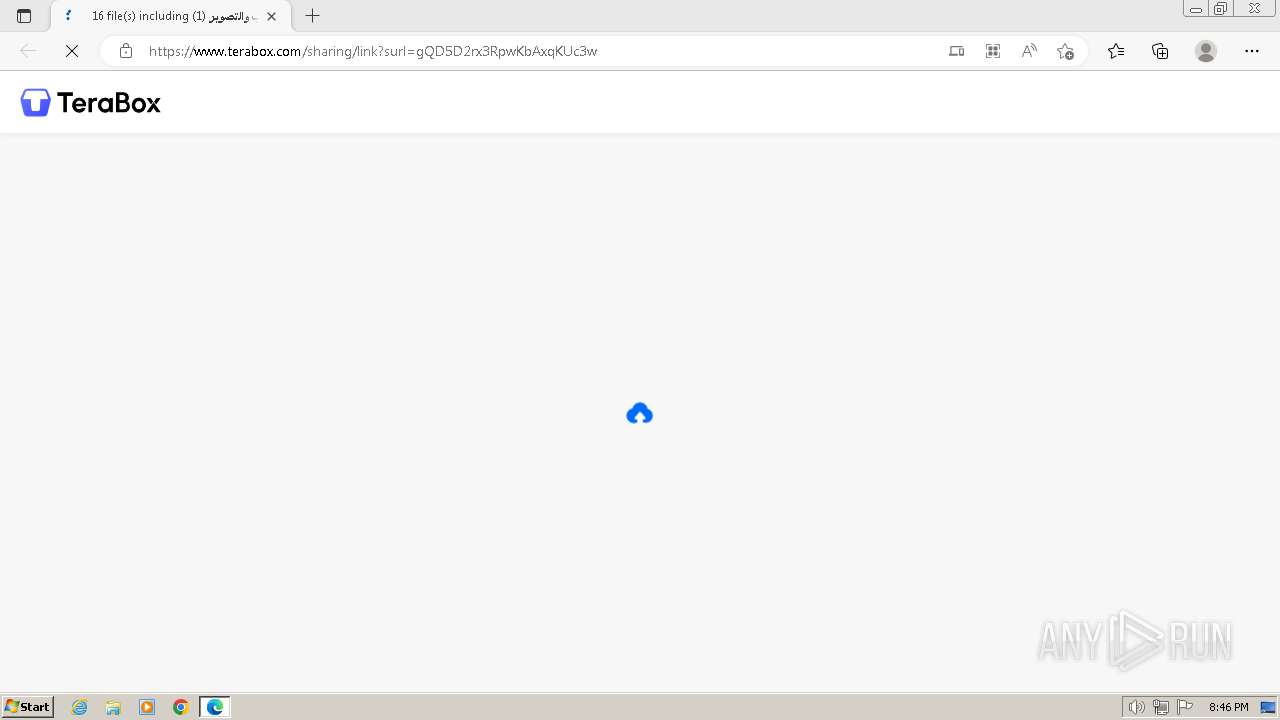
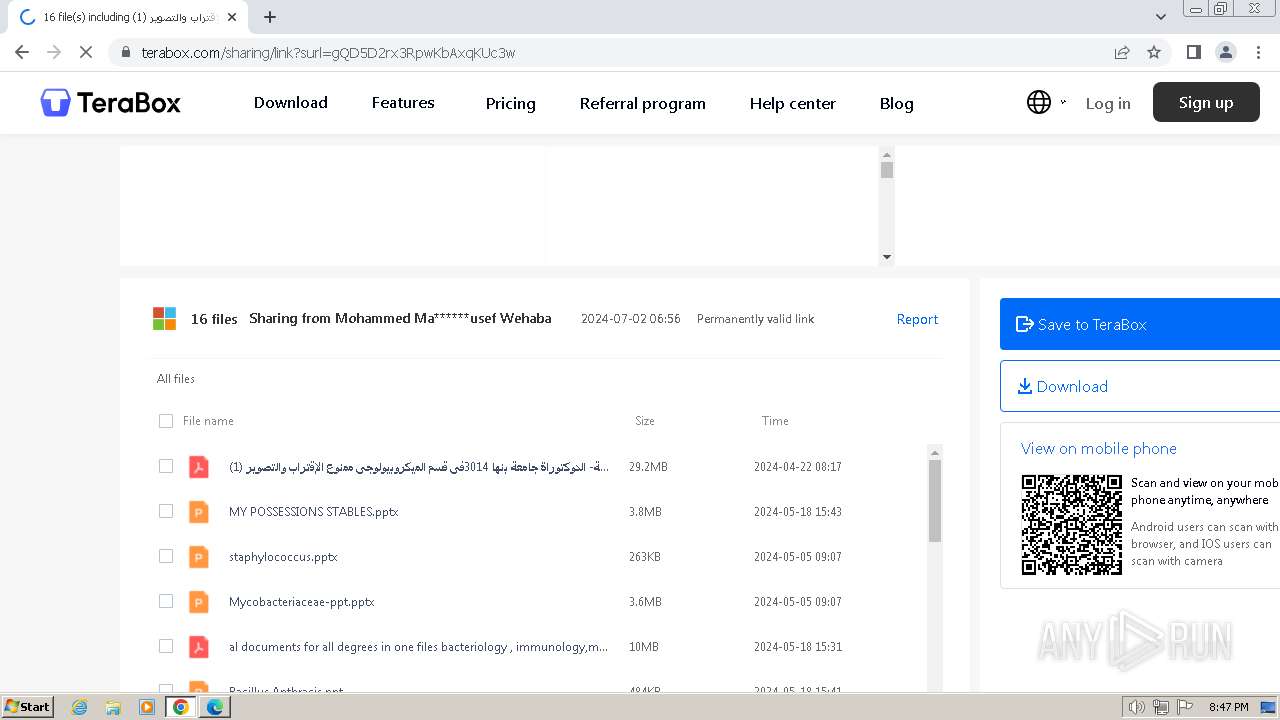
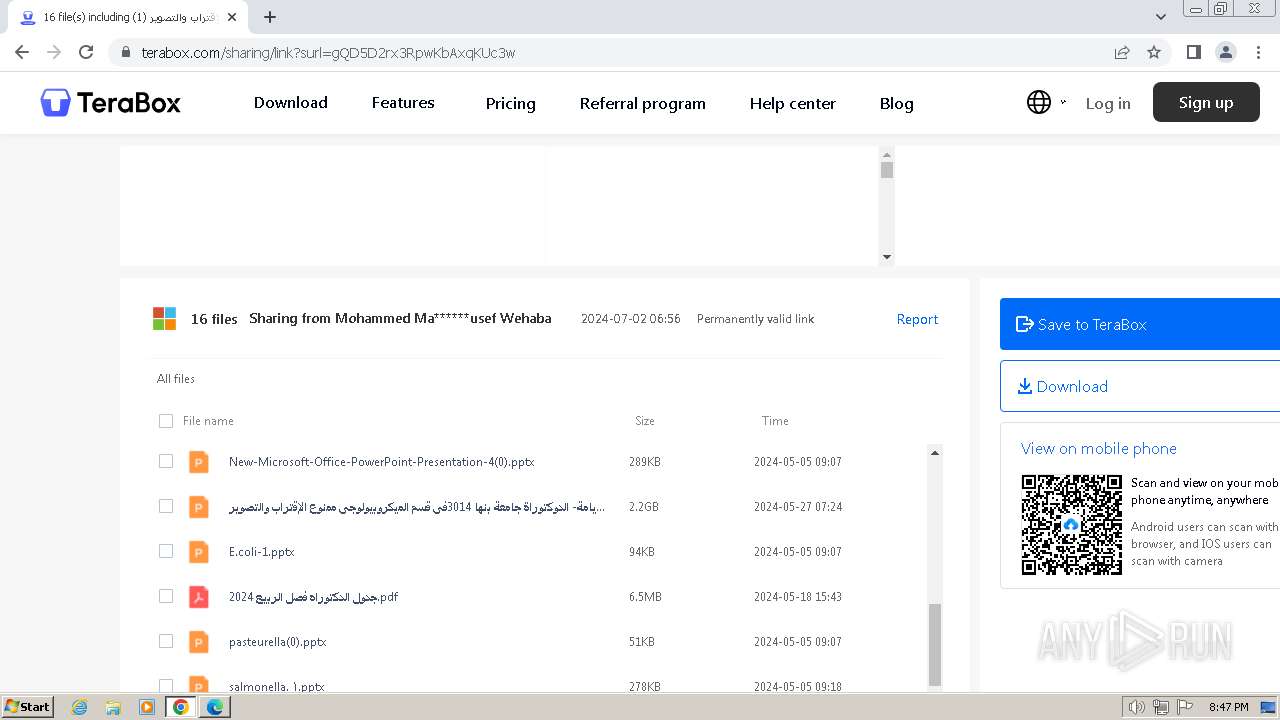
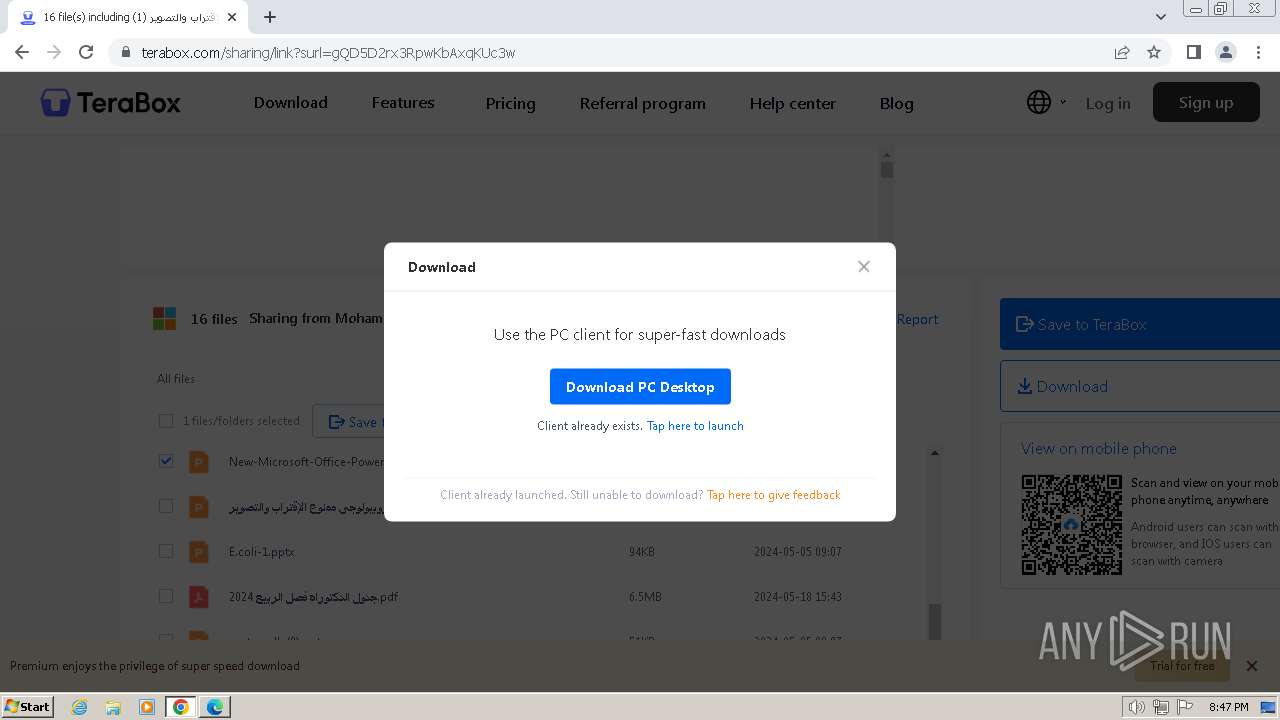
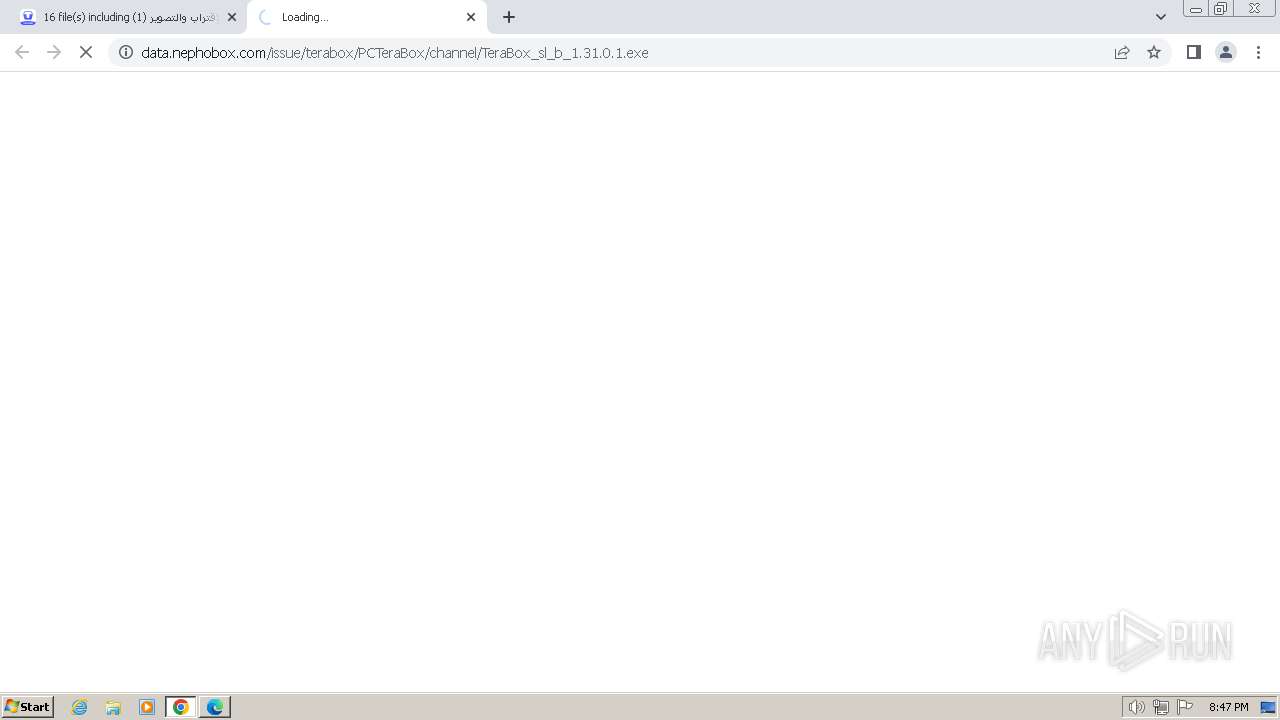
| URL: | https://terabox.com/s/1gQD5D2rx3RpwKbAxqKUc3w |
| Full analysis: | https://app.any.run/tasks/92e73686-1c41-4b6e-91e8-5b202fcfb1b4 |
| Verdict: | Malicious activity |
| Analysis date: | July 02, 2024, 19:46:43 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MD5: | 4D20FD16FE07C02E5CE50EFD9D3E4E96 |
| SHA1: | 289FE9D4CAA641C2504C6C88F96C4DC56555CDE1 |
| SHA256: | 64C8BBBA038B600E7AB57228ECC08803D01083E4B5E9C240965E705E8F71A3D3 |
| SSDEEP: | 3:N8IUq2eBE3VedjV:2IV2eBey |
MALICIOUS
Changes the autorun value in the registry
- TeraBox.exe (PID: 1976)
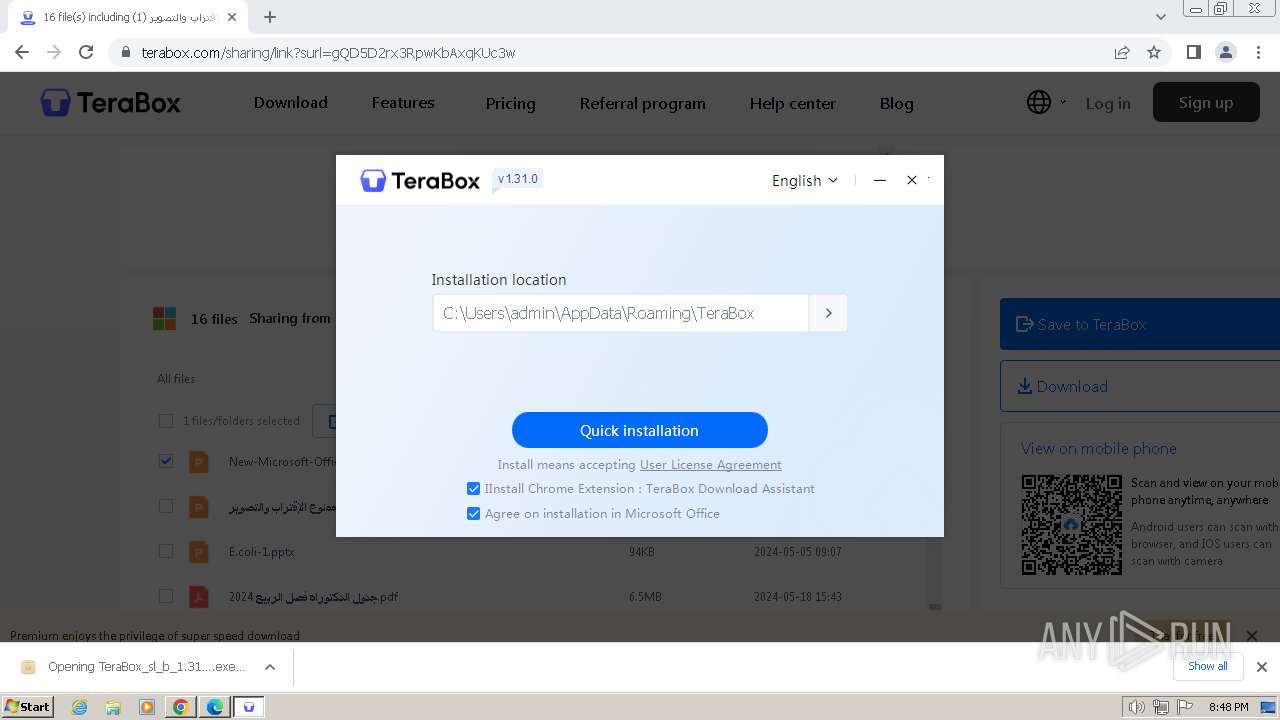
Registers / Runs the DLL via REGSVR32.EXE
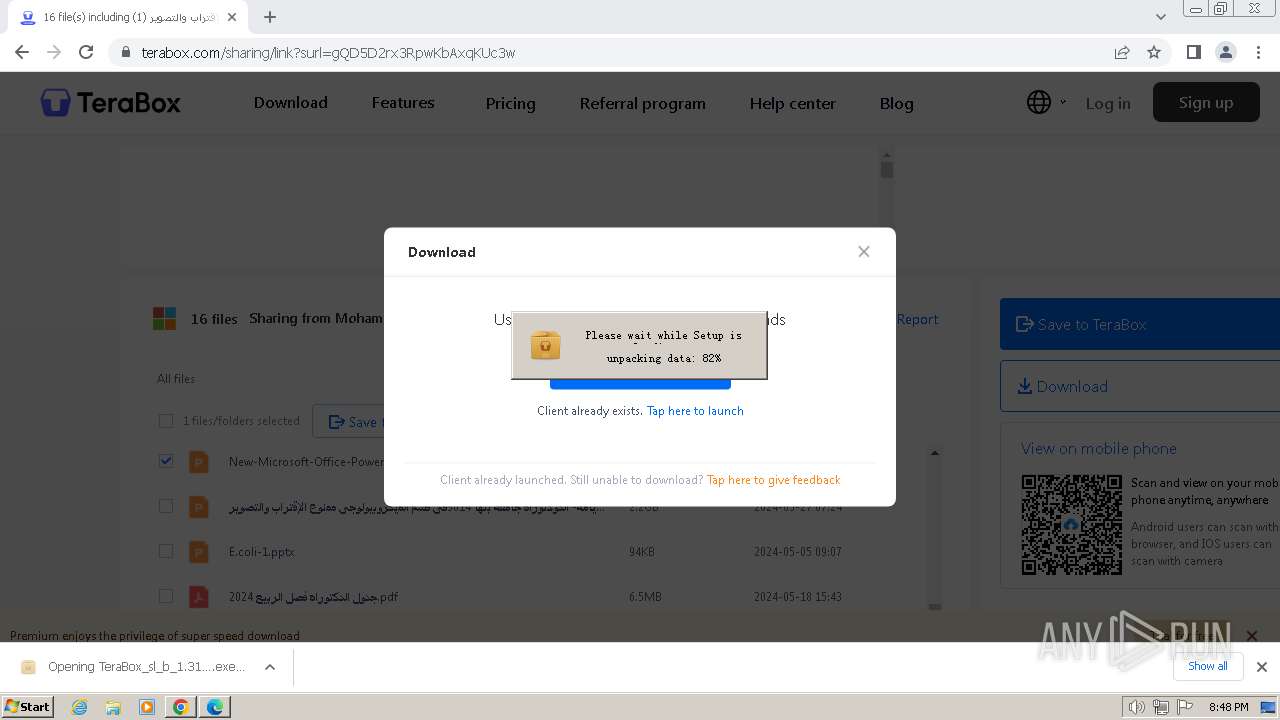
- TeraBox_sl_b_1.31.0.1.exe (PID: 3016)
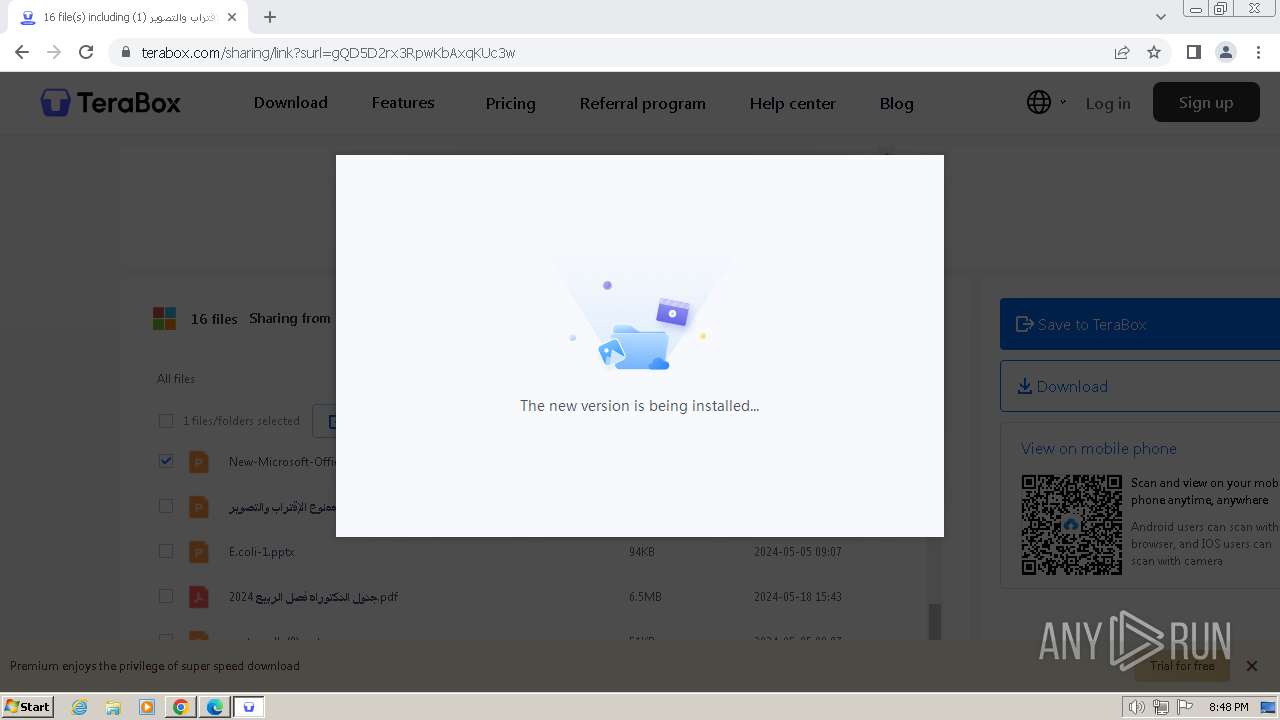
Drops the executable file immediately after the start
- TeraBox_sl_b_1.31.0.1.exe (PID: 3016)
Creates a writable file in the system directory
- YunUtilityService.exe (PID: 3772)
SUSPICIOUS
The process creates files with name similar to system file names
- TeraBox_sl_b_1.31.0.1.exe (PID: 3016)
- TeraBoxRender.exe (PID: 1944)
Executable content was dropped or overwritten
- TeraBox_sl_b_1.31.0.1.exe (PID: 3016)
Reads the date of Windows installation
- TeraBox.exe (PID: 1976)
Creates a software uninstall entry
- TeraBox_sl_b_1.31.0.1.exe (PID: 3016)
Creates/Modifies COM task schedule object
- regsvr32.exe (PID: 3708)
- regsvr32.exe (PID: 964)
Reads security settings of Internet Explorer
- TeraBoxWebService.exe (PID: 3972)
- TeraBox.exe (PID: 1744)
- AutoUpdate.exe (PID: 444)
Reads the Internet Settings
- TeraBoxWebService.exe (PID: 3972)
- TeraBox.exe (PID: 1744)
- AutoUpdate.exe (PID: 444)
Reads settings of System Certificates
- TeraBox.exe (PID: 1744)
- AutoUpdate.exe (PID: 444)
- TeraBoxRender.exe (PID: 3132)
Checks Windows Trust Settings
- TeraBox.exe (PID: 1744)
- YunUtilityService.exe (PID: 3772)
- AutoUpdate.exe (PID: 444)
Malware-specific behavior (creating "System.dll" in Temp)
- TeraBox_sl_b_1.31.0.1.exe (PID: 3016)
Process drops legitimate windows executable
- TeraBox_sl_b_1.31.0.1.exe (PID: 3016)
Executes as Windows Service
- YunUtilityService.exe (PID: 3772)
Adds/modifies Windows certificates
- YunUtilityService.exe (PID: 3772)
The process drops C-runtime libraries
- TeraBox_sl_b_1.31.0.1.exe (PID: 3016)
INFO
Application launched itself
- msedge.exe (PID: 3260)
- chrome.exe (PID: 1428)
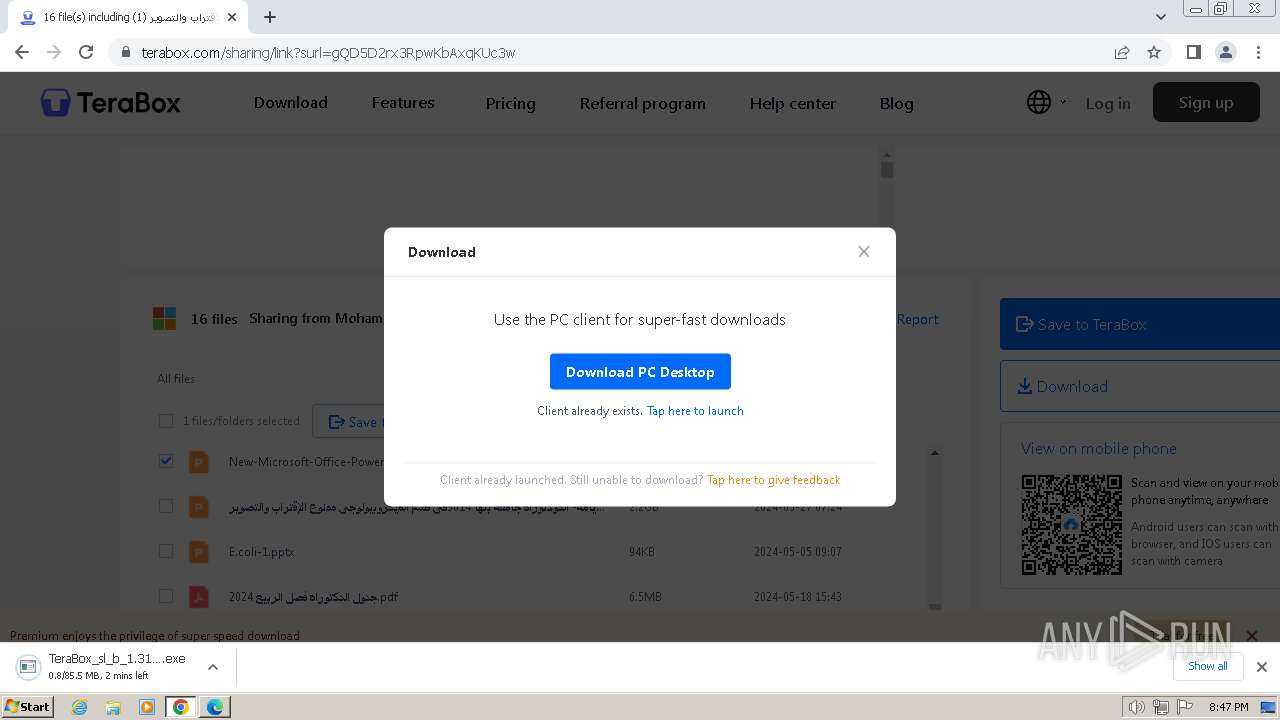
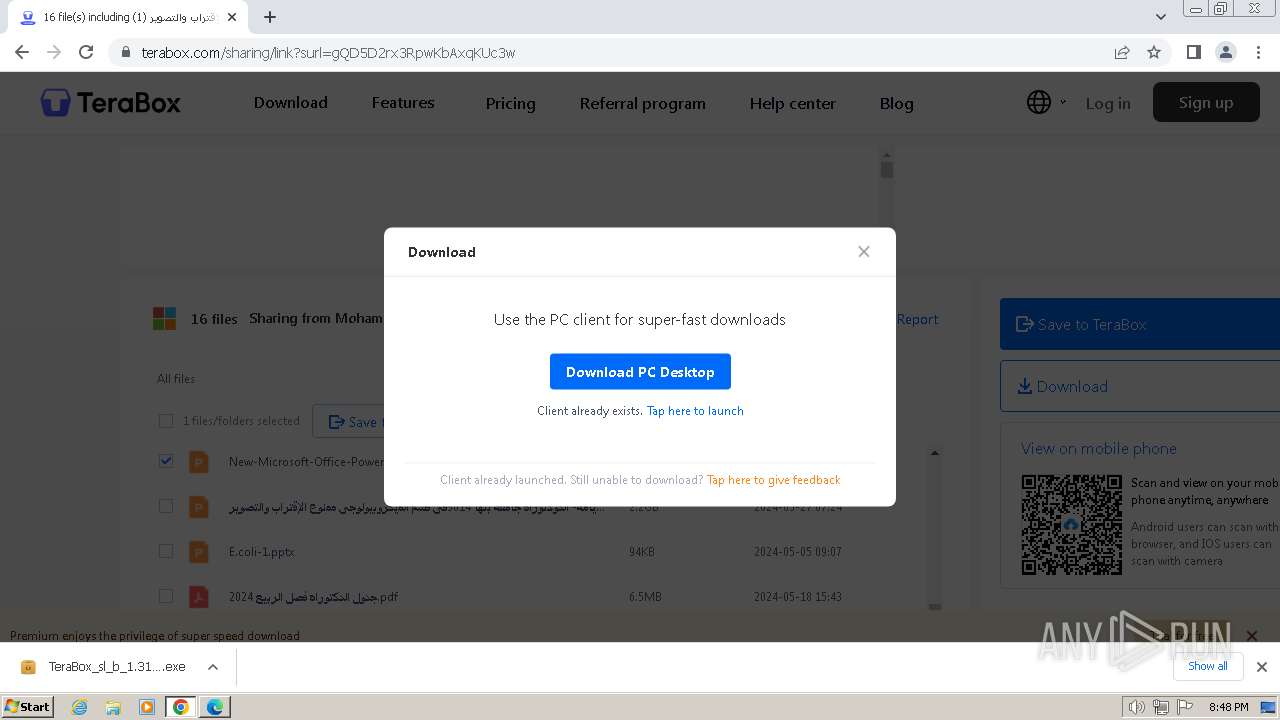
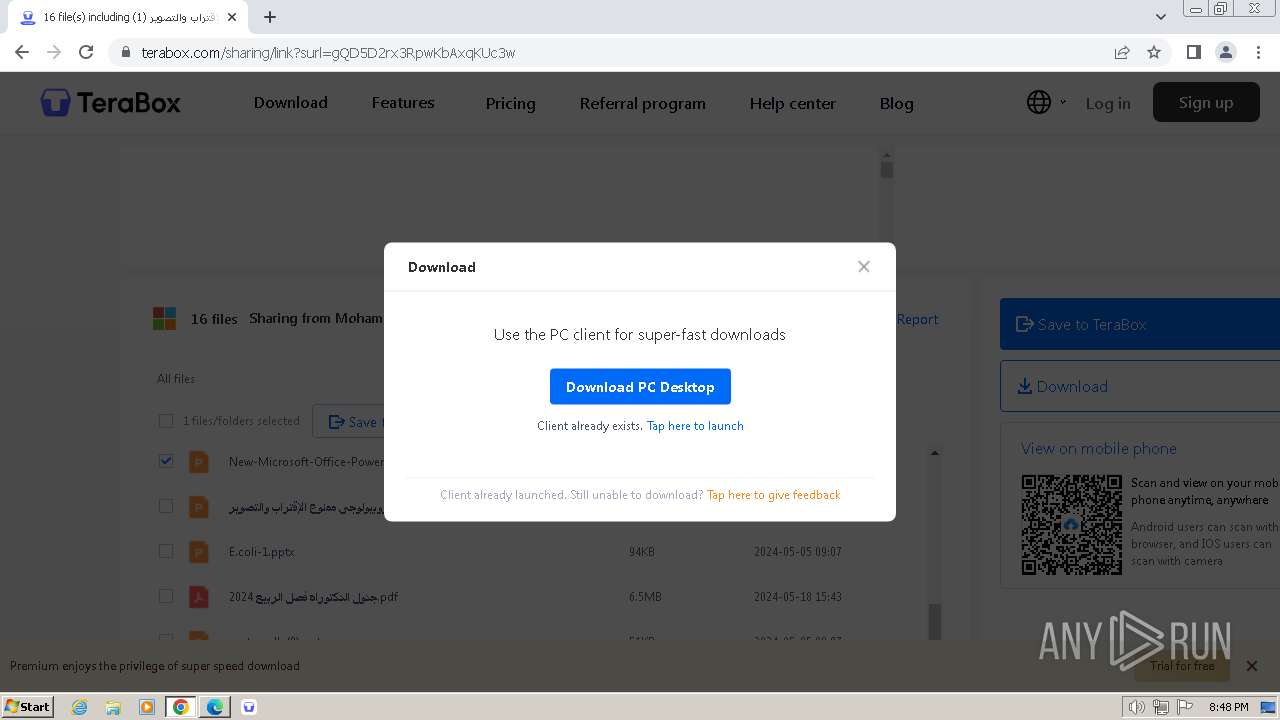
Manual execution by a user
- chrome.exe (PID: 1428)
- wmpnscfg.exe (PID: 1284)
Drops the executable file immediately after the start
- chrome.exe (PID: 1428)
- chrome.exe (PID: 900)
- chrome.exe (PID: 1748)
Executable content was dropped or overwritten
- chrome.exe (PID: 1428)
- chrome.exe (PID: 900)
- chrome.exe (PID: 1748)
The process uses the downloaded file
- chrome.exe (PID: 1140)
- chrome.exe (PID: 1428)
Reads the computer name
- TeraBox_sl_b_1.31.0.1.exe (PID: 3016)
- TeraBox.exe (PID: 1976)
- YunUtilityService.exe (PID: 3456)
- TeraBox.exe (PID: 1744)
- TeraBoxWebService.exe (PID: 3972)
- TeraBoxRender.exe (PID: 1944)
- TeraBoxRender.exe (PID: 3132)
- TeraBoxRender.exe (PID: 3212)
- YunUtilityService.exe (PID: 3772)
- TeraBoxHost.exe (PID: 3044)
- TeraBoxHost.exe (PID: 3596)
- AutoUpdate.exe (PID: 444)
- wmpnscfg.exe (PID: 1284)
Reads Environment values
- TeraBox_sl_b_1.31.0.1.exe (PID: 3016)
Create files in a temporary directory
- TeraBox_sl_b_1.31.0.1.exe (PID: 3016)
- TeraBox.exe (PID: 1744)
- TeraBoxRender.exe (PID: 3132)
Creates files or folders in the user directory
- TeraBox.exe (PID: 1976)
- TeraBox.exe (PID: 1744)
- TeraBoxWebService.exe (PID: 3972)
- TeraBox_sl_b_1.31.0.1.exe (PID: 3016)
- TeraBoxHost.exe (PID: 3044)
- TeraBoxHost.exe (PID: 3596)
- AutoUpdate.exe (PID: 444)
Reads the machine GUID from the registry
- TeraBox.exe (PID: 1976)
- TeraBox.exe (PID: 1744)
- TeraBoxWebService.exe (PID: 3972)
- TeraBoxRender.exe (PID: 3132)
- YunUtilityService.exe (PID: 3772)
- TeraBoxHost.exe (PID: 3044)
- AutoUpdate.exe (PID: 444)
Checks supported languages
- TeraBoxWebService.exe (PID: 3592)
- YunUtilityService.exe (PID: 3456)
- TeraBox.exe (PID: 1744)
- TeraBoxWebService.exe (PID: 3972)
- TeraBoxRender.exe (PID: 1944)
- TeraBoxRender.exe (PID: 1196)
- TeraBoxRender.exe (PID: 3204)
- TeraBoxRender.exe (PID: 3132)
- TeraBox.exe (PID: 1976)
- YunUtilityService.exe (PID: 3772)
- TeraBoxRender.exe (PID: 3212)
- TeraBoxHost.exe (PID: 3044)
- TeraBoxHost.exe (PID: 3596)
- AutoUpdate.exe (PID: 444)
- TeraBox_sl_b_1.31.0.1.exe (PID: 3016)
- wmpnscfg.exe (PID: 1284)
Checks proxy server information
- TeraBoxWebService.exe (PID: 3972)
- TeraBox.exe (PID: 1744)
- AutoUpdate.exe (PID: 444)
Process checks computer location settings
- TeraBox.exe (PID: 1744)
- TeraBoxRender.exe (PID: 1196)
- TeraBoxRender.exe (PID: 3204)
Reads the software policy settings
- TeraBox.exe (PID: 1744)
- TeraBoxRender.exe (PID: 3132)
- YunUtilityService.exe (PID: 3772)
- AutoUpdate.exe (PID: 444)
VMProtect protector has been detected
- TeraBoxHost.exe (PID: 3044)
Creates files in the program directory
- TeraBoxHost.exe (PID: 3044)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
120
Monitored processes
76
Malicious processes
6
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 312 | "C:\Program Files\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --mojo-platform-channel-handle=3416 --field-trial-handle=1356,i,9157590743650421898,1809091974747508563,131072 /prefetch:8 | C:\Program Files\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 109.0.1518.115 Modules
| |||||||||||||||
| 324 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=network.mojom.NetworkService --lang=en-US --service-sandbox-type=none --disable-quic --mojo-platform-channel-handle=1276 --field-trial-handle=1168,i,16992222878394433419,4439677709373685991,131072 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | chrome.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Version: 109.0.5414.120 Modules
| |||||||||||||||
| 444 | "C:\Users\admin\AppData\Roaming\TeraBox\AutoUpdate\AutoUpdate.exe" -client_info "C:\Users\admin\AppData\Local\Temp\TeraBox_status" -update_cfg_url "aHR0cHM6Ly90ZXJhYm94LmNvbS9hdXRvdXBkYXRl" -srvwnd 701d0 -unlogin | C:\Users\admin\AppData\Roaming\TeraBox\AutoUpdate\AutoUpdate.exe | TeraBox.exe | ||||||||||||
User: admin Company: Flextech Inc. Integrity Level: MEDIUM Description: TeraBoxUpdate Exit code: 0 Version: 1.31.0.1 Modules
| |||||||||||||||
| 568 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --disable-quic --mojo-platform-channel-handle=948 --field-trial-handle=1168,i,16992222878394433419,4439677709373685991,131072 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
| 744 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --disable-gpu-compositing --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=14 --mojo-platform-channel-handle=3904 --field-trial-handle=1168,i,16992222878394433419,4439677709373685991,131072 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Version: 109.0.5414.120 Modules
| |||||||||||||||
| 900 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=chrome.mojom.UtilWin --lang=en-US --service-sandbox-type=none --disable-quic --mojo-platform-channel-handle=3836 --field-trial-handle=1168,i,16992222878394433419,4439677709373685991,131072 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
| 900 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --disable-quic --mojo-platform-channel-handle=4544 --field-trial-handle=1168,i,16992222878394433419,4439677709373685991,131072 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | chrome.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
| 964 | "C:\Windows\system32\regsvr32.exe" "/s" "C:\Users\admin\AppData\Roaming\TeraBox\YunOfficeAddin.dll" | C:\Windows\System32\regsvr32.exe | — | TeraBox_sl_b_1.31.0.1.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft(C) Register Server Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 980 | "C:\Program Files\Microsoft\Edge\Application\msedge.exe" --type=renderer --first-renderer-process --lang=en-US --js-flags=--ms-user-locale= --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=6 --mojo-platform-channel-handle=2152 --field-trial-handle=1356,i,9157590743650421898,1809091974747508563,131072 /prefetch:1 | C:\Program Files\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Version: 109.0.1518.115 Modules
| |||||||||||||||
| 1044 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --disable-gpu-compositing --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=11 --mojo-platform-channel-handle=3896 --field-trial-handle=1168,i,16992222878394433419,4439677709373685991,131072 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 109.0.5414.120 Modules
| |||||||||||||||
Total events
67 504
Read events
66 869
Write events
595
Delete events
40
Modification events
| (PID) Process: | (3260) msedge.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (3260) msedge.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (3260) msedge.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Edge\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (3260) msedge.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Edge\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (3260) msedge.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (3260) msedge.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\EdgeUpdate\ClientState\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (3260) msedge.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Edge\StabilityMetrics |
| Operation: | write | Name: | user_experience_metrics.stability.exited_cleanly |
Value: 0 | |||
| (PID) Process: | (3260) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1302019708-1500728564-335382590-1000 |
Value: 10C6E541DF7A2F00 | |||
| (PID) Process: | (3260) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\FirstNotDefault |
| Operation: | delete value | Name: | S-1-5-21-1302019708-1500728564-335382590-1000 |
Value: | |||
| (PID) Process: | (3260) msedge.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Edge |
| Operation: | write | Name: | UsageStatsInSample |
Value: 1 | |||
Executable files
86
Suspicious files
661
Text files
121
Unknown types
220
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3260 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old~RF4def2.TMP | — | |
MD5:— | SHA256:— | |||
| 3260 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 3260 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old~RF4df12.TMP | — | |
MD5:— | SHA256:— | |||
| 3260 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old | — | |
MD5:— | SHA256:— | |||
| 3260 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\LOG.old~RF4df40.TMP | — | |
MD5:— | SHA256:— | |||
| 3260 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\LOG.old | — | |
MD5:— | SHA256:— | |||
| 3260 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Crashpad\settings.dat | binary | |
MD5:4B74C392839DDD59792975091A30DB00 | SHA256:7A5A3B8CC4D5BB579FA5E6C6A831964FB245A5CFF9AD3B80F5E9DC34DA4A7D53 | |||
| 3260 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\Service Worker\Database\LOG.old | text | |
MD5:7D952F199B55B9FF30CBFA594212118D | SHA256:044142A8DF492BF8517CAE73ECD782D98474ACE2D4807FED07B5CDCED4D5CF46 | |||
| 3344 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\CrashpadMetrics.pma | binary | |
MD5:886E82F2CA62ECCCE64601B30592078A | SHA256:E5E13D53601100FF3D6BB71514CBCCC4C73FE9B7EF5E930100E644187B42948E | |||
| 3260 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Variations | binary | |
MD5:961E3604F228B0D10541EBF921500C86 | SHA256:F7B24F2EB3D5EB0550527490395D2F61C3D2FE74BB9CB345197DAD81B58B5FED | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
62
TCP/UDP connections
170
DNS requests
171
Threats
91
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
1372 | svchost.exe | GET | 304 | 217.20.57.40:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?33775f6043c93e33 | unknown | — | — | unknown |
1372 | svchost.exe | GET | 200 | 88.221.169.152:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | unknown |
1372 | svchost.exe | GET | 200 | 2.19.11.105:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | unknown |
844 | svchost.exe | HEAD | 200 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvZjQwNTJmYzgtMzk5Yi00OTMxLTk0ZTQtMDlmZDM1MDk0MDM5/1.0.0.16_llkgjffcdpffmhiakmfcdcblohccpfmo.crx | unknown | — | — | unknown |
1060 | svchost.exe | GET | 304 | 217.20.57.18:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?a9f83325acc8ca75 | unknown | — | — | unknown |
844 | svchost.exe | HEAD | 200 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/adwaiz7g7wgja7jchnjhwbmhcy7a_20240624.647838354.14/obedbbhbpmojnkanicioggnmelmoomoc_20240624.647838354.14_all_ENUS500000_elxqk7lklxhgg5gymzglma3fei.crx3 | unknown | — | — | unknown |
844 | svchost.exe | GET | 200 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvZjQwNTJmYzgtMzk5Yi00OTMxLTk0ZTQtMDlmZDM1MDk0MDM5/1.0.0.16_llkgjffcdpffmhiakmfcdcblohccpfmo.crx | unknown | — | — | unknown |
844 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/adwaiz7g7wgja7jchnjhwbmhcy7a_20240624.647838354.14/obedbbhbpmojnkanicioggnmelmoomoc_20240624.647838354.14_all_ENUS500000_elxqk7lklxhgg5gymzglma3fei.crx3 | unknown | — | — | unknown |
844 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/adwaiz7g7wgja7jchnjhwbmhcy7a_20240624.647838354.14/obedbbhbpmojnkanicioggnmelmoomoc_20240624.647838354.14_all_ENUS500000_elxqk7lklxhgg5gymzglma3fei.crx3 | unknown | — | — | unknown |
844 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/adwaiz7g7wgja7jchnjhwbmhcy7a_20240624.647838354.14/obedbbhbpmojnkanicioggnmelmoomoc_20240624.647838354.14_all_ENUS500000_elxqk7lklxhgg5gymzglma3fei.crx3 | unknown | — | — | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3260 | msedge.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
1372 | svchost.exe | 51.104.136.2:443 | — | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
2300 | msedge.exe | 204.79.197.239:443 | edge.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | unknown |
2300 | msedge.exe | 13.107.42.16:443 | config.edge.skype.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
2300 | msedge.exe | 210.148.85.47:443 | terabox.com | Internet Initiative Japan Inc. | JP | unknown |
1060 | svchost.exe | 224.0.0.252:5355 | — | — | — | unknown |
2564 | svchost.exe | 239.255.255.250:3702 | — | — | — | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
2300 | msedge.exe | 128.1.34.164:443 | www.staticcc.com | ZEN-ECN | DE | unknown |
DNS requests
Domain | IP | Reputation |
|---|---|---|
config.edge.skype.com |
| whitelisted |
terabox.com |
| unknown |
edge.microsoft.com |
| whitelisted |
www.terabox.com |
| unknown |
www.staticcc.com |
| unknown |
blog.terabox.com |
| unknown |
data.terabox.com |
| unknown |
ymg-api.terabox.com |
| unknown |
s2.teraboxcdn.com |
| unknown |
accounts.google.com |
| shared |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2300 | msedge.exe | Misc activity | ET INFO DNS Query to File Sharing Domain (terabox .com) |
2300 | msedge.exe | Misc activity | ET INFO DNS Query to File Sharing Domain (terabox .com) |
2300 | msedge.exe | Misc activity | ET INFO Observed File Sharing Domain (terabox .com in TLS SNI) |
2300 | msedge.exe | Misc activity | ET INFO Observed File Sharing Domain (terabox .com in TLS SNI) |
2300 | msedge.exe | Misc activity | ET INFO Observed File Sharing Domain (terabox .com in TLS SNI) |
2300 | msedge.exe | Misc activity | ET INFO DNS Query to File Sharing Domain (terabox .com) |
2300 | msedge.exe | Misc activity | ET INFO DNS Query to File Sharing Domain (terabox .com) |
2300 | msedge.exe | Misc activity | ET INFO Observed File Sharing Domain (terabox .com in TLS SNI) |
2300 | msedge.exe | Misc activity | ET INFO Observed File Sharing Domain (terabox .com in TLS SNI) |
2300 | msedge.exe | Misc activity | ET INFO DNS Query to File Sharing Domain (terabox .com) |
Process | Message |
|---|---|
TeraBoxHost.exe | vast_media--[2024-07-02 20:49:09:353] Initialized sdl_video_render_driver=software
|
TeraBoxHost.exe | vast_media--[2024-07-02 20:49:09:353] Initialized sdl_audio_play_driver=directsound
|
TeraBoxHost.exe | vast_media--[2024-07-02 20:49:09:353] Initialized hardware_type=3001
|