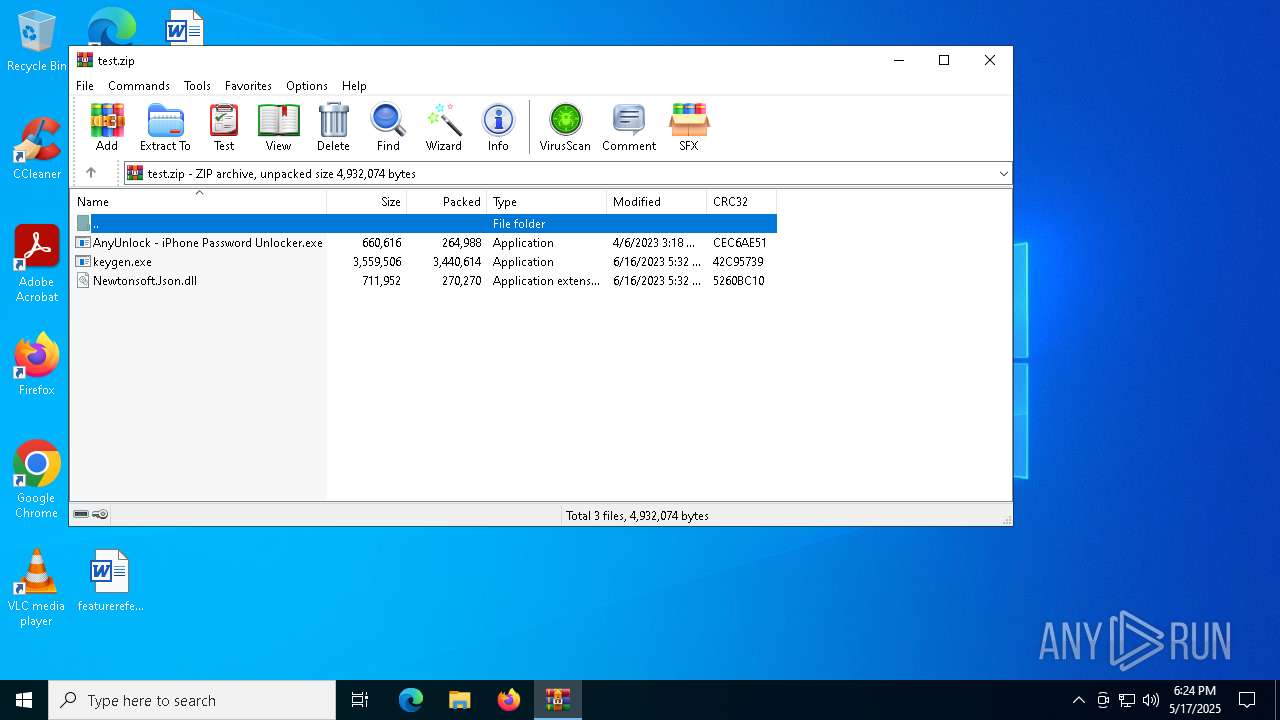
| File name: | test.zip |
| Full analysis: | https://app.any.run/tasks/f071b3e7-b9a5-40f2-b77a-f617faad7dcd |
| Verdict: | Malicious activity |
| Analysis date: | May 17, 2025, 18:24:30 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/zip |
| File info: | Zip archive data, at least v2.0 to extract, compression method=deflate |
| MD5: | A3CAC460303181B98D8EC68CB1987613 |
| SHA1: | F8D092F91DC2CC898EA0CBF90877FDF6AC7B8315 |
| SHA256: | 64EB69ACB0F4DC2DFB02DCB7FAE1CE643B7DFA09A4C202A81BC80EEC6A6A23A7 |
| SSDEEP: | 98304:7p6FHtn7/YVlL1FPr+YHOu/lNtV7KguzLd0BGzXu2nR7FmhhzIoeFqL6wB5l5TX7:MS2E9 |
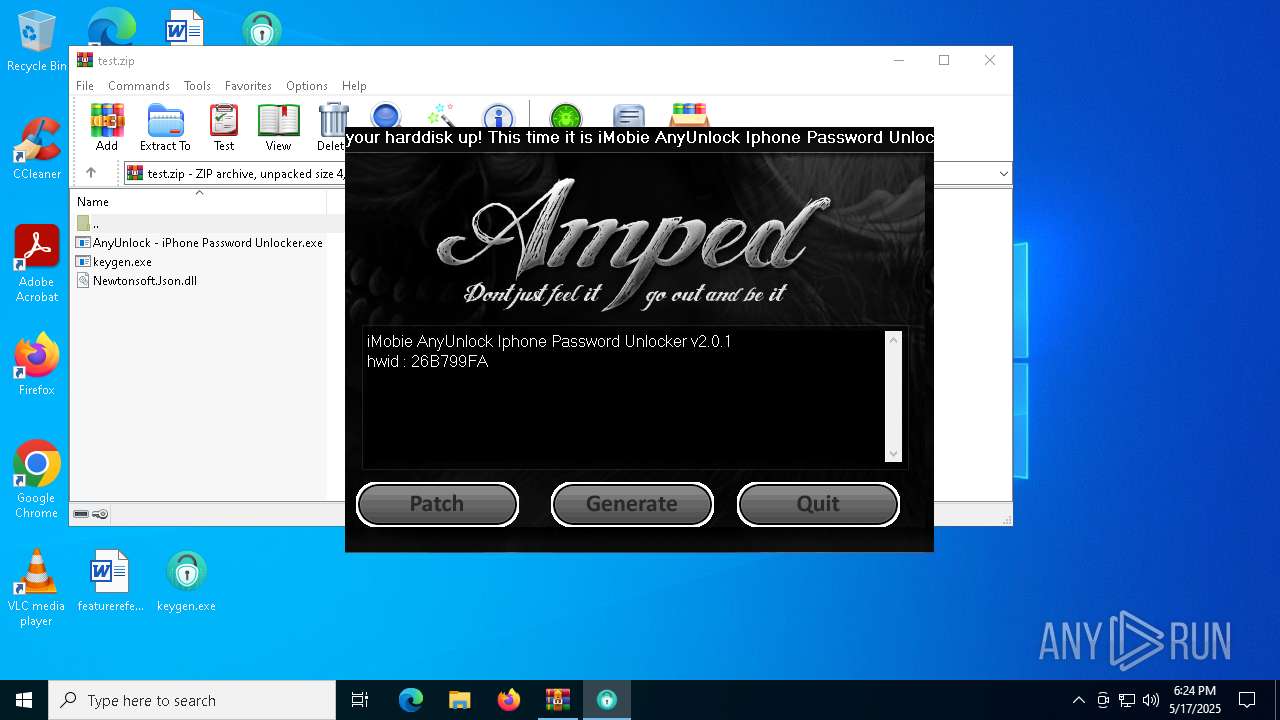
MALICIOUS
Generic archive extractor
- WinRAR.exe (PID: 7384)
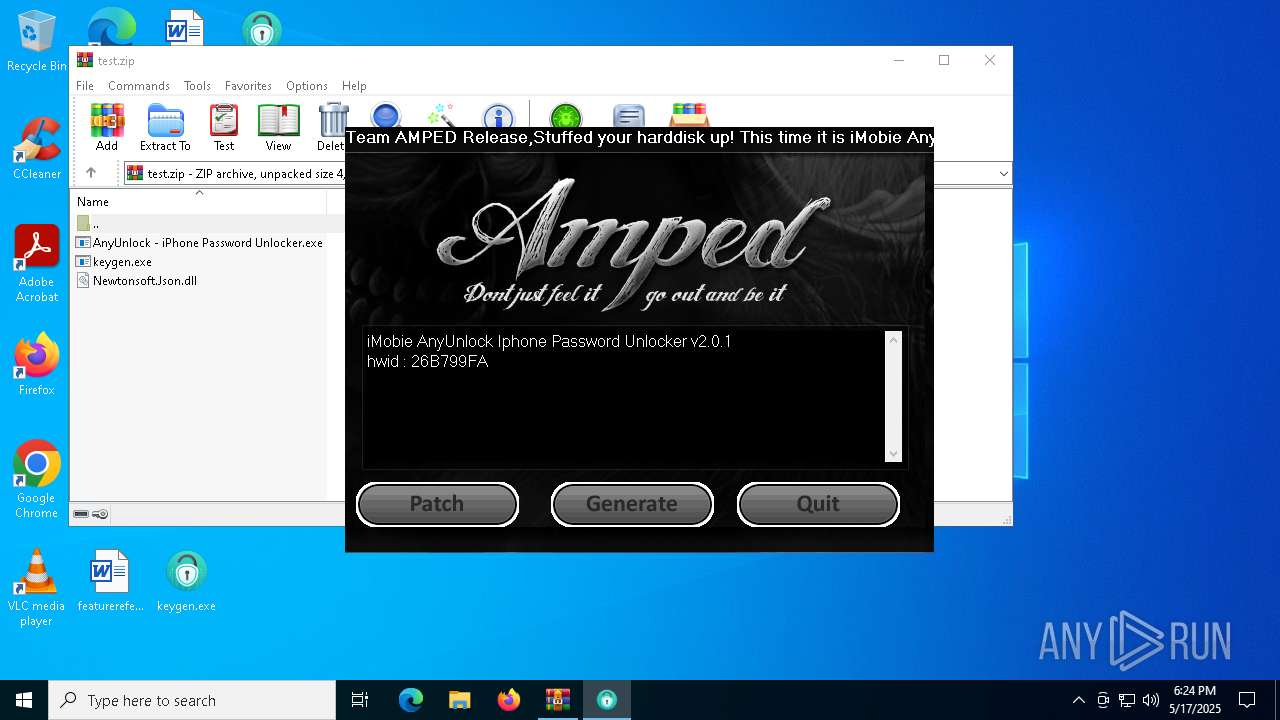
SUSPICIOUS
Reads the BIOS version
- keygen.exe (PID: 7540)
Executes application which crashes
- AnyUnlock - iPhone Password Unlocker.exe (PID: 7572)
INFO
Manual execution by a user
- keygen.exe (PID: 7540)
- AnyUnlock - iPhone Password Unlocker.exe (PID: 7572)
Checks supported languages
- keygen.exe (PID: 7540)
- AnyUnlock - iPhone Password Unlocker.exe (PID: 7572)
Reads the computer name
- AnyUnlock - iPhone Password Unlocker.exe (PID: 7572)
- keygen.exe (PID: 7540)
Creates files or folders in the user directory
- WerFault.exe (PID: 7672)
Reads the machine GUID from the registry
- keygen.exe (PID: 7540)
Executable content was dropped or overwritten
- WinRAR.exe (PID: 7384)
Themida protector has been detected
- keygen.exe (PID: 7540)
Checks proxy server information
- slui.exe (PID: 8124)
Reads the software policy settings
- slui.exe (PID: 8124)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .zip | | | ZIP compressed archive (100) |
|---|
EXIF
ZIP
| ZipRequiredVersion: | 20 |
|---|---|
| ZipBitFlag: | - |
| ZipCompression: | Deflated |
| ZipModifyDate: | 2023:04:06 03:18:38 |
| ZipCRC: | 0xcec6ae51 |
| ZipCompressedSize: | 264988 |
| ZipUncompressedSize: | 660616 |
| ZipFileName: | AnyUnlock - iPhone Password Unlocker.exe |
Total processes
134
Monitored processes
5
Malicious processes
0
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 7384 | "C:\Program Files\WinRAR\WinRAR.exe" C:\Users\admin\Desktop\test.zip | C:\Program Files\WinRAR\WinRAR.exe | explorer.exe | ||||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Version: 5.91.0 Modules
| |||||||||||||||
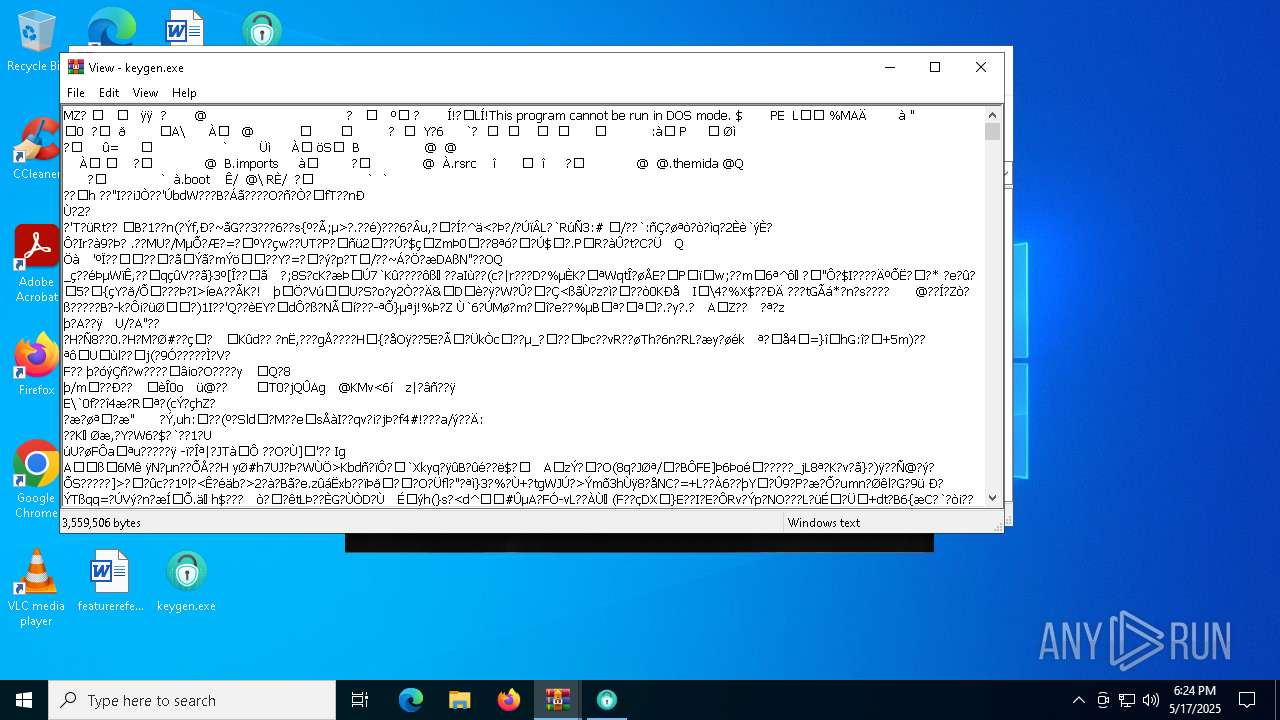
| 7540 | "C:\Users\admin\Desktop\keygen.exe" | C:\Users\admin\Desktop\keygen.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Description: Imobie_anyunlock Version: 1.0.0.0 Modules
| |||||||||||||||
| 7572 | "C:\Users\admin\Desktop\AnyUnlock - iPhone Password Unlocker.exe" | C:\Users\admin\Desktop\AnyUnlock - iPhone Password Unlocker.exe | explorer.exe | ||||||||||||
User: admin Company: iMobie Inc. Integrity Level: MEDIUM Description: AnyUnlock - iPhone Password Unlocker Exit code: 3762504530 Version: 2.0.1.6 Modules
| |||||||||||||||
| 7672 | C:\WINDOWS\system32\WerFault.exe -u -p 7572 -s 768 | C:\Windows\System32\WerFault.exe | — | AnyUnlock - iPhone Password Unlocker.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Problem Reporting Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 8124 | C:\WINDOWS\System32\slui.exe -Embedding | C:\Windows\System32\slui.exe | svchost.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Activation Client Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
6 583
Read events
6 574
Write events
9
Delete events
0
Modification events
| (PID) Process: | (7384) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 3 |
Value: C:\Users\admin\Desktop\preferences.zip | |||
| (PID) Process: | (7384) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 2 |
Value: C:\Users\admin\Desktop\chromium_ext.zip | |||
| (PID) Process: | (7384) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 1 |
Value: C:\Users\admin\Desktop\omni_23_10_2024_.zip | |||
| (PID) Process: | (7384) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\Desktop\test.zip | |||
| (PID) Process: | (7384) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (7384) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (7384) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (7384) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (7384) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList |
| Operation: | write | Name: | ArcSort |
Value: 32 | |||
Executable files
1
Suspicious files
2
Text files
1
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 7672 | WerFault.exe | C:\ProgramData\Microsoft\Windows\WER\ReportQueue\AppCrash_AnyUnlock - iPho_be9a4d1a7b7f5a2ce238c5236491c2ae287bfe91_85910fd4_29edd8f7-2307-4476-8f31-d7c1f348a408\Report.wer | — | |
MD5:— | SHA256:— | |||
| 7672 | WerFault.exe | C:\Users\admin\AppData\Local\CrashDumps\AnyUnlock - iPhone Password Unlocker.exe.7572.dmp | — | |
MD5:— | SHA256:— | |||
| 7672 | WerFault.exe | C:\ProgramData\Microsoft\Windows\WER\Temp\WERD572.tmp.dmp | binary | |
MD5:2F1CA1A52B7B76235E91C76E5C093023 | SHA256:93C2B81F847D88A896C1DED2528374267F006EBD9E66E1557CEA0522BBB1A2B2 | |||
| 7672 | WerFault.exe | C:\ProgramData\Microsoft\Windows\WER\Temp\WERD65E.tmp.WERInternalMetadata.xml | binary | |
MD5:94BA4D91314E70444D7421E5EFC33D53 | SHA256:0F6CCC80DC7C486C559257BE99417C6C07BA372CCFDBB23341EA2EDC0E5C8C68 | |||
| 7672 | WerFault.exe | C:\ProgramData\Microsoft\Windows\WER\Temp\WERD68E.tmp.xml | xml | |
MD5:93305951A98B89A02BEA908D49B68AD6 | SHA256:BE73CAE1317277685FFA9B71DF6E9B63F300B3BCC90332C1CBCC064AECCEEE71 | |||
| 7384 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DIa7384.10318\keygen.exe | executable | |
MD5:FD3C7EEEEF4616BBF185AA5D9B0F69D2 | SHA256:233C833F7C82525ADEA186D444784432E0D68982133E16EF90170171C055A1AA | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
2
TCP/UDP connections
21
DNS requests
6
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2104 | svchost.exe | GET | 200 | 2.16.168.124:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
2104 | svchost.exe | GET | 200 | 2.23.246.101:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4932 | RUXIMICS.exe | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
— | — | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
2104 | svchost.exe | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
2104 | svchost.exe | 2.16.168.124:80 | crl.microsoft.com | Akamai International B.V. | RU | whitelisted |
2104 | svchost.exe | 2.23.246.101:80 | www.microsoft.com | Ooredoo Q.S.C. | QA | whitelisted |
2104 | svchost.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
7196 | slui.exe | 40.91.76.224:443 | activation-v2.sls.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
8124 | slui.exe | 40.91.76.224:443 | activation-v2.sls.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
google.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
settings-win.data.microsoft.com |
| whitelisted |
activation-v2.sls.microsoft.com |
| whitelisted |