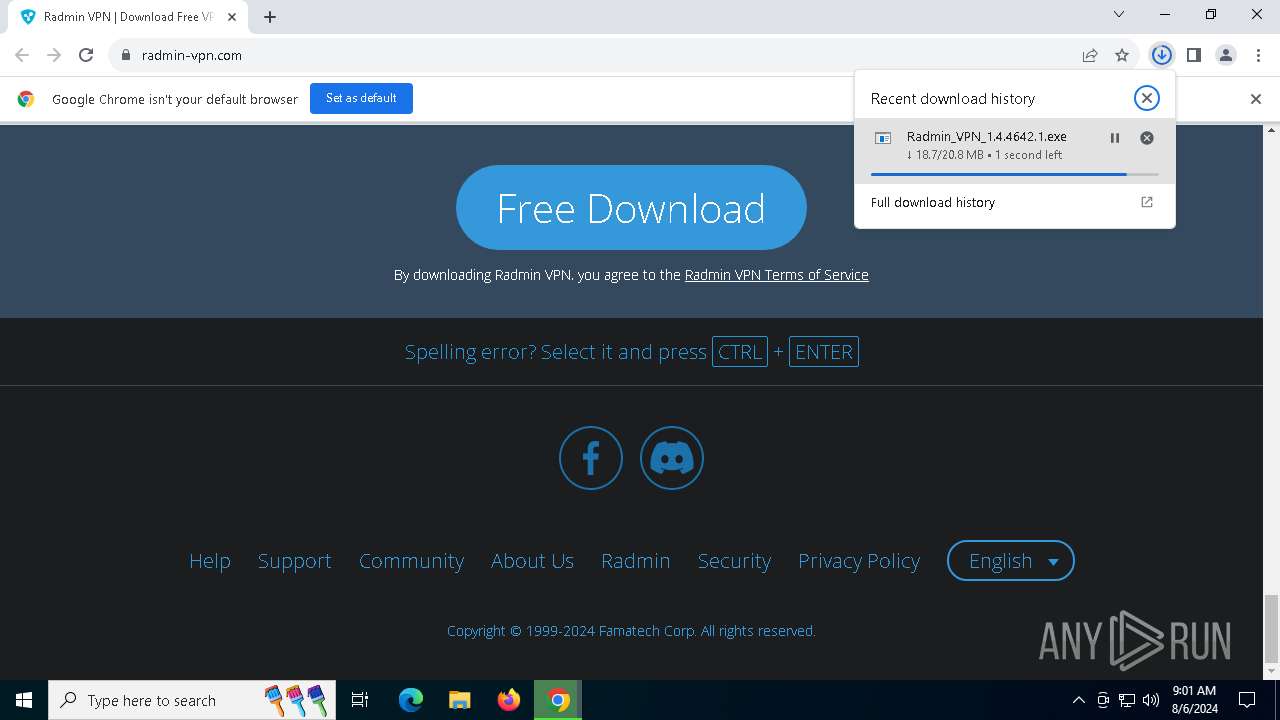
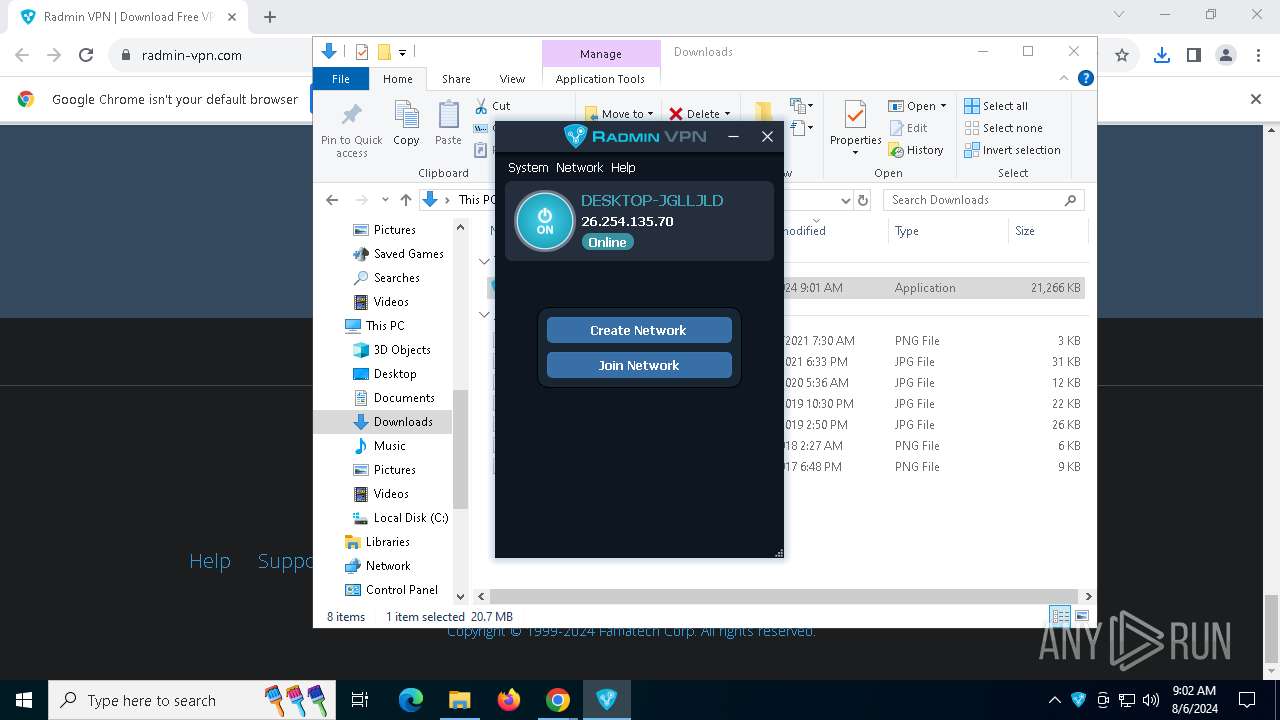
| URL: | https://www.radmin-vpn.com/ |
| Full analysis: | https://app.any.run/tasks/c0e2472a-cca3-4d43-bc16-454061ee0f74 |
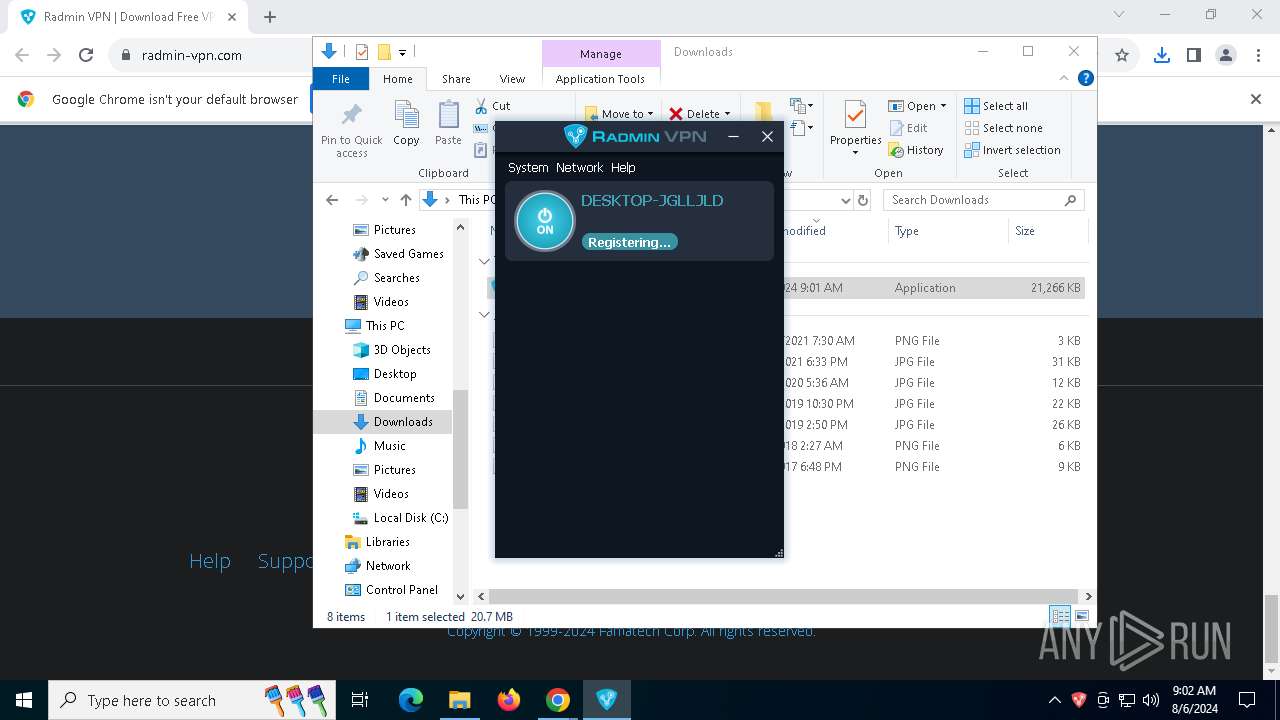
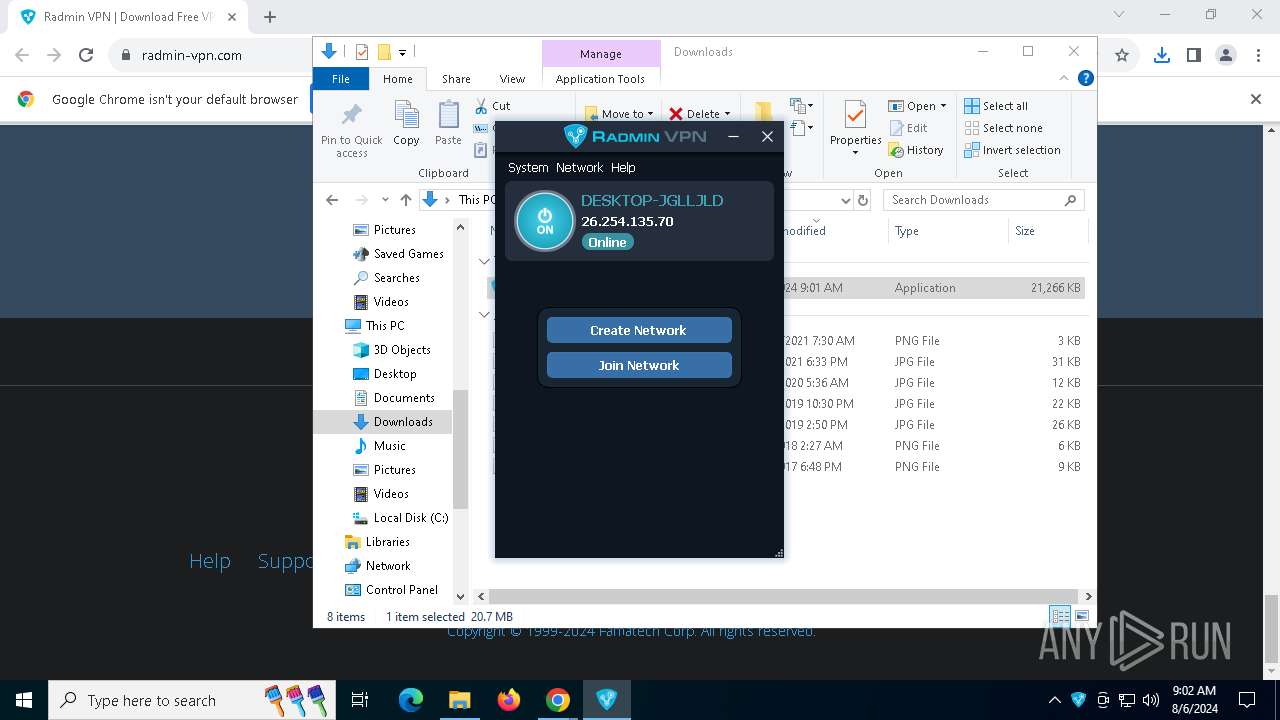
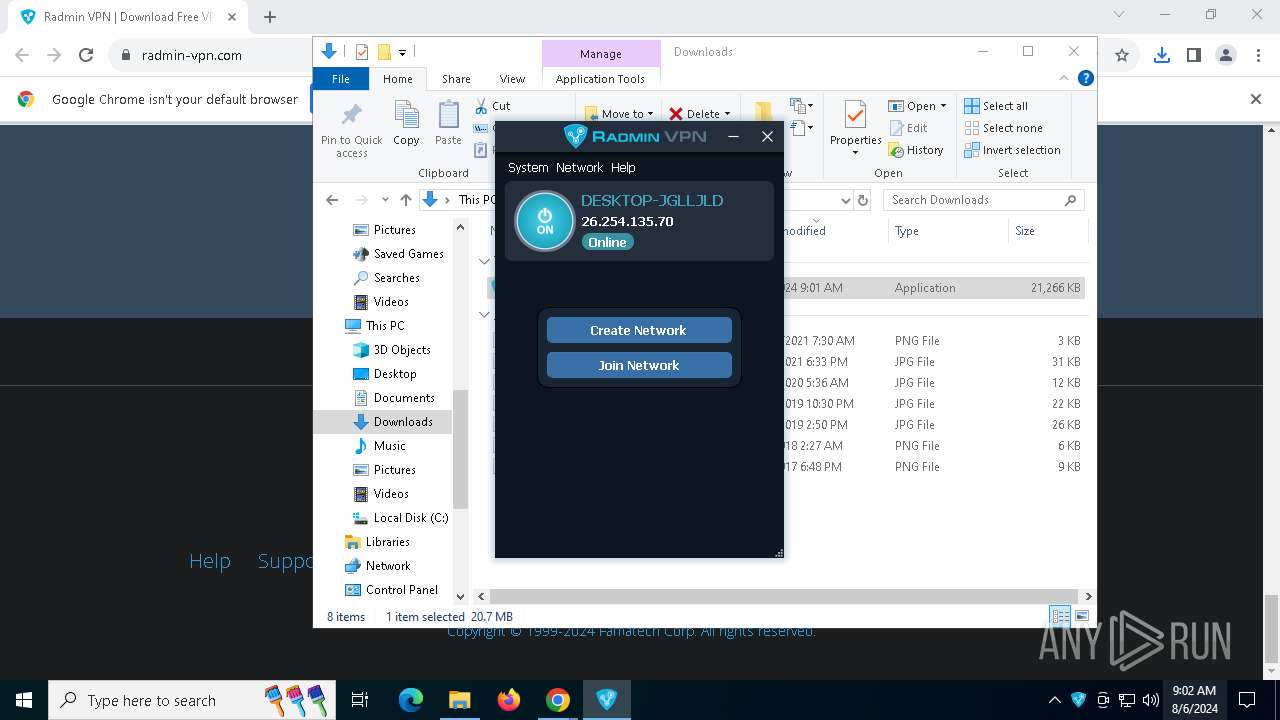
| Verdict: | Malicious activity |
| Analysis date: | August 06, 2024, 09:01:05 |
| OS: | Windows 10 Professional (build: 19045, 64 bit) |
| Indicators: | |
| MD5: | 44E57FB422BB4F974863C49AB77EC5EF |
| SHA1: | 7F77A55F800263C5AD694A81A6D7B070141A742F |
| SHA256: | 643949A5B28A0DE47985C225C923FF4C3B62A6B7B62169B32799B9124C8DABE0 |
| SSDEEP: | 3:N8DSLU+TZSK:2OLUIZ5 |
MALICIOUS
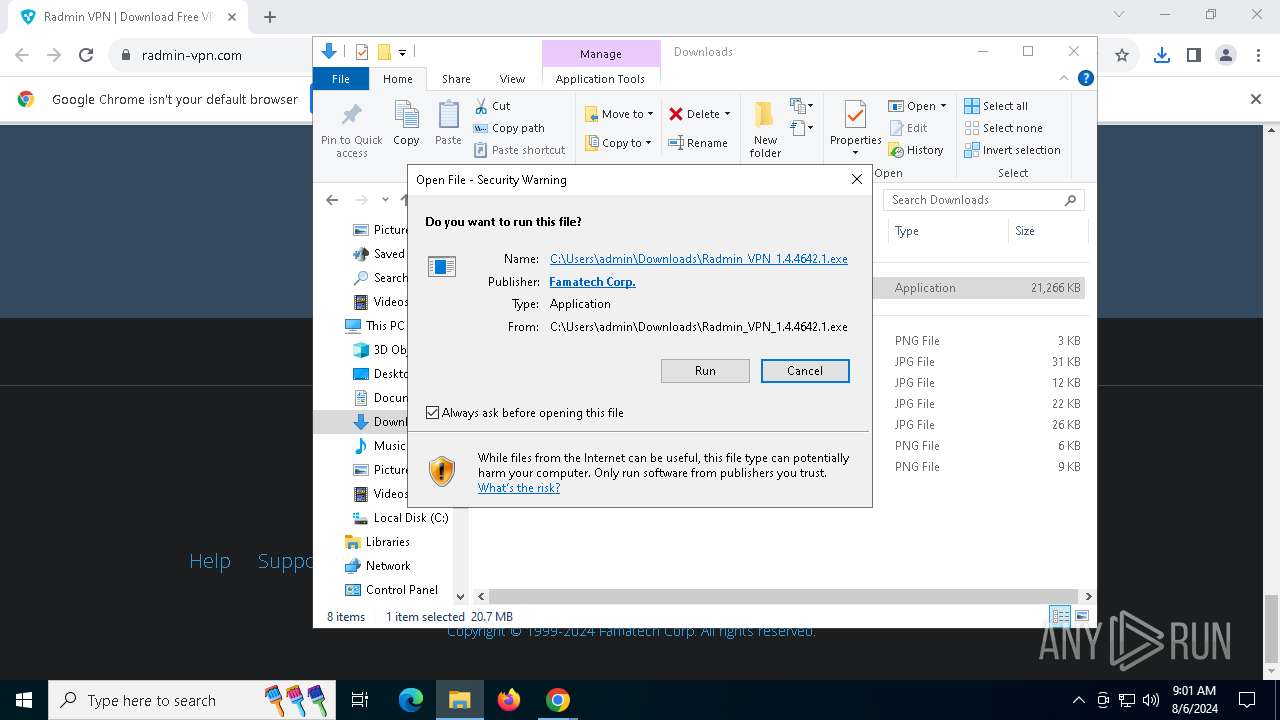
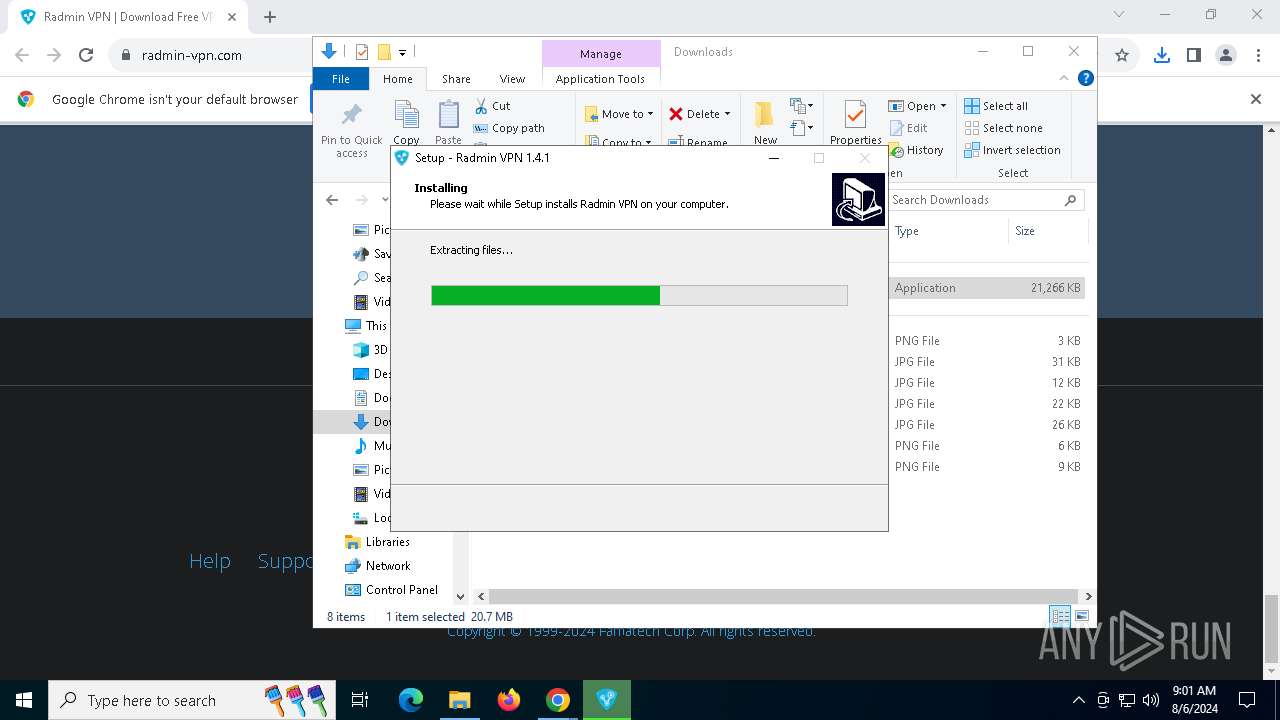
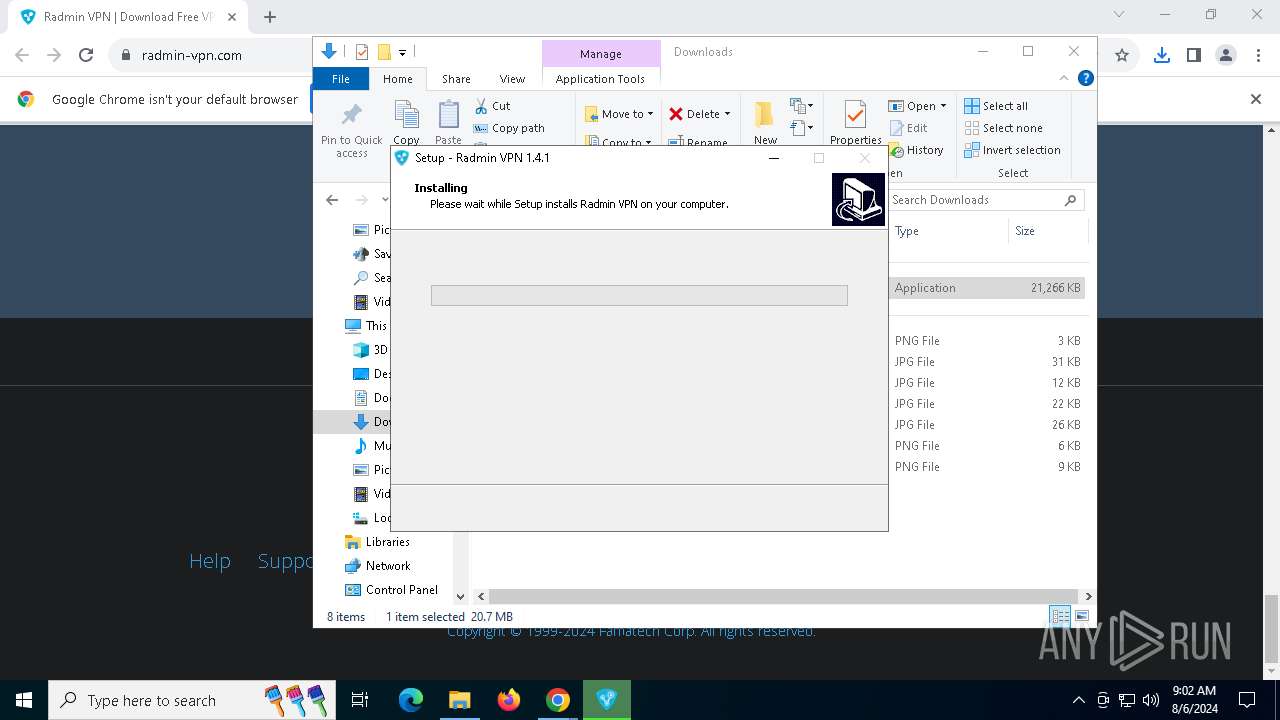
Drops the executable file immediately after the start
- Radmin_VPN_1.4.4642.1.exe (PID: 8064)
- Radmin_VPN_1.4.4642.1.exe (PID: 8160)
- Radmin_VPN_1.4.4642.1.tmp (PID: 8180)
- msiexec.exe (PID: 7352)
- drvinst.exe (PID: 7692)
- drvinst.exe (PID: 6872)
Changes the autorun value in the registry
- msiexec.exe (PID: 7352)
SUSPICIOUS
Reads security settings of Internet Explorer
- Radmin_VPN_1.4.4642.1.tmp (PID: 8084)
Executable content was dropped or overwritten
- Radmin_VPN_1.4.4642.1.exe (PID: 8064)
- Radmin_VPN_1.4.4642.1.exe (PID: 8160)
- Radmin_VPN_1.4.4642.1.tmp (PID: 8180)
- drvinst.exe (PID: 7692)
- drvinst.exe (PID: 6872)
Reads the date of Windows installation
- Radmin_VPN_1.4.4642.1.tmp (PID: 8084)
Reads the Windows owner or organization settings
- Radmin_VPN_1.4.4642.1.tmp (PID: 8180)
- msiexec.exe (PID: 7352)
Process drops legitimate windows executable
- Radmin_VPN_1.4.4642.1.tmp (PID: 8180)
- msiexec.exe (PID: 7352)
Checks Windows Trust Settings
- msiexec.exe (PID: 7352)
- MSI854.tmp (PID: 7520)
- drvinst.exe (PID: 7692)
Adds/modifies Windows certificates
- msiexec.exe (PID: 7352)
The process drops C-runtime libraries
- msiexec.exe (PID: 7352)
The process creates files with name similar to system file names
- msiexec.exe (PID: 7352)
Drops a system driver (possible attempt to evade defenses)
- msiexec.exe (PID: 7352)
- drvinst.exe (PID: 7692)
- drvinst.exe (PID: 6872)
Creates files in the driver directory
- drvinst.exe (PID: 7692)
- MSI854.tmp (PID: 7520)
- drvinst.exe (PID: 6872)
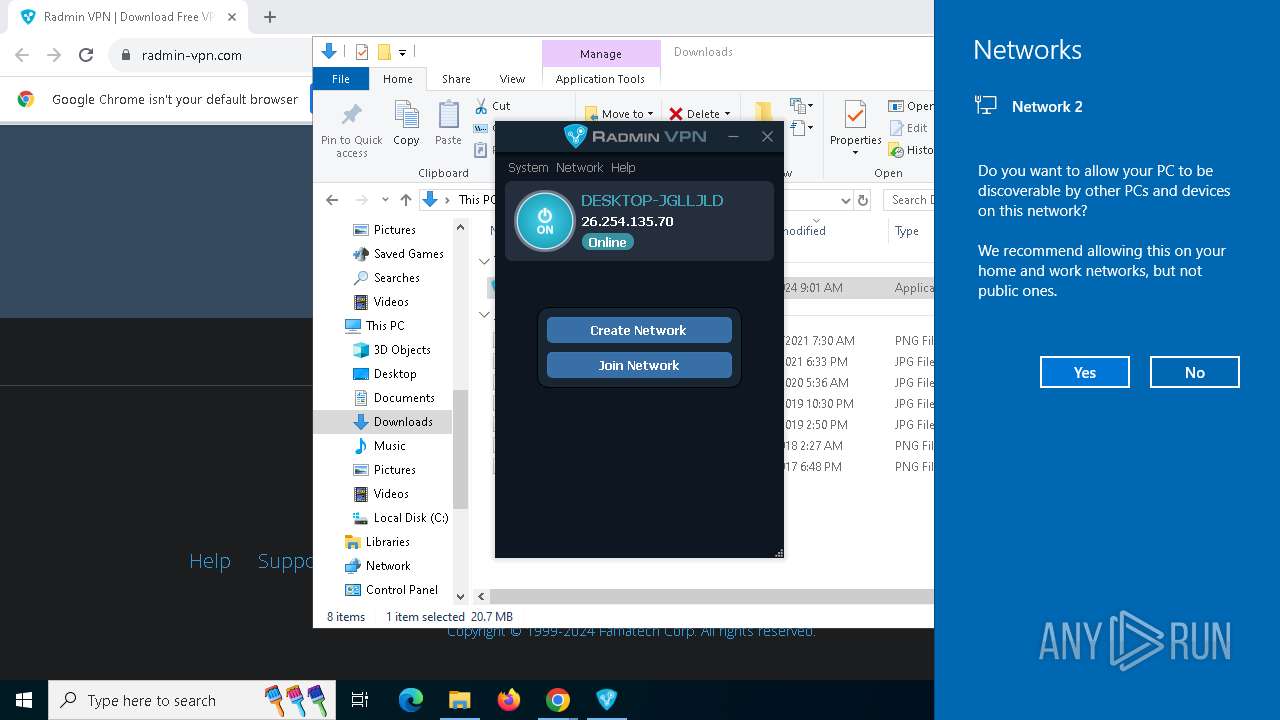
Creates or modifies Windows services
- drvinst.exe (PID: 6872)
Executes as Windows Service
- RvControlSvc.exe (PID: 8148)
Uses NETSH.EXE to add a firewall rule or allowed programs
- msiexec.exe (PID: 7876)
Suspicious use of NETSH.EXE
- cmd.exe (PID: 6872)
- cmd.exe (PID: 7924)
- cmd.exe (PID: 6724)
- cmd.exe (PID: 8024)
- cmd.exe (PID: 5288)
Starts CMD.EXE for commands execution
- RvControlSvc.exe (PID: 8148)
Connects to unusual port
- RvControlSvc.exe (PID: 8148)
There is functionality for taking screenshot (YARA)
- RvRvpnGui.exe (PID: 7332)
INFO
Checks supported languages
- Radmin_VPN_1.4.4642.1.exe (PID: 8064)
- Radmin_VPN_1.4.4642.1.tmp (PID: 8084)
- Radmin_VPN_1.4.4642.1.exe (PID: 8160)
- msiexec.exe (PID: 7352)
- msiexec.exe (PID: 1792)
- Radmin_VPN_1.4.4642.1.tmp (PID: 8180)
- MSI854.tmp (PID: 7520)
- drvinst.exe (PID: 7692)
- drvinst.exe (PID: 6872)
- RvControlSvc.exe (PID: 8148)
- RvRvpnGui.exe (PID: 7332)
- msiexec.exe (PID: 7876)
Reads the computer name
- Radmin_VPN_1.4.4642.1.tmp (PID: 8084)
- msiexec.exe (PID: 7352)
- msiexec.exe (PID: 1792)
- Radmin_VPN_1.4.4642.1.tmp (PID: 8180)
- MSI854.tmp (PID: 7520)
- drvinst.exe (PID: 7692)
- drvinst.exe (PID: 6872)
- msiexec.exe (PID: 7876)
- RvControlSvc.exe (PID: 8148)
- RvRvpnGui.exe (PID: 7332)
Create files in a temporary directory
- Radmin_VPN_1.4.4642.1.exe (PID: 8064)
- Radmin_VPN_1.4.4642.1.exe (PID: 8160)
- Radmin_VPN_1.4.4642.1.tmp (PID: 8180)
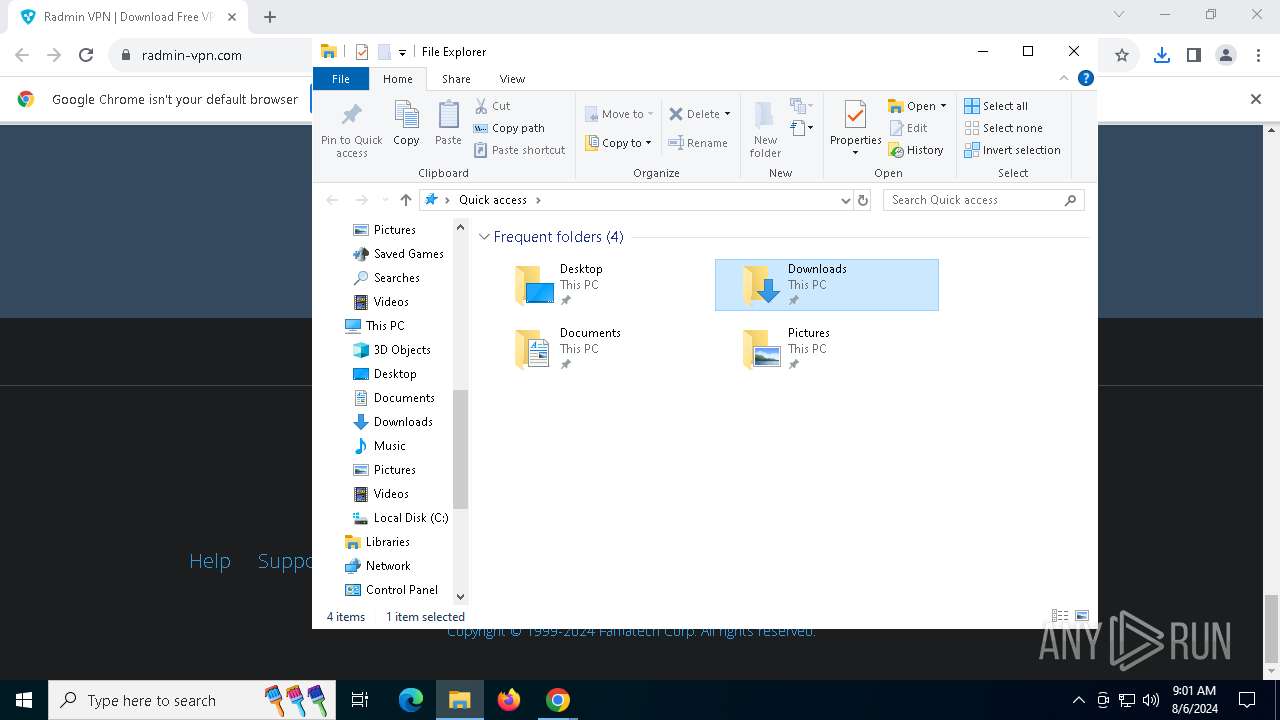
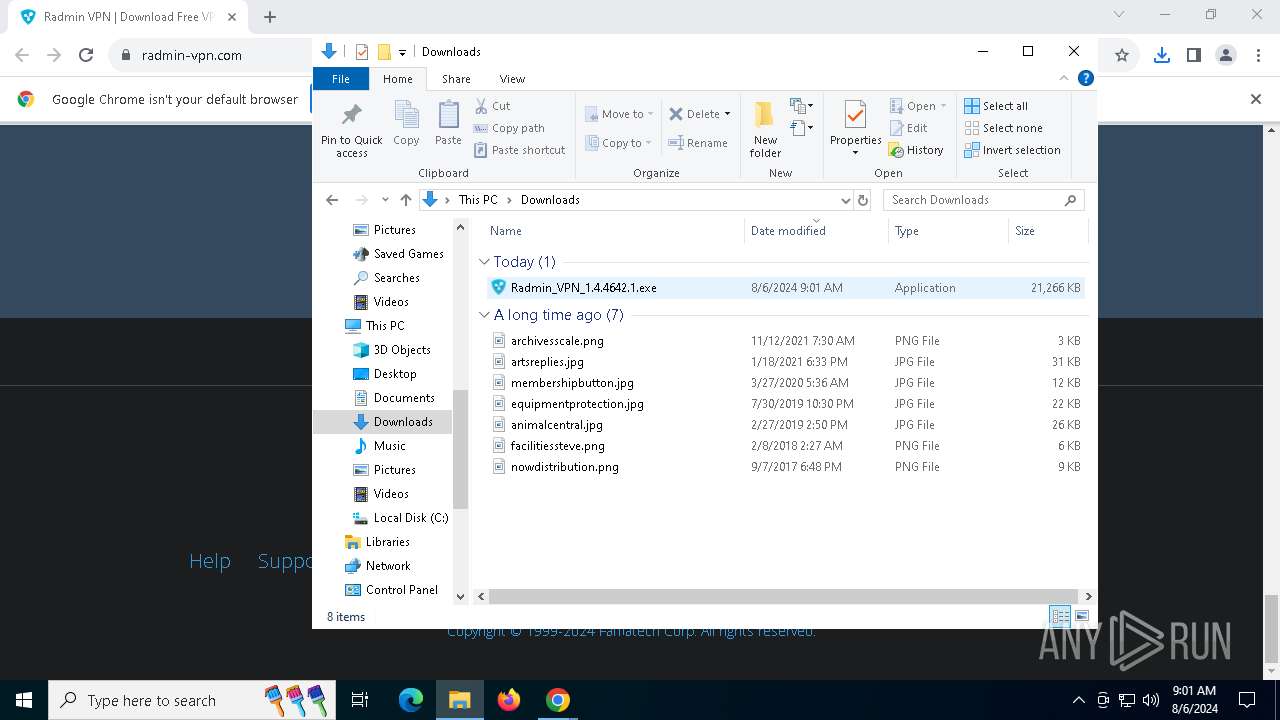
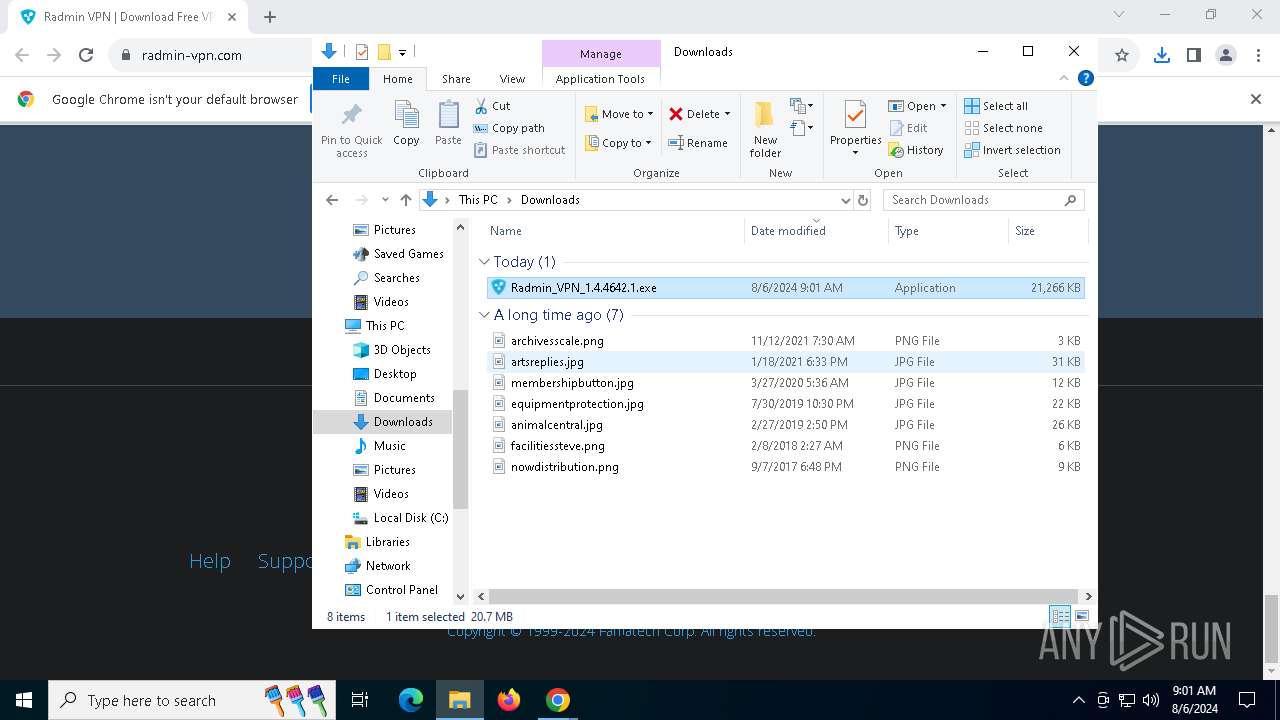
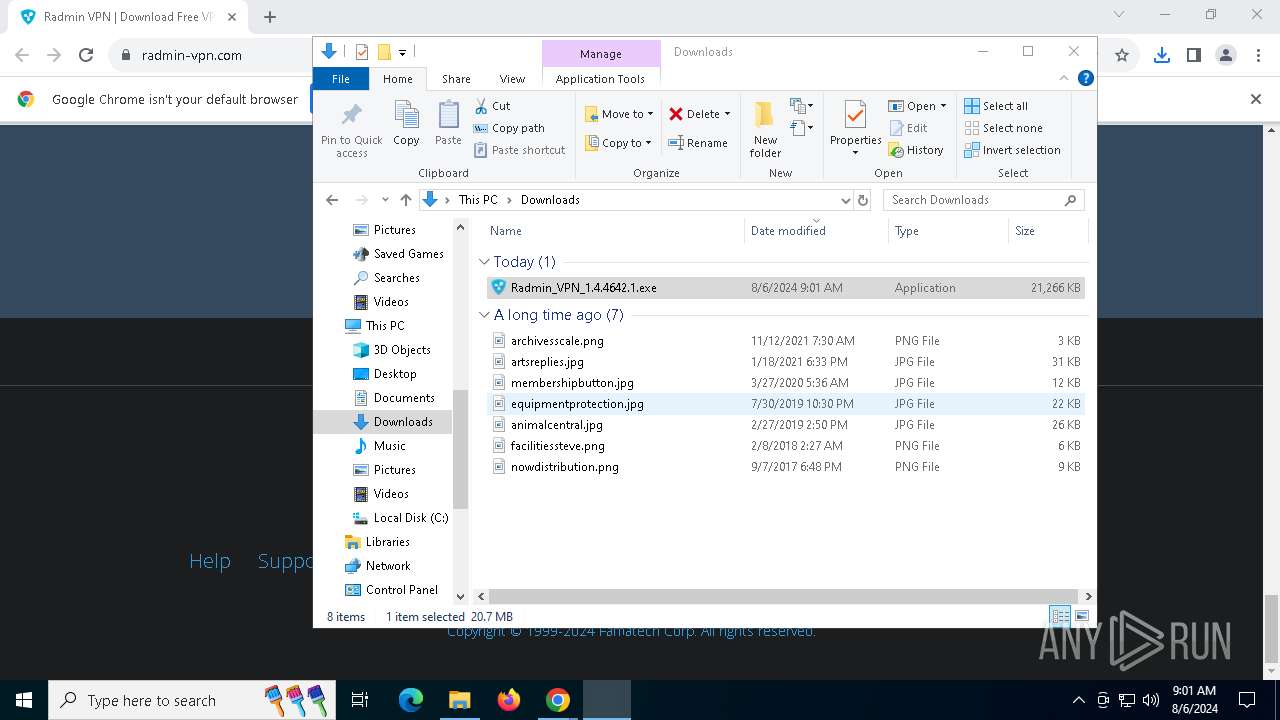
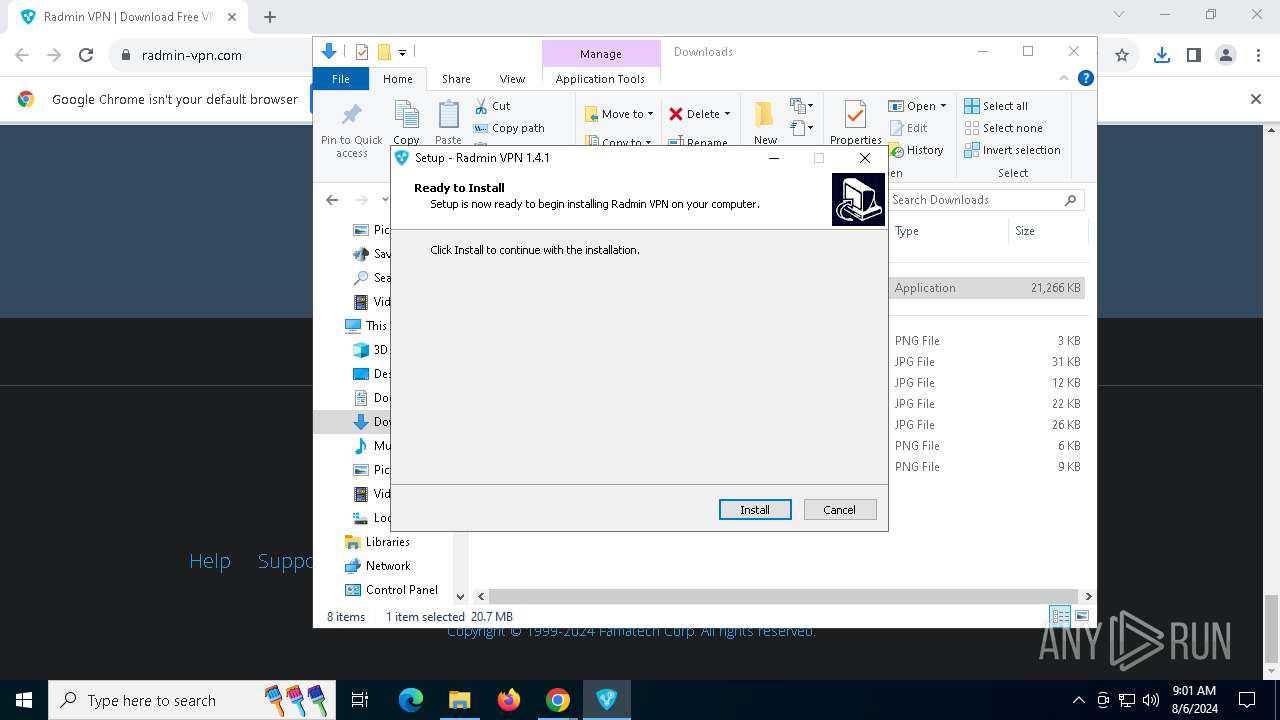
Manual execution by a user
- Radmin_VPN_1.4.4642.1.exe (PID: 8064)
- RvRvpnGui.exe (PID: 7332)
The process uses the downloaded file
- chrome.exe (PID: 7824)
- chrome.exe (PID: 6188)
Executable content was dropped or overwritten
- chrome.exe (PID: 6188)
- msiexec.exe (PID: 7352)
- chrome.exe (PID: 2648)
Reads Microsoft Office registry keys
- chrome.exe (PID: 6188)
Process checks computer location settings
- Radmin_VPN_1.4.4642.1.tmp (PID: 8084)
Drops the executable file immediately after the start
- chrome.exe (PID: 6188)
- chrome.exe (PID: 2648)
Application launched itself
- chrome.exe (PID: 6188)
Reads the software policy settings
- msiexec.exe (PID: 7352)
- MSI854.tmp (PID: 7520)
- drvinst.exe (PID: 7692)
Reads the machine GUID from the registry
- msiexec.exe (PID: 7352)
- MSI854.tmp (PID: 7520)
- drvinst.exe (PID: 7692)
- RvControlSvc.exe (PID: 8148)
- RvRvpnGui.exe (PID: 7332)
Reads Environment values
- msiexec.exe (PID: 1792)
Starts application with an unusual extension
- msiexec.exe (PID: 7352)
Creates files in the program directory
- RvControlSvc.exe (PID: 8148)
Creates a software uninstall entry
- msiexec.exe (PID: 7352)
Disables trace logs
- netsh.exe (PID: 6828)
- netsh.exe (PID: 7956)
- netsh.exe (PID: 7880)
- netsh.exe (PID: 7316)
- netsh.exe (PID: 4248)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
198
Monitored processes
51
Malicious processes
6
Suspicious processes
2
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1748 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --disable-quic --no-appcompat-clear --mojo-platform-channel-handle=5592 --field-trial-handle=1904,i,8682055627773276057,8939605804428396380,262144 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction --variations-seed-version /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 122.0.6261.70 Modules
| |||||||||||||||
| 1792 | C:\Windows\syswow64\MsiExec.exe -Embedding 77F0B6251D73D0A313C0C78B89E0C8CF | C:\Windows\SysWOW64\msiexec.exe | — | msiexec.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows® installer Exit code: 0 Version: 5.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1860 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2508 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2648 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --disable-quic --no-appcompat-clear --mojo-platform-channel-handle=5792 --field-trial-handle=1904,i,8682055627773276057,8939605804428396380,262144 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction --variations-seed-version /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | chrome.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 122.0.6261.70 Modules
| |||||||||||||||
| 3864 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --disable-gpu-sandbox --use-gl=disabled --gpu-vendor-id=5140 --gpu-device-id=140 --gpu-sub-system-id=0 --gpu-revision=0 --gpu-driver-version=10.0.19041.3636 --no-appcompat-clear --gpu-preferences=WAAAAAAAAADoABAMAAAAAAAAAAAAAAAAAABgAAAAAAA4AAAAAAAAAAAAAABEAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAAGAAAAAAAAAAYAAAAAAAAAAgAAAAAAAAACAAAAAAAAAAIAAAAAAAAAA== --mojo-platform-channel-handle=5468 --field-trial-handle=1904,i,8682055627773276057,8939605804428396380,262144 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction --variations-seed-version /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 122.0.6261.70 Modules
| |||||||||||||||
| 4160 | netsh advfirewall firewall add rule name="Radmin VPN Control Service" dir=in action=allow program="C:\Program Files (x86)\Radmin VPN\RvControlSvc.exe" enable=yes profile=any edge=yes | C:\Windows\SysWOW64\netsh.exe | — | msiexec.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Network Command Shell Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 4248 | C:\WINDOWS\system32\netsh.exe interface ip delete route prefix=0.0.0.0/0 interface="Radmin VPN" nexthop=26.0.0.1 | C:\Windows\SysWOW64\netsh.exe | — | cmd.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Network Command Shell Exit code: 1 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 5084 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | netsh.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 5152 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=unzip.mojom.Unzipper --lang=en-US --service-sandbox-type=service --disable-quic --no-appcompat-clear --mojo-platform-channel-handle=5544 --field-trial-handle=1904,i,8682055627773276057,8939605804428396380,262144 --disable-features=OptimizationGuideModelDownloading,OptimizationHints,OptimizationHintsFetching,OptimizationTargetPrediction --variations-seed-version /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 122.0.6261.70 Modules
| |||||||||||||||
Total events
34 895
Read events
34 621
Write events
236
Delete events
38
Modification events
| (PID) Process: | (6188) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (6188) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (6188) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (6188) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (6188) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (6188) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (6188) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\StabilityMetrics |
| Operation: | write | Name: | user_experience_metrics.stability.exited_cleanly |
Value: 0 | |||
| (PID) Process: | (6188) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (6188) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
| (PID) Process: | (6188) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | metricsid |
Value: | |||
Executable files
125
Suspicious files
197
Text files
39
Unknown types
4
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 6188 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\discounts_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6188 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\chrome_cart_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6188 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\coupon_db\LOG.old~RFe5cd1.TMP | — | |
MD5:— | SHA256:— | |||
| 6188 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\parcel_tracking_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6188 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\commerce_subscription_db\LOG.old~RFe5cd1.TMP | — | |
MD5:— | SHA256:— | |||
| 6188 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\commerce_subscription_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6188 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\coupon_db\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6188 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\PersistentOriginTrials\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6188 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Variations | binary | |
MD5:961E3604F228B0D10541EBF921500C86 | SHA256:F7B24F2EB3D5EB0550527490395D2F61C3D2FE74BB9CB345197DAD81B58B5FED | |||
| 6188 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Sync Data\LevelDB\LOG.old~RFe5cc2.TMP | text | |
MD5:8F45965291AB2DA10EEB049FB6E917C6 | SHA256:8A0DE526945B27CDBBD87357C85FDDD37B572370F894CB0A5AC533FD465D2166 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
30
TCP/UDP connections
90
DNS requests
53
Threats
2
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
5336 | SearchApp.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAI5PUjXAkJafLQcAAsO18o%3D | US | binary | 314 b | whitelisted |
3068 | svchost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | US | binary | 471 b | whitelisted |
3180 | backgroundTaskHost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAn5bsKVVV8kdJ6vHl3O1J0%3D | US | binary | 471 b | whitelisted |
1656 | backgroundTaskHost.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAn5bsKVVV8kdJ6vHl3O1J0%3D | US | binary | 471 b | whitelisted |
6188 | chrome.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTfIs%2BLjDtGwQ09XEB1Yeq%2BtX%2BBgQQU7NfjgtJxXWRM3y5nP%2Be6mK4cD08CEAitQLJg0pxMn17Nqb2Trtk%3D | US | binary | 727 b | whitelisted |
7020 | svchost.exe | HEAD | 200 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/imoffpf67hel7kbknqflao2oo4_1.0.2738.0/neifaoindggfcjicffkgpmnlppeffabd_1.0.2738.0_win64_kj4dp5kifwxbdodqls7e5nzhtm.crx3 | US | — | — | whitelisted |
6188 | chrome.exe | GET | 200 | 192.229.221.95:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSRXerF0eFeSWRripTgTkcJWMm7iQQUaDfg67Y7%2BF8Rhvv%2BYXsIiGX0TkICEANmchMIZYHj%2F%2B8%2Bj8Y68sw%3D | US | binary | 727 b | whitelisted |
7020 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/imoffpf67hel7kbknqflao2oo4_1.0.2738.0/neifaoindggfcjicffkgpmnlppeffabd_1.0.2738.0_win64_kj4dp5kifwxbdodqls7e5nzhtm.crx3 | US | binary | 1.09 Kb | whitelisted |
7020 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/imoffpf67hel7kbknqflao2oo4_1.0.2738.0/neifaoindggfcjicffkgpmnlppeffabd_1.0.2738.0_win64_kj4dp5kifwxbdodqls7e5nzhtm.crx3 | US | binary | 1.98 Kb | whitelisted |
7020 | svchost.exe | GET | 206 | 34.104.35.123:80 | http://edgedl.me.gvt1.com/edgedl/release2/chrome_component/imoffpf67hel7kbknqflao2oo4_1.0.2738.0/neifaoindggfcjicffkgpmnlppeffabd_1.0.2738.0_win64_kj4dp5kifwxbdodqls7e5nzhtm.crx3 | US | binary | 4.12 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
5040 | RUXIMICS.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | unknown |
3888 | svchost.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
2120 | MoUsoCoreWorker.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | unknown |
5044 | svchost.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | unknown |
6460 | chrome.exe | 142.251.31.84:443 | accounts.google.com | GOOGLE | US | unknown |
6188 | chrome.exe | 239.255.255.250:1900 | — | — | — | whitelisted |
6460 | chrome.exe | 104.26.15.96:443 | www.radmin-vpn.com | CLOUDFLARENET | US | unknown |
6460 | chrome.exe | 172.217.16.202:443 | fonts.googleapis.com | GOOGLE | US | whitelisted |
6460 | chrome.exe | 216.58.206.67:443 | fonts.gstatic.com | GOOGLE | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
www.radmin-vpn.com |
| unknown |
accounts.google.com |
| whitelisted |
fonts.googleapis.com |
| whitelisted |
fonts.gstatic.com |
| whitelisted |
www.googletagmanager.com |
| whitelisted |
ajax.googleapis.com |
| whitelisted |
content-autofill.googleapis.com |
| whitelisted |
region1.analytics.google.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
6460 | chrome.exe | Not Suspicious Traffic | INFO [ANY.RUN] Google Hosted Libraries (ajax .googleapis .com) |
6460 | chrome.exe | Not Suspicious Traffic | INFO [ANY.RUN] Google Hosted Libraries (ajax .googleapis .com) |