| File name: | 2025-05-18_7370145498ab184c3de0108b6b6be541_black-basta_elex_gcleaner_hijackloader_remcos |
| Full analysis: | https://app.any.run/tasks/7982617f-bd0c-430a-bc91-d36c3a43a53b |
| Verdict: | Malicious activity |
| Analysis date: | May 18, 2025, 19:19:50 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/vnd.microsoft.portable-executable |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, 8 sections |
| MD5: | 7370145498AB184C3DE0108B6B6BE541 |
| SHA1: | 8D94DDF6B3C5AF77CBAC1175E18682252BFDE5E1 |
| SHA256: | 643D98AD5C499BF615AC16943349FB1413BA934FED9CD55BDA1997E3683124F2 |
| SSDEEP: | 98304:zSYpVEm5sn6gNEkdfaTgmHihuRB3FKMvXj07kkFGZur7yv5FkGSthza1U7SZRYyN:5MGWZr4vEZGsuO/UffnApwmwX6hLA |
MALICIOUS
CANBIS mutex has been found
- 2025-05-18_7370145498ab184c3de0108b6b6be541_black-basta_elex_gcleaner_hijackloader_remcos.exe (PID: 7672)
SUSPICIOUS
Reads security settings of Internet Explorer
- 2025-05-18_7370145498ab184c3de0108b6b6be541_black-basta_elex_gcleaner_hijackloader_remcos.exe (PID: 7672)
- 9432752508.exe (PID: 7772)
Process drops legitimate windows executable
- 2025-05-18_7370145498ab184c3de0108b6b6be541_black-basta_elex_gcleaner_hijackloader_remcos.exe (PID: 7672)
Starts a Microsoft application from unusual location
- 9432752508.exe (PID: 7772)
Executable content was dropped or overwritten
- 2025-05-18_7370145498ab184c3de0108b6b6be541_black-basta_elex_gcleaner_hijackloader_remcos.exe (PID: 7672)
INFO
Reads the computer name
- 2025-05-18_7370145498ab184c3de0108b6b6be541_black-basta_elex_gcleaner_hijackloader_remcos.exe (PID: 7672)
- 9432752508.exe (PID: 7772)
Checks supported languages
- 2025-05-18_7370145498ab184c3de0108b6b6be541_black-basta_elex_gcleaner_hijackloader_remcos.exe (PID: 7672)
- 9432752508.exe (PID: 7772)
Process checks computer location settings
- 2025-05-18_7370145498ab184c3de0108b6b6be541_black-basta_elex_gcleaner_hijackloader_remcos.exe (PID: 7672)
- 9432752508.exe (PID: 7772)
Failed to create an executable file in Windows directory
- 2025-05-18_7370145498ab184c3de0108b6b6be541_black-basta_elex_gcleaner_hijackloader_remcos.exe (PID: 7672)
Checks proxy server information
- 9432752508.exe (PID: 7772)
- slui.exe (PID: 5680)
Reads the machine GUID from the registry
- 9432752508.exe (PID: 7772)
Reads the software policy settings
- 9432752508.exe (PID: 7772)
- slui.exe (PID: 5680)
Reads Microsoft Office registry keys
- 9432752508.exe (PID: 7772)
Create files in a temporary directory
- 9432752508.exe (PID: 7772)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable Borland Delphi 7 (55.2) |
|---|---|---|
| .exe | | | Win32 Executable Borland Delphi 5 (37.5) |
| .exe | | | InstallShield setup (3.5) |
| .exe | | | Win32 Executable Delphi generic (1.1) |
| .scr | | | Windows screen saver (1) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 1992:06:19 22:22:17+00:00 |
| ImageFileCharacteristics: | No relocs, Executable, No line numbers, No symbols, Bytes reversed lo, 32-bit, Bytes reversed hi |
| PEType: | PE32 |
| LinkerVersion: | 2.25 |
| CodeSize: | 46080 |
| InitializedDataSize: | 7680 |
| UninitializedDataSize: | - |
| EntryPoint: | 0xc254 |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
Total processes
127
Monitored processes
3
Malicious processes
1
Suspicious processes
0
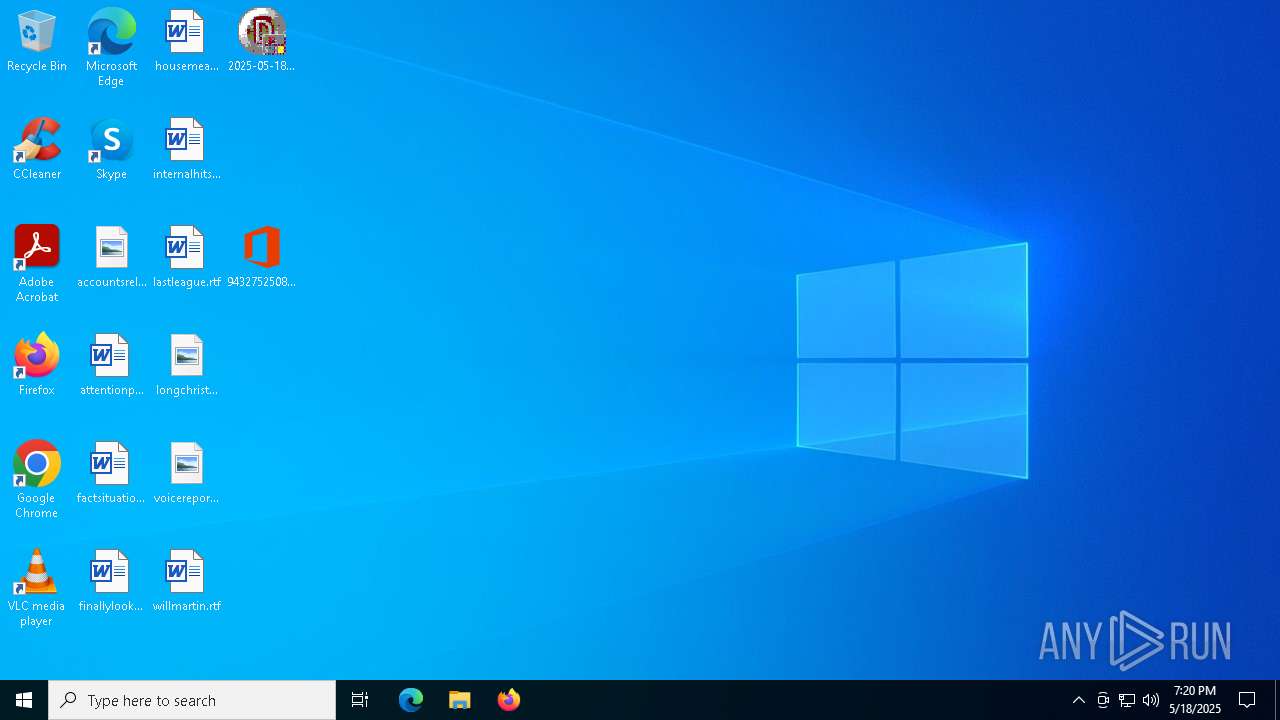
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 5680 | C:\WINDOWS\System32\slui.exe -Embedding | C:\Windows\System32\slui.exe | svchost.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Activation Client Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 7672 | "C:\Users\admin\Desktop\2025-05-18_7370145498ab184c3de0108b6b6be541_black-basta_elex_gcleaner_hijackloader_remcos.exe" | C:\Users\admin\Desktop\2025-05-18_7370145498ab184c3de0108b6b6be541_black-basta_elex_gcleaner_hijackloader_remcos.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 5 Modules
| |||||||||||||||
| 7772 | "C:\Users\admin\Desktop\9432752508.exe" | C:\Users\admin\Desktop\9432752508.exe | 2025-05-18_7370145498ab184c3de0108b6b6be541_black-basta_elex_gcleaner_hijackloader_remcos.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Office Click-to-Run IntegratedOfficeExe Exit code: 1639 Version: 16.0.12430.20172 Modules
| |||||||||||||||
Total events
8 047
Read events
7 891
Write events
150
Delete events
6
Modification events
| (PID) Process: | (7772) 9432752508.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Office\16.0\Common\ClientTelemetry\RulesLastModified |
| Operation: | write | Name: | 9432752508.exe_queried |
Value: E5322A6800000000 | |||
| (PID) Process: | (7772) 9432752508.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Office\16.0\Common\ClientTelemetry\RulesLastModified |
| Operation: | write | Name: | 9432752508.exe |
Value: Sun, 18 May 2025 19:20:05 GMT | |||
| (PID) Process: | (7772) 9432752508.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Office\16.0\Common\ClientTelemetry\RulesMetadata\9432752508.exe |
| Operation: | delete key | Name: | (default) |
Value: | |||
| (PID) Process: | (7772) 9432752508.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Office\16.0\Common\ClientTelemetry\RulesLastModified |
| Operation: | delete value | Name: | 9432752508.exe |
Value: Sun, 18 May 2025 19:20:05 GMT | |||
| (PID) Process: | (7772) 9432752508.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Office\16.0\Common\ClientTelemetry\RulesLastModified |
| Operation: | delete value | Name: | 9432752508.exe_queried |
Value: ㋥株 | |||
| (PID) Process: | (7772) 9432752508.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Office\16.0\Common\ClientTelemetry\RulesLastModified |
| Operation: | delete value | Name: | 9432752508.exe_expiration |
Value: | |||
| (PID) Process: | (7772) 9432752508.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Office\16.0\Common\Experiment\officeclicktorun |
| Operation: | write | Name: | BuildNumber |
Value: 16.0.12430 | |||
| (PID) Process: | (7772) 9432752508.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Office\16.0\Common\ExperimentConfigs\Ecs |
| Operation: | write | Name: | CountryCode |
Value: std::wstring|GB | |||
| (PID) Process: | (7772) 9432752508.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Office\16.0\Common\ExperimentConfigs\Ecs\officeclicktorun |
| Operation: | write | Name: | Expires |
Value: int64_t|0 | |||
| (PID) Process: | (7772) 9432752508.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Office\16.0\Common\ExperimentConfigs\Ecs\officeclicktorun |
| Operation: | delete value | Name: | ConfigIds |
Value: std::wstring|P-R-76757-1-2,P-R-54903-1-3,P-R-26146-7-17,P-D-29635-1-1,P-D-27087-1-9,P-R-79688-1-3,P-X-1056196-2-3,P-R-1065103-4-5,P-R-1040574-4-4,P-R-1021491-4-4,P-R-1020730-2-6,P-R-1019591-4-4,P-R-1004561-4-4,dhied660:310841,P-X-1021965-1-7,P-X-1021968-2-3,P-X-73639-1-5,P-R-1025444-4-5,72h8b859:284400,80ebc365:265669,aigdi533:274387,P-R-58640-1-3,P-X-74718-1-9,P-R-35099-2-4,auena724:270718,P-R-1053478-8-4,P-R-34843-4-6,P-X-1019945-1-7,P-X-1006899-1-5,P-X-109832-1-5,P-X-1020617-1-3,P-X-107951-1-9,P-X-118171-1-3,P-X-95300-3-11,P-X-87037-1-3,P-R-33822-14-62,P-R-45483-16-53,P-R-50717-18-60,P-R-87587-4-4,P-R-75069-1-3,P-R-75001-1-3,P-R-68152-18-21,P-R-52316-18-37,P-R-49162-18-13,P-R-49161-18-13,P-R-40253-6-19,P-R-40254-6-18,P-R-35401-6-7,P-R-32107-22-22,cl120:285524,clrep106:284807,clrep282:330897,clcdn389:241625,cl971:296514,clrep703:224719,upsell_and_hardlinking:176874,cluse576:243893,P-X-1003556-1-5,P-R-24980-8-48,P-R-18279-2-65,cuisf464:213639,P-R-113915-8-7,P-R-52982-18-34,P-R-51145-2-7,P-X-1012533-1-5,P-R-1050194-32-17,diasy932:273280,P-X-1048408-2-5,P-X-85359-1-13,P-X-89012-1-11,P-X-71449-1-3,P-R-1061651-8-6,P-R-1042420-4-3,P-R-1036164-4-7,P-R-113508-8-5,P-R-95616-8-4,P-R-79616-1-3,P-R-77621-1-3,P-R-77204-1-3,P-R-76107-1-3,P-R-74334-1-3,P-R-74439-1-3,P-R-73642-1-3,P-R-68938-1-5,P-R-62875-2-4,P-R-60579-2-2,P-R-60333-1-3,P-R-58107-2-2,P-R-55743-1-3,P-R-51958-1-5,P-R-38085-12-9,usev2endpointtreatment:333993,nativewin32rdl:186744,docshomepagesearchenableaggregatedmrusearchsource:175739,domod898:60719,P-R-1034169-10-7,P-X-1059111-1-3,P-X-80742-1-11,P-X-1005454-7-23,P-X-79961-1-7,P-X-1026498-1-5,P-X-99044-1-3,P-X-96141-1-3,P-X-73891-1-3,P-E-28677-2-3,P-R-55122-8-8,P-R-50255-10-9,P-R-45314-10-16,3jgh9488:327643,expow344:299586,exnewrecalcpaths7:334078,exavo833:249893,4abec944:333230,modernbrowseroauthdialog:208943,exisr448:208934,exena229:264853,P-E-38231-C1-4,P-R-94560-14-12,P-R-94189-14-13,P-R-93882-14-26,P-R-61147-C17-2,P-R-54728-16-23,P-R-54698-16-16,P-R-54658-18-19,P-R-38306-C17-3,P-R-34019-4-3,P-X-1011430-5-18,P-X-1007274-3-15,P-X-1007275-3-16,P-X-85896-1-19,P-X-91790-1-5,P-X-1014433-1-7,P-X-1014431-1-7,P-X-116115-2-7,P-X-107595-2-5,P-X-94145-1-11,P-X-61102-3-11,P-X-51262-1-11,P-X-52591-1-11,P-X-98665-1-9,P-X-98655-1-5,P-X-84464-1-5,P-X-78402-1-3,P-X-54358-1-7,P-X-72602-3-13,P-X-53975-3-9,P-X-58493-1-9,P-X-69189-1-7,P-X-66364-1-5,P-X-53845-1-9,P-X-56274-1-9,P-X-63134-1-7,P-X-62261-1-3,P-X-58678-1-5,P-X-55832-1-6,P-X-56147-1-5,P-X-56154-1-5,P-X-54212-1-5,P-E-42700-C1-4,P-R-1062852-8-9,P-R-1053269-8-5,P-R-1052170-8-4,P-R-95082-8-4,P-R-93970-8-4,P-R-69065-1-3,P-R-59193-1-3,P-R-45609-14-6,P-R-45197-2-6,P-R-40980-18-16,P-R-39029-5-18,P-R-38162-58-62,P-R-29809-1-6,P-R-26968-3-9,gracecyclesfor2minheartbeat:330250,hneditors:330255,fihos692_stageiii:330249,filis466:330247,fimoc248:193491,fi838:253776,betterbreadcrumbs:273308,fiall198cf:225338,fibac967cf:330033,enablebatchschedulerforcecancellation:247435,fites217:161468,firef346:34525,fimoc589:28979,graphapiforodenabledrollout:170001,onedriveconvergenceenlightenedrollout:159038,fiomi293:118081,fisha109:104700,fiena947:30635,16mbfragment:115145,fista407:61027,fileiosharingsuggestion:69876,fiena903:65944,fiena631:91186,fiser190:49498,fidav265:55035,ficac841:49664,fiena340:60251,fiena415:38780,fiena490:34181,remotemovedevice:42500,fiena276:41004,fiena381:49997,P-R-1034118-18-16,P-R-53545-4-5,P-R-49736-6-22,P-R-30085-1-9,P-R-24363-1-12,P-R-19814-1-62,P-R-19012-1-57,P-X-1020597-1-7,P-X-1009329-1-7,P-X-1011442-1-5,P-X-1019632-1-3,P-X-1015554-1-5,P-X-1010314-1-5,P-X-77742-1-5,P-X-86395-1-5,P-X-84321-1-5,P-X-50220-1-3,P-X-49730-1-3,P-R-1043885-6-4,P-R-1014452-8-8,P-R-64841-22-15,P-R-63100-28-10,P-R-40990-12-15,P-R-32744-14-15,P-R-32741-32-16,gralt193:305875,gralt222:263924,grgfx906:299968,gr234:264276,grski455:227436,gr312:218949,grdel347:127628,grsvg960:253794,gruse444:124091,gruse488:19772,grico406:19777,P-R-50429-18-8,P-X-1033360-1-5,P-X-1033355-1-3,P-X-1011173-1-5,P-X-1006182-1-5,P-X-71668-1-11,P-R-1026542-8-4,P-R-1021725-18-40,P-R-1020916-8-4,P-R-111752-4-6,P-R-53421-28-14,P-R-40475-28-28,P-R-35985-C13-20,P-R-32004-2-5,2dbbb579:286225,i83da489:287210,id592:288714,externalwithouthometenant:215345,idfea766:129381,P-X-88035-1-5,lalan231:140781,P-R-66895-18-19,P-R-61248-18-6,P-R-51995-18-28,P-X-1049649-2-5,P-X-1047715-1-7,P-X-1044514-2-5,P-X-1026131-2-5,P-X-1027913-1-11,P-X-1017745-8-14,P-X-108643-2-7,P-X-95605-2-3,P-R-1058675-8-4,P-R-1036576-4-4,P-R-98110-4-5,P-R-79963-1-2,P-R-60816-10-19,P-R-51764-1-4,P-R-42392-2-4,P-R-39073-1-5,4gh9e205:325592,22c5f675:334387,pipchybridt:317872,jj050827:245162,a0e72269:322094,7g636832:268698,76e4g975:324979,g0hd0221:210026,P-R-1009855-12-14,P-R-98856-18-48,P-R-1061239-8-4,P-R-38410-18-22,P-X-89878-1-5,P-X-1009237-4-17,P-X-1041756-2-5,P-X-1006174-1-5,P-X-51759-1-3,P-R-1017066-4-4,P-R-117941-4-4,P-R-59534-1-3,P-R-54557-1-3,oeuil820:326124,onlyswitchtowindowedforjaws:322054,gb08d752:292122,oeall843:258502,oemac358:20502,P-R-71360-18-19,P-X-76555-1-3,onmap366:81740,P-D-1037543-3-5,P-D-1037541-3-5,P-D-1033391-2-4,P-D-1031050-4-3,P-D-1031040-4-3,P-D-1030926-1-3,P-D-1030923-2-3,P-D-1030922-2-3,P-D-1030920-2-3,P-D-1030918-2-3,P-D-1030916-2-3,P-D-1030914-2-3,P-D-1030912-2-3,P-D-1030910-2-3,P-D-1030908-2-3,P-D-1030906-2-3,P-D-1030904-2-3,P-D-1030902-2-3,P-D-1030900-2-3,P-D-1030898-2-3,P-D-1030896-2-3,P-D-1030893-2-3,P-D-1030891-2-3,P-D-1030889-2-3,P-D-1030887-2-3,P-D-1030885-2-3,P-D-1030883-2-3,P-D-1030881-2-3,P-D-1030879-2-3,P-D-1030877-2-3,P-D-1030876-2-3,P-D-1030875-2-3,P-D-1030873-3-3,P-D-1030872-2-3,P-D-1030871-2-3,P-D-1030870-2-3,P-D-1030869-2-3,P-D-1030868-2-3,P-D-1030867-2-3,P-D-1030866-2-3,P-D-1030865-2-3,P-D-1030864-2-3,P-D-1030862-2-3,P-D-1030860-2-3,P-D-1030858-2-3,P-D-1030856-2-3,P-D-1030854-2-3,P-D-1030852-2-3,P-D-1030850-2-3,P-D-1030848-2-3,P-D-1030847-2-3,P-D-1030846-2-3,P-D-1030844-2-3,P-D-1030842-2-3,P-D-1030841-2-3,P-D-1030840-2-3,P-D-1030838-2-3,P-D-1030836-2-3,P-D-1030834-2-3,P-D-1030832-2-3,P-D-1030830-2-3,P-D-1030828-2-3,P-D-1030826-2-3,P-D-1030824-2-3,P-D-1030822-2-3,P-D-1030819-2-3,P-D-1030816-2-3,P-D-1030812-2-3,P-D-1030811-2-3,P-D-1030810-2-3,P-D-1030808-2-3,P-D-1030806-2-3,P-D-1030803-2-3,P-D-1030801-2-3,P-D-1030800-2-3,P-D-1030799-2-3,P-D-1030798-2-3,P-D-1030797-2-3,P-D-1030796-2-3,P-D-1030795-2-3,P-D-1030794-2-3,P-D-1030793-2-3,P-D-1030792-2-3,P-D-1030791-2-3,P-D-1030789-2-3,P-D-1030787-2-3,P-D-1030786-2-3,P-D-1030785-2-3,P-D-1030783-2-3,P-D-1030781-2-3,P-D-1030779-2-3,P-D-1030777-2-3,P-D-1030775-2-3,P-D-1030773-2-3,P-D-1030771-2-3,P-D-1030769-2-3,P-D-1030767-2-3,P-D-1030765-2-3,P-D-1030763-2-3,P-D-1030761-2-3,P-D-1030760-2-3,P-D-1030759-2-3,P-D-1030758-2-3,P-D-1030757-2-3,P-D-1030756-2-3,P-D-1030755-2-3,P-D-1030753-2-3,P-D-1030751-2-3,P-D-1030749-2-3,P-D-1030747-2-3,P-D-1030745-2-3,P-D-1030743-2-3,P-D-1030740-3-3,P-D-1030738-2-3,P-D-1030737-2-3,P-D-1030736-2-3,P-D-1030734-2-3,P-D-1030732-2-3,P-D-1030730-2-3,P-D-1030728-2-3,P-D-1030726-2-3,P-D-1030724-2-3,P-D-1030722-2-3,P-D-1030719-2-3,P-D-1030717-2-3,P-D-1030715-2-3,P-D-1030713-2-3,P-D-1030712-2-3,P-D-1030711-2-3,P-D-1030709-2-3,P-D-1030708-2-3,P-D-1030707-2-3,P-D-1030706-2-3,P-D-1030705-2-3,P-D-1030704-2-3,P-D-1030703-2-3,P-D-1030702-2-3,P-D-1030701-2-3,P-D-1030699-2-3,P-D-1030697-2-3,P-D-1030696-2-3,P-D-1030695-2-3,P-D-1030693-2-3,P-D-1030691-2-3,P-D-1030690-2-3,P-D-1030689-2-3,P-D-1030687-2-3,P-D-1030685-2-3,P-D-1030683-2-3,P-D-1030681-2-3,P-D-1030679-2-3,P-D-1030677-2-3,P-D-1030675-2-3,P-D-1030673-2-3,P-D-1030671-2-3,P-D-1030669-2-3,P-D-1030668-2-3,P-D-1030665-2-3,P-D-1030664-2-3,P-D-1030663-2-3,P-D-1030661-2-3,P-D-1030659-2-3,P-D-1030656-1-3,P-D-1030642-7-6,P-D-1030600-6-4,P-D-1030512-1-3,P-D-1029290-5-3,P-D-1029289-4-3,P-D-1029243-1-3,P-D-1029097-2-3,P-D-1029096-2-3,P-D-1029093-2-3,P-D-1029092-2-3,P-D-1029091-2-3,P-D-1029090-2-3,P-X-1020529-1-3,P-R-1016539-8-5,P-R-82473-1-4,P-R-56618-1-3,peinp694:246849,P-R-61718-18-3,P-R-33696-1-5,P-R-39912-1-2,P-R-50380-18-18,P-X-115166-2-3,pu469cf:318518,P-X-1027341-2-5,P-X-1048046-2-3,P-X-1045269-1-5,P-X-1045059-1-3,P-X-1044286-1-5,P-X-1000569-6-19,P-X-1018117-1-5,P-X-1021187-1-3,P-R-1064159-8-6,P-R-1040579-26-14,P-R-1038629-8-4,P-R-63338-18-11,P-R-58251-18-11,P-R-33737-1-4,jcged970:323776,8f9fb771cf:330156,8b0a1245:322013,66eh1308:319749,3fh1b283:318487,hi56g585:329453,justificationotherwithsecuritywarning:272552,36823626:289365,P-X-116286-1-3,P-X-116085-1-3,P-X-116078-1-5,P-X-116065-1-3,P-X-78545-1-3,P-X-74234-1-11,P-X-73718-1-3,P-E-29662-2-3,P-R-1059764-4-4,P-R-1055495-2-7,P-R-1055351-2-6,P-R-67809-2-12,P-R-1049526-2-7,P-R-1049535-2-7,P-R-1049352-2-7,P-R-29303-2-19,P-R-29393-6-25,P-R-33922-6-19,P-R-29307-2-15,P-R-52189-2-15,P-R-29031-2-19,P-R-36316-6-20,P-R-29197-2-17,P-R-30290-6-22,P-R-28982-3-18,P-R-63947-18-2,P-R-61361-18-26,P-R-53256-2-11,P-R-48634-2-14,P-R-47242-18-11,P-R-42512-1-2,P-R-41549-18-20,P-R-36664-4-3,P-R-35407-4-3,P-R-33134-2-16,P-R-30292-4-7,P-R-28644-1-4,P-R-24037-1-6,P-R-23445-3-6,P-R-23434-3-7,P-R-23403-3-8,P-R-18513-1-30,shgra498:227707,shgra601:184080,shgra355:208049,shgra502:189924,shaut596:92107,shgra747:86677,shicr317:94521,P-R-65011-1-3,P-R-50541-2-7,P-X-71568-1-5,P-R-69232-38-12,P-R-23681-2-7,P-D-32502-2-3,P-D-32501-2-3,P-D-32415-2-3,taena576:90265,P-X-1027163-2-9,P-X-1059212-2-3,P-X-109662-1-17,P-X-83304-1-3,P-X-71671-1-5,P-R-64513-18-10,P-R-51916-84-31,oteleudb:326826,54679646:322119,teari352:233774,teuae310:138428,uaecallstack:84401,P-R-1068115-1-3,P-R-1064262-1-3,P-R-23746-29-39,P-R-1024076-3-7,P-R-1024074-3-7,P-R-1059494-2-4,P-R-1058643-3-5,P-R-1058117-2-4,P-R-1045118-2-4,P-R-25269-14-21,P-R-1044408-1-3,P-R-1042833-1-3,P-R-1041682-1-3,P-R-1037887-1-3,P-R-1037879-1-3,P-R-1036293-1-3,P-R-1036292-1-3,P-R-1036289-2-4,P-R-1036288-1-3,P-R-1036068-2-4,P-R-1035933-2-4,P-R-1035149-2-4,P-R-1033817-1-3,P-R-1033624-2-4,P-R-1028550-2-4,P-R-1028168-1-3,P-R-1027535-3-5,P-R-1024188-2-4,P-R-1024071-2-4,P-R-1006896-1-3,P-R-1006894-1-3,P-R-1006562-2-4,P-R-1000061-2-4,P-R-111682-1-3,P-R-105731-36-38,P-R-104435-13-15,P-R-100294-1-3,P-R-99633-1-3,P-R-98929-2-4,P-R-98926-1-3,P-R-98250-1-3,P-R-94809-2-4,P-R-94556-2-4,P-R-94299-1-3,P-R-93077-1-3,P-R-88309-2-4,P-R-86118-1-3,P-R-80517-6-8,P-R-78852-3-5,P-R-78112-4-6,P-R-76918-2-4,P-R-76721-1-3,P-R-76253-1-3,P-R-75440-2-4,P-R-75436-1-3,P-R-75434-1-3,P-R-75433-1-3,P-R-72449-7-10,P-R-68864-5-7,P-R-68069-2-4,P-R-66975-1-3,P-R-65567-1-3,P-R-60602-1-3,P-R-53309-1-3,P-R-52633-1-3,P-R-52171-2-4,P-R-51921-8-10,P-R-51258-6-8,P-R-50752-2-4,P-R-50681-2-4,P-R-50599-4-6,P-R-50596-4-8,P-R-50553-1-3,P-R-49597-3-5,P-R-49458-2-4,P-R-48530-5-7,P-R-47948-1-4,P-R-46580-3-5,P-R-46484-10-12,P-R-46122-1-3,P-R-45858-2-4,P-R-43966-2-4,P-R-43502-19-21,P-R-38248-17-21,P-R-41430-1-3,P-R-40751-8-10,P-R-40273-4-6,P-R-39238-2-4,P-R-38682-3-5,P-R-37588-2-4,P-R-34355-8-10,P-R-26266-4-9,P-R-26834-3-8,P-R-24662-16-22,P-R-27479-6-11,P-R-26056-7-15,P-R-27006-7-12,P-R-30338-3-7,P-R-30178-78-80,P-R-30053-7-9,P-R-27458-1-5,P-R-25822-16-19,P-R-25083-6-9,P-R-24690-33-37,P-R-24689-2-5,P-R-24666-2-5,P-R-24663-6-11,P-R-24659-7-10,P-R-23744-7-9,P-R-23739-7-9,P-R-23736-14-17,P-R-23734-7-9,P-R-23730-21-24,P-R-23723-9-11,P-D-32588-1-3,P-D-32534-1-3,P-D-32524-1-3,P-D-32518-1-3,P-D-32512-1-3,P-D-32509-1-3,P-D-32486-1-3,P-D-32485-1-4,P-D-32484-1-4,P-D-32405-1-3,P-X-71999-3-11,P-R-1013930-4-5,P-R-47601-18-13,P-R-33916-1-5,P-R-33580-8-9,ucsha660:76558,P-X-1051763-2-7,P-X-1010572-1-3,P-X-1000465-1-3,P-X-105697-1-9,P-X-94972-1-3,P-X-77252-1-5,P-X-71712-1-5,P-R-1035921-4-4,P-R-61426-C17-6,P-R-59426-1-3,P-R-46913-18-8,mecontrol_weakptr_integration_enabled:331562,ux446:326431,uxflu234:304714,fluentbackstagerefresh:246412,uxena101:288818,uxpro637:147594,checkoutdeviceonpaint:122110,P-R-19262-1-12,P-X-1042275-2-3,P-X-1037196-1-3,P-X-107619-1-5,P-X-115167-2-3,P-X-77184-1-3,g1h6b692:334682,4f3fb843:291239,wofus947:333624,wo380754cf:318520,wocol936:80031,P-R-81720-1-2,P-R-58406-1-5,P-D-50697-2-4,P-D-29719-1-1,P-D-29718-1-1,P-D-29593-1-6 | |||
Executable files
2
Suspicious files
1
Text files
0
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 7672 | 2025-05-18_7370145498ab184c3de0108b6b6be541_black-basta_elex_gcleaner_hijackloader_remcos.exe | C:\Users\admin\Desktop\3974693082.exe | executable | |
MD5:7370145498AB184C3DE0108B6B6BE541 | SHA256:643D98AD5C499BF615AC16943349FB1413BA934FED9CD55BDA1997E3683124F2 | |||
| 7772 | 9432752508.exe | C:\Users\admin\AppData\Local\Temp\DESKTOP-JGLLJLD-20250518-1920.log | binary | |
MD5:AF4B8E92123765B592449BB01A2A9807 | SHA256:B4D7F6DB8665584ABCAF34C916D56464789F7CC40A4894A366ED0052328237FC | |||
| 7672 | 2025-05-18_7370145498ab184c3de0108b6b6be541_black-basta_elex_gcleaner_hijackloader_remcos.exe | C:\Users\admin\Desktop\9432752508.exe | executable | |
MD5:E31BD41B3A0214D7F38724894D9A3B14 | SHA256:332EEE2E0C6D24704B8C805B890F48E0B21BE5C041E7147258DDD3DBC2D1EC92 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
9
TCP/UDP connections
43
DNS requests
19
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2656 | RUXIMICS.exe | GET | 200 | 23.48.23.150:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
2656 | RUXIMICS.exe | GET | 200 | 23.52.120.96:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
8112 | SIHClient.exe | GET | 200 | 23.52.120.96:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20Update%20Signing%20CA%202.1.crl | unknown | — | — | whitelisted |
8112 | SIHClient.exe | GET | 200 | 23.48.23.164:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut_2010-06-23.crl | unknown | — | — | whitelisted |
8112 | SIHClient.exe | GET | 200 | 23.48.23.164:80 | http://crl.microsoft.com/pki/crl/products/MicTimStaPCA_2010-07-01.crl | unknown | — | — | whitelisted |
8112 | SIHClient.exe | GET | 200 | 23.52.120.96:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
8112 | SIHClient.exe | GET | 200 | 23.52.120.96:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Signing%20CA%202.1.crl | unknown | — | — | whitelisted |
8112 | SIHClient.exe | GET | 200 | 23.52.120.96:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20Update%20Signing%20CA%202.2.crl | unknown | — | — | whitelisted |
8112 | SIHClient.exe | GET | 200 | 23.52.120.96:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Signing%20CA%202.2.crl | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2656 | RUXIMICS.exe | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
— | — | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
3216 | svchost.exe | 172.211.123.248:443 | client.wns.windows.com | MICROSOFT-CORP-MSN-AS-BLOCK | FR | whitelisted |
2656 | RUXIMICS.exe | 23.48.23.150:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
2656 | RUXIMICS.exe | 23.52.120.96:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
7772 | 9432752508.exe | 13.107.42.16:443 | config.edge.skype.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
7772 | 9432752508.exe | 52.111.227.11:443 | nexusrules.officeapps.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
8112 | SIHClient.exe | 172.202.163.200:443 | slscr.update.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | GB | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
uk.undernet.org |
| unknown |
client.wns.windows.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
config.edge.skype.com |
| whitelisted |
nexusrules.officeapps.live.com |
| whitelisted |
slscr.update.microsoft.com |
| whitelisted |
fe3cr.delivery.mp.microsoft.com |
| whitelisted |