| File name: | __입사지원서(221003) 경력사항도 같이 기재하였습니다 잘 부탁드립니다1.exe |
| Full analysis: | https://app.any.run/tasks/c1d85456-321b-4b23-9a5a-6875dd5fa328 |
| Verdict: | Malicious activity |
| Analysis date: | October 05, 2022, 07:30:25 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, Nullsoft Installer self-extracting archive |
| MD5: | 71D5AEA26377D283B4216BDBB6558AD0 |
| SHA1: | 1BBF332186F4D071D75E3FAED6C2254B815AEB82 |
| SHA256: | 642CB9A61F0AEF9F6CCBA823F82826E484C7A00EB1BBE639CA3063EA8E8473D2 |
| SSDEEP: | 12288:RbRi5GsduvOU0flCkllkIfddKGRsXfg0gq+NIYgH0zl4D6MNO:RbRi5PuMvfdMGmfg0gN5goqGM0 |
MALICIOUS
Loads dropped or rewritten executable
- __입사지원서(221003) 경력사항도 같이 기재하였습니다 잘 부탁드립니다1.exe (PID: 3432)
Drops the executable file immediately after the start
- __입사지원서(221003) 경력사항도 같이 기재하였습니다 잘 부탁드립니다1.exe (PID: 3432)
SUSPICIOUS
Executable content was dropped or overwritten
- __입사지원서(221003) 경력사항도 같이 기재하였습니다 잘 부탁드립니다1.exe (PID: 3432)
Reads the machine GUID from the registry
- __입사지원서(221003) 경력사항도 같이 기재하였습니다 잘 부탁드립니다1.exe (PID: 3432)
- __입사지원서(221003) 경력사항도 같이 기재하였습니다 잘 부탁드립니다1.exe (PID: 3316)
Application launched itself
- __입사지원서(221003) 경력사항도 같이 기재하였습니다 잘 부탁드립니다1.exe (PID: 3432)
Reads Internet Settings
- __입사지원서(221003) 경력사항도 같이 기재하였습니다 잘 부탁드립니다1.exe (PID: 3316)
INFO
Reads the computer name
- __입사지원서(221003) 경력사항도 같이 기재하였습니다 잘 부탁드립니다1.exe (PID: 3432)
- __입사지원서(221003) 경력사항도 같이 기재하였습니다 잘 부탁드립니다1.exe (PID: 3316)
Checks supported languages
- __입사지원서(221003) 경력사항도 같이 기재하였습니다 잘 부탁드립니다1.exe (PID: 3432)
- __입사지원서(221003) 경력사항도 같이 기재하였습니다 잘 부탁드립니다1.exe (PID: 3316)
Process checks LSA protection
- __입사지원서(221003) 경력사항도 같이 기재하였습니다 잘 부탁드립니다1.exe (PID: 3432)
- __입사지원서(221003) 경력사항도 같이 기재하였습니다 잘 부탁드립니다1.exe (PID: 3316)
Creates a file in a temporary directory
- __입사지원서(221003) 경력사항도 같이 기재하였습니다 잘 부탁드립니다1.exe (PID: 3432)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable MS Visual C++ (generic) (67.4) |
|---|---|---|
| .dll | | | Win32 Dynamic Link Library (generic) (14.2) |
| .exe | | | Win32 Executable (generic) (9.7) |
| .exe | | | Generic Win/DOS Executable (4.3) |
| .exe | | | DOS Executable Generic (4.3) |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 2021-Sep-25 21:57:46 |
| Detected languages: |
|
| Comments: | For additional details, visit PortableApps.com |
| CompanyName: | PortableApps.com |
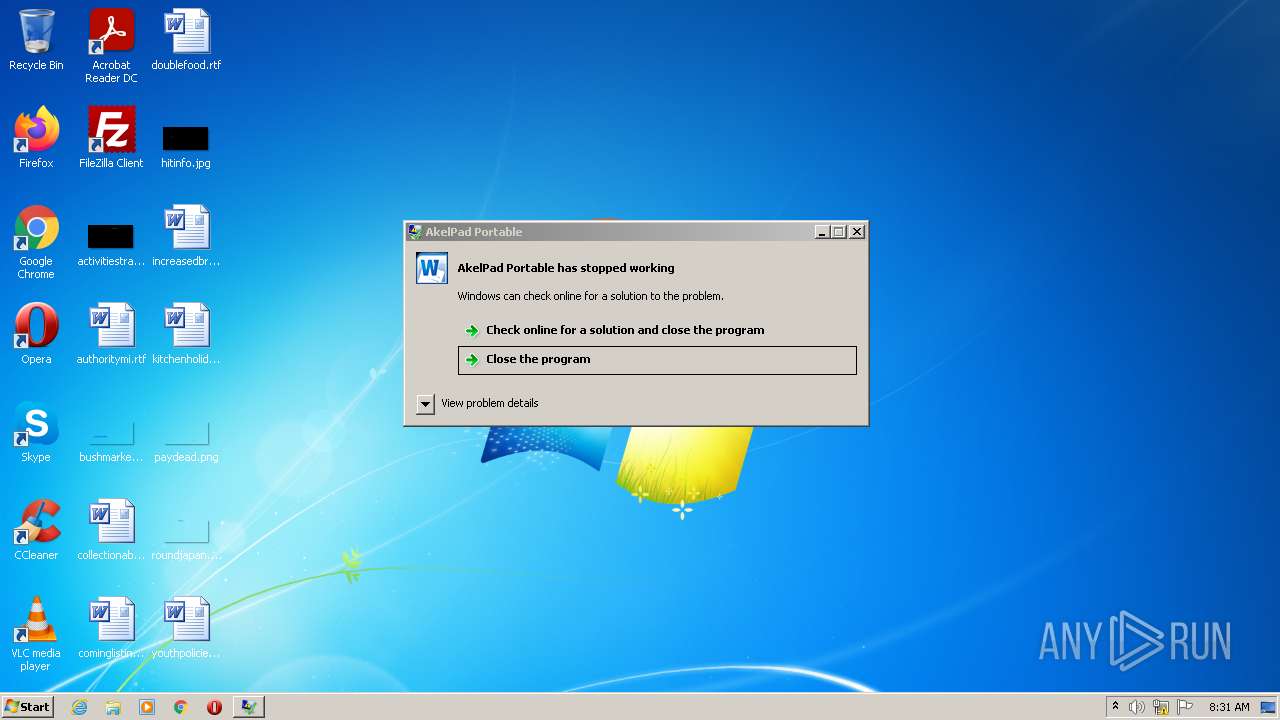
| FileDescription: | AkelPad Portable |
| FileVersion: | 4.9.8.0 |
| InternalName: | AkelPad Portable |
| LegalCopyright: | 2007-2016 PortableApps.com, PortableApps.com Installer 3.3.2.0 |
| LegalTrademarks: | PortableApps.com is a registered trademark of Rare Ideas, LLC. |
| OriginalFilename: | AkelPadPortable_4.9.8.paf.exe |
| PortableApps.comAppID: | AkelPadPortable |
| PortableApps.comFormatVersion: | 3.3 |
| PortableApps.comInstallerVersion: | 3.3.2.0 |
| ProductName: | AkelPad Portable |
| ProductVersion: | 4.9.8.0 |
DOS Header
| e_magic: | MZ |
|---|---|
| e_cblp: | 144 |
| e_cp: | 3 |
| e_crlc: | - |
| e_cparhdr: | 4 |
| e_minalloc: | - |
| e_maxalloc: | 65535 |
| e_ss: | - |
| e_sp: | 184 |
| e_csum: | - |
| e_ip: | - |
| e_cs: | - |
| e_ovno: | - |
| e_oemid: | - |
| e_oeminfo: | - |
| e_lfanew: | 216 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| NumberofSections: | 5 |
| TimeDateStamp: | 2021-Sep-25 21:57:46 |
| PointerToSymbolTable: | - |
| NumberOfSymbols: | - |
| SizeOfOptionalHeader: | 224 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 4096 | 26775 | 27136 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.4584 |
.rdata | 32768 | 5286 | 5632 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 5.02411 |
.data | 40960 | 176152 | 1536 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 4.15458 |
.ndata | 221184 | 65536 | 0 | IMAGE_SCN_CNT_UNINITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | |
.rsrc | 286720 | 419642 | 419840 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 5.11741 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 3.50665 | 744 | UNKNOWN | English - United States | RT_ICON |
2 | 5.34748 | 1128 | UNKNOWN | UNKNOWN | RT_ICON |
3 | 5.42724 | 2440 | UNKNOWN | UNKNOWN | RT_ICON |
4 | 5.43636 | 4264 | UNKNOWN | UNKNOWN | RT_ICON |
5 | 5.3803 | 9640 | UNKNOWN | UNKNOWN | RT_ICON |
6 | 5.34565 | 16936 | UNKNOWN | UNKNOWN | RT_ICON |
7 | 5.16345 | 38056 | UNKNOWN | UNKNOWN | RT_ICON |
8 | 5.1243 | 67624 | UNKNOWN | UNKNOWN | RT_ICON |
9 | 5.0017 | 270376 | UNKNOWN | UNKNOWN | RT_ICON |
103 | 2.16096 | 20 | UNKNOWN | English - United States | RT_GROUP_ICON |
Imports
ADVAPI32.dll |
COMCTL32.dll |
GDI32.dll |
KERNEL32.dll |
SHELL32.dll |
USER32.dll |
ole32.dll |
Total processes
37
Monitored processes
2
Malicious processes
2
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 3316 | ﮅ | C:\Users\admin\AppData\Local\Temp\__입사지원서(221003) 경력사항도 같이 기재하였습니다 잘 부탁드립니다1.exe | — | __입사지원서(221003) 경력사항도 같이 기재하였습니다 잘 부탁드립니다1.exe | |||||||||||
User: admin Company: PortableApps.com Integrity Level: MEDIUM Description: AkelPad Portable Exit code: 0 Version: 4.9.8.0 Modules
| |||||||||||||||
| 3432 | "C:\Users\admin\AppData\Local\Temp\__입사지원서(221003) 경력사항도 같이 기재하였습니다 잘 부탁드립니다1.exe" | C:\Users\admin\AppData\Local\Temp\__입사지원서(221003) 경력사항도 같이 기재하였습니다 잘 부탁드립니다1.exe | Explorer.EXE | ||||||||||||
User: admin Company: PortableApps.com Integrity Level: MEDIUM Description: AkelPad Portable Exit code: 0 Version: 4.9.8.0 Modules
| |||||||||||||||
Total events
1 042
Read events
1 022
Write events
20
Delete events
0
Modification events
| (PID) Process: | (3316) __입사지원서(221003) 경력사항도 같이 기재하였습니다 잘 부탁드립니다1.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (3316) __입사지원서(221003) 경력사항도 같이 기재하였습니다 잘 부탁드립니다1.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (3316) __입사지원서(221003) 경력사항도 같이 기재하였습니다 잘 부탁드립니다1.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (3316) __입사지원서(221003) 경력사항도 같이 기재하였습니다 잘 부탁드립니다1.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | write | Name: | ProxyEnable |
Value: 0 | |||
| (PID) Process: | (3316) __입사지원서(221003) 경력사항도 같이 기재하였습니다 잘 부탁드립니다1.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Connections |
| Operation: | write | Name: | SavedLegacySettings |
Value: 460000003B010000090000000000000000000000000000000400000000000000C0E333BBEAB1D3010000000000000000000000000100000002000000C0A80164000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
| (PID) Process: | (3316) __입사지원서(221003) 경력사항도 같이 기재하였습니다 잘 부탁드립니다1.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | ProxyBypass |
Value: 1 | |||
| (PID) Process: | (3316) __입사지원서(221003) 경력사항도 같이 기재하였습니다 잘 부탁드립니다1.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | IntranetName |
Value: 1 | |||
| (PID) Process: | (3316) __입사지원서(221003) 경력사항도 같이 기재하였습니다 잘 부탁드립니다1.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 1 | |||
| (PID) Process: | (3316) __입사지원서(221003) 경력사항도 같이 기재하였습니다 잘 부탁드립니다1.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 0 | |||
| (PID) Process: | (3316) __입사지원서(221003) 경력사항도 같이 기재하였습니다 잘 부탁드립니다1.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Wpad\{362E934C-743B-4588-8259-D2482DB771A8} |
| Operation: | write | Name: | WpadDecisionReason |
Value: 1 | |||
Executable files
1
Suspicious files
0
Text files
0
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3432 | __입사지원서(221003) 경력사항도 같이 기재하였습니다 잘 부탁드립니다1.exe | C:\Users\admin\AppData\Local\Temp\1228324467 | — | |
MD5:— | SHA256:— | |||
| 3432 | __입사지원서(221003) 경력사항도 같이 기재하였습니다 잘 부탁드립니다1.exe | C:\Users\admin\AppData\Local\Temp\nsqDAE5.tmp\System.dll | executable | |
MD5:CFF85C549D536F651D4FB8387F1976F2 | SHA256:8DC562CDA7217A3A52DB898243DE3E2ED68B80E62DDCB8619545ED0B4E7F65A8 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
0
DNS requests
1
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
DNS requests
Domain | IP | Reputation |
|---|---|---|
tinneatonenessnabobical.com |
| suspicious |