| File name: | spsetup132.exe |
| Full analysis: | https://app.any.run/tasks/fd7afea8-e852-48d3-b55b-ca0058017db7 |
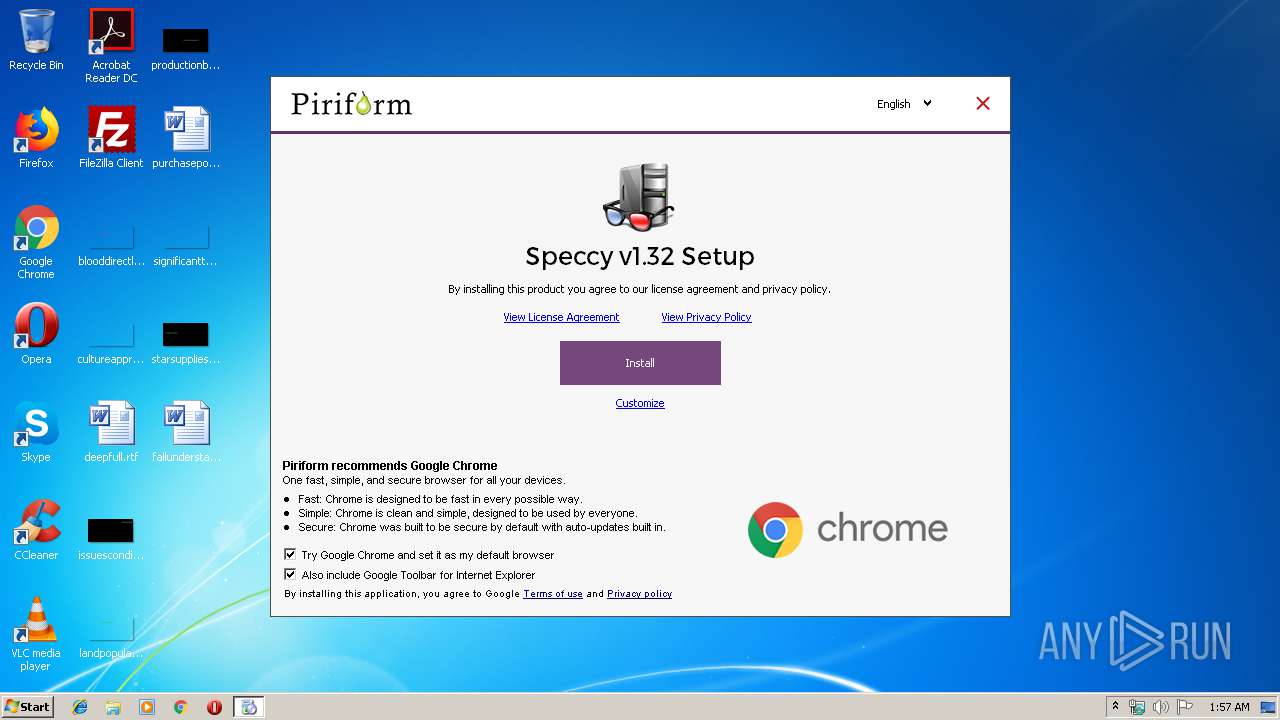
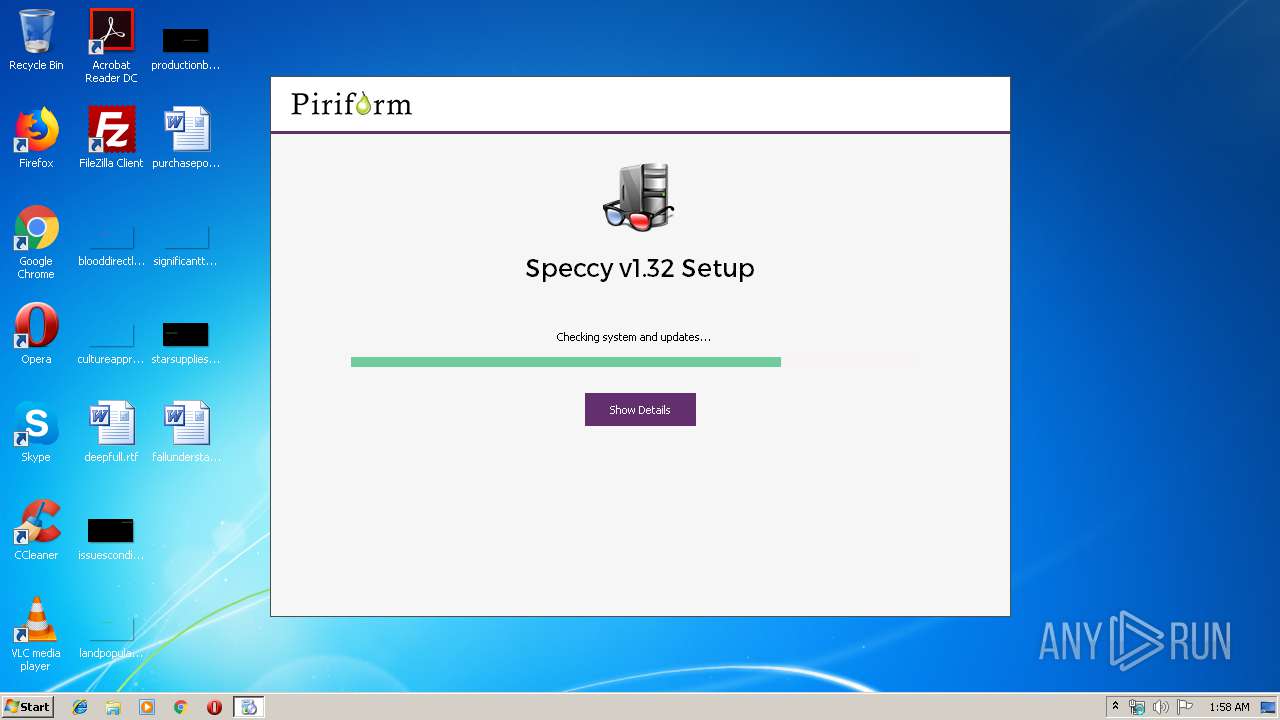
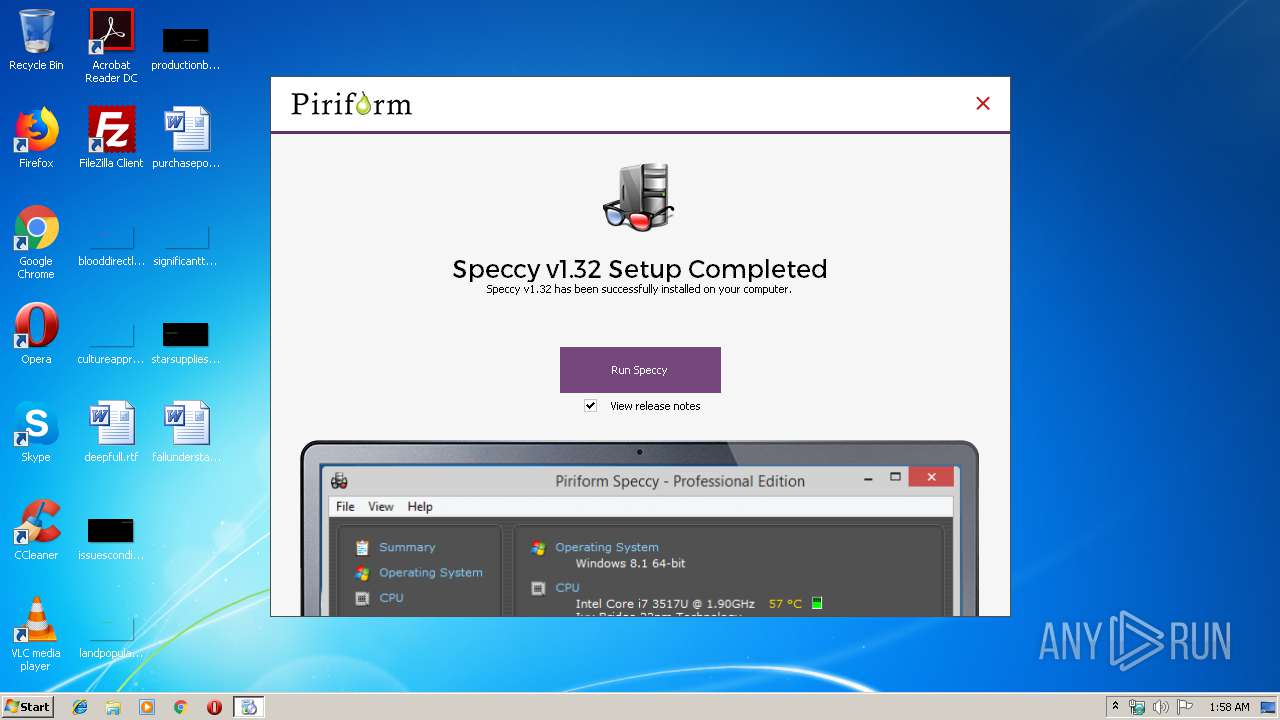
| Verdict: | Malicious activity |
| Analysis date: | July 08, 2019, 00:57:30 |
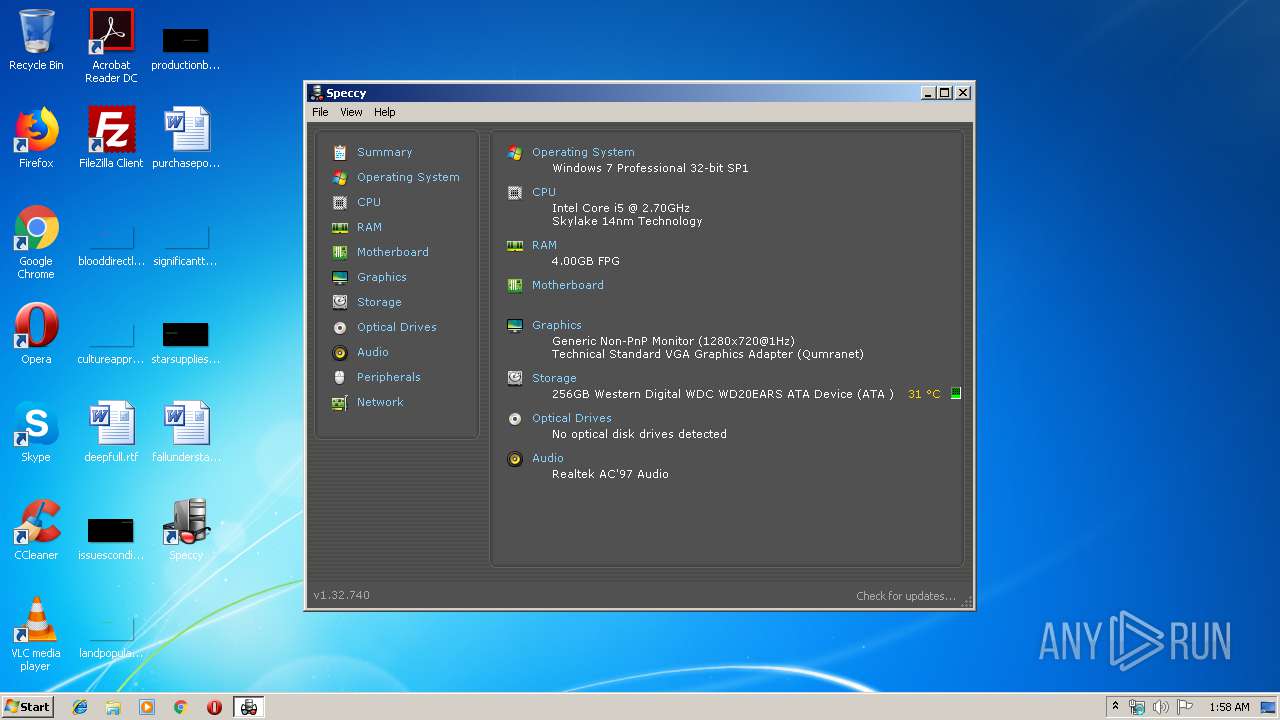
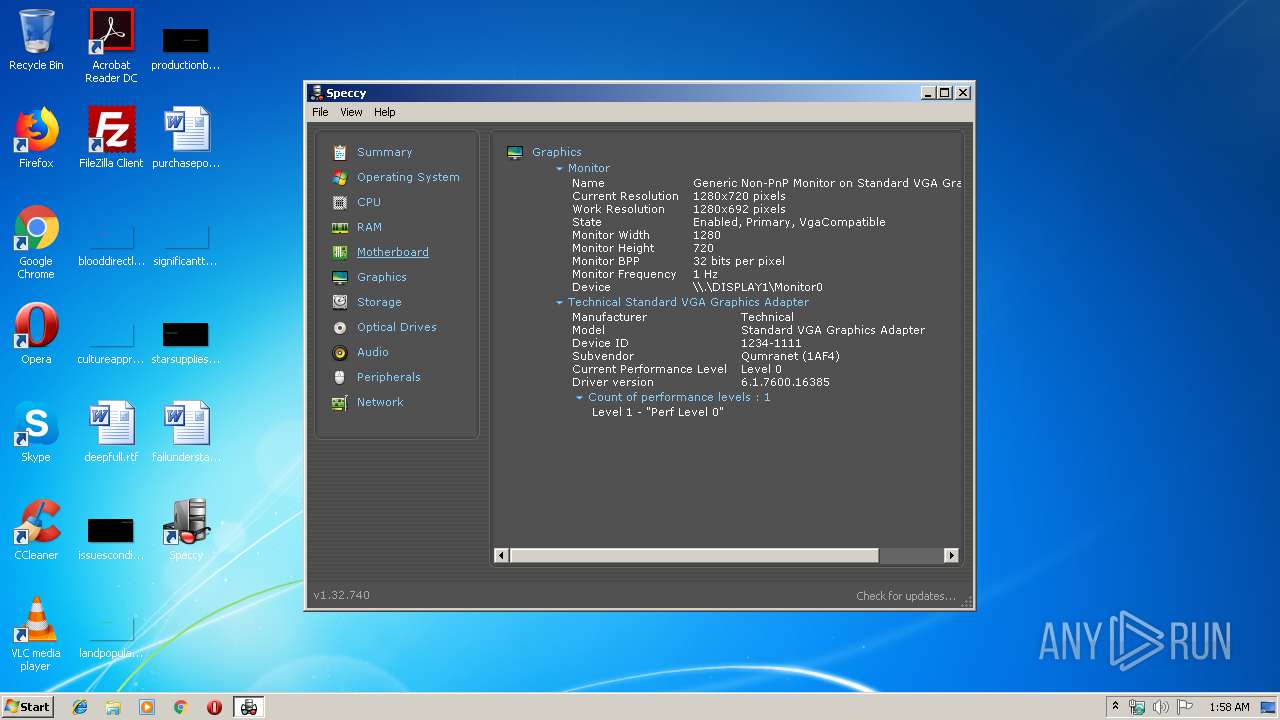
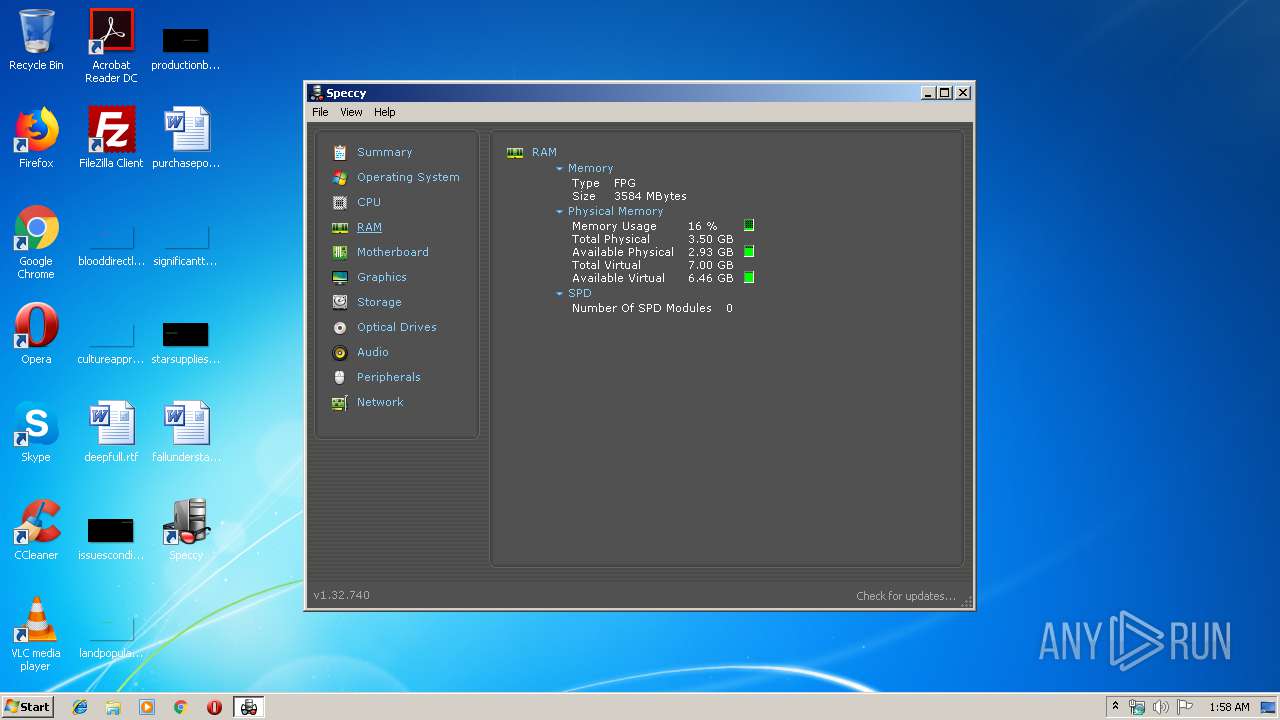
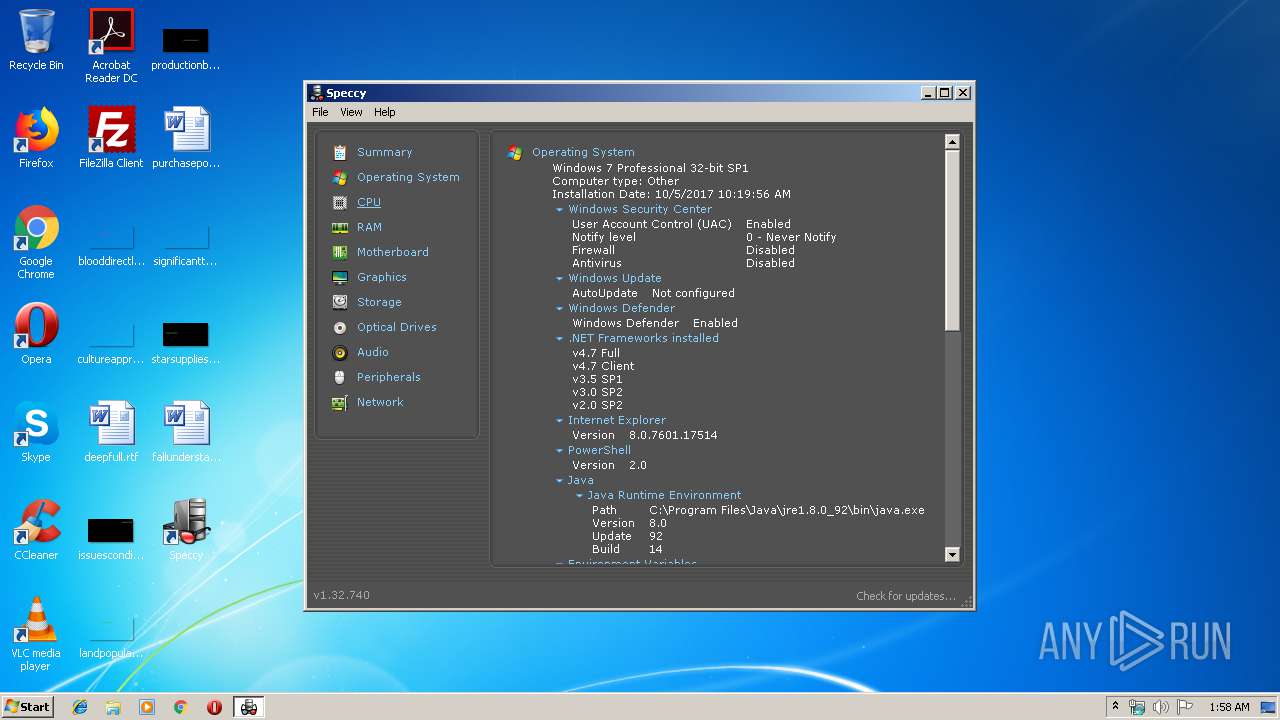
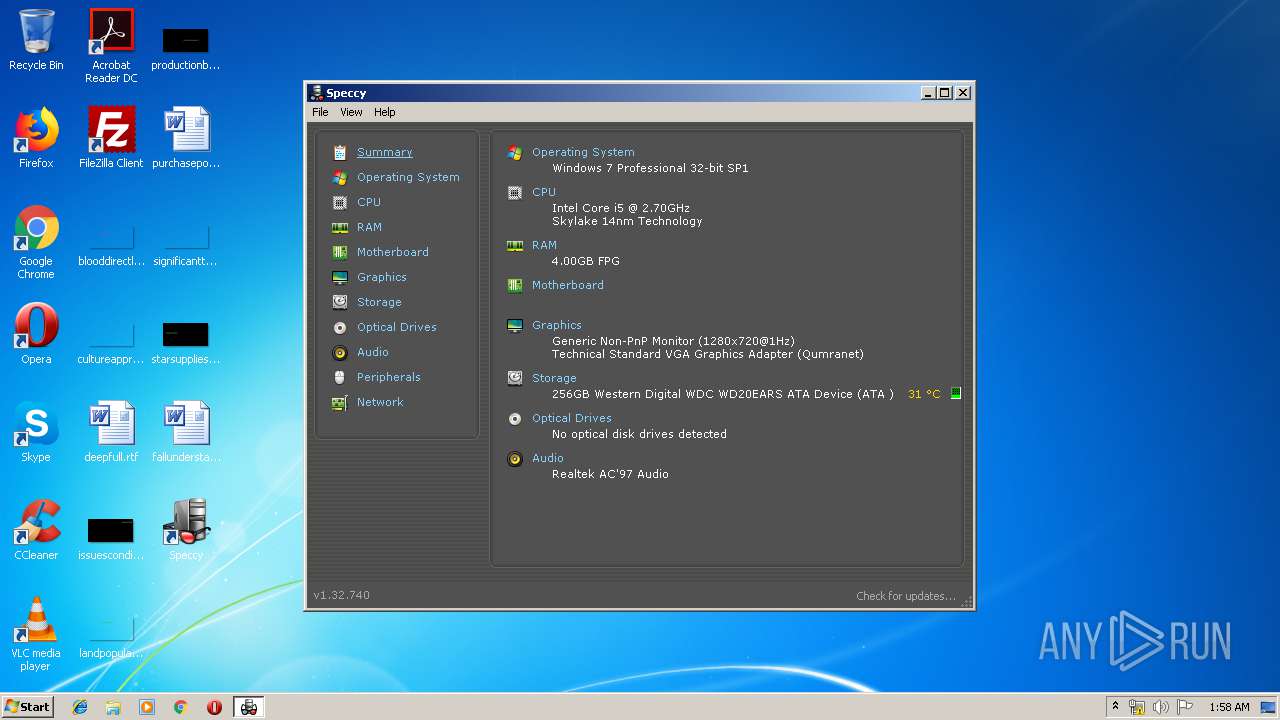
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, Nullsoft Installer self-extracting archive |
| MD5: | 659A1F2110DE9F2DB50B5D698C9E5E3B |
| SHA1: | 0969083828549E92CE50BAD28D52BDEEC9B491DD |
| SHA256: | 64A5BA6D65E0B73AE6987C561C86B1E2338A1F337AB5BD5A87C9EEBA4963CC3F |
| SSDEEP: | 98304:PayQv8yZDjDaZHHQL2B+RyqXq7o6EP/HQp/Umzj0BaUKw32r7aiiAi+ko:P48yZDIHw6kRyIySXQp/UYgBaG2HaWqo |
MALICIOUS
Loads dropped or rewritten executable
- spsetup132.exe (PID: 3288)
- Speccy.exe (PID: 3204)
Actions looks like stealing of personal data
- spsetup132.exe (PID: 3288)
Application was dropped or rewritten from another process
- nsA560.tmp (PID: 3560)
- Speccy.exe (PID: 3204)
Loads the Task Scheduler COM API
- Speccy.exe (PID: 3204)
SUSPICIOUS
Reads the cookies of Mozilla Firefox
- spsetup132.exe (PID: 3288)
Creates files in the user directory
- spsetup132.exe (PID: 3288)
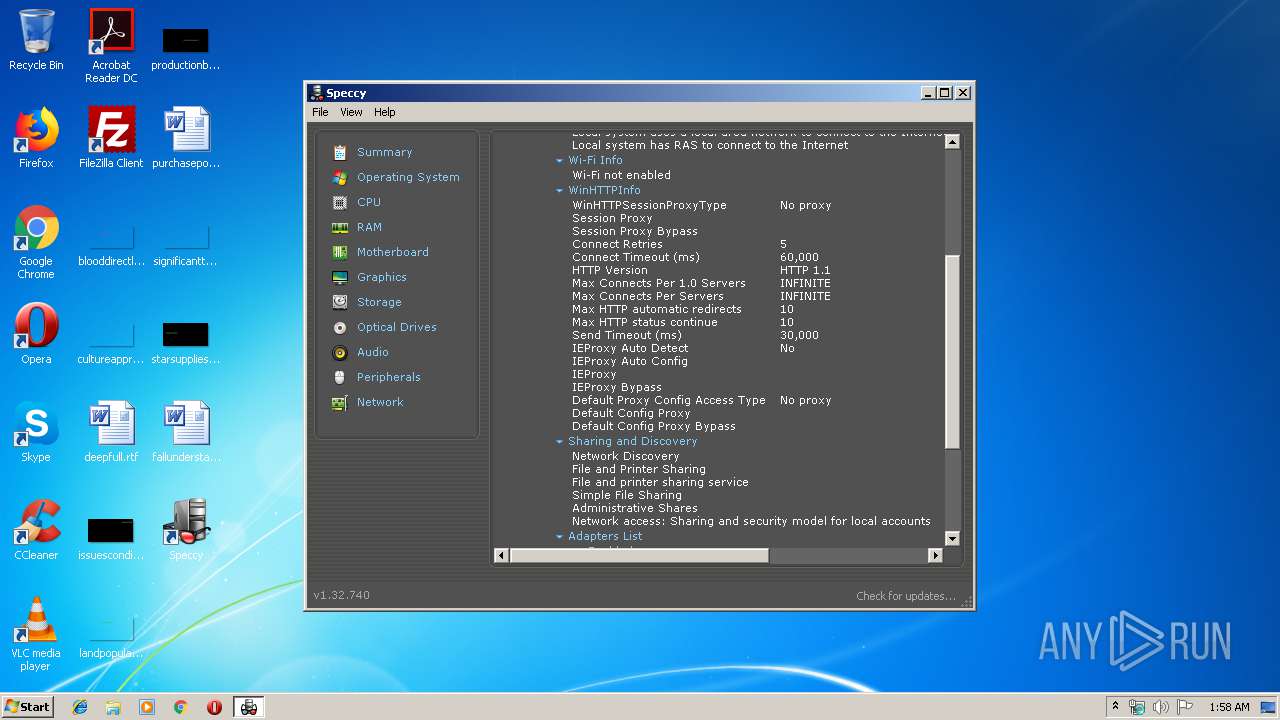
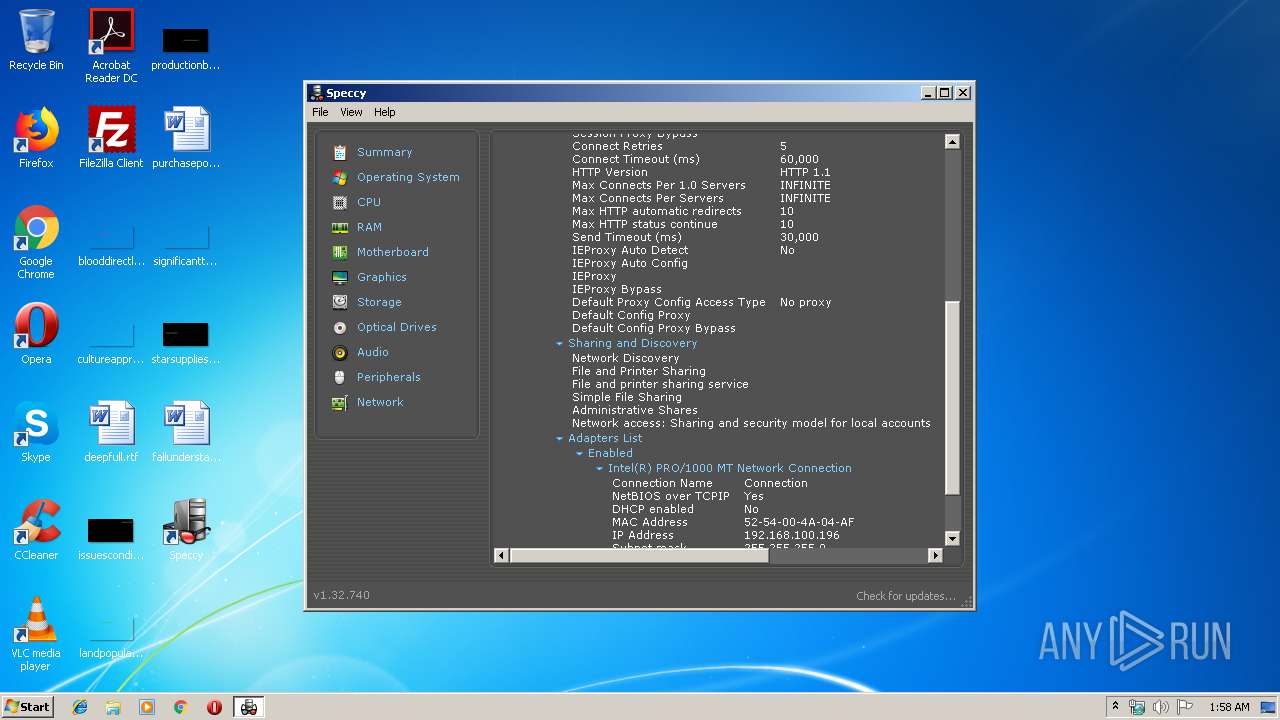
Reads internet explorer settings
- spsetup132.exe (PID: 3288)
- Speccy.exe (PID: 3204)
Reads the cookies of Google Chrome
- spsetup132.exe (PID: 3288)
Executable content was dropped or overwritten
- spsetup132.exe (PID: 3288)
- Speccy.exe (PID: 3204)
Starts application with an unusual extension
- spsetup132.exe (PID: 3288)
Creates a software uninstall entry
- spsetup132.exe (PID: 3288)
Creates files in the program directory
- spsetup132.exe (PID: 3288)
Modifies the open verb of a shell class
- spsetup132.exe (PID: 3288)
Low-level read access rights to disk partition
- Speccy.exe (PID: 3204)
Reads Internet Cache Settings
- Speccy.exe (PID: 3204)
Executes JAVA applets
- Speccy.exe (PID: 3204)
Checks supported languages
- Speccy.exe (PID: 3204)
INFO
No info indicators.
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable MS Visual C++ (generic) (67.4) |
|---|---|---|
| .dll | | | Win32 Dynamic Link Library (generic) (14.2) |
| .exe | | | Win32 Executable (generic) (9.7) |
| .exe | | | Generic Win/DOS Executable (4.3) |
| .exe | | | DOS Executable Generic (4.3) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2015:12:29 22:34:49+01:00 |
| PEType: | PE32 |
| LinkerVersion: | 9 |
| CodeSize: | 29696 |
| InitializedDataSize: | 441856 |
| UninitializedDataSize: | 16896 |
| EntryPoint: | 0x3a1c |
| OSVersion: | 5 |
| ImageVersion: | 6 |
| SubsystemVersion: | 5 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 1.32.26.740 |
| ProductVersionNumber: | 1.32.26.740 |
| FileFlagsMask: | 0x0000 |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | Neutral |
| CharacterSet: | Unicode |
| CompanyName: | Piriform Ltd |
| FileDescription: | Speccy Installer |
| FileVersion: | 1.32.26.740 |
| LegalCopyright: | Copyright © 2006-2018 Piriform Ltd |
| ProductName: | Speccy |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 29-Dec-2015 21:34:49 |
| Detected languages: |
|
| CompanyName: | Piriform Ltd |
| FileDescription: | Speccy Installer |
| FileVersion: | 1.32.26.740 |
| LegalCopyright: | Copyright © 2006-2018 Piriform Ltd |
| ProductName: | Speccy |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x000000D8 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 5 |
| Time date stamp: | 29-Dec-2015 21:34:49 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x00007250 | 0x00007400 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.46491 |
.rdata | 0x00009000 | 0x00002B38 | 0x00002C00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 4.41939 |
.data | 0x0000C000 | 0x00067EDC | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 1.89689 |
.ndata | 0x00074000 | 0x00311000 | 0x00000000 | IMAGE_SCN_CNT_UNINITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 0 |
.rsrc | 0x00385000 | 0x00006F90 | 0x00007000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 5.16623 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.21562 | 968 | UNKNOWN | English - United States | RT_MANIFEST |
2 | 5.62687 | 4264 | UNKNOWN | English - United States | RT_ICON |
3 | 4.7389 | 2216 | UNKNOWN | English - United States | RT_ICON |
4 | 3.91559 | 1384 | UNKNOWN | English - United States | RT_ICON |
5 | 5.97397 | 1128 | UNKNOWN | English - United States | RT_ICON |
6 | 3.89369 | 744 | UNKNOWN | English - United States | RT_ICON |
103 | 2.72033 | 90 | UNKNOWN | English - United States | RT_GROUP_ICON |
105 | 2.704 | 688 | UNKNOWN | English - United States | RT_DIALOG |
106 | 2.92897 | 344 | UNKNOWN | English - United States | RT_DIALOG |
111 | 2.92787 | 238 | UNKNOWN | English - United States | RT_DIALOG |
Imports
ADVAPI32.dll |
COMCTL32.dll |
GDI32.dll |
KERNEL32.dll |
SHELL32.dll |
USER32.dll |
ole32.dll |
Total processes
48
Monitored processes
7
Malicious processes
2
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 564 | "C:\Users\admin\AppData\Local\Temp\spsetup132.exe" | C:\Users\admin\AppData\Local\Temp\spsetup132.exe | — | explorer.exe | |||||||||||
User: admin Company: Piriform Ltd Integrity Level: MEDIUM Description: Speccy Installer Exit code: 3221226540 Version: 1.32.26.740 Modules
| |||||||||||||||
| 972 | "C:\Program Files\Java\jre1.8.0_92\bin\java" -version | C:\Program Files\Java\jre1.8.0_92\bin\java.exe | — | Speccy.exe | |||||||||||
User: admin Company: Oracle Corporation Integrity Level: HIGH Description: Java(TM) Platform SE binary Exit code: 0 Version: 8.0.920.14 Modules
| |||||||||||||||
| 2148 | ping -n 1 -w 5000 www.ccleaner.com | C:\Windows\system32\ping.exe | — | nsA560.tmp | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: TCP/IP Ping Command Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3204 | "C:\Program Files\Speccy\Speccy.exe" | C:\Program Files\Speccy\Speccy.exe | spsetup132.exe | ||||||||||||
User: admin Company: Piriform Ltd Integrity Level: HIGH Description: Speccy Exit code: 0 Version: 1.32.26.740 Modules
| |||||||||||||||
| 3288 | "C:\Users\admin\AppData\Local\Temp\spsetup132.exe" | C:\Users\admin\AppData\Local\Temp\spsetup132.exe | explorer.exe | ||||||||||||
User: admin Company: Piriform Ltd Integrity Level: HIGH Description: Speccy Installer Exit code: 0 Version: 1.32.26.740 Modules
| |||||||||||||||
| 3504 | /export /cfg "C:\Users\admin\AppData\Local\Temp\spc_se.txt" /quiet /areas SECURITYPOLICY | C:\Windows\system32\secedit.exe | — | Speccy.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Security Configuration Editor Command Tool Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3560 | "C:\Users\admin\AppData\Local\Temp\nsm7AE4.tmp\nsA560.tmp" ping -n 1 -w 5000 www.ccleaner.com | C:\Users\admin\AppData\Local\Temp\nsm7AE4.tmp\nsA560.tmp | — | spsetup132.exe | |||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
Total events
746
Read events
662
Write events
79
Delete events
5
Modification events
| (PID) Process: | (3288) spsetup132.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Google Toolbar |
| Operation: | write | Name: | test |
Value: test | |||
| (PID) Process: | (3288) spsetup132.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Google Toolbar |
| Operation: | delete value | Name: | test |
Value: test | |||
| (PID) Process: | (3288) spsetup132.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Google Toolbar |
| Operation: | delete key | Name: | |
Value: | |||
| (PID) Process: | (3288) spsetup132.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (3288) spsetup132.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (3288) spsetup132.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Extensible Cache\MSHist012019070820190709 |
| Operation: | write | Name: | CachePath |
Value: %USERPROFILE%\AppData\Local\Microsoft\Windows\History\History.IE5\MSHist012019070820190709 | |||
| (PID) Process: | (3288) spsetup132.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Extensible Cache\MSHist012019070820190709 |
| Operation: | write | Name: | CachePrefix |
Value: :2019070820190709: | |||
| (PID) Process: | (3288) spsetup132.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Extensible Cache\MSHist012019070820190709 |
| Operation: | write | Name: | CacheLimit |
Value: 8192 | |||
| (PID) Process: | (3288) spsetup132.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Extensible Cache\MSHist012019070820190709 |
| Operation: | write | Name: | CacheOptions |
Value: 11 | |||
| (PID) Process: | (3288) spsetup132.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Extensible Cache\MSHist012019070820190709 |
| Operation: | write | Name: | CacheRepair |
Value: 0 | |||
Executable files
82
Suspicious files
0
Text files
86
Unknown types
10
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3288 | spsetup132.exe | C:\Users\admin\AppData\Local\Temp\nsm7AE4.tmp\System.dll | executable | |
MD5:41A3C964232EDD2D7D5EDEA53E8245CD | SHA256:8B65FEC615C7B371C23F8F7F344B12DC5085E40A556F96DB318ED757494D62D5 | |||
| 3288 | spsetup132.exe | C:\Users\admin\AppData\Local\Temp\nsm7AE4.tmp\g\gcombo\ComboOffer_1030.html | html | |
MD5:74FB5C6592947C542FD036FE1D332AAF | SHA256:63B9E98CBD2CA35590318A0307145A5BC541CAC4E06EF93D6C0095E5692E5172 | |||
| 3288 | spsetup132.exe | C:\Users\admin\AppData\Local\Temp\nsm7AE4.tmp\g\gcombo\ComboOffer_1028.html | html | |
MD5:3C9D9A1818BEDE3E8E7FA99685D503DF | SHA256:5CDEAA26F12096E1AECDA8ACC42516341599AE4122D8E9C95D461CEB0A7E3010 | |||
| 3288 | spsetup132.exe | C:\Users\admin\AppData\Local\Temp\nsm7AE4.tmp\g\gcombo\ComboOffer_1034.html | html | |
MD5:E9FFD57DCDB8C4E634DCA2FBF9E19E70 | SHA256:70AD2C871E0A5A842A3089C62CB80F9DDCD7FA99FB016991CC30395B2A27786C | |||
| 3288 | spsetup132.exe | C:\Users\admin\AppData\Local\Temp\nsm7AE4.tmp\g\gcombo\ComboOffer_1040.html | html | |
MD5:D598BBD0693932B30F089181119861E0 | SHA256:DA1198DAA69C3803B0643D33024CB8A4B8A3B783BFED3226311535639B1D5BA5 | |||
| 3288 | spsetup132.exe | C:\Users\admin\AppData\Local\Temp\nsm7AE4.tmp\g\gcombo\ComboOffer_1038.html | html | |
MD5:7F6619F86770AE2DD1D8184E8CD95757 | SHA256:98975EA1660FD6C28BA74F5ED6B1491294ABBE13D11E54D21DB4FBEBE162E359 | |||
| 3288 | spsetup132.exe | C:\Users\admin\AppData\Local\Temp\nsm7AE4.tmp\g\gcombo\ComboOffer_1036.html | html | |
MD5:C69DA1C2761D758F92603D59F4ADDB28 | SHA256:4BD2DFB0D9D60F7B83942D8F43A45597BBBBA427359FE5497267BDC87B17C904 | |||
| 3288 | spsetup132.exe | C:\Users\admin\AppData\Local\Temp\nsm7AE4.tmp\g\gcombo\ComboOffer_1033.html | html | |
MD5:016F10E3840423FD75A776923AA3E57D | SHA256:C89B3683C75B641526524E2397D9BEB24F5BBD0D813D60CEB2B5B8896AE17659 | |||
| 3288 | spsetup132.exe | C:\Users\admin\AppData\Local\Temp\nsm7AE4.tmp\g\gcombo\ComboOffer_1037.html | html | |
MD5:9B97C8EB5DF75C96F82A4630935040CC | SHA256:603ADCA2B2A4BB0767F059F2C8F94BE036432BBA121DD750470B4FAD2B3907D1 | |||
| 3288 | spsetup132.exe | C:\Users\admin\AppData\Local\Temp\nsm7AE4.tmp\g\gcombo\ComboOffer_1041.html | html | |
MD5:7AB9531BD9E2038BE1A8497D49145424 | SHA256:A513D80F8FC3AC157F70948EBBC134190BAD6169CEC6DF2871FF8D21B9DC2F0A | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
2
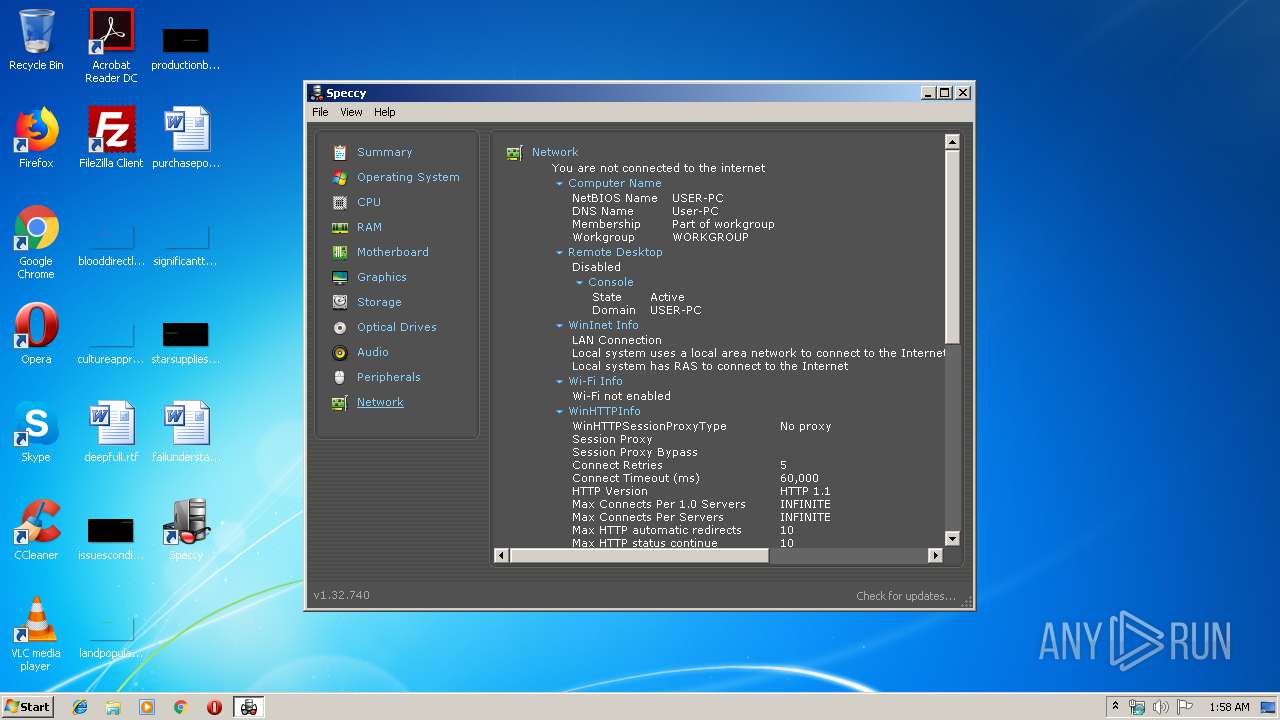
TCP/UDP connections
2
DNS requests
2
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3204 | Speccy.exe | GET | 200 | 151.101.2.202:80 | http://www.ccleaner.com/auto?p=sp&v=1.32.740&l=1033&o=6.1W3&lk=&mk=IJR6-W5SV-5KYR-QBZD-6BY4-RN5Z-WAV9-RVK2-VJCA | US | text | 22 b | whitelisted |
3288 | spsetup132.exe | GET | 200 | 151.101.0.64:80 | http://service.piriform.com/installcheck.aspx?p=4&v=1.32.740&vx=&l=1033&b=1&o=6.1W3&g=14&i=1&a=0&e=0&n=spsetup132.exe&id=003 | US | text | 4 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3288 | spsetup132.exe | 151.101.0.64:80 | service.piriform.com | Fastly | US | whitelisted |
— | — | 151.101.2.202:80 | www.ccleaner.com | Fastly | US | suspicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.ccleaner.com |
| whitelisted |
service.piriform.com |
| whitelisted |