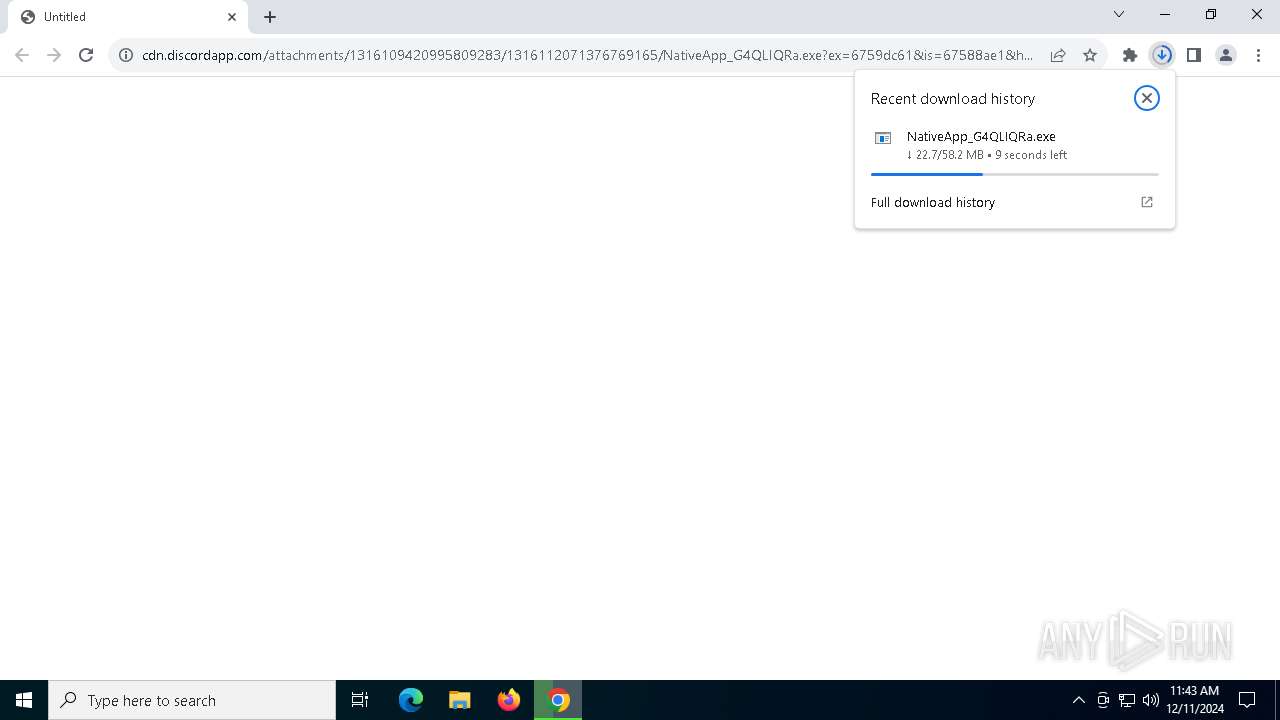
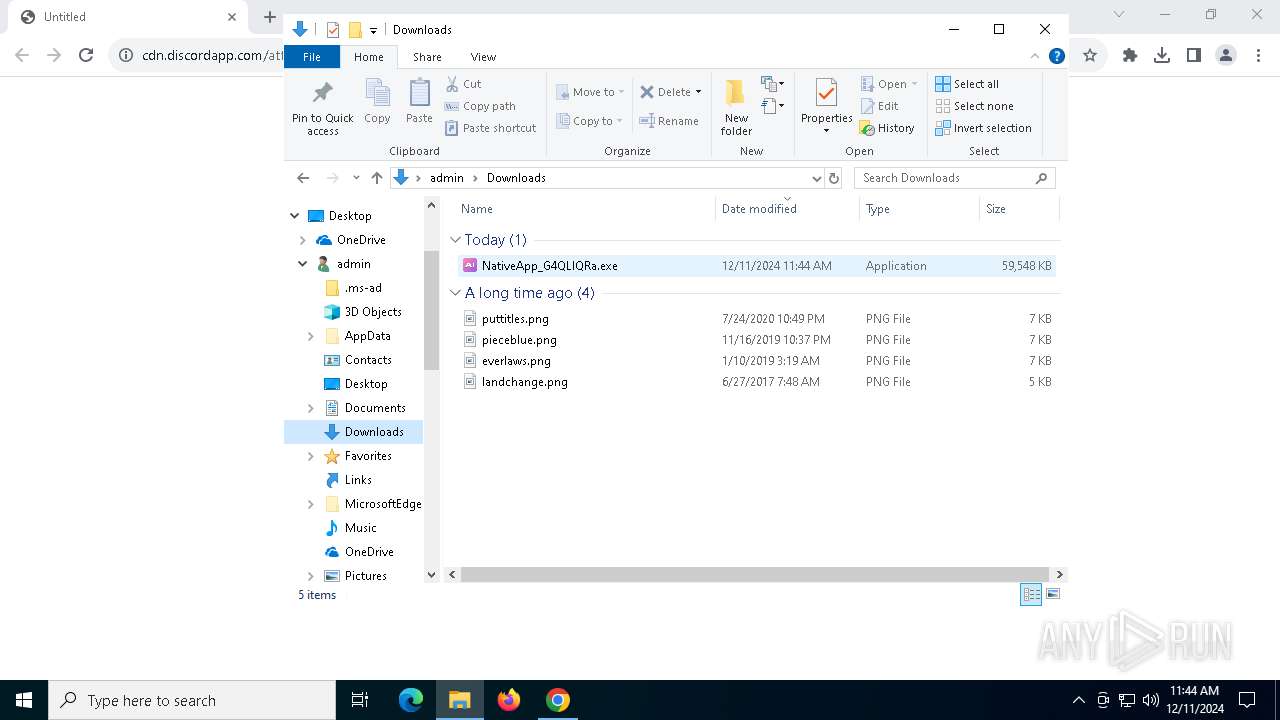
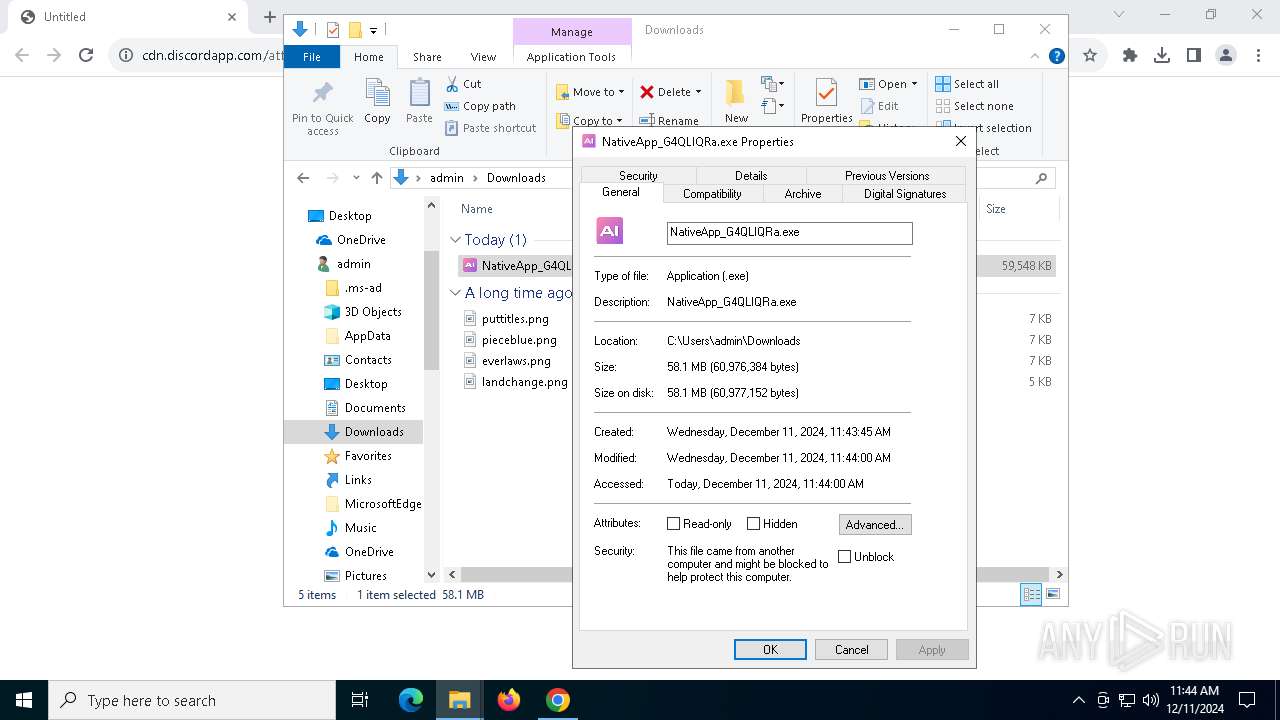
| URL: | https://cdn.discordapp.com/attachments/1316109420995809283/1316112071376769165/NativeApp_G4QLIQRa.exe?ex=6759dc61&is=67588ae1&hm=b8f8b70b147eb747dc58599d481dc346e0a336f8e169ca1858537e8f578eb335& |
| Full analysis: | https://app.any.run/tasks/0048f776-dc72-4b75-9952-2e49a6946b68 |
| Verdict: | Malicious activity |
| Analysis date: | December 11, 2024, 11:43:38 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Tags: | |
| Indicators: | |
| MD5: | E6914A3C5F07B7049FA71CFA2FCDBDC9 |
| SHA1: | F0899F97B4204D9B51C4C1A3846ACB0889716CCC |
| SHA256: | 648A888E9E545C3366AC9EC98FDCED9AC03222FDA885C8FF7EDD4541C6140DD3 |
| SSDEEP: | 6:2cry6XPU2c6WKU1nA2MRfYhFSaHdQ6CTZ:2cjU2PWP1RhFSQQ1 |
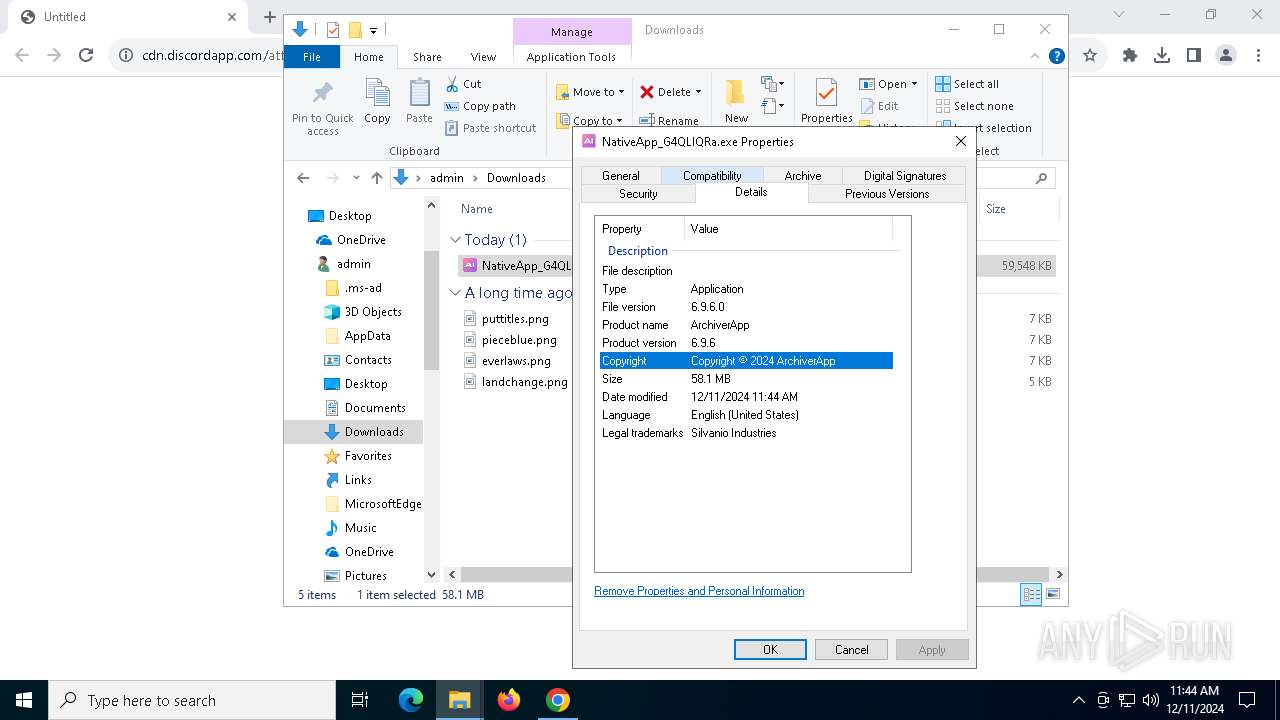
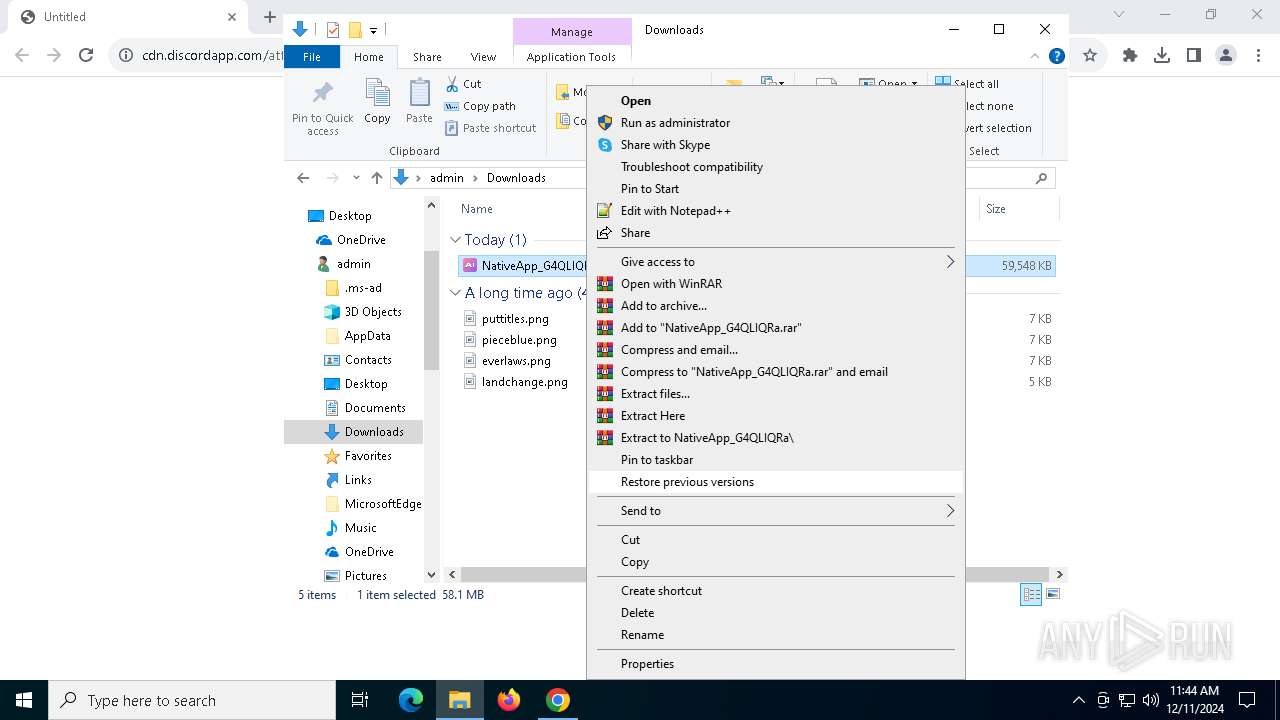
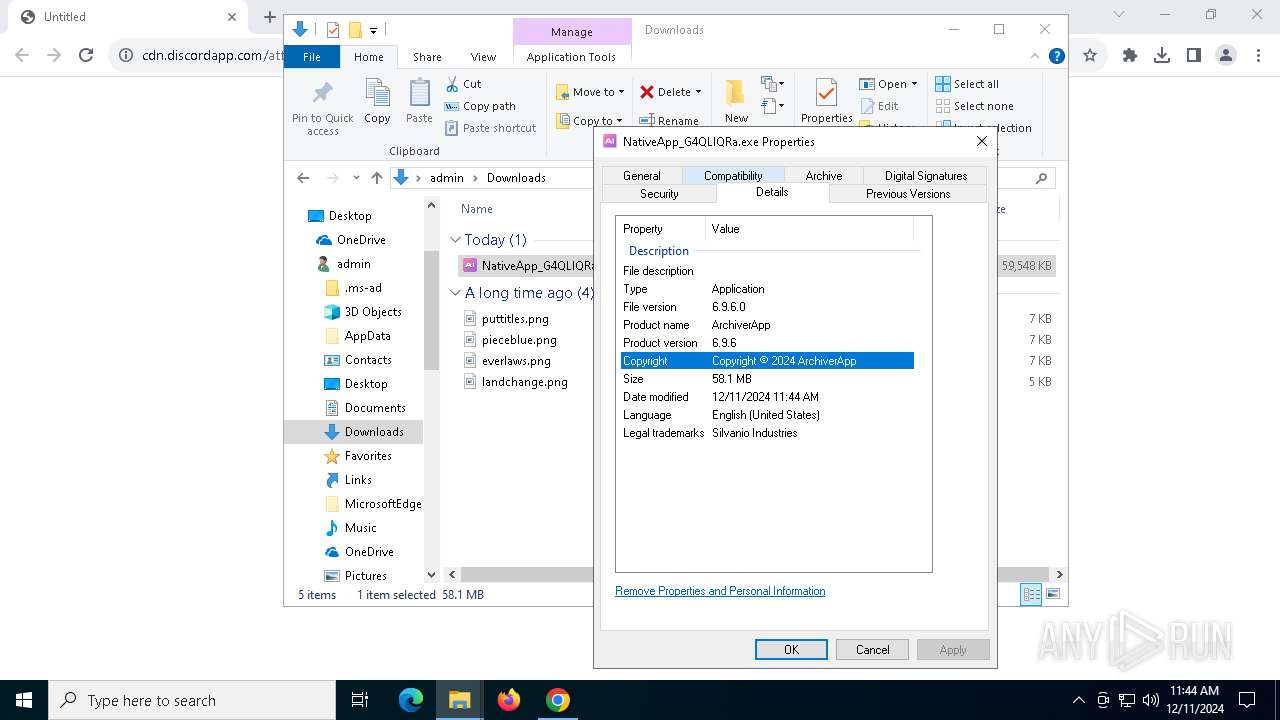
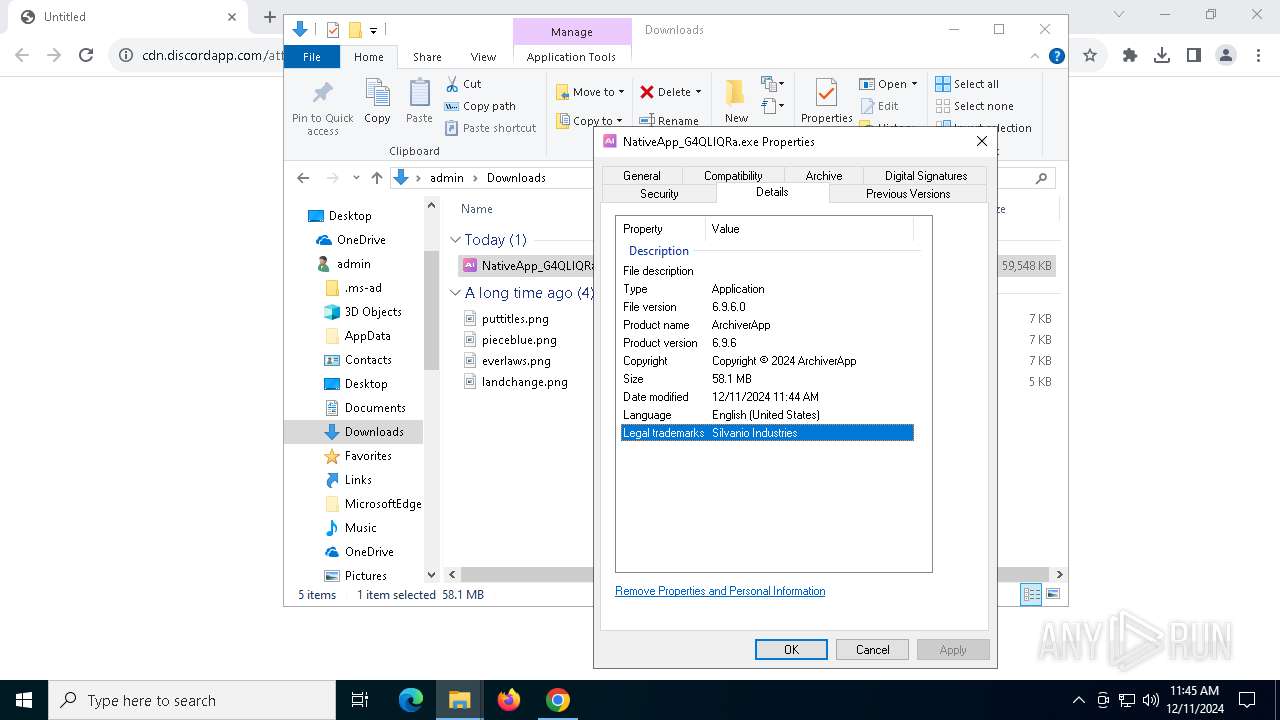
MALICIOUS
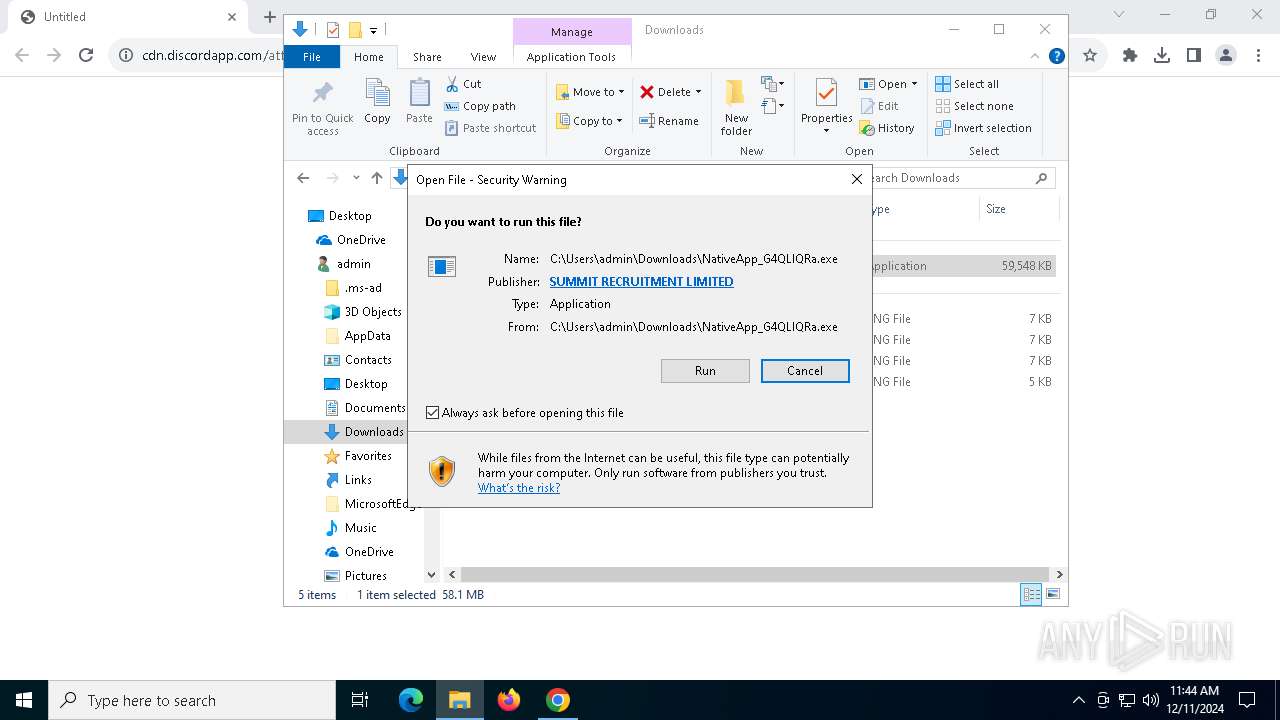
Executing a file with an untrusted certificate
- NativeApp_G4QLIQRa.exe (PID: 1144)
- NativeApp_G4QLIQRa.exe (PID: 2672)
SUSPICIOUS
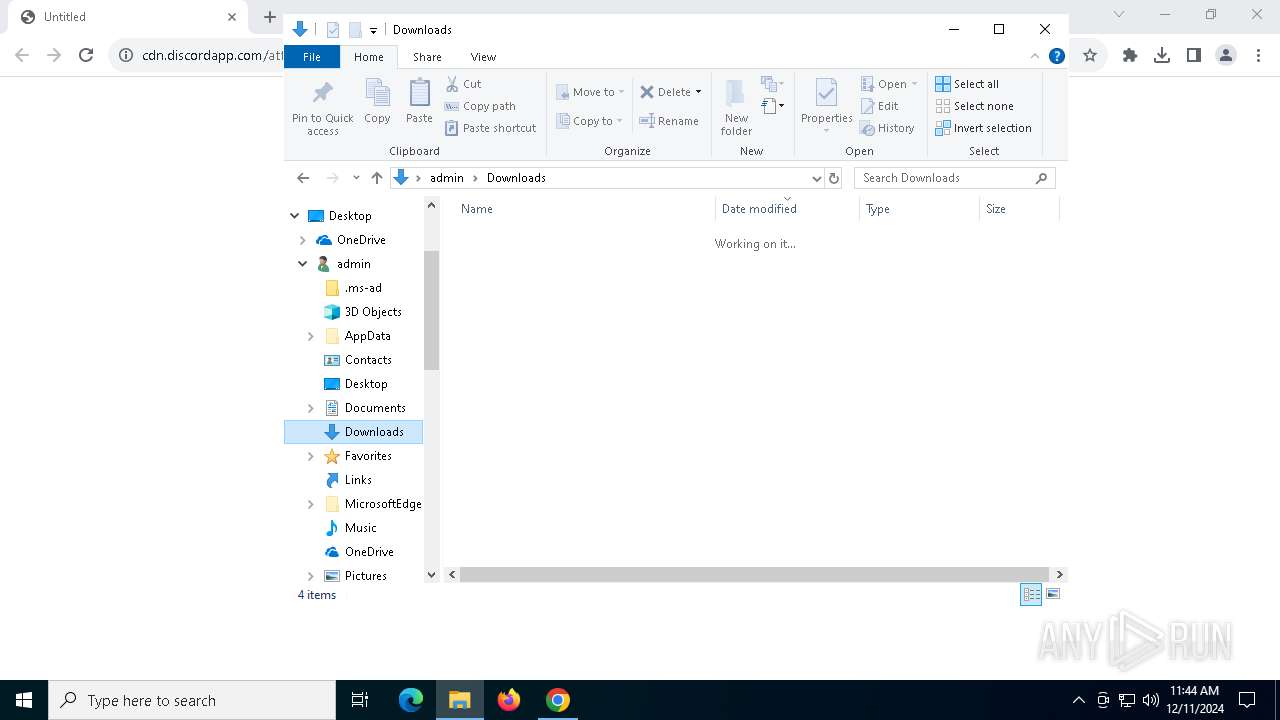
Discord domain found in command line (probably downloading payload)
- chrome.exe (PID: 4052)
Malware-specific behavior (creating "System.dll" in Temp)
- NativeApp_G4QLIQRa.exe (PID: 1144)
- NativeApp_G4QLIQRa.exe (PID: 2672)
Executable content was dropped or overwritten
- NativeApp_G4QLIQRa.exe (PID: 1144)
- NativeApp_G4QLIQRa.exe (PID: 2672)
The process creates files with name similar to system file names
- NativeApp_G4QLIQRa.exe (PID: 1144)
Drops 7-zip archiver for unpacking
- NativeApp_G4QLIQRa.exe (PID: 1144)
- NativeApp_G4QLIQRa.exe (PID: 2672)
Starts CMD.EXE for commands execution
- ArchiverApp.exe (PID: 3840)
- ArchiverApp.exe (PID: 6620)
Starts application with an unusual extension
- cmd.exe (PID: 5268)
- cmd.exe (PID: 6096)
Process drops legitimate windows executable
- NativeApp_G4QLIQRa.exe (PID: 1144)
- NativeApp_G4QLIQRa.exe (PID: 2672)
Application launched itself
- ArchiverApp.exe (PID: 3840)
- ArchiverApp.exe (PID: 6620)
INFO
Application launched itself
- chrome.exe (PID: 4052)
The sample compiled with english language support
- chrome.exe (PID: 4052)
- NativeApp_G4QLIQRa.exe (PID: 1144)
- NativeApp_G4QLIQRa.exe (PID: 2672)
Attempting to use instant messaging service
- chrome.exe (PID: 6428)
Executable content was dropped or overwritten
- chrome.exe (PID: 4052)
The process uses the downloaded file
- chrome.exe (PID: 2928)
Checks supported languages
- NativeApp_G4QLIQRa.exe (PID: 1144)
- ArchiverApp.exe (PID: 3840)
- chcp.com (PID: 4144)
- ArchiverApp.exe (PID: 5728)
- ArchiverApp.exe (PID: 3652)
- NativeApp_G4QLIQRa.exe (PID: 2672)
- ArchiverApp.exe (PID: 6620)
- ArchiverApp.exe (PID: 6804)
- ArchiverApp.exe (PID: 4140)
- chcp.com (PID: 1400)
Reads the computer name
- NativeApp_G4QLIQRa.exe (PID: 1144)
- ArchiverApp.exe (PID: 3840)
- ArchiverApp.exe (PID: 4140)
- ArchiverApp.exe (PID: 5728)
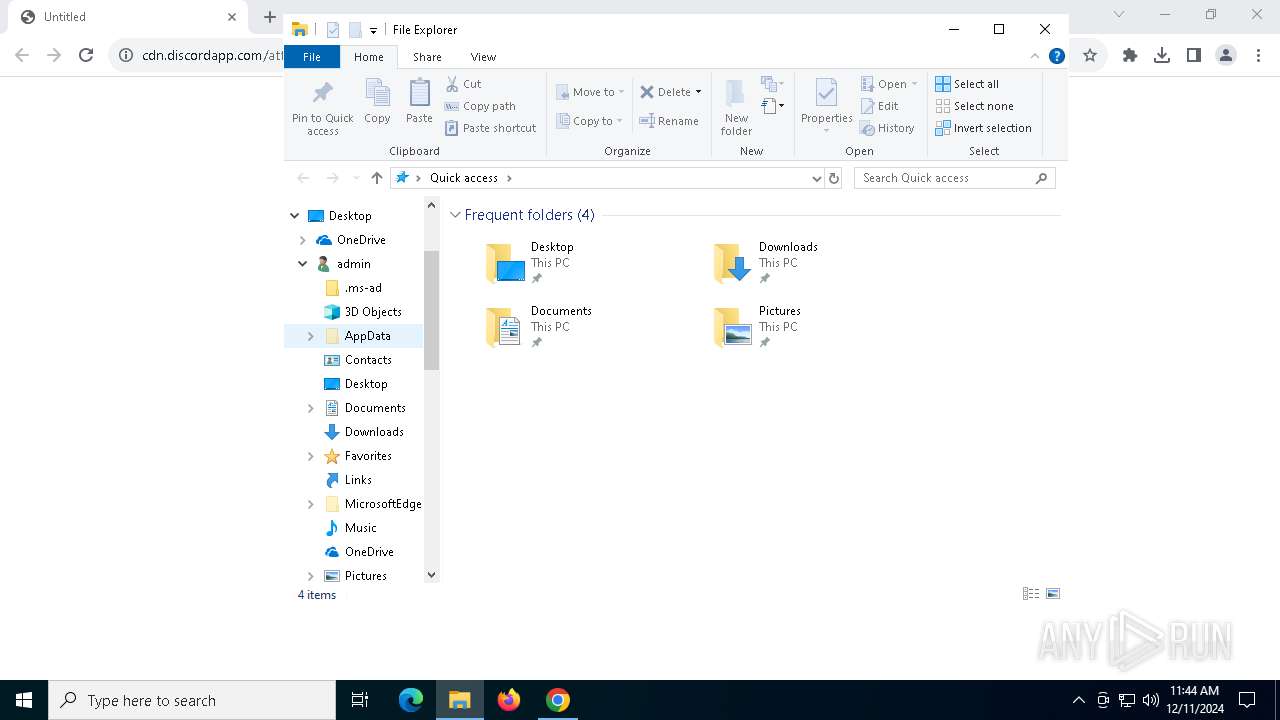
Create files in a temporary directory
- NativeApp_G4QLIQRa.exe (PID: 1144)
- NativeApp_G4QLIQRa.exe (PID: 2672)
Changes the display of characters in the console
- cmd.exe (PID: 5268)
- cmd.exe (PID: 6096)
Reads the machine GUID from the registry
- ArchiverApp.exe (PID: 3840)
- ArchiverApp.exe (PID: 6620)
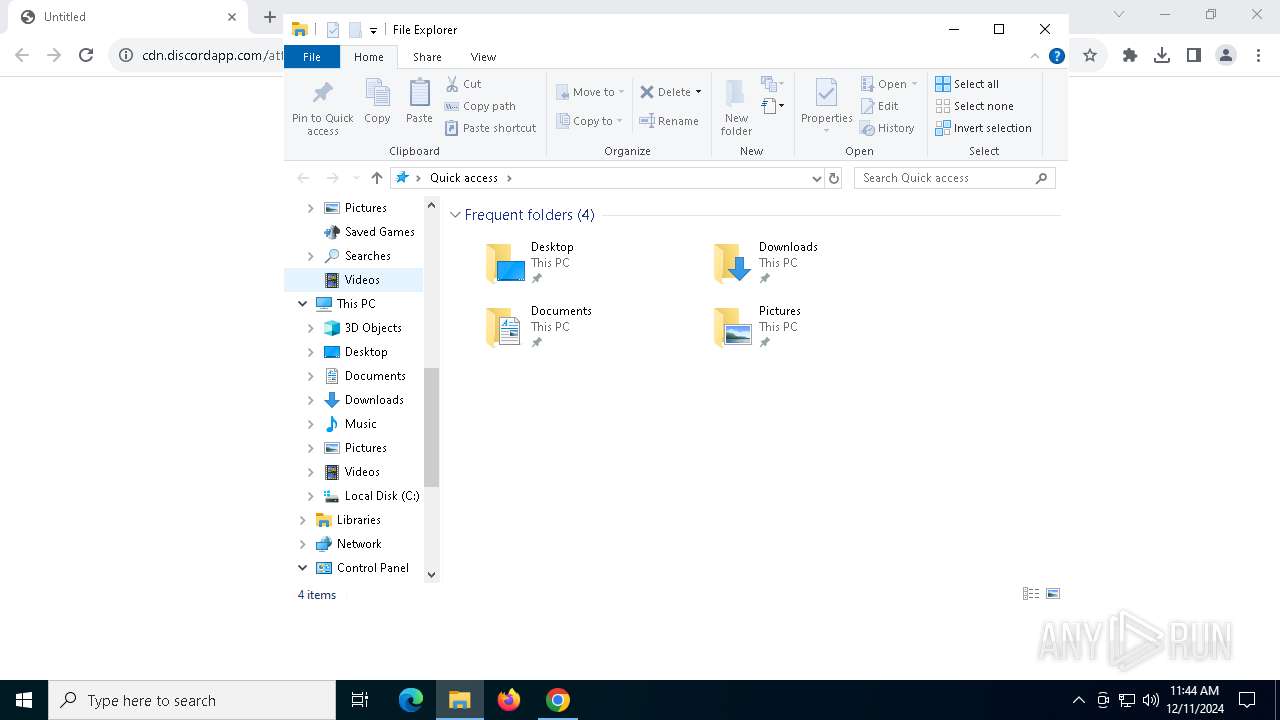
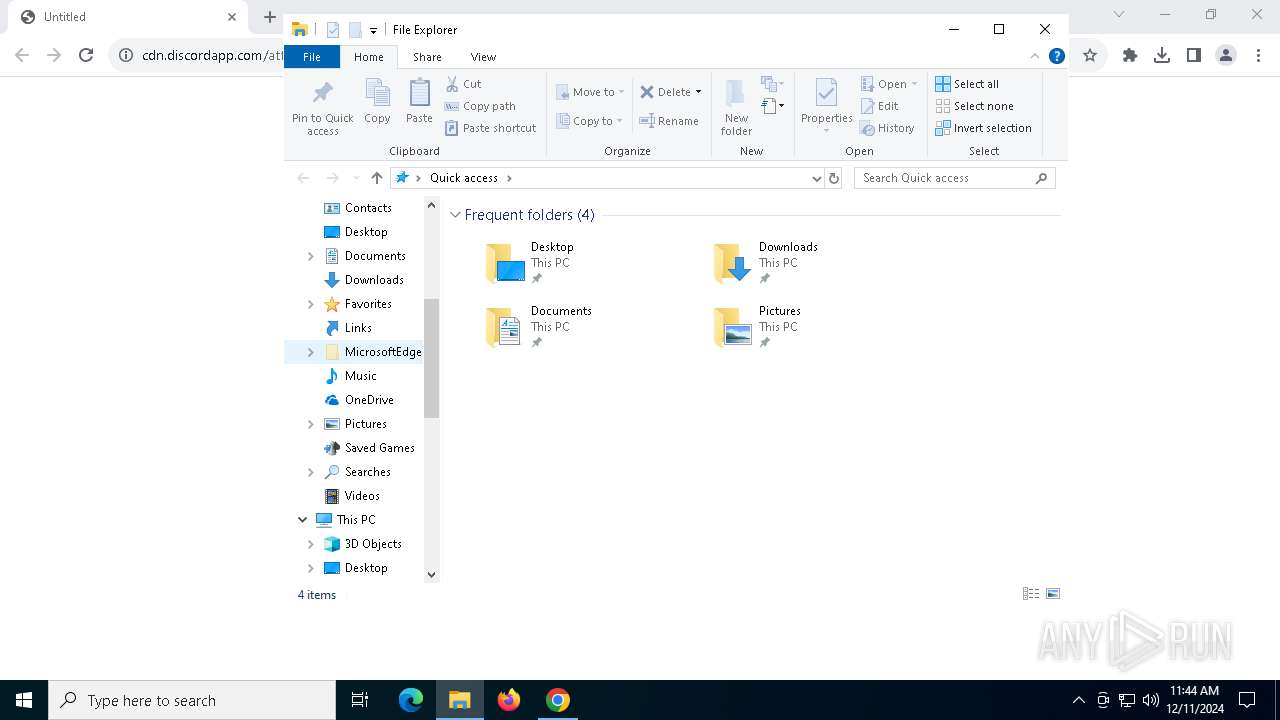
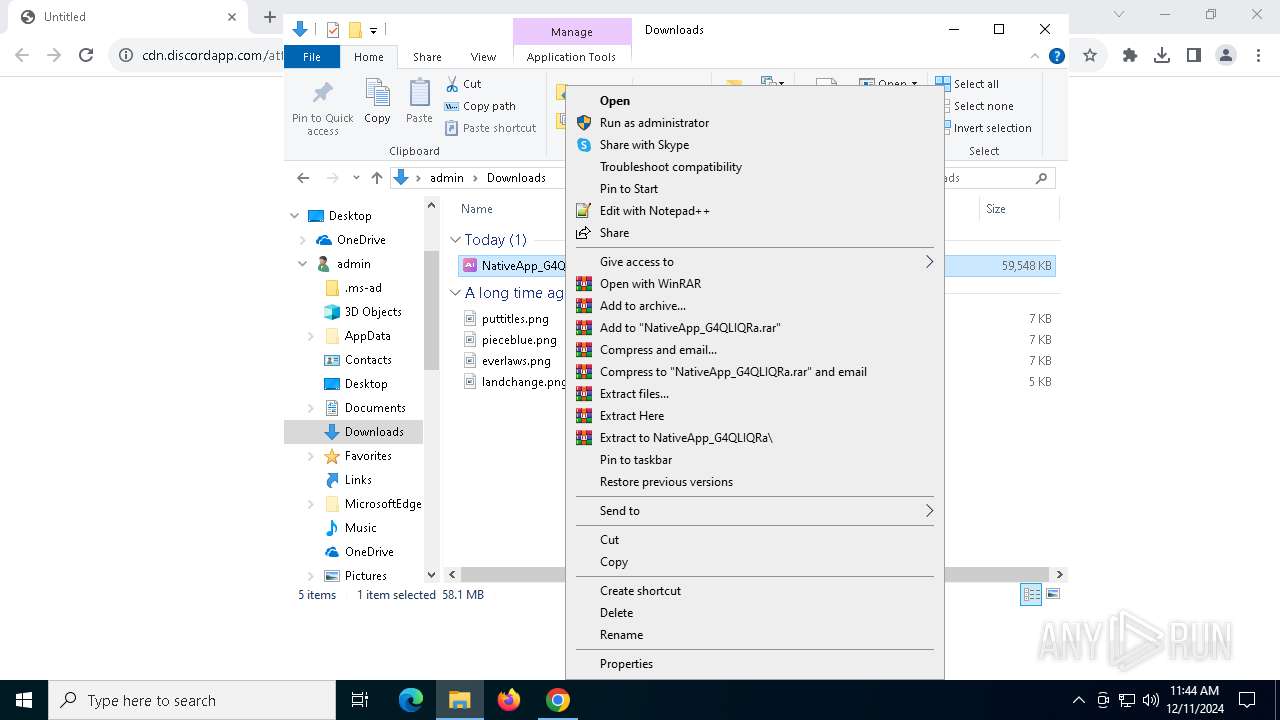
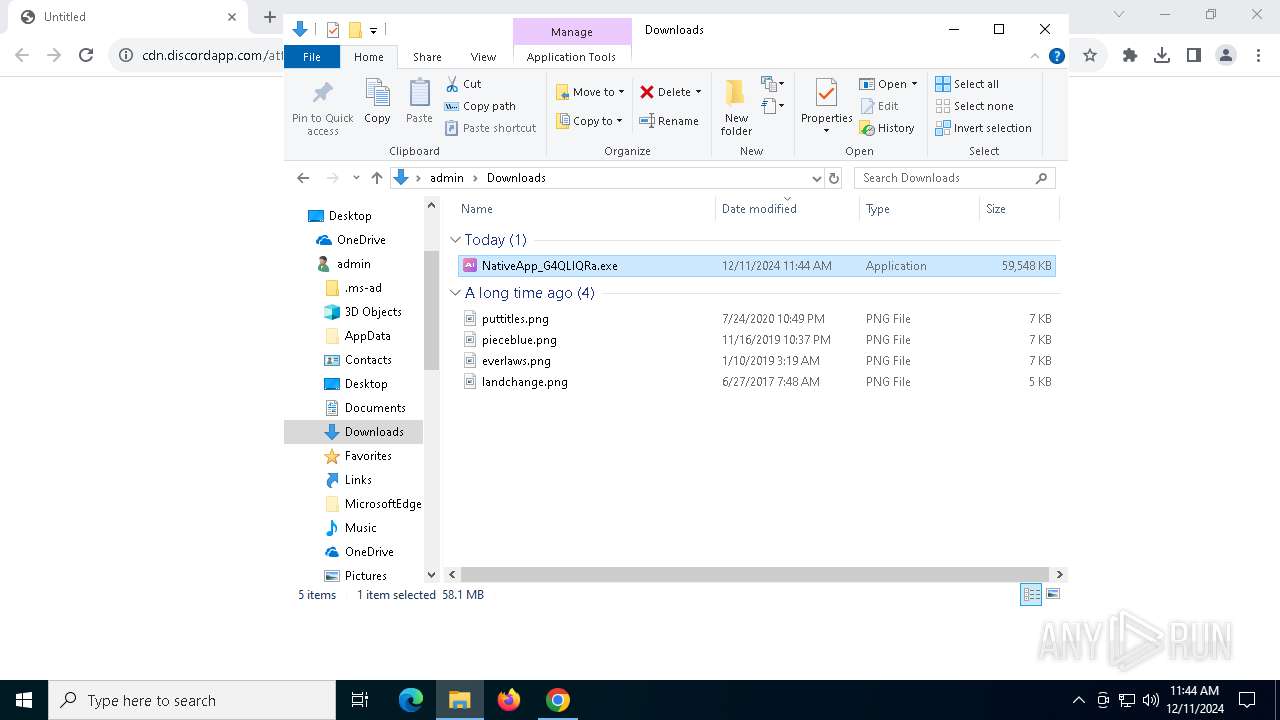
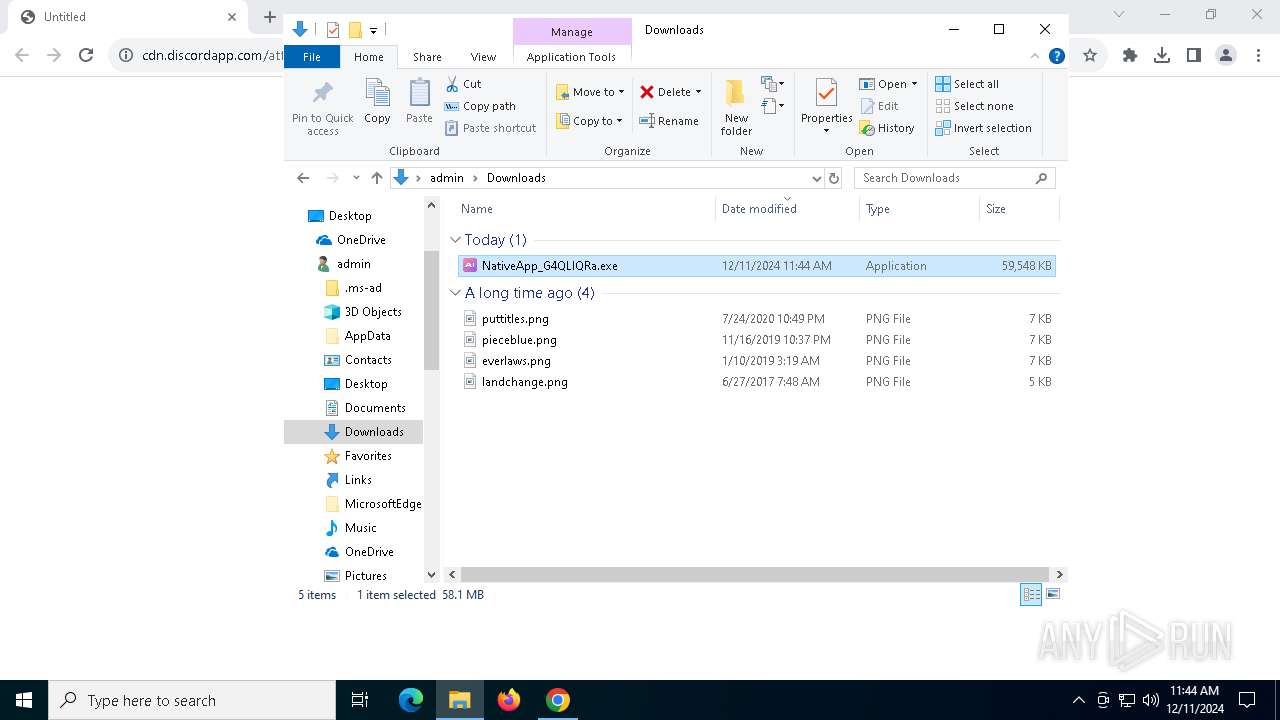
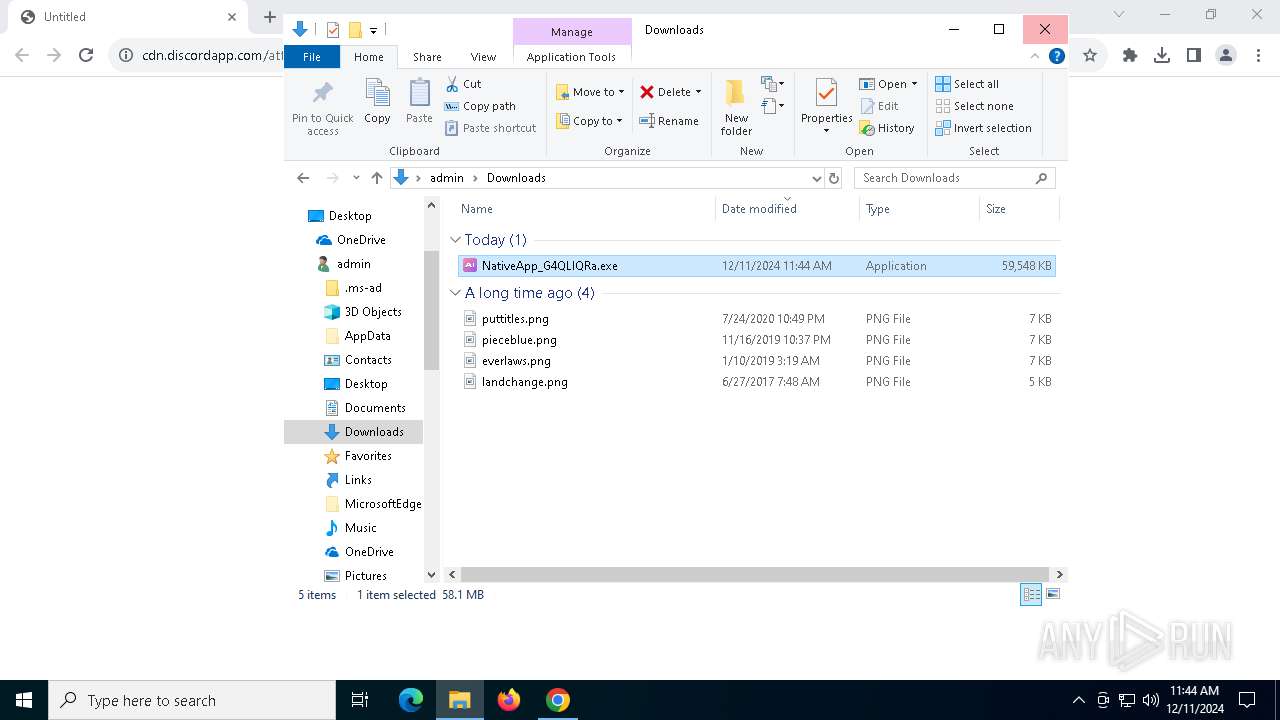
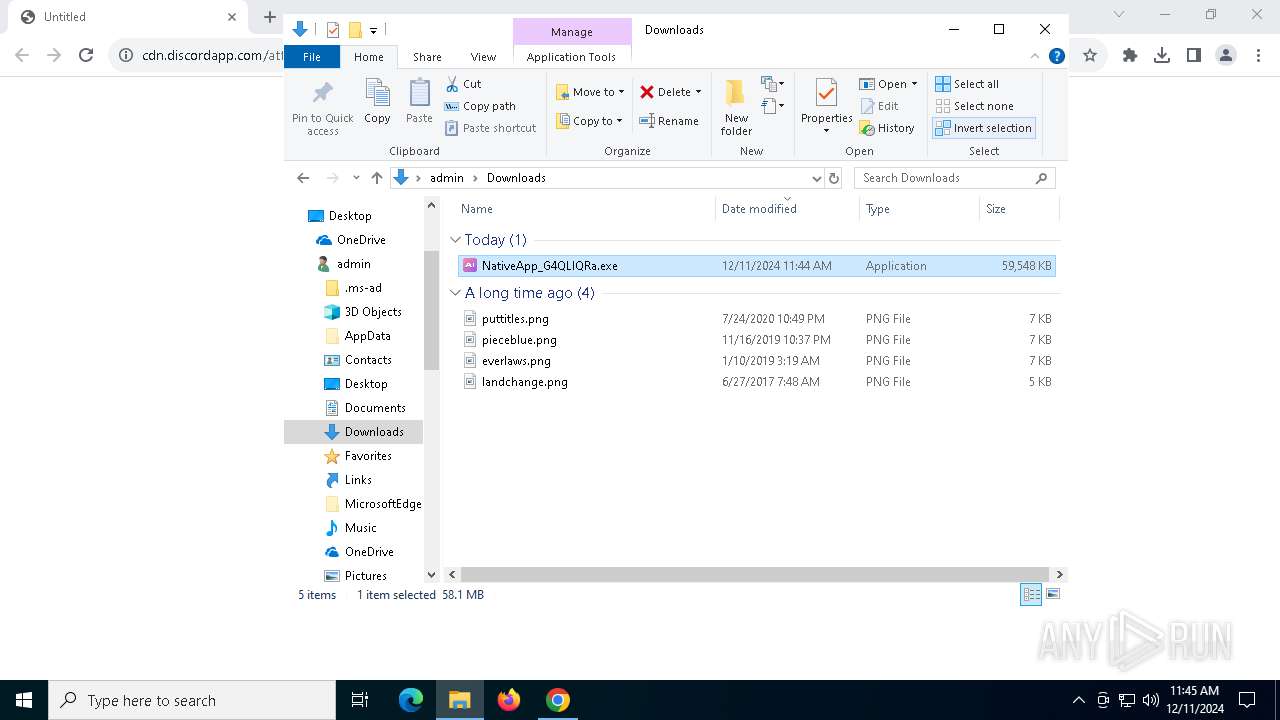
Manual execution by a user
- NativeApp_G4QLIQRa.exe (PID: 2672)
Creates files or folders in the user directory
- ArchiverApp.exe (PID: 3840)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
158
Monitored processes
28
Malicious processes
3
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1144 | "C:\Users\admin\Downloads\NativeApp_G4QLIQRa.exe" | C:\Users\admin\Downloads\NativeApp_G4QLIQRa.exe | chrome.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Version: 7.0.0 Modules
| |||||||||||||||
| 1400 | chcp | C:\Windows\SysWOW64\chcp.com | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Change CodePage Utility Exit code: 0 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2672 | "C:\Users\admin\Downloads\NativeApp_G4QLIQRa.exe" | C:\Users\admin\Downloads\NativeApp_G4QLIQRa.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Version: 7.0.0 Modules
| |||||||||||||||
| 2756 | C:\WINDOWS\System32\rundll32.exe C:\WINDOWS\System32\shell32.dll,SHCreateLocalServerRunDll {9aa46009-3ce0-458a-a354-715610a075e6} -Embedding | C:\Windows\System32\rundll32.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows host process (Rundll32) Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2800 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2928 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=quarantine.mojom.Quarantine --lang=en-US --service-sandbox-type=none --disable-quic --no-appcompat-clear --mojo-platform-channel-handle=5552 --field-trial-handle=1944,i,2668647170223072828,11399842024141675477,262144 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction --variations-seed-version /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 122.0.6261.70 Modules
| |||||||||||||||
| 3652 | "C:\Users\admin\AppData\Local\Temp\2q1oo5RcYTQ2dy9Id93vQ9yupDA\ArchiverApp.exe" --type=utility --utility-sub-type=network.mojom.NetworkService --lang=en-US --service-sandbox-type=none --user-data-dir="C:\Users\admin\AppData\Roaming\bmzyxxofvcrvmhzr" --mojo-platform-channel-handle=2148 --field-trial-handle=1904,i,9315788440001652124,13518770970503920700,131072 --disable-features=SpareRendererForSitePerProcess,WinRetrieveSuggestionsOnlyOnDemand /prefetch:8 | C:\Users\admin\AppData\Local\Temp\2q1oo5RcYTQ2dy9Id93vQ9yupDA\ArchiverApp.exe | — | ArchiverApp.exe | |||||||||||
User: admin Company: GitHub, Inc. Integrity Level: MEDIUM Description: ArchiverApp Version: 7.0.0 Modules
| |||||||||||||||
| 3840 | C:\Users\admin\AppData\Local\Temp\2q1oo5RcYTQ2dy9Id93vQ9yupDA\ArchiverApp.exe | C:\Users\admin\AppData\Local\Temp\2q1oo5RcYTQ2dy9Id93vQ9yupDA\ArchiverApp.exe | NativeApp_G4QLIQRa.exe | ||||||||||||
User: admin Company: GitHub, Inc. Integrity Level: MEDIUM Description: ArchiverApp Version: 7.0.0 Modules
| |||||||||||||||
| 4052 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --disk-cache-dir=null --disk-cache-size=1 --media-cache-size=1 --disable-gpu-shader-disk-cache --disable-background-networking --disable-features=OptimizationGuideModelDownloading,OptimizationHintsFetching,OptimizationTargetPrediction,OptimizationHints "https://cdn.discordapp.com/attachments/1316109420995809283/1316112071376769165/NativeApp_G4QLIQRa.exe?ex=6759dc61&is=67588ae1&hm=b8f8b70b147eb747dc58599d481dc346e0a336f8e169ca1858537e8f578eb335&" | C:\Program Files\Google\Chrome\Application\chrome.exe | explorer.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Version: 122.0.6261.70 Modules
| |||||||||||||||
| 4140 | "C:\Users\admin\AppData\Local\Temp\2q1oo5RcYTQ2dy9Id93vQ9yupDA\ArchiverApp.exe" --type=utility --utility-sub-type=network.mojom.NetworkService --lang=en-US --service-sandbox-type=none --user-data-dir="C:\Users\admin\AppData\Roaming\bmzyxxofvcrvmhzr" --mojo-platform-channel-handle=2056 --field-trial-handle=1956,i,3724978213196281162,17190360885811503905,131072 --disable-features=SpareRendererForSitePerProcess,WinRetrieveSuggestionsOnlyOnDemand /prefetch:8 | C:\Users\admin\AppData\Local\Temp\2q1oo5RcYTQ2dy9Id93vQ9yupDA\ArchiverApp.exe | — | ArchiverApp.exe | |||||||||||
User: admin Company: GitHub, Inc. Integrity Level: MEDIUM Description: ArchiverApp Version: 7.0.0 Modules
| |||||||||||||||
Total events
10 479
Read events
10 454
Write events
19
Delete events
6
Modification events
| (PID) Process: | (4052) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
| (PID) Process: | (4052) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (4052) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (4052) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (4052) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\StabilityMetrics |
| Operation: | write | Name: | user_experience_metrics.stability.exited_cleanly |
Value: 0 | |||
| (PID) Process: | (2928) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Shell Extensions\Cached |
| Operation: | write | Name: | {2781761E-28E0-4109-99FE-B9D127C57AFE} {56FFCC30-D398-11D0-B2AE-00A0C908FA49} 0xFFFF |
Value: 0100000000000000FA3B6AF8C14BDB01 | |||
| (PID) Process: | (4052) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Common\Rlz\Events\C |
| Operation: | write | Name: | C1I |
Value: 1 | |||
| (PID) Process: | (4052) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Common\Rlz\Events\C |
| Operation: | write | Name: | C2I |
Value: 1 | |||
| (PID) Process: | (4052) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Common\Rlz\Events\C |
| Operation: | write | Name: | C7I |
Value: 1 | |||
| (PID) Process: | (4052) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Common\Rlz\Events\C |
| Operation: | write | Name: | C1S |
Value: 1 | |||
Executable files
31
Suspicious files
339
Text files
27
Unknown types
21
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 4052 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\chrome_cart_db\LOG.old~RF135ebd.TMP | — | |
MD5:— | SHA256:— | |||
| 4052 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\chrome_cart_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 4052 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\parcel_tracking_db\LOG.old~RF135ecd.TMP | — | |
MD5:— | SHA256:— | |||
| 4052 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\parcel_tracking_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 4052 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\PersistentOriginTrials\LOG.old~RF135ecd.TMP | — | |
MD5:— | SHA256:— | |||
| 4052 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\discounts_db\LOG.old~RF135ecd.TMP | — | |
MD5:— | SHA256:— | |||
| 4052 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\coupon_db\LOG.old~RF135ecd.TMP | — | |
MD5:— | SHA256:— | |||
| 4052 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\PersistentOriginTrials\LOG.old | — | |
MD5:— | SHA256:— | |||
| 4052 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\commerce_subscription_db\LOG.old~RF135ecd.TMP | — | |
MD5:— | SHA256:— | |||
| 4052 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\discounts_db\LOG.old | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
23
TCP/UDP connections
124
DNS requests
36
Threats
2
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
— | — | GET | 200 | 2.16.164.18:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
— | — | GET | 200 | 88.221.169.152:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
— | — | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAI5PUjXAkJafLQcAAsO18o%3D | unknown | — | — | whitelisted |
4052 | chrome.exe | GET | 200 | 18.66.147.89:80 | http://ocsps.ssl.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQg3SSkKA74hABkhmlBtJTz8w3hlAQU%2BWC71OPVNPa49QaAJadz20ZpqJ4CEEJLalPOx2YUHCpjsaUcQQQ%3D | unknown | — | — | whitelisted |
4052 | chrome.exe | GET | 200 | 18.66.147.89:80 | http://ocsps.ssl.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSoEwb5tith0jIBy9frSyNGB1lsAAQUNr1J%2FzEs669qQP6ZwBbtuvxI3V8CEDqcdvgwT3e9Jxkh2ZgvGrY%3D | unknown | — | — | whitelisted |
1176 | svchost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
1476 | SIHClient.exe | GET | 200 | 88.221.169.152:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
5968 | svchost.exe | HEAD | 200 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/ads7ltfl2gw6hxwgakn3sxrkoijq_9.53.0/gcmjkmgdlgnkkcocmoeiminaijmmjnii_9.53.0_all_iky7dhj3jd5su3axccoshyd4xm.crx3 | unknown | — | — | whitelisted |
1476 | SIHClient.exe | GET | 200 | 88.221.169.152:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
6252 | backgroundTaskHost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAn5bsKVVV8kdJ6vHl3O1J0%3D | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
5160 | svchost.exe | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
4712 | MoUsoCoreWorker.exe | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
— | — | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
— | — | 2.16.164.18:80 | crl.microsoft.com | Akamai International B.V. | NL | whitelisted |
— | — | 88.221.169.152:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
5064 | SearchApp.exe | 2.23.209.185:443 | www.bing.com | Akamai International B.V. | GB | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
— | — | 192.229.221.95:80 | ocsp.digicert.com | EDGECAST | US | whitelisted |
4052 | chrome.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
www.bing.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
cdn.discordapp.com |
| shared |
accounts.google.com |
| whitelisted |
go.microsoft.com |
| whitelisted |
login.live.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
6428 | chrome.exe | Misc activity | ET INFO Observed Discord Domain in DNS Lookup (discordapp .com) |
6428 | chrome.exe | Misc activity | ET INFO Observed Discord Domain in DNS Lookup (discordapp .com) |