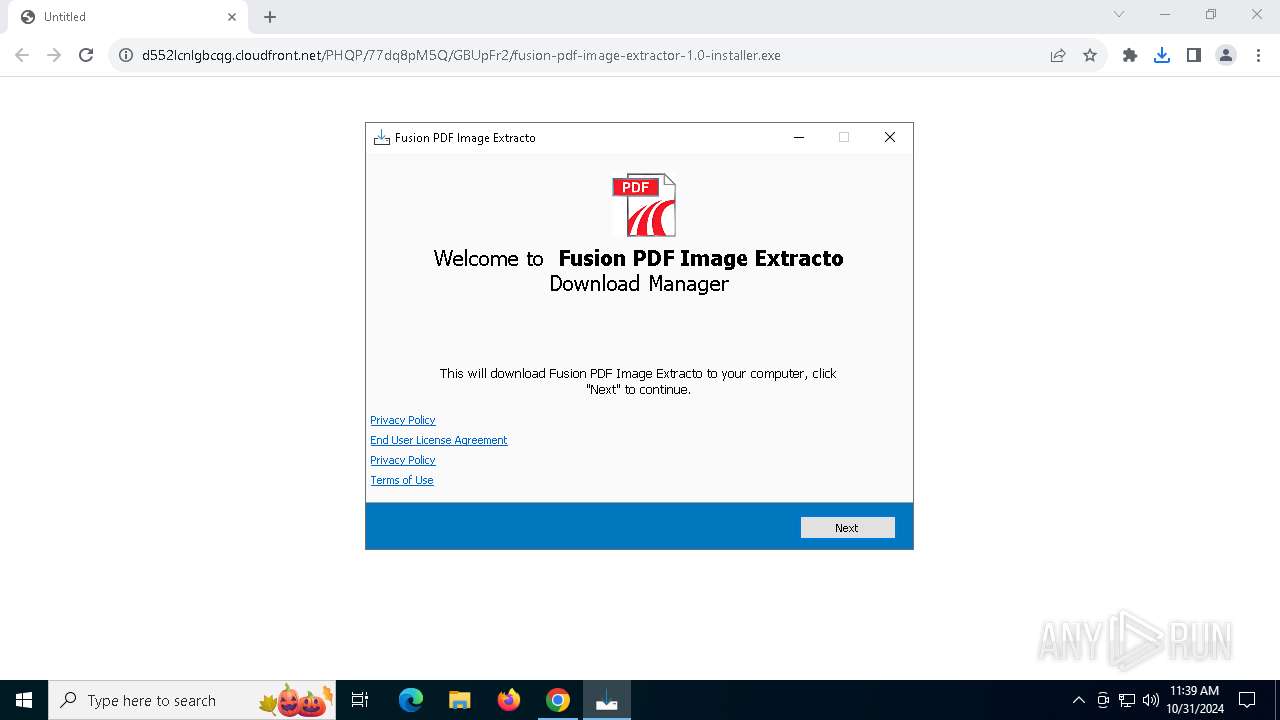
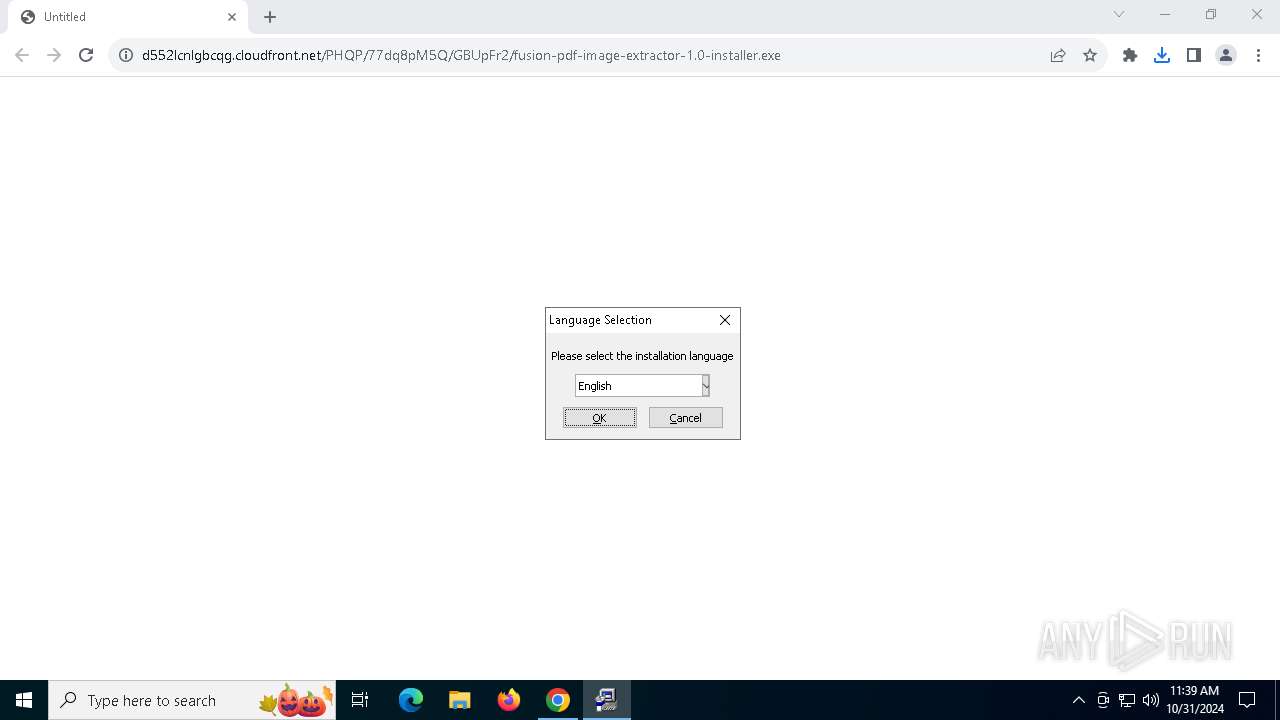
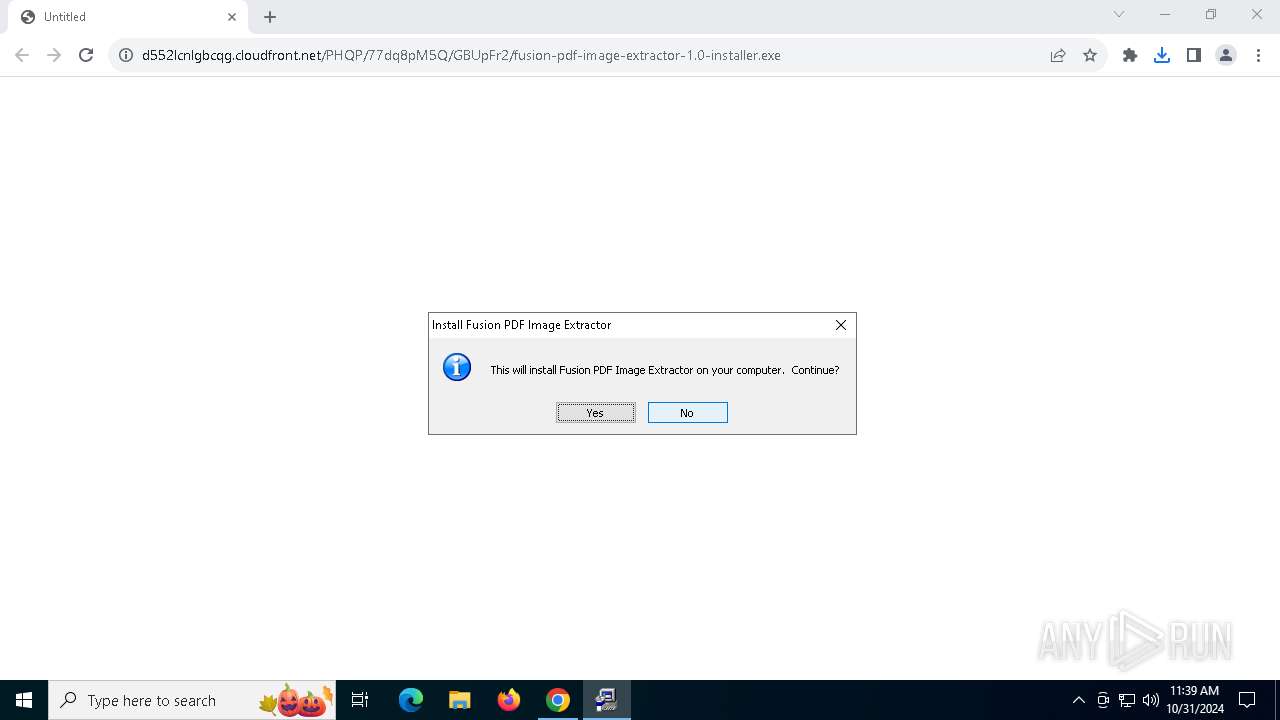
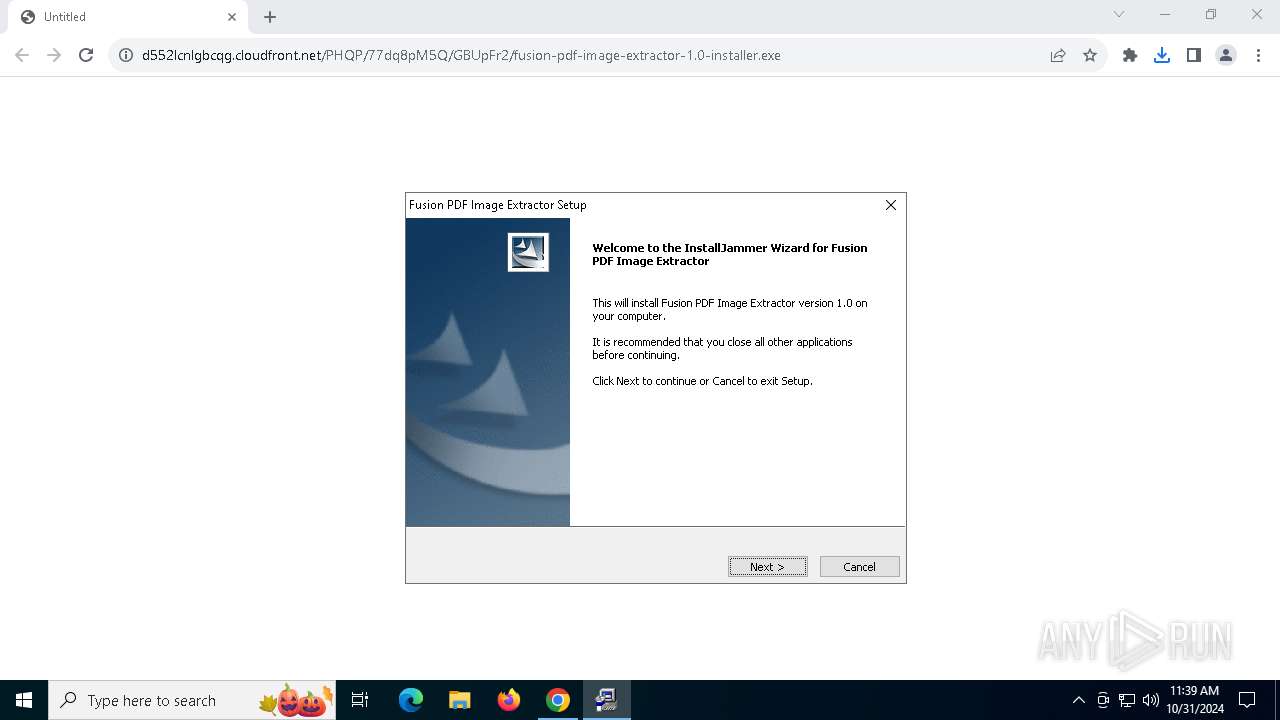
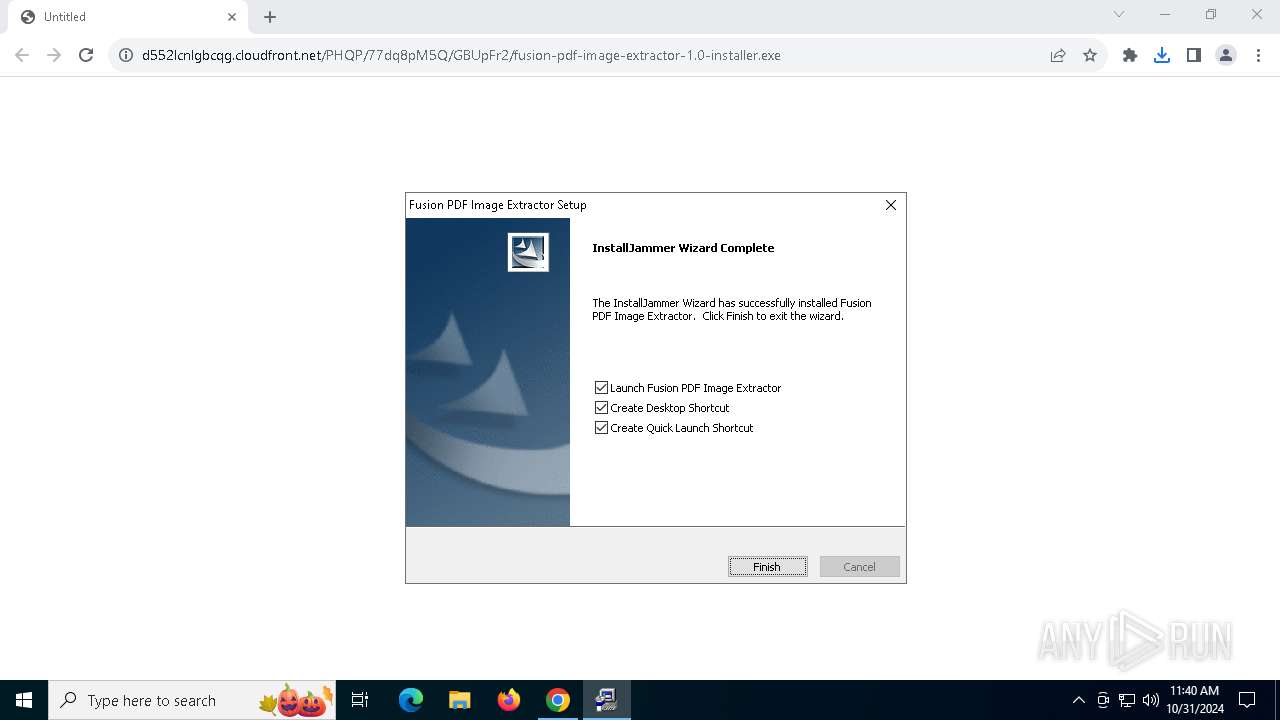
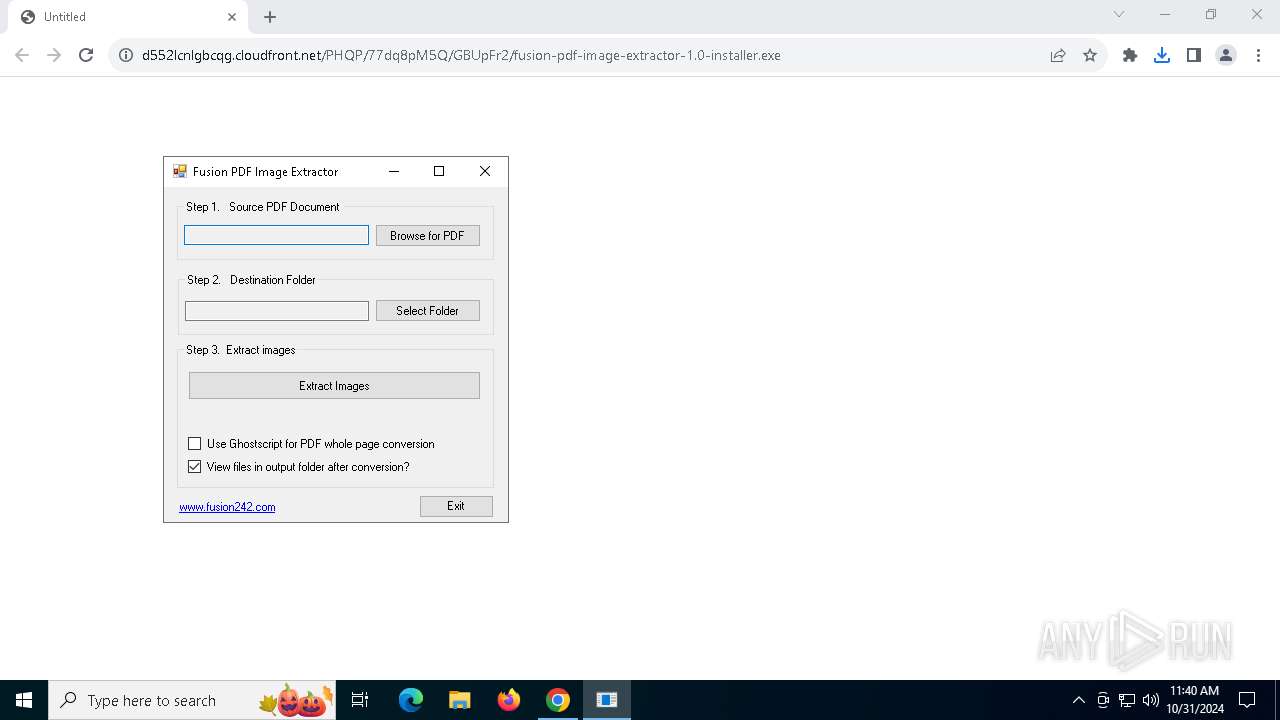
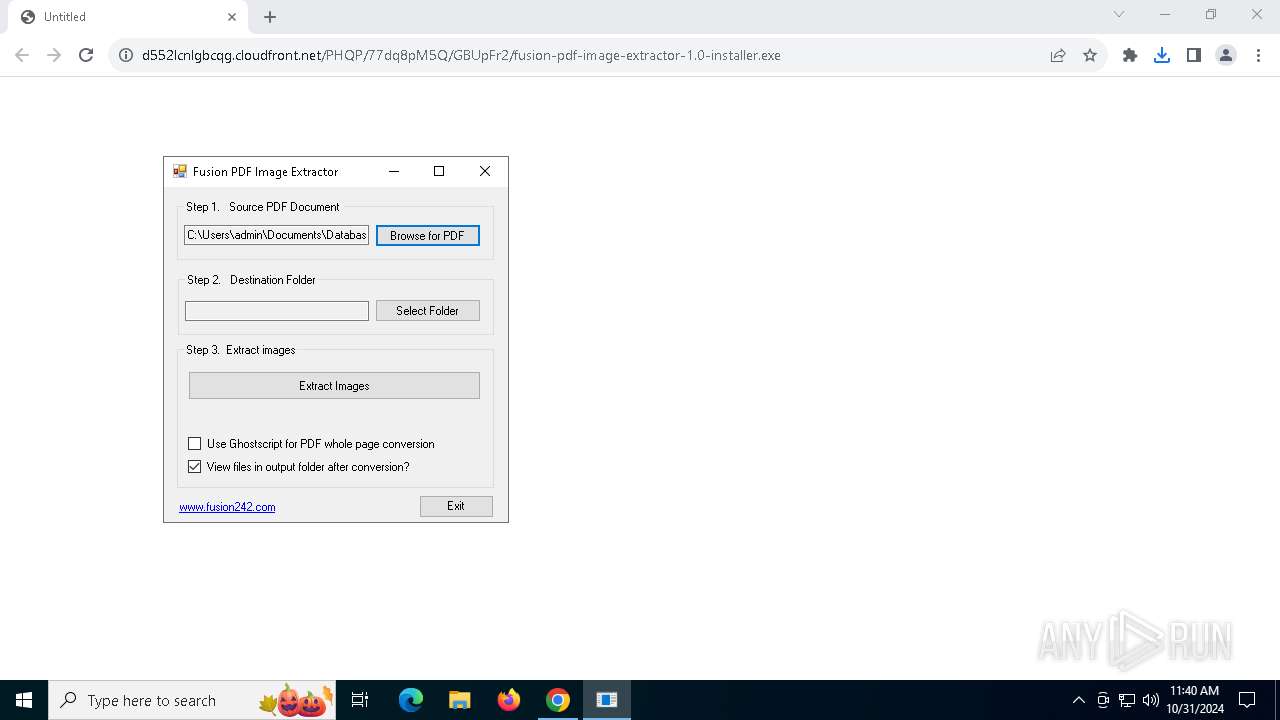
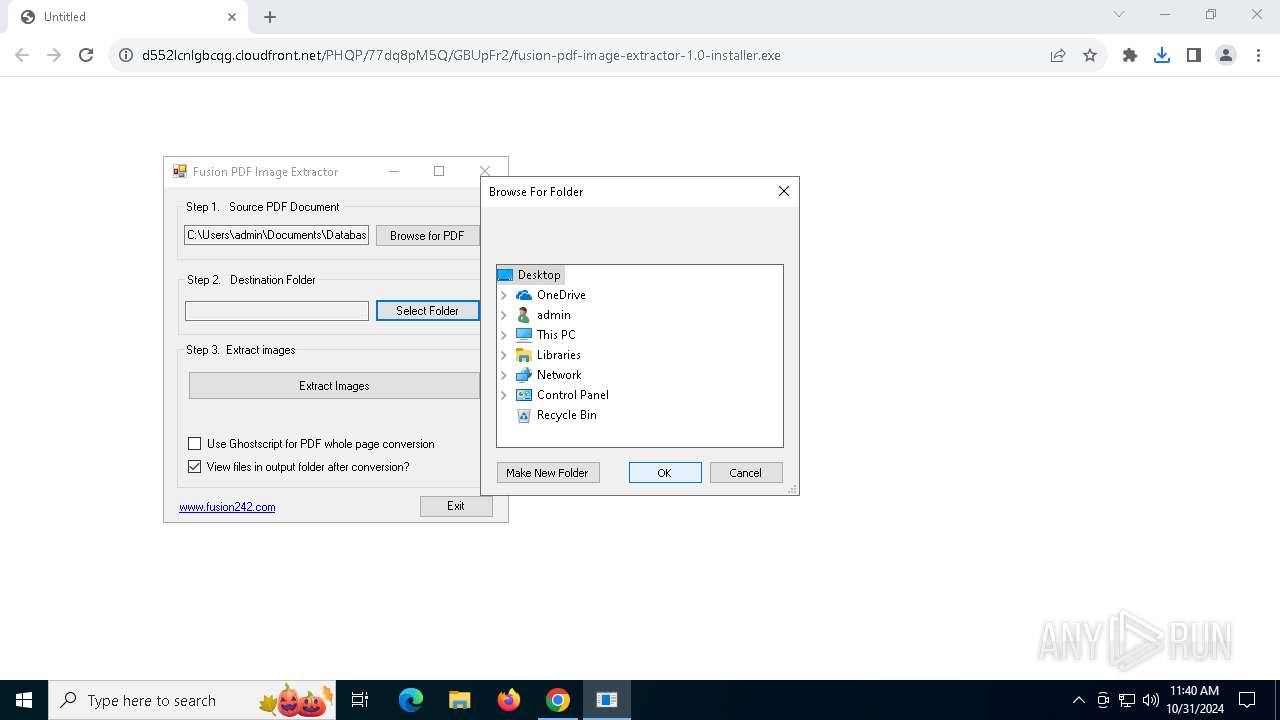
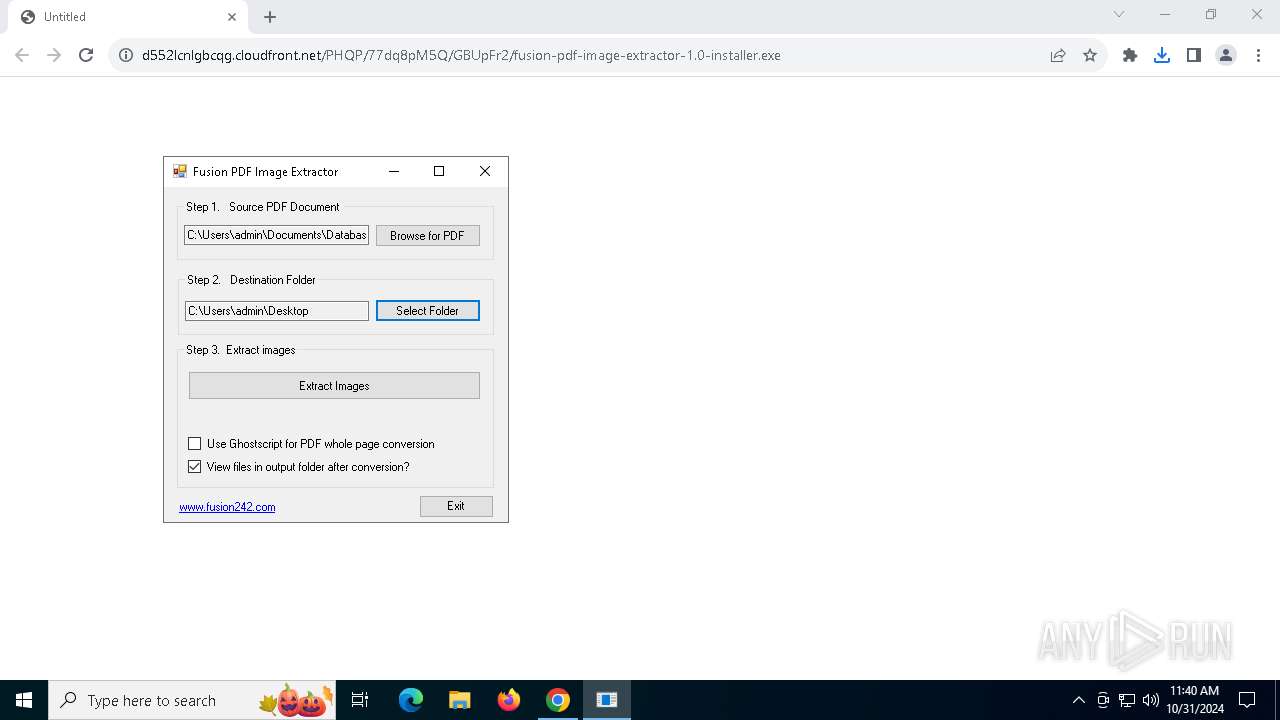
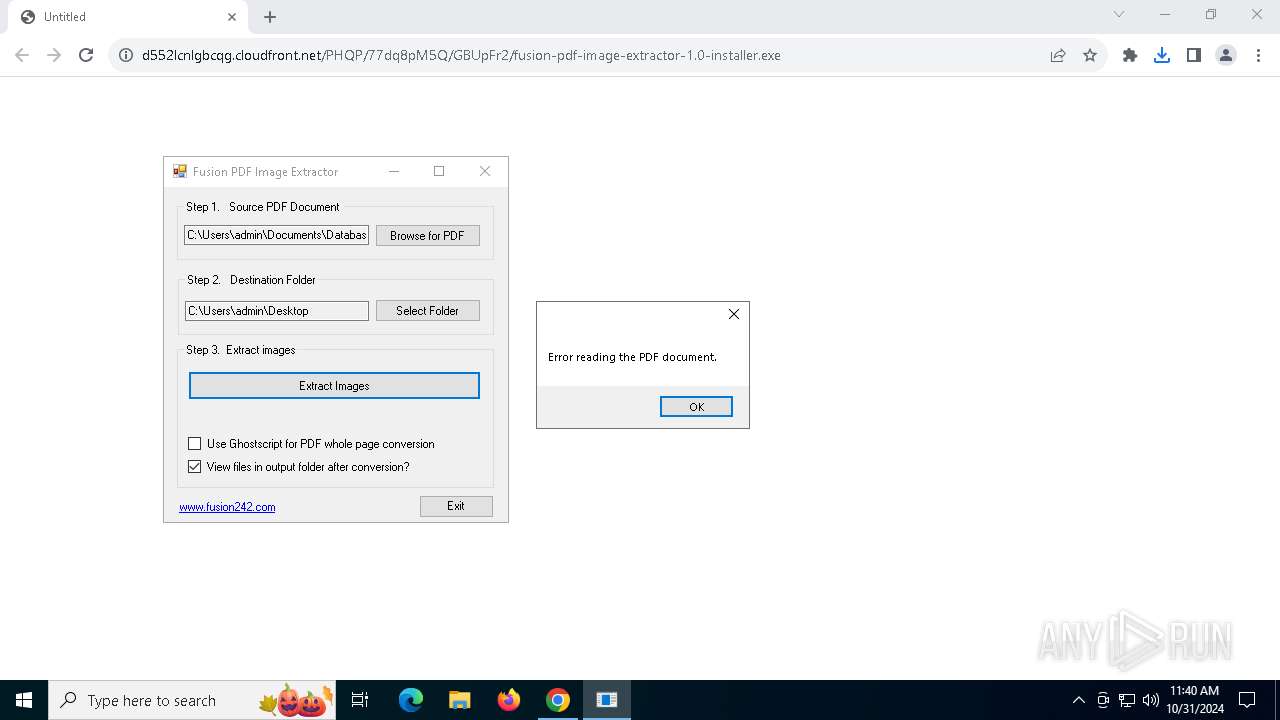
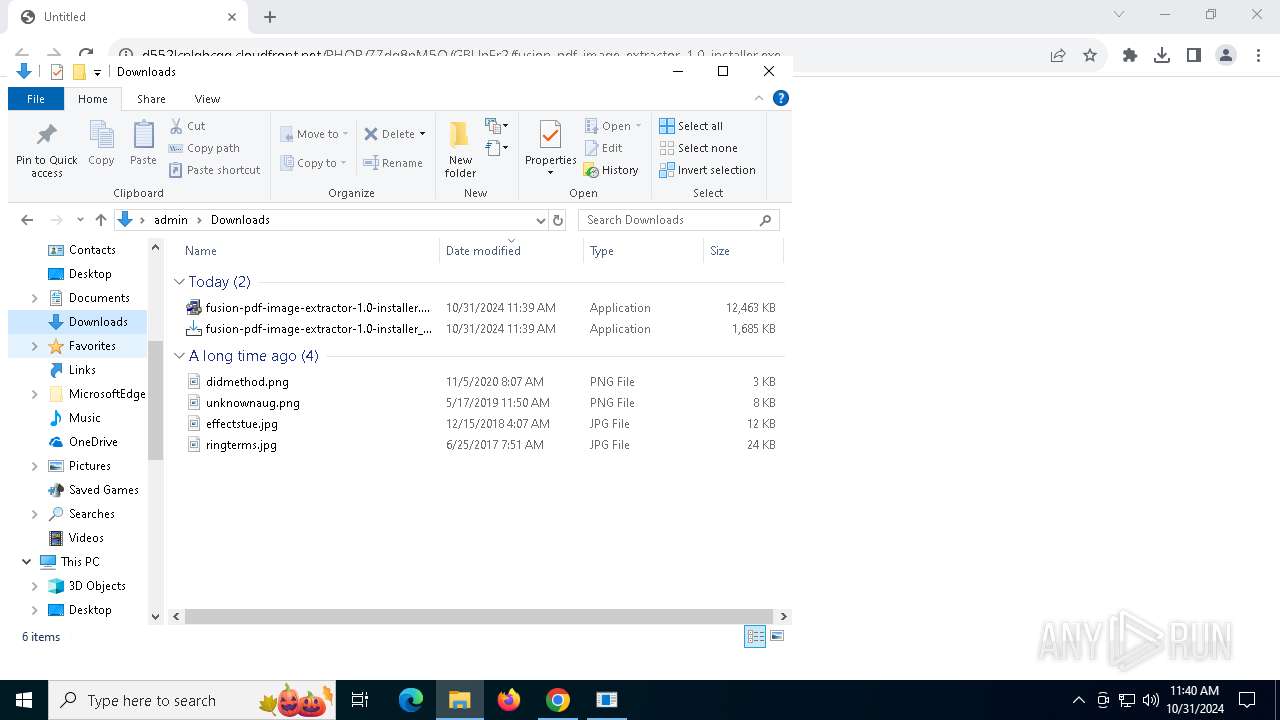
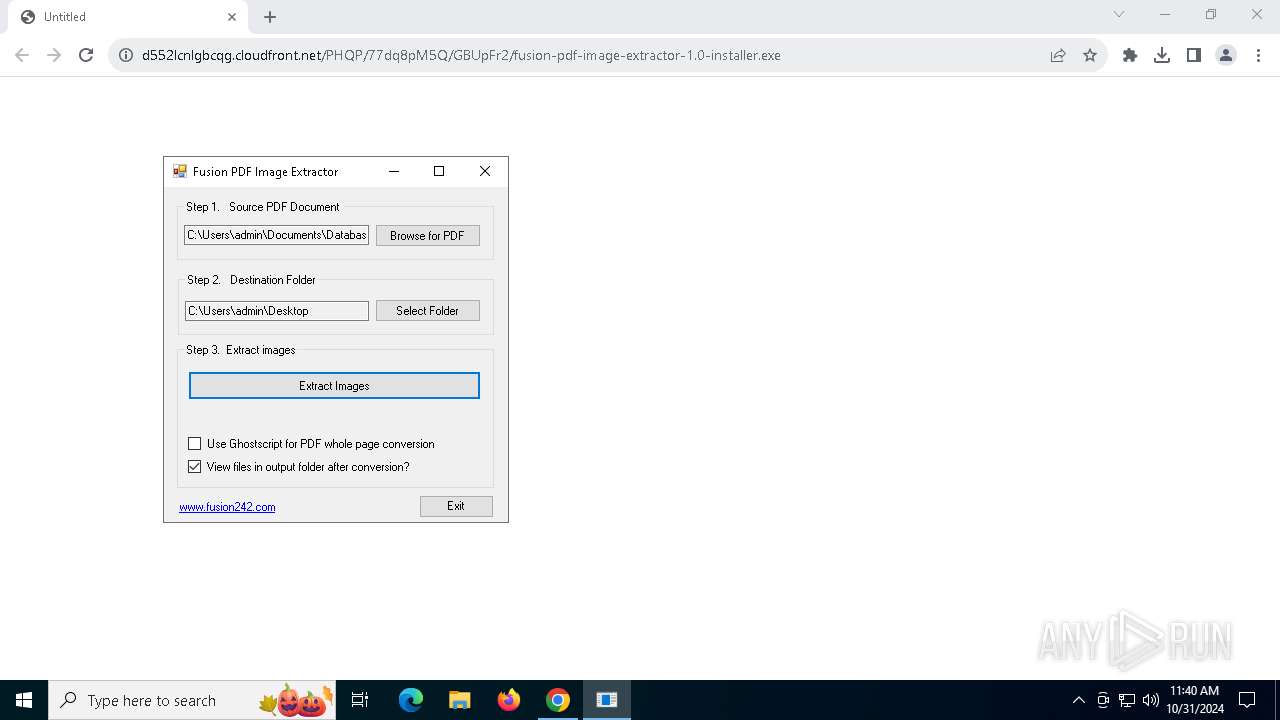
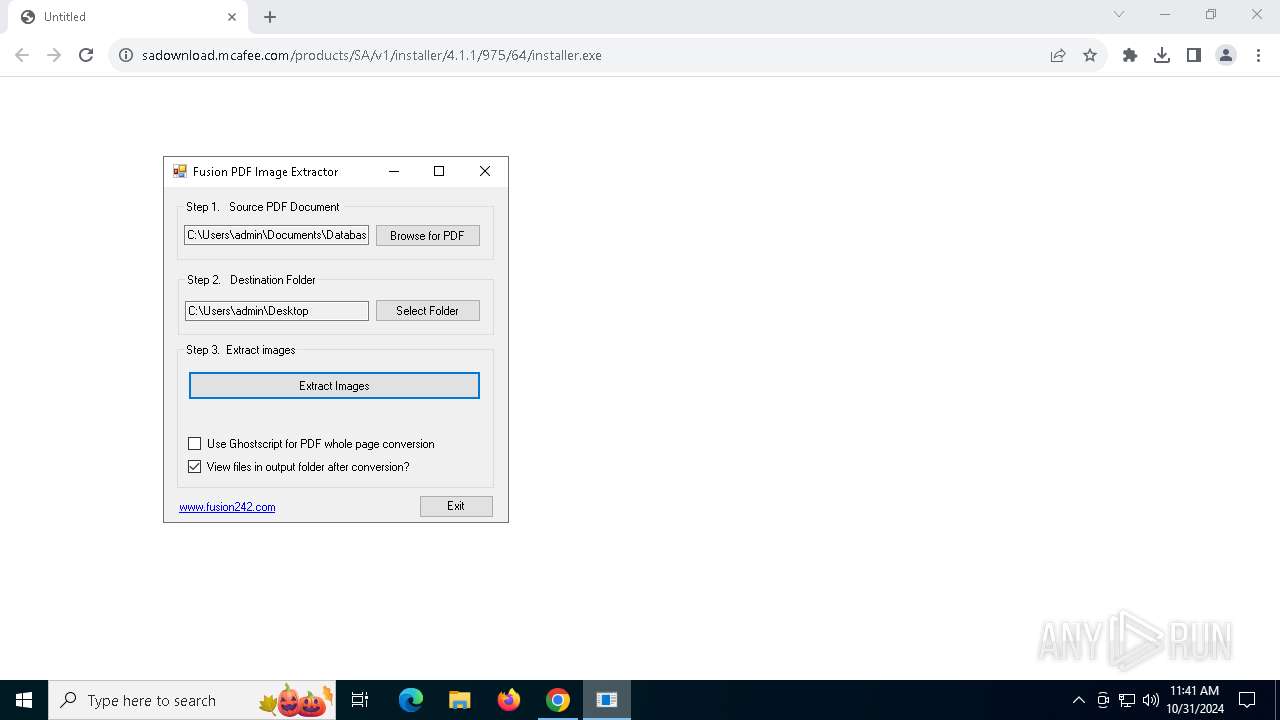
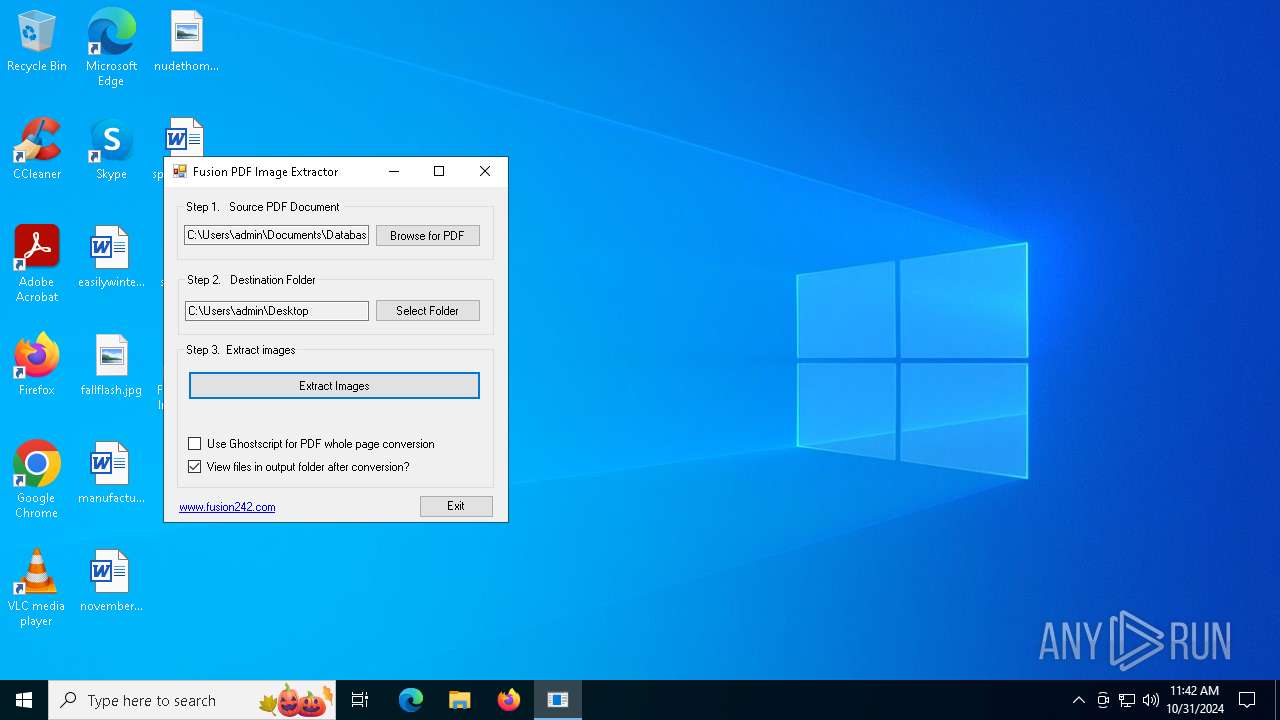
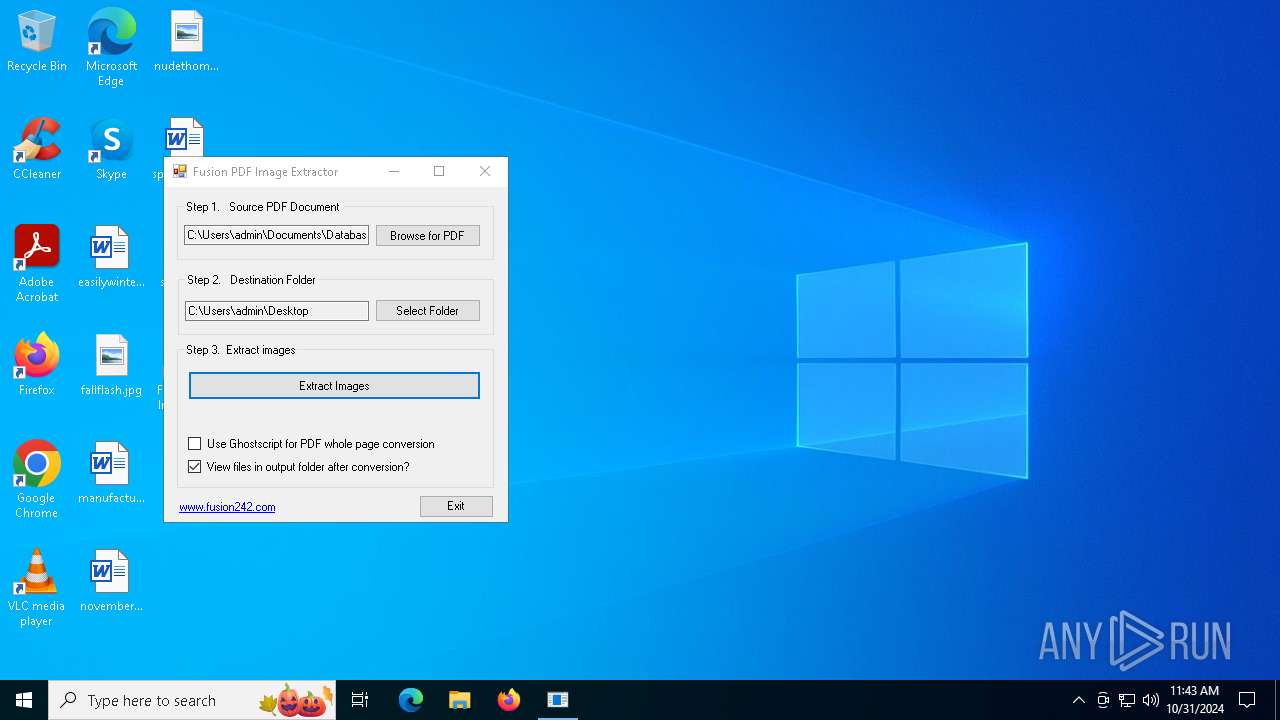
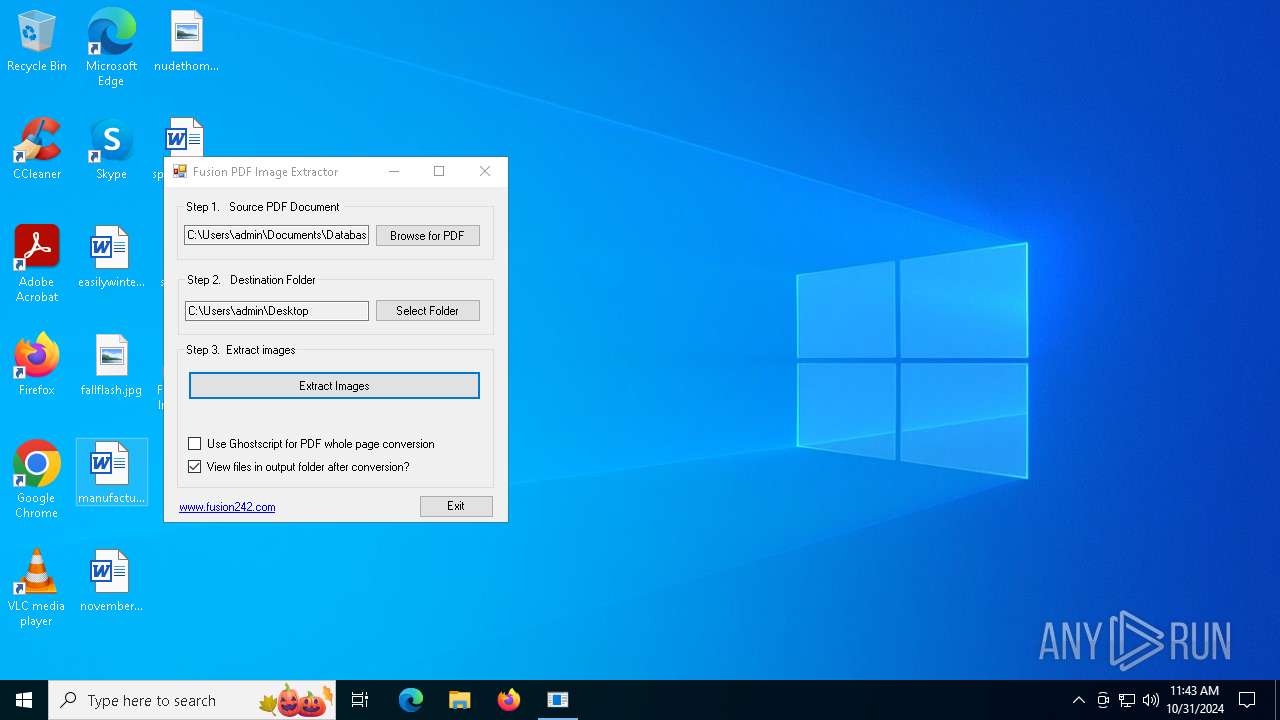
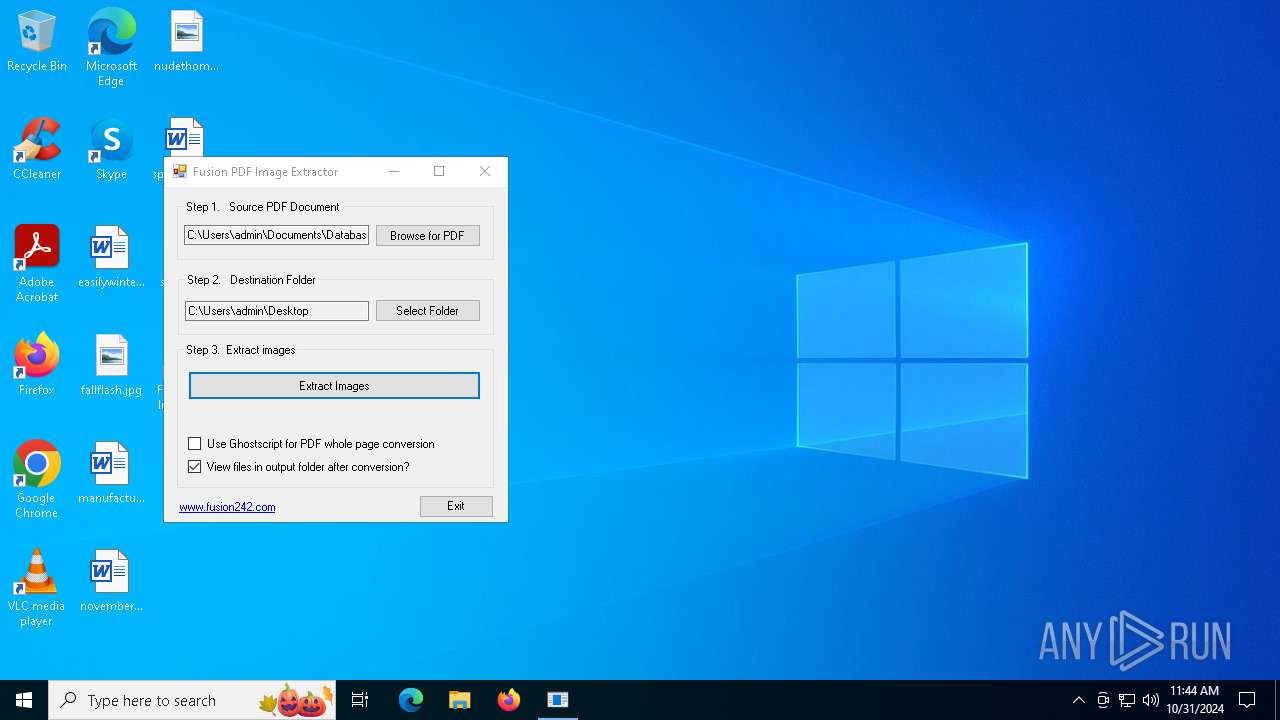
| URL: | https://d552lcnlgbcqg.cloudfront.net/PHQP/77dq8pM5Q/GBUpFr2/fusion-pdf-image-extractor-1.0-installer.exe |
| Full analysis: | https://app.any.run/tasks/f1442df5-d6c9-43e7-a1b4-191fa5e76d26 |
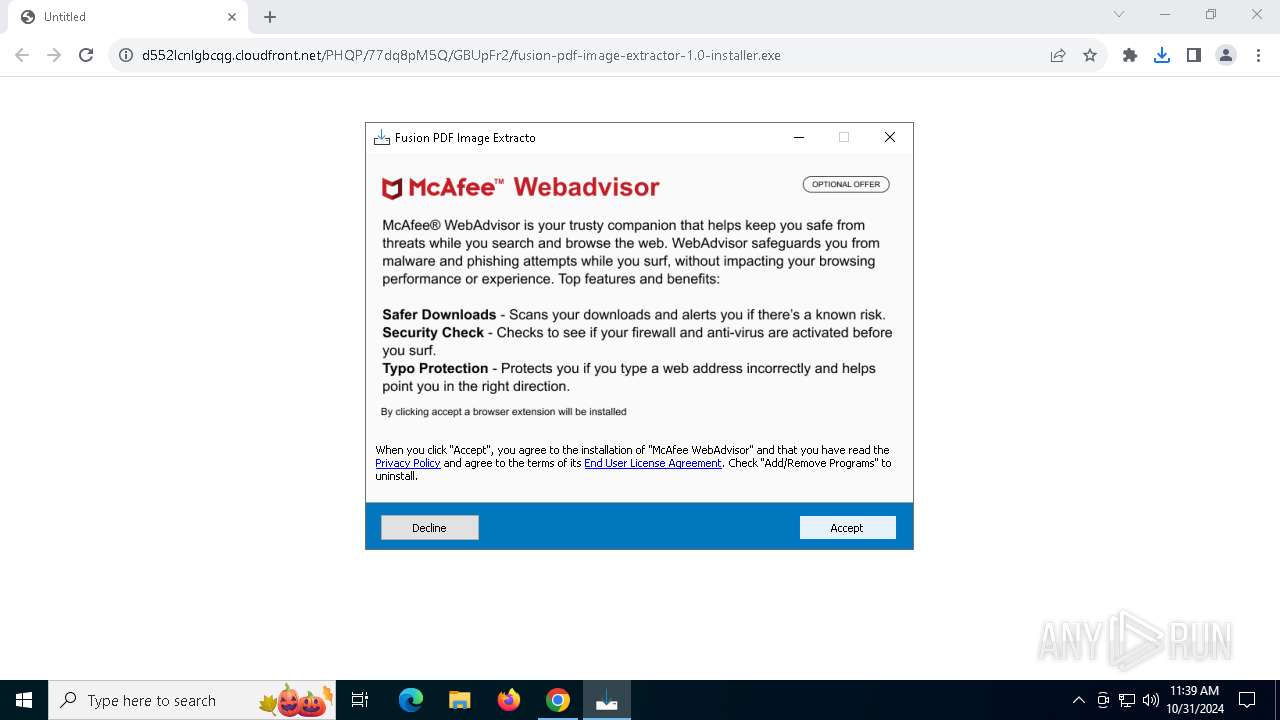
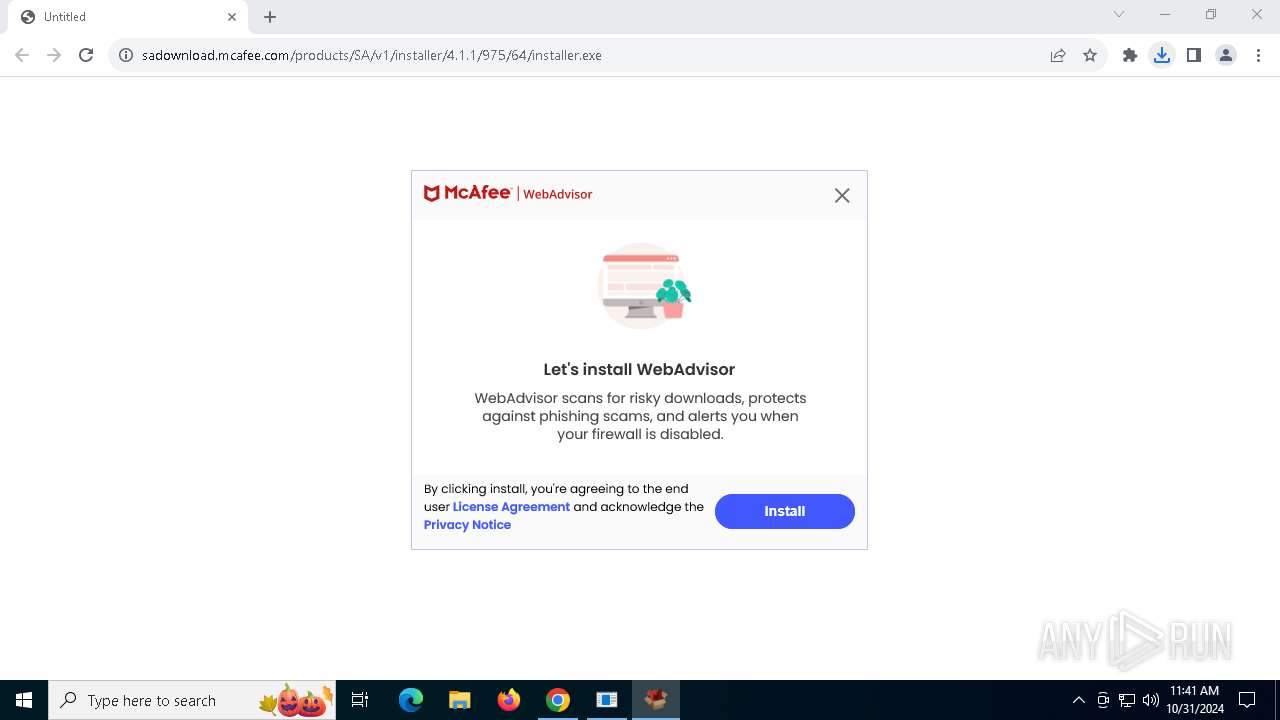
| Verdict: | Malicious activity |
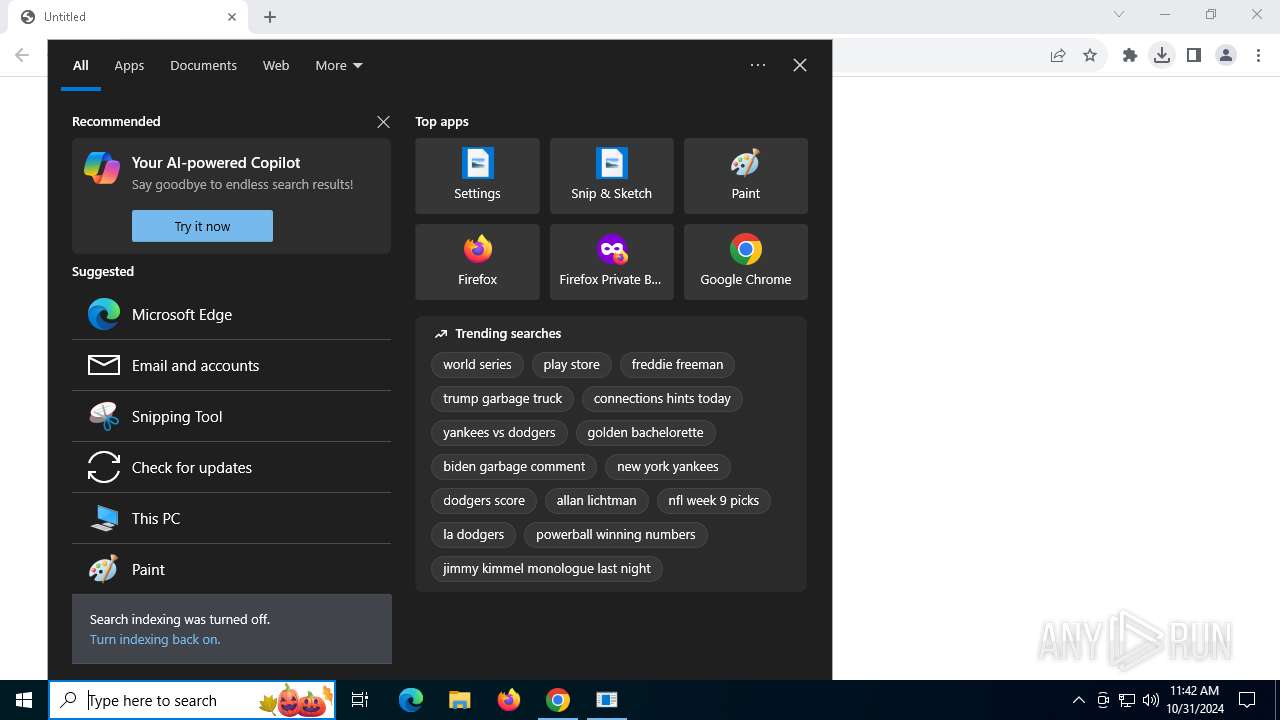
| Analysis date: | October 31, 2024, 11:39:16 |
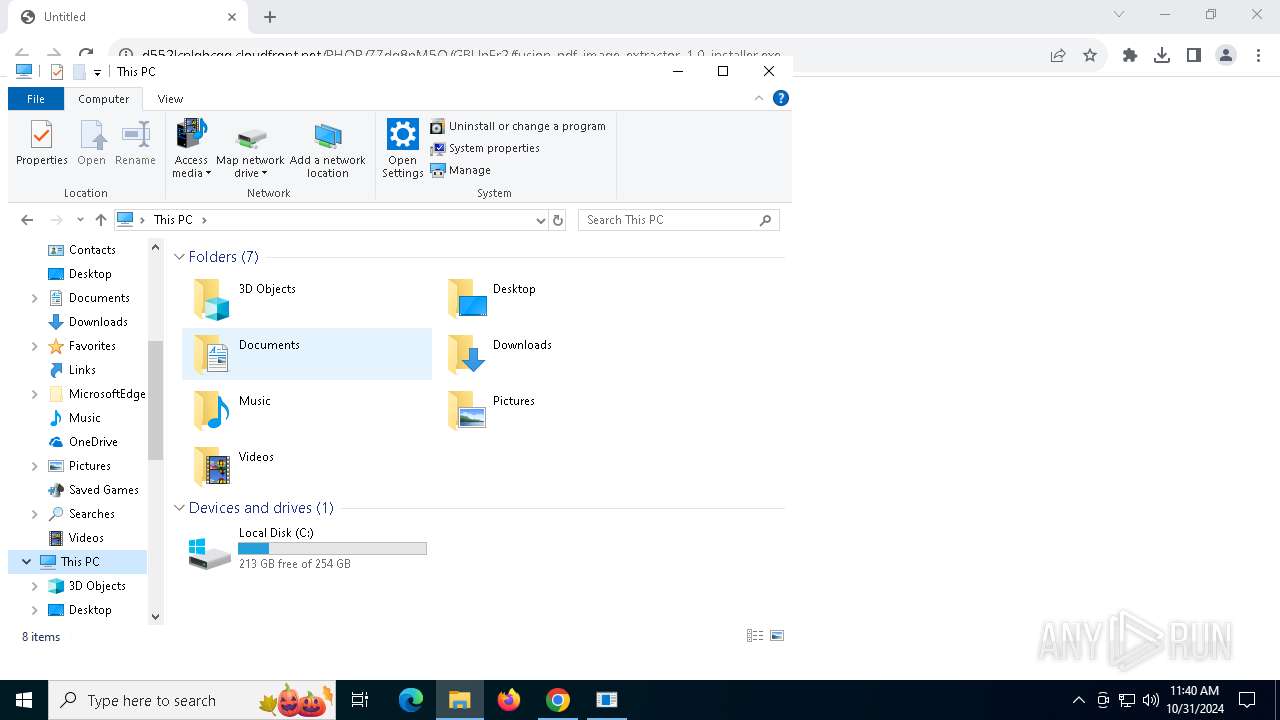
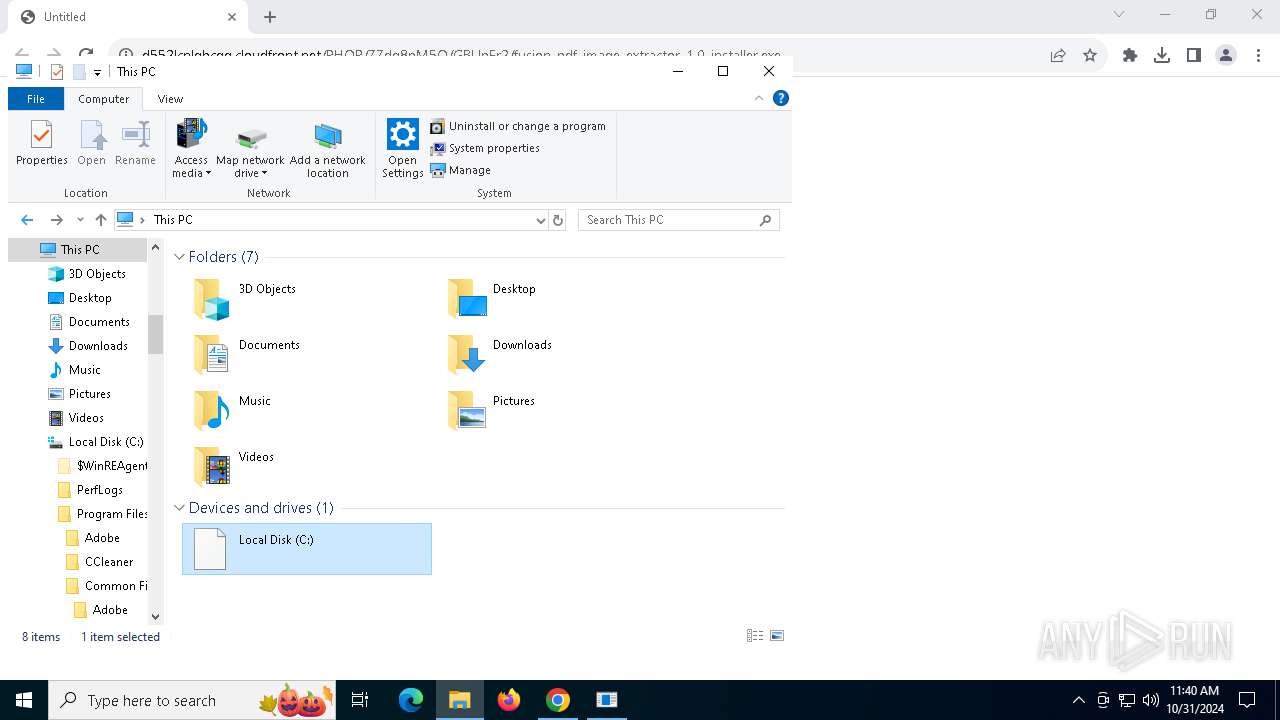
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
| MD5: | 920AA57EA0E1226427E86341CE31284E |
| SHA1: | 7E177316C3AB3FD9969699AEC31F2F919F59514B |
| SHA256: | 651EA3E1D3676356FF8E2CCA12CD92AEAA3DEA41AF9637EDBF8E3684DA8B4DA7 |
| SSDEEP: | 3:N8ICVGeEQB+l/0uG3SidTzrDAL0FOIKWBXLNn:2IkXnX39HrrFlXLN |
MALICIOUS
No malicious indicators.SUSPICIOUS
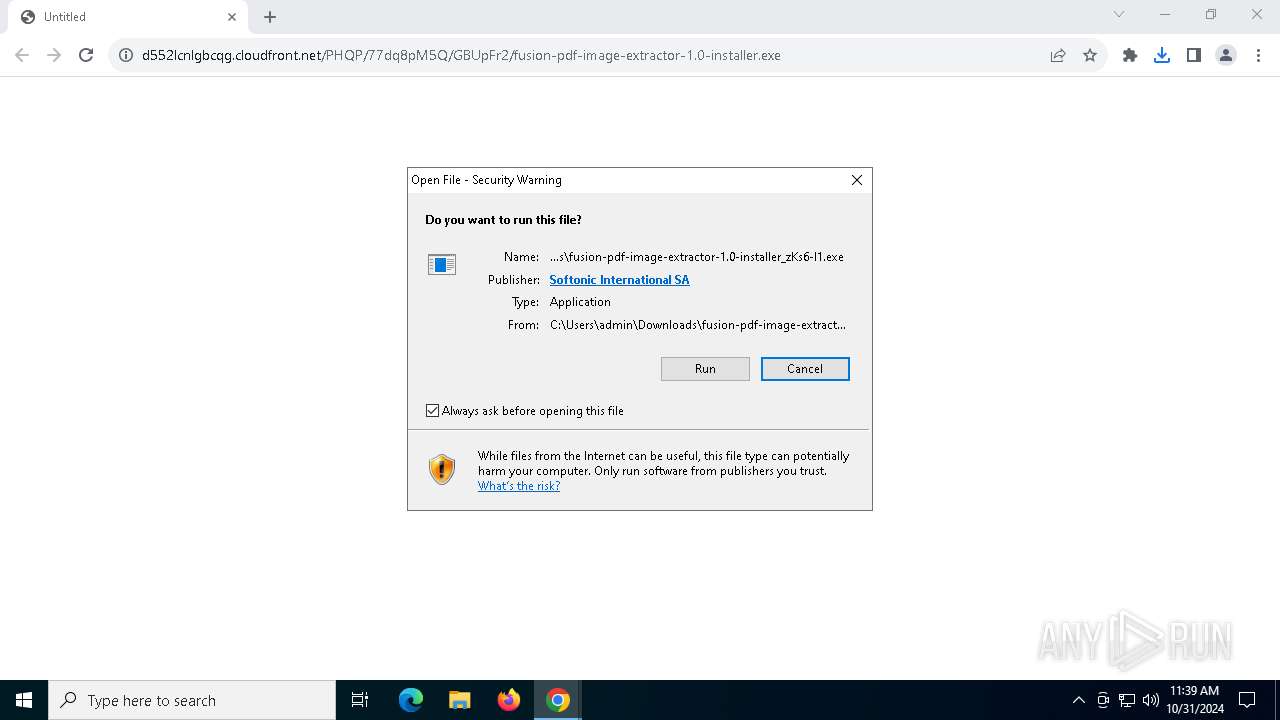
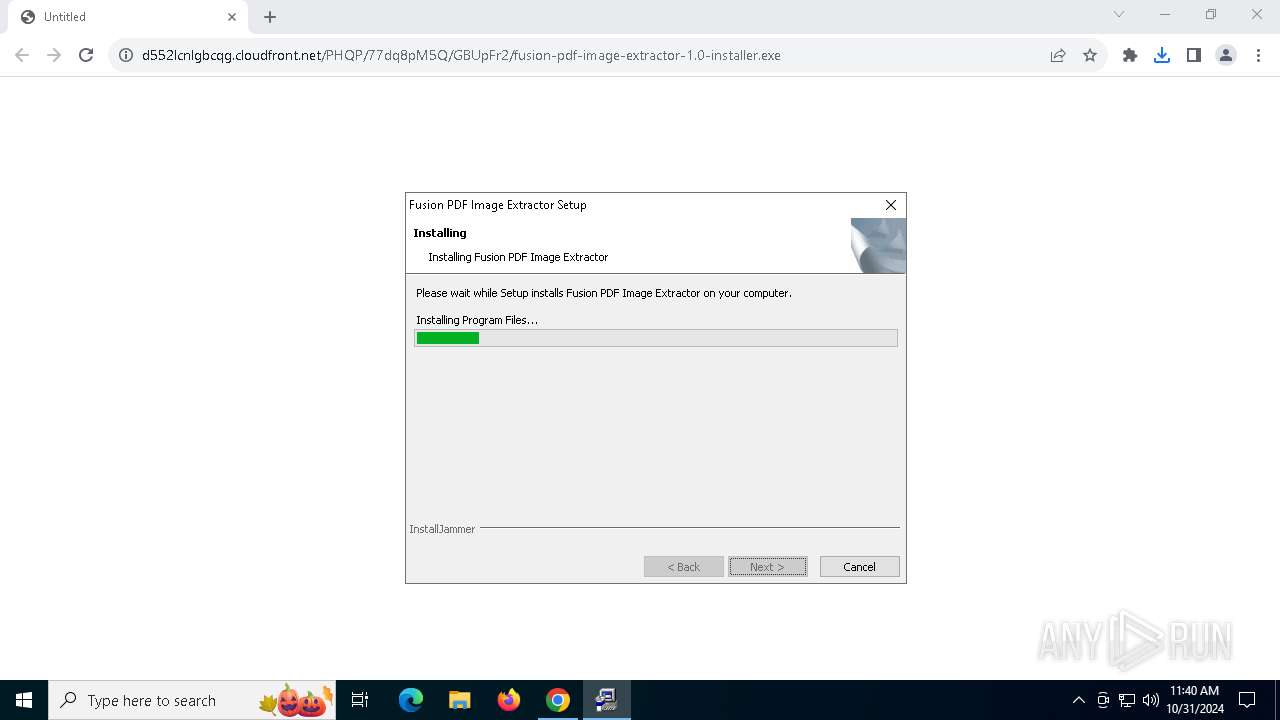
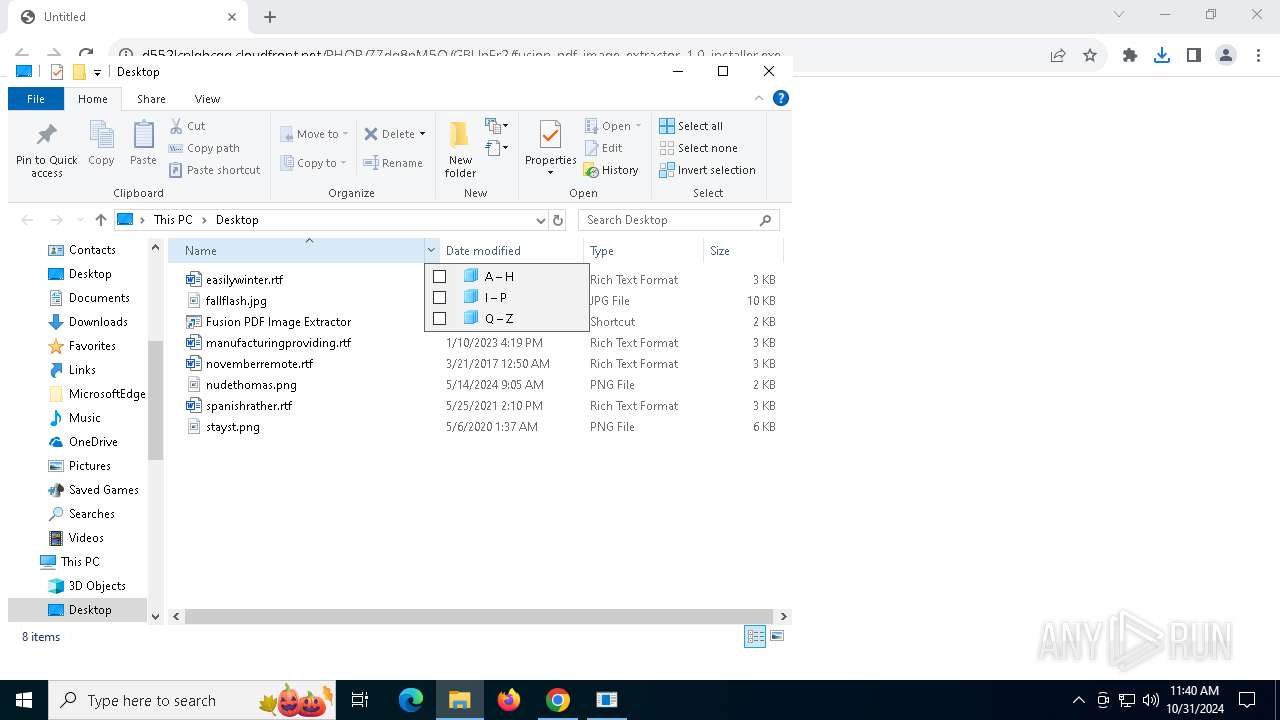
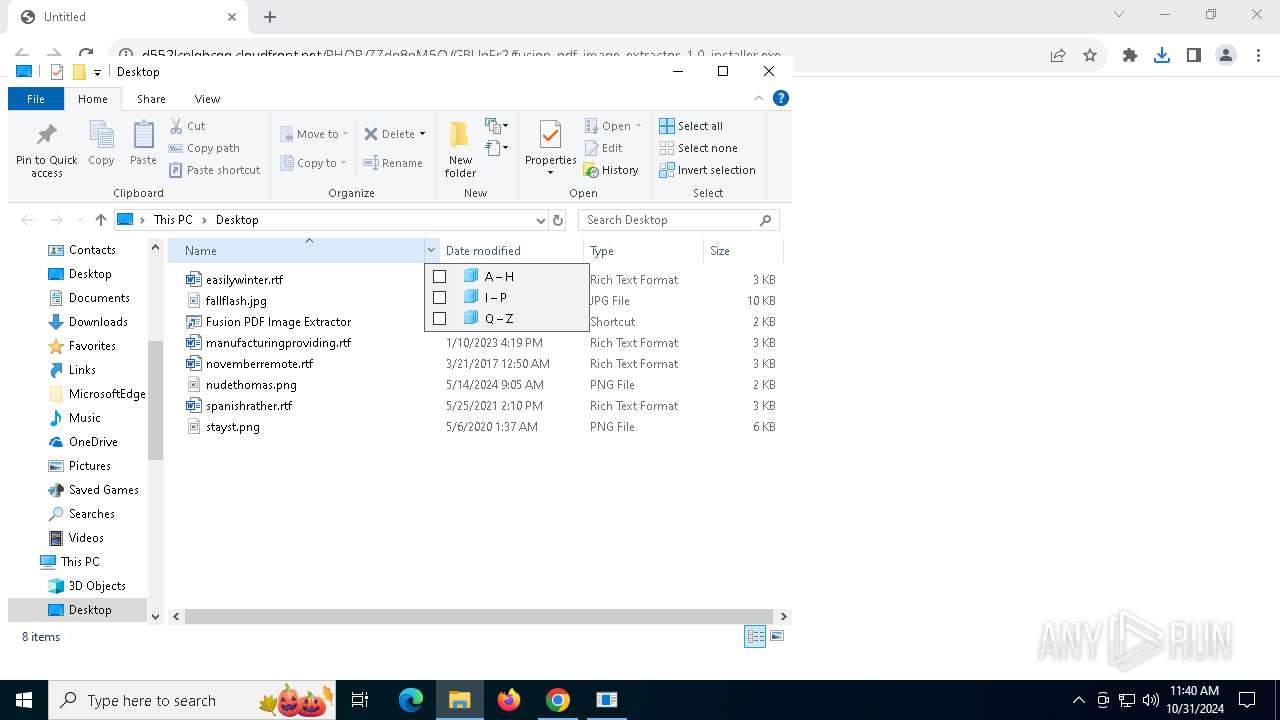
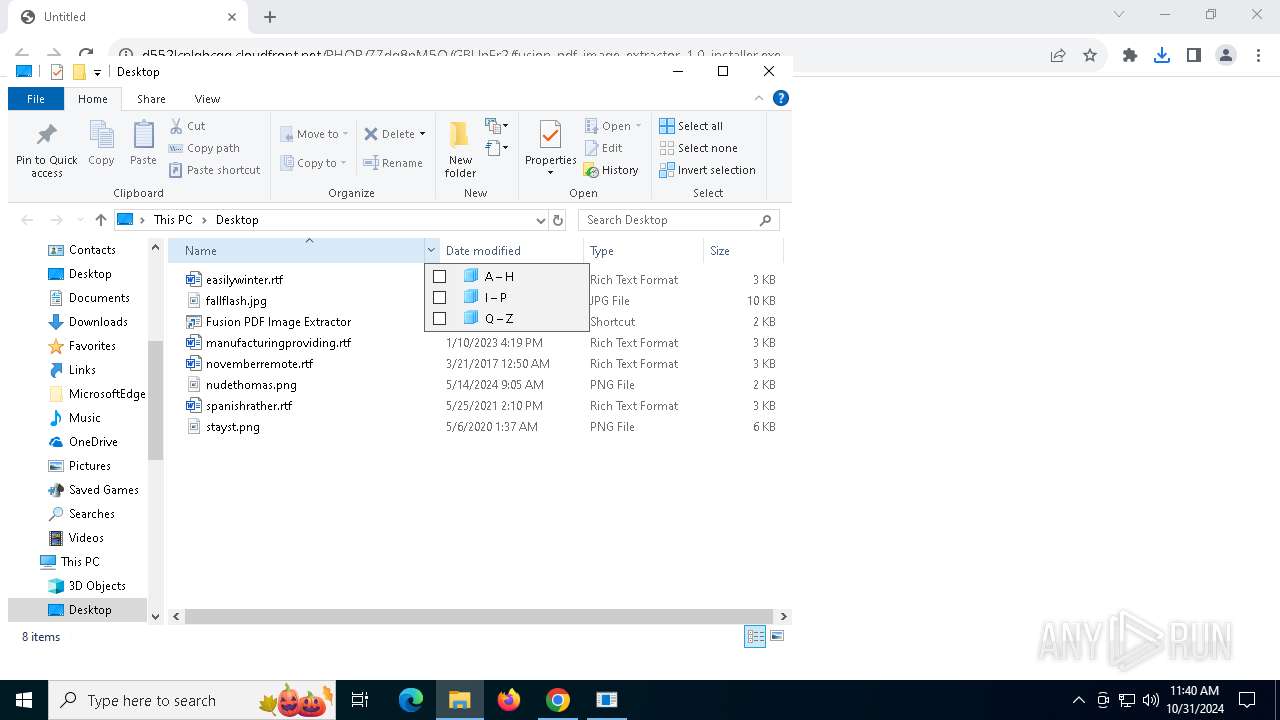
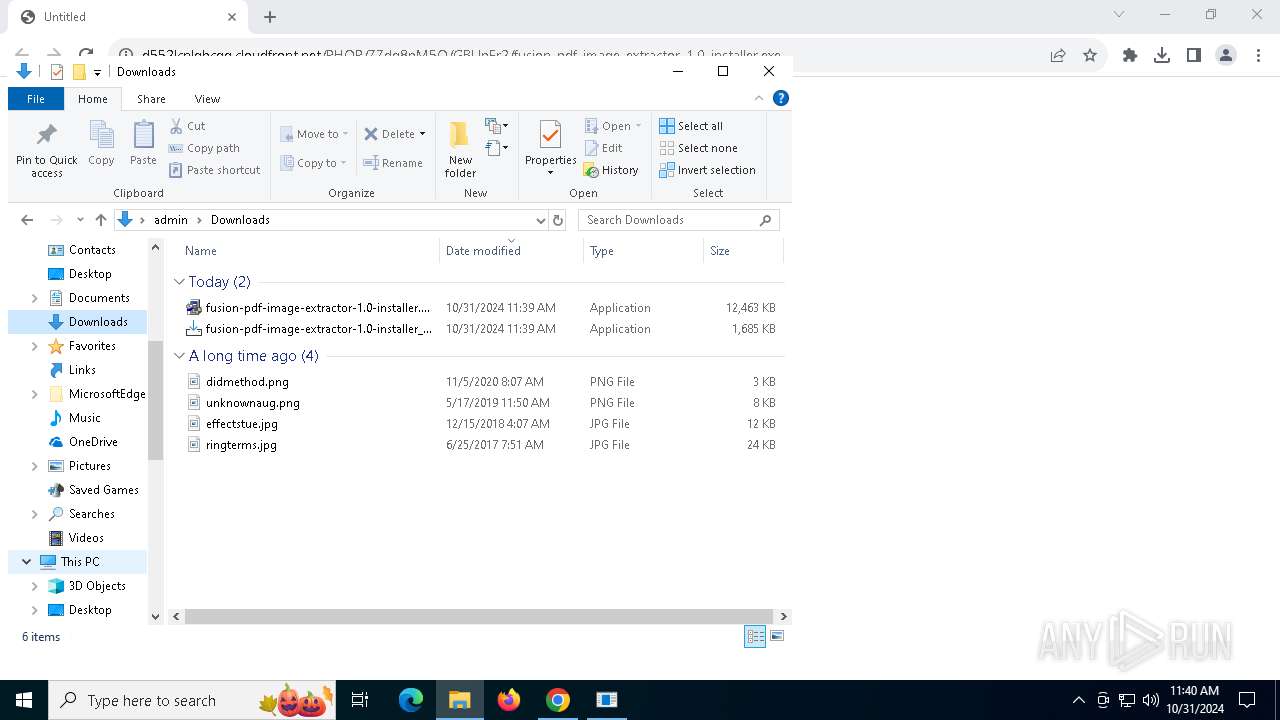
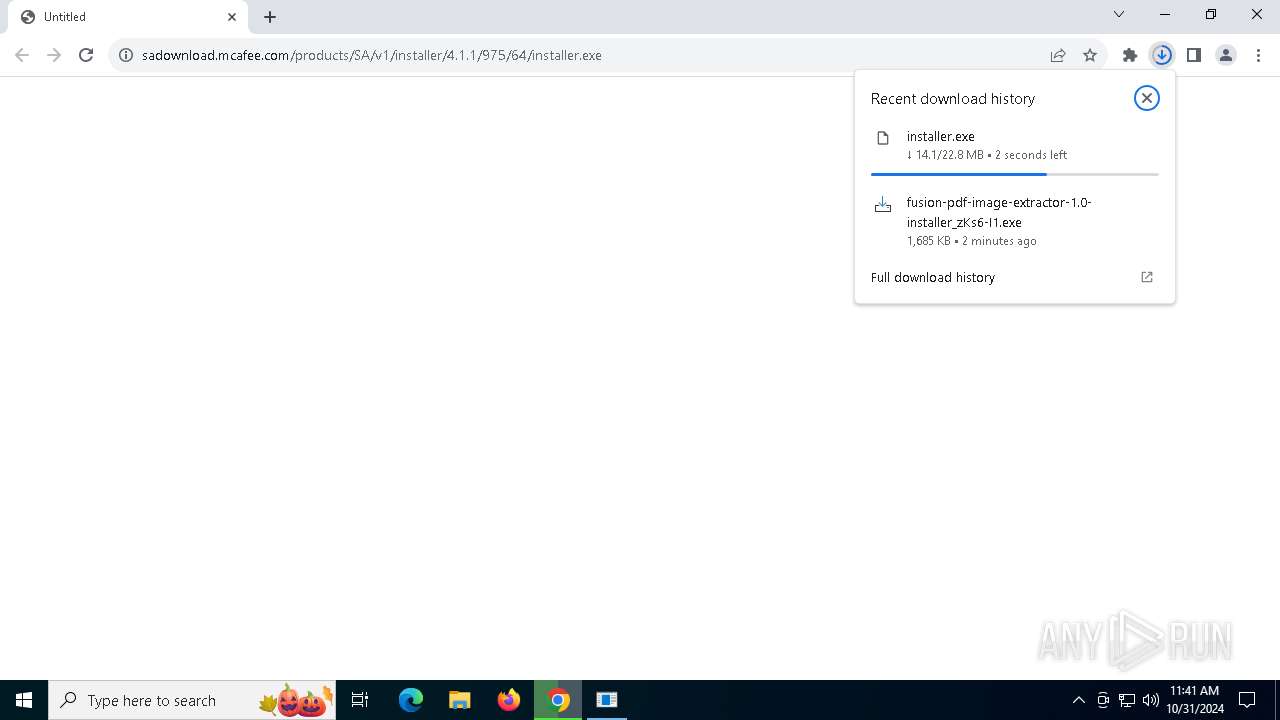
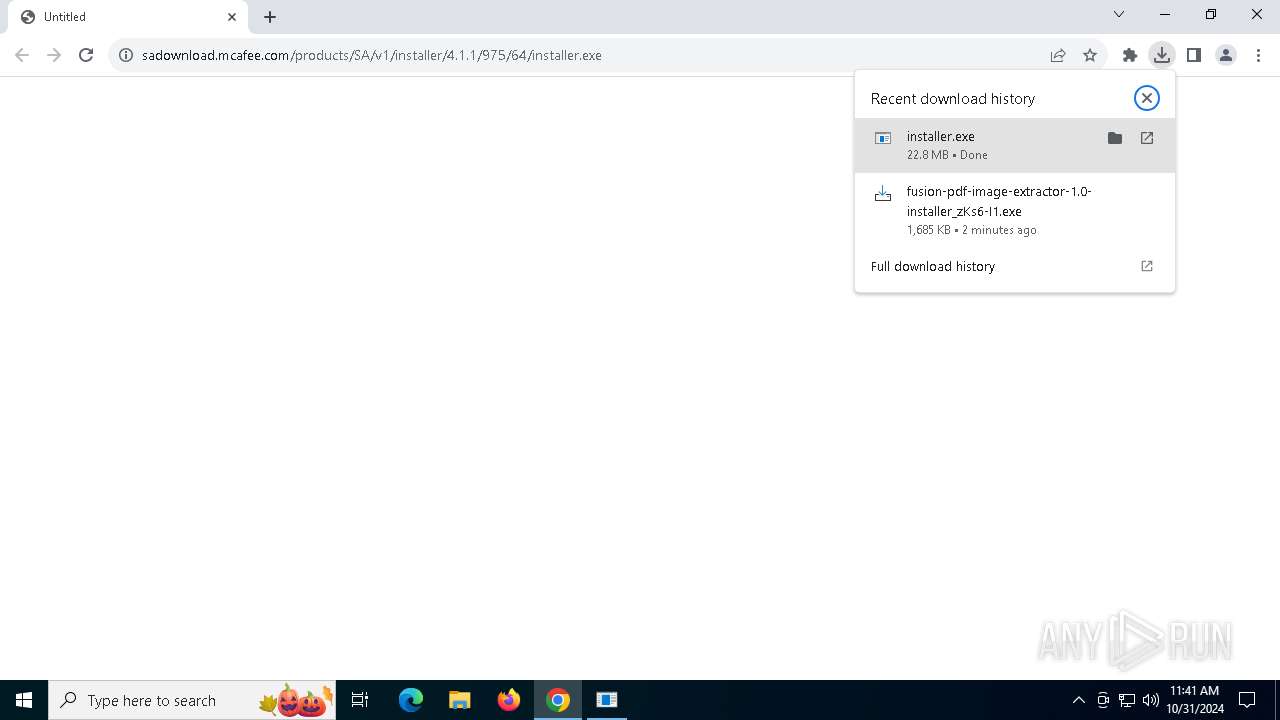
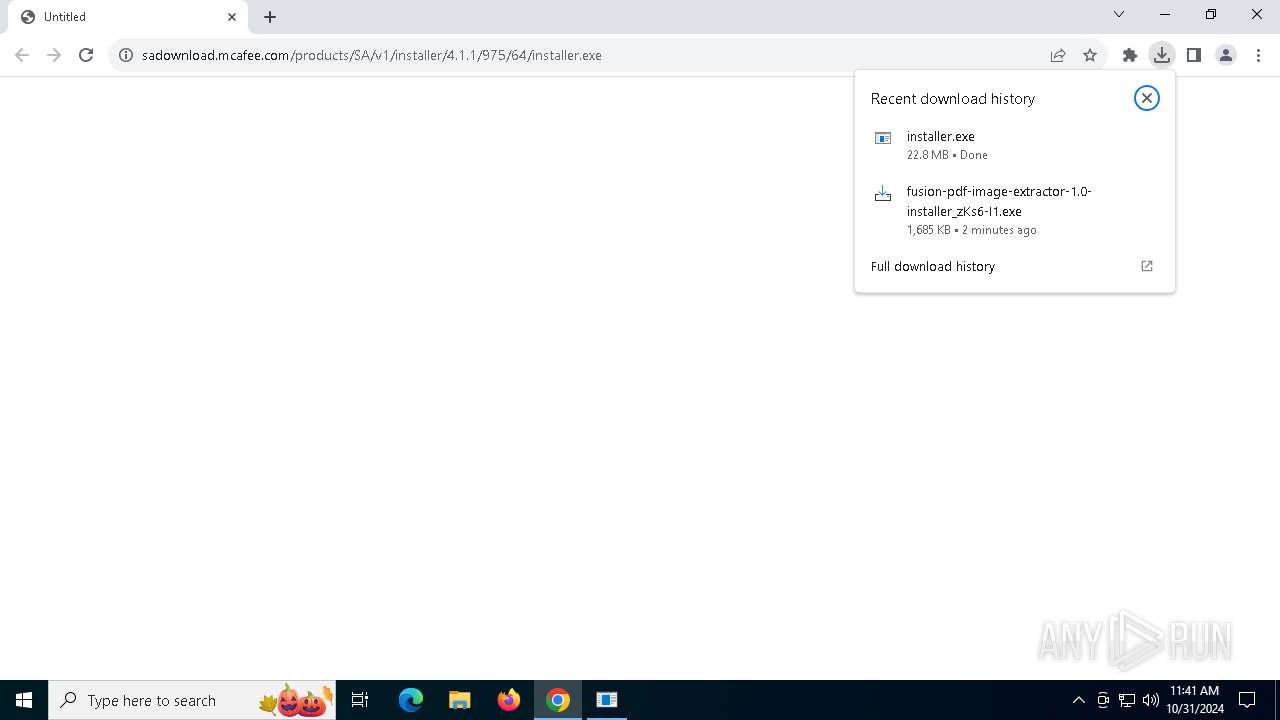
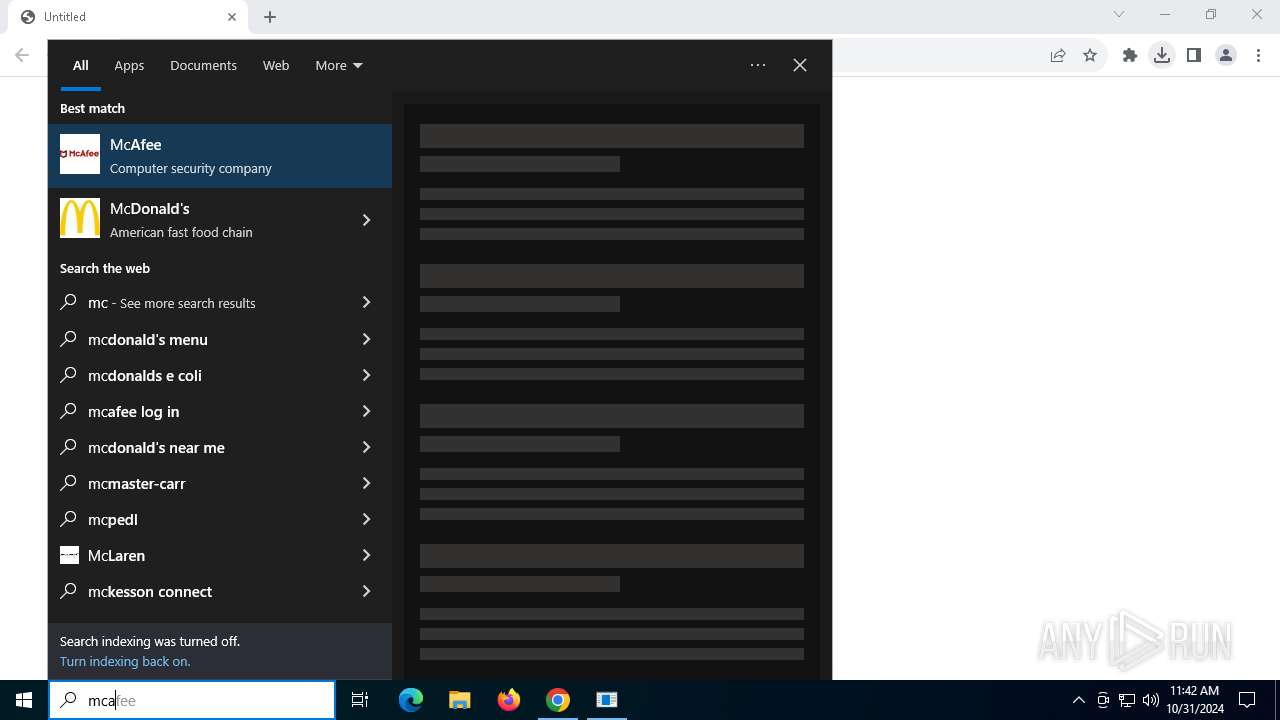
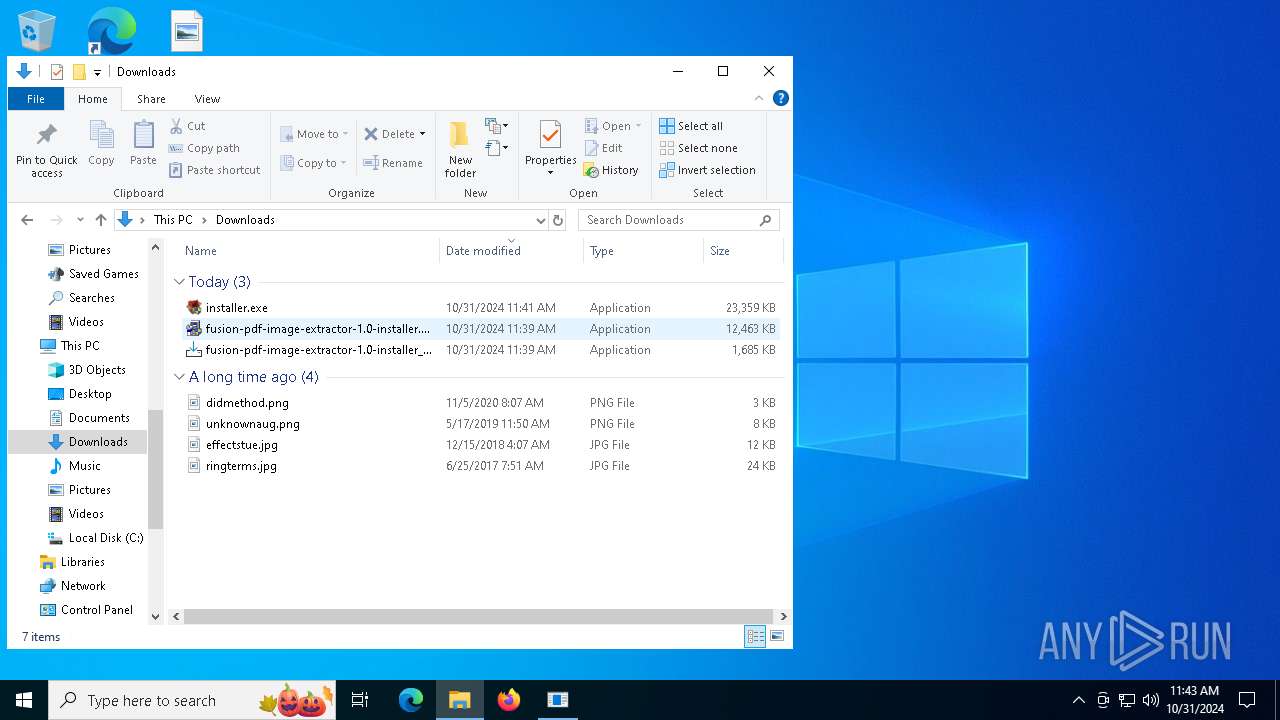
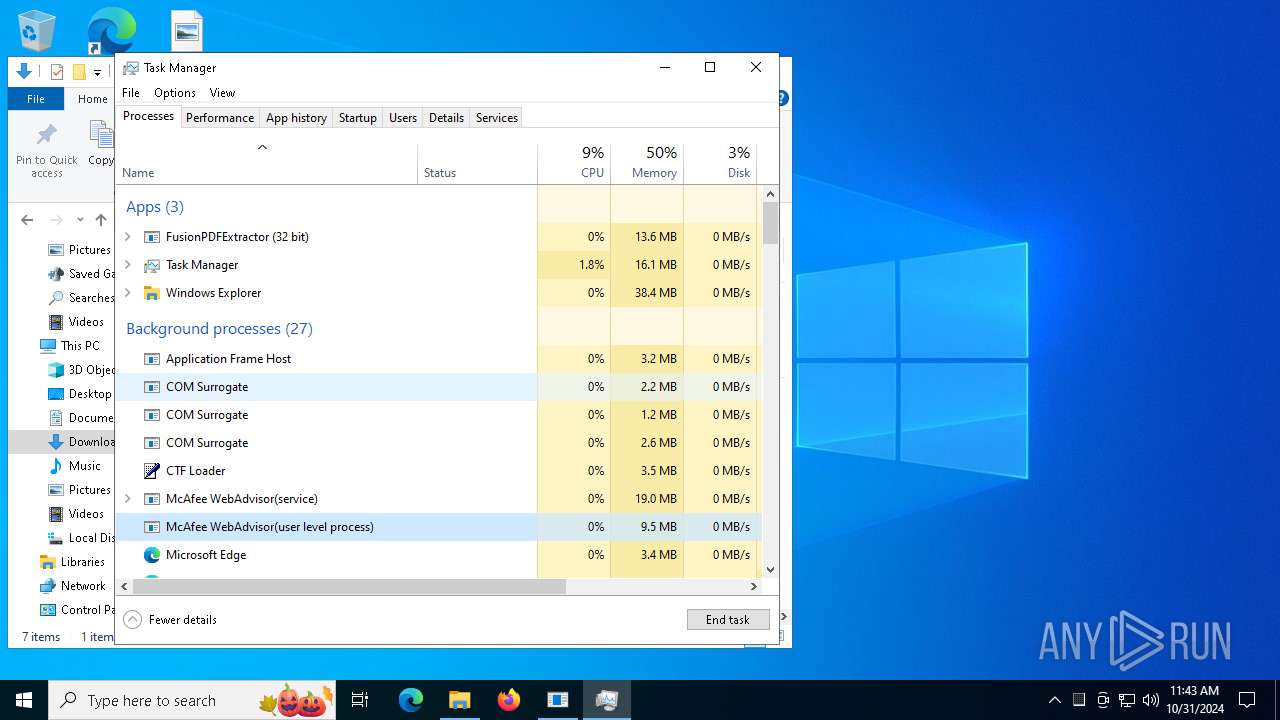
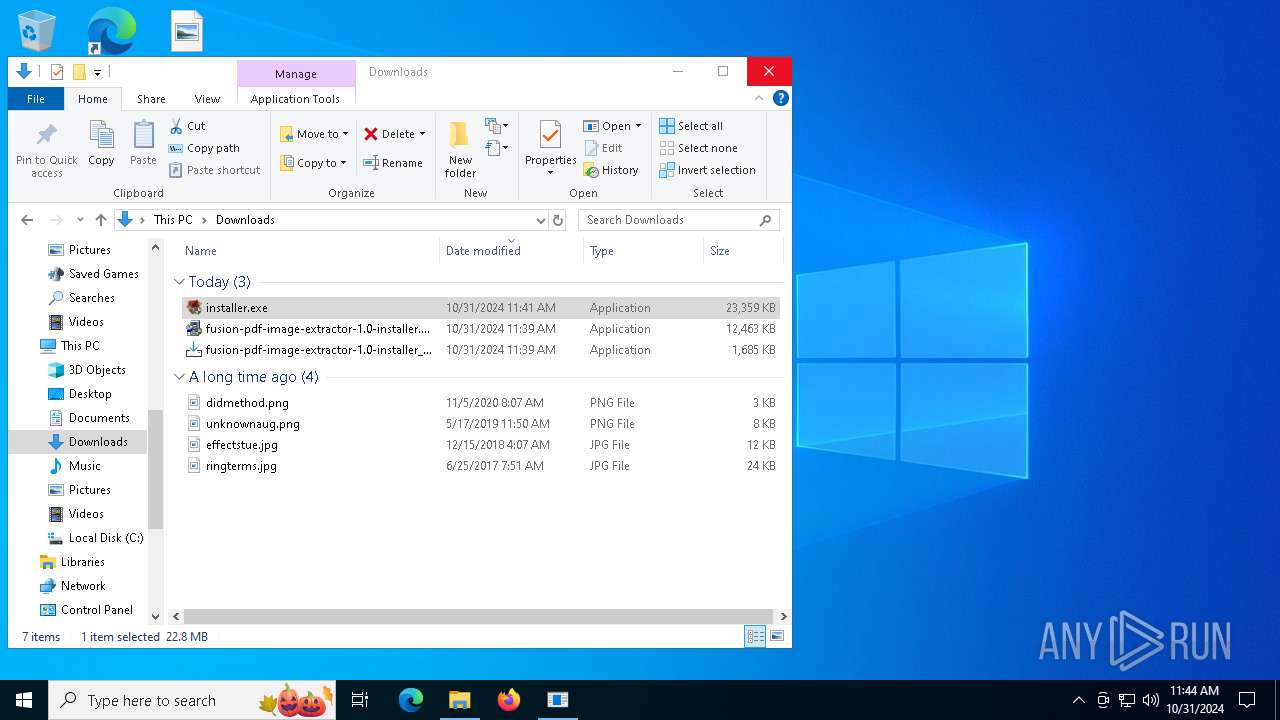
Executable content was dropped or overwritten
- fusion-pdf-image-extractor-1.0-installer_zKs6-I1.exe (PID: 7668)
- fusion-pdf-image-extractor-1.0-installer_zKs6-I1.exe (PID: 7356)
- fusion-pdf-image-extractor-1.0-installer_zKs6-I1.tmp (PID: 7696)
- fusion-pdf-image-extractor-1.0-installer.exe (PID: 7604)
- saBSI.exe (PID: 6376)
- installer.exe (PID: 7348)
- installer.exe (PID: 2888)
- installer.exe (PID: 1580)
- installer.exe (PID: 6976)
- installer.exe (PID: 6184)
- installer.exe (PID: 5824)
- installer.exe (PID: 8136)
- installer.exe (PID: 7136)
Executes application which crashes
- fusion-pdf-image-extractor-1.0-installer_zKs6-I1.tmp (PID: 7696)
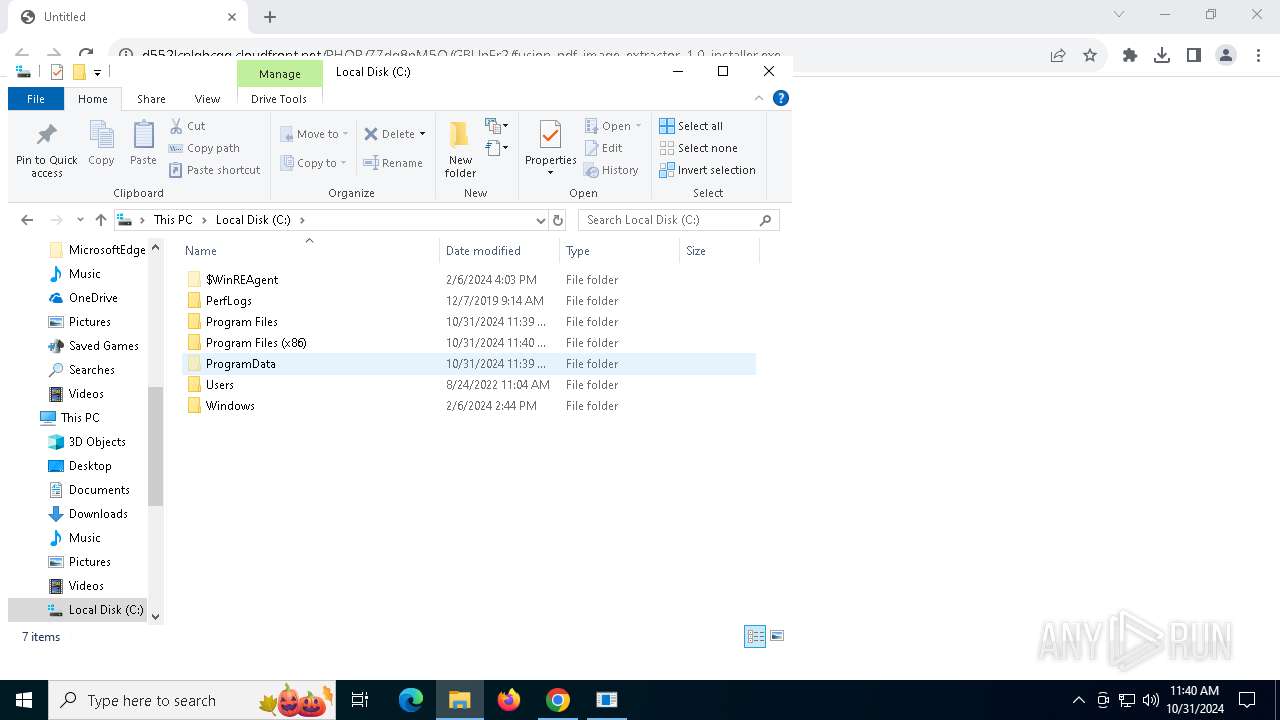
Process drops legitimate windows executable
- installer.exe (PID: 2888)
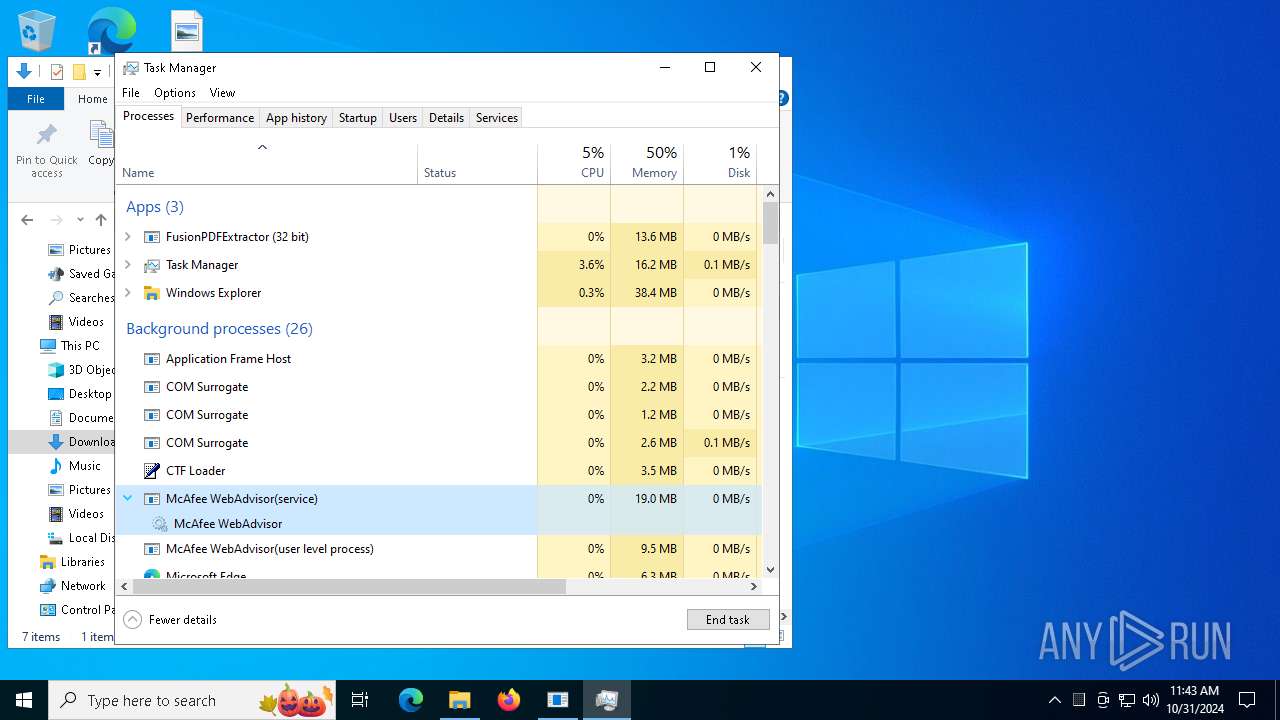
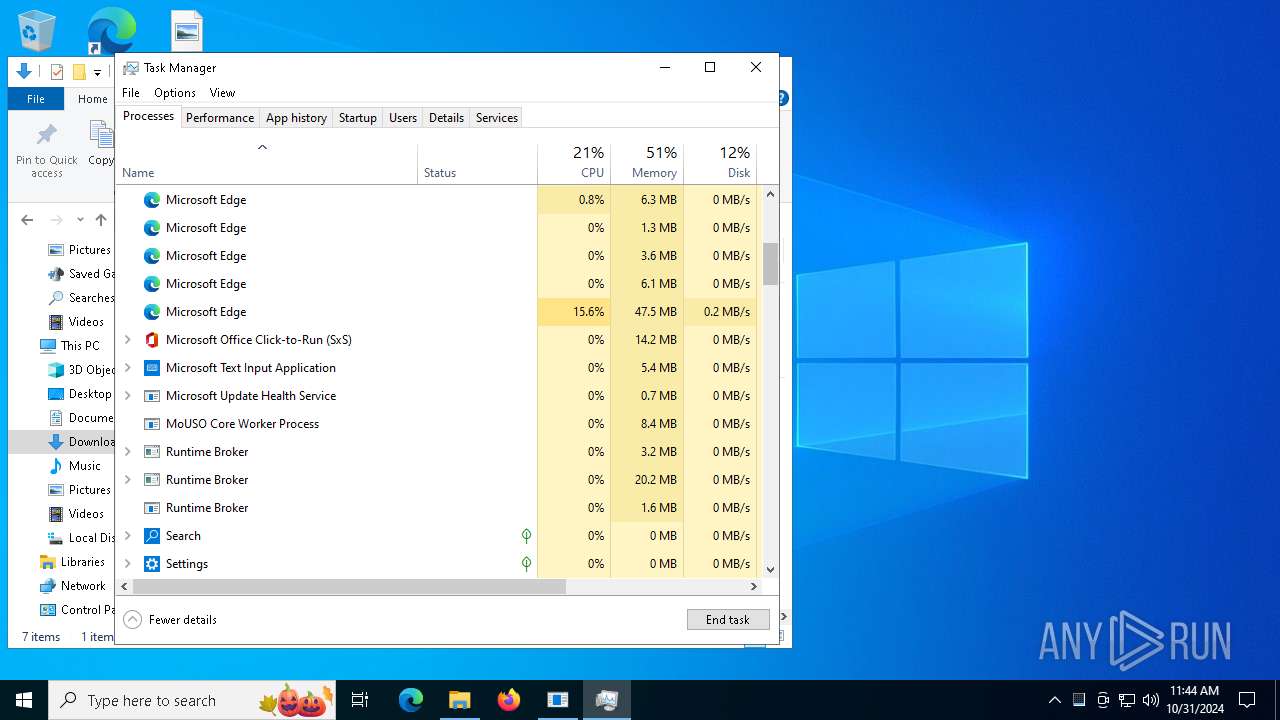
Executes as Windows Service
- servicehost.exe (PID: 7328)
Hides command output
- cmd.exe (PID: 3620)
Starts CMD.EXE for commands execution
- servicehost.exe (PID: 7328)
- updater.exe (PID: 4996)
INFO
Executable content was dropped or overwritten
- chrome.exe (PID: 4060)
- chrome.exe (PID: 6000)
Application launched itself
- chrome.exe (PID: 4060)
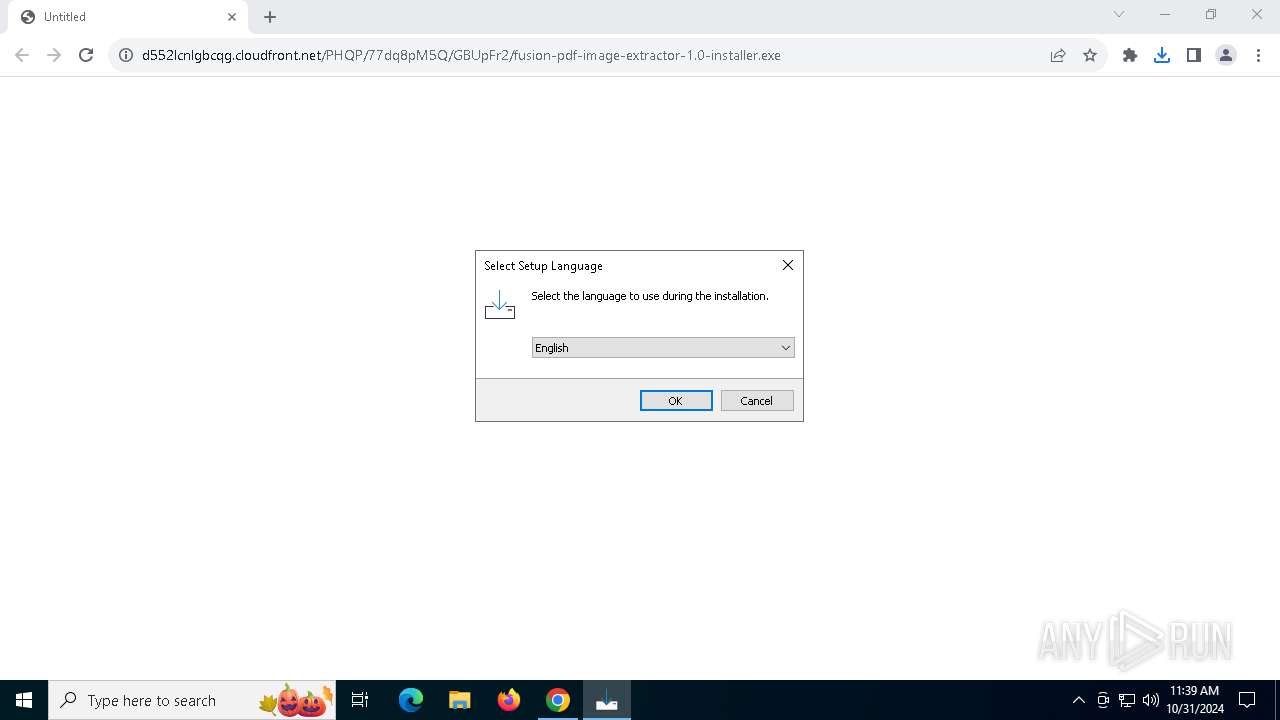
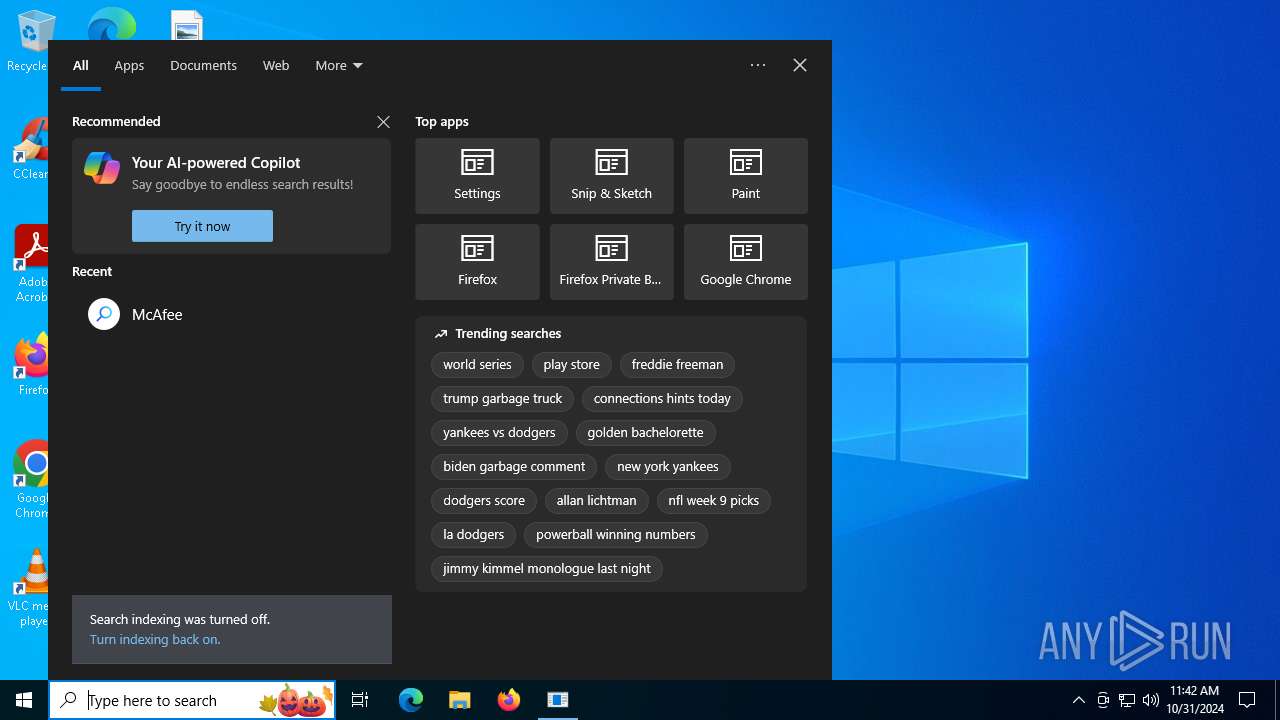
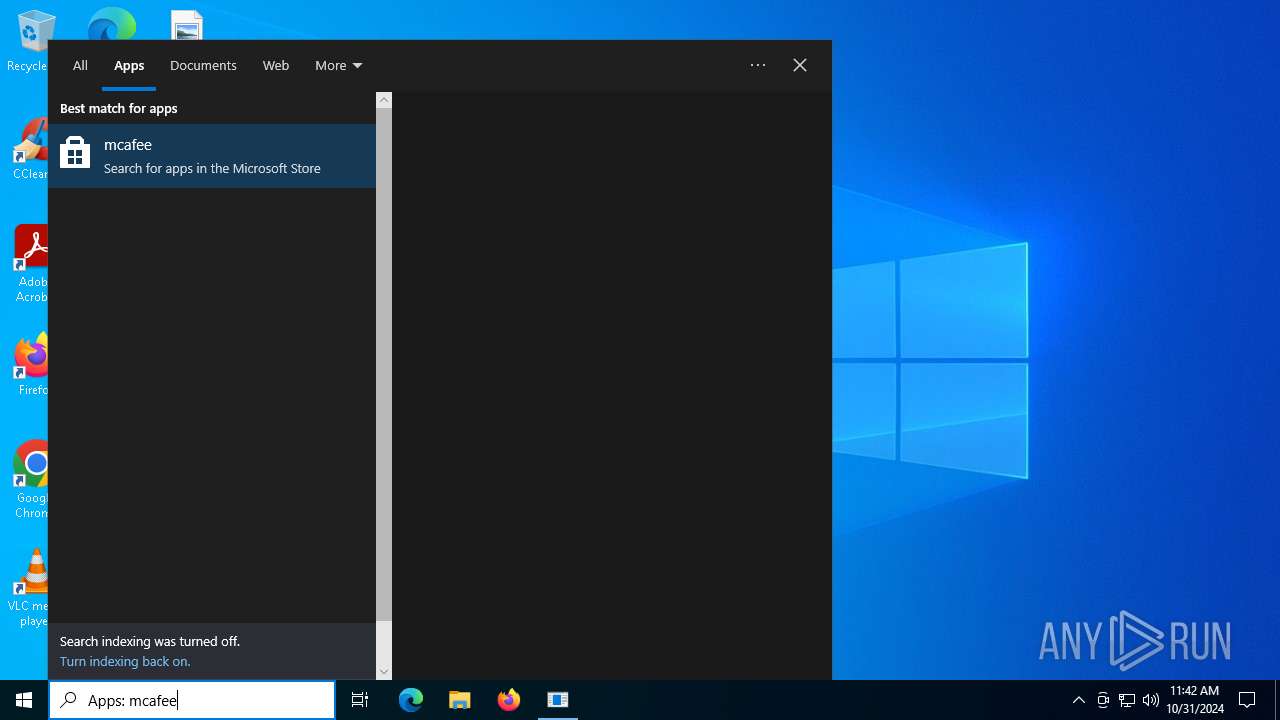
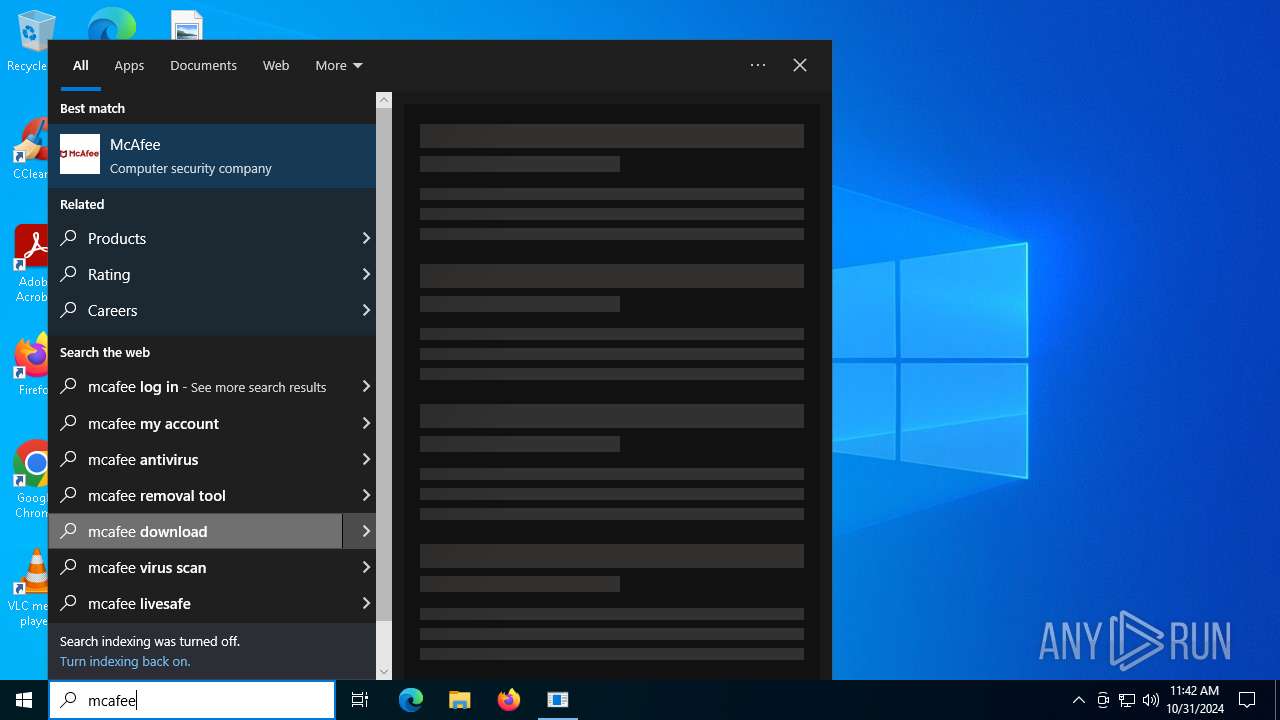
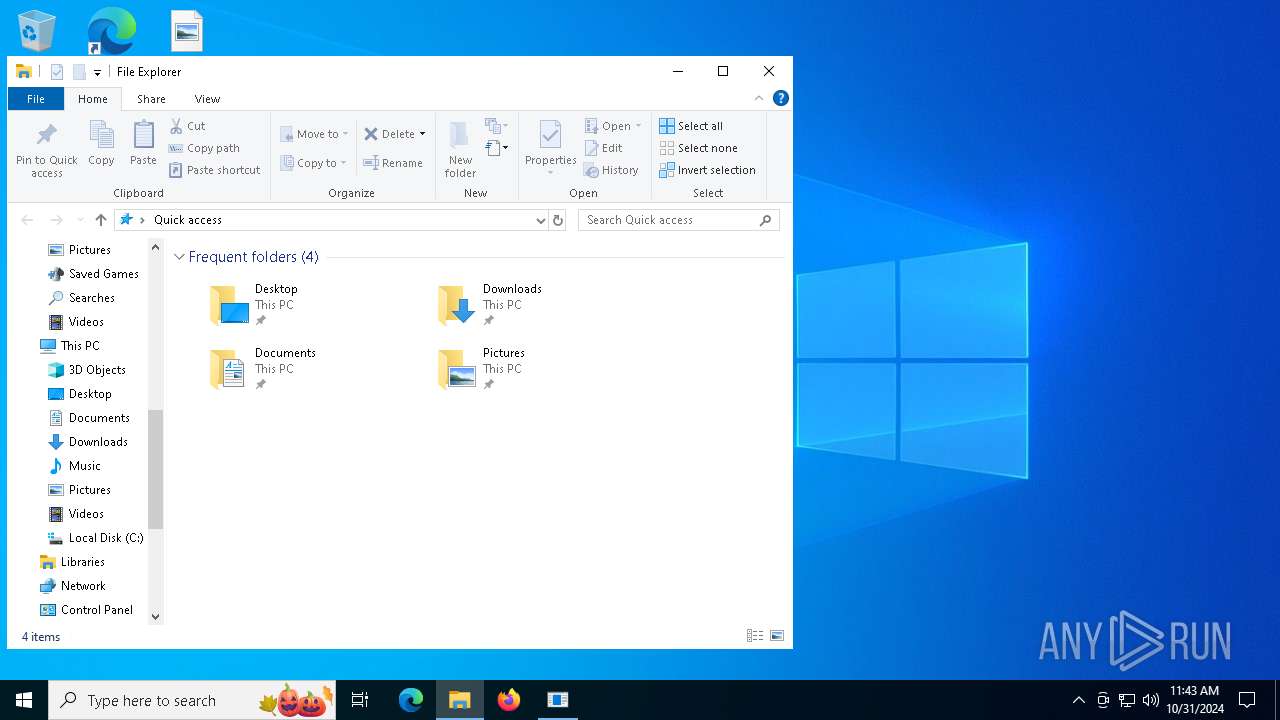
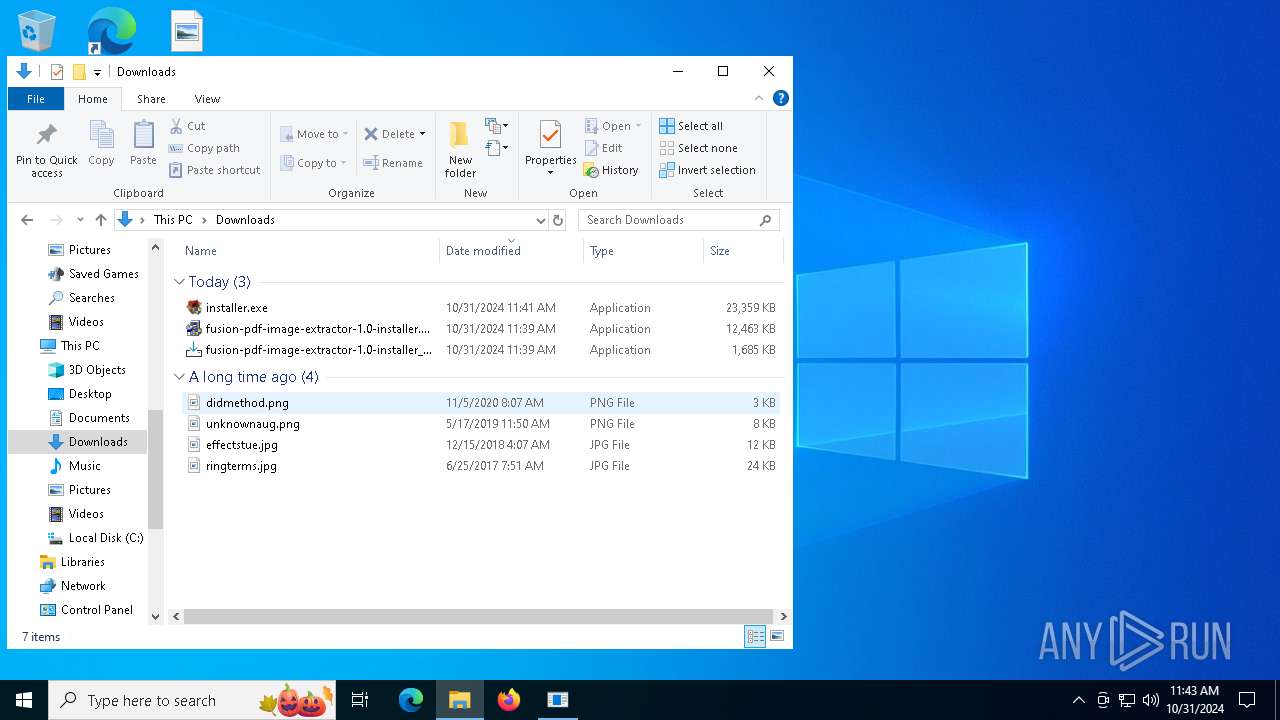
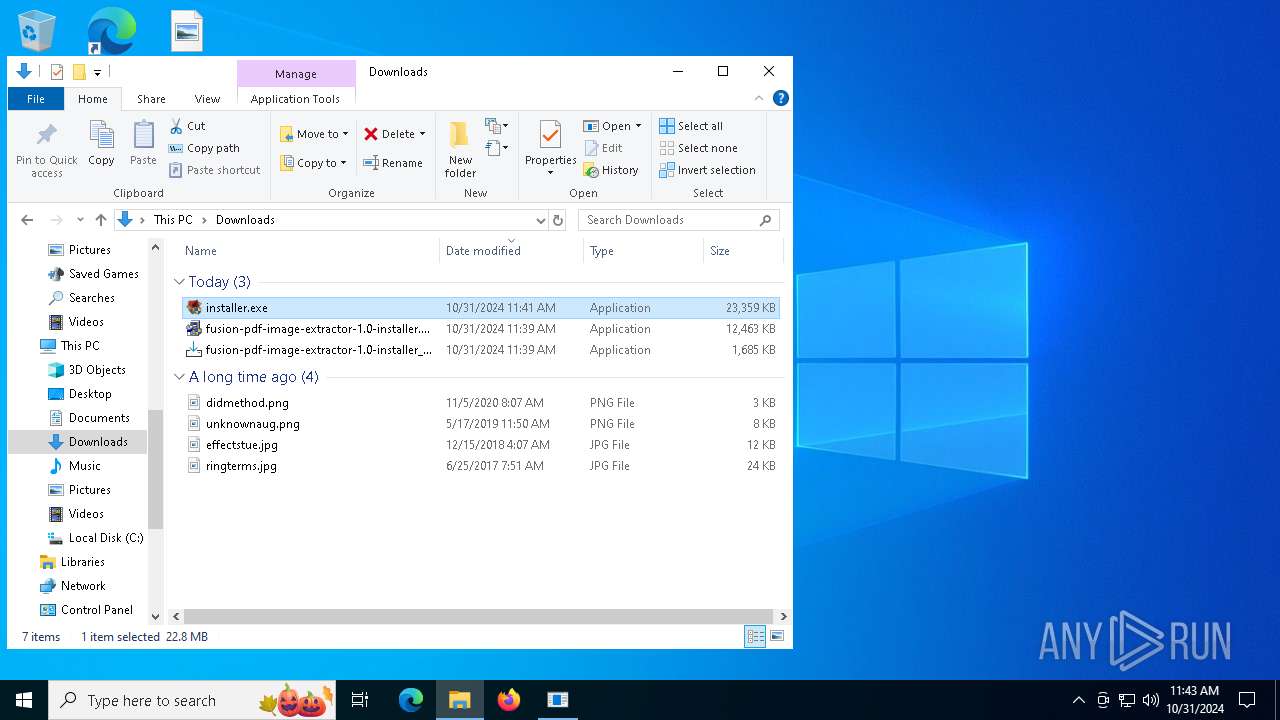
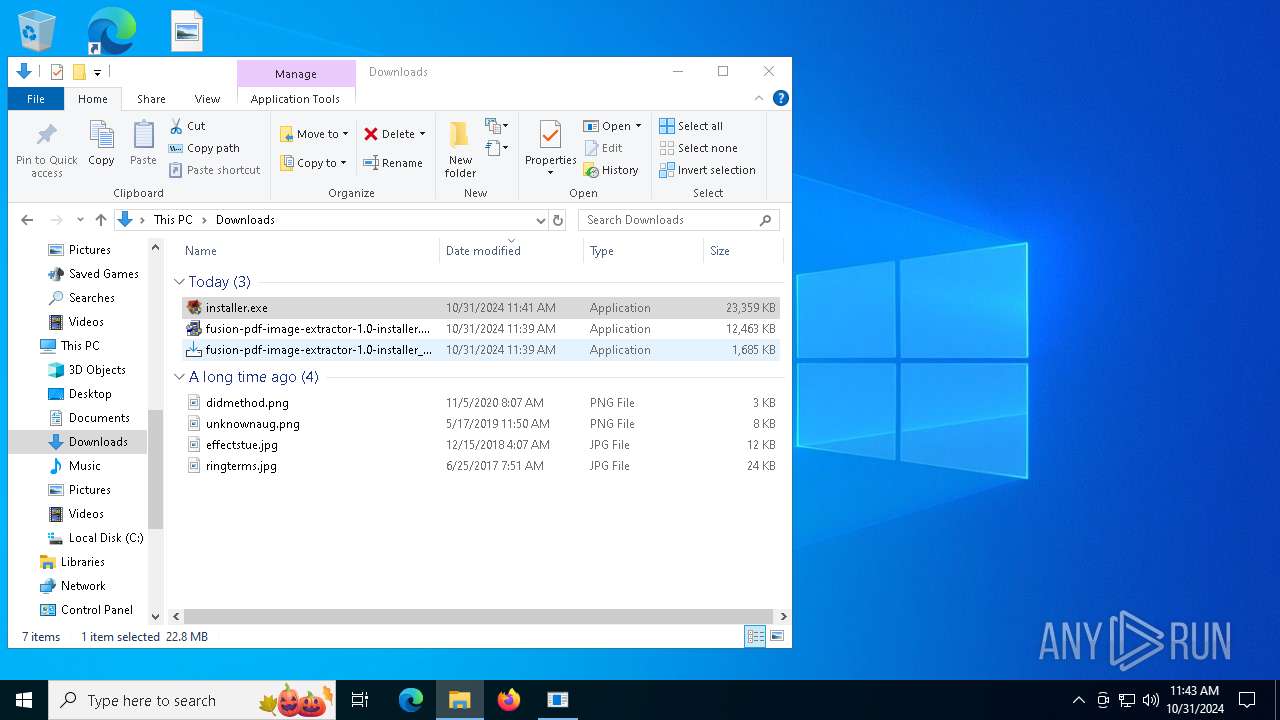
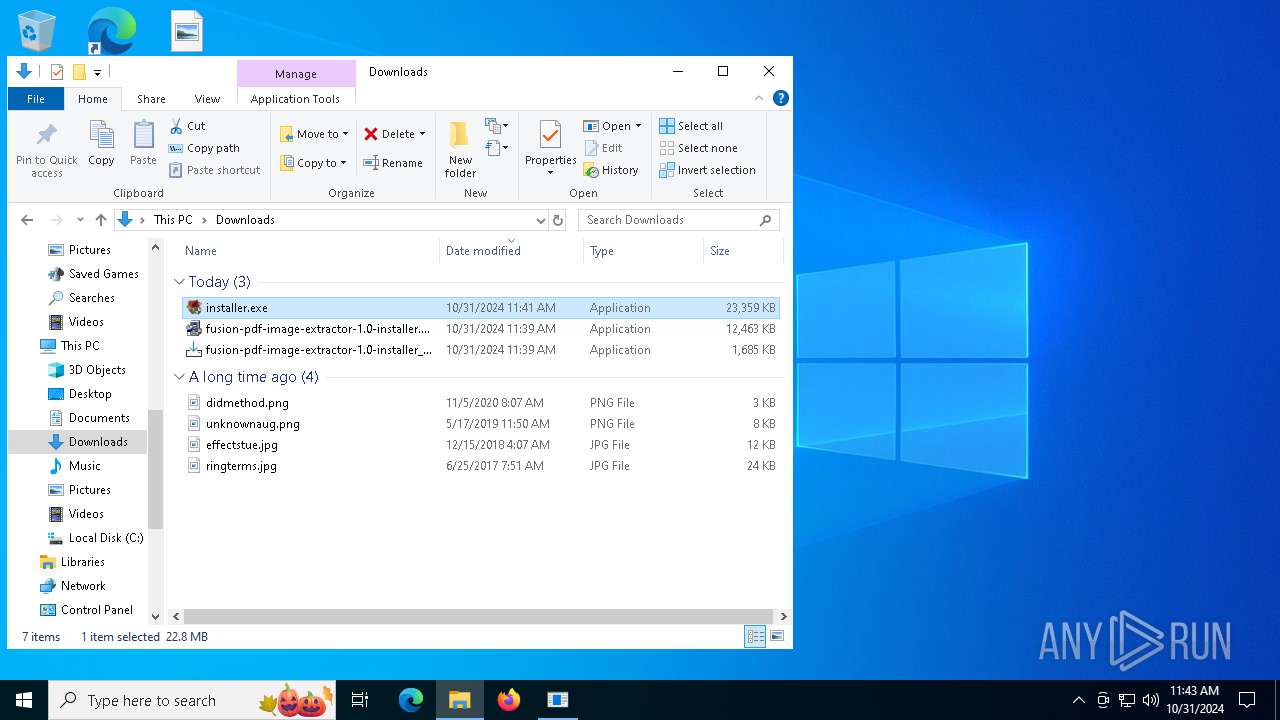
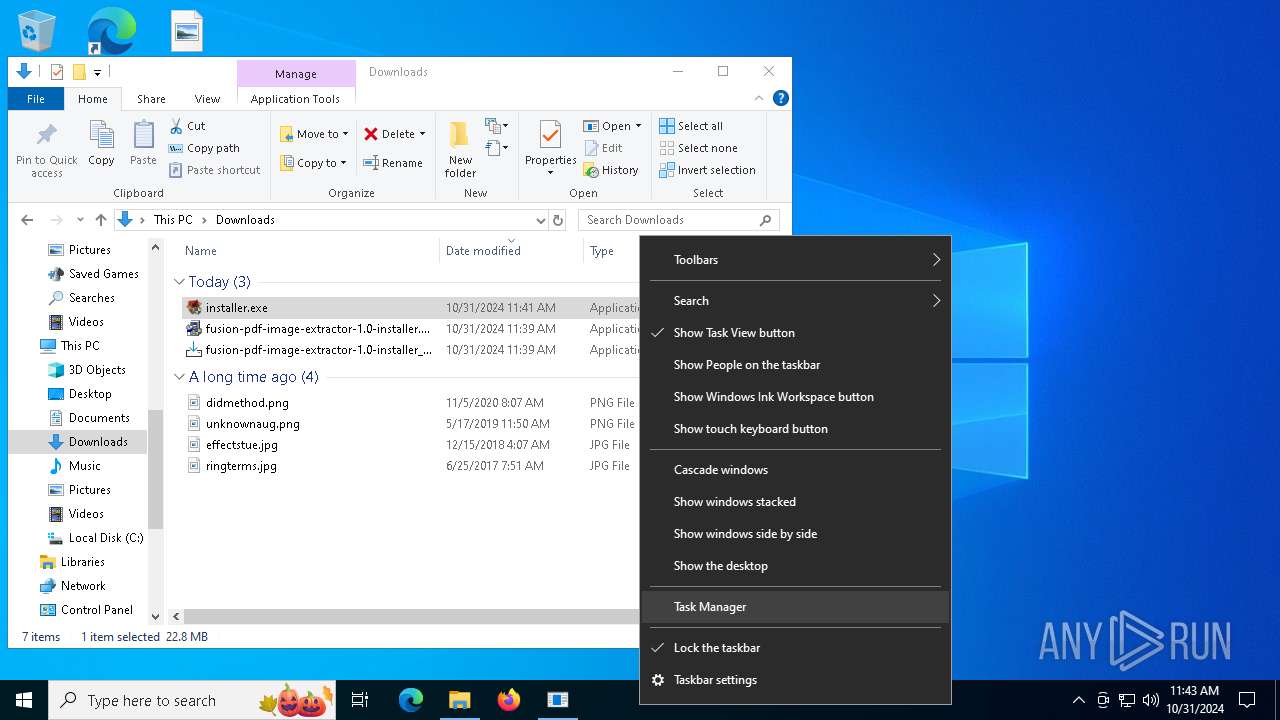
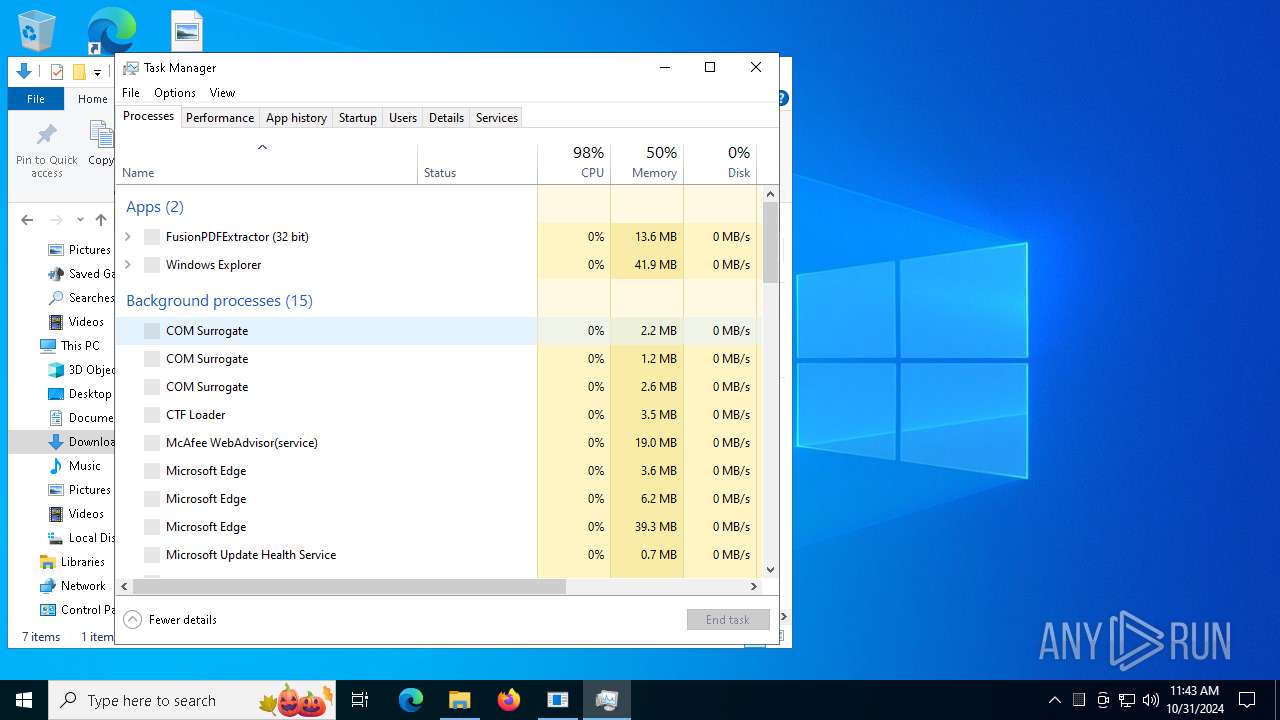
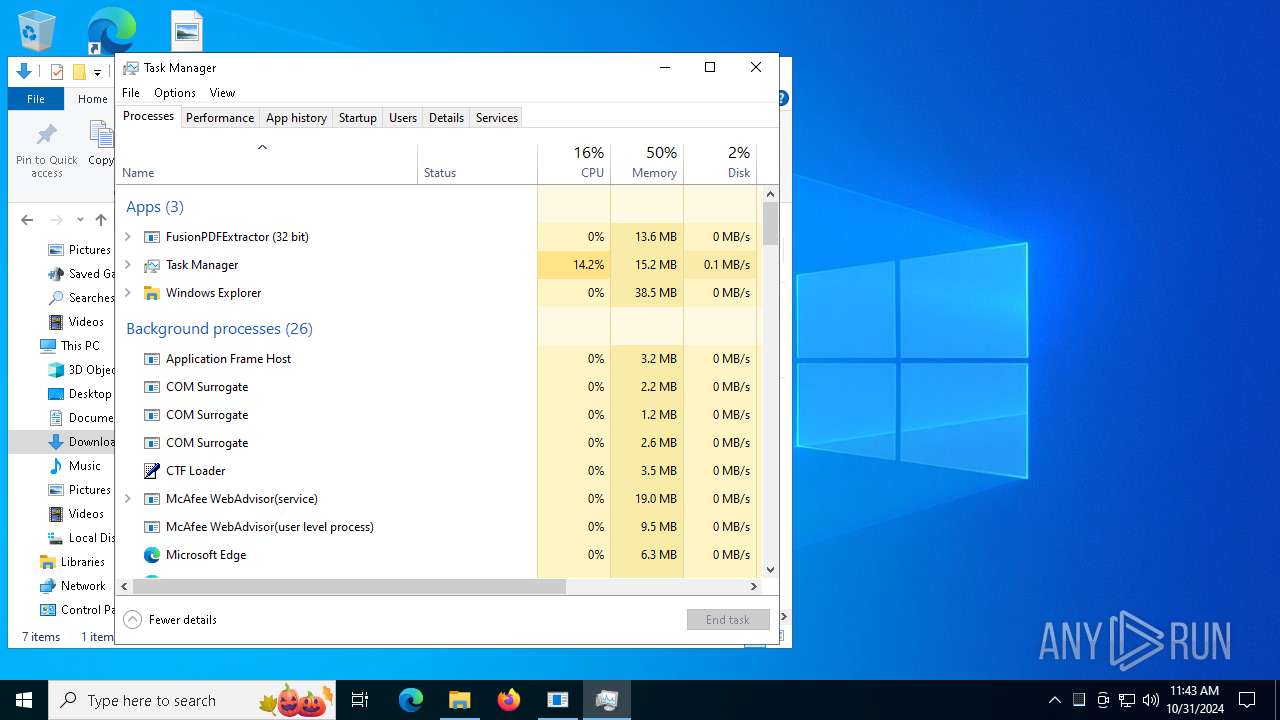
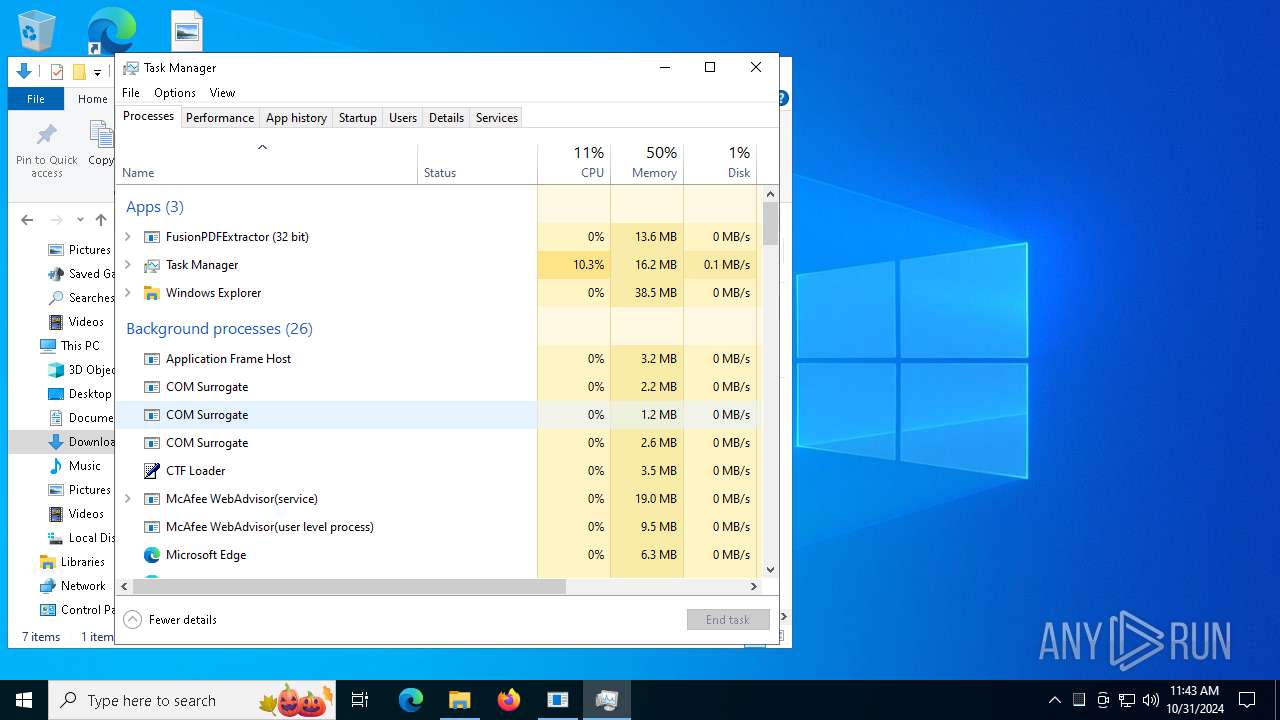
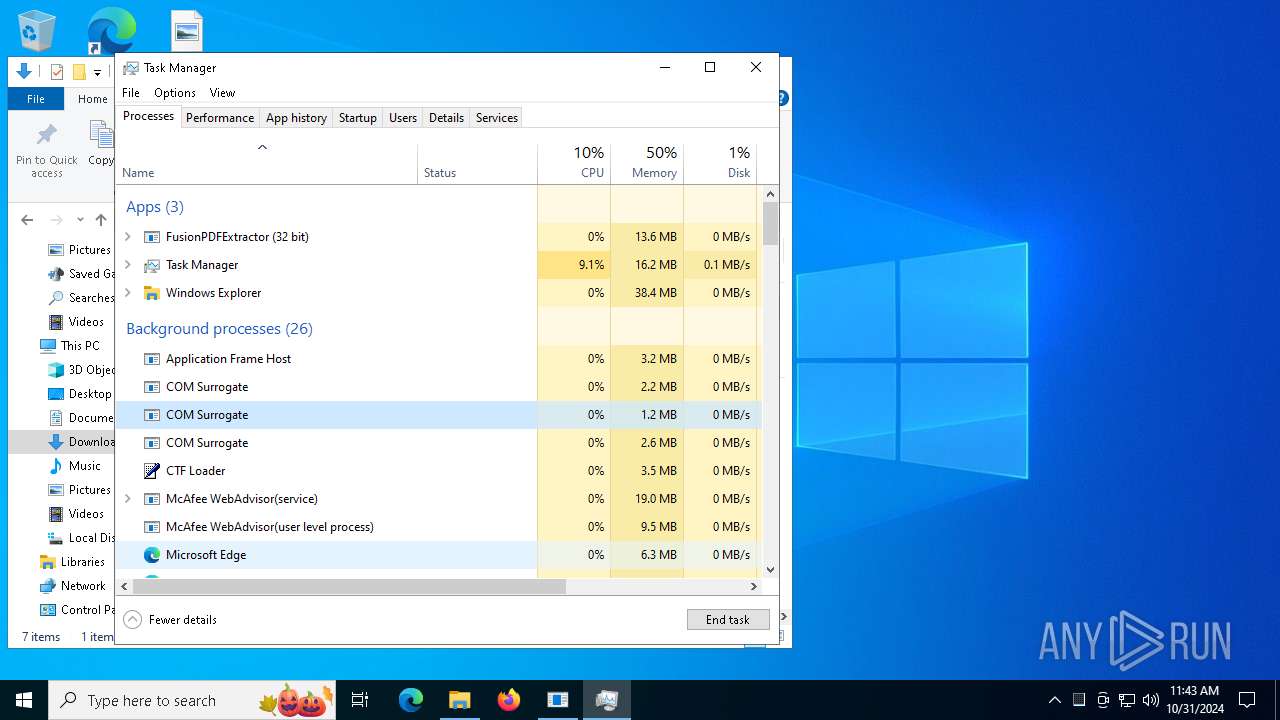
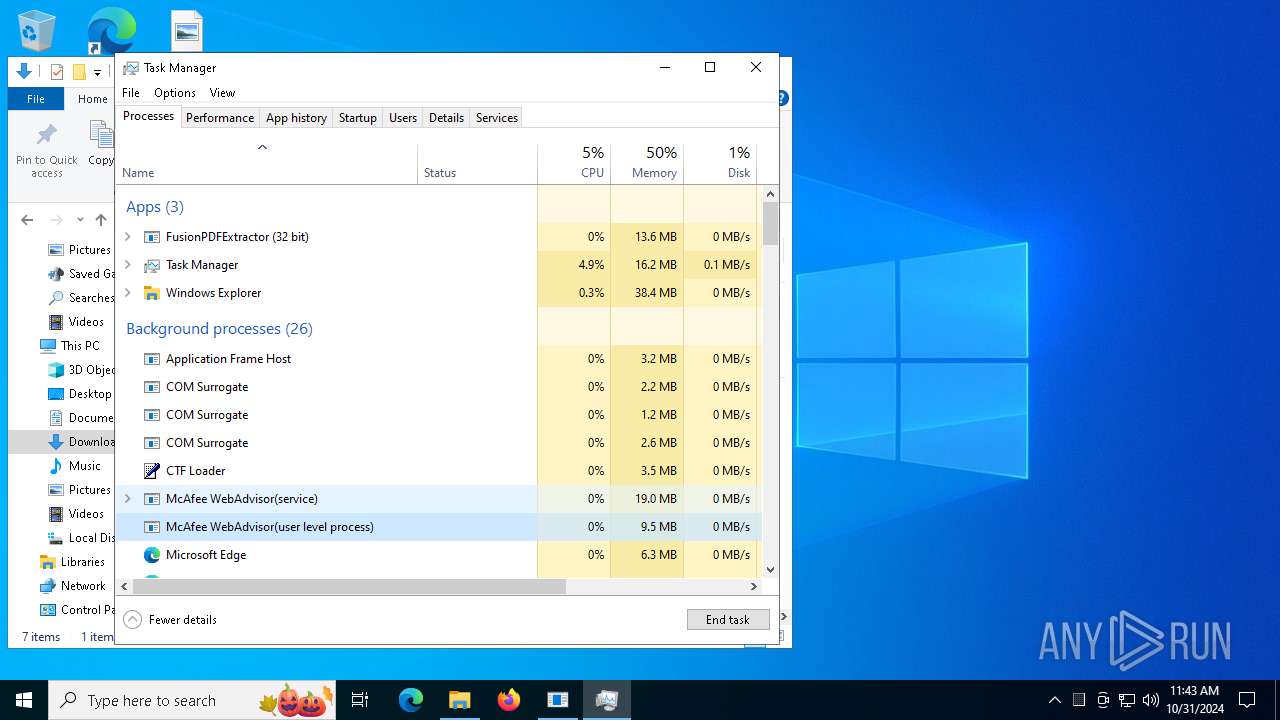
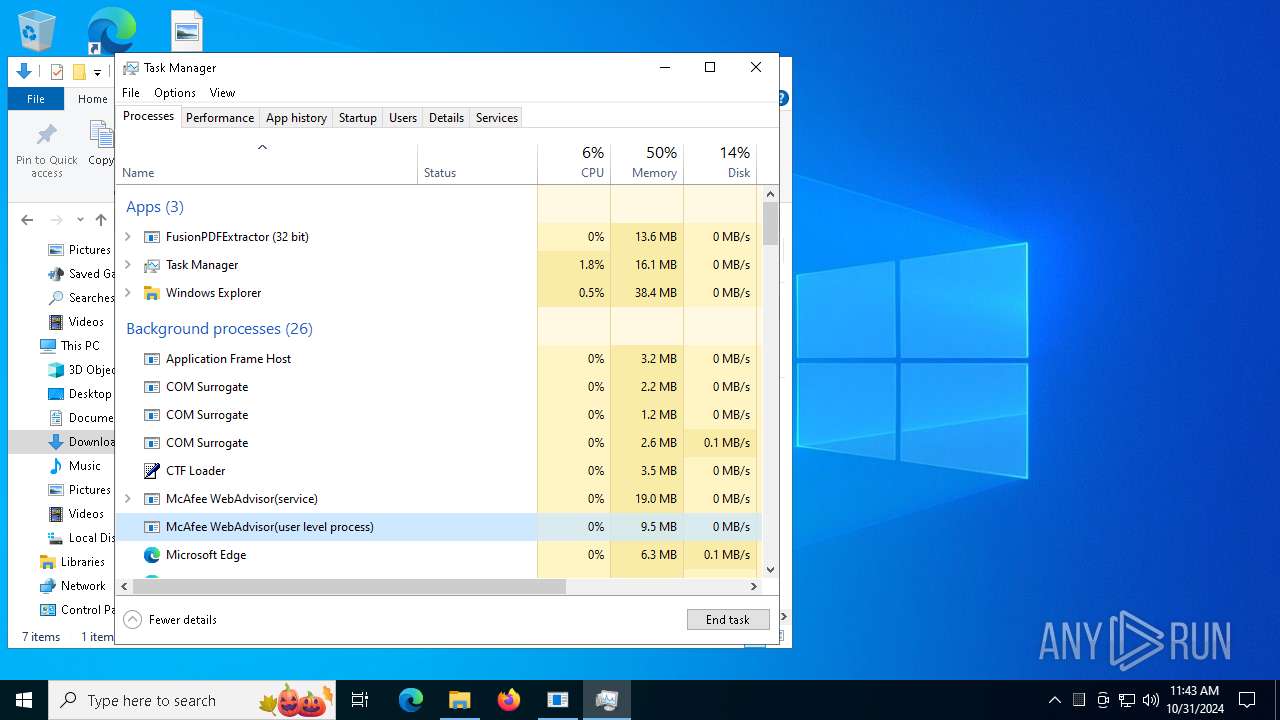
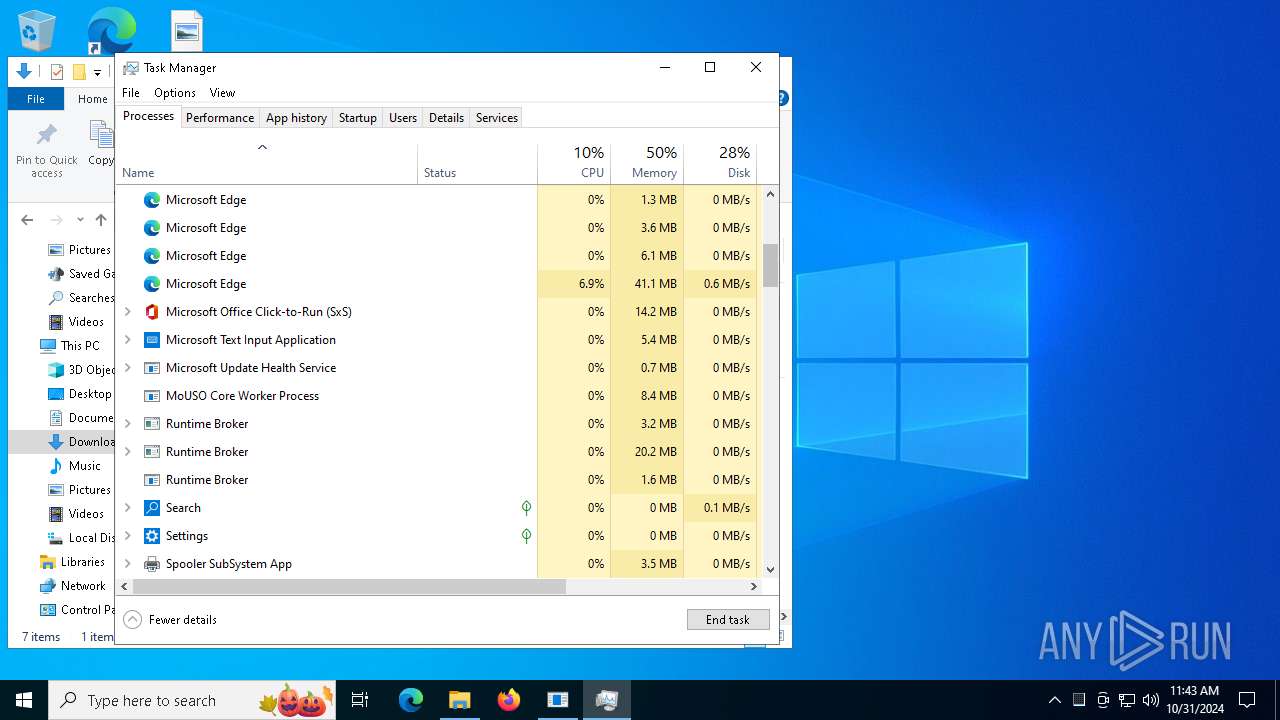
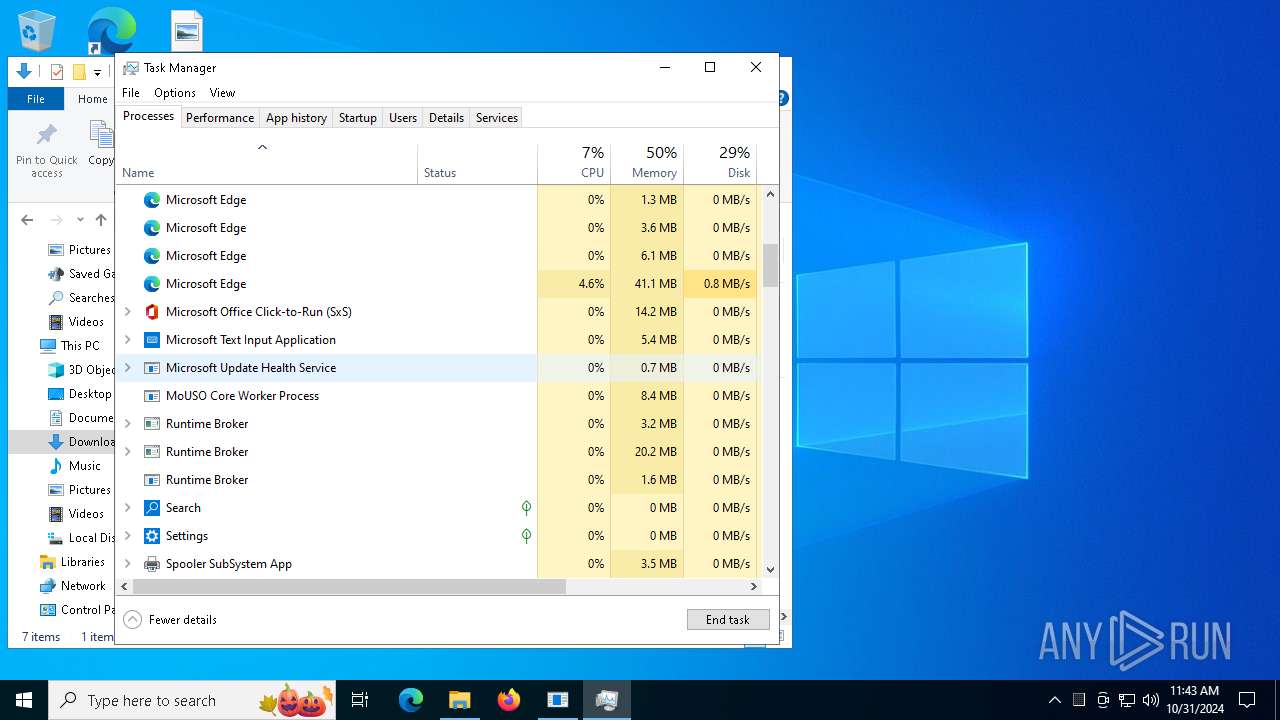
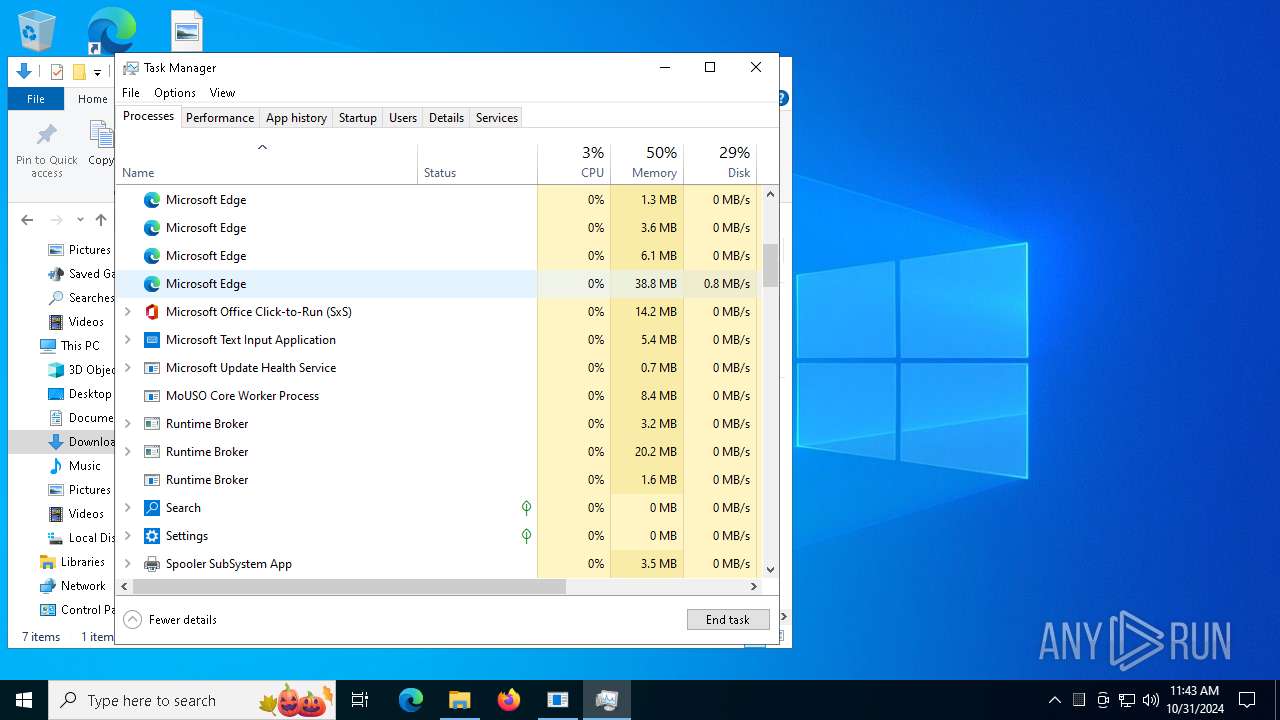
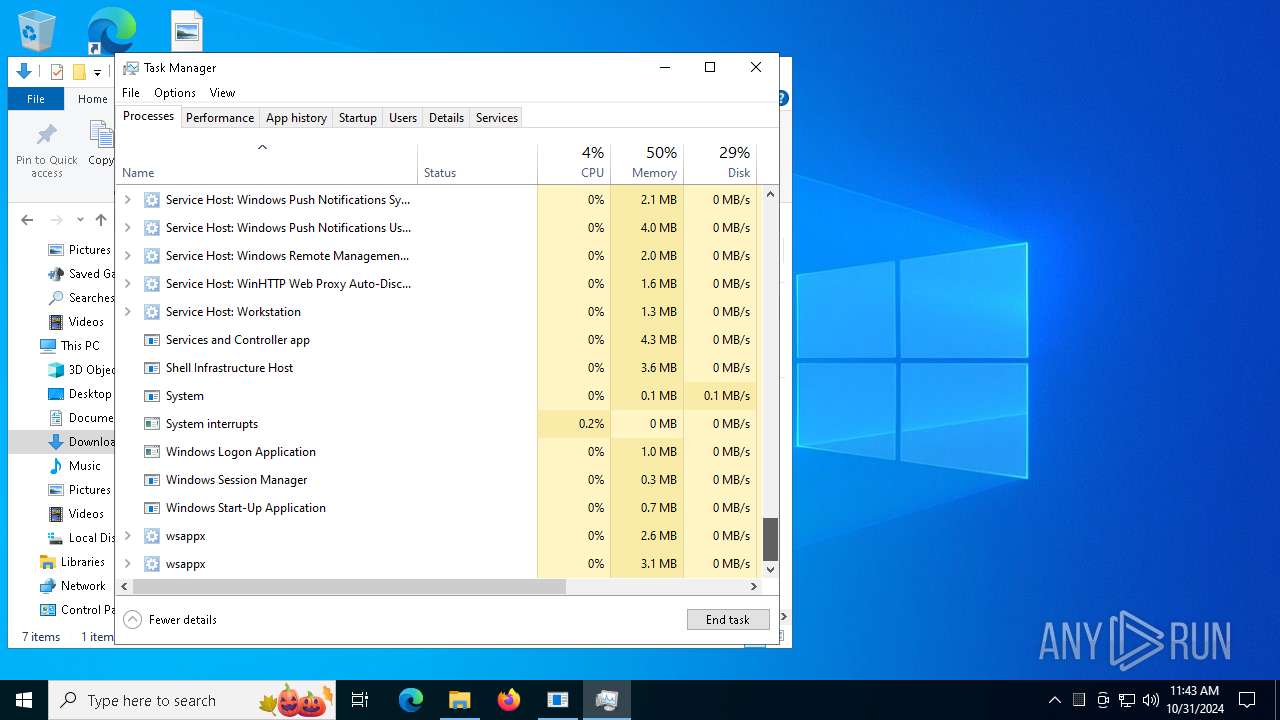
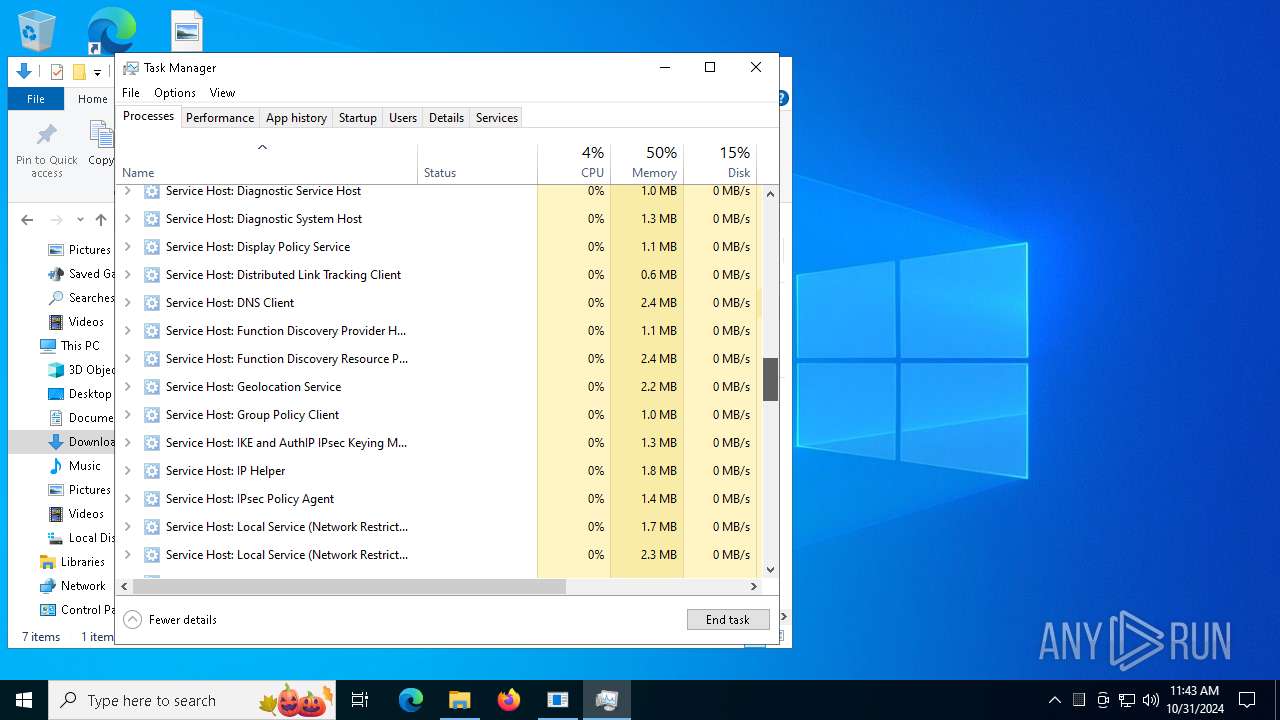
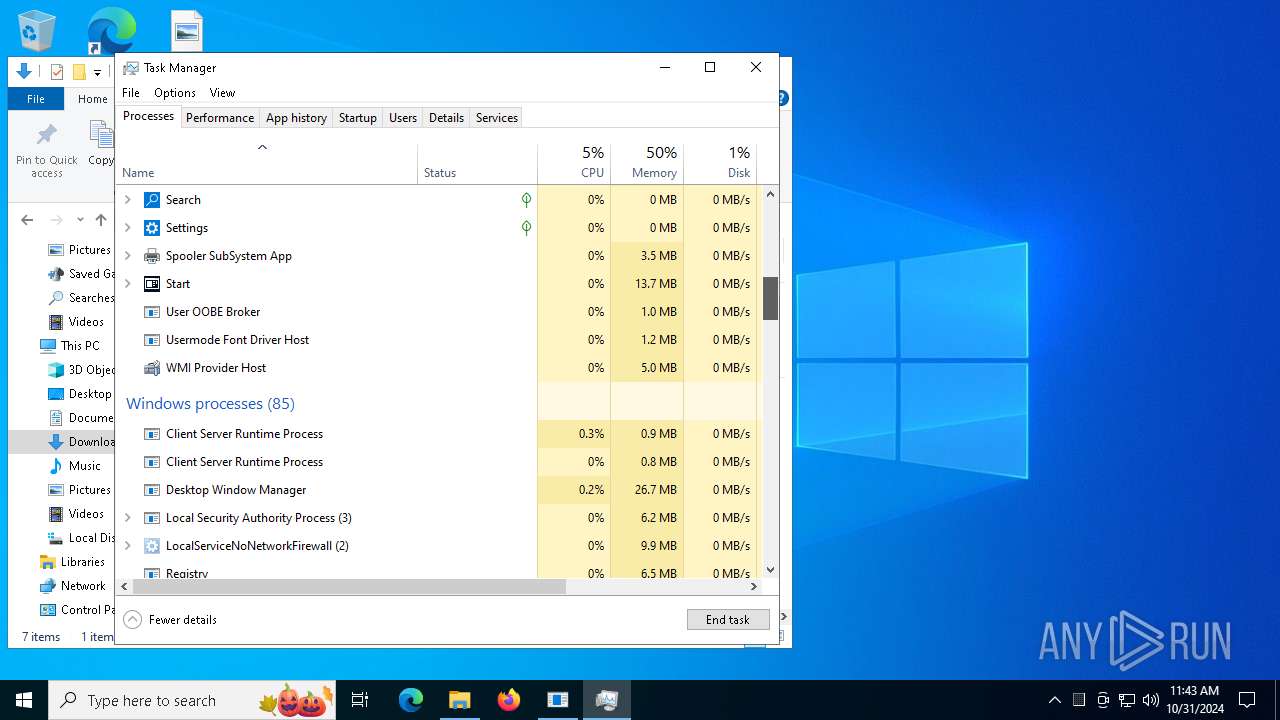
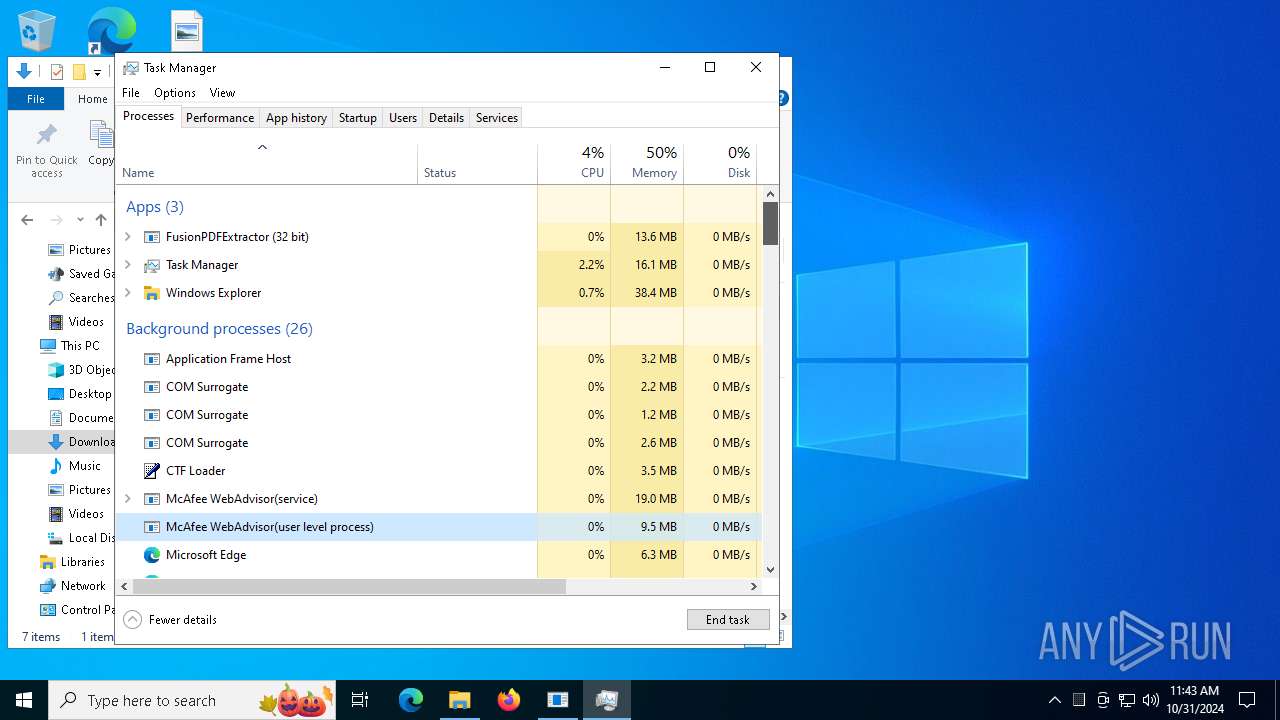
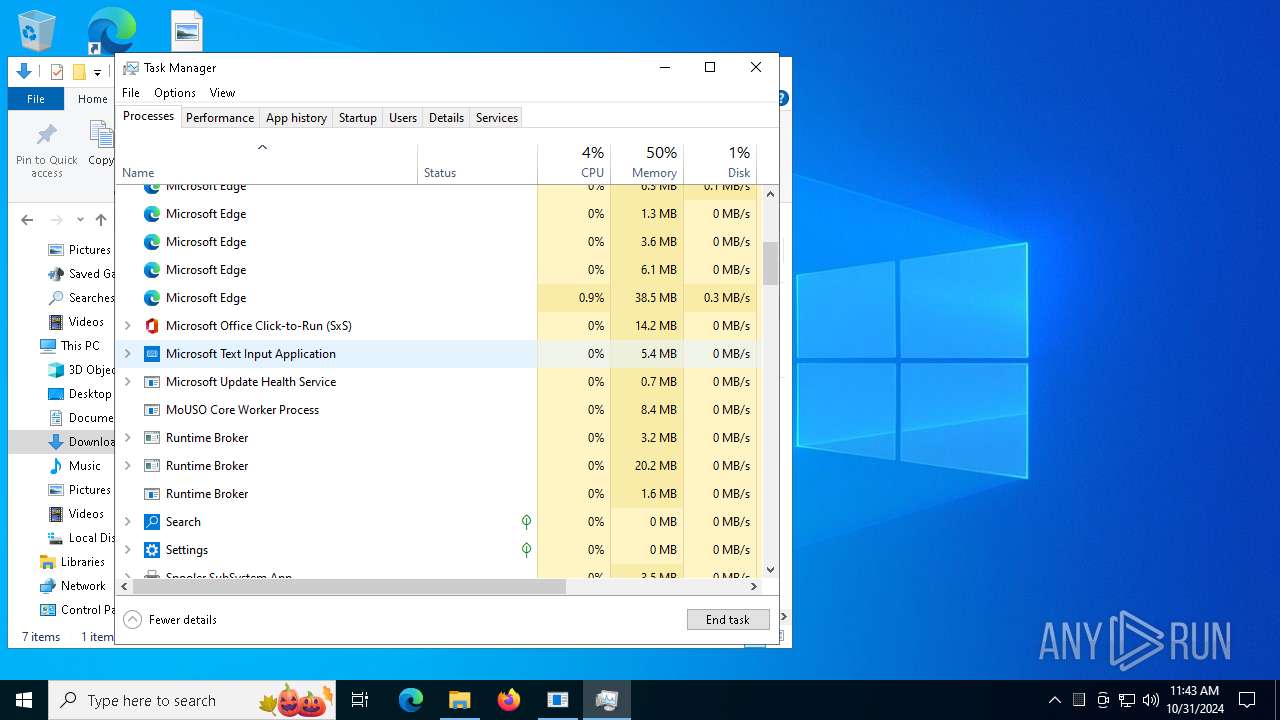
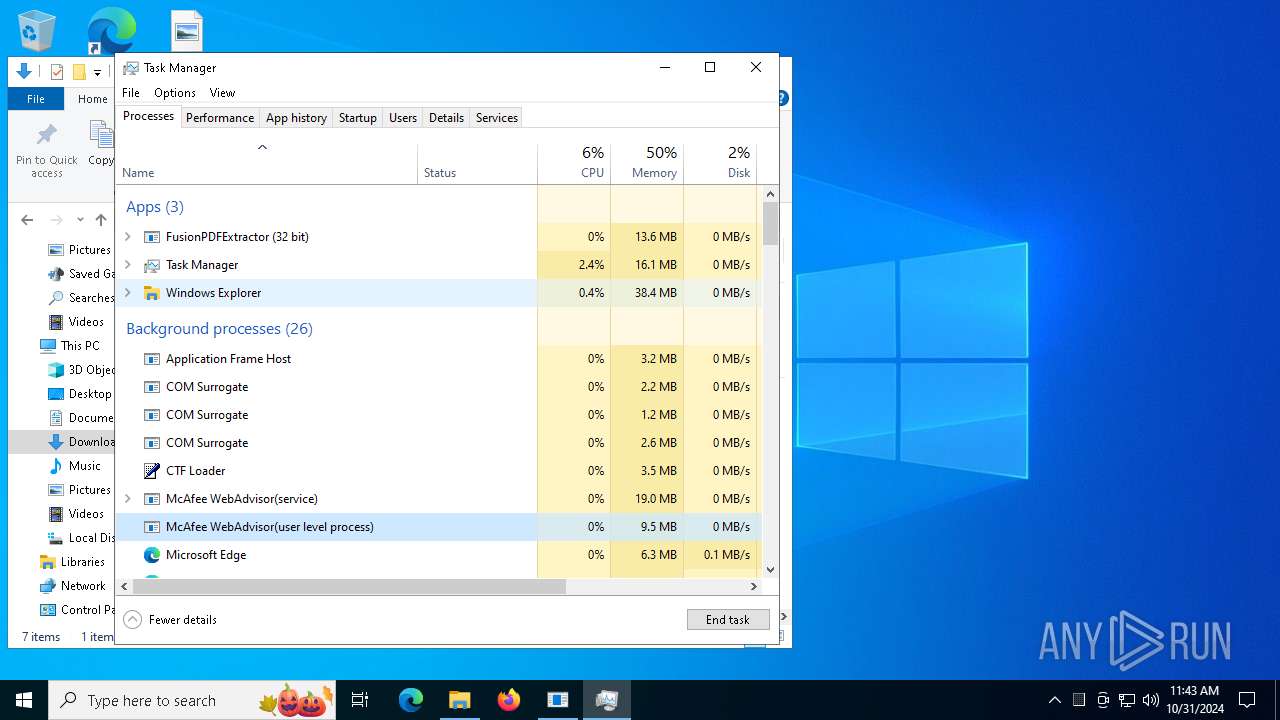
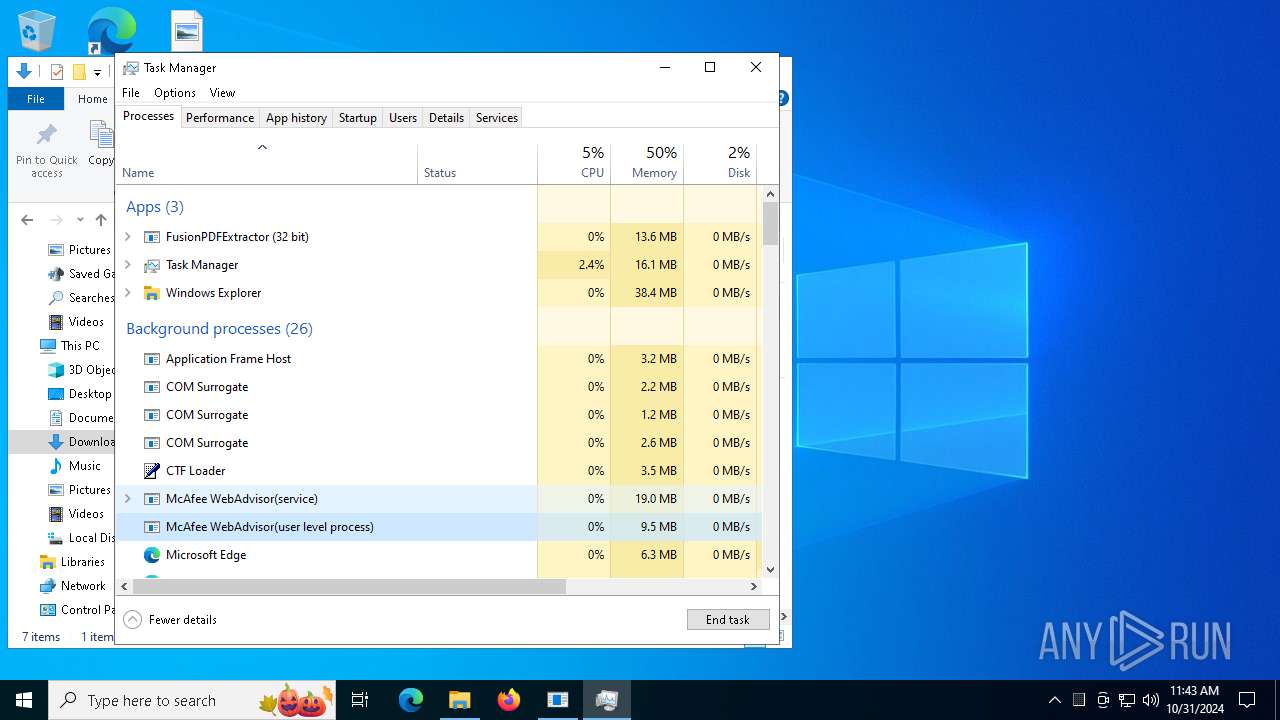
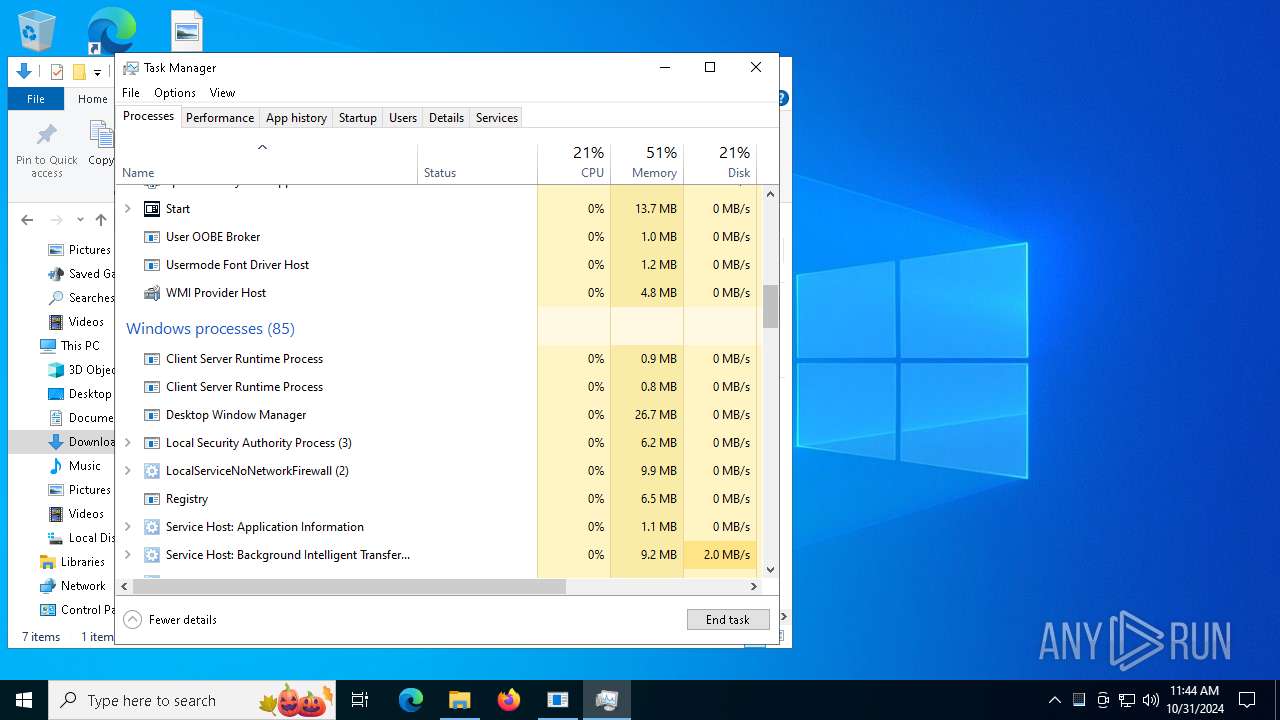
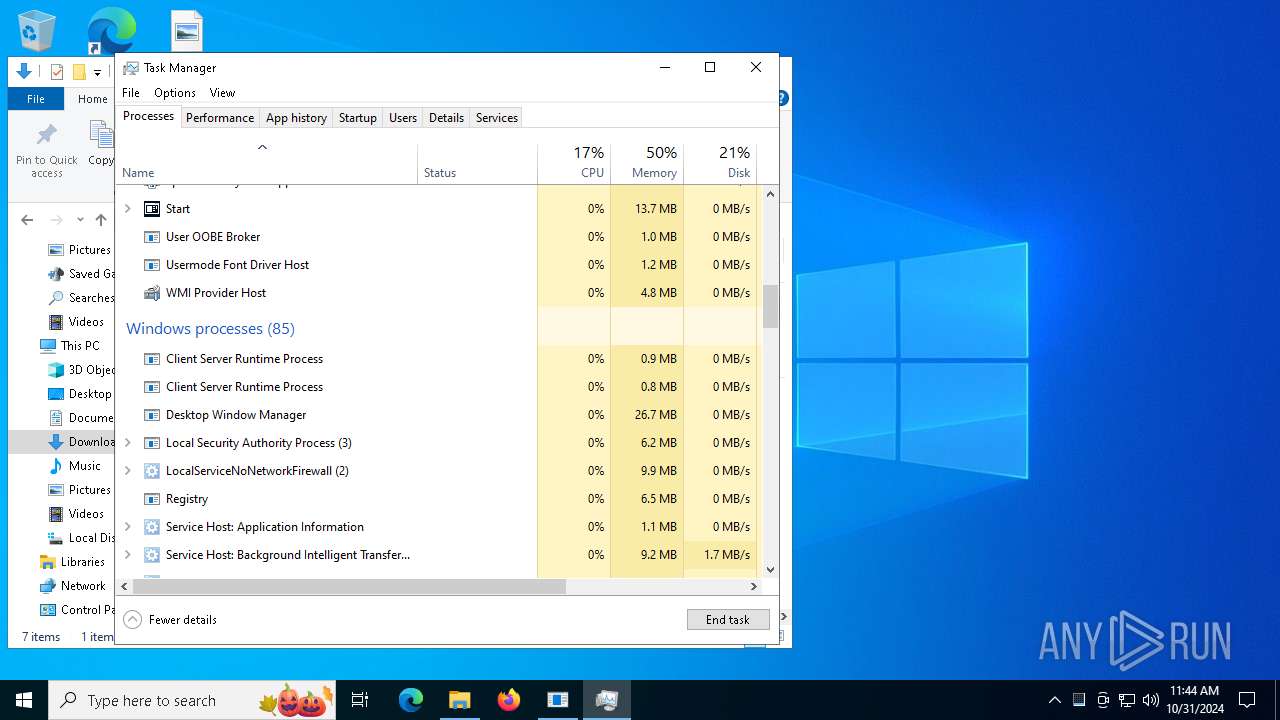
Manual execution by a user
- installer.exe (PID: 5952)
- installer.exe (PID: 7136)
- Taskmgr.exe (PID: 9056)
- Taskmgr.exe (PID: 8168)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
255
Monitored processes
56
Malicious processes
0
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1204 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --disable-quic --no-appcompat-clear --mojo-platform-channel-handle=5608 --field-trial-handle=1904,i,5169647220609545486,11968780291207105708,262144 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction --variations-seed-version /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 122.0.6261.70 | |||||||||||||||
| 1396 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --extension-process --no-appcompat-clear --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=7 --mojo-platform-channel-handle=3540 --field-trial-handle=1904,i,5169647220609545486,11968780291207105708,262144 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction --variations-seed-version /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 122.0.6261.70 Modules
| |||||||||||||||
| 1580 | "C:\Users\admin\Downloads\installer.exe" | C:\Users\admin\Downloads\installer.exe | chrome.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 1024 | |||||||||||||||
| 1580 | "C:\Users\admin\Downloads\installer.exe" | C:\Users\admin\Downloads\installer.exe | — | chrome.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 3221226540 | |||||||||||||||
| 1752 | C:\WINDOWS\system32\cmd.exe /c DEL "C:\Program Files\McAfee\WebAdvisor\*.tmp" | C:\Windows\System32\cmd.exe | — | updater.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) | |||||||||||||||
| 2084 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) | |||||||||||||||
| 2708 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=storage.mojom.StorageService --lang=en-US --service-sandbox-type=service --disable-quic --no-appcompat-clear --mojo-platform-channel-handle=2316 --field-trial-handle=1904,i,5169647220609545486,11968780291207105708,262144 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction --variations-seed-version /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 122.0.6261.70 Modules
| |||||||||||||||
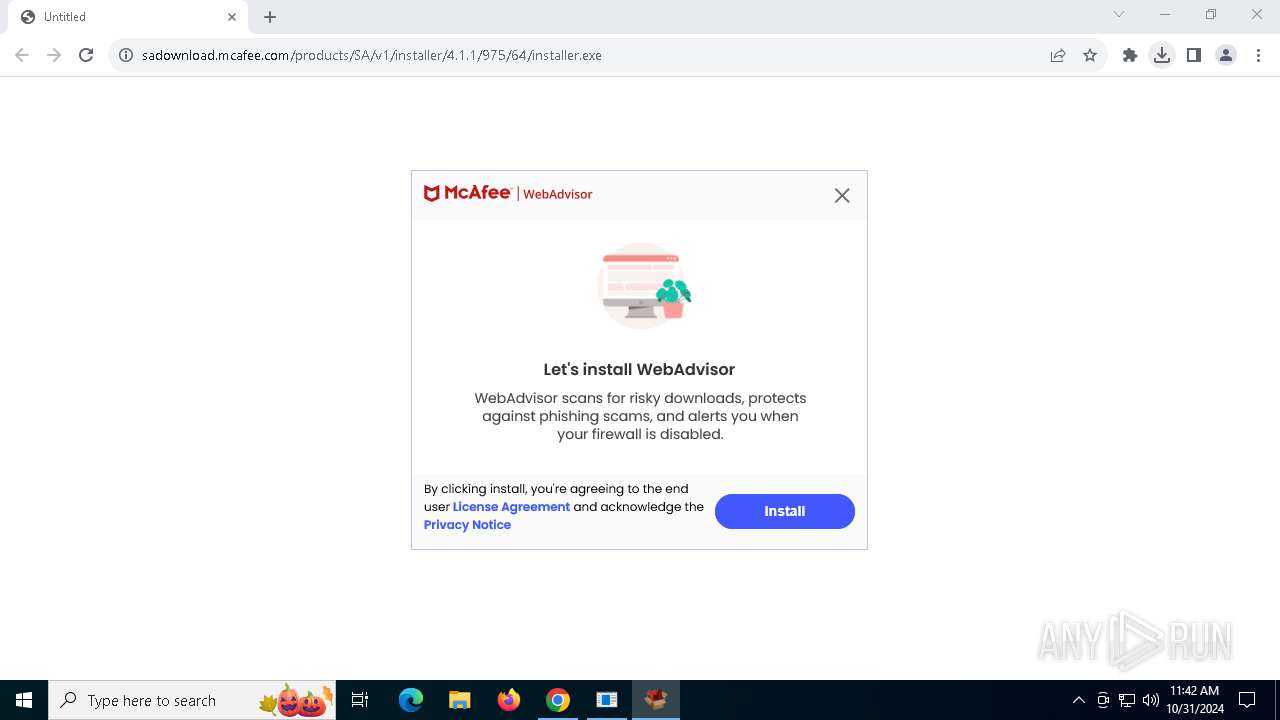
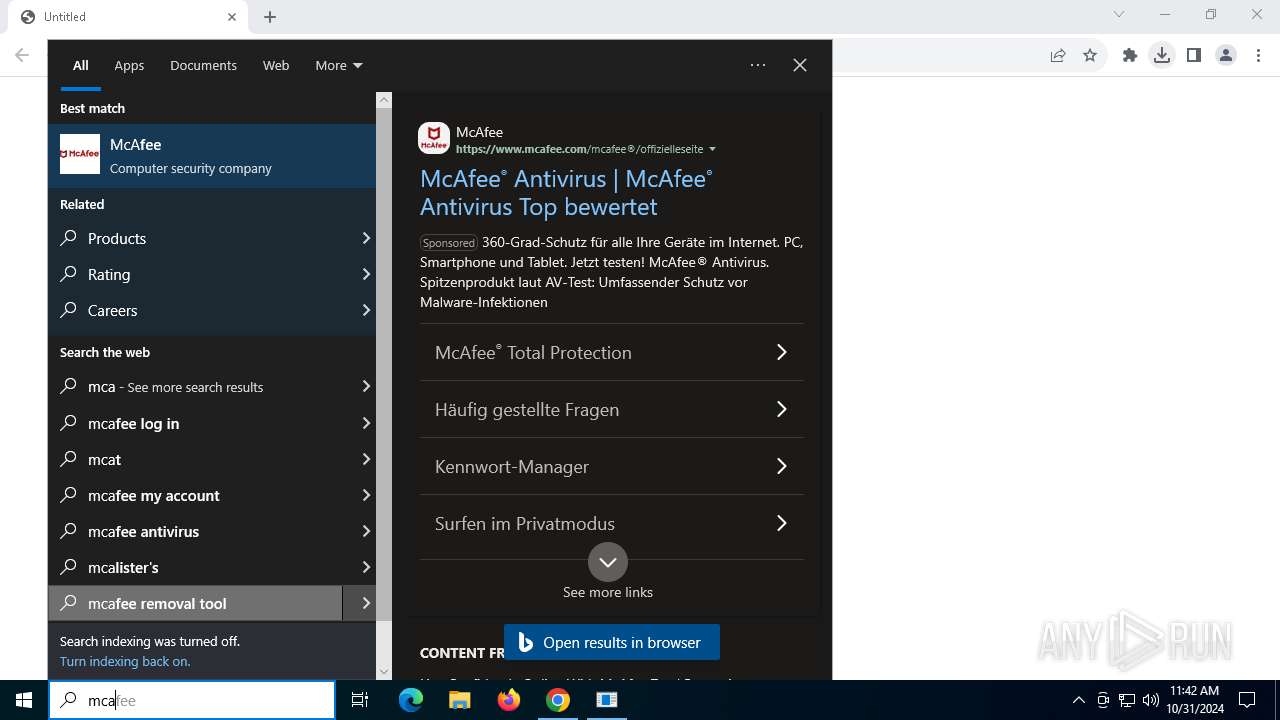
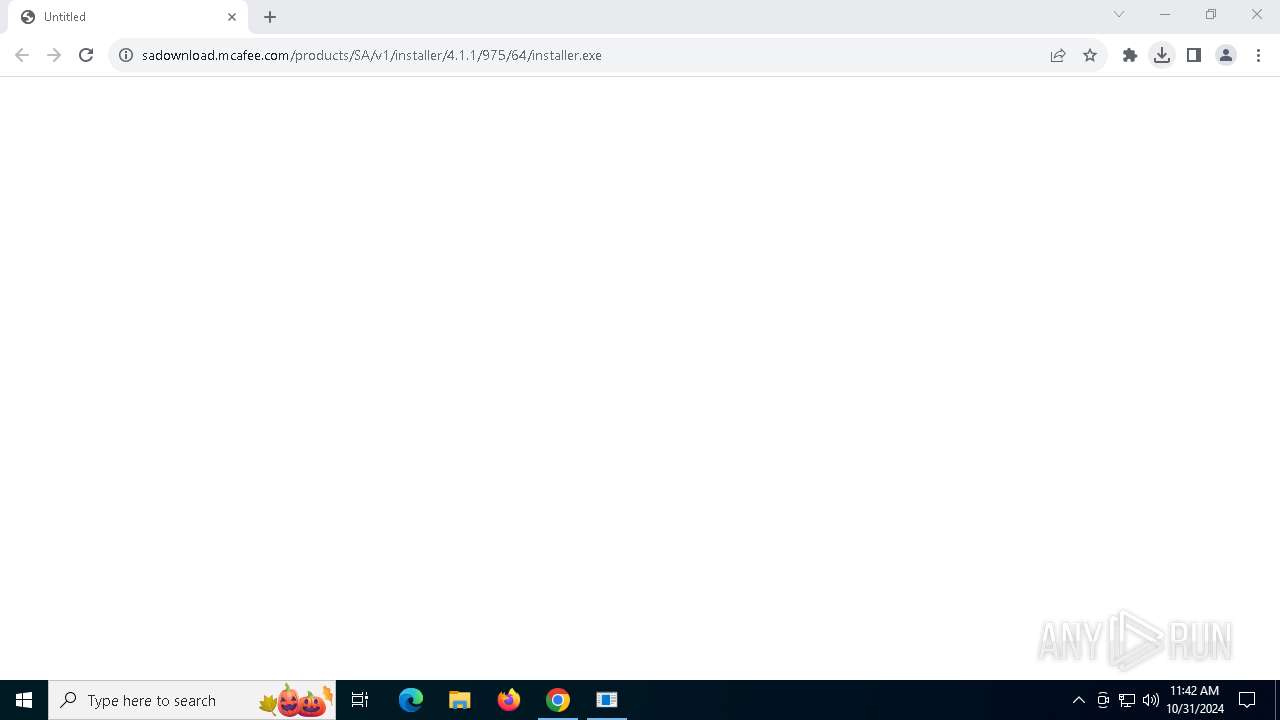
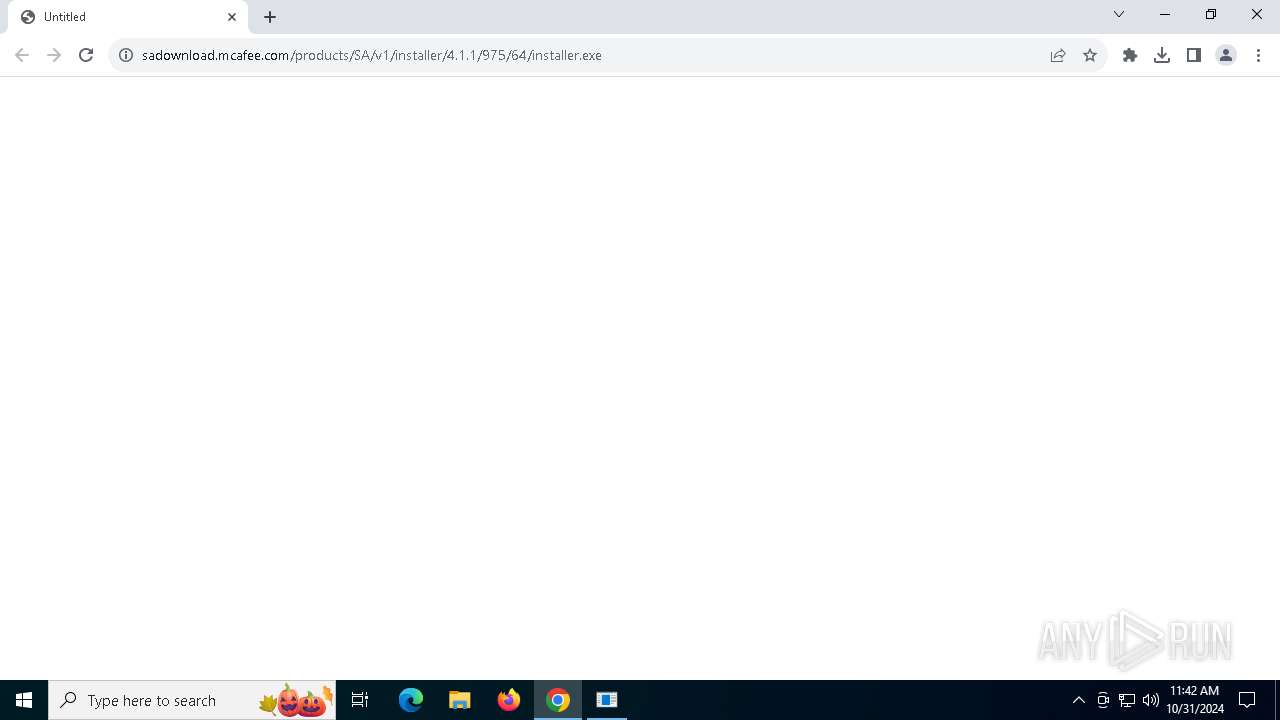
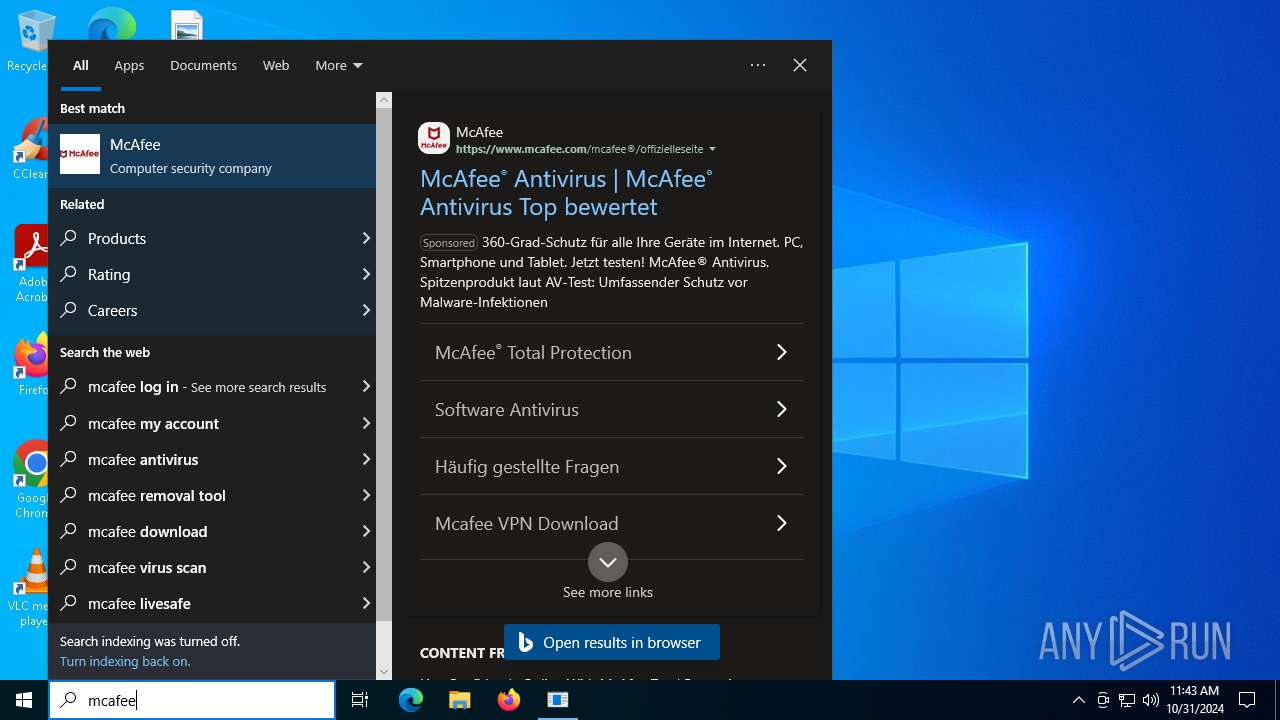
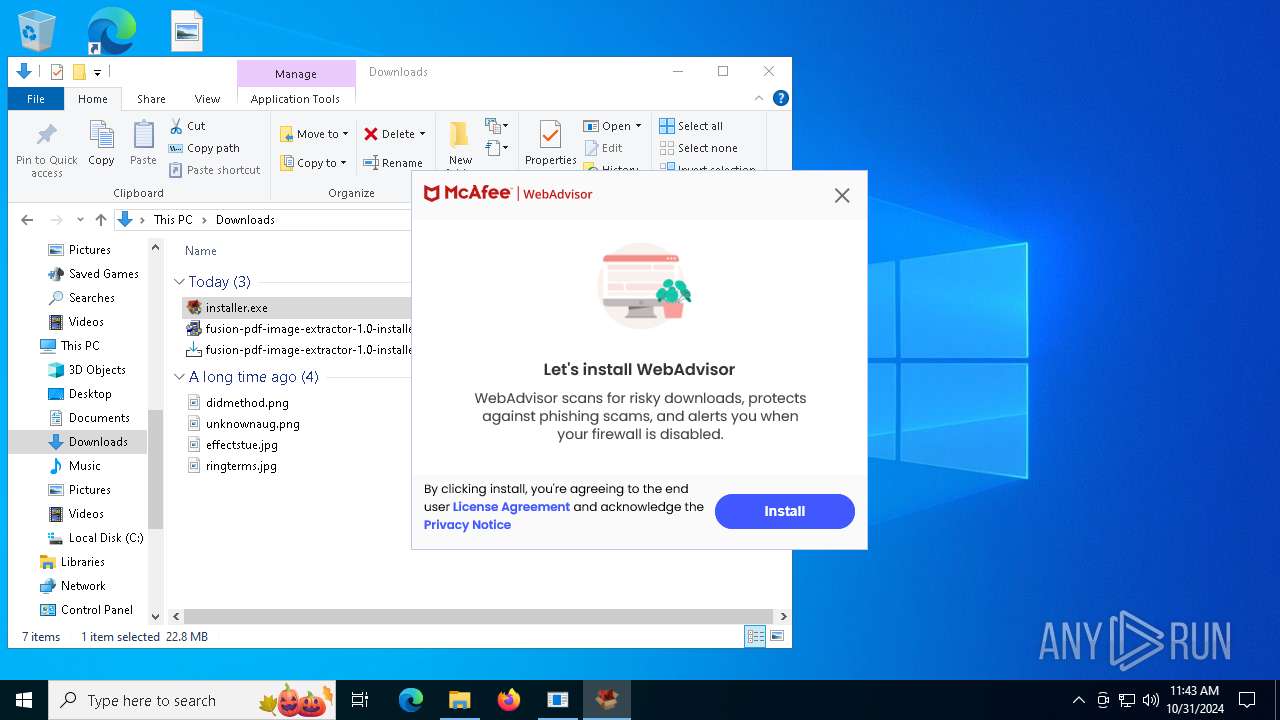
| 2888 | "C:\Program Files\McAfee\Temp42018143\installer.exe" /setOem:Affid=91082 /s /thirdparty /upgrade | C:\Program Files\McAfee\Temp42018143\installer.exe | installer.exe | ||||||||||||
User: admin Company: McAfee, LLC Integrity Level: HIGH Description: McAfee WebAdvisor(installer) Exit code: 0 Version: 4,1,1,975 | |||||||||||||||
| 3620 | C:\WINDOWS\system32\cmd.exe /c dir "C:\Program Files (x86)\McAfee Security Scan" 2>nul | C:\Windows\System32\cmd.exe | — | servicehost.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows Command Processor Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) | |||||||||||||||
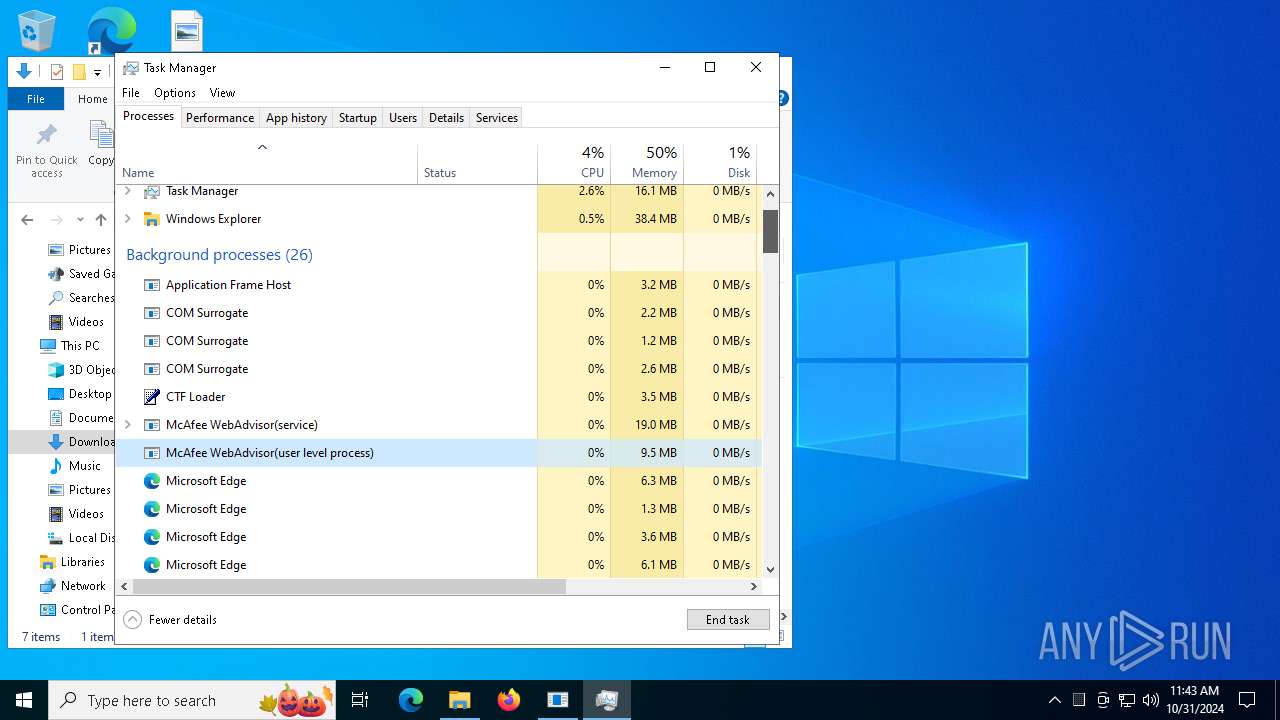
| 3952 | "C:\Program Files\McAfee\WebAdvisor\UIHost.exe" | C:\Program Files\McAfee\WebAdvisor\uihost.exe | — | servicehost.exe | |||||||||||
User: admin Company: McAfee, LLC Integrity Level: MEDIUM Description: McAfee WebAdvisor(user level process) Version: 4,1,1,975 | |||||||||||||||
Total events
4 880
Read events
4 874
Write events
6
Delete events
0
Modification events
| (PID) Process: | (4060) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (4060) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (4060) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (4060) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\StabilityMetrics |
| Operation: | write | Name: | user_experience_metrics.stability.exited_cleanly |
Value: 0 | |||
| (PID) Process: | (4060) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
| (PID) Process: | (5980) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Shell Extensions\Cached |
| Operation: | write | Name: | {2781761E-28E0-4109-99FE-B9D127C57AFE} {56FFCC30-D398-11D0-B2AE-00A0C908FA49} 0xFFFF |
Value: 01000000000000007882D68B892BDB01 | |||
Executable files
51
Suspicious files
458
Text files
1 190
Unknown types
227
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 4060 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\PersistentOriginTrials\LOG.old~RF8c695.TMP | — | |
MD5:— | SHA256:— | |||
| 4060 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\PersistentOriginTrials\LOG.old | — | |
MD5:— | SHA256:— | |||
| 4060 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\chrome_cart_db\LOG.old~RF8c6b4.TMP | — | |
MD5:— | SHA256:— | |||
| 4060 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\discounts_db\LOG.old~RF8c6b4.TMP | — | |
MD5:— | SHA256:— | |||
| 4060 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\commerce_subscription_db\LOG.old~RF8c6b4.TMP | — | |
MD5:— | SHA256:— | |||
| 4060 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\discounts_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 4060 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 4060 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\chrome_cart_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 4060 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\coupon_db\LOG.old~RF8c6c3.TMP | — | |
MD5:— | SHA256:— | |||
| 4060 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\coupon_db\LOG.old | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
46
TCP/UDP connections
135
DNS requests
116
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
— | — | GET | 200 | 23.48.23.176:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
— | — | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
— | — | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAI5PUjXAkJafLQcAAsO18o%3D | unknown | — | — | whitelisted |
— | — | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTfIs%2BLjDtGwQ09XEB1Yeq%2BtX%2BBgQQU7NfjgtJxXWRM3y5nP%2Be6mK4cD08CEAitQLJg0pxMn17Nqb2Trtk%3D | unknown | — | — | whitelisted |
— | — | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
— | — | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSRXerF0eFeSWRripTgTkcJWMm7iQQUaDfg67Y7%2BF8Rhvv%2BYXsIiGX0TkICEApJaqM%2Bmgz234UUEUR6Zyc%3D | unknown | — | — | whitelisted |
— | — | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
— | — | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
— | — | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAn5bsKVVV8kdJ6vHl3O1J0%3D | unknown | — | — | whitelisted |
— | — | GET | 200 | 184.30.21.171:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
6944 | svchost.exe | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
— | — | 192.168.100.255:137 | — | — | — | whitelisted |
5488 | MoUsoCoreWorker.exe | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
— | — | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
— | — | 23.48.23.176:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
— | — | 184.30.21.171:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
— | — | 52.222.190.41:443 | d552lcnlgbcqg.cloudfront.net | AMAZON-02 | US | whitelisted |
— | — | 239.255.255.250:1900 | — | — | — | whitelisted |
— | — | 142.251.31.84:443 | accounts.google.com | GOOGLE | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
d552lcnlgbcqg.cloudfront.net |
| whitelisted |
accounts.google.com |
| whitelisted |
www.bing.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
sb-ssl.google.com |
| whitelisted |
login.live.com |
| whitelisted |