| File name: | example.zip |
| Full analysis: | https://app.any.run/tasks/0c6fd492-83ce-45cd-9ae7-4cdfde4fe1e1 |
| Verdict: | Malicious activity |
| Analysis date: | April 23, 2019, 13:39:31 |
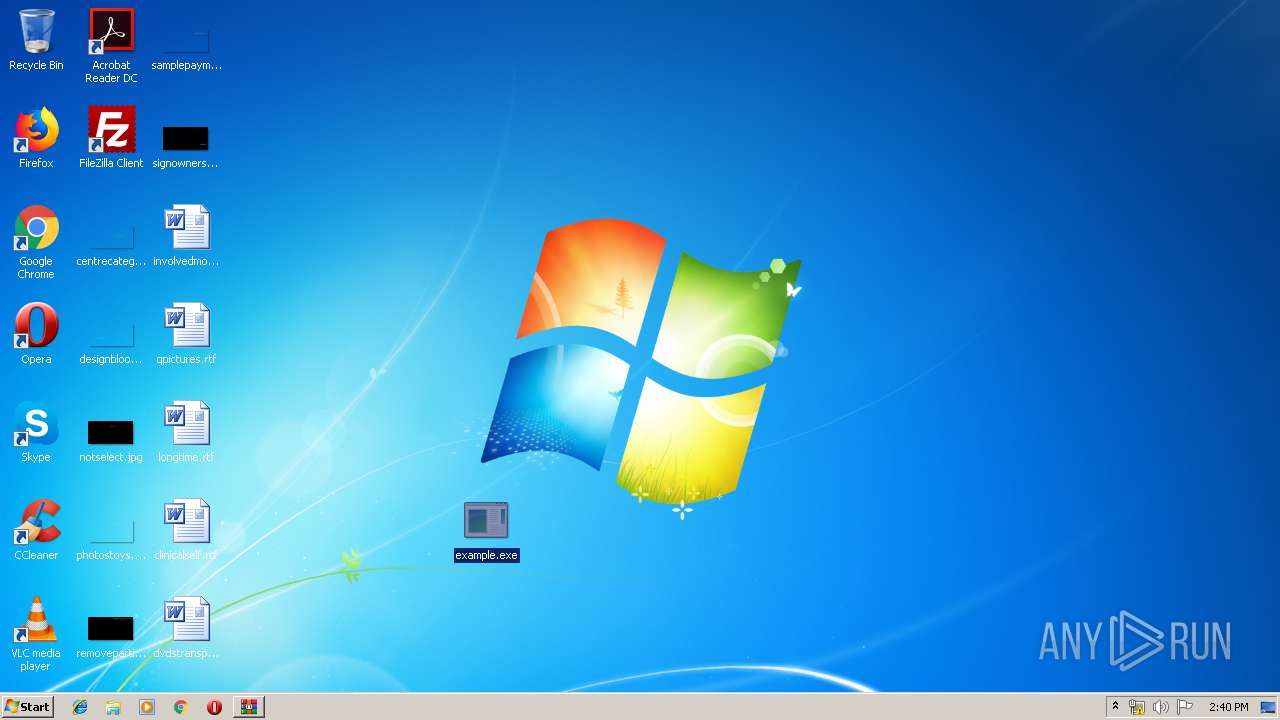
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/zip |
| File info: | Zip archive data, at least v2.0 to extract |
| MD5: | E0C0F3D09F77B0FE3B8DF12BC8C6A7F4 |
| SHA1: | 09934C0D7E16EF4860D830E3529F0A1D74F242DA |
| SHA256: | 643E100448D0E23A77F56276F1E02E9F0B842A7C06FEDC4993EC27570FBDD53A |
| SSDEEP: | 1536:c422oph9vVMpvQCqwInSkS2vXwGIYAxWYBRqPAPB151TEst98RVHU5xE:Rop/9MpYCynS5EIBDBYPA7E+kqE |
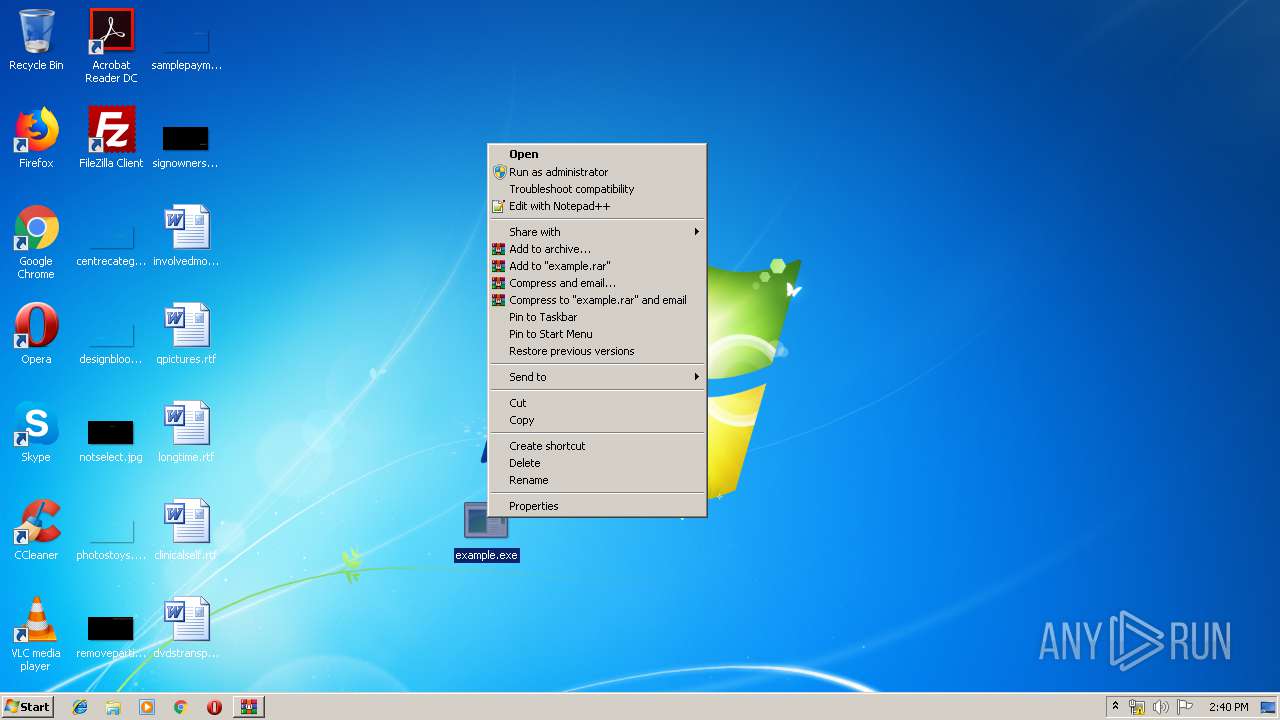
MALICIOUS
Application was dropped or rewritten from another process
- example.exe (PID: 3416)
Uses SVCHOST.EXE for hidden code execution
- example.exe (PID: 3416)
- svchost.exe (PID: 676)
SUSPICIOUS
Application launched itself
- svchost.exe (PID: 676)
Executable content was dropped or overwritten
- WinRAR.exe (PID: 1012)
- svchost.exe (PID: 676)
Creates files in the program directory
- svchost.exe (PID: 676)
INFO
No info indicators.
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
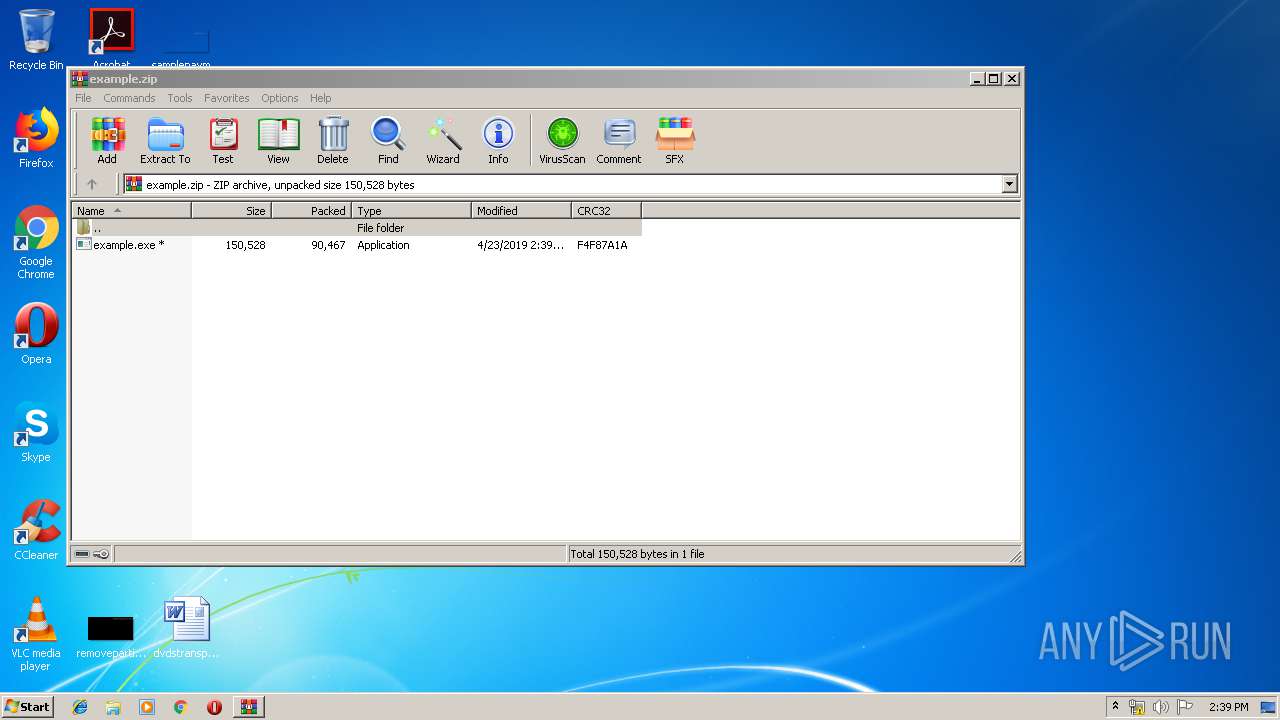
| .zip | | | ZIP compressed archive (100) |
|---|
EXIF
ZIP
| ZipRequiredVersion: | 20 |
|---|---|
| ZipBitFlag: | 0x0009 |
| ZipCompression: | Unknown (99) |
| ZipModifyDate: | 2019:04:23 16:39:02 |
| ZipCRC: | 0xf4f87a1a |
| ZipCompressedSize: | 90467 |
| ZipUncompressedSize: | 150528 |
| ZipFileName: | example.exe |
Total processes
39
Monitored processes
4
Malicious processes
2
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 676 | C:\Windows\system32\svchost.exe -k netsvcs | C:\Windows\system32\svchost.exe | example.exe | ||||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Host Process for Windows Services Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1004 | C:\Windows\system32\svchost.exe -k netsvcs | C:\Windows\system32\svchost.exe | svchost.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Host Process for Windows Services Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
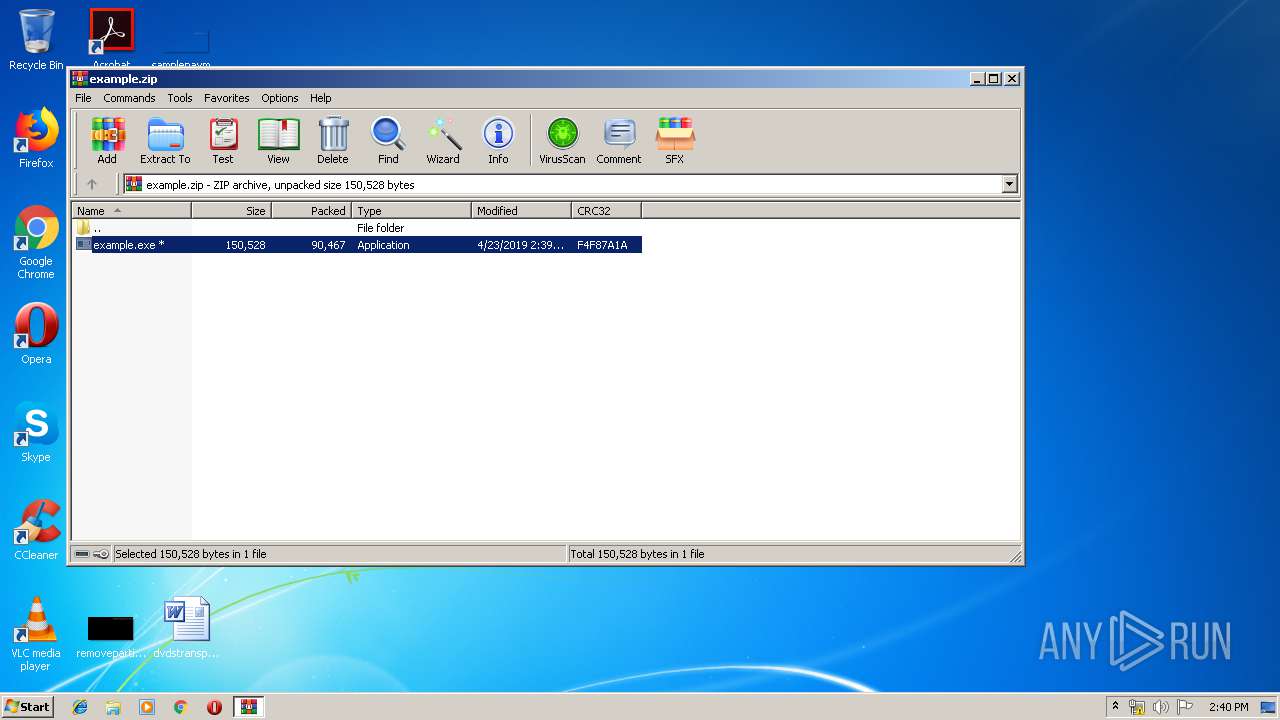
| 1012 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\AppData\Local\Temp\example.zip" | C:\Program Files\WinRAR\WinRAR.exe | explorer.exe | ||||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.60.0 Modules
| |||||||||||||||
| 3416 | "C:\Users\admin\Desktop\example.exe" | C:\Users\admin\Desktop\example.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
Total events
430
Read events
421
Write events
9
Delete events
0
Modification events
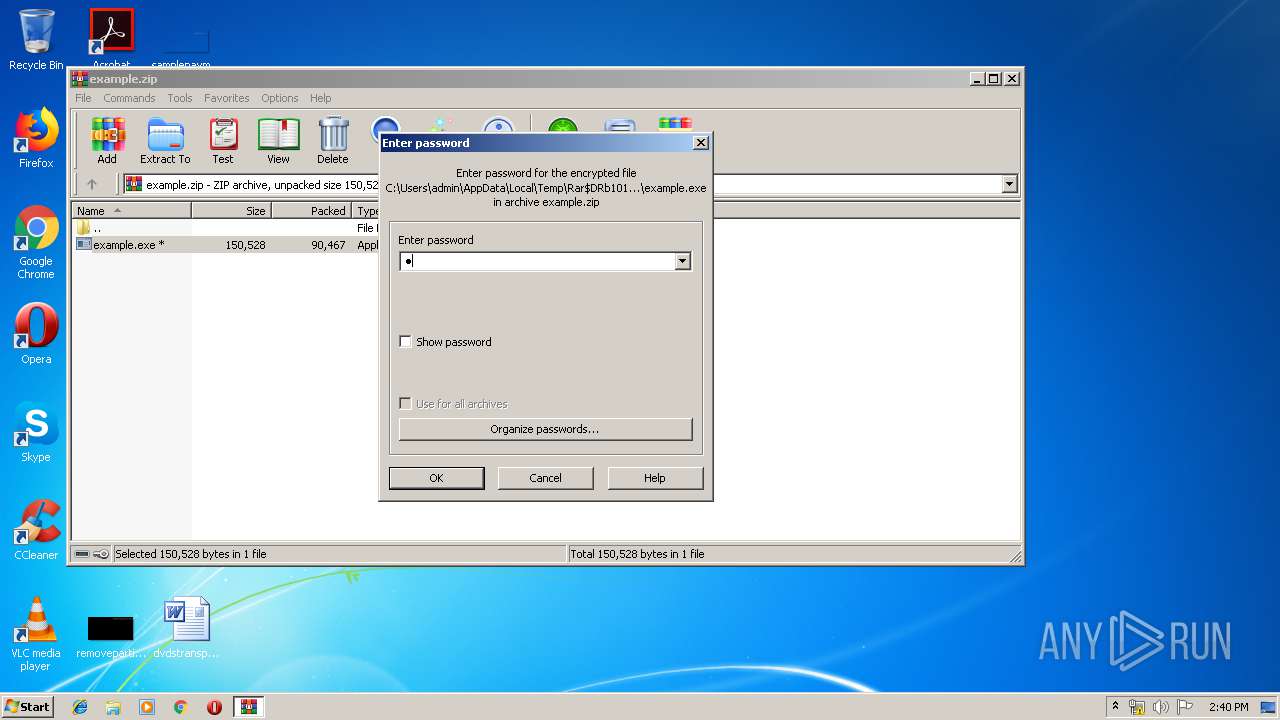
| (PID) Process: | (1012) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (1012) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
| (PID) Process: | (1012) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\62\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (1012) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\example.zip | |||
| (PID) Process: | (1012) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (1012) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (1012) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (1012) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (1012) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface |
| Operation: | write | Name: | ShowPassword |
Value: 0 | |||
Executable files
2
Suspicious files
0
Text files
0
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 676 | svchost.exe | C:\ProgramData\Adobe\966859.txt | — | |
MD5:— | SHA256:— | |||
| 676 | svchost.exe | C:\ProgramData\966859.txt | — | |
MD5:— | SHA256:— | |||
| 676 | svchost.exe | C:\Users\Public\Desktop\966859.txt | — | |
MD5:— | SHA256:— | |||
| 676 | svchost.exe | C:\Users\Public\Documents\966859.txt | — | |
MD5:— | SHA256:— | |||
| 676 | svchost.exe | C:\Users\Public\Favorites\966859.txt | — | |
MD5:— | SHA256:— | |||
| 676 | svchost.exe | C:\ProgramData\Microsoft\966859.txt | — | |
MD5:— | SHA256:— | |||
| 676 | svchost.exe | C:\ProgramData\Microsoft Help\966859.txt | — | |
MD5:— | SHA256:— | |||
| 676 | svchost.exe | C:\ProgramData\Mozilla\966859.txt | — | |
MD5:— | SHA256:— | |||
| 676 | svchost.exe | C:\ProgramData\Oracle\966859.txt | — | |
MD5:— | SHA256:— | |||
| 676 | svchost.exe | C:\ProgramData\Package Cache\966859.txt | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
0
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report