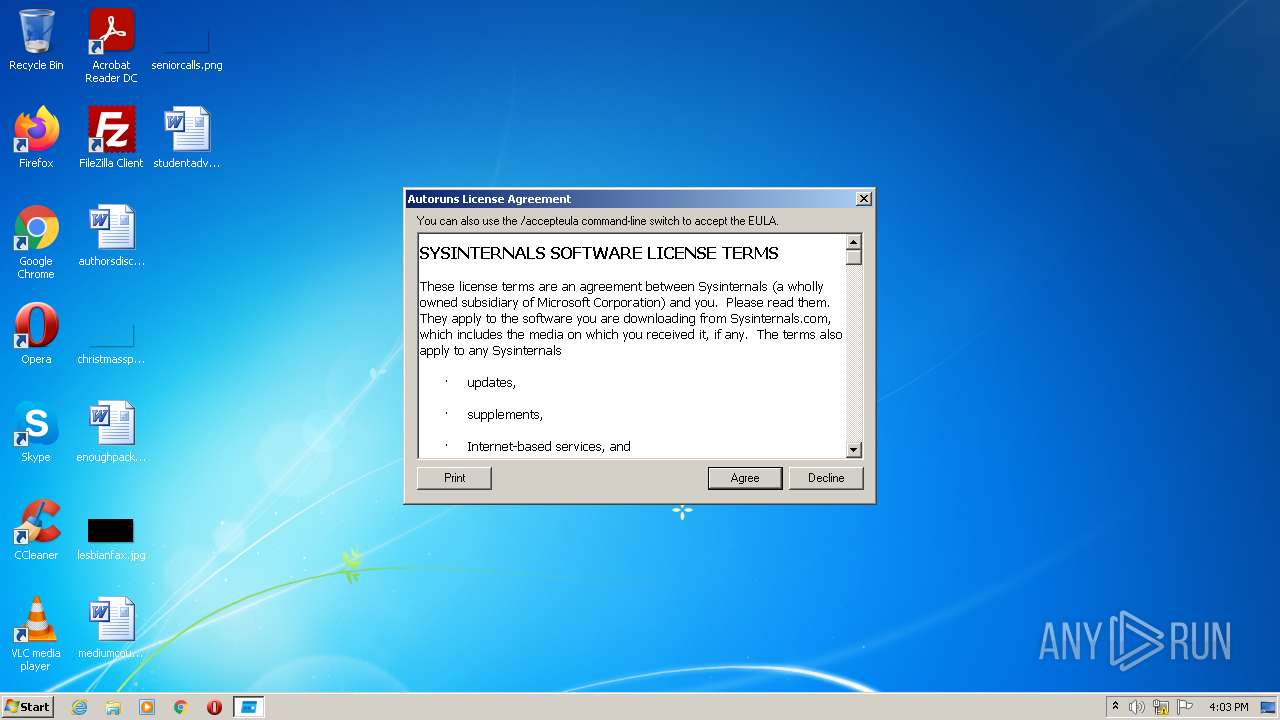
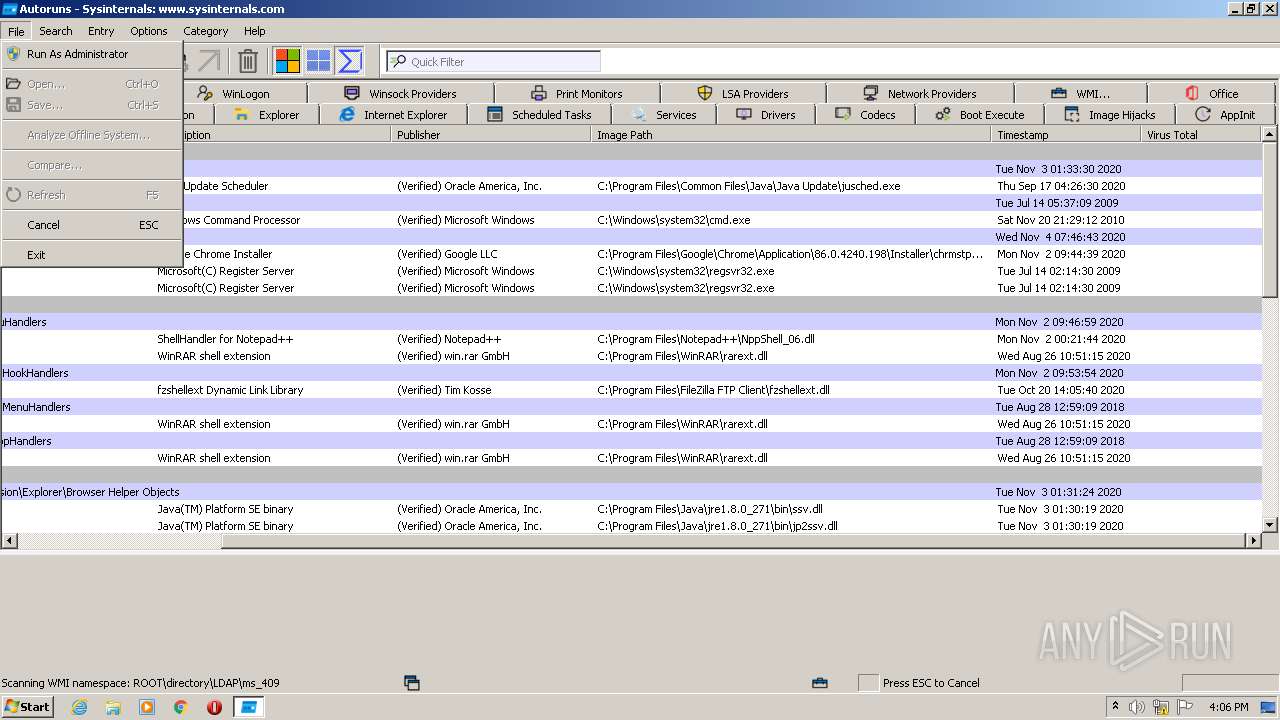
| File name: | Autoruns.exe |
| Full analysis: | https://app.any.run/tasks/f5bb2b7c-3a31-4f81-95f7-1c255b51b1c1 |
| Verdict: | Malicious activity |
| Analysis date: | June 28, 2022, 15:03:09 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | 583ED542BE17B83F3C102D49FE984E26 |
| SHA1: | 142FC798C0E89B55198C3DFC5CAAB8A10D9AA150 |
| SHA256: | 64D490783ABD017AC36A017B9CB7DCFC2FCEE85F7AE8EE203A0C898DA6D37533 |
| SSDEEP: | 49152:wjLCJSLYIujU519eCvepXi/Wsqo69n1lme8CeD3p:wjLCJSLYdjkrWsqo691lmJ |
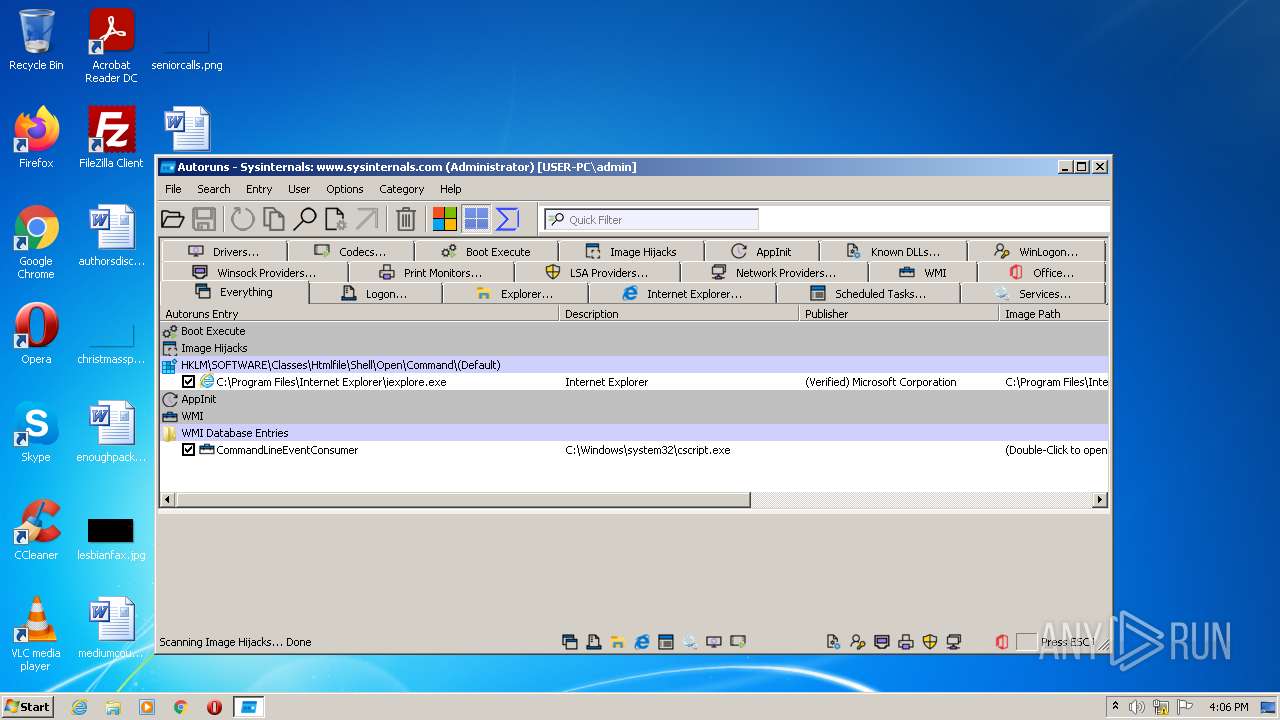
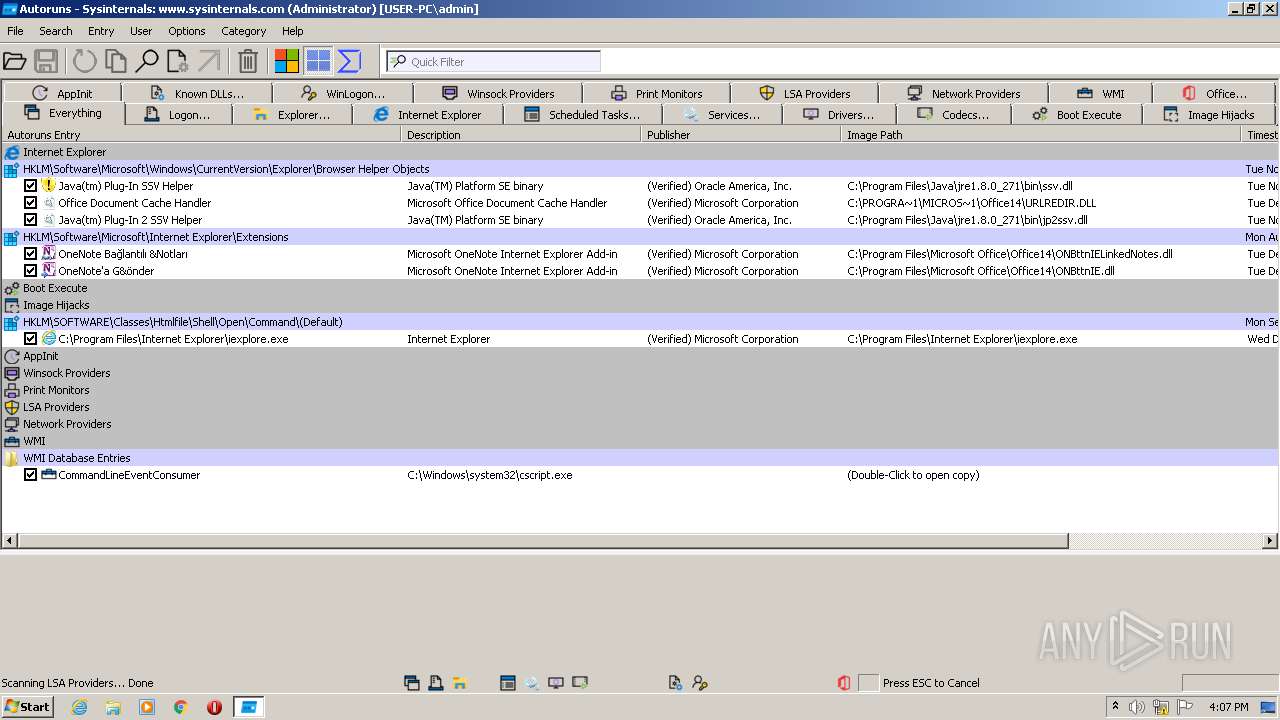
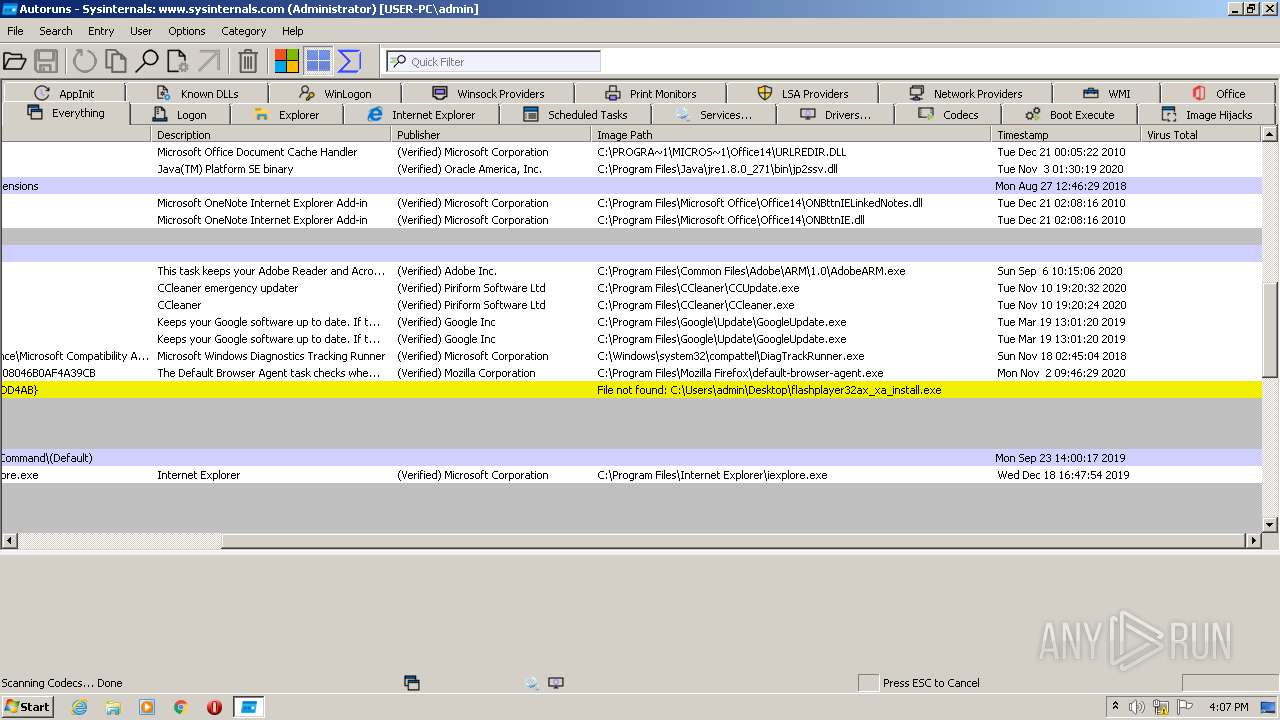
MALICIOUS
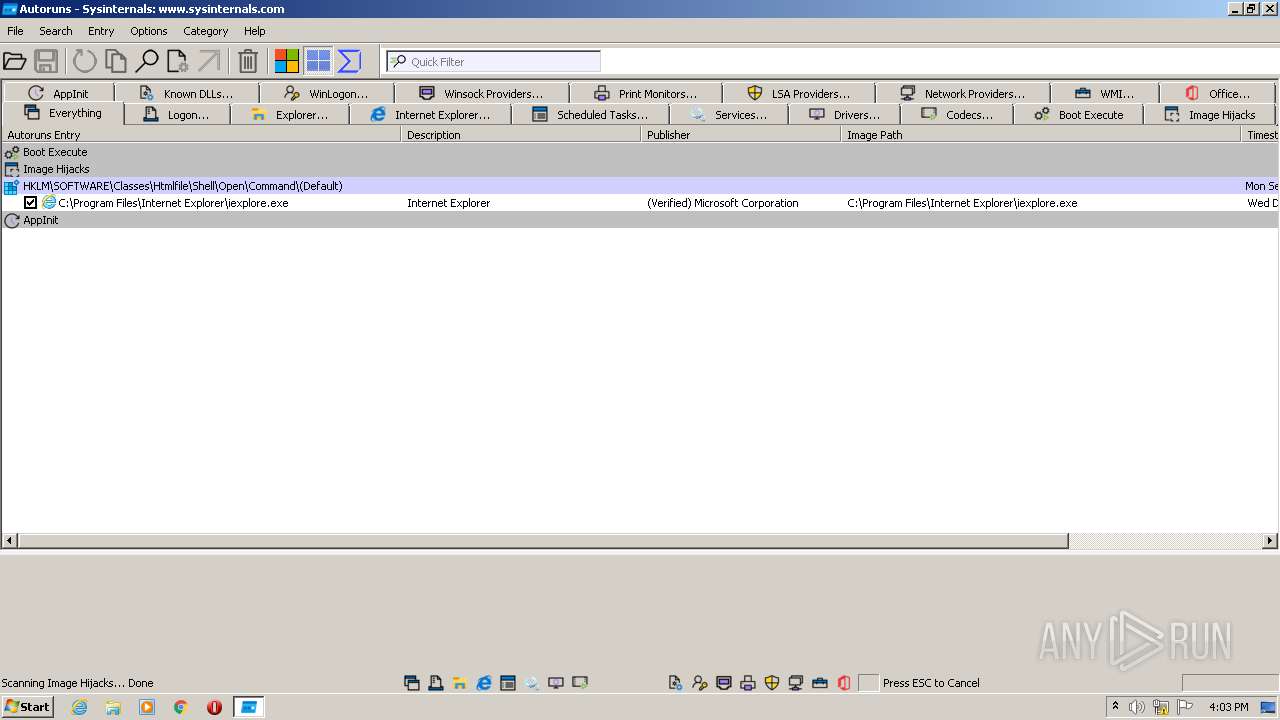
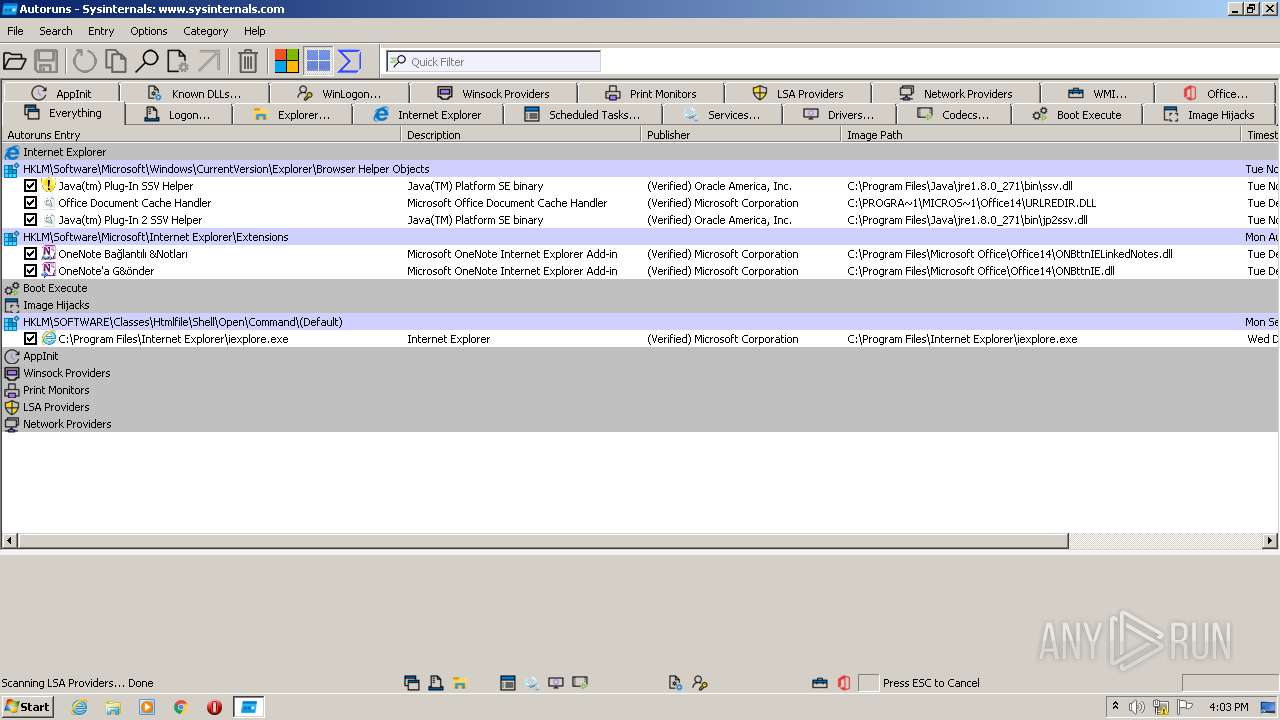
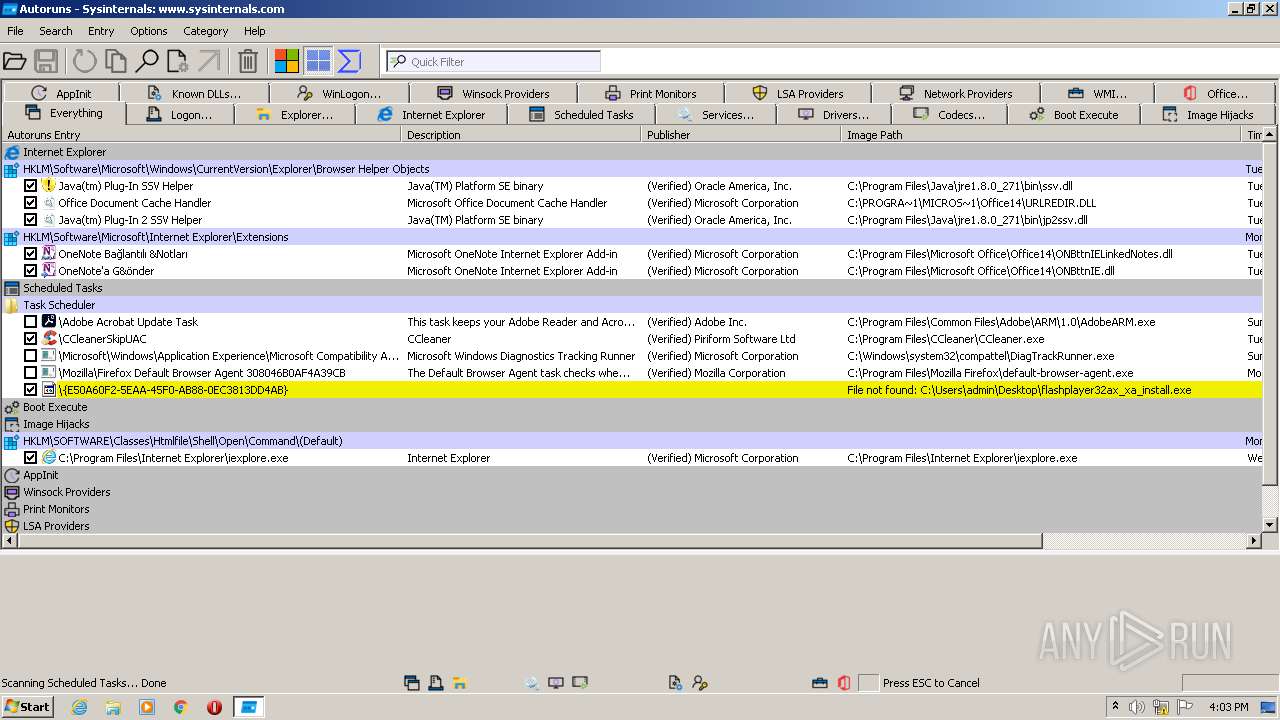
Loads the Task Scheduler COM API
- Autoruns.exe (PID: 2592)
- Autoruns.exe (PID: 2212)
Changes settings of System certificates
- Autoruns.exe (PID: 2212)
SUSPICIOUS
Checks supported languages
- Autoruns.exe (PID: 2592)
- Autoruns.exe (PID: 2212)
Reads the computer name
- Autoruns.exe (PID: 2592)
- Autoruns.exe (PID: 2212)
Reads Environment values
- Autoruns.exe (PID: 2592)
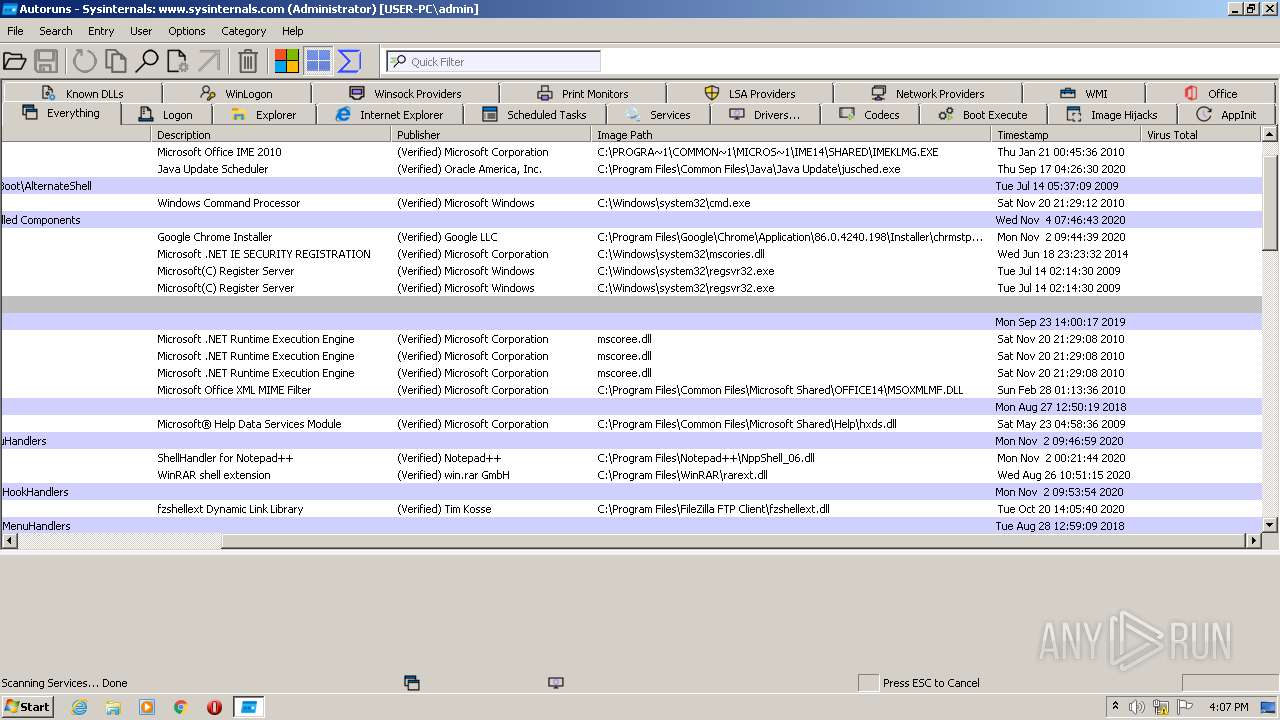
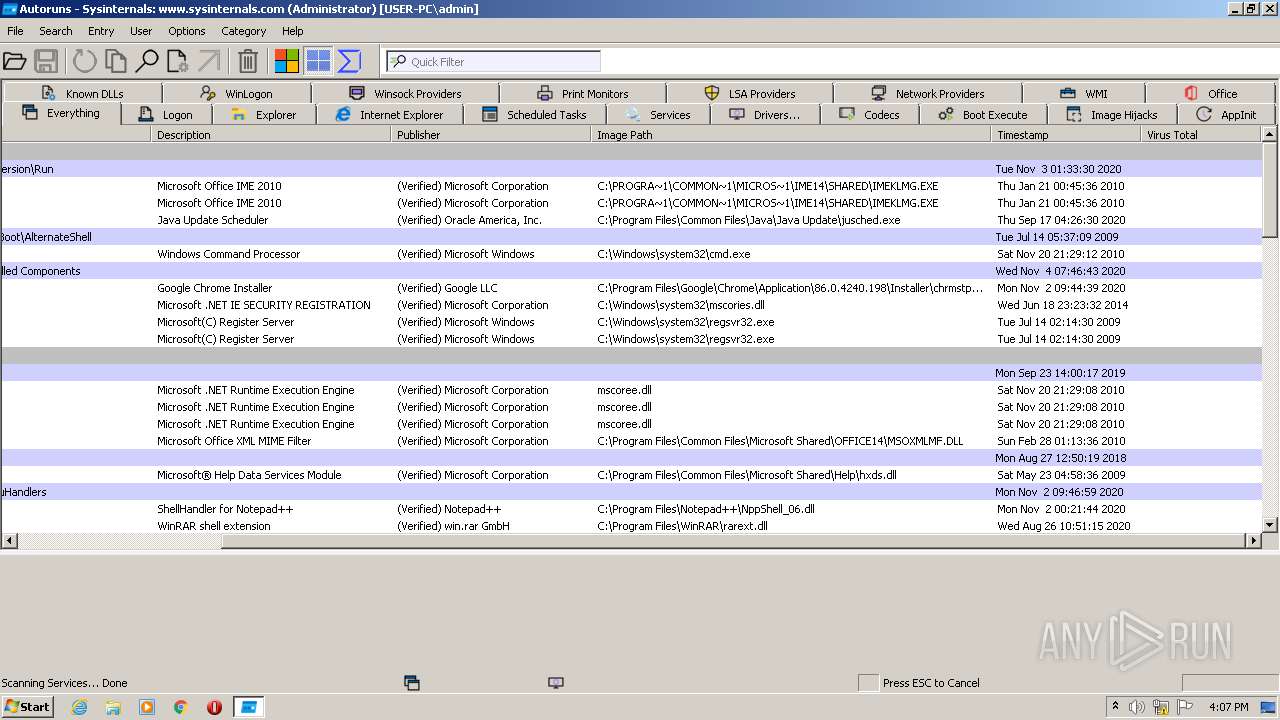
Reads default file associations for system extensions
- Autoruns.exe (PID: 2592)
- Autoruns.exe (PID: 2212)
Application launched itself
- Autoruns.exe (PID: 2592)
Adds / modifies Windows certificates
- Autoruns.exe (PID: 2212)
INFO
Reads settings of System Certificates
- Autoruns.exe (PID: 2592)
- Autoruns.exe (PID: 2212)
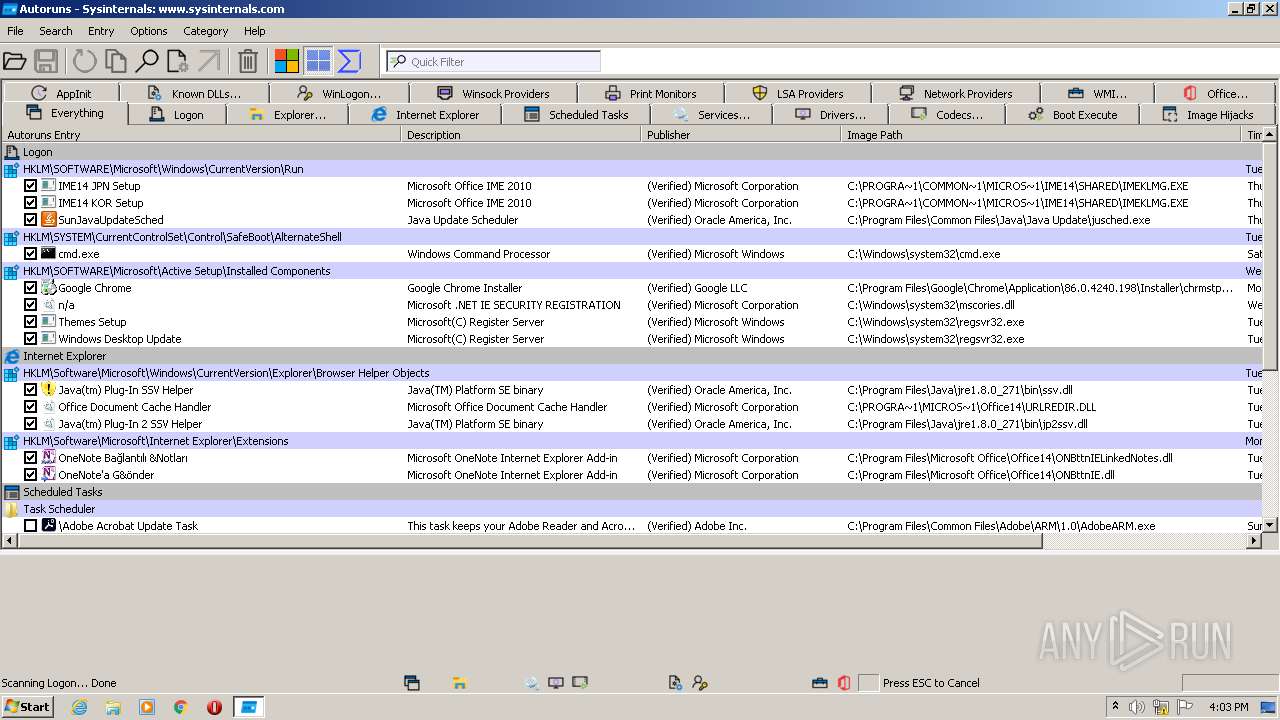
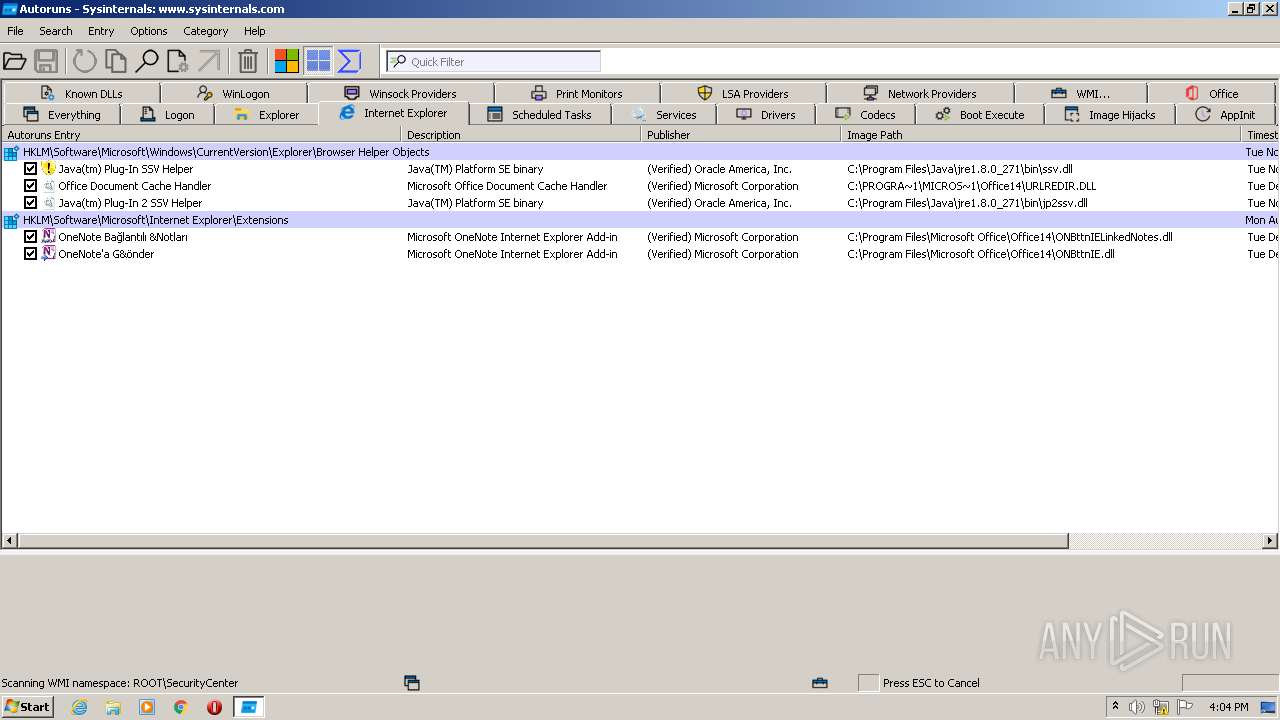
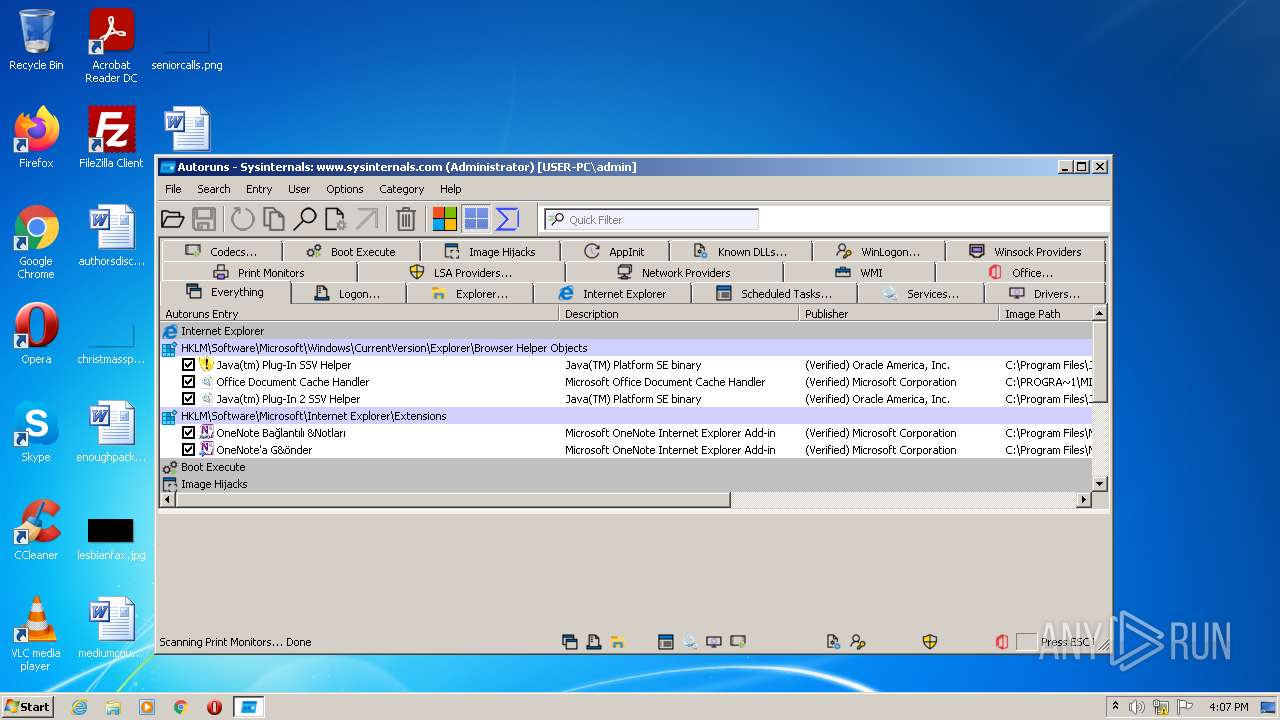
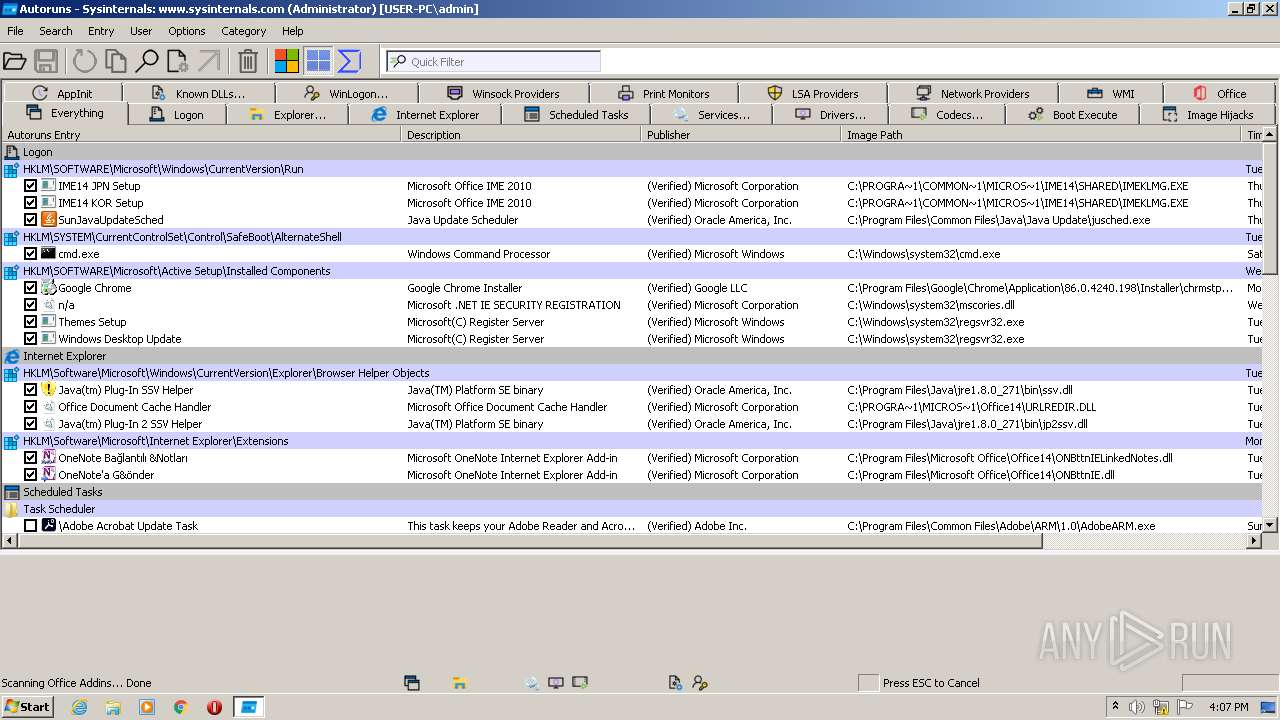
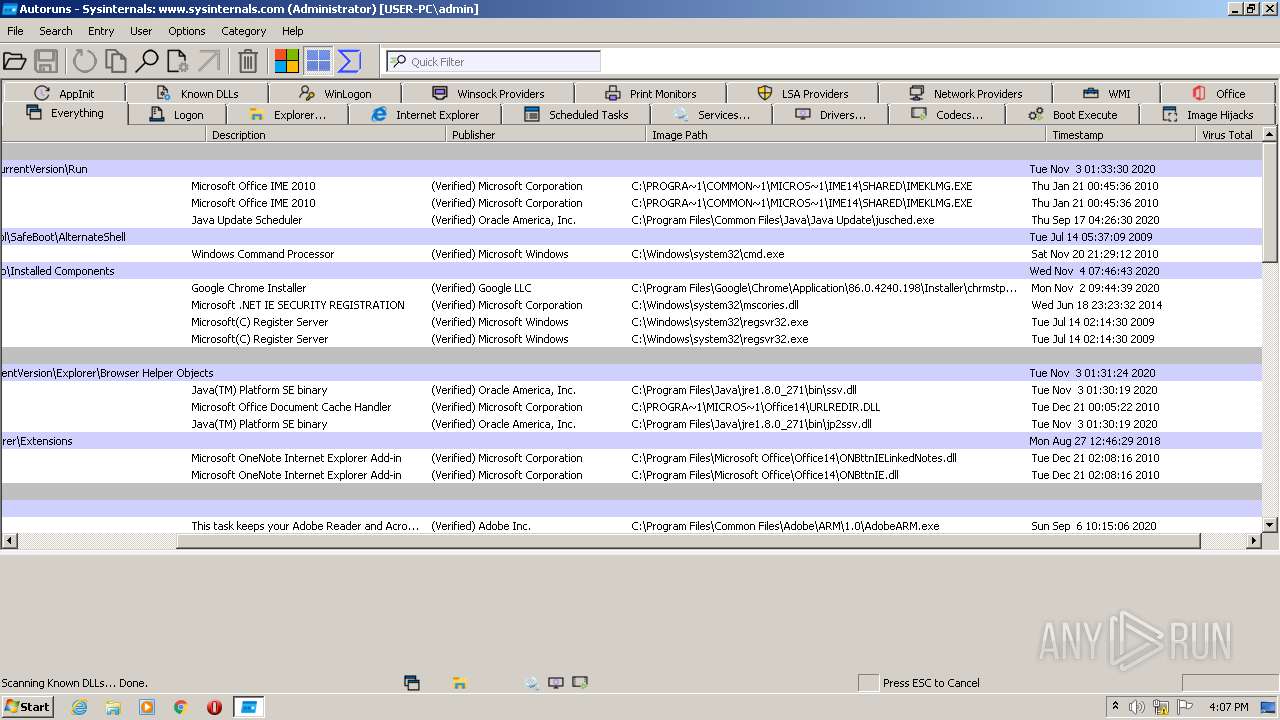
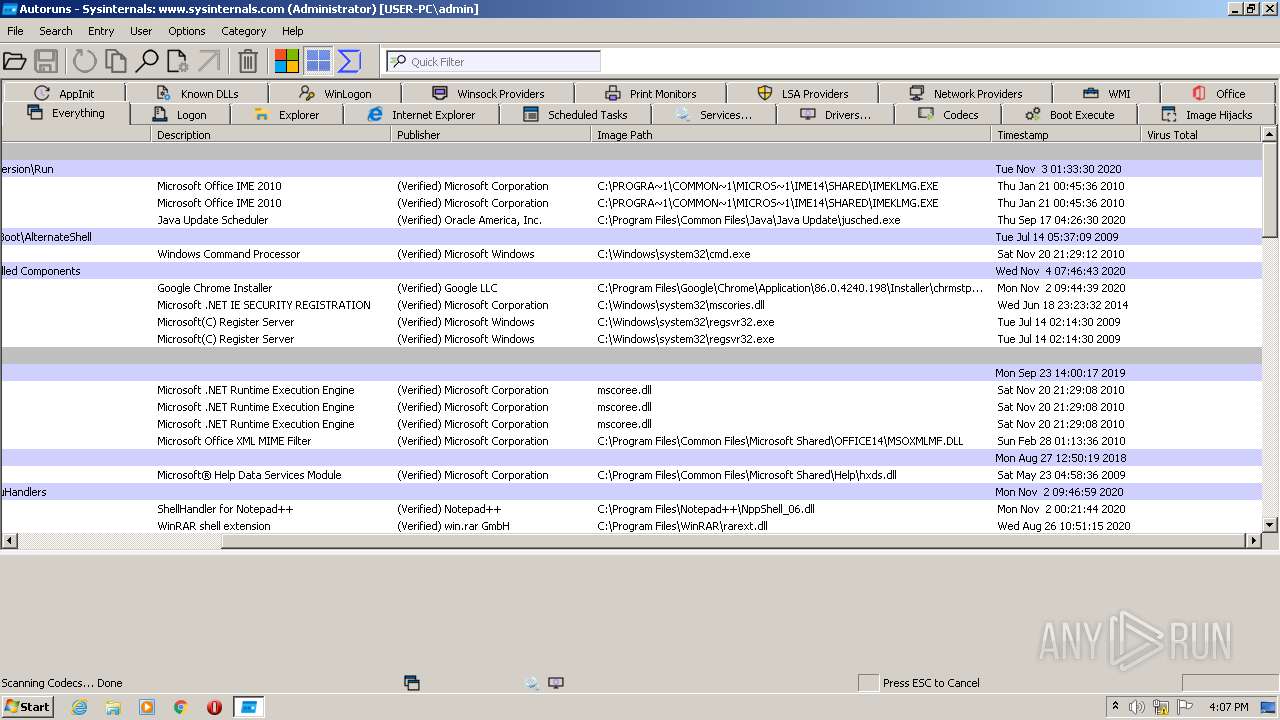
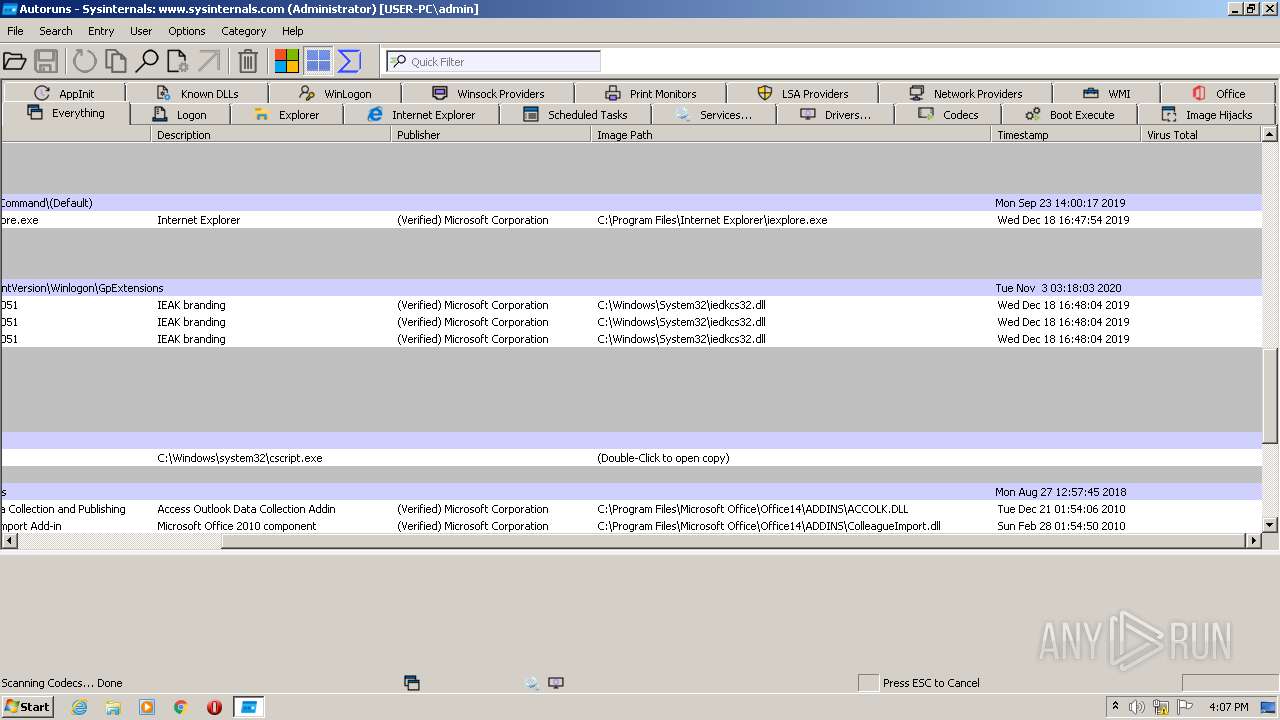
Reads Microsoft Office registry keys
- Autoruns.exe (PID: 2212)
- Autoruns.exe (PID: 2592)
Checks Windows Trust Settings
- Autoruns.exe (PID: 2592)
- Autoruns.exe (PID: 2212)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable (generic) (52.9) |
|---|---|---|
| .exe | | | Generic Win/DOS Executable (23.5) |
| .exe | | | DOS Executable Generic (23.5) |
EXIF
EXE
| ProductVersion: | 14.09 |
|---|---|
| ProductName: | Sysinternals autoruns |
| OriginalFileName: | autoruns.exe |
| LegalCopyright: | Copyright (C) 2002-2022 Mark Russinovich |
| InternalName: | Sysinternals Autoruns |
| FileVersion: | 14.09 |
| FileDescription: | Autostart program viewer |
| CompanyName: | Sysinternals - www.sysinternals.com |
| CharacterSet: | Unicode |
| LanguageCode: | English (U.S.) |
| FileSubtype: | - |
| ObjectFileType: | Dynamic link library |
| FileOS: | Win32 |
| FileFlags: | (none) |
| FileFlagsMask: | 0x003f |
| ProductVersionNumber: | 14.0.9.0 |
| FileVersionNumber: | 14.0.9.0 |
| Subsystem: | Windows GUI |
| SubsystemVersion: | 6 |
| ImageVersion: | - |
| OSVersion: | 6 |
| EntryPoint: | 0xd36ae |
| UninitializedDataSize: | - |
| InitializedDataSize: | 1189888 |
| CodeSize: | 1309184 |
| LinkerVersion: | 14.29 |
| PEType: | PE32 |
| TimeStamp: | 2022:02:14 21:13:32+01:00 |
| MachineType: | Intel 386 or later, and compatibles |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 14-Feb-2022 20:13:32 |
| Detected languages: |
|
| TLS Callbacks: | 1 callback(s) detected. |
| Debug artifacts: |
|
| CompanyName: | Sysinternals - www.sysinternals.com |
| FileDescription: | Autostart program viewer |
| FileVersion: | 14.09 |
| InternalName: | Sysinternals Autoruns |
| LegalCopyright: | Copyright (C) 2002-2022 Mark Russinovich |
| OriginalFilename: | autoruns.exe |
| ProductName: | Sysinternals autoruns |
| ProductVersion: | 14.09 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000128 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 7 |
| Time date stamp: | 14-Feb-2022 20:13:32 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x0013F816 | 0x0013FA00 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.50453 |
.rdata | 0x00141000 | 0x0004C414 | 0x0004C600 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 5.07321 |
.data | 0x0018E000 | 0x0000A7B8 | 0x00008800 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 4.29635 |
.detourc\x886 | 0x00199000 | 0x00003688 | 0x00003800 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 4.25173 |
.detourd$ | 0x0019D000 | 0x00000024 | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0.160329 |
.rsrc | 0x0019E000 | 0x000B5918 | 0x000B5A00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 4.50782 |
.reloc | 0x00254000 | 0x000125C8 | 0x00012600 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_DISCARDABLE, IMAGE_SCN_MEM_READ | 6.67034 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.19312 | 2033 | UNKNOWN | English - United States | RT_MANIFEST |
2 | 5.29011 | 2440 | UNKNOWN | English - United States | RT_ICON |
3 | 5.13304 | 4264 | UNKNOWN | English - United States | RT_ICON |
4 | 4.87852 | 9640 | UNKNOWN | English - United States | RT_ICON |
5 | 4.74127 | 16936 | UNKNOWN | English - United States | RT_ICON |
6 | 4.62992 | 38056 | UNKNOWN | English - United States | RT_ICON |
7 | 4.58855 | 67624 | UNKNOWN | English - United States | RT_ICON |
8 | 4.52782 | 152104 | UNKNOWN | English - United States | RT_ICON |
9 | 2.62625 | 138 | UNKNOWN | English - United States | RT_STRING |
10 | 1.95558 | 4264 | UNKNOWN | English - United States | RT_ICON |
Imports
ADVAPI32.dll |
COMCTL32.dll |
COMDLG32.dll |
CRYPT32.dll |
GDI32.dll |
KERNEL32.dll |
MSIMG32.dll |
OLEAUT32.dll |
SHELL32.dll |
SHLWAPI.dll |
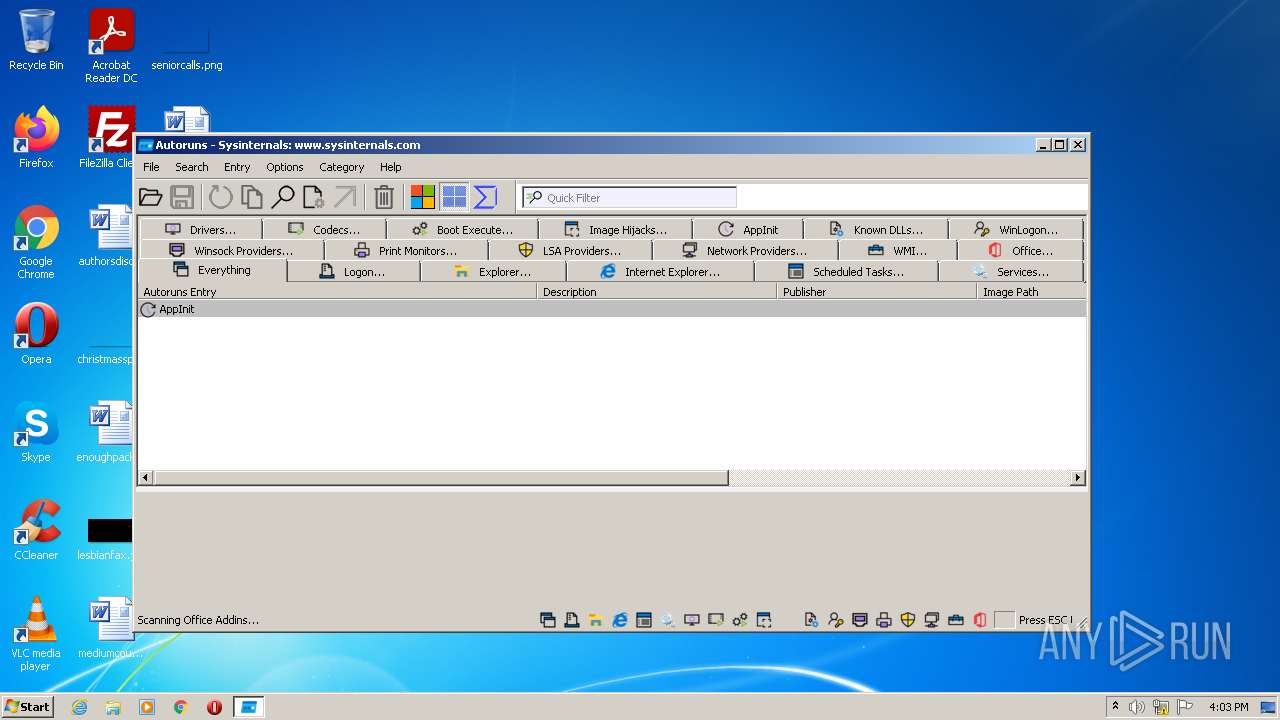
Total processes
39
Monitored processes
2
Malicious processes
2
Suspicious processes
0
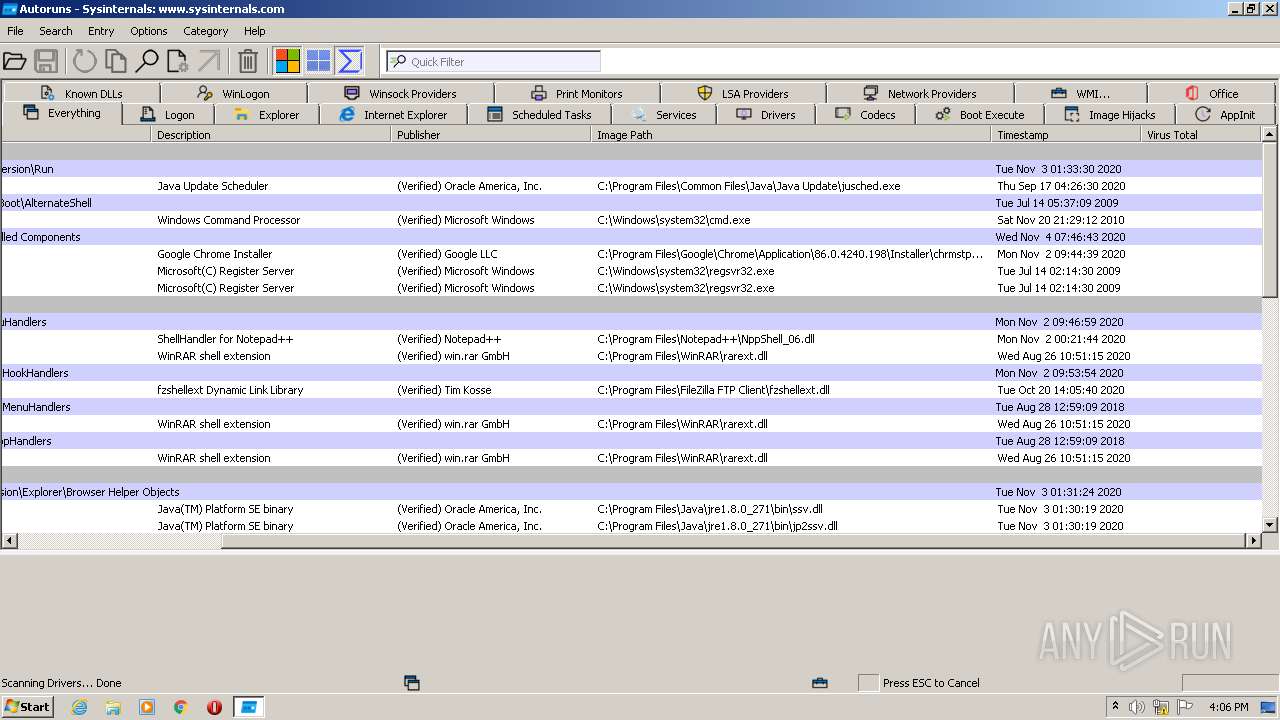
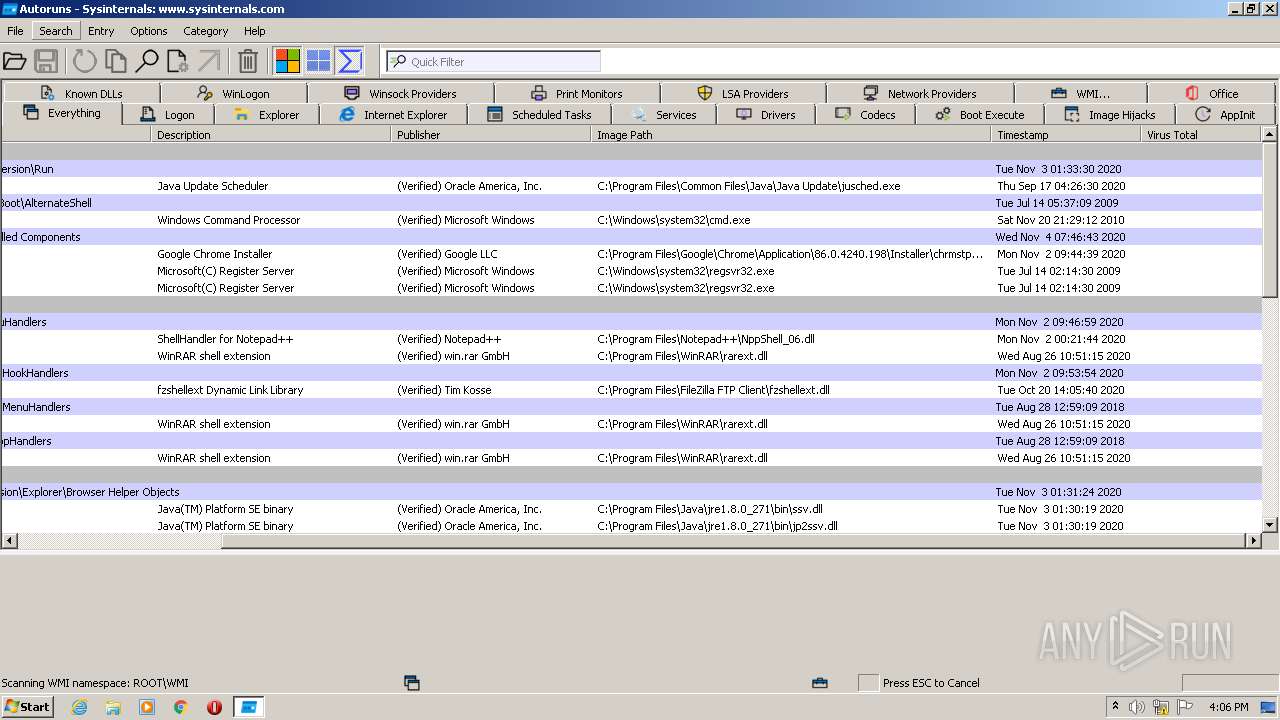
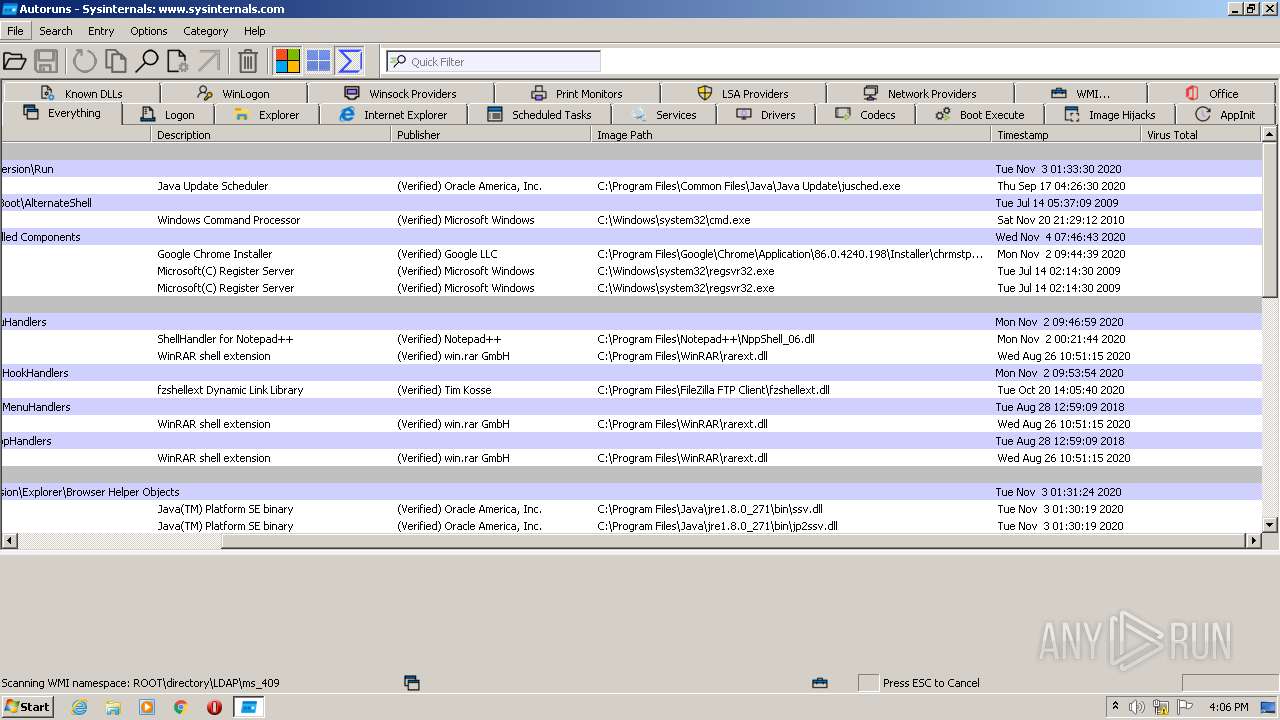
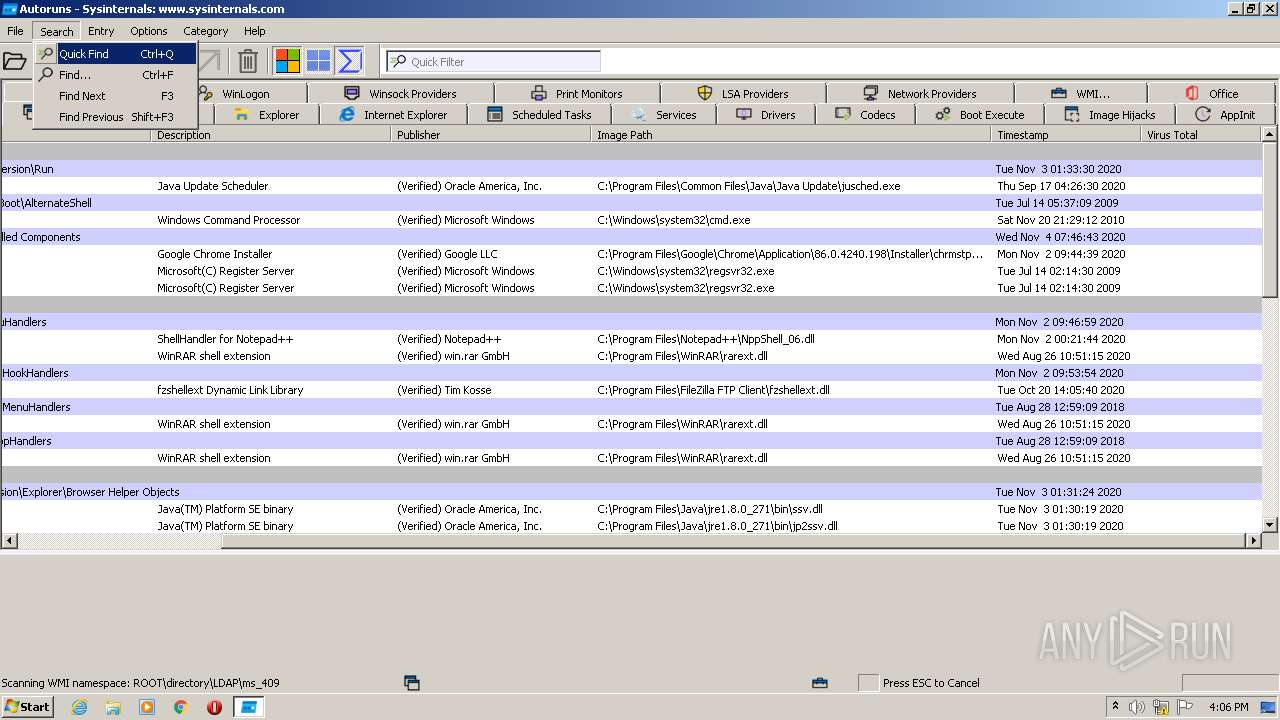
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2212 | "C:\Users\admin\AppData\Local\Temp\Autoruns.exe" | C:\Users\admin\AppData\Local\Temp\Autoruns.exe | Autoruns.exe | ||||||||||||
User: admin Company: Sysinternals - www.sysinternals.com Integrity Level: HIGH Description: Autostart program viewer Exit code: 0 Version: 14.09 Modules
| |||||||||||||||
| 2592 | "C:\Users\admin\AppData\Local\Temp\Autoruns.exe" | C:\Users\admin\AppData\Local\Temp\Autoruns.exe | Explorer.EXE | ||||||||||||
User: admin Company: Sysinternals - www.sysinternals.com Integrity Level: MEDIUM Description: Autostart program viewer Exit code: 1 Version: 14.09 Modules
| |||||||||||||||
Total events
248 637
Read events
248 259
Write events
378
Delete events
0
Modification events
| (PID) Process: | (2592) Autoruns.exe | Key: | HKEY_CURRENT_USER\Software\Sysinternals\Autoruns |
| Operation: | write | Name: | EulaAccepted |
Value: 1 | |||
| (PID) Process: | (2592) Autoruns.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\16C\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (2592) Autoruns.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\16C\52C64B7E |
| Operation: | write | Name: | @%SystemRoot%\System32\wshtcpip.dll,-60100 |
Value: MSAFD Tcpip [TCP/IP] | |||
| (PID) Process: | (2592) Autoruns.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\16C\52C64B7E |
| Operation: | write | Name: | @%SystemRoot%\System32\wshtcpip.dll,-60101 |
Value: MSAFD Tcpip [UDP/IP] | |||
| (PID) Process: | (2592) Autoruns.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\16C\52C64B7E |
| Operation: | write | Name: | @%SystemRoot%\System32\wshtcpip.dll,-60102 |
Value: MSAFD Tcpip [RAW/IP] | |||
| (PID) Process: | (2592) Autoruns.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\16C\52C64B7E |
| Operation: | write | Name: | @%SystemRoot%\System32\wship6.dll,-60100 |
Value: MSAFD Tcpip [TCP/IPv6] | |||
| (PID) Process: | (2592) Autoruns.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\16C\52C64B7E |
| Operation: | write | Name: | @%SystemRoot%\System32\wship6.dll,-60101 |
Value: MSAFD Tcpip [UDP/IPv6] | |||
| (PID) Process: | (2592) Autoruns.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\16C\52C64B7E |
| Operation: | write | Name: | @%SystemRoot%\System32\wship6.dll,-60102 |
Value: MSAFD Tcpip [RAW/IPv6] | |||
| (PID) Process: | (2592) Autoruns.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\16C\52C64B7E |
| Operation: | write | Name: | @%SystemRoot%\System32\wshqos.dll,-100 |
Value: RSVP TCPv6 Service Provider | |||
| (PID) Process: | (2592) Autoruns.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\16C\52C64B7E |
| Operation: | write | Name: | @%SystemRoot%\System32\wshqos.dll,-101 |
Value: RSVP TCP Service Provider | |||
Executable files
0
Suspicious files
13
Text files
0
Unknown types
9
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2592 | Autoruns.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\A583E2A51BFBDC1E492A57B7C8325850 | der | |
MD5:— | SHA256:— | |||
| 2592 | Autoruns.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\4C7F163ED126D5C3CB9457F68EC64E9E | der | |
MD5:— | SHA256:— | |||
| 2592 | Autoruns.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\A583E2A51BFBDC1E492A57B7C8325850 | binary | |
MD5:— | SHA256:— | |||
| 2592 | Autoruns.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\4C7F163ED126D5C3CB9457F68EC64E9E | binary | |
MD5:— | SHA256:— | |||
| 2592 | Autoruns.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\696F3DE637E6DE85B458996D49D759AD | binary | |
MD5:— | SHA256:— | |||
| 2592 | Autoruns.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\57C8EDB95DF3F0AD4EE2DC2B8CFD4157 | binary | |
MD5:— | SHA256:— | |||
| 2592 | Autoruns.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\57C8EDB95DF3F0AD4EE2DC2B8CFD4157 | compressed | |
MD5:F7DCB24540769805E5BB30D193944DCE | SHA256:6B88C6AC55BBD6FEA0EBE5A760D1AD2CFCE251C59D0151A1400701CB927E36EA | |||
| 2592 | Autoruns.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\73B97032D4E1E3BA6D88F3C20916B632 | binary | |
MD5:— | SHA256:— | |||
| 2592 | Autoruns.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\696F3DE637E6DE85B458996D49D759AD | der | |
MD5:6872FAE8288DB34207D9E7EE350157F4 | SHA256:50795B027E2BC566D3B7ACB89913F8EFD23B70615C9DB9BF5B23323AD3132A7D | |||
| 2592 | Autoruns.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\77EC63BDA74BD0D0E0426DC8F8008506 | compressed | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
10
TCP/UDP connections
5
DNS requests
3
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2592 | Autoruns.exe | GET | 200 | 8.253.95.120:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?75a8b94757507a47 | US | compressed | 4.70 Kb | whitelisted |
2592 | Autoruns.exe | GET | 200 | 92.123.224.184:80 | http://crl.microsoft.com/pki/crl/products/MicTimStaPCA_2010-07-01.crl | unknown | der | 555 b | whitelisted |
2592 | Autoruns.exe | GET | 200 | 104.79.89.142:80 | http://www.microsoft.com/pkiops/crl/MicWinProPCA2011_2011-10-19.crl | US | der | 564 b | whitelisted |
2592 | Autoruns.exe | GET | 200 | 92.123.224.184:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut_2010-06-23.crl | unknown | der | 824 b | whitelisted |
2592 | Autoruns.exe | GET | 200 | 8.253.95.120:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/authrootstl.cab?8773f936f45f3e56 | US | compressed | 60.0 Kb | whitelisted |
2592 | Autoruns.exe | GET | 200 | 104.79.89.142:80 | http://www.microsoft.com/pkiops/certs/Microsoft%20Development%20Root%20Certificate%20Authority%202014.crt | US | der | 1.51 Kb | whitelisted |
2592 | Autoruns.exe | GET | 200 | 92.123.224.184:80 | http://crl.microsoft.com/pki/crl/products/WinPCA.crl | unknown | der | 530 b | whitelisted |
2592 | Autoruns.exe | GET | 200 | 92.123.224.184:80 | http://crl.microsoft.com/pki/crl/products/MicrosoftTimeStampPCA.crl | unknown | der | 519 b | whitelisted |
2592 | Autoruns.exe | GET | 200 | 104.79.89.142:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20Windows%20Verification%20PCA(1).crl | US | der | 532 b | whitelisted |
2592 | Autoruns.exe | GET | 200 | 92.123.224.184:80 | http://crl.microsoft.com/pki/crl/products/microsoftrootcert.crl | unknown | der | 767 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2592 | Autoruns.exe | 8.253.95.120:80 | ctldl.windowsupdate.com | Global Crossing | US | suspicious |
2592 | Autoruns.exe | 104.79.89.142:80 | www.microsoft.com | Time Warner Cable Internet LLC | US | unknown |
2592 | Autoruns.exe | 92.123.224.184:80 | crl.microsoft.com | Akamai International B.V. | — | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
ctldl.windowsupdate.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |