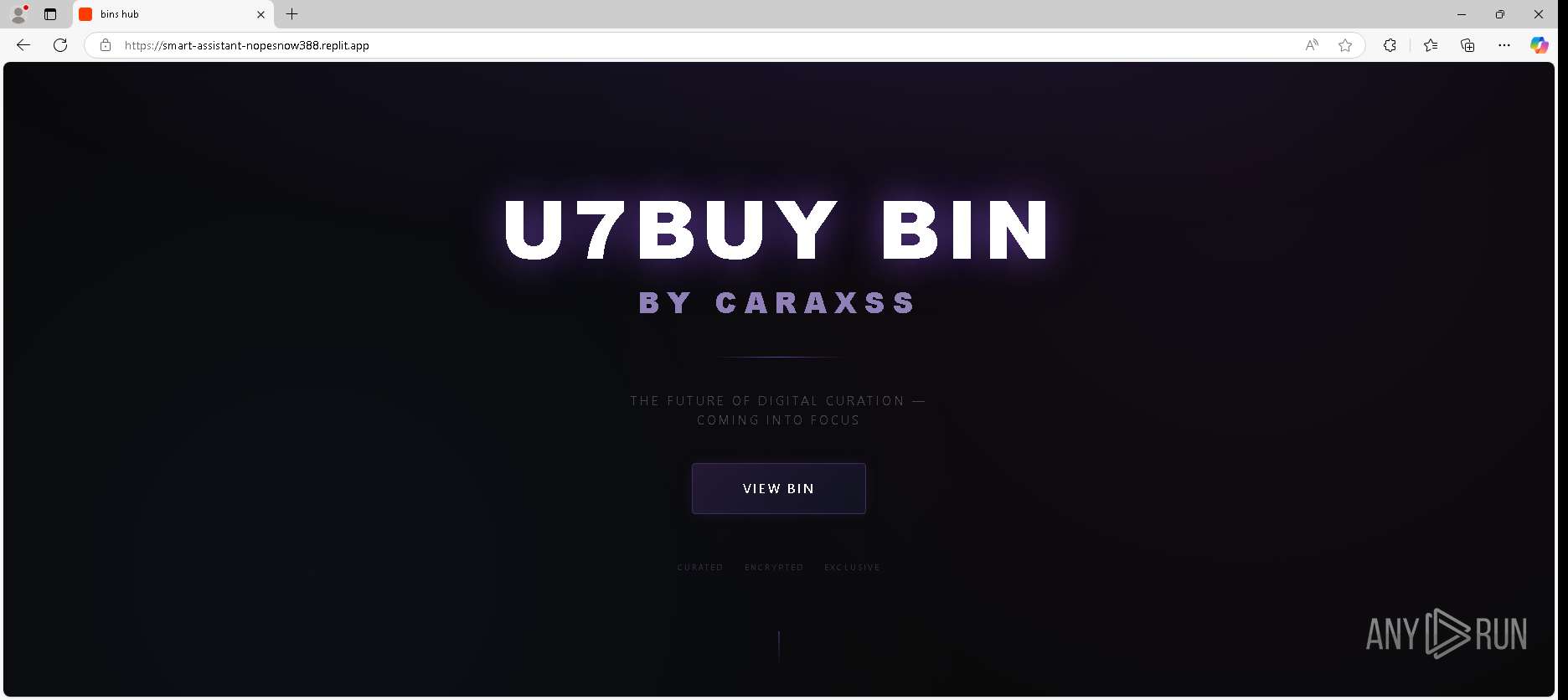
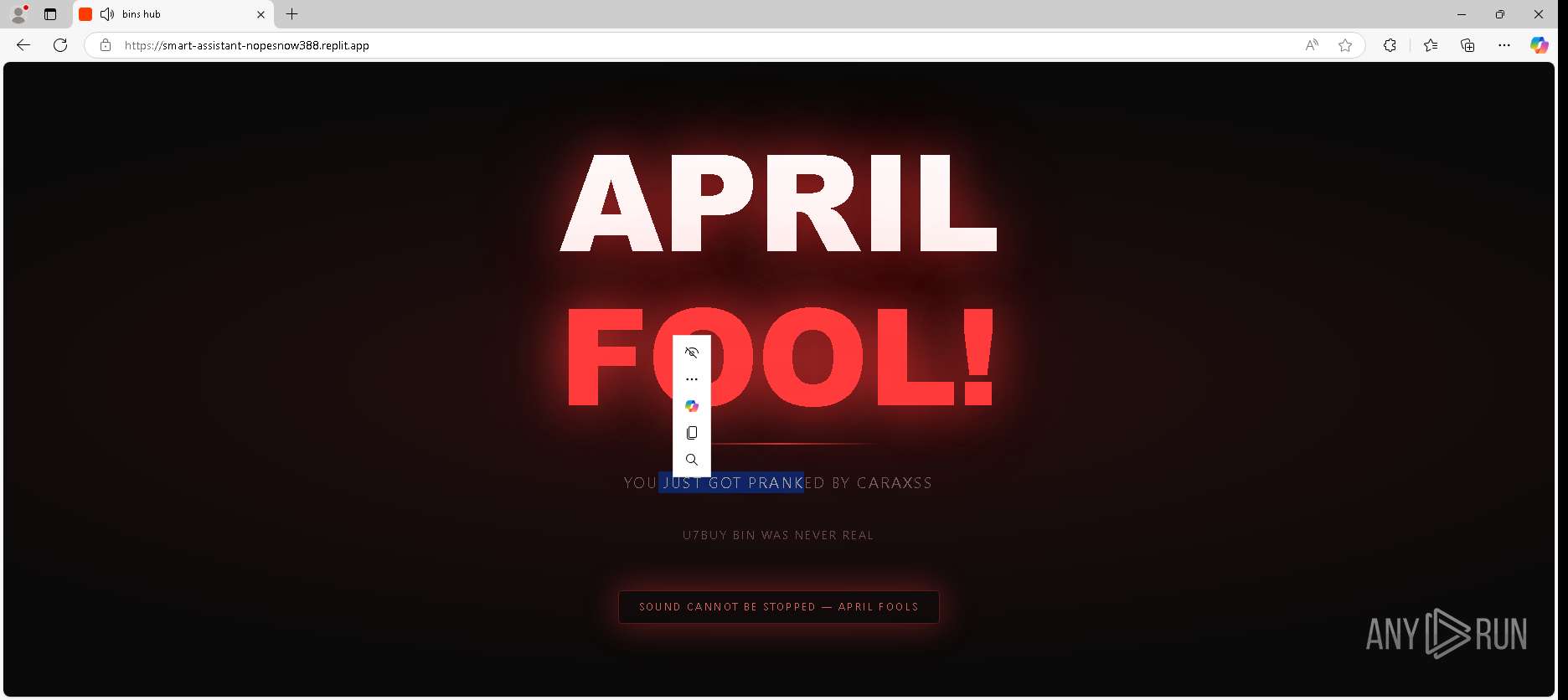
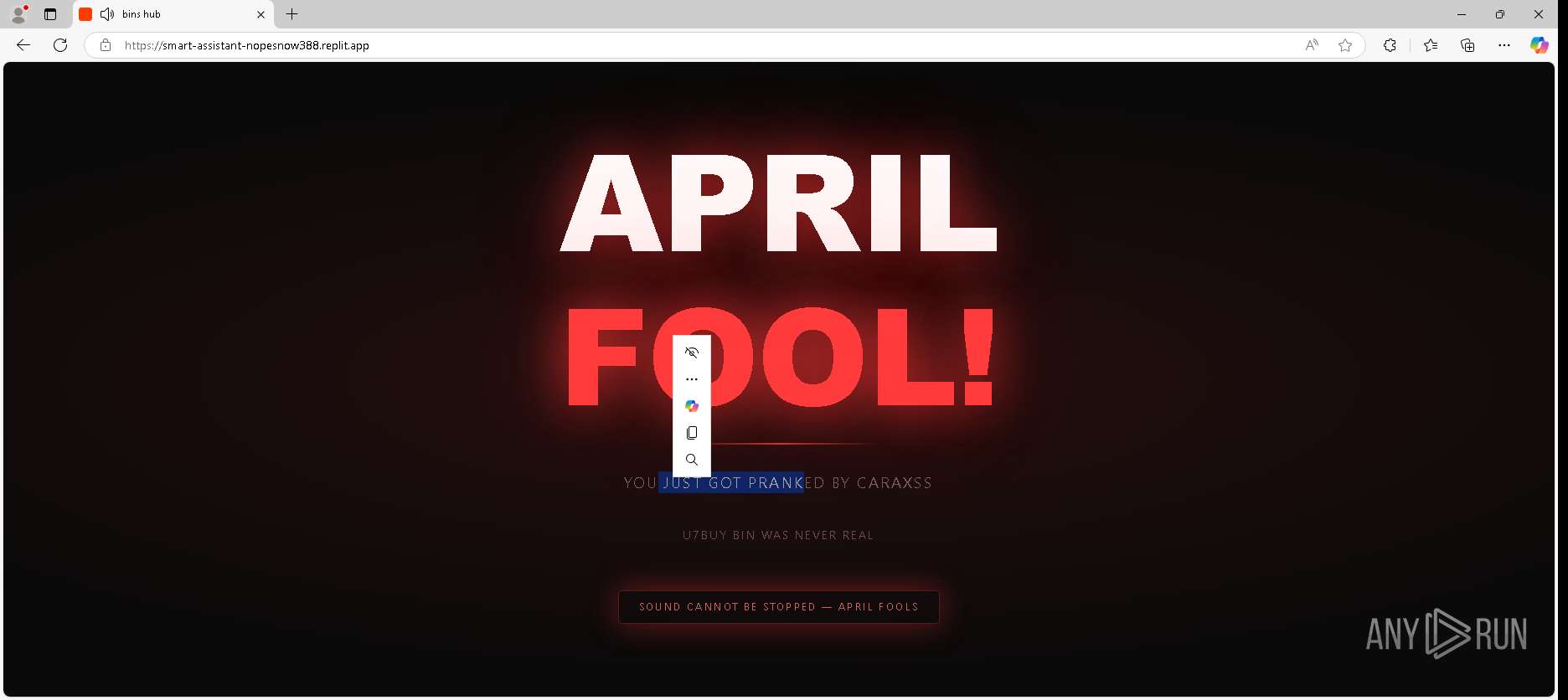
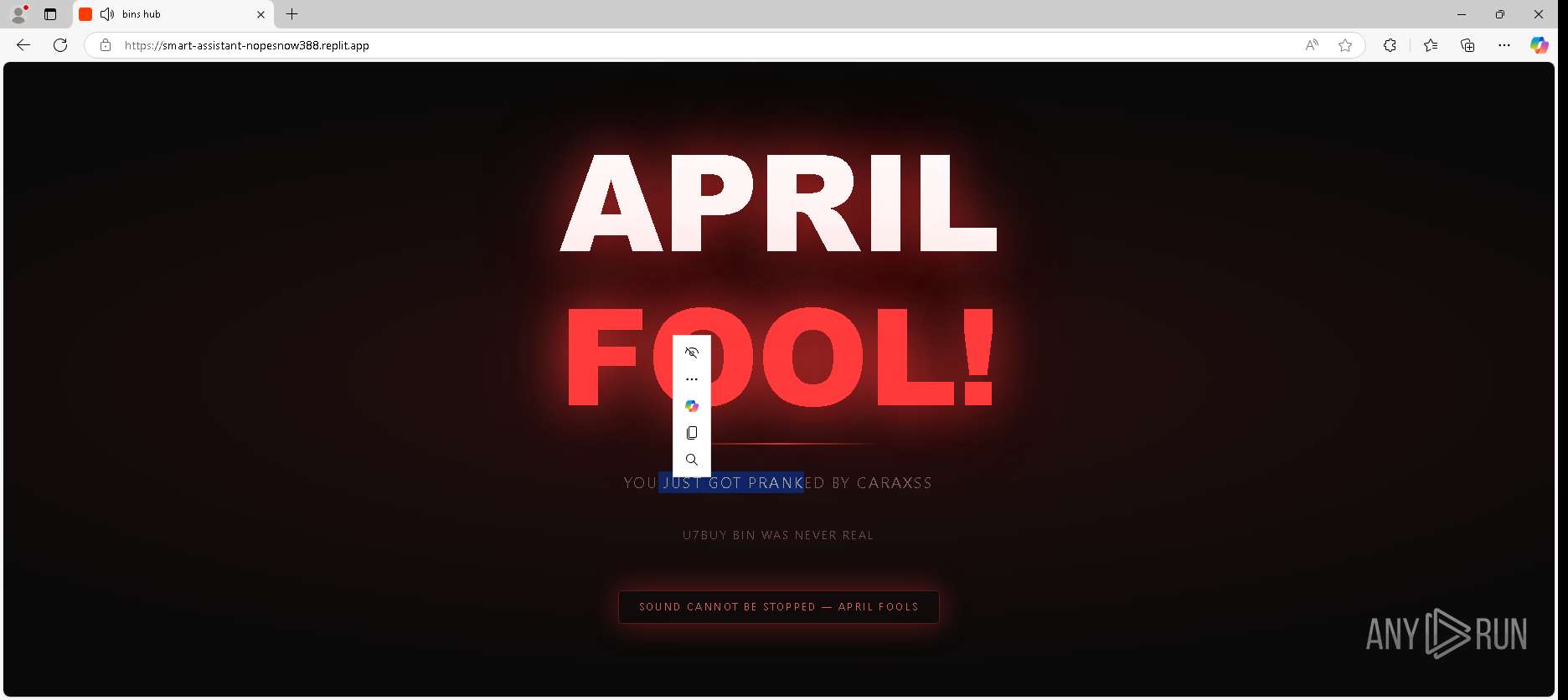
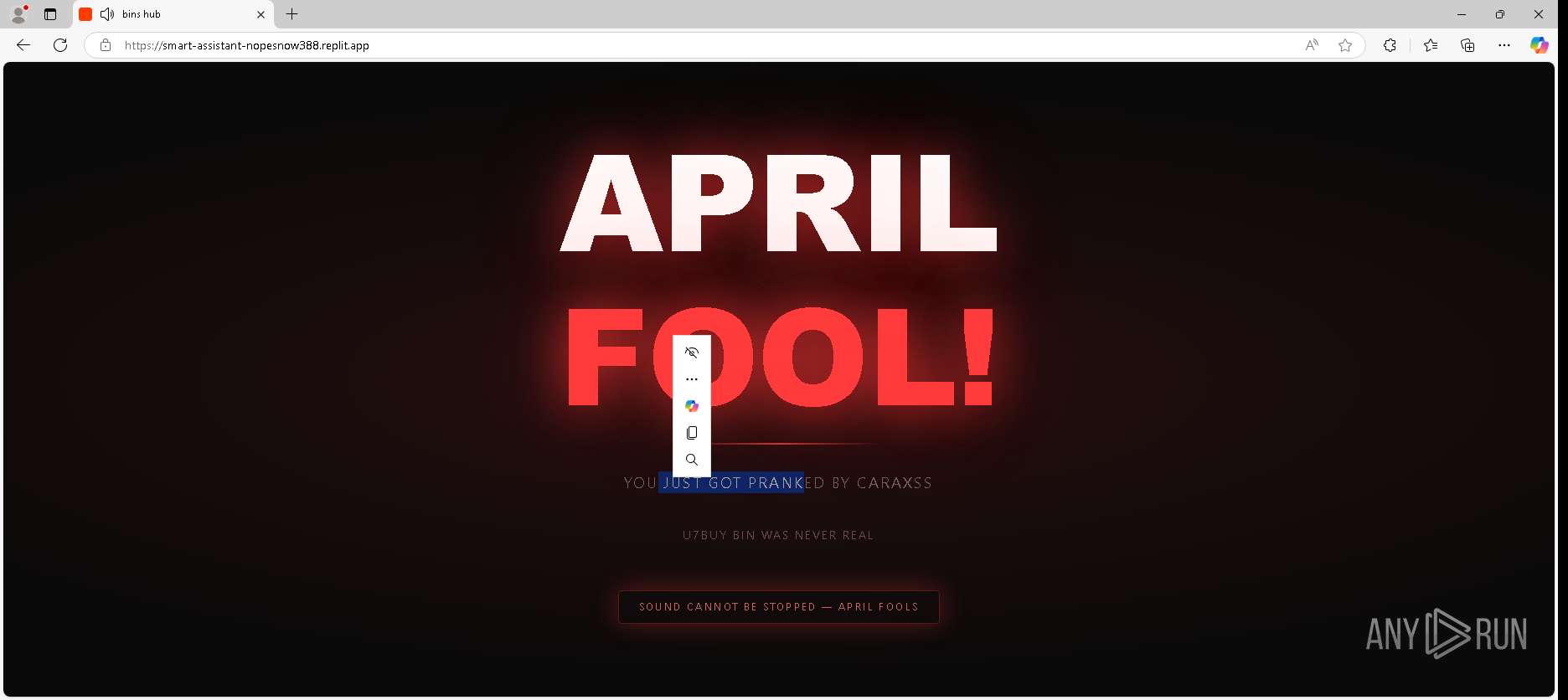
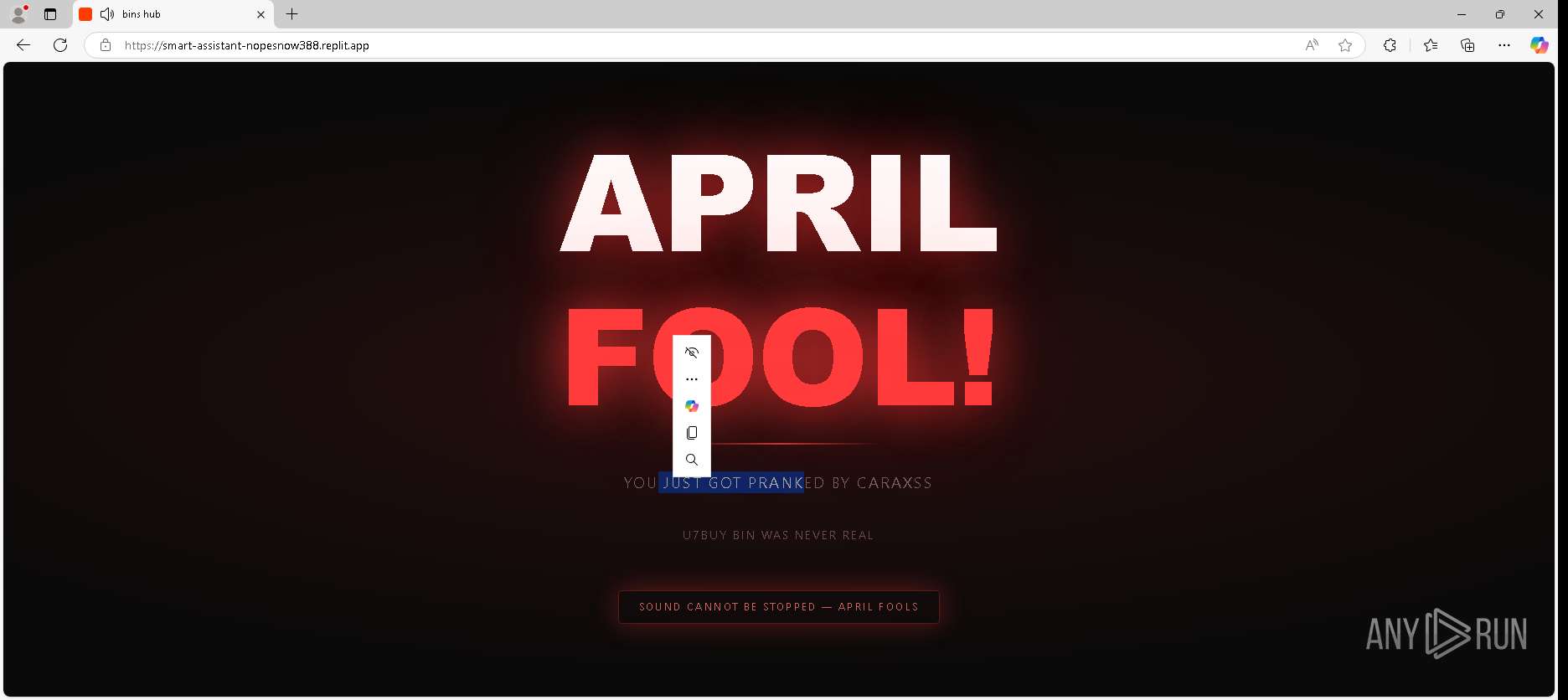
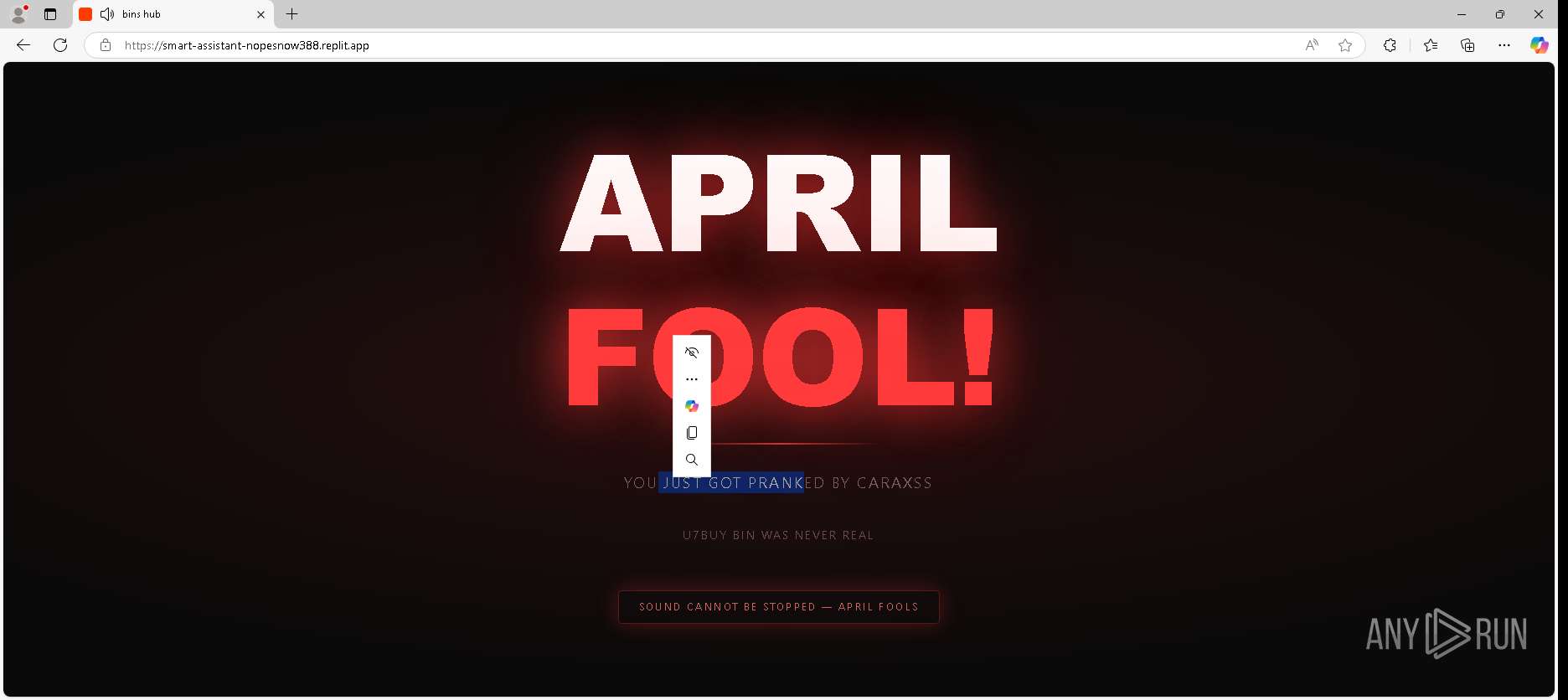
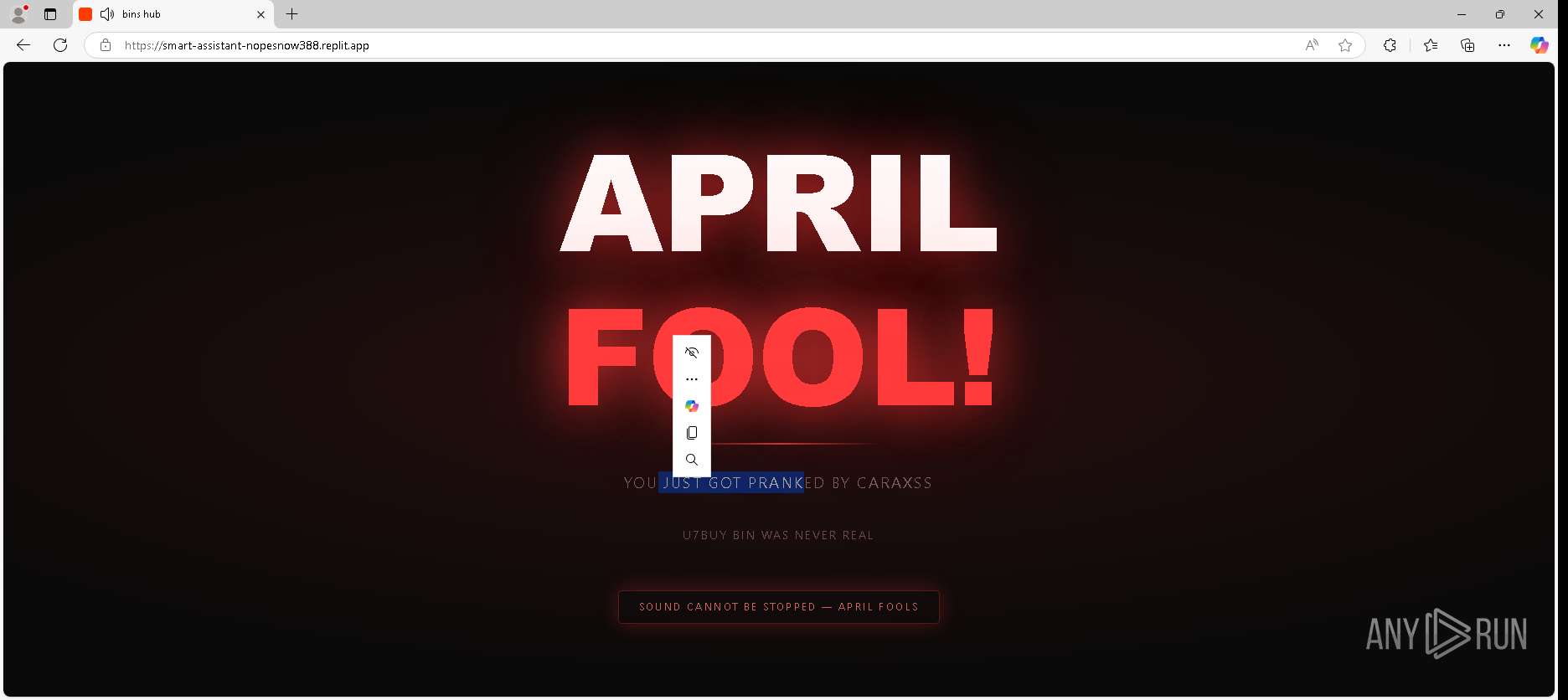
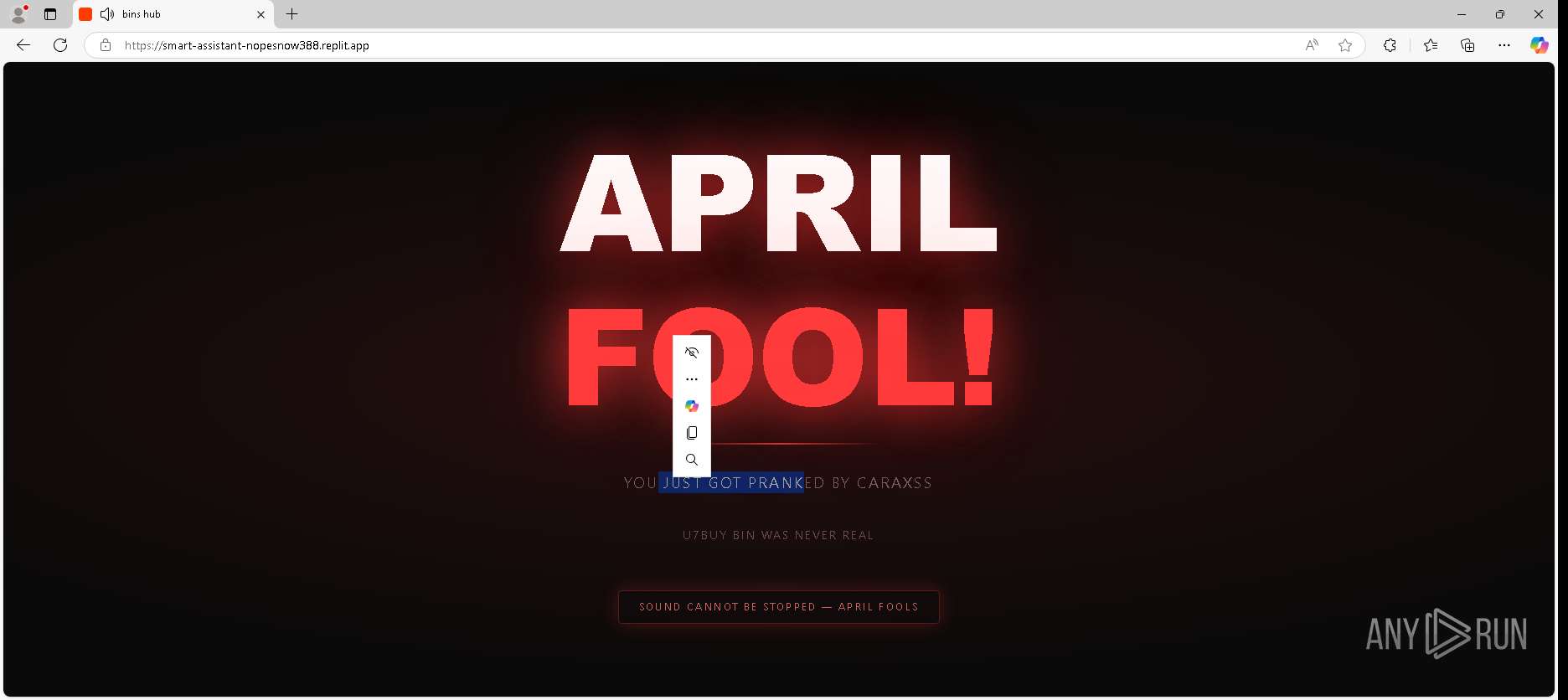
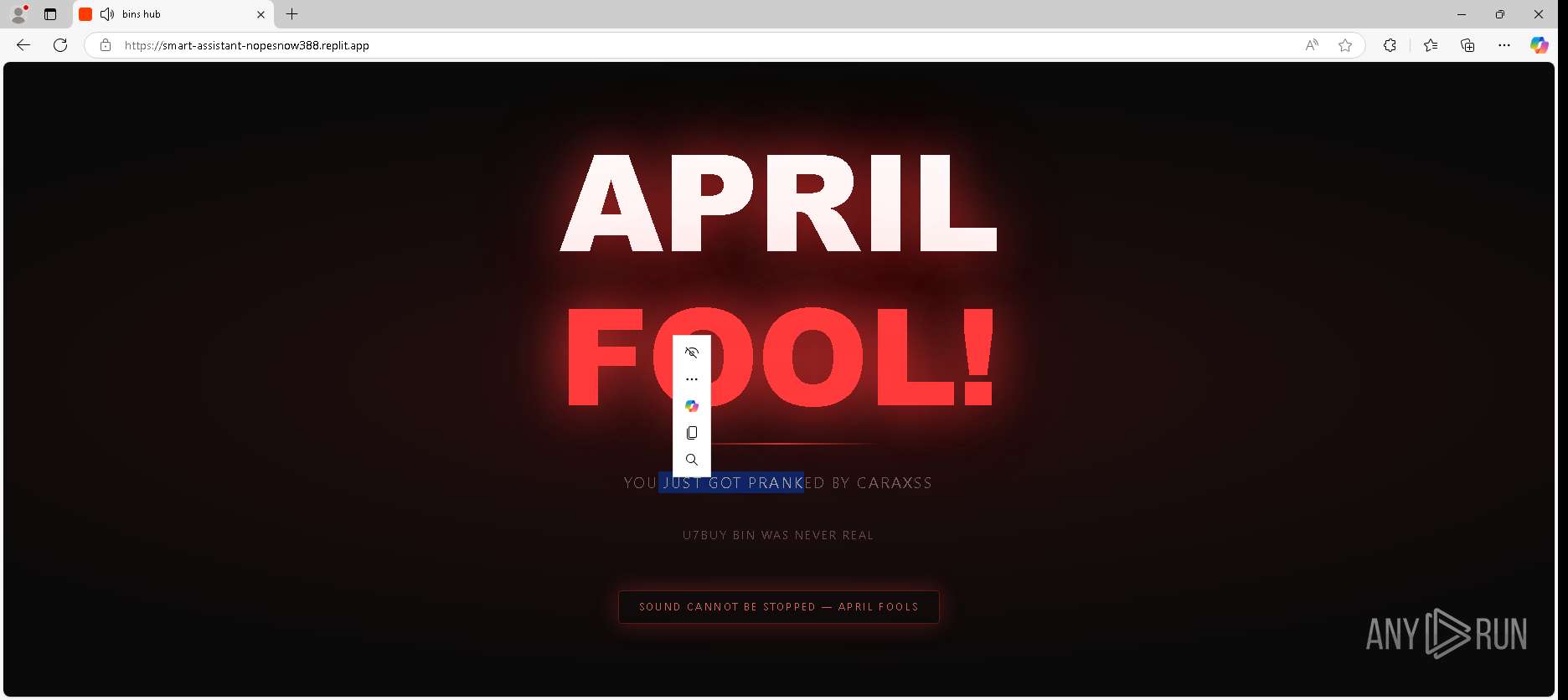
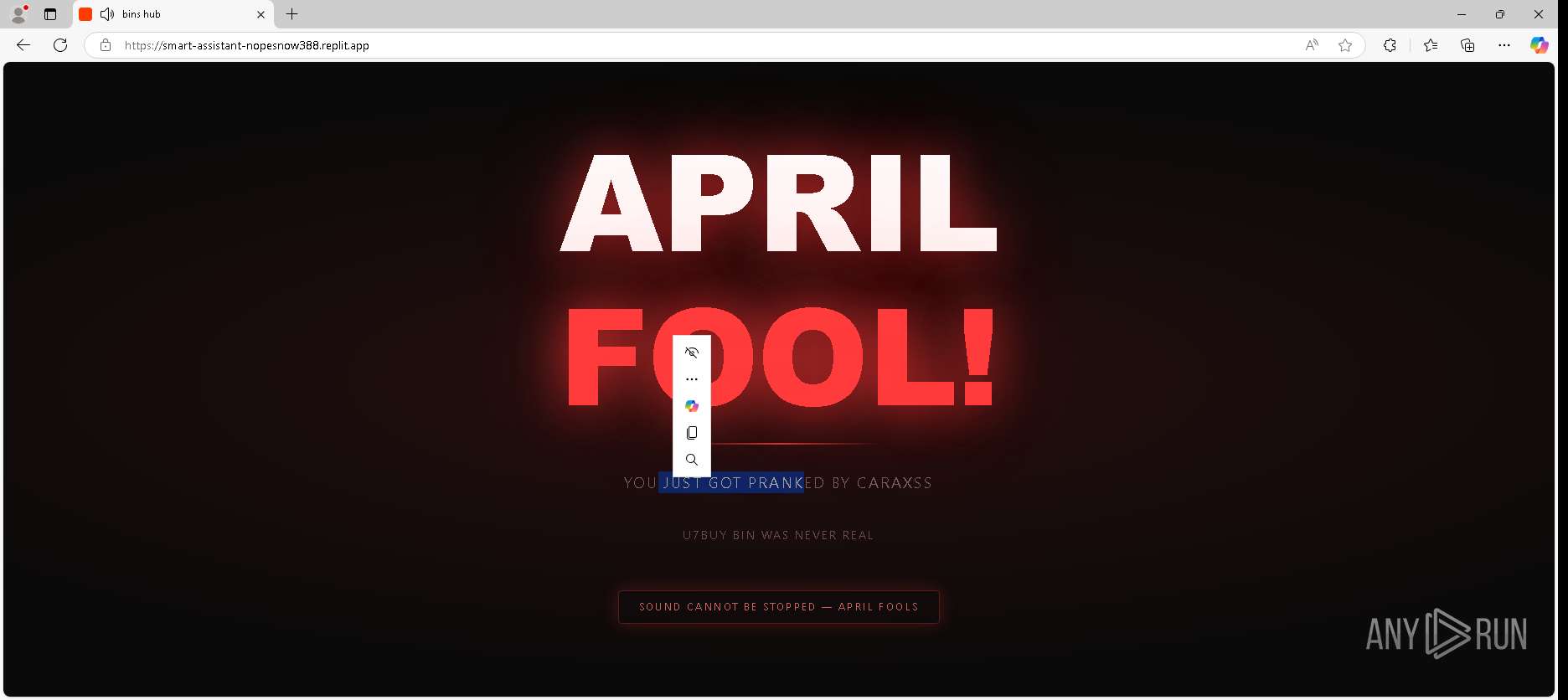
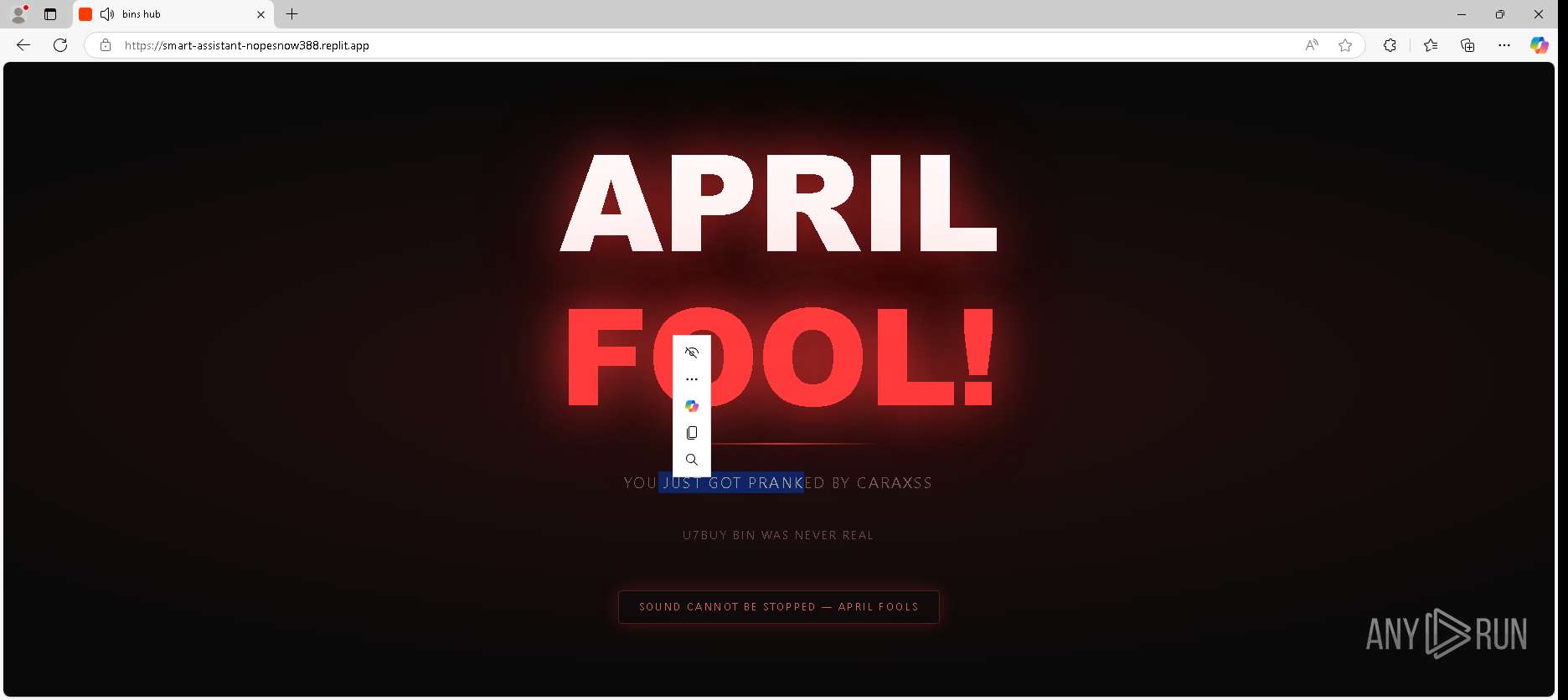
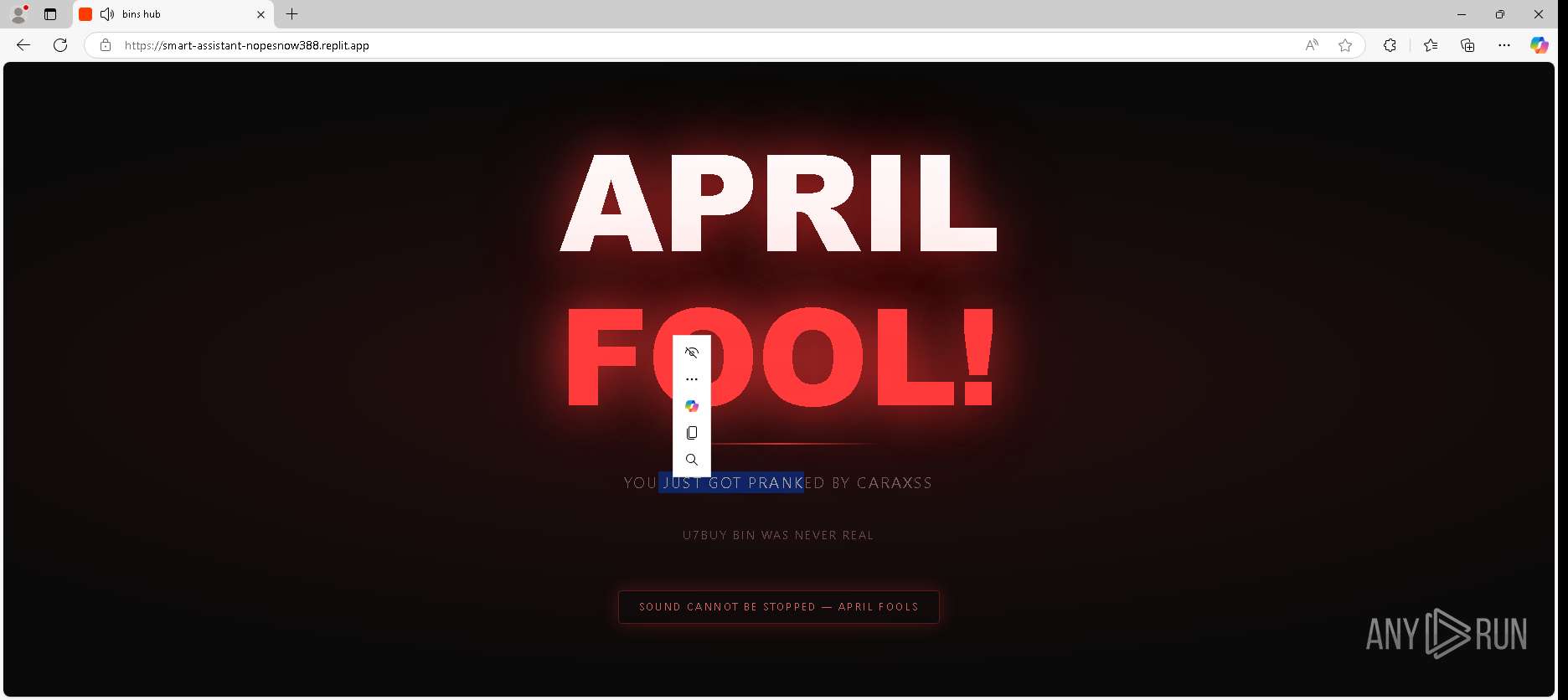
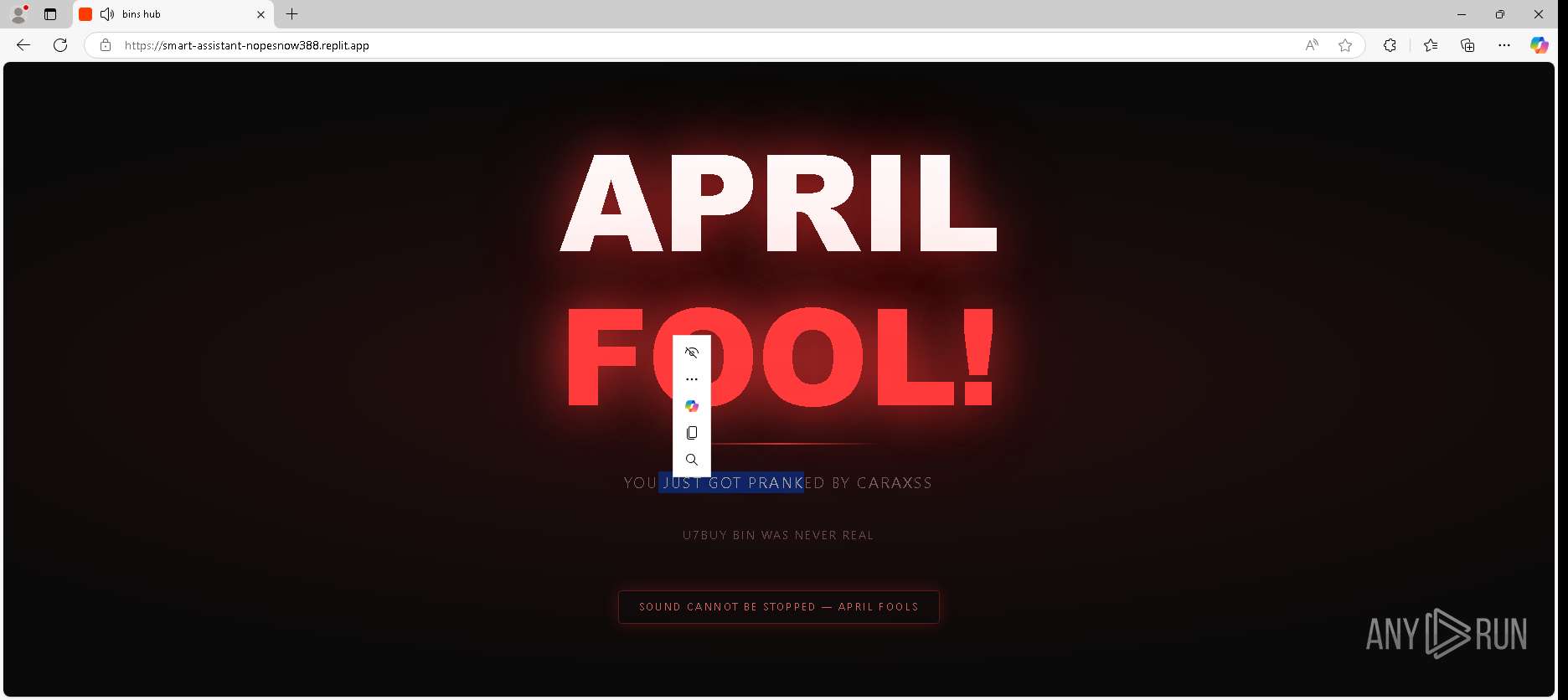
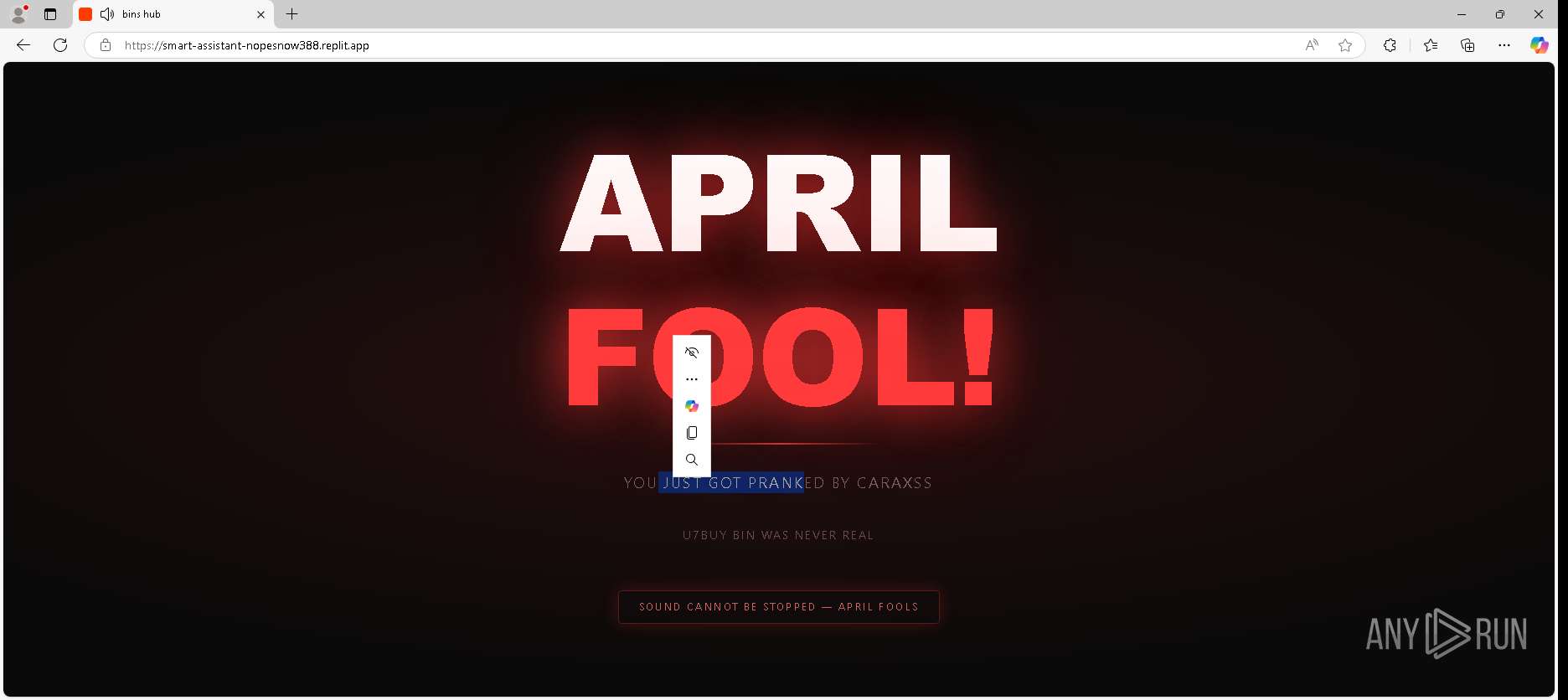
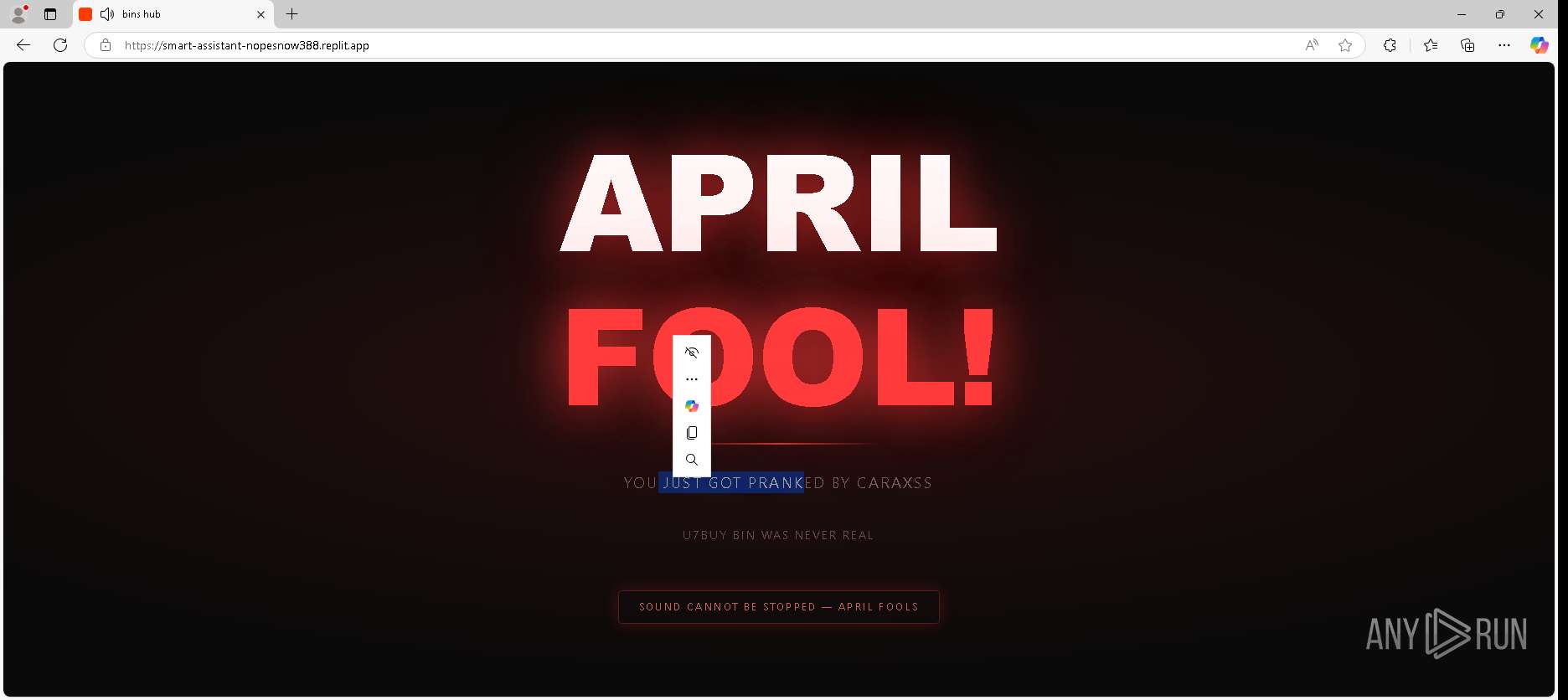
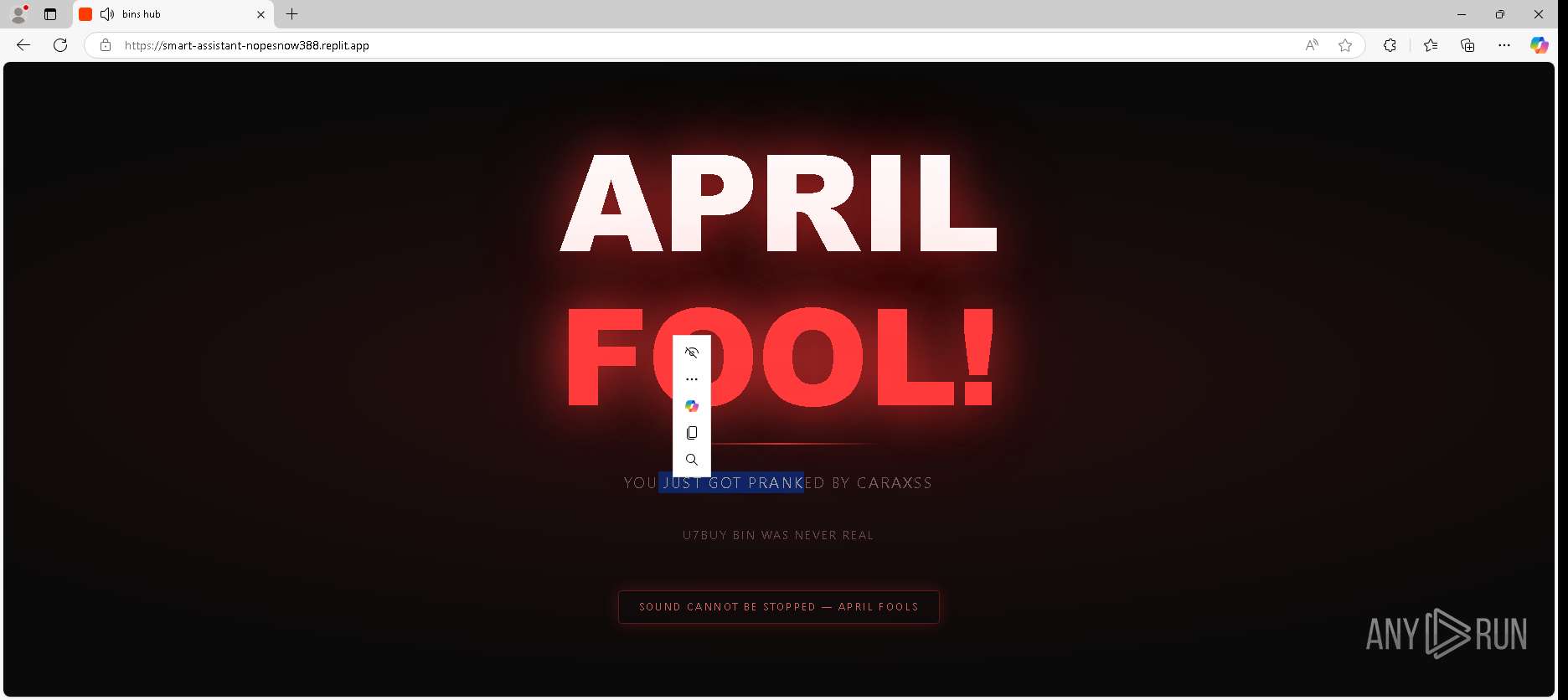
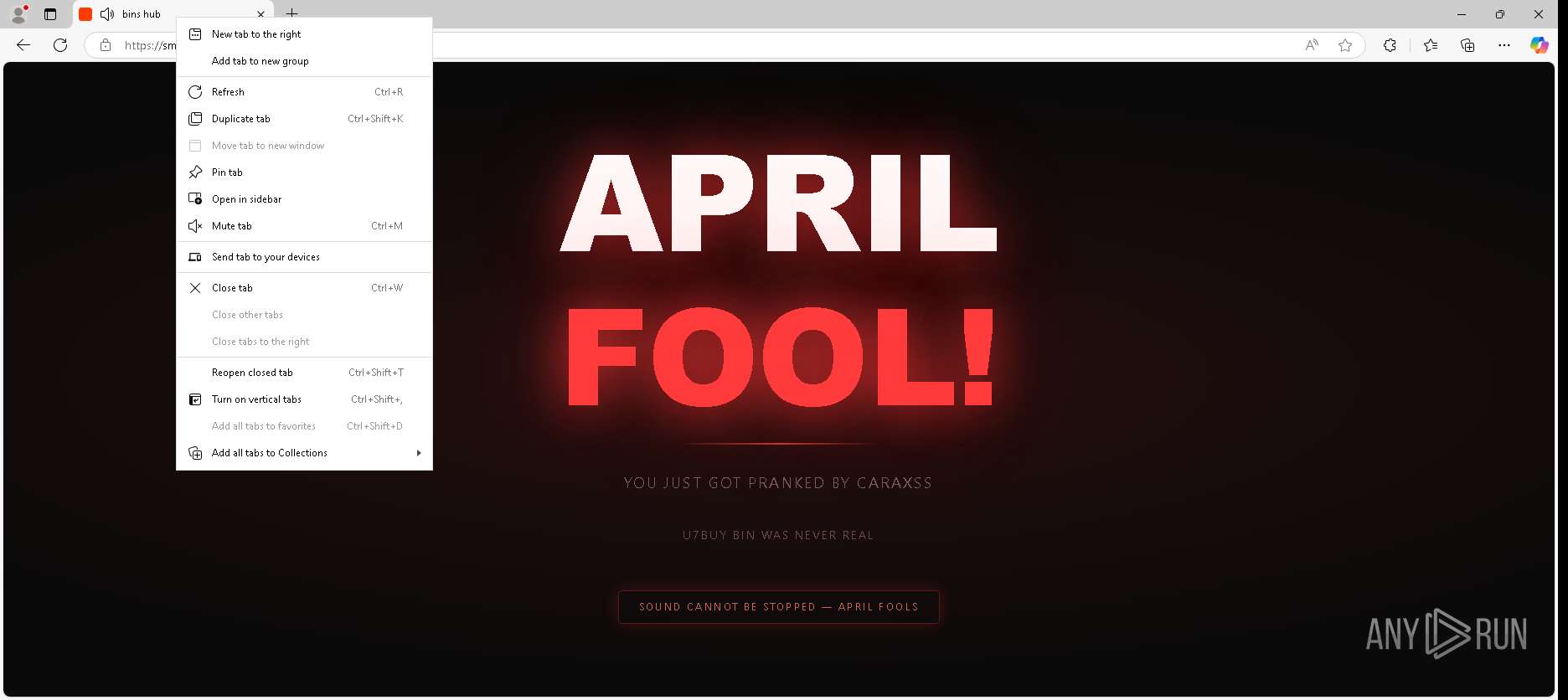
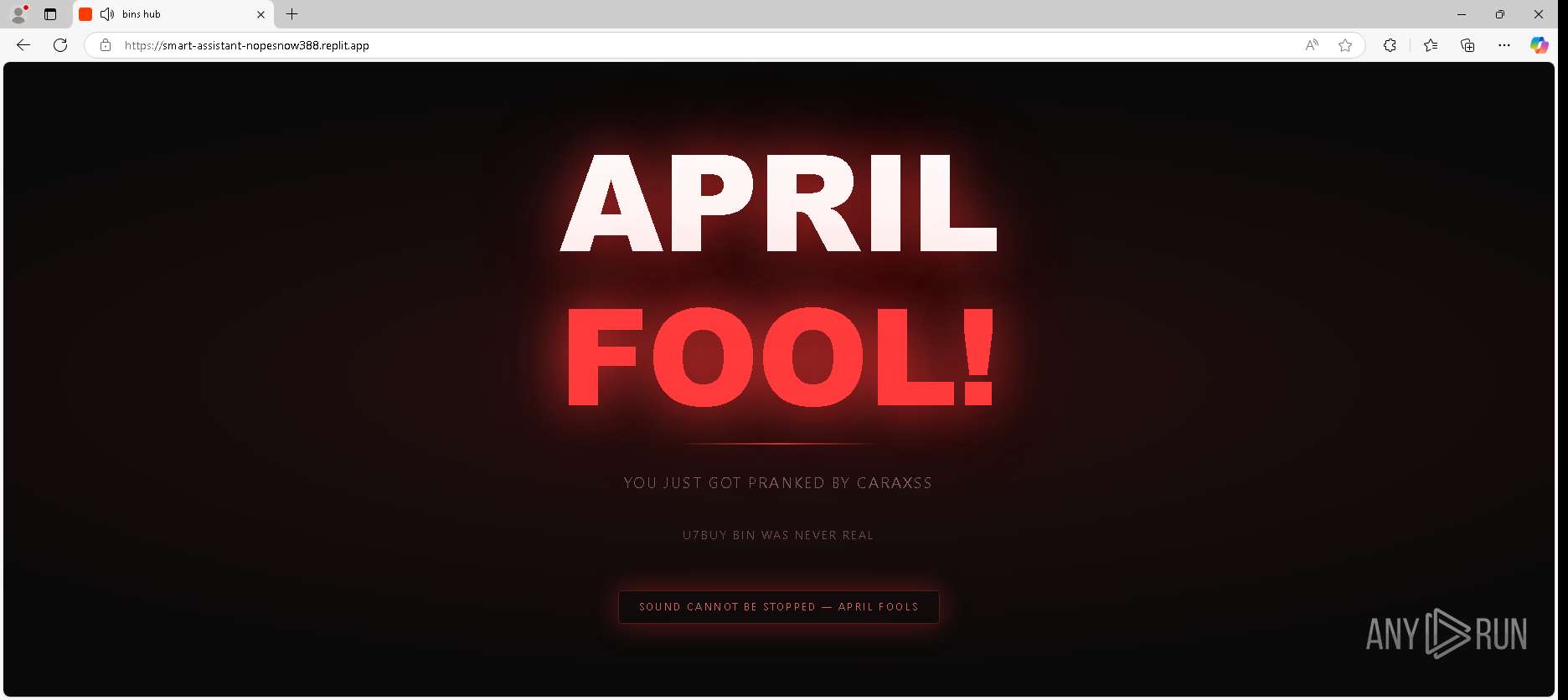
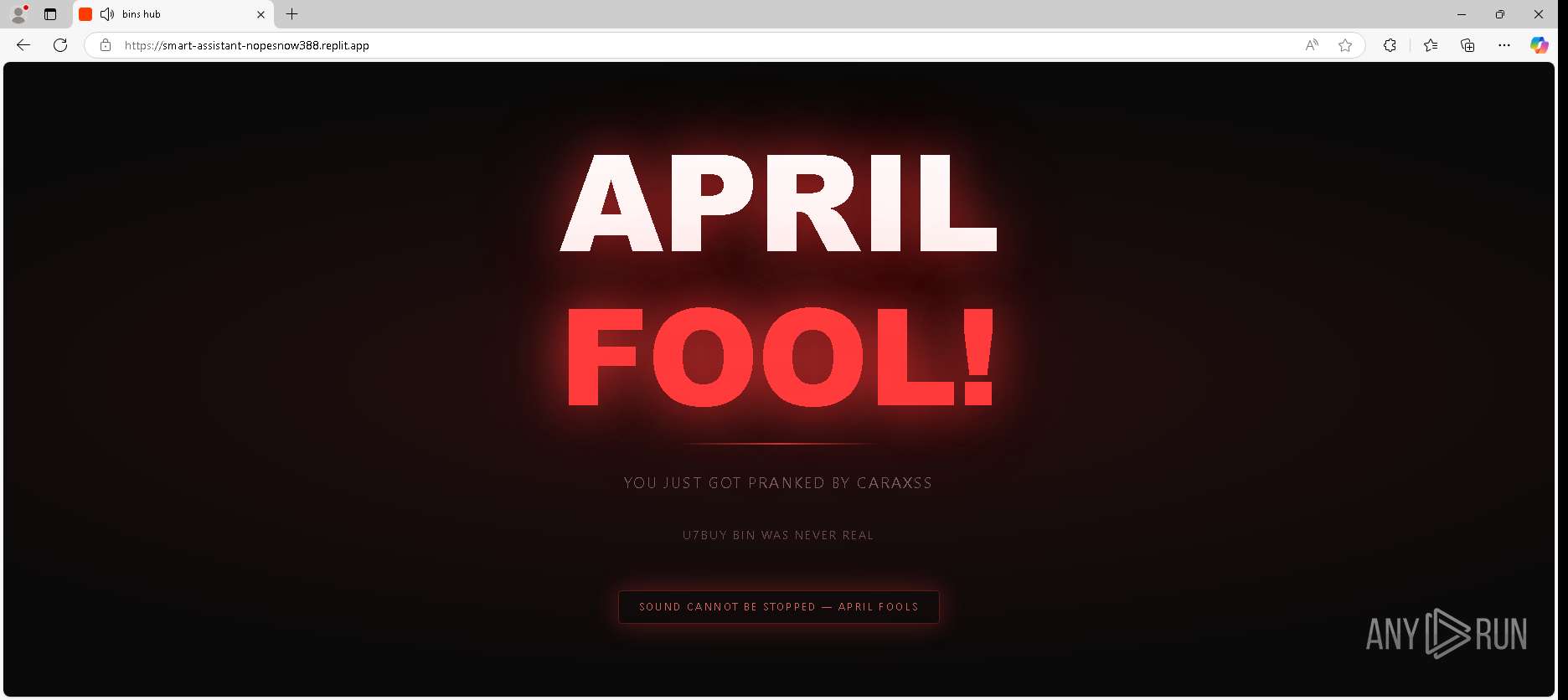
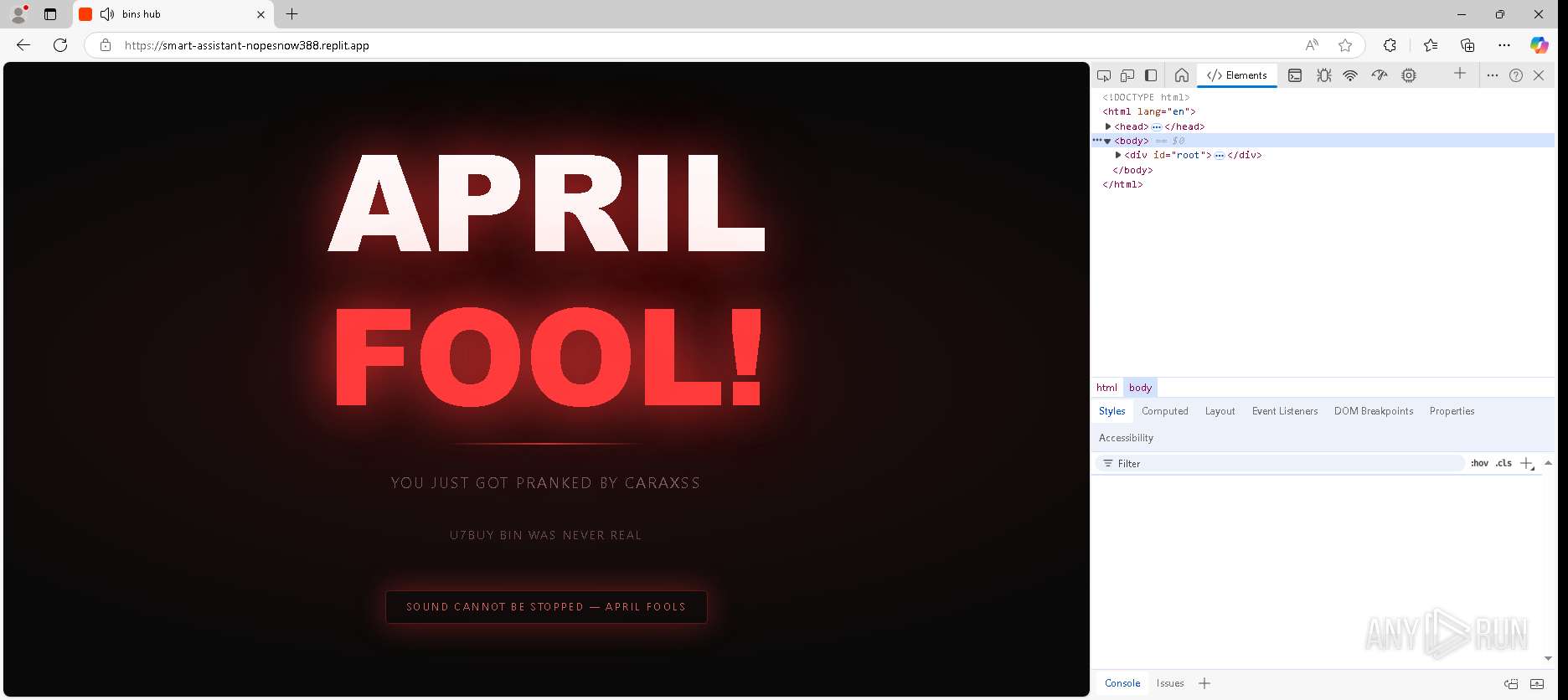
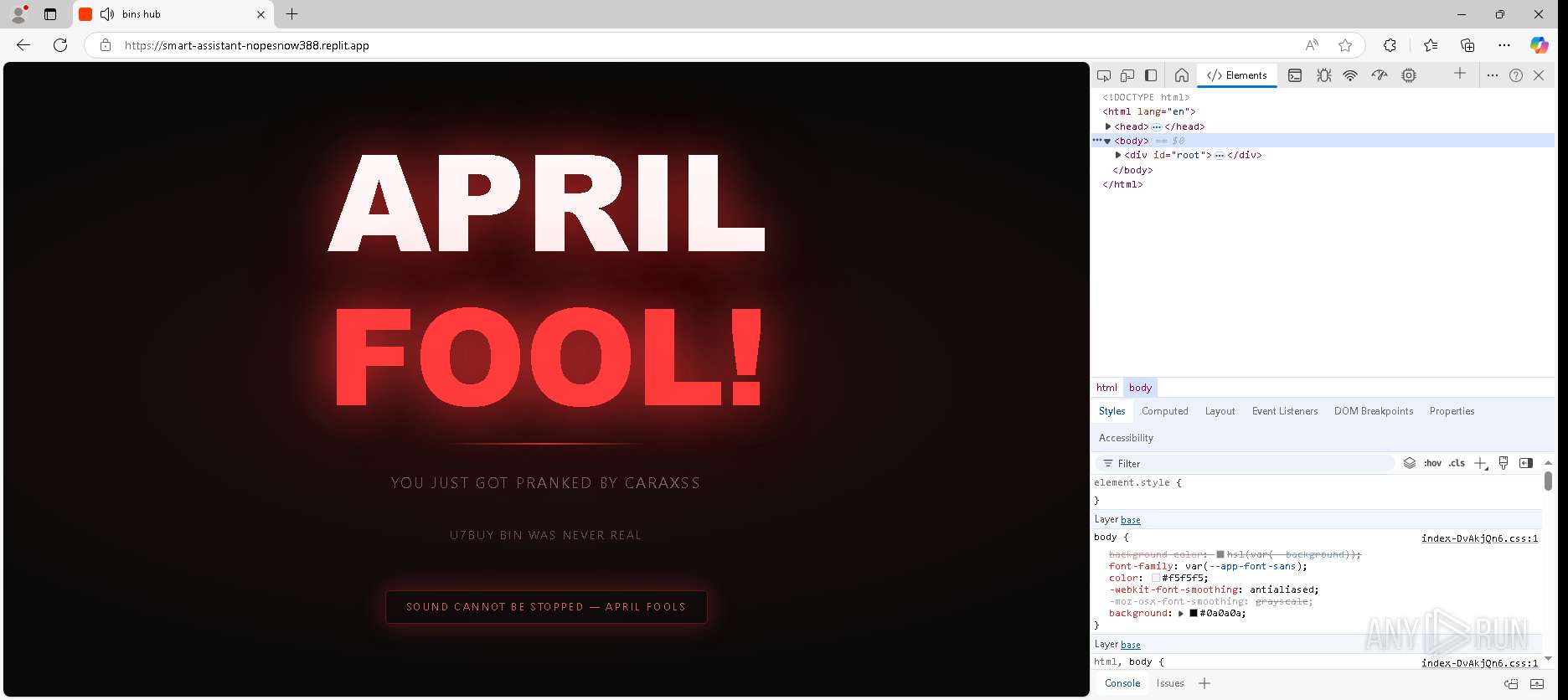
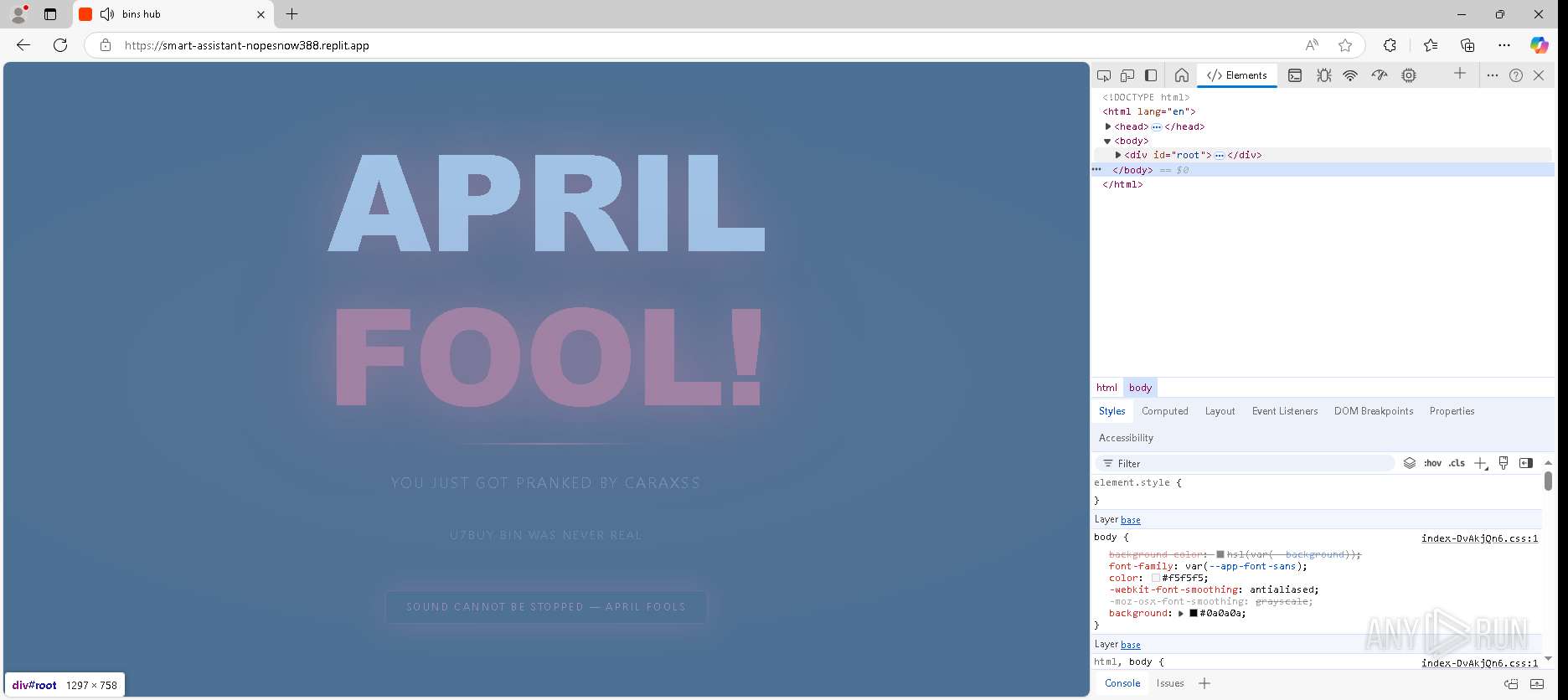
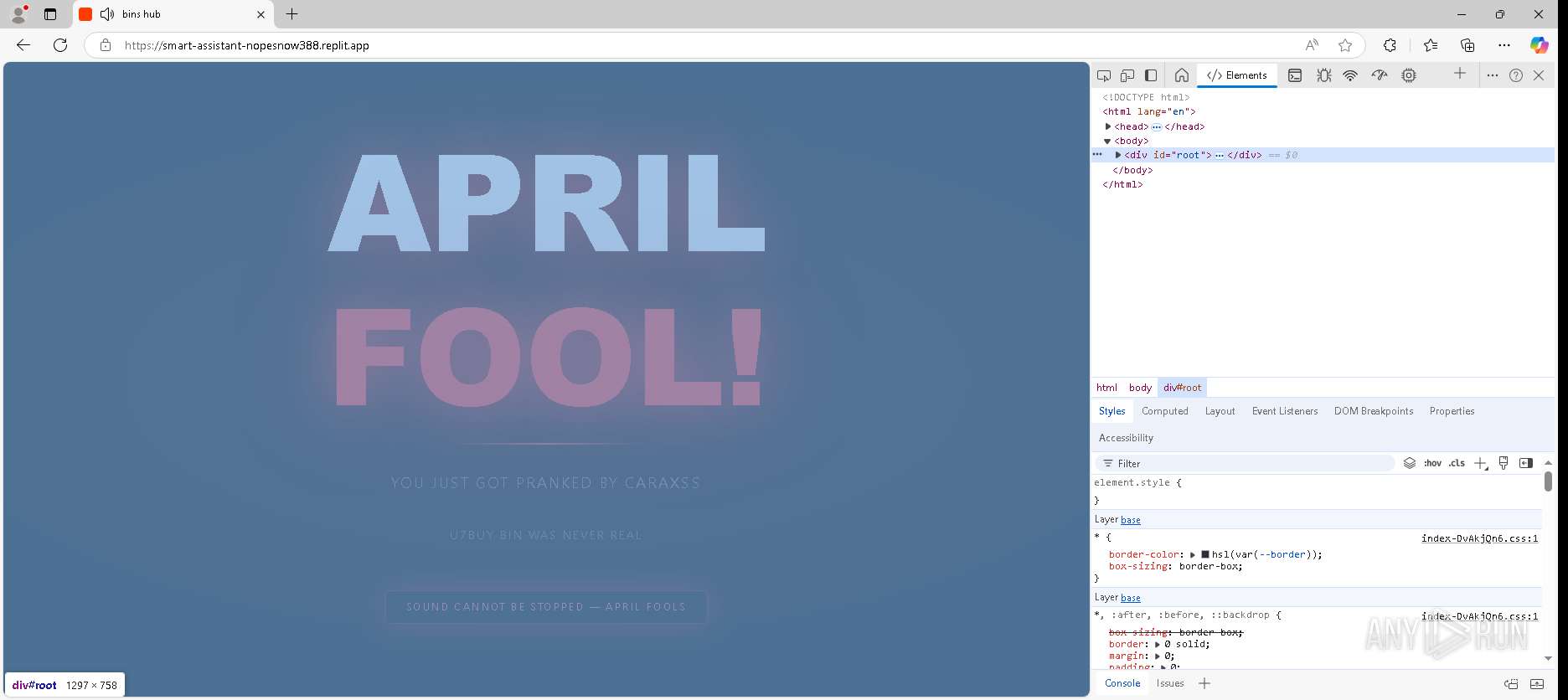
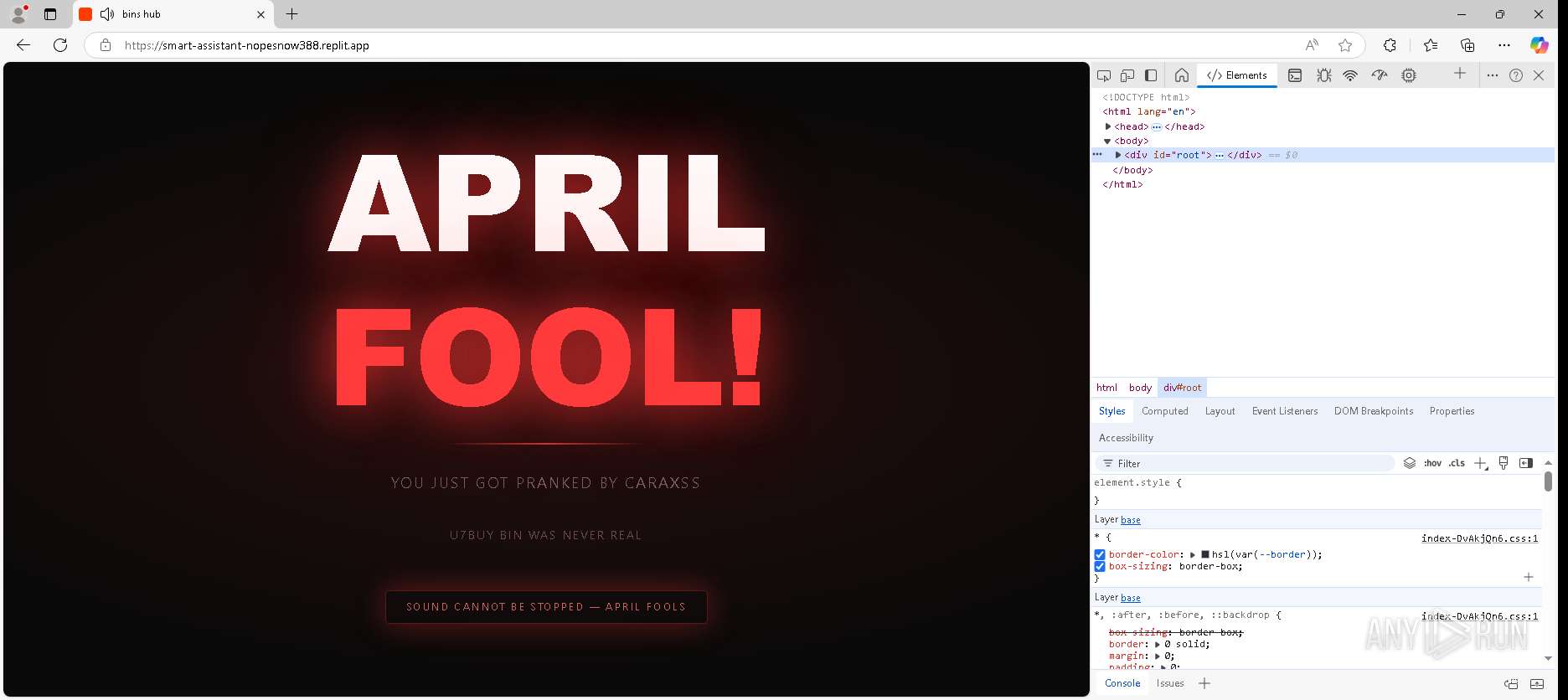
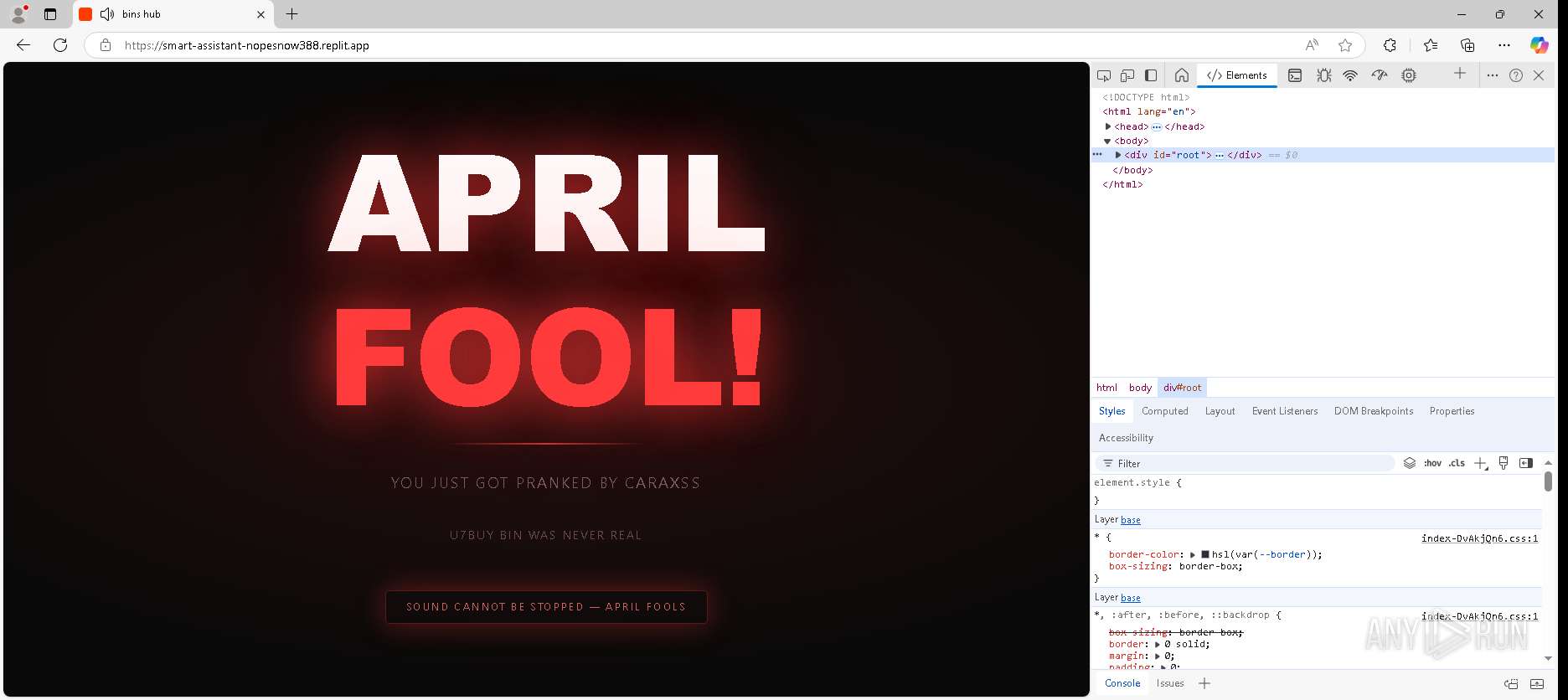
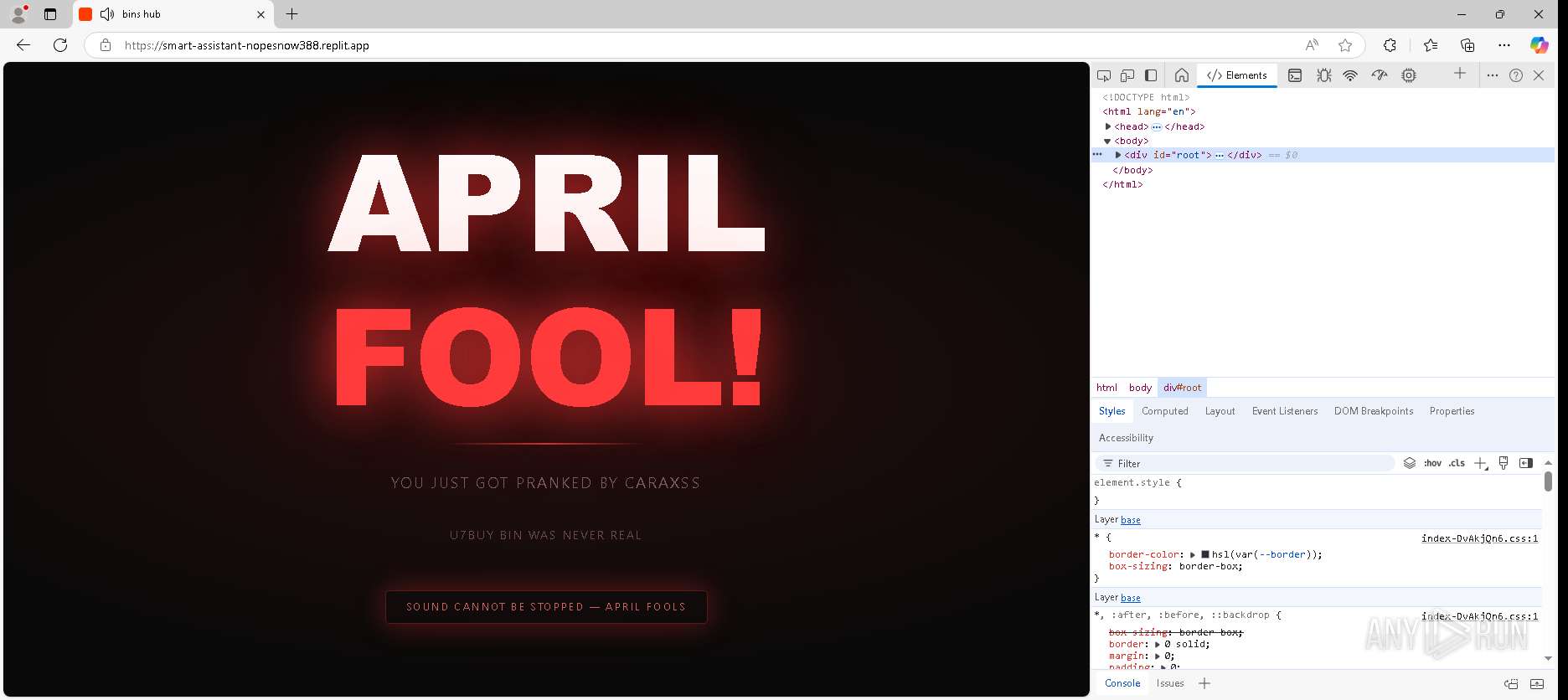
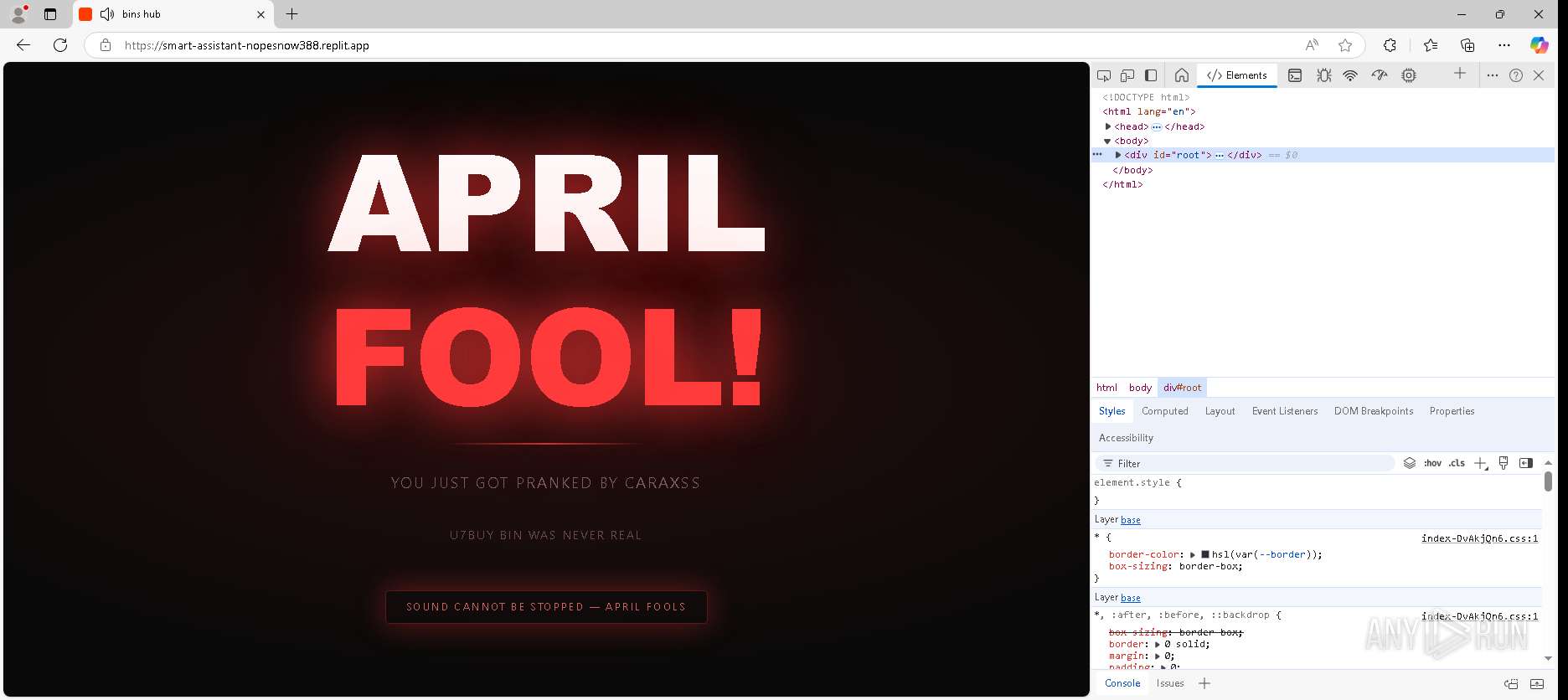
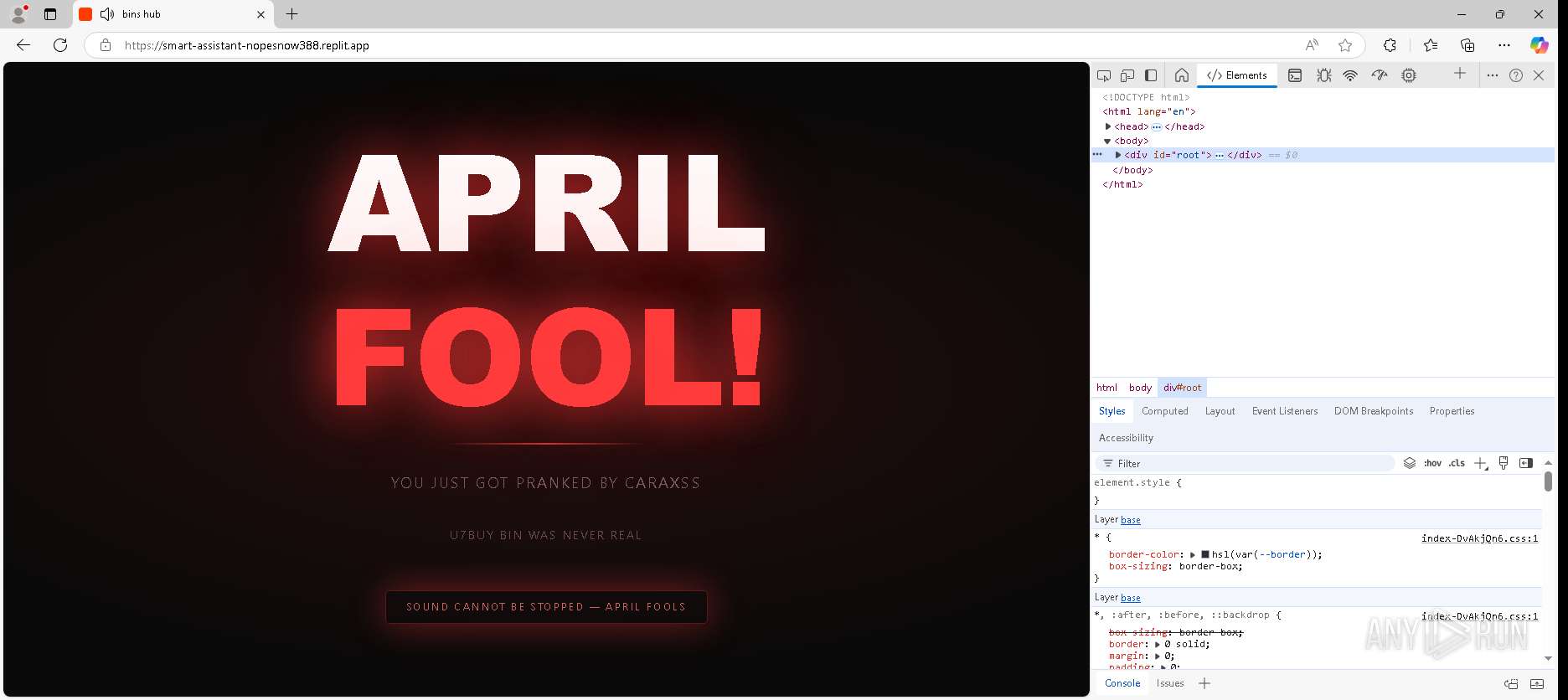
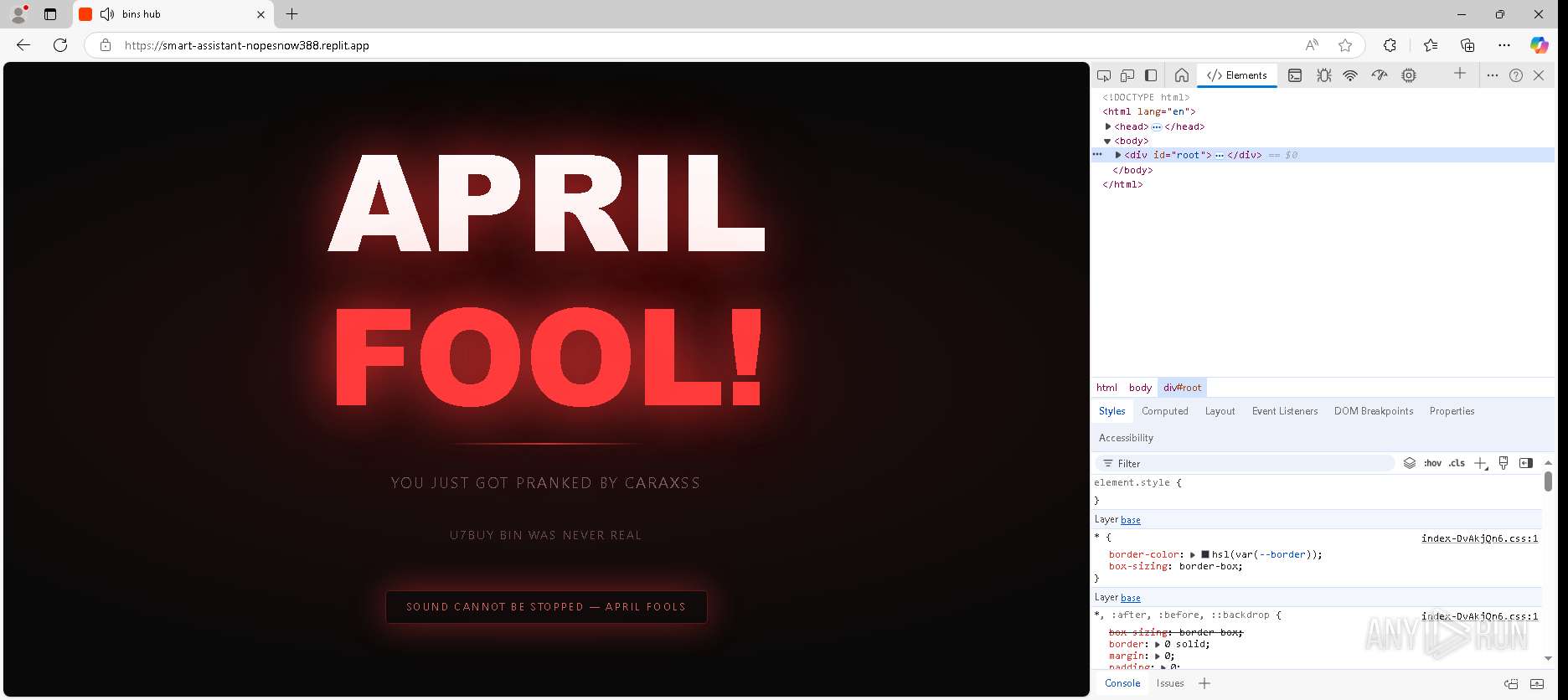
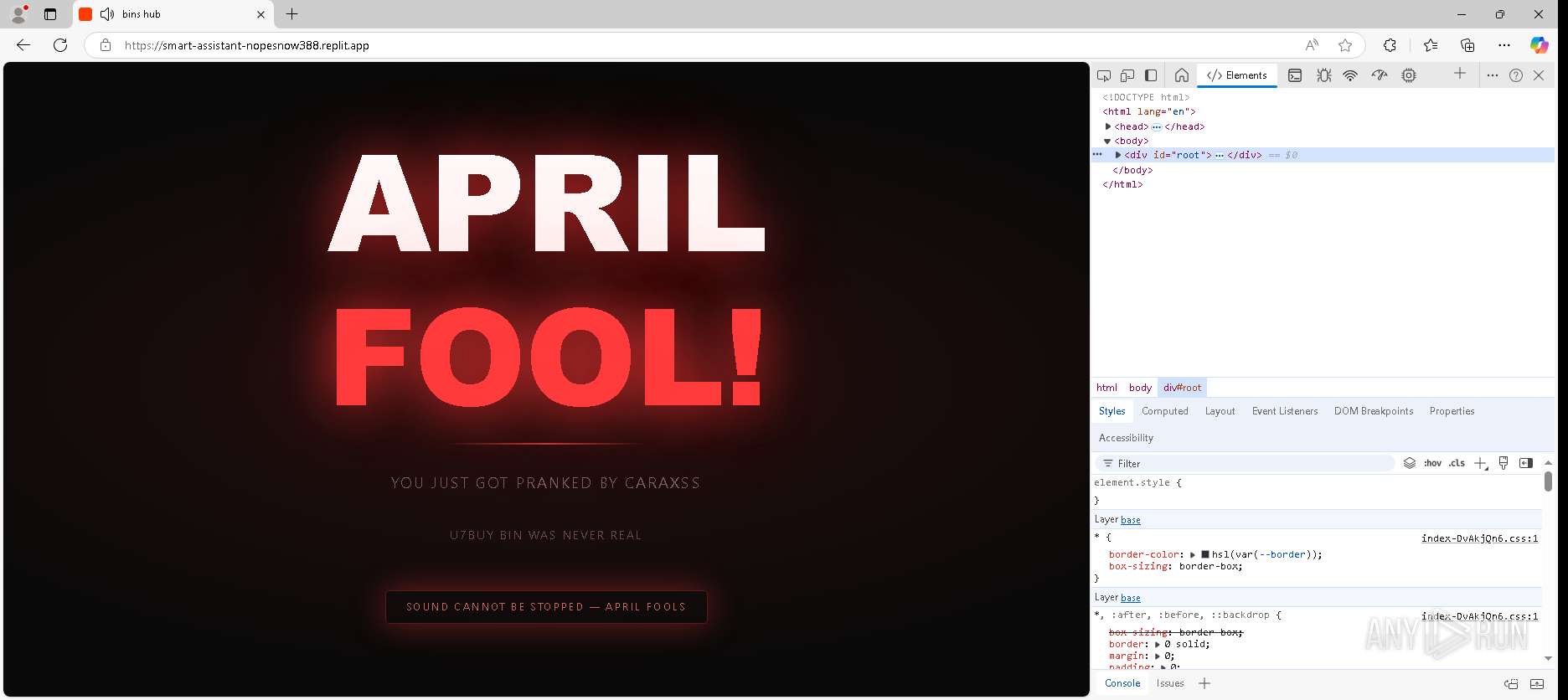
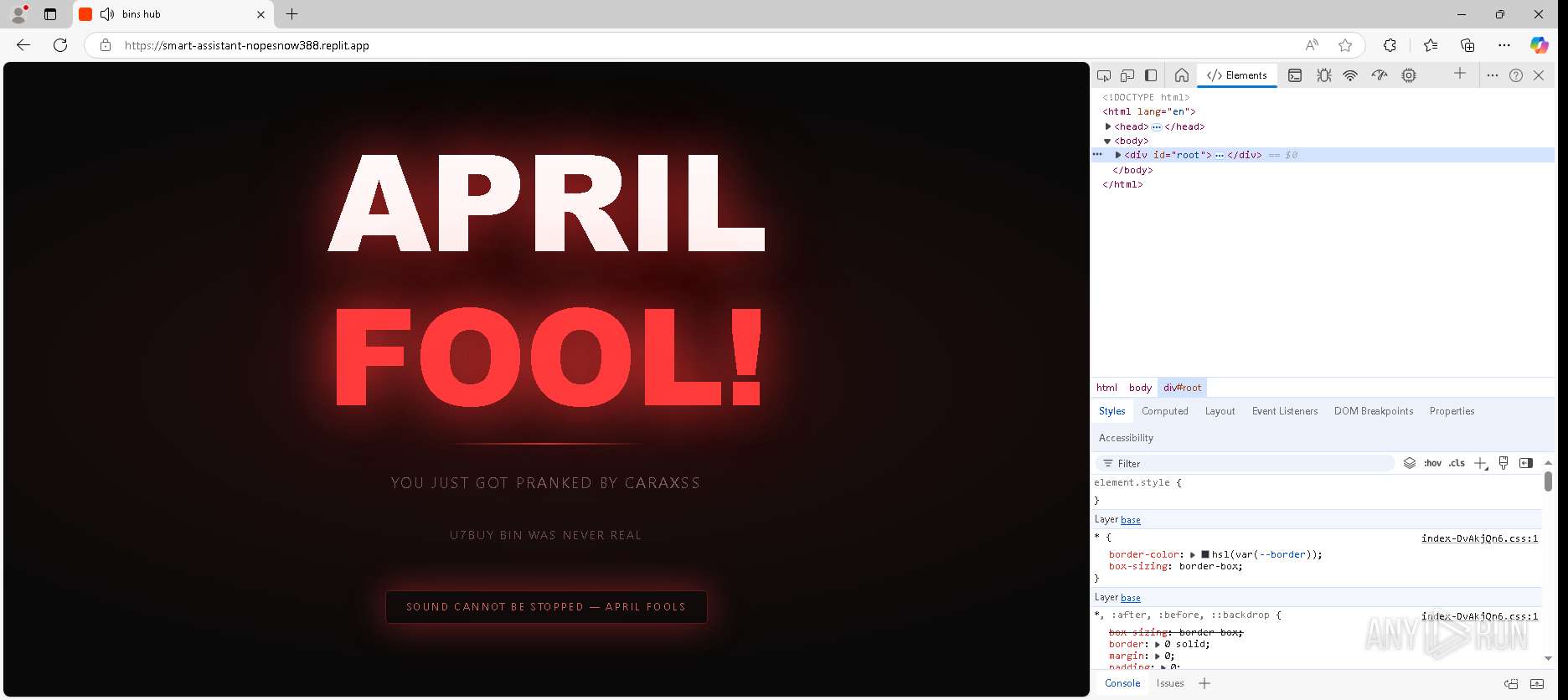
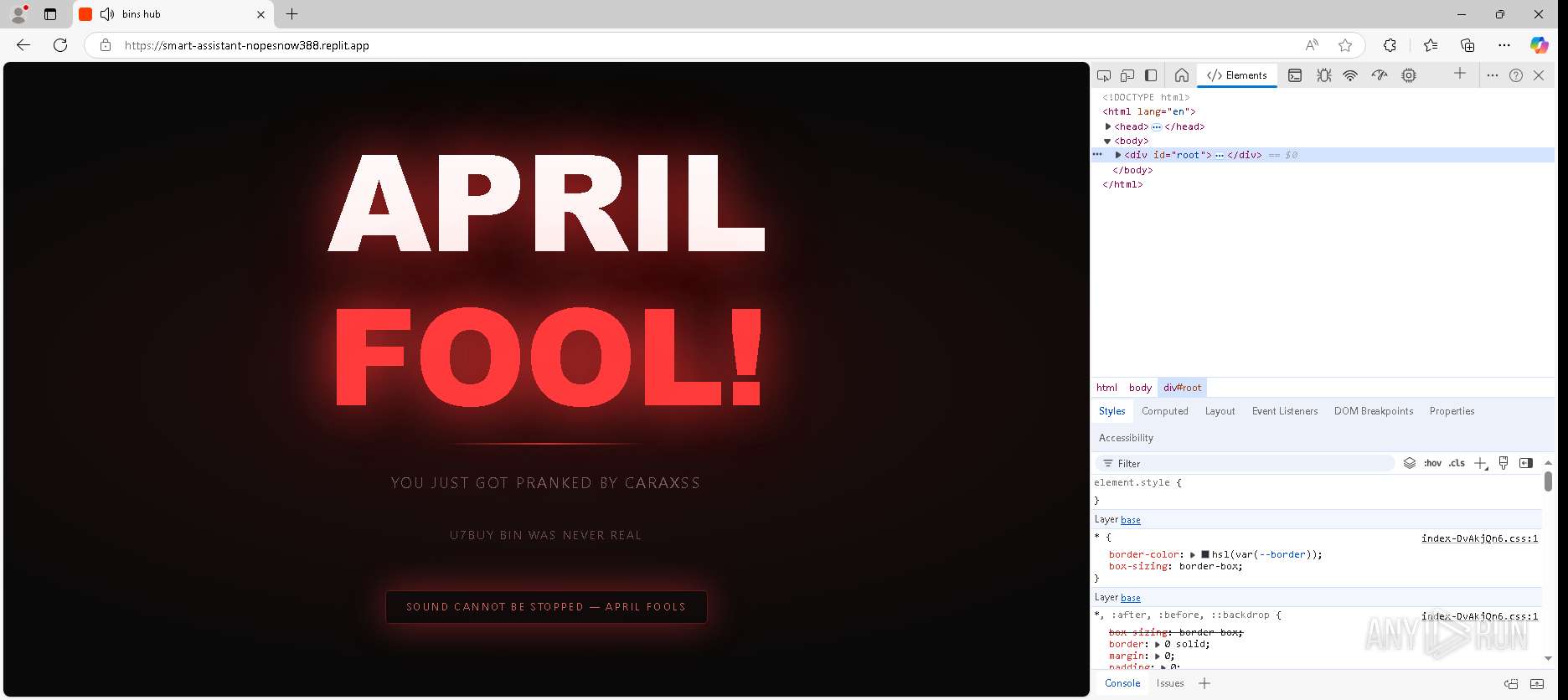
| URL: | https://smart-assistant-nopesnow388.replit.app/ |
| Full analysis: | https://app.any.run/tasks/21519b03-8a9f-49e5-9f0a-eaa07d8d568e |
| Verdict: | Malicious activity |
| Analysis date: | April 02, 2026, 18:30:31 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MD5: | 4D4AA984FC42E67C04A77834894DC1D7 |
| SHA1: | C73165A0B3A0B351E70B26EE3728F8772CA16E5C |
| SHA256: | 652E1DD3FFCAF7C097631DB34D029E931DC5FC89DD16F529B2219F5A98DA3D60 |
| SSDEEP: | 3:N8FuIE4lnWQwdn:2JE4lnk |
MALICIOUS
PHISHING has been detected (SURICATA)
- msedge.exe (PID: 7028)
SUSPICIOUS
No suspicious indicators.INFO
No info indicators.
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
162
Monitored processes
1
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 7028 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=network.mojom.NetworkService --lang=en-US --service-sandbox-type=none --disable-quic --webtransport-developer-mode --string-annotations --always-read-main-dll --field-trial-handle=2256,i,13378875761215938322,9620771509043916482,262144 --variations-seed-version --mojo-platform-channel-handle=2616 /prefetch:3 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | msedge.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Version: 133.0.3065.92 Modules
| |||||||||||||||
Total events
0
Read events
0
Write events
0
Delete events
0
Modification events
Executable files
0
Suspicious files
5
Text files
4
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 7028 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\Network\Network Persistent State~RFf6a88.TMP | text | |
MD5:8CA6AC4CD0D4F8B2EA5A9FC6FD4311D7 | SHA256:EE810A451AEA499C3D6F89EDB840ED025DF0937874485A211A3BB39F915F4EA0 | |||
| 7028 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\Cache\Cache_Data\f_0000b6 | binary | |
MD5:A9123BC9C71B21A22DBBA84EAB1A5615 | SHA256:189FD8447C779A006AC506F94C43BE3771BF3090443D762F3EF22C9C5134D5A0 | |||
| 7028 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\Network\94135e46-d468-465a-bc2d-1922e102e449.tmp | text | |
MD5:F054A7D6E382DF24018FE84986B710A2 | SHA256:4E5235C6B40BCE6C5FD0554D554FCDB38E8016DCDDFA9CAB63103407CAF8DAEB | |||
| 7028 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\Cache\Cache_Data\f_0000b5 | text | |
MD5:AD528D8C1E165081896E88270BCD4D3F | SHA256:9C5D62EA749DFA66DE3F2928D65EEC1C8F2398AD2B79EFF18C0232537D7D1B99 | |||
| 7028 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\Cache\Cache_Data\f_0000b8 | binary | |
MD5:A9123BC9C71B21A22DBBA84EAB1A5615 | SHA256:189FD8447C779A006AC506F94C43BE3771BF3090443D762F3EF22C9C5134D5A0 | |||
| 7028 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\Cache\Cache_Data\f_0000b7 | binary | |
MD5:6F657199C6D8D395218B09DD34ECD11F | SHA256:1EE8691D91D5F076A512C67E07F0FECC60A9A35512F0F6C119C92A88E59A23E3 | |||
| 7028 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\Cache\Cache_Data\f_0000b9 | compressed | |
MD5:F3AD19FDBD15A27B32A4D25E49CC266E | SHA256:3A657EDDEC2905CE29950E37A3CC78C6839AFC858FE26A89490A1502BE032D13 | |||
| 7028 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\Network\Network Persistent State | text | |
MD5:F054A7D6E382DF24018FE84986B710A2 | SHA256:4E5235C6B40BCE6C5FD0554D554FCDB38E8016DCDDFA9CAB63103407CAF8DAEB | |||
| 7028 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\Cache\Cache_Data\f_0000ba | binary | |
MD5:5E67A6EF34FA21F24259250187259C64 | SHA256:FA0FCF2A49A7DBBDCBAC318BF492E1DA907D938657D13892ED61AF36FC78E52B | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
64
TCP/UDP connections
56
DNS requests
58
Threats
5
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
5244 | RUXIMICS.exe | GET | 304 | 20.73.194.208:443 | https://settings-win.data.microsoft.com/settings/v3.0/WSD/RUXIM?os=Windows&osVer=10.0.19045.4046.amd64fre.vb_release.191206-1406&sku=48&deviceClass=Windows.Desktop&locale=en-US&deviceId=s:BAD99146-31D3-4EC6-A1A4-BE76F32BA5D4&sampleId=s:95271487&appVer=10.0.19041.3623&OSVersionFull=10.0.19045.4046.amd64fre.vb_release.191206-1406&FlightRing=Retail&AttrDataVer=188&App=RUXIM&AppVer=&DeviceFamily=Windows.Desktop | US | — | — | whitelisted |
5336 | MoUsoCoreWorker.exe | GET | 304 | 20.73.194.208:443 | https://settings-win.data.microsoft.com/settings/v3.0/wsd/muse?ProcessorClockSpeed=3593&FlightIds=&UpdateOfferedDays=344&BranchReadinessLevel=CB&OEMManufacturerName=DELL&IsCloudDomainJoined=0&ProcessorIdentifier=AMD64%20Family%206%20Model%2014%20Stepping%203&sku=48&ActivationChannel=Retail&AttrDataVer=188&IsMDMEnrolled=0&ProcessorCores=4&ProcessorModel=Intel%28R%29%20Core%28TM%29%20i5-6400%20CPU%20%40%202.70GHz&TotalPhysicalRAM=4096&PrimaryDiskType=4294967295&FlightingBranchName=&ChassisTypeId=1&OEMModelNumber=DELL&SystemVolumeTotalCapacity=260246&sampleId=95271487&deviceClass=Windows.Desktop&App=muse&DisableDualScan=0&AppVer=10.0&OEMSubModel=J5CR&locale=en-US&IsAlwaysOnAlwaysConnectedCapable=0&ms=0&DefaultUserRegion=244&osVer=10.0.19045.4046.amd64fre.vb_release.191206-1406&os=windows&deviceId=s%3ABAD99146-31D3-4EC6-A1A4-BE76F32BA5D4&DeferQualityUpdatePeriodInDays=0&ring=Retail&DeferFeatureUpdatePeriodInDays=30 | US | — | — | whitelisted |
7760 | svchost.exe | HEAD | 200 | 104.102.63.189:443 | https://fs.microsoft.com/fs/windows/config.json | US | — | — | whitelisted |
7028 | msedge.exe | GET | 200 | 34.117.33.233:443 | https://smart-assistant-nopesnow388.replit.app/ | US | binary | 728 b | unknown |
5188 | svchost.exe | GET | 200 | 184.24.77.12:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | NL | binary | 825 b | whitelisted |
7028 | msedge.exe | GET | 200 | 34.117.33.233:443 | https://smart-assistant-nopesnow388.replit.app/assets/index-6cl_hwSi.js | US | binary | 369 Kb | unknown |
5244 | RUXIMICS.exe | GET | 200 | 184.24.77.12:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | NL | binary | 825 b | whitelisted |
7028 | msedge.exe | GET | 200 | 34.117.33.233:443 | https://smart-assistant-nopesnow388.replit.app/assets/index-DvAkjQn6.css | US | binary | 74.2 Kb | unknown |
7028 | msedge.exe | GET | 200 | 92.123.104.37:443 | https://www.bing.com/bloomfilterfiles/ExpandedDomainsFilterGlobal.json | unknown | text | 665 Kb | whitelisted |
7028 | msedge.exe | GET | 200 | 142.251.110.95:443 | https://fonts.googleapis.com/css2?family=Inter:wght@400;500;600;700&display=swap | US | binary | 9.65 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
5188 | svchost.exe | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
5244 | RUXIMICS.exe | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
5336 | MoUsoCoreWorker.exe | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
— | — | 224.0.0.251:5353 | — | — | — | whitelisted |
7028 | msedge.exe | 34.117.33.233:443 | smart-assistant-nopesnow388.replit.app | GOOGLE-CLOUD-PLATFORM | US | whitelisted |
5188 | svchost.exe | 184.24.77.12:80 | crl.microsoft.com | AKAMAI-ASN1 | NL | whitelisted |
5244 | RUXIMICS.exe | 184.24.77.12:80 | crl.microsoft.com | AKAMAI-ASN1 | NL | whitelisted |
5336 | MoUsoCoreWorker.exe | 184.24.77.12:80 | crl.microsoft.com | AKAMAI-ASN1 | NL | whitelisted |
5188 | svchost.exe | 23.52.181.212:80 | www.microsoft.com | AKAMAI-AS | US | whitelisted |
7028 | msedge.exe | 142.251.110.95:443 | fonts.googleapis.com | GOOGLE | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
smart-assistant-nopesnow388.replit.app |
| unknown |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
www.bing.com |
| whitelisted |
fonts.googleapis.com |
| whitelisted |
fonts.gstatic.com |
| whitelisted |
fs.microsoft.com |
| whitelisted |
xpaywalletcdn.azureedge.net |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
7028 | msedge.exe | Possible Social Engineering Attempted | PHISHING [ANY.RUN] Abusing Replit Desktop App domain has been detected |
7028 | msedge.exe | Possible Social Engineering Attempted | PHISHING [ANY.RUN] Abusing Replit Desktop App domain has been detected |
5188 | svchost.exe | Unknown Traffic | ET USER_AGENTS Microsoft Dr Watson User-Agent (MSDW) |
7028 | msedge.exe | Possible Social Engineering Attempted | PHISHING [ANY.RUN] Abusing Replit Desktop App domain has been detected |
7028 | msedge.exe | Possible Social Engineering Attempted | PHISHING [ANY.RUN] Abusing Replit Desktop App domain has been detected |