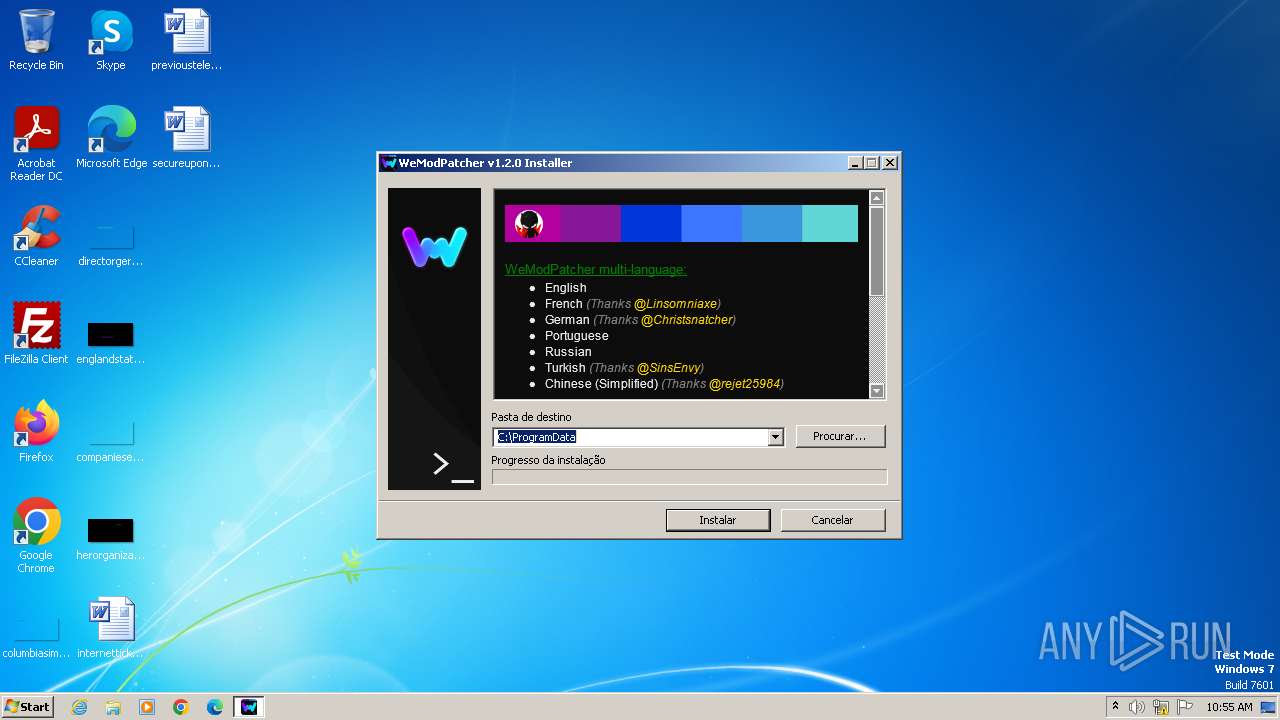
| File name: | WeModPatcher v1.2.0 Installer.exe |
| Full analysis: | https://app.any.run/tasks/f8a466c7-0de2-4878-8f14-4aeafd78a5bc |
| Verdict: | Malicious activity |
| Analysis date: | December 01, 2023, 10:55:46 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows |
| MD5: | 099C89D14AC9E0573483C3A704F1824D |
| SHA1: | 0B573E79CA0B38EB747FE165D2AB2C0333B0F462 |
| SHA256: | 6432E913FCD2DC3BF0D8567B0B842998F834DA2A3A0C752B0C405EAEDCBC679C |
| SSDEEP: | 98304:dsQ4fETCCh2OVNYDptL/MduV6bzBGnQAJZSJ9e7SVyZcyMvUE8MjPY0gcNicGyq2:/Y3cetg |
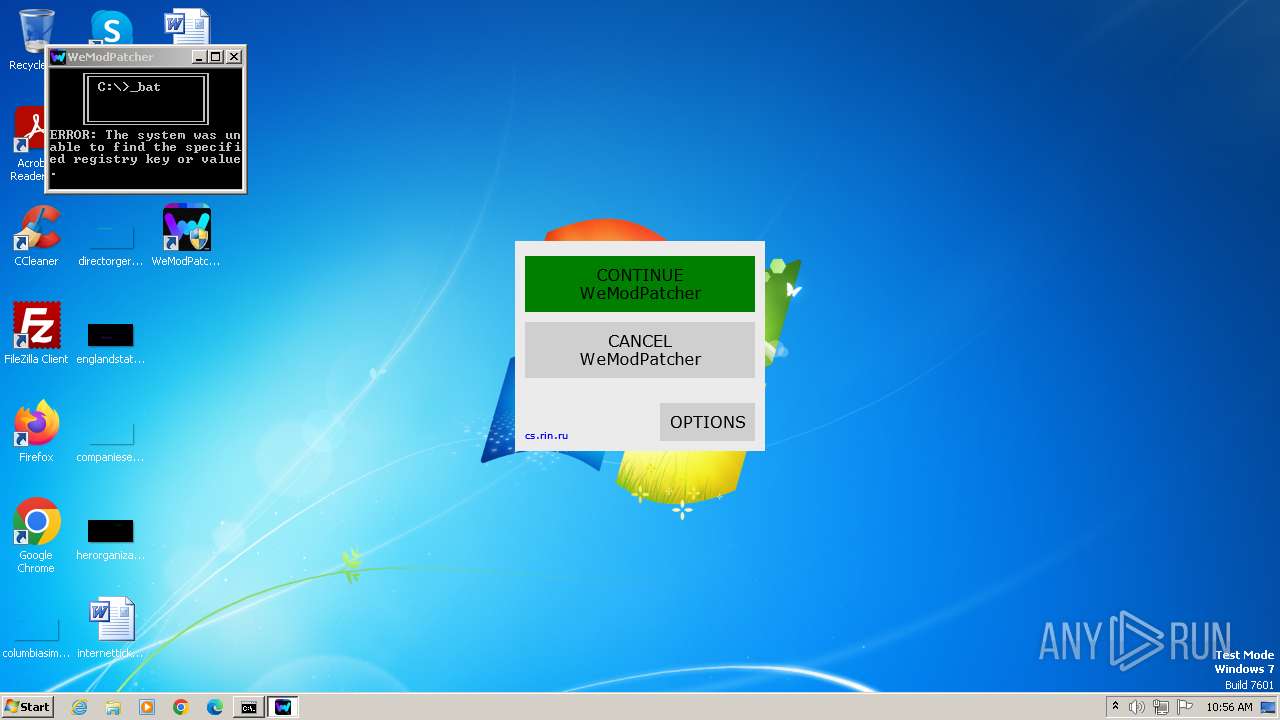
MALICIOUS
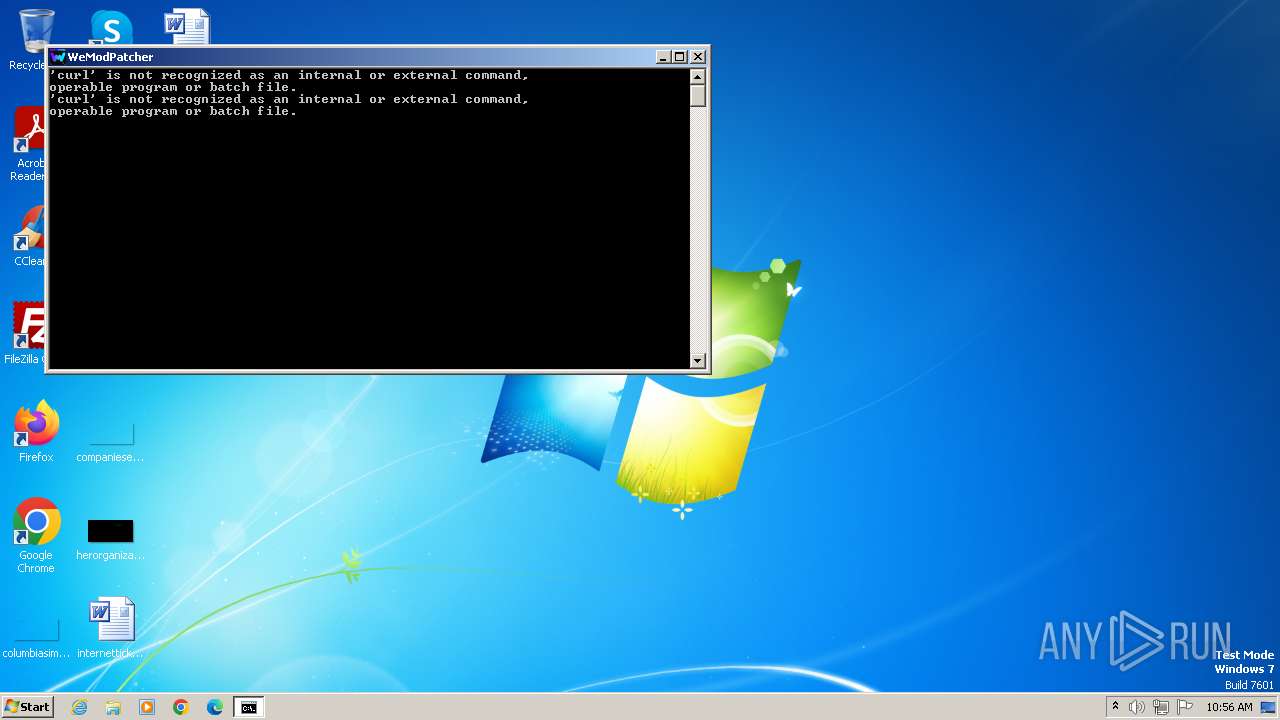
Starts Visual C# compiler
- powershell.exe (PID: 3744)
Drops the executable file immediately after the start
- csc.exe (PID: 2748)
SUSPICIOUS
Reads the Internet Settings
- WeModPatcher v1.2.0 Installer.exe (PID: 564)
- mshta.exe (PID: 3412)
- mshta.exe (PID: 3148)
Reads Microsoft Outlook installation path
- WeModPatcher v1.2.0 Installer.exe (PID: 564)
Reads Internet Explorer settings
- WeModPatcher v1.2.0 Installer.exe (PID: 564)
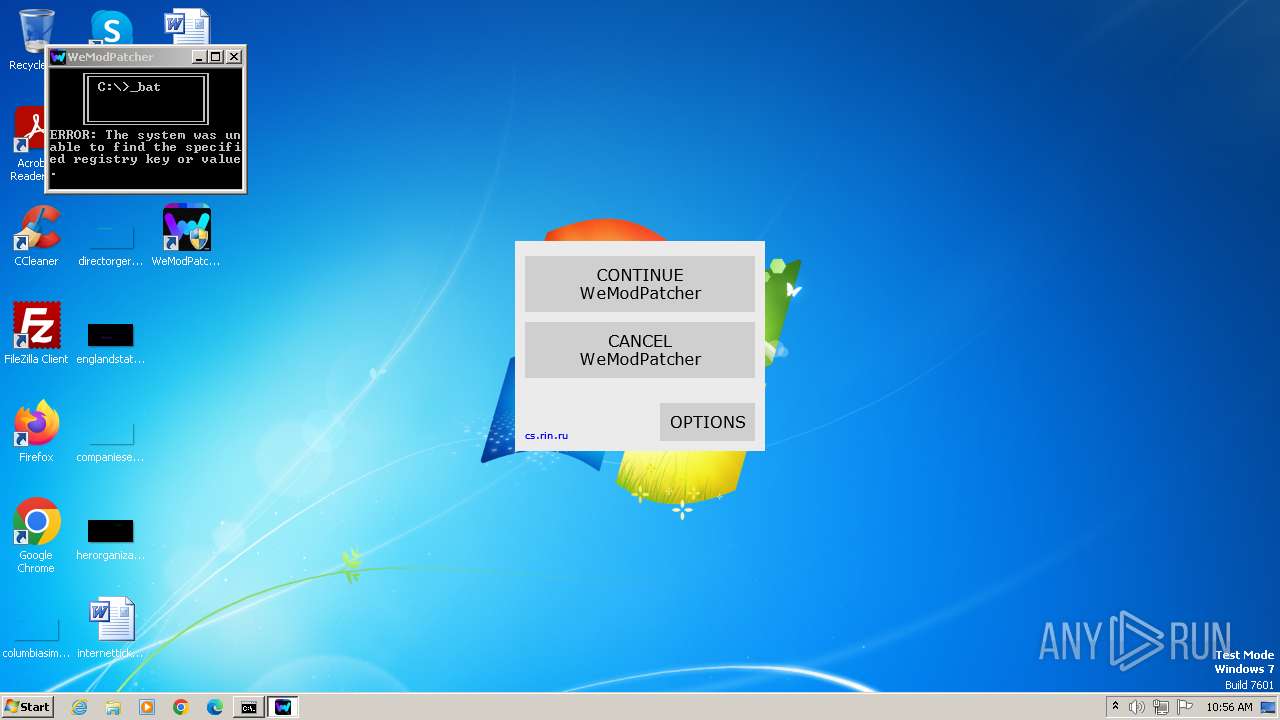
Application launched itself
- cmd.exe (PID: 2528)
Starts POWERSHELL.EXE for commands execution
- cmd.exe (PID: 2528)
- cmd.exe (PID: 3680)
- cmd.exe (PID: 3288)
- cmd.exe (PID: 4088)
- cmd.exe (PID: 276)
- cmd.exe (PID: 2932)
- cmd.exe (PID: 2760)
- cmd.exe (PID: 3820)
- cmd.exe (PID: 2500)
- cmd.exe (PID: 3860)
- cmd.exe (PID: 3020)
- cmd.exe (PID: 2472)
Powershell version downgrade attack
- powershell.exe (PID: 2544)
- powershell.exe (PID: 3296)
- powershell.exe (PID: 3340)
- powershell.exe (PID: 3756)
- powershell.exe (PID: 1004)
- powershell.exe (PID: 2912)
- powershell.exe (PID: 1872)
- powershell.exe (PID: 3640)
- powershell.exe (PID: 2996)
- powershell.exe (PID: 2892)
- powershell.exe (PID: 1600)
- powershell.exe (PID: 3096)
- powershell.exe (PID: 1248)
- powershell.exe (PID: 3576)
- powershell.exe (PID: 3744)
- powershell.exe (PID: 372)
- powershell.exe (PID: 2676)
Starts CMD.EXE for commands execution
- cmd.exe (PID: 2528)
Get information on the list of running processes
- cmd.exe (PID: 2528)
- cmd.exe (PID: 3856)
- cmd.exe (PID: 3680)
- cmd.exe (PID: 2100)
Starts application with an unusual extension
- cmd.exe (PID: 3200)
- cmd.exe (PID: 2528)
The process bypasses the loading of PowerShell profile settings
- cmd.exe (PID: 2760)
- cmd.exe (PID: 3820)
Creates FileSystem object to access computer's file system (SCRIPT)
- mshta.exe (PID: 3412)
Checks whether a specific file exists (SCRIPT)
- mshta.exe (PID: 3412)
Writes binary data to a Stream object (SCRIPT)
- mshta.exe (PID: 3412)
Probably obfuscated PowerShell command line is found
- cmd.exe (PID: 2528)
Uses .NET C# to load dll
- powershell.exe (PID: 3744)
INFO
Checks supported languages
- WeModPatcher v1.2.0 Installer.exe (PID: 564)
- wmpnscfg.exe (PID: 2620)
- chcp.com (PID: 3108)
- chcp.com (PID: 2072)
- mode.com (PID: 2548)
- chcp.com (PID: 3532)
- chcp.com (PID: 3324)
- mode.com (PID: 2052)
- csc.exe (PID: 2748)
- cvtres.exe (PID: 552)
Reads the computer name
- WeModPatcher v1.2.0 Installer.exe (PID: 564)
- wmpnscfg.exe (PID: 2620)
Checks proxy server information
- WeModPatcher v1.2.0 Installer.exe (PID: 564)
Reads the machine GUID from the registry
- WeModPatcher v1.2.0 Installer.exe (PID: 564)
- cvtres.exe (PID: 552)
- csc.exe (PID: 2748)
Creates files in the program directory
- WeModPatcher v1.2.0 Installer.exe (PID: 564)
- cmd.exe (PID: 2528)
Manual execution by a user
- wmpnscfg.exe (PID: 2620)
- cmd.exe (PID: 2528)
Reads Internet Explorer settings
- mshta.exe (PID: 3412)
- mshta.exe (PID: 3148)
Create files in a temporary directory
- csc.exe (PID: 2748)
- cvtres.exe (PID: 552)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win64 Executable (generic) (76.4) |
|---|---|---|
| .exe | | | Win32 Executable (generic) (12.4) |
| .exe | | | Generic Win/DOS Executable (5.5) |
| .exe | | | DOS Executable Generic (5.5) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2023:02:16 13:31:25+01:00 |
| ImageFileCharacteristics: | Executable, 32-bit |
| PEType: | PE32 |
| LinkerVersion: | 14.33 |
| CodeSize: | 208384 |
| InitializedDataSize: | 474624 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x205e0 |
| OSVersion: | 5.1 |
| ImageVersion: | - |
| SubsystemVersion: | 5.1 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 0.1.2.0 |
| ProductVersionNumber: | 0.0.0.0 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Windows NT 32-bit |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | English (U.S.) |
| CharacterSet: | Unicode |
| FileDescription: | WeModPatcher Installer |
| LegalCopyright: | brunolee© |
| LegalTrademarks: | brunolee™ |
| OriginalFileName: | WeModPatcher Installer |
| ProductName: | WeModPatcher Installer |
| ProductVersion: | 1.2.0 |
Total processes
91
Monitored processes
53
Malicious processes
31
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 276 | C:\Windows\system32\cmd.exe /c powershell -Command "(Get-FileHash Options.ini -Algorithm MD5).Hash" | C:\Windows\System32\cmd.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 1 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 372 | powershell -Command "(gc -LiteralPath 'C:\ProgramData\WeModPatcher\Splash.hta') -replace 'REPLACE_TITLE', 'WeModPatcher' -replace 'REPLACE_VERSION', '1.2.0' -replace 'REPLACE_LANG01', 'WELCOME' | Out-File -LiteralPath 'C:\ProgramData\WeModPatcher\splash.hta' -encoding UTF8" | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 552 | C:\Windows\Microsoft.NET\Framework\v2.0.50727\cvtres.exe /NOLOGO /READONLY /MACHINE:IX86 "/OUT:C:\Users\admin\AppData\Local\Temp\RES36B.tmp" "c:\Users\admin\AppData\Local\Temp\CSC35A.tmp" | C:\Windows\Microsoft.NET\Framework\v2.0.50727\cvtres.exe | — | csc.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft® Resource File To COFF Object Conversion Utility Exit code: 0 Version: 8.00.50727.5003 (Win7SP1GDR.050727-5400) Modules
| |||||||||||||||
| 564 | "C:\Users\admin\AppData\Local\Temp\WeModPatcher v1.2.0 Installer.exe" | C:\Users\admin\AppData\Local\Temp\WeModPatcher v1.2.0 Installer.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Description: WeModPatcher Installer Exit code: 0 Modules
| |||||||||||||||
| 1004 | powershell -Command "[console]::title='WeModPatcher'" | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1152 | C:\Windows\system32\net1 session | C:\Windows\System32\net1.exe | — | net.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Net Command Exit code: 2 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 1248 | powershell -Command "[math]::Round(( - 818) / 2)" | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1296 | tasklist /NH /FI "WindowTitle eq "WeModPatcher"" | C:\Windows\System32\tasklist.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Lists the current running tasks Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1344 | C:\Windows\system32\cmd.exe /c curl -s https://pastebin.com/raw/ebBuTvpj | C:\Windows\System32\cmd.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 1 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 1420 | reg query "HKCU\SOFTWARE\Microsoft\Windows\CurrentVersion\Themes\Personalize" /V "AppsUseLightTheme" | C:\Windows\System32\reg.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Registry Console Tool Exit code: 1 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
22 839
Read events
21 891
Write events
948
Delete events
0
Modification events
| (PID) Process: | (564) WeModPatcher v1.2.0 Installer.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (564) WeModPatcher v1.2.0 Installer.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
| (PID) Process: | (564) WeModPatcher v1.2.0 Installer.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 1 | |||
| (PID) Process: | (564) WeModPatcher v1.2.0 Installer.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 0 | |||
| (PID) Process: | (564) WeModPatcher v1.2.0 Installer.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (564) WeModPatcher v1.2.0 Installer.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (2544) powershell.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\17F\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (2996) powershell.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\17F\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (3296) powershell.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\17F\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (3756) powershell.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\17F\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
Executable files
1
Suspicious files
57
Text files
15
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 564 | WeModPatcher v1.2.0 Installer.exe | C:\ProgramData\WeModPatcher\lang\lang_ru.ini | text | |
MD5:F24DD061213AD81D4726BE14039E385C | SHA256:060A6B9D9B29A52BDF91345C3D339C1EDAC8271A0F6EAB7BDA70F30E7AFC9227 | |||
| 564 | WeModPatcher v1.2.0 Installer.exe | C:\ProgramData\WeModPatcher\lang\lang_de.ini | text | |
MD5:608471B82E5FCF2ECF3A3F378F35147A | SHA256:ED5910859C5E75FC9702B53D255B9DC0FFEB3840E78111CF761A36370D8ED905 | |||
| 564 | WeModPatcher v1.2.0 Installer.exe | C:\ProgramData\WeModPatcher\lang\lang_en.ini | text | |
MD5:A9E2358A418971E211D6A144B3EC5E4C | SHA256:C782E16257E4AE02139F8F41807EDCBF66CD4D4A1605E1C3F137331587654143 | |||
| 564 | WeModPatcher v1.2.0 Installer.exe | C:\ProgramData\WeModPatcher\Options.hta | html | |
MD5:C0826786D1B58B03C4C134865CD0A0A6 | SHA256:E4CDEA4433591103E4C416165B9B7EEBFF79C30B011EEE839064C0621FE0B209 | |||
| 564 | WeModPatcher v1.2.0 Installer.exe | C:\ProgramData\WeModPatcher\lang\lang_tr.ini | text | |
MD5:9C37C75A5846D581B6F860ED909E7E9D | SHA256:9FC3E91EA3C8E00D48EC02F74B8002F19A63AEC9099371F0E475B0C39800F41E | |||
| 564 | WeModPatcher v1.2.0 Installer.exe | C:\ProgramData\WeModPatcher\lang\lang_fr.ini | text | |
MD5:89281E6F5ECB3C0E31EAB6C84E50B5B3 | SHA256:EAC750074AD4F4C623F5B35024E9FB43034825DF979435095E4978BD6E3AD7B2 | |||
| 2996 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\HYZPUQDTHP9ZUVZUCI3S.temp | binary | |
MD5:6B35579772ED1D0D0E199670AF663C90 | SHA256:65F6FE65E798AE0B1A04E964F2943A22AD91E03EE10C46FEDF85FFD992D90351 | |||
| 564 | WeModPatcher v1.2.0 Installer.exe | C:\ProgramData\WeModPatcher\WeModPatcher.bat | binary | |
MD5:702C3D176D7F2A4D2AC0B461248D1E4B | SHA256:686EDF85F7C29C72AB5FD09624974C2F7CE27AE4E8910DFC1754027DF1F9EA3D | |||
| 2528 | cmd.exe | C:\ProgramData\WeModPatcher\IsAdminNecessary | text | |
MD5:81051BCC2CF1BEDF378224B0A93E2877 | SHA256:7EB70257593DA06F682A3DDDA54A9D260D4FC514F645237F5CA74B08F8DA61A6 | |||
| 2544 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\6RYMZ20QPFHMA14659SE.temp | binary | |
MD5:6B35579772ED1D0D0E199670AF663C90 | SHA256:65F6FE65E798AE0B1A04E964F2943A22AD91E03EE10C46FEDF85FFD992D90351 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
4
DNS requests
1
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
868 | svchost.exe | 23.35.228.137:80 | — | AKAMAI-AS | DE | unknown |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
868 | svchost.exe | 95.101.148.135:80 | armmf.adobe.com | Akamai International B.V. | NL | unknown |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
armmf.adobe.com |
| whitelisted |
Threats
Process | Message |
|---|---|
csc.exe |
*** HR originated: -2147024774
*** Source File: d:\iso_whid\x86fre\base\isolation\com\copyout.cpp, line 1302
|
csc.exe |
*** HR originated: -2147024774
*** Source File: d:\iso_whid\x86fre\base\isolation\com\copyout.cpp, line 1302
|
csc.exe |
*** HR originated: -2147024774
*** Source File: d:\iso_whid\x86fre\base\isolation\com\copyout.cpp, line 1302
|
csc.exe |
*** HR propagated: -2147024774
*** Source File: d:\iso_whid\x86fre\base\isolation\com\enumidentityattribute.cpp, line 144
|
csc.exe |
*** HR propagated: -2147024774
*** Source File: d:\iso_whid\x86fre\base\isolation\com\enumidentityattribute.cpp, line 144
|
csc.exe |
*** HR propagated: -2147024774
*** Source File: d:\iso_whid\x86fre\base\isolation\com\enumidentityattribute.cpp, line 144
|
csc.exe |
*** HR propagated: -2147024774
*** Source File: d:\iso_whid\x86fre\base\isolation\com\enumidentityattribute.cpp, line 144
|
csc.exe |
*** HR originated: -2147024774
*** Source File: d:\iso_whid\x86fre\base\isolation\com\copyout.cpp, line 1302
|
csc.exe |
*** HR originated: -2147024774
*** Source File: d:\iso_whid\x86fre\base\isolation\com\copyout.cpp, line 1302
|
csc.exe |
*** HR propagated: -2147024774
*** Source File: d:\iso_whid\x86fre\base\isolation\com\enumidentityattribute.cpp, line 144
|