| File name: | MikuV4_eng.exe |
| Full analysis: | https://app.any.run/tasks/8c1097cf-ce8f-4e59-bfe3-5a9dd75b77be |
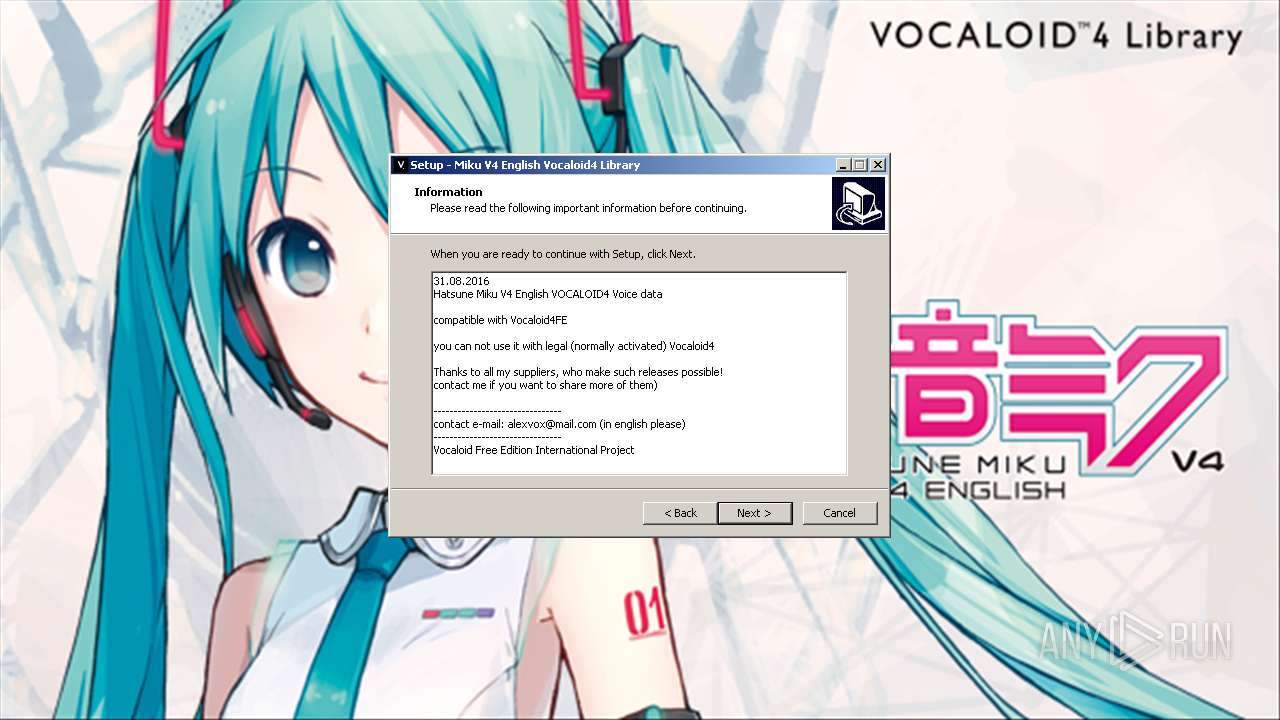
| Verdict: | Malicious activity |
| Analysis date: | April 23, 2024, 23:07:18 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | B6E8345FD264F444C730696B05A0022A |
| SHA1: | 7EF7D1D127FE501416A1AF2EE3C1208BE3B57E24 |
| SHA256: | 64A89EC75B5EB904137B8D44E8095E23DDA9CB55CB4AF7C2ECF697512F80FBCF |
| SSDEEP: | 98304:Q5LKpCi75Vfjg57/Q9W/Evy1NTk2QLhAC3:esVfC710y1NBQNZ |
MALICIOUS
Drops the executable file immediately after the start
- MikuV4_eng.exe (PID: 2032)
- MikuV4_eng.exe (PID: 2548)
- MikuV4_eng.tmp (PID: 3988)
SUSPICIOUS
Executable content was dropped or overwritten
- MikuV4_eng.exe (PID: 2032)
- MikuV4_eng.exe (PID: 2548)
- MikuV4_eng.tmp (PID: 3988)
Reads the Windows owner or organization settings
- MikuV4_eng.tmp (PID: 3988)
Non-standard symbols in registry
- MikuV4_eng.tmp (PID: 3988)
INFO
Checks supported languages
- MikuV4_eng.tmp (PID: 392)
- MikuV4_eng.exe (PID: 2032)
- MikuV4_eng.exe (PID: 2548)
- MikuV4_eng.tmp (PID: 3988)
Create files in a temporary directory
- MikuV4_eng.exe (PID: 2032)
- MikuV4_eng.exe (PID: 2548)
- MikuV4_eng.tmp (PID: 3988)
Reads the computer name
- MikuV4_eng.tmp (PID: 392)
- MikuV4_eng.tmp (PID: 3988)
Creates files in the program directory
- MikuV4_eng.tmp (PID: 3988)
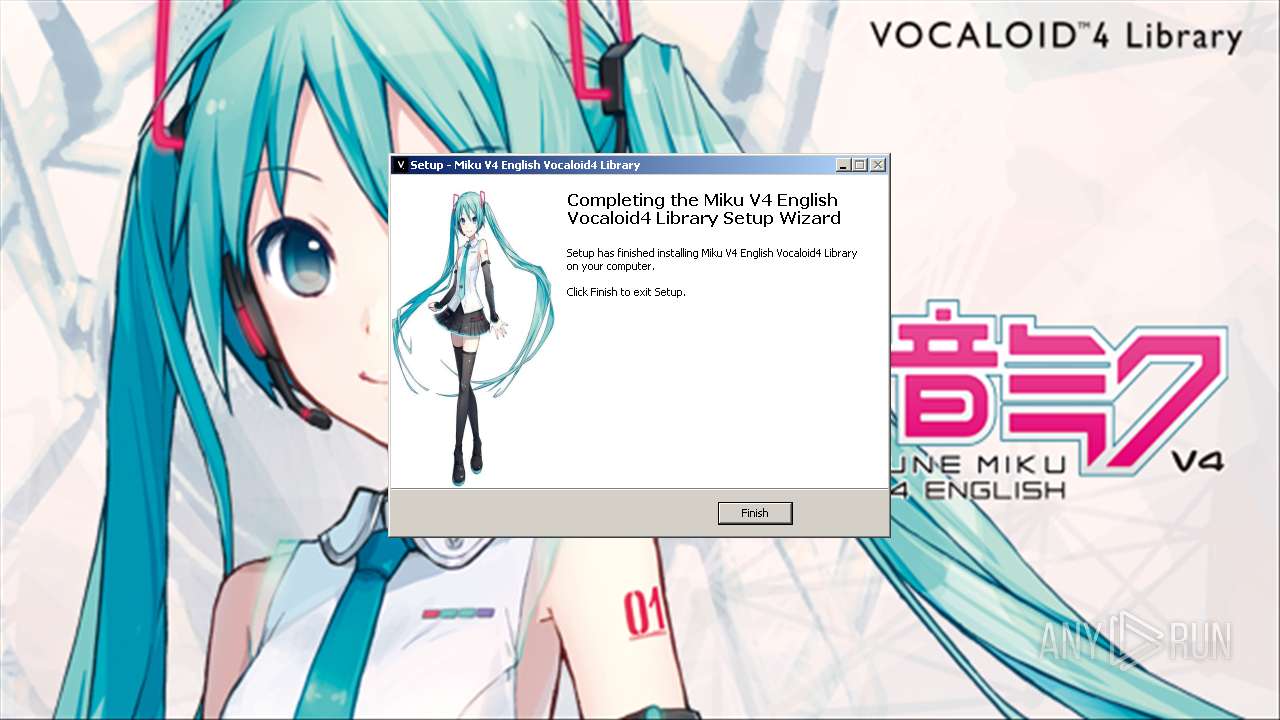
Creates a software uninstall entry
- MikuV4_eng.tmp (PID: 3988)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Inno Setup installer (77.7) |
|---|---|---|
| .exe | | | Win32 Executable Delphi generic (10) |
| .dll | | | Win32 Dynamic Link Library (generic) (4.6) |
| .exe | | | Win32 Executable (generic) (3.1) |
| .exe | | | Win16/32 Executable Delphi generic (1.4) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 1992:06:19 22:22:17+00:00 |
| ImageFileCharacteristics: | No relocs, Executable, No line numbers, No symbols, Bytes reversed lo, 32-bit, Bytes reversed hi |
| PEType: | PE32 |
| LinkerVersion: | 2.25 |
| CodeSize: | 41472 |
| InitializedDataSize: | 22016 |
| UninitializedDataSize: | - |
| EntryPoint: | 0xaa98 |
| OSVersion: | 1 |
| ImageVersion: | 6 |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 0.0.0.0 |
| ProductVersionNumber: | 0.0.0.0 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | Neutral |
| CharacterSet: | Unicode |
| Comments: | This installation was built with Inno Setup. |
| CompanyName: | |
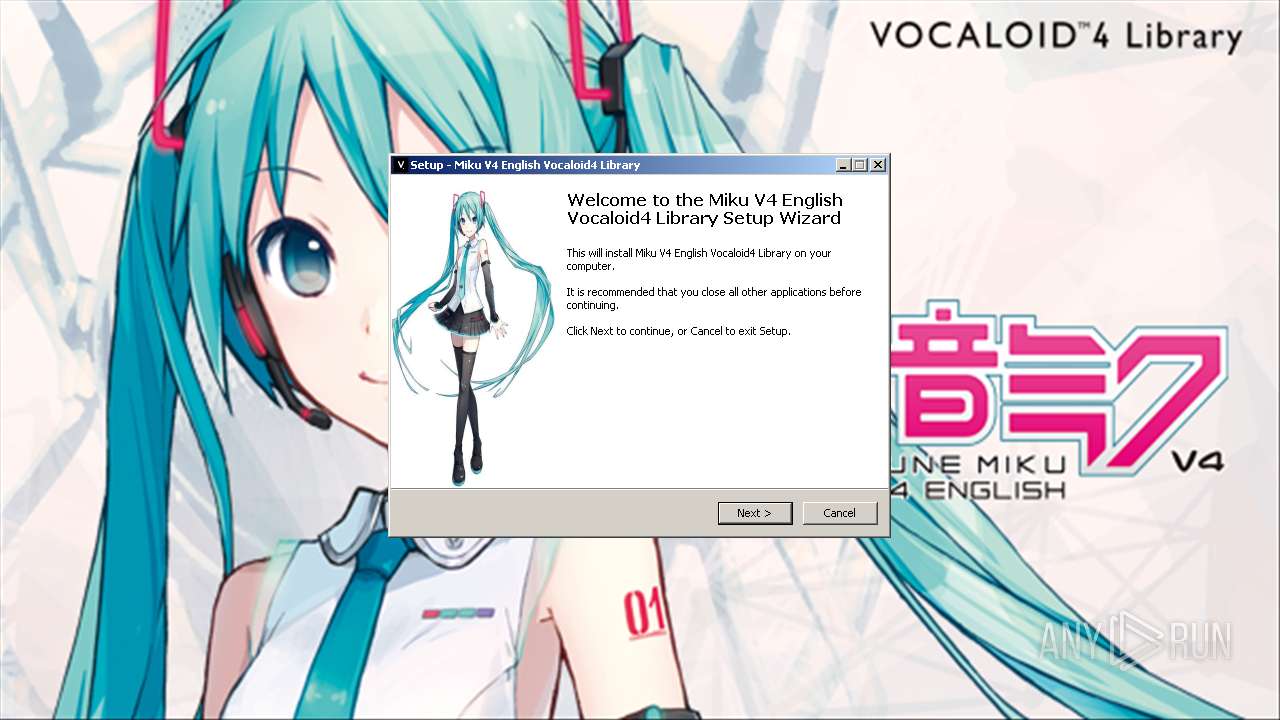
| FileDescription: | Miku V4 English Vocaloid4 Library Setup |
| FileVersion: | |
| LegalCopyright: | |
| ProductName: | Miku V4 English Vocaloid4 Library |
| ProductVersion: | Vocaloid4 Library |
Total processes
40
Monitored processes
4
Malicious processes
3
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 392 | "C:\Users\admin\AppData\Local\Temp\is-U3VB4.tmp\MikuV4_eng.tmp" /SL5="$22016A,3468732,64512,C:\Users\admin\AppData\Local\Temp\MikuV4_eng.exe" | C:\Users\admin\AppData\Local\Temp\is-U3VB4.tmp\MikuV4_eng.tmp | — | MikuV4_eng.exe | |||||||||||
User: admin Integrity Level: MEDIUM Description: Setup/Uninstall Exit code: 0 Version: 51.52.0.0 Modules
| |||||||||||||||
| 2032 | "C:\Users\admin\AppData\Local\Temp\MikuV4_eng.exe" | C:\Users\admin\AppData\Local\Temp\MikuV4_eng.exe | explorer.exe | ||||||||||||
User: admin Company: Integrity Level: MEDIUM Description: Miku V4 English Vocaloid4 Library Setup Exit code: 0 Version: Modules
| |||||||||||||||
| 2548 | "C:\Users\admin\AppData\Local\Temp\MikuV4_eng.exe" /SPAWNWND=$2901BC /NOTIFYWND=$22016A | C:\Users\admin\AppData\Local\Temp\MikuV4_eng.exe | MikuV4_eng.tmp | ||||||||||||
User: admin Company: Integrity Level: HIGH Description: Miku V4 English Vocaloid4 Library Setup Exit code: 0 Version: Modules
| |||||||||||||||
| 3988 | "C:\Users\admin\AppData\Local\Temp\is-NHO1H.tmp\MikuV4_eng.tmp" /SL5="$1B0140,3468732,64512,C:\Users\admin\AppData\Local\Temp\MikuV4_eng.exe" /SPAWNWND=$2901BC /NOTIFYWND=$22016A | C:\Users\admin\AppData\Local\Temp\is-NHO1H.tmp\MikuV4_eng.tmp | MikuV4_eng.exe | ||||||||||||
User: admin Integrity Level: HIGH Description: Setup/Uninstall Exit code: 0 Version: 51.52.0.0 Modules
| |||||||||||||||
Total events
2 868
Read events
2 833
Write events
31
Delete events
4
Modification events
| (PID) Process: | (3988) MikuV4_eng.tmp | Key: | HKEY_CURRENT_USER\Software\Microsoft\RestartManager\Session0000 |
| Operation: | write | Name: | Owner |
Value: 940F0000680D0B03D395DA01 | |||
| (PID) Process: | (3988) MikuV4_eng.tmp | Key: | HKEY_CURRENT_USER\Software\Microsoft\RestartManager\Session0000 |
| Operation: | write | Name: | SessionHash |
Value: C4A13A7966F8B5D0054160AFA1013E4393F6E81FE8FA52AFE7875B4047C441C9 | |||
| (PID) Process: | (3988) MikuV4_eng.tmp | Key: | HKEY_CURRENT_USER\Software\Microsoft\RestartManager\Session0000 |
| Operation: | write | Name: | Sequence |
Value: 1 | |||
| (PID) Process: | (3988) MikuV4_eng.tmp | Key: | HKEY_LOCAL_MACHINE\SYSTEM\ControlSet001\Control\MediaResources\DirectSound\Speaker Configuration |
| Operation: | write | Name: | Speaker Configuration |
Value: 4 | |||
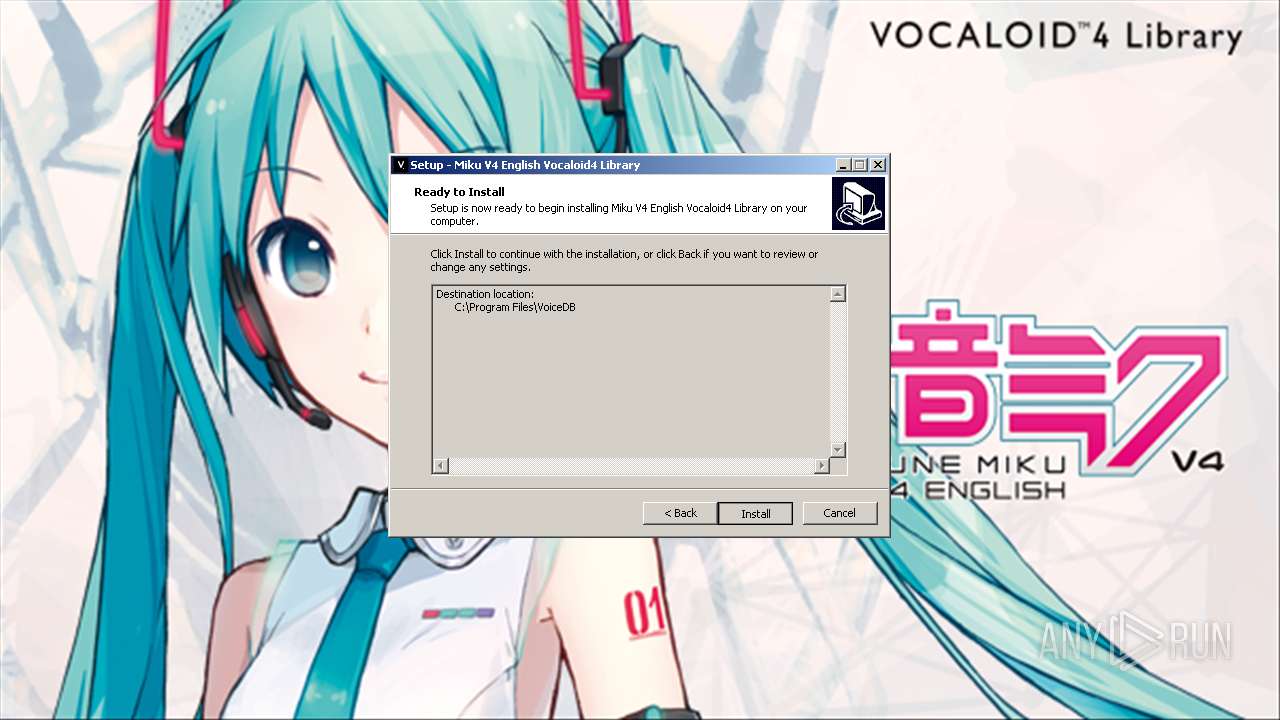
| (PID) Process: | (3988) MikuV4_eng.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\POCALOID4\DATABASE\BMLTD846MLYP2MEK |
| Operation: | write | Name: | PATH |
Value: C:\Program Files\VoiceDB\MikuV4_ENG | |||
| (PID) Process: | (3988) MikuV4_eng.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\POCALOID4\DATABASE\BMLTD846MLYP2MEK |
| Operation: | write | Name: | DRP |
Value: 0B0032 | |||
| (PID) Process: | (3988) MikuV4_eng.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\POCALOID4\DATABASE\BMLTD846MLYP2MEK |
| Operation: | write | Name: | INSTALLED |
Value: 1 | |||
| (PID) Process: | (3988) MikuV4_eng.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\POCALOID4\DATABASE\BMLTD846MLYP2MEK |
| Operation: | write | Name: | NAME |
Value: VOCALOID4 Library (MIKU_V4_English) | |||
| (PID) Process: | (3988) MikuV4_eng.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\POCALOID4\DATABASE\BMLTD846MLYP2MEK |
| Operation: | write | Name: | TIME |
Value: BHMN74F9ED86FKAB | |||
| (PID) Process: | (3988) MikuV4_eng.tmp | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\POCALOID4\DATABASE\BMLTD846MLYP2MEK\KEYS |
| Operation: | write | Name: | default |
Value: c845cfd4b8a90614d5b0f09eba7144d1 | |||
Executable files
8
Suspicious files
2
Text files
1
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2032 | MikuV4_eng.exe | C:\Users\admin\AppData\Local\Temp\is-U3VB4.tmp\MikuV4_eng.tmp | executable | |
MD5:FBEBDCF5181CE8F757C0B86F39EDFAFF | SHA256:22A18BAD4B76B35566FB76BD37E6B3785498C3363673443D1D954F88F66F7E19 | |||
| 3988 | MikuV4_eng.tmp | C:\Users\admin\AppData\Local\Temp\is-K6G8N.tmp\bass.dll | executable | |
MD5:26295A0BAF87955F2E37735AF135CA45 | SHA256:0BD42C13DD0A5C881E80F161F7548B093C4FD99A747C13568AF983E2C76CD71A | |||
| 3988 | MikuV4_eng.tmp | C:\Program Files\VoiceDB\is-BC8K2.tmp | executable | |
MD5:01014B4191245E3B82F1AE5A86718526 | SHA256:F2FBAB850FACCFF16DADD5FE234B2516198F7ECB64C57DE1434523CB411880D9 | |||
| 3988 | MikuV4_eng.tmp | C:\Users\admin\AppData\Local\Temp\is-K6G8N.tmp\innocallback.dll | executable | |
MD5:1C55AE5EF9980E3B1028447DA6105C75 | SHA256:6AFA2D104BE6EFE3D9A2AB96DBB75DB31565DAD64DD0B791E402ECC25529809F | |||
| 3988 | MikuV4_eng.tmp | C:\Users\admin\AppData\Local\Temp\is-K6G8N.tmp\mikuv4_eng.bmp | image | |
MD5:5438220DE58C188DC09D70CC20C57370 | SHA256:B201FFDD451406A42B15F294C706841DD221EA6B9D0969A49EF668FA317F201B | |||
| 3988 | MikuV4_eng.tmp | C:\Program Files\VoiceDB\unins000.exe | executable | |
MD5:01014B4191245E3B82F1AE5A86718526 | SHA256:F2FBAB850FACCFF16DADD5FE234B2516198F7ECB64C57DE1434523CB411880D9 | |||
| 3988 | MikuV4_eng.tmp | C:\Program Files\VoiceDB\unins000.dat | dat | |
MD5:EA00CC590EDFC565FCA555A4114565CD | SHA256:62AAE1C5C92CC452DB55BF87908411FD9AB4DCA1973BA41AC0D60CC6184FE026 | |||
| 3988 | MikuV4_eng.tmp | C:\Users\admin\AppData\Local\Temp\is-K6G8N.tmp\isgsg.dll | executable | |
MD5:09974EAFF6DEFADDE38B1328754DBE09 | SHA256:9EEEF28D82FC4DB7D1269DFBC0EA282768CE5E2E4E4BDC867D80D6847468DCA7 | |||
| 2548 | MikuV4_eng.exe | C:\Users\admin\AppData\Local\Temp\is-NHO1H.tmp\MikuV4_eng.tmp | executable | |
MD5:FBEBDCF5181CE8F757C0B86F39EDFAFF | SHA256:22A18BAD4B76B35566FB76BD37E6B3785498C3363673443D1D954F88F66F7E19 | |||
| 3988 | MikuV4_eng.tmp | C:\Users\admin\AppData\Local\Temp\is-K6G8N.tmp\unarc.dll | executable | |
MD5:56A2BCECBD3CDDD6F4A35361BF4920D6 | SHA256:5FCFAC18758A12E0E717A5189F379922A32B5AC12F26491E638D70B54AE1DCAB | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
4
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
— | — | 224.0.0.252:5355 | — | — | — | unknown |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
1080 | svchost.exe | 224.0.0.252:5355 | — | — | — | unknown |