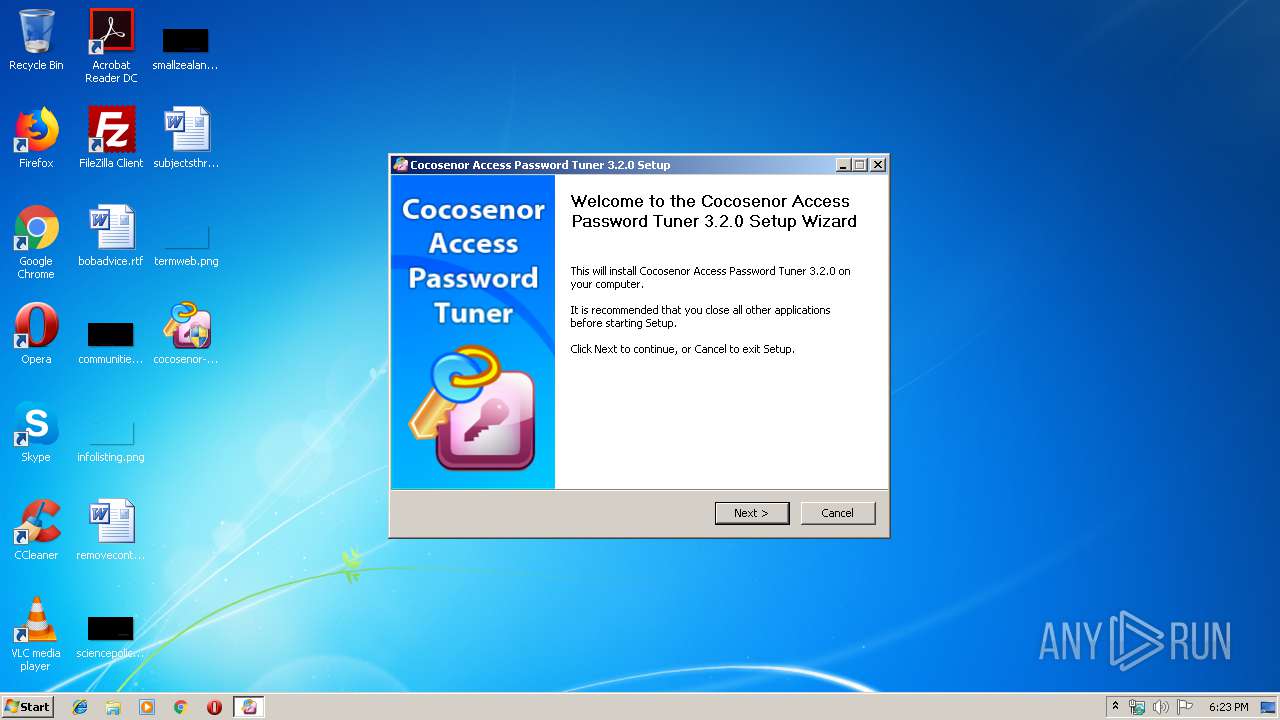
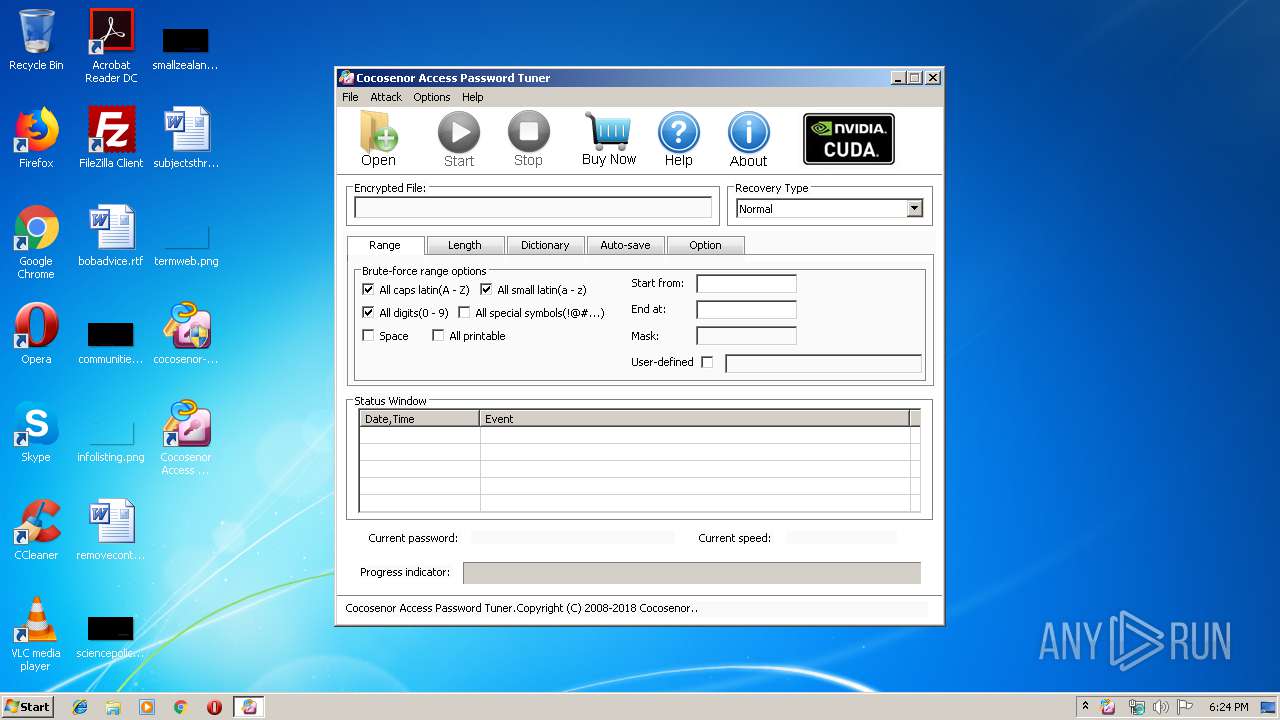
| download: | cocosenor-access-password-tuner.exe |
| Full analysis: | https://app.any.run/tasks/0cdd5987-831f-4325-a602-39e2fd55bcf5 |
| Verdict: | Malicious activity |
| Analysis date: | January 03, 2020, 18:23:07 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, Nullsoft Installer self-extracting archive |
| MD5: | B48F688CA8CFEFDB47BD0353AE35241D |
| SHA1: | F000D94D718D9E5193523AEFCE84979A6D8776ED |
| SHA256: | 64A80D23BA63C041D3DF21ECD1AFF015C7899BDB6EF21E5FB6808876F75A7EF4 |
| SSDEEP: | 98304:di5HDvCWlsGzeFjxMS3UJCnLKBV+F15jJMsK86FGyo2muIyycs+G4VOEhGutZeQK:Ad3P+DEhVw1YsK55+uIyucXEcZeQK |
MALICIOUS
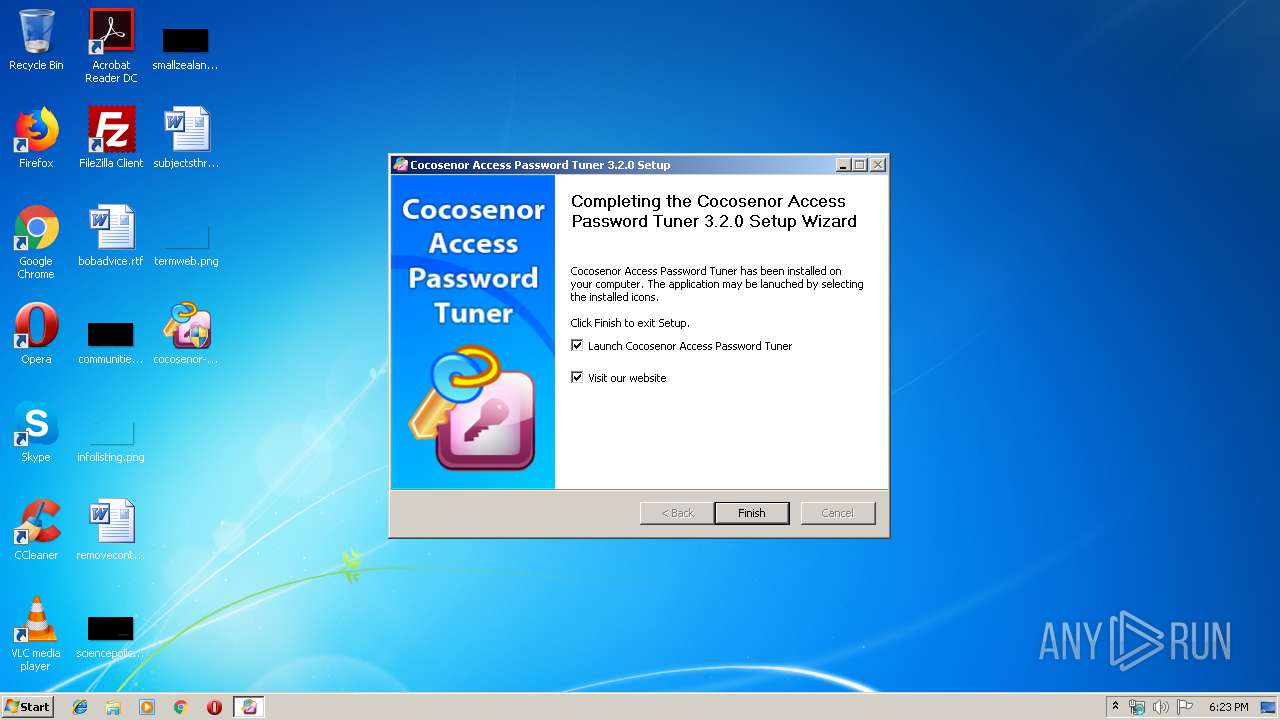
Application was dropped or rewritten from another process
- CocosenorAccessPasswordTuner.exe (PID: 3116)
Loads dropped or rewritten executable
- cocosenor-access-password-tuner.exe (PID: 1952)
- CocosenorAccessPasswordTuner.exe (PID: 3116)
SUSPICIOUS
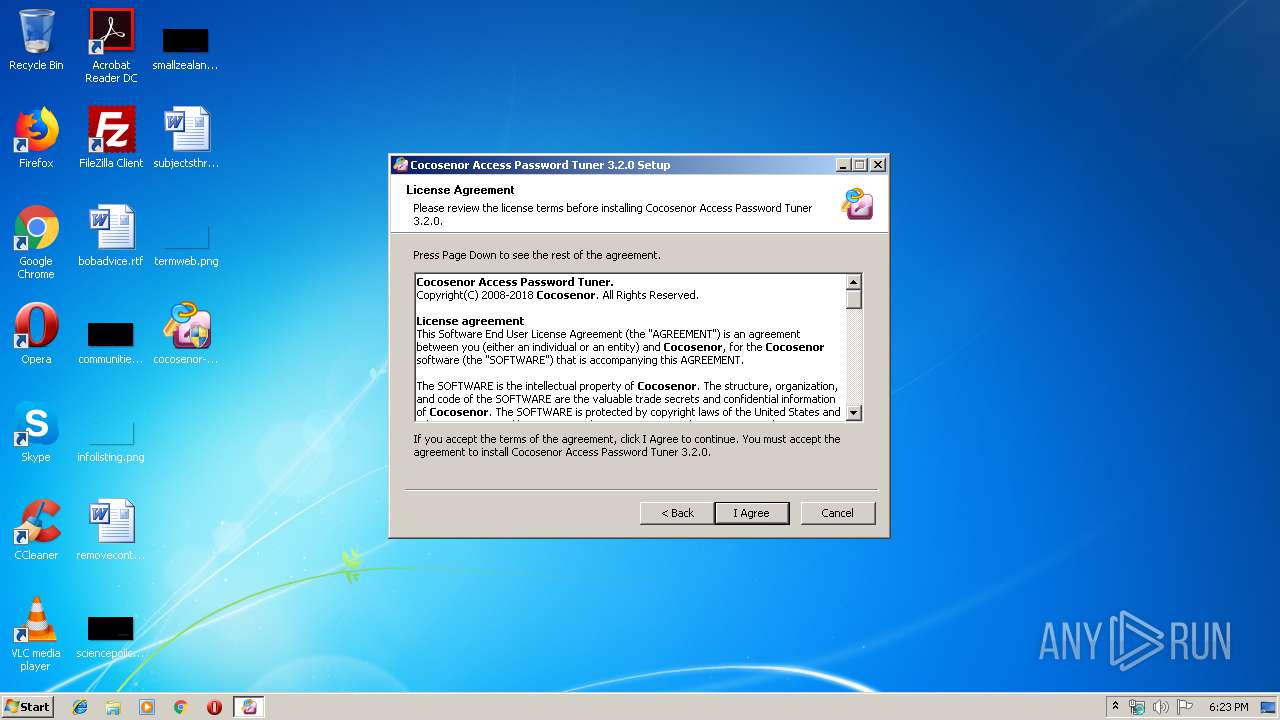
Creates files in the program directory
- cocosenor-access-password-tuner.exe (PID: 1952)
Creates a software uninstall entry
- cocosenor-access-password-tuner.exe (PID: 1952)
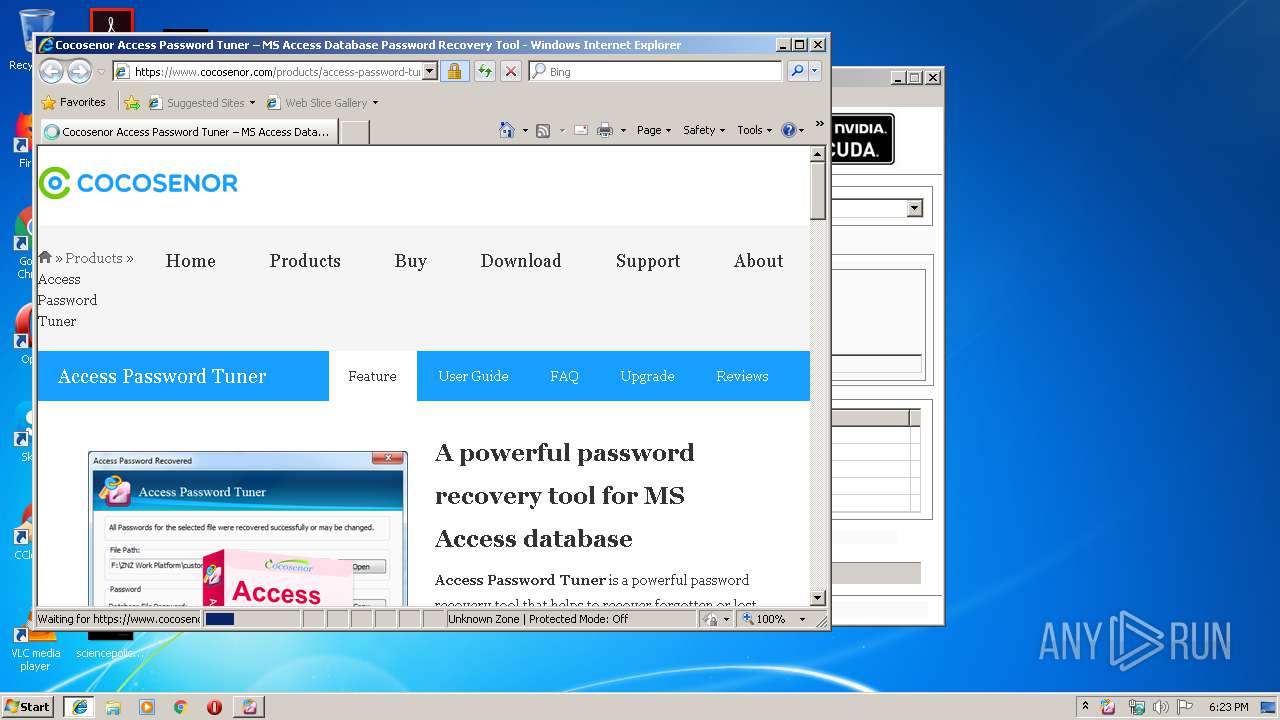
Starts Internet Explorer
- cocosenor-access-password-tuner.exe (PID: 1952)
Executable content was dropped or overwritten
- cocosenor-access-password-tuner.exe (PID: 1952)
Creates files in the user directory
- cocosenor-access-password-tuner.exe (PID: 1952)
INFO
Changes internet zones settings
- iexplore.exe (PID: 2932)
Reads internet explorer settings
- iexplore.exe (PID: 3172)
Creates files in the user directory
- iexplore.exe (PID: 3172)
Reads Internet Cache Settings
- iexplore.exe (PID: 3172)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | NSIS - Nullsoft Scriptable Install System (94.8) |
|---|---|---|
| .exe | | | Win32 Executable MS Visual C++ (generic) (3.4) |
| .dll | | | Win32 Dynamic Link Library (generic) (0.7) |
| .exe | | | Win32 Executable (generic) (0.5) |
| .exe | | | Generic Win/DOS Executable (0.2) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2009:06:06 23:41:59+02:00 |
| PEType: | PE32 |
| LinkerVersion: | 6 |
| CodeSize: | 24064 |
| InitializedDataSize: | 164864 |
| UninitializedDataSize: | 1024 |
| EntryPoint: | 0x30fa |
| OSVersion: | 4 |
| ImageVersion: | 6.1 |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 06-Jun-2009 21:41:59 |
| Detected languages: |
|
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x000000D8 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 5 |
| Time date stamp: | 06-Jun-2009 21:41:59 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x00005C4C | 0x00005E00 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.44011 |
.rdata | 0x00007000 | 0x0000129C | 0x00001400 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 5.04684 |
.data | 0x00009000 | 0x00025C58 | 0x00000400 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 4.801 |
.ndata | 0x0002F000 | 0x00009000 | 0x00000000 | IMAGE_SCN_CNT_UNINITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.rsrc | 0x00038000 | 0x00047DA8 | 0x00047E00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 6.63801 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.21446 | 958 | UNKNOWN | English - United States | RT_MANIFEST |
2 | 7.97319 | 48675 | UNKNOWN | English - United States | RT_ICON |
3 | 7.95598 | 44386 | UNKNOWN | English - United States | RT_ICON |
4 | 5.69195 | 38056 | UNKNOWN | English - United States | RT_ICON |
5 | 5.70619 | 26600 | UNKNOWN | English - United States | RT_ICON |
6 | 5.6846 | 21640 | UNKNOWN | English - United States | RT_ICON |
7 | 5.64234 | 16936 | UNKNOWN | English - United States | RT_ICON |
8 | 5.83545 | 9640 | UNKNOWN | English - United States | RT_ICON |
9 | 5.95788 | 4264 | UNKNOWN | English - United States | RT_ICON |
10 | 6.00585 | 3752 | UNKNOWN | English - United States | RT_ICON |
Imports
ADVAPI32.dll |
COMCTL32.dll |
GDI32.dll |
KERNEL32.dll |
SHELL32.dll |
USER32.dll |
VERSION.dll |
ole32.dll |
Total processes
43
Monitored processes
5
Malicious processes
2
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1952 | "C:\Users\admin\Desktop\cocosenor-access-password-tuner.exe" | C:\Users\admin\Desktop\cocosenor-access-password-tuner.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 2284 | "C:\Users\admin\Desktop\cocosenor-access-password-tuner.exe" | C:\Users\admin\Desktop\cocosenor-access-password-tuner.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 3221226540 Modules
| |||||||||||||||
| 2932 | "C:\Program Files\Internet Explorer\iexplore.exe" -nohome | C:\Program Files\Internet Explorer\iexplore.exe | cocosenor-access-password-tuner.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Internet Explorer Exit code: 1 Version: 8.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
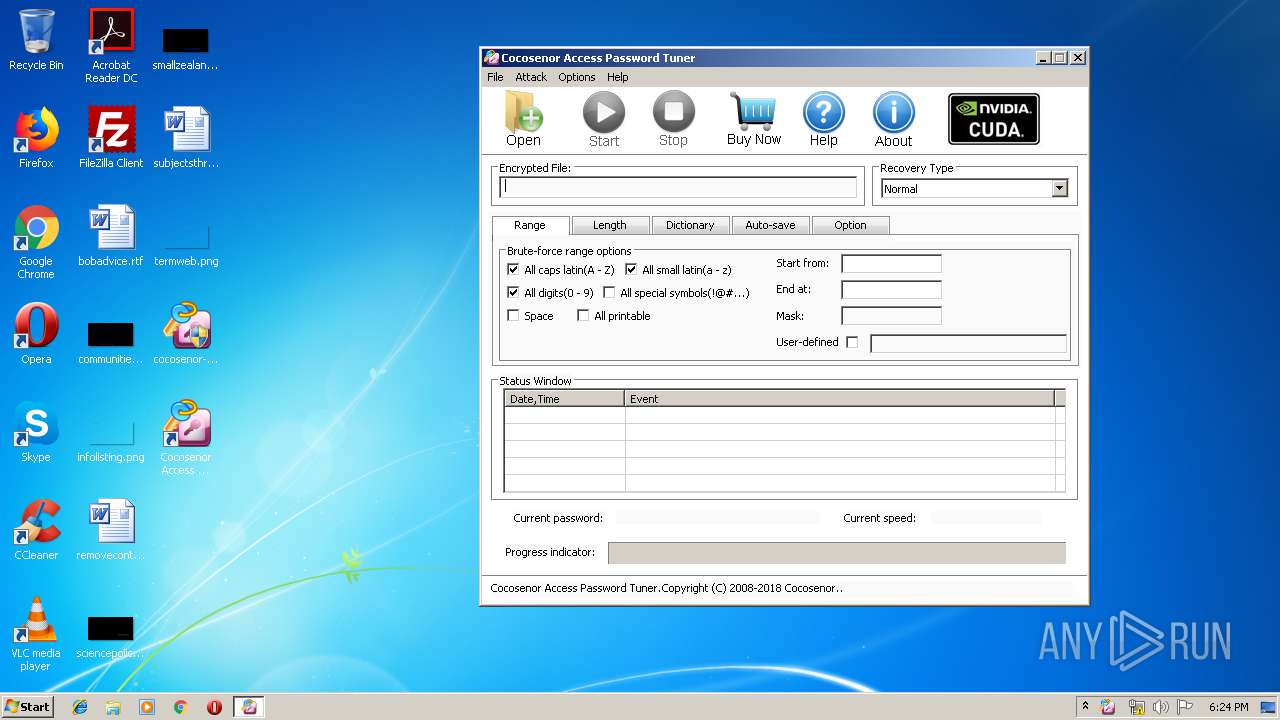
| 3116 | "C:\Program Files\Cocosenor Access Password Tuner\CocosenorAccessPasswordTuner.exe" | C:\Program Files\Cocosenor Access Password Tuner\CocosenorAccessPasswordTuner.exe | — | cocosenor-access-password-tuner.exe | |||||||||||
User: admin Company: Cocosenor Integrity Level: HIGH Description: Access Password Tuner Exit code: 0 Version: 3.2.0.0 Modules
| |||||||||||||||
| 3172 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:2932 CREDAT:79873 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Internet Explorer Exit code: 0 Version: 8.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
649
Read events
552
Write events
95
Delete events
2
Modification events
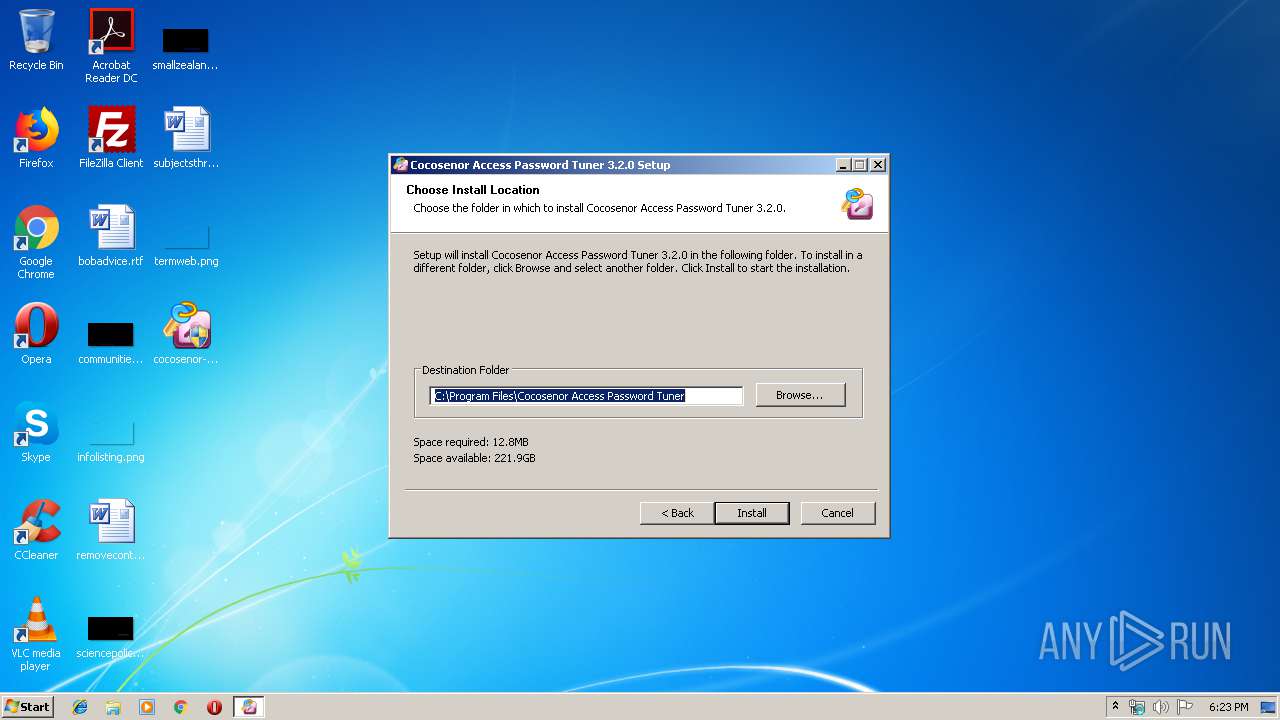
| (PID) Process: | (1952) cocosenor-access-password-tuner.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\App Paths\CocosenorAccessPasswordTuner.exe |
| Operation: | write | Name: | |
Value: C:\Program Files\Cocosenor Access Password Tuner\CocosenorAccessPasswordTuner.exe | |||
| (PID) Process: | (1952) cocosenor-access-password-tuner.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\Cocosenor Access Password Tuner |
| Operation: | write | Name: | DisplayName |
Value: Cocosenor Access Password Tuner 3.2.0 | |||
| (PID) Process: | (1952) cocosenor-access-password-tuner.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\Cocosenor Access Password Tuner |
| Operation: | write | Name: | UninstallString |
Value: C:\Program Files\Cocosenor Access Password Tuner\uninst.exe | |||
| (PID) Process: | (1952) cocosenor-access-password-tuner.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\Cocosenor Access Password Tuner |
| Operation: | write | Name: | DisplayIcon |
Value: C:\Program Files\Cocosenor Access Password Tuner\CocosenorAccessPasswordTuner.exe | |||
| (PID) Process: | (1952) cocosenor-access-password-tuner.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\Cocosenor Access Password Tuner |
| Operation: | write | Name: | DisplayVersion |
Value: 3.2.0 | |||
| (PID) Process: | (1952) cocosenor-access-password-tuner.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\Cocosenor Access Password Tuner |
| Operation: | write | Name: | URLInfoAbout |
Value: https://www.cocosenor.com/products/access-password-tuner/ | |||
| (PID) Process: | (1952) cocosenor-access-password-tuner.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Uninstall\Cocosenor Access Password Tuner |
| Operation: | write | Name: | Publisher |
Value: Cocosenor | |||
| (PID) Process: | (2932) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (2932) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (2932) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
Executable files
12
Suspicious files
2
Text files
78
Unknown types
8
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1952 | cocosenor-access-password-tuner.exe | C:\Program Files\Cocosenor Access Password Tuner\CocosenorDictionary.txt | — | |
MD5:— | SHA256:— | |||
| 1952 | cocosenor-access-password-tuner.exe | C:\Users\admin\AppData\Local\Temp\nshA45A.tmp\ioSpecial.ini | text | |
MD5:— | SHA256:— | |||
| 1952 | cocosenor-access-password-tuner.exe | C:\Program Files\Cocosenor Access Password Tuner\CocosenorAccessPasswordTuner.exe | executable | |
MD5:— | SHA256:— | |||
| 1952 | cocosenor-access-password-tuner.exe | C:\Users\admin\AppData\Local\Temp\nshA45A.tmp\InstallOptions.dll | executable | |
MD5:0DC0CC7A6D9DB685BF05A7E5F3EA4781 | SHA256:8E287326F1CDD5EF2DCD7A72537C68CBE4299CEB1F820707C5820F3AA6D8206C | |||
| 1952 | cocosenor-access-password-tuner.exe | C:\Users\admin\AppData\Local\Temp\nshA45A.tmp\modern-wizard.bmp | image | |
MD5:— | SHA256:— | |||
| 1952 | cocosenor-access-password-tuner.exe | C:\Program Files\Cocosenor Access Password Tuner\Images\Button_OpenFile.png | image | |
MD5:7C5A4B8CD247344083CDBC056A197CD3 | SHA256:D0A00837F7080721D7EE46FDBC6FBD1ADC293C5979D6020C61C2CC7E46D5D3E1 | |||
| 1952 | cocosenor-access-password-tuner.exe | C:\Program Files\Cocosenor Access Password Tuner\Images\Button_Top_BuyNow.png | image | |
MD5:C337DB311C615B7CB955CEEE342DCA89 | SHA256:9DADE4B7275BB6F39979E70A5F3D97E89750D482882C7EF95091DB2F878D3719 | |||
| 1952 | cocosenor-access-password-tuner.exe | C:\Program Files\Cocosenor Access Password Tuner\Images\Button_Top_Start.png | image | |
MD5:B28606D089F875AD276E518026CA3236 | SHA256:4A353B3DD2E528EB837588A51FC2B6FAF76C0F1221BE8523E7AF46977F4DE4E1 | |||
| 1952 | cocosenor-access-password-tuner.exe | C:\Program Files\Cocosenor Access Password Tuner\Images\Button_Top_OpenFile.png | image | |
MD5:52A5144CE7E5110F6F2337329C2069FC | SHA256:C87744EC54AB5A1EE03EFDEA69B2A62553BE5C65A95063806EFFCB944196159B | |||
| 1952 | cocosenor-access-password-tuner.exe | C:\Program Files\Cocosenor Access Password Tuner\Images\Button_Top_About.png | image | |
MD5:E70D13EB681BD7F1277E6090E366AD8F | SHA256:17DE079DCBFD7F4DC303337C04DF2CD280325BDA35BEF36308347BC4E185B2B7 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
1
TCP/UDP connections
13
DNS requests
4
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2932 | iexplore.exe | GET | 200 | 204.79.197.200:80 | http://www.bing.com/favicon.ico | US | image | 237 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3172 | iexplore.exe | 162.241.172.26:443 | www.cocosenor.com | CyrusOne LLC | US | unknown |
3172 | iexplore.exe | 104.20.2.47:443 | www.statcounter.com | Cloudflare Inc | US | shared |
2932 | iexplore.exe | 204.79.197.200:80 | www.bing.com | Microsoft Corporation | US | whitelisted |
3172 | iexplore.exe | 104.20.3.47:443 | www.statcounter.com | Cloudflare Inc | US | shared |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.cocosenor.com |
| unknown |
www.bing.com |
| whitelisted |
www.statcounter.com |
| whitelisted |
c.statcounter.com |
| whitelisted |