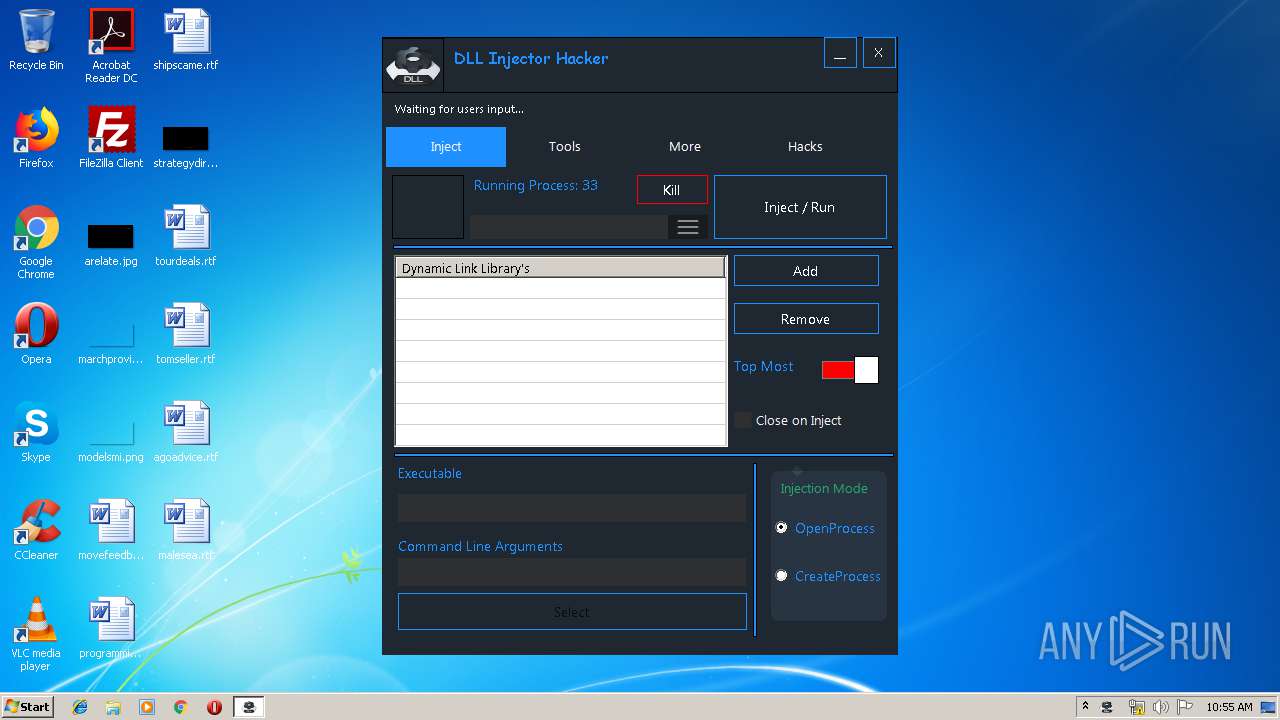
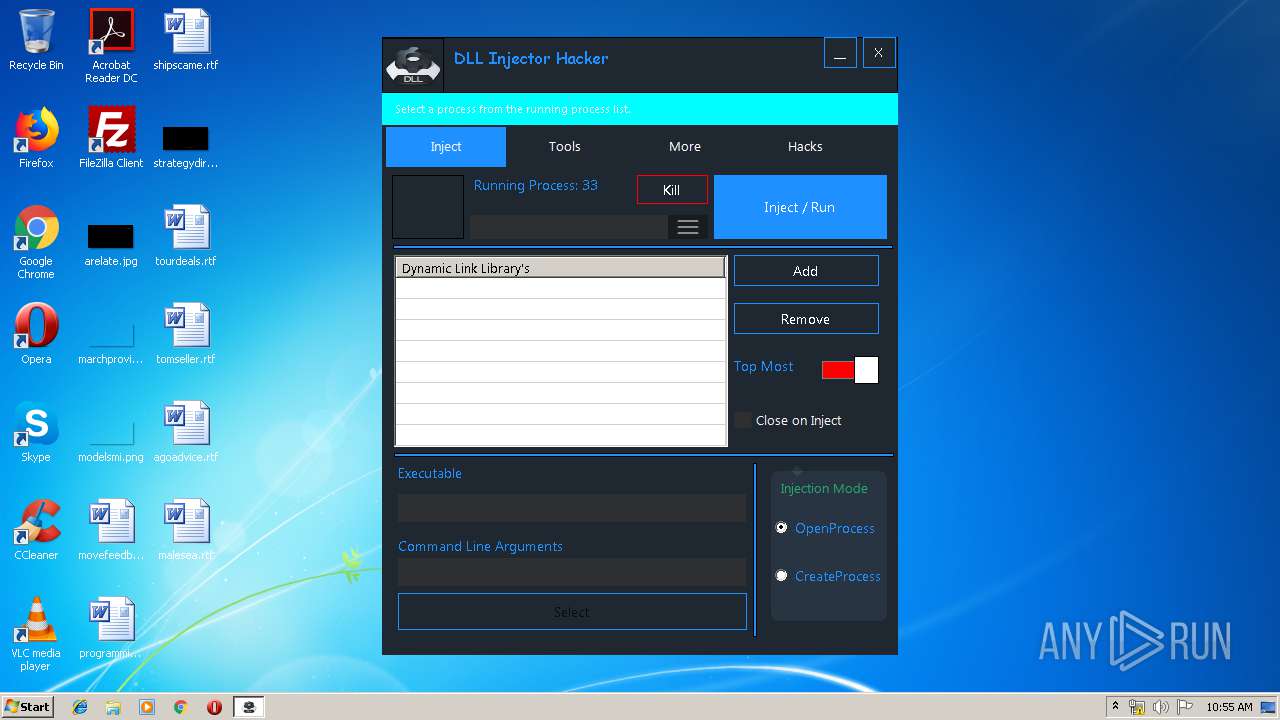
| File name: | dll-injector-hacker_0.6.6_Fix.exe |
| Full analysis: | https://app.any.run/tasks/6b0458df-afc2-462c-a95c-39d0a9ce2492 |
| Verdict: | Malicious activity |
| Analysis date: | May 27, 2019, 09:54:39 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386 Mono/.Net assembly, for MS Windows |
| MD5: | 04B807184E6D7F01268279CB7220E35F |
| SHA1: | 0DC2416F49B0B6FDF2ADF16C2F0C5BCB1C975286 |
| SHA256: | 64A884F92C37E0CCCF062CE9F39C154ED5A6A9978A3F573C116AE1C908263B92 |
| SSDEEP: | 24576:DY6DFIipHT1L6LRB+CNpJdFMzQxVsE79yU0kbfUluzQNYAj4ulIP:zhT1ixNpDFs2y/uU8K4ulI |
MALICIOUS
Changes settings of System certificates
- dll-injector-hacker_0.6.6_Fix.exe (PID: 2536)
SUSPICIOUS
Creates files in the user directory
- dll-injector-hacker_0.6.6_Fix.exe (PID: 2536)
Changes IE settings (feature browser emulation)
- dll-injector-hacker_0.6.6_Fix.exe (PID: 2536)
Reads Internet Cache Settings
- dll-injector-hacker_0.6.6_Fix.exe (PID: 2536)
Adds / modifies Windows certificates
- dll-injector-hacker_0.6.6_Fix.exe (PID: 2536)
Reads internet explorer settings
- dll-injector-hacker_0.6.6_Fix.exe (PID: 2536)
INFO
Reads settings of System Certificates
- dll-injector-hacker_0.6.6_Fix.exe (PID: 2536)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable MS Visual C++ (generic) (41) |
|---|---|---|
| .exe | | | Win64 Executable (generic) (36.3) |
| .dll | | | Win32 Dynamic Link Library (generic) (8.6) |
| .exe | | | Win32 Executable (generic) (5.9) |
| .exe | | | Win16/32 Executable Delphi generic (2.7) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2019:04:09 18:31:05+02:00 |
| PEType: | PE32 |
| LinkerVersion: | 11 |
| CodeSize: | 229376 |
| InitializedDataSize: | 1441280 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x19e00a |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
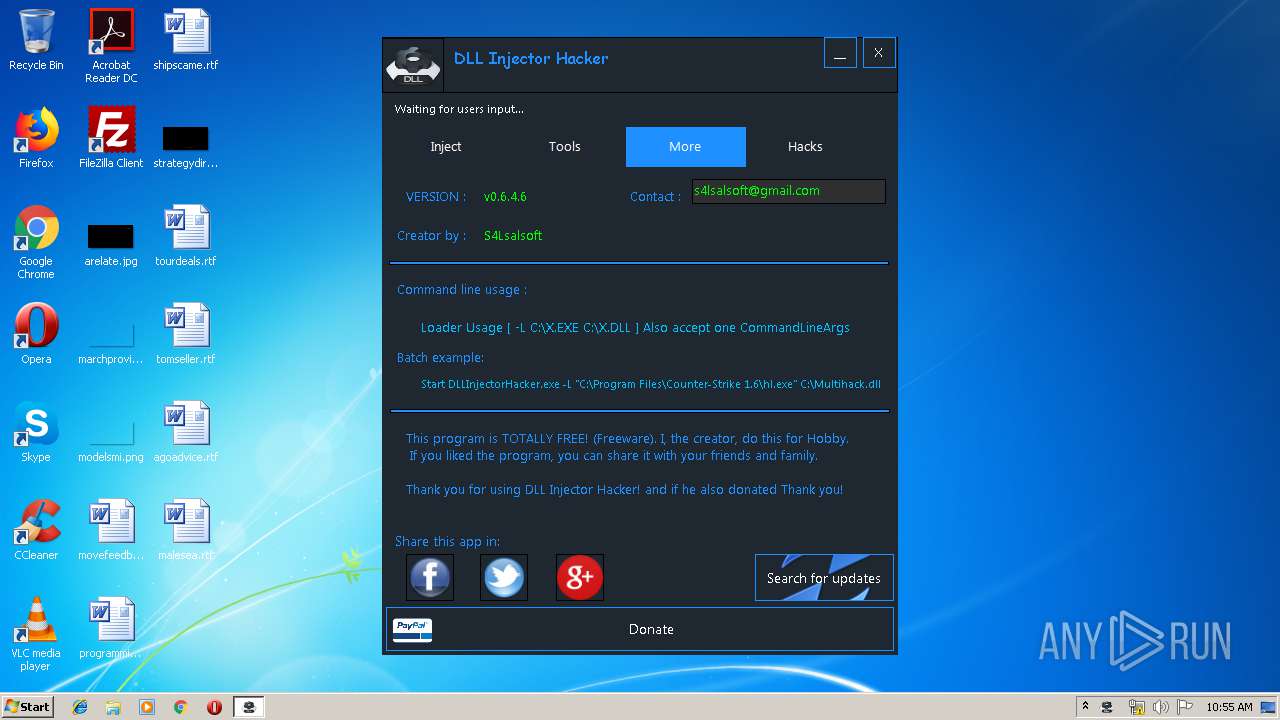
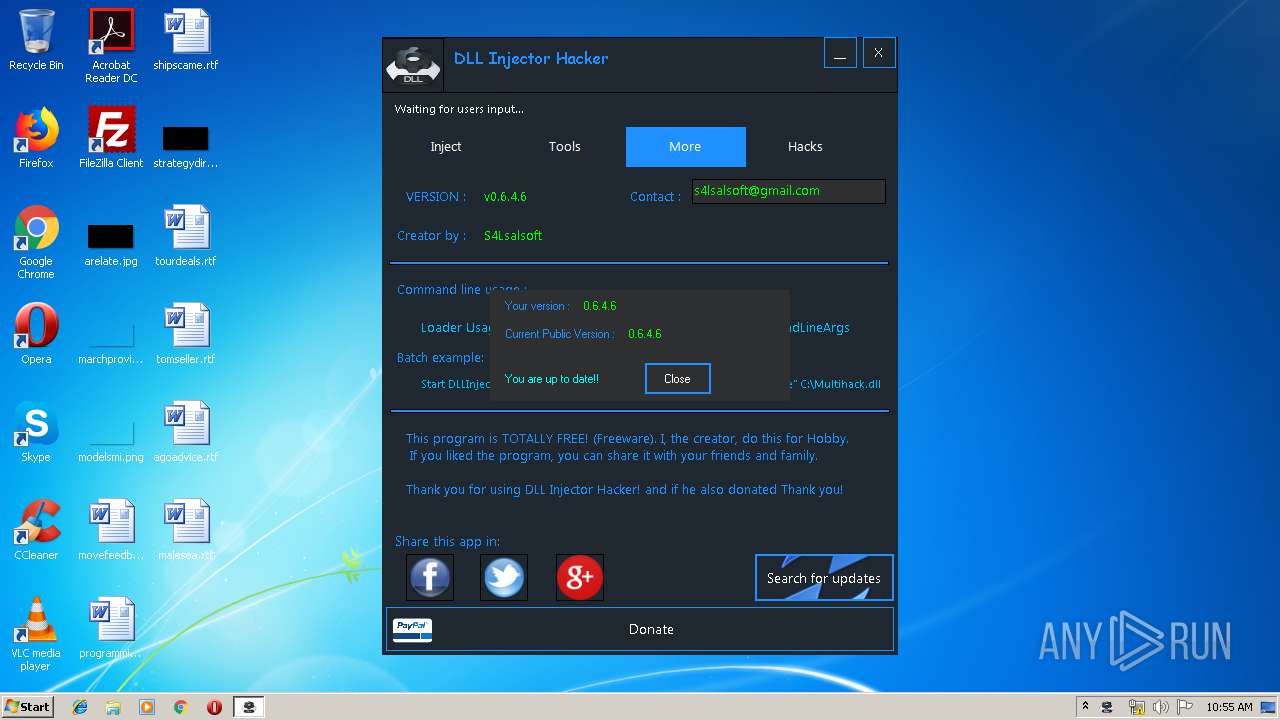
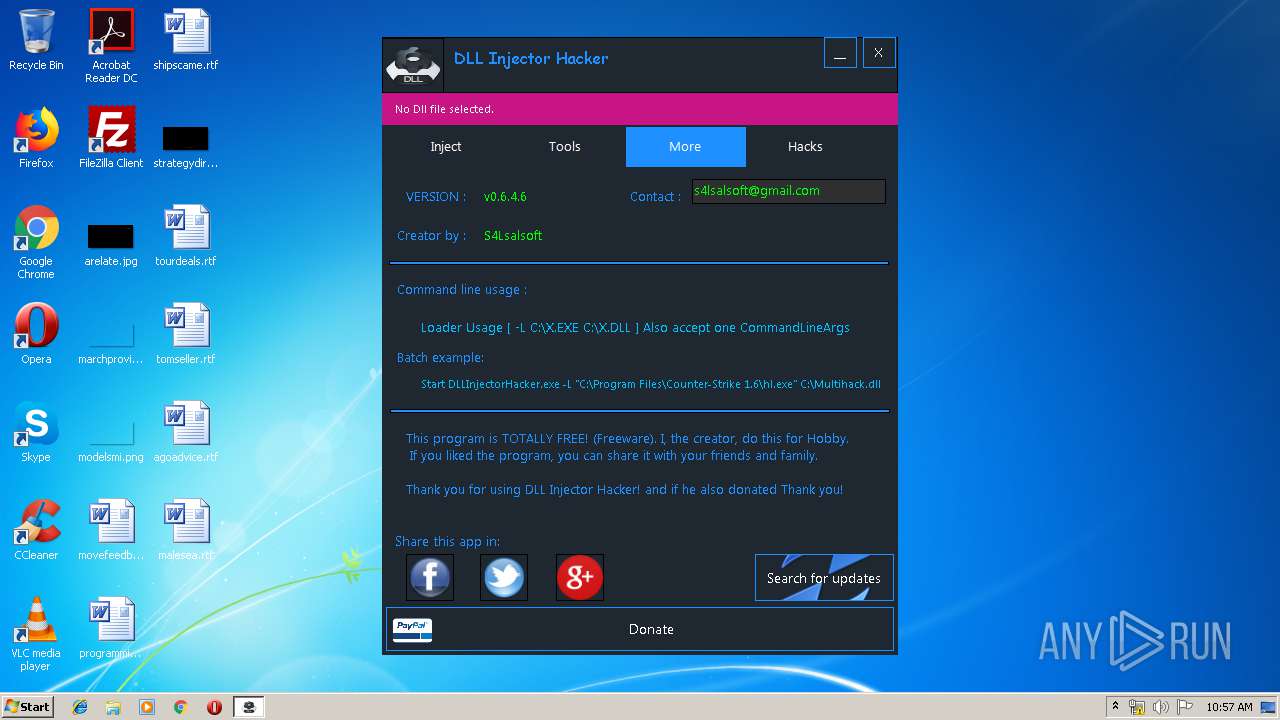
| FileVersionNumber: | 0.6.4.6 |
| ProductVersionNumber: | 0.6.4.6 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | Neutral |
| CharacterSet: | Unicode |
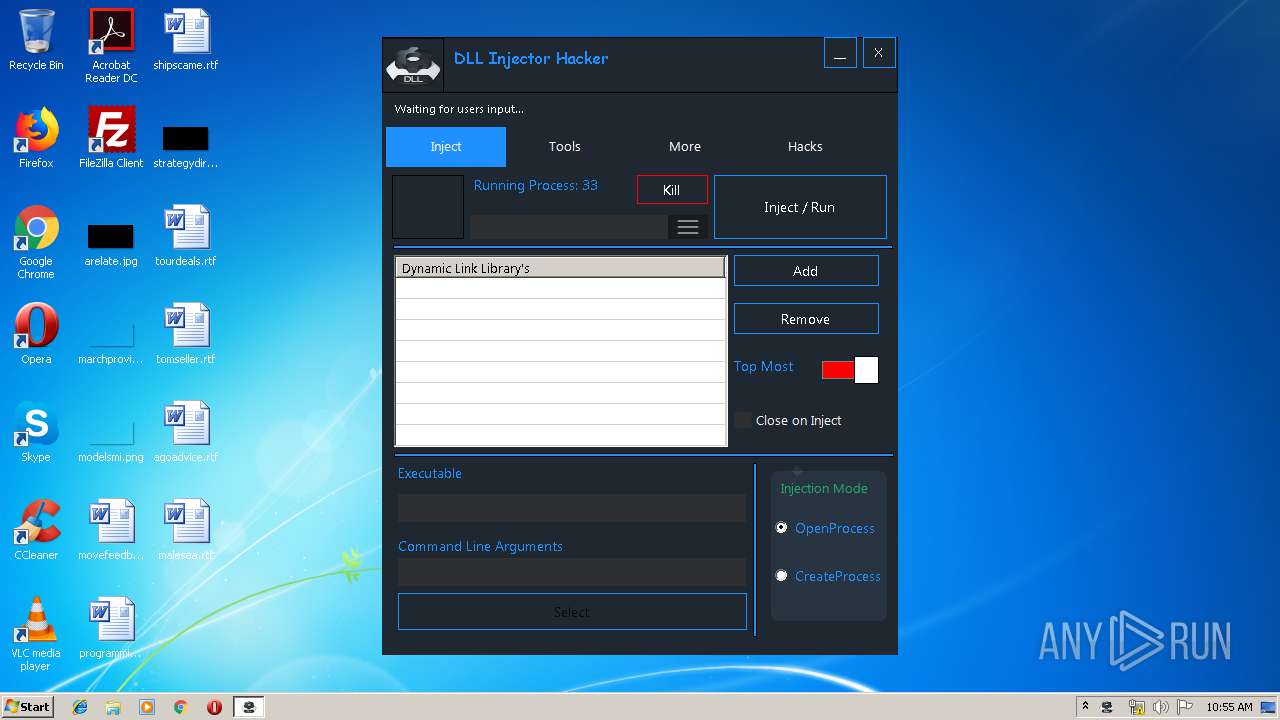
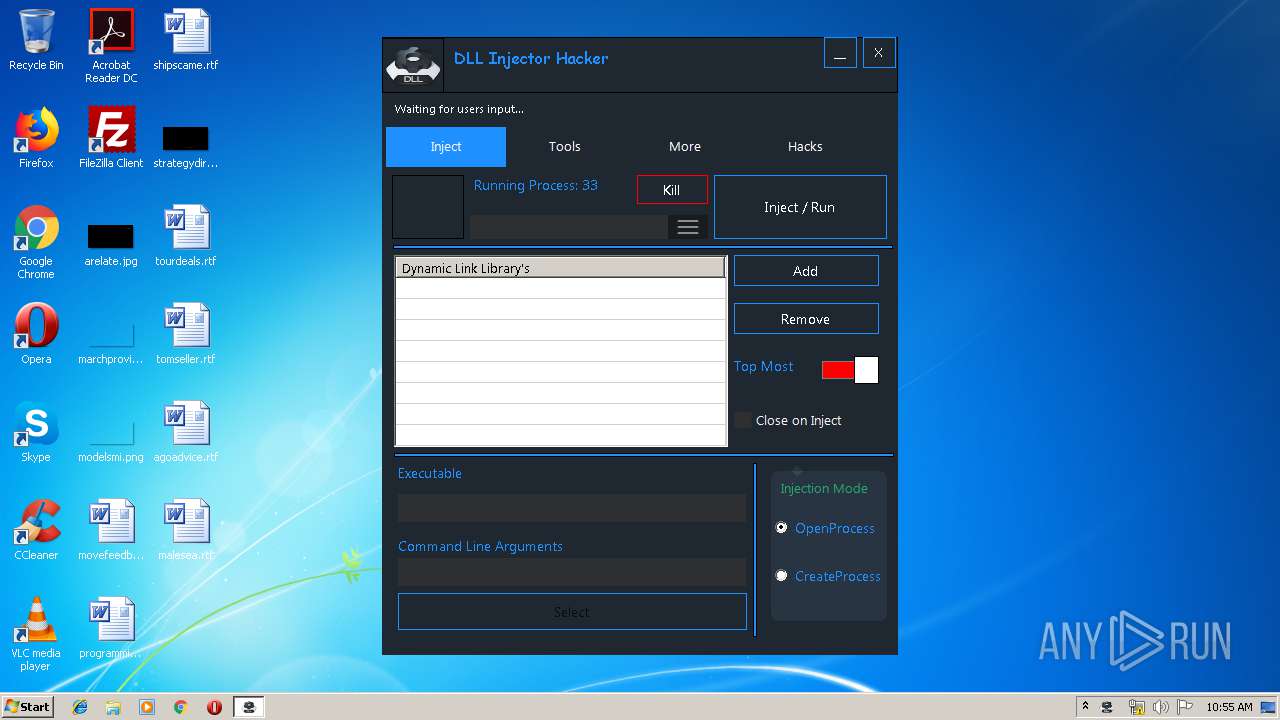
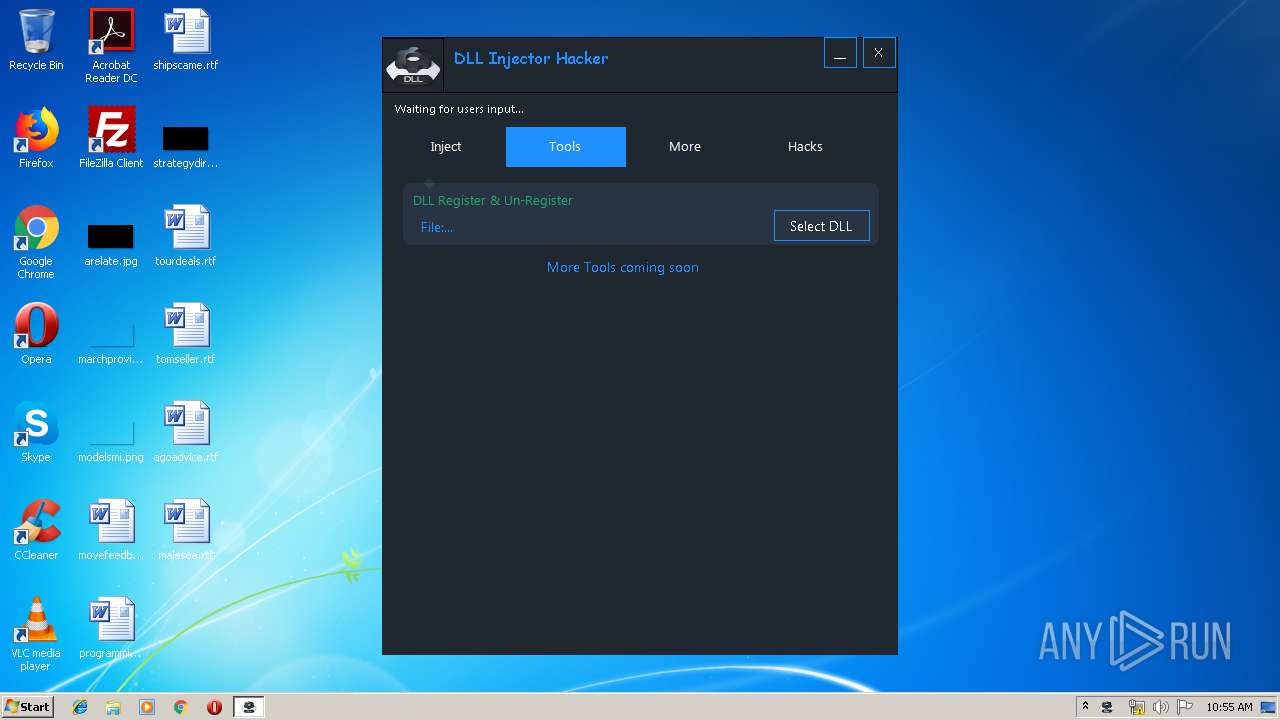
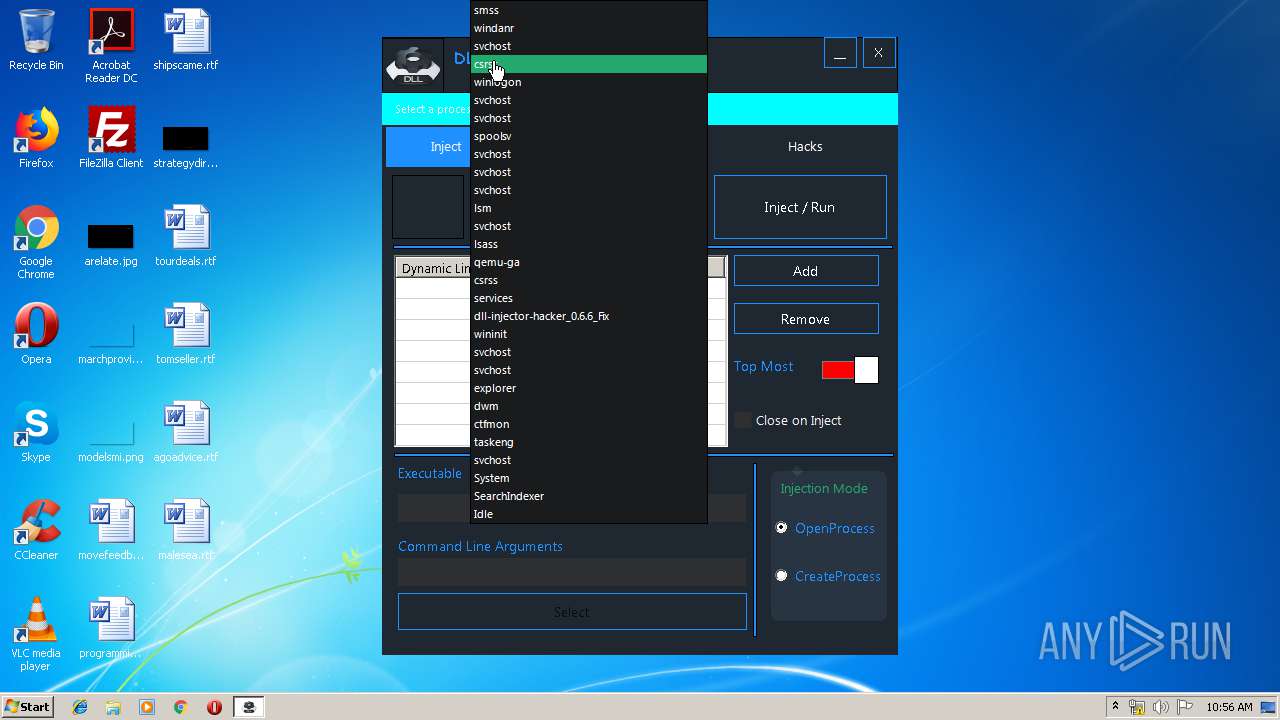
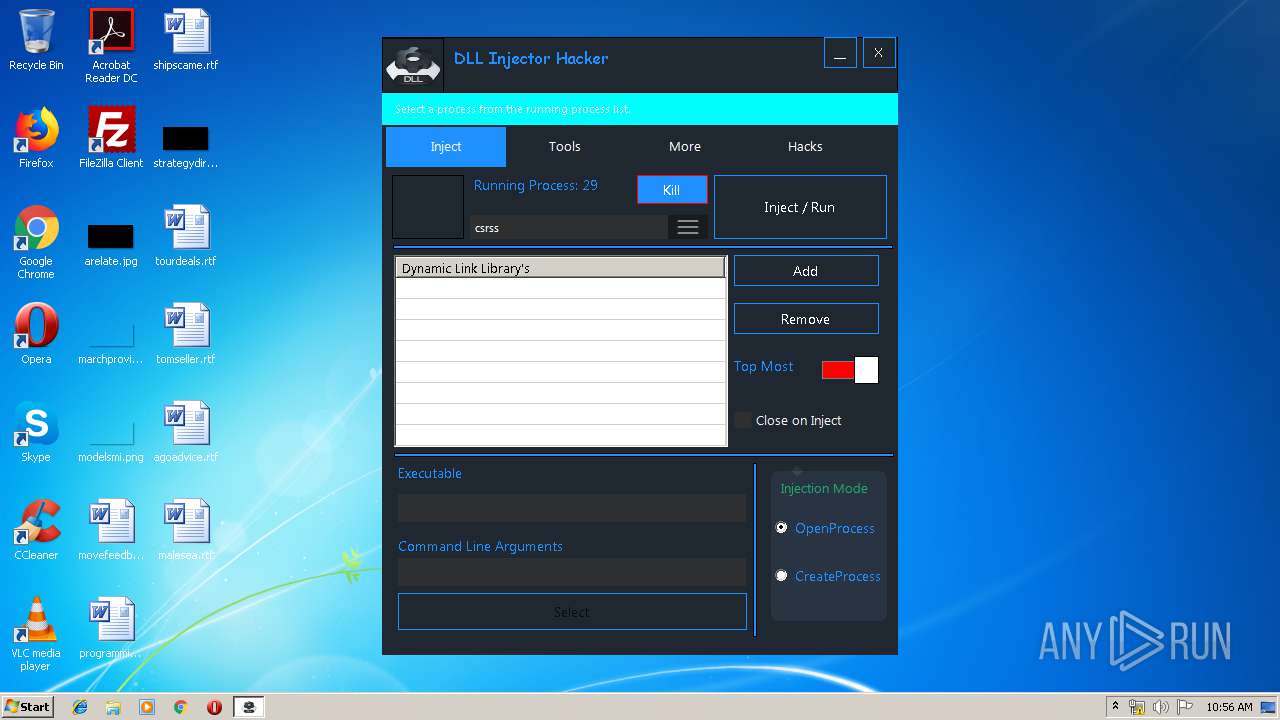
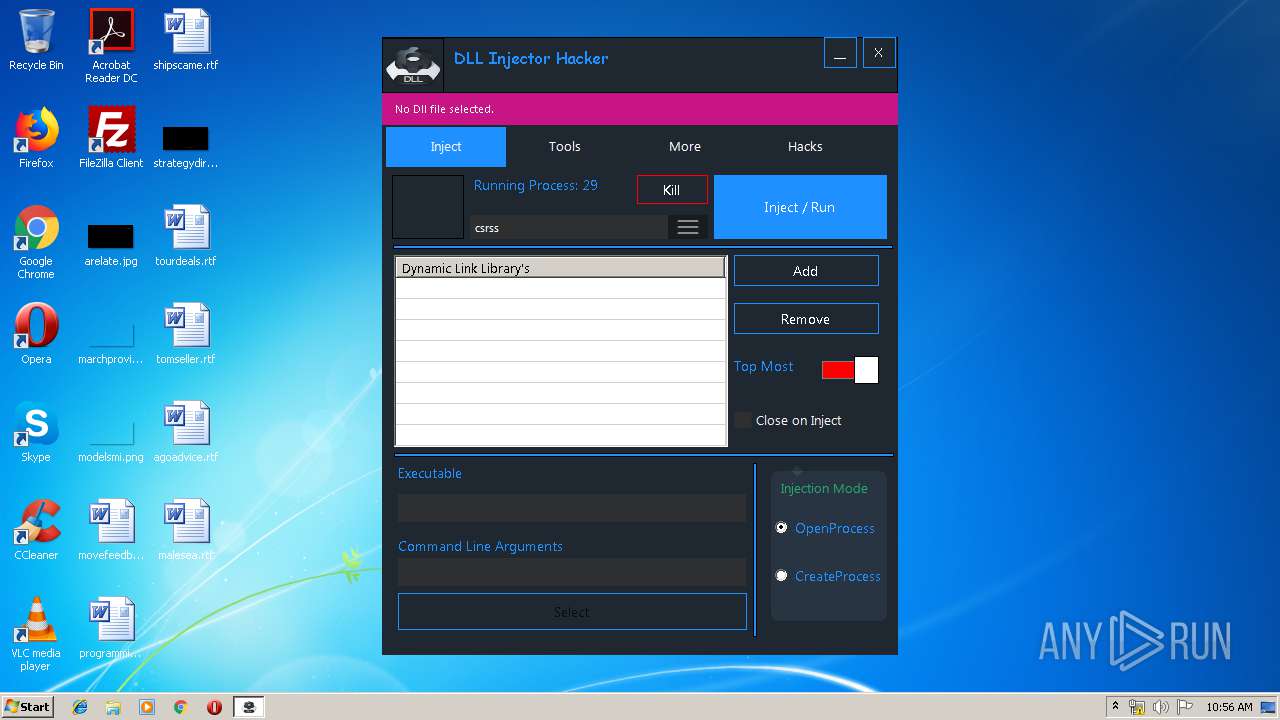
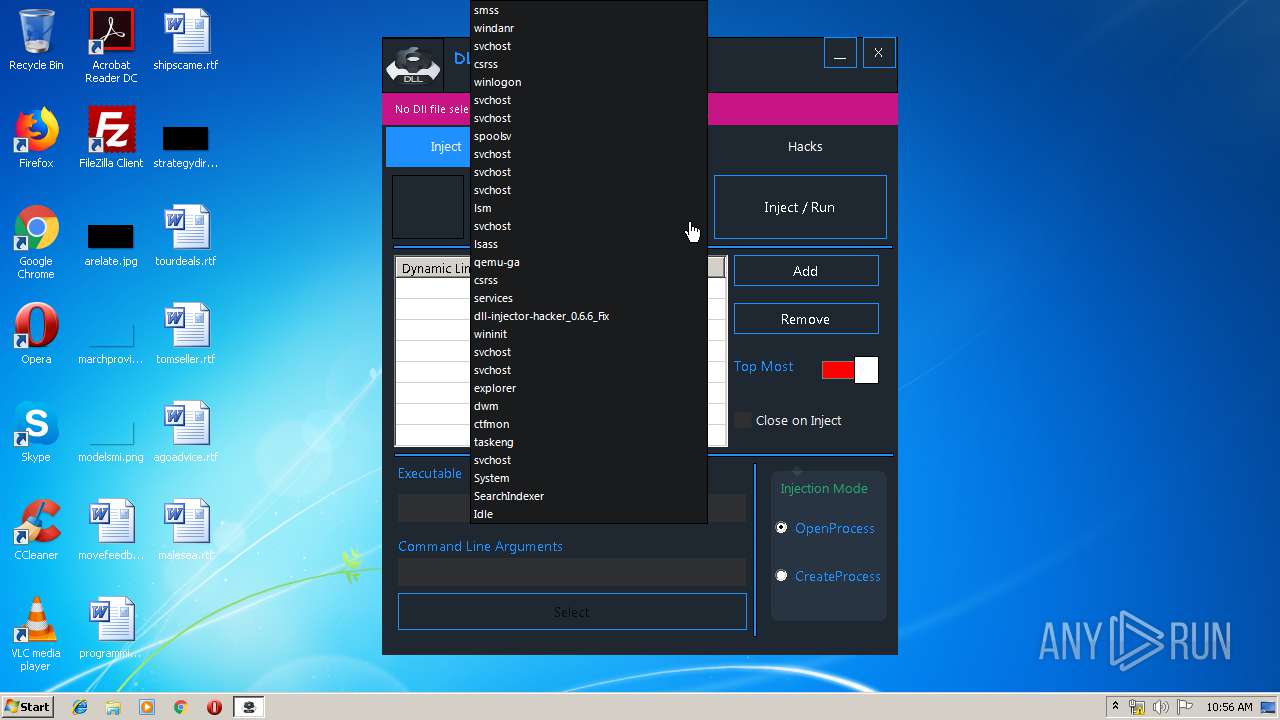
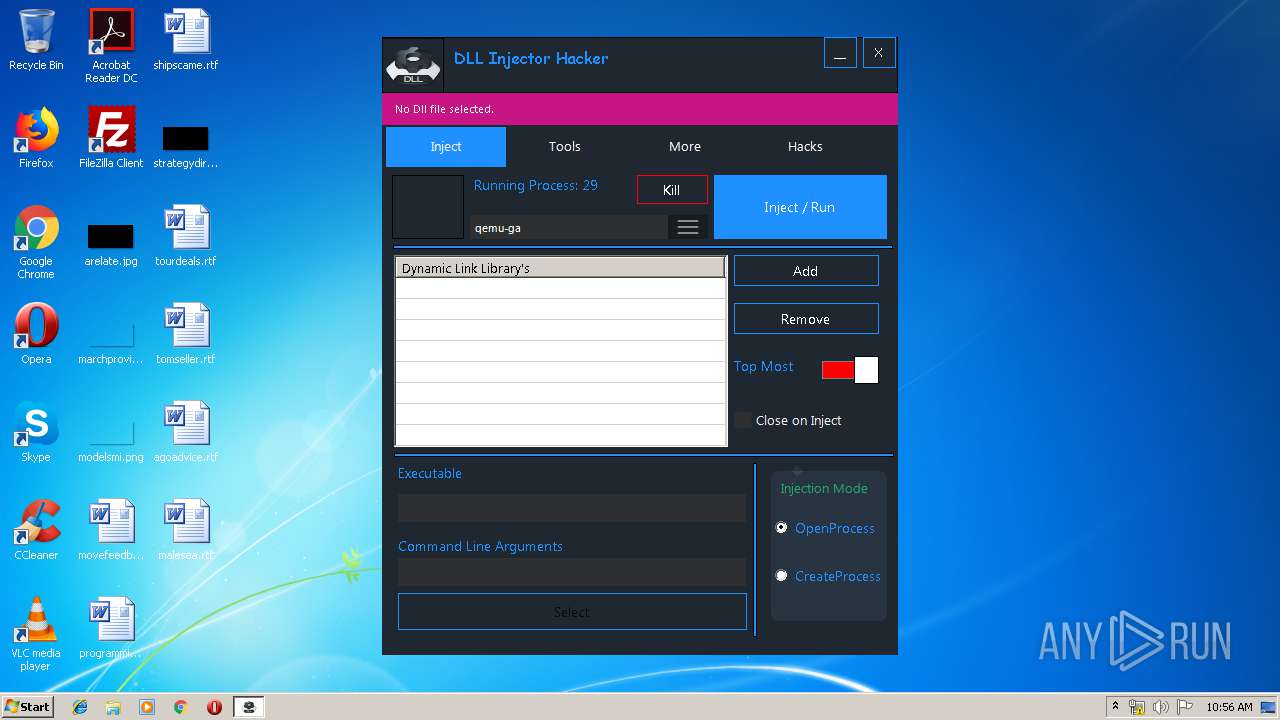
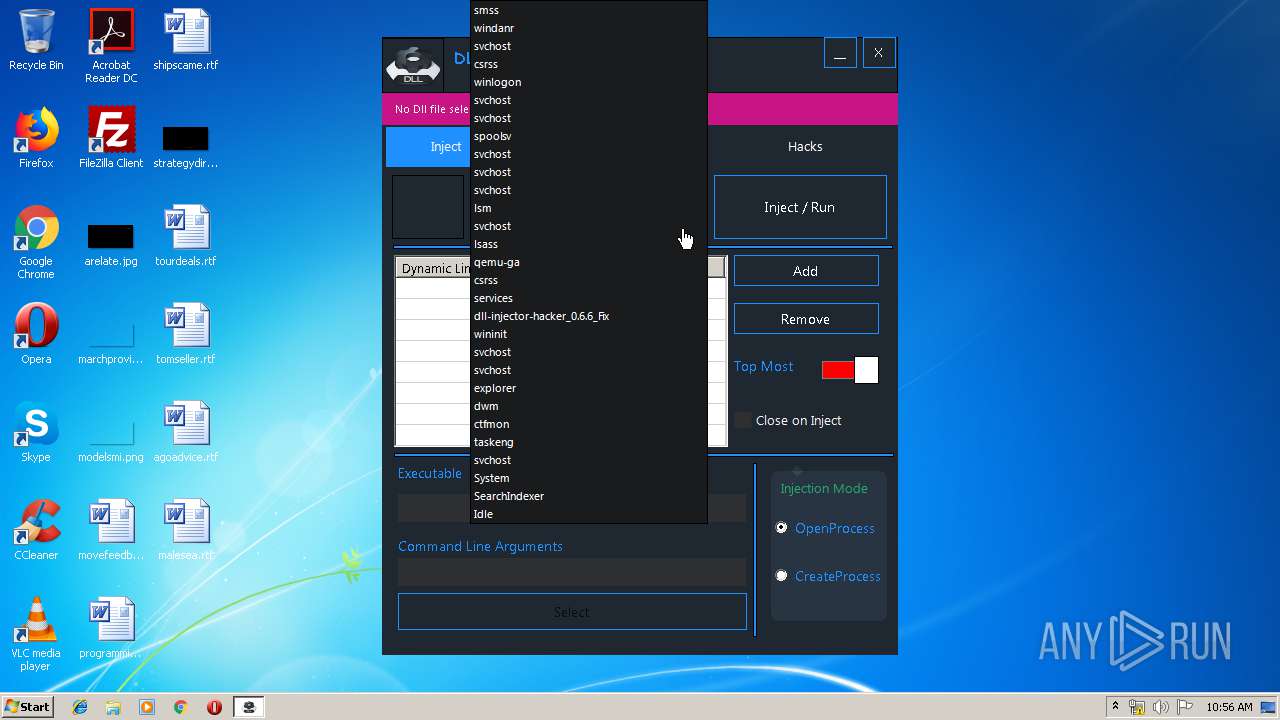
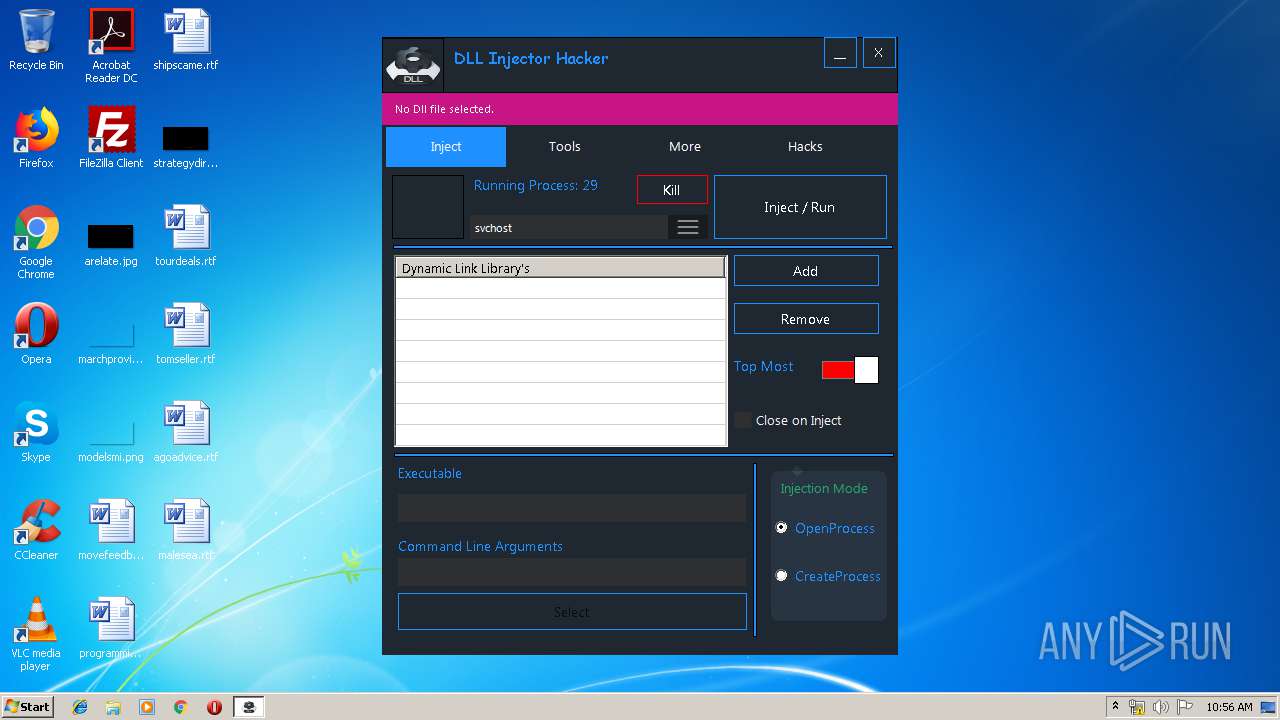
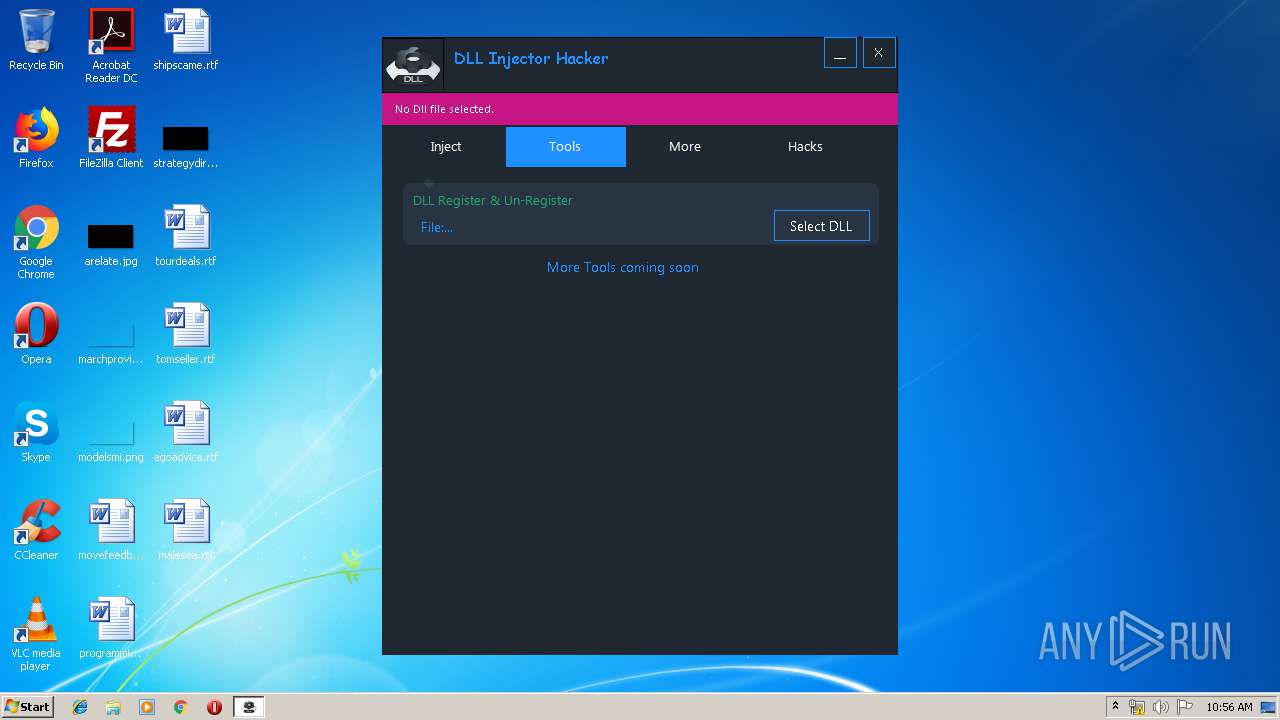
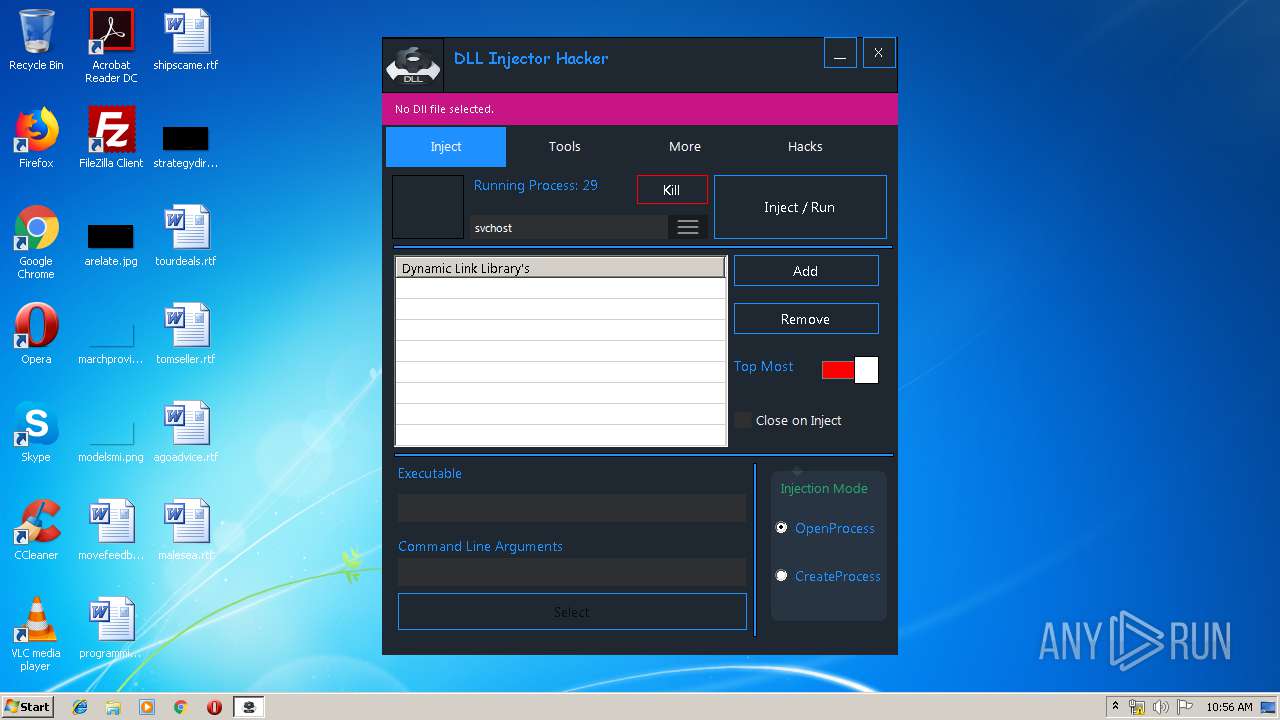
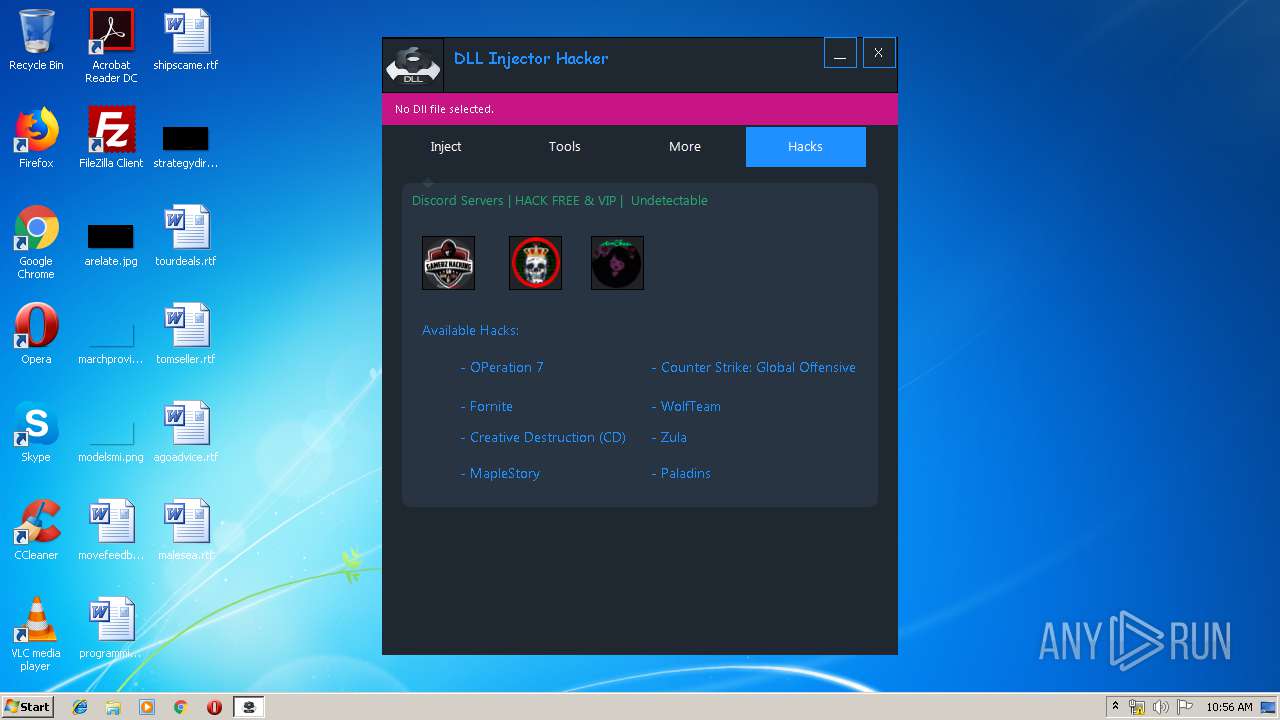
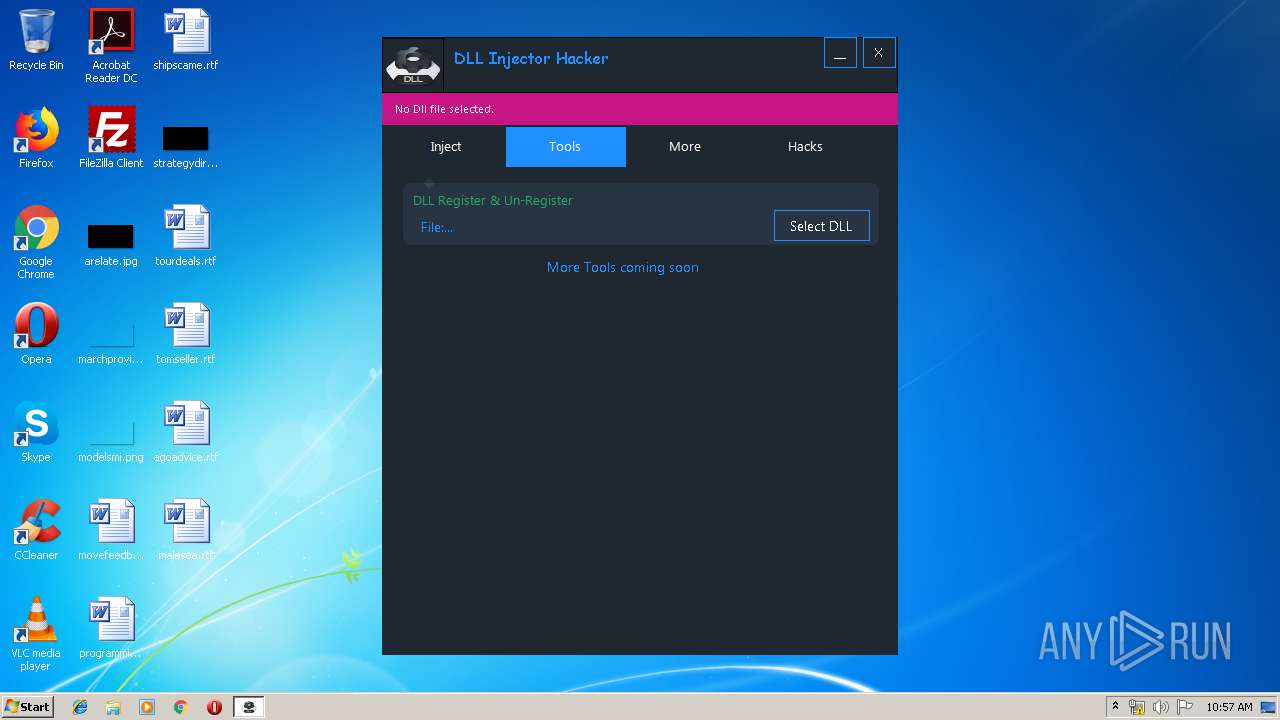
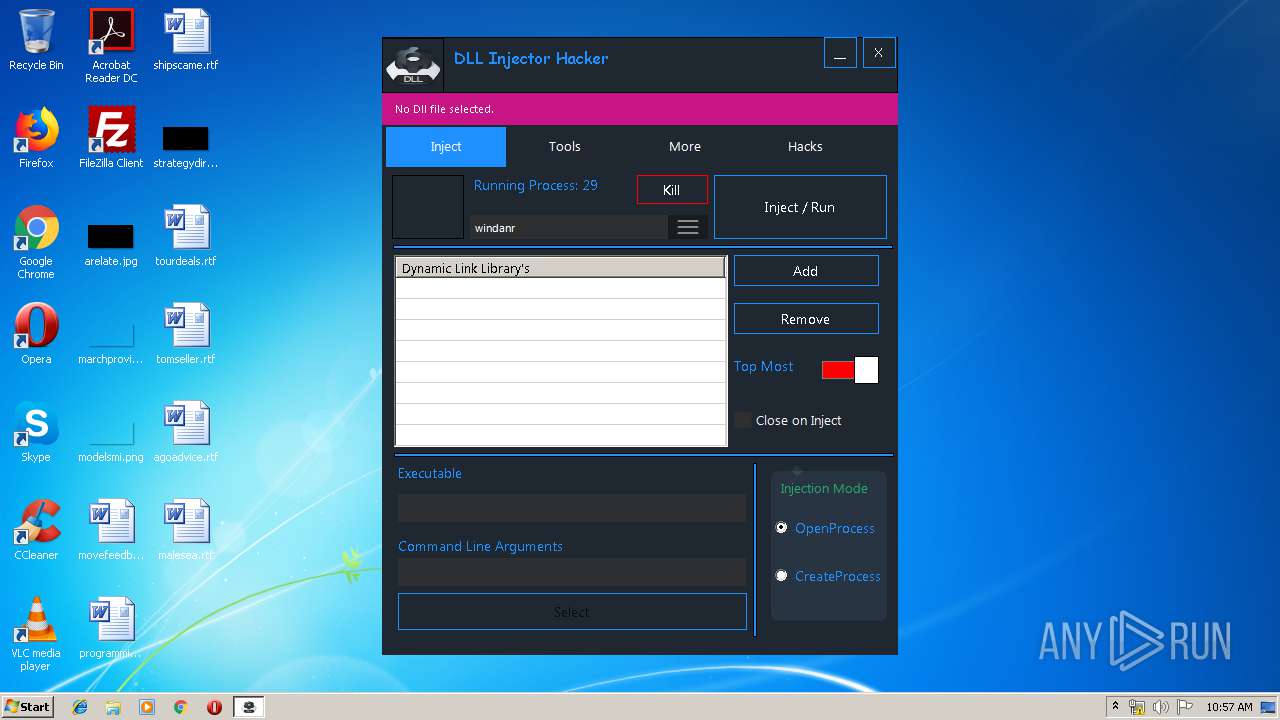
| Comments: | Inject your DLLs into games, etc. |
| CompanyName: | none |
| FileDescription: | DLL Injector Hacker |
| FileVersion: | 0.6.4.6 |
| InternalName: | DLL Injector Hacker.exe |
| LegalCopyright: | Copyright © 2018 |
| LegalTrademarks: | DLL Injector Hacker |
| OriginalFileName: | DLL Injector Hacker.exe |
| ProductName: | DLL Injector Hacker |
| ProductVersion: | 0.6.4.6 |
| AssemblyVersion: | 0.6.4.6 |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 09-Apr-2019 16:31:05 |
| Comments: | Inject your DLLs into games, etc. |
| CompanyName: | none |
| FileDescription: | DLL Injector Hacker |
| FileVersion: | 0.6.4.6 |
| InternalName: | DLL Injector Hacker.exe |
| LegalCopyright: | Copyright © 2018 |
| LegalTrademarks: | DLL Injector Hacker |
| OriginalFilename: | DLL Injector Hacker.exe |
| ProductName: | DLL Injector Hacker |
| ProductVersion: | 0.6.4.6 |
| Assembly Version: | 0.6.4.6 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000080 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 5 |
| Time date stamp: | 09-Apr-2019 16:31:05 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
\x0f>'e)AK\x0c\x10\xa5\x13 | 0x00002000 | 0x0013A510 | 0x0013A600 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 7.99985 |
.text | 0x0013E000 | 0x00037C68 | 0x00037E00 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.12342 |
.rsrc | 0x00176000 | 0x00025560 | 0x00025600 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 5.76659 |
.reloc | 0x0019C000 | 0x0000000C | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_DISCARDABLE, IMAGE_SCN_MEM_READ | 0.0980042 |
0x0019E000 | 0x00000010 | 0x00000200 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 0.142636 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 4.9039 | 2461 | UNKNOWN | UNKNOWN | RT_MANIFEST |
2 | 7.98004 | 46751 | UNKNOWN | UNKNOWN | RT_ICON |
3 | 4.01669 | 67624 | UNKNOWN | UNKNOWN | RT_ICON |
4 | 4.11498 | 16936 | UNKNOWN | UNKNOWN | RT_ICON |
5 | 4.38792 | 9640 | UNKNOWN | UNKNOWN | RT_ICON |
6 | 4.35826 | 4264 | UNKNOWN | UNKNOWN | RT_ICON |
7 | 4.58366 | 2440 | UNKNOWN | UNKNOWN | RT_ICON |
8 | 4.59271 | 1128 | UNKNOWN | UNKNOWN | RT_ICON |
32512 | 2.94489 | 104 | UNKNOWN | UNKNOWN | RT_GROUP_ICON |
Imports
mscoree.dll |
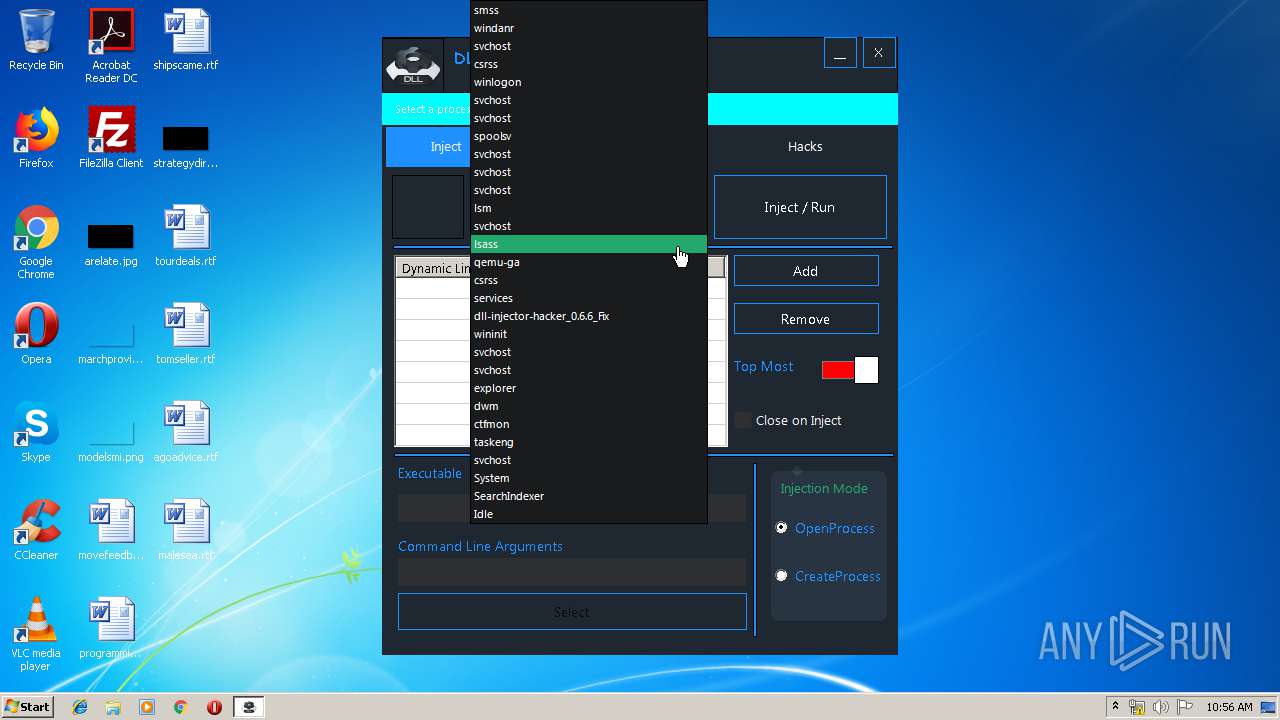
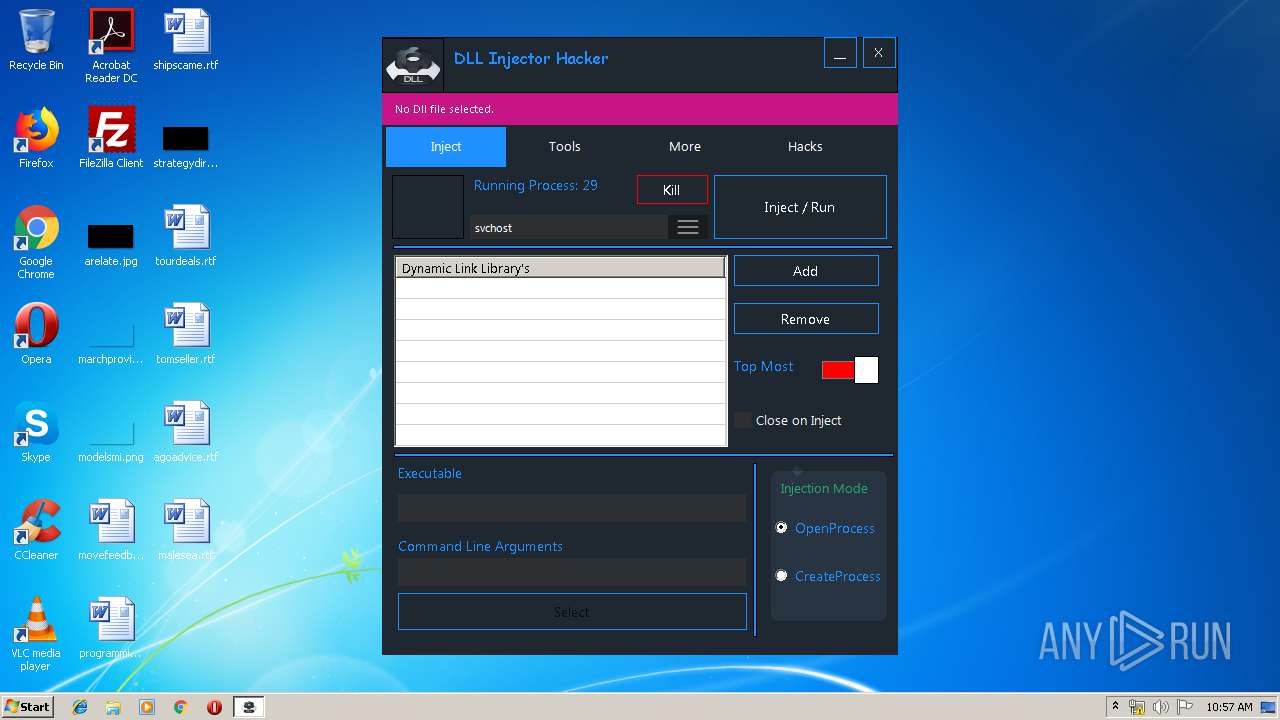
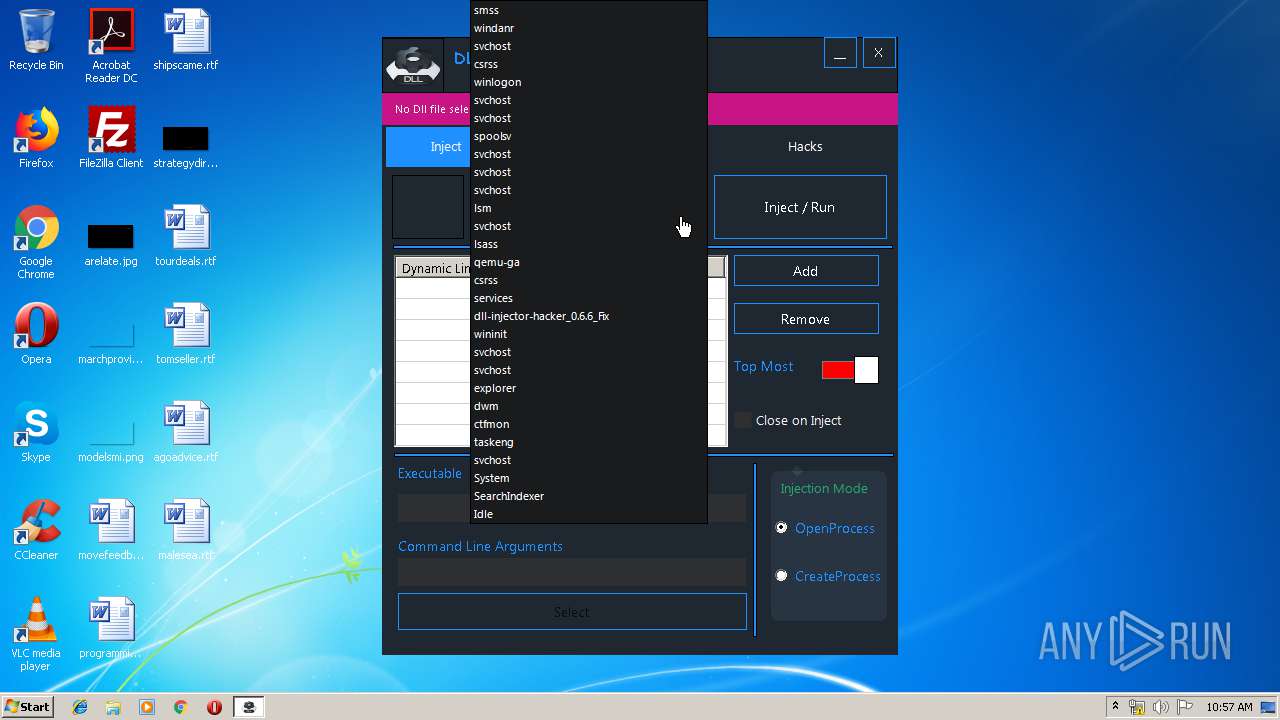
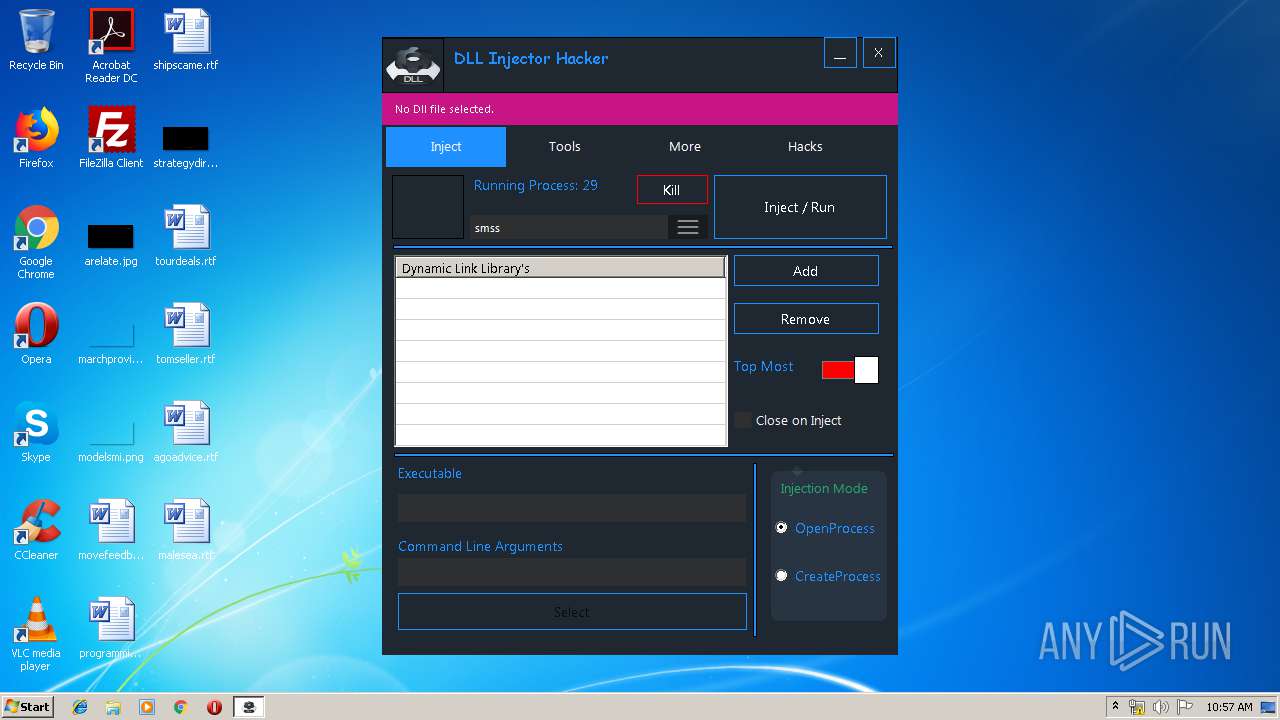
Total processes
36
Monitored processes
2
Malicious processes
1
Suspicious processes
0
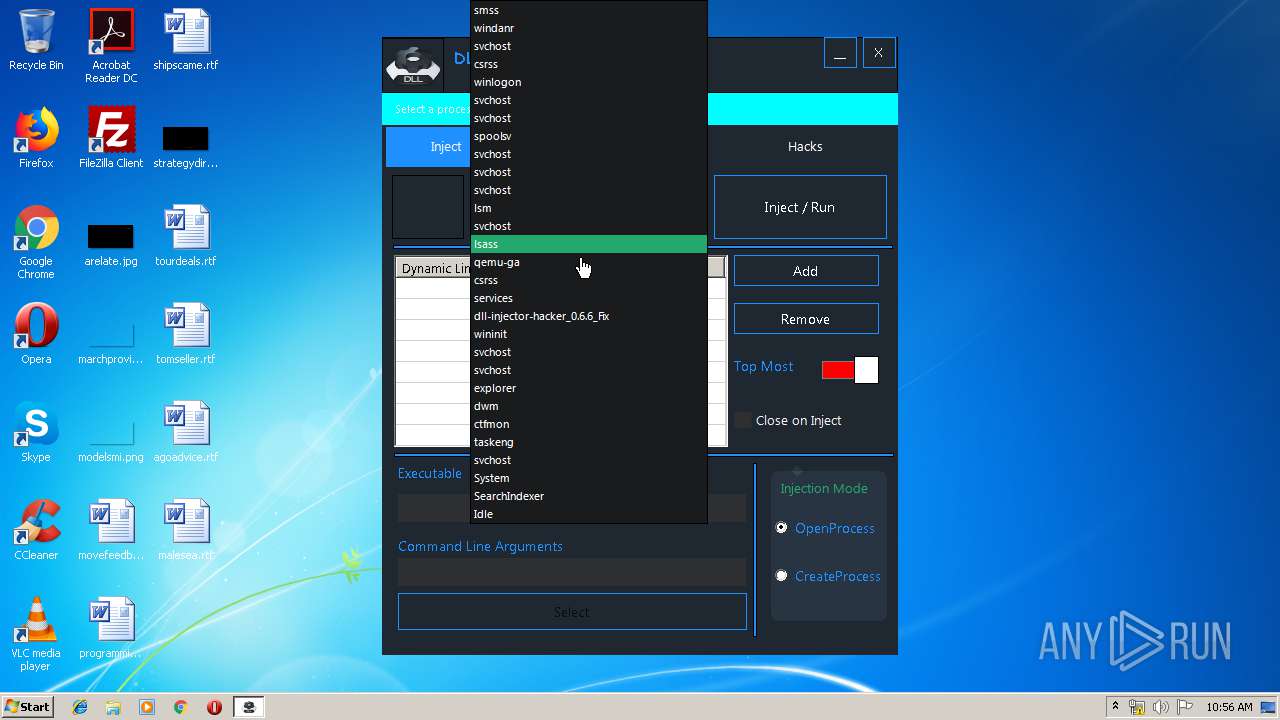
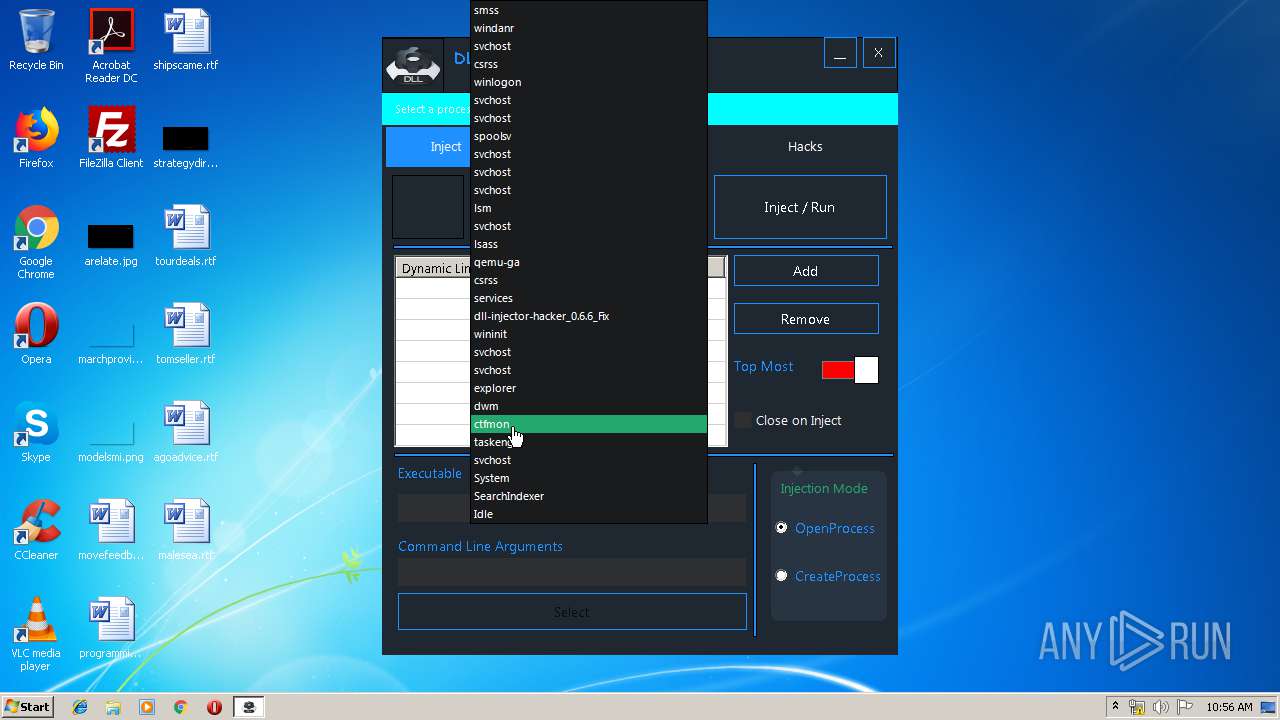
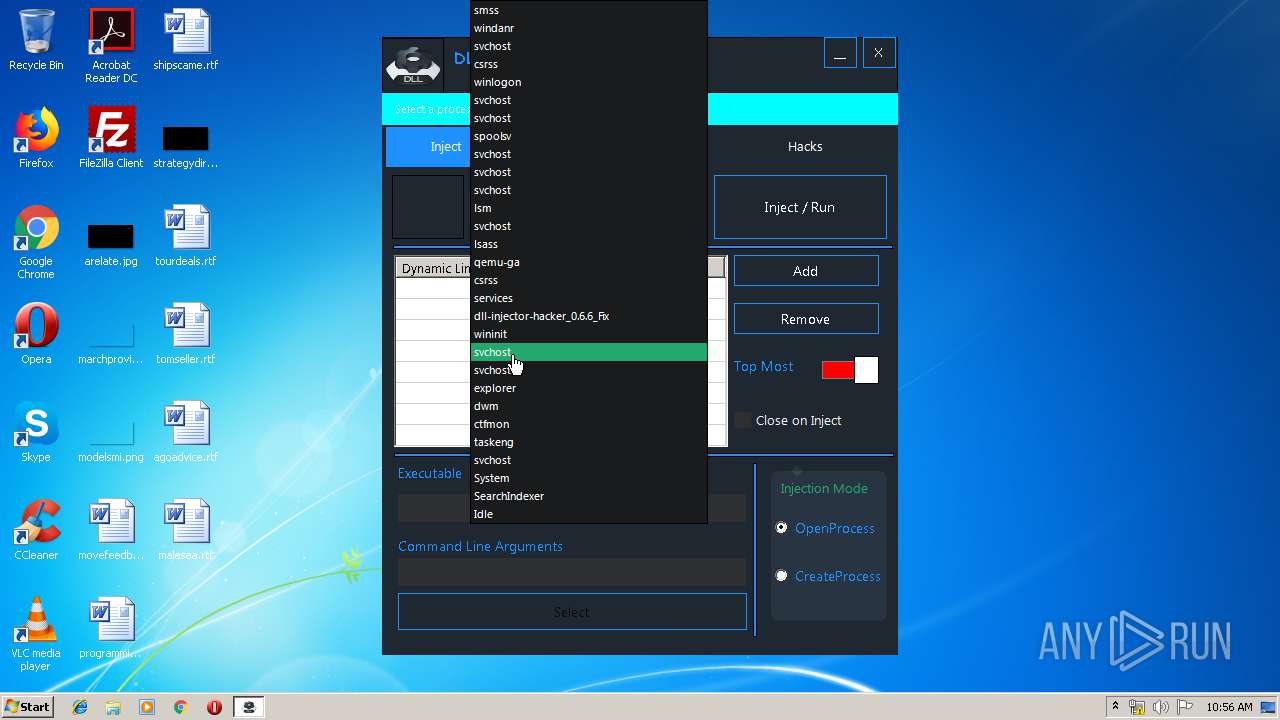
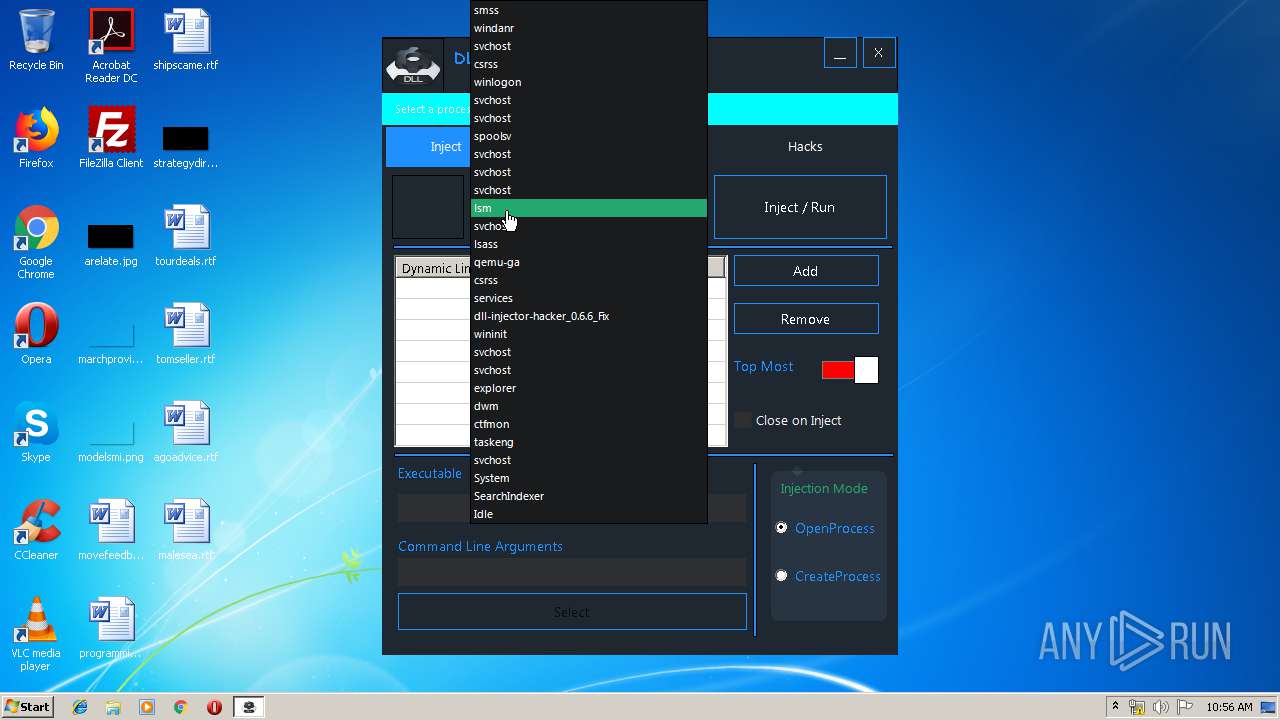
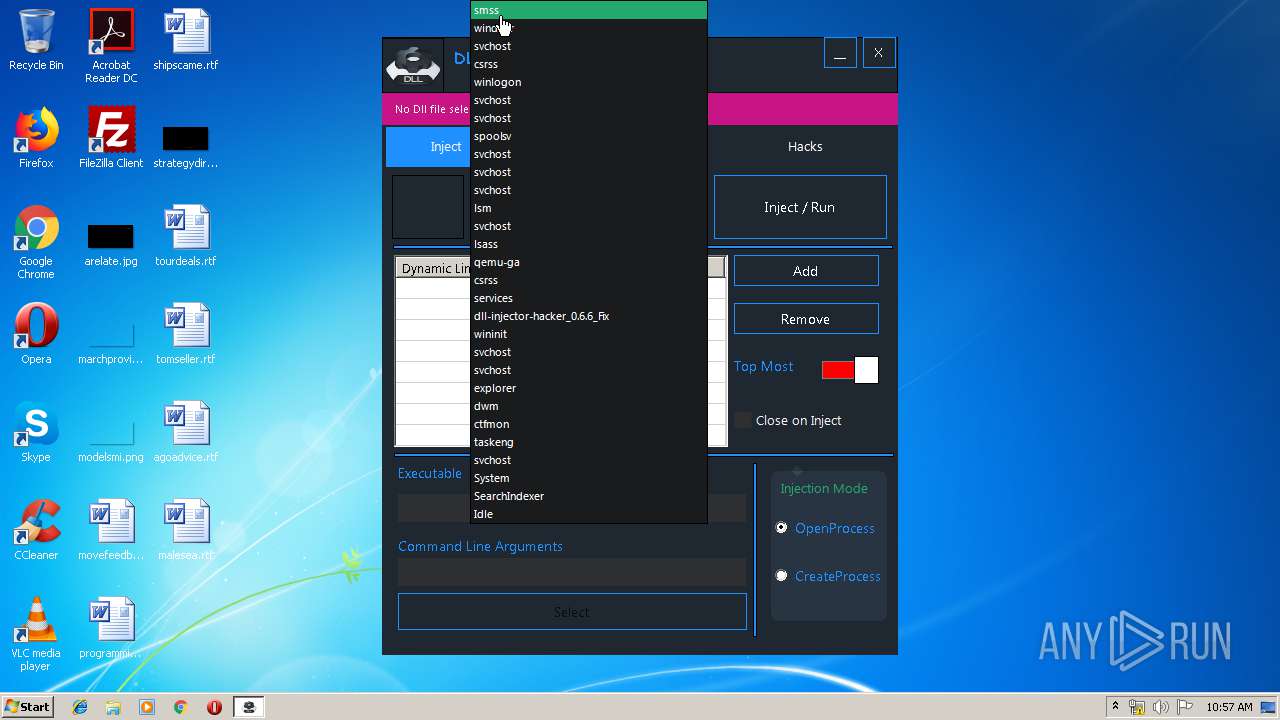
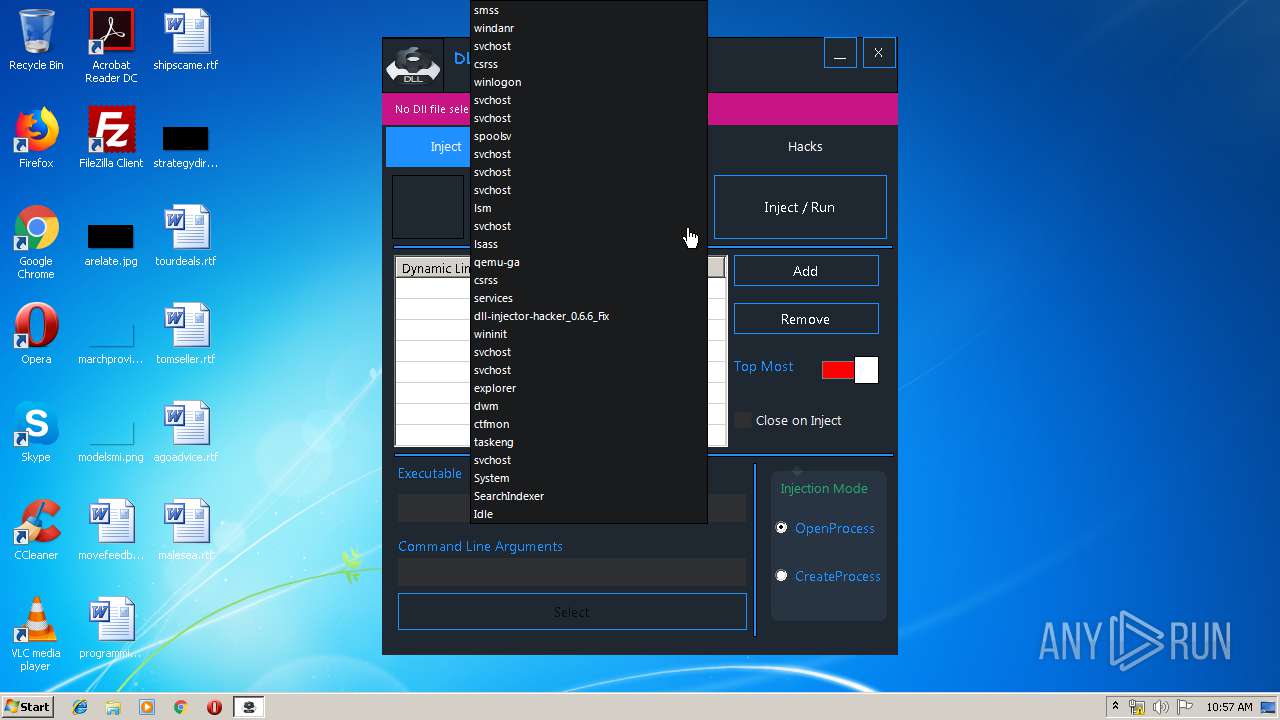
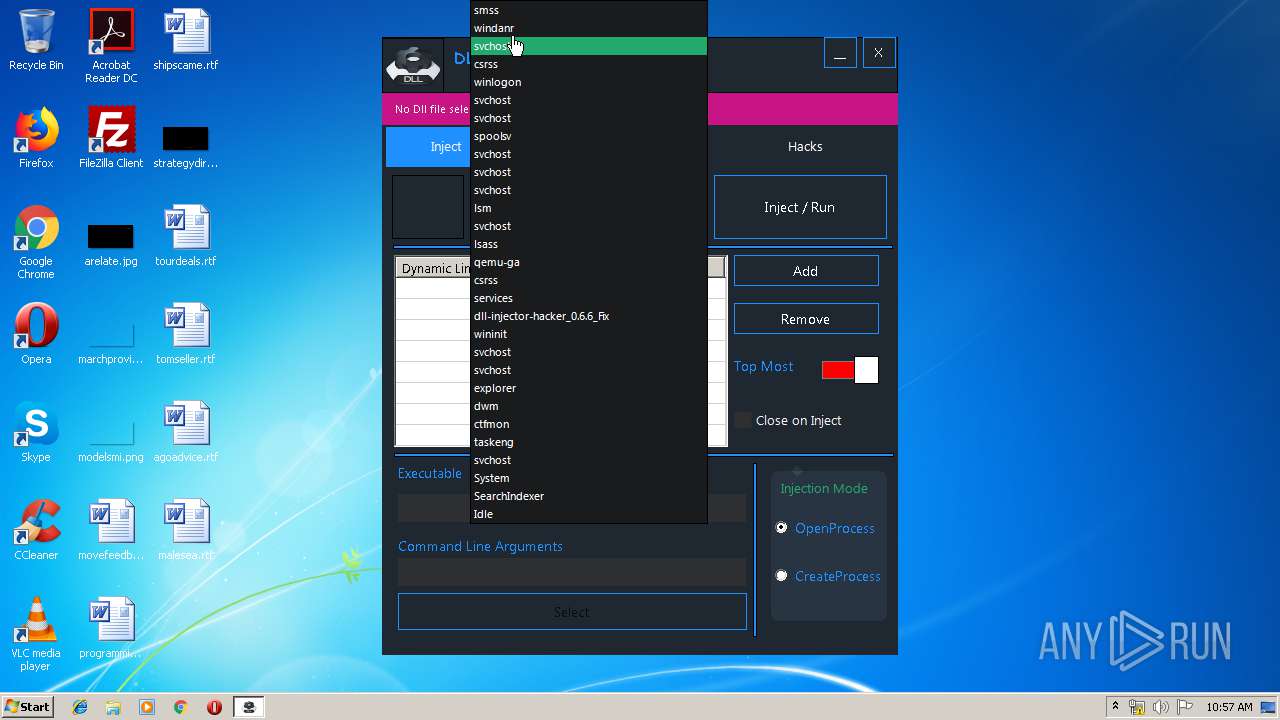
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 900 | "C:\Users\admin\AppData\Local\Temp\dll-injector-hacker_0.6.6_Fix.exe" | C:\Users\admin\AppData\Local\Temp\dll-injector-hacker_0.6.6_Fix.exe | — | explorer.exe | |||||||||||
User: admin Company: none Integrity Level: MEDIUM Description: DLL Injector Hacker Exit code: 3221226540 Version: 0.6.4.6 Modules
| |||||||||||||||
| 2536 | "C:\Users\admin\AppData\Local\Temp\dll-injector-hacker_0.6.6_Fix.exe" | C:\Users\admin\AppData\Local\Temp\dll-injector-hacker_0.6.6_Fix.exe | explorer.exe | ||||||||||||
User: admin Company: none Integrity Level: HIGH Description: DLL Injector Hacker Exit code: 0 Version: 0.6.4.6 Modules
| |||||||||||||||
Total events
1 489
Read events
1 165
Write events
321
Delete events
3
Modification events
| (PID) Process: | (2536) dll-injector-hacker_0.6.6_Fix.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\dll-injector-hacker_0_RASAPI32 |
| Operation: | write | Name: | EnableFileTracing |
Value: 0 | |||
| (PID) Process: | (2536) dll-injector-hacker_0.6.6_Fix.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\dll-injector-hacker_0_RASAPI32 |
| Operation: | write | Name: | EnableConsoleTracing |
Value: 0 | |||
| (PID) Process: | (2536) dll-injector-hacker_0.6.6_Fix.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\dll-injector-hacker_0_RASAPI32 |
| Operation: | write | Name: | FileTracingMask |
Value: 4294901760 | |||
| (PID) Process: | (2536) dll-injector-hacker_0.6.6_Fix.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\dll-injector-hacker_0_RASAPI32 |
| Operation: | write | Name: | ConsoleTracingMask |
Value: 4294901760 | |||
| (PID) Process: | (2536) dll-injector-hacker_0.6.6_Fix.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\dll-injector-hacker_0_RASAPI32 |
| Operation: | write | Name: | MaxFileSize |
Value: 1048576 | |||
| (PID) Process: | (2536) dll-injector-hacker_0.6.6_Fix.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\dll-injector-hacker_0_RASAPI32 |
| Operation: | write | Name: | FileDirectory |
Value: %windir%\tracing | |||
| (PID) Process: | (2536) dll-injector-hacker_0.6.6_Fix.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\dll-injector-hacker_0_RASMANCS |
| Operation: | write | Name: | EnableFileTracing |
Value: 0 | |||
| (PID) Process: | (2536) dll-injector-hacker_0.6.6_Fix.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\dll-injector-hacker_0_RASMANCS |
| Operation: | write | Name: | EnableConsoleTracing |
Value: 0 | |||
| (PID) Process: | (2536) dll-injector-hacker_0.6.6_Fix.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\dll-injector-hacker_0_RASMANCS |
| Operation: | write | Name: | FileTracingMask |
Value: 4294901760 | |||
| (PID) Process: | (2536) dll-injector-hacker_0.6.6_Fix.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\dll-injector-hacker_0_RASMANCS |
| Operation: | write | Name: | ConsoleTracingMask |
Value: 4294901760 | |||
Executable files
0
Suspicious files
0
Text files
30
Unknown types
1
Dropped files
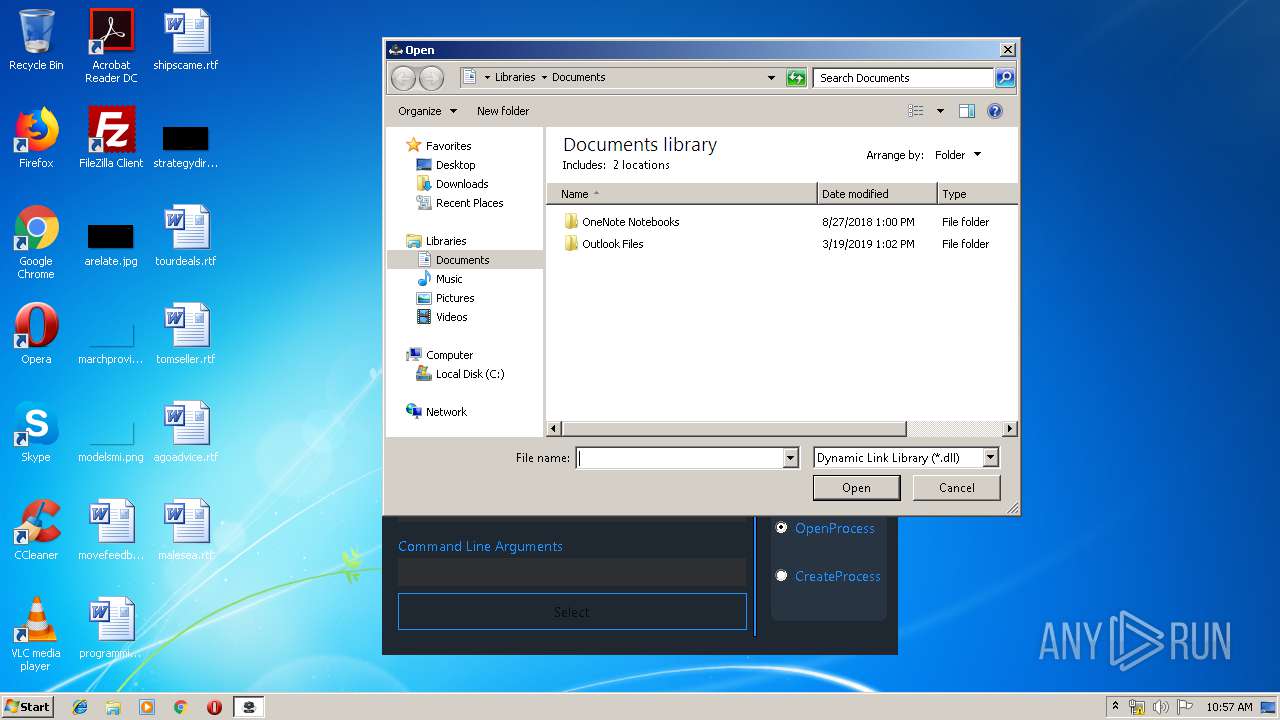
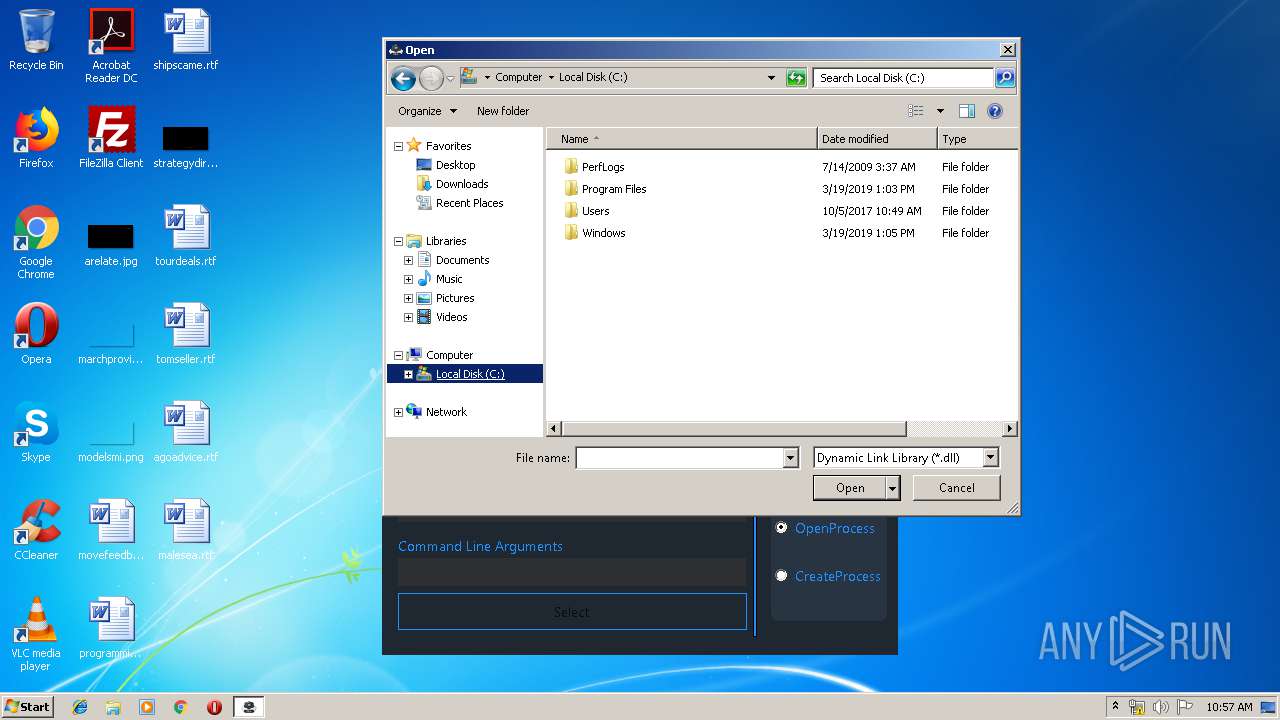
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2536 | dll-injector-hacker_0.6.6_Fix.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\admin@gloyah[1].txt | — | |
MD5:— | SHA256:— | |||
| 2536 | dll-injector-hacker_0.6.6_Fix.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\admin@gloyah[2].txt | text | |
MD5:— | SHA256:— | |||
| 2536 | dll-injector-hacker_0.6.6_Fix.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\H6QNMHE9\BxPw[1].txt | html | |
MD5:— | SHA256:— | |||
| 2536 | dll-injector-hacker_0.6.6_Fix.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\JGRR2OYX\view105c2[1].js | text | |
MD5:— | SHA256:— | |||
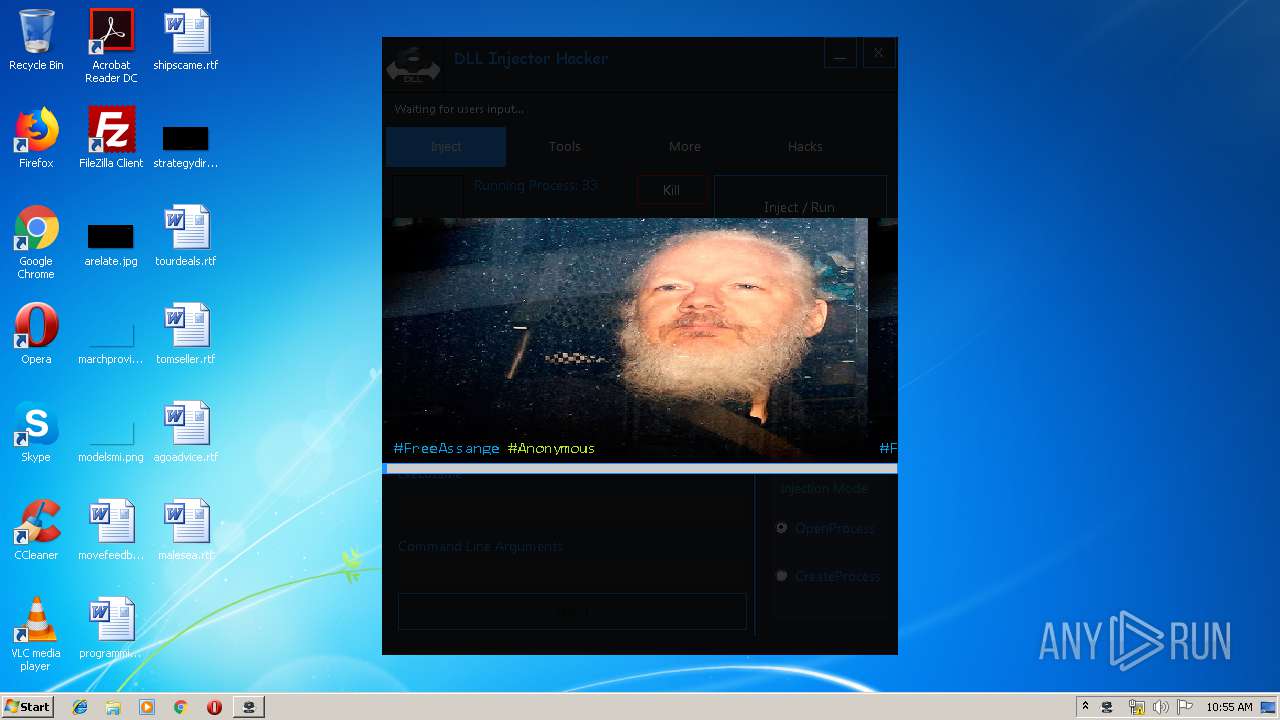
| 2536 | dll-injector-hacker_0.6.6_Fix.exe | C:\Users\admin\AppData\Local\Temp\a1a.jpg | image | |
MD5:— | SHA256:— | |||
| 2536 | dll-injector-hacker_0.6.6_Fix.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\H6QNMHE9\adfly_7[1].css | text | |
MD5:— | SHA256:— | |||
| 2536 | dll-injector-hacker_0.6.6_Fix.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\I0488CJO\b64[1].js | text | |
MD5:— | SHA256:— | |||
| 2536 | dll-injector-hacker_0.6.6_Fix.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\LH043OAM\d1nmxiiewlx627_cloudfront_net[1] | text | |
MD5:— | SHA256:— | |||
| 2536 | dll-injector-hacker_0.6.6_Fix.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\JGRR2OYX\main[1].js | text | |
MD5:— | SHA256:— | |||
| 2536 | dll-injector-hacker_0.6.6_Fix.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\admin@adf[1].txt | text | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
22
TCP/UDP connections
14
DNS requests
12
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2536 | dll-injector-hacker_0.6.6_Fix.exe | GET | 301 | 104.24.5.46:80 | http://j.gs/BxPw | US | — | — | malicious |
2536 | dll-injector-hacker_0.6.6_Fix.exe | GET | 302 | 185.60.216.35:80 | http://www.facebook.com/plugins/like.php?href=https%3A%2F%2Fwww.facebook.com%2Fx19ltd.adfly&width=150&fb_source=unshorten&layout=button_count&action=like&show_faces=false&share=true&height=21&appId=399141353502152 | IE | — | — | whitelisted |
2536 | dll-injector-hacker_0.6.6_Fix.exe | GET | 200 | 104.28.29.118:80 | http://cdn.gloyah.net/static/js/main.js | US | text | 673 b | suspicious |
2536 | dll-injector-hacker_0.6.6_Fix.exe | GET | 200 | 104.28.29.118:80 | http://gloyah.net/-12NVMI/BxPw?rndad=3650312466-1558950903 | US | html | 5.58 Kb | suspicious |
2536 | dll-injector-hacker_0.6.6_Fix.exe | GET | 200 | 104.28.29.118:80 | http://cdn.gloyah.net/static/js/amvn.js | US | text | 78.0 Kb | suspicious |
2536 | dll-injector-hacker_0.6.6_Fix.exe | GET | 404 | 104.28.29.118:80 | http://cdn.gloyah.net/static/image/ad_top_bg2.png?&ad_box_=1 | US | html | 392 b | suspicious |
2536 | dll-injector-hacker_0.6.6_Fix.exe | GET | 200 | 104.20.18.254:80 | http://adf.ly/funcript1558950905327.php?pub=20620799&v=z4MSDNcuyMODTIsSgxL0kQ5gFQVVCRBOD5TCFII7gcMjyM43wALTjNMuwANjzLIy5AOiyUBMNNZEWIRUpVYkSTBuDAZyWO5y0MZ0XQIMgNUFEIM7gANjiL40w8OCydAuuVTGkZVpUJNHCV4gwsQTzMsugYLDkI5UF5VEDIQzudM3EbUkp5IWiawXiBdyWOQwi4OCjOIgwUNUjSITw1NEzIk75ULGCbJi2lIGjdohyBLXCbJvjNaGyKIg6AdjHLJ018ZSSYwsixcWGaF609IWjToi0oMjiIw0i5YWmZlnuFZmEcVlsNZXWd1ilwbinIQzidO3ibJkz5aW2alXwJXi2OJi1MM3nbRf0Bb32b40itL2CcJloRYmXINsoIIyjboOiJMimOYiwMO3GbEf1VMGDblpjJM2jbMtxJZCDLcw3oYjTIYl4xNWzaYix9YWTbZihwNCmME6zIOCTaAz0FOGDbgmiJfyQe== | US | text | 58.0 Kb | shared |
2536 | dll-injector-hacker_0.6.6_Fix.exe | GET | 200 | 104.28.29.118:80 | http://gloyah.net/js/display.js | US | text | 20.8 Kb | suspicious |
2536 | dll-injector-hacker_0.6.6_Fix.exe | GET | 200 | 104.28.29.118:80 | http://gloyah.net/fp.rev10.php?nocache=9457 | US | text | 14.3 Kb | suspicious |
2536 | dll-injector-hacker_0.6.6_Fix.exe | GET | 200 | 104.28.29.118:80 | http://cdn.gloyah.net/static/css/adfly_7.css | US | text | 869 b | suspicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2536 | dll-injector-hacker_0.6.6_Fix.exe | 193.70.81.190:443 | hax4ever.com | OVH SAS | FR | unknown |
2536 | dll-injector-hacker_0.6.6_Fix.exe | 104.28.29.118:80 | gloyah.net | Cloudflare Inc | US | shared |
2536 | dll-injector-hacker_0.6.6_Fix.exe | 104.24.5.46:80 | j.gs | Cloudflare Inc | US | shared |
2536 | dll-injector-hacker_0.6.6_Fix.exe | 52.85.188.38:80 | d1nmxiiewlx627.cloudfront.net | Amazon.com, Inc. | US | unknown |
2536 | dll-injector-hacker_0.6.6_Fix.exe | 104.20.208.21:443 | pastebin.com | Cloudflare Inc | US | shared |
2536 | dll-injector-hacker_0.6.6_Fix.exe | 172.217.22.42:80 | ajax.googleapis.com | Google Inc. | US | whitelisted |
2536 | dll-injector-hacker_0.6.6_Fix.exe | 51.15.74.77:443 | i.ibb.co | Online S.a.s. | FR | unknown |
2536 | dll-injector-hacker_0.6.6_Fix.exe | 104.20.18.254:80 | adf.ly | Cloudflare Inc | US | shared |
2536 | dll-injector-hacker_0.6.6_Fix.exe | 185.60.216.35:80 | www.facebook.com | Facebook, Inc. | IE | whitelisted |
2536 | dll-injector-hacker_0.6.6_Fix.exe | 216.58.207.78:80 | www.google-analytics.com | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
hax4ever.com |
| unknown |
j.gs |
| malicious |
gloyah.net |
| suspicious |
ajax.googleapis.com |
| whitelisted |
cdn.gloyah.net |
| suspicious |
d1nmxiiewlx627.cloudfront.net |
| whitelisted |
pastebin.com |
| malicious |
i.ibb.co |
| shared |
adf.ly |
| shared |
www.google-analytics.com |
| whitelisted |