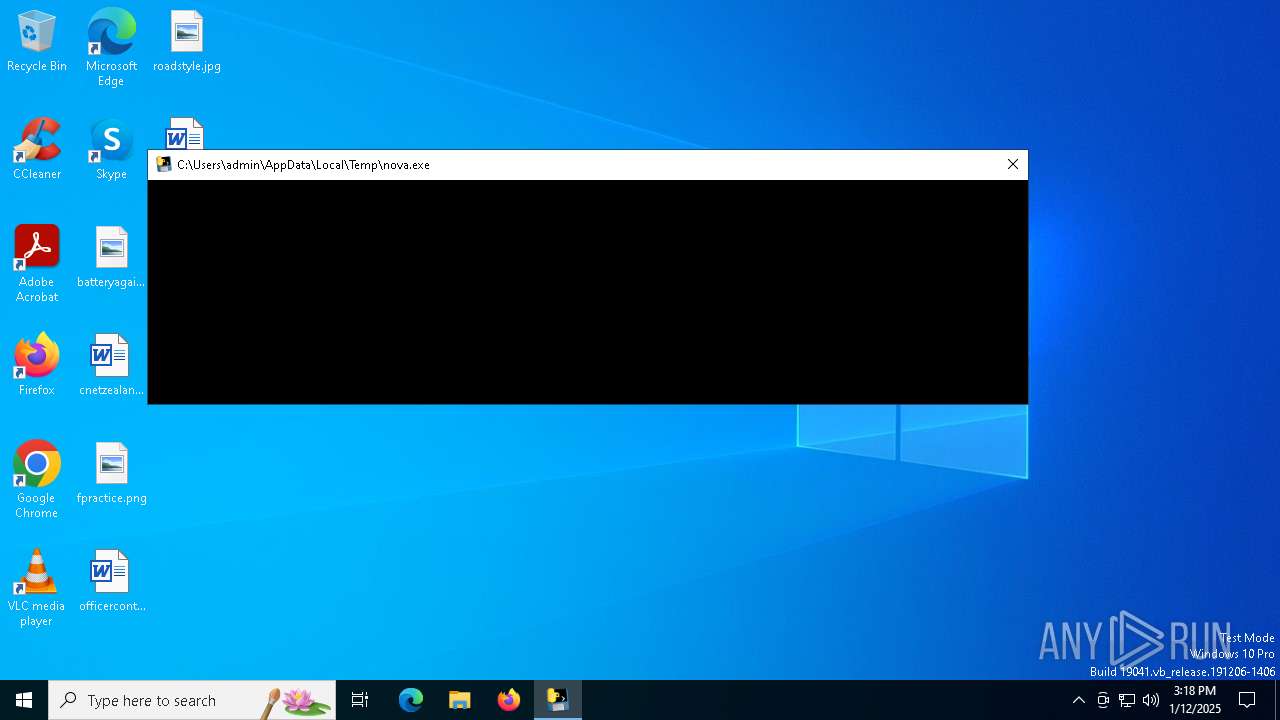
| File name: | nova.exe |
| Full analysis: | https://app.any.run/tasks/deaad7c8-d6d7-408d-922c-6595c044fe52 |
| Verdict: | Malicious activity |
| Analysis date: | January 12, 2025, 15:17:44 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/vnd.microsoft.portable-executable |
| File info: | PE32+ executable (console) x86-64, for MS Windows, 6 sections |
| MD5: | 74F5A4B133CB2E142F2572C8C5D53658 |
| SHA1: | D4AA0BB7ED8E58C38F602F831B88821014124A0C |
| SHA256: | 648F73D38C063FEEE68A6BF772D35FDFB45DFA3CAE7C8C6446FCA1C233B7D7EC |
| SSDEEP: | 98304:1IyDygzmSyuJtP8YJbebWn7Cv1aMh3pmV4CsFtHfktEzafhOsE+XZ0PEesQHc//W:FfrmXzJqsOkmn1mGj |
MALICIOUS
No malicious indicators.SUSPICIOUS
The process drops C-runtime libraries
- nova.exe (PID: 6536)
Process drops python dynamic module
- nova.exe (PID: 6536)
Process drops legitimate windows executable
- nova.exe (PID: 6536)
Executable content was dropped or overwritten
- nova.exe (PID: 6536)
Reads security settings of Internet Explorer
- GameBar.exe (PID: 6652)
Application launched itself
- nova.exe (PID: 6536)
Starts CMD.EXE for commands execution
- nova.exe (PID: 6904)
Loads Python modules
- nova.exe (PID: 6904)
Starts POWERSHELL.EXE for commands execution
- nova.exe (PID: 6904)
Potential Corporate Privacy Violation
- nova.exe (PID: 6904)
INFO
Create files in a temporary directory
- nova.exe (PID: 6536)
Reads the computer name
- nova.exe (PID: 6536)
- GameBar.exe (PID: 6652)
- nova.exe (PID: 6904)
The sample compiled with english language support
- nova.exe (PID: 6536)
Checks supported languages
- nova.exe (PID: 6536)
- GameBar.exe (PID: 6652)
- nova.exe (PID: 6904)
- mode.com (PID: 6972)
Starts MODE.COM to configure console settings
- mode.com (PID: 6972)
Checks proxy server information
- nova.exe (PID: 6904)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | InstallShield setup (57.6) |
|---|---|---|
| .exe | | | Win64 Executable (generic) (36.9) |
| .exe | | | Generic Win/DOS Executable (2.6) |
| .exe | | | DOS Executable Generic (2.6) |
EXIF
EXE
| MachineType: | AMD AMD64 |
|---|---|
| TimeStamp: | 2025:01:08 13:34:08+00:00 |
| ImageFileCharacteristics: | Executable, Large address aware |
| PEType: | PE32+ |
| LinkerVersion: | 14.41 |
| CodeSize: | 176640 |
| InitializedDataSize: | 152576 |
| UninitializedDataSize: | - |
| EntryPoint: | 0xc320 |
| OSVersion: | 6 |
| ImageVersion: | - |
| SubsystemVersion: | 6 |
| Subsystem: | Windows command line |
Total processes
128
Monitored processes
7
Malicious processes
1
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 6536 | "C:\Users\admin\AppData\Local\Temp\nova.exe" | C:\Users\admin\AppData\Local\Temp\nova.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 1 Modules
| |||||||||||||||
| 6544 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | nova.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6652 | "C:\Program Files\WindowsApps\Microsoft.XboxGamingOverlay_2.34.28001.0_x64__8wekyb3d8bbwe\GameBar.exe" -ServerName:App.AppXbdkk0yrkwpcgeaem8zk81k8py1eaahny.mca | C:\Program Files\WindowsApps\Microsoft.XboxGamingOverlay_2.34.28001.0_x64__8wekyb3d8bbwe\GameBar.exe | — | svchost.exe | |||||||||||
User: admin Integrity Level: MEDIUM Modules
| |||||||||||||||
| 6904 | "C:\Users\admin\AppData\Local\Temp\nova.exe" | C:\Users\admin\AppData\Local\Temp\nova.exe | nova.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 1 Modules
| |||||||||||||||
| 6956 | C:\WINDOWS\system32\cmd.exe /c mode con: cols=110 lines=14 | C:\Windows\System32\cmd.exe | — | nova.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6972 | mode con: cols=110 lines=14 | C:\Windows\System32\mode.com | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: DOS Device MODE Utility Exit code: 0 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 7000 | powershell -Command "(Get-WmiObject -Class Win32_ComputerSystemProduct).UUID" | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | nova.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
5 210
Read events
5 203
Write events
7
Delete events
0
Modification events
| (PID) Process: | (6652) GameBar.exe | Key: | \REGISTRY\A\{03aabe00-218b-7803-1d6f-06fc6605c191}\LocalState |
| Operation: | write | Name: | InstalledVersionMajor |
Value: 0200BDA22F270565DB01 | |||
| (PID) Process: | (6652) GameBar.exe | Key: | \REGISTRY\A\{03aabe00-218b-7803-1d6f-06fc6605c191}\LocalState |
| Operation: | write | Name: | InstalledVersionMinor |
Value: 220060F331270565DB01 | |||
| (PID) Process: | (6652) GameBar.exe | Key: | \REGISTRY\A\{03aabe00-218b-7803-1d6f-06fc6605c191}\LocalState |
| Operation: | write | Name: | InstalledVersionBuild |
Value: 616D60F331270565DB01 | |||
| (PID) Process: | (6652) GameBar.exe | Key: | \REGISTRY\A\{03aabe00-218b-7803-1d6f-06fc6605c191}\LocalState |
| Operation: | write | Name: | InstalledVersionRevision |
Value: 000060F331270565DB01 | |||
| (PID) Process: | (6652) GameBar.exe | Key: | \REGISTRY\A\{03aabe00-218b-7803-1d6f-06fc6605c191}\LocalState |
| Operation: | write | Name: | PreviousAppTerminationFromSuspended |
Value: 0060F331270565DB01 | |||
| (PID) Process: | (6652) GameBar.exe | Key: | \REGISTRY\A\{03aabe00-218b-7803-1d6f-06fc6605c191}\LocalState |
| Operation: | write | Name: | CurrentDisplayMonitor |
Value: 670061006D006500000068BB36270565DB01 | |||
| (PID) Process: | (6652) GameBar.exe | Key: | \REGISTRY\A\{03aabe00-218b-7803-1d6f-06fc6605c191}\LocalState |
| Operation: | write | Name: | StartupTipIndex |
Value: 0100000000000000A31245270565DB01 | |||
Executable files
59
Suspicious files
2
Text files
10
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 6536 | nova.exe | C:\Users\admin\AppData\Local\Temp\_MEI65362\_ctypes.pyd | executable | |
MD5:C8AFA1EBB28828E1115C110313D2A810 | SHA256:8978972CF341CCD0EDF8435D63909A739DF7EF29EC7DD57ED5CAB64B342891F0 | |||
| 6536 | nova.exe | C:\Users\admin\AppData\Local\Temp\_MEI65362\_queue.pyd | executable | |
MD5:7D91DD8E5F1DBC3058EA399F5F31C1E6 | SHA256:76BBA42B1392DC57A867AEF385B990FA302A4F1DCF453705AC119C9C98A36E8D | |||
| 6536 | nova.exe | C:\Users\admin\AppData\Local\Temp\_MEI65362\_bz2.pyd | executable | |
MD5:DD26ED92888DE9C57660A7AD631BB916 | SHA256:324268786921EC940CBD4B5E2F71DAFD08E578A12E373A715658527E5B211697 | |||
| 6536 | nova.exe | C:\Users\admin\AppData\Local\Temp\_MEI65362\_decimal.pyd | executable | |
MD5:CEA3B419C7CA87140A157629C6DBD299 | SHA256:95B9850E6FB335B235589DD1348E007507C6B28E332C9ABB111F2A0035C358E5 | |||
| 6536 | nova.exe | C:\Users\admin\AppData\Local\Temp\_MEI65362\api-ms-win-core-datetime-l1-1-0.dll | executable | |
MD5:CFE0C1DFDE224EA5FED9BD5FF778A6E0 | SHA256:0D0F80CBF476AF5B1C9FD3775E086ED0DFDB510CD0CC208EC1CCB04572396E3E | |||
| 6536 | nova.exe | C:\Users\admin\AppData\Local\Temp\_MEI65362\_cffi_backend.cp312-win_amd64.pyd | executable | |
MD5:0572B13646141D0B1A5718E35549577C | SHA256:D8A76D1E31BBD62A482DEA9115FC1A109CB39AF4CF6D1323409175F3C93113A7 | |||
| 6536 | nova.exe | C:\Users\admin\AppData\Local\Temp\_MEI65362\_socket.pyd | executable | |
MD5:E43AED7D6A8BCD9DDFC59C2D1A2C4B02 | SHA256:2C2A6A6BA360E38F0C2B5A53B4626F833A3111844D95615EBF35BE0E76B1EF7A | |||
| 6536 | nova.exe | C:\Users\admin\AppData\Local\Temp\_MEI65362\api-ms-win-core-debug-l1-1-0.dll | executable | |
MD5:33BBECE432F8DA57F17BF2E396EBAA58 | SHA256:7CF0944901F7F7E0D0B9AD62753FC2FE380461B1CCE8CDC7E9C9867C980E3B0E | |||
| 6536 | nova.exe | C:\Users\admin\AppData\Local\Temp\_MEI65362\_ssl.pyd | executable | |
MD5:6A2B0F8F50B47D05F96DEFF7883C1270 | SHA256:68DAD60FF6FB36C88EF1C47D1855517BFE8DE0F5DDEA0F630B65B622A645D53A | |||
| 6536 | nova.exe | C:\Users\admin\AppData\Local\Temp\_MEI65362\api-ms-win-core-errorhandling-l1-1-0.dll | executable | |
MD5:EB0978A9213E7F6FDD63B2967F02D999 | SHA256:AB25A1FE836FC68BCB199F1FE565C27D26AF0C390A38DA158E0D8815EFE1103E | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
5
TCP/UDP connections
19
DNS requests
9
Threats
1
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
— | — | GET | 200 | 23.216.77.28:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
6904 | nova.exe | GET | 200 | 92.60.224.54:80 | http://api.novaclient.lol/auth.txt | unknown | — | — | unknown |
— | — | GET | 200 | 23.37.237.227:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
5064 | SearchApp.exe | GET | 200 | 184.30.131.245:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAI5PUjXAkJafLQcAAsO18o%3D | unknown | — | — | whitelisted |
1176 | svchost.exe | GET | 200 | 184.30.131.245:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4712 | MoUsoCoreWorker.exe | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
— | — | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
— | — | 23.216.77.28:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
— | — | 23.37.237.227:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
6904 | nova.exe | 92.60.224.54:80 | api.novaclient.lol | TELEKOM SRBIJA a.d. | RS | unknown |
5064 | SearchApp.exe | 2.16.204.161:443 | www.bing.com | Akamai International B.V. | DE | whitelisted |
1176 | svchost.exe | 20.190.160.14:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
5064 | SearchApp.exe | 184.30.131.245:80 | ocsp.digicert.com | AKAMAI-AS | US | whitelisted |
1176 | svchost.exe | 184.30.131.245:80 | ocsp.digicert.com | AKAMAI-AS | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
api.novaclient.lol |
| unknown |
www.bing.com |
| whitelisted |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
go.microsoft.com |
| whitelisted |
Threats
1 ETPRO signatures available at the full report