| File name: | SecuriteInfo.com.Win64.Malware-gen.8360.5215 |
| Full analysis: | https://app.any.run/tasks/f9f178c8-9f4b-4695-9950-a85b79e0fbdc |
| Verdict: | Malicious activity |
| Analysis date: | April 20, 2025, 08:54:34 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/vnd.microsoft.portable-executable |
| File info: | PE32+ executable (GUI) x86-64 (stripped to external PDB), for MS Windows, 12 sections |
| MD5: | 808C6FA683FD69A2A82C51A9EA9FB573 |
| SHA1: | CF0097060043C2985D4DB8DB0F57DA29B0910B74 |
| SHA256: | 6478B146391A79A87287563521A4F7D318E87D84B1304D51A17CFF511F2A3AE3 |
| SSDEEP: | 98304:AI270KK4ick/rGlvQWvHaYMz5sohB13uXFRy3D9c+wWzQIKxnx5AhtIoD99FQ5YT:iiNYTOo2l |
MALICIOUS
No malicious indicators.SUSPICIOUS
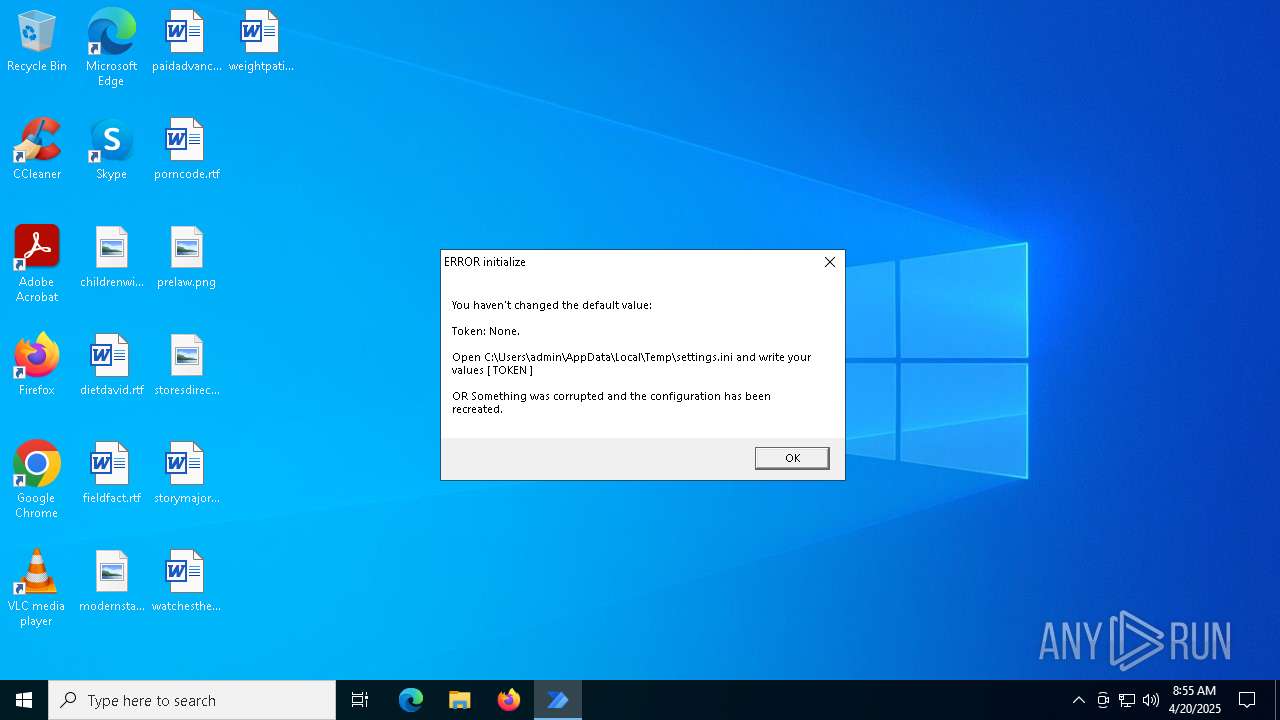
Executable content was dropped or overwritten
- SecuriteInfo.com.Win64.Malware-gen.8360.5215.exe (PID: 6728)
- WindowsScriptHost.exe (PID: 6632)
The process drops C-runtime libraries
- SecuriteInfo.com.Win64.Malware-gen.8360.5215.exe (PID: 6728)
- WindowsScriptHost.exe (PID: 6632)
Process drops python dynamic module
- SecuriteInfo.com.Win64.Malware-gen.8360.5215.exe (PID: 6728)
- WindowsScriptHost.exe (PID: 6632)
Process drops legitimate windows executable
- SecuriteInfo.com.Win64.Malware-gen.8360.5215.exe (PID: 6728)
- WindowsScriptHost.exe (PID: 6632)
Loads Python modules
- git_update.exe (PID: 4756)
- WindowsScriptHost.exe (PID: 2088)
The process creates files with name similar to system file names
- WindowsScriptHost.exe (PID: 6632)
- git_update.exe (PID: 4756)
Reads security settings of Internet Explorer
- SecuriteInfo.com.Win64.Malware-gen.8360.5215.exe (PID: 6728)
- WindowsScriptHost.exe (PID: 6632)
Starts POWERSHELL.EXE for commands execution
- WindowsScriptHost.exe (PID: 2088)
Checks for external IP
- svchost.exe (PID: 2196)
- WindowsScriptHost.exe (PID: 2088)
INFO
Checks supported languages
- SecuriteInfo.com.Win64.Malware-gen.8360.5215.exe (PID: 6728)
- WindowsScriptHost.exe (PID: 6632)
- git_update.exe (PID: 4756)
- WindowsScriptHost.exe (PID: 2088)
Reads the computer name
- git_update.exe (PID: 4756)
- SecuriteInfo.com.Win64.Malware-gen.8360.5215.exe (PID: 6728)
- WindowsScriptHost.exe (PID: 2088)
- WindowsScriptHost.exe (PID: 6632)
Create files in a temporary directory
- SecuriteInfo.com.Win64.Malware-gen.8360.5215.exe (PID: 6728)
- WindowsScriptHost.exe (PID: 6632)
- git_update.exe (PID: 4756)
- powershell.exe (PID: 960)
- WindowsScriptHost.exe (PID: 2088)
Checks proxy server information
- git_update.exe (PID: 4756)
The sample compiled with english language support
- SecuriteInfo.com.Win64.Malware-gen.8360.5215.exe (PID: 6728)
- WindowsScriptHost.exe (PID: 6632)
Reads the machine GUID from the registry
- git_update.exe (PID: 4756)
- WindowsScriptHost.exe (PID: 2088)
Creates files or folders in the user directory
- WindowsScriptHost.exe (PID: 2088)
Reads the software policy settings
- powershell.exe (PID: 960)
- slui.exe (PID: 6652)
Reads security settings of Internet Explorer
- powershell.exe (PID: 960)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win64 Executable (generic) (87.3) |
|---|---|---|
| .exe | | | Generic Win/DOS Executable (6.3) |
| .exe | | | DOS Executable Generic (6.3) |
EXIF
EXE
| MachineType: | AMD AMD64 |
|---|---|
| TimeStamp: | 2025:03:25 18:48:39+00:00 |
| ImageFileCharacteristics: | Executable, No line numbers, No symbols, Large address aware, No debug |
| PEType: | PE32+ |
| LinkerVersion: | 2.41 |
| CodeSize: | 111104 |
| InitializedDataSize: | 6721024 |
| UninitializedDataSize: | 146944 |
| EntryPoint: | 0x10f6 |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 5.2 |
| Subsystem: | Windows GUI |
Total processes
137
Monitored processes
10
Malicious processes
3
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 960 | powershell -Command " $os = Get-CimInstance Win32_OperatingSystem $result = @{ Caption = $os.Caption Version = $os.Version OSArchitecture = $os.OSArchitecture RegisteredUser = $os.RegisteredUser } ConvertTo-Json -InputObject $result " | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | WindowsScriptHost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1128 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2088 | C:\Users\admin\AppData\Local\Temp\WindowsScriptHost.exe updated | C:\Users\admin\AppData\Local\Temp\temp_WinScriptHost_6632_133896128997610699\WindowsScriptHost.exe | WindowsScriptHost.exe | ||||||||||||
User: admin Company: insiderkeeps Integrity Level: MEDIUM Description: Microsoft-UWP-Standalone-Provisioning-Service Exit code: 0 Version: 9.8.1.0 Modules
| |||||||||||||||
| 2196 | C:\WINDOWS\system32\svchost.exe -k NetworkService -p -s Dnscache | C:\Windows\System32\svchost.exe | services.exe | ||||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: Host Process for Windows Services Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 3192 | C:\WINDOWS\system32\SppExtComObj.exe -Embedding | C:\Windows\System32\SppExtComObj.Exe | — | svchost.exe | |||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: KMS Connection Broker Version: 10.0.19041.3996 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 4756 | C:\Users\admin\AppData\Local\Temp\SecuriteInfo.com.Win64.Malware-gen.8360.5215.exe | C:\Users\admin\AppData\Local\Temp\temp_WinScriptHost_6728_133896128819019814\git_update.exe | SecuriteInfo.com.Win64.Malware-gen.8360.5215.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 5352 | C:\WINDOWS\System32\slui.exe -Embedding | C:\Windows\System32\slui.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Activation Client Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6632 | C:\Users\admin\AppData\Local\Temp\WindowsScriptHost.exe updated | C:\Users\admin\AppData\Local\Temp\WindowsScriptHost.exe | git_update.exe | ||||||||||||
User: admin Company: insiderkeeps Integrity Level: MEDIUM Description: Microsoft-UWP-Standalone-Provisioning-Service Exit code: 0 Version: 9.8.1.0 Modules
| |||||||||||||||
| 6652 | "C:\WINDOWS\System32\SLUI.exe" RuleId=3482d82e-ca2c-4e1f-8864-da0267b484b2;Action=AutoActivate;AppId=55c92734-d682-4d71-983e-d6ec3f16059f;SkuId=4de7cb65-cdf1-4de9-8ae8-e3cce27b9f2c;NotificationInterval=1440;Trigger=TimerEvent | C:\Windows\System32\slui.exe | SppExtComObj.Exe | ||||||||||||
User: NETWORK SERVICE Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows Activation Client Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6728 | "C:\Users\admin\AppData\Local\Temp\SecuriteInfo.com.Win64.Malware-gen.8360.5215.exe" | C:\Users\admin\AppData\Local\Temp\SecuriteInfo.com.Win64.Malware-gen.8360.5215.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
Total events
6 500
Read events
6 500
Write events
0
Delete events
0
Modification events
Executable files
88
Suspicious files
3
Text files
923
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 6728 | SecuriteInfo.com.Win64.Malware-gen.8360.5215.exe | C:\Users\admin\AppData\Local\Temp\temp_WinScriptHost_6728_133896128819019814\_bz2.pyd | executable | |
MD5:6C7565C1EFFFE44CB0616F5B34FAA628 | SHA256:FE63361F6C439C6AA26FD795AF3FD805FF5B60B3B14F9B8C60C50A8F3449060A | |||
| 4756 | git_update.exe | C:\Users\admin\AppData\Local\Temp\WindowsScriptHost.exe.new | — | |
MD5:— | SHA256:— | |||
| 4756 | git_update.exe | C:\Users\admin\AppData\Local\Temp\WindowsScriptHost.exe | — | |
MD5:— | SHA256:— | |||
| 6632 | WindowsScriptHost.exe | C:\Users\admin\AppData\Local\Temp\temp_WinScriptHost_6632_133896128997610699\WindowsScriptHost.exe | — | |
MD5:— | SHA256:— | |||
| 6728 | SecuriteInfo.com.Win64.Malware-gen.8360.5215.exe | C:\Users\admin\AppData\Local\Temp\temp_WinScriptHost_6728_133896128819019814\git_update.exe | executable | |
MD5:B5564AAC5C7149DB342366D91E3CA23A | SHA256:46DEBDE762F5732996C36DAB0A3556B95D81AACBA43CFC1F24DDE0524BCB106B | |||
| 6728 | SecuriteInfo.com.Win64.Malware-gen.8360.5215.exe | C:\Users\admin\AppData\Local\Temp\temp_WinScriptHost_6728_133896128819019814\zstandard\backend_c.pyd | executable | |
MD5:2DCEE3AED139B2FE36BEAAC7EF702FD7 | SHA256:C14DBEDC05695C70C75E98368FB01ED898131D104E1E4C006D5A57E1294177E6 | |||
| 6728 | SecuriteInfo.com.Win64.Malware-gen.8360.5215.exe | C:\Users\admin\AppData\Local\Temp\temp_WinScriptHost_6728_133896128819019814\_lzma.pyd | executable | |
MD5:B5355DD319FB3C122BB7BF4598AD7570 | SHA256:B9BC7F1D8AA8498CB8B5DC75BB0DBB6E721B48953A3F295870938B27267FB5F5 | |||
| 6728 | SecuriteInfo.com.Win64.Malware-gen.8360.5215.exe | C:\Users\admin\AppData\Local\Temp\temp_WinScriptHost_6728_133896128819019814\_hashlib.pyd | executable | |
MD5:F377A418ADDEEB02F223F45F6F168FE6 | SHA256:9551431425E9680660C6BAF7B67A262040FD2EFCEB241E4C9430560C3C1FAFAC | |||
| 6728 | SecuriteInfo.com.Win64.Malware-gen.8360.5215.exe | C:\Users\admin\AppData\Local\Temp\temp_WinScriptHost_6728_133896128819019814\libssl-1_1.dll | executable | |
MD5:BC778F33480148EFA5D62B2EC85AAA7D | SHA256:9D4CF1C03629F92662FC8D7E3F1094A7FC93CB41634994464B853DF8036AF843 | |||
| 6728 | SecuriteInfo.com.Win64.Malware-gen.8360.5215.exe | C:\Users\admin\AppData\Local\Temp\temp_WinScriptHost_6728_133896128819019814\libcrypto-1_1.dll | executable | |
MD5:CC4CBF715966CDCAD95A1E6C95592B3D | SHA256:594303E2CE6A4A02439054C84592791BF4AB0B7C12E9BBDB4B040E27251521F1 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
5
TCP/UDP connections
24
DNS requests
18
Threats
3
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2088 | WindowsScriptHost.exe | GET | 200 | 34.160.111.145:80 | http://ifconfig.me/ip | unknown | — | — | shared |
— | — | GET | 200 | 23.216.77.30:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
6544 | svchost.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
5332 | SIHClient.exe | GET | 200 | 2.23.181.156:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
5332 | SIHClient.exe | GET | 200 | 2.23.181.156:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2104 | svchost.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
— | — | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
— | — | 23.216.77.30:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
3216 | svchost.exe | 172.211.123.248:443 | client.wns.windows.com | MICROSOFT-CORP-MSN-AS-BLOCK | FR | whitelisted |
4756 | git_update.exe | 140.82.121.6:443 | api.github.com | GITHUB | US | whitelisted |
4756 | git_update.exe | 140.82.121.3:443 | github.com | GITHUB | US | whitelisted |
4756 | git_update.exe | 185.199.109.133:443 | objects.githubusercontent.com | FASTLY | US | whitelisted |
6544 | svchost.exe | 20.190.159.71:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
6544 | svchost.exe | 2.17.190.73:80 | ocsp.digicert.com | AKAMAI-AS | DE | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
api.github.com |
| whitelisted |
github.com |
| whitelisted |
objects.githubusercontent.com |
| whitelisted |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
slscr.update.microsoft.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2196 | svchost.exe | Device Retrieving External IP Address Detected | INFO [ANY.RUN] External IP Lookup Domain (ifconfig .me) |
2088 | WindowsScriptHost.exe | Device Retrieving External IP Address Detected | ET INFO External IP Lookup Domain (ifconfig .me) |
2088 | WindowsScriptHost.exe | Device Retrieving External IP Address Detected | SUSPICIOUS [ANY.RUN] An IP address was received from the server as a result of an HTTP request |