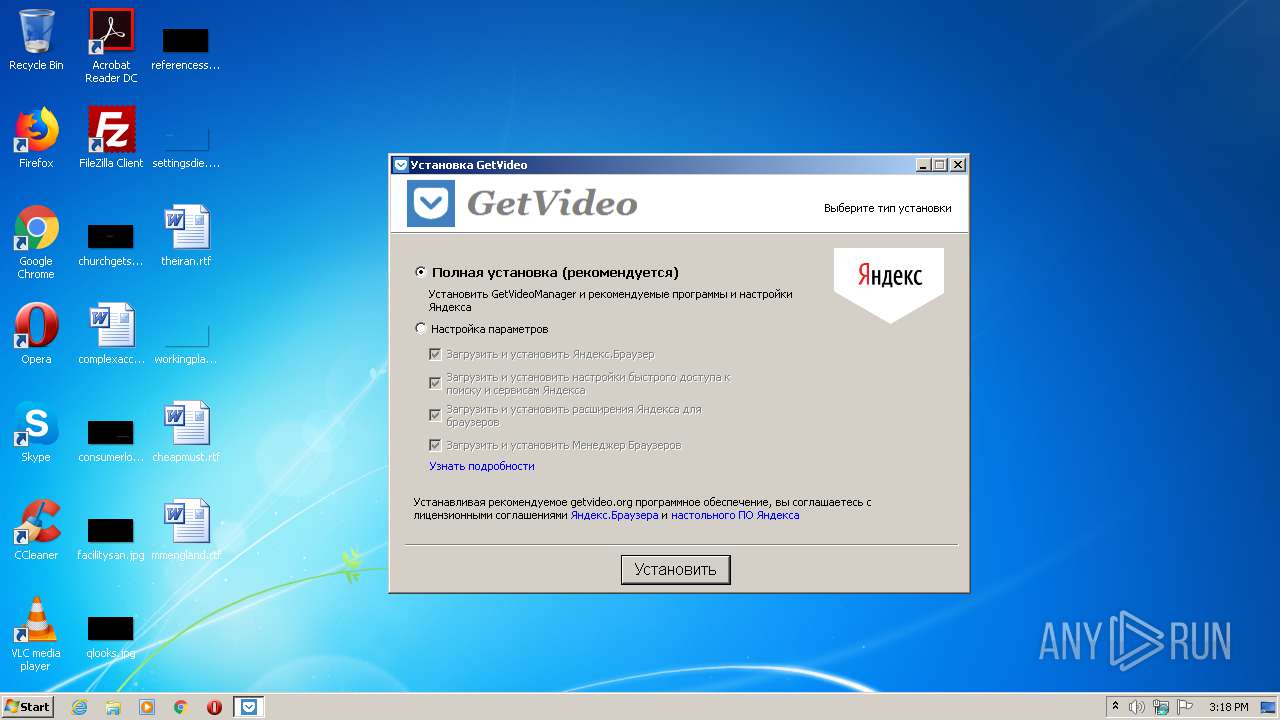
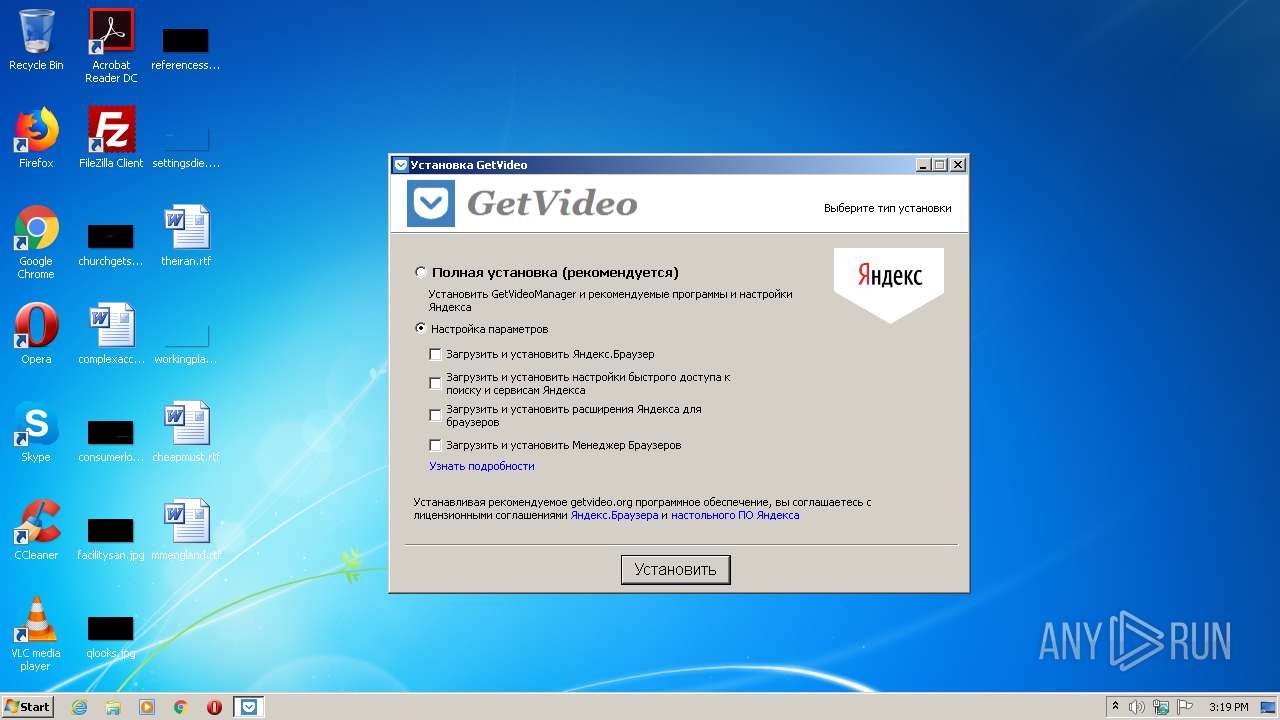
| File name: | GetVideoSetup_v1.8.0.7.ru.exe |
| Full analysis: | https://app.any.run/tasks/b75c114b-8d03-44fc-b4f2-77d9c29b9a03 |
| Verdict: | Malicious activity |
| Analysis date: | March 12, 2021, 15:18:27 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | 8BA7EF67ED4111377D65CD3E3C9885DB |
| SHA1: | E6548F38DE75C2134FEC51F688D1BA64810ABE55 |
| SHA256: | 6523C47241FA57C45A46AB8F452AF2FC516FA413C72C2B6A86E2AE855424A052 |
| SSDEEP: | 49152:+3+5Wz6+JEKohF3PgAKk8yVZC++B4vBXX+CyFcJ:+3+LGohF/xCyS+K4vBH3yuJ |
MALICIOUS
Loads dropped or rewritten executable
- GetVideoSetup_v1.8.0.7.ru.exe (PID: 1624)
- GetVideo.exe (PID: 752)
- GetVideoSetup_v1.8.0.7.ru.exe (PID: 3464)
Drops executable file immediately after starts
- GetVideoSetup_v1.8.0.7.ru.exe (PID: 3464)
Application was dropped or rewritten from another process
- GetVideo.exe (PID: 752)
Changes the autorun value in the registry
- GetVideoSetup_v1.8.0.7.ru.exe (PID: 3464)
Changes settings of System certificates
- GetVideo.exe (PID: 752)
SUSPICIOUS
Drops a file that was compiled in debug mode
- GetVideoSetup_v1.8.0.7.ru.exe (PID: 3464)
- GetVideoSetup_v1.8.0.7.ru.exe (PID: 1624)
Executable content was dropped or overwritten
- GetVideoSetup_v1.8.0.7.ru.exe (PID: 1624)
- GetVideoSetup_v1.8.0.7.ru.exe (PID: 3464)
Application launched itself
- GetVideoSetup_v1.8.0.7.ru.exe (PID: 1624)
Creates files in the Windows directory
- GetVideoSetup_v1.8.0.7.ru.exe (PID: 3464)
Drops a file with too old compile date
- GetVideoSetup_v1.8.0.7.ru.exe (PID: 3464)
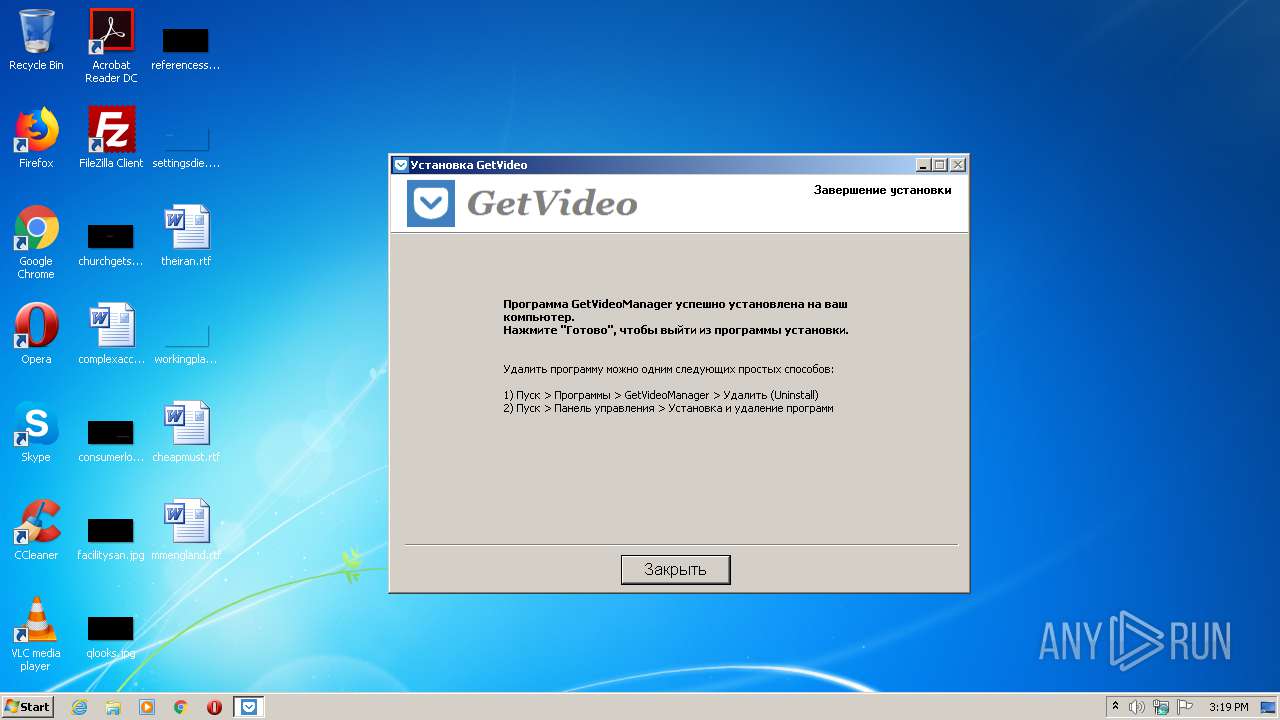
Creates a software uninstall entry
- GetVideoSetup_v1.8.0.7.ru.exe (PID: 3464)
Creates files in the user directory
- GetVideoSetup_v1.8.0.7.ru.exe (PID: 3464)
Starts Internet Explorer
- GetVideoSetup_v1.8.0.7.ru.exe (PID: 3464)
Drops a file with a compile date too recent
- GetVideoSetup_v1.8.0.7.ru.exe (PID: 3464)
Reads internet explorer settings
- GetVideo.exe (PID: 752)
Adds / modifies Windows certificates
- GetVideo.exe (PID: 752)
INFO
Application launched itself
- iexplore.exe (PID: 2000)
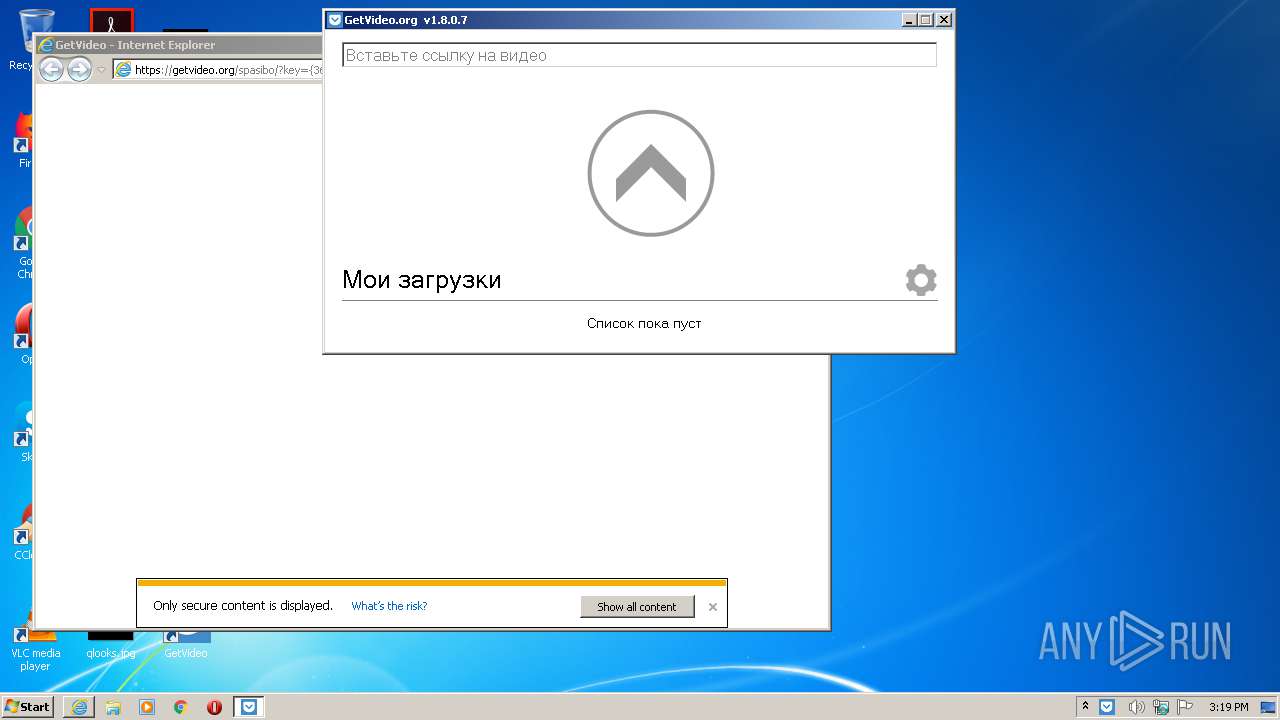
Changes internet zones settings
- iexplore.exe (PID: 2000)
Dropped object may contain Bitcoin addresses
- GetVideoSetup_v1.8.0.7.ru.exe (PID: 3464)
Reads settings of System Certificates
- iexplore.exe (PID: 480)
- iexplore.exe (PID: 2000)
Reads internet explorer settings
- iexplore.exe (PID: 480)
Creates files in the user directory
- iexplore.exe (PID: 480)
Changes settings of System certificates
- iexplore.exe (PID: 480)
Adds / modifies Windows certificates
- iexplore.exe (PID: 480)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable MS Visual C++ (generic) (42.2) |
|---|---|---|
| .exe | | | Win64 Executable (generic) (37.3) |
| .dll | | | Win32 Dynamic Link Library (generic) (8.8) |
| .exe | | | Win32 Executable (generic) (6) |
| .exe | | | Generic Win/DOS Executable (2.7) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2012:02:24 20:19:54+01:00 |
| PEType: | PE32 |
| LinkerVersion: | 10 |
| CodeSize: | 28160 |
| InitializedDataSize: | 445952 |
| UninitializedDataSize: | 16896 |
| EntryPoint: | 0x3883 |
| OSVersion: | 5 |
| ImageVersion: | 6 |
| SubsystemVersion: | 5 |
| Subsystem: | Windows GUI |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 24-Feb-2012 19:19:54 |
| Detected languages: |
|
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x000000D0 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 6 |
| Time date stamp: | 24-Feb-2012 19:19:54 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x00006DAE | 0x00006E00 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.50853 |
.rdata | 0x00008000 | 0x00002A62 | 0x00002C00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 4.39054 |
.data | 0x0000B000 | 0x00067EBC | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 1.43086 |
.ndata | 0x00073000 | 0x000E9000 | 0x00000000 | IMAGE_SCN_CNT_UNINITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.rsrc | 0x0015C000 | 0x00007CE8 | 0x00007E00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 2.53402 |
.reloc | 0x00164000 | 0x00000F32 | 0x00001000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_DISCARDABLE, IMAGE_SCN_MEM_READ | 1.67426 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.2266 | 957 | UNKNOWN | English - United States | RT_MANIFEST |
2 | 0 | 3752 | UNKNOWN | English - United States | RT_ICON |
3 | 0 | 2216 | UNKNOWN | English - United States | RT_ICON |
4 | 0 | 1384 | UNKNOWN | English - United States | RT_ICON |
5 | 0 | 1128 | UNKNOWN | English - United States | RT_ICON |
6 | 0 | 744 | UNKNOWN | English - United States | RT_ICON |
7 | 0 | 296 | UNKNOWN | English - United States | RT_ICON |
103 | 3.56762 | 104 | UNKNOWN | English - United States | RT_GROUP_ICON |
105 | 2.68964 | 512 | UNKNOWN | English - United States | RT_DIALOG |
106 | 2.91148 | 248 | UNKNOWN | English - United States | RT_DIALOG |
Imports
ADVAPI32.dll |
COMCTL32.dll |
GDI32.dll |
KERNEL32.dll |
SHELL32.dll |
USER32.dll |
VERSION.dll |
ole32.dll |
Total processes
45
Monitored processes
5
Malicious processes
3
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 480 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:2000 CREDAT:275457 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
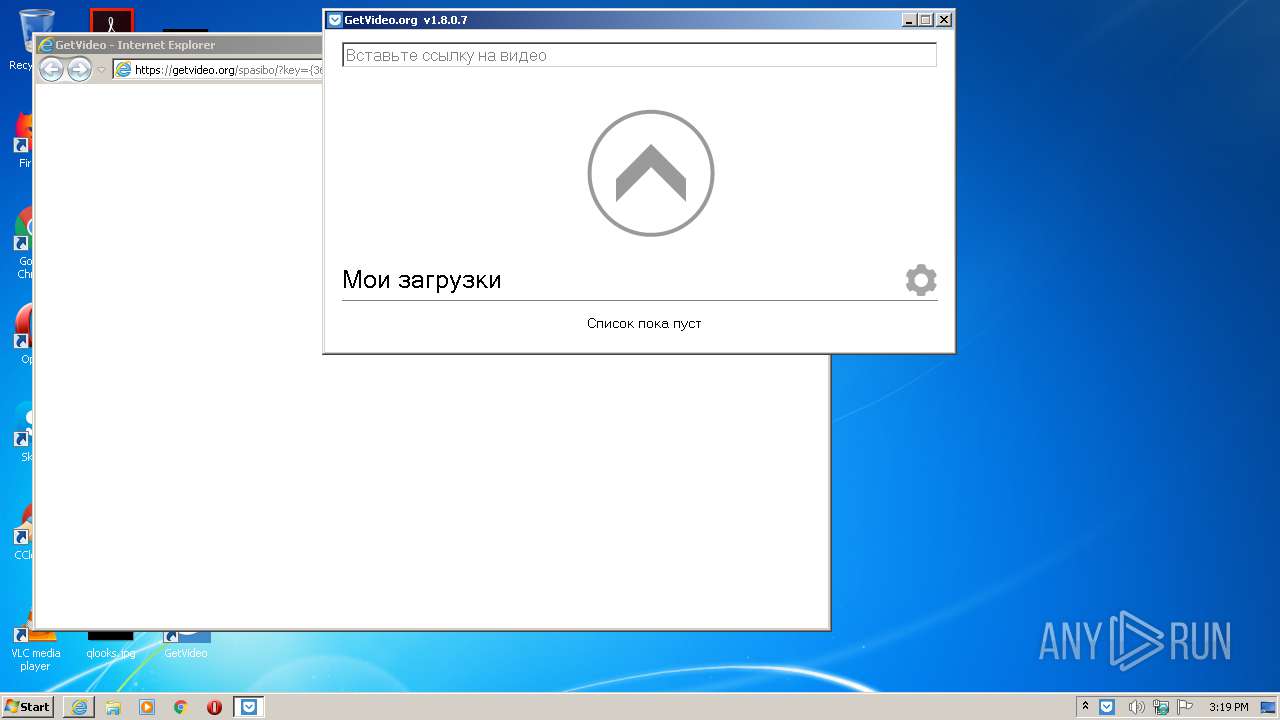
| 752 | C:\Users\admin\AppData\Local\GetVideo\GetVideo.exe | C:\Users\admin\AppData\Local\GetVideo\GetVideo.exe | GetVideoSetup_v1.8.0.7.ru.exe | ||||||||||||
User: admin Company: GetVideo.org Integrity Level: HIGH Description: GetVideo Exit code: 0 Version: 1.8.0.7 Modules
| |||||||||||||||
| 1624 | "C:\Users\admin\AppData\Local\Temp\GetVideoSetup_v1.8.0.7.ru.exe" | C:\Users\admin\AppData\Local\Temp\GetVideoSetup_v1.8.0.7.ru.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 1223 Modules
| |||||||||||||||
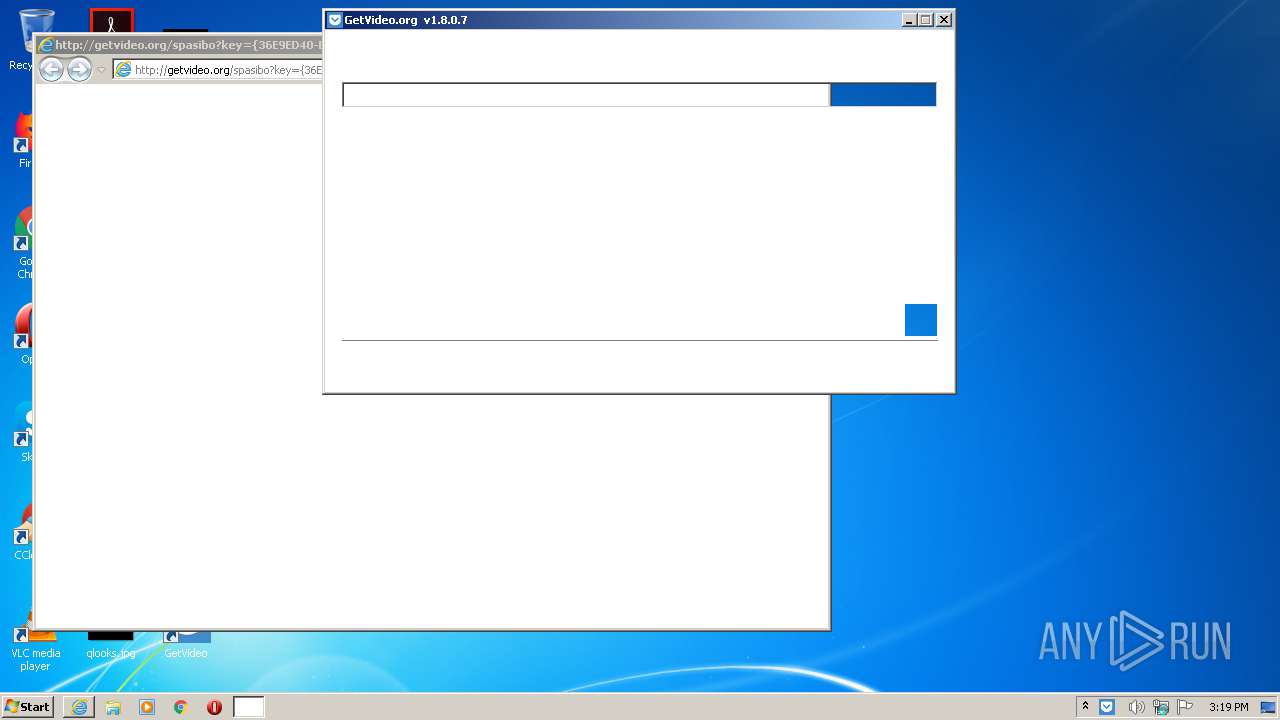
| 2000 | "C:\Program Files\Internet Explorer\iexplore.exe" http://getvideo.org/spasibo?key={36E9ED40-BD83-44F8-B564-DECD057E4138} | C:\Program Files\Internet Explorer\iexplore.exe | GetVideoSetup_v1.8.0.7.ru.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 3464 | "C:\Users\admin\AppData\Local\Temp\GetVideoSetup_v1.8.0.7.ru.exe" /UAC:4013C /NCRC | C:\Users\admin\AppData\Local\Temp\GetVideoSetup_v1.8.0.7.ru.exe | GetVideoSetup_v1.8.0.7.ru.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 1223 Modules
| |||||||||||||||
Total events
1 684
Read events
1 517
Write events
166
Delete events
1
Modification events
| (PID) Process: | (3464) GetVideoSetup_v1.8.0.7.ru.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Uninstall\GetVideo |
| Operation: | write | Name: | DisplayName |
Value: GetVideo | |||
| (PID) Process: | (3464) GetVideoSetup_v1.8.0.7.ru.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Uninstall\GetVideo |
| Operation: | write | Name: | UninstallString |
Value: C:\Users\admin\AppData\Local\GetVideo\Удаление (Uninstall).exe | |||
| (PID) Process: | (3464) GetVideoSetup_v1.8.0.7.ru.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Uninstall\GetVideo |
| Operation: | write | Name: | DisplayIcon |
Value: C:\Users\admin\AppData\Local\GetVideo\logo-128.ico | |||
| (PID) Process: | (3464) GetVideoSetup_v1.8.0.7.ru.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Uninstall\GetVideo |
| Operation: | write | Name: | Publisher |
Value: Online Center ltd | |||
| (PID) Process: | (3464) GetVideoSetup_v1.8.0.7.ru.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Run |
| Operation: | write | Name: | GetVideo |
Value: C:\Users\admin\AppData\Local\GetVideo\GetVideo.exe -h | |||
| (PID) Process: | (3464) GetVideoSetup_v1.8.0.7.ru.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\GetVideo |
| Operation: | write | Name: | InstallID |
Value: {36E9ED40-BD83-44F8-B564-DECD057E4138} | |||
| (PID) Process: | (3464) GetVideoSetup_v1.8.0.7.ru.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Shell Extensions\Cached |
| Operation: | write | Name: | {17FE9752-0B5A-4665-84CD-569794602F5C} {7F9185B0-CB92-43C5-80A9-92277A4F7B54} 0xFFFF |
Value: 01000000000000000083B40C5317D701 | |||
| (PID) Process: | (3464) GetVideoSetup_v1.8.0.7.ru.exe | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Control\Session Manager |
| Operation: | write | Name: | PendingFileRenameOperations |
Value: \??\C:\Users\admin\AppData\Local\Temp\nse851B.tmp\registry.dll | |||
| (PID) Process: | (2000) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateLowDateTime |
Value: 515187858 | |||
| (PID) Process: | (2000) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateHighDateTime |
Value: 30873427 | |||
Executable files
17
Suspicious files
36
Text files
186
Unknown types
19
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3464 | GetVideoSetup_v1.8.0.7.ru.exe | C:\Users\admin\AppData\Local\Temp\nse851B.tmp\modern-header.bmp | image | |
MD5:— | SHA256:— | |||
| 3464 | GetVideoSetup_v1.8.0.7.ru.exe | C:\Users\admin\AppData\Local\Temp\nse851B.tmp\yandexbarpage2.ini | text | |
MD5:— | SHA256:— | |||
| 1624 | GetVideoSetup_v1.8.0.7.ru.exe | C:\Users\admin\AppData\Local\Temp\nsc8171.tmp\downloader.exe | executable | |
MD5:70FE52D099713FD74B6AC07CC5C9703B | SHA256:304318534E2D5D671D90185CFF006716FFE488B3607F11D73CAEA2B58AA759D9 | |||
| 1624 | GetVideoSetup_v1.8.0.7.ru.exe | C:\Users\admin\AppData\Local\Temp\nsc8171.tmp\logo_Yandex_RU_UA_vertical.ico | image | |
MD5:A8C1505AB92AA6C40999984BD88B4C42 | SHA256:5C833846B1205E4ACD2F53C513E7526B99C1950F608C71A943C98BC385ACD32B | |||
| 1624 | GetVideoSetup_v1.8.0.7.ru.exe | C:\Users\admin\AppData\Local\Temp\nsc8171.tmp\yandexbrowsersetup.ico | image | |
MD5:6839E8022C8C1104081348D0510DB061 | SHA256:F366E0FC45225F7858154D0C91AADE7868133E45EB2F829ABC647BE3376FC8FF | |||
| 3464 | GetVideoSetup_v1.8.0.7.ru.exe | C:\Users\admin\AppData\Local\Temp\nse851B.tmp\dotNetFx45_Full_setup.exe | executable | |
MD5:9E8253F0A993E53B4809DBD74B335227 | SHA256:E434828818F81E6E1F5955E84CAEC08662BD154A80B24A71A2EDA530D8B2F66A | |||
| 3464 | GetVideoSetup_v1.8.0.7.ru.exe | C:\Users\admin\AppData\Local\Temp\nse851B.tmp\nsResize.dll | executable | |
MD5:A8655E0CA9E079EDC631838273AFC087 | SHA256:EEB2705599C3075E652762E74C88D3CB482E01AD8CAE65F02022F91AEBF13CB5 | |||
| 3464 | GetVideoSetup_v1.8.0.7.ru.exe | C:\Users\admin\AppData\Local\Temp\nse851B.tmp\yandexbrowsersetup.ico | image | |
MD5:6839E8022C8C1104081348D0510DB061 | SHA256:F366E0FC45225F7858154D0C91AADE7868133E45EB2F829ABC647BE3376FC8FF | |||
| 3464 | GetVideoSetup_v1.8.0.7.ru.exe | C:\Users\admin\AppData\Local\Temp\nse851B.tmp\UAC.dll | executable | |
MD5:ADB29E6B186DAA765DC750128649B63D | SHA256:2F7F8FC05DC4FD0D5CDA501B47E4433357E887BBFED7292C028D99C73B52DC08 | |||
| 1624 | GetVideoSetup_v1.8.0.7.ru.exe | C:\Users\admin\AppData\Local\Temp\nsc8171.tmp\UAC.dll | executable | |
MD5:ADB29E6B186DAA765DC750128649B63D | SHA256:2F7F8FC05DC4FD0D5CDA501B47E4433357E887BBFED7292C028D99C73B52DC08 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
24
TCP/UDP connections
55
DNS requests
27
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
752 | GetVideo.exe | GET | 302 | 178.162.205.104:80 | http://api.getvideo.org/windows/get-supported-services | DE | — | — | unknown |
752 | GetVideo.exe | GET | 200 | 195.201.85.230:80 | http://s5230.getvideo.org/windows/get-supported-services?country=RU&token=f0b23cdc72847cdcad9c20c6fab97683 | RU | text | 140 b | unknown |
752 | GetVideo.exe | GET | 404 | 172.217.16.148:80 | http://proxer-1336.appspot.com/getvideo-win-ru-5?id=L9DE5RXY60LTHAG7 | US | html | 1.51 Kb | suspicious |
480 | iexplore.exe | GET | 200 | 216.58.211.2:80 | http://www.googleadservices.com/pagead/conversion.js | US | text | 14.9 Kb | whitelisted |
480 | iexplore.exe | GET | 200 | 23.55.163.73:80 | http://crl.identrust.com/DSTROOTCAX3CRL.crl | US | der | 1.16 Kb | whitelisted |
480 | iexplore.exe | GET | 200 | 184.86.103.198:80 | http://subca.ocsp-certum.com/MFIwUDBOMEwwSjAJBgUrDgMCGgUABBR5iK7tYk9tqQEoeQhZNkKcAol9bgQUjEPEy22YwaechGnr30oNYJY6w%2FsCEQCTkoVAAWVxX5R%2FKI%2FvyZso | US | der | 1.58 Kb | whitelisted |
480 | iexplore.exe | GET | 200 | 142.250.186.131:80 | http://ocsp.pki.goog/gts1o1core/MFEwTzBNMEswSTAJBgUrDgMCGgUABBRCRjDCJxnb3nDwj%2Fxz5aZfZjgXvAQUmNH4bhDrz5vsYJ8YkBug630J%2FSsCEECx%2Fl4bakX1AwAAAADLnko%3D | US | der | 471 b | whitelisted |
480 | iexplore.exe | GET | 200 | 5.45.205.241:80 | http://yandex.ocsp-responder.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBStniMGfahyWUWDEeSLUFbNR9JLAgQUN1zjGeCyjqGoTtLPq9Dc4wtcNU0CECTuh4yBvsxbK3yLRmtRvuI%3D | RU | der | 1.48 Kb | whitelisted |
480 | iexplore.exe | GET | 200 | 5.45.205.241:80 | http://yandex.ocsp-responder.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBStniMGfahyWUWDEeSLUFbNR9JLAgQUN1zjGeCyjqGoTtLPq9Dc4wtcNU0CEDbEISBuJVGq0KdX46enAhA%3D | RU | der | 1.48 Kb | whitelisted |
480 | iexplore.exe | GET | 200 | 5.45.205.241:80 | http://yandex.ocsp-responder.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBStniMGfahyWUWDEeSLUFbNR9JLAgQUN1zjGeCyjqGoTtLPq9Dc4wtcNU0CECTuh4yBvsxbK3yLRmtRvuI%3D | RU | der | 1.48 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
752 | GetVideo.exe | 142.250.186.180:443 | track4app.appspot.com | Google Inc. | US | suspicious |
480 | iexplore.exe | 144.76.25.173:80 | getvideo.org | Hetzner Online GmbH | DE | malicious |
480 | iexplore.exe | 144.76.25.173:443 | getvideo.org | Hetzner Online GmbH | DE | malicious |
752 | GetVideo.exe | 178.162.205.104:80 | api.getvideo.org | Leaseweb Deutschland GmbH | DE | unknown |
752 | GetVideo.exe | 195.201.85.230:80 | s5230.getvideo.org | Awanti Ltd. | RU | unknown |
752 | GetVideo.exe | 144.76.25.173:80 | getvideo.org | Hetzner Online GmbH | DE | malicious |
752 | GetVideo.exe | 144.76.25.173:443 | getvideo.org | Hetzner Online GmbH | DE | malicious |
— | — | 23.55.163.73:80 | crl.identrust.com | Akamai International B.V. | US | unknown |
— | — | 172.217.16.148:80 | proxer-1336.appspot.com | Google Inc. | US | suspicious |
— | — | 144.76.25.173:443 | getvideo.org | Hetzner Online GmbH | DE | malicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
getvideo.org |
| whitelisted |
track4app.appspot.com |
| suspicious |
api.getvideo.org |
| unknown |
s5230.getvideo.org |
| unknown |
crl.identrust.com |
| whitelisted |
proxer-1336.appspot.com |
| suspicious |
s7.addthis.com |
| whitelisted |
yastatic.net |
| whitelisted |
www.googleadservices.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |