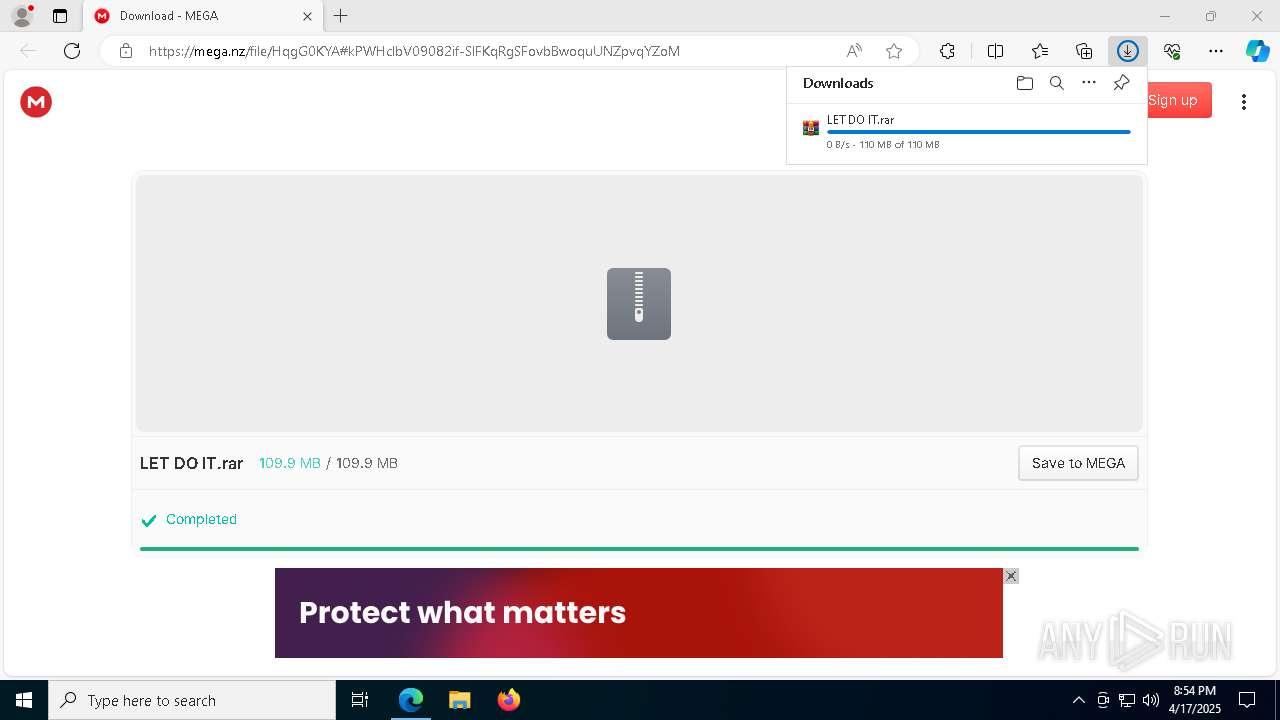
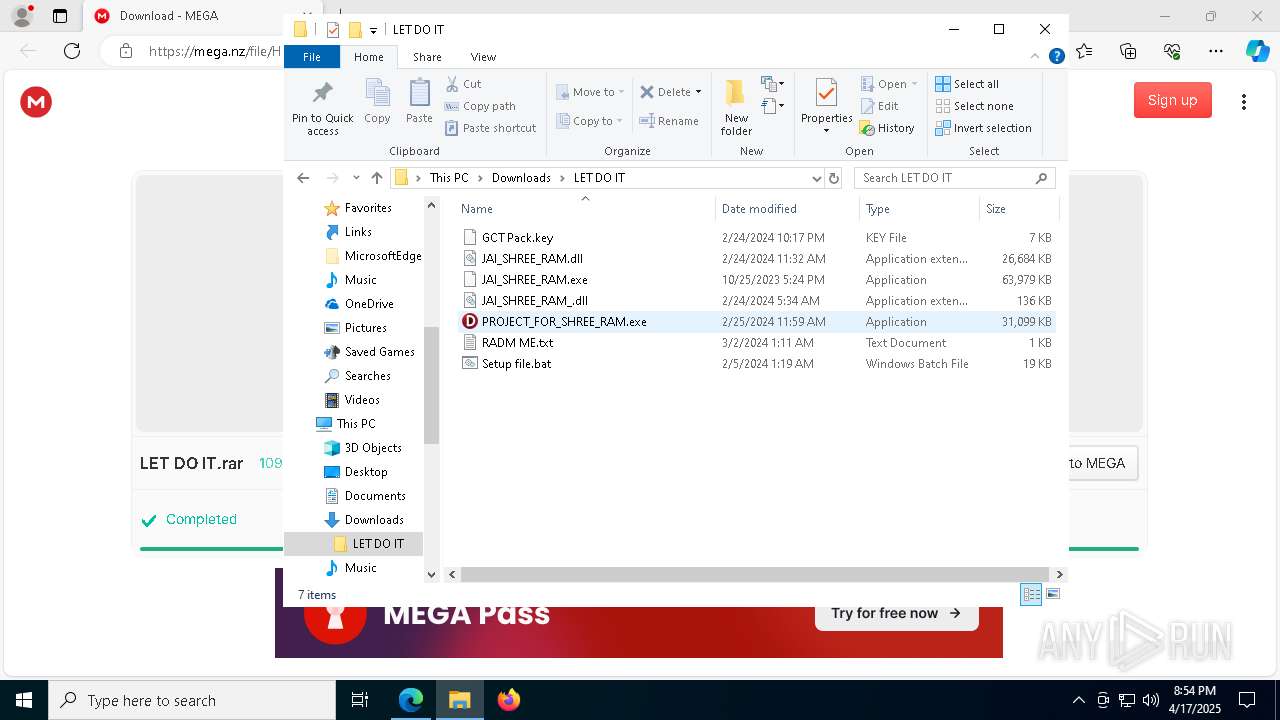
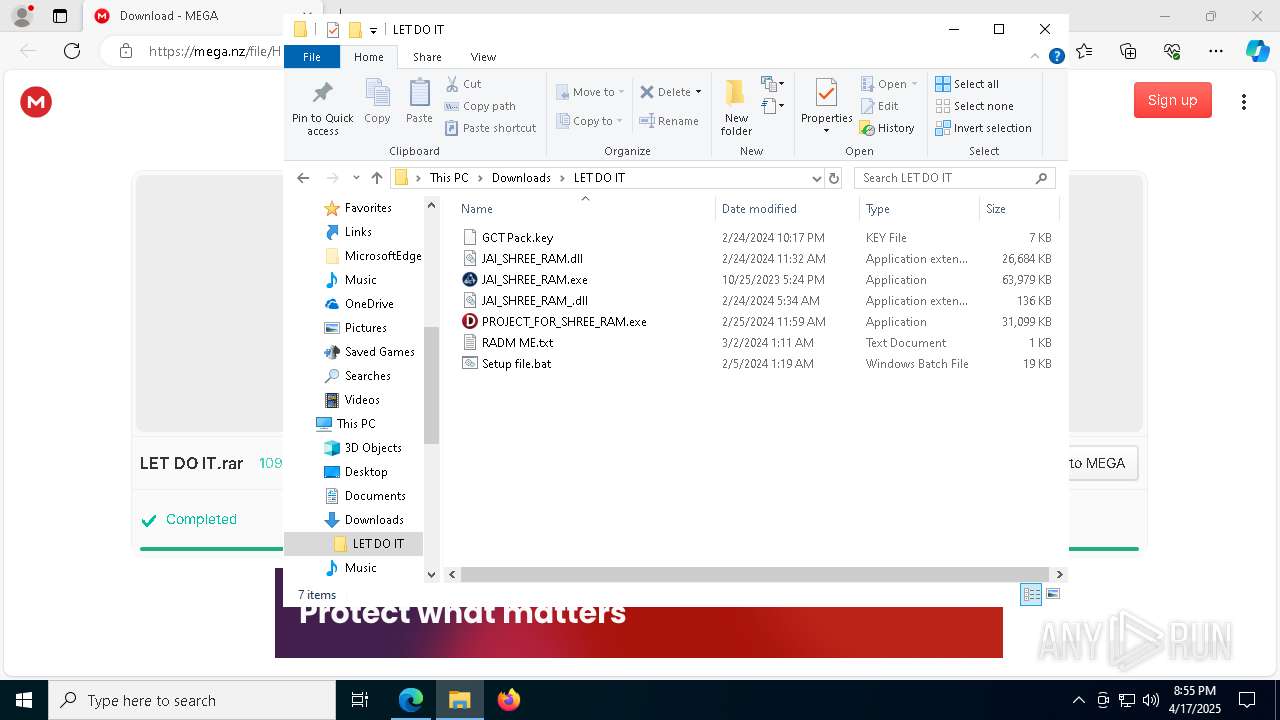
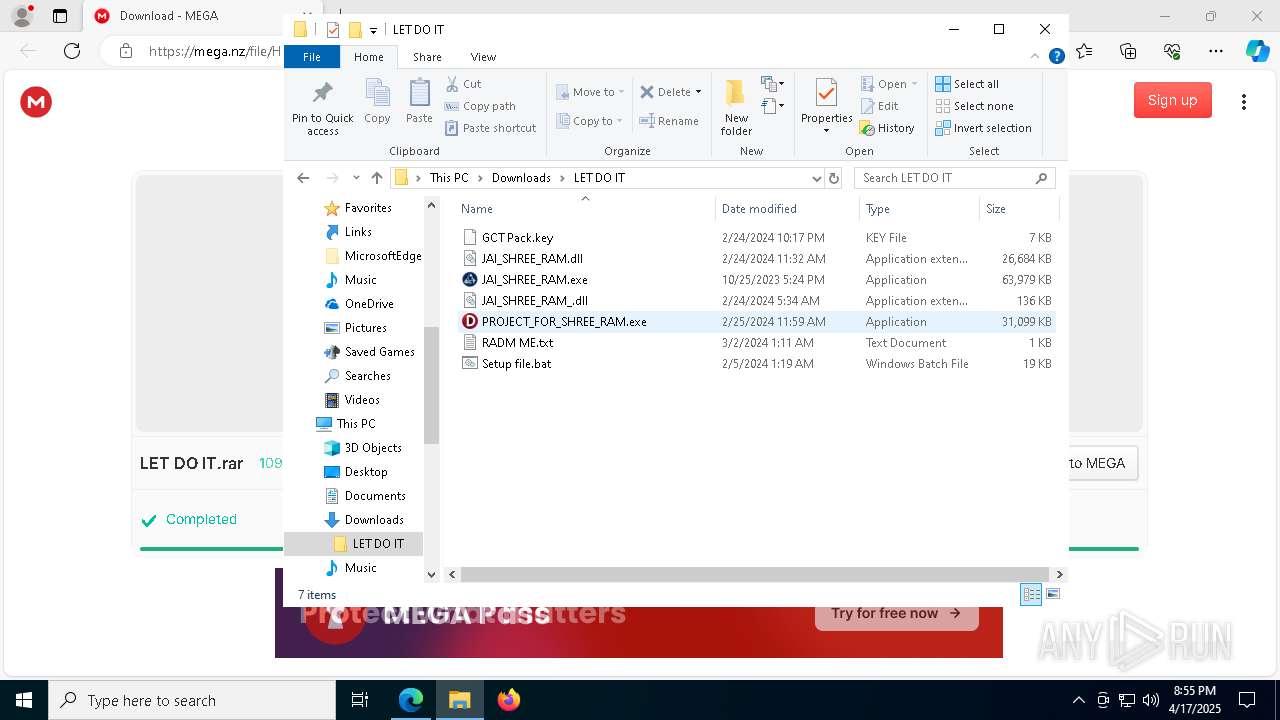
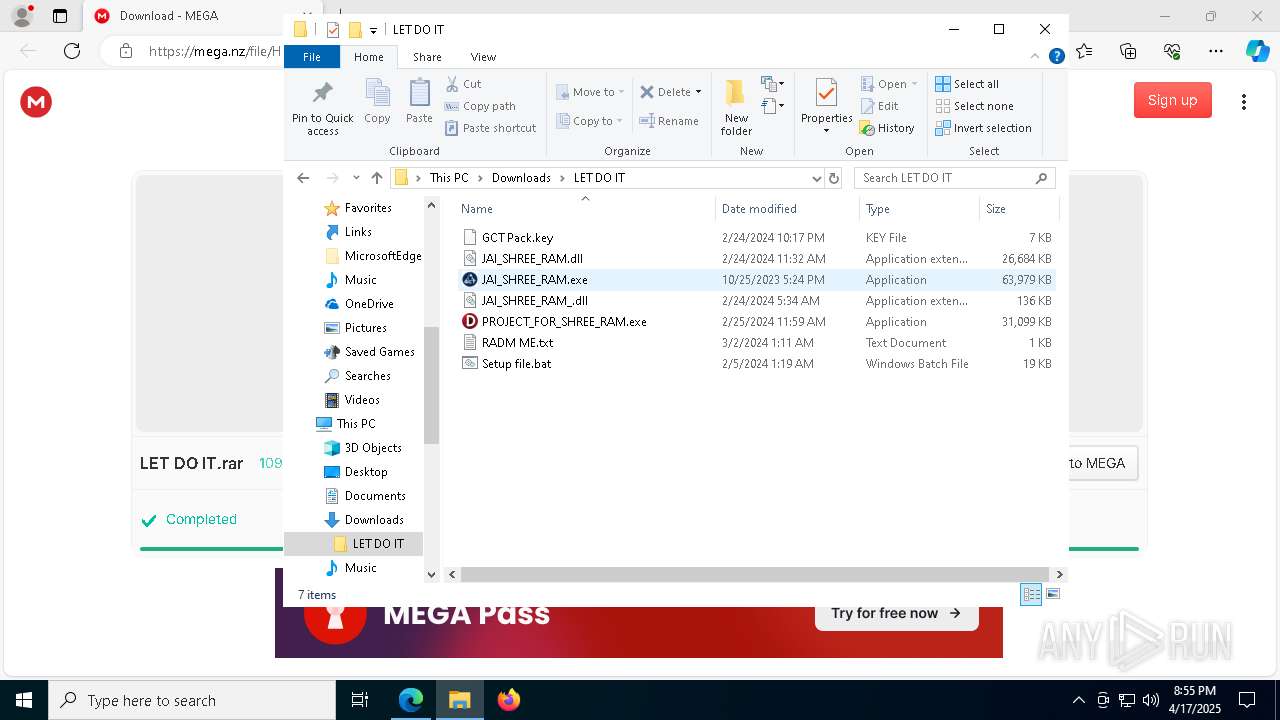
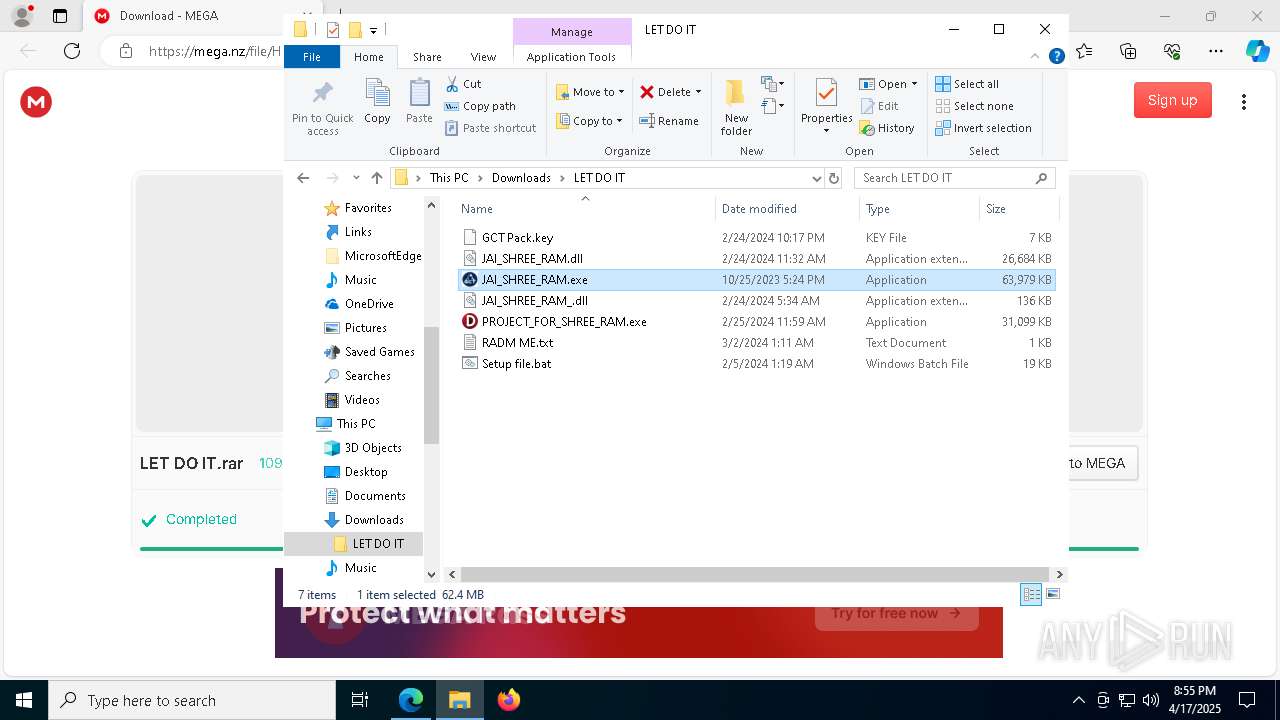
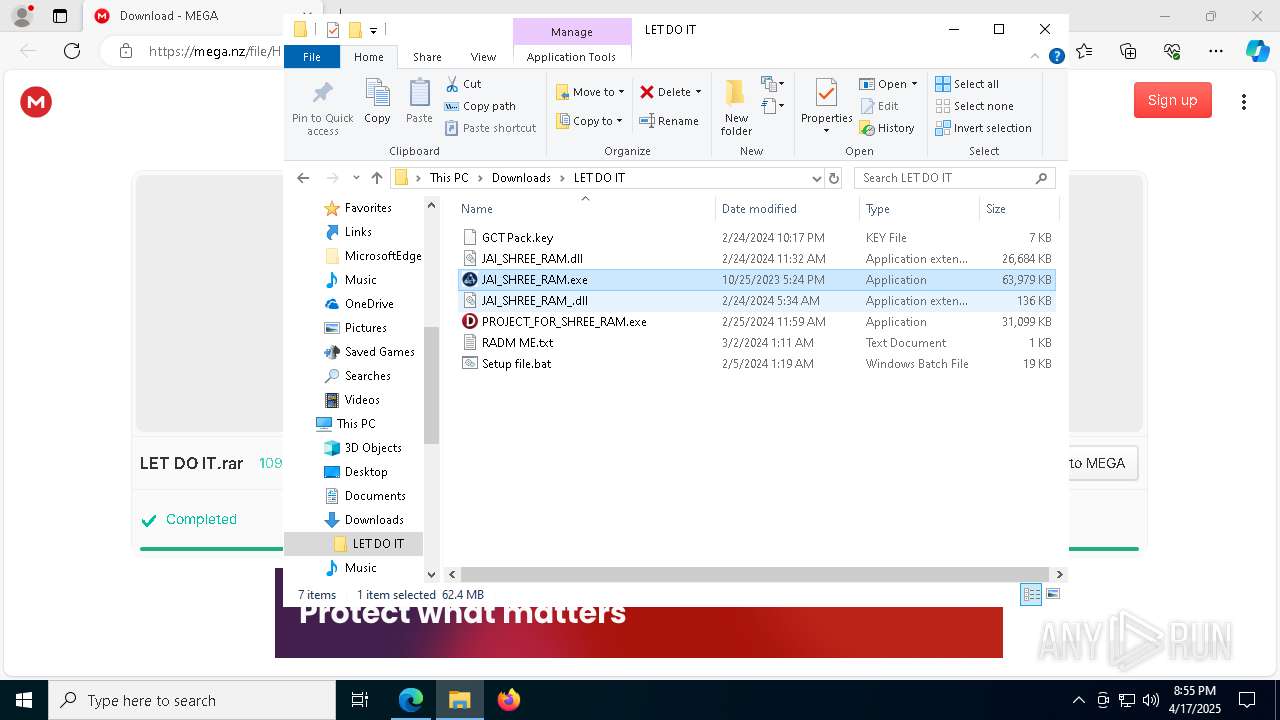
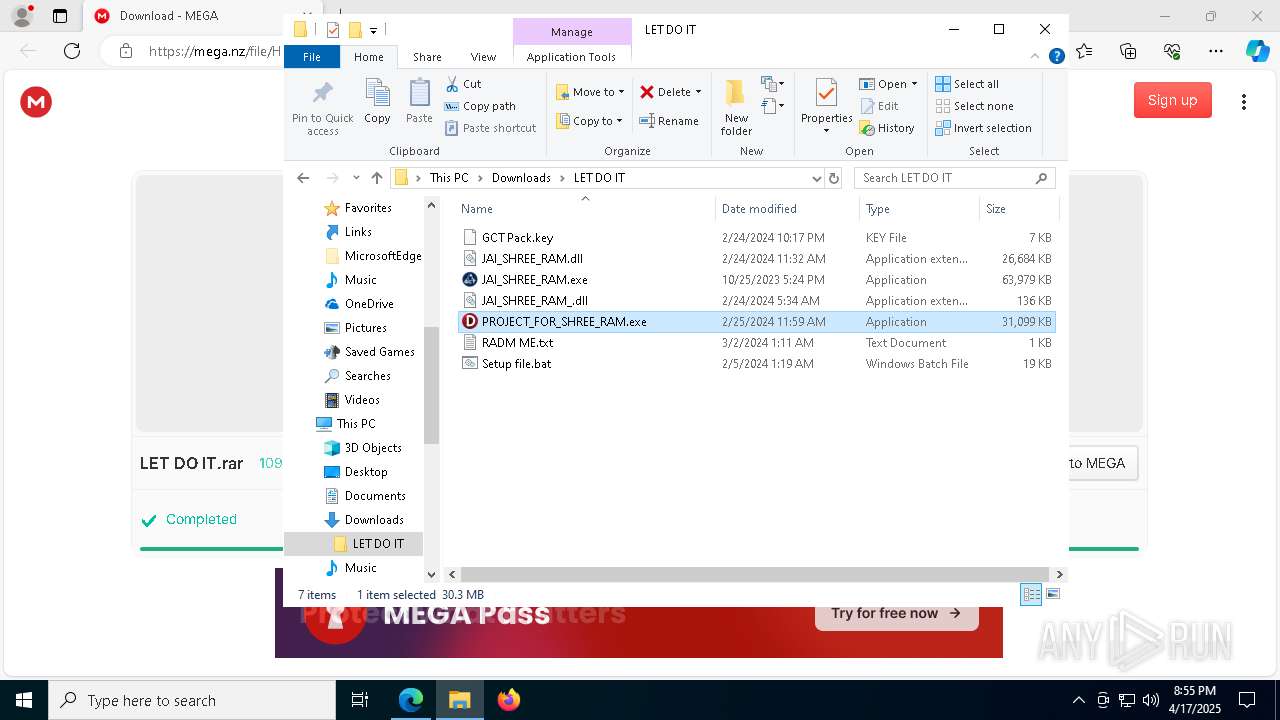
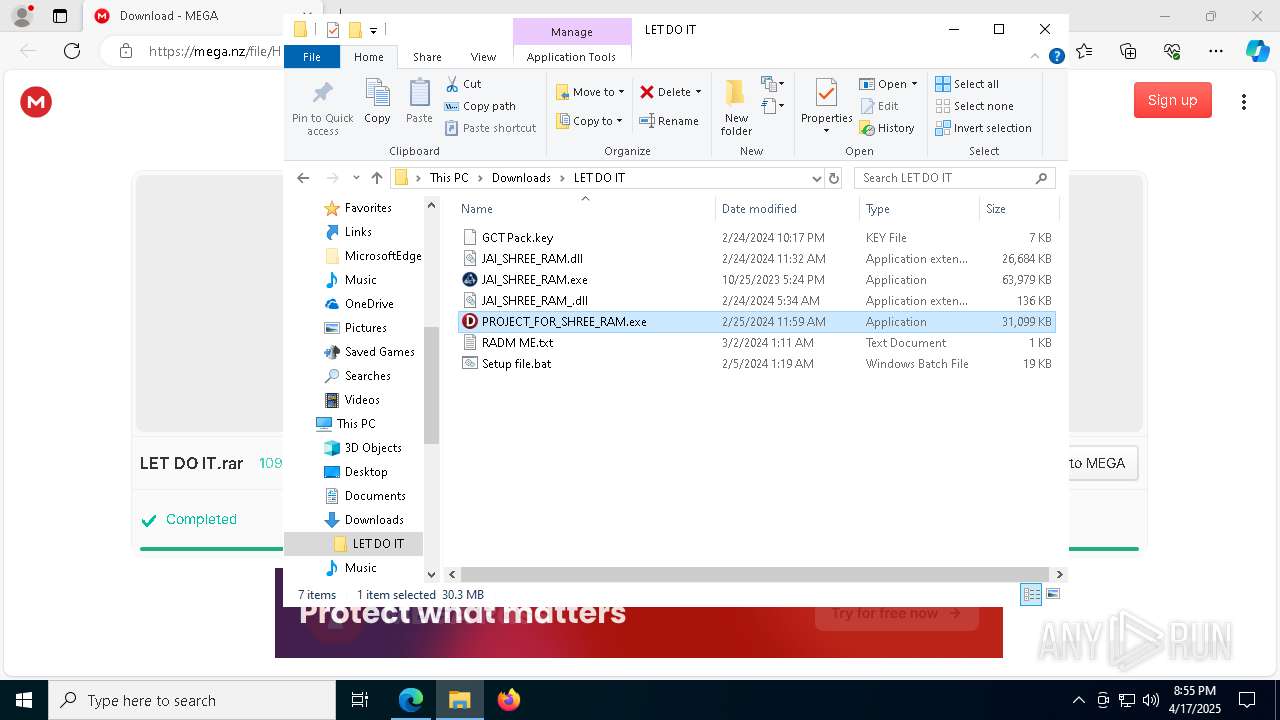
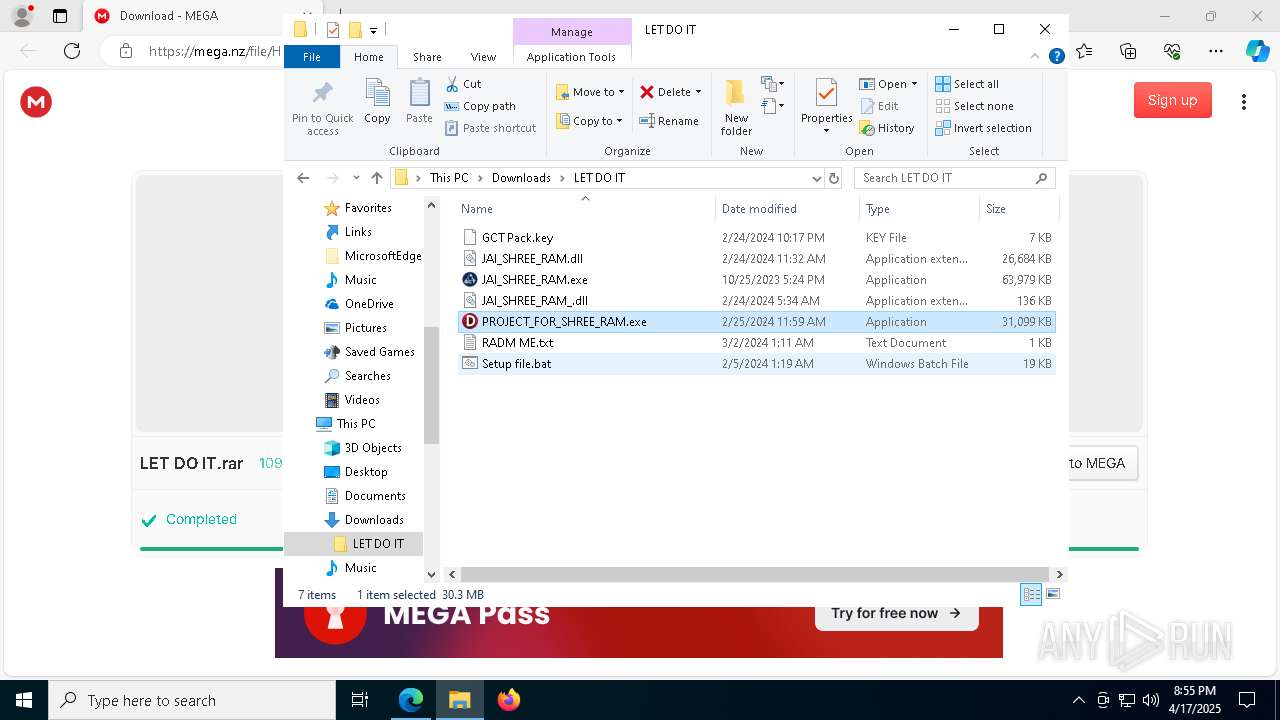
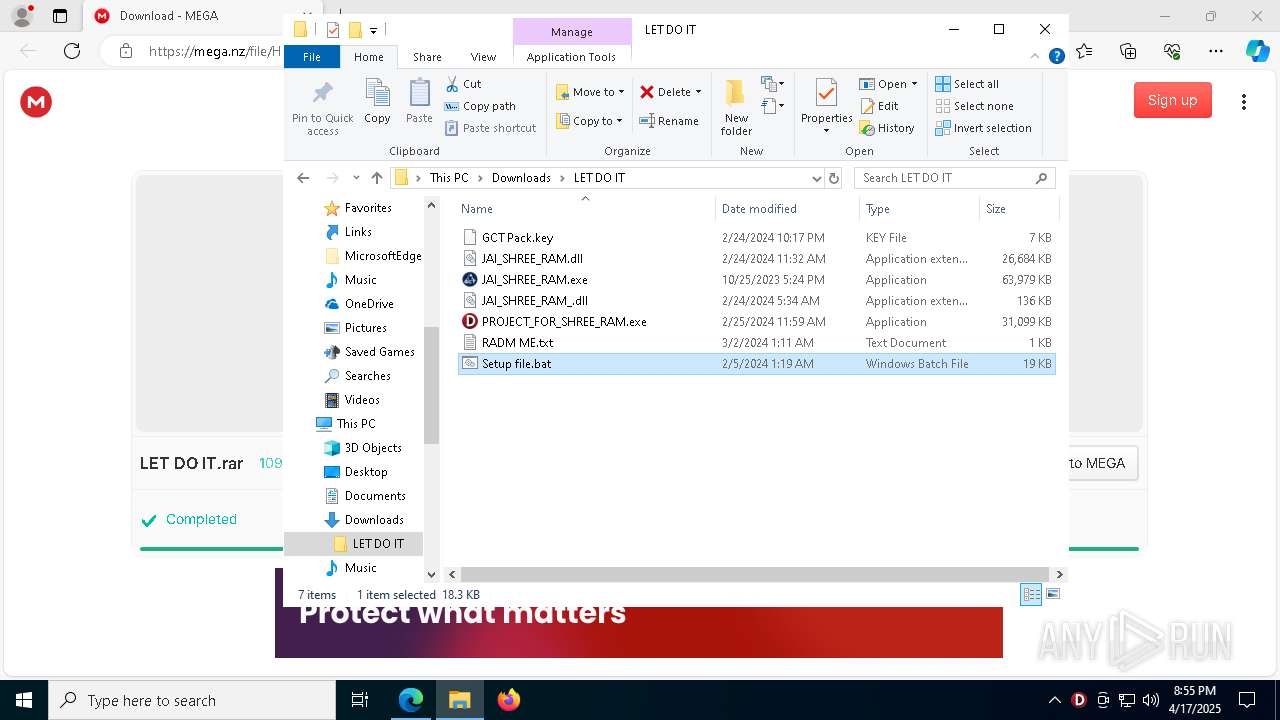
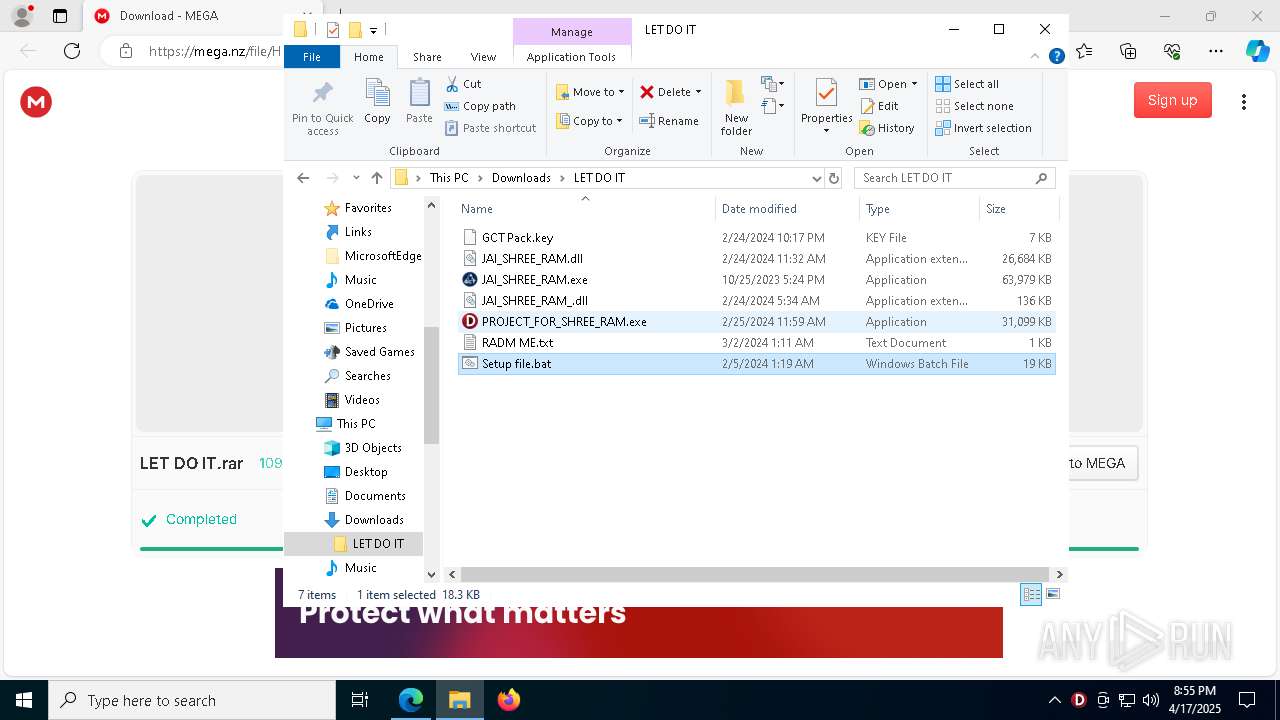
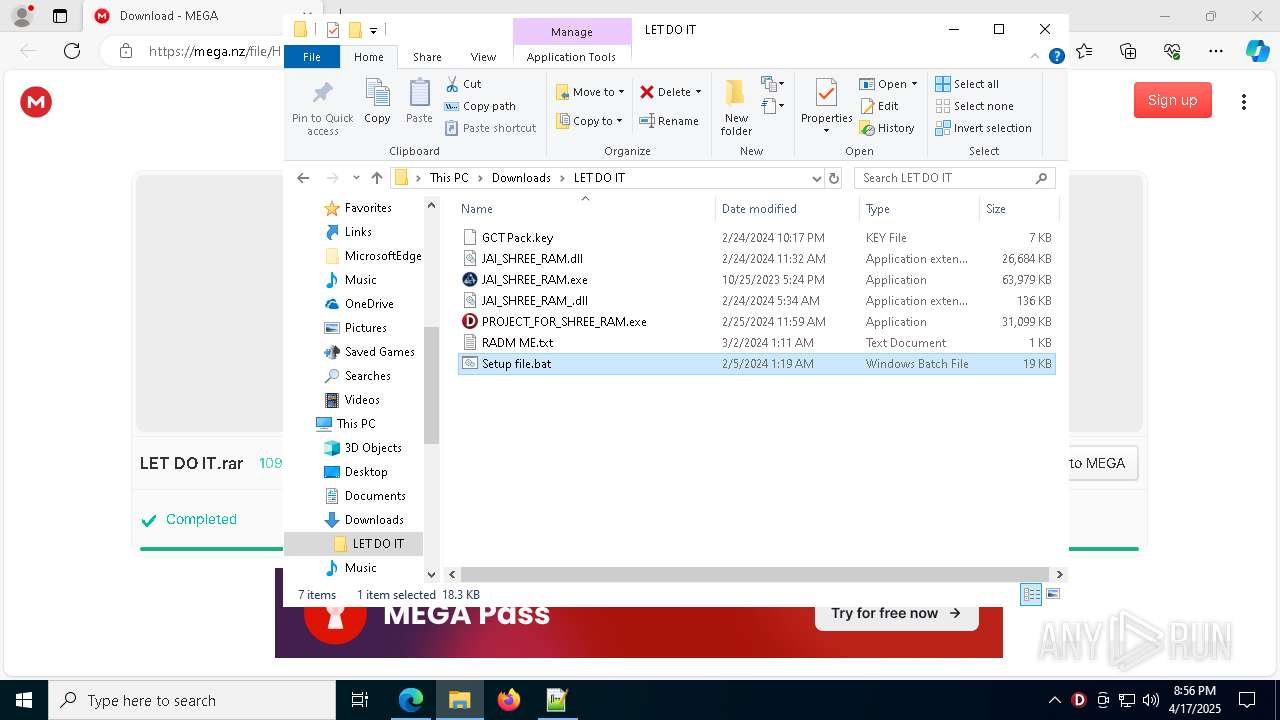
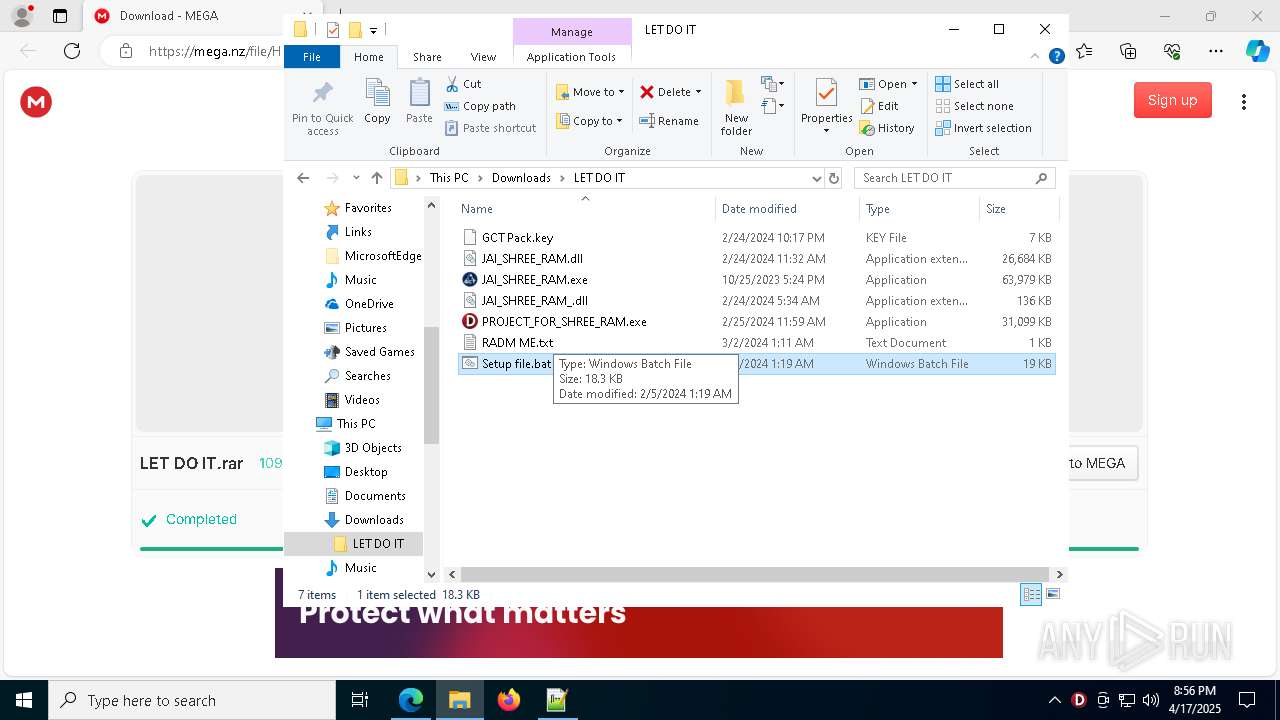
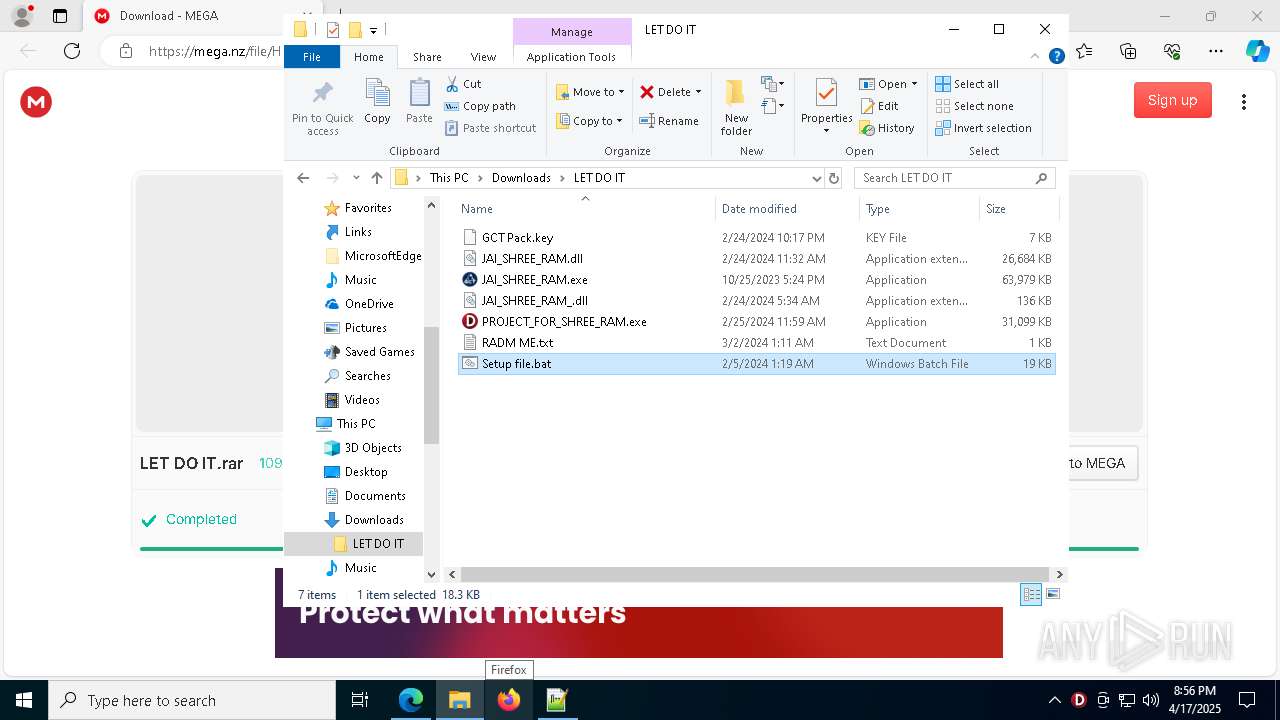
| URL: | https://mega.nz/file/HqgG0KYA#kPWHclbV09082if-SlFKqRgSFovbBwoquUNZpvqYZoM |
| Full analysis: | https://app.any.run/tasks/e087f50d-290a-48cf-8b74-974e37bab3ac |
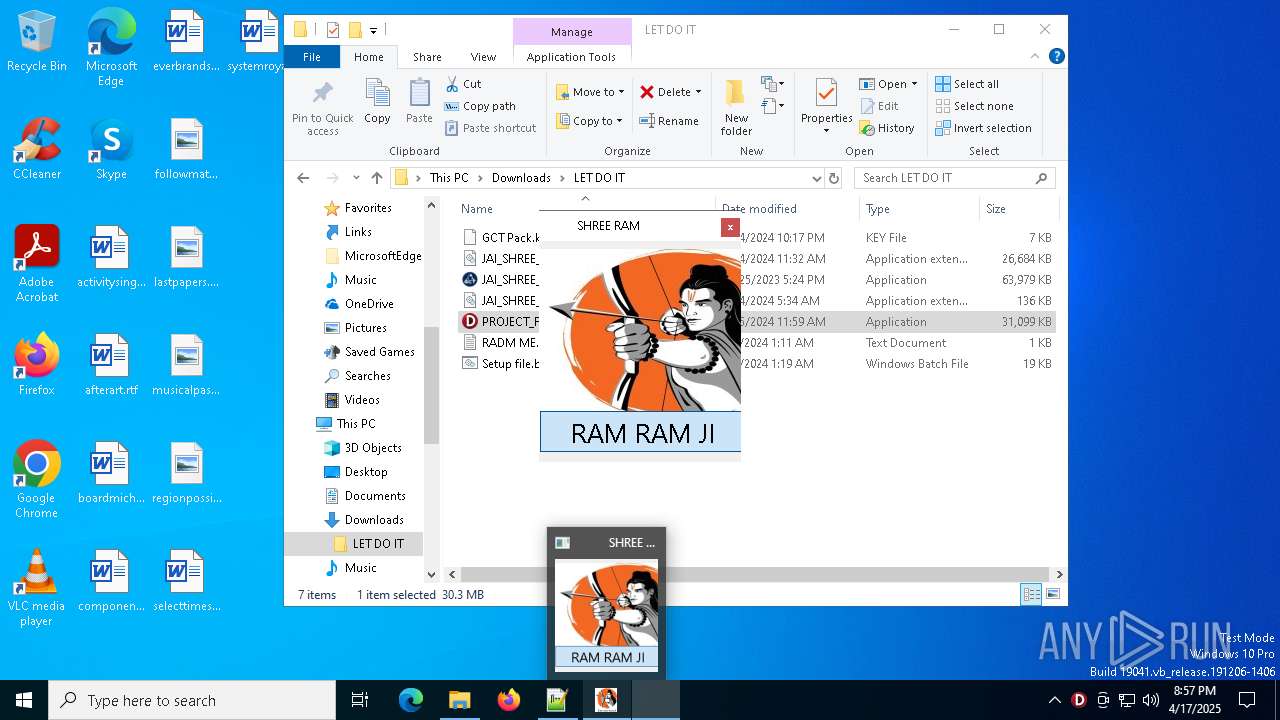
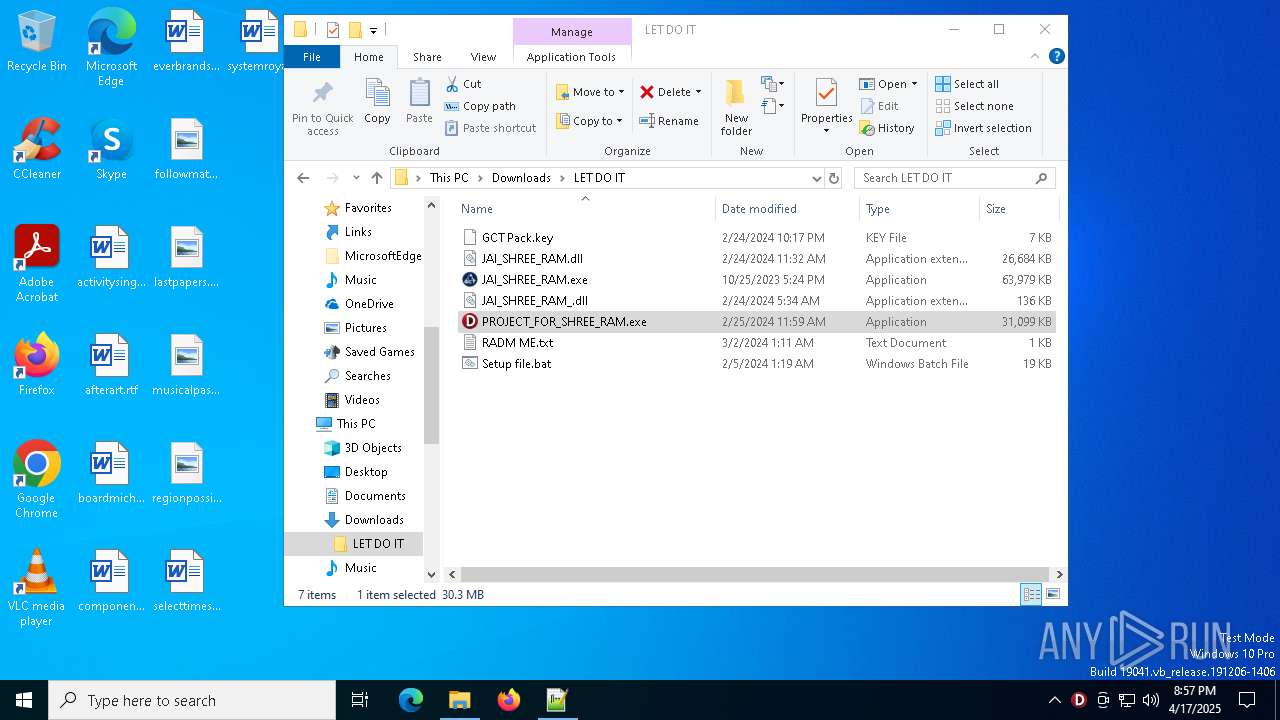
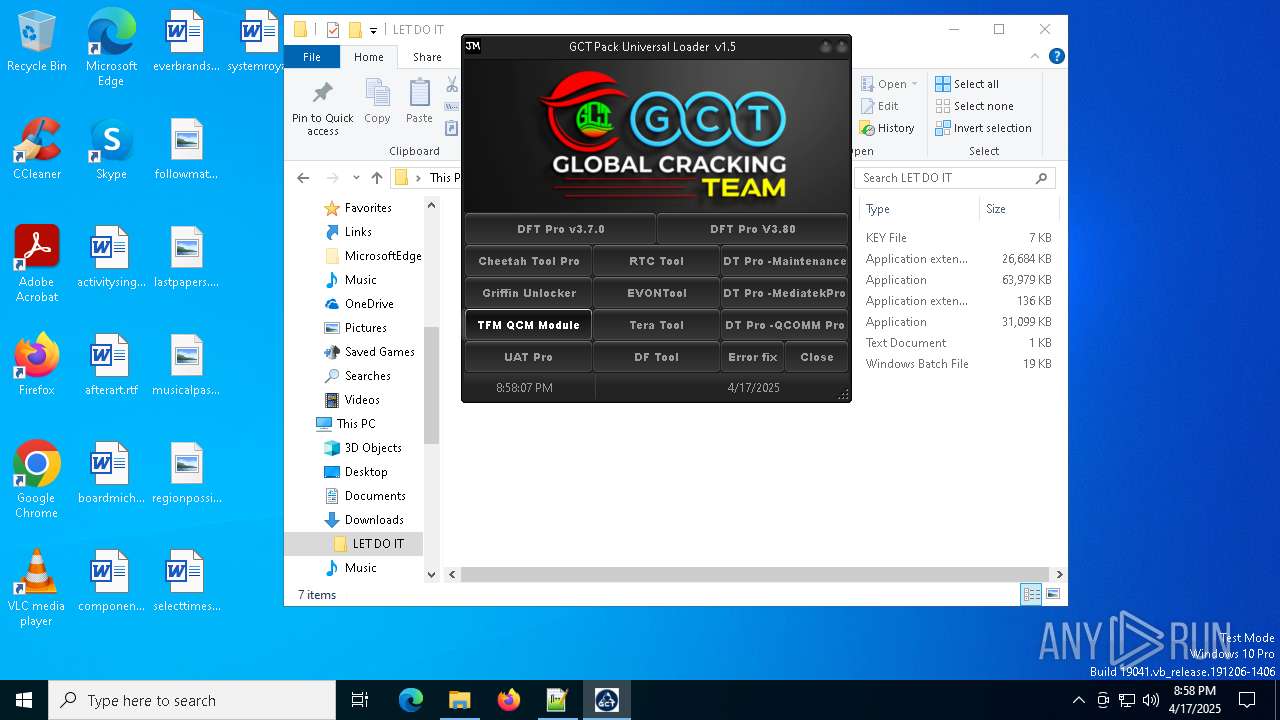
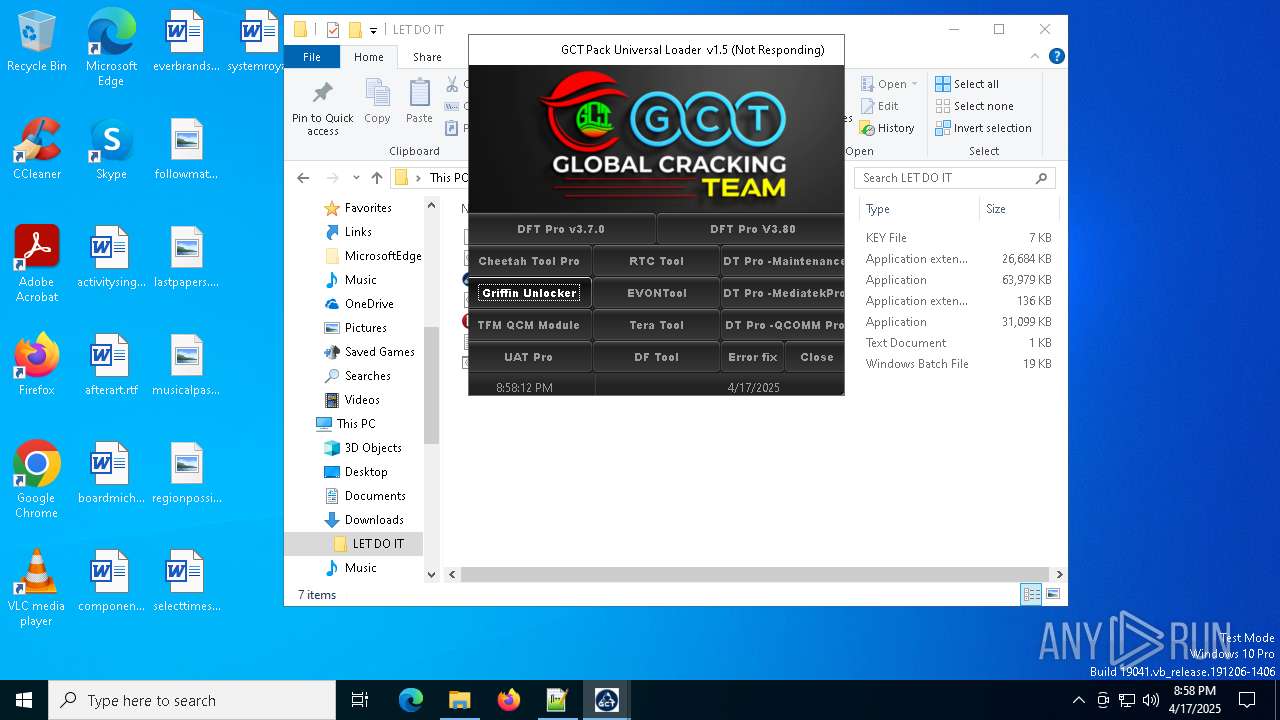
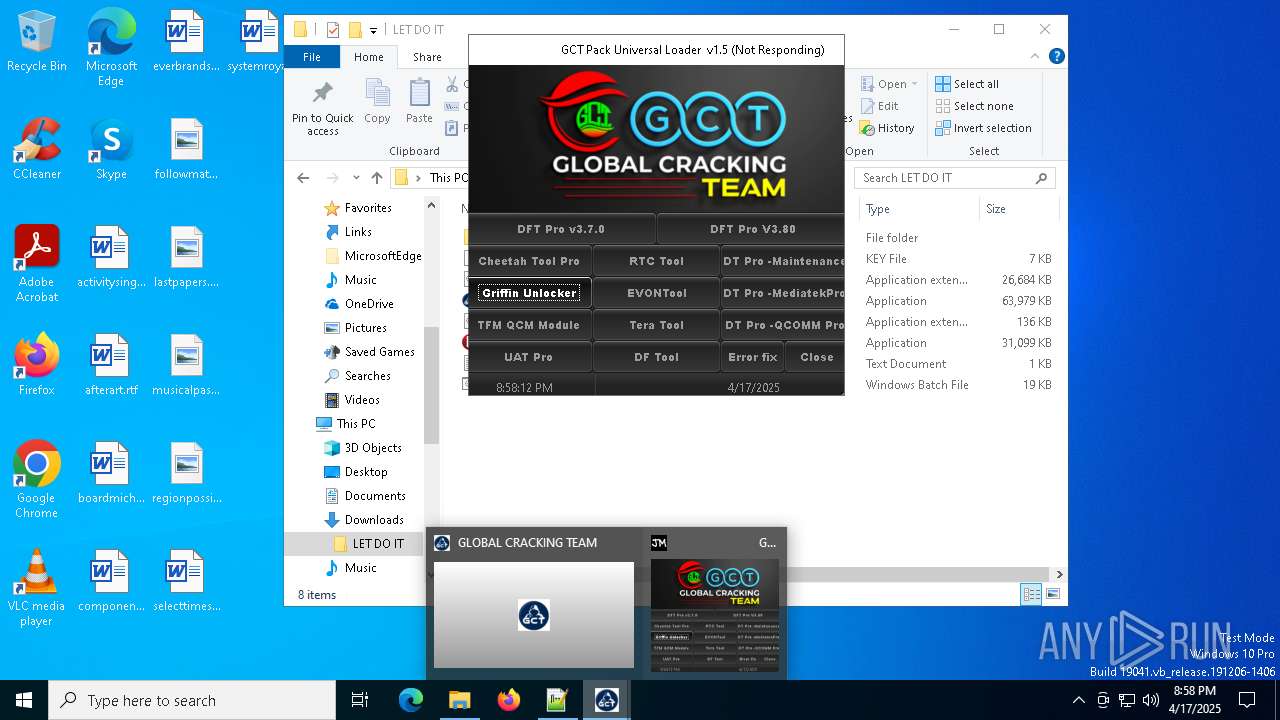
| Verdict: | Malicious activity |
| Analysis date: | April 17, 2025, 20:53:53 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MD5: | 137F0700A02A7EA4249E22BC75221213 |
| SHA1: | 16064E04A91D6F95E7090F94AC9C25B9A22ED4BE |
| SHA256: | 648CD228EC80DCD856D5724B215C08F77F0AC4E261BE372250C89954A5F5BF34 |
| SSDEEP: | 3:N8X/i1D90JinjNPLg5Uuzn:2WD9w8VGlzn |
MALICIOUS
No malicious indicators.SUSPICIOUS
There is functionality for taking screenshot (YARA)
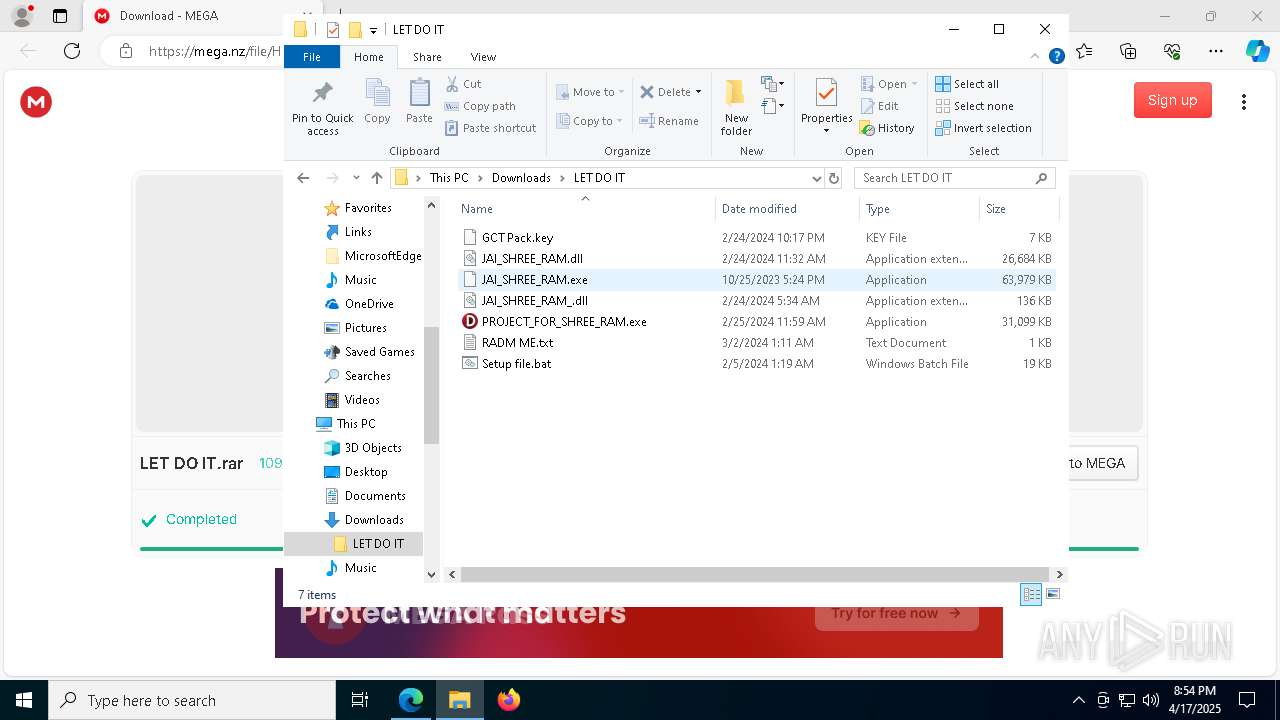
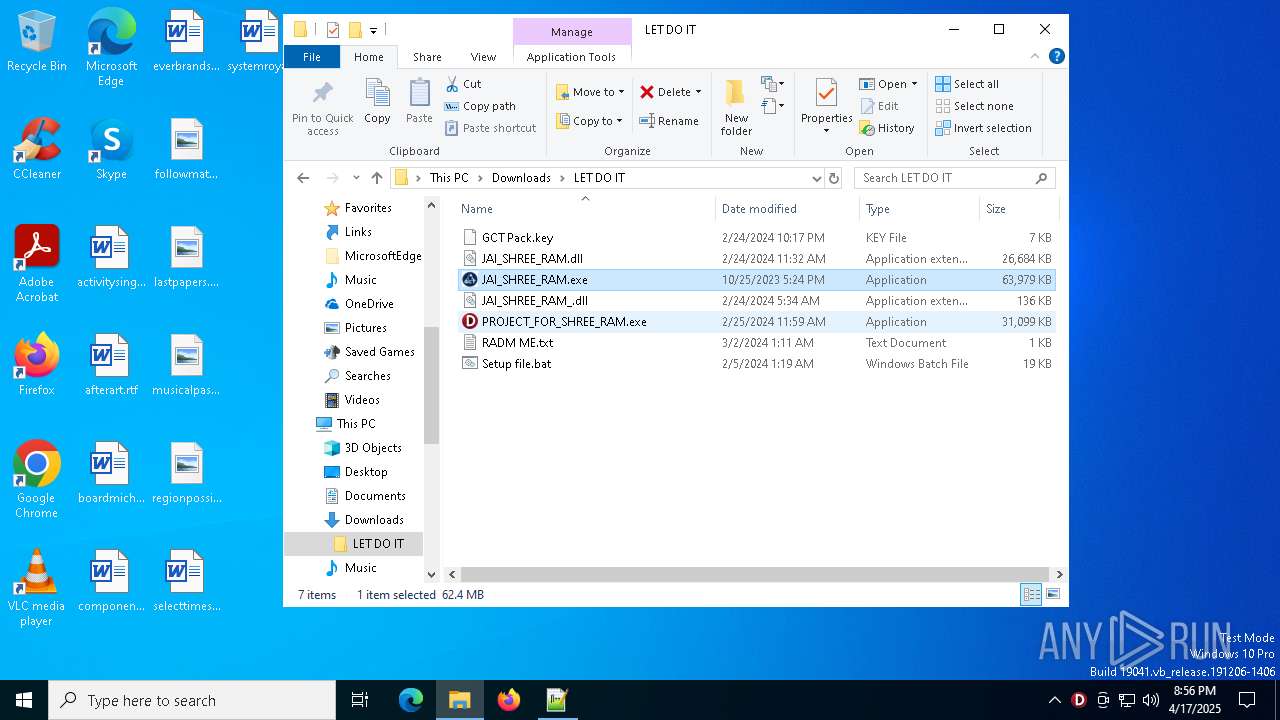
- PROJECT_FOR_SHREE_RAM.exe (PID: 5156)
- PROJECT_FOR_SHREE_RAM.exe (PID: 7336)
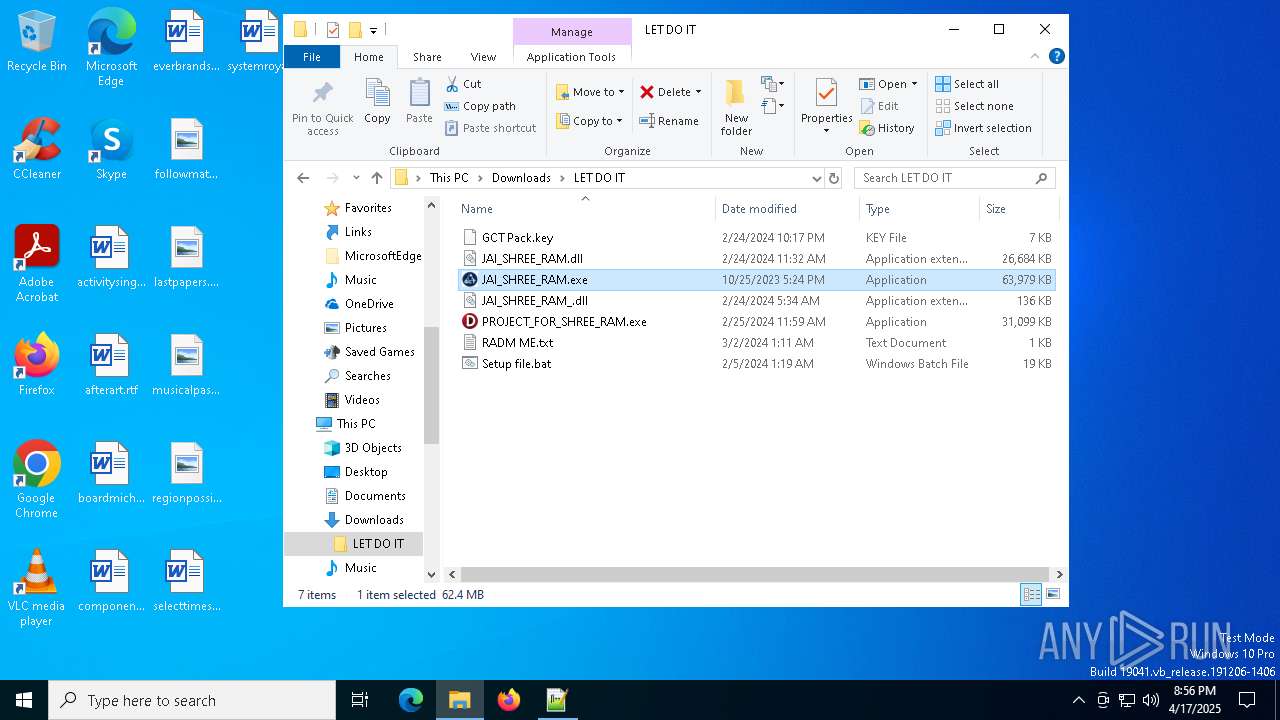
- JAI_SHREE_RAM.exe (PID: 8132)
- evbCDE8.tmp (PID: 4276)
Uses REG/REGEDIT.EXE to modify registry
- cmd.exe (PID: 1452)
- cmd.exe (PID: 6468)
There is functionality for VM detection VirtualBox (YARA)
- JAI_SHREE_RAM.exe (PID: 8132)
Creates files in the driver directory
- evbB5F5.tmp (PID: 6136)
Reads the BIOS version
- JAI_SHREE_RAM.exe (PID: 8132)
Starts application with an unusual extension
- JAI_SHREE_RAM.exe (PID: 8132)
Executable content was dropped or overwritten
- evbB5F5.tmp (PID: 6136)
- JAI_SHREE_RAM.exe (PID: 8132)
- evbCDE8.tmp (PID: 4276)
Reads security settings of Internet Explorer
- JAI_SHREE_RAM.exe (PID: 8132)
INFO
Checks supported languages
- identity_helper.exe (PID: 7892)
- JAI_SHREE_RAM.exe (PID: 4488)
- PROJECT_FOR_SHREE_RAM.exe (PID: 5156)
- identity_helper.exe (PID: 6892)
- PROJECT_FOR_SHREE_RAM.exe (PID: 7544)
- JAI_SHREE_RAM.exe (PID: 7800)
- PROJECT_FOR_SHREE_RAM.exe (PID: 7336)
- JAI_SHREE_RAM.exe (PID: 8132)
- evbB5F5.tmp (PID: 6136)
- evbCDE8.tmp (PID: 4276)
Application launched itself
- msedge.exe (PID: 6048)
- msedge.exe (PID: 736)
Reads Environment values
- identity_helper.exe (PID: 7892)
- identity_helper.exe (PID: 6892)
Reads the computer name
- identity_helper.exe (PID: 7892)
- PROJECT_FOR_SHREE_RAM.exe (PID: 5156)
- PROJECT_FOR_SHREE_RAM.exe (PID: 7544)
- PROJECT_FOR_SHREE_RAM.exe (PID: 7336)
- JAI_SHREE_RAM.exe (PID: 8132)
- identity_helper.exe (PID: 6892)
- evbB5F5.tmp (PID: 6136)
- evbCDE8.tmp (PID: 4276)
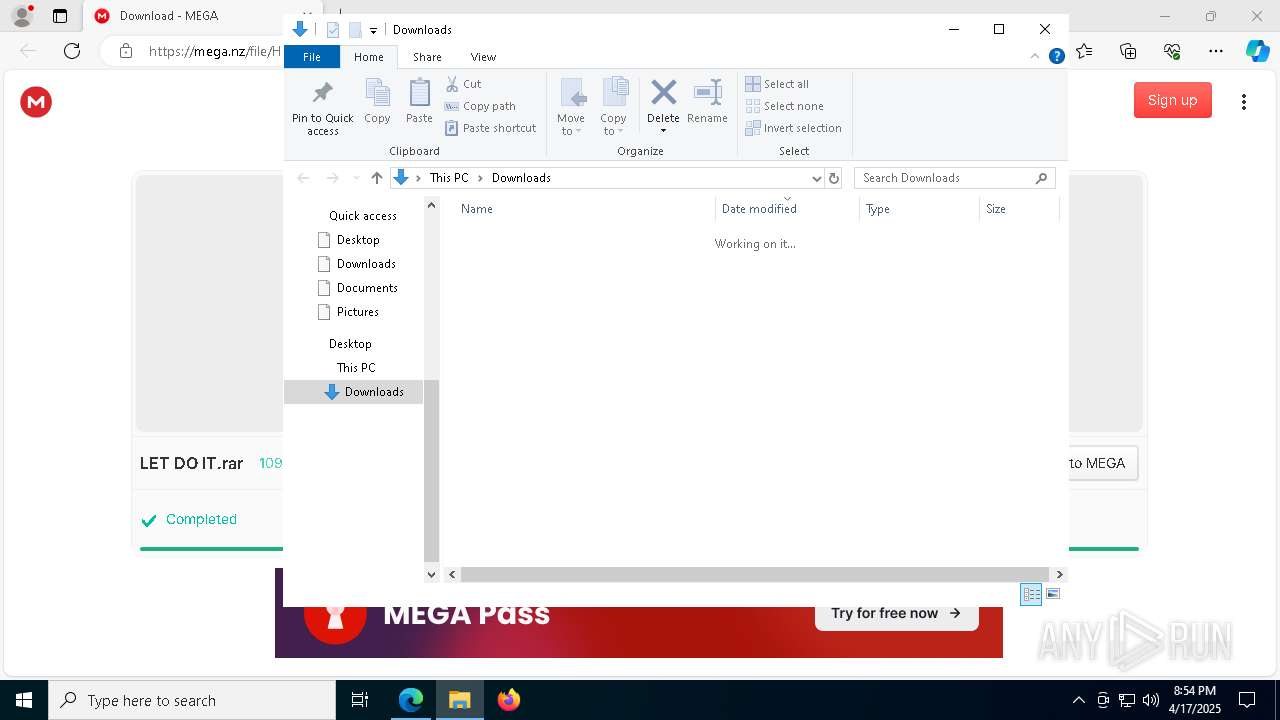
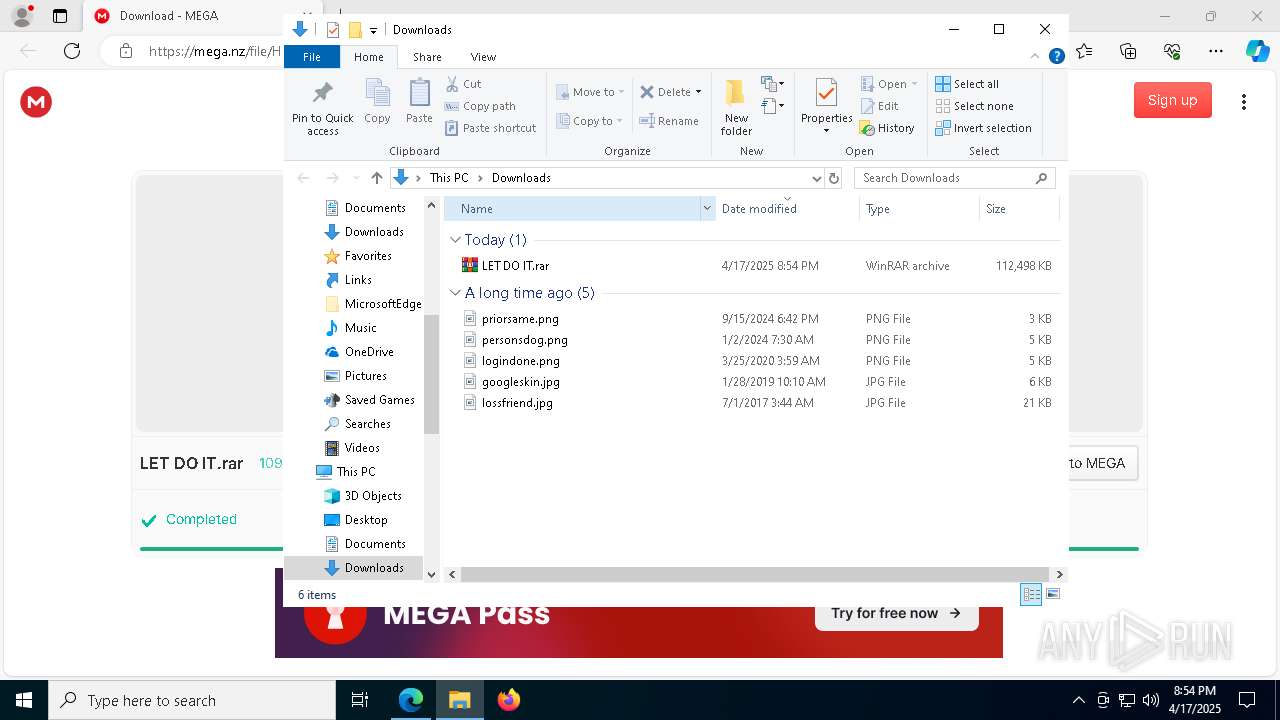
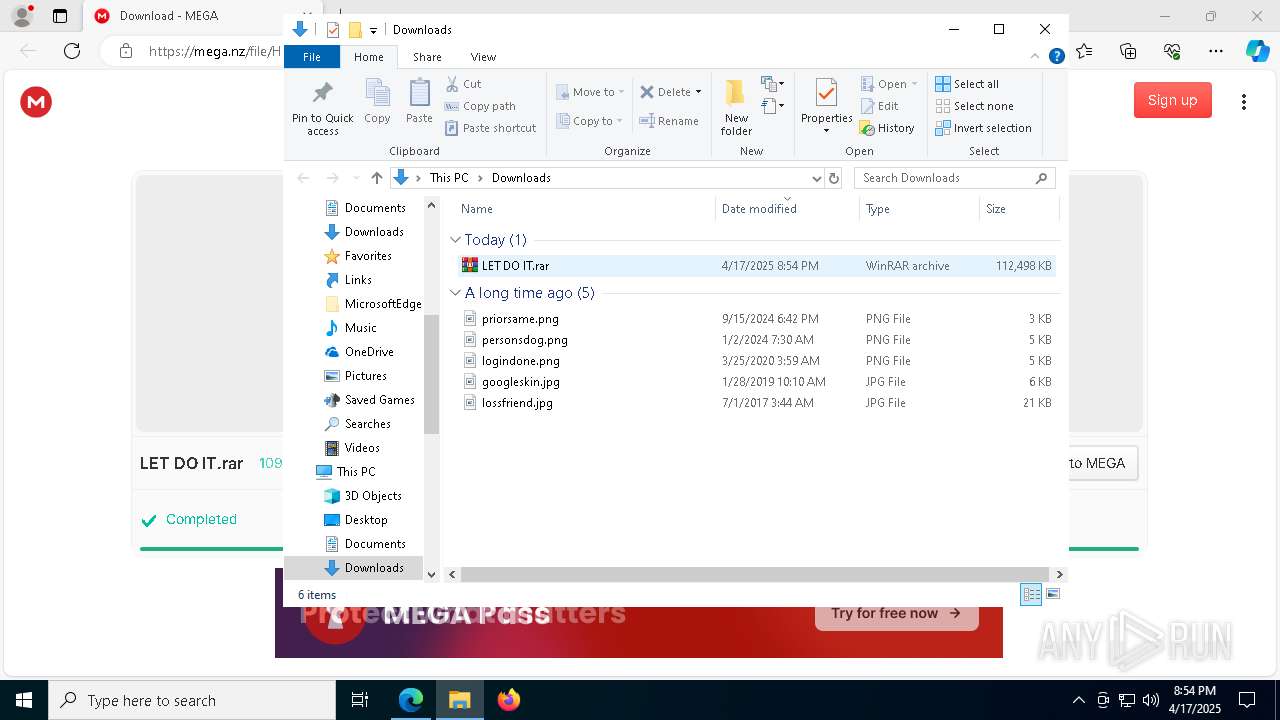
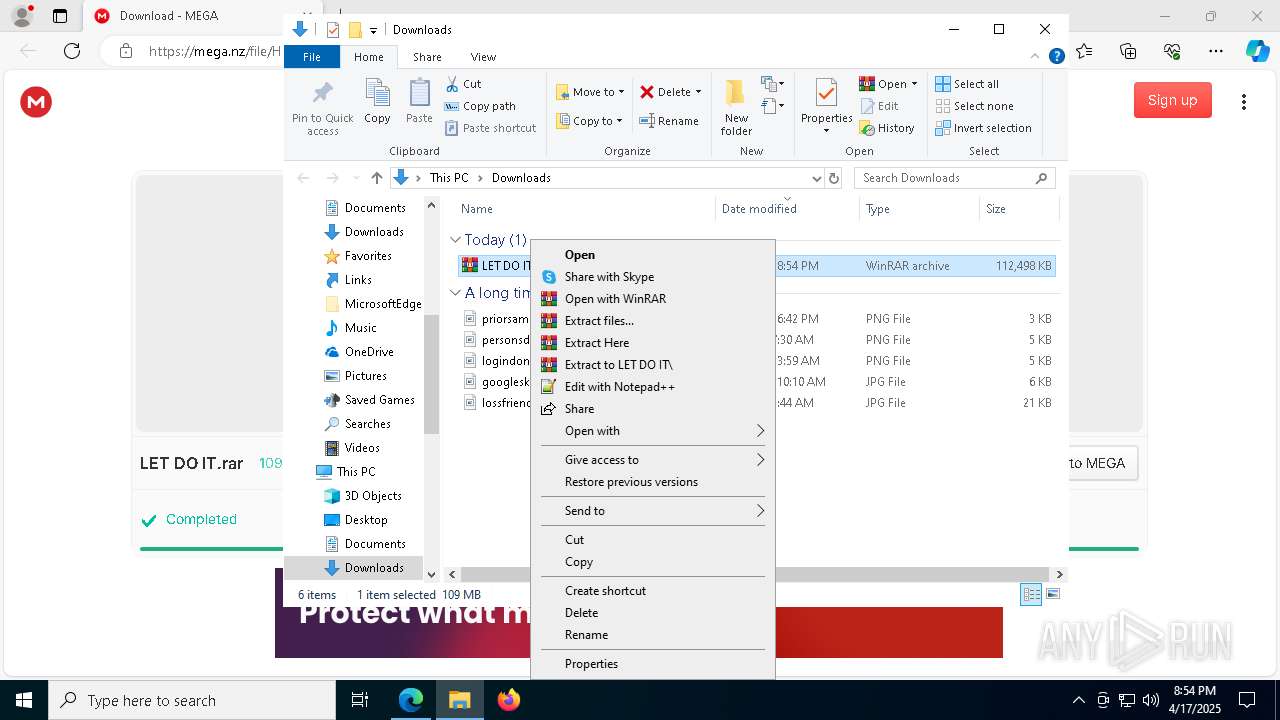
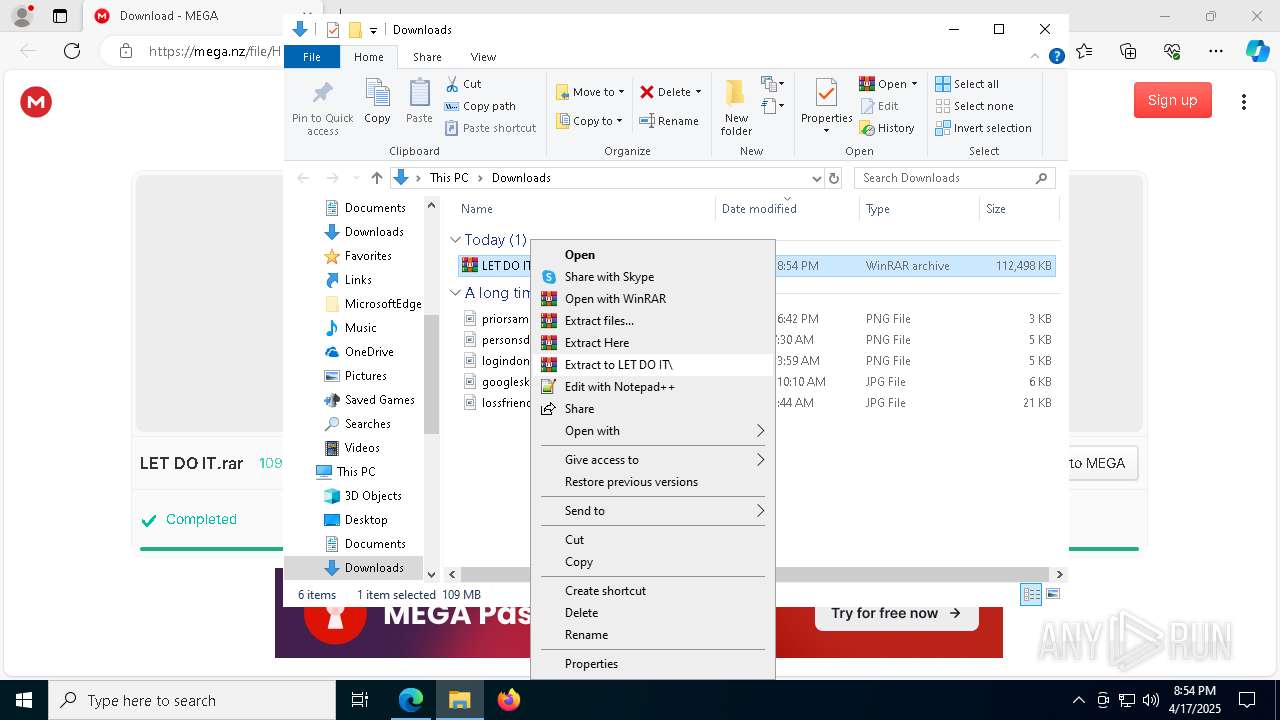
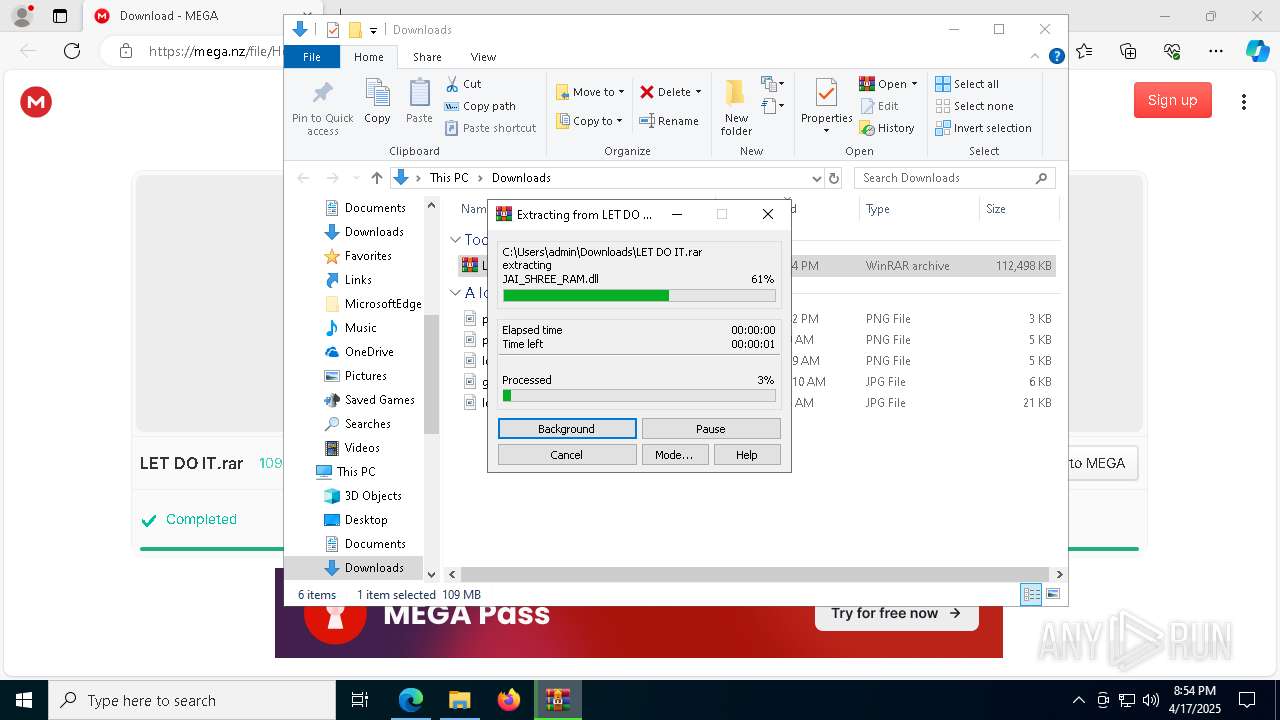
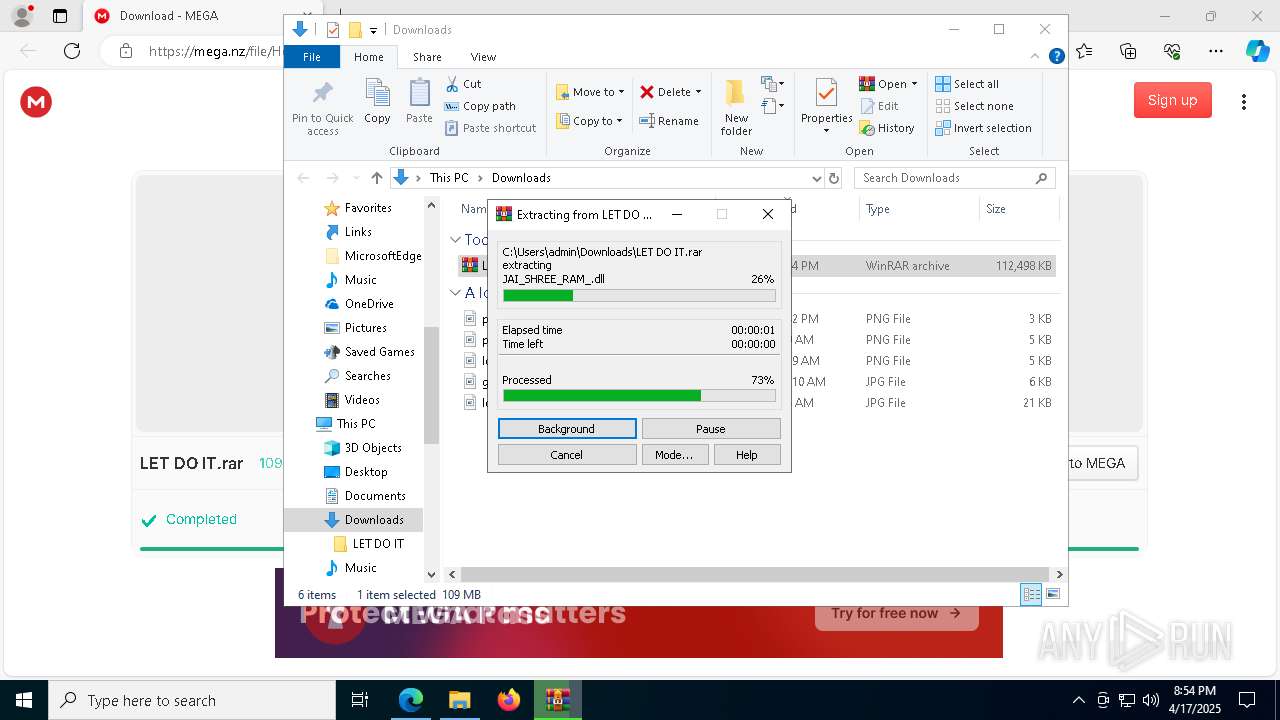
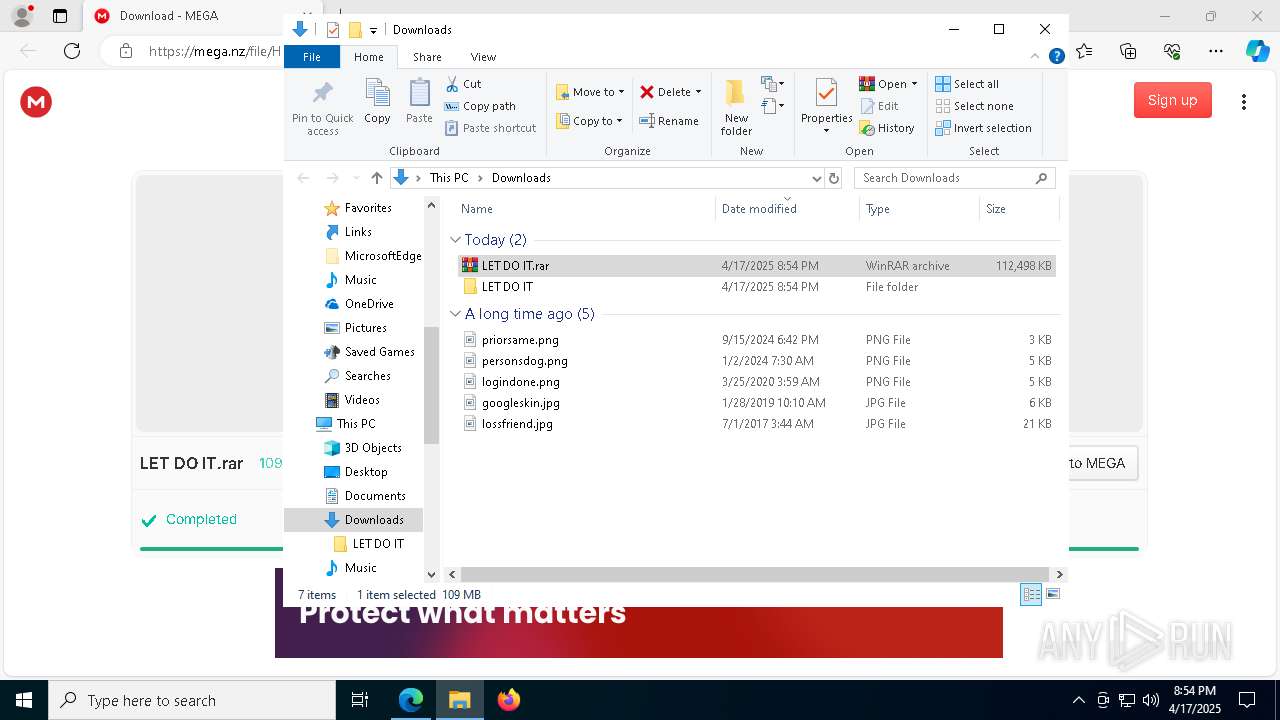
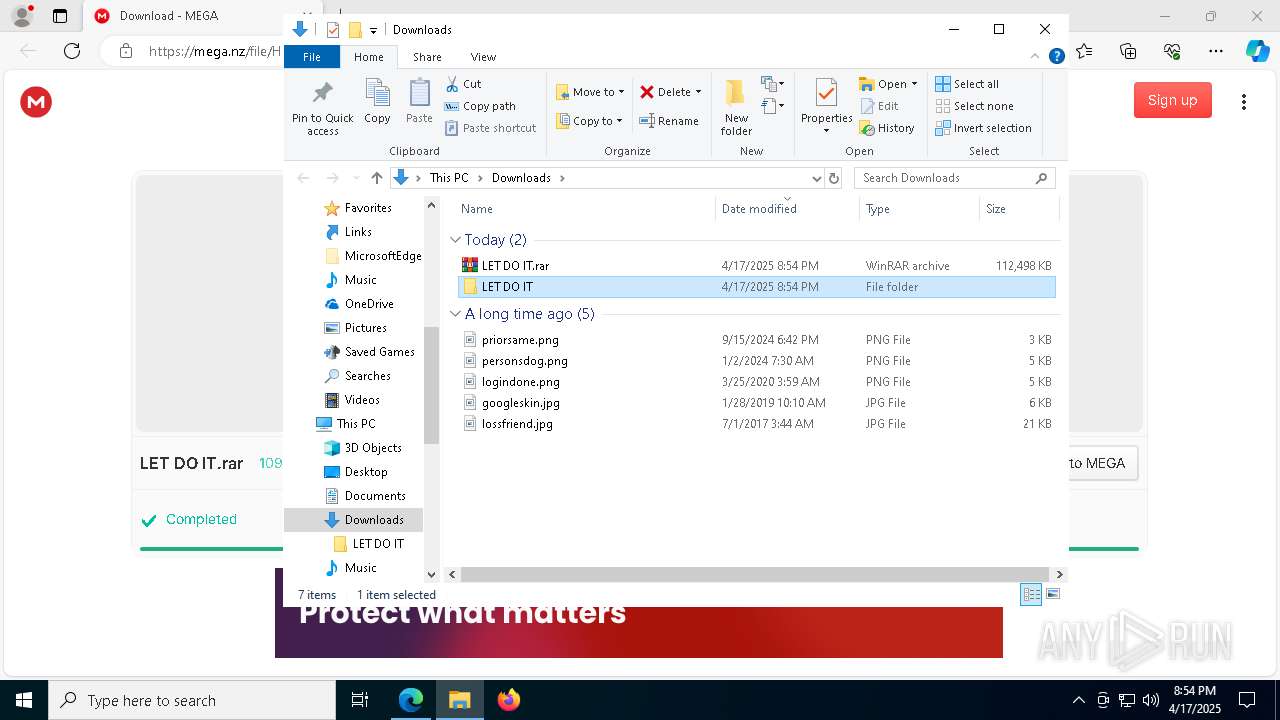
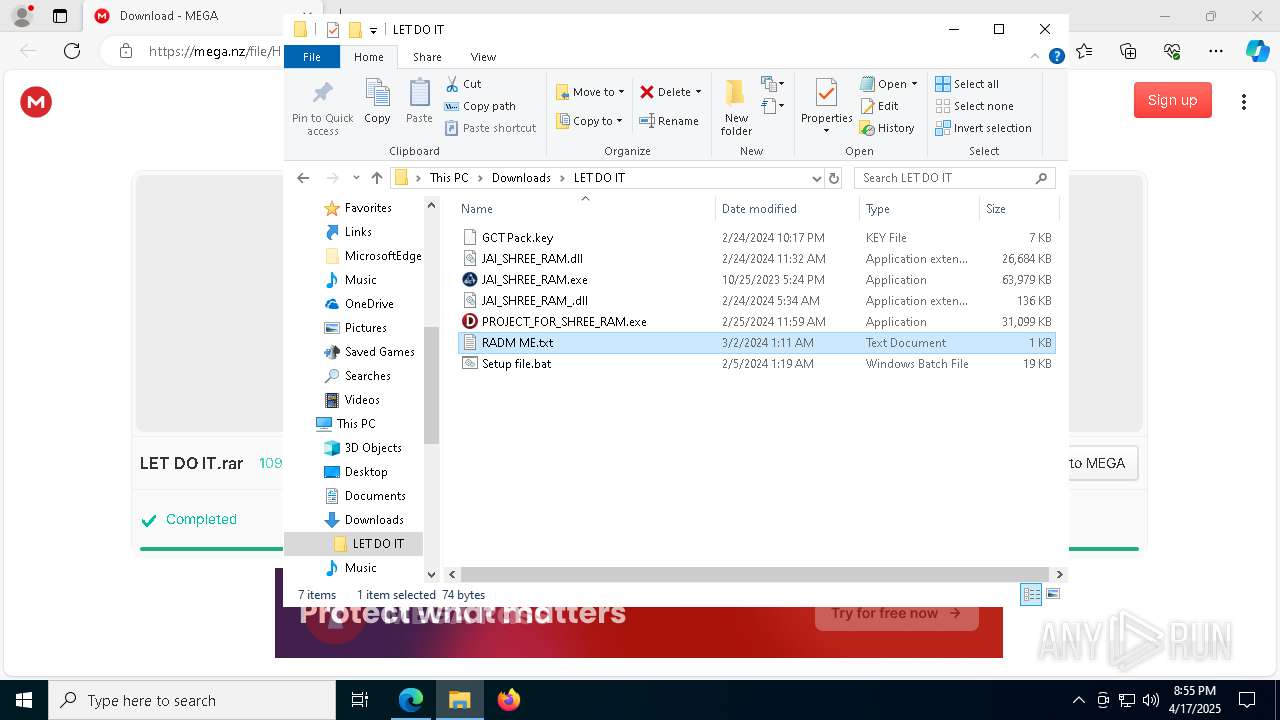
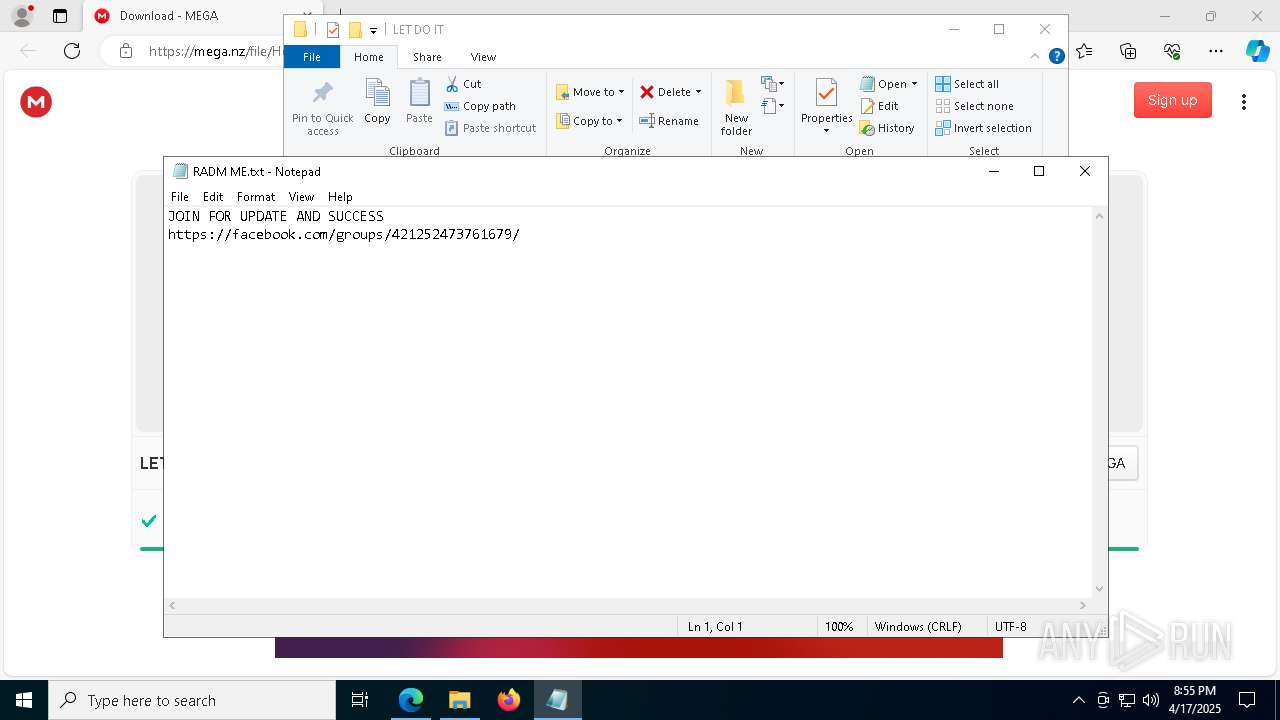
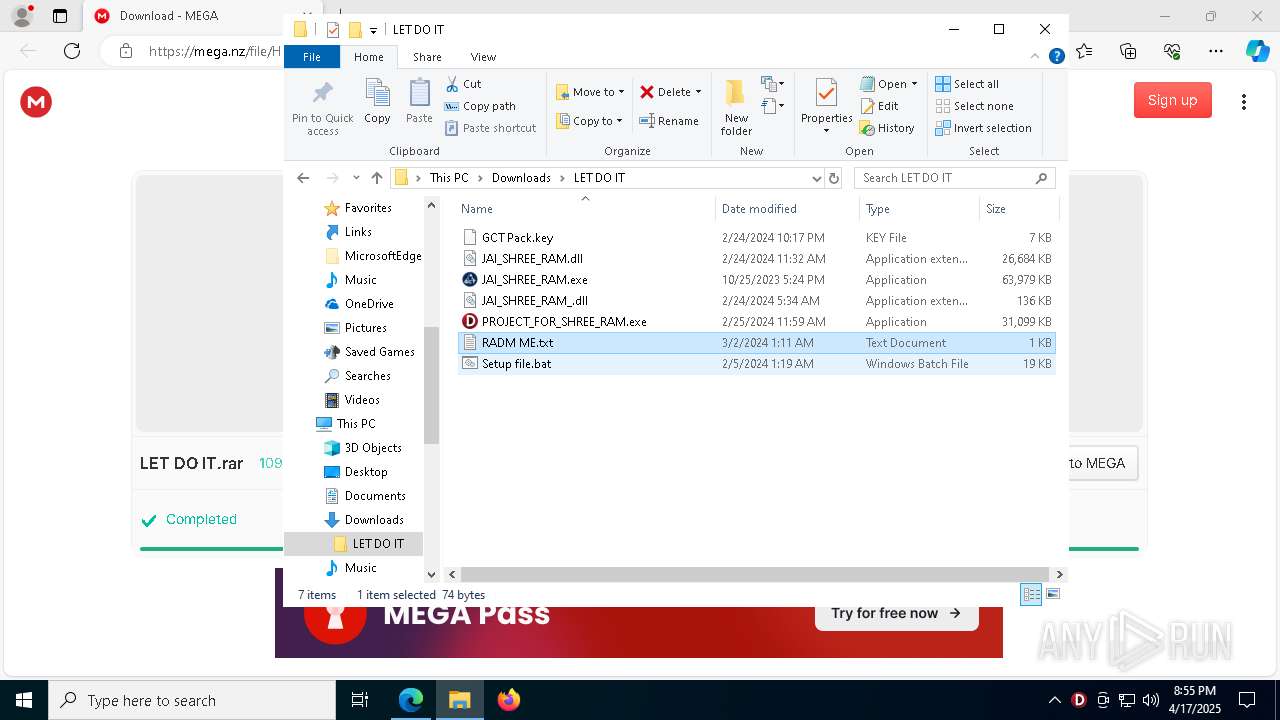
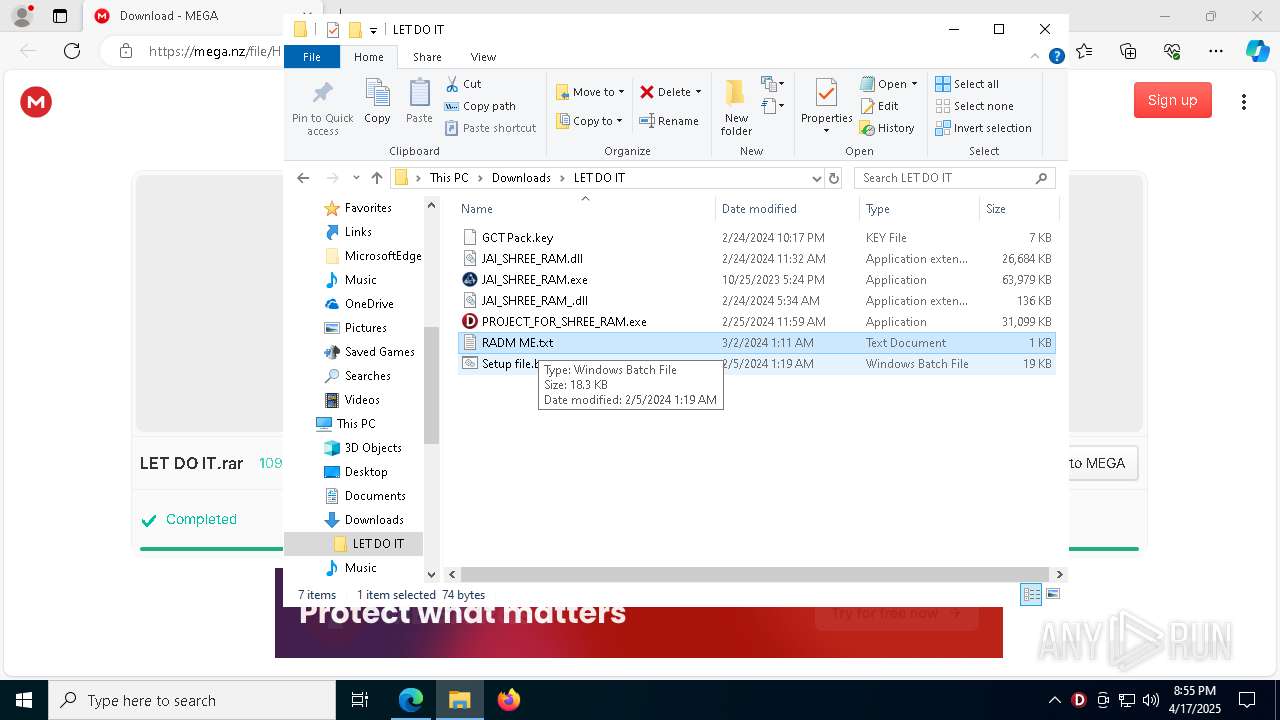
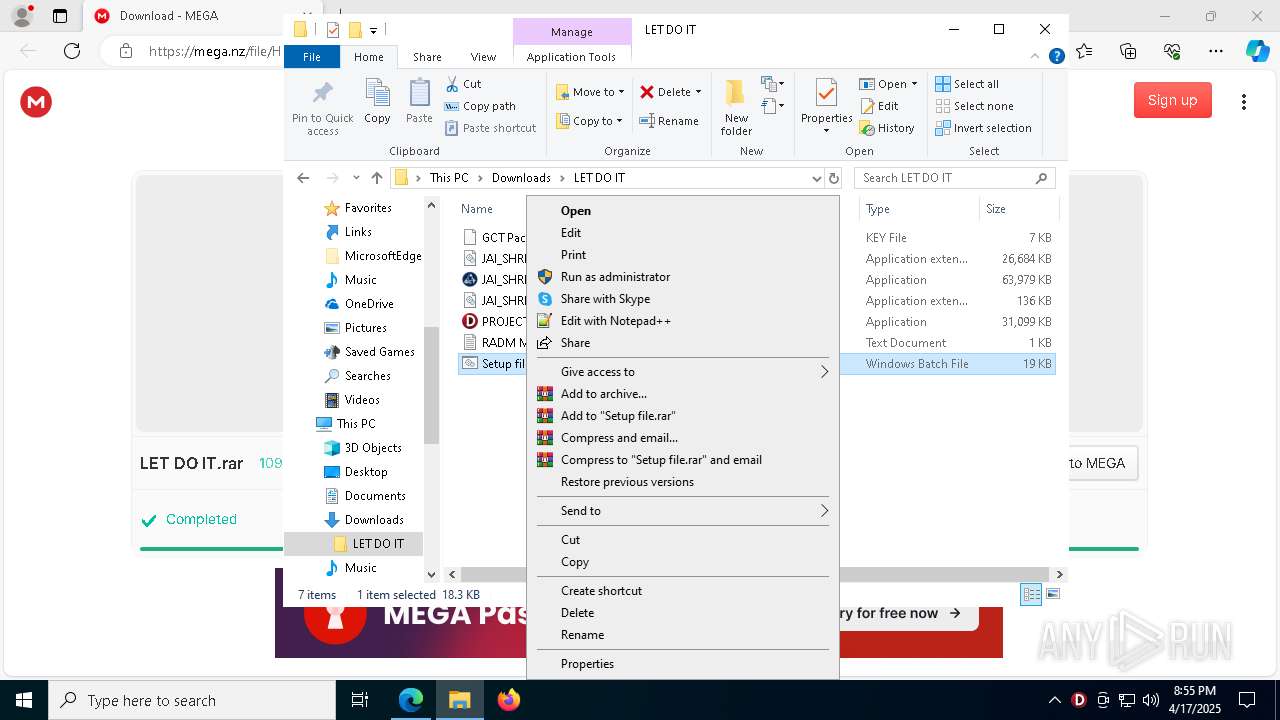
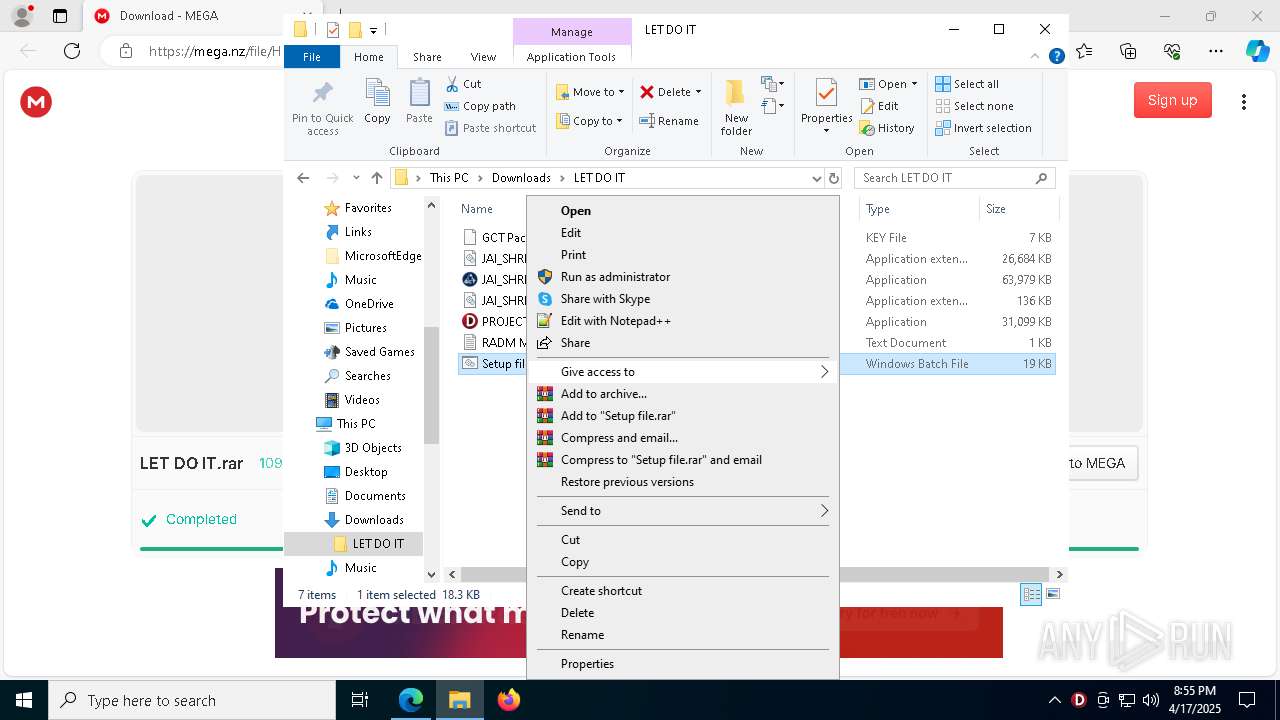
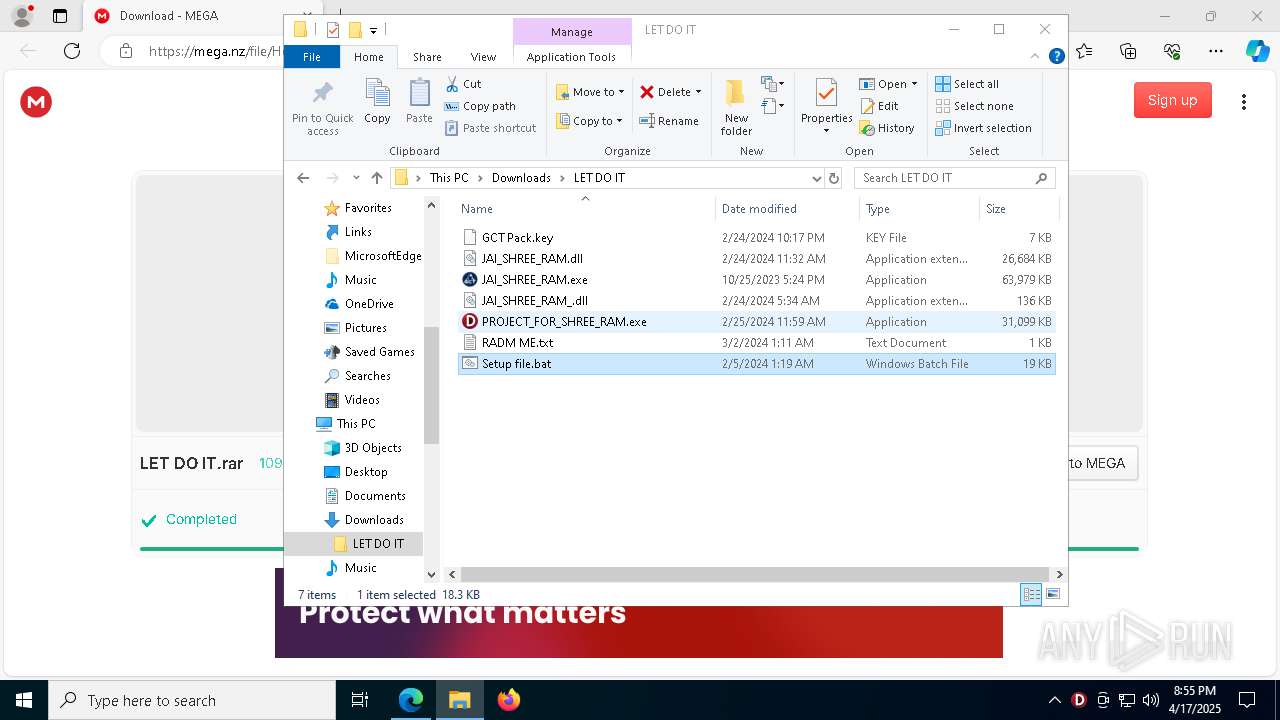
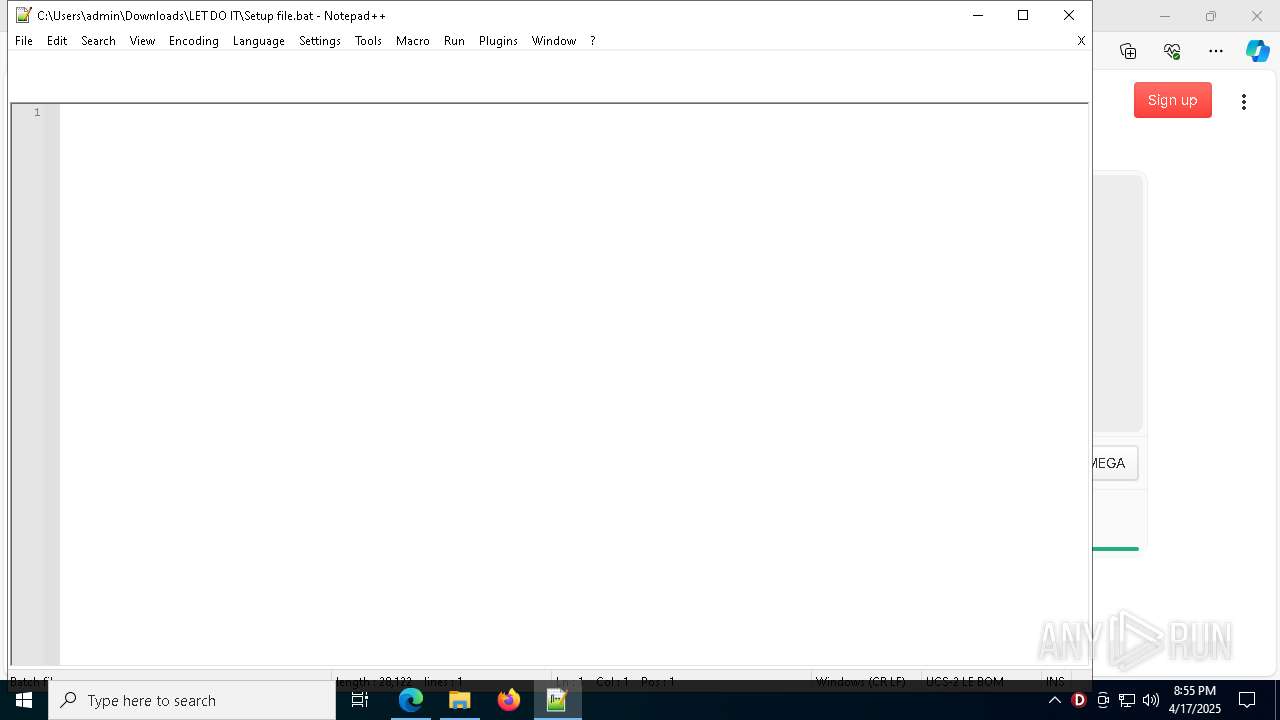
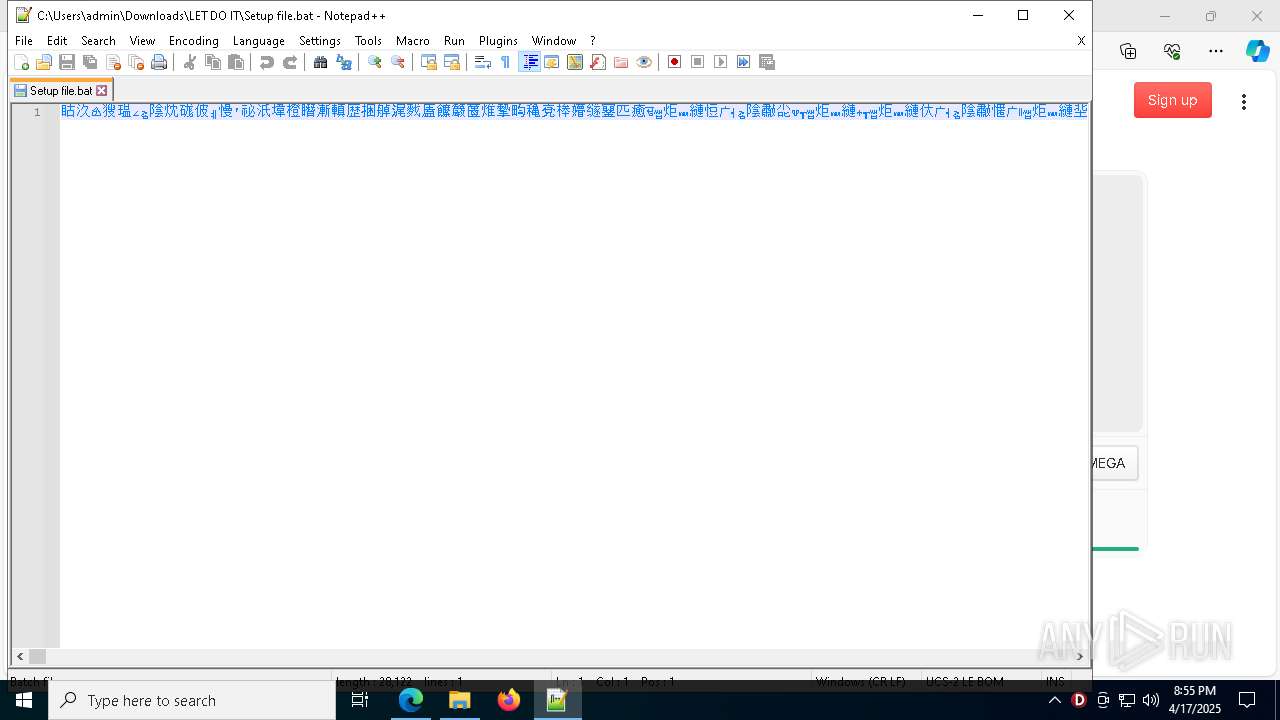
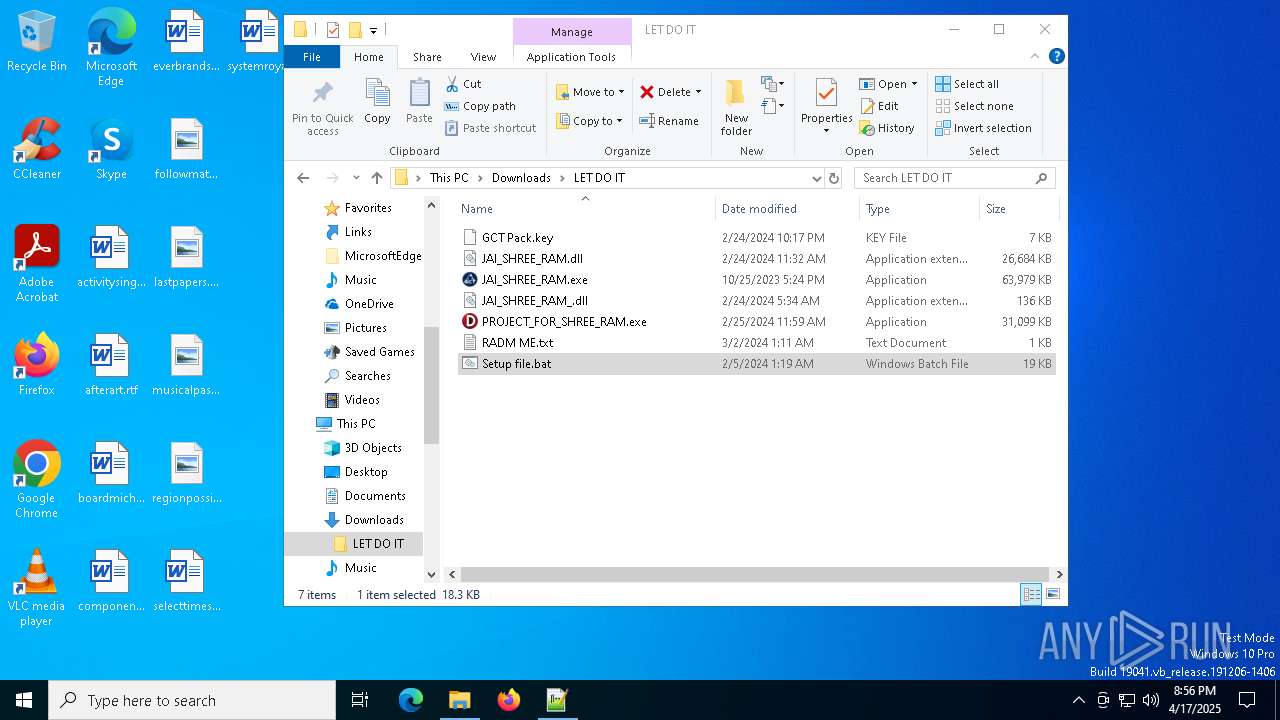
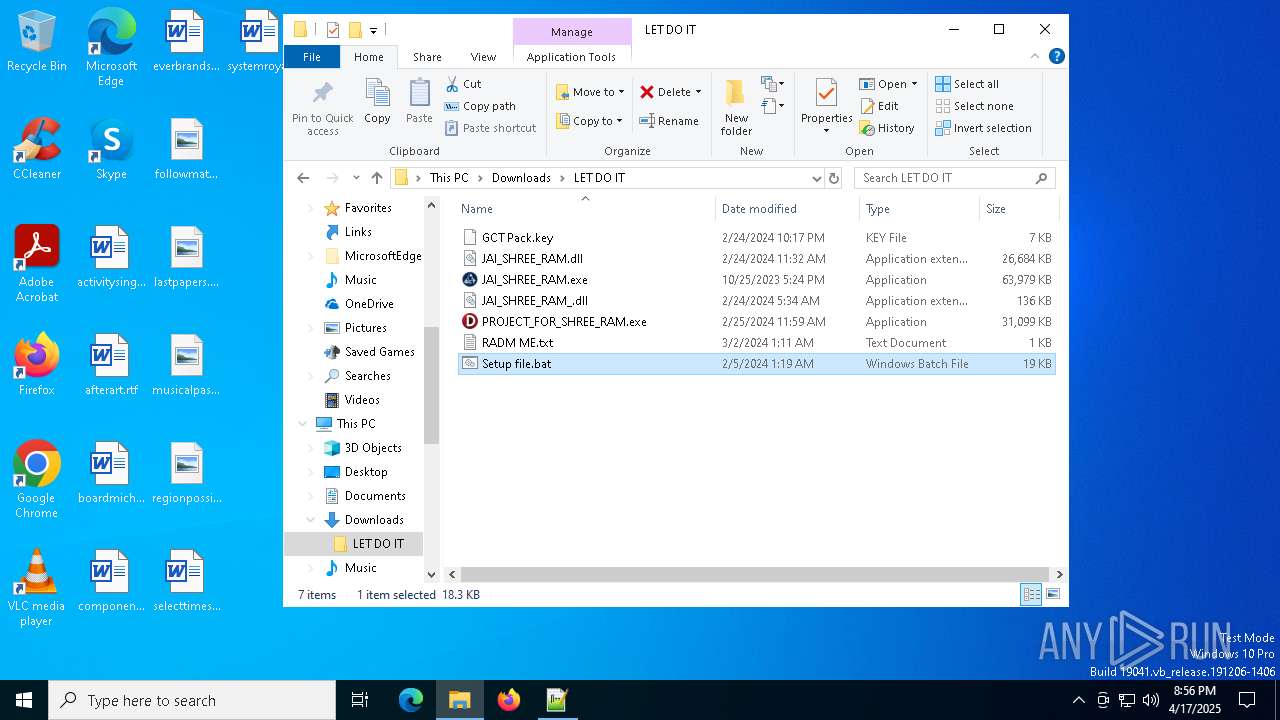
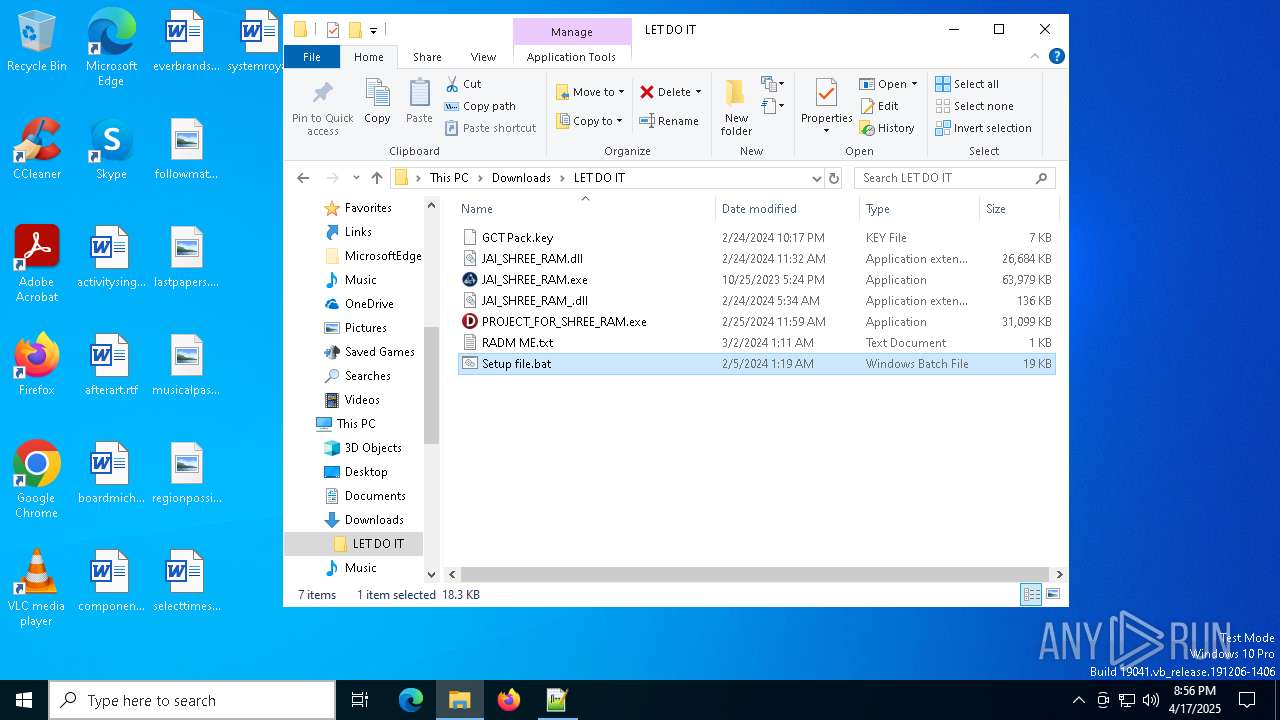
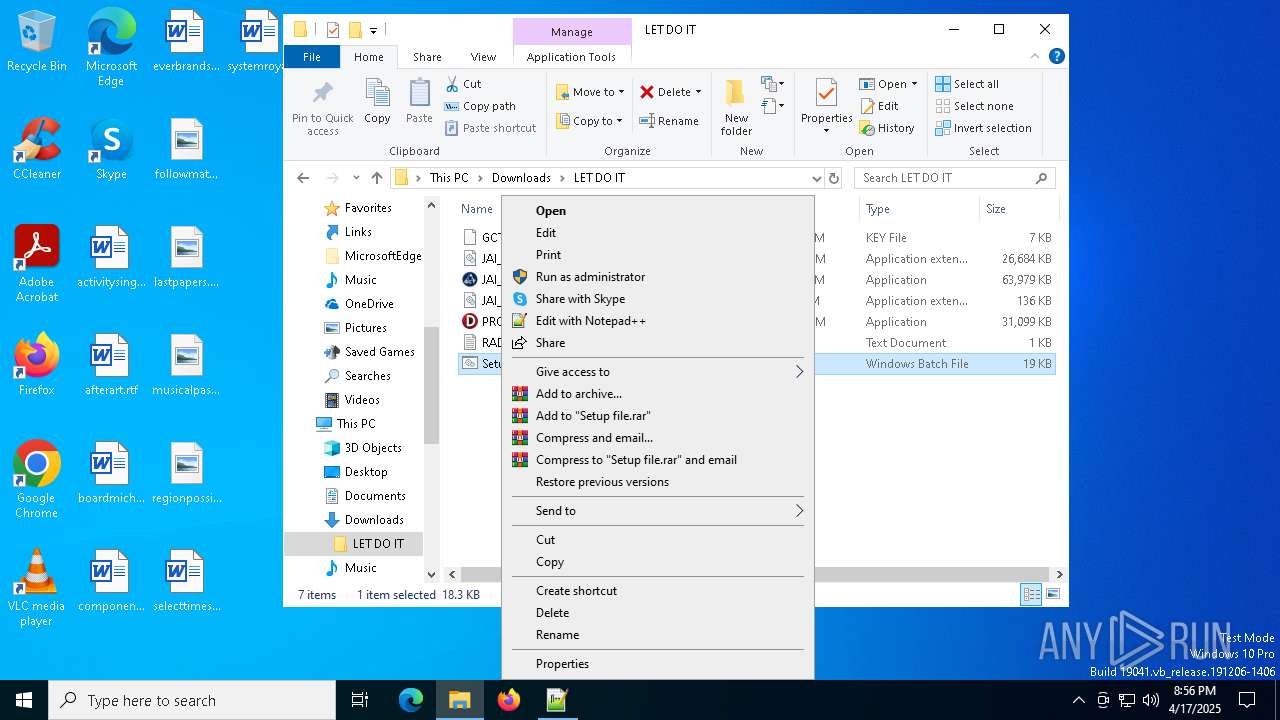
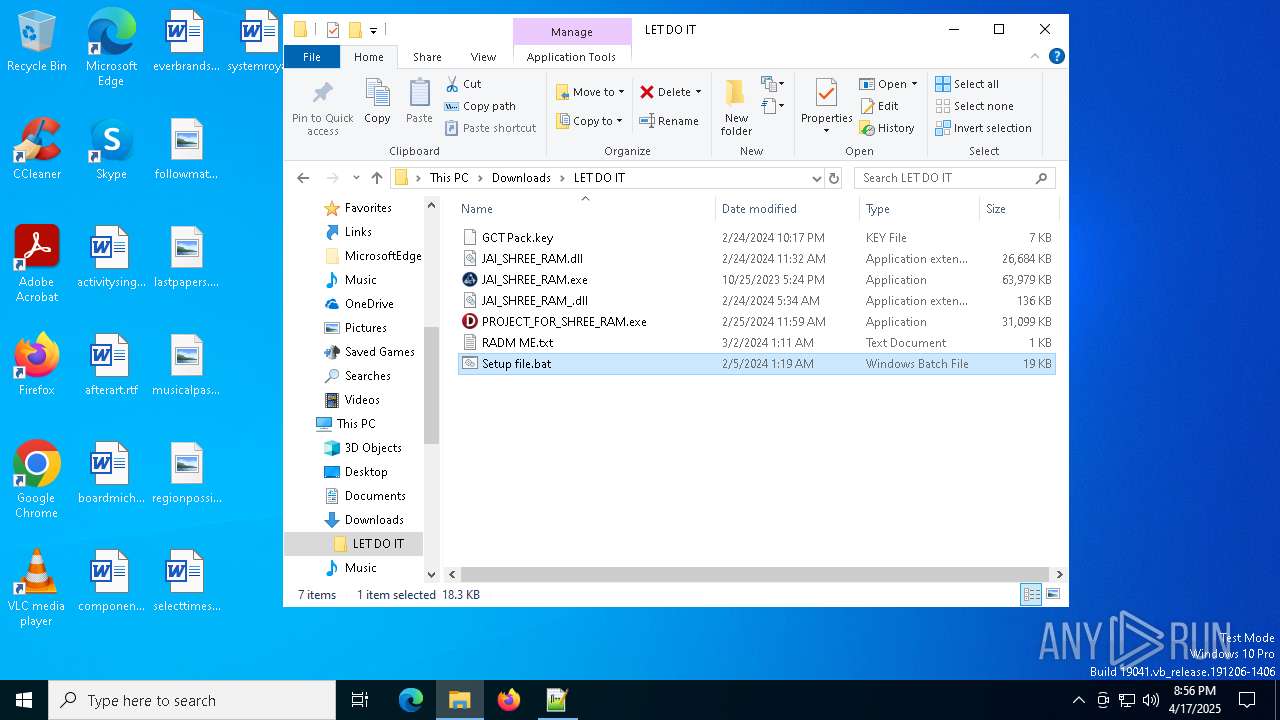
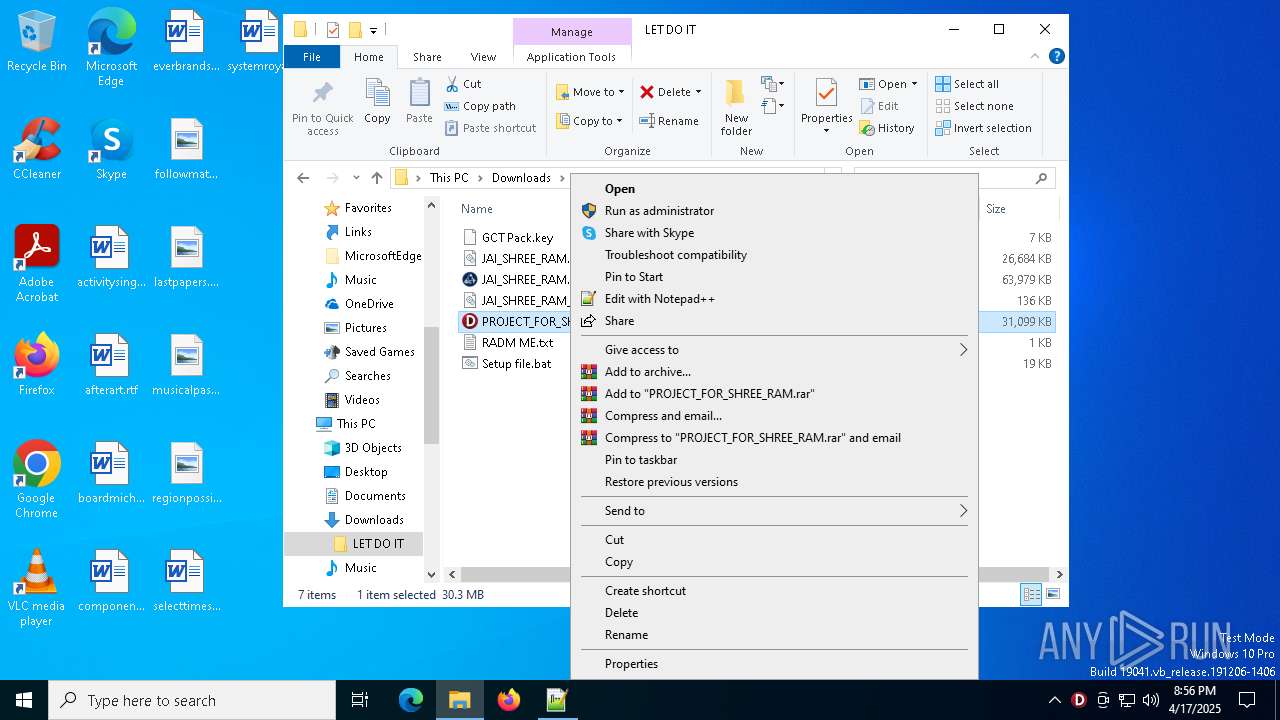
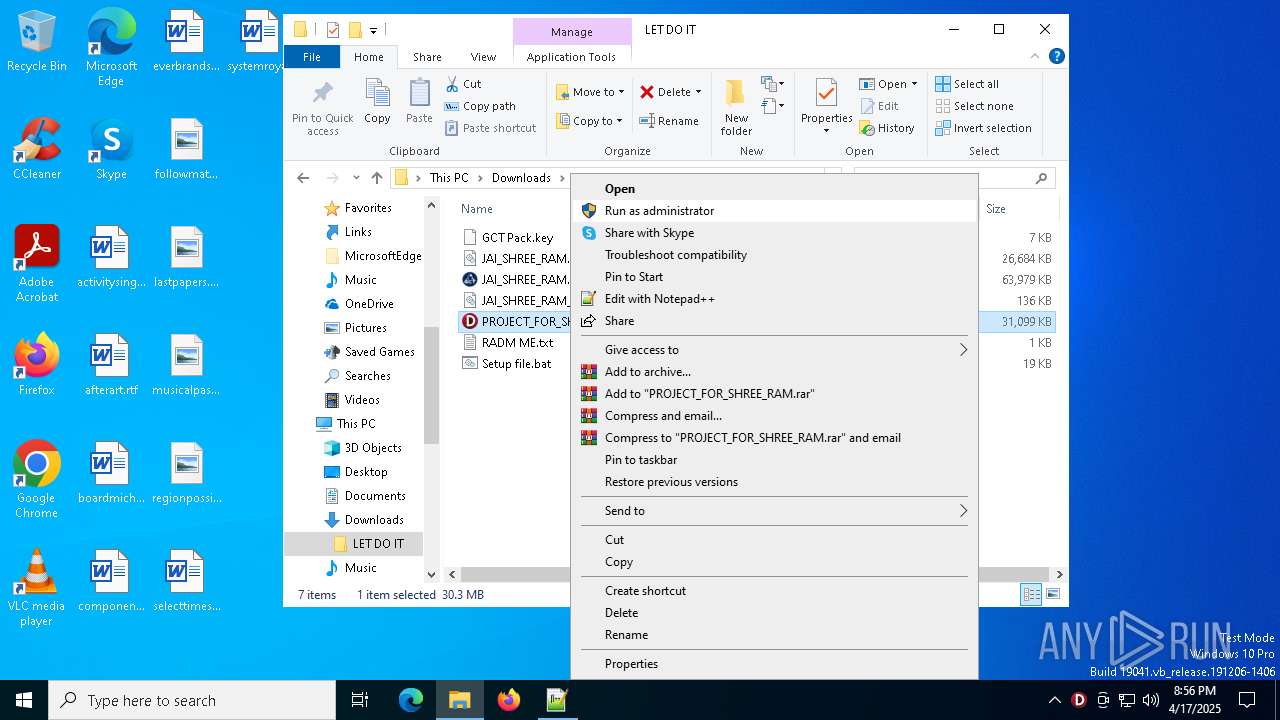
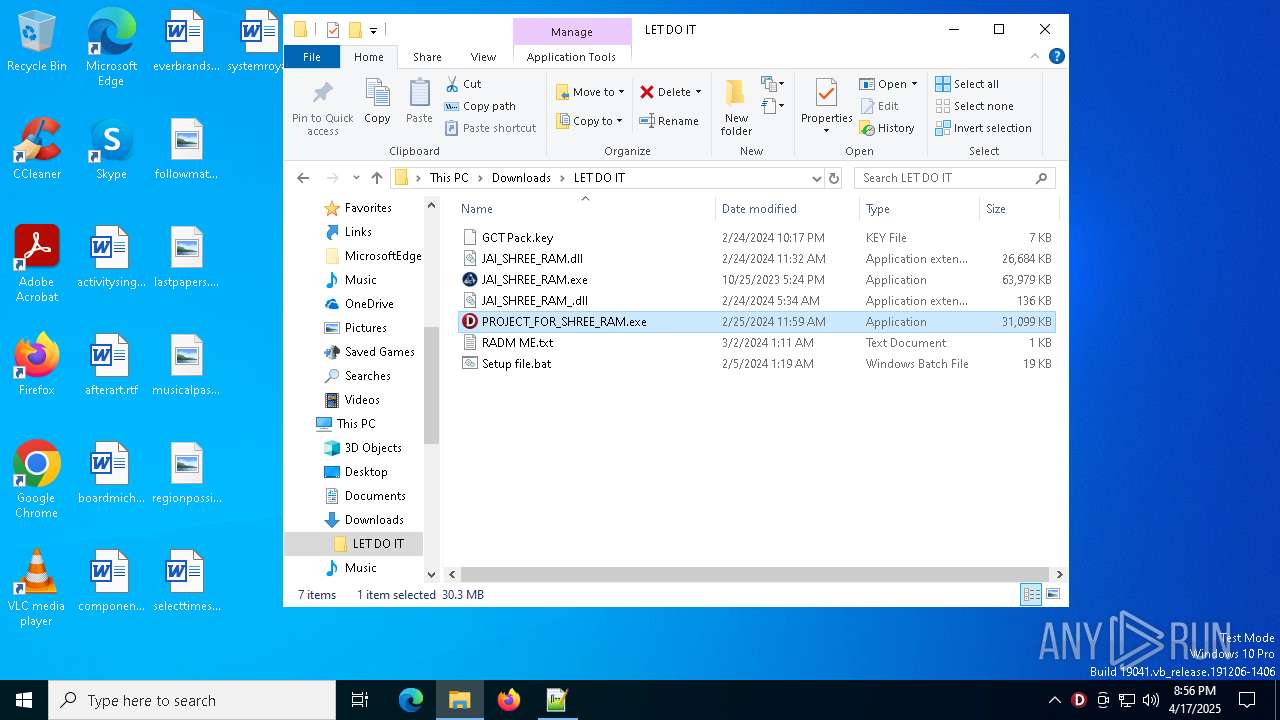
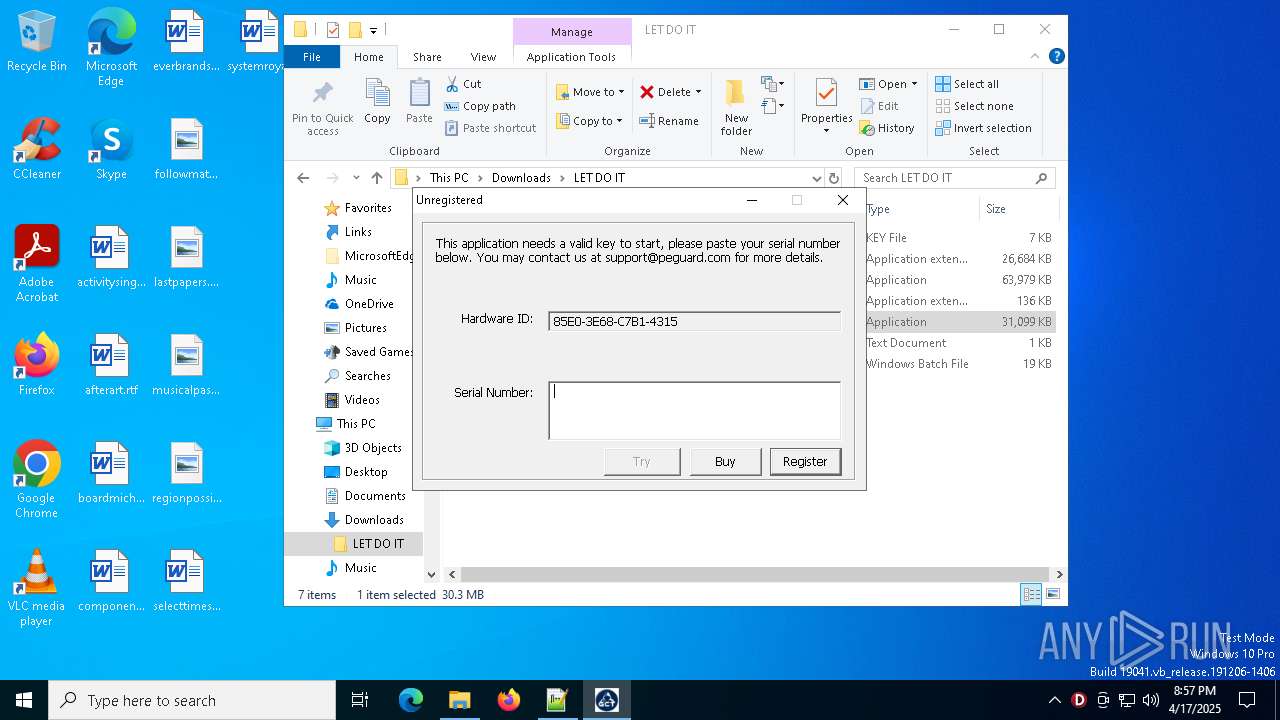
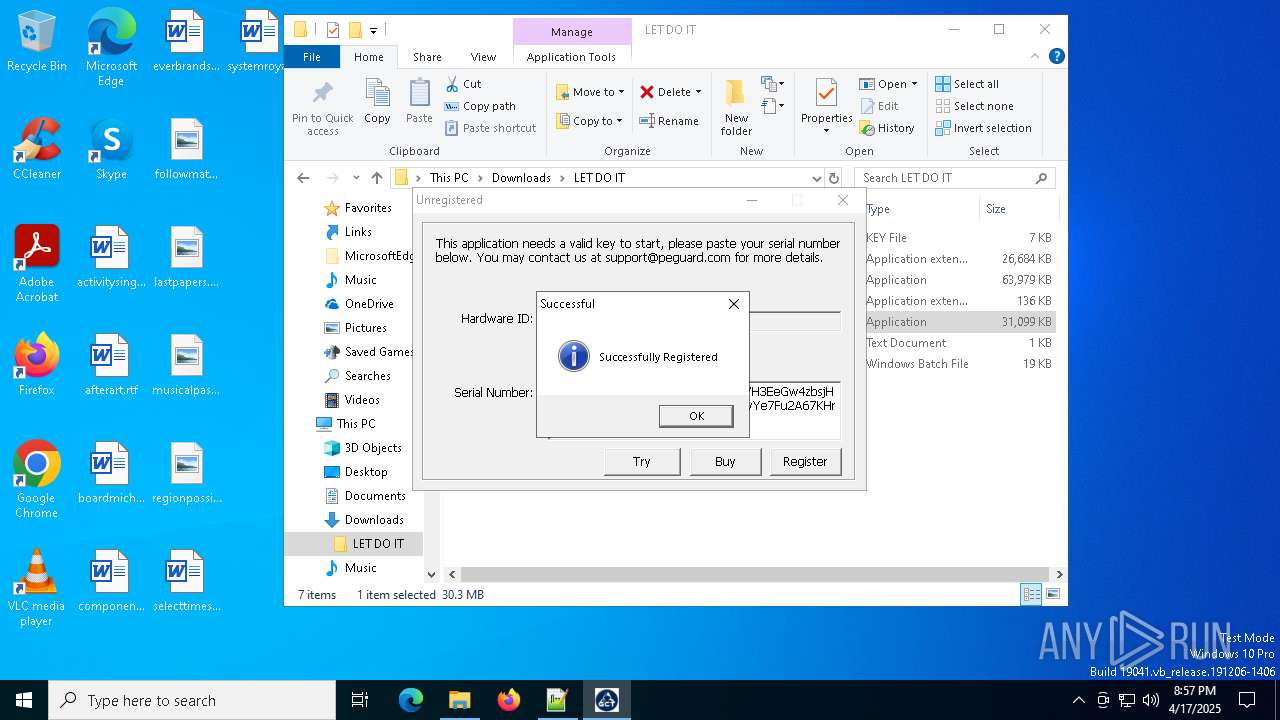
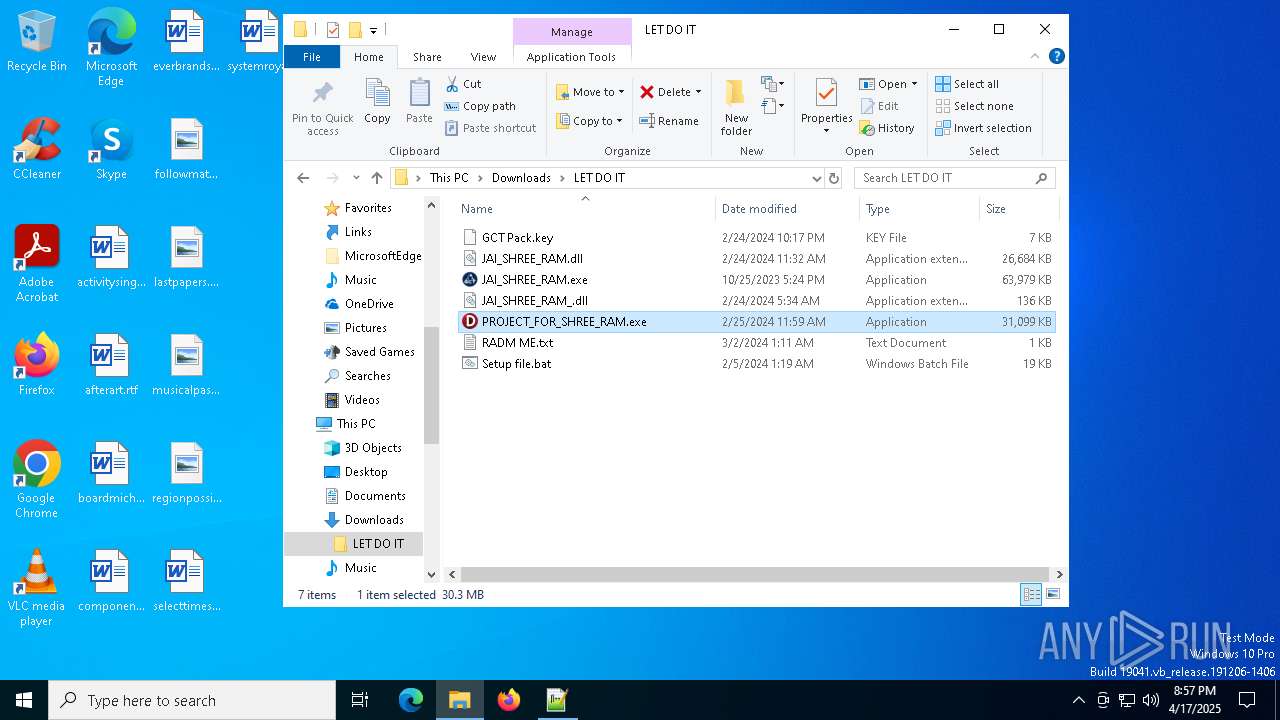
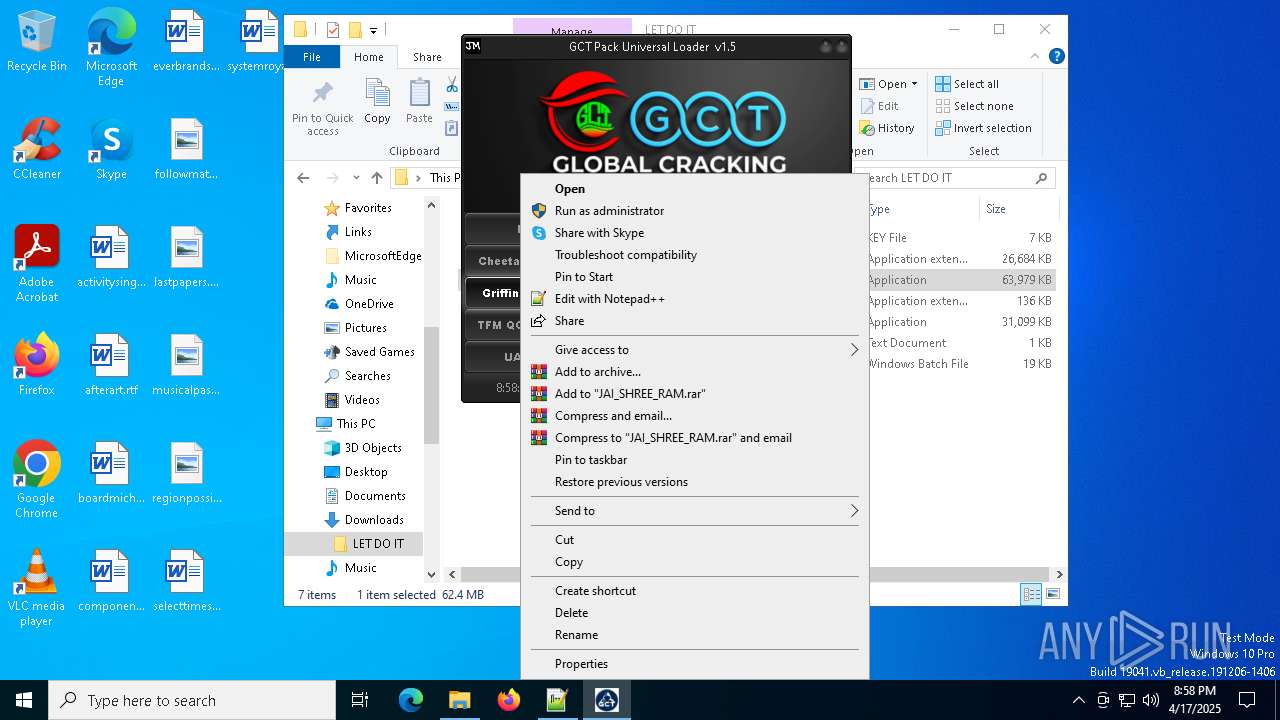
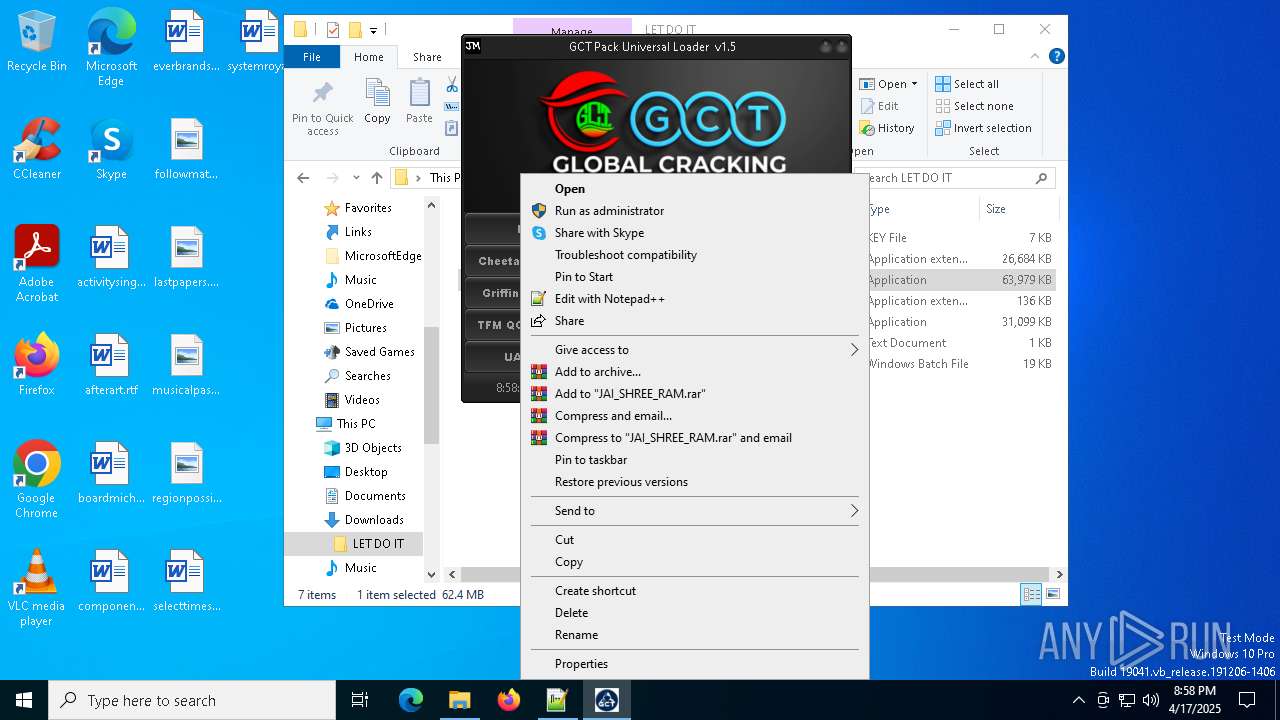
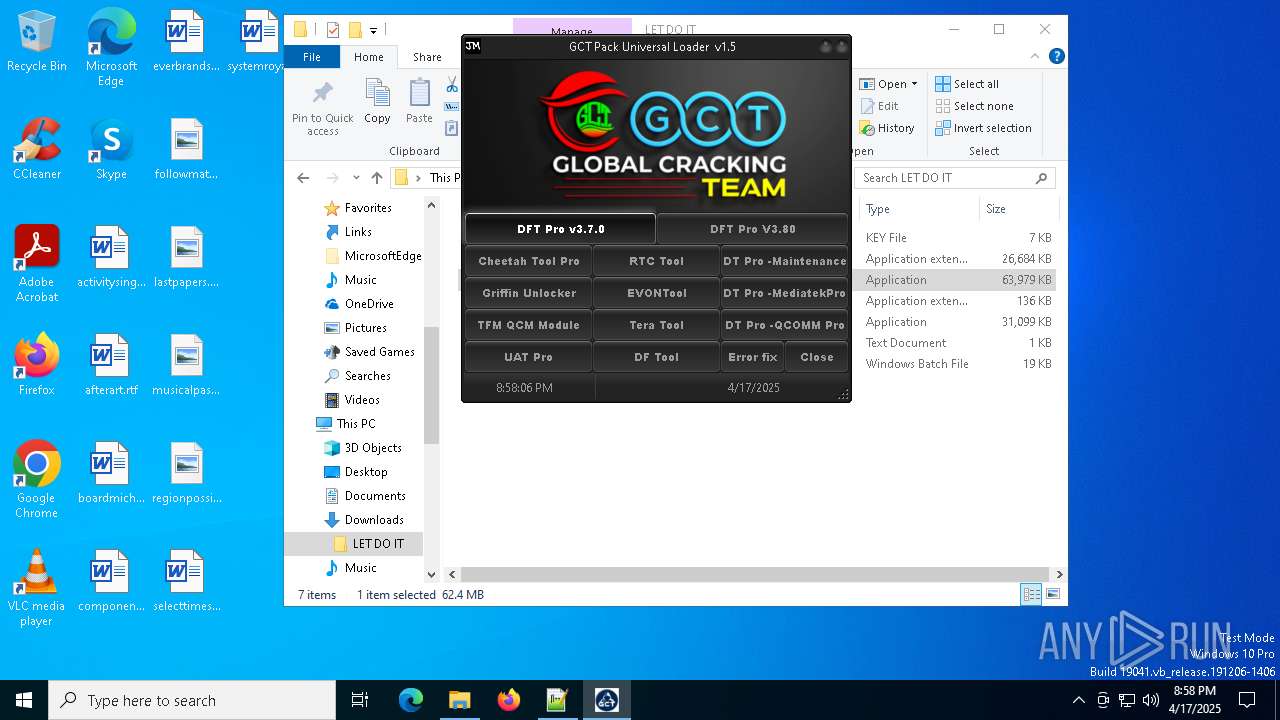
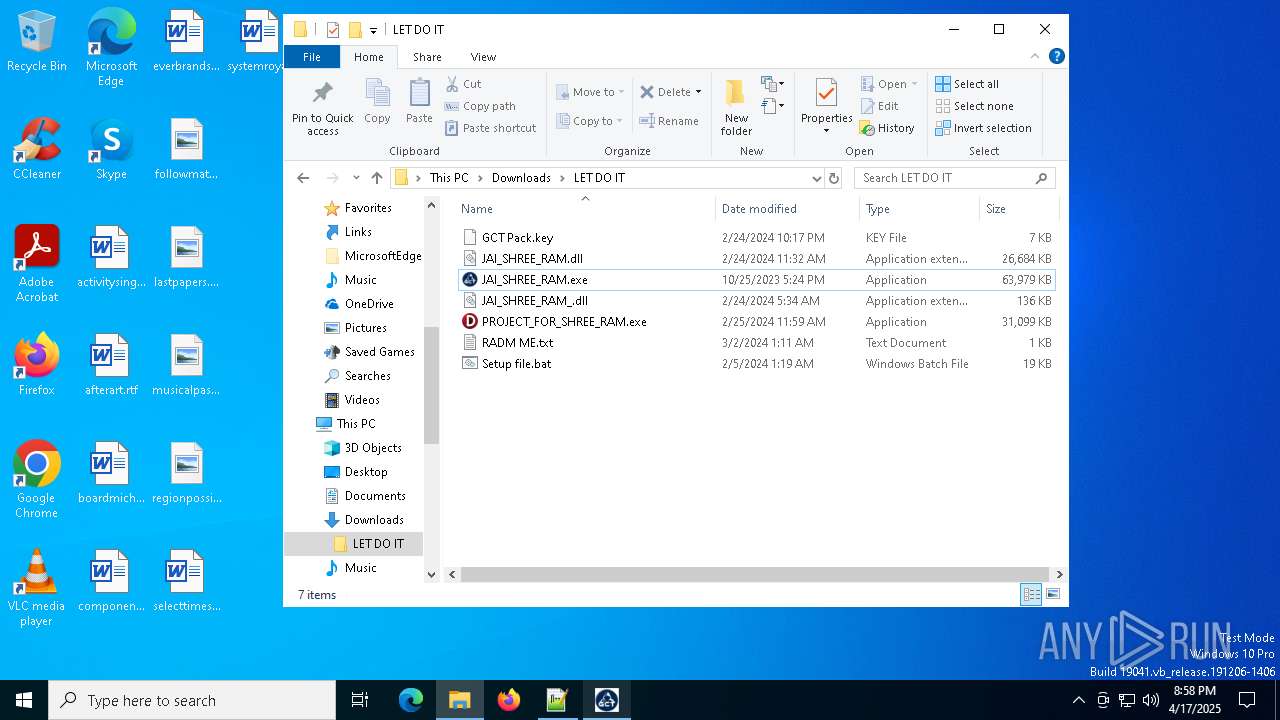
Manual execution by a user
- WinRAR.exe (PID: 2040)
- JAI_SHREE_RAM.exe (PID: 4488)
- PROJECT_FOR_SHREE_RAM.exe (PID: 5156)
- notepad.exe (PID: 7820)
- cmd.exe (PID: 1452)
- notepad++.exe (PID: 2852)
- PROJECT_FOR_SHREE_RAM.exe (PID: 7544)
- cmd.exe (PID: 6468)
- JAI_SHREE_RAM.exe (PID: 7800)
- PROJECT_FOR_SHREE_RAM.exe (PID: 7336)
Reads the software policy settings
- slui.exe (PID: 8068)
- slui.exe (PID: 924)
Executable content was dropped or overwritten
- WinRAR.exe (PID: 2040)
- msedge.exe (PID: 5500)
The sample compiled with english language support
- WinRAR.exe (PID: 2040)
- msedge.exe (PID: 5500)
Reads security settings of Internet Explorer
- notepad.exe (PID: 7820)
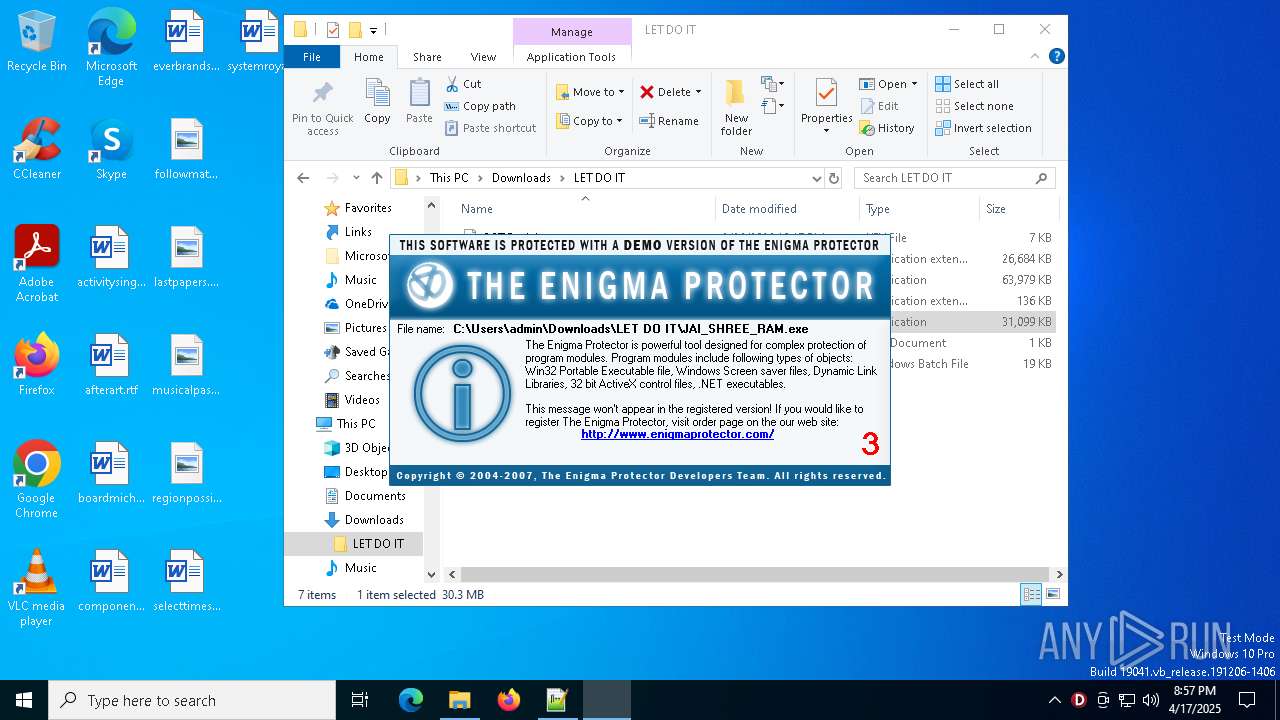
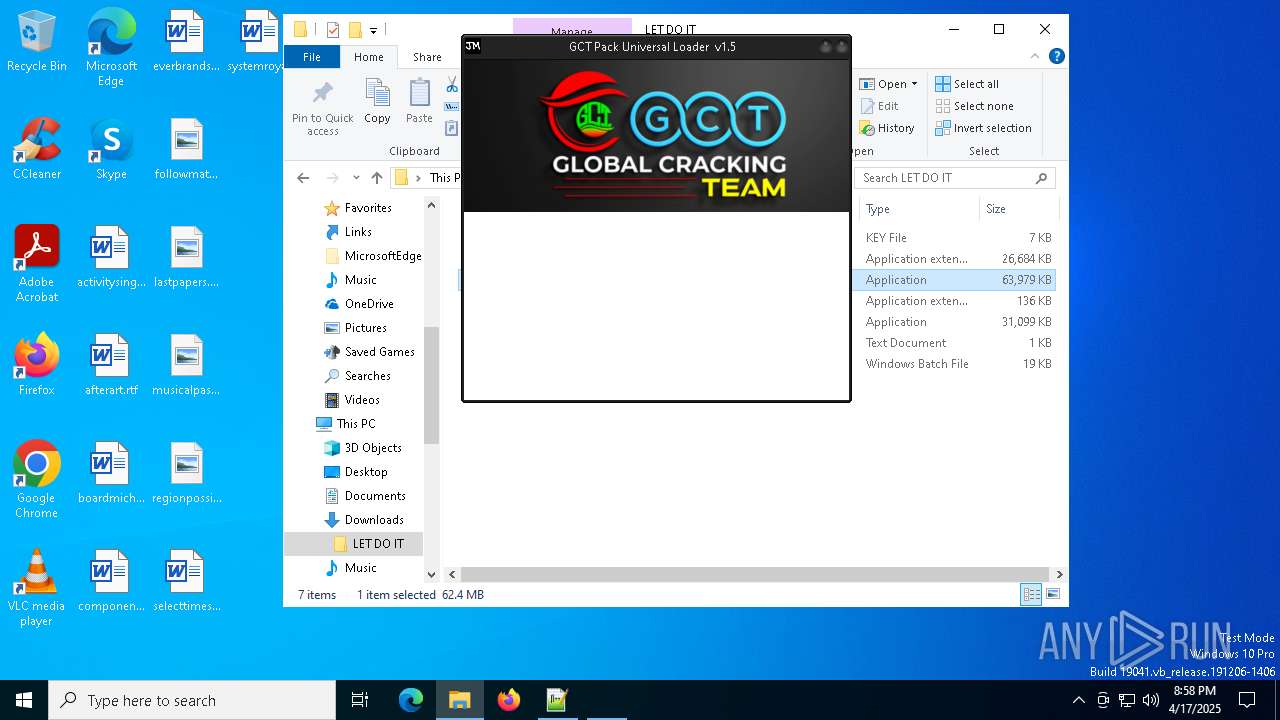
Compiled with Borland Delphi (YARA)
- PROJECT_FOR_SHREE_RAM.exe (PID: 5156)
- PROJECT_FOR_SHREE_RAM.exe (PID: 7336)
- JAI_SHREE_RAM.exe (PID: 8132)
- evbB5F5.tmp (PID: 6136)
- evbCDE8.tmp (PID: 4276)
Checks proxy server information
- slui.exe (PID: 924)
Create files in a temporary directory
- JAI_SHREE_RAM.exe (PID: 8132)
- evbB5F5.tmp (PID: 6136)
- evbCDE8.tmp (PID: 4276)
Process checks computer location settings
- JAI_SHREE_RAM.exe (PID: 8132)
Reads the machine GUID from the registry
- evbB5F5.tmp (PID: 6136)
- evbCDE8.tmp (PID: 4276)
VMProtect protector has been detected
- JAI_SHREE_RAM.exe (PID: 8132)
- evbB5F5.tmp (PID: 6136)
- evbCDE8.tmp (PID: 4276)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
231
Monitored processes
93
Malicious processes
1
Suspicious processes
2
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 632 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=6820 --field-trial-handle=2348,i,12967683653973425576,7588442327609758248,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 736 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --no-startup-window | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | msedge.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Version: 122.0.2365.59 Modules
| |||||||||||||||
| 744 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=edge_collections.mojom.CollectionsDataManager --lang=en-US --service-sandbox-type=collections --no-appcompat-clear --mojo-platform-channel-handle=4220 --field-trial-handle=2348,i,12967683653973425576,7588442327609758248,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 780 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=renderer --extension-process --renderer-sub-type=extension --no-appcompat-clear --lang=en-US --js-flags=--ms-user-locale= --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=5 --mojo-platform-channel-handle=3204 --field-trial-handle=2388,i,12541544780086140609,15139165665113770159,262144 --variations-seed-version /prefetch:2 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 924 | C:\WINDOWS\System32\slui.exe -Embedding | C:\Windows\System32\slui.exe | svchost.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Activation Client Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1164 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=gpu-process --disable-gpu-sandbox --use-gl=disabled --gpu-vendor-id=5140 --gpu-device-id=140 --gpu-sub-system-id=0 --gpu-revision=0 --gpu-driver-version=10.0.19041.3636 --no-appcompat-clear --gpu-preferences=WAAAAAAAAADoAAAMAAAAAAAAAAAAAAAAAABgAAAAAAA4AAAAAAAAAAAAAABEAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAGAAAAAAAAAAYAAAAAAAAAAgAAAAAAAAACAAAAAAAAAAIAAAAAAAAAA== --mojo-platform-channel-handle=916 --field-trial-handle=2348,i,12967683653973425576,7588442327609758248,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 1452 | C:\WINDOWS\system32\cmd.exe /c ""C:\Users\admin\Downloads\LET DO IT\Setup file.bat" " | C:\Windows\System32\cmd.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1568 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=data_decoder.mojom.DataDecoderService --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=6992 --field-trial-handle=2348,i,12967683653973425576,7588442327609758248,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 1912 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --no-appcompat-clear --mojo-platform-channel-handle=5452 --field-trial-handle=2388,i,12541544780086140609,15139165665113770159,262144 --variations-seed-version /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 122.0.2365.59 Modules
| |||||||||||||||
| 2040 | "C:\Program Files\WinRAR\WinRAR.exe" x -iext -ow -ver -- "C:\Users\admin\Downloads\LET DO IT.rar" "C:\Users\admin\Downloads\LET DO IT\" | C:\Program Files\WinRAR\WinRAR.exe | explorer.exe | ||||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.91.0 Modules
| |||||||||||||||
Total events
13 474
Read events
13 369
Write events
105
Delete events
0
Modification events
| (PID) Process: | (6048) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1693682860-607145093-2874071422-1001 |
Value: C5F953E295912F00 | |||
| (PID) Process: | (6048) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1693682860-607145093-2874071422-1001 |
Value: D07076E295912F00 | |||
| (PID) Process: | (6048) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\262794 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {770C4FF5-8C8C-4B24-8315-69B86E187DEE} | |||
| (PID) Process: | (6048) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (6048) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (6048) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (6048) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Edge\StabilityMetrics |
| Operation: | write | Name: | user_experience_metrics.stability.exited_cleanly |
Value: 0 | |||
| (PID) Process: | (6048) msedge.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Microsoft\EdgeUpdate\ClientStateMedium\{56EB18F8-B008-4CBD-B6D2-8C97FE7E9062}\LastWasDefault |
| Operation: | write | Name: | S-1-5-21-1693682860-607145093-2874071422-1001 |
Value: CCC0D7E295912F00 | |||
| (PID) Process: | (6048) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\262794 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {7B6D26A0-FA84-48D8-B25C-DFA3AC4C452A} | |||
| (PID) Process: | (6048) msedge.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\WindowProperties\262794 |
| Operation: | write | Name: | WindowTabManagerFileMappingId |
Value: {A983D520-598F-4E3C-8B74-9F20FB09DB5C} | |||
Executable files
84
Suspicious files
406
Text files
114
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 6048 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old~RF10c7c6.TMP | — | |
MD5:— | SHA256:— | |||
| 6048 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old~RF10c7d6.TMP | — | |
MD5:— | SHA256:— | |||
| 6048 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\parcel_tracking_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6048 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\discounts_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6048 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old~RF10c834.TMP | — | |
MD5:— | SHA256:— | |||
| 6048 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\PersistentOriginTrials\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6048 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old~RF10c853.TMP | — | |
MD5:— | SHA256:— | |||
| 6048 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6048 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old~RF10c8b1.TMP | — | |
MD5:— | SHA256:— | |||
| 6048 | msedge.exe | C:\Users\admin\AppData\Local\Microsoft\Edge\User Data\Default\EdgePushStorageWithConnectTokenAndKey\LOG.old | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
44
TCP/UDP connections
112
DNS requests
102
Threats
29
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
— | — | GET | 200 | 23.216.77.43:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | DE | binary | 825 b | whitelisted |
7908 | SIHClient.exe | GET | 200 | 2.23.181.156:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | DE | binary | 419 b | whitelisted |
6544 | svchost.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | DE | binary | 471 b | whitelisted |
6972 | svchost.exe | HEAD | 200 | 208.89.74.23:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/fb6dd03b-99d7-4cc8-a878-91c8e655c2d3?P1=1745356200&P2=404&P3=2&P4=Roc5g2IPFQpFv%2fhWMouBDzXmR1O58x9RO0fXwifLbmXkBOI4kwGPaqe7eIWeRmBlQ0S%2b8C9KehNROuaGxd9MEQ%3d%3d | US | — | — | whitelisted |
6972 | svchost.exe | GET | 206 | 208.89.74.23:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/fb6dd03b-99d7-4cc8-a878-91c8e655c2d3?P1=1745356200&P2=404&P3=2&P4=Roc5g2IPFQpFv%2fhWMouBDzXmR1O58x9RO0fXwifLbmXkBOI4kwGPaqe7eIWeRmBlQ0S%2b8C9KehNROuaGxd9MEQ%3d%3d | US | compressed | 235 b | whitelisted |
6972 | svchost.exe | GET | 206 | 208.89.74.23:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/23e5dd61-e224-4d56-858f-6ee086574ada?P1=1745356203&P2=404&P3=2&P4=X3%2fxlFJlq22qpInrZId3OkU2i6Y91MjuUIyWLasdXn7t4FgeooEWPoi%2fDmcKTw%2b5TT25ioM7S9%2fCzhH0rtEMVw%3d%3d | US | binary | 10.5 Kb | whitelisted |
6972 | svchost.exe | GET | 206 | 208.89.74.23:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/fb6dd03b-99d7-4cc8-a878-91c8e655c2d3?P1=1745356200&P2=404&P3=2&P4=Roc5g2IPFQpFv%2fhWMouBDzXmR1O58x9RO0fXwifLbmXkBOI4kwGPaqe7eIWeRmBlQ0S%2b8C9KehNROuaGxd9MEQ%3d%3d | US | binary | 1.09 Kb | whitelisted |
6972 | svchost.exe | GET | 206 | 208.89.74.23:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/23e5dd61-e224-4d56-858f-6ee086574ada?P1=1745356203&P2=404&P3=2&P4=X3%2fxlFJlq22qpInrZId3OkU2i6Y91MjuUIyWLasdXn7t4FgeooEWPoi%2fDmcKTw%2b5TT25ioM7S9%2fCzhH0rtEMVw%3d%3d | US | binary | 5.00 Kb | whitelisted |
6972 | svchost.exe | HEAD | 200 | 208.89.74.23:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/23e5dd61-e224-4d56-858f-6ee086574ada?P1=1745356203&P2=404&P3=2&P4=X3%2fxlFJlq22qpInrZId3OkU2i6Y91MjuUIyWLasdXn7t4FgeooEWPoi%2fDmcKTw%2b5TT25ioM7S9%2fCzhH0rtEMVw%3d%3d | US | compressed | 235 b | whitelisted |
6972 | svchost.exe | GET | 206 | 208.89.74.23:80 | http://msedge.b.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/68591036-2289-4858-9f7f-9149e89c8a08?P1=1745356201&P2=404&P3=2&P4=NZ%2fMmKxcAWWvlN8AysvukkvThtODKxPMKkUPPiNedADfqb85xyUtiO4MDBgQ9GenUjblOaoXPIRetHB31nkAiA%3d%3d | US | binary | 45.5 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
— | — | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
— | — | 23.216.77.43:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
6048 | msedge.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
7232 | msedge.exe | 13.107.42.16:443 | config.edge.skype.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
7232 | msedge.exe | 31.216.145.5:443 | mega.nz | Datacenter Luxembourg S.A. | LU | whitelisted |
7232 | msedge.exe | 150.171.28.11:443 | edge.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
7232 | msedge.exe | 13.107.6.158:443 | business.bing.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
7232 | msedge.exe | 13.107.246.45:443 | edge-mobile-static.azureedge.net | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
3216 | svchost.exe | 172.211.123.248:443 | client.wns.windows.com | MICROSOFT-CORP-MSN-AS-BLOCK | FR | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
config.edge.skype.com |
| whitelisted |
mega.nz |
| whitelisted |
edge.microsoft.com |
| whitelisted |
business.bing.com |
| whitelisted |
edge-mobile-static.azureedge.net |
| whitelisted |
client.wns.windows.com |
| whitelisted |
www.bing.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
7232 | msedge.exe | Misc activity | ET FILE_SHARING File Sharing Related Domain in DNS Lookup (mega .nz) |
7232 | msedge.exe | Misc activity | ET FILE_SHARING File Sharing Domain Observed in TLS SNI (mega .nz) |
7232 | msedge.exe | Misc activity | ET FILE_SHARING File Sharing Related Domain in DNS Lookup (mega .nz) |
7232 | msedge.exe | Misc activity | ET FILE_SHARING Observed DNS Query to Filesharing Service (mega .co .nz) |
7232 | msedge.exe | Misc activity | ET FILE_SHARING Observed DNS Query to Filesharing Service (mega .co .nz) |
7232 | msedge.exe | Misc activity | ET FILE_SHARING File Sharing Domain Observed in TLS SNI (mega .nz) |
7232 | msedge.exe | Misc activity | ET FILE_SHARING Observed DNS Query to Filesharing Service (mega .co .nz) |
7232 | msedge.exe | Misc activity | ET FILE_SHARING Observed DNS Query to Filesharing Service (mega .co .nz) |
7232 | msedge.exe | Misc activity | ET FILE_SHARING File Sharing Related Domain in DNS Lookup (mega .nz) |
7232 | msedge.exe | Misc activity | ET FILE_SHARING File Sharing Related Domain in DNS Lookup (mega .nz) |