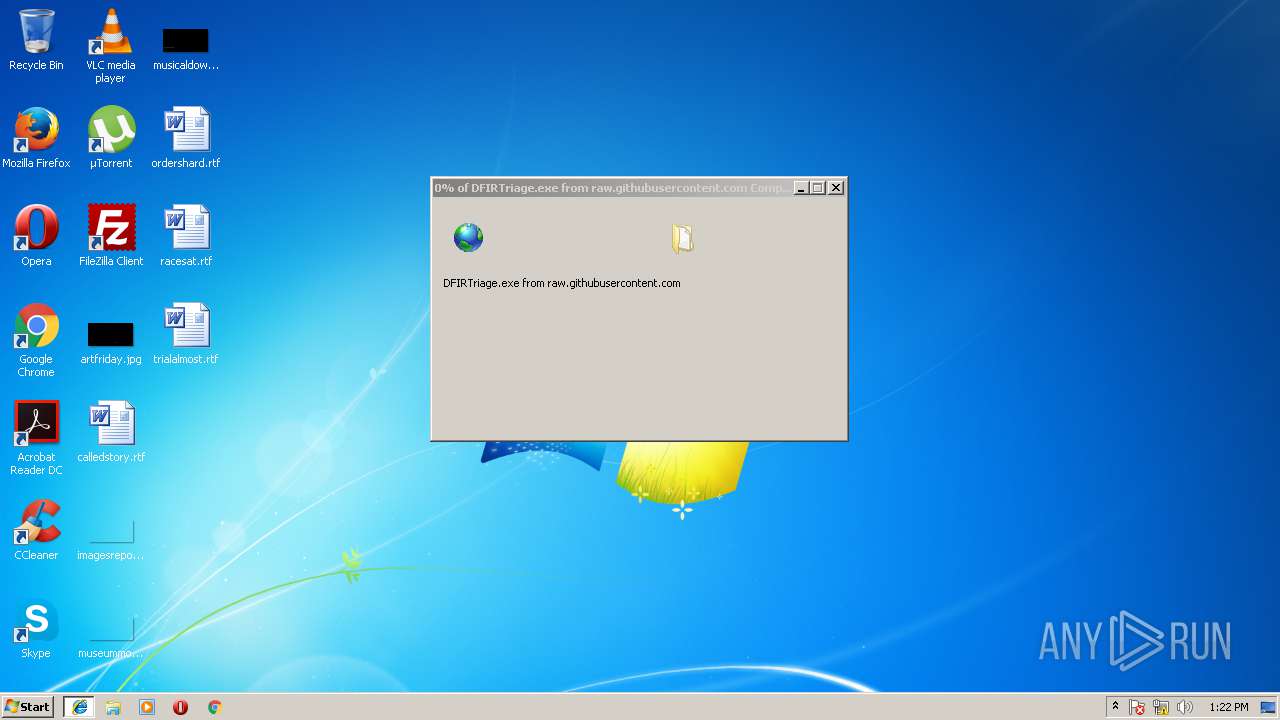
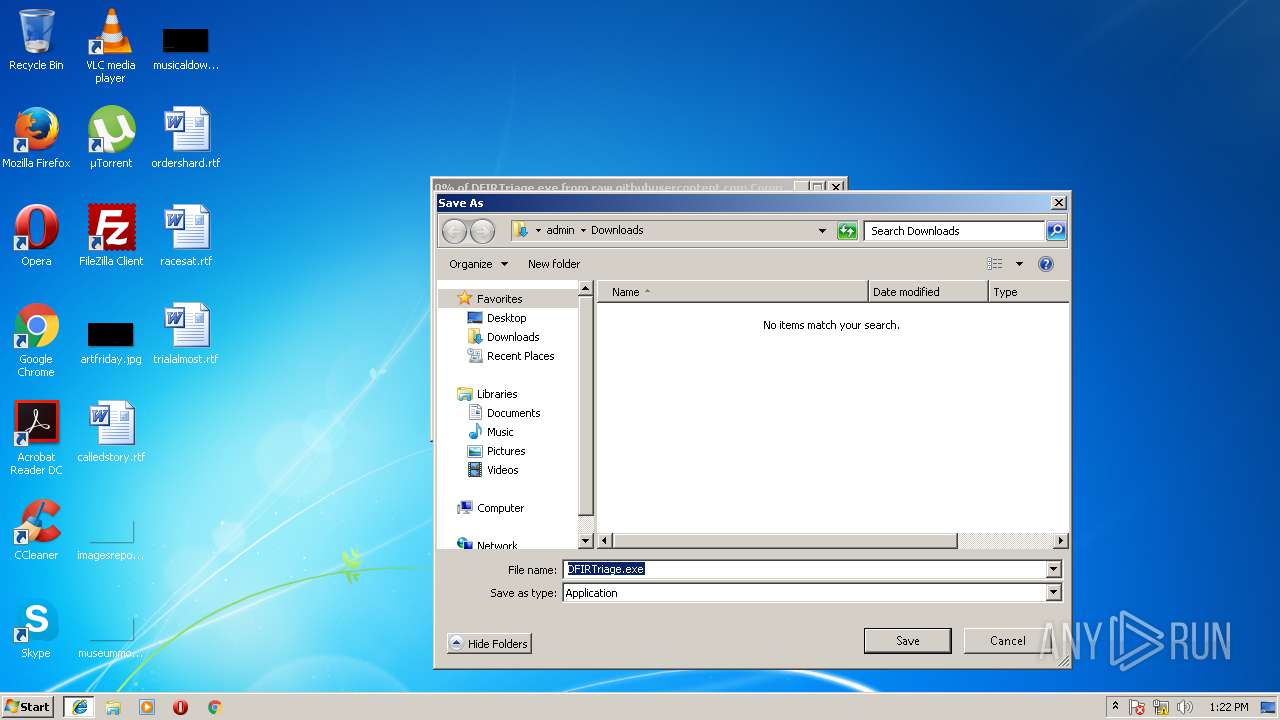
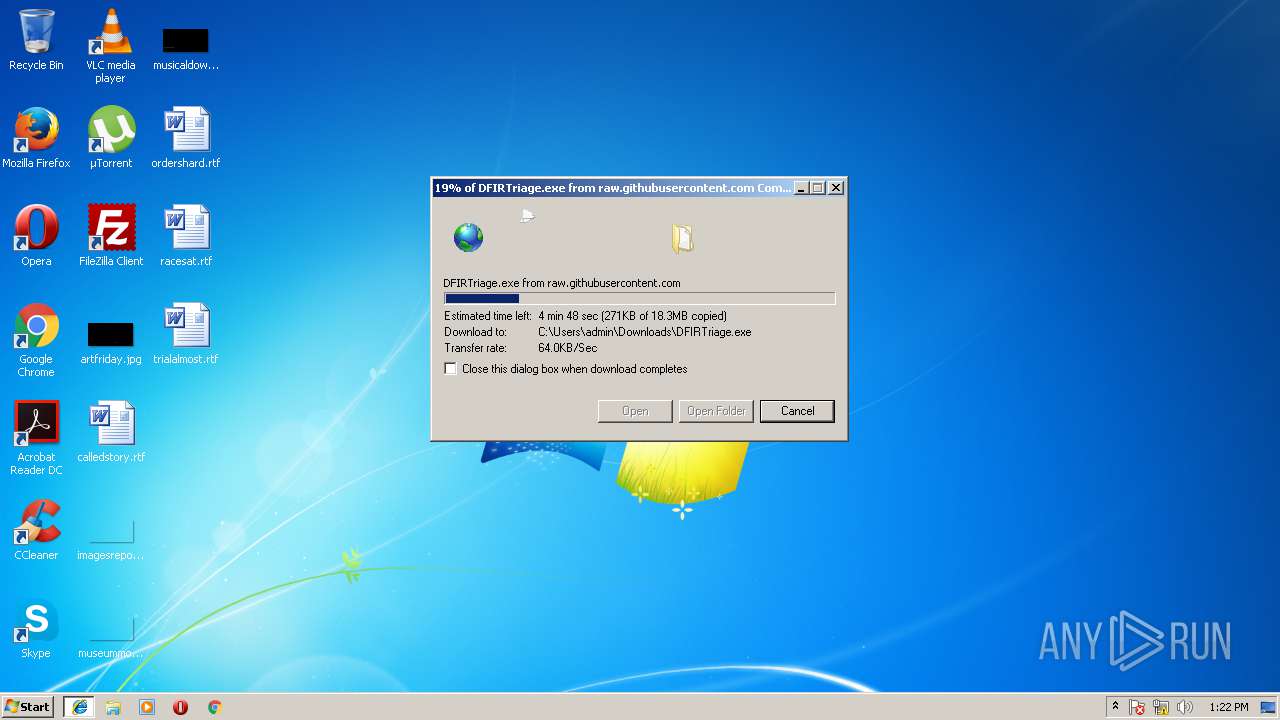
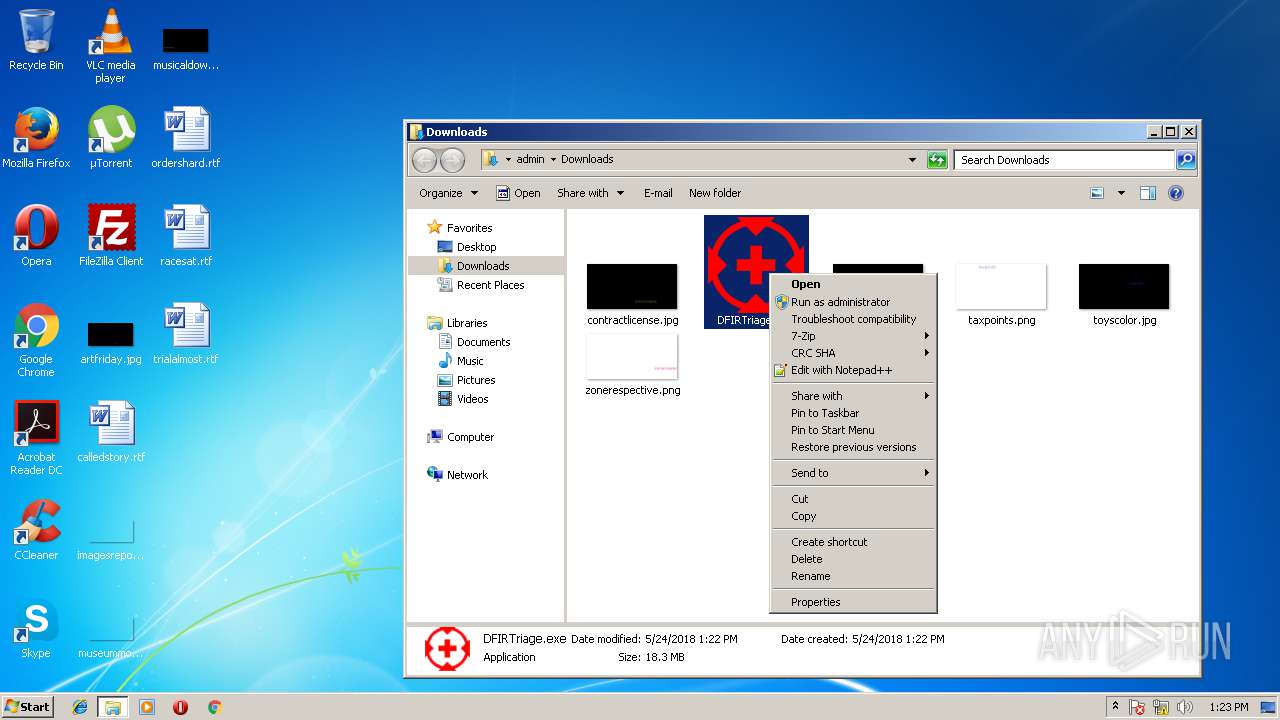
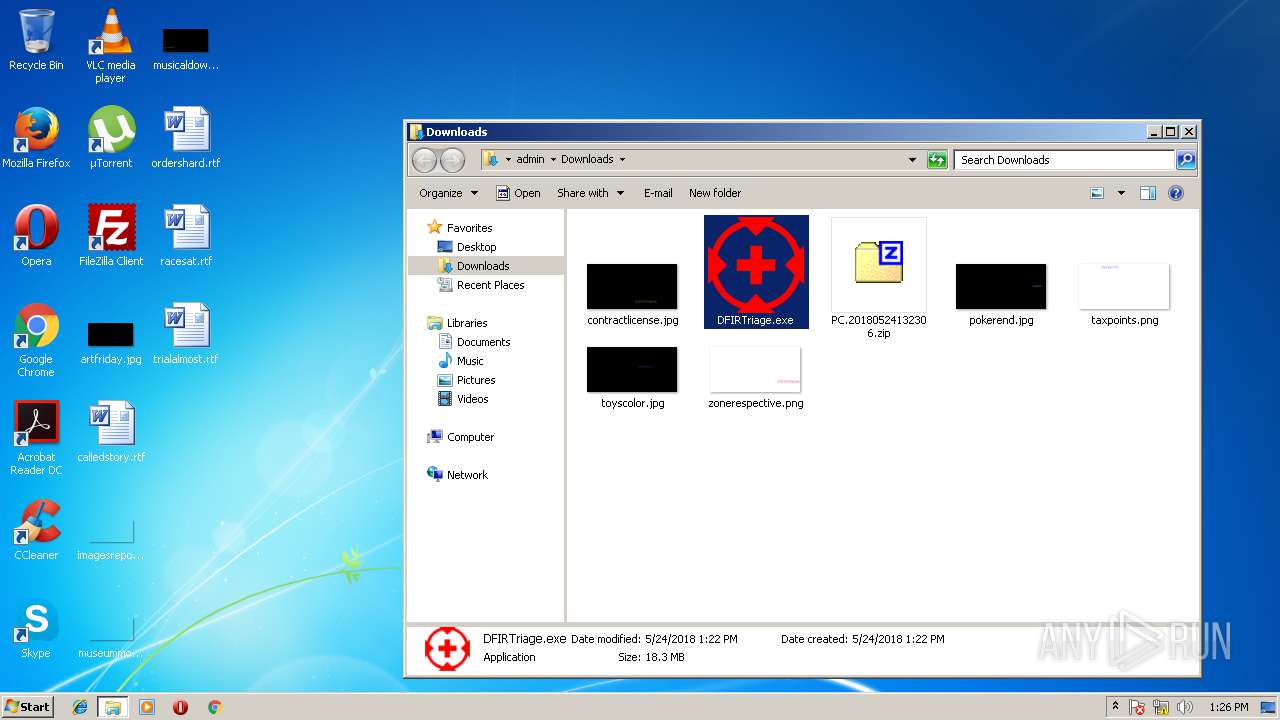
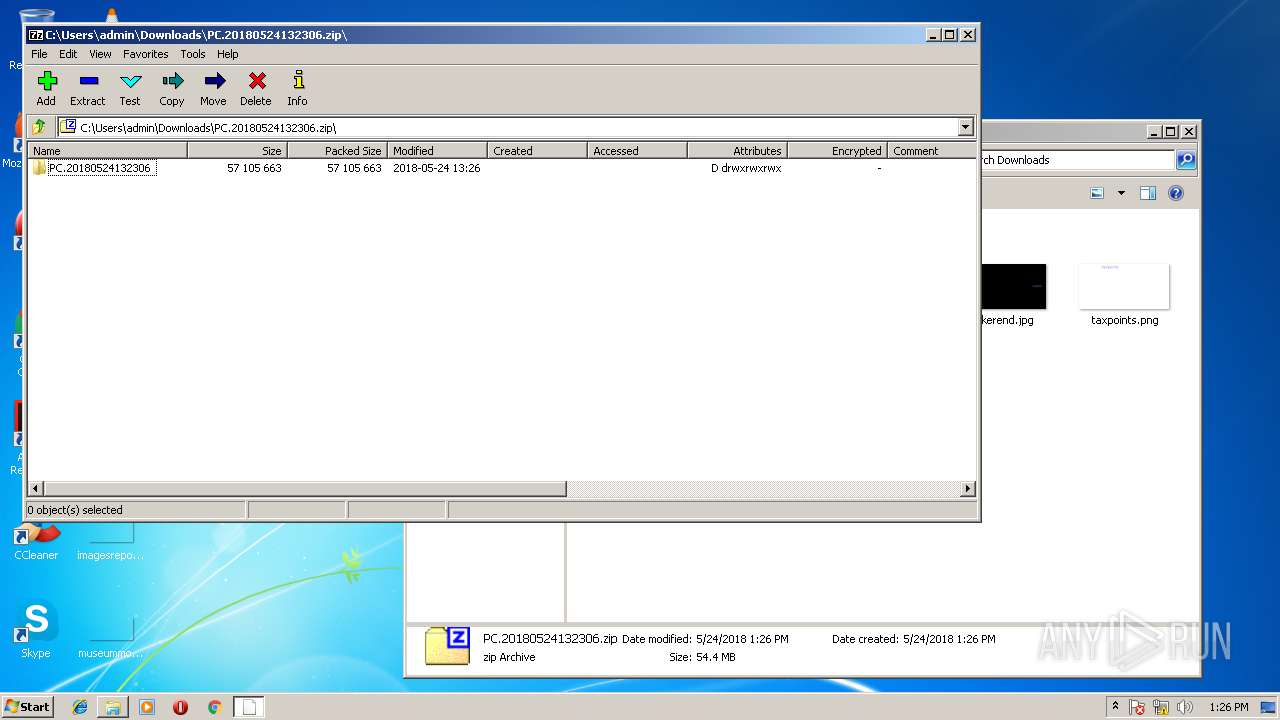
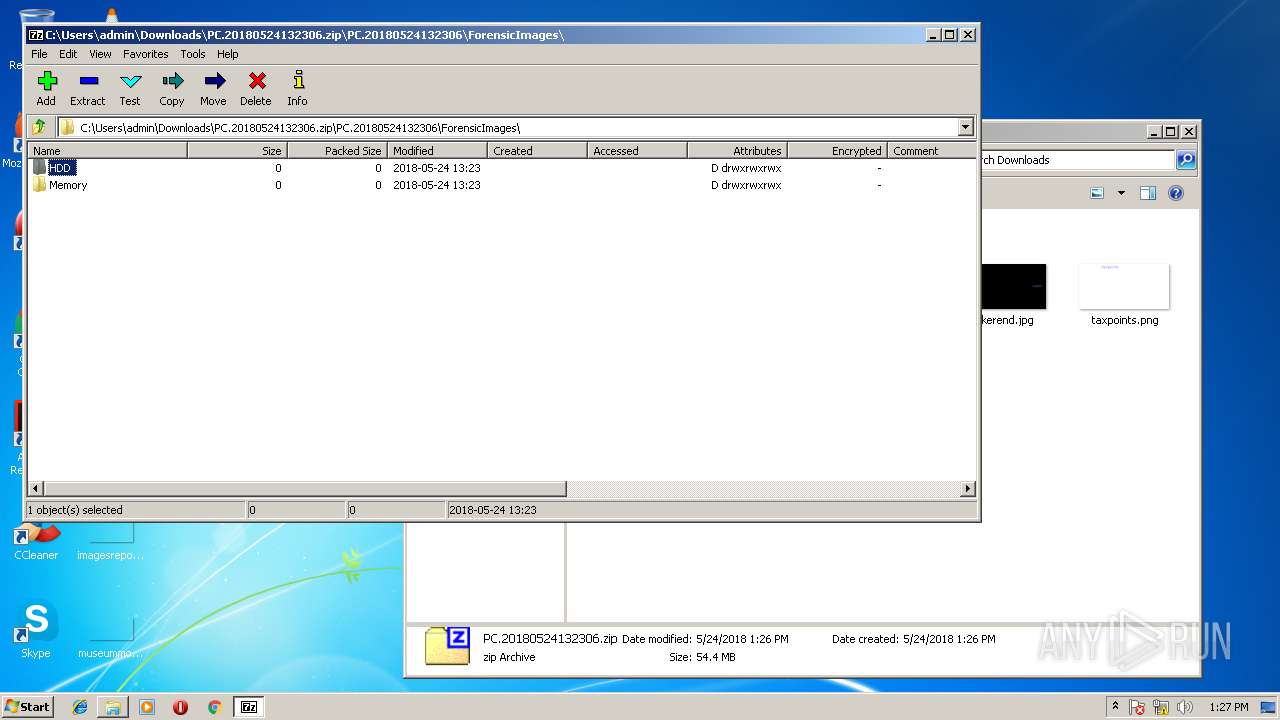
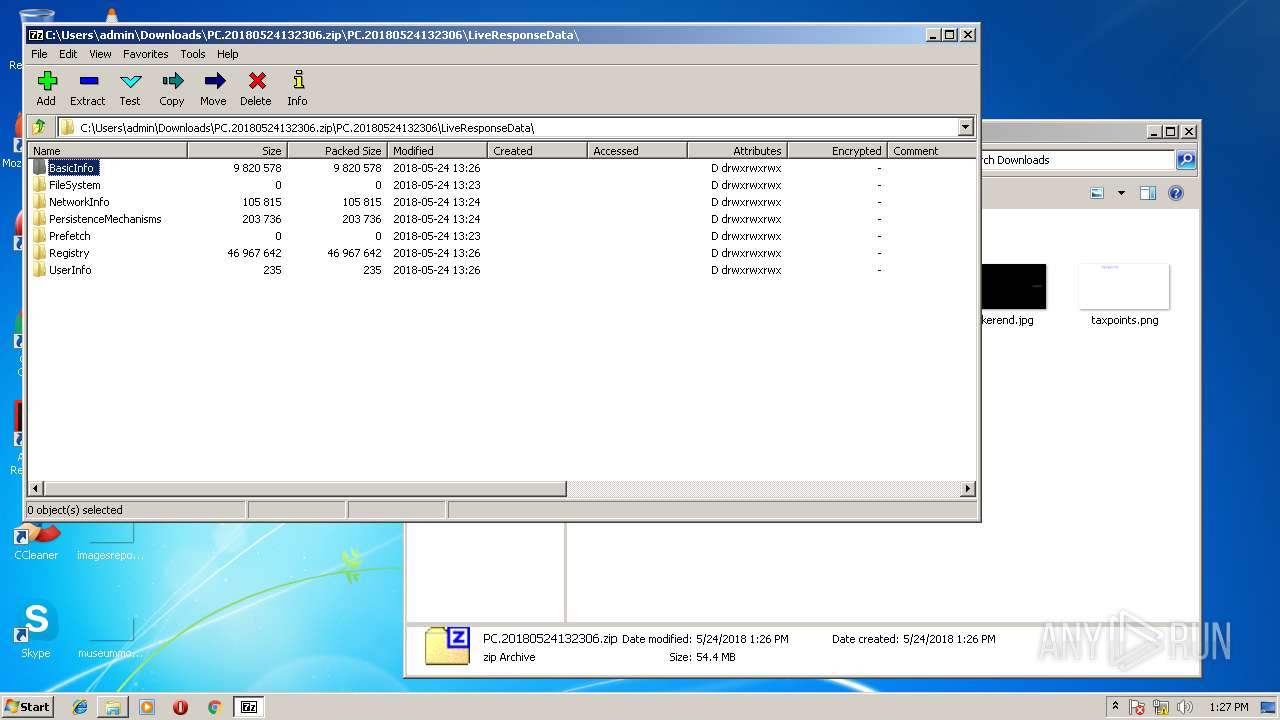
| URL: | https://raw.githubusercontent.com/travisfoley/dfirtriage/master/DFIRTriage.exe |
| Full analysis: | https://app.any.run/tasks/fc7ae326-18b2-4bf7-b151-7fc44f8d494a |
| Verdict: | Malicious activity |
| Analysis date: | May 24, 2018, 12:21:58 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | A22CB40F63C450F1F3E46D47D7F29AC8 |
| SHA1: | 9554690ACF5B92D905964B39A7916807D96EB392 |
| SHA256: | 6421F99209414A06E98590F66A82E502F1AB84329BAC9E22E5833F7E8F042445 |
| SSDEEP: | 3:N8SGfALtGTMETTSAcKDECArRABvAdA:2FMGhvrEDFABYdA |
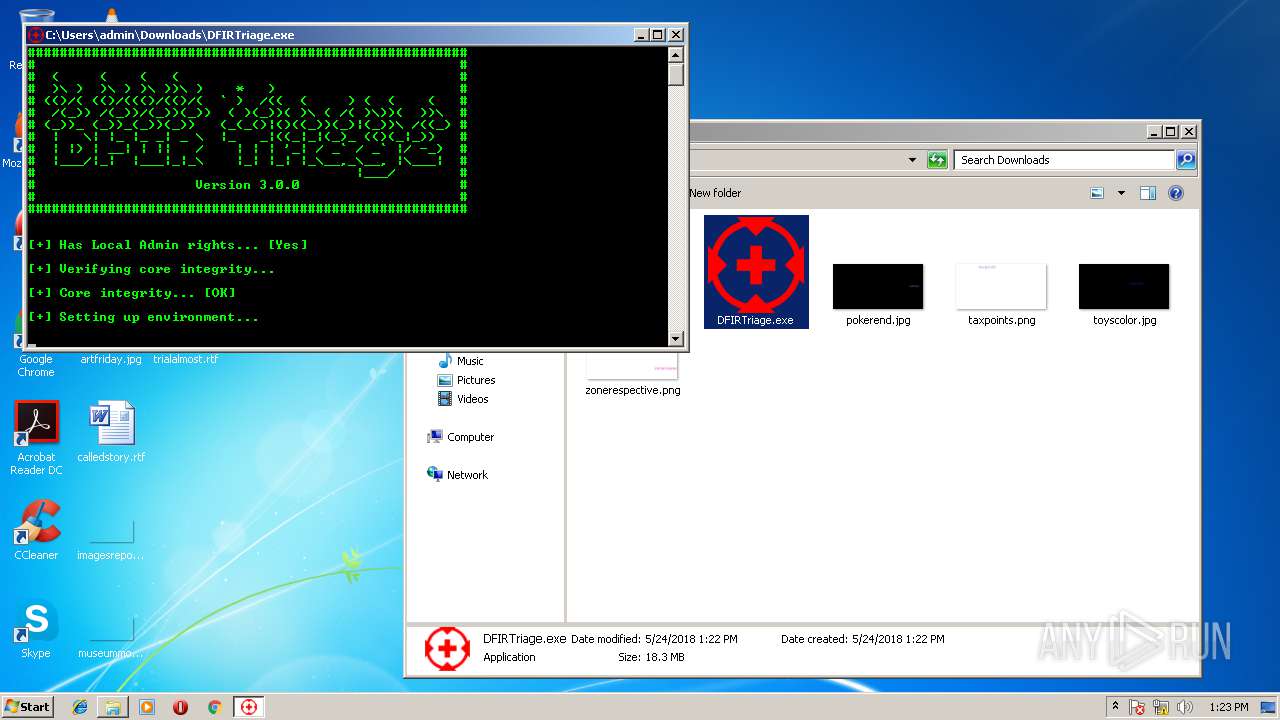
MALICIOUS
Application was dropped or rewritten from another process
- DFIRTriage.exe (PID: 4044)
- DFIRTriage.exe (PID: 2924)
- BrowsingHistoryView32.exe (PID: 2672)
Loads dropped or rewritten executable
- DFIRTriage.exe (PID: 4044)
- iexplore.exe (PID: 2708)
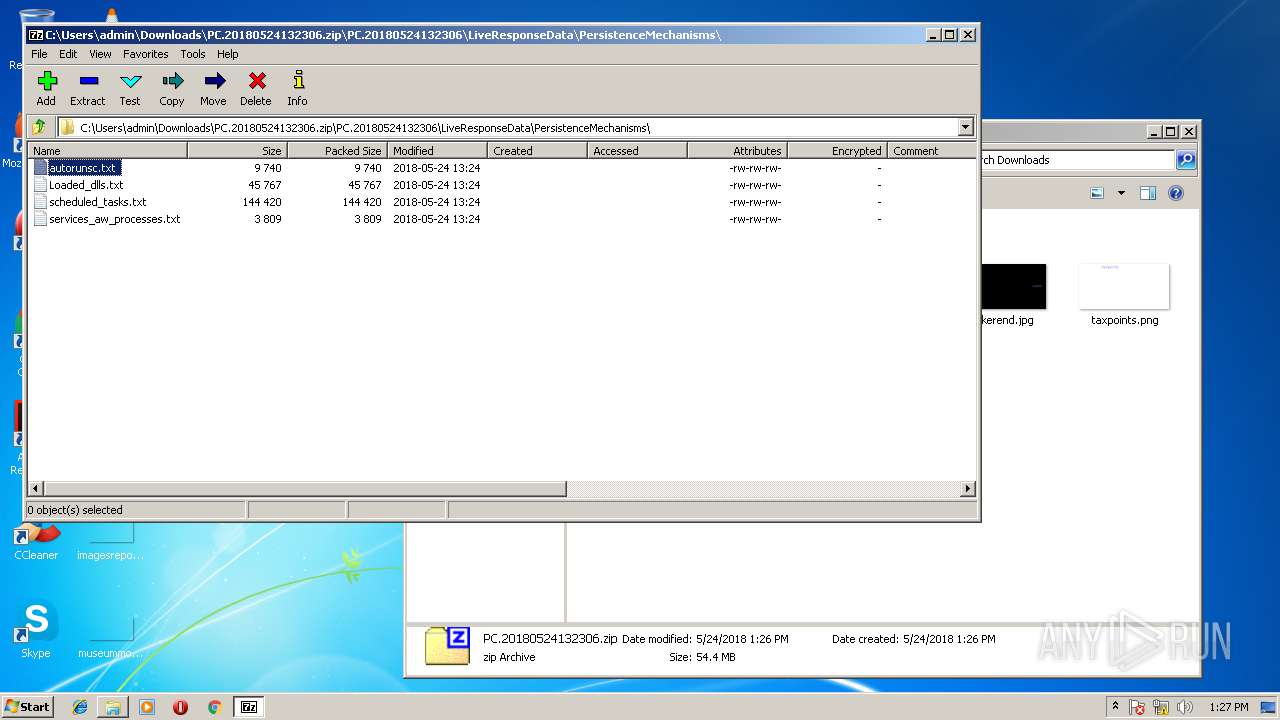
Uses Task Scheduler to run other applications
- cmd.exe (PID: 3872)
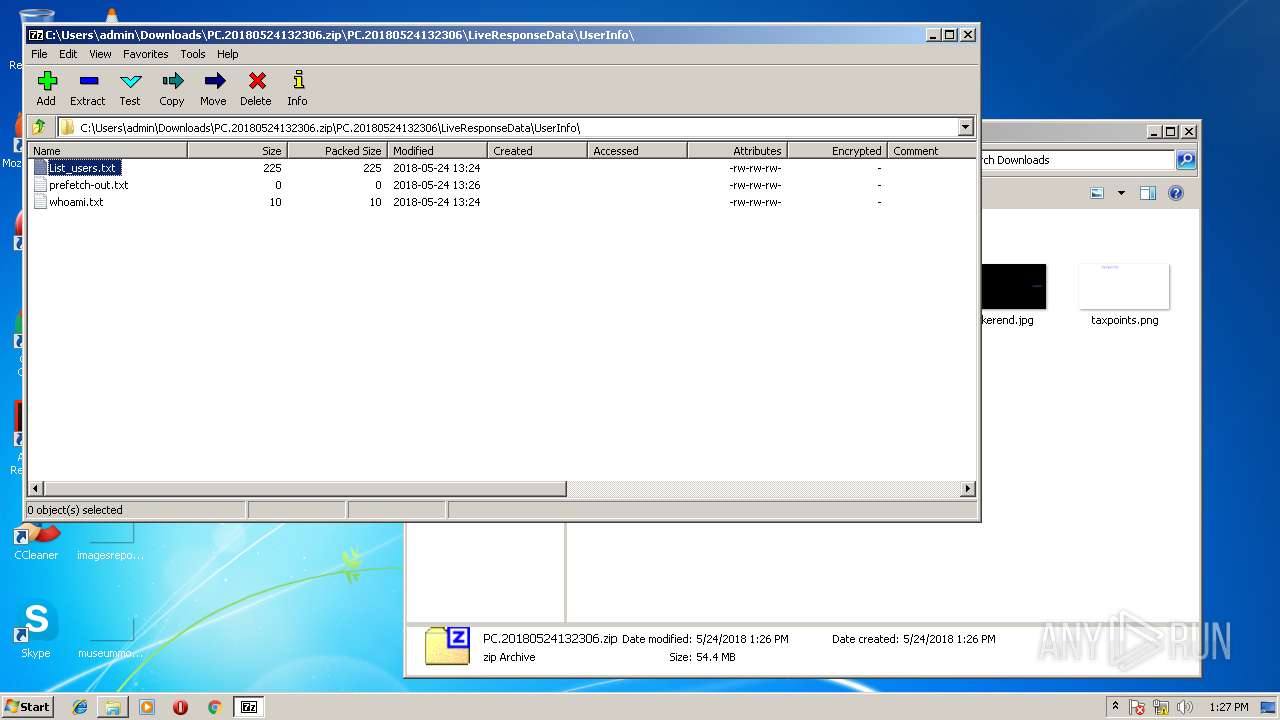
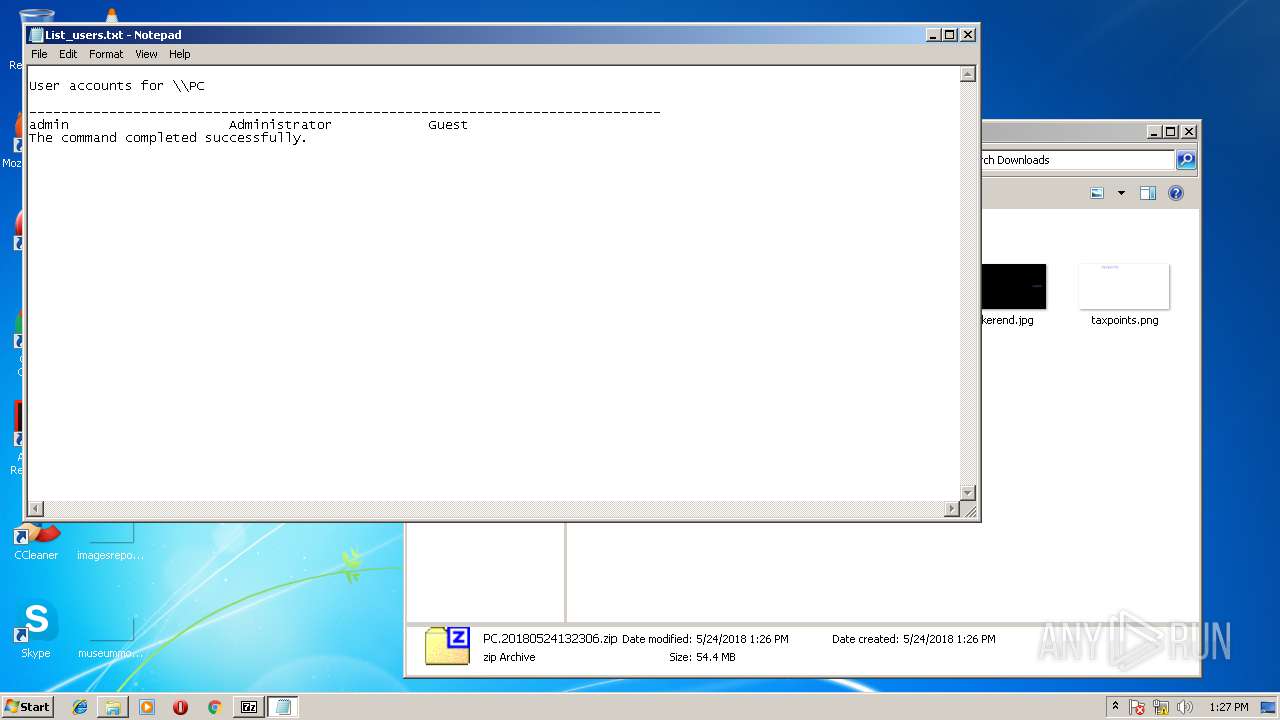
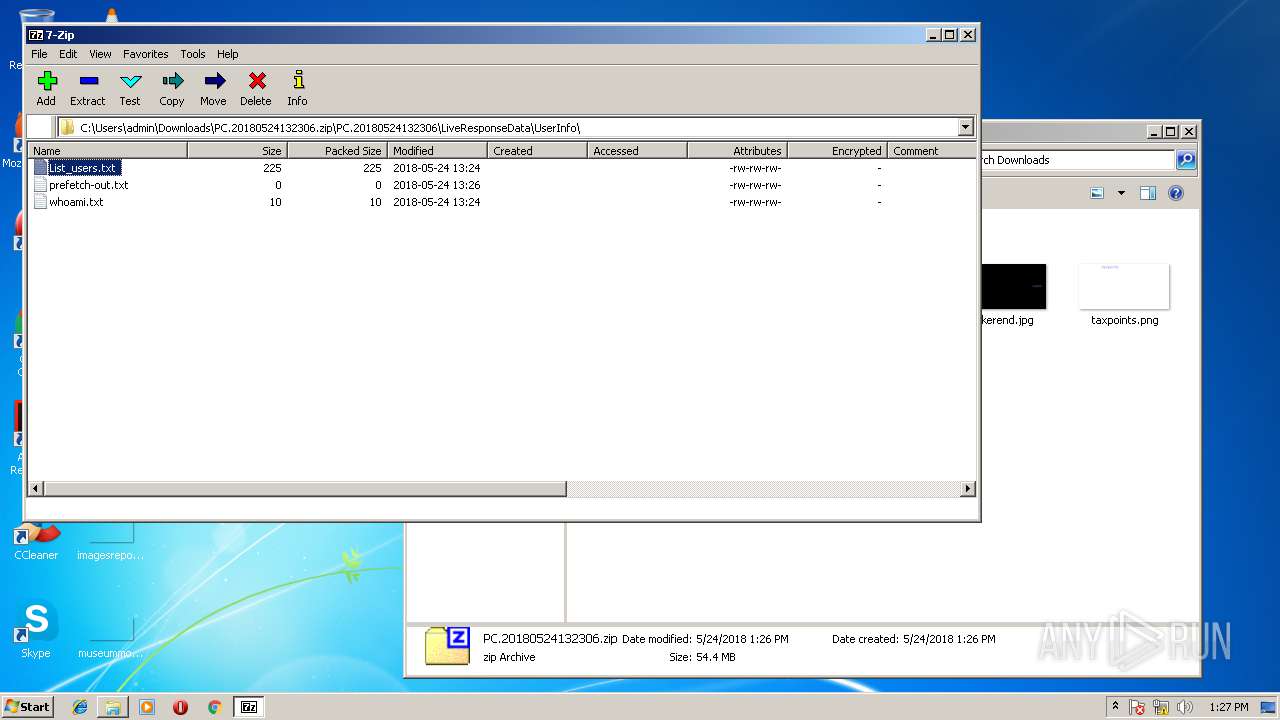
Starts NET.EXE to view/add/change user profiles
- cmd.exe (PID: 3608)
Loads the Task Scheduler COM API
- schtasks.exe (PID: 2604)
SUSPICIOUS
Starts CMD.EXE for commands execution
- DFIRTriage.exe (PID: 4044)
- NETSTAT.EXE (PID: 3932)
- cmd.exe (PID: 1208)
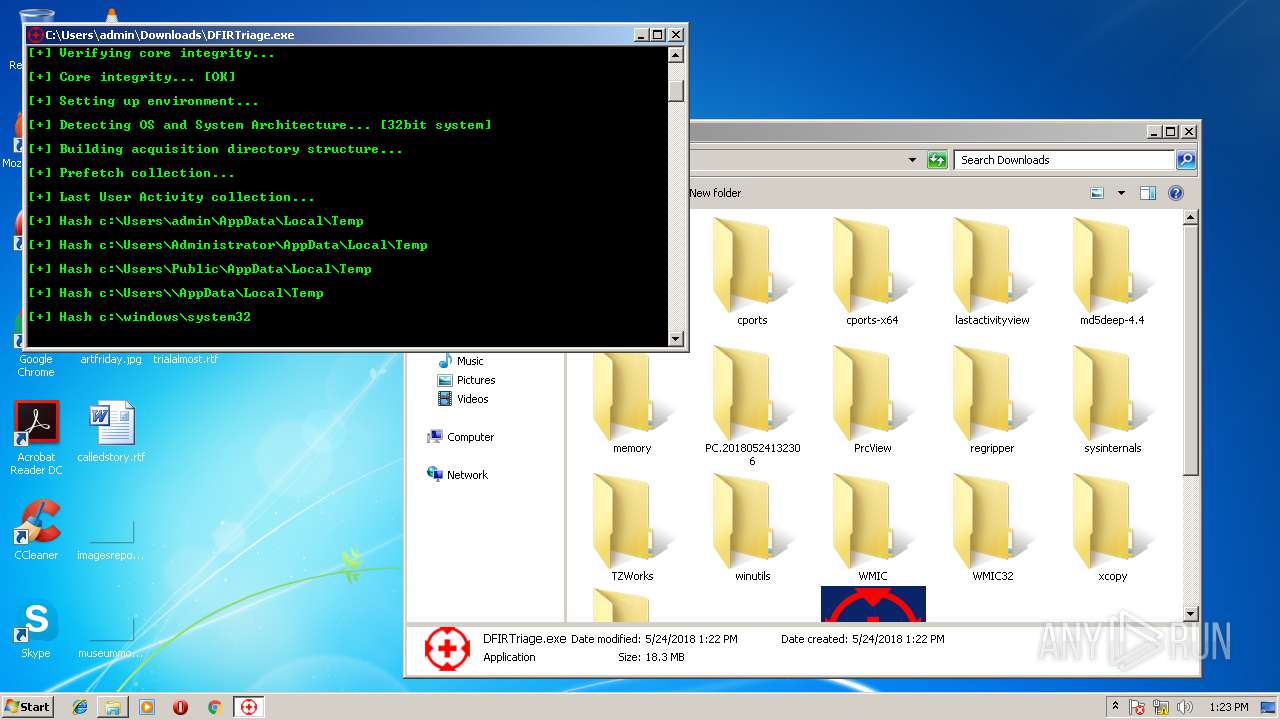
Executable content was dropped or overwritten
- iexplore.exe (PID: 3228)
- iexplore.exe (PID: 2708)
- DFIRTriage.exe (PID: 2924)
- DFIRTriage.exe (PID: 4044)
Uses TASKLIST.EXE to query information about running processes
- cmd.exe (PID: 2940)
- cmd.exe (PID: 3096)
- cmd.exe (PID: 3300)
Uses REG.EXE to modify Windows registry
- cmd.exe (PID: 3904)
- cmd.exe (PID: 1896)
- cmd.exe (PID: 1172)
- cmd.exe (PID: 2524)
- cmd.exe (PID: 1132)
- cmd.exe (PID: 1212)
- cmd.exe (PID: 1088)
- cmd.exe (PID: 3192)
- cmd.exe (PID: 3252)
- cmd.exe (PID: 3948)
- cmd.exe (PID: 3880)
- cmd.exe (PID: 3804)
- cmd.exe (PID: 3676)
- cmd.exe (PID: 2740)
- cmd.exe (PID: 2456)
Reads Windows owner settings
- psinfo.exe (PID: 3096)
Reads CPU info
- psinfo.exe (PID: 3096)
Reads the Windows organization settings
- psinfo.exe (PID: 3096)
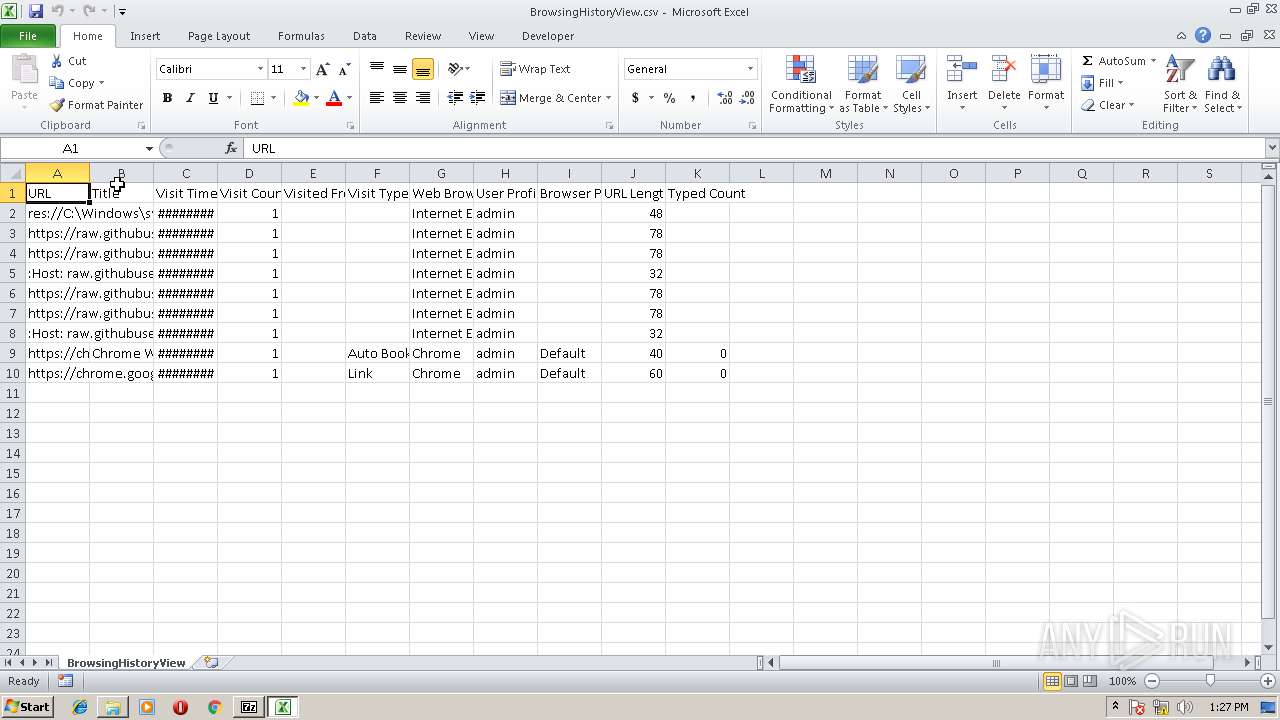
Creates files in the user directory
- BrowsingHistoryView32.exe (PID: 2672)
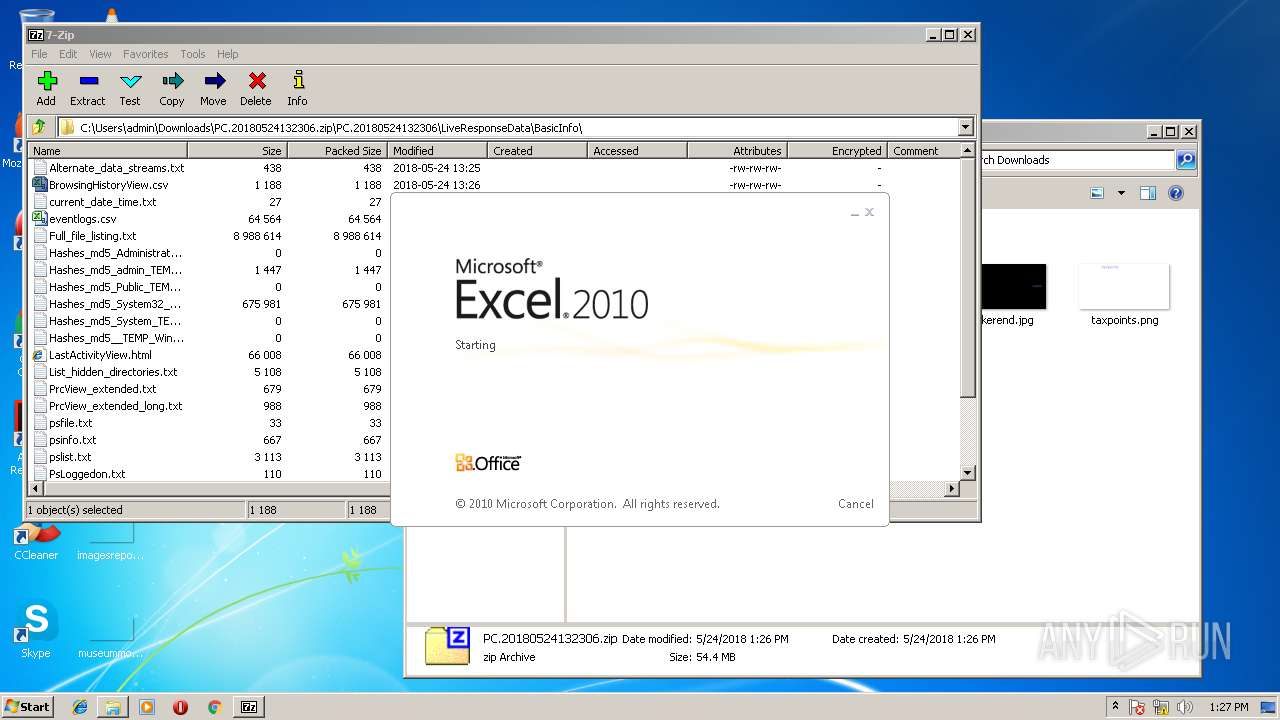
Starts Microsoft Office Application
- 7zFM.exe (PID: 3748)
INFO
Dropped object may contain URL's
- iexplore.exe (PID: 2708)
- DFIRTriage.exe (PID: 2924)
- iexplore.exe (PID: 3228)
- DFIRTriage.exe (PID: 4044)
Reads Internet Cache Settings
- iexplore.exe (PID: 2708)
- iexplore.exe (PID: 3228)
Application launched itself
- iexplore.exe (PID: 3228)
Changes internet zones settings
- iexplore.exe (PID: 3228)
Reads Microsoft Office registry keys
- EXCEL.EXE (PID: 1376)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
155
Monitored processes
105
Malicious processes
2
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 348 | reg.exe ADD HKCU\Software\Sysinternals\Tcpvcon /v EulaAccepted /t REG_DWORD /d 1 /f | C:\Windows\system32\reg.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Registry Console Tool Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 568 | C:\Users\admin\Downloads\sysinternals\PsLoggedon.exe | C:\Users\admin\Downloads\sysinternals\PsLoggedon.exe | — | DFIRTriage.exe | |||||||||||
User: admin Company: Sysinternals - www.sysinternals.com Integrity Level: HIGH Description: See who's logged on Exit code: 0 Version: 1.34 Modules
| |||||||||||||||
| 572 | C:\Users\admin\Downloads\regripper\rip.exe -r PC.20180524132306\LiveResponseData\Registry\NTUSER -f NTUSER | C:\Users\admin\Downloads\regripper\rip.exe | — | DFIRTriage.exe | |||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Version: 1.0.0.0 Modules
| |||||||||||||||
| 888 | cmd.exe /C ipconfig /all | C:\Windows\system32\cmd.exe | — | DFIRTriage.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 1004 | cmd.exe /C date /T | C:\Windows\system32\cmd.exe | — | DFIRTriage.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 1088 | cmd.exe /C reg.exe ADD HKCU\Software\Sysinternals\Tcpvcon /v EulaAccepted /t REG_DWORD /d 1 /f | C:\Windows\system32\cmd.exe | — | DFIRTriage.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 1132 | cmd.exe /C reg.exe ADD HKCU\Software\Sysinternals\PsLogList /v EulaAccepted /t REG_DWORD /d 1 /f | C:\Windows\system32\cmd.exe | — | DFIRTriage.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 1172 | cmd.exe /C dir c:\Users /b | C:\Windows\system32\cmd.exe | — | DFIRTriage.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 1172 | cmd.exe /C reg.exe ADD HKCU\Software\Sysinternals\PsInfo /v EulaAccepted /t REG_DWORD /d 1 /f | C:\Windows\system32\cmd.exe | — | DFIRTriage.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 1208 | cmd.exe /C dir PC.20180524132306\LiveResponseData\Prefetch\*.pf /b /s | C:\Users\admin\Downloads\TZWorks\pf.exe -pipe -v > PC.20180524132306\LiveResponseData\UserInfo\prefetch-out.txt | C:\Windows\system32\cmd.exe | — | DFIRTriage.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 4294967295 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
Total events
2 533
Read events
2 355
Write events
152
Delete events
26
Modification events
| (PID) Process: | (3228) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (3228) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (3228) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (3228) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Zones |
| Operation: | write | Name: | SecuritySafe |
Value: 1 | |||
| (PID) Process: | (3228) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | write | Name: | ProxyEnable |
Value: 0 | |||
| (PID) Process: | (3228) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Connections |
| Operation: | write | Name: | SavedLegacySettings |
Value: 460000006B000000010000000000000000000000000000000000000000000000400C35B347C7D301000000000000000000000000020000001700000000000000FE80000000000000D45917EAB3ED3D860B000000000000001700000000000000FE80000000000000D45917EAB3ED3D860B000000000000001C00000000000000000000000000000000000000000000000000000000000000170000000000000000000000000000000000FFFFC0A8640B000000000000000002000000C0A801640000000000000000000000000000000000000000000000000C00000C37D0000010A73800D8703600000000000000000000000000000000000000000000000000000000000000000000000000000000000000000081F800009000230090002300380023000000000000702C000A00000000000000F8412C00 | |||
| (PID) Process: | (3228) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Recovery\Active |
| Operation: | write | Name: | {21CAE74D-5F4D-11E8-B27F-5254004AAD21} |
Value: 0 | |||
| (PID) Process: | (3228) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Ext\Stats\{2670000A-7350-4F3C-8081-5663EE0C6C49}\iexplore |
| Operation: | write | Name: | Type |
Value: 4 | |||
| (PID) Process: | (3228) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Ext\Stats\{2670000A-7350-4F3C-8081-5663EE0C6C49}\iexplore |
| Operation: | write | Name: | Count |
Value: 5 | |||
| (PID) Process: | (3228) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Ext\Stats\{2670000A-7350-4F3C-8081-5663EE0C6C49}\iexplore |
| Operation: | write | Name: | Time |
Value: E2070500040018000C00160021001E02 | |||
Executable files
12
Suspicious files
1
Text files
7
Unknown types
4
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3228 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\2LKO8ICX\favicon[1].ico | — | |
MD5:— | SHA256:— | |||
| 3228 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\Internet Explorer\Services\search_{0633EE93-D776-472f-A0FF-E1416B8B2E3A}.ico | — | |
MD5:— | SHA256:— | |||
| 3228 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\~DFB65EBA1BE14ED244.TMP | — | |
MD5:— | SHA256:— | |||
| 3228 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\~DF47336C448E2747F1.TMP | — | |
MD5:— | SHA256:— | |||
| 3228 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Internet Explorer\Recovery\Active\RecoveryStore.{21CAE74D-5F4D-11E8-B27F-5254004AAD21}.dat | — | |
MD5:— | SHA256:— | |||
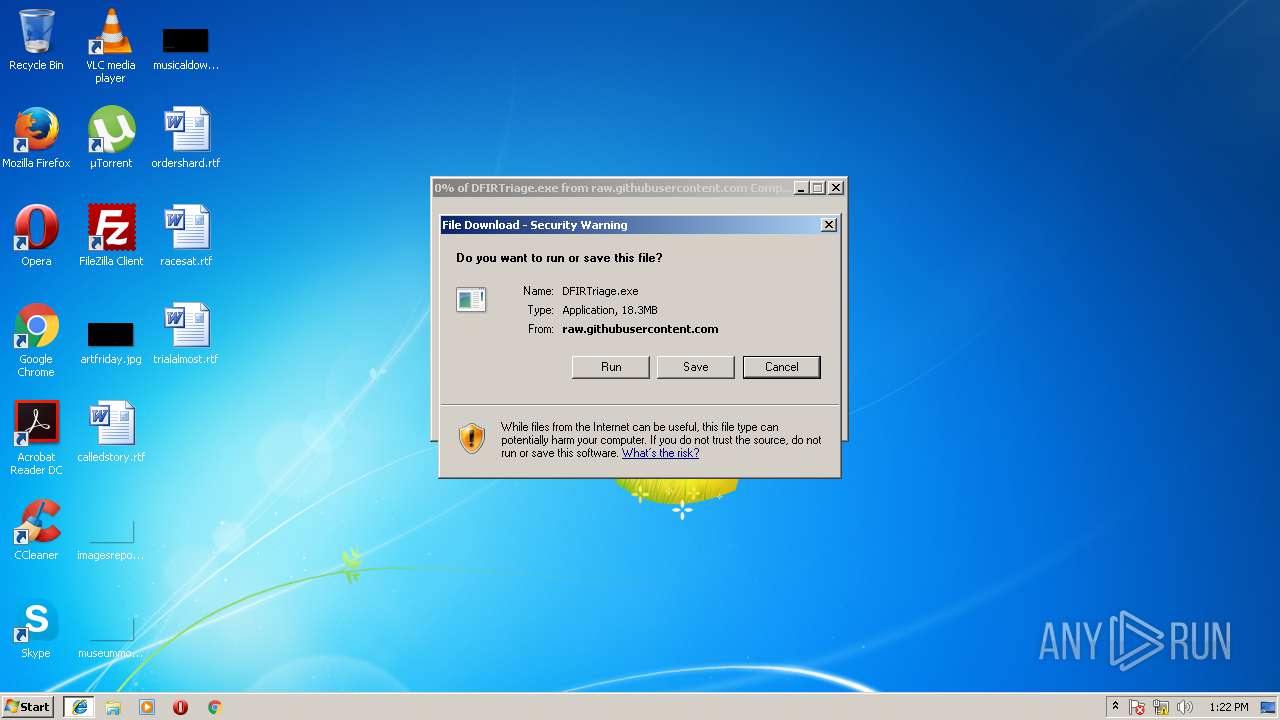
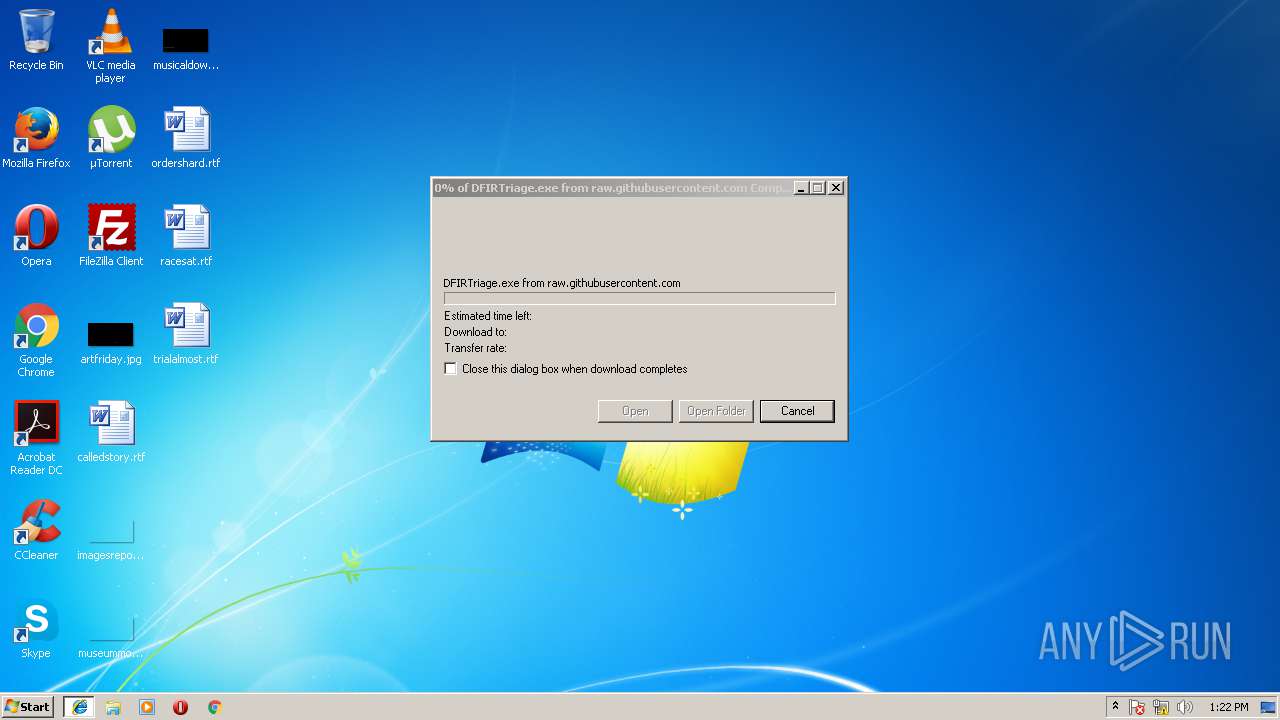
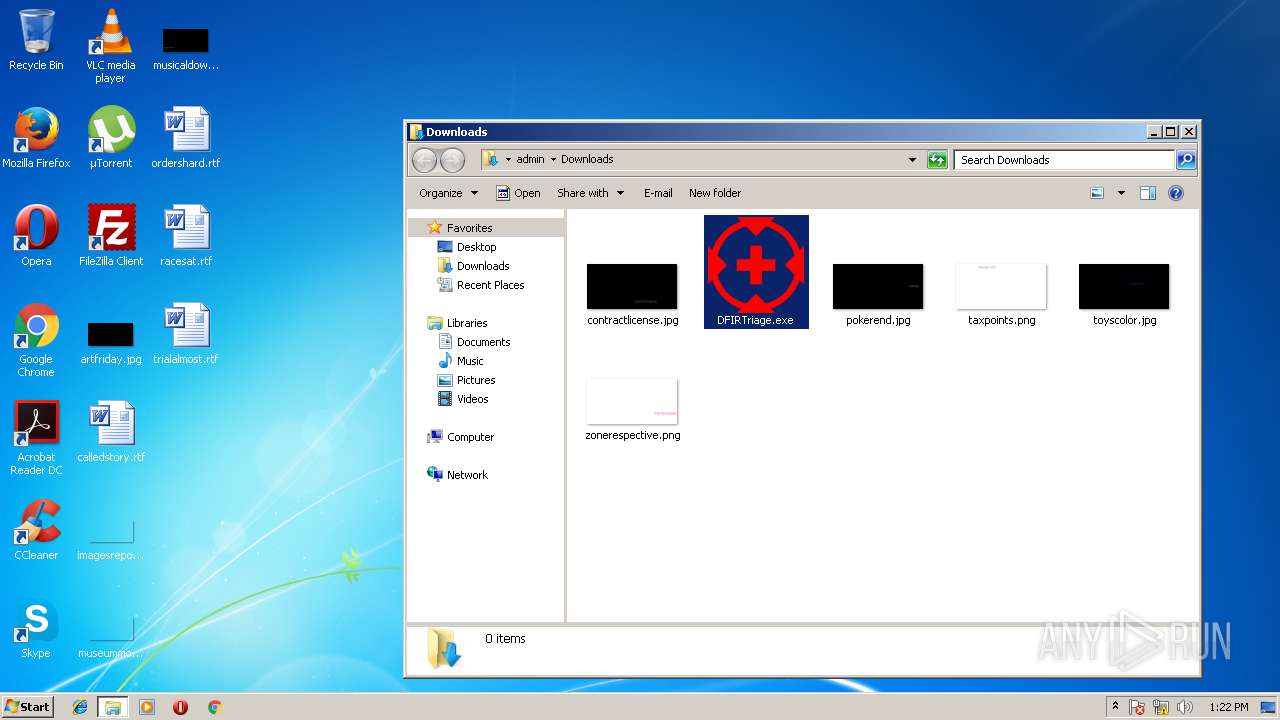
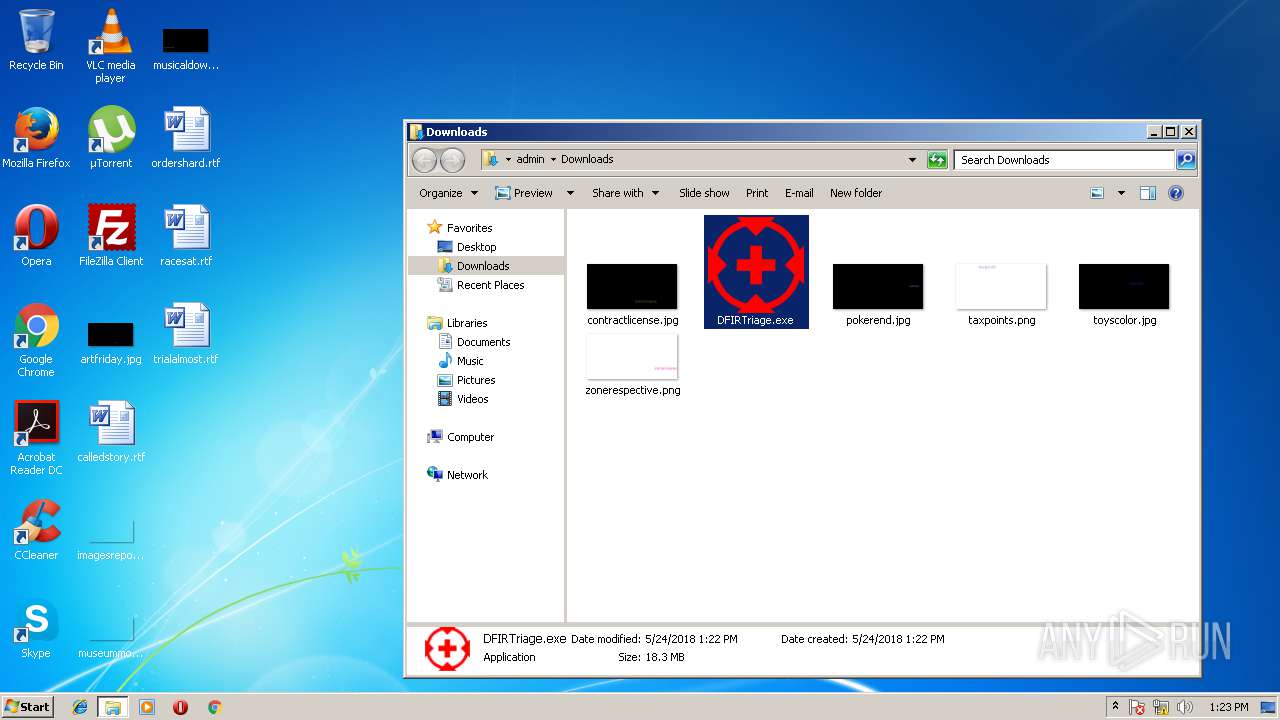
| 3228 | iexplore.exe | C:\Users\admin\Downloads\DFIRTriage.exe | executable | |
MD5:— | SHA256:— | |||
| 3228 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Internet Explorer\Recovery\Active\{21CAE74E-5F4D-11E8-B27F-5254004AAD21}.dat | binary | |
MD5:— | SHA256:— | |||
| 2708 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Low\Content.IE5\WF2FXMJU\DFIRTriage[1].exe | executable | |
MD5:— | SHA256:— | |||
| 3228 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\History\History.IE5\MSHist012018052420180525\index.dat | dat | |
MD5:— | SHA256:— | |||
| 2708 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\Low\JavaDeployReg.log | text | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
1
TCP/UDP connections
2
DNS requests
2
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3228 | iexplore.exe | GET | 200 | 204.79.197.200:80 | http://www.bing.com/favicon.ico | US | image | 237 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3228 | iexplore.exe | 204.79.197.200:80 | www.bing.com | Microsoft Corporation | US | whitelisted |
2708 | iexplore.exe | 151.101.0.133:443 | raw.githubusercontent.com | Fastly | US | malicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.bing.com |
| whitelisted |
raw.githubusercontent.com |
| shared |