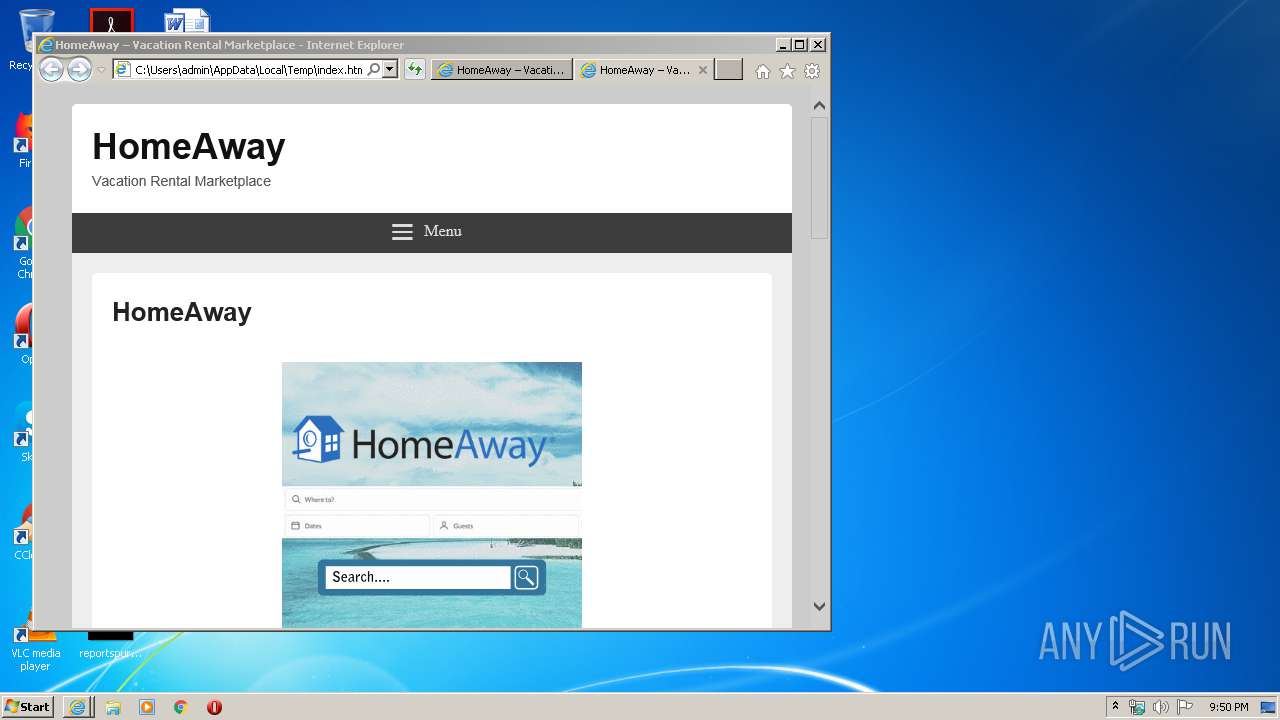
| download: | index.html |
| Full analysis: | https://app.any.run/tasks/99e35fa6-35cb-46f6-8b8f-c28181d67565 |
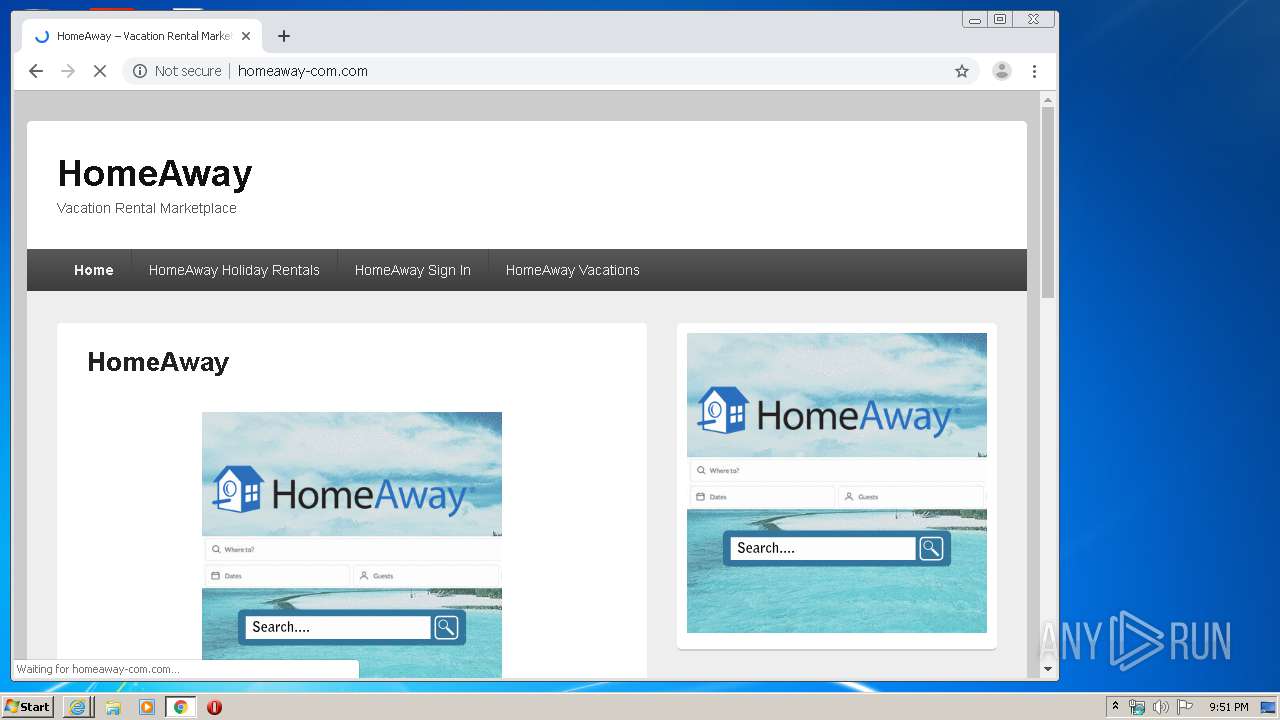
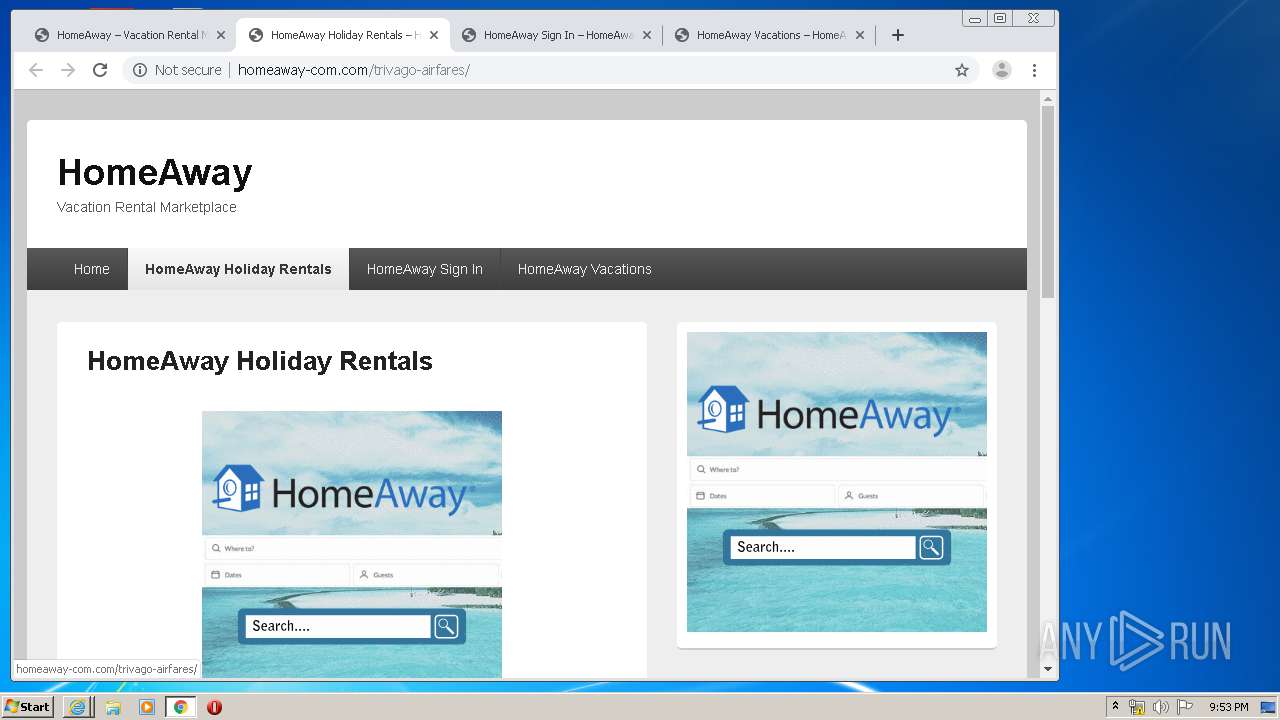
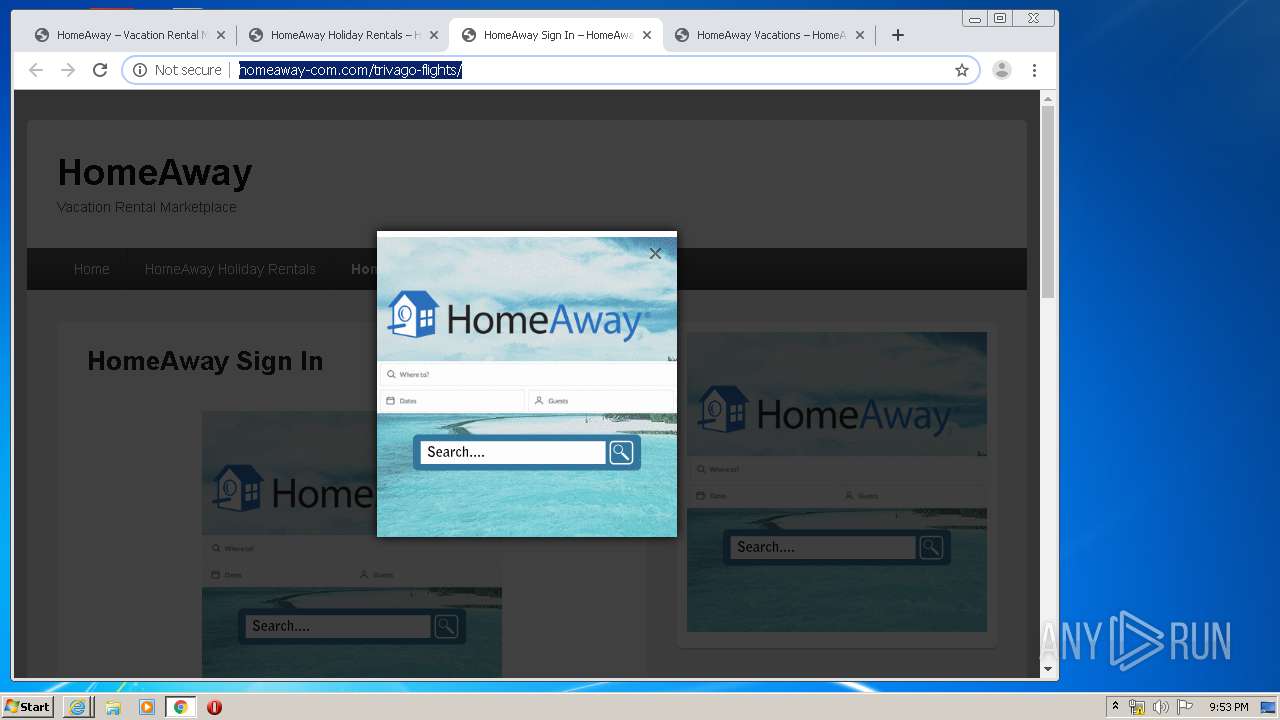
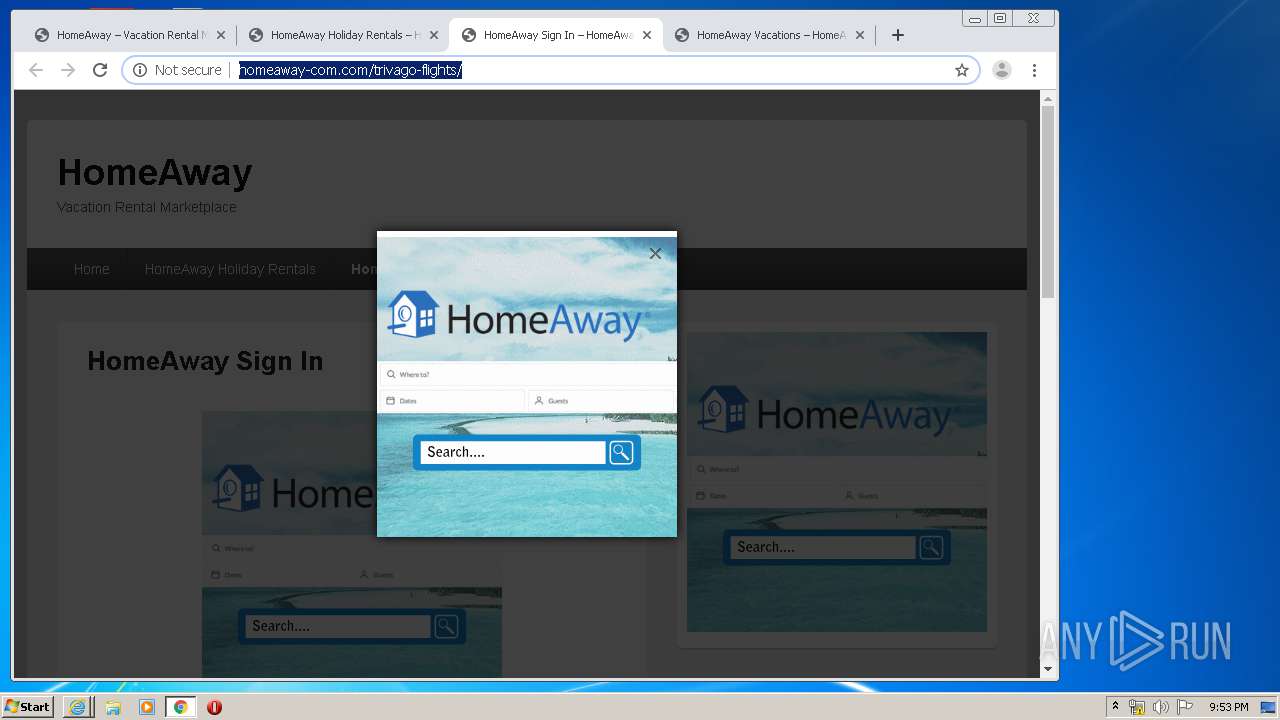
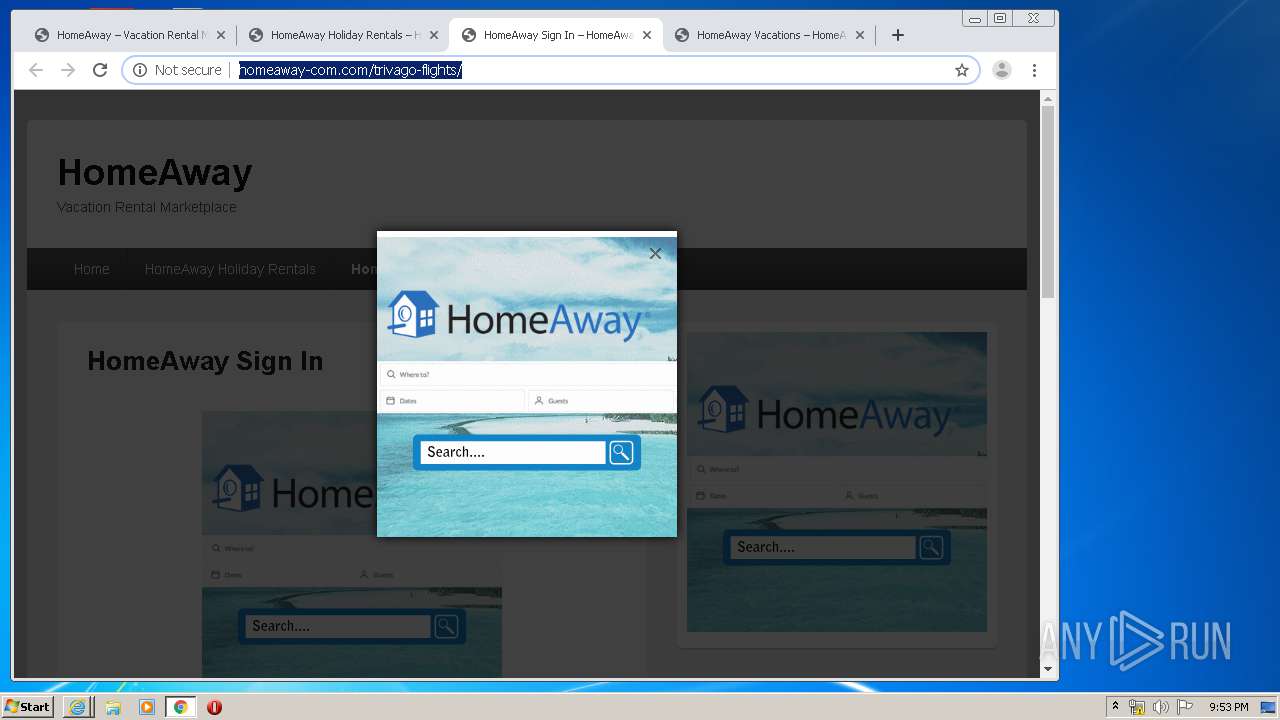
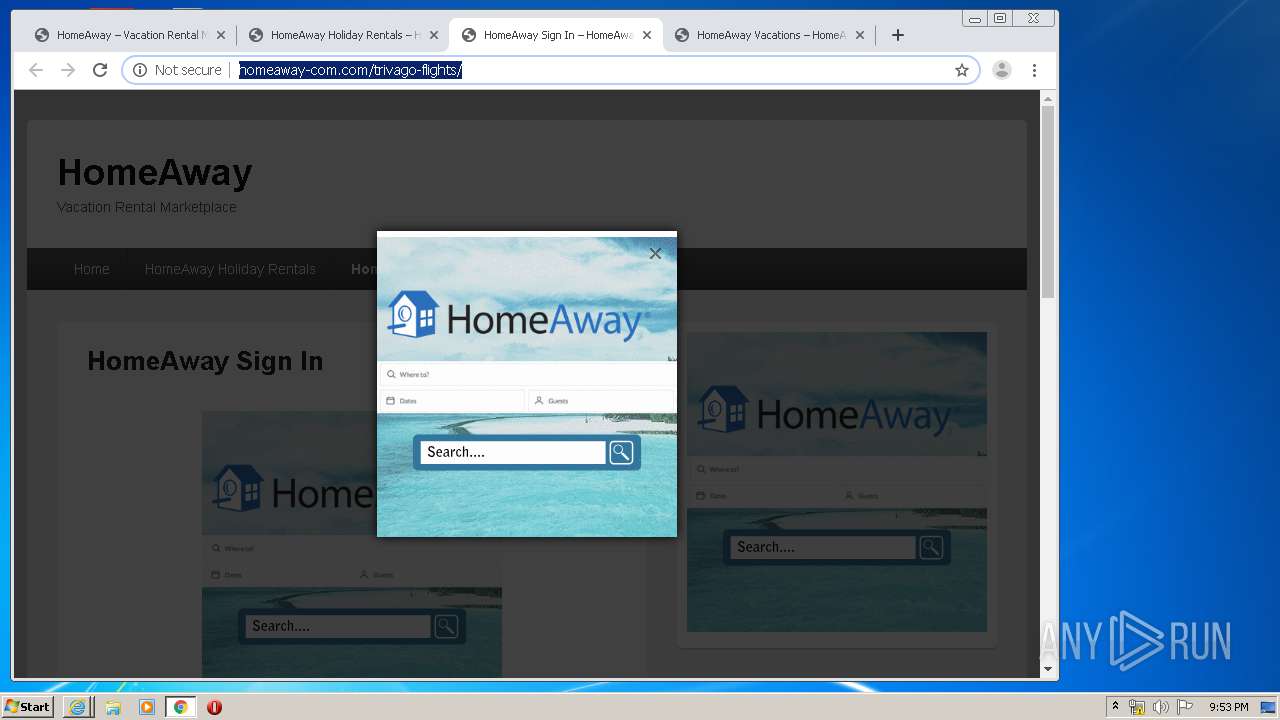
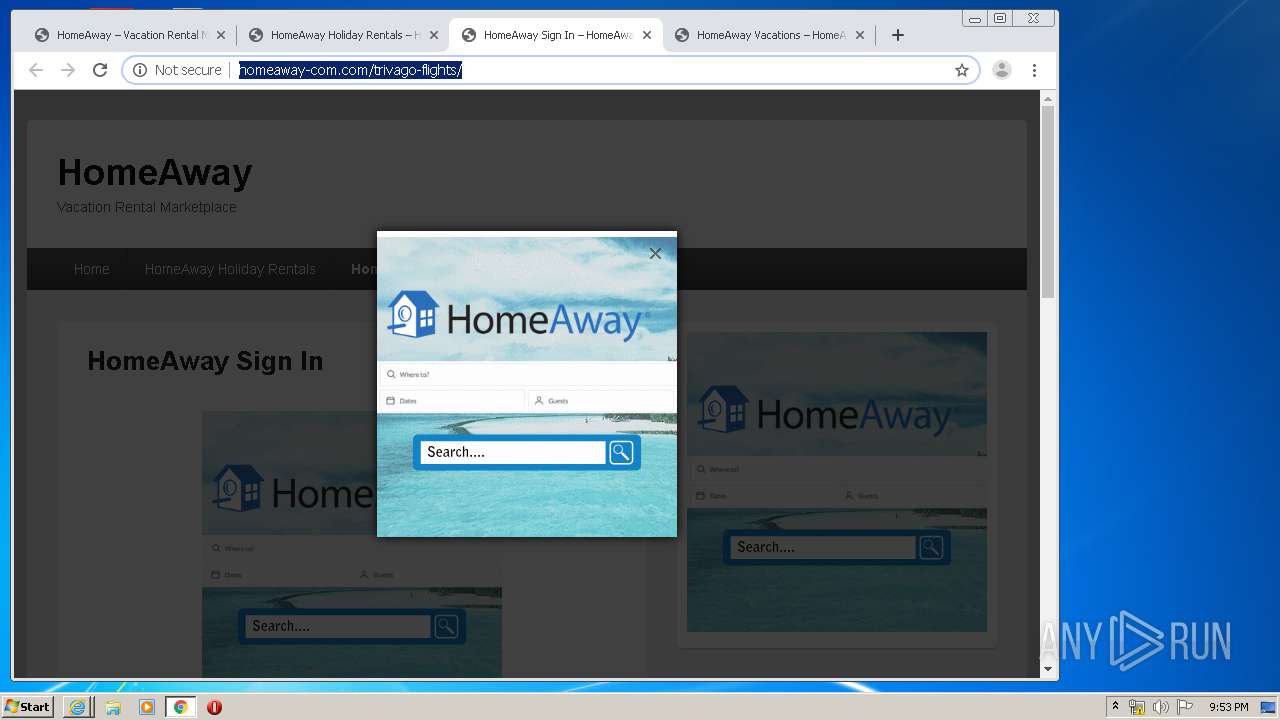
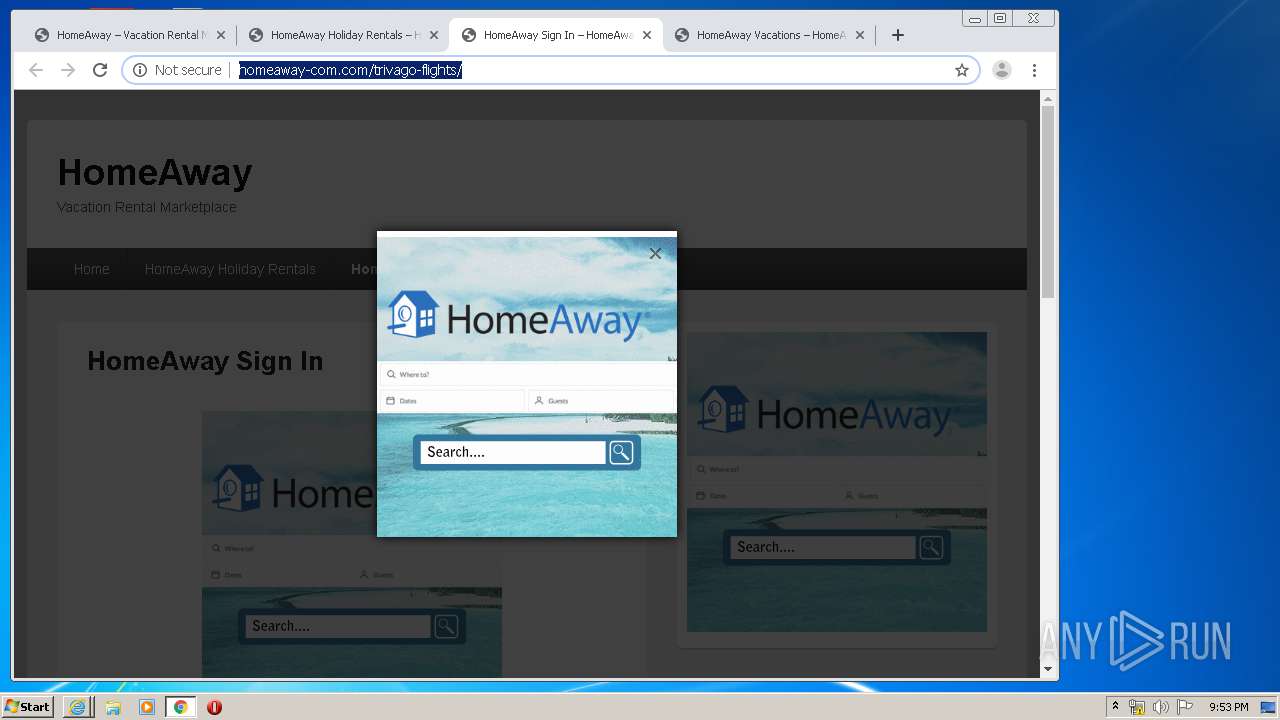
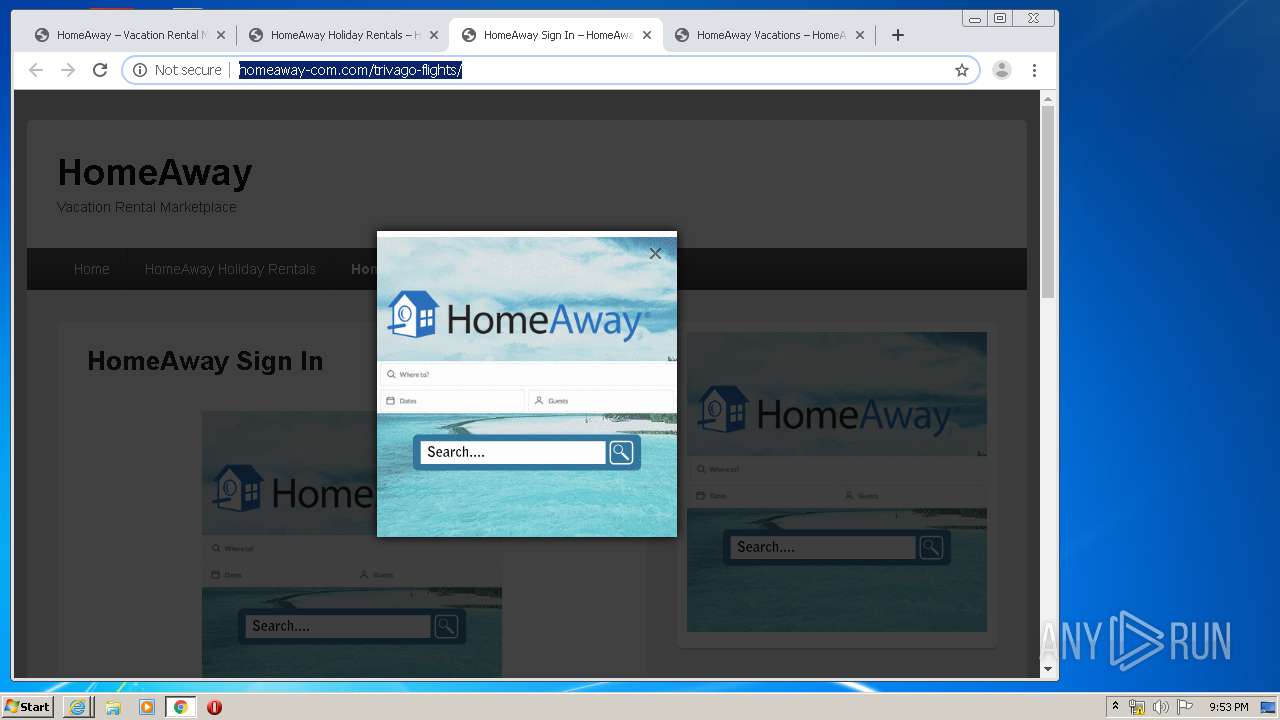
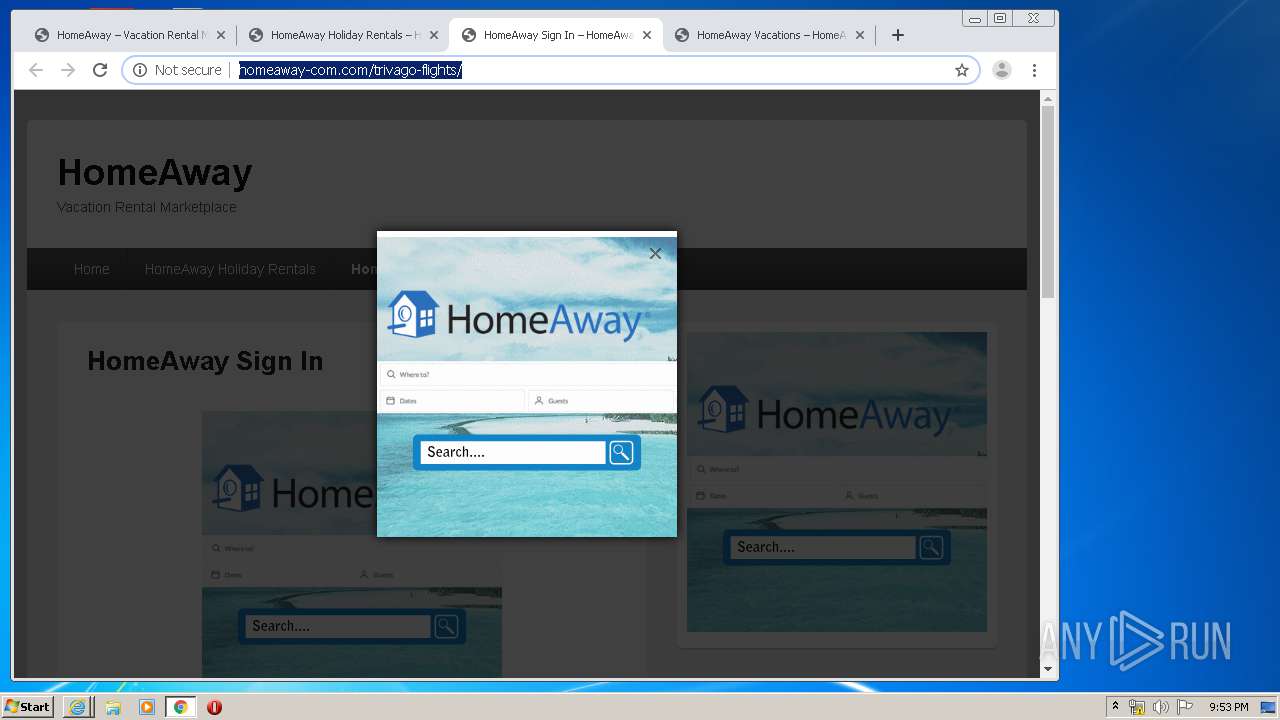
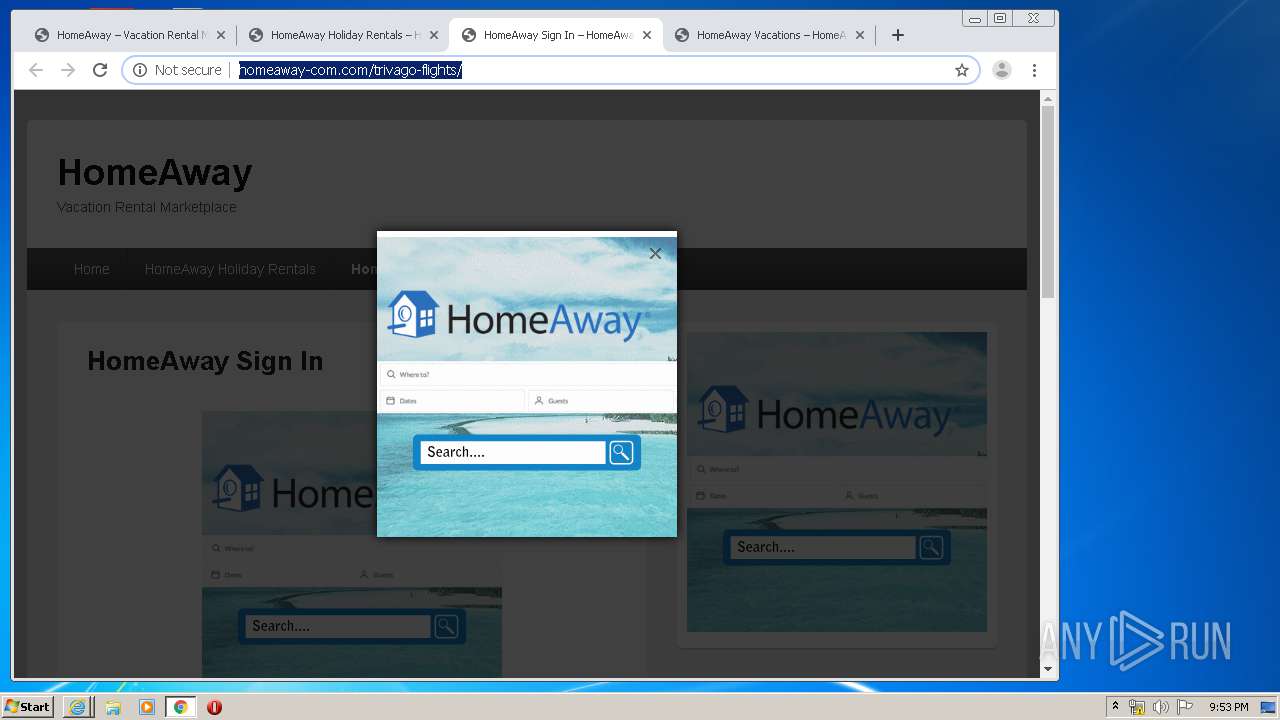
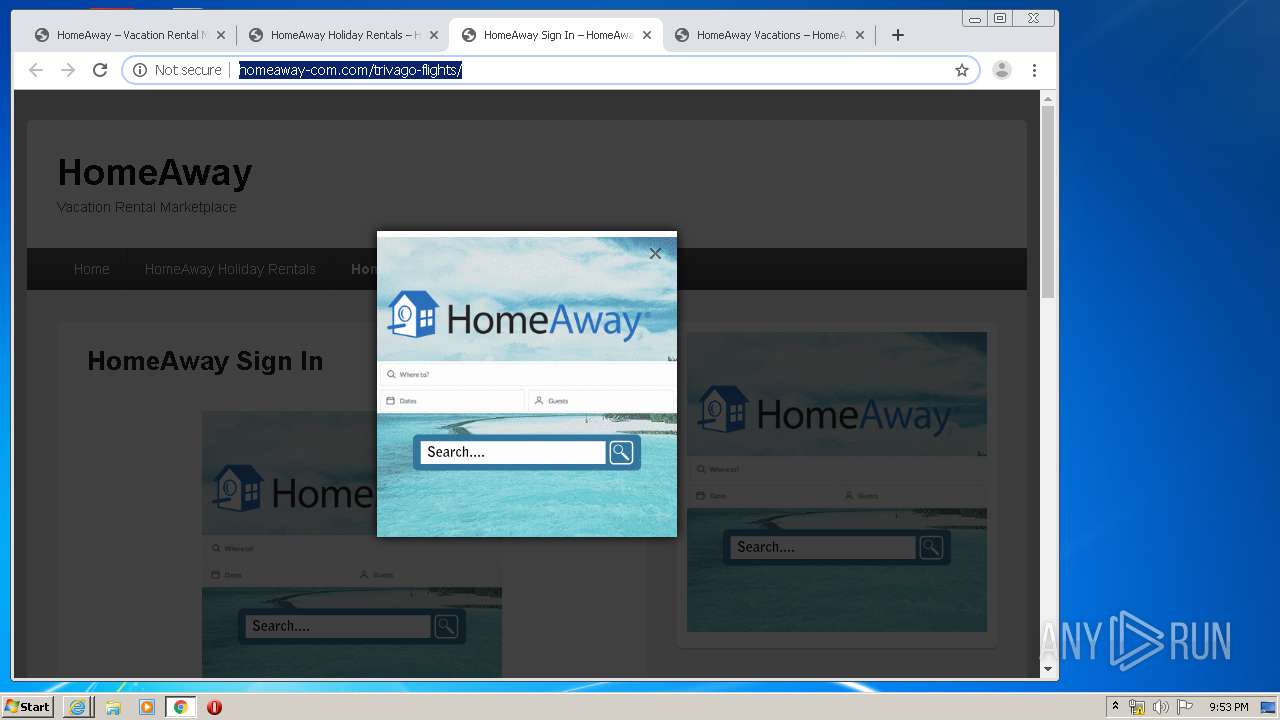
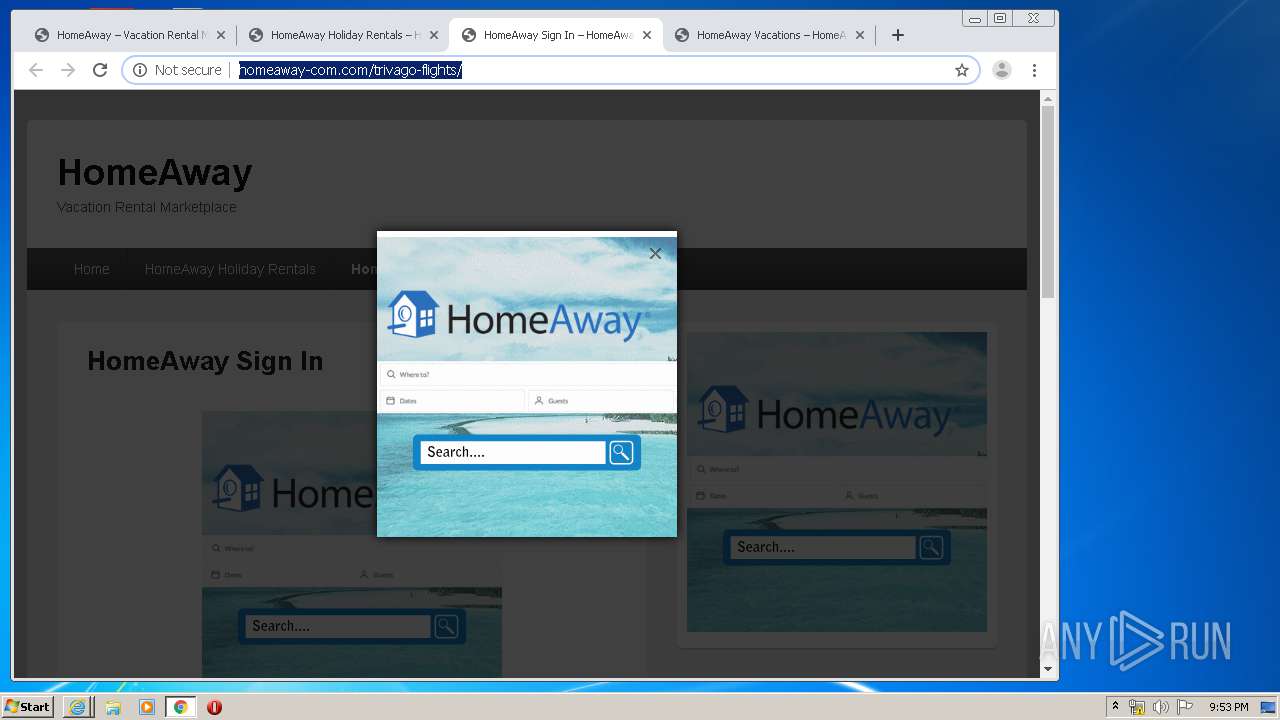
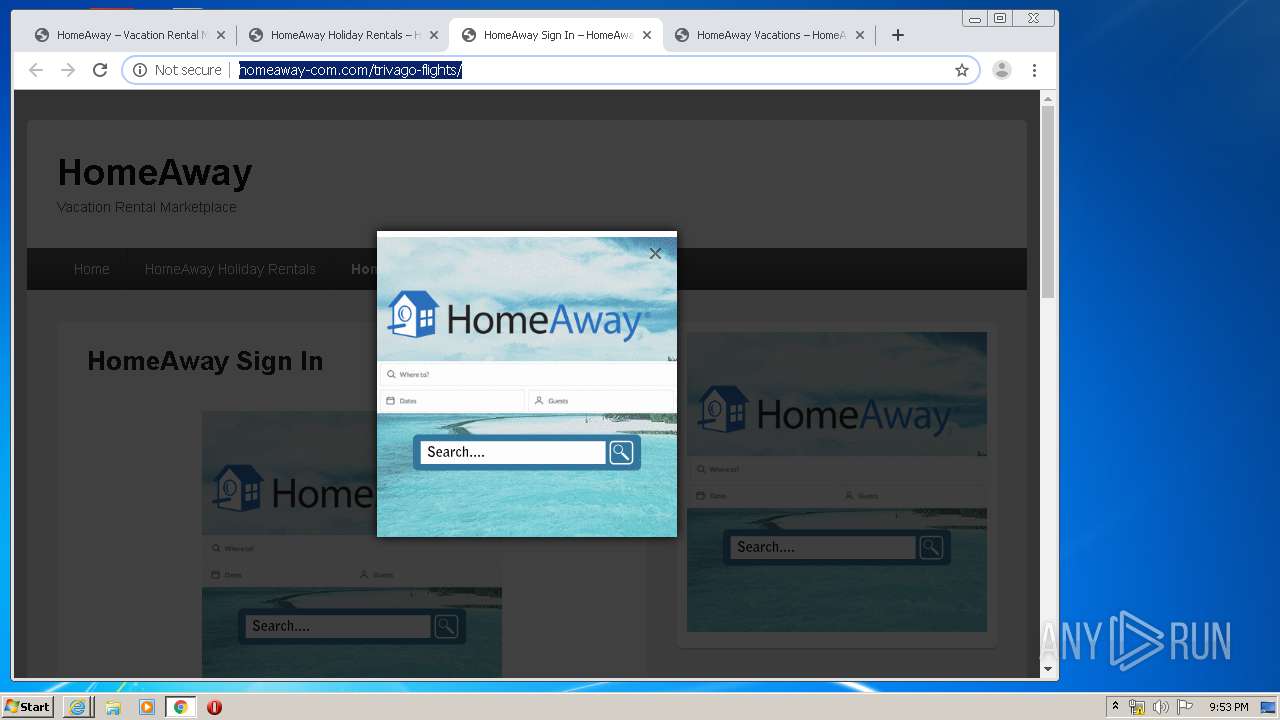
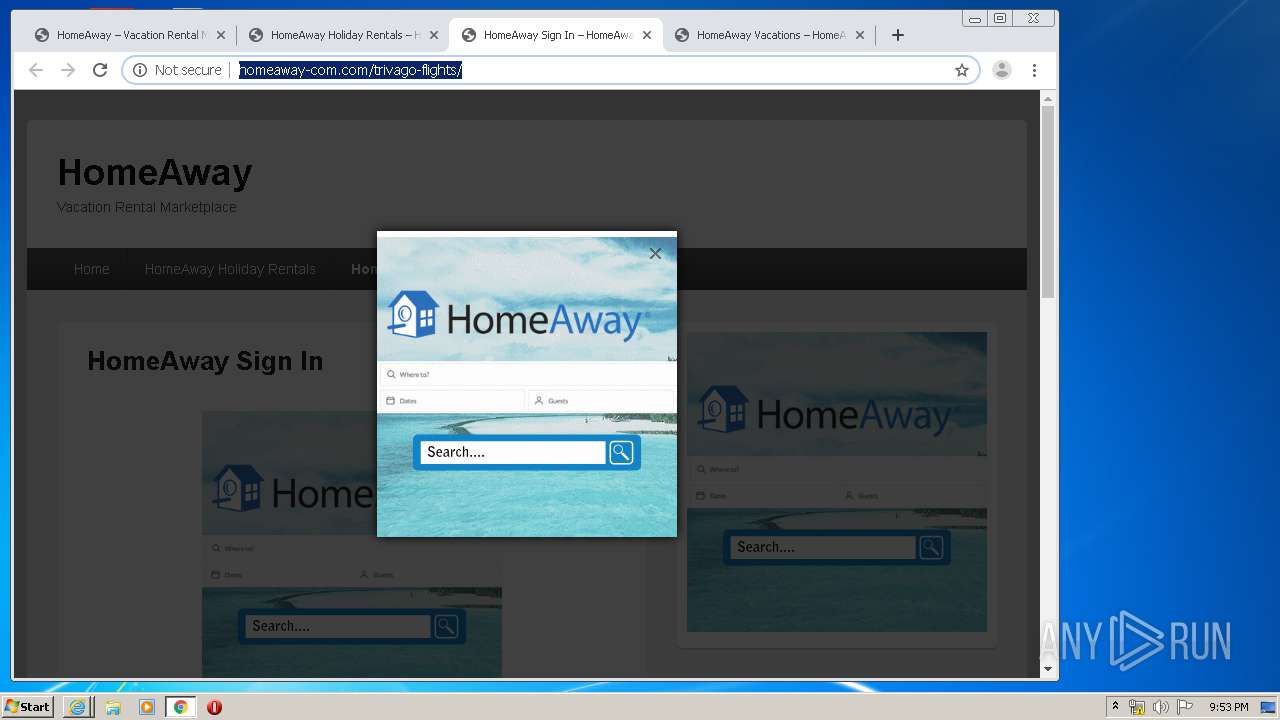
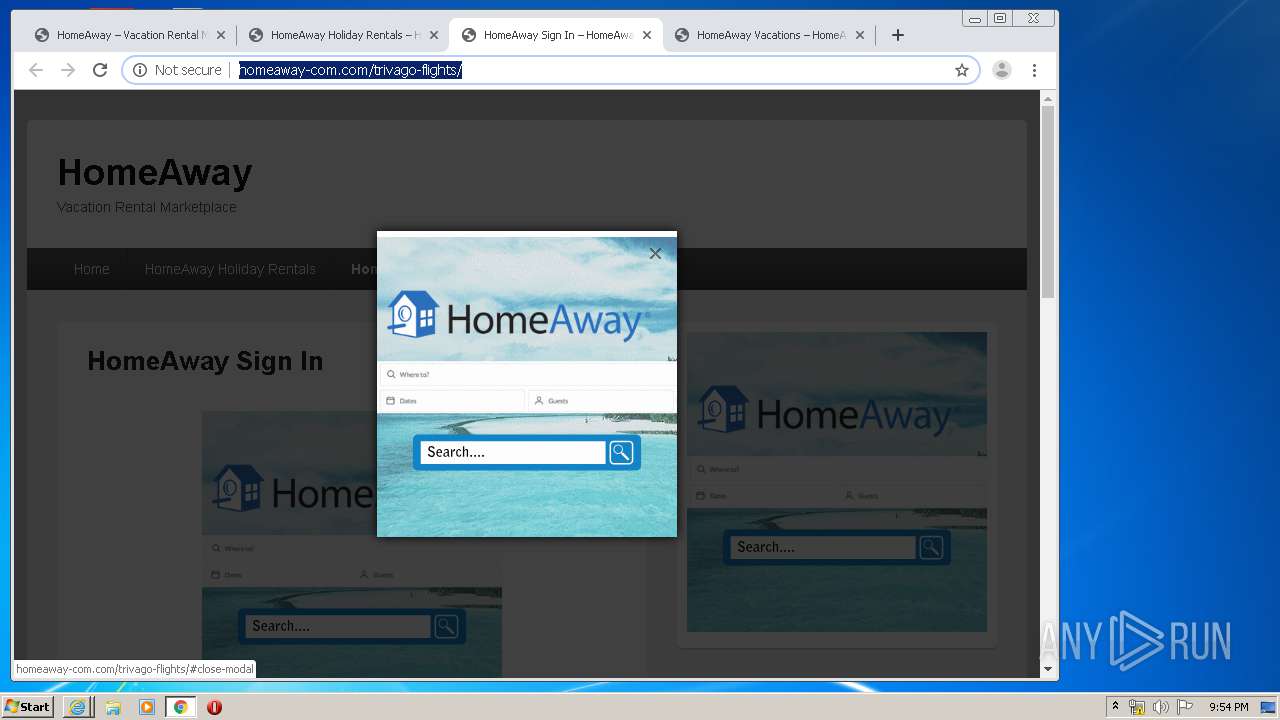
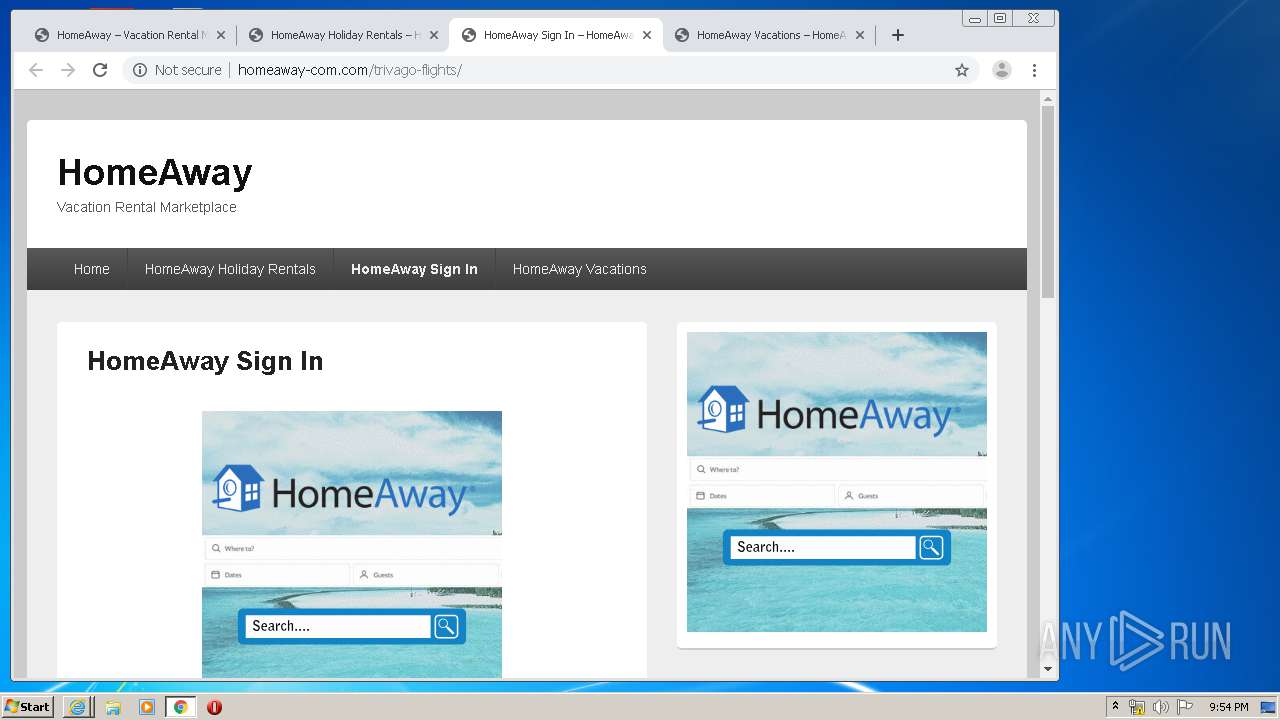
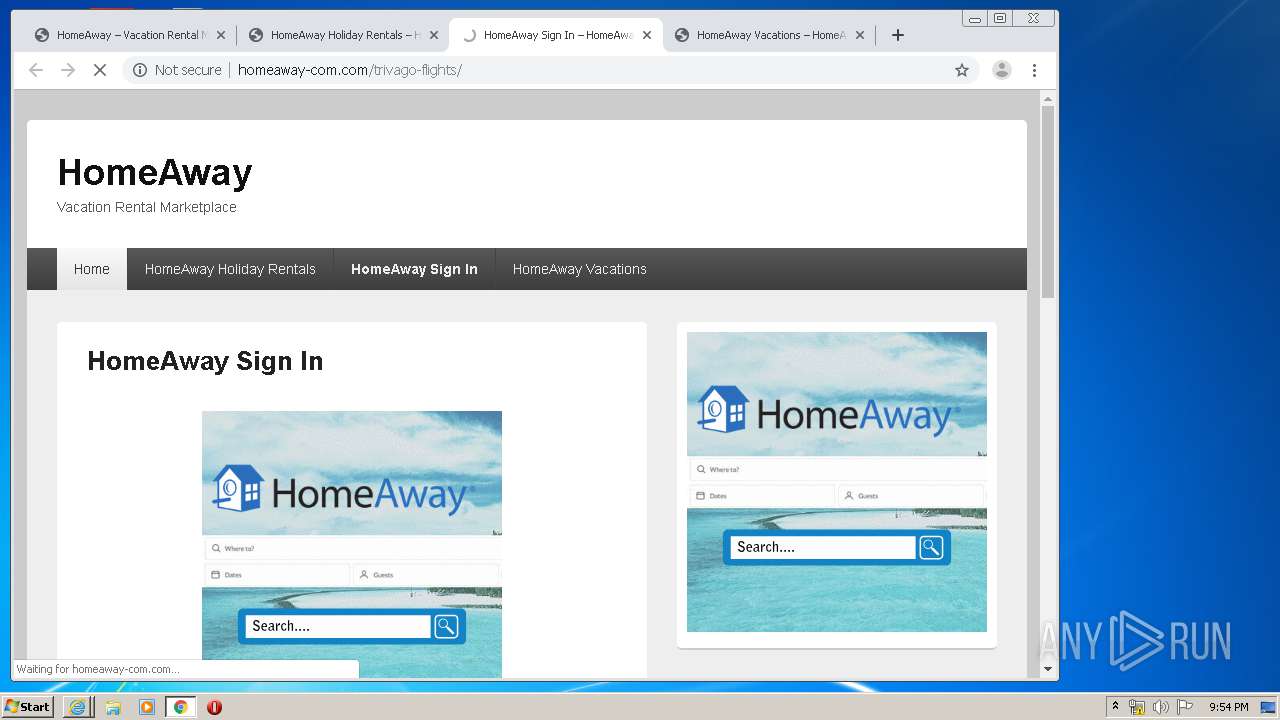
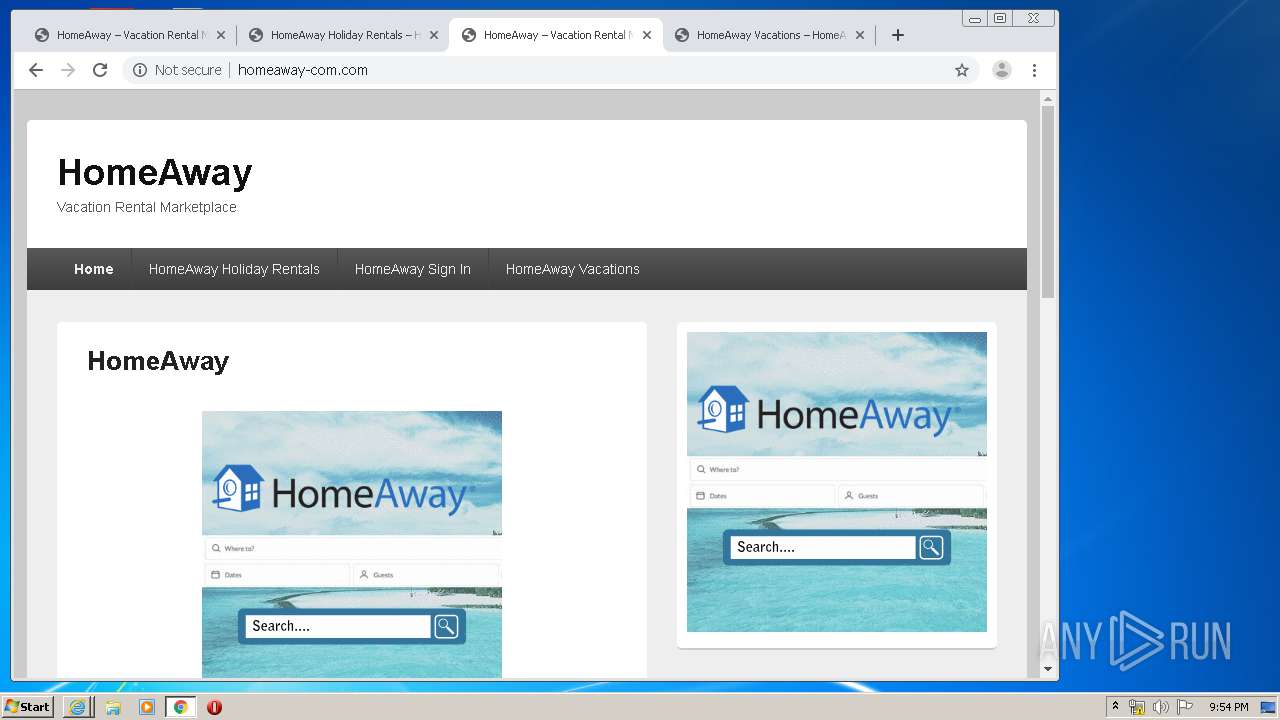
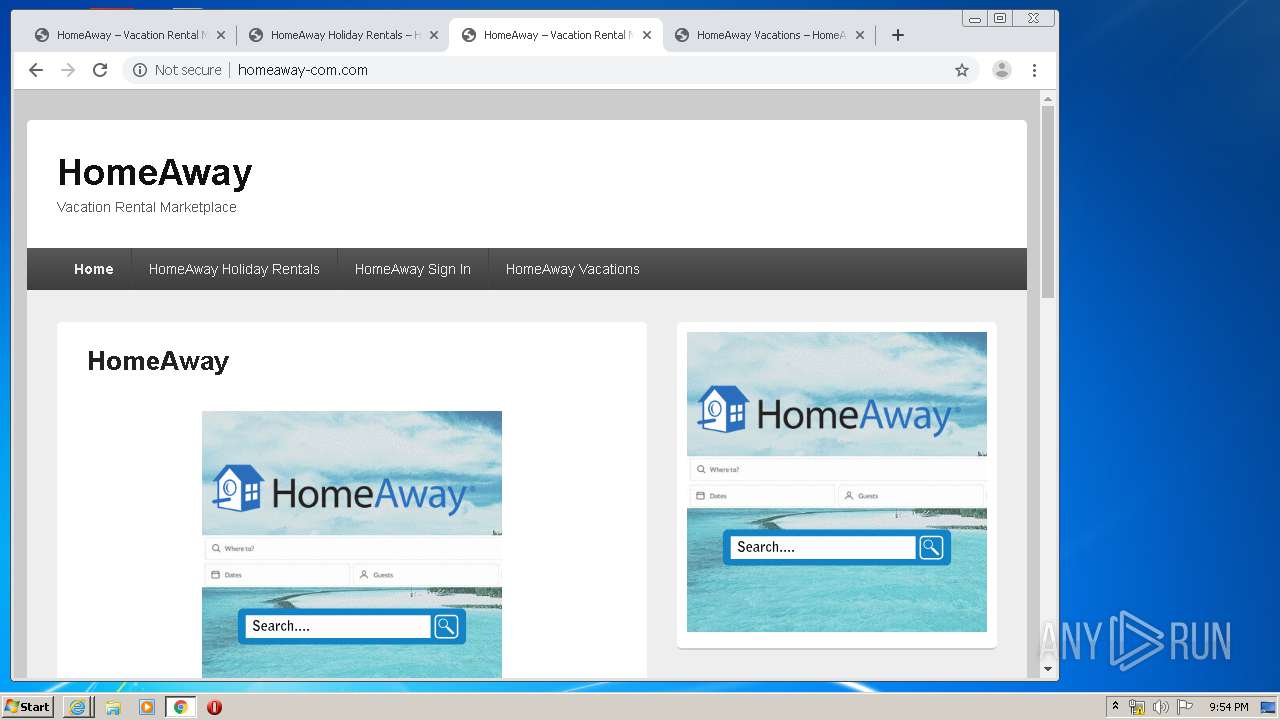
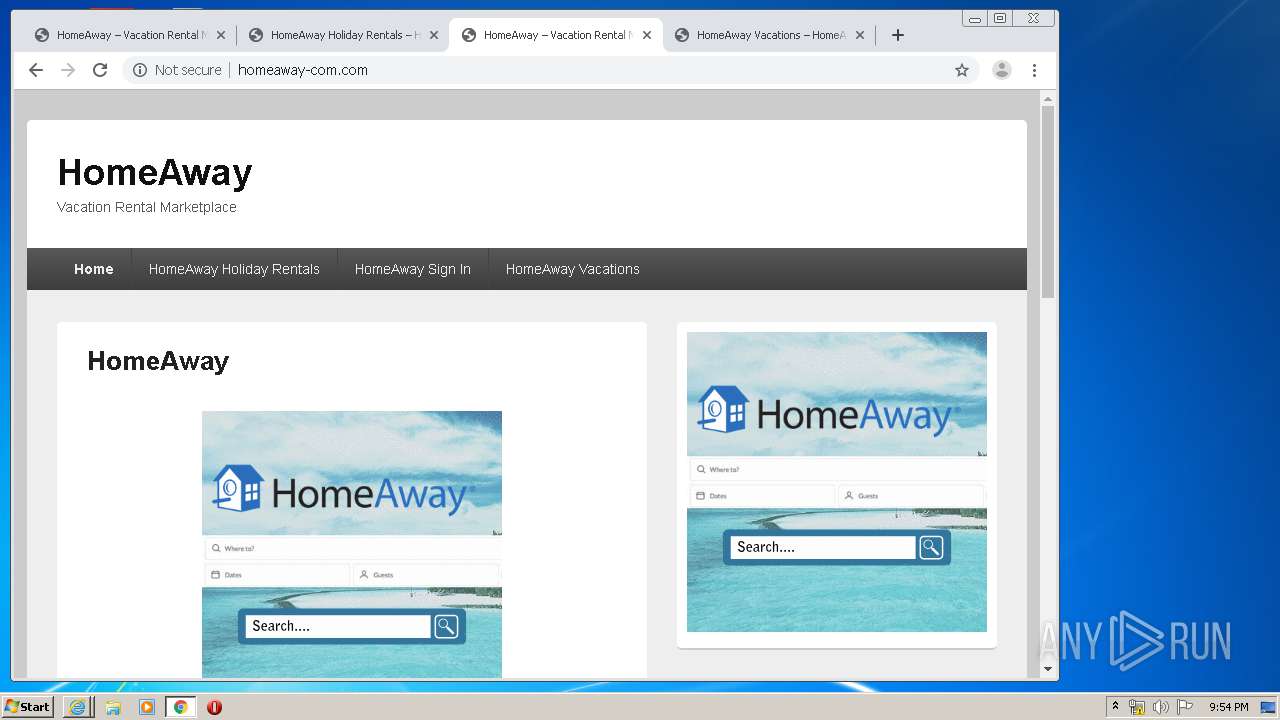
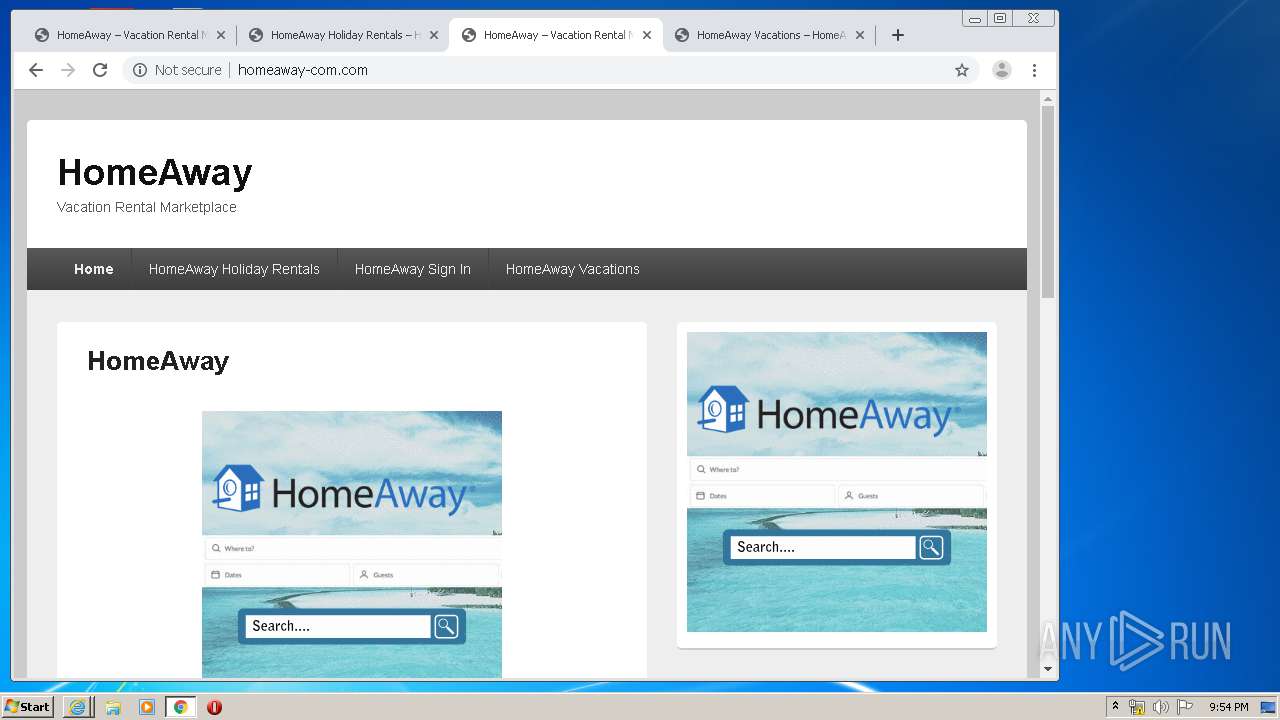
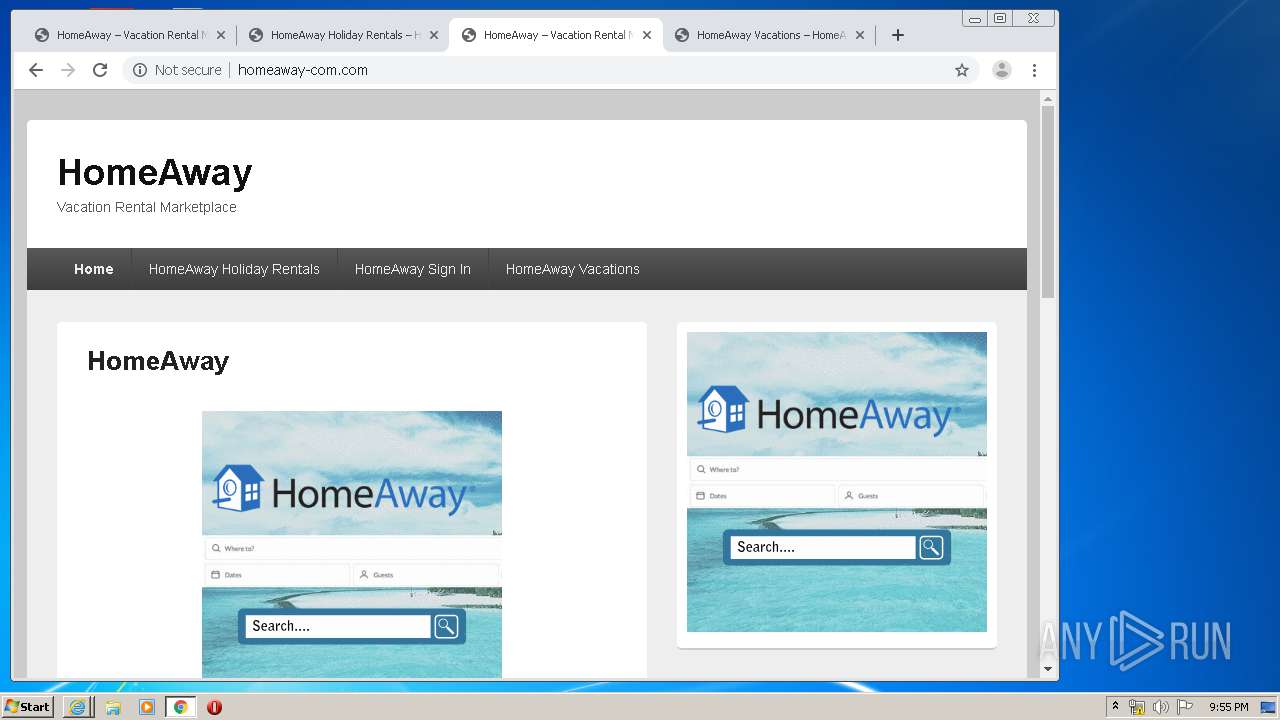
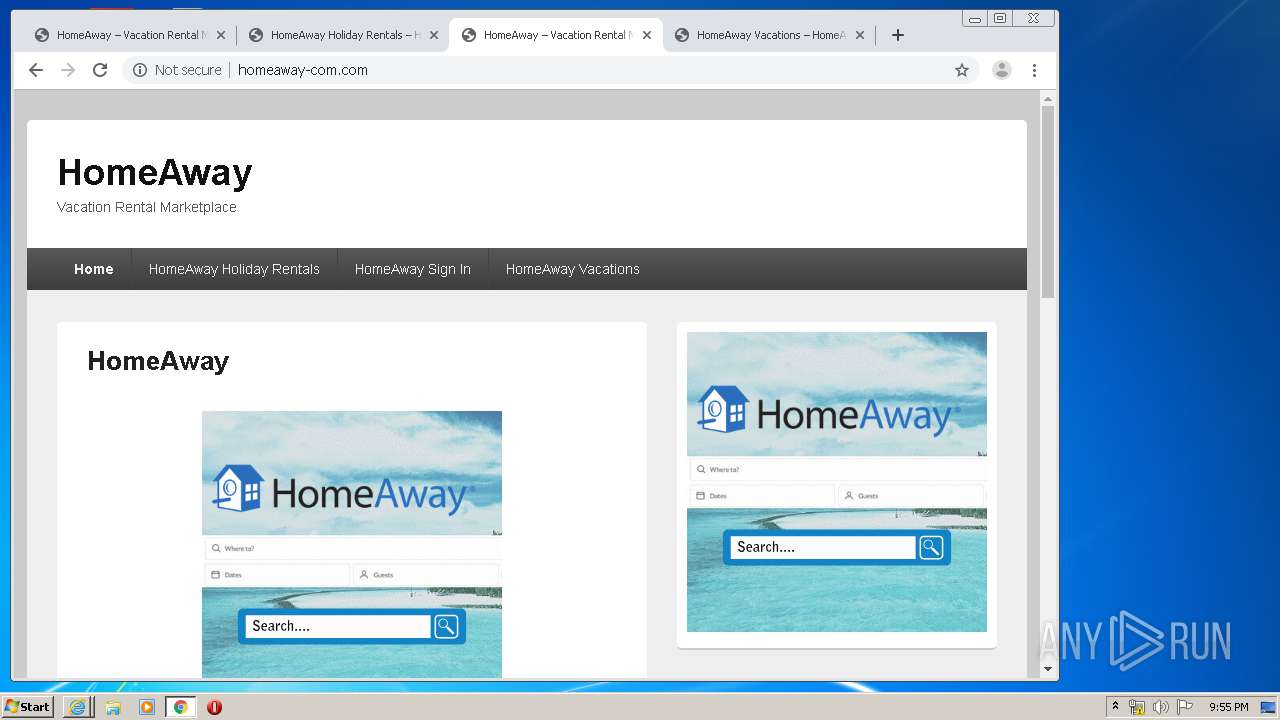
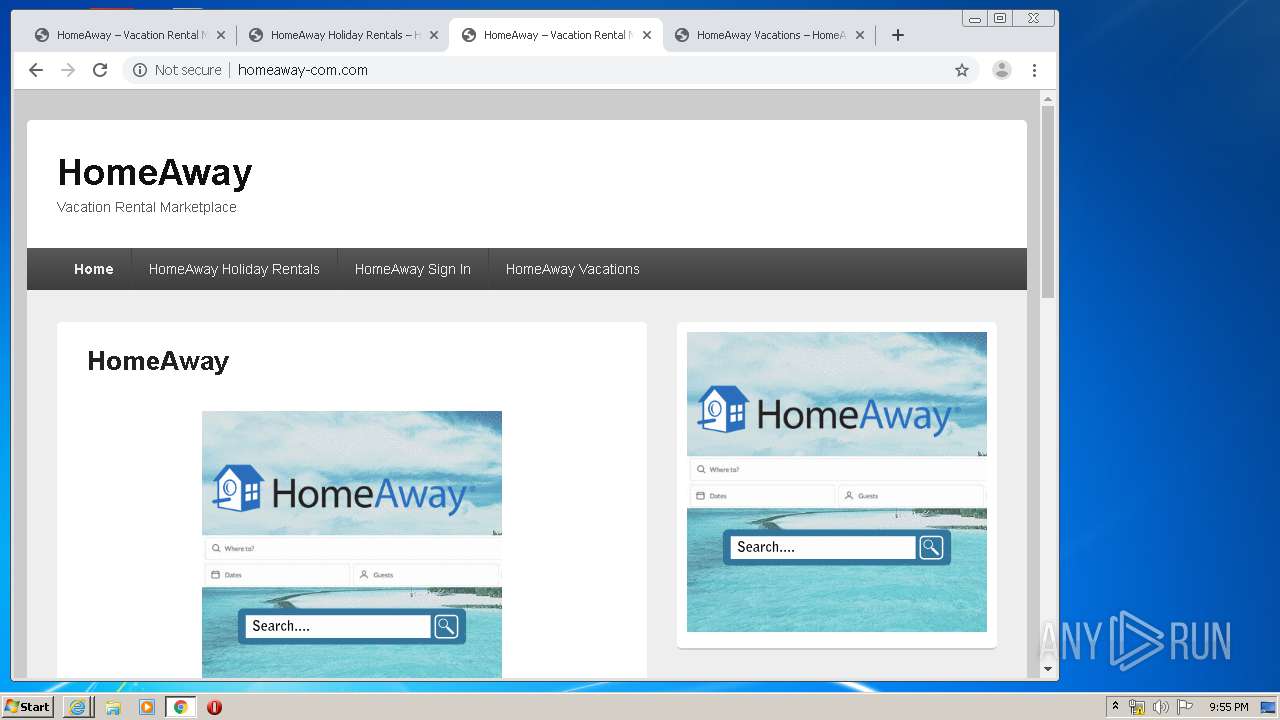
| Verdict: | Malicious activity |
| Analysis date: | February 21, 2020, 21:50:13 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | text/html |
| File info: | HTML document, ASCII text, with very long lines, with CRLF, LF line terminators |
| MD5: | 48AC6FD0B98D498D576F96C54AFC7F02 |
| SHA1: | A3298249AF2C55C075F552D3FCCD93BAA15F9593 |
| SHA256: | 6425EFA5040BF7CE4ACB4BB5A7AB15D9EAD987F0881C594C76B74F541AB65279 |
| SSDEEP: | 384:hvyiysCo8RKXTGNR58rDslFfk5HzolGkFt5xi9RGrqgSKML:L198OTGNL8rDaizolGkFtbi9RGrq9KML |
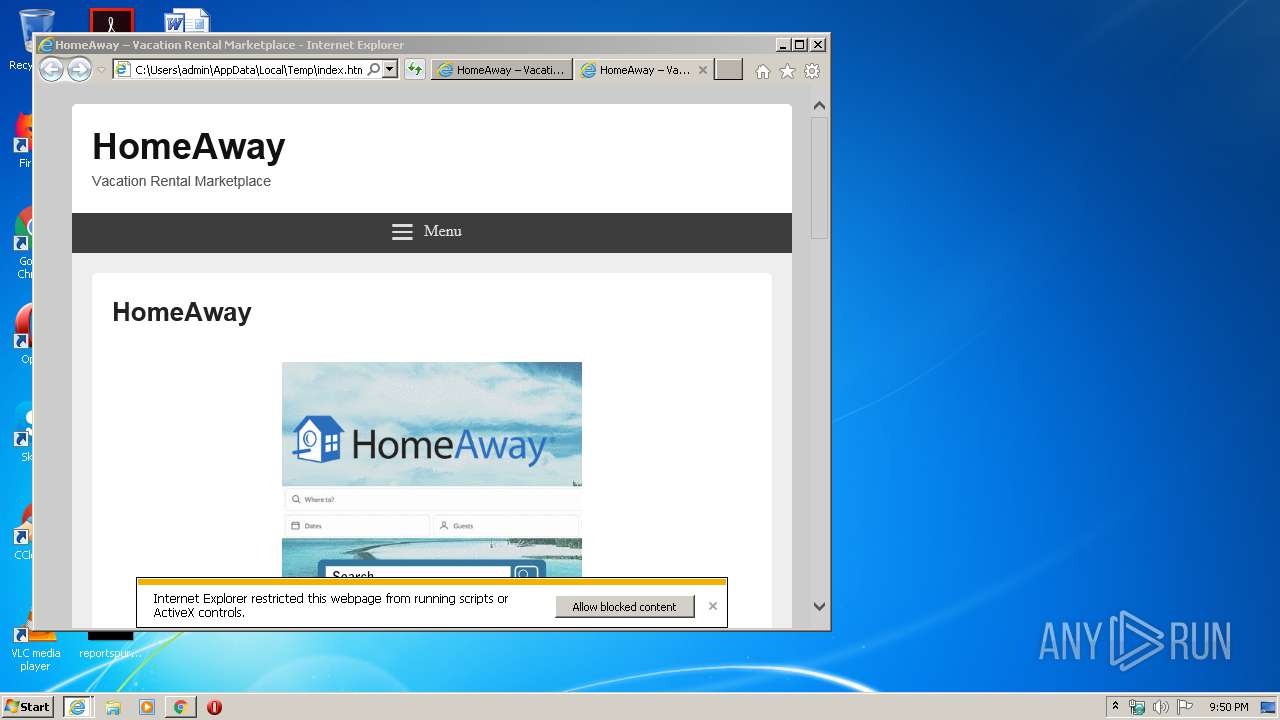
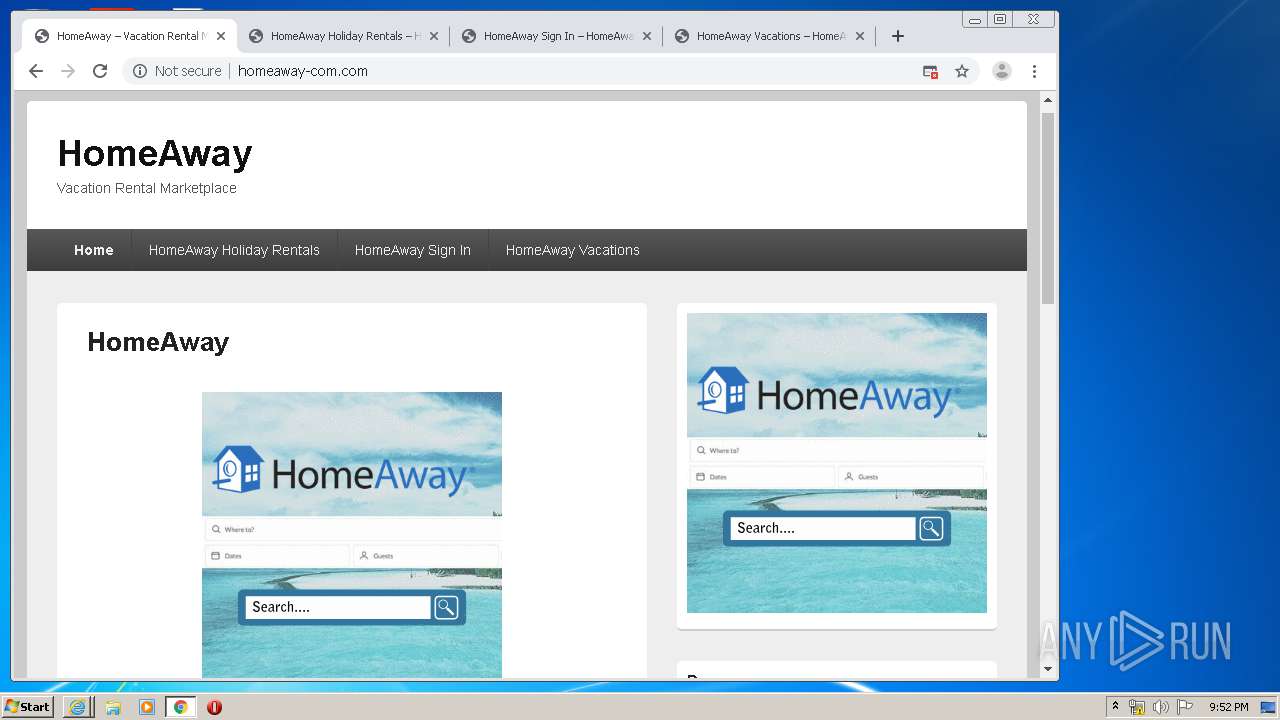
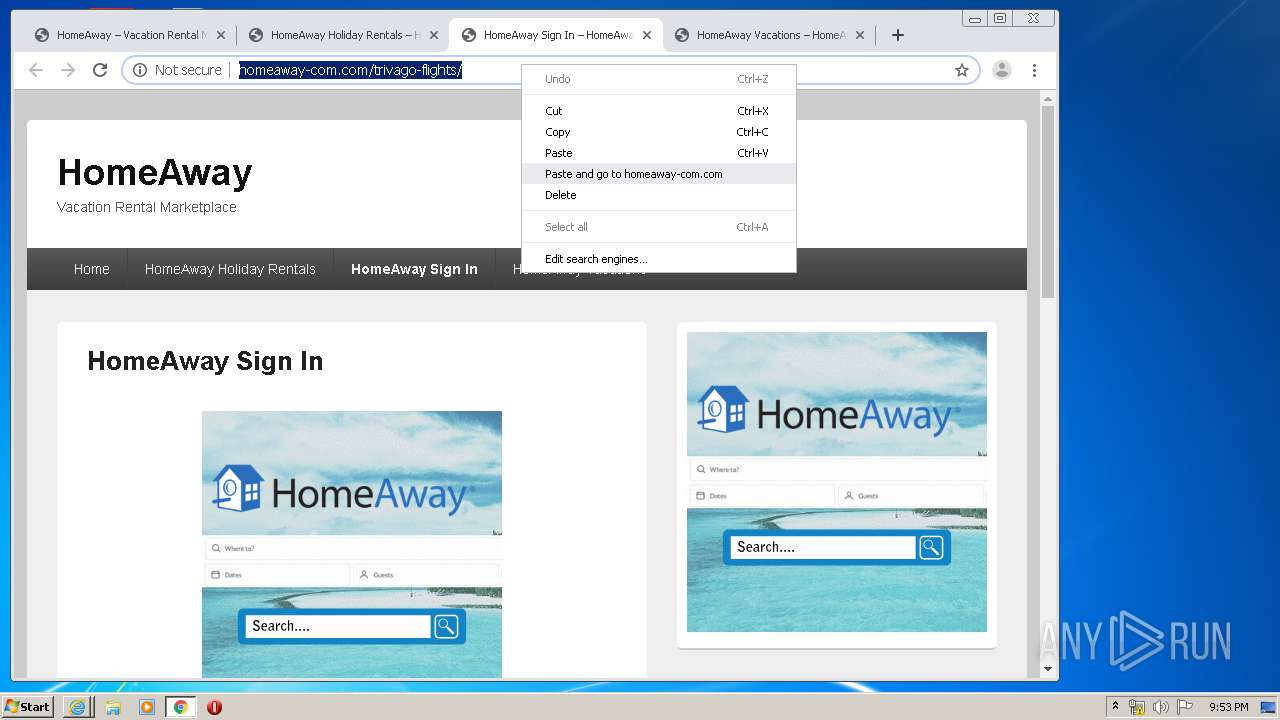
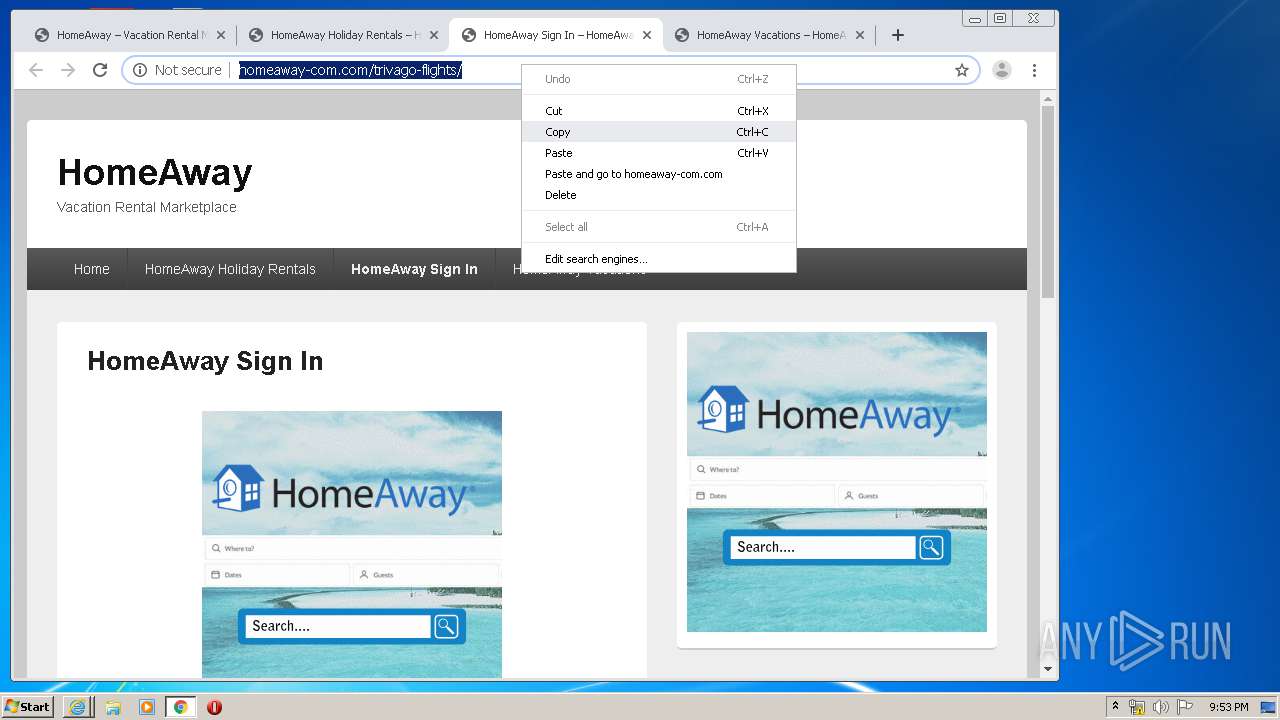
MALICIOUS
No malicious indicators.SUSPICIOUS
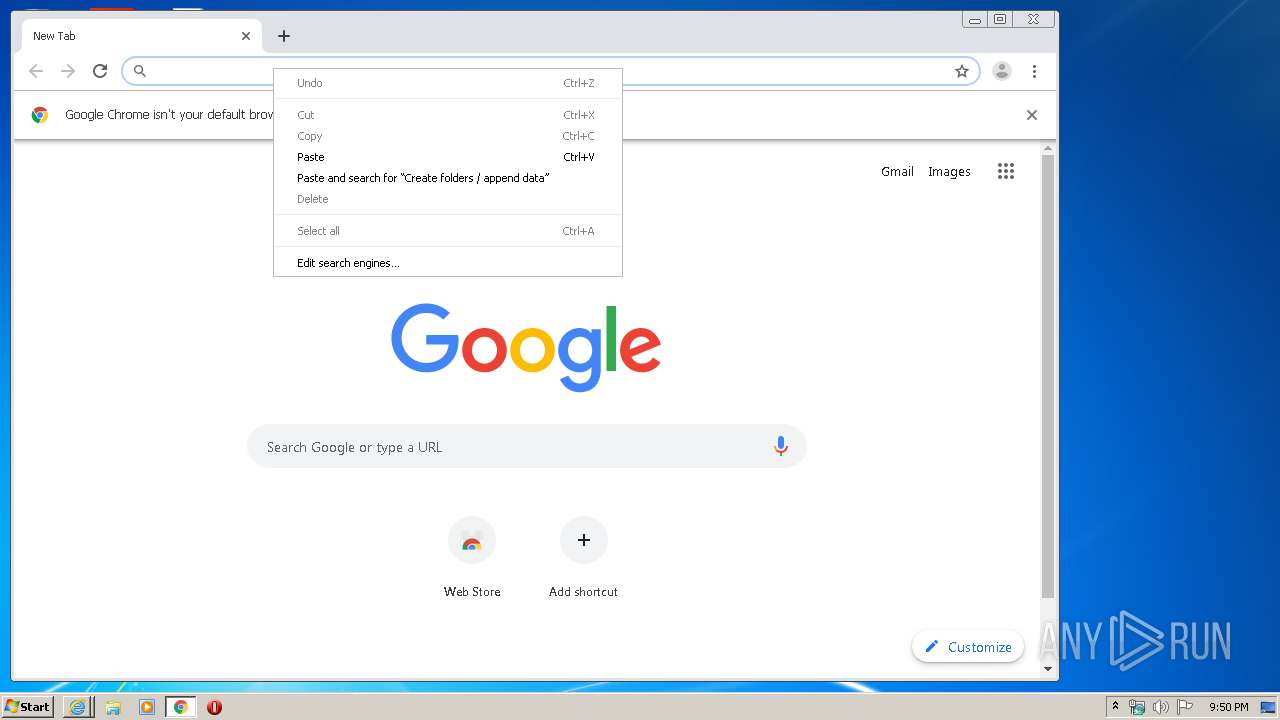
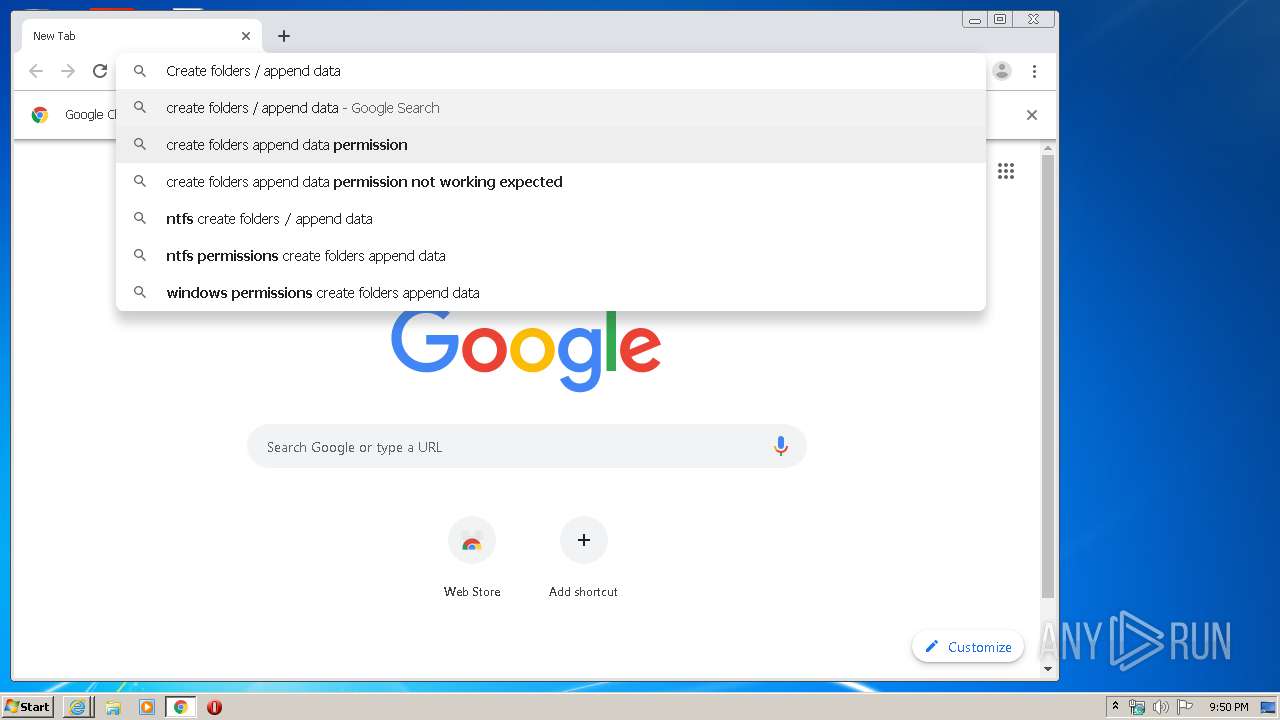
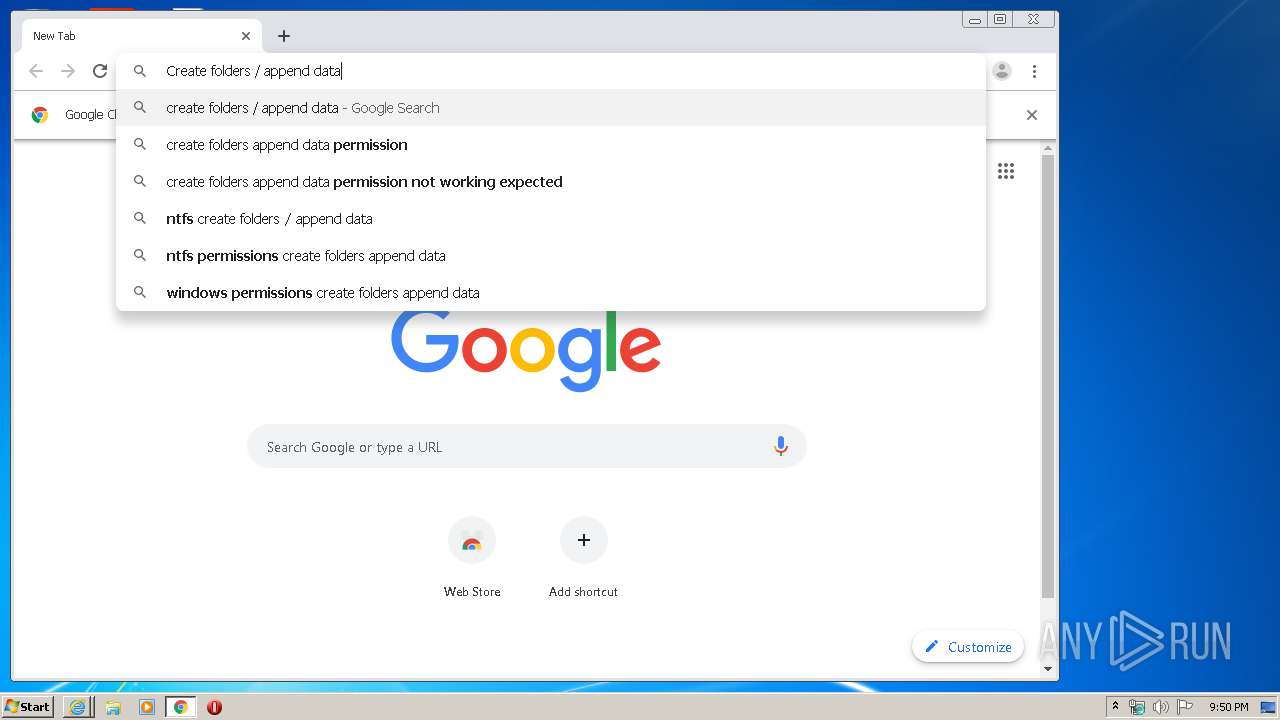
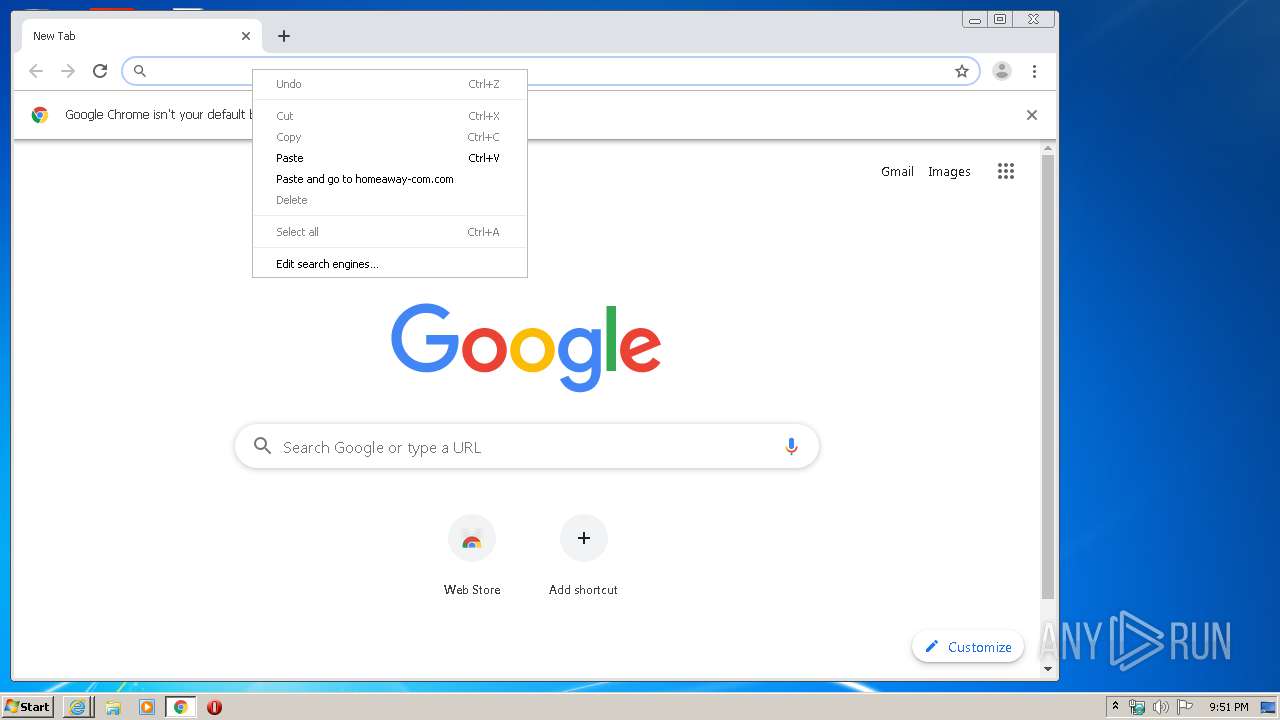
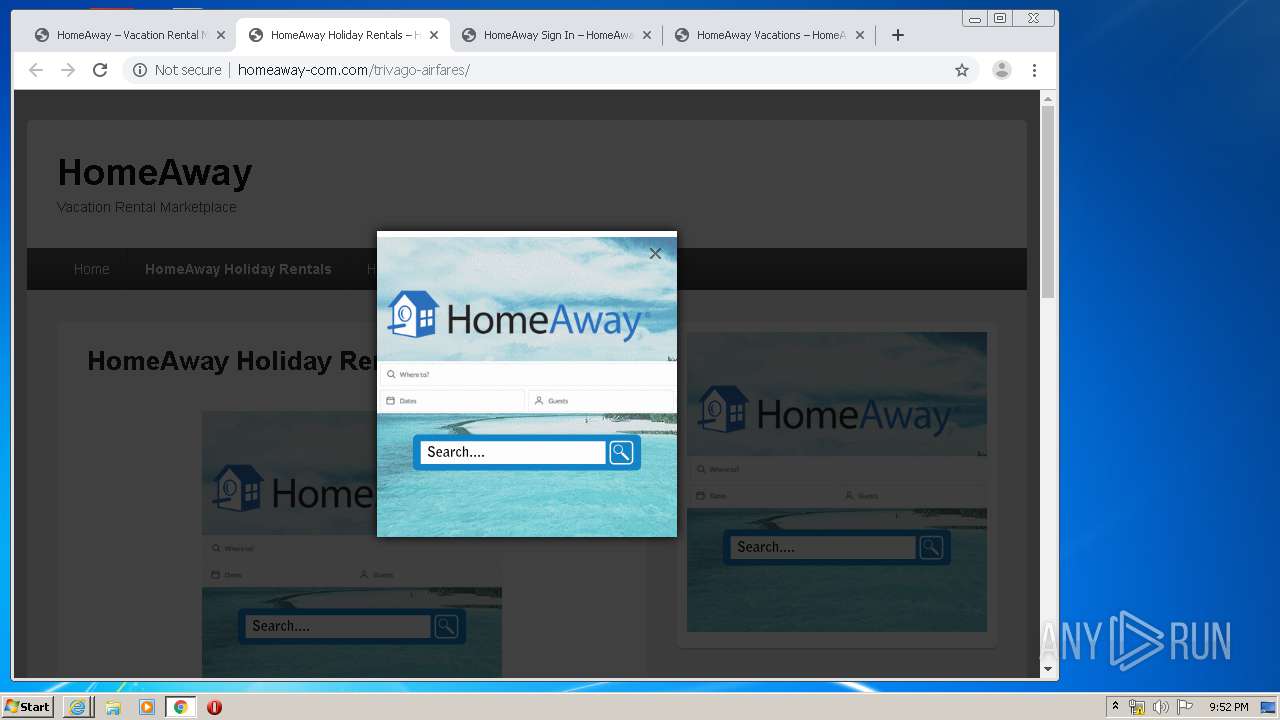
Modifies files in Chrome extension folder
- chrome.exe (PID: 3428)
INFO
Reads Internet Cache Settings
- iexplore.exe (PID: 3952)
- iexplore.exe (PID: 2480)
Changes internet zones settings
- iexplore.exe (PID: 3952)
Application launched itself
- iexplore.exe (PID: 3952)
- iexplore.exe (PID: 2944)
- chrome.exe (PID: 2464)
- chrome.exe (PID: 3428)
Manual execution by user
- chrome.exe (PID: 2464)
- chrome.exe (PID: 3428)
Reads the hosts file
- chrome.exe (PID: 2464)
- chrome.exe (PID: 3748)
- chrome.exe (PID: 3428)
- chrome.exe (PID: 3740)
Reads internet explorer settings
- iexplore.exe (PID: 2944)
- iexplore.exe (PID: 1800)
Reads settings of System Certificates
- chrome.exe (PID: 3740)
- iexplore.exe (PID: 1800)
- iexplore.exe (PID: 2944)
- chrome.exe (PID: 3748)
- iexplore.exe (PID: 3952)
Creates files in the user directory
- iexplore.exe (PID: 3952)
Changes settings of System certificates
- iexplore.exe (PID: 1800)
- iexplore.exe (PID: 2944)
- iexplore.exe (PID: 3952)
Adds / modifies Windows certificates
- iexplore.exe (PID: 2944)
- iexplore.exe (PID: 1800)
- iexplore.exe (PID: 3952)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .htm/html | | | HyperText Markup Language with DOCTYPE (80.6) |
|---|---|---|
| .html | | | HyperText Markup Language (19.3) |
EXIF
HTML
| viewport: | width=device-width, initial-scale=1, minimum-scale=1 |
|---|---|
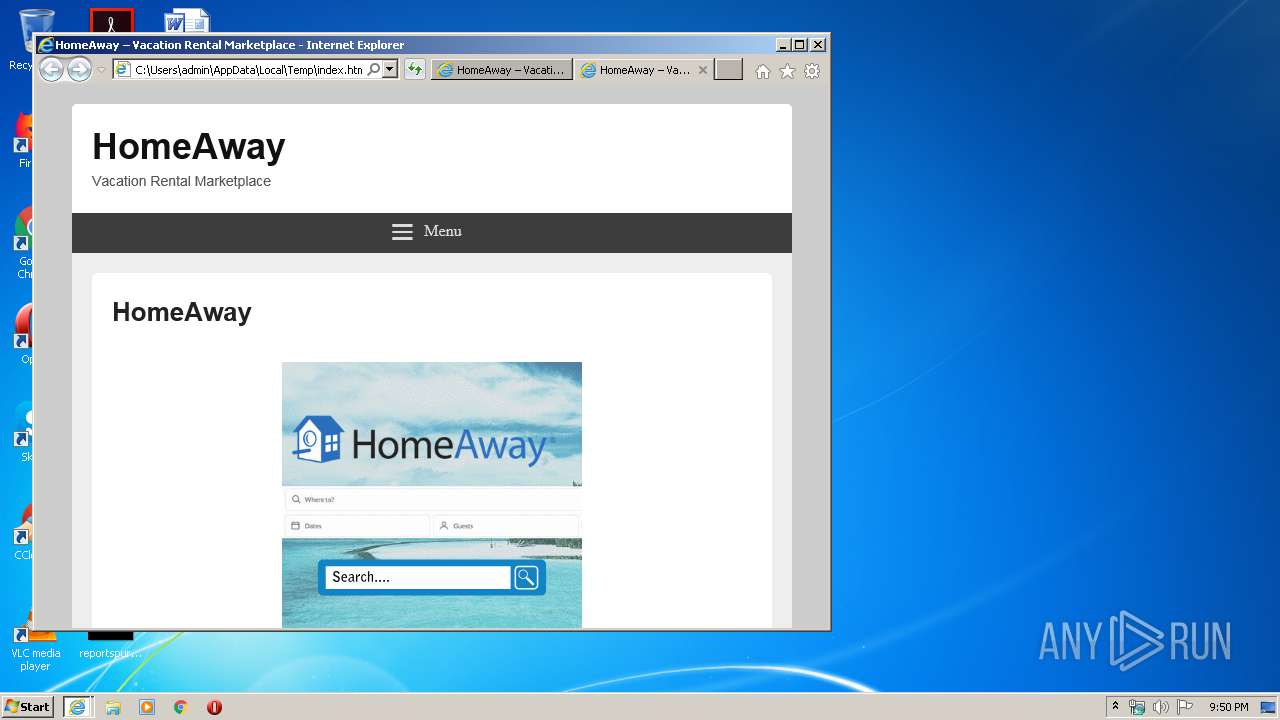
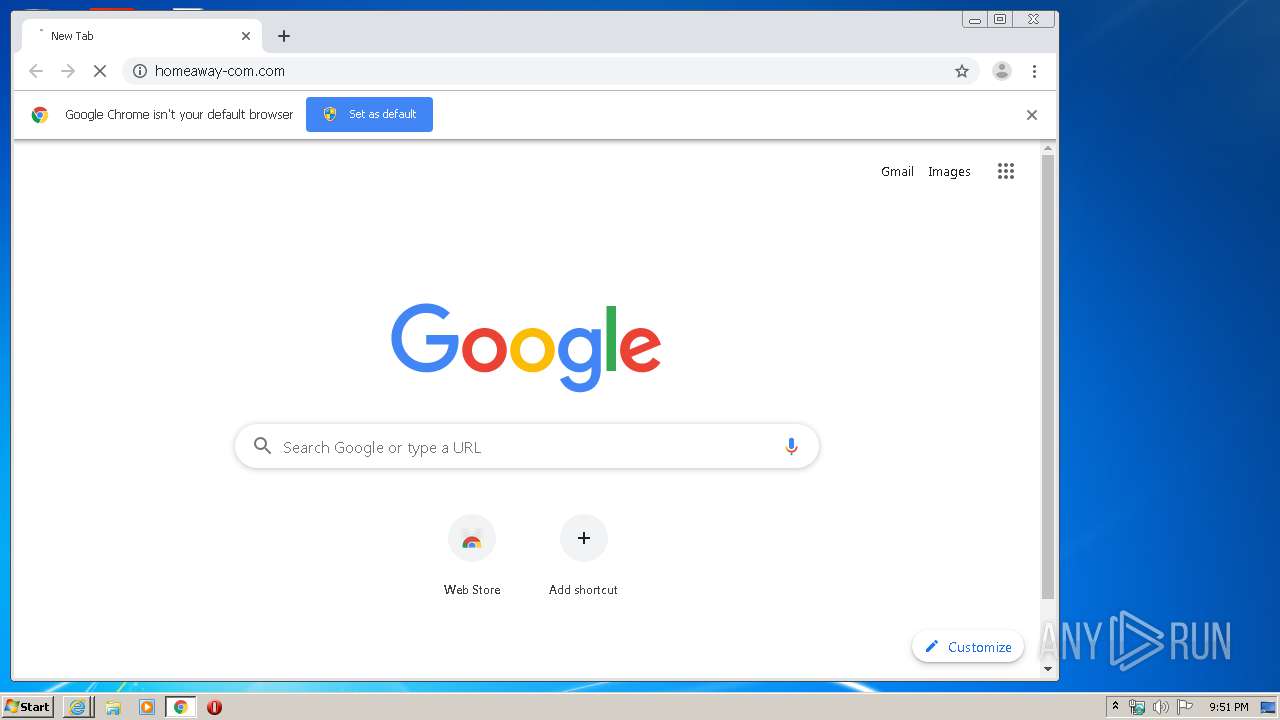
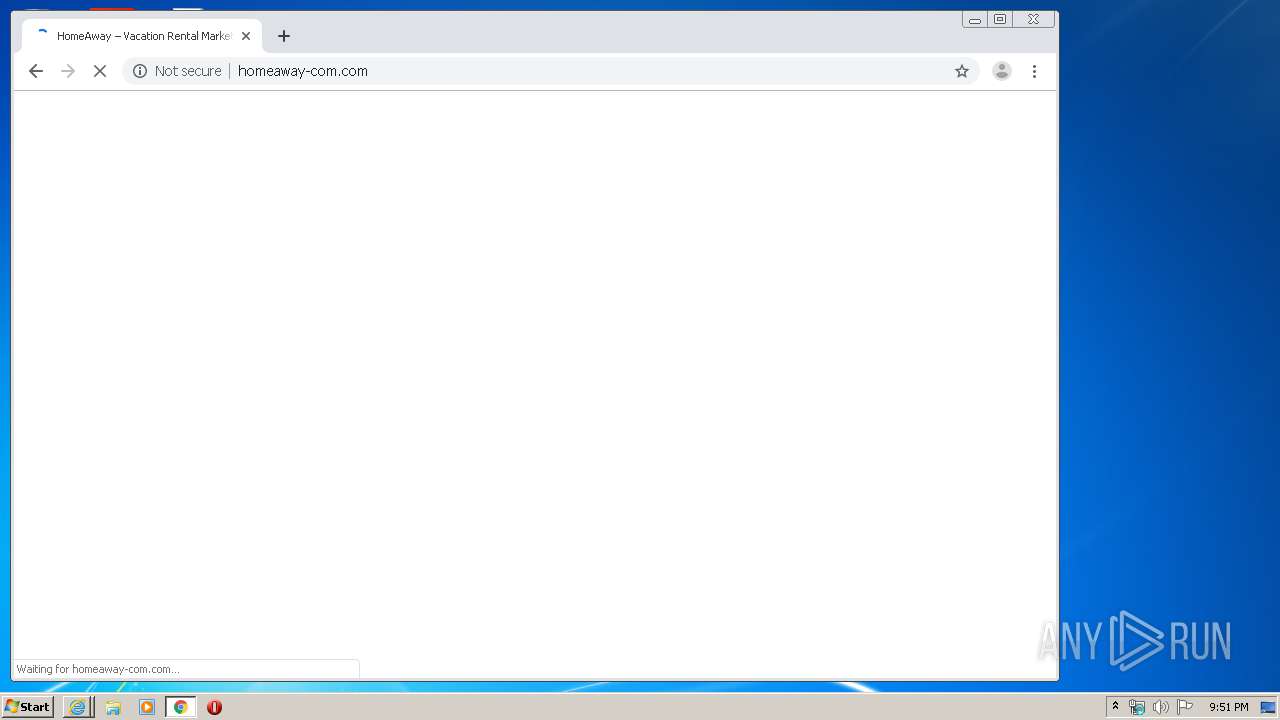
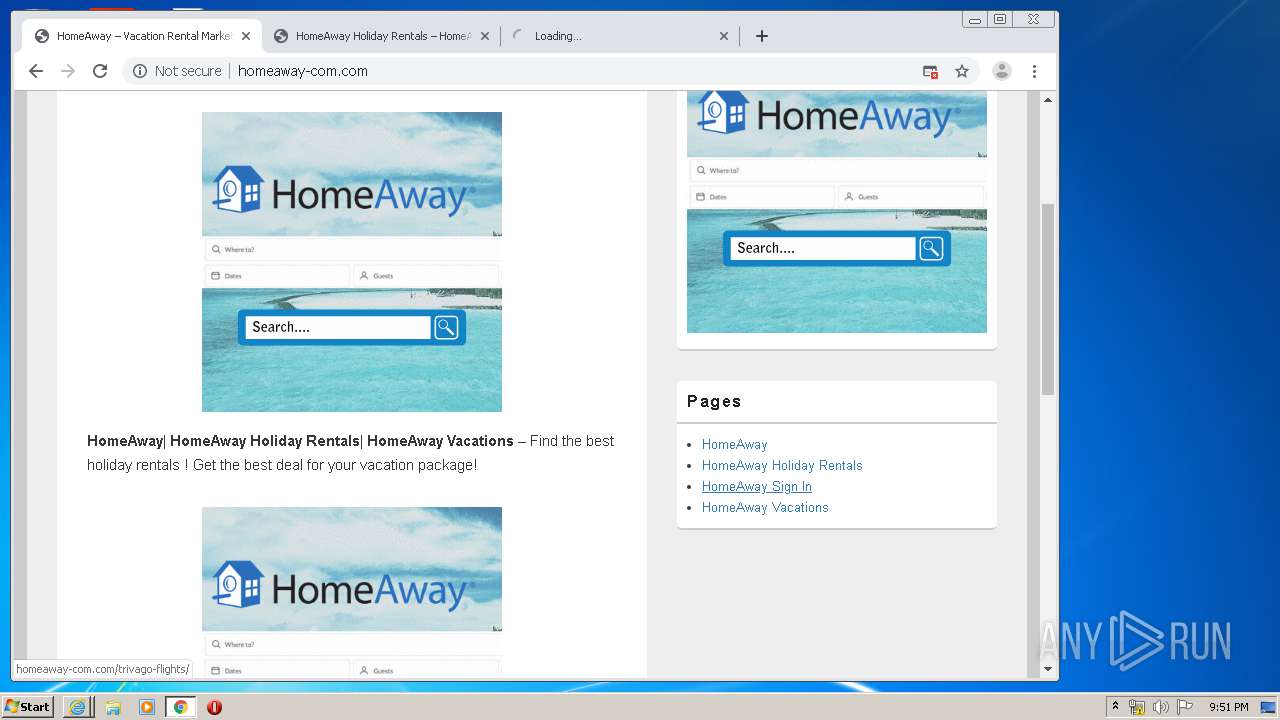
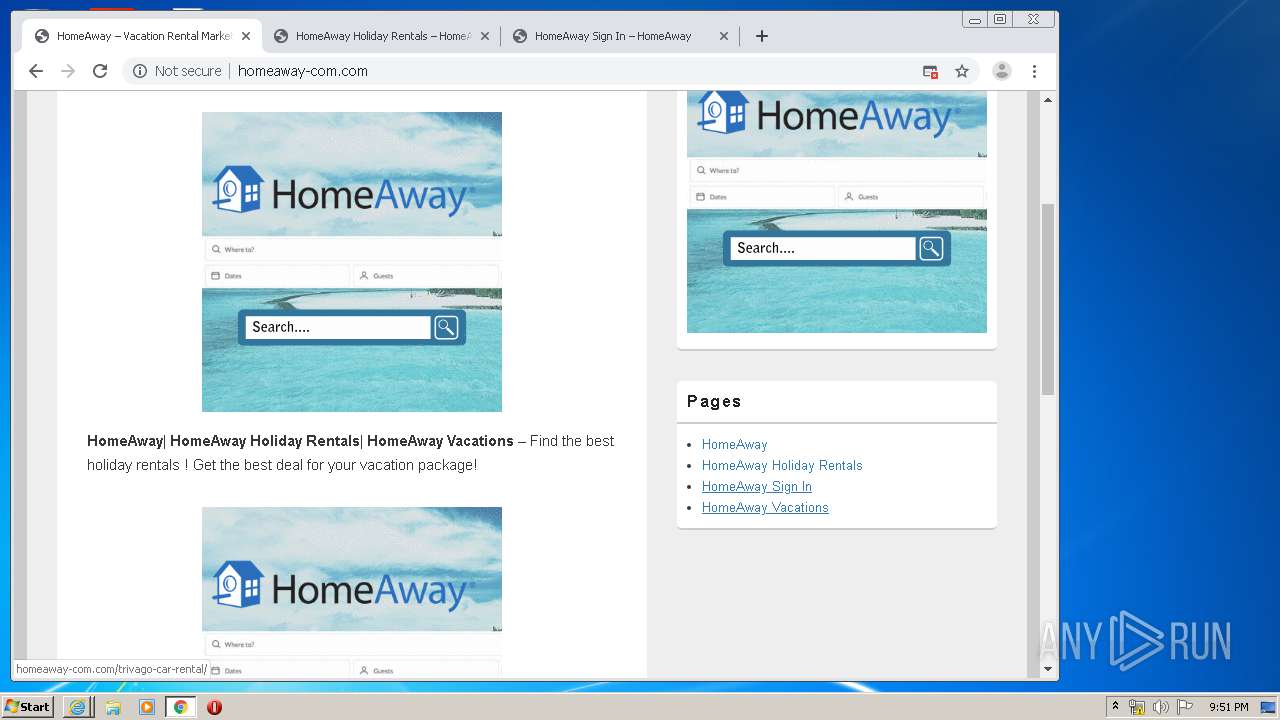
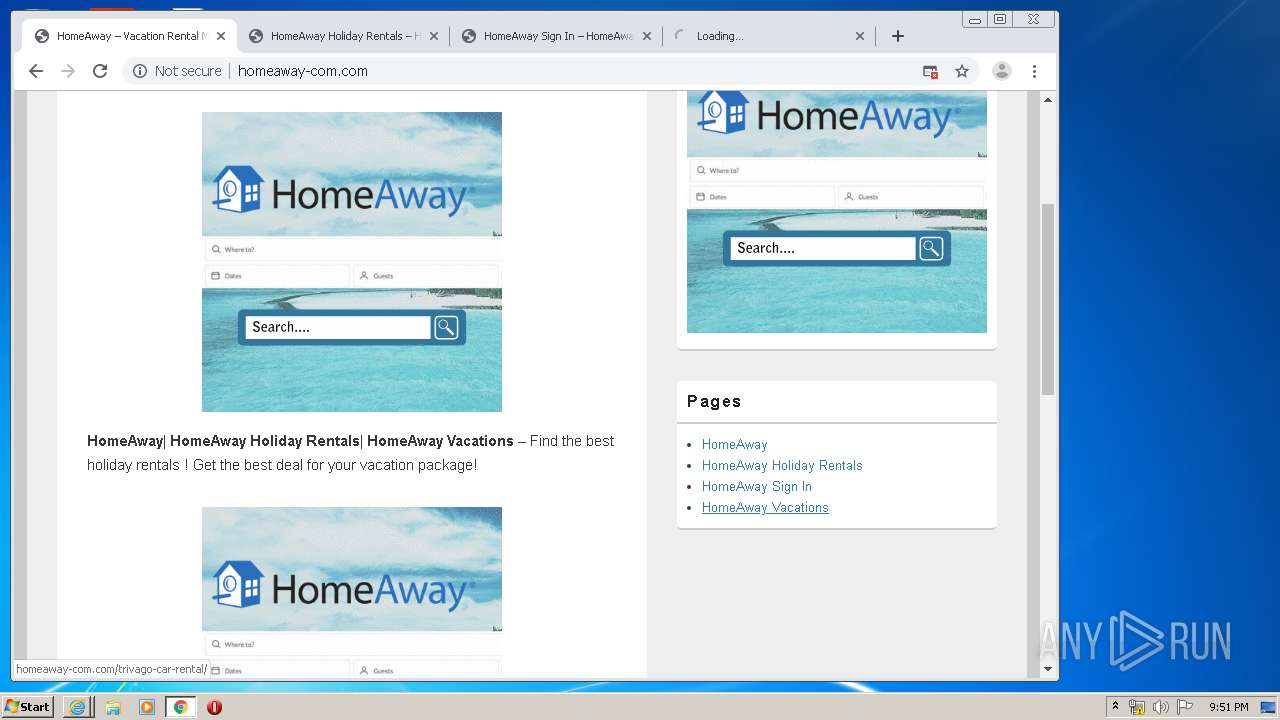
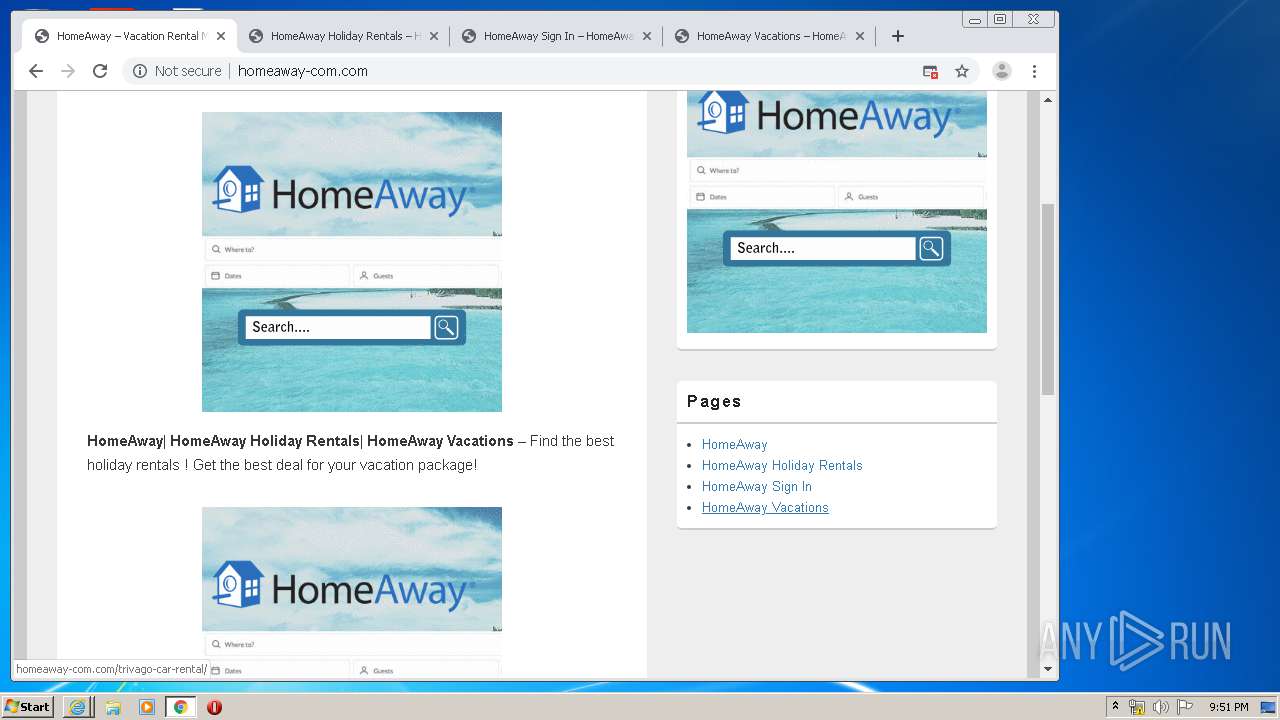
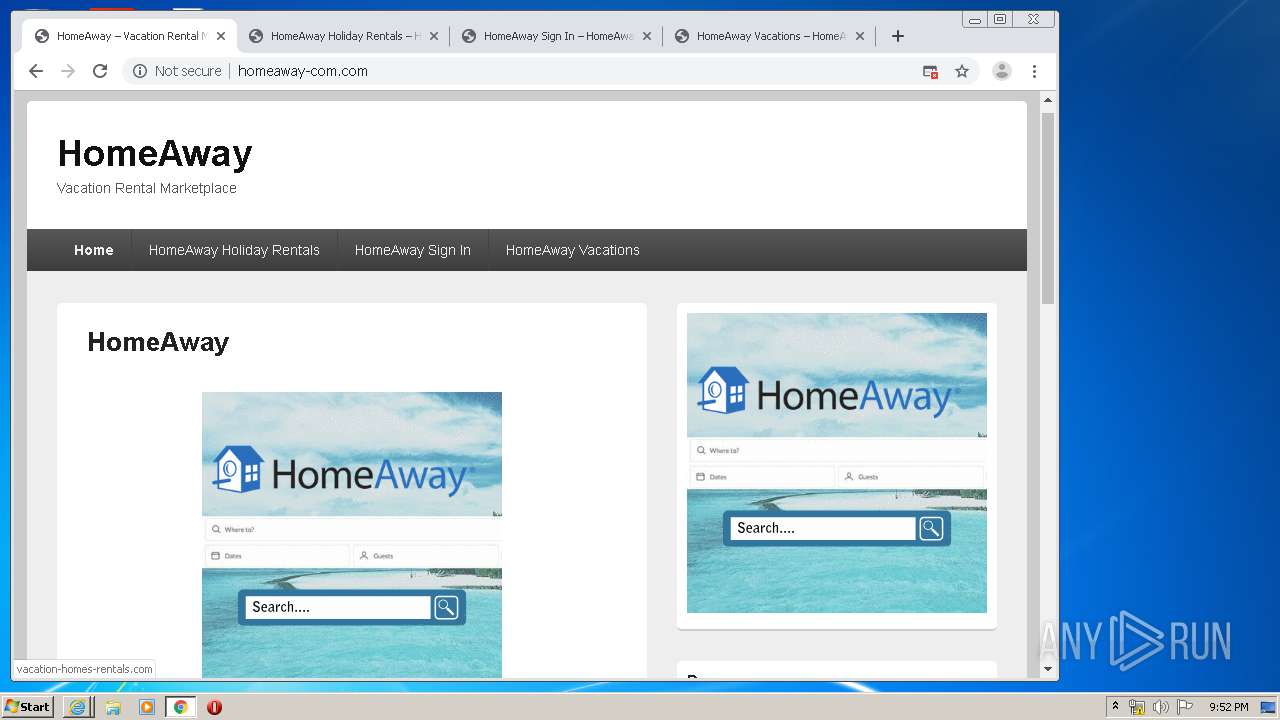
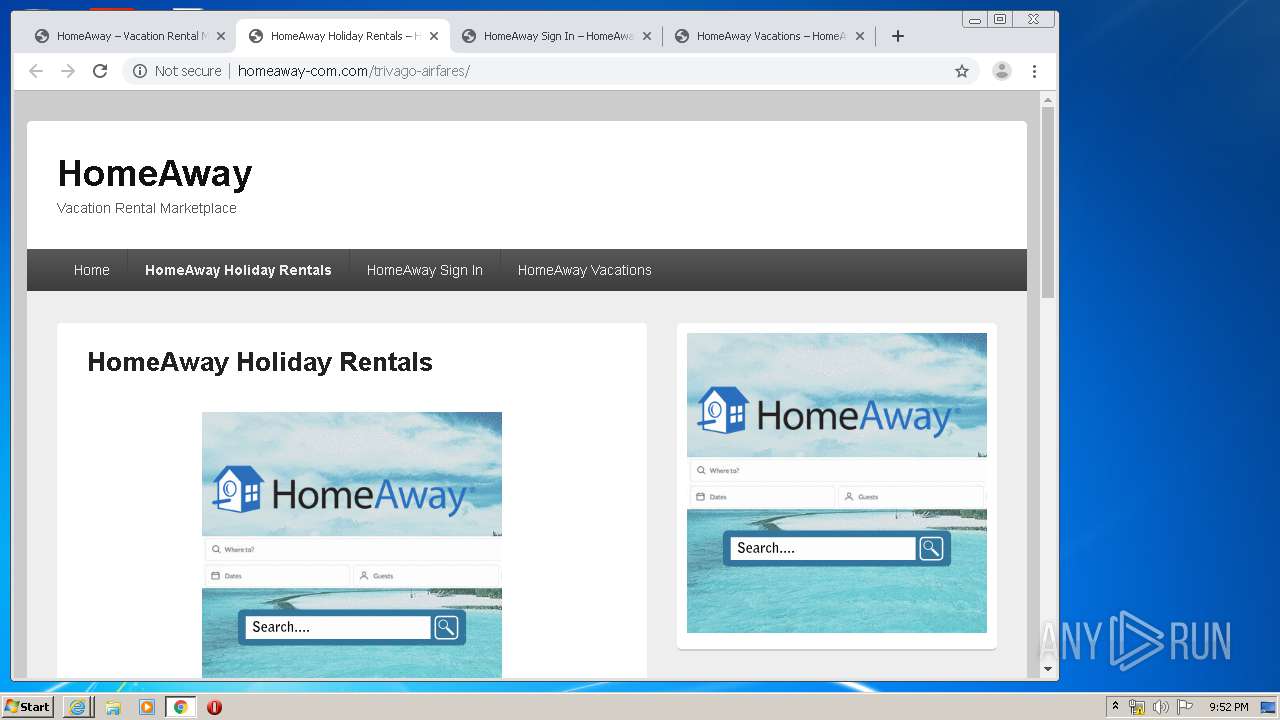
| Title: | HomeAway – Vacation Rental Marketplace |
| Generator: | WordPress 5.2.5 |
Total processes
89
Monitored processes
52
Malicious processes
0
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 604 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1024,3651265405203887917,8601017099927580032,131072 --enable-features=PasswordImport --lang=en-US --extension-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=9394654320962157130 --renderer-client-id=6 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2652 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1352 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1032,18203460625819124879,5451794596612743729,131072 --enable-features=PasswordImport --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=3158852237217085337 --renderer-client-id=7 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2336 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1392 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=watcher --main-thread-id=3808 --on-initialized-event-handle=324 --parent-handle=328 /prefetch:6 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1636 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1032,18203460625819124879,5451794596612743729,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=3856847580599755176 --mojo-platform-channel-handle=3612 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1800 | "C:\Program Files\Internet Explorer\iexplore.exe" SCODEF:3952 CREDAT:144395 /prefetch:2 | C:\Program Files\Internet Explorer\iexplore.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 0 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 1828 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1024,3651265405203887917,8601017099927580032,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=1292054851238684115 --mojo-platform-channel-handle=3328 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 1876 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=1032,18203460625819124879,5451794596612743729,131072 --enable-features=PasswordImport --lang=en-US --instant-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=11130130404879206508 --renderer-client-id=6 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=1976 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2000 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1032,18203460625819124879,5451794596612743729,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=7002570438187382555 --mojo-platform-channel-handle=4000 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2132 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=1032,18203460625819124879,5451794596612743729,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=14787750845565251580 --mojo-platform-channel-handle=3840 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
| 2276 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=1024,3651265405203887917,8601017099927580032,131072 --enable-features=PasswordImport --gpu-preferences=KAAAAAAAAADgAAAgAQAAAAAAAAAAAGAAAAAAAAAAAAAIAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAFAAAAEAAAAAAAAAAAAAAABgAAABAAAAAAAAAAAQAAAAUAAAAQAAAAAAAAAAEAAAAGAAAA --service-request-channel-token=16034865626587584156 --mojo-platform-channel-handle=1040 --ignored=" --type=renderer " /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 75.0.3770.100 Modules
| |||||||||||||||
Total events
15 488
Read events
1 787
Write events
9 185
Delete events
4 516
Modification events
| (PID) Process: | (2944) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (2944) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (2944) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
| (PID) Process: | (2944) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (2944) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (3952) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateLowDateTime |
Value: 18151982 | |||
| (PID) Process: | (3952) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\UrlBlockManager |
| Operation: | write | Name: | NextCheckForUpdateHighDateTime |
Value: 30796033 | |||
| (PID) Process: | (3952) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Content |
| Operation: | write | Name: | CachePrefix |
Value: | |||
| (PID) Process: | (3952) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\Cookies |
| Operation: | write | Name: | CachePrefix |
Value: Cookie: | |||
| (PID) Process: | (3952) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\5.0\Cache\History |
| Operation: | write | Name: | CachePrefix |
Value: Visited: | |||
Executable files
0
Suspicious files
104
Text files
322
Unknown types
22
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2944 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\78RFYB7Z\popups[1].css | — | |
MD5:— | SHA256:— | |||
| 2944 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\6Z2BCOUL\jquery[1].js | — | |
MD5:— | SHA256:— | |||
| 2944 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\PO2HN1X2\ezgif.com-gif-maker[1].gif | — | |
MD5:— | SHA256:— | |||
| 3952 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\Internet Explorer\Services\search_{0633EE93-D776-472f-A0FF-E1416B8B2E3A}.ico | — | |
MD5:— | SHA256:— | |||
| 2464 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\BrowserMetrics\BrowserMetrics-5E5050AB-9A0.pma | — | |
MD5:— | SHA256:— | |||
| 2944 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\PO2HN1X2\modal.modern[1].css | text | |
MD5:— | SHA256:— | |||
| 1800 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\78RFYB7Z\modal.modern[1].css | text | |
MD5:— | SHA256:— | |||
| 2944 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\B6QGX7LP\style[1].css | text | |
MD5:— | SHA256:— | |||
| 1800 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\6Z2BCOUL\ezgif.com-gif-maker[1].gif | image | |
MD5:— | SHA256:— | |||
| 2464 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old | text | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
69
TCP/UDP connections
79
DNS requests
37
Threats
1
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
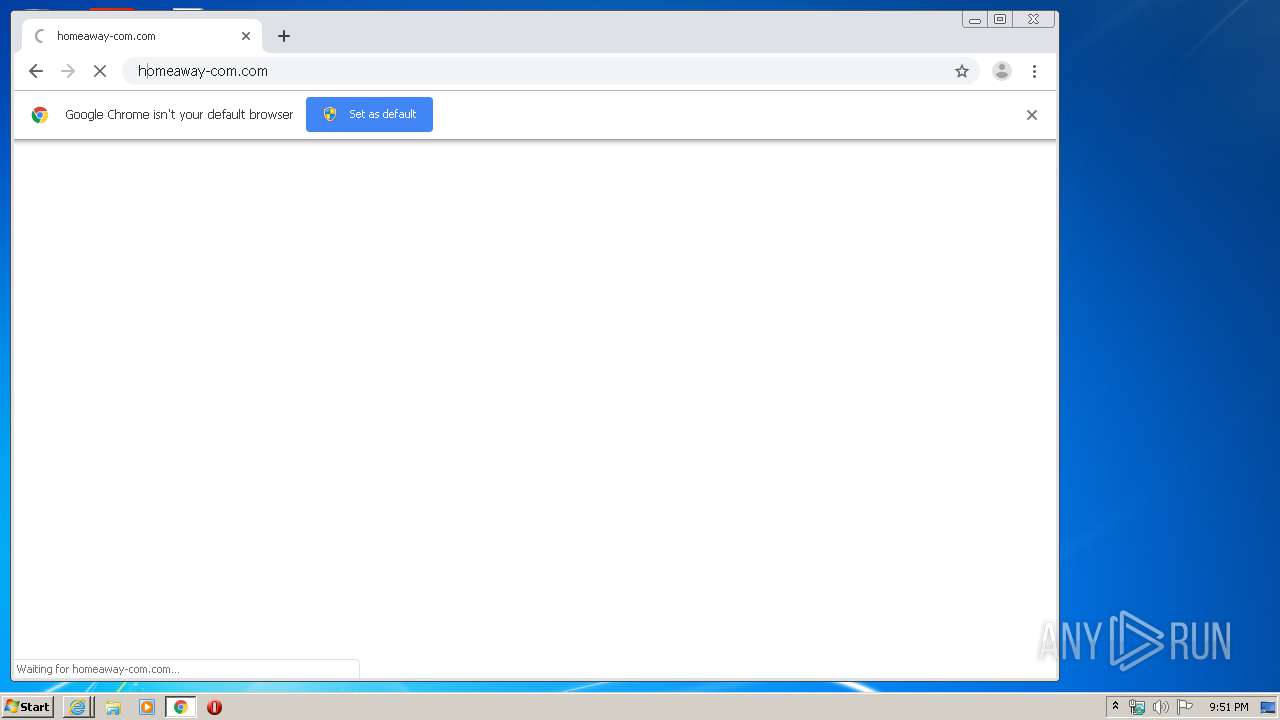
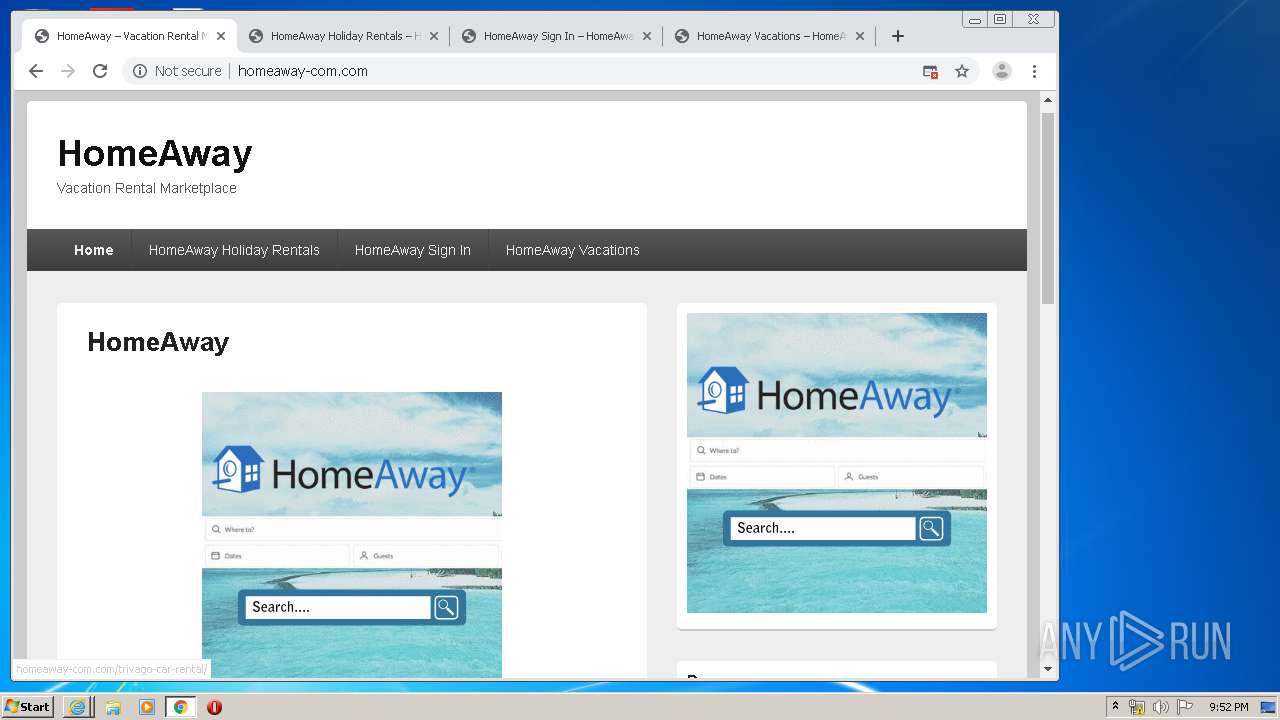
2944 | iexplore.exe | GET | — | 207.244.100.237:80 | http://homeaway-com.com/wp-includes/js/jquery/jquery.js?ver=1.12.4-wp | US | — | — | suspicious |
1800 | iexplore.exe | GET | — | 207.244.100.237:80 | http://homeaway-com.com/wp-includes/js/jquery/jquery.js?ver=1.12.4-wp | US | — | — | suspicious |
1800 | iexplore.exe | GET | — | 207.244.100.237:80 | http://homeaway-com.com/wp-content/themes/catch-box/js/jquery.sidr.min.js?ver=2.1.1.1 | US | — | — | suspicious |
2944 | iexplore.exe | GET | — | 207.244.100.237:80 | http://homeaway-com.com/wp-content/themes/catch-box/js/html5.min.js?ver=3.7.3 | US | — | — | suspicious |
2944 | iexplore.exe | GET | — | 207.244.100.237:80 | http://homeaway-com.com/wp-content/plugins/ultimate-popunder/assets/lanund.js?ver=1.2.6 | US | — | — | suspicious |
1800 | iexplore.exe | GET | — | 207.244.100.237:80 | http://homeaway-com.com/wp-content/plugins/ultimate-popunder/assets/ultimate-popunder.js?ver=1.2.6 | US | — | — | suspicious |
2944 | iexplore.exe | GET | — | 207.244.100.237:80 | http://homeaway-com.com/wp-content/themes/catch-box/js/catchbox_slider.js?ver=1.0 | US | — | — | suspicious |
2944 | iexplore.exe | GET | 200 | 207.244.100.237:80 | http://homeaway-com.com/wp-content/themes/catch-box/style.css?ver=5.2.5 | US | text | 82.1 Kb | suspicious |
2944 | iexplore.exe | GET | 200 | 207.244.100.237:80 | http://homeaway-com.com/wp-content/plugins/uji-popup/modal/css/modal.modern.css?ver=0.1 | US | text | 1.25 Kb | suspicious |
1800 | iexplore.exe | GET | 200 | 207.244.100.237:80 | http://homeaway-com.com/wp-content/plugins/uji-popup/modal/css/modal.modern.css?ver=0.1 | US | text | 1.25 Kb | suspicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3748 | chrome.exe | 172.217.16.142:443 | ogs.google.com.ua | Google Inc. | US | whitelisted |
3748 | chrome.exe | 216.58.207.67:443 | www.google.co.uk | Google Inc. | US | whitelisted |
3748 | chrome.exe | 172.217.22.100:443 | www.google.com | Google Inc. | US | whitelisted |
3748 | chrome.exe | 172.217.16.142:80 | ogs.google.com.ua | Google Inc. | US | whitelisted |
3748 | chrome.exe | 172.217.22.110:443 | clients2.google.com | Google Inc. | US | whitelisted |
3748 | chrome.exe | 173.194.139.6:80 | r1---sn-aigzrn7k.gvt1.com | Google Inc. | US | whitelisted |
3748 | chrome.exe | 172.217.18.97:443 | clients2.googleusercontent.com | Google Inc. | US | whitelisted |
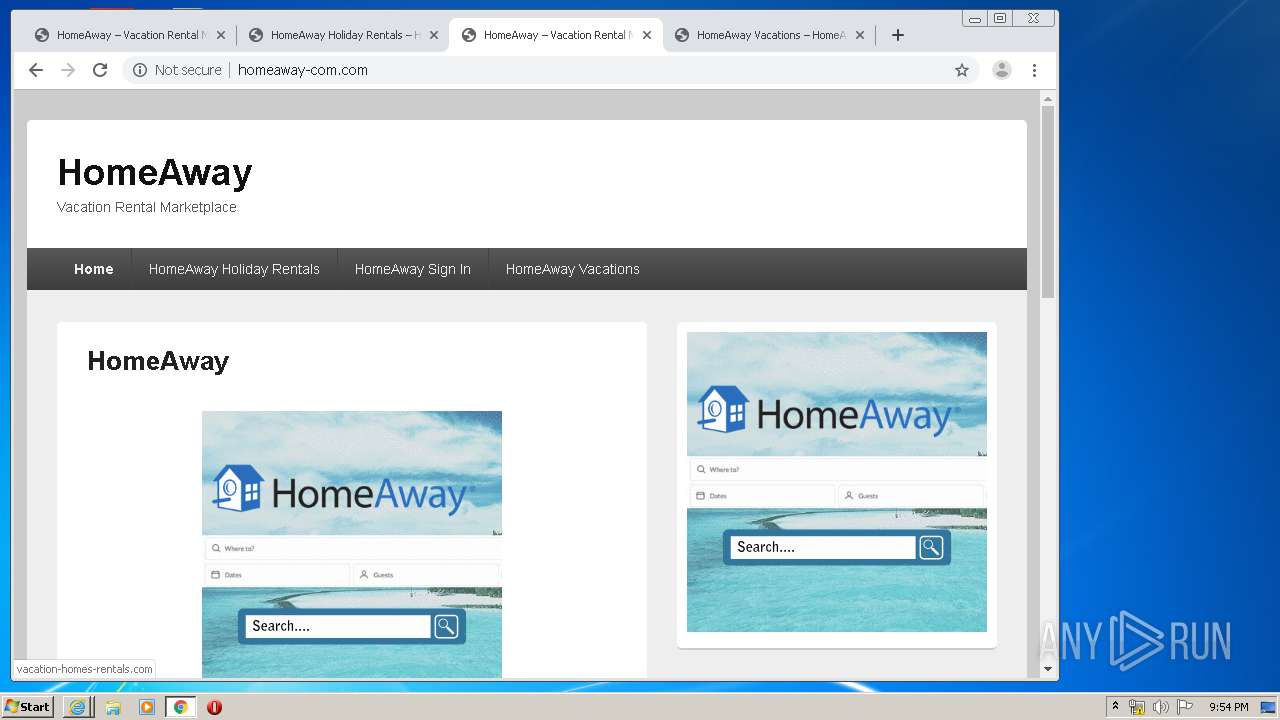
2944 | iexplore.exe | 207.244.100.237:80 | homeaway-com.com | Leaseweb USA, Inc. | US | unknown |
1800 | iexplore.exe | 207.244.100.237:80 | homeaway-com.com | Leaseweb USA, Inc. | US | unknown |
3748 | chrome.exe | 172.217.16.163:443 | clientservices.googleapis.com | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
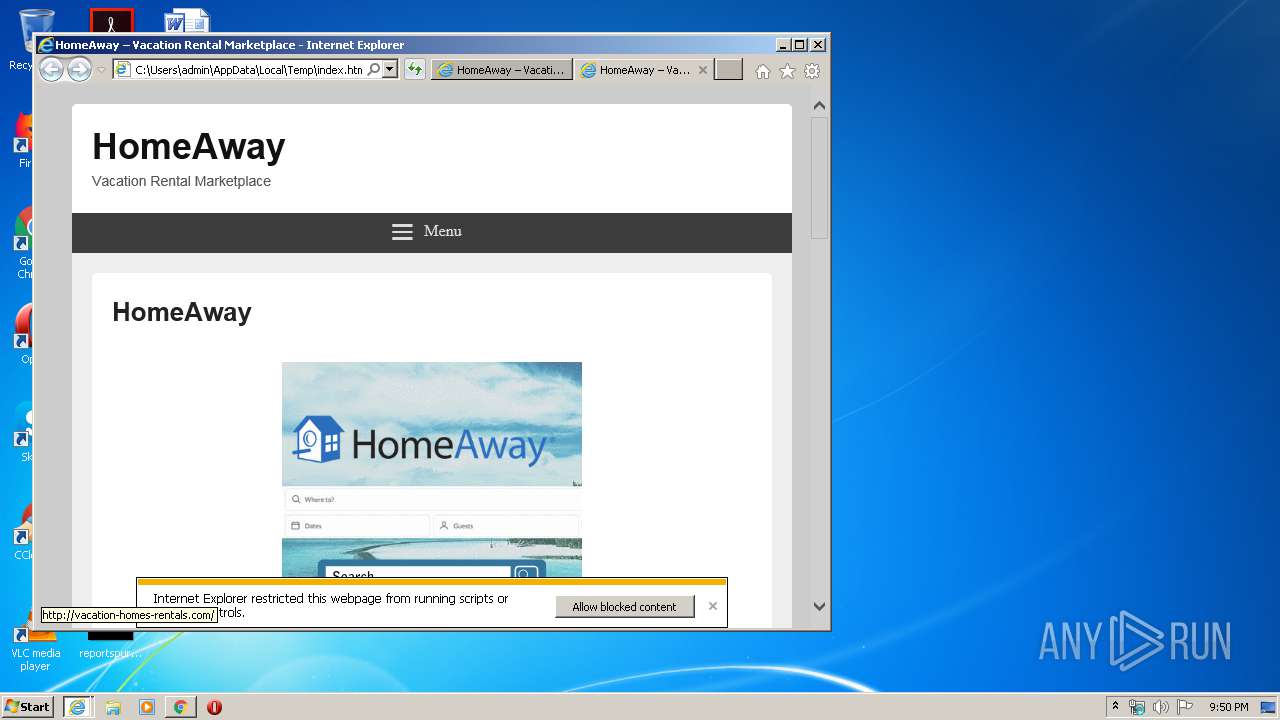
homeaway-com.com |
| suspicious |
www.bing.com |
| whitelisted |
api.bing.com |
| whitelisted |
clientservices.googleapis.com |
| whitelisted |
accounts.google.com |
| shared |
www.google.com.ua |
| whitelisted |
fonts.googleapis.com |
| whitelisted |
www.gstatic.com |
| whitelisted |
fonts.gstatic.com |
| whitelisted |
apis.google.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
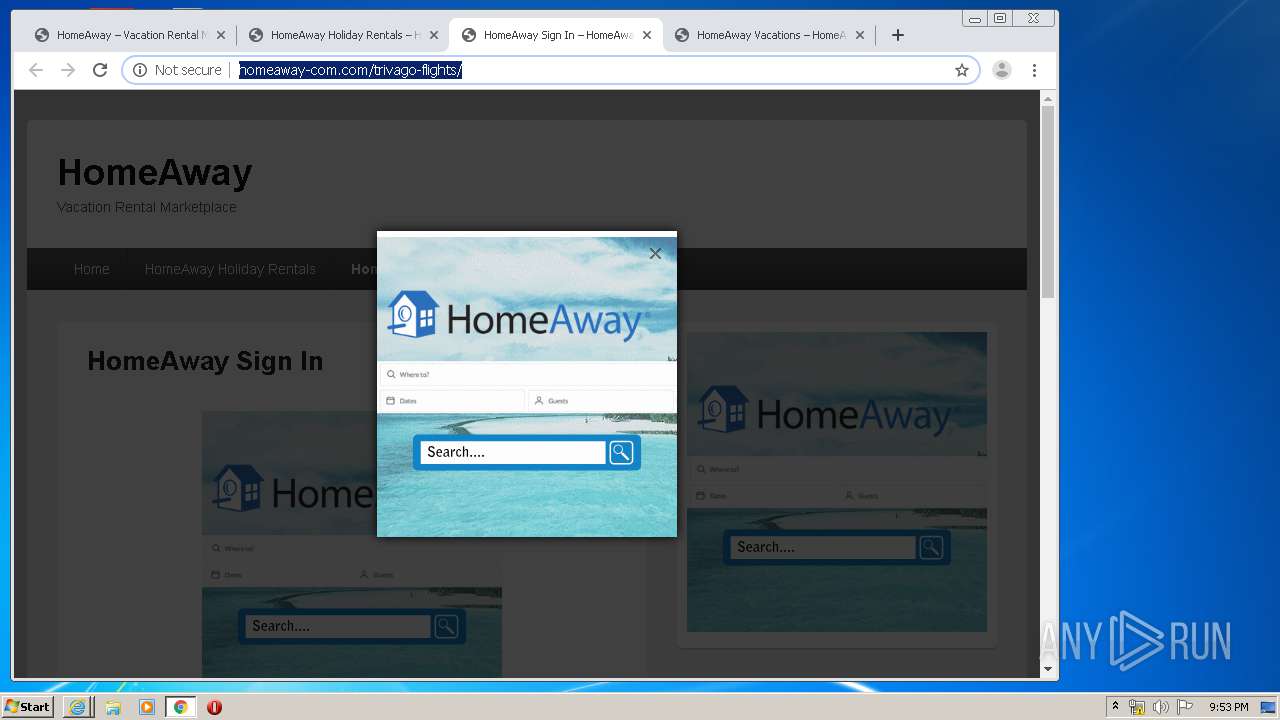
3740 | chrome.exe | Misc activity | SUSPICIOUS [PTsecurity] Drive-by Evil Redirector |