| File name: | wan-miniport-repair-x64.exe |
| Full analysis: | https://app.any.run/tasks/de4281b1-44b3-4960-9adc-2ffa0fdab385 |
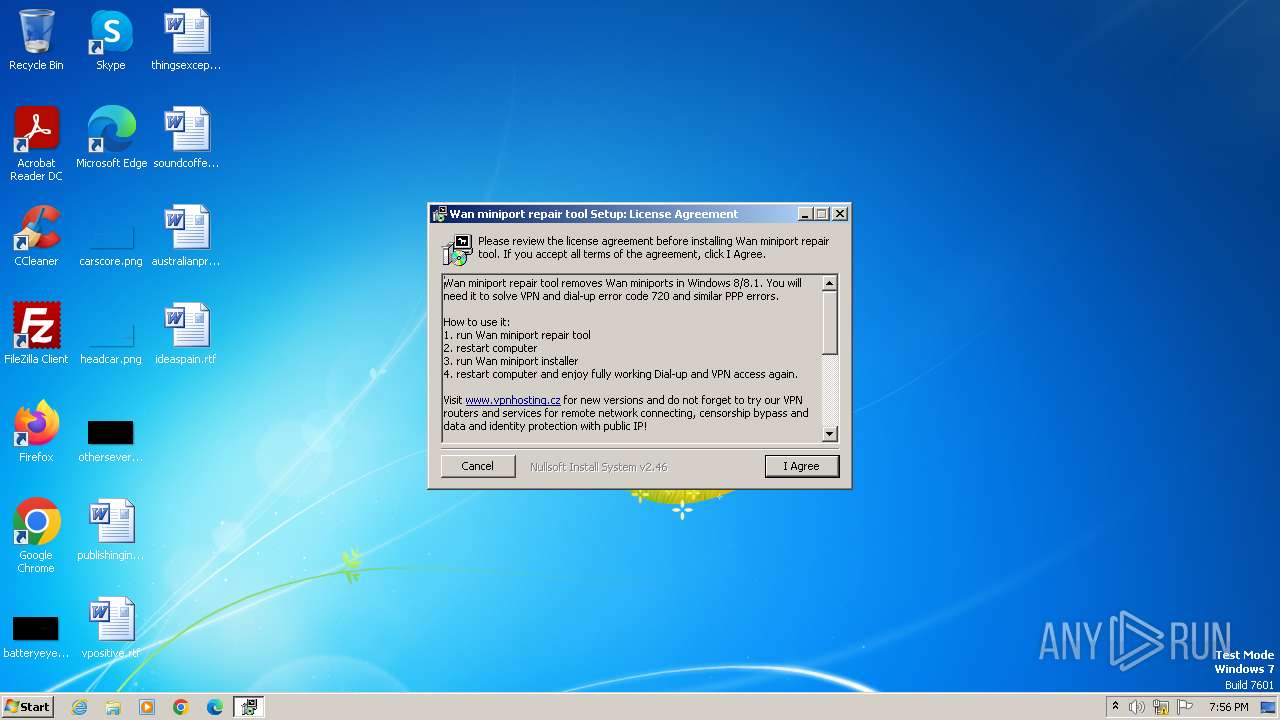
| Verdict: | Malicious activity |
| Analysis date: | November 10, 2023, 19:56:40 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, Nullsoft Installer self-extracting archive |
| MD5: | A9E41DF4320A6F46238DDECF655AF083 |
| SHA1: | 4A10A3B94535B76E395AADF5A93F0C5CCF6B4500 |
| SHA256: | 6486428E347F4E47260AD3243F87F9CCDDDE24A0C05B136190D6D1EEA610CA73 |
| SSDEEP: | 3072:XmtMnJNW8V3D8WwwStjbapdvx4vW4WI7AzzUemkwidSmr7D0:WtMDJVz8WwBpapZuvtZAzokZdSmr7D0 |
MALICIOUS
Changes powershell execution policy (RemoteSigned)
- nsAD20.tmp (PID: 3420)
Drops the executable file immediately after the start
- wan-miniport-repair-x64.exe (PID: 3228)
SUSPICIOUS
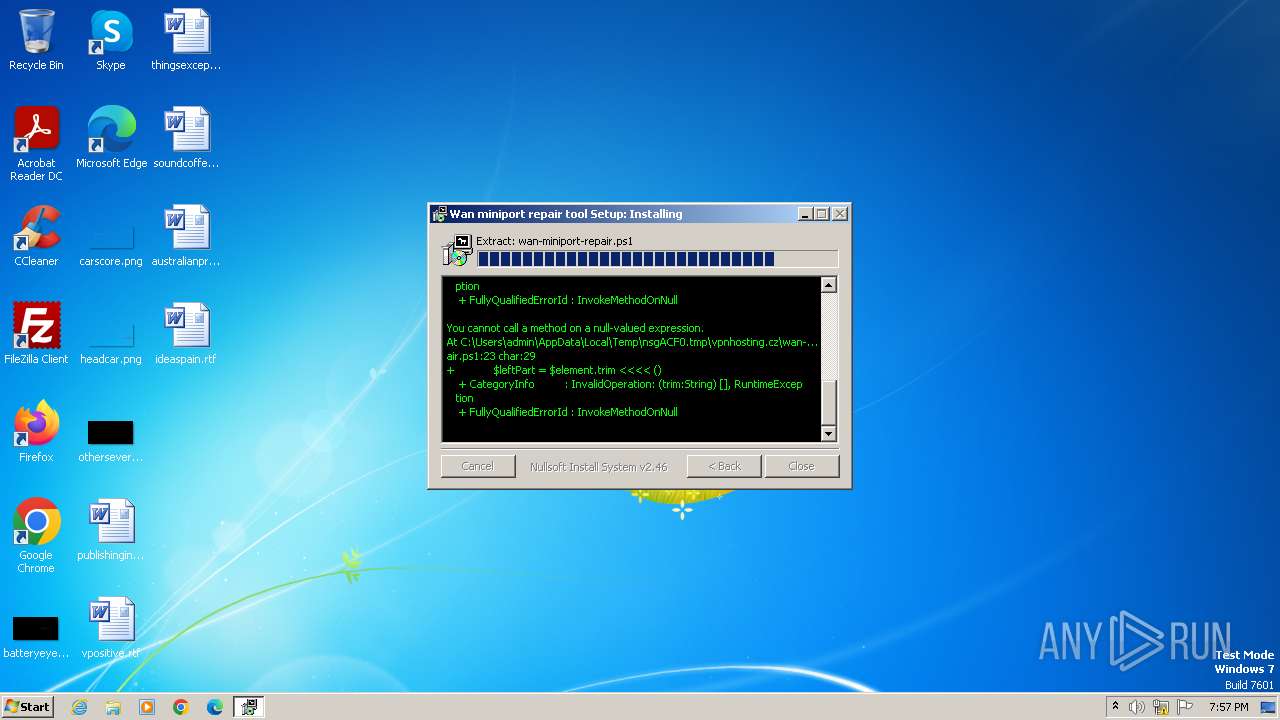
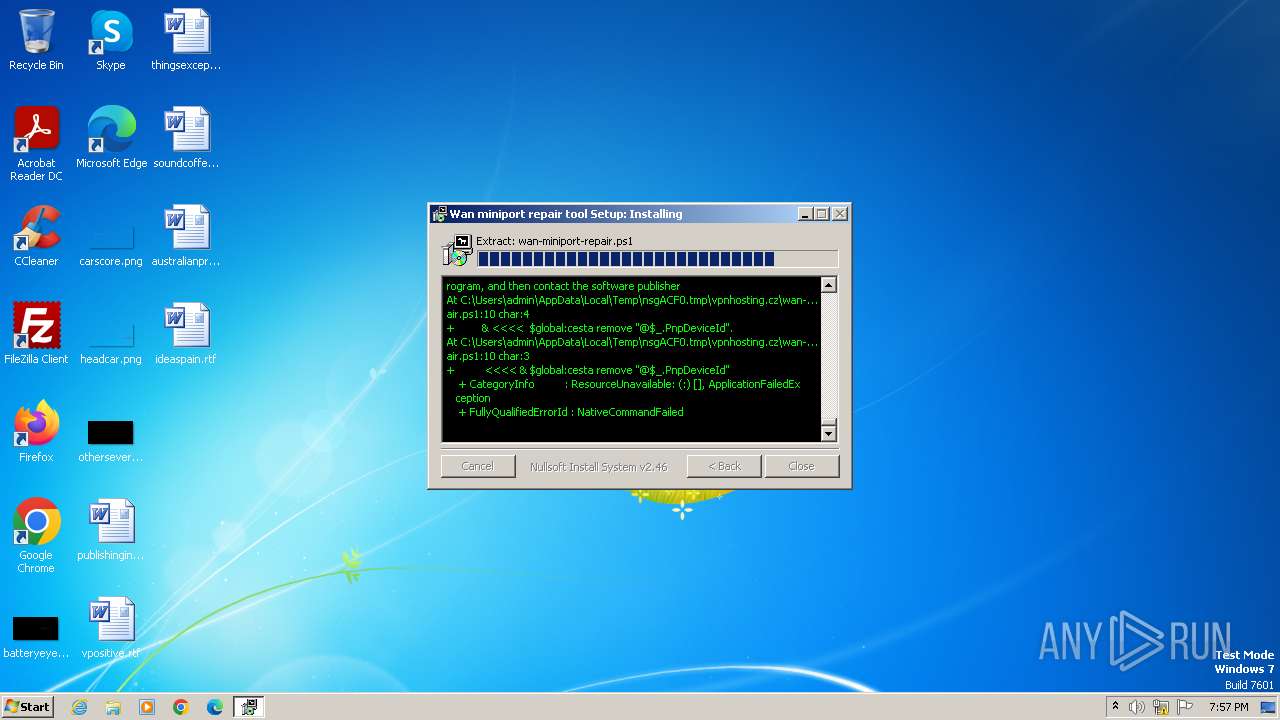
Powershell version downgrade attack
- powershell.exe (PID: 3404)
The process executes Powershell scripts
- nsAD20.tmp (PID: 3420)
Starts POWERSHELL.EXE for commands execution
- nsAD20.tmp (PID: 3420)
Starts application with an unusual extension
- wan-miniport-repair-x64.exe (PID: 3228)
Reads the Internet Settings
- powershell.exe (PID: 3404)
INFO
Reads the computer name
- wan-miniport-repair-x64.exe (PID: 3228)
Checks supported languages
- wan-miniport-repair-x64.exe (PID: 3228)
- nsAD20.tmp (PID: 3420)
Create files in a temporary directory
- wan-miniport-repair-x64.exe (PID: 3228)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | NSIS - Nullsoft Scriptable Install System (94.8) |
|---|---|---|
| .exe | | | Win32 Executable MS Visual C++ (generic) (3.4) |
| .dll | | | Win32 Dynamic Link Library (generic) (0.7) |
| .exe | | | Win32 Executable (generic) (0.5) |
| .exe | | | Generic Win/DOS Executable (0.2) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2009:12:05 23:50:46+01:00 |
| ImageFileCharacteristics: | No relocs, Executable, No line numbers, No symbols, 32-bit |
| PEType: | PE32 |
| LinkerVersion: | 6 |
| CodeSize: | 23552 |
| InitializedDataSize: | 119808 |
| UninitializedDataSize: | 1024 |
| EntryPoint: | 0x323c |
| OSVersion: | 4 |
| ImageVersion: | 6 |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
Total processes
42
Monitored processes
4
Malicious processes
3
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 3128 | "C:\Users\admin\AppData\Local\Temp\wan-miniport-repair-x64.exe" | C:\Users\admin\AppData\Local\Temp\wan-miniport-repair-x64.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 3221226540 Modules
| |||||||||||||||
| 3228 | "C:\Users\admin\AppData\Local\Temp\wan-miniport-repair-x64.exe" | C:\Users\admin\AppData\Local\Temp\wan-miniport-repair-x64.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 3404 | powershell -inputformat none -ExecutionPolicy RemoteSigned -File "C:\Users\admin\AppData\Local\Temp\nsgACF0.tmp\vpnhosting.cz\wan-miniport-repair.ps1" | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | nsAD20.tmp | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows PowerShell Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3420 | "C:\Users\admin\AppData\Local\Temp\nsgACF0.tmp\nsAD20.tmp" powershell -inputformat none -ExecutionPolicy RemoteSigned -File "C:\Users\admin\AppData\Local\Temp\nsgACF0.tmp\vpnhosting.cz\wan-miniport-repair.ps1" | C:\Users\admin\AppData\Local\Temp\nsgACF0.tmp\nsAD20.tmp | — | wan-miniport-repair-x64.exe | |||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
Total events
6 512
Read events
6 438
Write events
74
Delete events
0
Modification events
| (PID) Process: | (3404) powershell.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\17A\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (3404) powershell.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (3404) powershell.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
| (PID) Process: | (3404) powershell.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 1 | |||
| (PID) Process: | (3404) powershell.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 0 | |||
Executable files
3
Suspicious files
4
Text files
1
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3228 | wan-miniport-repair-x64.exe | C:\Users\admin\AppData\Local\Temp\nsgACF0.tmp\nsExec.dll | executable | |
MD5:ACC2B699EDFEA5BF5AAE45ABA3A41E96 | SHA256:168A974EAA3F588D759DB3F47C1A9FDC3494BA1FA1A73A84E5E3B2A4D58ABD7E | |||
| 3404 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\d93f411851d7c929.customDestinations-ms | binary | |
MD5:C681106A4168B935996B10134404F885 | SHA256:89AB4ECFBB5C1FD07CF99465E36B1A08F51E2512AA60DDD616D4A37753FC112D | |||
| 3228 | wan-miniport-repair-x64.exe | C:\Users\admin\AppData\Local\Temp\nsgACF0.tmp\vpnhosting.cz\devcon-x64.exe | executable | |
MD5:EB8C277FAEEE2206120EE0F2B1D71F05 | SHA256:25CEA7E13CB42DCA048323BFE914CC89ED82CCE33FAD13C7703918D8FC24D1CC | |||
| 3228 | wan-miniport-repair-x64.exe | C:\Users\admin\AppData\Local\Temp\nsgACF0.tmp\vpnhosting.cz\wan-miniport-repair.ps1 | text | |
MD5:A98AEC31D2DA3536D96F10E73B90F6F2 | SHA256:1C0F7C18CD91920121FE06ABC593C38E4AE28AB2F795421ADEB98988FDF68BC9 | |||
| 3228 | wan-miniport-repair-x64.exe | C:\Users\admin\AppData\Local\Temp\nsgACF0.tmp\nsAD20.tmp | executable | |
MD5:ACC2B699EDFEA5BF5AAE45ABA3A41E96 | SHA256:168A974EAA3F588D759DB3F47C1A9FDC3494BA1FA1A73A84E5E3B2A4D58ABD7E | |||
| 3404 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\d93f411851d7c929.customDestinations-ms~RF16ade8.TMP | binary | |
MD5:C681106A4168B935996B10134404F885 | SHA256:89AB4ECFBB5C1FD07CF99465E36B1A08F51E2512AA60DDD616D4A37753FC112D | |||
| 3404 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\NYCSX8IN8JEJNSPDYU7X.temp | binary | |
MD5:C681106A4168B935996B10134404F885 | SHA256:89AB4ECFBB5C1FD07CF99465E36B1A08F51E2512AA60DDD616D4A37753FC112D | |||
| 3228 | wan-miniport-repair-x64.exe | C:\Users\admin\AppData\Local\Temp\nsz8E8A.tmp | binary | |
MD5:307B2C3491300AAE8C67CA310FBE9EF2 | SHA256:ED8BBE0B3137CB8DAA59D27ECD792A13E752363D4379CC39B245448E9204F5EE | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
2
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |