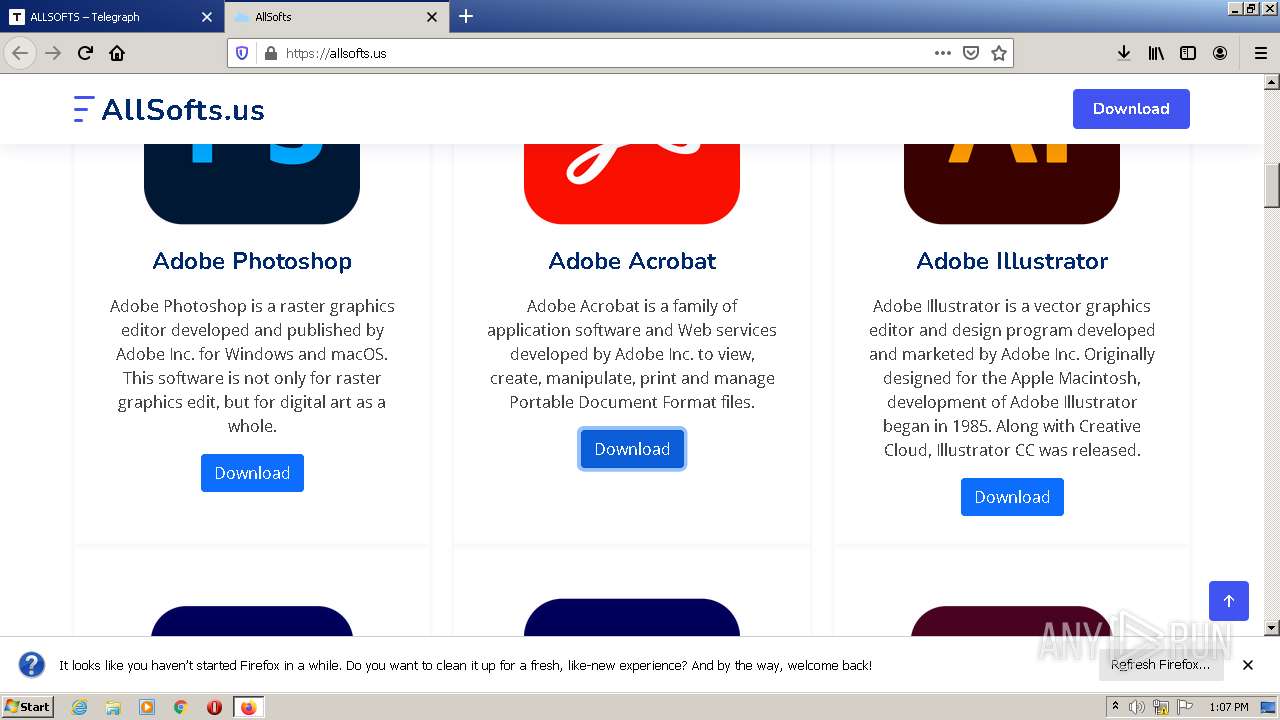
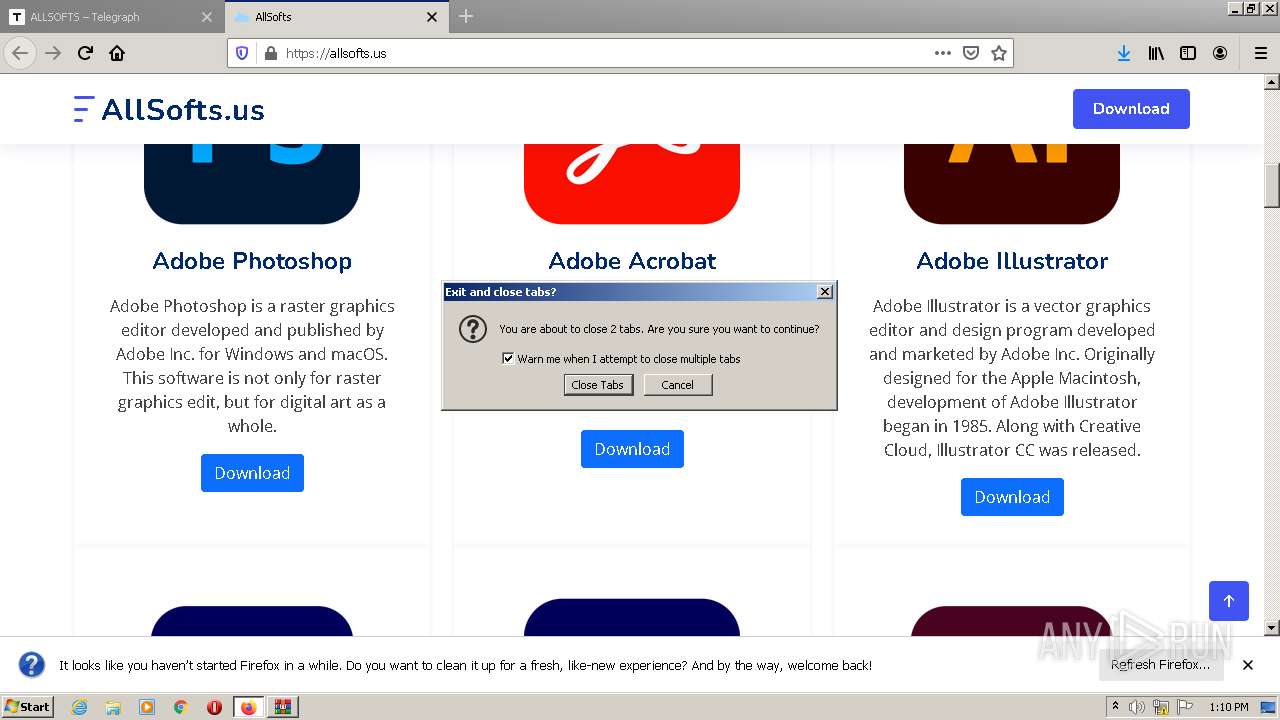
| URL: | https://www.telegra.ph/ALLSOFTS-03-21 |
| Full analysis: | https://app.any.run/tasks/2078121b-520e-43e1-ad99-4d71e6f5595b |
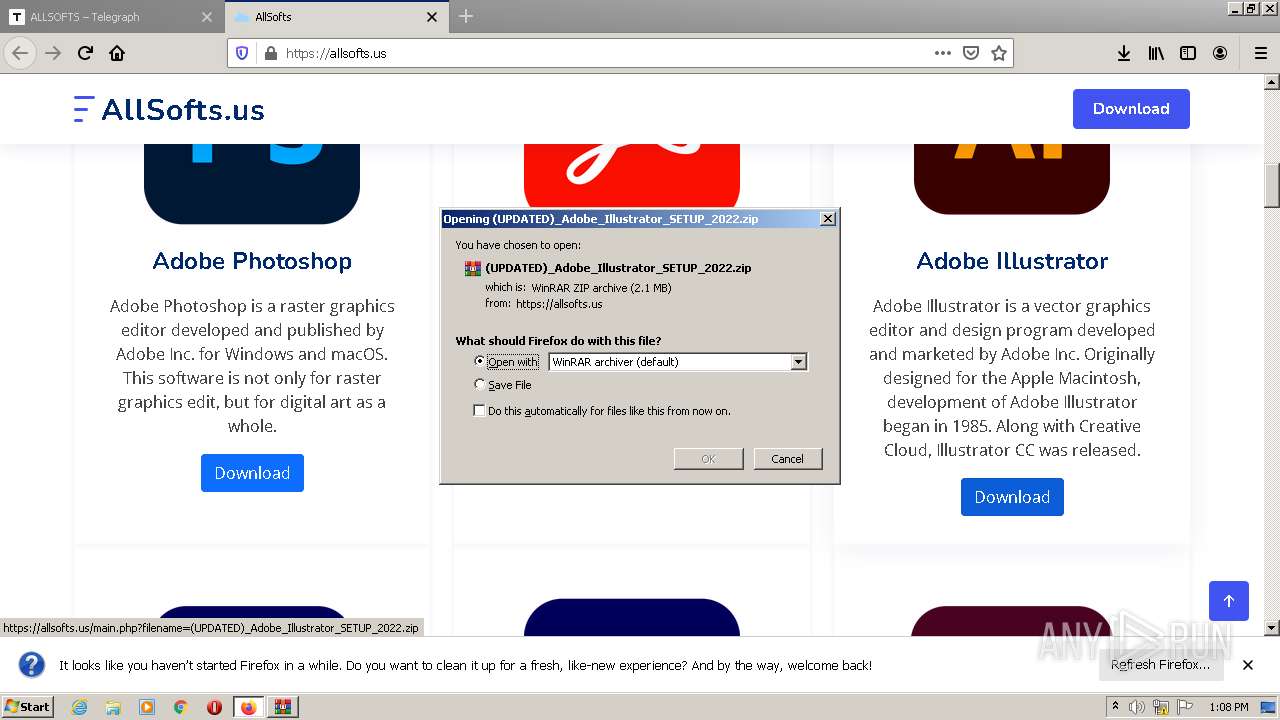
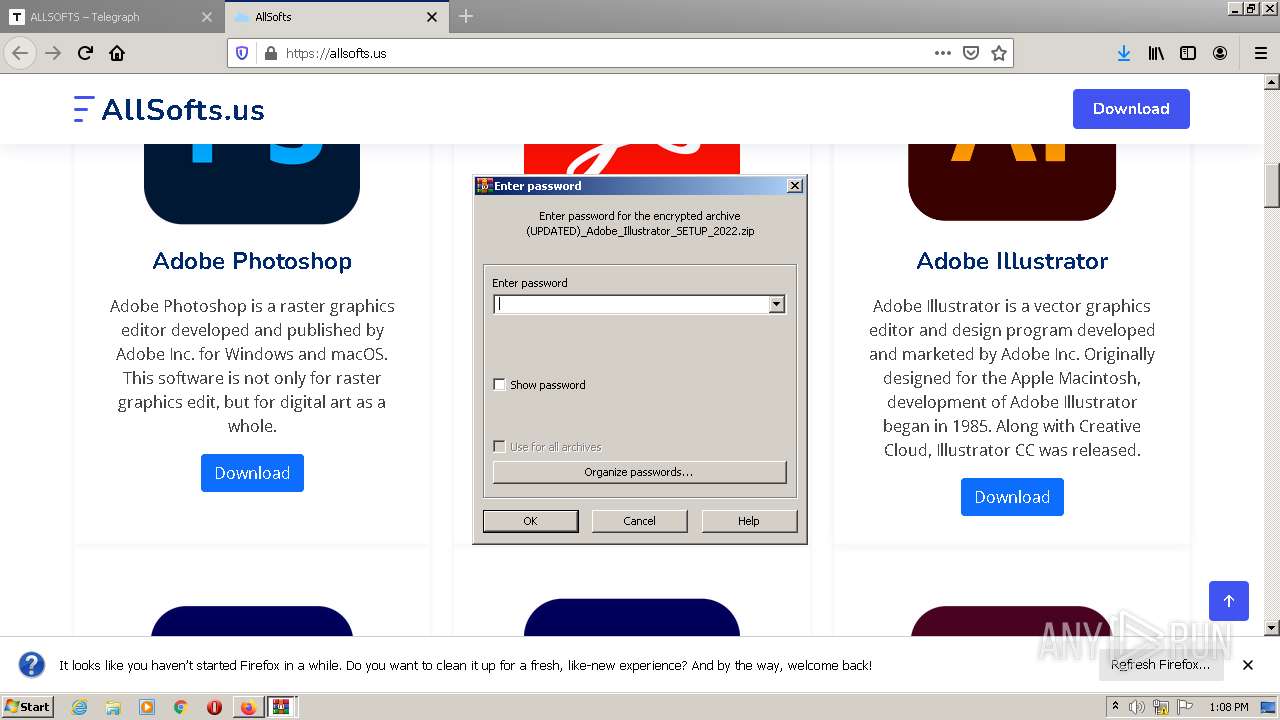
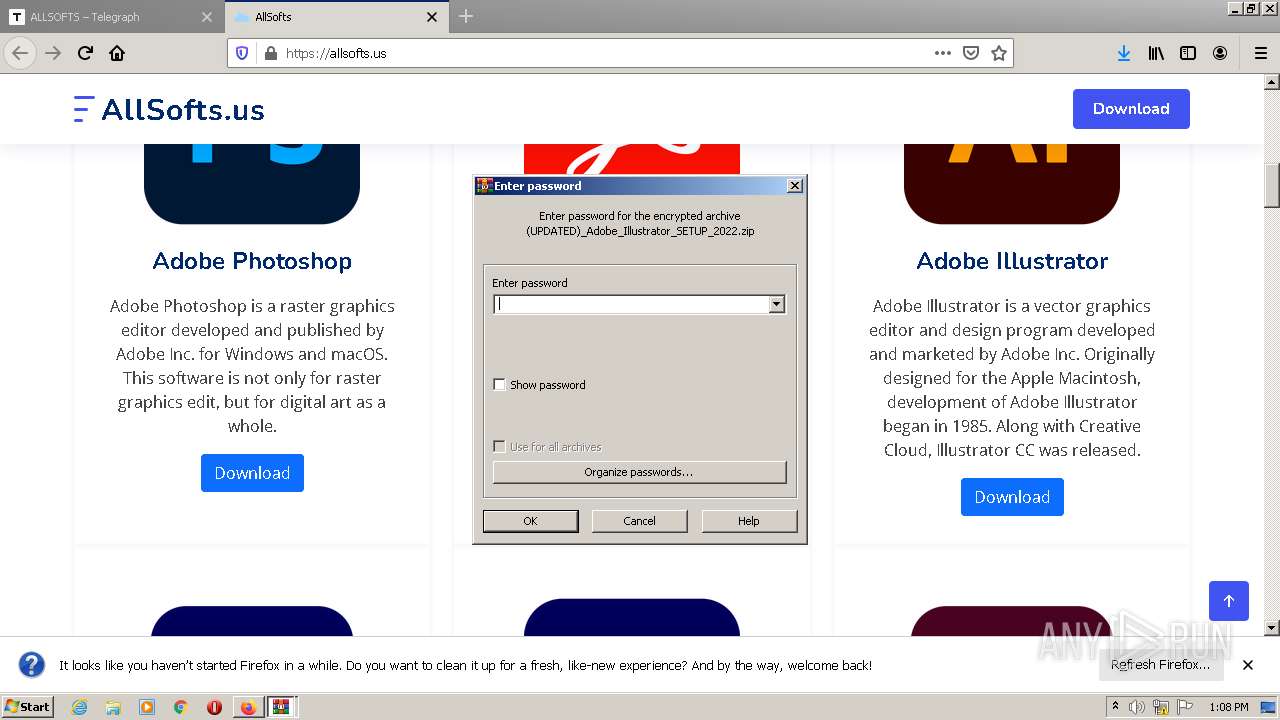
| Verdict: | Malicious activity |
| Analysis date: | April 01, 2023, 12:06:52 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | 32044F79C6FE59F5A52888D421B3D014 |
| SHA1: | DBCE174A759BA0F42C37794E42D22B06FEC60FA3 |
| SHA256: | 644D9A416A5552940CB9A15A3DF889F93EEDDB75EF3D55898DB4F9EBFA1DD843 |
| SSDEEP: | 3:N8DSLVy:2OLVy |
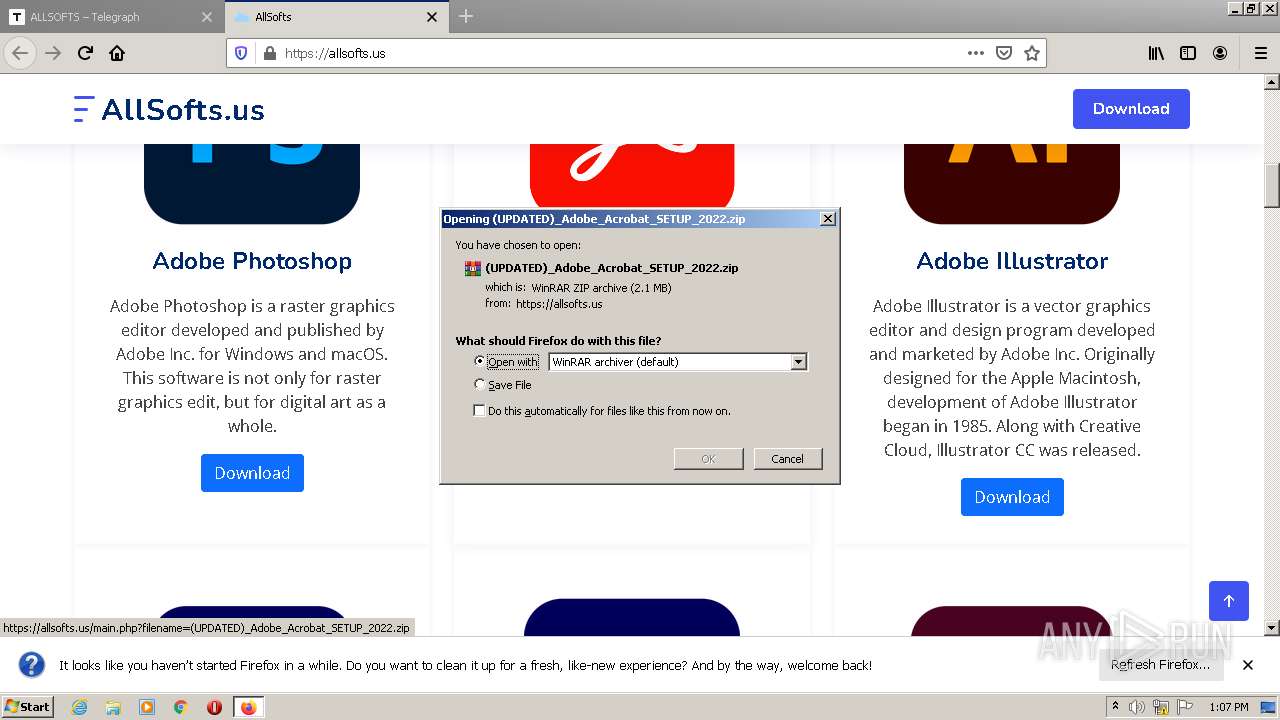
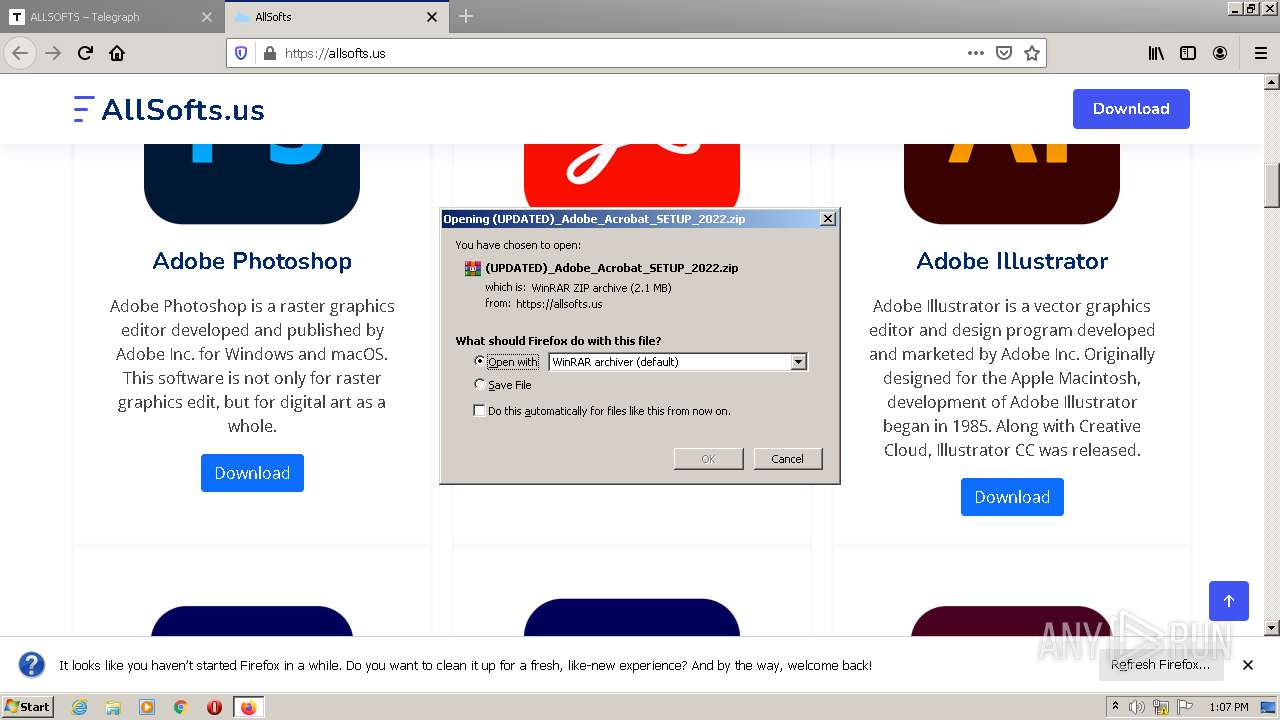
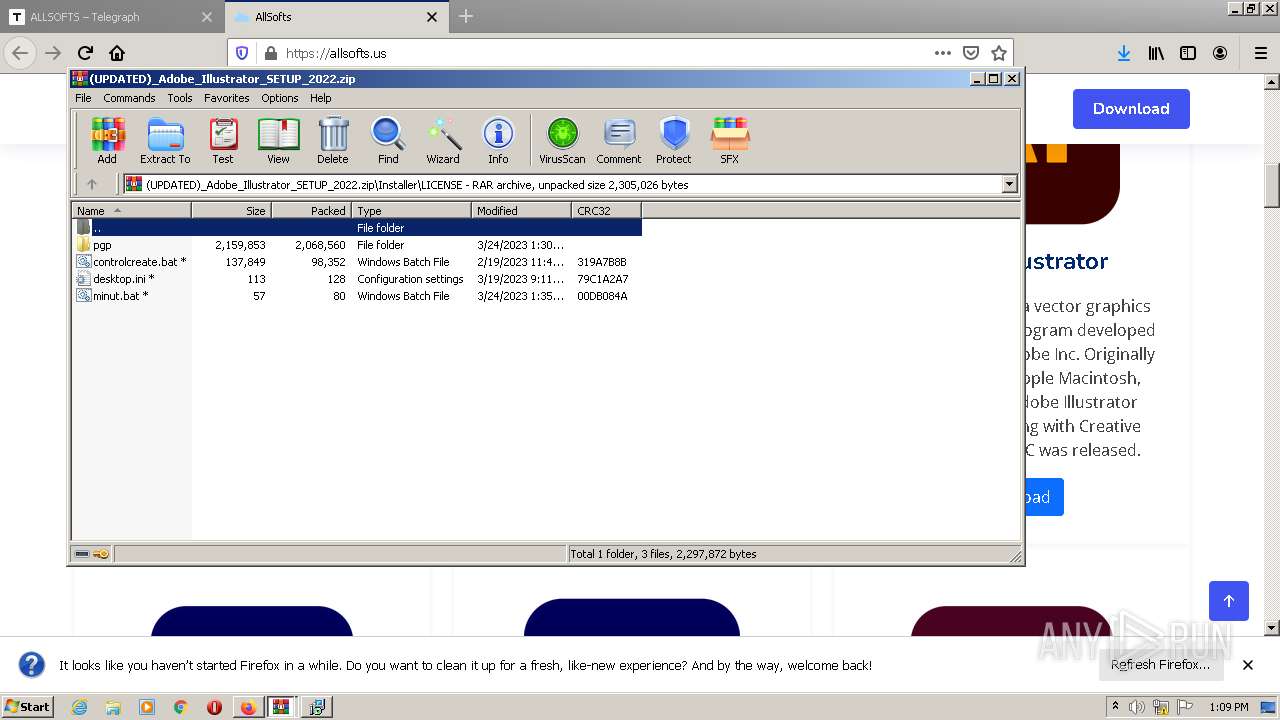
MALICIOUS
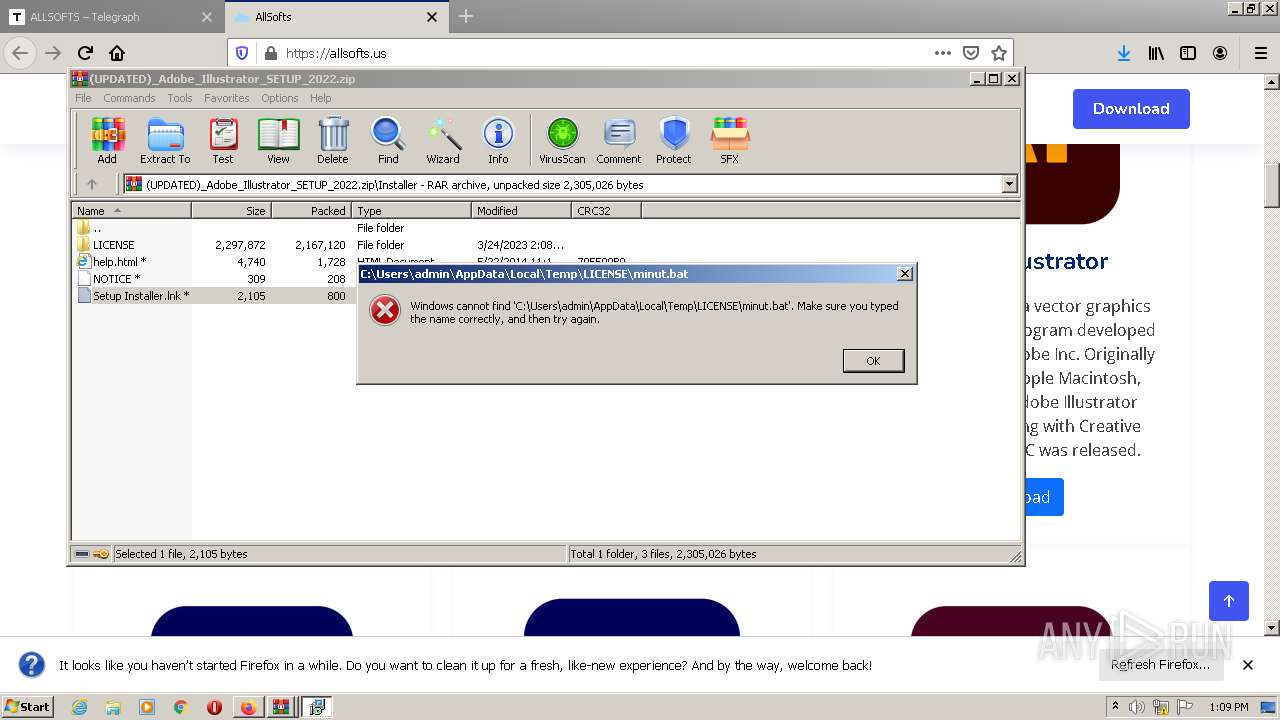
Starts PowerShell from an unusual location
- cmd.exe (PID: 920)
Application was dropped or rewritten from another process
- controlcreate.bat.exe (PID: 2924)
SUSPICIOUS
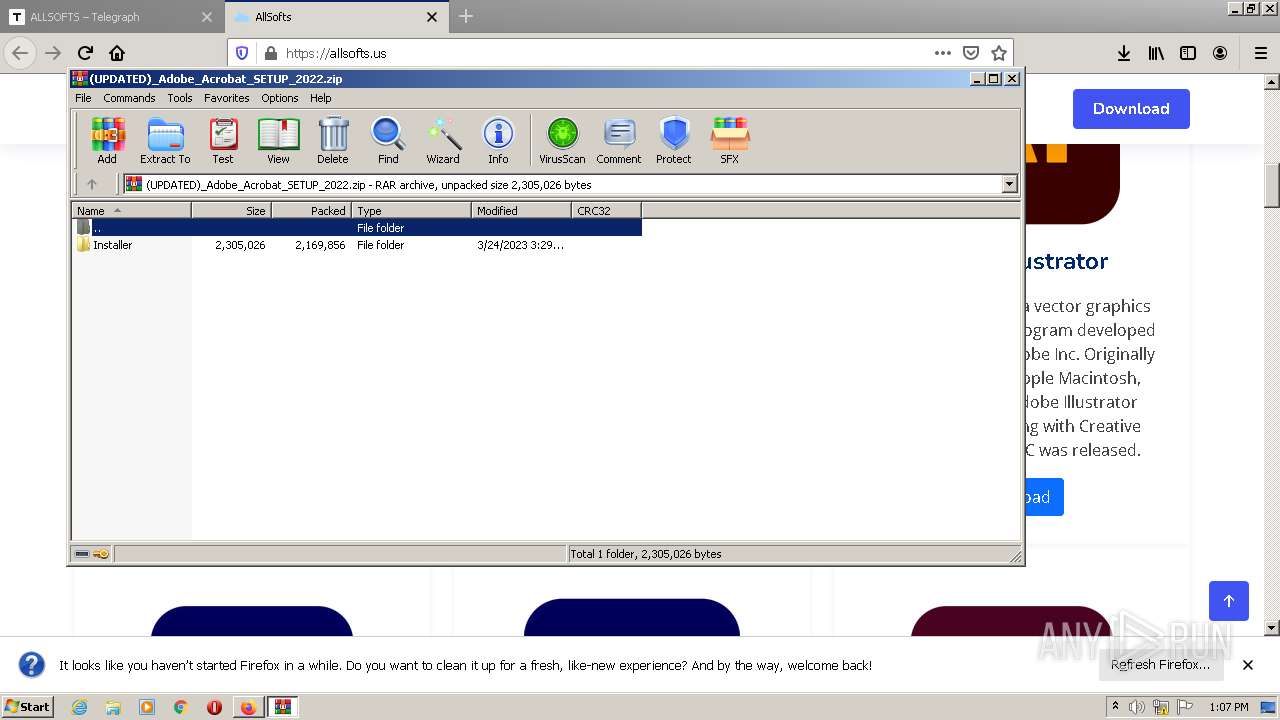
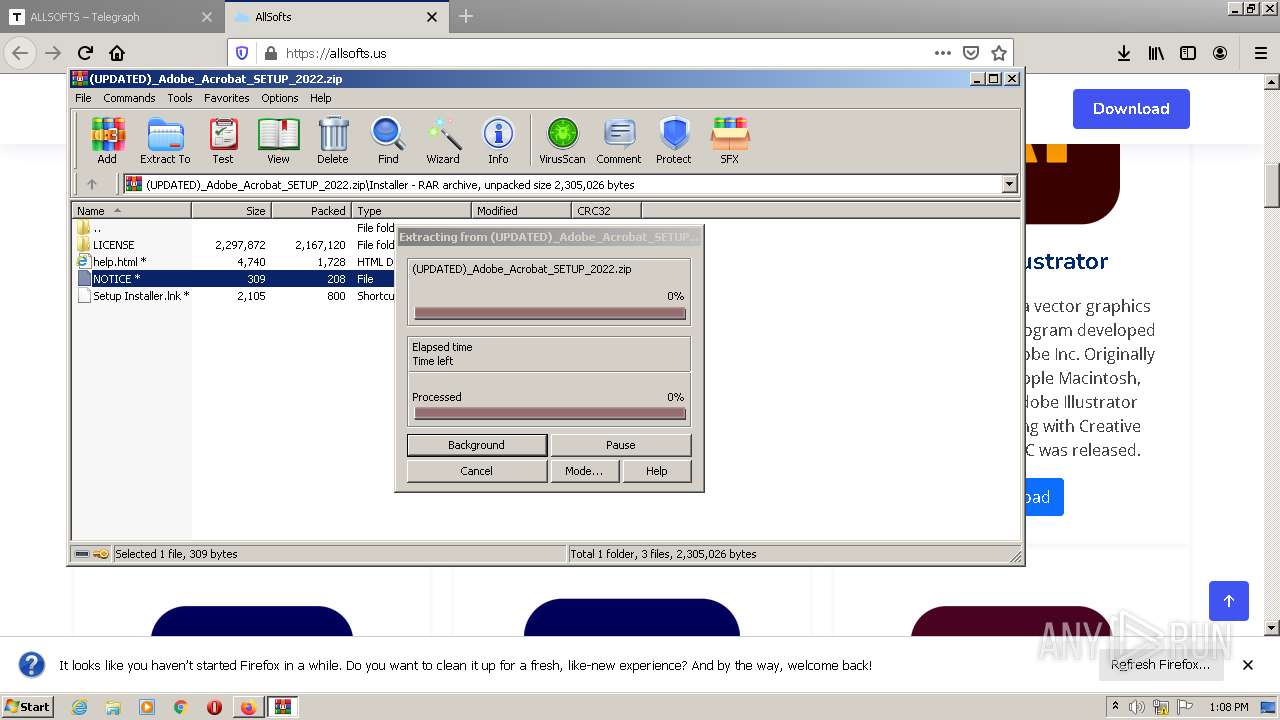
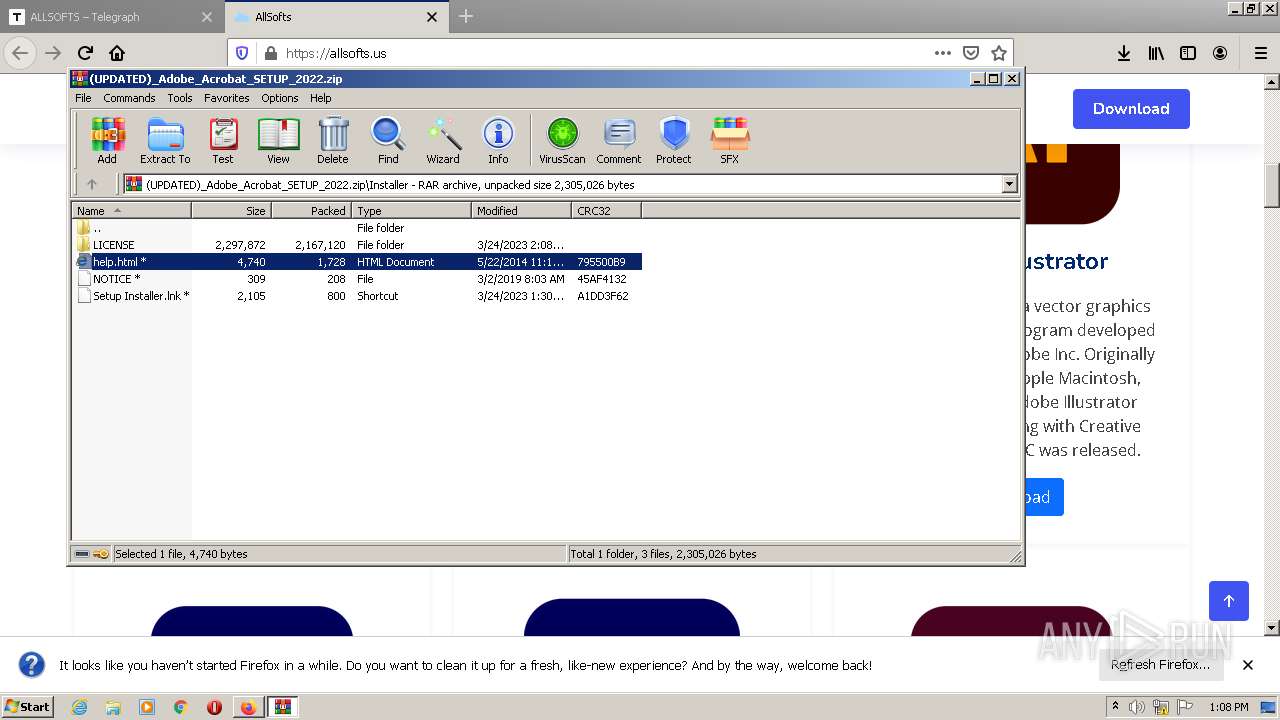
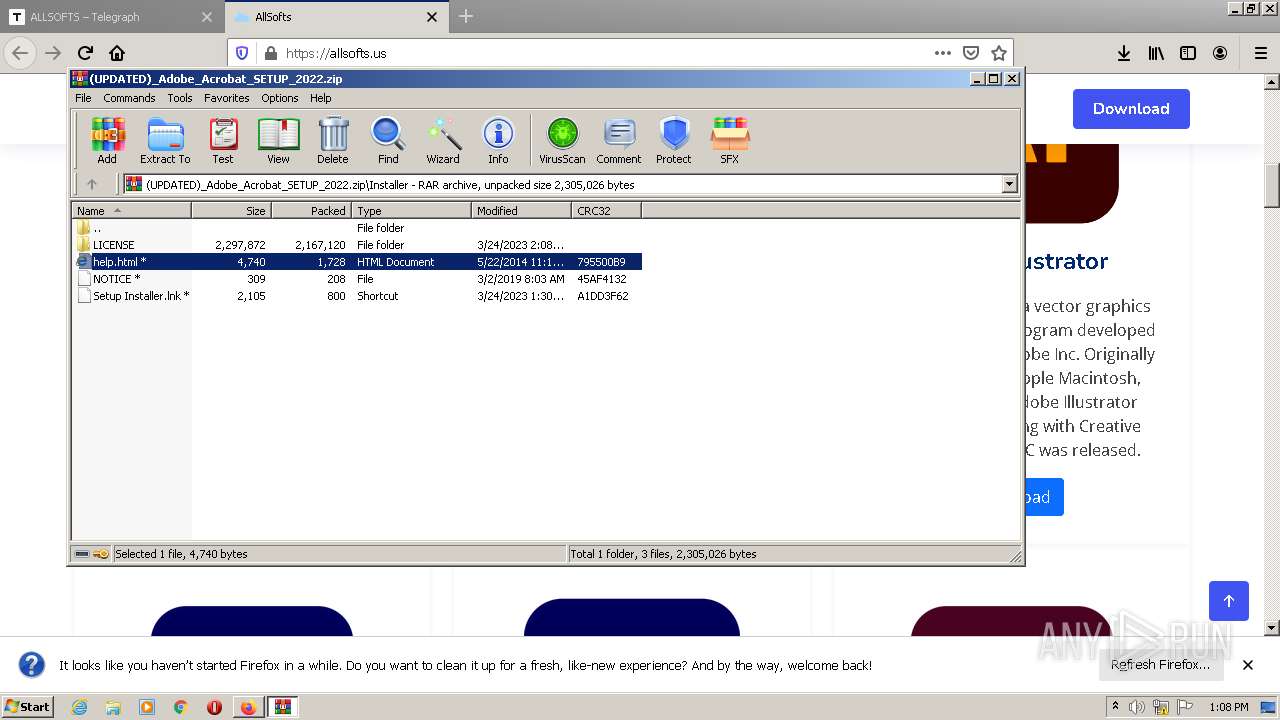
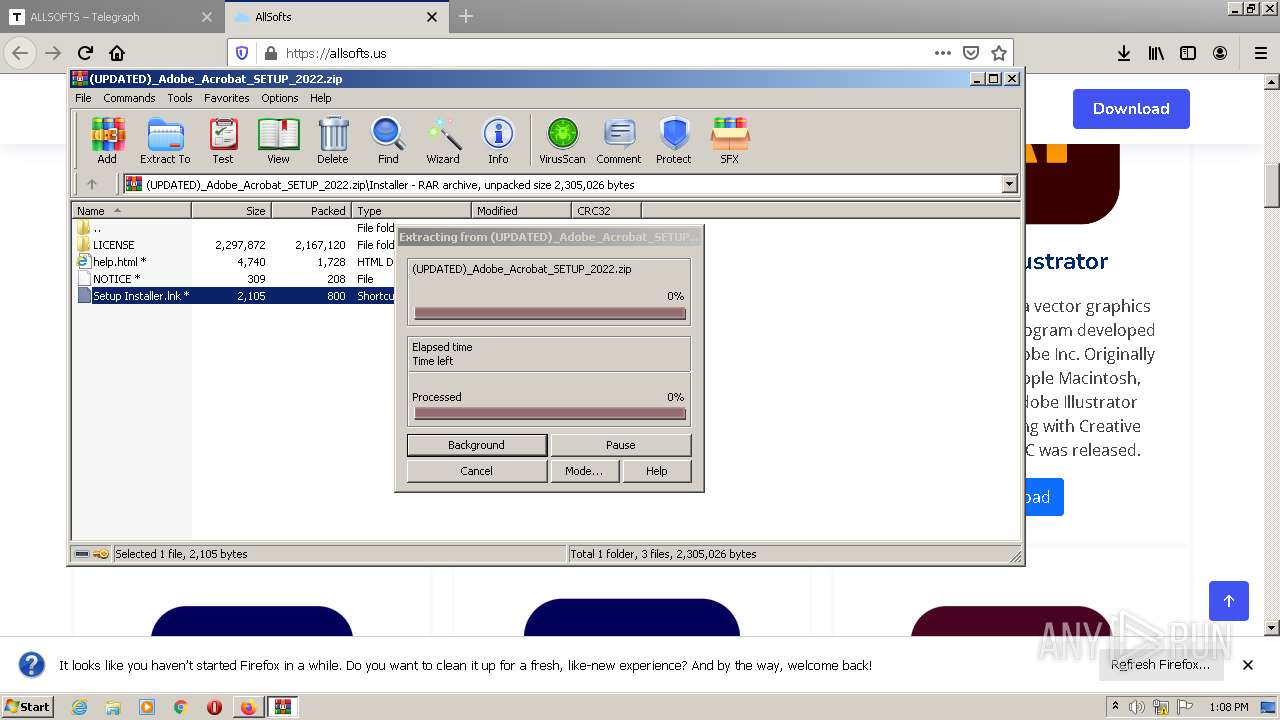
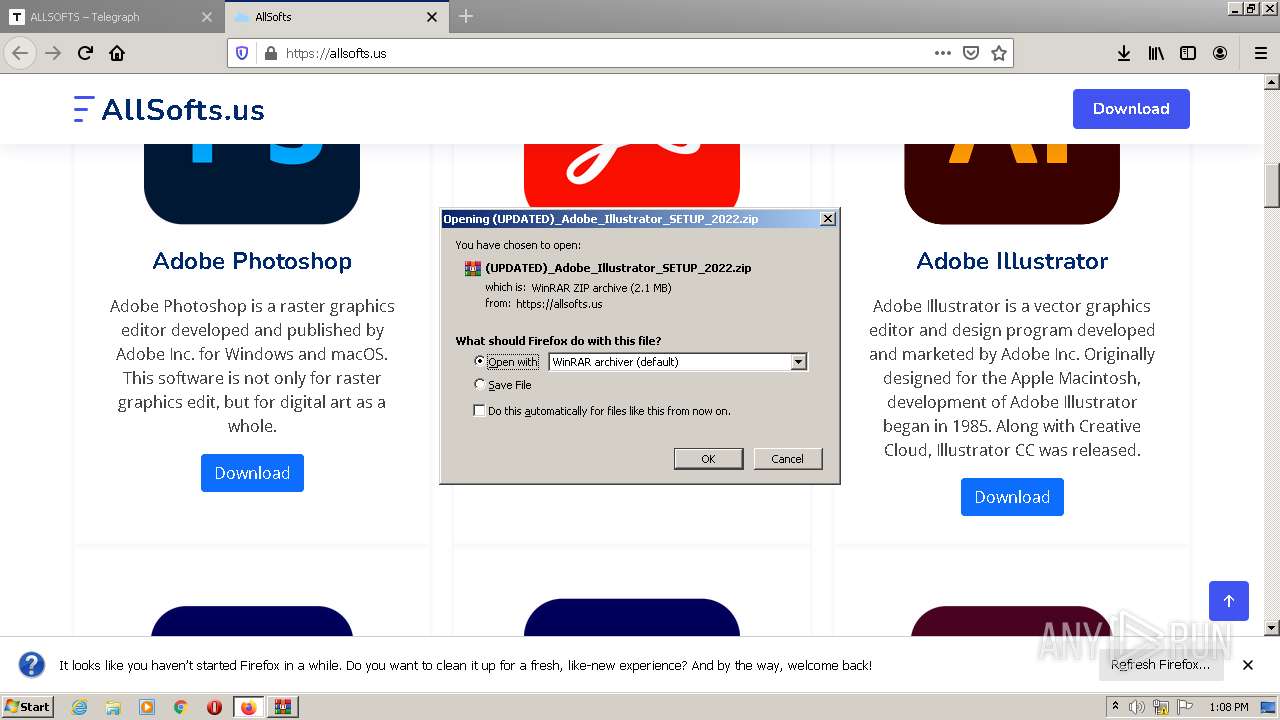
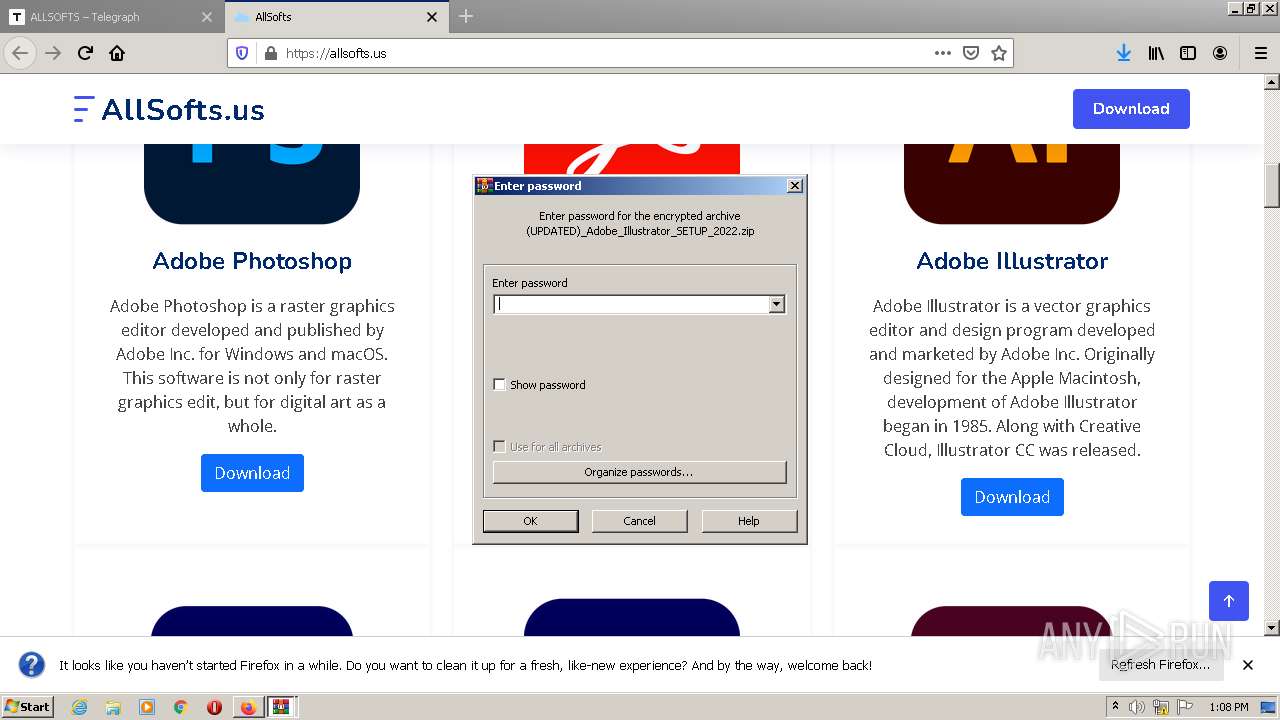
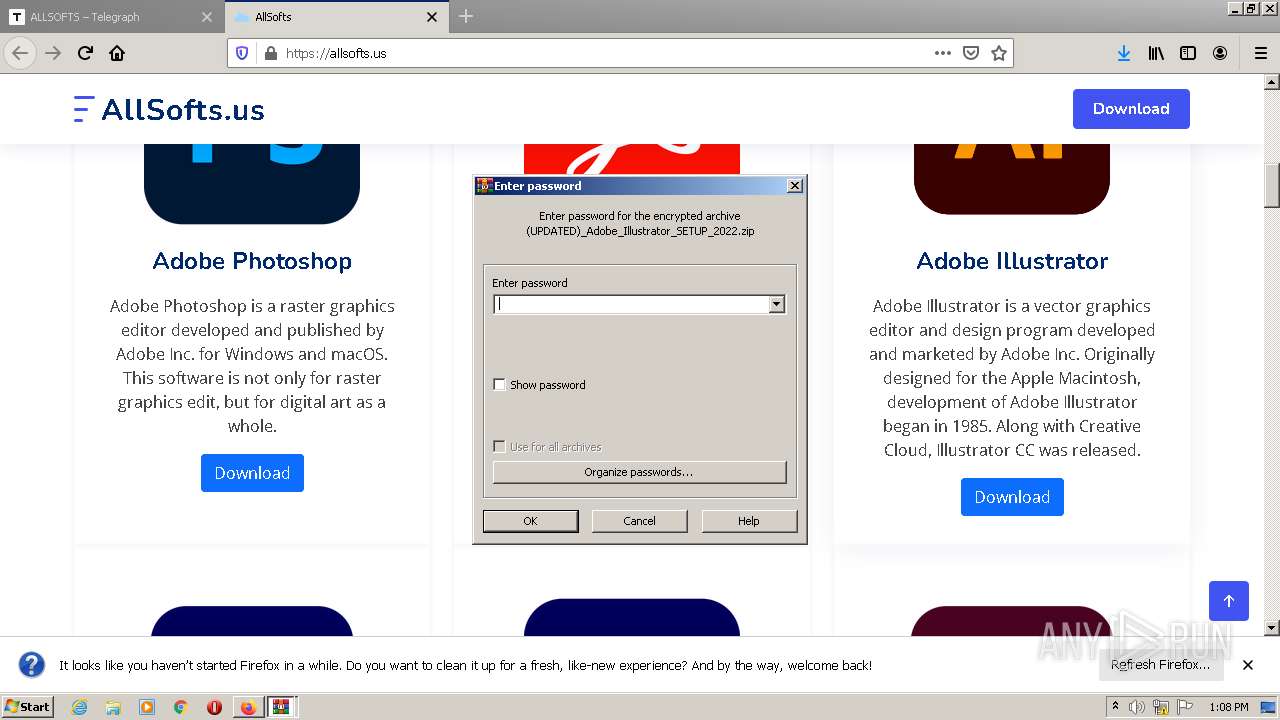
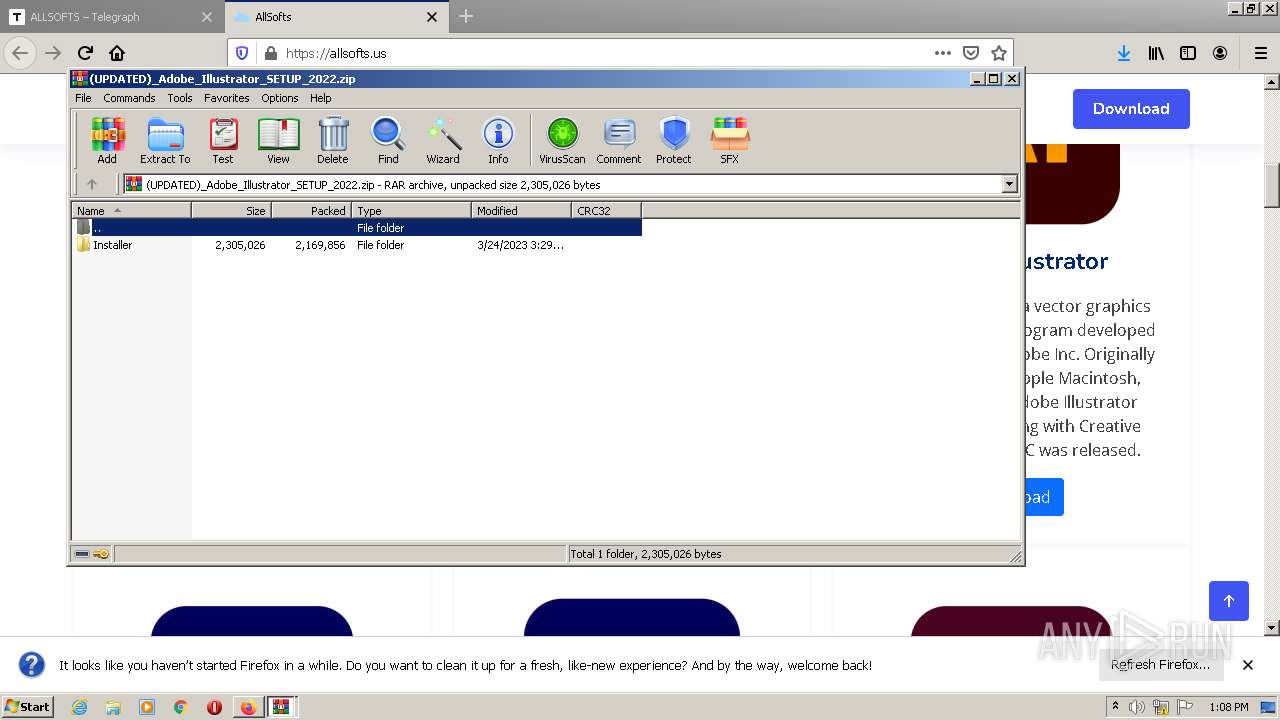
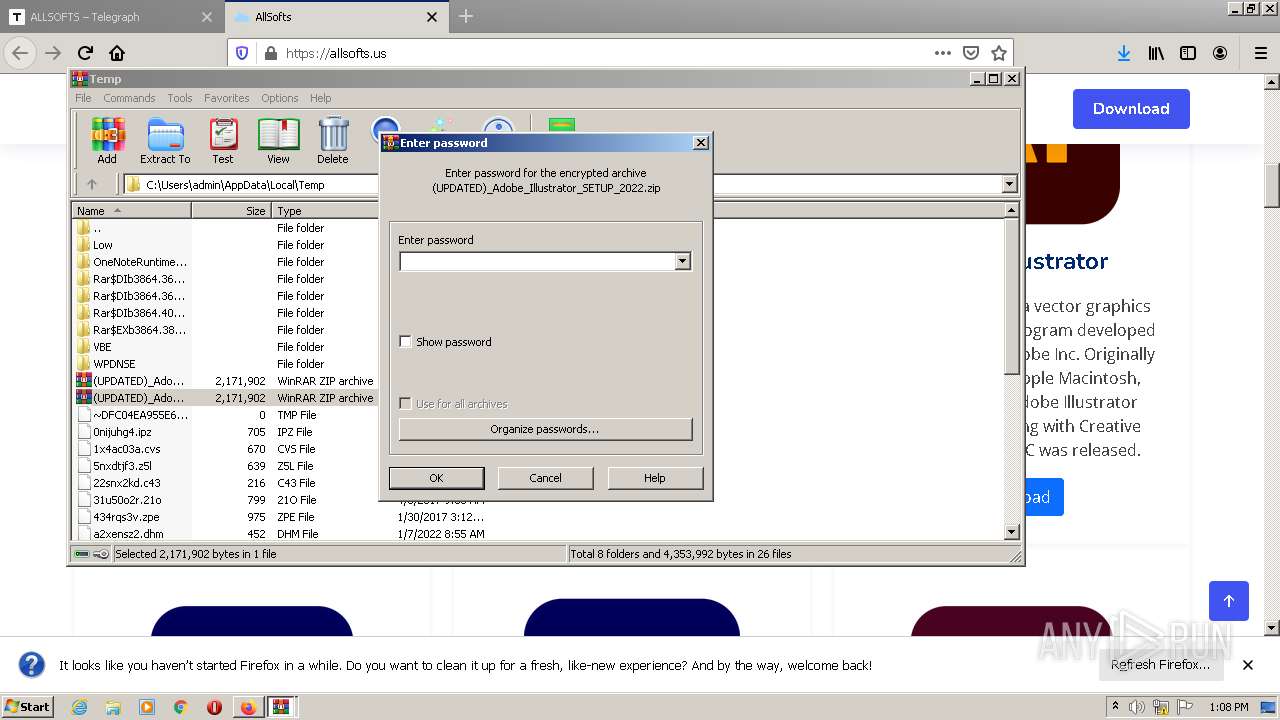
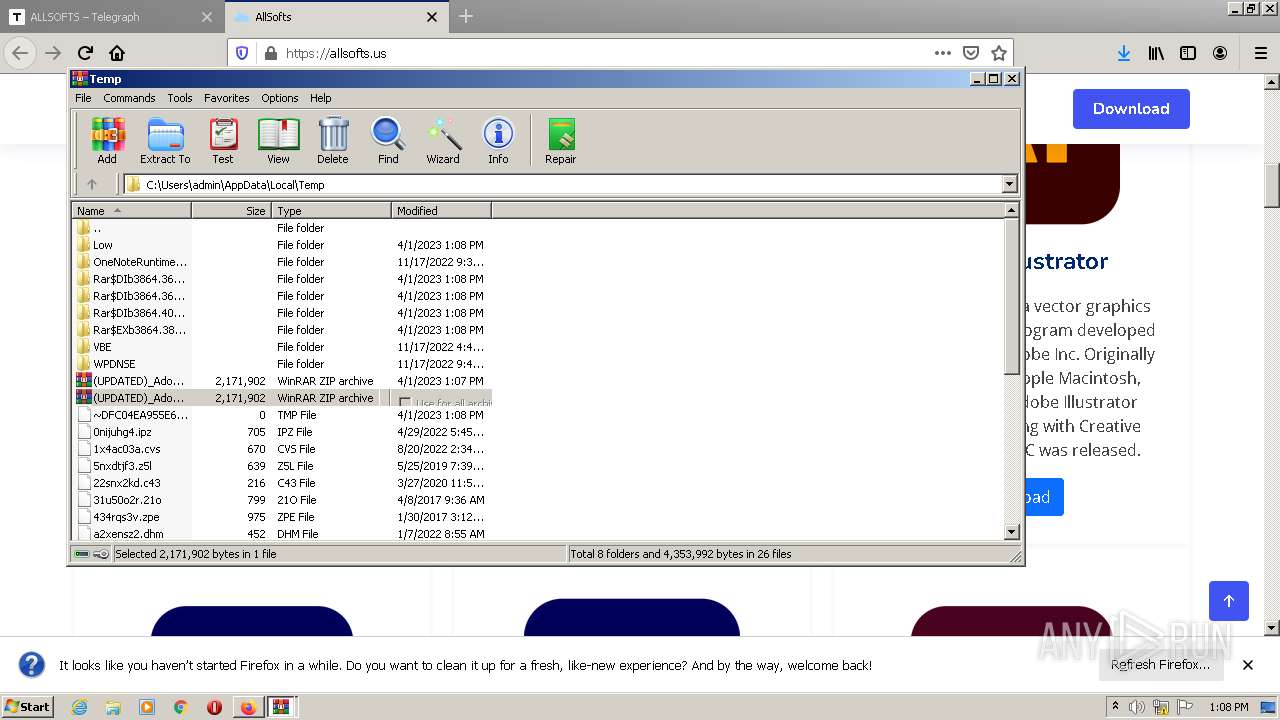
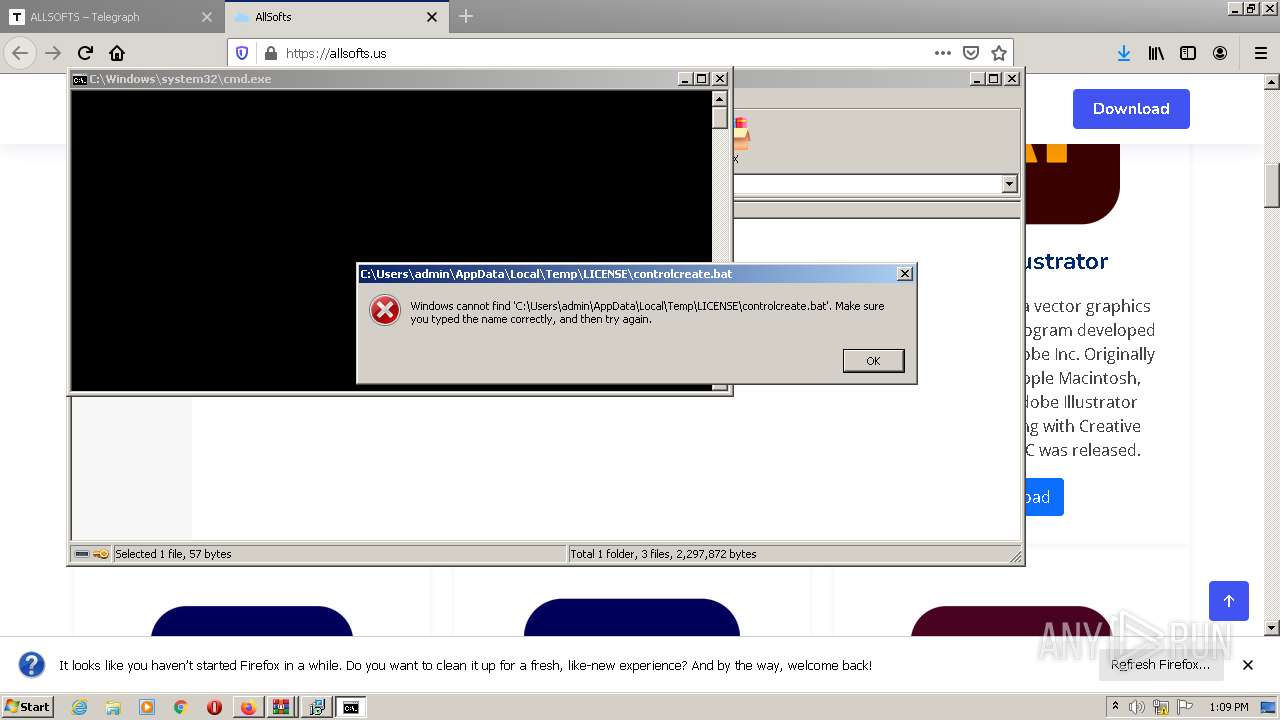
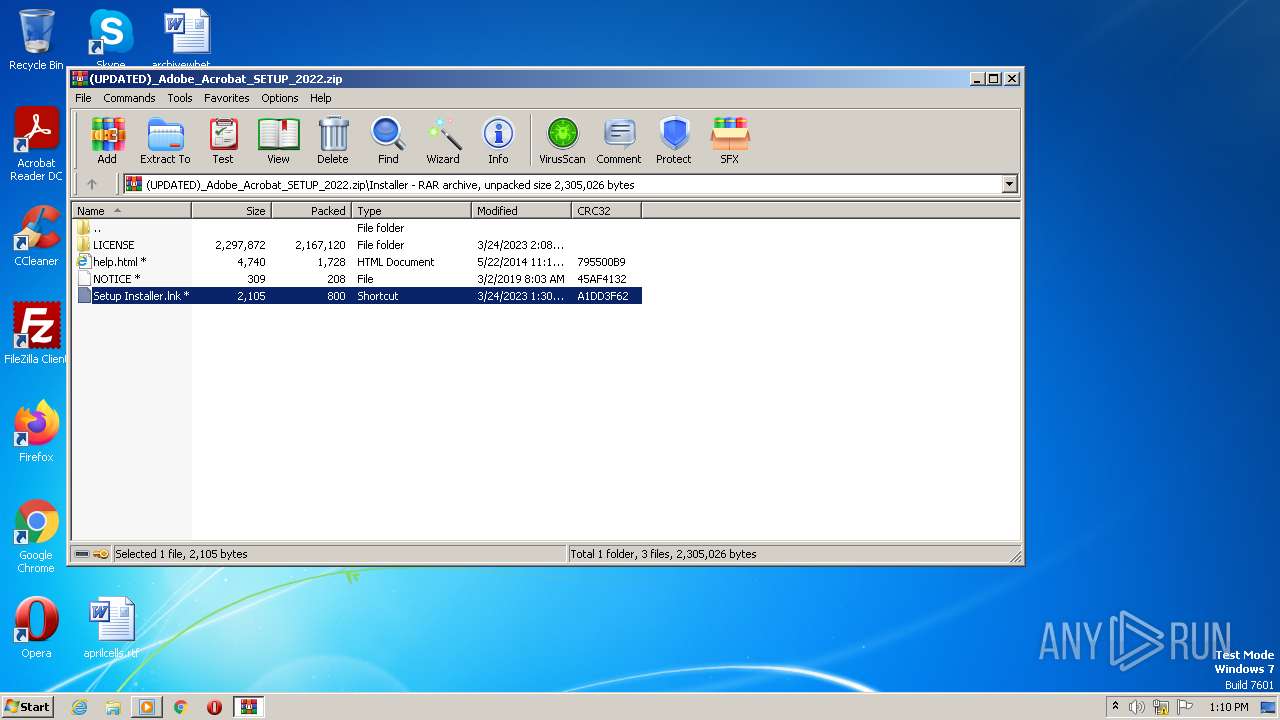
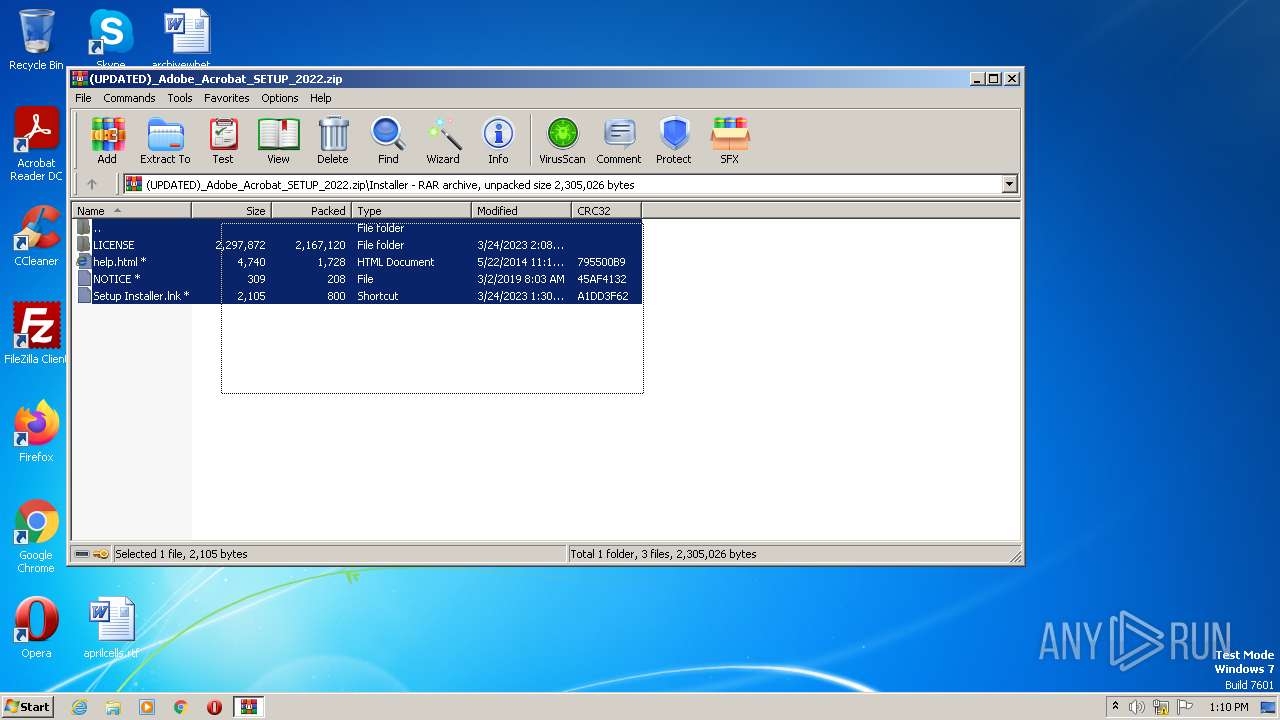
Starts CMD.EXE for commands execution
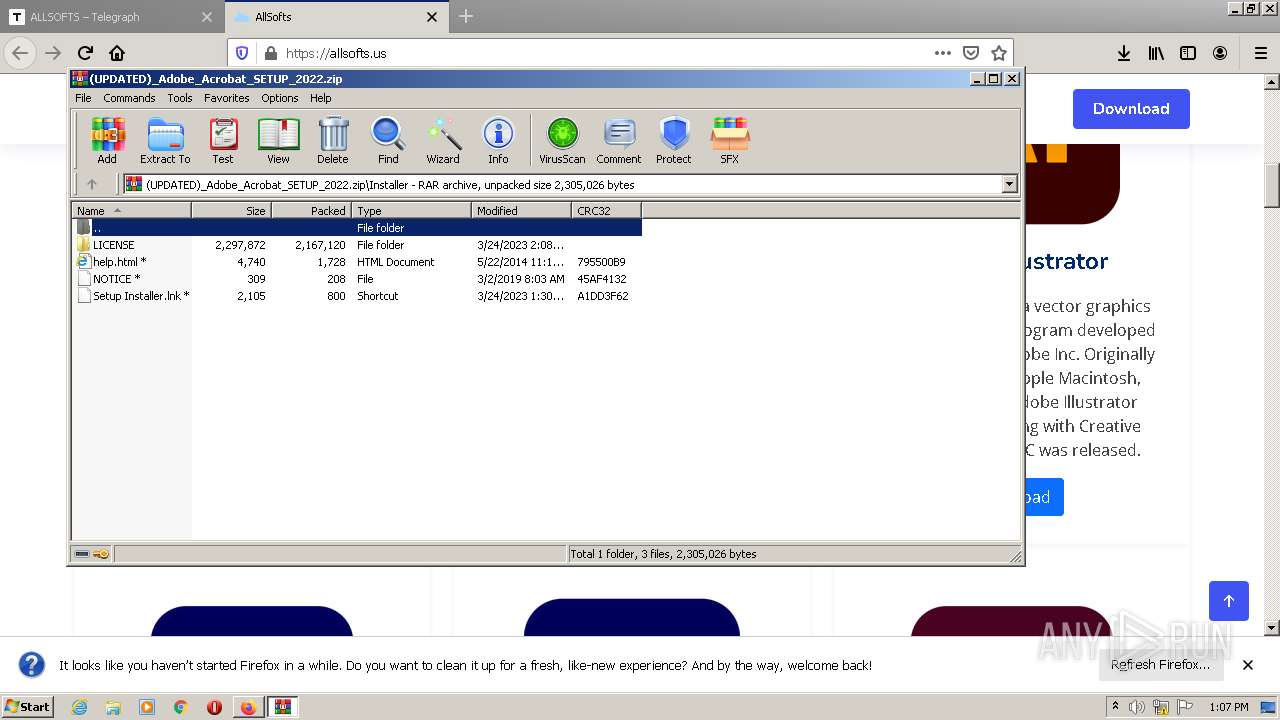
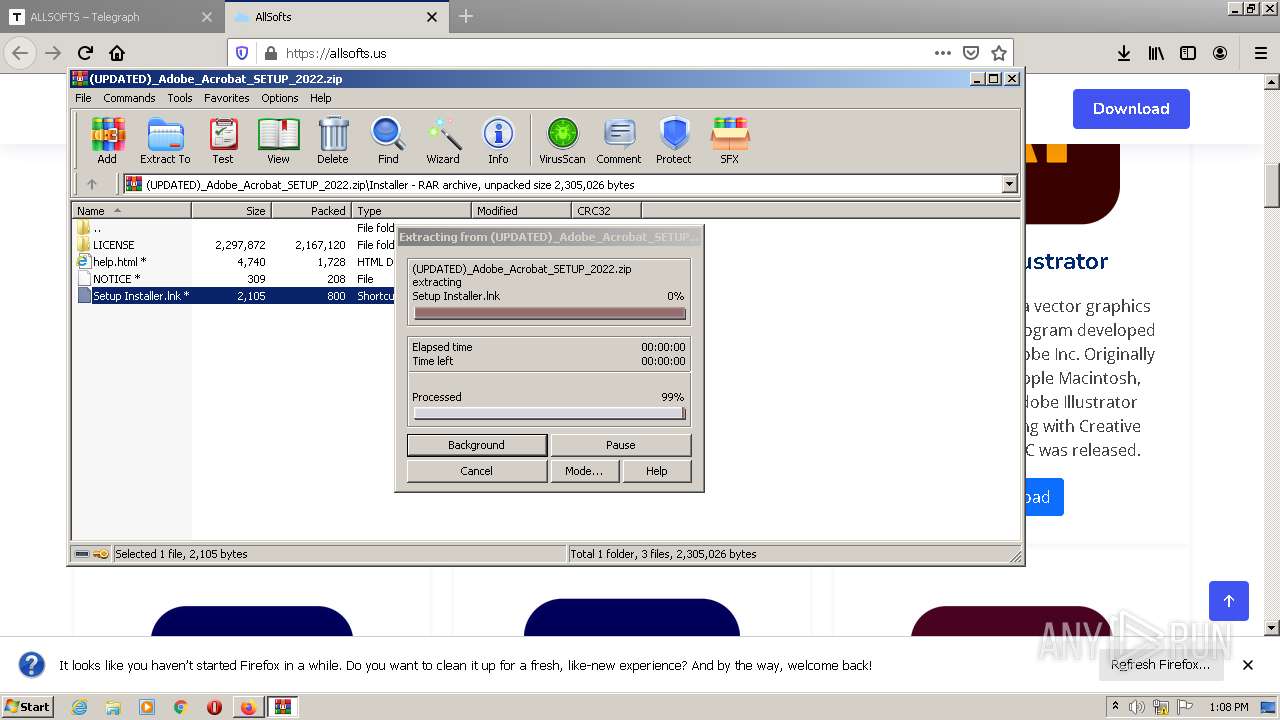
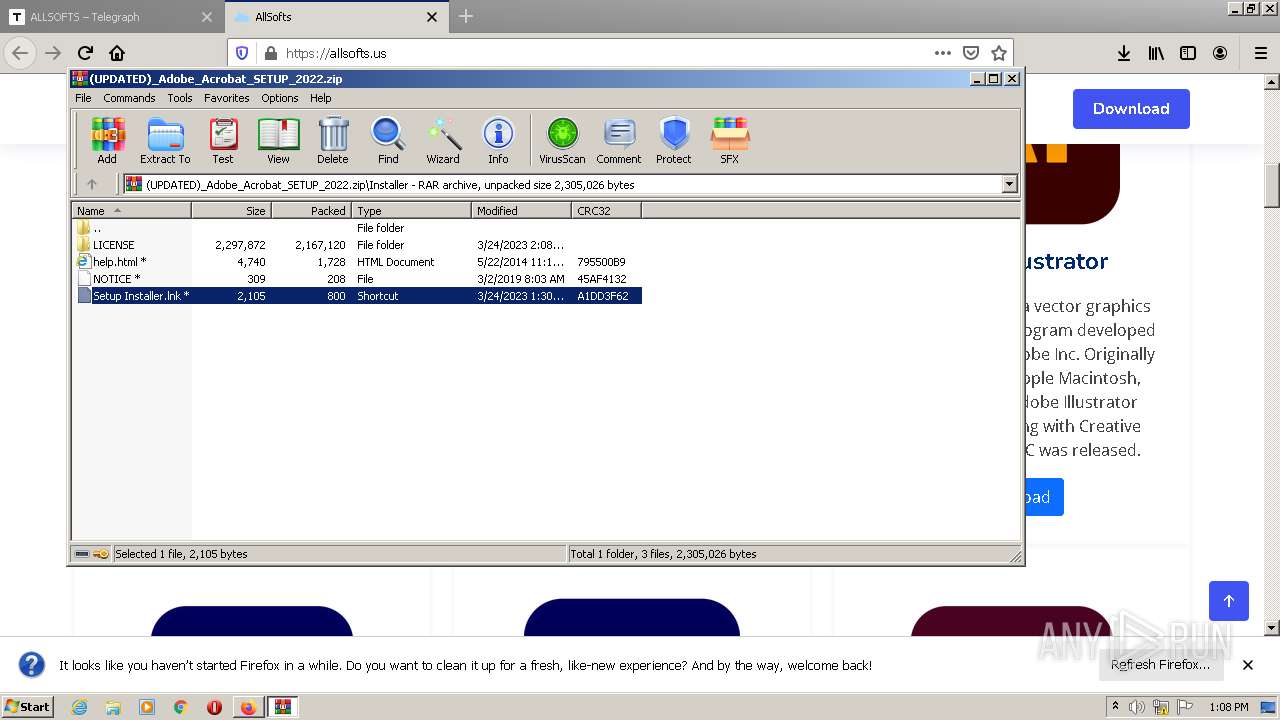
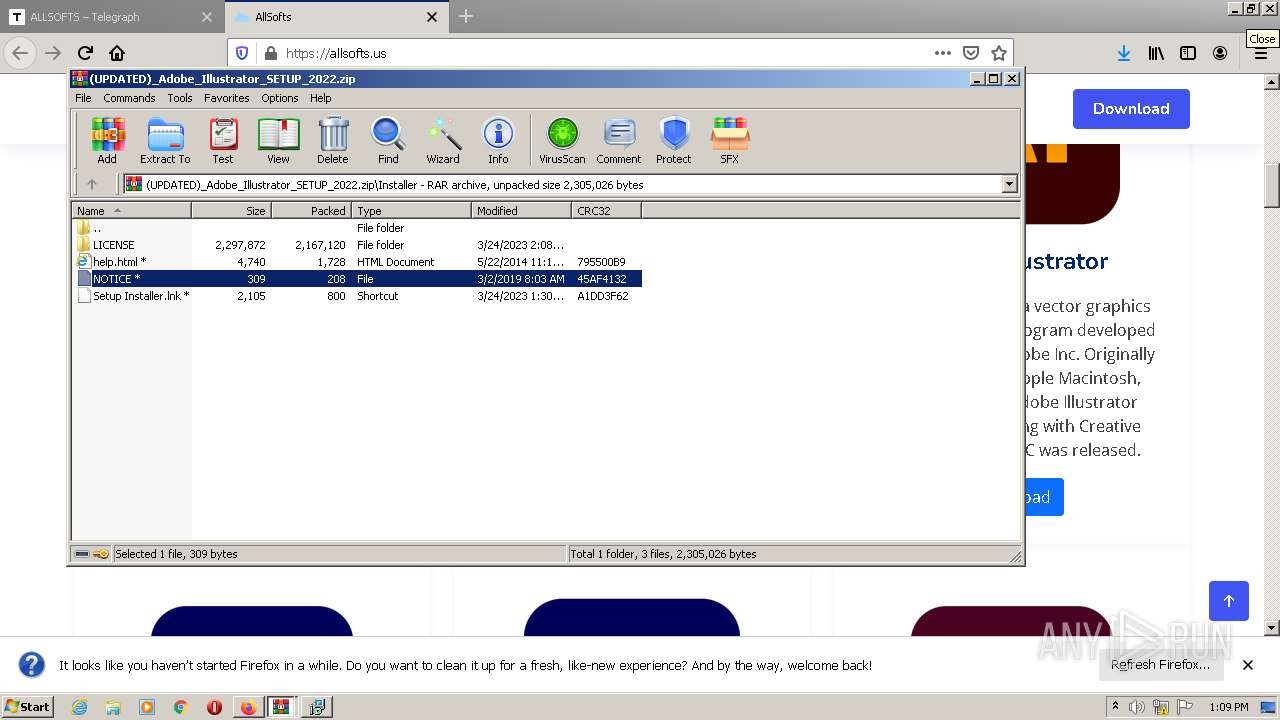
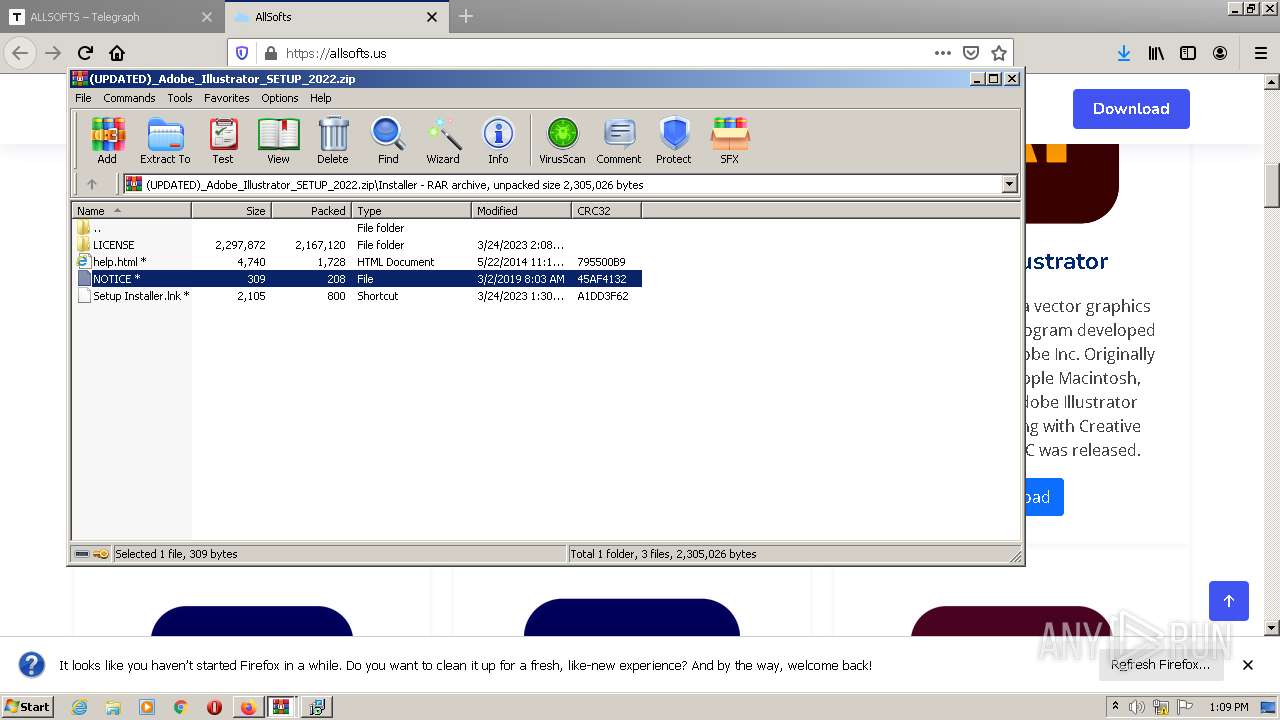
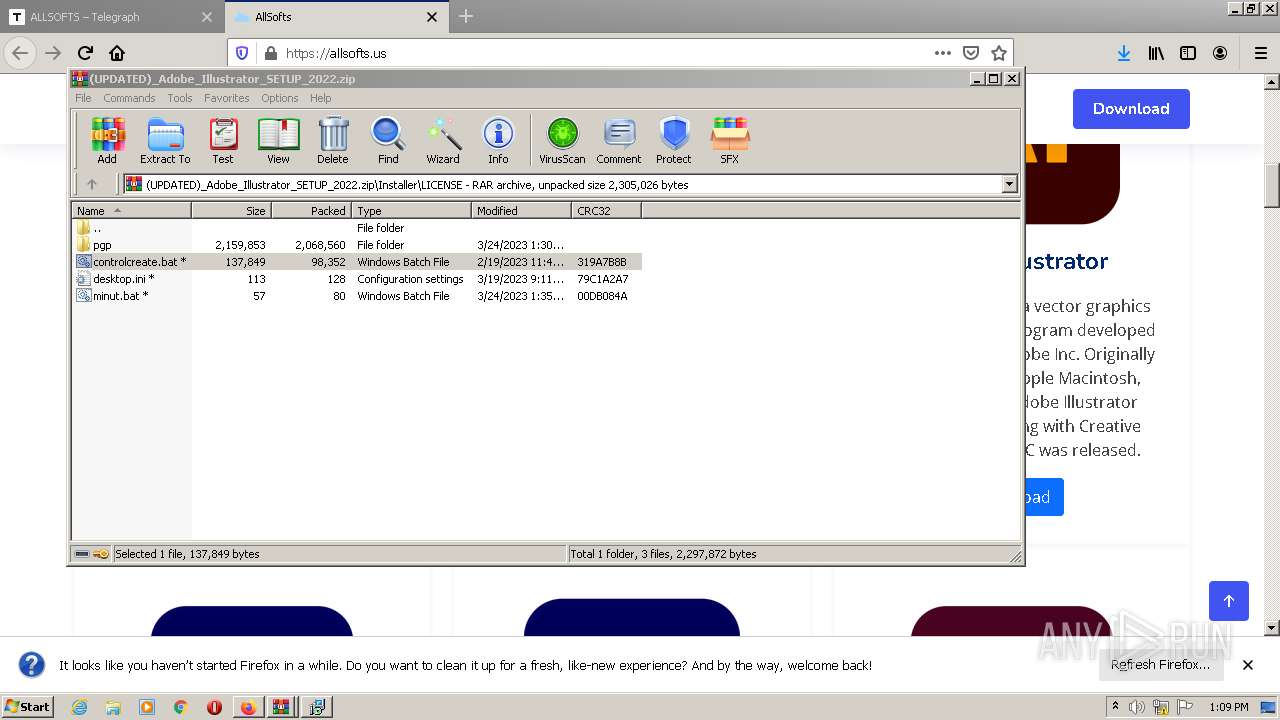
- WinRAR.exe (PID: 3864)
- WinRAR.exe (PID: 3784)
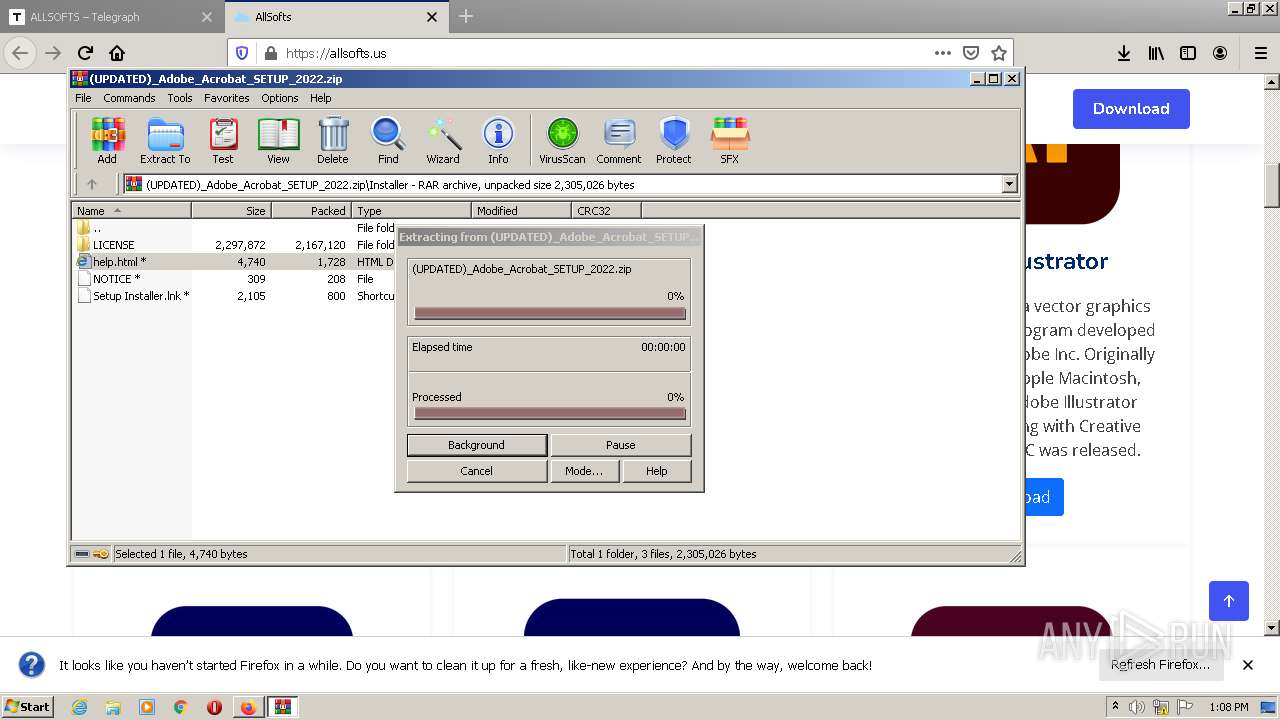
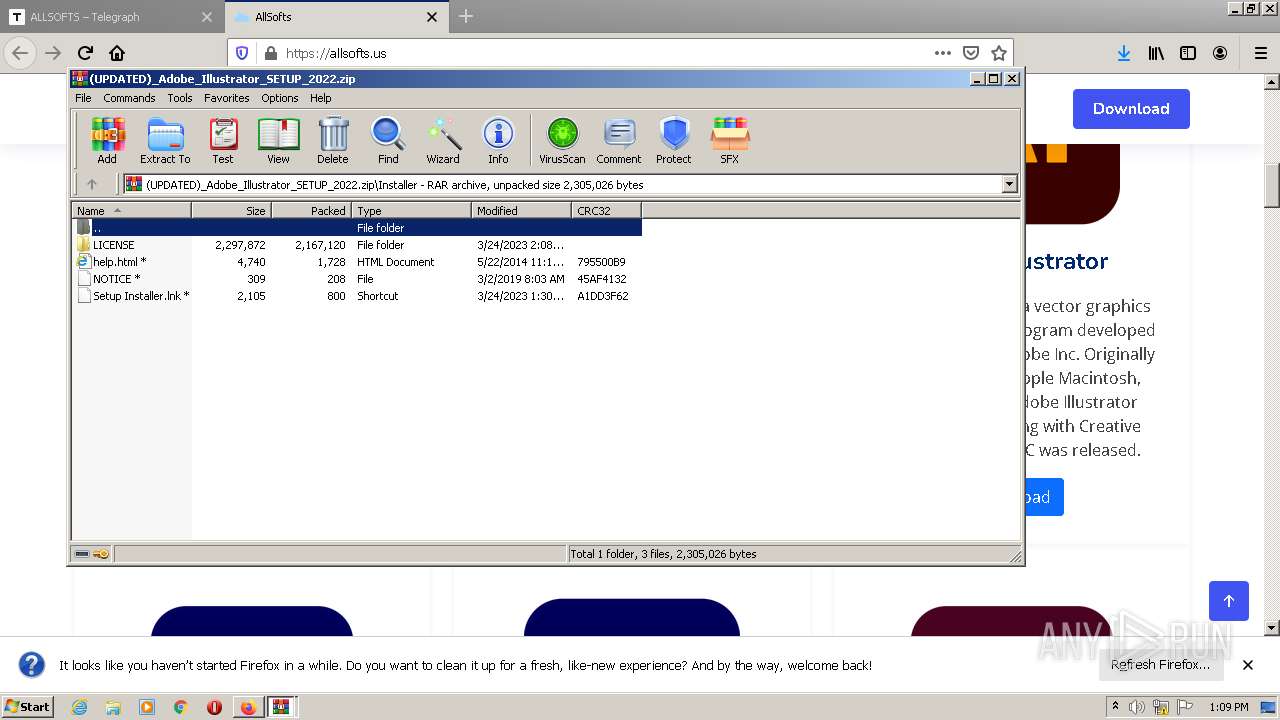
Executing commands from a ".bat" file
- WinRAR.exe (PID: 3864)
- WinRAR.exe (PID: 3784)
Process communicates with Telegram (possibly using it as an attacker's C2 server)
- firefox.exe (PID: 976)
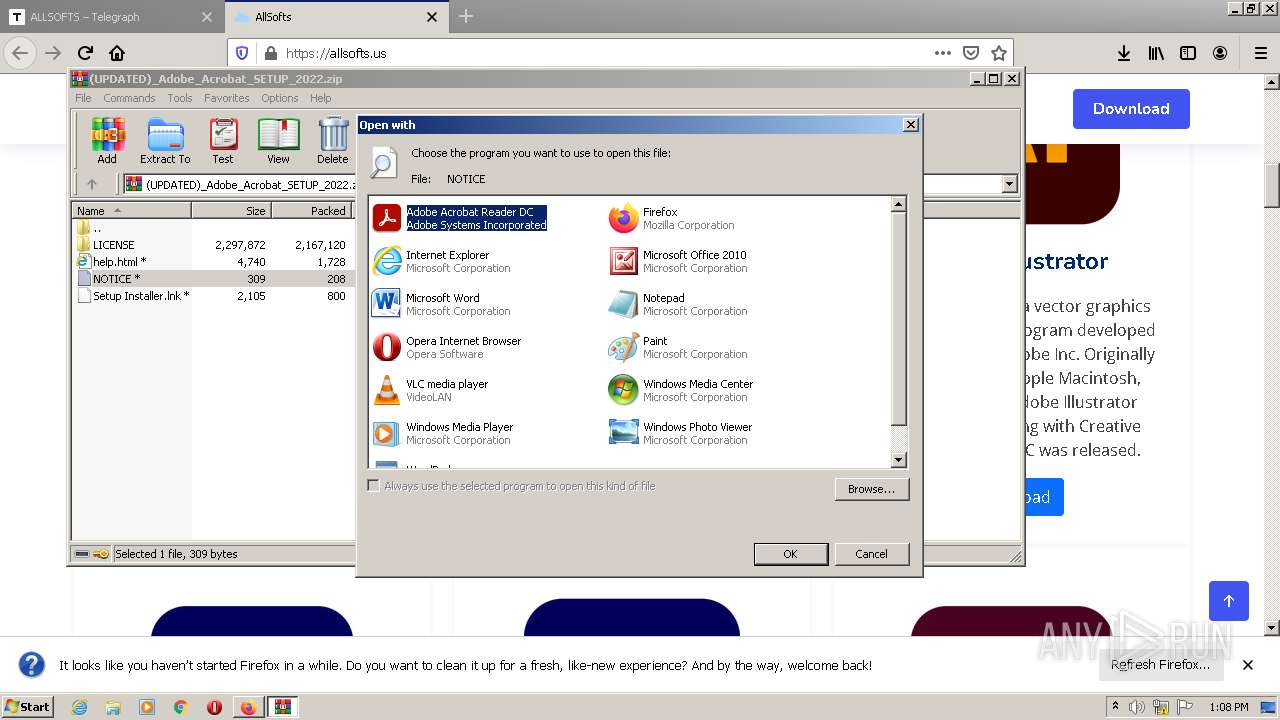
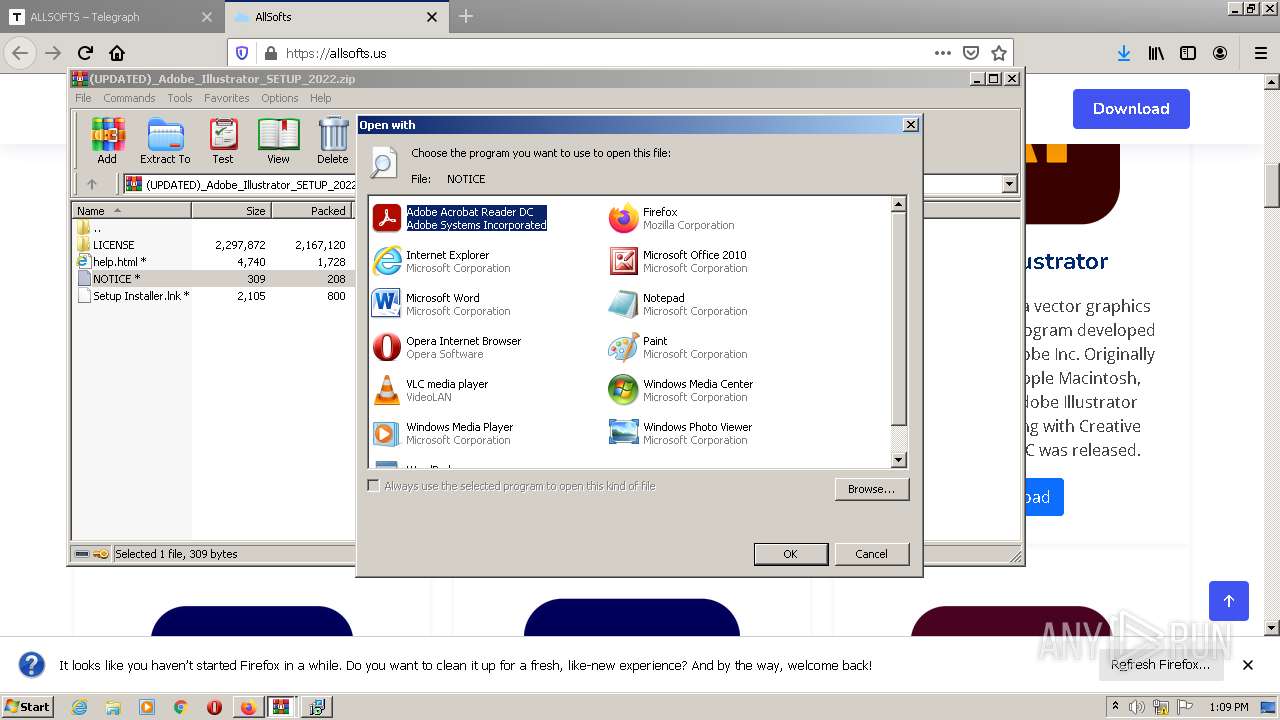
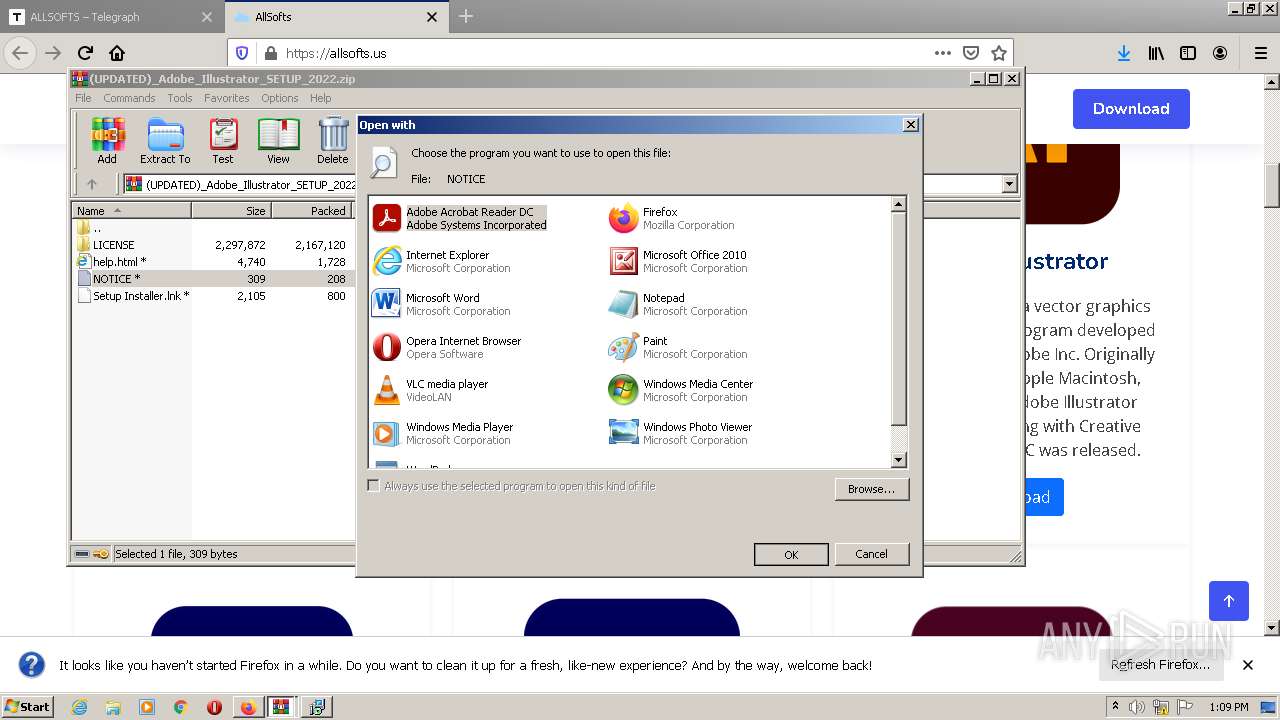
Uses RUNDLL32.EXE to load library
- WinRAR.exe (PID: 3864)
- WinRAR.exe (PID: 3784)
Write to the desktop.ini file (may be used to cloak folders)
- WinRAR.exe (PID: 3864)
Reads the Internet Settings
- rundll32.exe (PID: 1068)
Executable content was dropped or overwritten
- cmd.exe (PID: 920)
Uses ATTRIB.EXE to modify file attributes
- cmd.exe (PID: 920)
Checks Windows Trust Settings
- controlcreate.bat.exe (PID: 2924)
Reads security settings of Internet Explorer
- controlcreate.bat.exe (PID: 2924)
Connects to FTP
- controlcreate.bat.exe (PID: 2924)
INFO
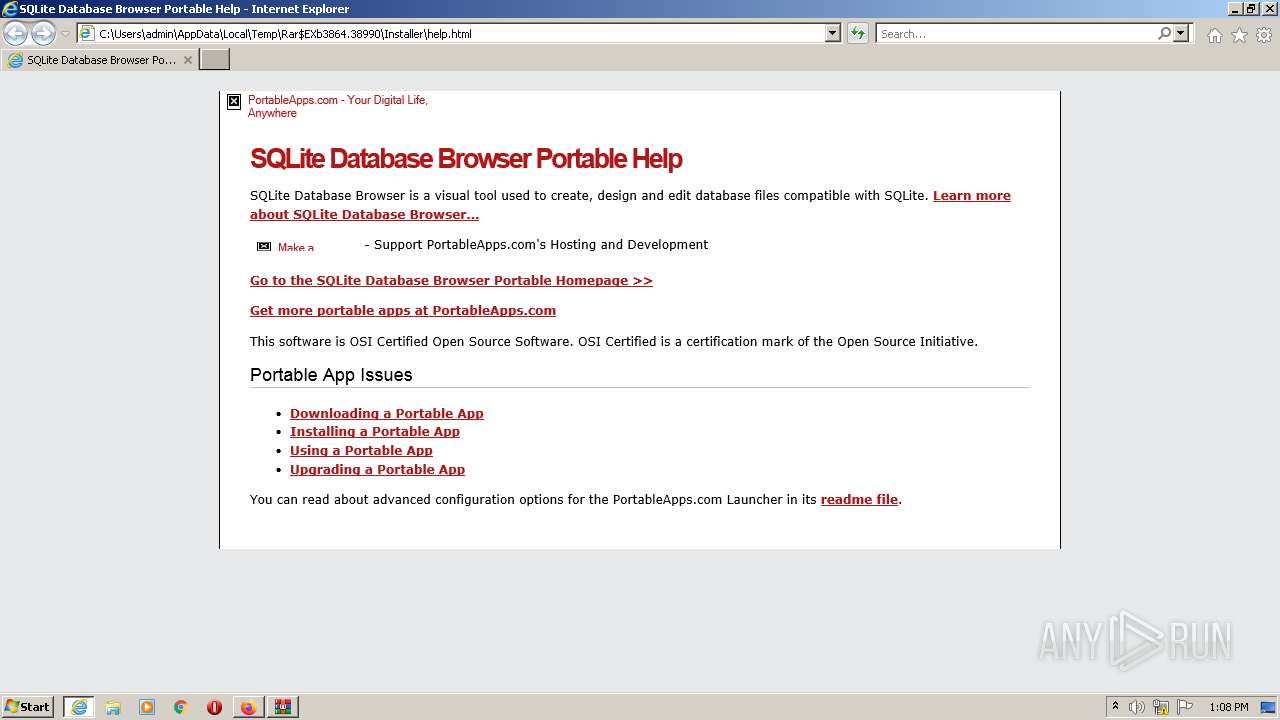
Application launched itself
- firefox.exe (PID: 976)
- iexplore.exe (PID: 3124)
- iexplore.exe (PID: 3164)
- firefox.exe (PID: 2660)
- RdrCEF.exe (PID: 2136)
- AcroRd32.exe (PID: 1800)
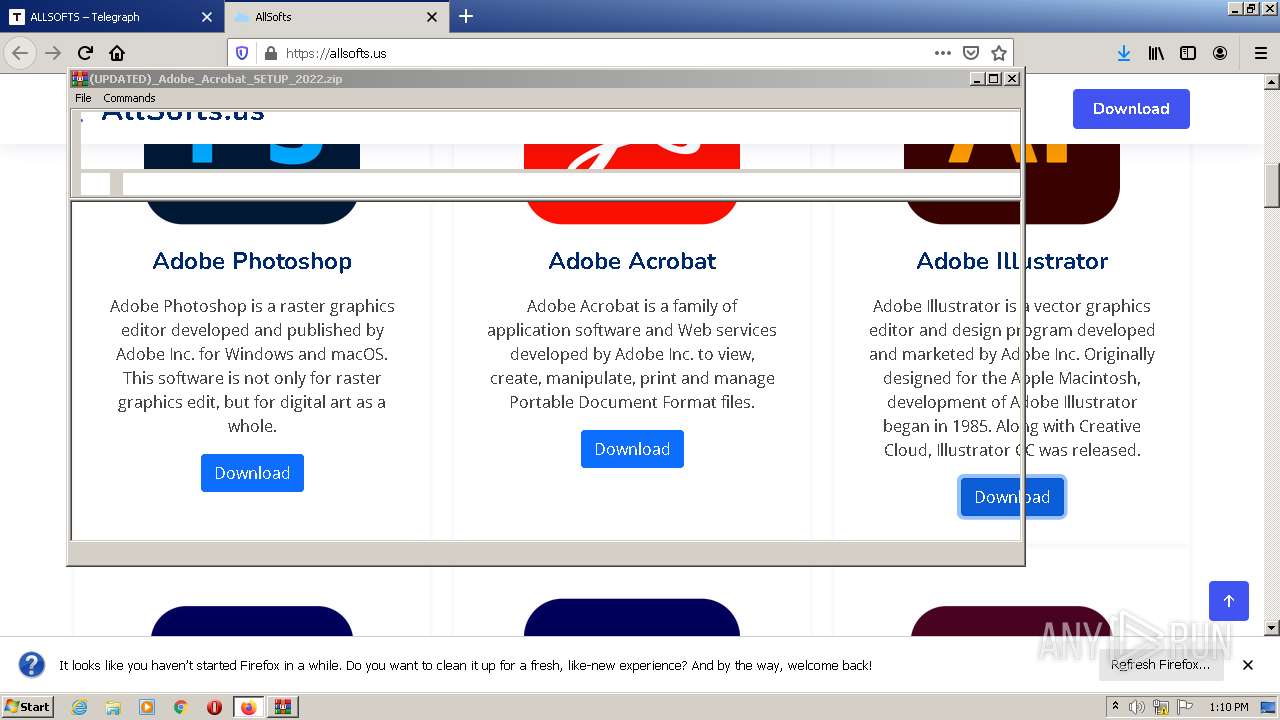
The process uses the downloaded file
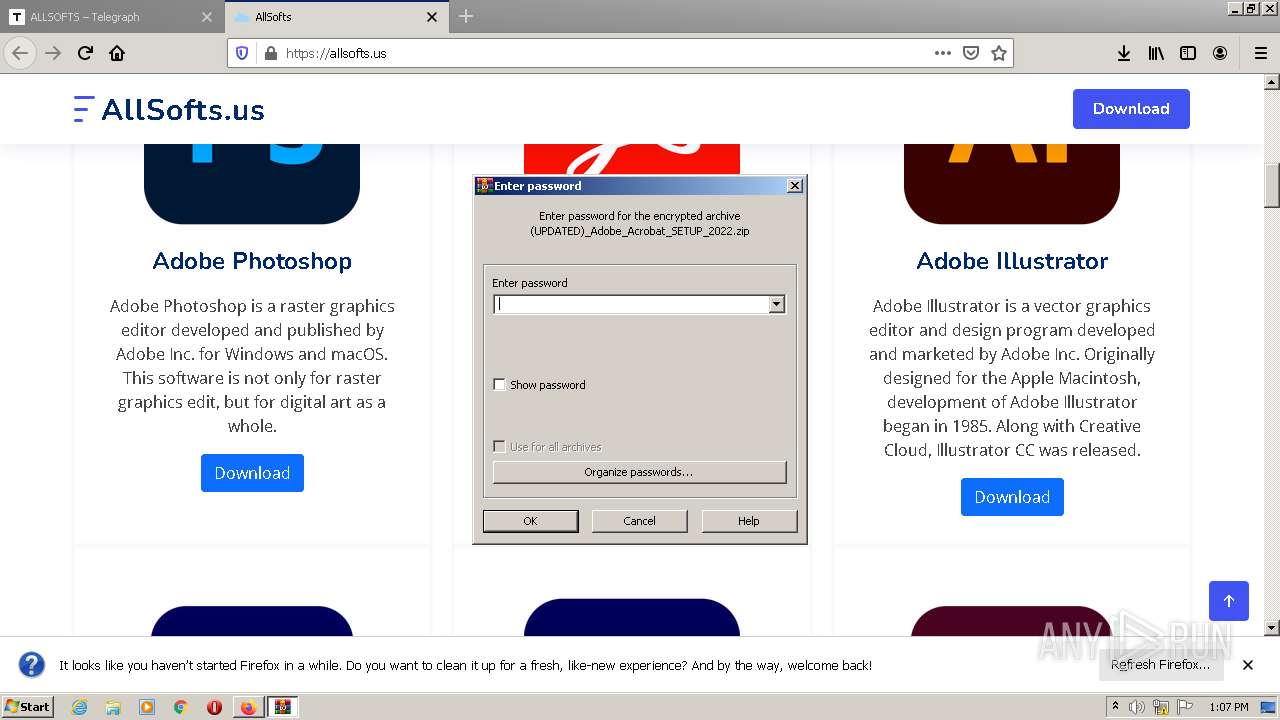
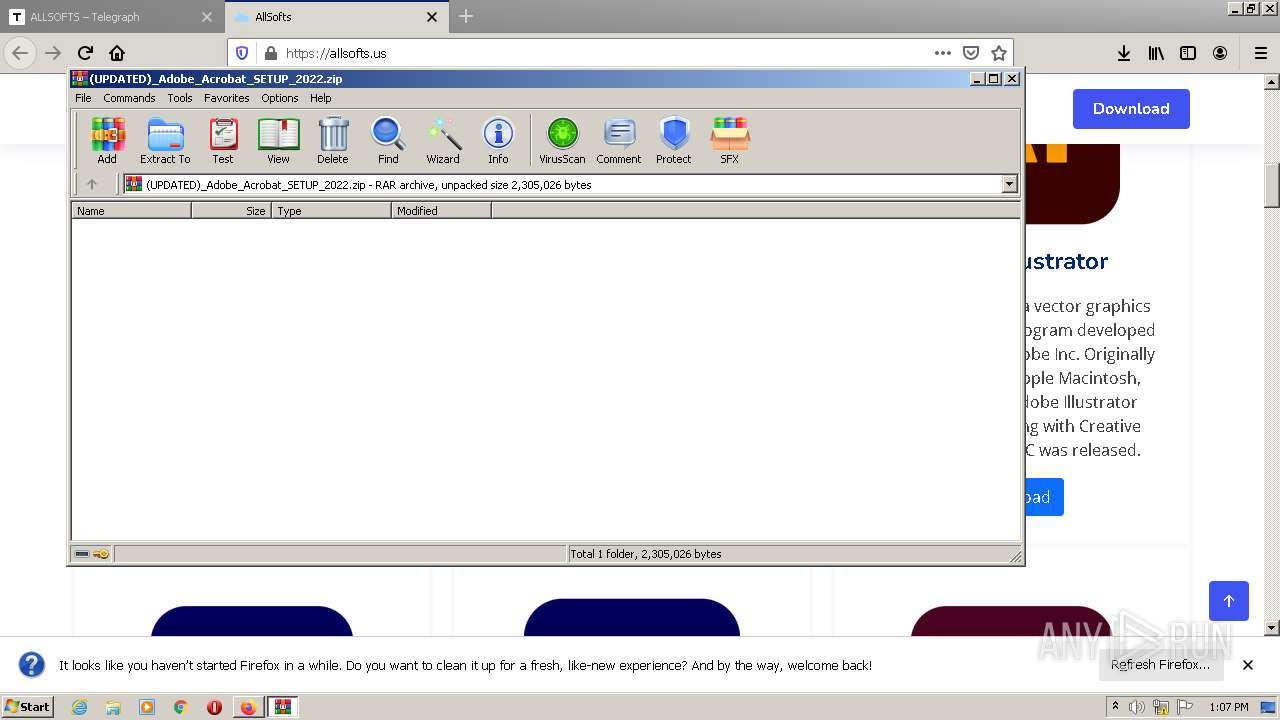
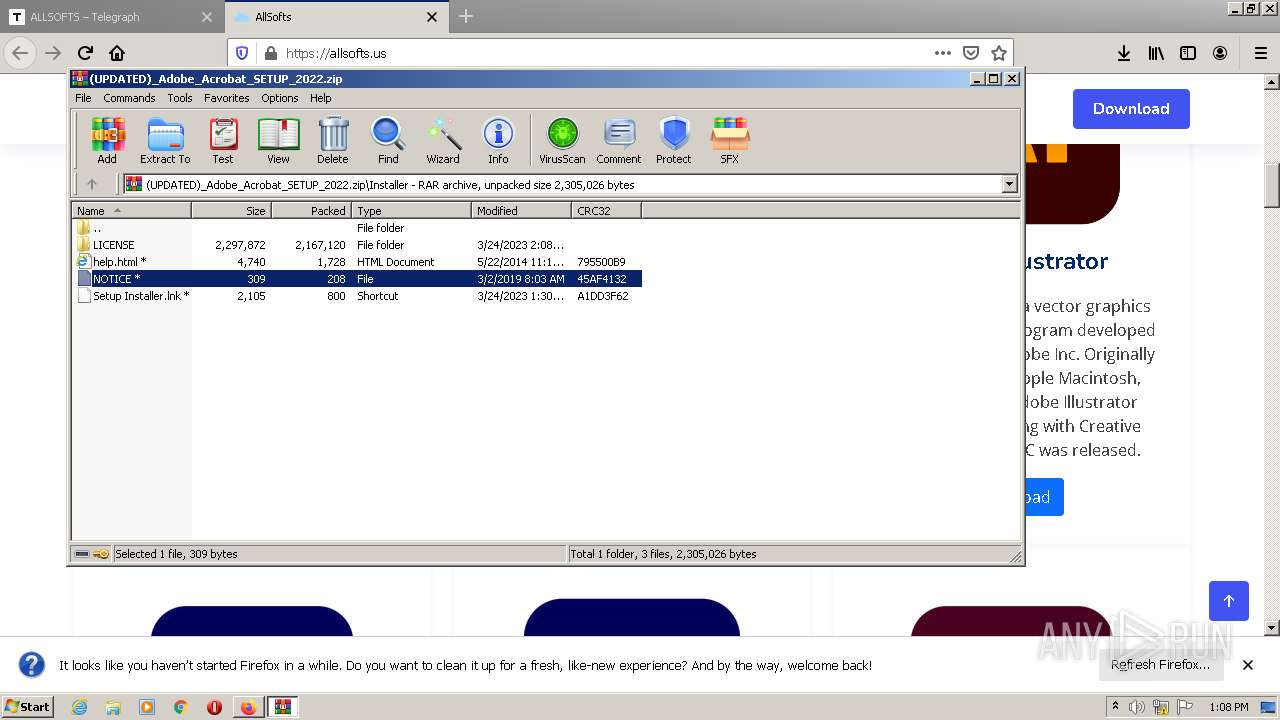
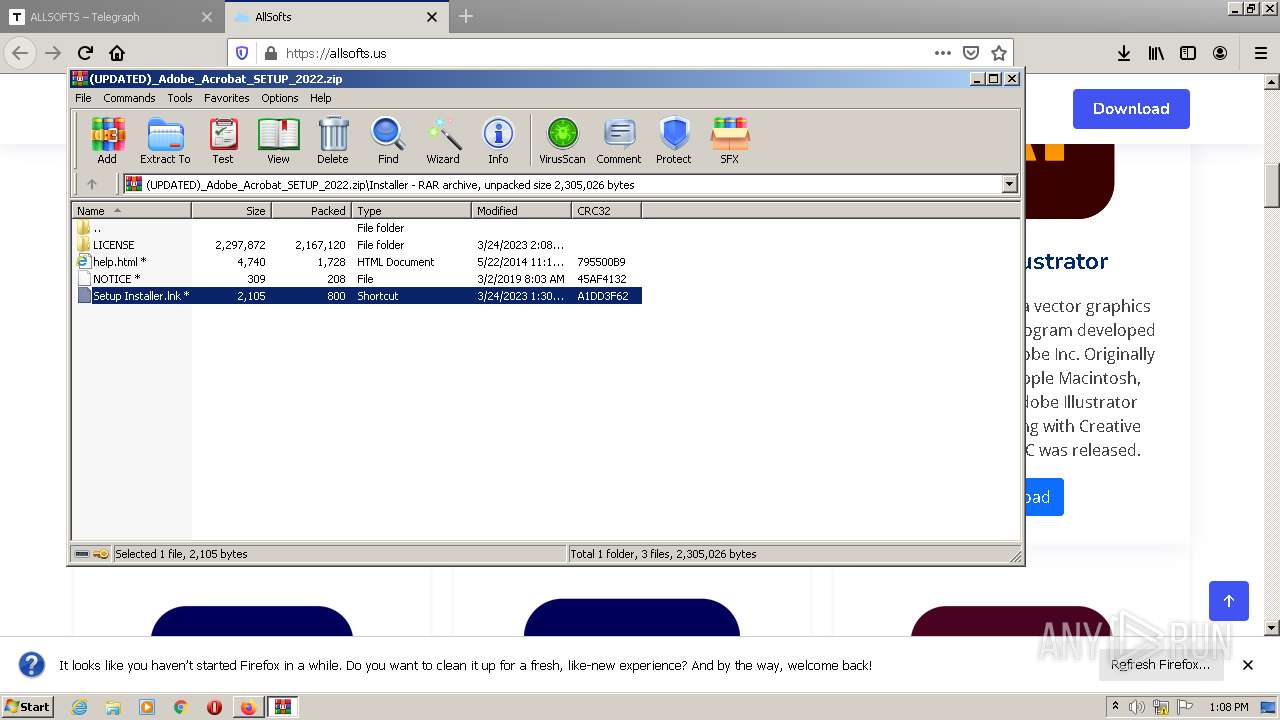
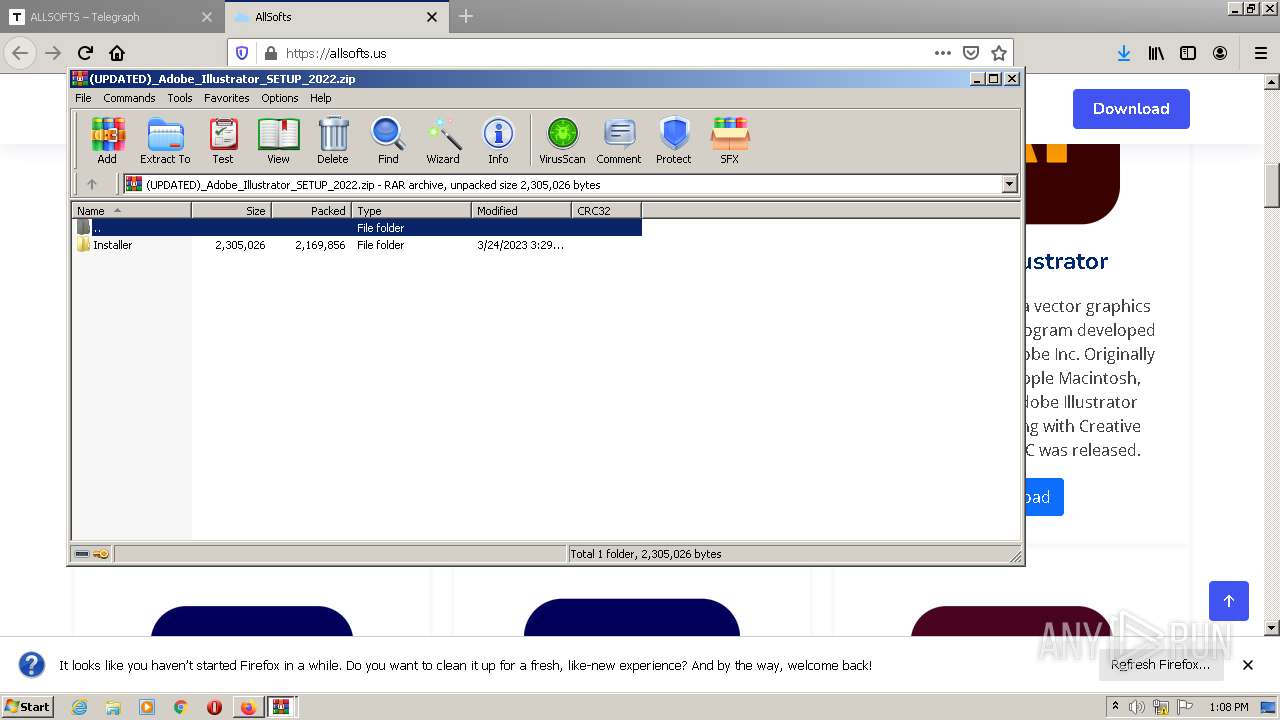
- WinRAR.exe (PID: 3864)
- firefox.exe (PID: 976)
- WinRAR.exe (PID: 3784)
The process checks LSA protection
- rundll32.exe (PID: 3852)
- cmd.exe (PID: 1960)
- cmd.exe (PID: 1592)
- cmd.exe (PID: 3580)
- controlcreate.bat.exe (PID: 2924)
- rundll32.exe (PID: 1068)
- cmd.exe (PID: 2860)
- explorer.exe (PID: 2344)
Manual execution by a user
- WinRAR.exe (PID: 3784)
- WinRAR.exe (PID: 3864)
- explorer.exe (PID: 2344)
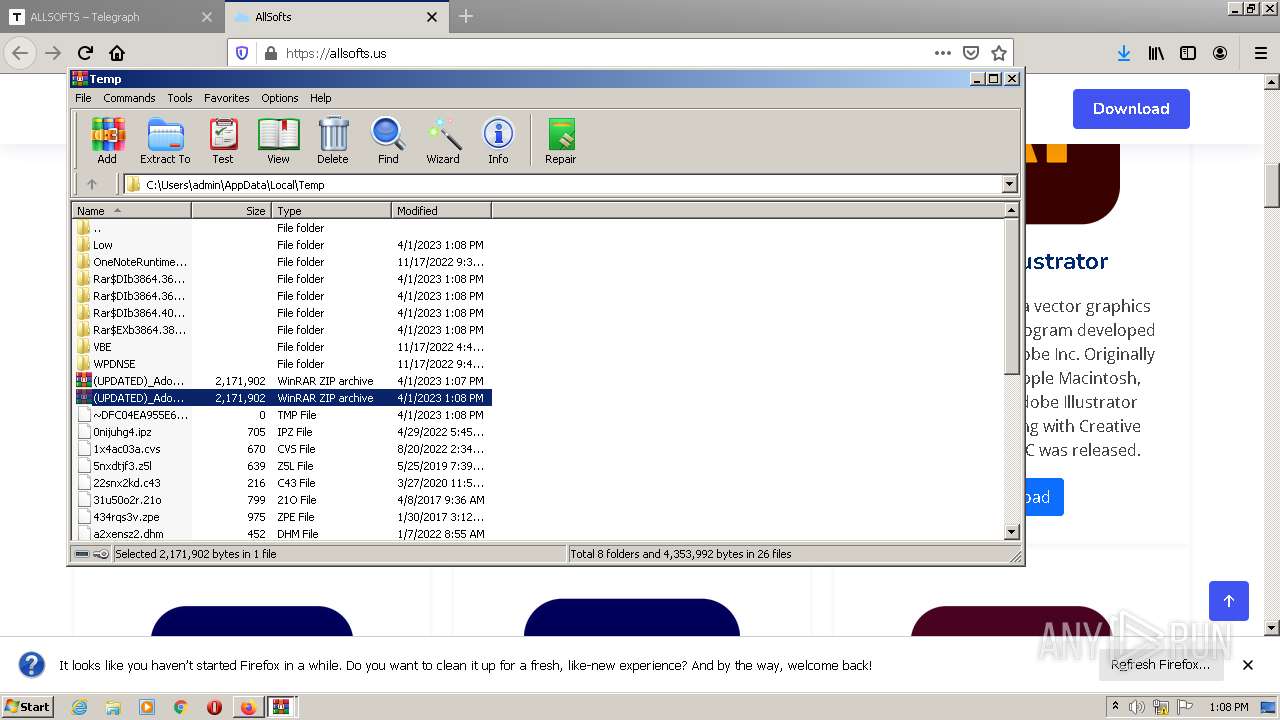
Create files in a temporary directory
- iexplore.exe (PID: 3124)
- firefox.exe (PID: 976)
- cmd.exe (PID: 920)
- controlcreate.bat.exe (PID: 2924)
Checks supported languages
- controlcreate.bat.exe (PID: 2924)
Reads the computer name
- controlcreate.bat.exe (PID: 2924)
Process checks Powershell version
- controlcreate.bat.exe (PID: 2924)
Reads the machine GUID from the registry
- controlcreate.bat.exe (PID: 2924)
Executable content was dropped or overwritten
- firefox.exe (PID: 976)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
79
Monitored processes
33
Malicious processes
5
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 660 | "C:\Program Files\Adobe\Acrobat Reader DC\Reader\AcroCEF\RdrCEF.exe" --type=renderer --log-file="C:\Program Files\Adobe\Acrobat Reader DC\Reader\AcroCEF\debug.log" --touch-events=enabled --field-trial-handle=1156,9197454262383184080,11901390317728797055,131072 --disable-features=NetworkService,VizDisplayCompositor --disable-gpu-compositing --lang=en-US --disable-pack-loading --log-file="C:\Program Files\Adobe\Acrobat Reader DC\Reader\AcroCEF\debug.log" --log-severity=disable --product-version="ReaderServices/20.13.20064 Chrome/80.0.0.0" --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=12707390342553446080 --renderer-client-id=7 --mojo-platform-channel-handle=1360 --allow-no-sandbox-job /prefetch:1 | C:\Program Files\Adobe\Acrobat Reader DC\Reader\AcroCEF\RdrCEF.exe | — | RdrCEF.exe | |||||||||||
User: admin Company: Adobe Systems Incorporated Integrity Level: LOW Description: Adobe RdrCEF Exit code: 0 Version: 20.13.20064.405839 Modules
| |||||||||||||||
| 664 | "C:\Program Files\Mozilla Firefox\firefox.exe" -contentproc --channel="976.20.2075635672\893083289" -childID 3 -isForBrowser -prefsHandle 2052 -prefMapHandle 1716 -prefsLen 6644 -prefMapSize 238726 -parentBuildID 20201112153044 -appdir "C:\Program Files\Mozilla Firefox\browser" - 976 "\\.\pipe\gecko-crash-server-pipe.976" 3376 tab | C:\Program Files\Mozilla Firefox\firefox.exe | — | firefox.exe | |||||||||||
User: admin Company: Mozilla Corporation Integrity Level: LOW Description: Firefox Exit code: 0 Version: 83.0 Modules
| |||||||||||||||
| 920 | C:\Windows\system32\cmd.exe /c ""C:\Users\admin\AppData\Local\Temp\Rar$DIb3784.46931\controlcreate.bat" " | C:\Windows\System32\cmd.exe | WinRAR.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 976 | "C:\Program Files\Mozilla Firefox\firefox.exe" https://www.telegra.ph/ALLSOFTS-03-21 | C:\Program Files\Mozilla Firefox\firefox.exe | firefox.exe | ||||||||||||
User: admin Company: Mozilla Corporation Integrity Level: MEDIUM Description: Firefox Exit code: 0 Version: 83.0 Modules
| |||||||||||||||
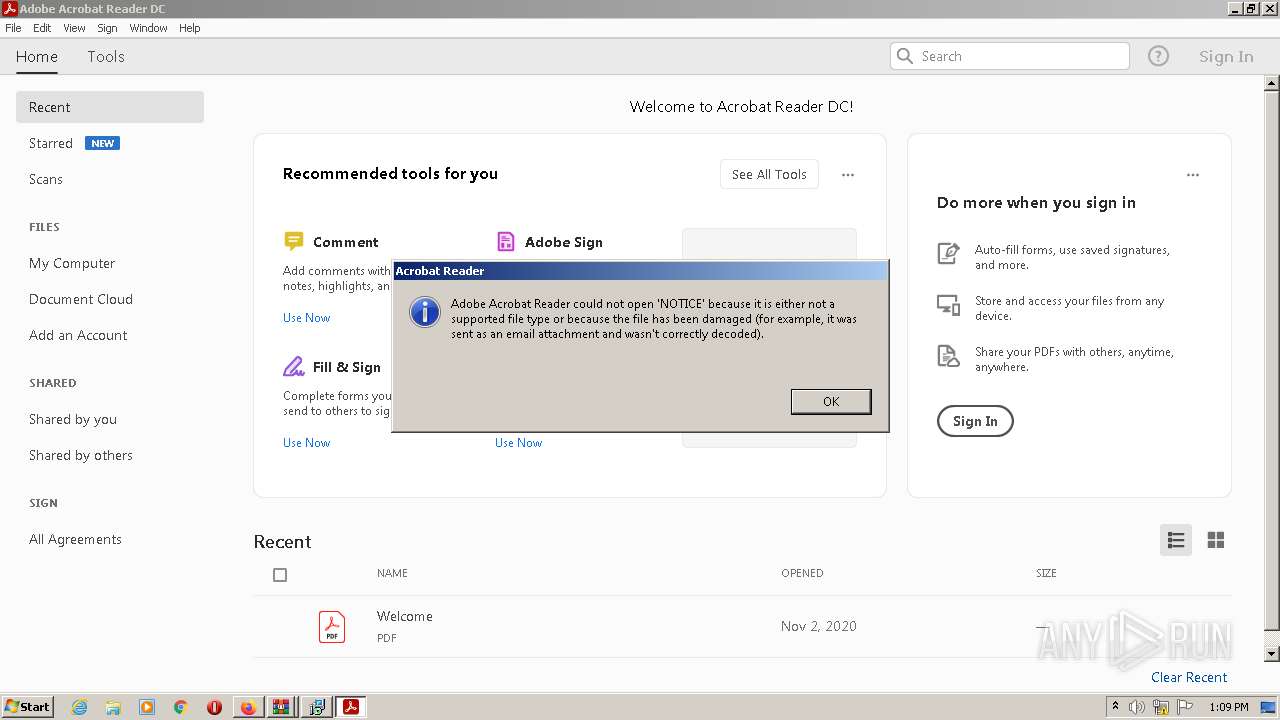
| 1068 | "C:\Windows\system32\rundll32.exe" C:\Windows\system32\shell32.dll,OpenAs_RunDLL C:\Users\admin\AppData\Local\Temp\Rar$DIb3784.42631\NOTICE | C:\Windows\System32\rundll32.exe | — | WinRAR.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows host process (Rundll32) Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1116 | attrib -s -h "C:\Users\admin\AppData\Local\Temp\Rar$DIb3784.46931\controlcreate.bat".exe | C:\Windows\System32\attrib.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Attribute Utility Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
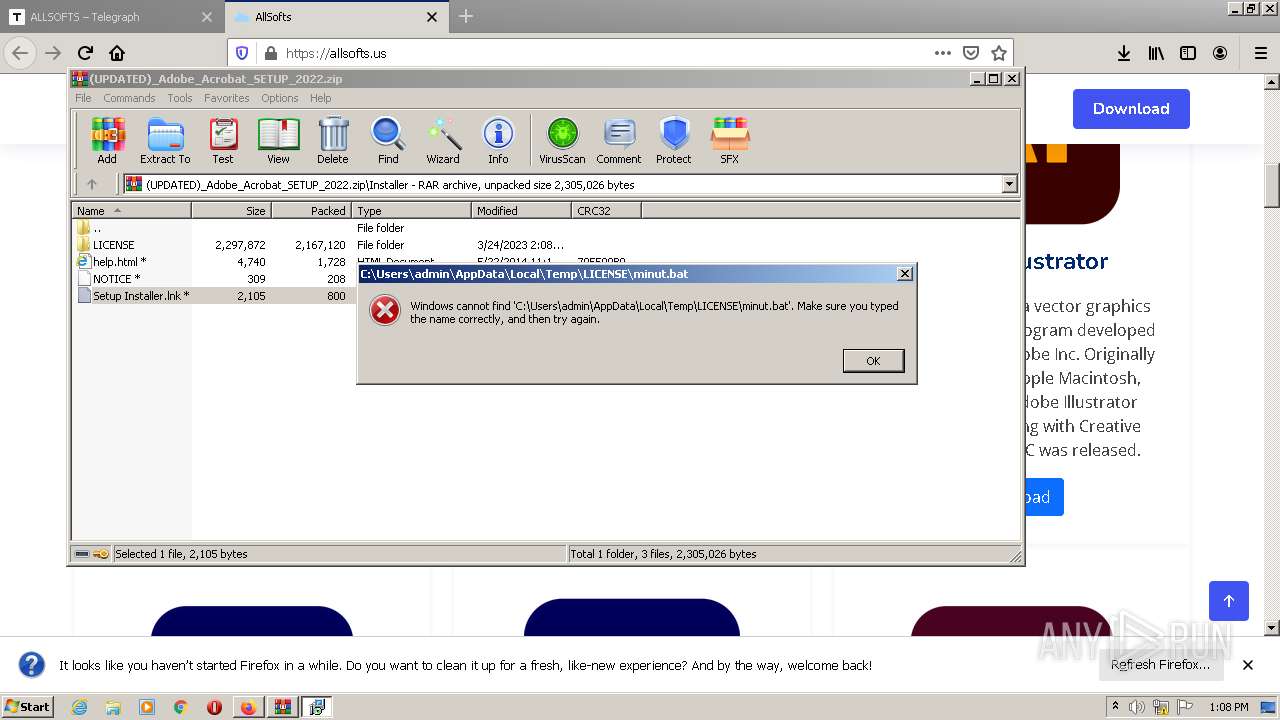
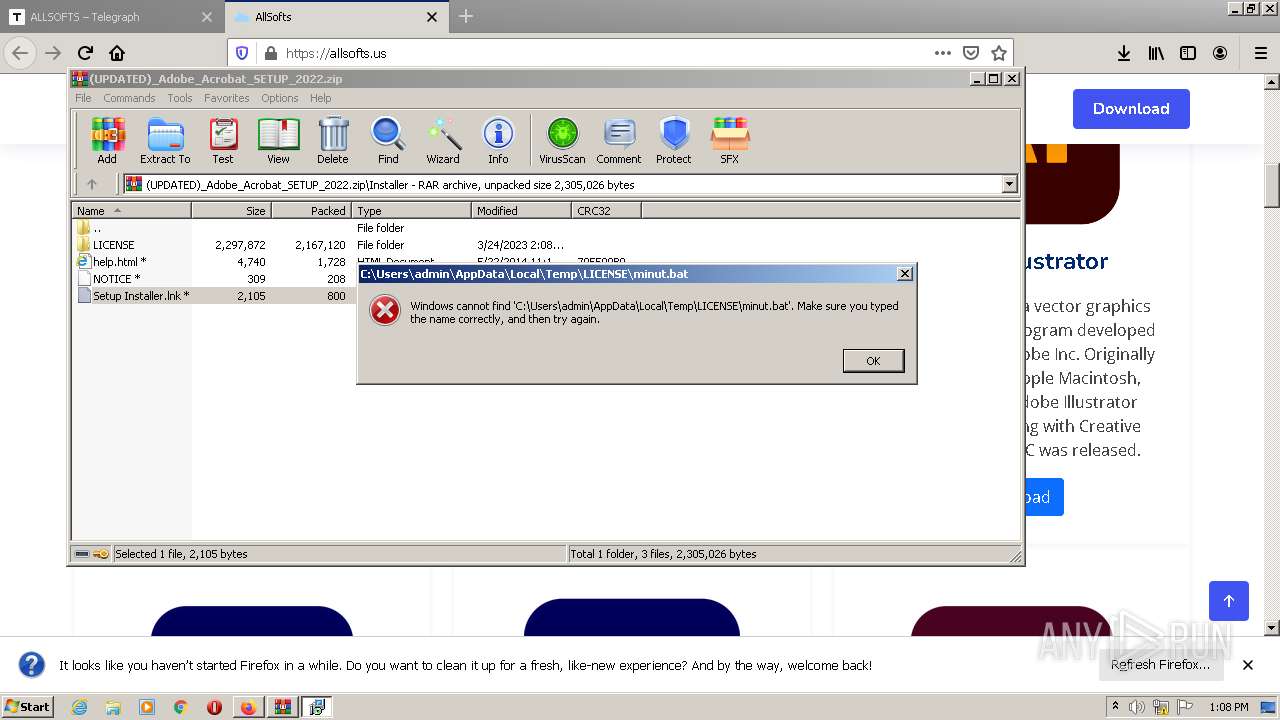
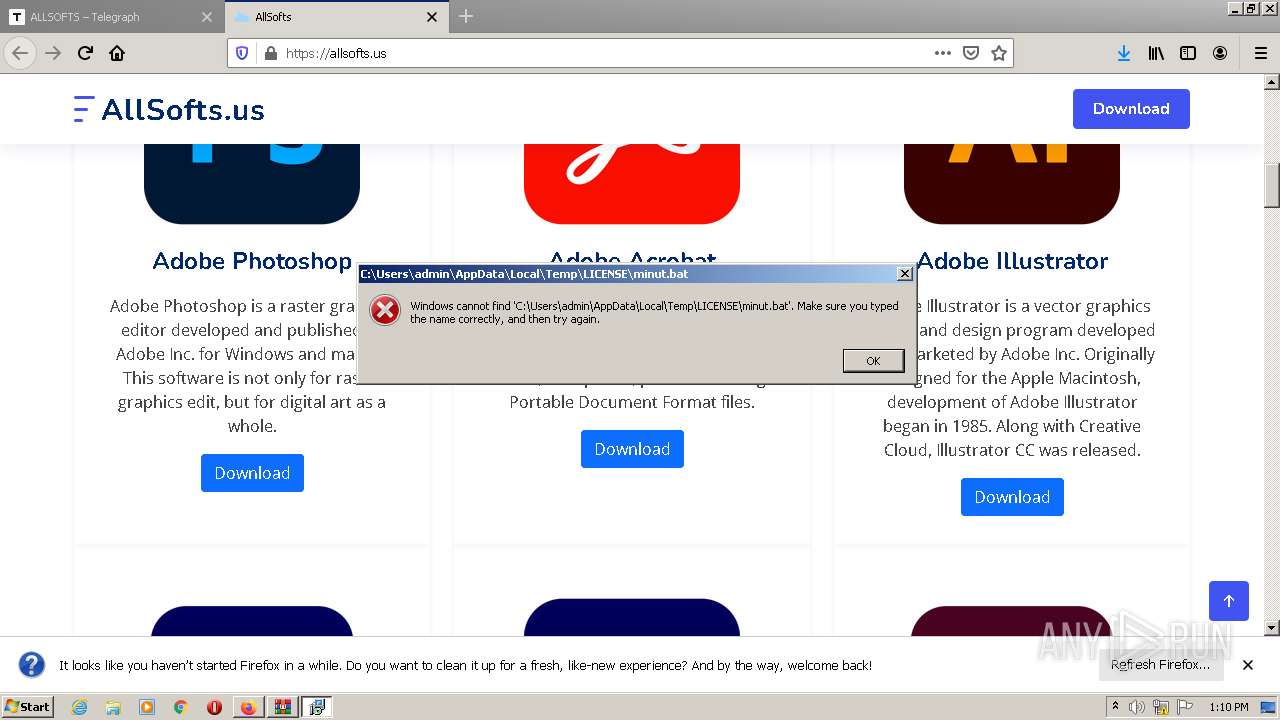
| 1592 | "C:\Windows\System32\cmd.exe" /C start "" /B "%CD%\LICENSE\minut.bat" | C:\Windows\System32\cmd.exe | — | WinRAR.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 1 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
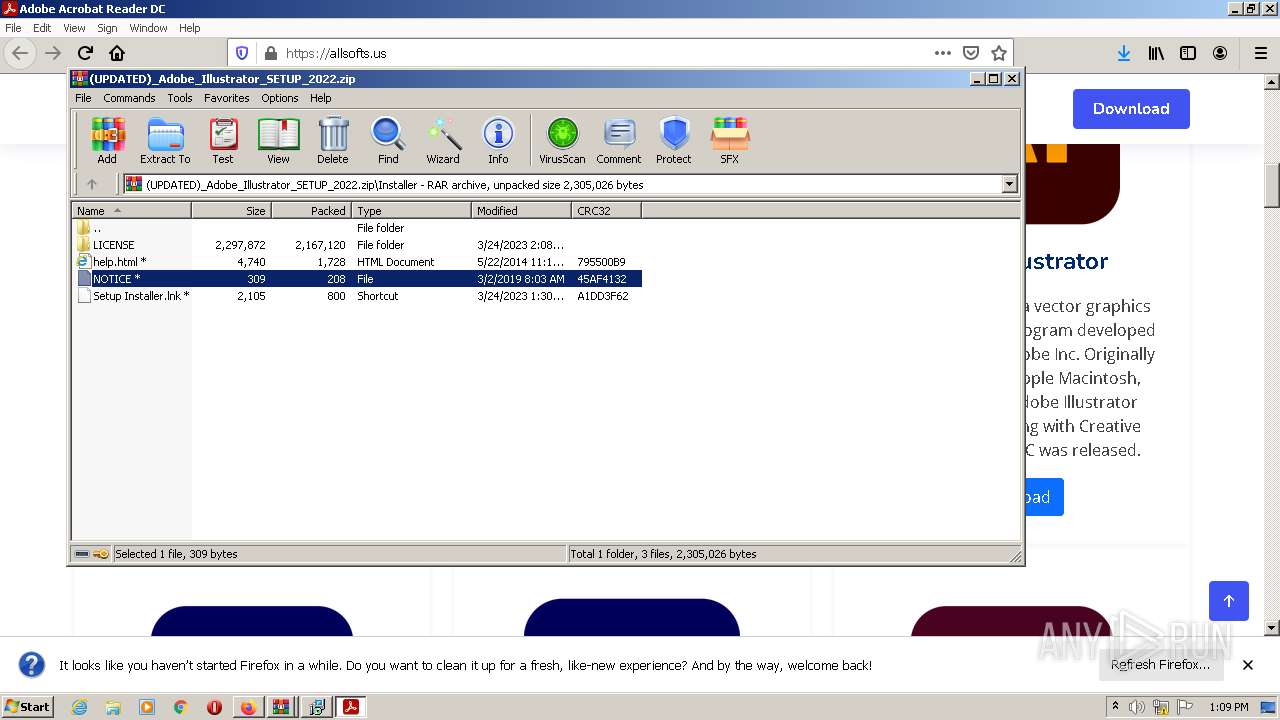
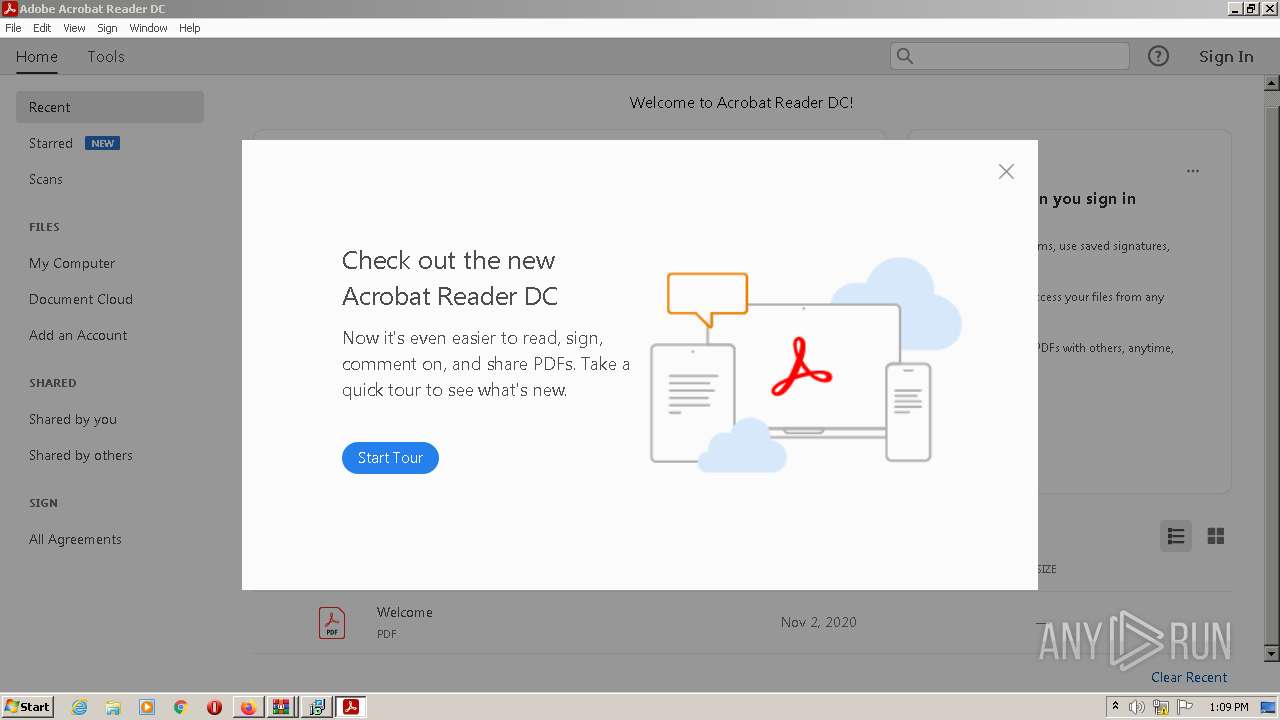
| 1800 | "C:\Program Files\Adobe\Acrobat Reader DC\Reader\AcroRd32.exe" "C:\Users\admin\AppData\Local\Temp\Rar$DIb3784.42631\NOTICE" | C:\Program Files\Adobe\Acrobat Reader DC\Reader\AcroRd32.exe | rundll32.exe | ||||||||||||
User: admin Company: Adobe Systems Incorporated Integrity Level: MEDIUM Description: Adobe Acrobat Reader DC Exit code: 1 Version: 20.13.20064.405839 Modules
| |||||||||||||||
| 1960 | "C:\Windows\System32\cmd.exe" /C start "" /B "%CD%\LICENSE\minut.bat" | C:\Windows\System32\cmd.exe | — | WinRAR.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 1 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 2136 | "C:\Program Files\Adobe\Acrobat Reader DC\Reader\AcroCEF\RdrCEF.exe" --backgroundcolor=16514043 | C:\Program Files\Adobe\Acrobat Reader DC\Reader\AcroCEF\RdrCEF.exe | AcroRd32.exe | ||||||||||||
User: admin Company: Adobe Systems Incorporated Integrity Level: LOW Description: Adobe RdrCEF Exit code: 0 Version: 20.13.20064.405839 Modules
| |||||||||||||||
Total events
76 694
Read events
76 010
Write events
674
Delete events
10
Modification events
| (PID) Process: | (2660) firefox.exe | Key: | HKEY_CURRENT_USER\Software\Mozilla\Firefox\Launcher |
| Operation: | write | Name: | C:\Program Files\Mozilla Firefox\firefox.exe|Launcher |
Value: 09611C1E1E000000 | |||
| (PID) Process: | (976) firefox.exe | Key: | HKEY_CURRENT_USER\Software\Mozilla\Firefox\Launcher |
| Operation: | write | Name: | C:\Program Files\Mozilla Firefox\firefox.exe|Browser |
Value: AD681C1E1E000000 | |||
| (PID) Process: | (976) firefox.exe | Key: | HKEY_CURRENT_USER\Software\Mozilla\Firefox\Launcher |
| Operation: | write | Name: | C:\Program Files\Mozilla Firefox\firefox.exe|Telemetry |
Value: 0 | |||
| (PID) Process: | (976) firefox.exe | Key: | HKEY_CURRENT_USER\Software\Mozilla\Firefox\DllPrefetchExperiment |
| Operation: | write | Name: | C:\Program Files\Mozilla Firefox\firefox.exe |
Value: 0 | |||
| (PID) Process: | (976) firefox.exe | Key: | HKEY_CURRENT_USER\Software\Mozilla\Firefox\Default Browser Agent |
| Operation: | write | Name: | C:\Program Files\Mozilla Firefox|DisableTelemetry |
Value: 1 | |||
| (PID) Process: | (976) firefox.exe | Key: | HKEY_CURRENT_USER\Software\Mozilla\Firefox\Default Browser Agent |
| Operation: | write | Name: | C:\Program Files\Mozilla Firefox|DisableDefaultBrowserAgent |
Value: 0 | |||
| (PID) Process: | (976) firefox.exe | Key: | HKEY_CURRENT_USER\Software\Mozilla\Firefox\Default Browser Agent |
| Operation: | write | Name: | C:\Program Files\Mozilla Firefox|ServicesSettingsServer |
Value: https://firefox.settings.services.mozilla.com/v1 | |||
| (PID) Process: | (976) firefox.exe | Key: | HKEY_CURRENT_USER\Software\Mozilla\Firefox\Default Browser Agent |
| Operation: | write | Name: | C:\Program Files\Mozilla Firefox|SecurityContentSignatureRootHash |
Value: 97:E8:BA:9C:F1:2F:B3:DE:53:CC:42:A4:E6:57:7E:D6:4D:F4:93:C2:47:B4:14:FE:A0:36:81:8D:38:23:56:0E | |||
| (PID) Process: | (976) firefox.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | write | Name: | ProxyEnable |
Value: 0 | |||
| (PID) Process: | (976) firefox.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Connections |
| Operation: | write | Name: | SavedLegacySettings |
Value: 460000003D010000090000000000000000000000000000000400000000000000C0E333BBEAB1D3010000000000000000000000000100000002000000C0A80164000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
Executable files
10
Suspicious files
576
Text files
142
Unknown types
130
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 976 | firefox.exe | C:\Users\admin\AppData\Local\Mozilla\Firefox\Profiles\qldyz51w.default\startupCache\scriptCache-current.bin | — | |
MD5:— | SHA256:— | |||
| 976 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\qldyz51w.default\storage\permanent\chrome\idb\3870112724rsegmnoittet-es.sqlite | — | |
MD5:— | SHA256:— | |||
| 976 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\qldyz51w.default\places.sqlite-wal | sqlite-wal | |
MD5:— | SHA256:— | |||
| 976 | firefox.exe | C:\Users\admin\AppData\Local\Temp\mz_etilqs_o4LAwRr1W5OEZzB | binary | |
MD5:— | SHA256:— | |||
| 976 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\qldyz51w.default\storage\permanent\chrome\idb\3870112724rsegmnoittet-es.sqlite-wal | binary | |
MD5:— | SHA256:— | |||
| 976 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\qldyz51w.default\prefs.js | text | |
MD5:299A2B747C11E4BDA194E563FEA4A699 | SHA256:94EE461F62E8B4A0A65471A41E10C8C56722B73C0A019D76ACA7F5BAF109813E | |||
| 976 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\qldyz51w.default\prefs-1.js | text | |
MD5:299A2B747C11E4BDA194E563FEA4A699 | SHA256:94EE461F62E8B4A0A65471A41E10C8C56722B73C0A019D76ACA7F5BAF109813E | |||
| 976 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\qldyz51w.default\storage\permanent\chrome\idb\3870112724rsegmnoittet-es.sqlite-shm | binary | |
MD5:B7C14EC6110FA820CA6B65F5AEC85911 | SHA256:FD4C9FDA9CD3F9AE7C962B0DDF37232294D55580E1AA165AA06129B8549389EB | |||
| 976 | firefox.exe | C:\Users\admin\AppData\Local\Temp\mz_etilqs_wDEeewxwNdO7x54 | binary | |
MD5:— | SHA256:— | |||
| 976 | firefox.exe | C:\Users\admin\AppData\Roaming\Mozilla\Firefox\Profiles\qldyz51w.default\sessionCheckpoints.json.tmp | binary | |
MD5:EA8B62857DFDBD3D0BE7D7E4A954EC9A | SHA256:792955295AE9C382986222C6731C5870BD0E921E7F7E34CC4615F5CD67F225DA | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
31
TCP/UDP connections
66
DNS requests
165
Threats
1
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
976 | firefox.exe | POST | 200 | 104.18.21.226:80 | http://ocsp.globalsign.com/gseccovsslca2018 | US | der | 939 b | whitelisted |
976 | firefox.exe | POST | 200 | 142.250.185.227:80 | http://ocsp.pki.goog/gts1c3 | US | der | 471 b | whitelisted |
976 | firefox.exe | GET | 200 | 34.107.221.82:80 | http://detectportal.firefox.com/success.txt | US | text | 8 b | whitelisted |
976 | firefox.exe | POST | 200 | 192.124.249.36:80 | http://ocsp.godaddy.com/ | US | der | 1.74 Kb | whitelisted |
976 | firefox.exe | POST | 200 | 142.250.185.227:80 | http://ocsp.pki.goog/gts1c3 | US | der | 472 b | whitelisted |
976 | firefox.exe | POST | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/ | US | der | 471 b | whitelisted |
976 | firefox.exe | GET | 200 | 34.107.221.82:80 | http://detectportal.firefox.com/success.txt?ipv4 | US | text | 8 b | whitelisted |
976 | firefox.exe | POST | 200 | 2.16.186.25:80 | http://r3.o.lencr.org/ | unknown | der | 503 b | shared |
976 | firefox.exe | POST | 200 | 2.16.186.25:80 | http://r3.o.lencr.org/ | unknown | der | 503 b | shared |
976 | firefox.exe | POST | 200 | 2.16.186.25:80 | http://r3.o.lencr.org/ | unknown | der | 503 b | shared |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
976 | firefox.exe | 34.107.221.82:80 | detectportal.firefox.com | GOOGLE | US | whitelisted |
976 | firefox.exe | 149.154.164.13:443 | www.telegra.ph | Telegram Messenger Inc | GB | suspicious |
976 | firefox.exe | 35.241.9.150:443 | firefox.settings.services.mozilla.com | GOOGLE | US | suspicious |
976 | firefox.exe | 52.40.44.47:443 | location.services.mozilla.com | AMAZON-02 | US | unknown |
976 | firefox.exe | 2.16.186.25:80 | r3.o.lencr.org | Akamai International B.V. | DE | whitelisted |
976 | firefox.exe | 34.160.144.191:443 | content-signature-2.cdn.mozilla.net | GOOGLE | US | suspicious |
976 | firefox.exe | 192.124.249.36:80 | ocsp.godaddy.com | SUCURI-SEC | US | suspicious |
976 | firefox.exe | 192.229.221.95:80 | ocsp.digicert.com | EDGECAST | US | whitelisted |
976 | firefox.exe | 142.250.185.227:80 | ocsp.pki.goog | GOOGLE | US | whitelisted |
976 | firefox.exe | 149.154.167.99:443 | t.me | Telegram Messenger Inc | GB | malicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
detectportal.firefox.com |
| whitelisted |
www.telegra.ph |
| suspicious |
prod.detectportal.prod.cloudops.mozgcp.net |
| whitelisted |
firefox.settings.services.mozilla.com |
| whitelisted |
location.services.mozilla.com |
| whitelisted |
locprod2-elb-us-west-2.prod.mozaws.net |
| whitelisted |
example.org |
| whitelisted |
ipv4only.arpa |
| whitelisted |
r3.o.lencr.org |
| shared |
ocsp.godaddy.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
976 | firefox.exe | Misc activity | ET INFO Observed Telegram Domain (t .me in TLS SNI) |
Process | Message |
|---|---|
controlcreate.bat.exe | |
controlcreate.bat.exe | |
controlcreate.bat.exe | # AutoDetect(True, False)
|
controlcreate.bat.exe | # AutoDetect(True, False)
|
controlcreate.bat.exe | # Connect()
|
controlcreate.bat.exe | # Connect()
|
controlcreate.bat.exe | |
controlcreate.bat.exe | # AutoConnect()
|
controlcreate.bat.exe | # AutoConnect()
|
controlcreate.bat.exe | |