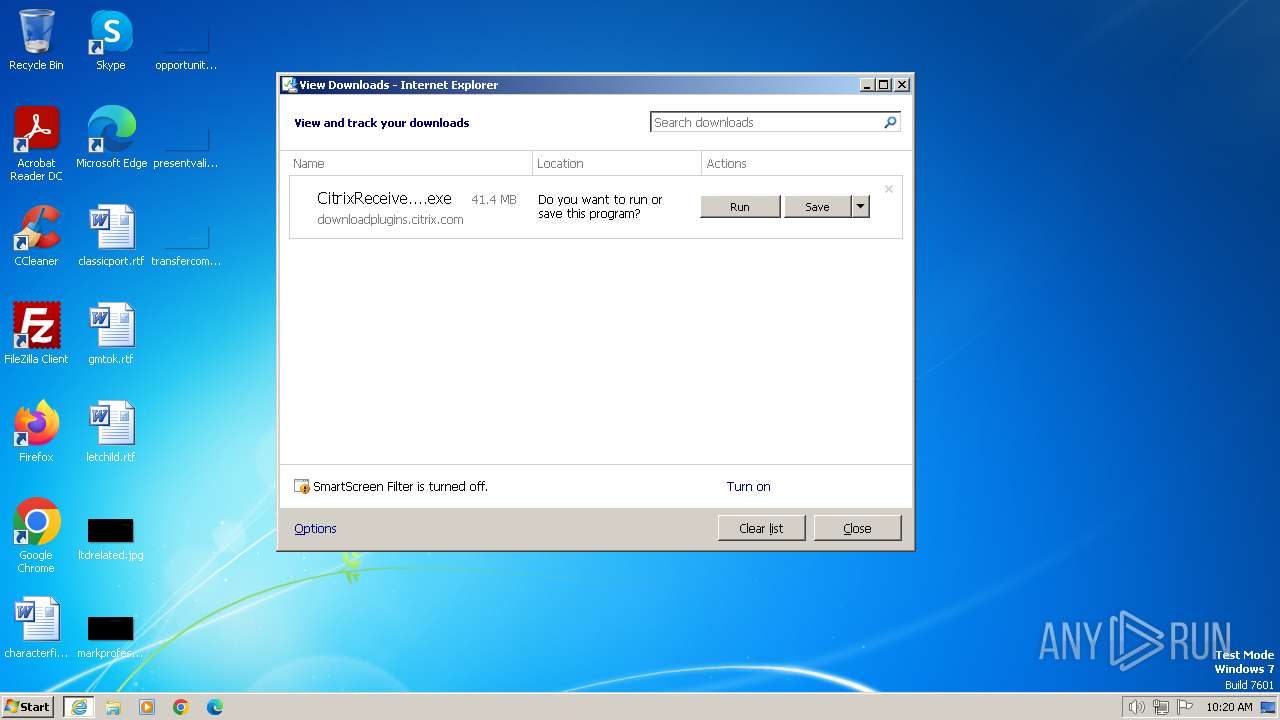
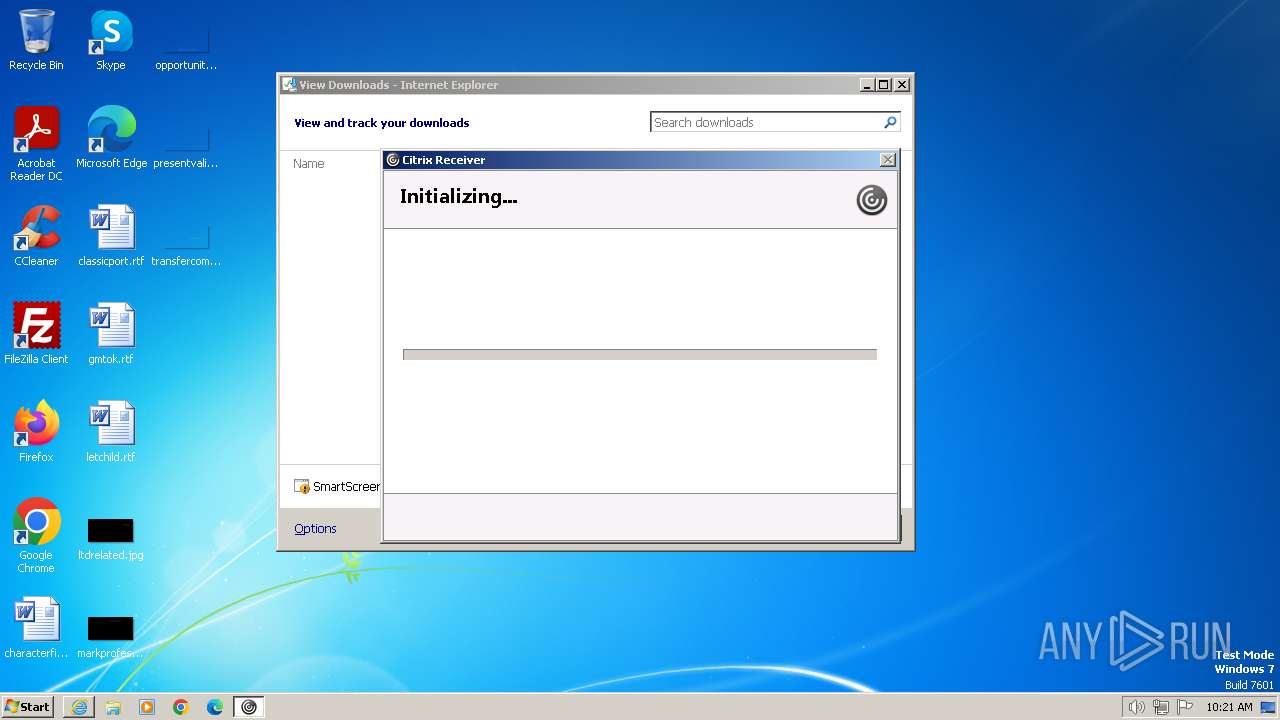
| URL: | http://downloadplugins.citrix.com/Windows/CitrixReceiverWeb.exe |
| Full analysis: | https://app.any.run/tasks/7c7db177-5e45-4222-bd3a-2659f76b92c2 |
| Verdict: | Malicious activity |
| Threats: | A loader is malicious software that infiltrates devices to deliver malicious payloads. This malware is capable of infecting victims’ computers, analyzing their system information, and installing other types of threats, such as trojans or stealers. Criminals usually deliver loaders through phishing emails and links by relying on social engineering to trick users into downloading and running their executables. Loaders employ advanced evasion and persistence tactics to avoid detection. |
| Analysis date: | December 21, 2023, 10:20:07 |
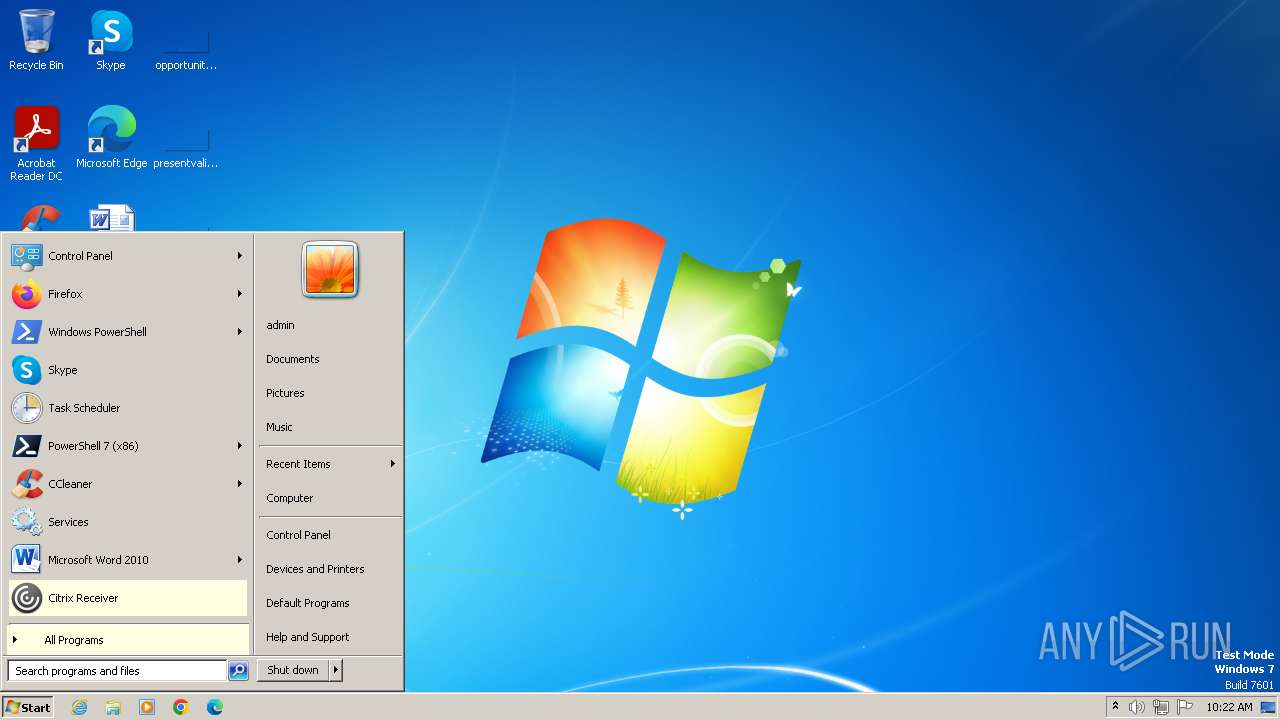
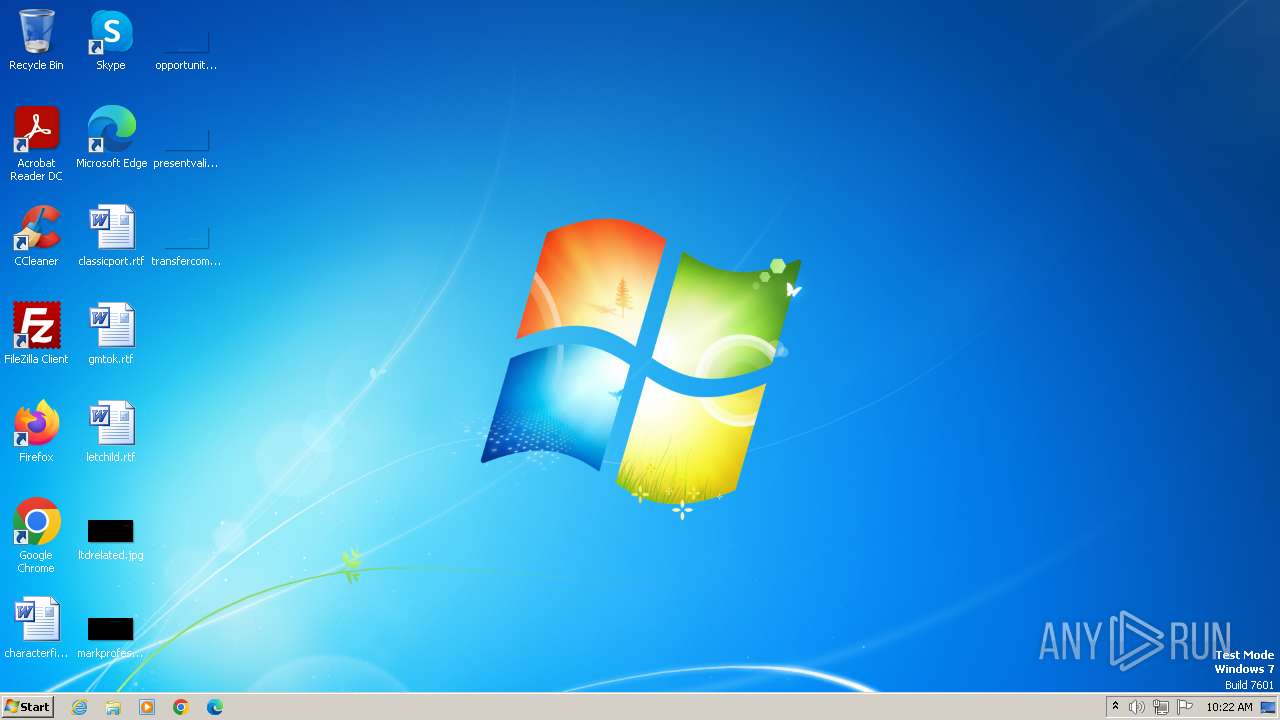
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MD5: | 9BE28B9BC97F70BEB3360D24AD8A6D70 |
| SHA1: | 78922A9C0769F36A61F84708EB29B49124B3D29E |
| SHA256: | 64F05A48E42A266032FEEEF41BB63ABC537F422609CC25F47A1090C246485054 |
| SSDEEP: | 3:N1KaKE7eDQXMJGTKjDLGArAC:CanRqKKjDTp |
MALICIOUS
Creates a writable file in the system directory
- DXSETUP.exe (PID: 1384)
- drvinst.exe (PID: 1820)
- usbinst.exe (PID: 664)
- drvinst.exe (PID: 2516)
Actions looks like stealing of personal data
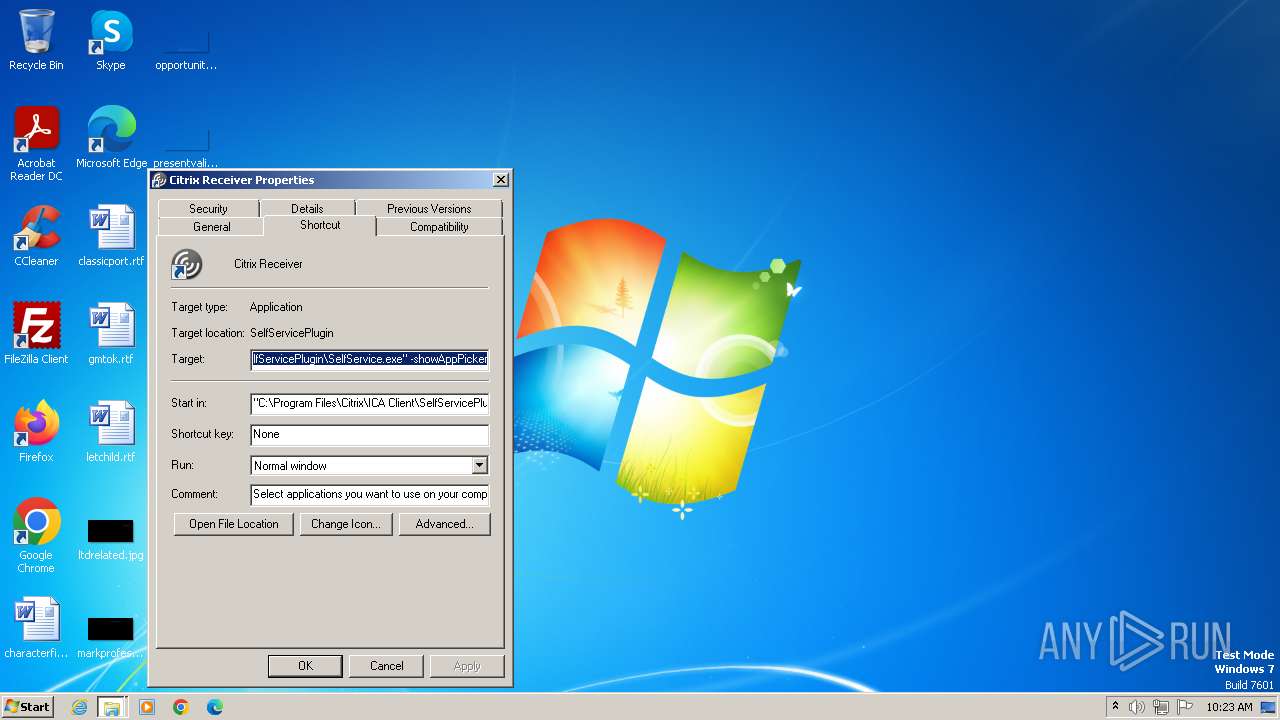
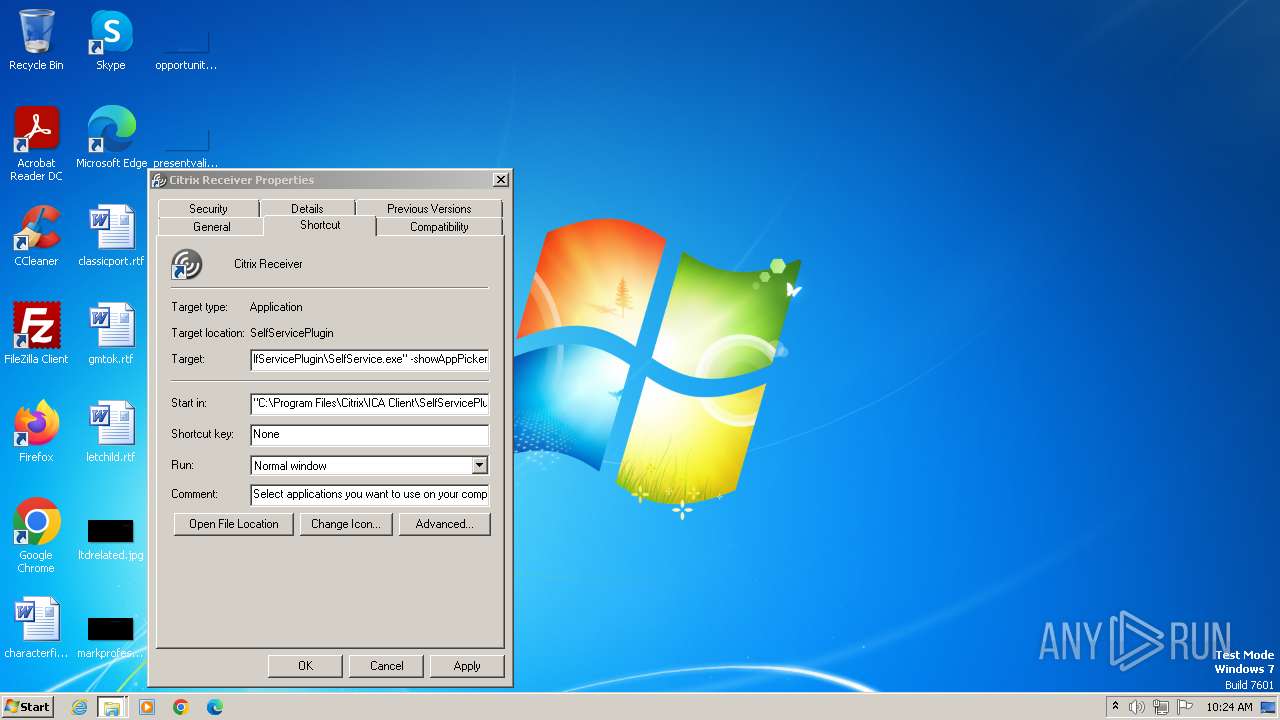
- SelfService.exe (PID: 2956)
SUSPICIOUS
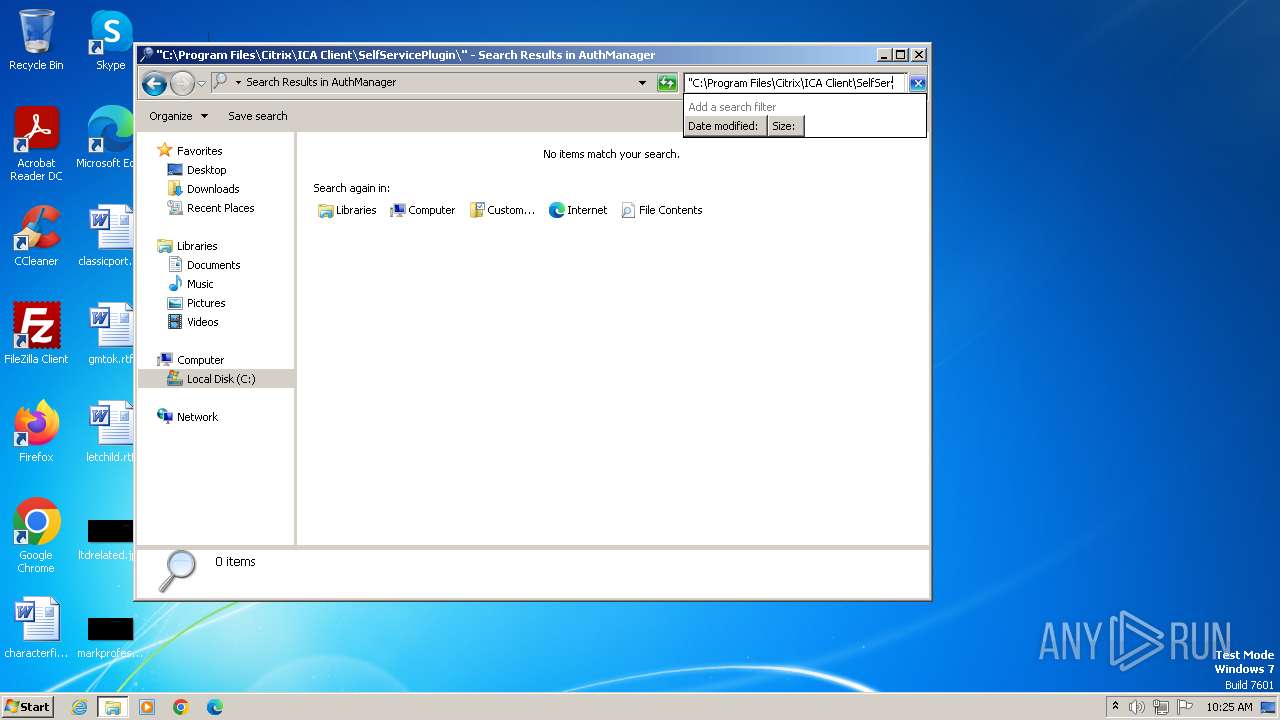
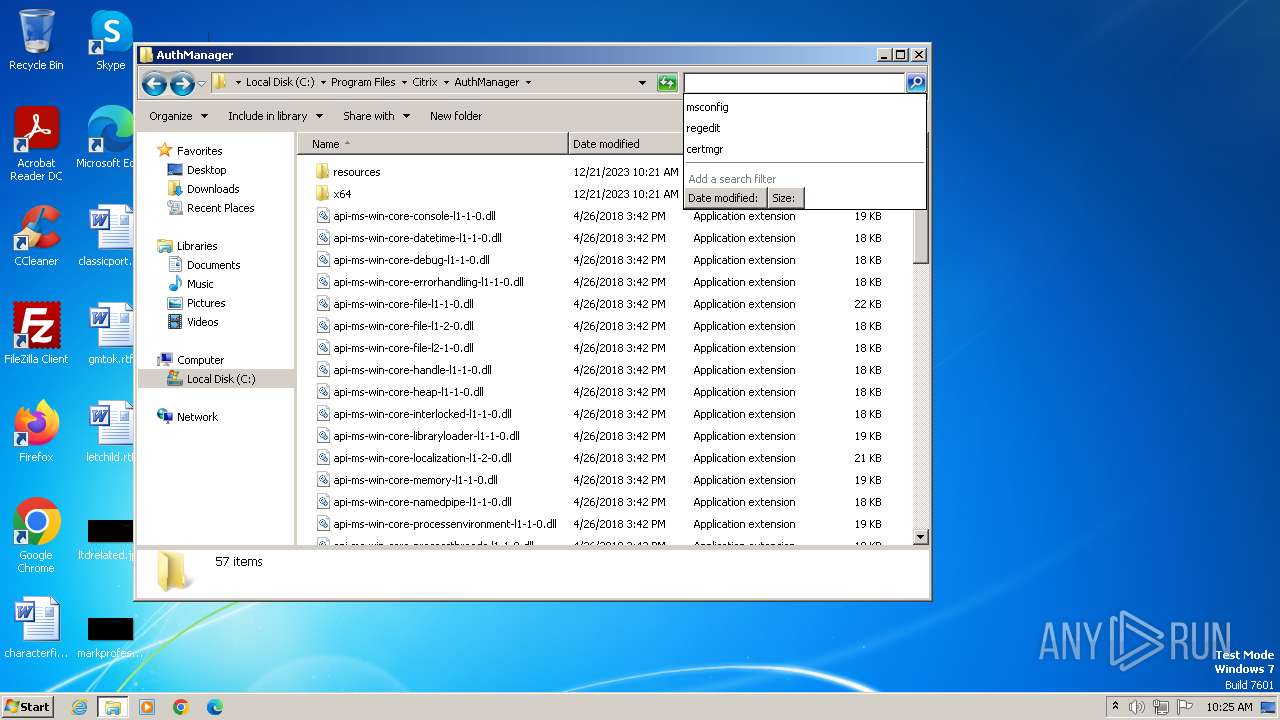
Searches for installed software
- TrolleyExpress.exe (PID: 1540)
- DXSETUP.exe (PID: 1384)
- dllhost.exe (PID: 2452)
- SelfService.exe (PID: 3896)
Reads the Windows owner or organization settings
- TrolleyExpress.exe (PID: 1540)
- msiexec.exe (PID: 2448)
Reads the Internet Settings
- CitrixReceiverWeb.exe (PID: 1780)
- Receiver.exe (PID: 3084)
- concentr.exe (PID: 3320)
- SelfServicePlugin.exe (PID: 3312)
Reads settings of System Certificates
- DXSETUP.exe (PID: 1384)
Reads security settings of Internet Explorer
- DXSETUP.exe (PID: 1384)
Checks Windows Trust Settings
- DXSETUP.exe (PID: 1384)
- msiexec.exe (PID: 2448)
- drvinst.exe (PID: 1820)
- drvinst.exe (PID: 2516)
Changes default file association
- msiexec.exe (PID: 2448)
Uses RUNDLL32.EXE to load library
- msiexec.exe (PID: 2448)
Drops a system driver (possible attempt to evade defenses)
- msiexec.exe (PID: 2448)
- drvinst.exe (PID: 1820)
- usbinst.exe (PID: 664)
- usbinst.exe (PID: 1748)
- usbinst.exe (PID: 3804)
- drvinst.exe (PID: 2516)
Creates files in the driver directory
- drvinst.exe (PID: 1820)
- drvinst.exe (PID: 2516)
- usbinst.exe (PID: 664)
INFO
The process uses the downloaded file
- iexplore.exe (PID: 2184)
Drops the executable file immediately after the start
- iexplore.exe (PID: 864)
- CitrixReceiverWeb.exe (PID: 1780)
- DXSETUP.exe (PID: 1384)
- drvinst.exe (PID: 1820)
- msiexec.exe (PID: 2448)
- usbinst.exe (PID: 1748)
- usbinst.exe (PID: 3804)
- usbinst.exe (PID: 664)
- drvinst.exe (PID: 2516)
- TrolleyExpress.exe (PID: 1540)
Create files in a temporary directory
- CitrixReceiverWeb.exe (PID: 1780)
- TrolleyExpress.exe (PID: 1540)
- msiexec.exe (PID: 2448)
- DXSETUP.exe (PID: 1384)
- Receiver.exe (PID: 3084)
- wfcrun32.exe (PID: 1380)
- usbinst.exe (PID: 1748)
- usbinst.exe (PID: 3804)
- SelfService.exe (PID: 2956)
- SelfServicePlugin.exe (PID: 3312)
- SelfService.exe (PID: 3896)
Application launched itself
- iexplore.exe (PID: 2184)
- msiexec.exe (PID: 2448)
Process drops legitimate windows executable
- CitrixReceiverWeb.exe (PID: 1780)
- DXSETUP.exe (PID: 1384)
- msiexec.exe (PID: 2448)
- usbinst.exe (PID: 3804)
- drvinst.exe (PID: 2516)
- TrolleyExpress.exe (PID: 1540)
Checks supported languages
- TrolleyExpress.exe (PID: 1540)
- CitrixReceiverWeb.exe (PID: 1780)
- msiexec.exe (PID: 2448)
- DXSETUP.exe (PID: 1384)
- msiexec.exe (PID: 2836)
- msiexec.exe (PID: 3156)
- msiexec.exe (PID: 3180)
- icaconf.exe (PID: 3268)
- SetIntegrityLevel.exe (PID: 3304)
- SetIntegrityLevel.exe (PID: 2812)
- concentr.exe (PID: 3320)
- redirector.exe (PID: 3252)
- Receiver.exe (PID: 3084)
- ConfigurationWizard.exe (PID: 3516)
- wfcrun32.exe (PID: 1380)
- concentr.exe (PID: 2016)
- msiexec.exe (PID: 712)
- usbinst.exe (PID: 1748)
- drvinst.exe (PID: 1820)
- usbinst.exe (PID: 664)
- drvinst.exe (PID: 2516)
- usbinst.exe (PID: 3804)
- msiexec.exe (PID: 3060)
- msiexec.exe (PID: 1584)
- msiexec.exe (PID: 3024)
- msiexec.exe (PID: 2732)
- msiexec.exe (PID: 2728)
- msiexec.exe (PID: 3104)
- SelfService.exe (PID: 2956)
- SelfServicePlugin.exe (PID: 3312)
- SelfService.exe (PID: 3896)
- SelfService.exe (PID: 2444)
- SelfService.exe (PID: 3104)
Reads the computer name
- TrolleyExpress.exe (PID: 1540)
- msiexec.exe (PID: 2448)
- CitrixReceiverWeb.exe (PID: 1780)
- msiexec.exe (PID: 2836)
- DXSETUP.exe (PID: 1384)
- msiexec.exe (PID: 3156)
- SetIntegrityLevel.exe (PID: 3304)
- msiexec.exe (PID: 3180)
- ConfigurationWizard.exe (PID: 3516)
- Receiver.exe (PID: 3084)
- concentr.exe (PID: 3320)
- msiexec.exe (PID: 712)
- usbinst.exe (PID: 1748)
- wfcrun32.exe (PID: 1380)
- usbinst.exe (PID: 664)
- drvinst.exe (PID: 1820)
- drvinst.exe (PID: 2516)
- usbinst.exe (PID: 3804)
- msiexec.exe (PID: 3060)
- msiexec.exe (PID: 1584)
- msiexec.exe (PID: 2732)
- msiexec.exe (PID: 2728)
- msiexec.exe (PID: 3024)
- msiexec.exe (PID: 3104)
- SelfService.exe (PID: 2956)
- SelfServicePlugin.exe (PID: 3312)
- SelfService.exe (PID: 3896)
- SelfService.exe (PID: 2444)
- SelfService.exe (PID: 3104)
Reads the machine GUID from the registry
- TrolleyExpress.exe (PID: 1540)
- msiexec.exe (PID: 2448)
- DXSETUP.exe (PID: 1384)
- msiexec.exe (PID: 2836)
- msiexec.exe (PID: 3156)
- msiexec.exe (PID: 3180)
- Receiver.exe (PID: 3084)
- ConfigurationWizard.exe (PID: 3516)
- concentr.exe (PID: 3320)
- wfcrun32.exe (PID: 1380)
- msiexec.exe (PID: 712)
- drvinst.exe (PID: 1820)
- usbinst.exe (PID: 1748)
- drvinst.exe (PID: 2516)
- usbinst.exe (PID: 3804)
- msiexec.exe (PID: 3060)
- msiexec.exe (PID: 1584)
- msiexec.exe (PID: 2732)
- msiexec.exe (PID: 3024)
- msiexec.exe (PID: 2728)
- msiexec.exe (PID: 3104)
- SelfService.exe (PID: 2956)
- SelfServicePlugin.exe (PID: 3312)
- SelfService.exe (PID: 3896)
- SelfService.exe (PID: 2444)
- SelfService.exe (PID: 3104)
Process checks the number of cached credentials
- TrolleyExpress.exe (PID: 1540)
Executes as Windows Service
- VSSVC.exe (PID: 2428)
The process drops C-runtime libraries
- msiexec.exe (PID: 2448)
Creates files or folders in the user directory
- msiexec.exe (PID: 2448)
- Receiver.exe (PID: 3084)
- wfcrun32.exe (PID: 1380)
Reads CPU info
- Receiver.exe (PID: 3084)
- wfcrun32.exe (PID: 1380)
- SelfService.exe (PID: 2956)
- SelfServicePlugin.exe (PID: 3312)
- SelfService.exe (PID: 3896)
Reads the time zone
- Receiver.exe (PID: 3084)
- wfcrun32.exe (PID: 1380)
- runonce.exe (PID: 1376)
- SelfService.exe (PID: 2956)
- SelfServicePlugin.exe (PID: 3312)
- SelfService.exe (PID: 3896)
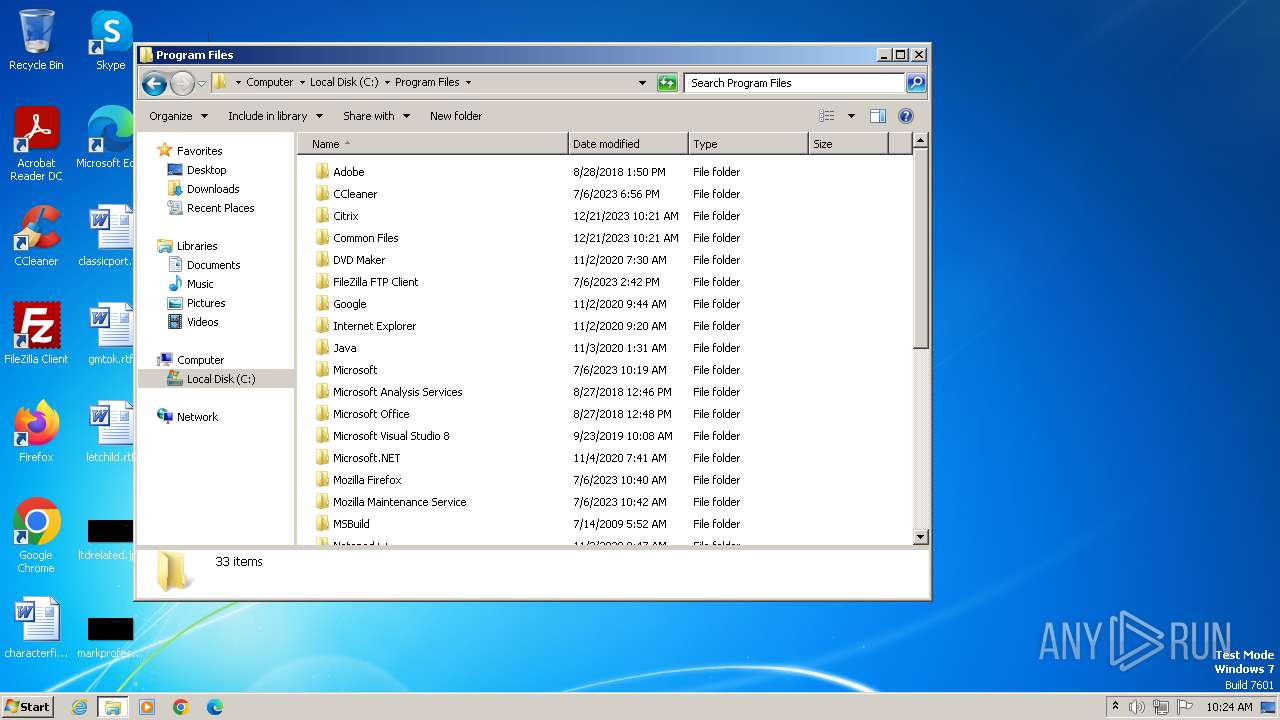
Creates files in the program directory
- Receiver.exe (PID: 3084)
- TrolleyExpress.exe (PID: 1540)
Reads Environment values
- msiexec.exe (PID: 3104)
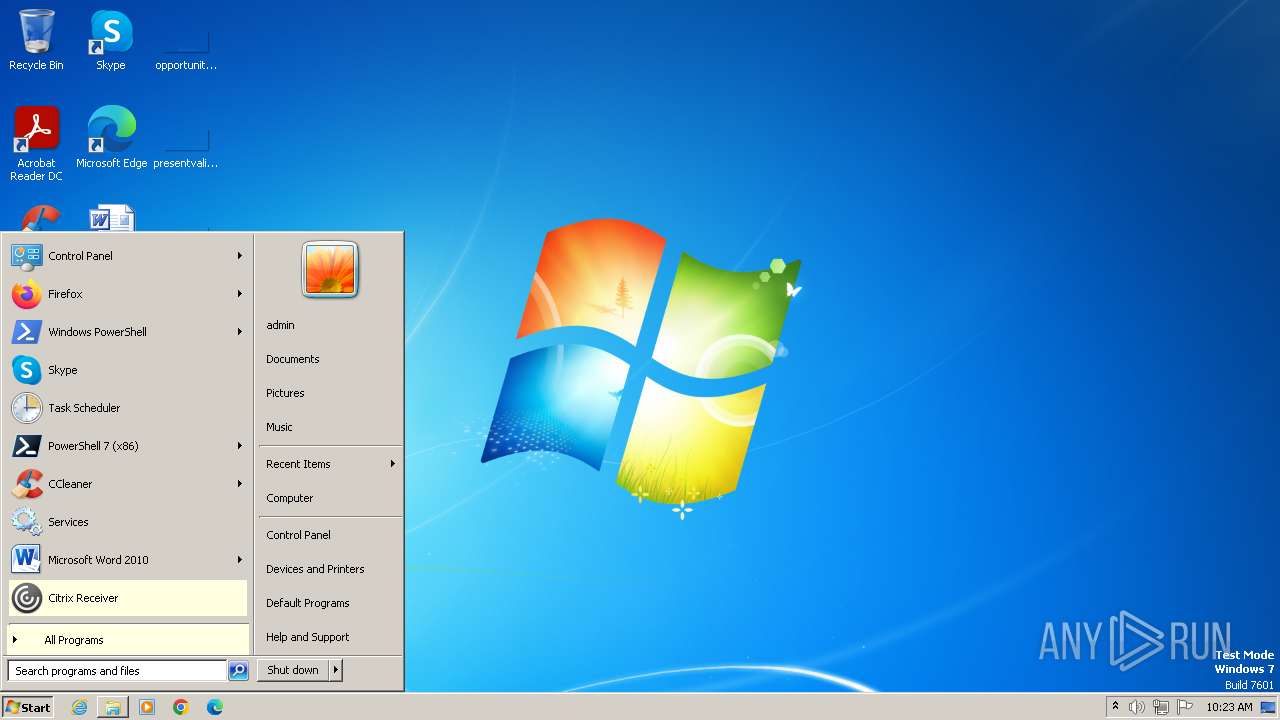
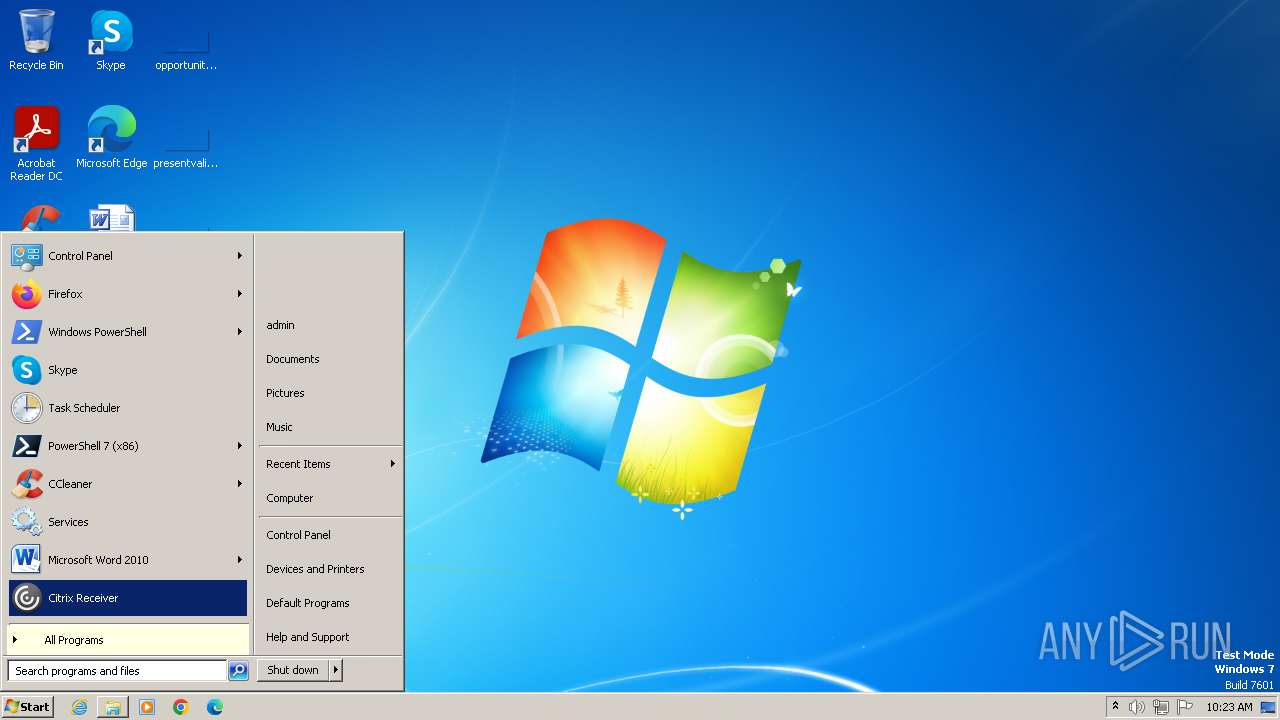
Manual execution by a user
- SelfService.exe (PID: 3896)
- SelfService.exe (PID: 2444)
- explorer.exe (PID: 2440)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
93
Monitored processes
43
Malicious processes
7
Suspicious processes
3
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
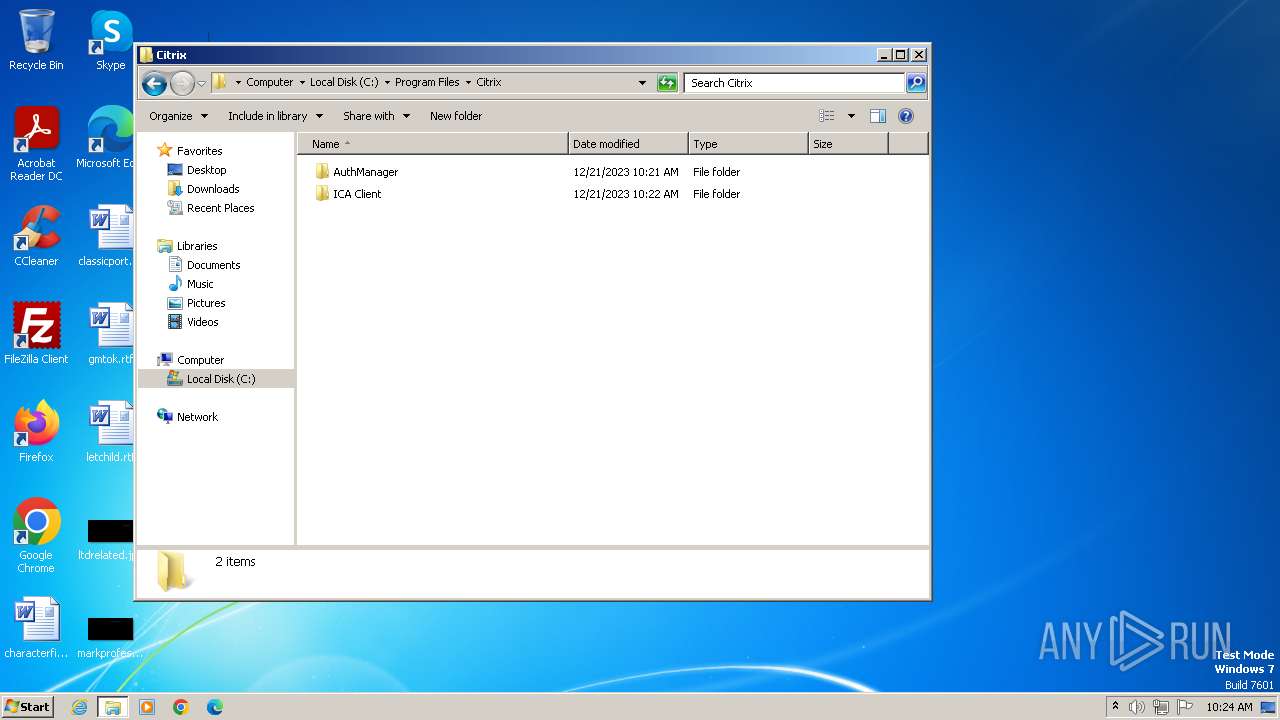
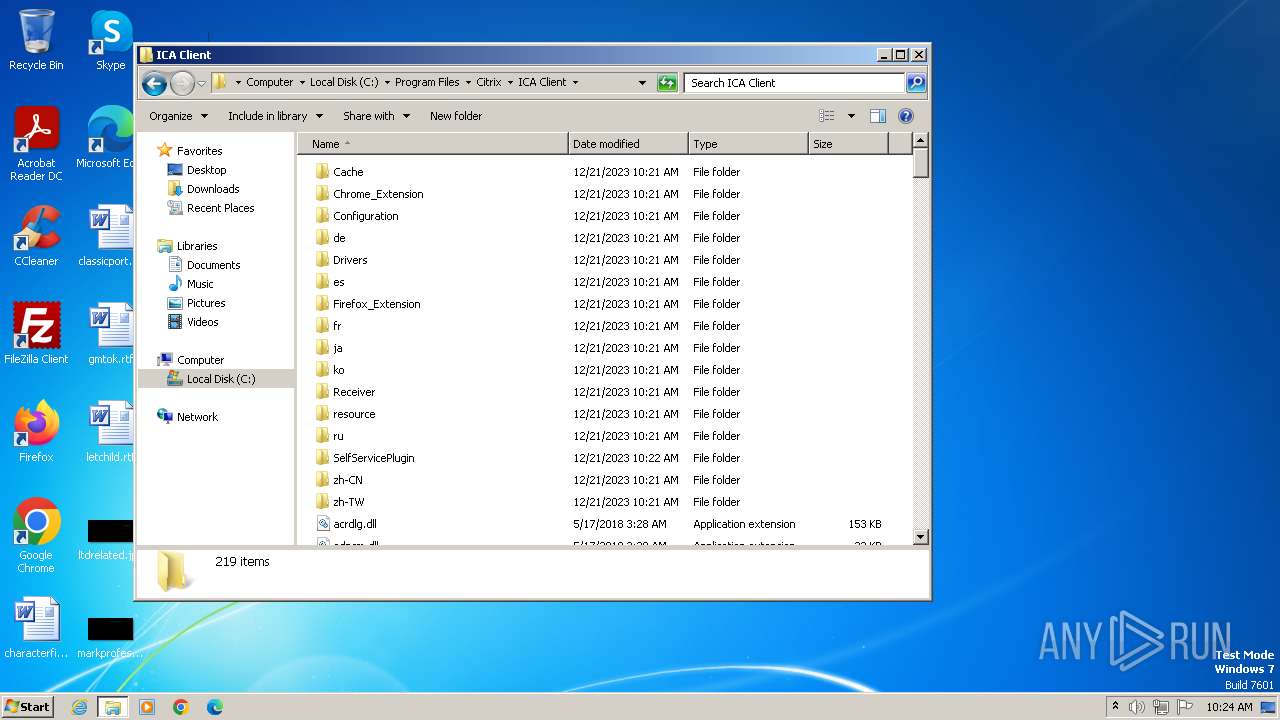
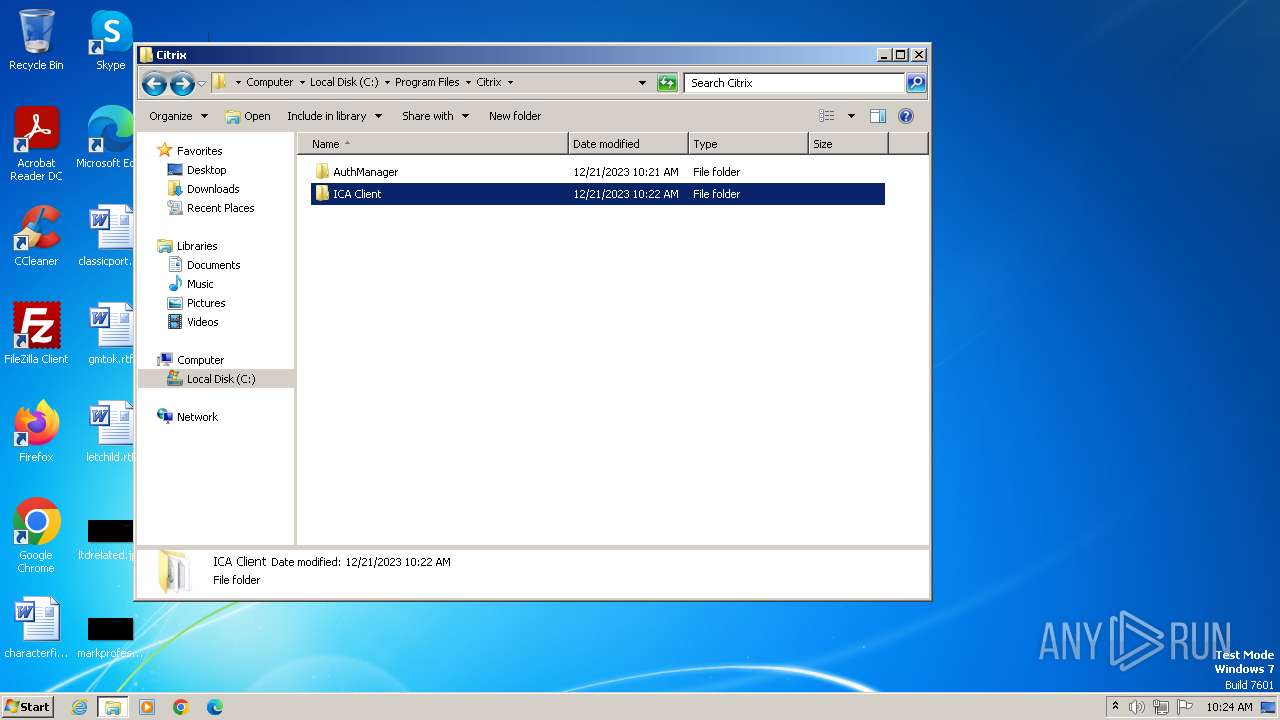
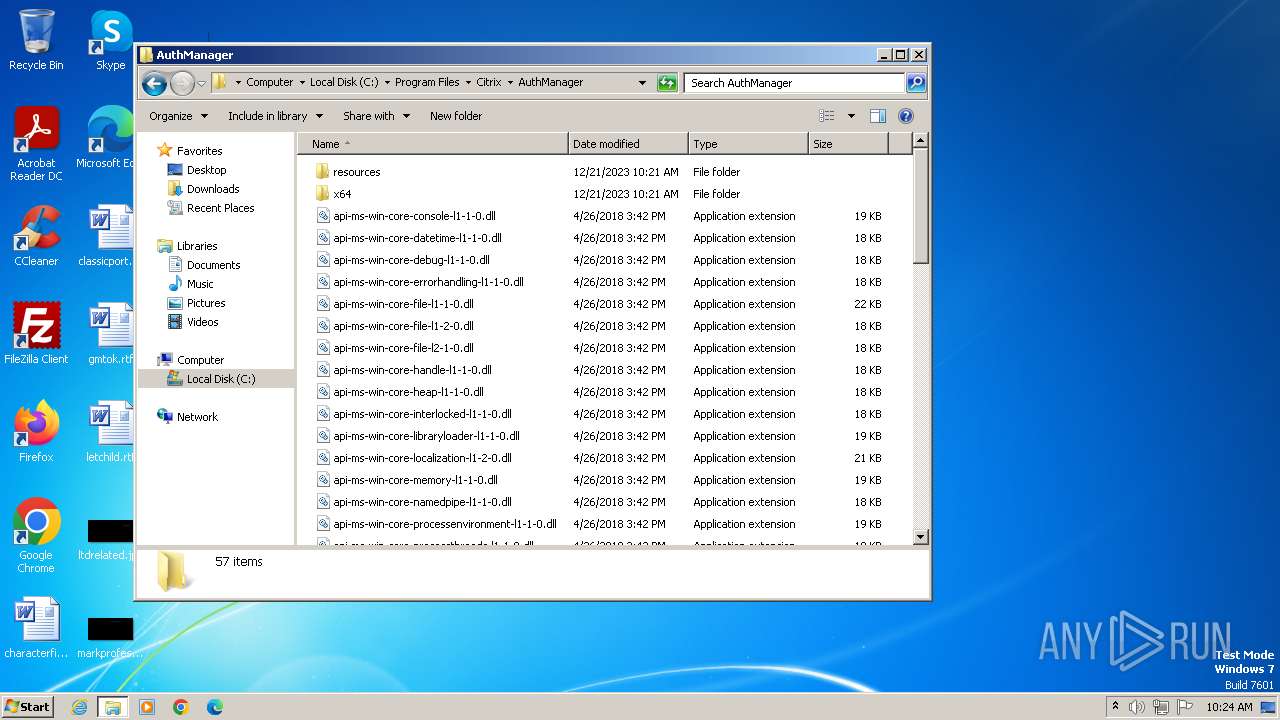
| 664 | "C:\Program Files\Citrix\ICA Client\Drivers\usbinst.exe" InstallHinfSection "DefaultInstall 128 C:\Program Files\Citrix\ICA Client\Drivers\ctxusbm\ctxusbm.inf" | C:\Program Files\Citrix\ICA Client\Drivers\usbinst.exe | — | msiexec.exe | |||||||||||
User: SYSTEM Company: Citrix Systems, Inc. Integrity Level: SYSTEM Description: Citrix USB Install Helper Exit code: 0 Version: 14.12.0.18020 Modules
| |||||||||||||||
| 712 | C:\Windows\system32\MsiExec.exe -Embedding C5DF357DD3DC6E76BB85D08827BD548E E Global\MSI0000 | C:\Windows\System32\msiexec.exe | — | msiexec.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows® installer Exit code: 0 Version: 5.0.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 864 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:2184 CREDAT:267521 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 1376 | "C:\Windows\system32\runonce.exe" -r | C:\Windows\System32\runonce.exe | — | usbinst.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Run Once Wrapper Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1380 | "C:\Program Files\Citrix\ICA Client\wfcrun32.exe" -Embedding | C:\Program Files\Citrix\ICA Client\wfcrun32.exe | svchost.exe | ||||||||||||
User: admin Company: Citrix Systems, Inc. Integrity Level: MEDIUM Description: Citrix Connection Manager Exit code: 0 Version: 14.12.0.18020 Modules
| |||||||||||||||
| 1384 | C:\Users\admin\AppData\Local\Temp\Ctx-B8FA0231-A336-4426-8612-1A3CF5AABB7F\Extract\\DxSetup.exe /silent | C:\Users\admin\AppData\Local\Temp\Ctx-B8FA0231-A336-4426-8612-1A3CF5AABB7F\Extract\DXSETUP.exe | TrolleyExpress.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft DirectX Setup Exit code: 0 Version: 4.9.0.0904 Modules
| |||||||||||||||
| 1540 | "C:\Users\admin\AppData\Local\Temp\Ctx-B8FA0231-A336-4426-8612-1A3CF5AABB7F\Extract\TrolleyExpress.exe" "C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\PO2HN1X2\CitrixReceiverWeb.exe" | C:\Users\admin\AppData\Local\Temp\Ctx-B8FA0231-A336-4426-8612-1A3CF5AABB7F\Extract\TrolleyExpress.exe | CitrixReceiverWeb.exe | ||||||||||||
User: admin Company: Citrix Systems, Inc. Integrity Level: HIGH Description: Citrix Receiver Exit code: 0 Version: 14.12.0.18020 Modules
| |||||||||||||||
| 1584 | C:\Windows\system32\MsiExec.exe -Embedding 0E52DBC99B512F741A4DCBB82759F820 | C:\Windows\System32\msiexec.exe | — | msiexec.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows® installer Exit code: 0 Version: 5.0.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1644 | rundll32.exe "C:\Program Files\Citrix\ICA Client\icaconfs.dll", ApplyConfigurationA import --replace -f -all "C:\Program Files\Citrix\ICA Client\Configuration" --RunAsAdmin | C:\Windows\System32\rundll32.exe | — | msiexec.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows host process (Rundll32) Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1748 | "C:\Program Files\Citrix\ICA Client\Drivers\usbinst.exe" SetupCopyOEMInf "C:\Program Files\Citrix\ICA Client\Drivers\ctxusbm\ctxusbm.inf" | C:\Program Files\Citrix\ICA Client\Drivers\usbinst.exe | — | msiexec.exe | |||||||||||
User: SYSTEM Company: Citrix Systems, Inc. Integrity Level: SYSTEM Description: Citrix USB Install Helper Exit code: 0 Version: 14.12.0.18020 Modules
| |||||||||||||||
Total events
61 981
Read events
61 216
Write events
671
Delete events
94
Modification events
| (PID) Process: | (2184) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPDaysSinceLastAutoMigration |
Value: 0 | |||
| (PID) Process: | (2184) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\TabbedBrowsing |
| Operation: | write | Name: | NTPLastLaunchHighDateTime |
Value: 30847387 | |||
| (PID) Process: | (2184) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateHighDateTime |
Value: 30847437 | |||
| (PID) Process: | (2184) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (2184) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (2184) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (2184) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (2184) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
| (PID) Process: | (2184) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 1 | |||
| (PID) Process: | (2184) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 0 | |||
Executable files
939
Suspicious files
161
Text files
181
Unknown types
4
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 864 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\PO2HN1X2\CitrixReceiverWeb.exe.1gxywgb.partial | — | |
MD5:— | SHA256:— | |||
| 2184 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\PO2HN1X2\CitrixReceiverWeb.exe | — | |
MD5:— | SHA256:— | |||
| 1780 | CitrixReceiverWeb.exe | C:\Users\admin\AppData\Local\Temp\Ctx-B8FA0231-A336-4426-8612-1A3CF5AABB7F\CTX_UPDATE_PACKAGE | — | |
MD5:— | SHA256:— | |||
| 2184 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\7423F88C7F265F0DEFC08EA88C3BDE45_AA1E8580D4EBC816148CE81268683776 | der | |
MD5:F44345321E1CC4C047E0C07FA3C9AA85 | SHA256:DC61C05AD3A2914DBF8315FCF2A8624C34A23310D0938DE2116C49C81E7D27BC | |||
| 864 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\MFAQUS6V\CitrixReceiverWeb[1].exe | executable | |
MD5:44E3B127B9B86E3F2F0114330D618C03 | SHA256:3A3FCEDBA26ACE1441D0E52F0233128548D2F7E76A20DEDEC980CE8695CDBE3F | |||
| 2184 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\57C8EDB95DF3F0AD4EE2DC2B8CFD4157 | compressed | |
MD5:1BFE591A4FE3D91B03CDF26EAACD8F89 | SHA256:9CF94355051BF0F4A45724CA20D1CC02F76371B963AB7D1E38BD8997737B13D8 | |||
| 2184 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\PO2HN1X2\urlblockindex[1].bin | binary | |
MD5:FA518E3DFAE8CA3A0E495460FD60C791 | SHA256:775853600060162C4B4E5F883F9FD5A278E61C471B3EE1826396B6D129499AA7 | |||
| 2184 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\7423F88C7F265F0DEFC08EA88C3BDE45_AA1E8580D4EBC816148CE81268683776 | binary | |
MD5:BA0149505C8DE4F593C388E5044C314B | SHA256:39F4B299F4D9017A4EEFFA60026364526994E9C6E87068A319A854F10292B75B | |||
| 2184 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Internet Explorer\VersionManager\ver6F11.tmp | xml | |
MD5:CBD0581678FA40F0EDCBC7C59E0CAD10 | SHA256:159BD4343F344A08F6AF3B716B6FA679859C1BD1D7030D26FF5EF0255B86E1D9 | |||
| 1780 | CitrixReceiverWeb.exe | C:\Users\admin\AppData\Local\Temp\Ctx-B8FA0231-A336-4426-8612-1A3CF5AABB7F\Extract\Localized_es.xml | xml | |
MD5:95A36AECC074648412E8710C1BBE1234 | SHA256:1E8E752BEE427ED4F50185AA2F7A909650F7EEEED0F032609DBB1FD6133E39D4 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
9
TCP/UDP connections
20
DNS requests
9
Threats
2
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
864 | iexplore.exe | GET | 200 | 2.16.184.251:80 | http://downloadplugins.citrix.com/Windows/CitrixReceiverWeb.exe | unknown | executable | 41.4 Mb | unknown |
2184 | iexplore.exe | GET | 200 | 93.184.221.240:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?914f352674d8023c | unknown | compressed | 4.66 Kb | unknown |
2184 | iexplore.exe | GET | 200 | 93.184.221.240:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?a85e8d0c2f0a71a5 | unknown | compressed | 4.66 Kb | unknown |
2184 | iexplore.exe | GET | 200 | 93.184.221.240:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?0cd9c6b93b31954c | unknown | compressed | 4.66 Kb | unknown |
2184 | iexplore.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | binary | 471 b | unknown |
1080 | svchost.exe | GET | 304 | 93.184.221.240:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?34275567a5b520f7 | unknown | — | — | unknown |
2184 | iexplore.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAqvpsXKY8RRQeo74ffHUxc%3D | unknown | binary | 471 b | unknown |
2184 | iexplore.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEA177el9ggmWelJjG4vdGL0%3D | unknown | binary | 471 b | unknown |
2184 | iexplore.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAn5bsKVVV8kdJ6vHl3O1J0%3D | unknown | binary | 471 b | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
864 | iexplore.exe | 2.16.184.251:80 | downloadplugins.citrix.com | AKAMAI-AS | DE | unknown |
1080 | svchost.exe | 224.0.0.252:5355 | — | — | — | unknown |
2184 | iexplore.exe | 152.199.19.161:443 | r20swj13mr.microsoft.com | EDGECAST | US | whitelisted |
2184 | iexplore.exe | 93.184.221.240:80 | ctldl.windowsupdate.com | EDGECAST | GB | whitelisted |
2184 | iexplore.exe | 192.229.221.95:80 | ocsp.digicert.com | EDGECAST | US | whitelisted |
1080 | svchost.exe | 93.184.221.240:80 | ctldl.windowsupdate.com | EDGECAST | GB | whitelisted |
2184 | iexplore.exe | 204.79.197.200:443 | ieonline.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
2184 | iexplore.exe | 2.19.105.250:443 | go.microsoft.com | AKAMAI-AS | DE | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
downloadplugins.citrix.com |
| unknown |
r20swj13mr.microsoft.com |
| whitelisted |
iecvlist.microsoft.com |
| whitelisted |
ctldl.windowsupdate.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
ieonline.microsoft.com |
| whitelisted |
go.microsoft.com |
| whitelisted |
www.msn.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
864 | iexplore.exe | Potential Corporate Privacy Violation | ET POLICY PE EXE or DLL Windows file download HTTP |
864 | iexplore.exe | Misc activity | ET INFO EXE - Served Attached HTTP |
Process | Message |
|---|---|
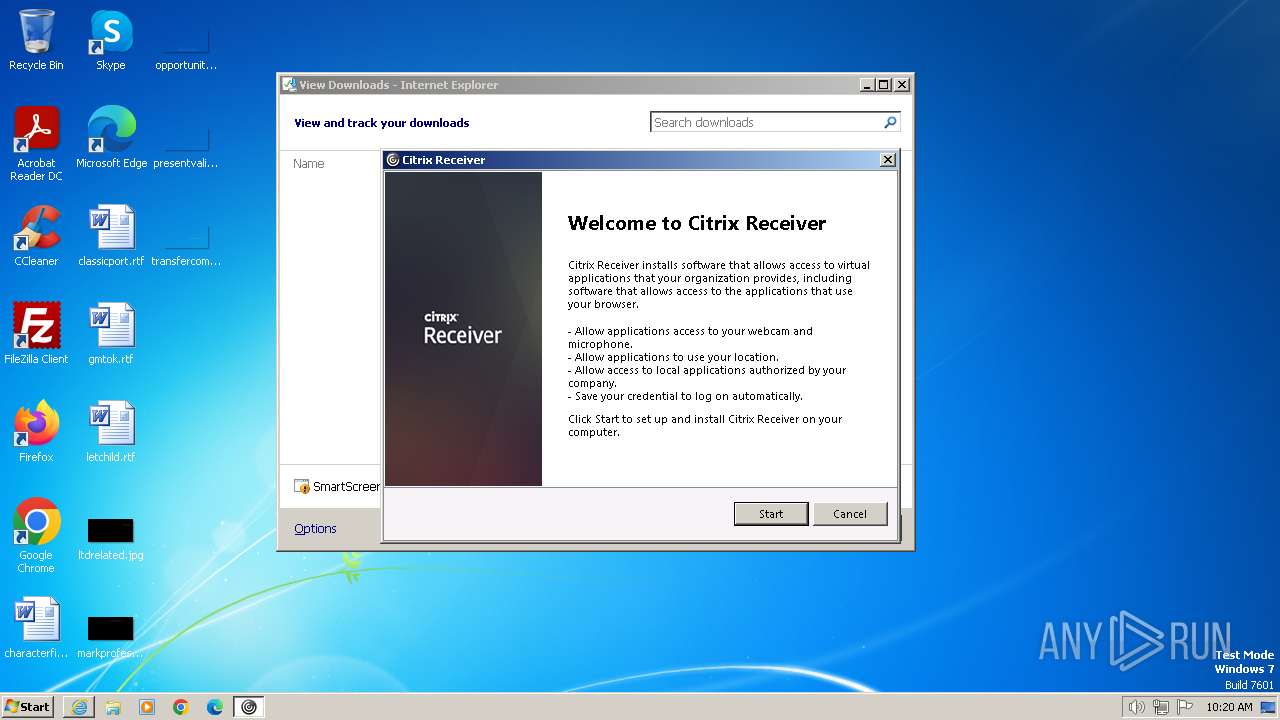
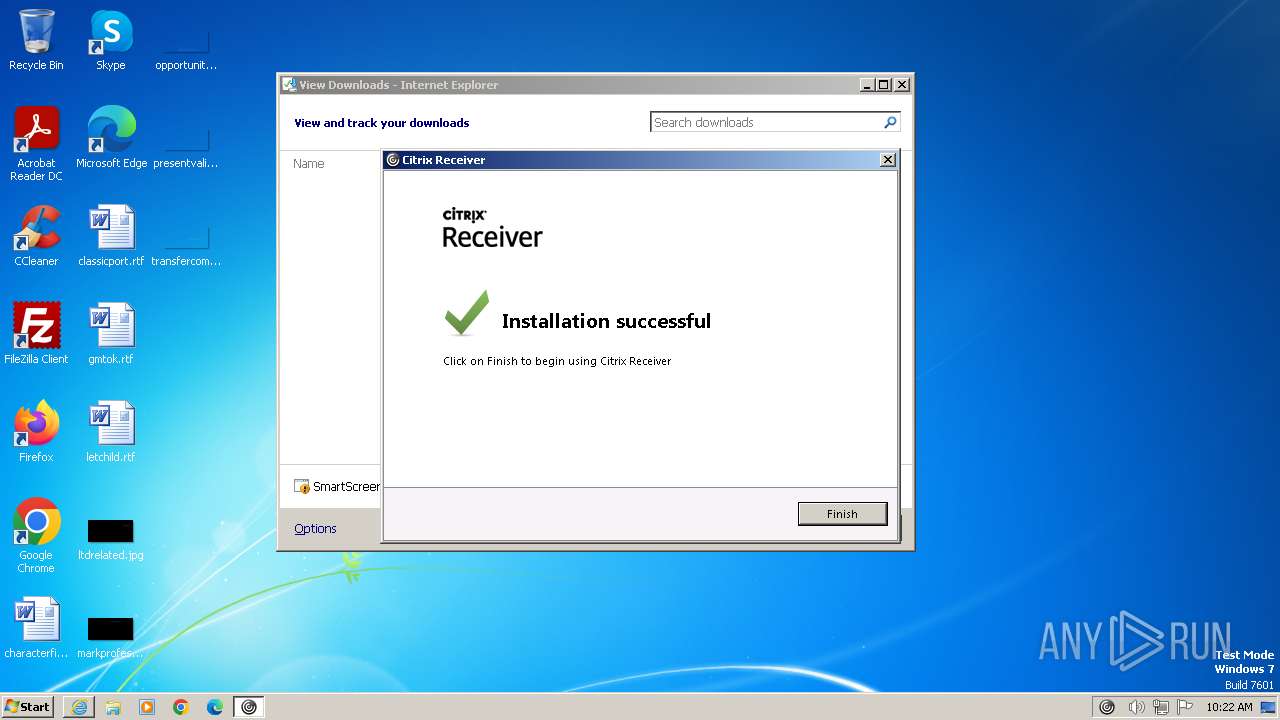
CitrixReceiverWeb.exe | RunPackage: bootstrap install started
|
CitrixReceiverWeb.exe | Extracting files to folder with index -1
|
CitrixReceiverWeb.exe | FindExplorerHandle: Found explorer
|
CitrixReceiverWeb.exe | CUpdatePackage::dualpk does not exist...C:\Users\admin\AppData\Local\Temp\Ctx-B8FA0231-A336-4426-8612-1A3CF5AABB7F\Extract\dualpk.cab
|
CitrixReceiverWeb.exe | CtxIsUserAdmin: CheckTokenMembership with linked token passed
|
CitrixReceiverWeb.exe | CUpdatePackage::InternalRun: User`is an Admin
|
TrolleyExpress.exe | Information - CApp::InitializeLog(1435) - * Build Time: 02:34:36
|
TrolleyExpress.exe | Information - CApp::InitializeResourceModule(1616) - Processing Resource Module Path: C:\Users\admin\AppData\Local\Temp\Ctx-B8FA0231-A336-4426-8612-1A3CF5AABB7F\Extract\en
|
TrolleyExpress.exe | Information - CApp::InitializeResourceModule(1627) - Resource Module Path 1: C:\Users\admin\AppData\Local\Temp\Ctx-B8FA0231-A336-4426-8612-1A3CF5AABB7F\Extract\en\en-US\TrolleyExpressUI_en.dll
|
TrolleyExpress.exe | Information - CApp::InitInstance(541) - User is Admin User : 1
|