| File name: | GeForceNow.exe |
| Full analysis: | https://app.any.run/tasks/56dc9c1e-41ce-468e-a053-ab888c06a6dd |
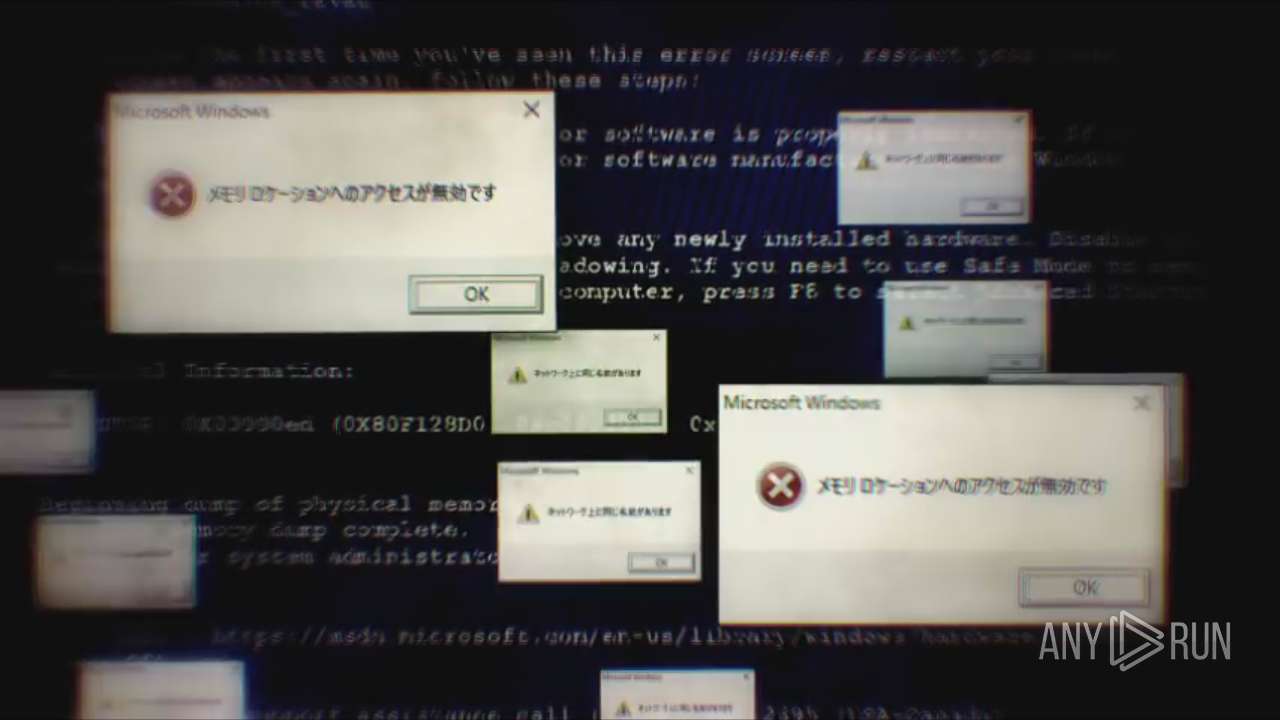
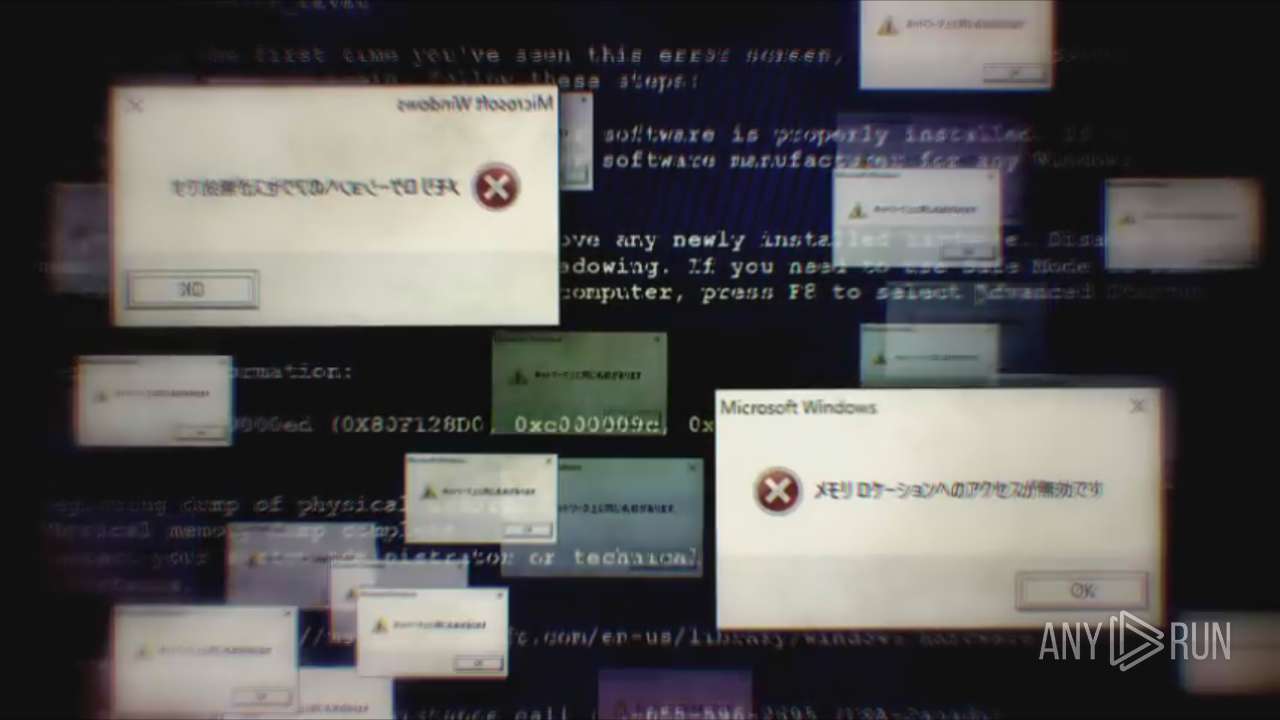
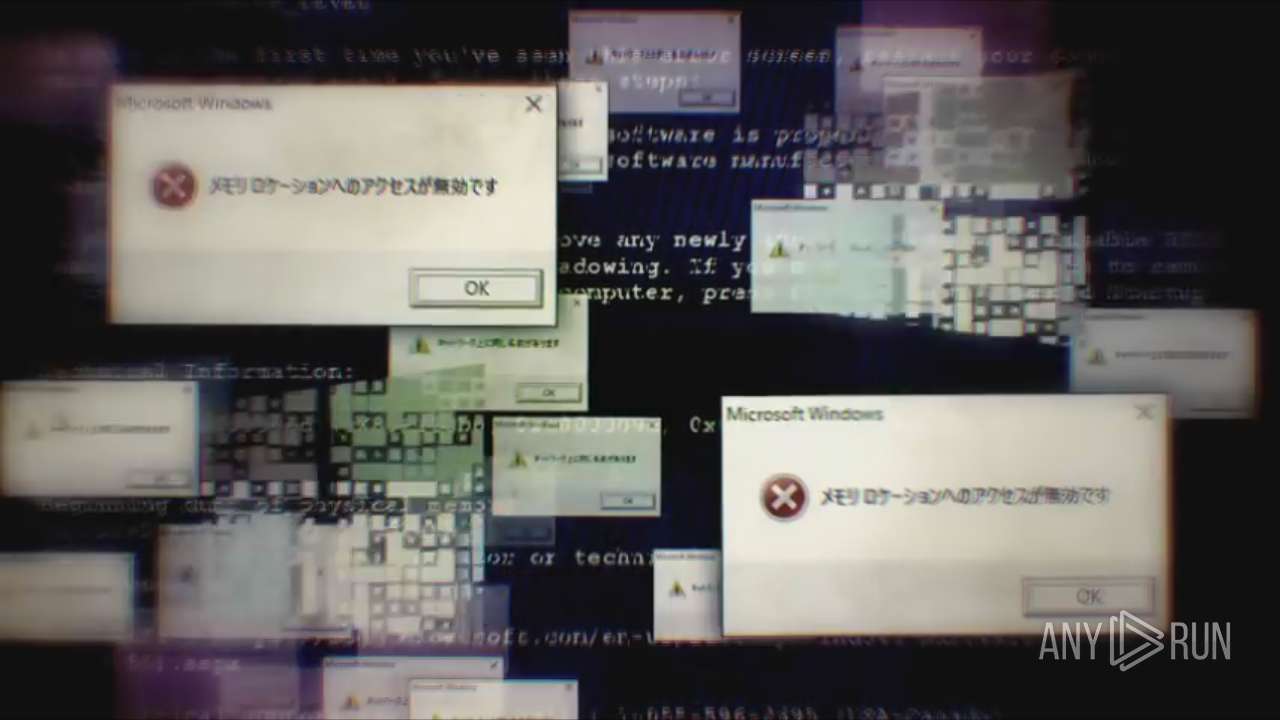
| Verdict: | Malicious activity |
| Analysis date: | December 06, 2022, 04:29:52 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386 Mono/.Net assembly, for MS Windows |
| MD5: | FD2C1F69F7E4ABD27519B30E858A7A71 |
| SHA1: | E4CD6DCD27AB5483BF36CD010F75E4B3AB400277 |
| SHA256: | 64FEA8D763D01854992B22766BF21DA7B63FFA4F87D319FF27EB56CC27E589C2 |
| SSDEEP: | 98304:VyDt6K4MJVnjOobt/JN1LA5elHc+S4fRp5UvluK:VyDtK8bbxn+IHcBEV/ |
MALICIOUS
No malicious indicators.SUSPICIOUS
Reads the Internet Settings
- GeForceNow.exe (PID: 1328)
INFO
Reads the computer name
- GeForceNow.exe (PID: 1328)
Checks supported languages
- GeForceNow.exe (PID: 1328)
Checks proxy server information
- GeForceNow.exe (PID: 1328)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Generic CIL Executable (.NET, Mono, etc.) (72.2) |
|---|---|---|
| .scr | | | Windows screen saver (12.9) |
| .dll | | | Win32 Dynamic Link Library (generic) (6.4) |
| .exe | | | Win32 Executable (generic) (4.4) |
| .exe | | | Generic Win/DOS Executable (1.9) |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 2016-Sep-10 17:32:23 |
| Debug artifacts: |
|
| Comments: | - |
| CompanyName: | GAMELASTER |
| FileDescription: | ChilledWindows |
| FileVersion: | 1.0.0.0 |
| InternalName: | ChilledWindows.exe |
| LegalCopyright: | Copyright © GAMELASTER 2016 |
| LegalTrademarks: | - |
| OriginalFilename: | ChilledWindows.exe |
| ProductName: | ChilledWindows |
| ProductVersion: | 1.0.0.0 |
| Assembly Version: | 1.0.0.0 |
DOS Header
| e_magic: | MZ |
|---|---|
| e_cblp: | 144 |
| e_cp: | 3 |
| e_crlc: | - |
| e_cparhdr: | 4 |
| e_minalloc: | - |
| e_maxalloc: | 65535 |
| e_ss: | - |
| e_sp: | 184 |
| e_csum: | - |
| e_ip: | - |
| e_cs: | - |
| e_ovno: | - |
| e_oemid: | - |
| e_oeminfo: | - |
| e_lfanew: | 128 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| NumberofSections: | 3 |
| TimeDateStamp: | 2016-Sep-10 17:32:23 |
| PointerToSymbolTable: | - |
| NumberOfSymbols: | - |
| SizeOfOptionalHeader: | 224 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 8192 | 4399908 | 4400128 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 7.95766 |
.rsrc | 4415488 | 13266 | 13312 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 7.73 |
.reloc | 4431872 | 12 | 512 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_DISCARDABLE, IMAGE_SCN_MEM_READ | 0.10191 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 7.94675 | 11568 | UNKNOWN | UNKNOWN | RT_ICON |
32512 | 1.51664 | 20 | UNKNOWN | UNKNOWN | RT_GROUP_ICON |
1 (#2) | 3.33192 | 884 | UNKNOWN | UNKNOWN | RT_VERSION |
1 (#3) | 5.00112 | 490 | UNKNOWN | UNKNOWN | RT_MANIFEST |
Imports
mscoree.dll |
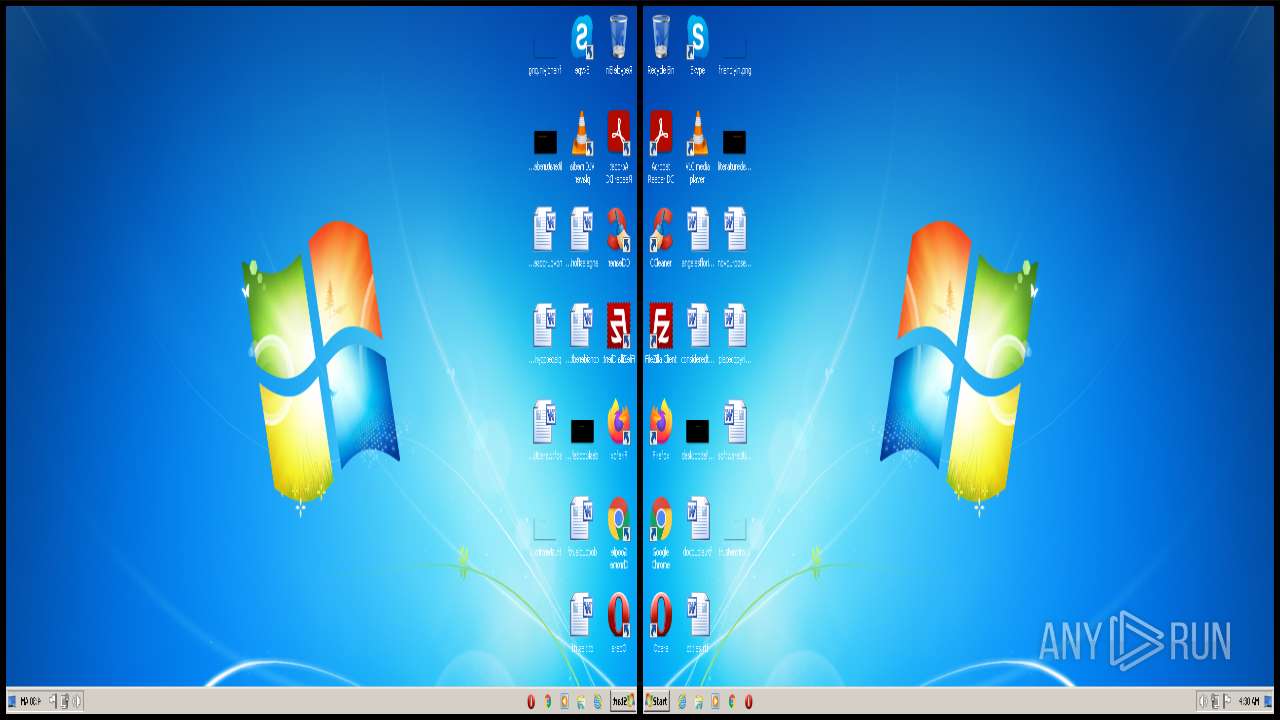
Total processes
38
Monitored processes
3
Malicious processes
1
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1328 | "C:\Users\admin\AppData\Local\Temp\GeForceNow.exe" | C:\Users\admin\AppData\Local\Temp\GeForceNow.exe | — | Explorer.EXE | |||||||||||
User: admin Company: GAMELASTER Integrity Level: MEDIUM Description: ChilledWindows Exit code: 3221225547 Version: 1.0.0.0 Modules
| |||||||||||||||
| 2924 | "C:\Windows\SYSTEM32\WISPTIS.EXE" /ManualLaunch; | C:\Windows\SYSTEM32\WISPTIS.EXE | — | GeForceNow.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Pen and Touch Input Component Exit code: 3221226540 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3432 | "C:\Windows\SYSTEM32\WISPTIS.EXE" /ManualLaunch; | C:\Windows\SYSTEM32\WISPTIS.EXE | GeForceNow.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft Pen and Touch Input Component Exit code: 24 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
1 535
Read events
1 470
Write events
64
Delete events
1
Modification events
| (PID) Process: | (1328) GeForceNow.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Direct3D\MostRecentApplication |
| Operation: | write | Name: | Name |
Value: GeForceNow.exe | |||
| (PID) Process: | (1328) GeForceNow.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (1328) GeForceNow.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
| (PID) Process: | (1328) GeForceNow.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 1 | |||
| (PID) Process: | (1328) GeForceNow.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 0 | |||
| (PID) Process: | (3432) WISPTIS.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Direct3D\MostRecentApplication |
| Operation: | write | Name: | Name |
Value: WISPTIS.EXE | |||
| (PID) Process: | (3432) WISPTIS.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Wisp\Touch |
| Operation: | write | Name: | TouchGate |
Value: 1 | |||
| (PID) Process: | (3432) WISPTIS.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Wisp\MultiTouch |
| Operation: | write | Name: | MultiTouchEnabled |
Value: 1 | |||
| (PID) Process: | (3432) WISPTIS.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Wisp\Pen\SysEventParameters |
| Operation: | write | Name: | FlickMode |
Value: 1 | |||
| (PID) Process: | (3432) WISPTIS.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Wisp\Pen\SysEventParameters |
| Operation: | write | Name: | TouchFlickTolerance |
Value: 50 | |||
Executable files
0
Suspicious files
1
Text files
0
Unknown types
1
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1328 | GeForceNow.exe | C:\Users\admin\AppData\Local\Microsoft\Media Player\CurrentDatabase_372.wmdb | binary | |
MD5:4269D0A30E37B26F401184AB6D204330 | SHA256:3628B1849B3FB93FA7A7DE280D96CFF1AC285C99774BA722C60C01027A3D9E4B | |||
| 1328 | GeForceNow.exe | C:\Users\admin\AppData\Local\Temp\chilledwindows.mp4 | m4v | |
MD5:698DDCAEC1EDCF1245807627884EDF9C | SHA256:CDE975F975D21EDB2E5FAA505205AB8A2C5A565BA1FF8585D1F0E372B2A1D78B | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
0
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report