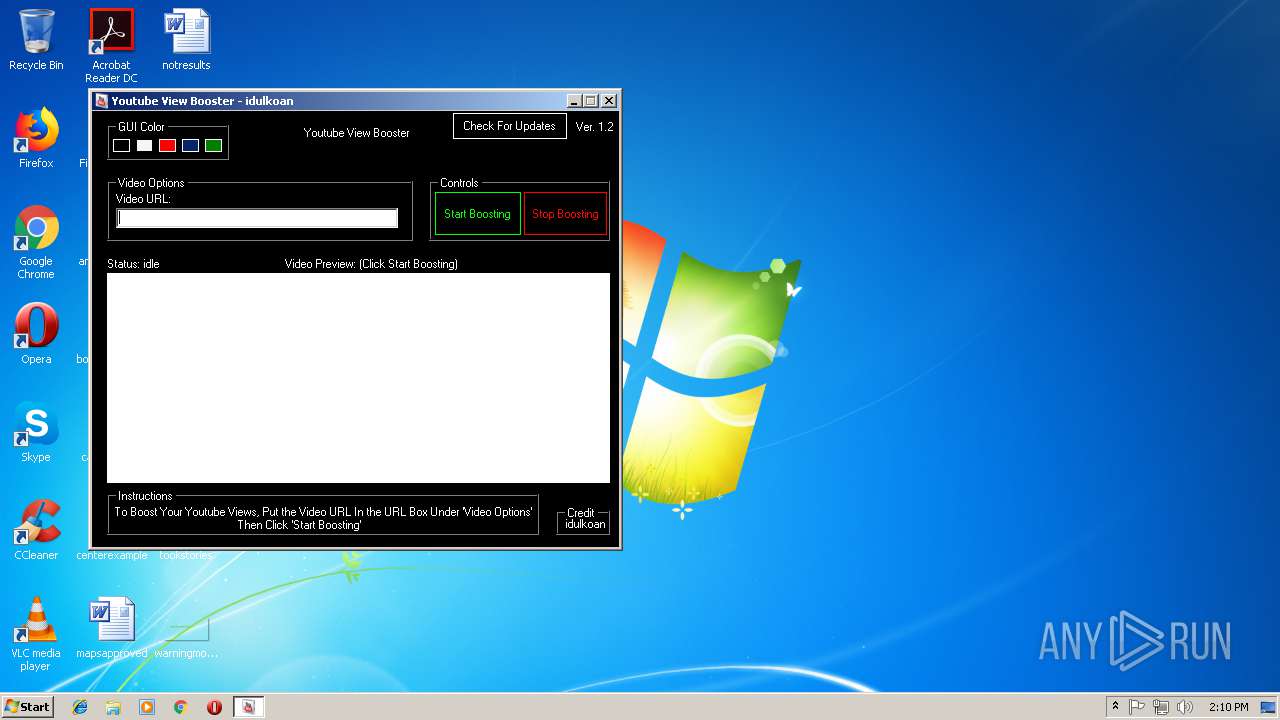
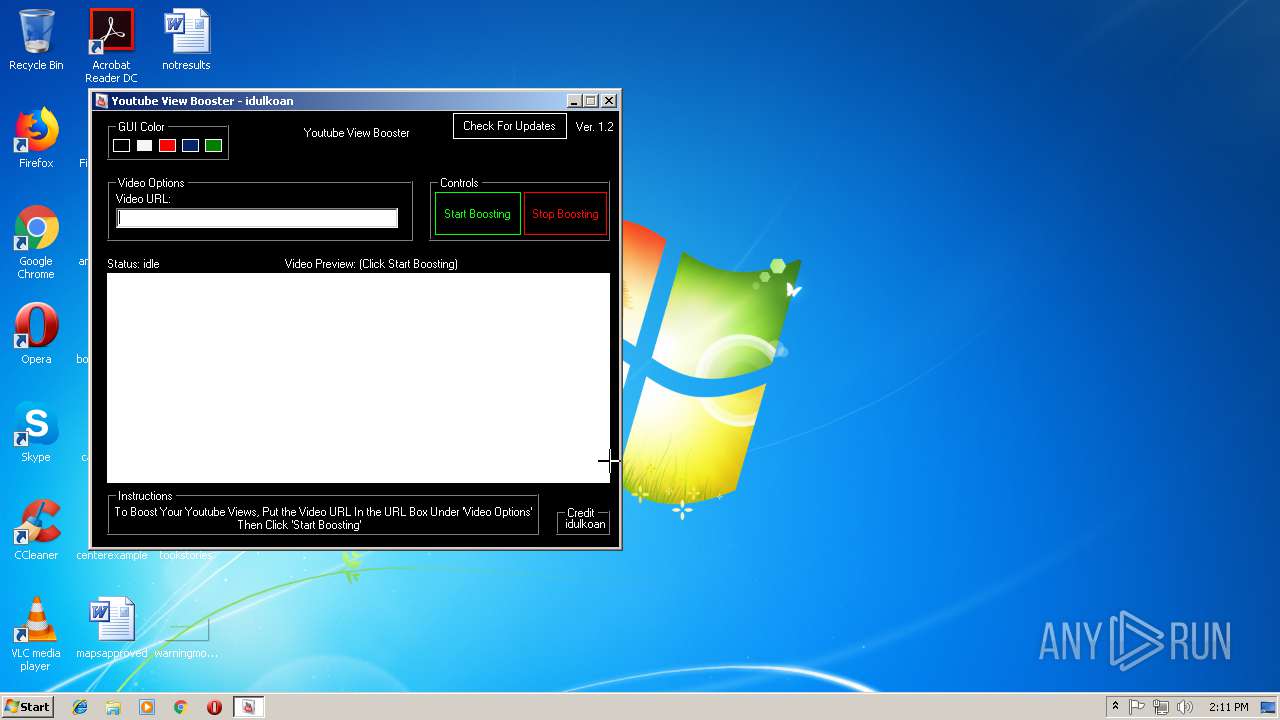
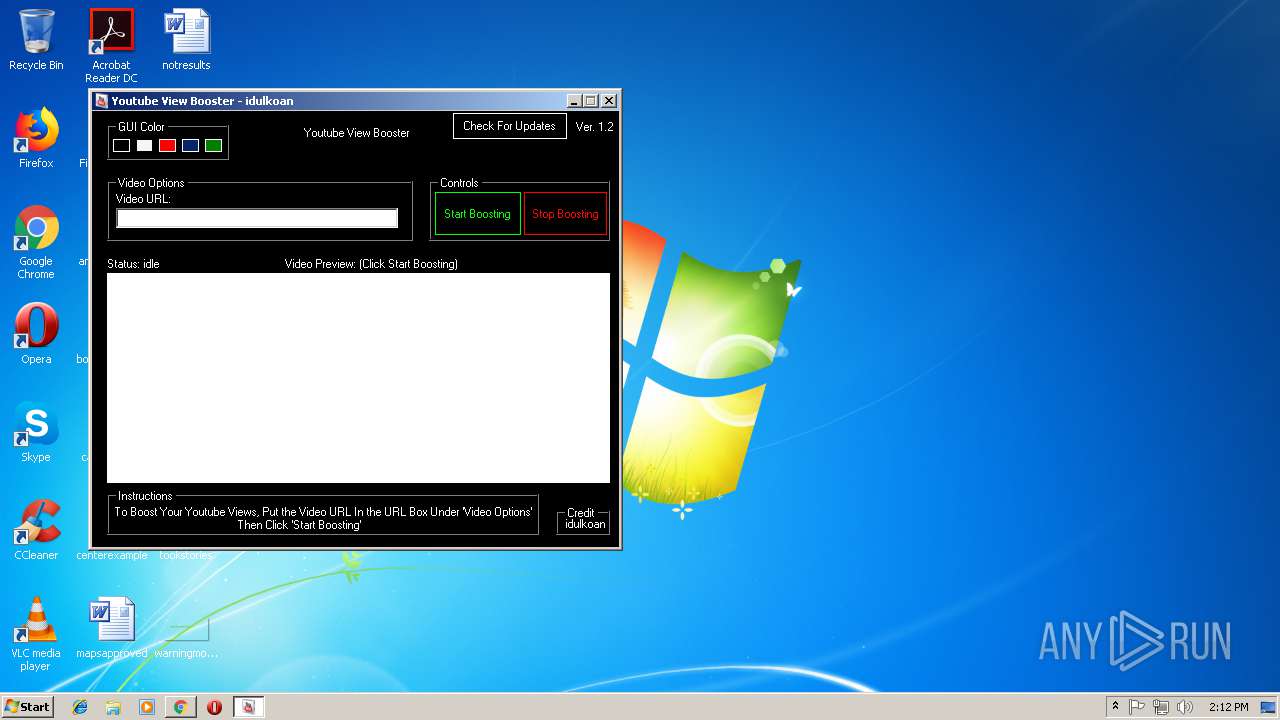
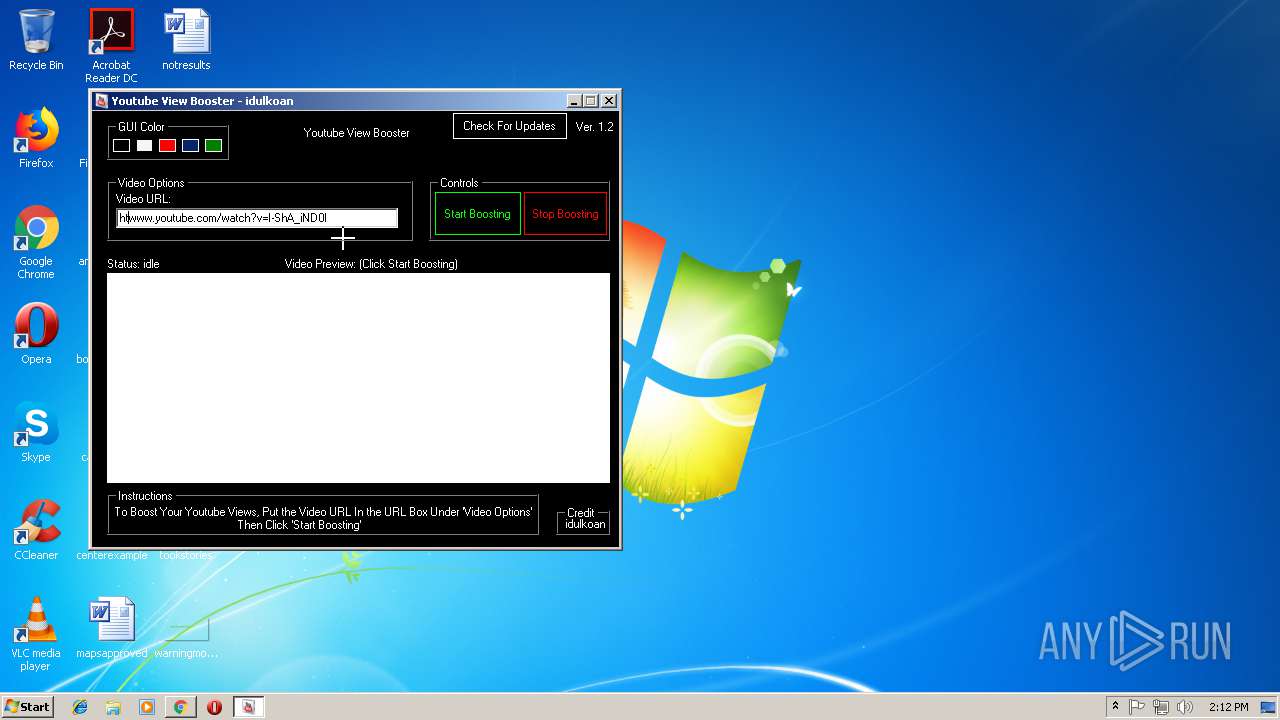
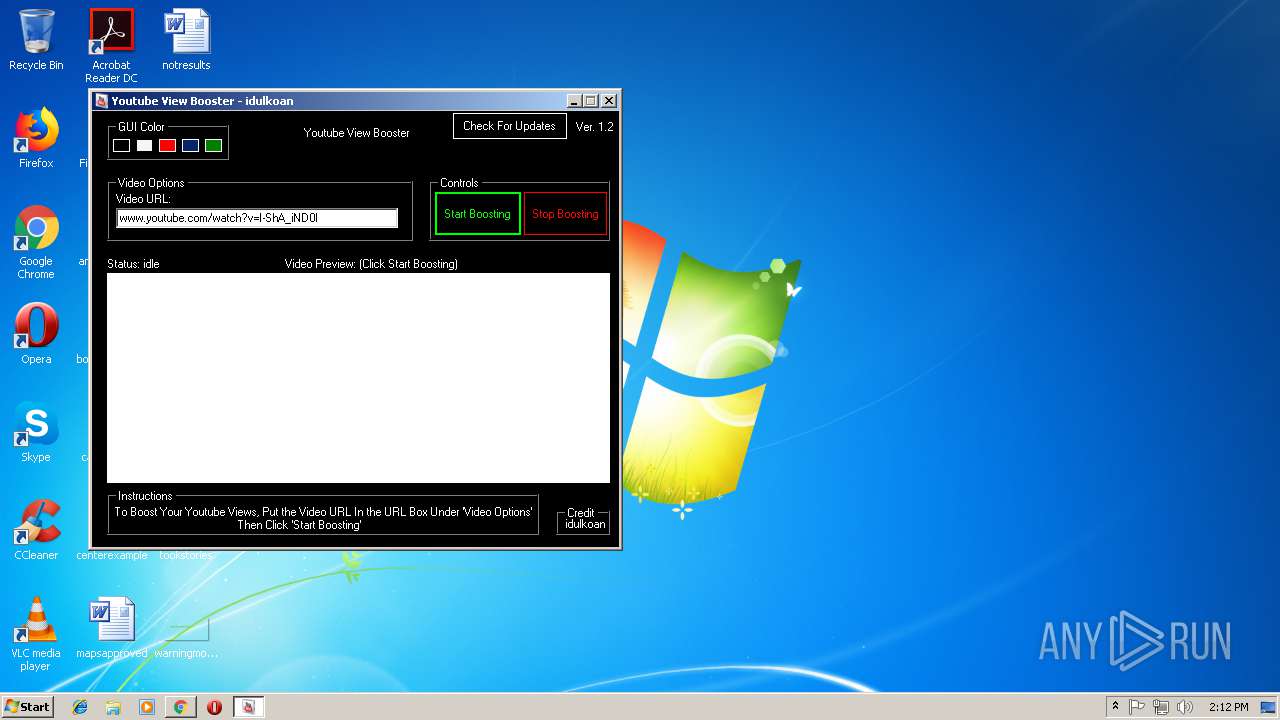
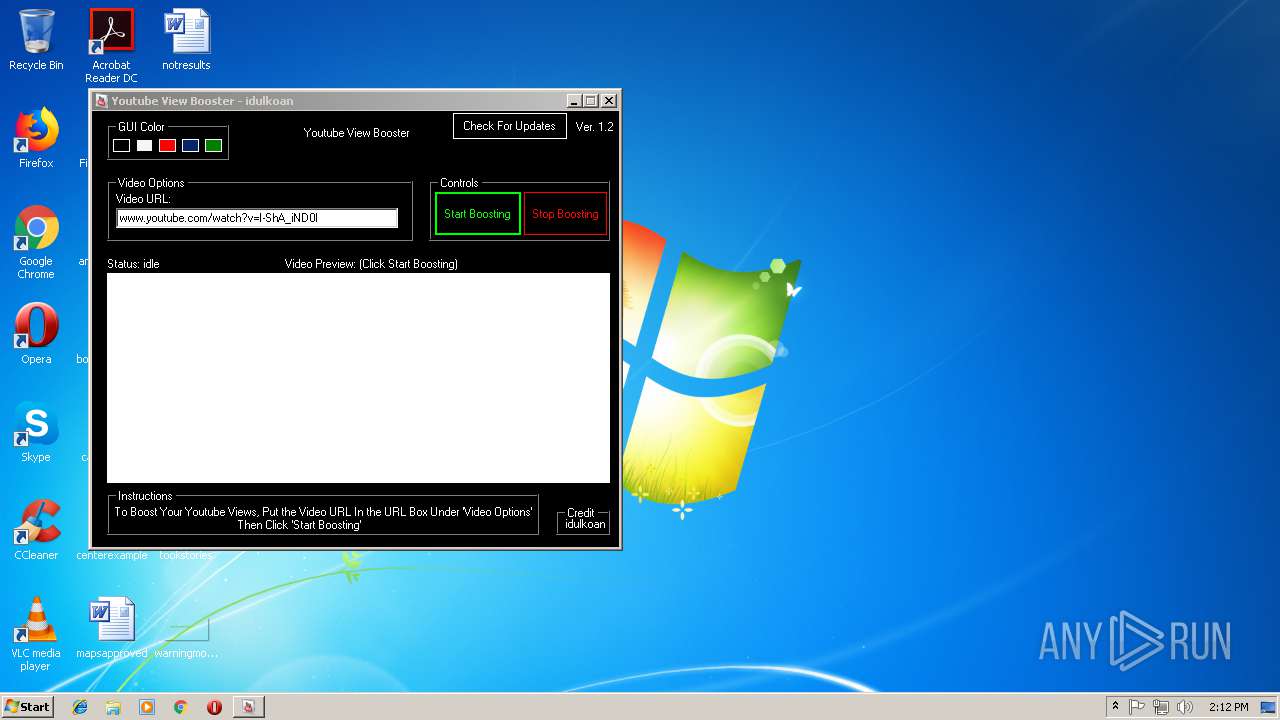
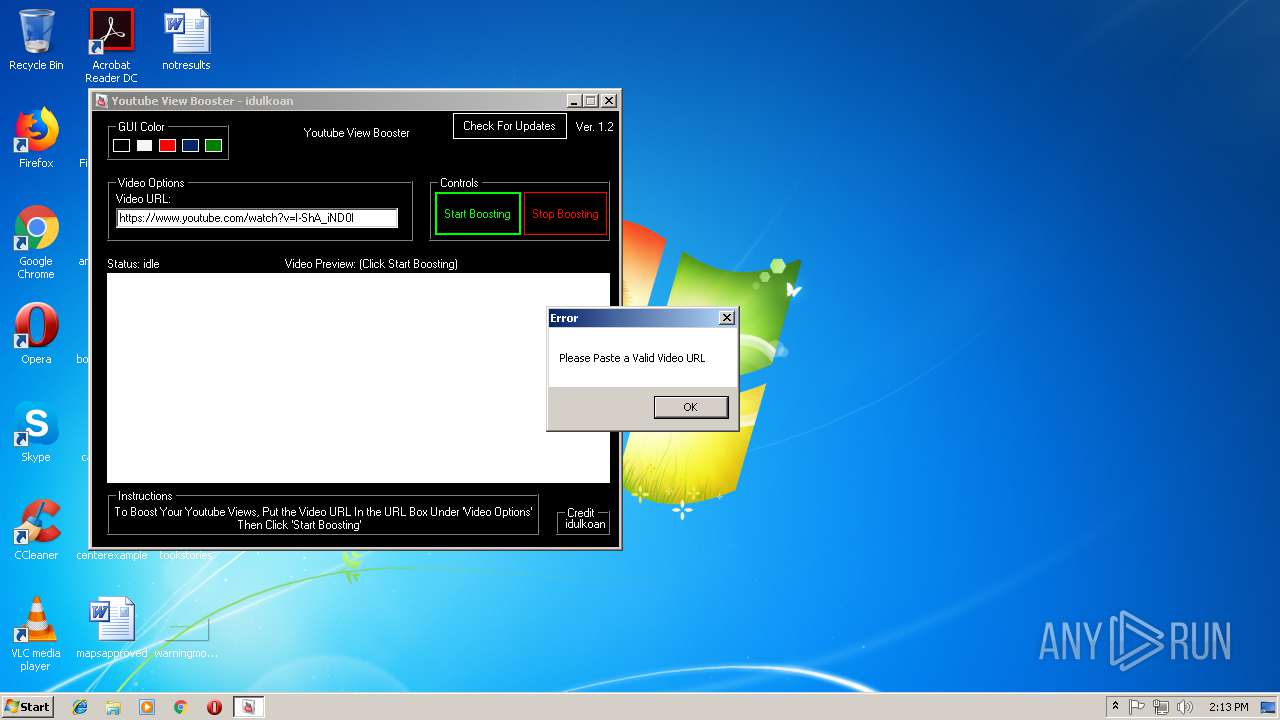
| File name: | YouTube View Booster.exe |
| Full analysis: | https://app.any.run/tasks/eeb3fed4-6c0e-414e-b543-23643cf42a58 |
| Verdict: | Malicious activity |
| Analysis date: | September 10, 2018, 13:10:38 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386 Mono/.Net assembly, for MS Windows |
| MD5: | 456773EF51F0E5F2877CE710386B7ADF |
| SHA1: | FDA7883AB598D85BF33A8CABDA44B42019974BD7 |
| SHA256: | 641FD5033E881C0F12ED901E66F4151D0392F9F31F079E0E4F5C0A8BB2EE061C |
| SSDEEP: | 6144:VPt2jWNPmHdBMpqs9mDTjQAidhaPt2jWNPmHdBMpqs9mDTjQAidhMGPqVrY2hrFk:VPt2jWN+OHJMPt2jWN+OHJ3SVr72 |
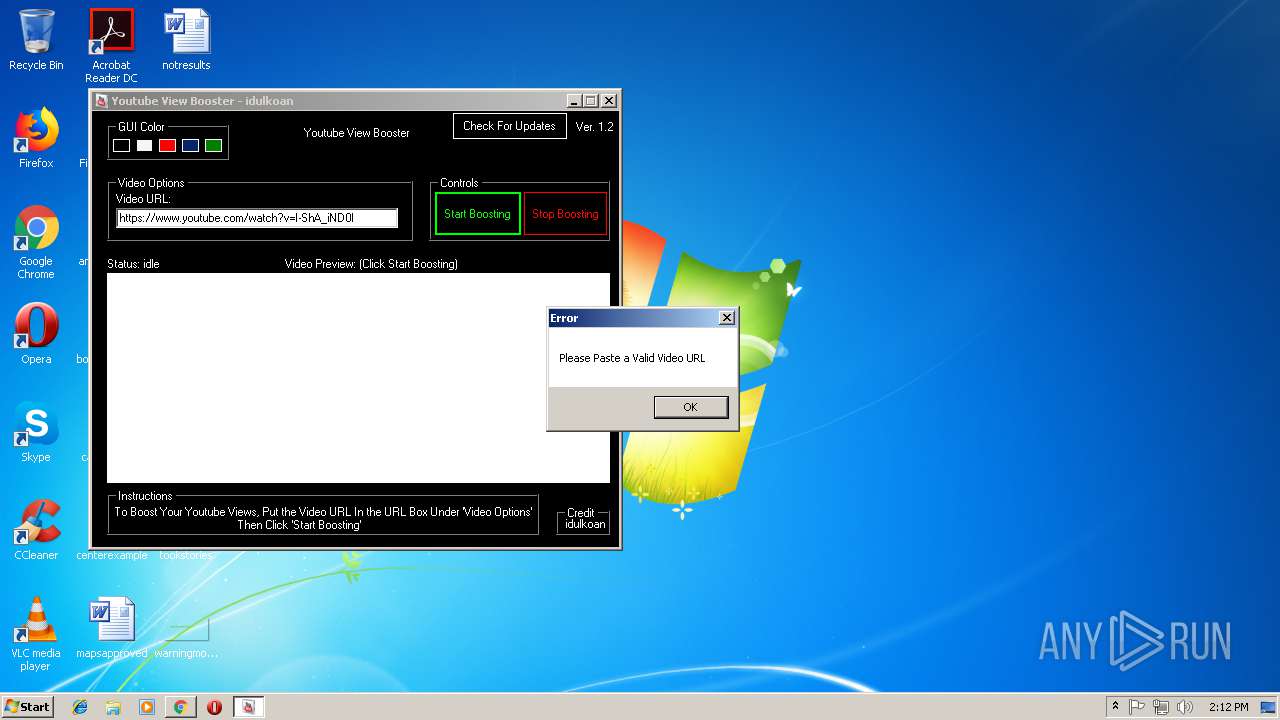
MALICIOUS
Loads dropped or rewritten executable
- software_reporter_tool.exe (PID: 272)
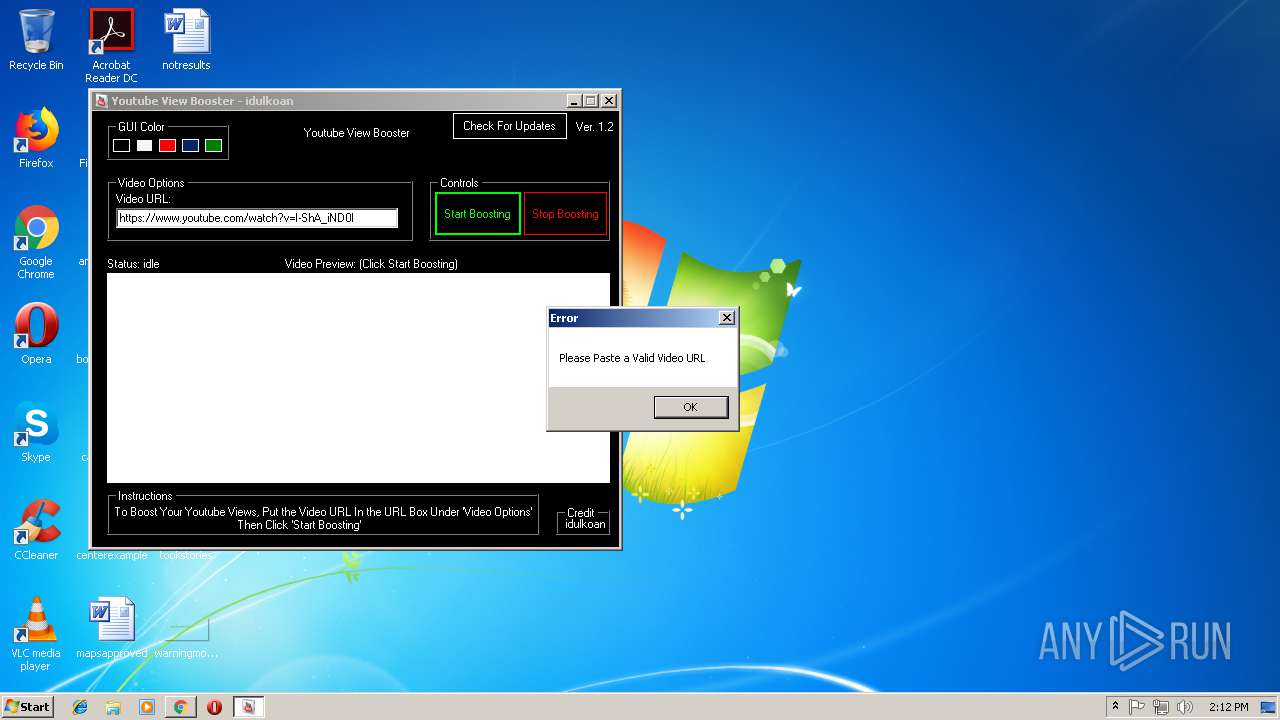
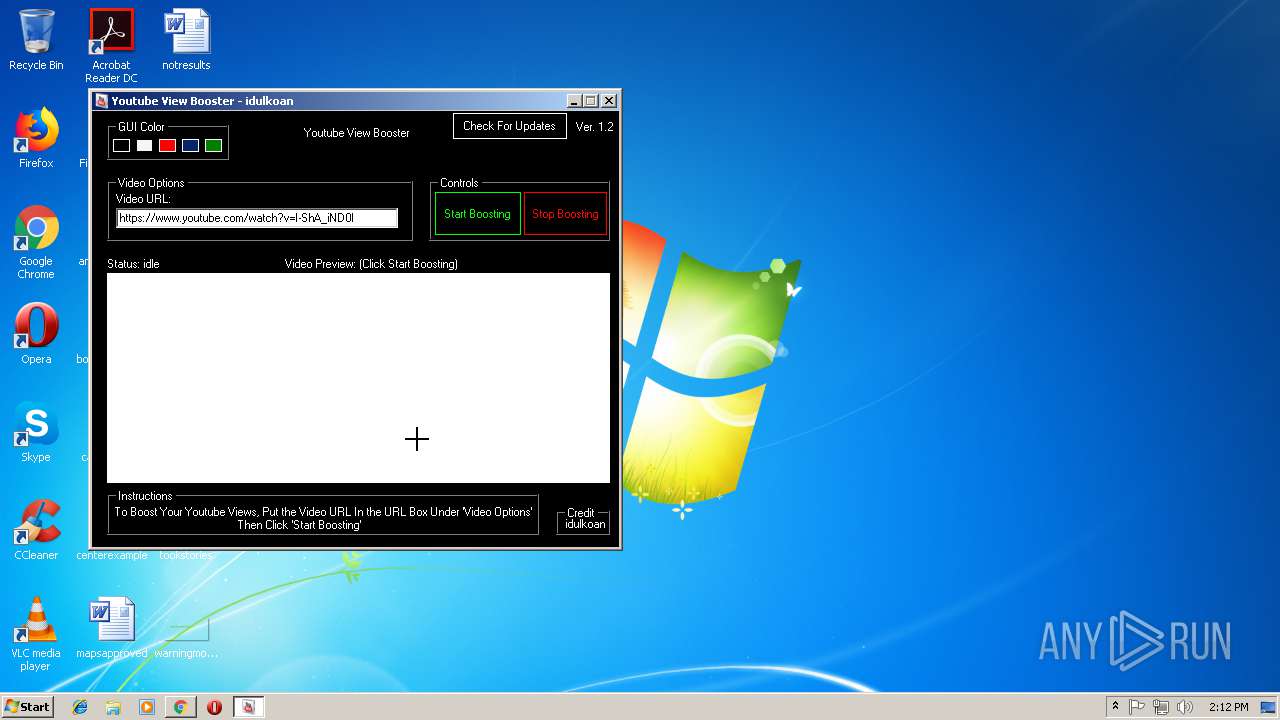
SUSPICIOUS
Reads internet explorer settings
- YouTube View Booster.exe (PID: 1072)
Executable content was dropped or overwritten
- software_reporter_tool.exe (PID: 272)
Creates files in the user directory
- YouTube View Booster.exe (PID: 1072)
Application launched itself
- software_reporter_tool.exe (PID: 1476)
Searches for installed software
- software_reporter_tool.exe (PID: 272)
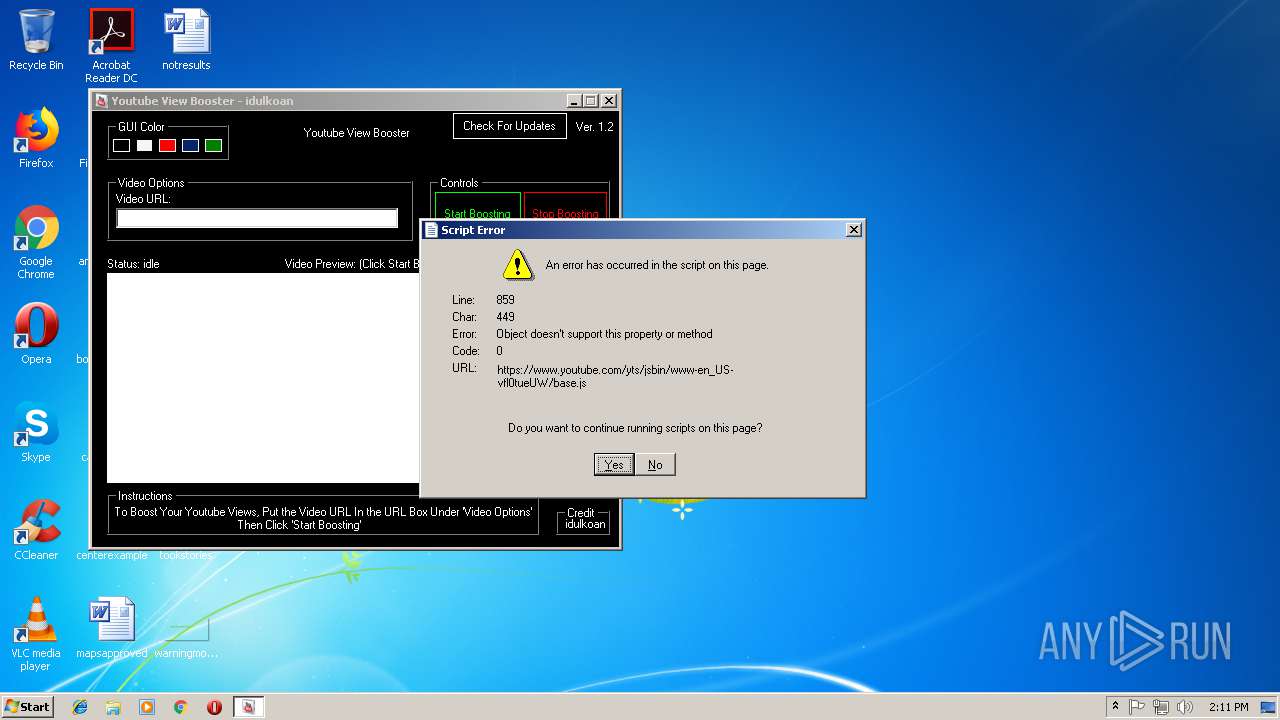
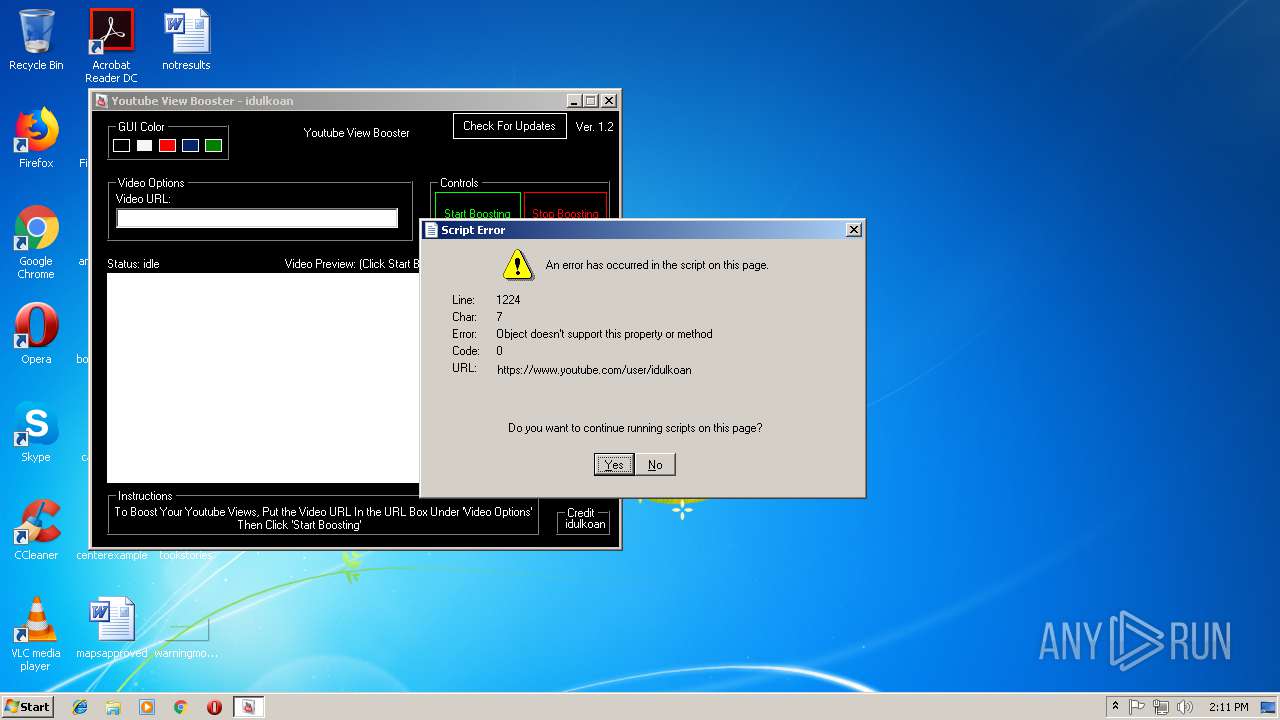
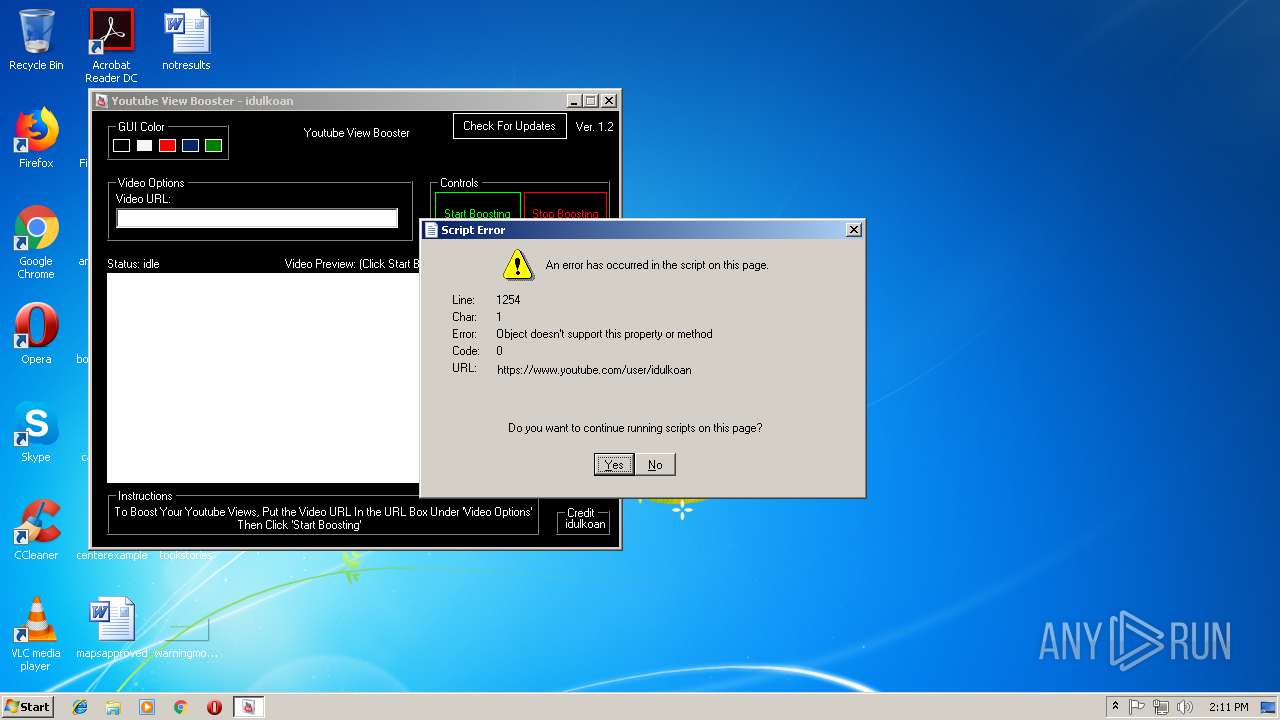
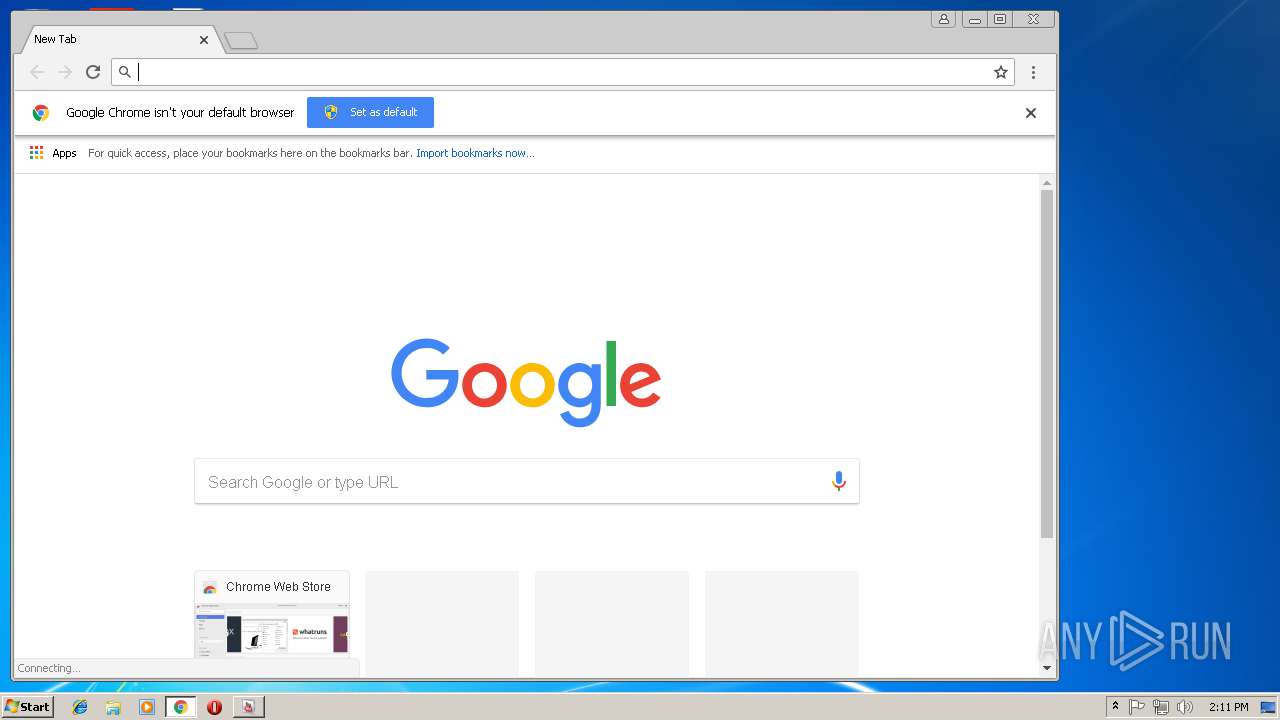
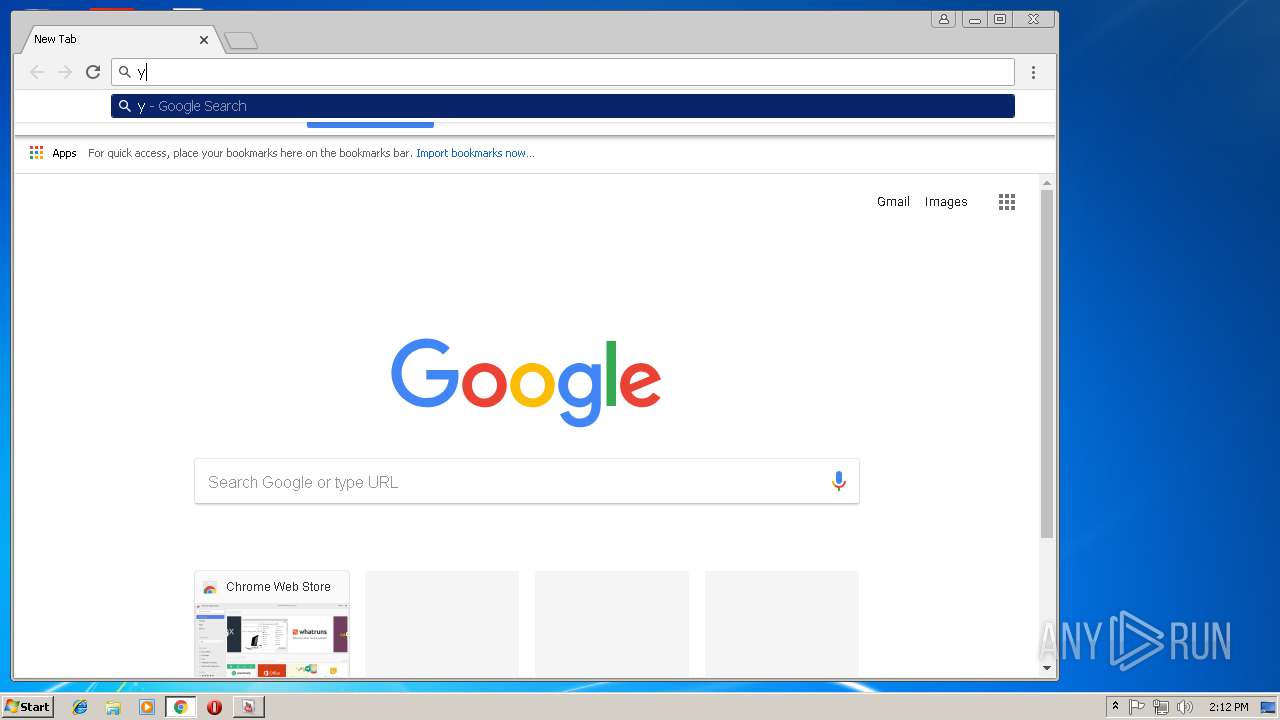
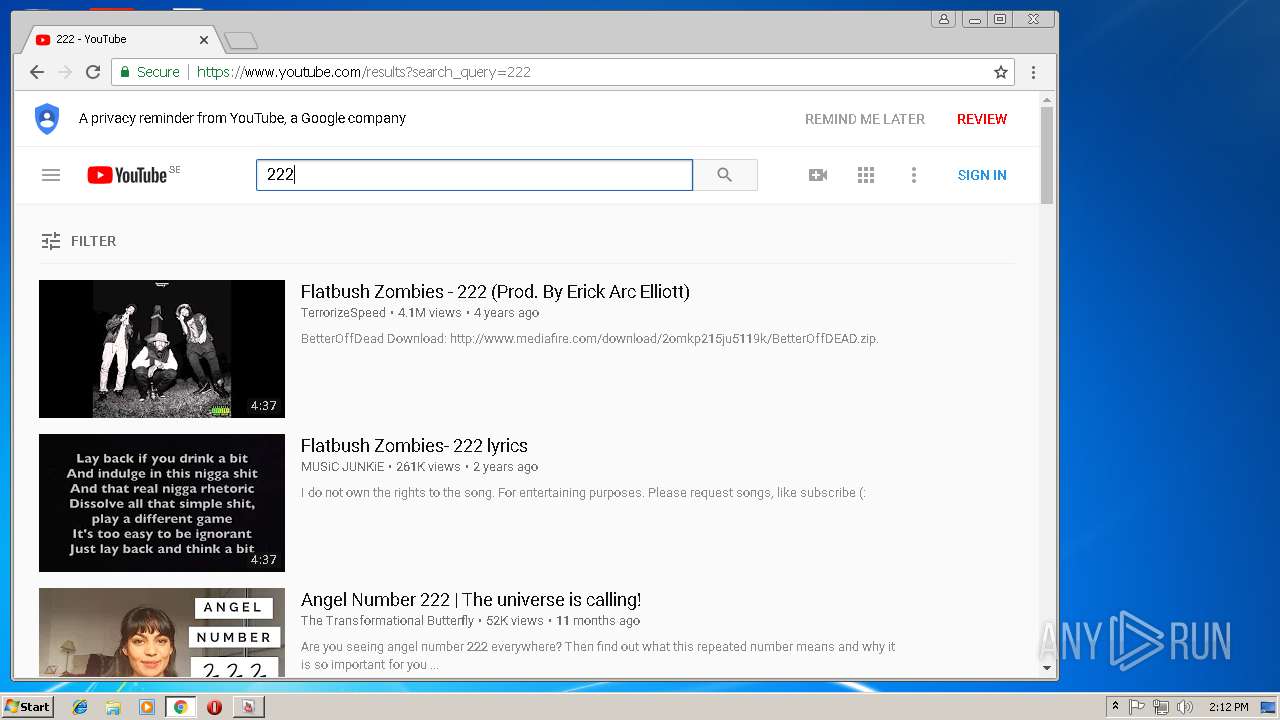
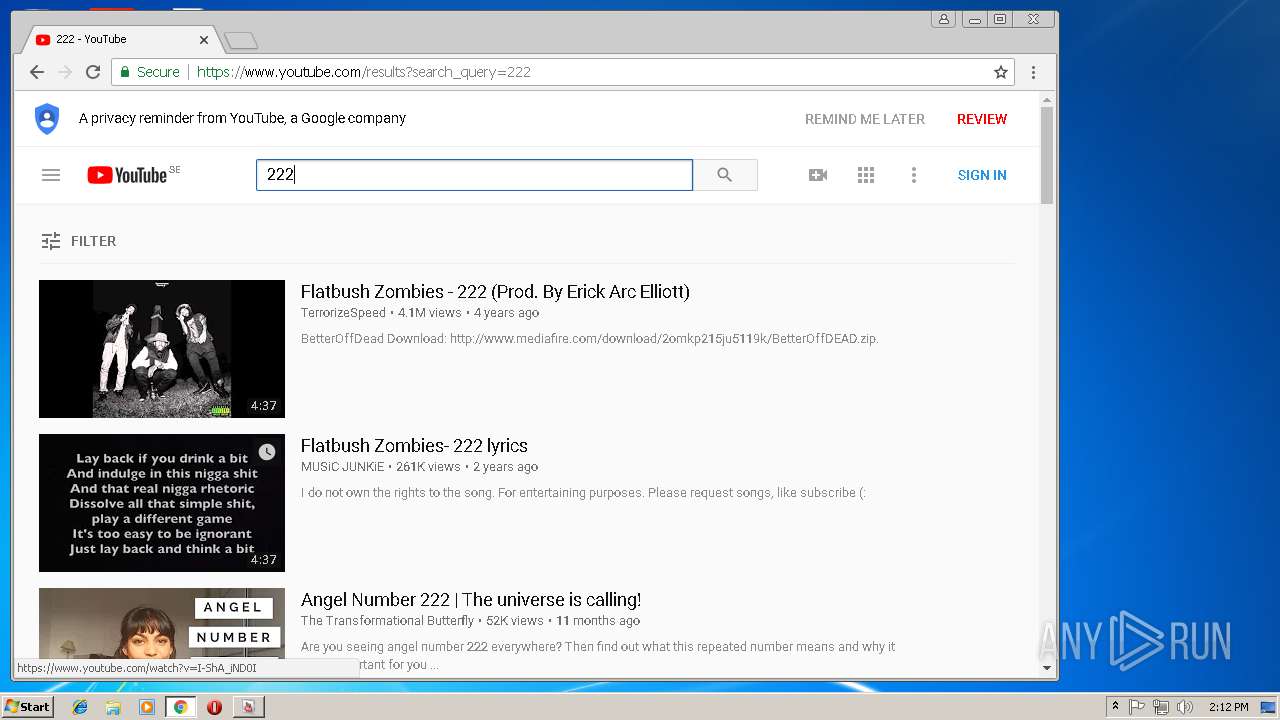
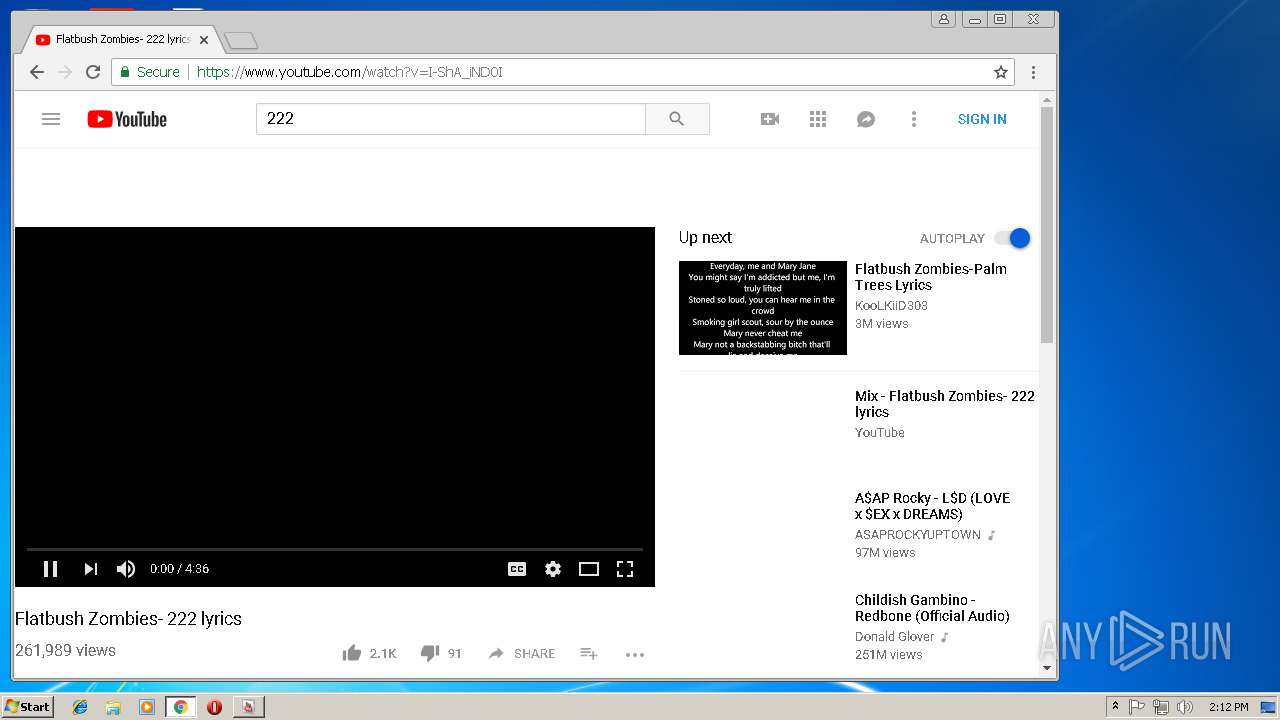
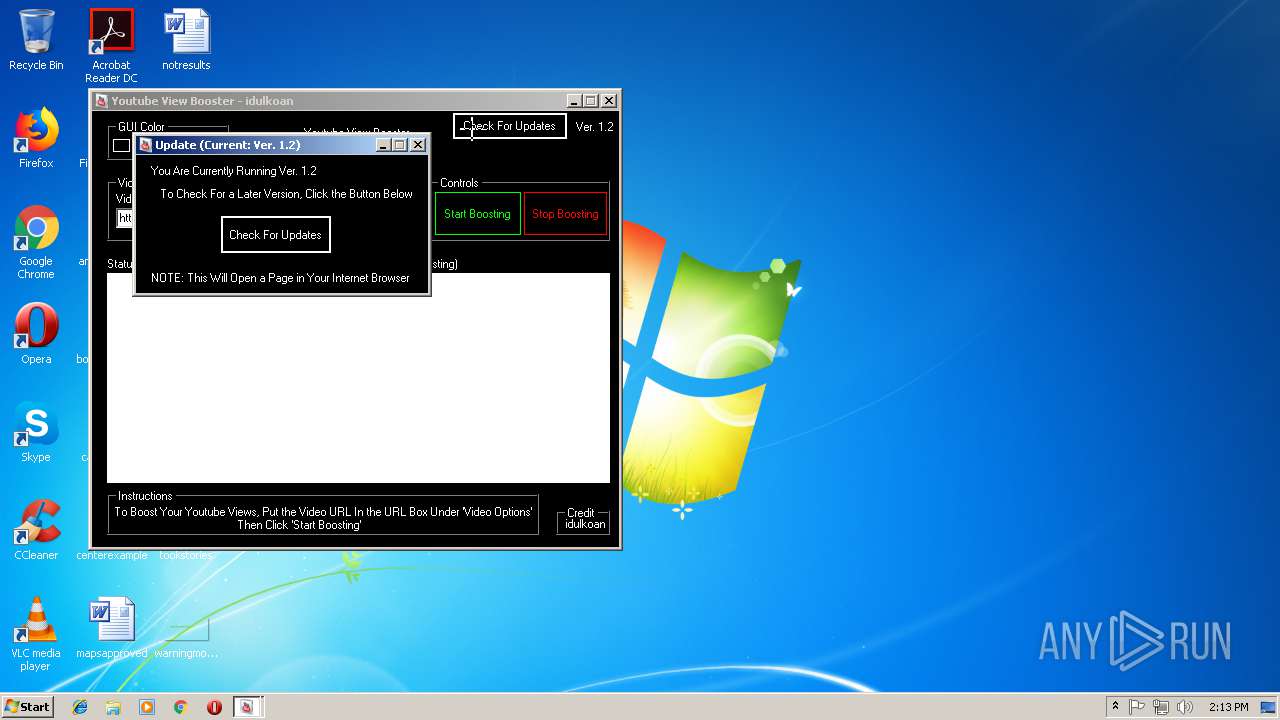
Starts Internet Explorer
- YouTube View Booster.exe (PID: 1072)
INFO
Application launched itself
- chrome.exe (PID: 3128)
Reads settings of System Certificates
- chrome.exe (PID: 3128)
- iexplore.exe (PID: 4016)
Loads the Task Scheduler COM API
- software_reporter_tool.exe (PID: 1476)
- software_reporter_tool.exe (PID: 2148)
Reads internet explorer settings
- iexplore.exe (PID: 4016)
Changes internet zones settings
- iexplore.exe (PID: 3348)
Reads Internet Cache Settings
- iexplore.exe (PID: 4016)
Creates files in the user directory
- iexplore.exe (PID: 4016)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Generic CIL Executable (.NET, Mono, etc.) (55.8) |
|---|---|---|
| .exe | | | Win64 Executable (generic) (21) |
| .scr | | | Windows screen saver (9.9) |
| .dll | | | Win32 Dynamic Link Library (generic) (5) |
| .exe | | | Win32 Executable (generic) (3.4) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2011:05:22 02:17:12+02:00 |
| PEType: | PE32 |
| LinkerVersion: | 8 |
| CodeSize: | 575488 |
| InitializedDataSize: | 373248 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x8e79e |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 4 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 1.0.0.0 |
| ProductVersionNumber: | 1.0.0.0 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Win32 |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | Neutral |
| CharacterSet: | Unicode |
| CompanyName: | Proactive QA Solutions |
| FileDescription: | WindowsApplication1 |
| FileVersion: | 1.0.0.0 |
| InternalName: | Youtube View Booster By idulkoan.exe |
| LegalCopyright: | Copyright © Proactive QA Solutions 2011 |
| OriginalFileName: | Youtube View Booster By idulkoan.exe |
| ProductName: | WindowsApplication1 |
| ProductVersion: | 1.0.0.0 |
| AssemblyVersion: | 1.0.0.0 |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 22-May-2011 00:17:12 |
| Debug artifacts: |
|
| CompanyName: | Proactive QA Solutions |
| FileDescription: | WindowsApplication1 |
| FileVersion: | 1.0.0.0 |
| InternalName: | Youtube View Booster By idulkoan.exe |
| LegalCopyright: | Copyright © Proactive QA Solutions 2011 |
| OriginalFilename: | Youtube View Booster By idulkoan.exe |
| ProductName: | WindowsApplication1 |
| ProductVersion: | 1.0.0.0 |
| Assembly Version: | 1.0.0.0 |
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x00000080 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 4 |
| Time date stamp: | 22-May-2011 00:17:12 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00002000 | 0x0008C7A4 | 0x0008C800 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 5.1927 |
.sdata | 0x00090000 | 0x000000FC | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 3.29965 |
.rsrc | 0x00092000 | 0x0005AD58 | 0x0005AE00 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 4.63203 |
.reloc | 0x000EE000 | 0x0000000C | 0x00000200 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_DISCARDABLE, IMAGE_SCN_MEM_READ | 0.10191 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.00112 | 490 | UNKNOWN | UNKNOWN | RT_MANIFEST |
2 | 4.83522 | 1128 | UNKNOWN | UNKNOWN | RT_ICON |
3 | 4.93964 | 4264 | UNKNOWN | UNKNOWN | RT_ICON |
4 | 4.81482 | 9640 | UNKNOWN | UNKNOWN | RT_ICON |
5 | 4.7364 | 16936 | UNKNOWN | UNKNOWN | RT_ICON |
6 | 4.63338 | 67624 | UNKNOWN | UNKNOWN | RT_ICON |
7 | 4.57133 | 270376 | UNKNOWN | UNKNOWN | RT_ICON |
32512 | 2.81543 | 90 | UNKNOWN | UNKNOWN | RT_GROUP_ICON |
Imports
mscoree.dll |
Total processes
55
Monitored processes
23
Malicious processes
1
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 272 | "c:\users\admin\appdata\local\google\chrome\user data\swreporter\33.170.201\software_reporter_tool.exe" --use-crash-handler-with-id="\\.\pipe\crashpad_2148_SXAYRGUUHXRKDUIV" --sandboxed-process-id=2 --init-done-notifier=344 --sandbox-mojo-pipe-token=1A51837CC75362AE8306BEEBDF71AE25 --mojo-platform-channel-handle=280 --engine=2 | c:\users\admin\appdata\local\google\chrome\user data\swreporter\33.170.201\software_reporter_tool.exe | software_reporter_tool.exe | ||||||||||||
User: admin Company: Google Integrity Level: MEDIUM Description: Software Reporter Tool Exit code: 1 Version: 33.170.201 Modules
| |||||||||||||||
| 1072 | "C:\Users\admin\AppData\Local\Temp\YouTube View Booster.exe" | C:\Users\admin\AppData\Local\Temp\YouTube View Booster.exe | explorer.exe | ||||||||||||
User: admin Company: Proactive QA Solutions Integrity Level: MEDIUM Description: WindowsApplication1 Exit code: 0 Version: 1.0.0.0 Modules
| |||||||||||||||
| 1088 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=956,1690638638439552184,8443914666595302215,131072 --enable-features=PasswordImport --gpu-preferences=KAAAAAAAAACAAwBAAQAAAAAAAAAAAGAAEAAAAAAAAAAAAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAKAAAAEAAAAAAAAAAAAAAACwAAABAAAAAAAAAAAQAAAAoAAAAQAAAAAAAAAAEAAAALAAAA --service-request-channel-token=74CFFD8800F56ED6BFAA4DC5FAF1C02E --mojo-platform-channel-handle=964 --ignored=" --type=renderer " /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 1256 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=956,1690638638439552184,8443914666595302215,131072 --enable-features=PasswordImport --service-pipe-token=A132E34A7492E1149CA4C17EA6EAFD3C --lang=en-US --extension-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=A132E34A7492E1149CA4C17EA6EAFD3C --renderer-client-id=3 --mojo-platform-channel-handle=2084 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 1476 | "C:\Users\admin\AppData\Local\Google\Chrome\User Data\SwReporter\33.170.201\software_reporter_tool.exe" --session-id=Atb95LT3kIXMd7ekj9HqGfJ7dSuxbEoGcj4sO/ay --registry-suffix=URZA --srt-field-trial-group-name=NewCleanerUIExperiment | C:\Users\admin\AppData\Local\Google\Chrome\User Data\SwReporter\33.170.201\software_reporter_tool.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Integrity Level: MEDIUM Description: Software Reporter Tool Exit code: 2 Version: 33.170.201 Modules
| |||||||||||||||
| 1600 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=956,1690638638439552184,8443914666595302215,131072 --enable-features=PasswordImport --lang=en-US --no-sandbox --service-request-channel-token=85F2B0E41E78C3A45A47C4EDBD4427FC --mojo-platform-channel-handle=4332 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 1672 | "c:\users\admin\appdata\local\google\chrome\user data\swreporter\33.170.201\software_reporter_tool.exe" --crash-handler "--database=c:\users\admin\appdata\local\Google\Software Reporter Tool" --url=https://clients2.google.com/cr/report --annotation=plat=Win32 --annotation=prod=ChromeFoil --annotation=ver=33.170.201 --initial-client-data=0xe4,0xec,0xf0,0xe8,0xf4,0x424c10,0x424c20,0x424c2c | c:\users\admin\appdata\local\google\chrome\user data\swreporter\33.170.201\software_reporter_tool.exe | — | software_reporter_tool.exe | |||||||||||
User: admin Company: Google Integrity Level: MEDIUM Description: Software Reporter Tool Exit code: 0 Version: 33.170.201 Modules
| |||||||||||||||
| 1824 | "c:\users\admin\appdata\local\google\chrome\user data\swreporter\33.170.201\software_reporter_tool.exe" --crash-handler "--database=c:\users\admin\appdata\local\Google\Software Reporter Tool" --url=https://clients2.google.com/cr/report --annotation=plat=Win32 --annotation=prod=ChromeFoil --annotation=ver=33.170.201 --initial-client-data=0xe4,0xec,0xf0,0xe8,0xf4,0x424c10,0x424c20,0x424c2c | c:\users\admin\appdata\local\google\chrome\user data\swreporter\33.170.201\software_reporter_tool.exe | — | software_reporter_tool.exe | |||||||||||
User: admin Company: Google Integrity Level: MEDIUM Description: Software Reporter Tool Exit code: 0 Version: 33.170.201 Modules
| |||||||||||||||
| 1860 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=956,1690638638439552184,8443914666595302215,131072 --enable-features=PasswordImport --disable-gpu-compositing --service-pipe-token=8944283C207CE23C9580FB7D4063C13E --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=8944283C207CE23C9580FB7D4063C13E --renderer-client-id=11 --mojo-platform-channel-handle=4432 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
| 2020 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=956,1690638638439552184,8443914666595302215,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=D986F11288999561ED4FD71C23563F70 --mojo-platform-channel-handle=4308 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 68.0.3440.106 Modules
| |||||||||||||||
Total events
1 680
Read events
1 454
Write events
214
Delete events
12
Modification events
| (PID) Process: | (1072) YouTube View Booster.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (1072) YouTube View Booster.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (1072) YouTube View Booster.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\YouTube View Booster_RASAPI32 |
| Operation: | write | Name: | EnableFileTracing |
Value: 0 | |||
| (PID) Process: | (1072) YouTube View Booster.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\YouTube View Booster_RASAPI32 |
| Operation: | write | Name: | EnableConsoleTracing |
Value: 0 | |||
| (PID) Process: | (1072) YouTube View Booster.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\YouTube View Booster_RASAPI32 |
| Operation: | write | Name: | FileTracingMask |
Value: 4294901760 | |||
| (PID) Process: | (1072) YouTube View Booster.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\YouTube View Booster_RASAPI32 |
| Operation: | write | Name: | ConsoleTracingMask |
Value: 4294901760 | |||
| (PID) Process: | (1072) YouTube View Booster.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\YouTube View Booster_RASAPI32 |
| Operation: | write | Name: | MaxFileSize |
Value: 1048576 | |||
| (PID) Process: | (1072) YouTube View Booster.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\YouTube View Booster_RASAPI32 |
| Operation: | write | Name: | FileDirectory |
Value: %windir%\tracing | |||
| (PID) Process: | (1072) YouTube View Booster.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\YouTube View Booster_RASMANCS |
| Operation: | write | Name: | EnableFileTracing |
Value: 0 | |||
| (PID) Process: | (1072) YouTube View Booster.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Tracing\YouTube View Booster_RASMANCS |
| Operation: | write | Name: | EnableConsoleTracing |
Value: 0 | |||
Executable files
7
Suspicious files
89
Text files
134
Unknown types
18
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1072 | YouTube View Booster.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\admin@youtube[2].txt | — | |
MD5:— | SHA256:— | |||
| 1072 | YouTube View Booster.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\0UU90R59\www-core-vfly_6Bdv[1].css | text | |
MD5:— | SHA256:— | |||
| 1072 | YouTube View Booster.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\admin@youtube[1].txt | text | |
MD5:— | SHA256:— | |||
| 1072 | YouTube View Booster.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\R9ZEWH8D\unnamed[1].jpg | image | |
MD5:— | SHA256:— | |||
| 1072 | YouTube View Booster.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\R9ZEWH8D\www-guide-vflNDDMf7[1].css | text | |
MD5:— | SHA256:— | |||
| 1072 | YouTube View Booster.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\R9ZEWH8D\spf[1].js | text | |
MD5:— | SHA256:— | |||
| 1072 | YouTube View Booster.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\0UU90R59\KFOjCnqEu92Fr1Mu51S7ACc6CsA[1].eot | eot | |
MD5:3D24765047E383A80652F464D8D8DC34 | SHA256:54412FAEB9ED658523D5BAC0FDC02A6D59285621062FC5F4FDBECACCA2C7DFC4 | |||
| 1072 | YouTube View Booster.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\RB73MZ6Y\www-pageframe-vfl2QekqP[1].css | text | |
MD5:— | SHA256:— | |||
| 1072 | YouTube View Booster.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\R9ZEWH8D\www-home-c4-vflopQeuE[1].css | text | |
MD5:— | SHA256:— | |||
| 1072 | YouTube View Booster.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\R9ZEWH8D\scheduler[1].js | text | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
6
TCP/UDP connections
96
DNS requests
42
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
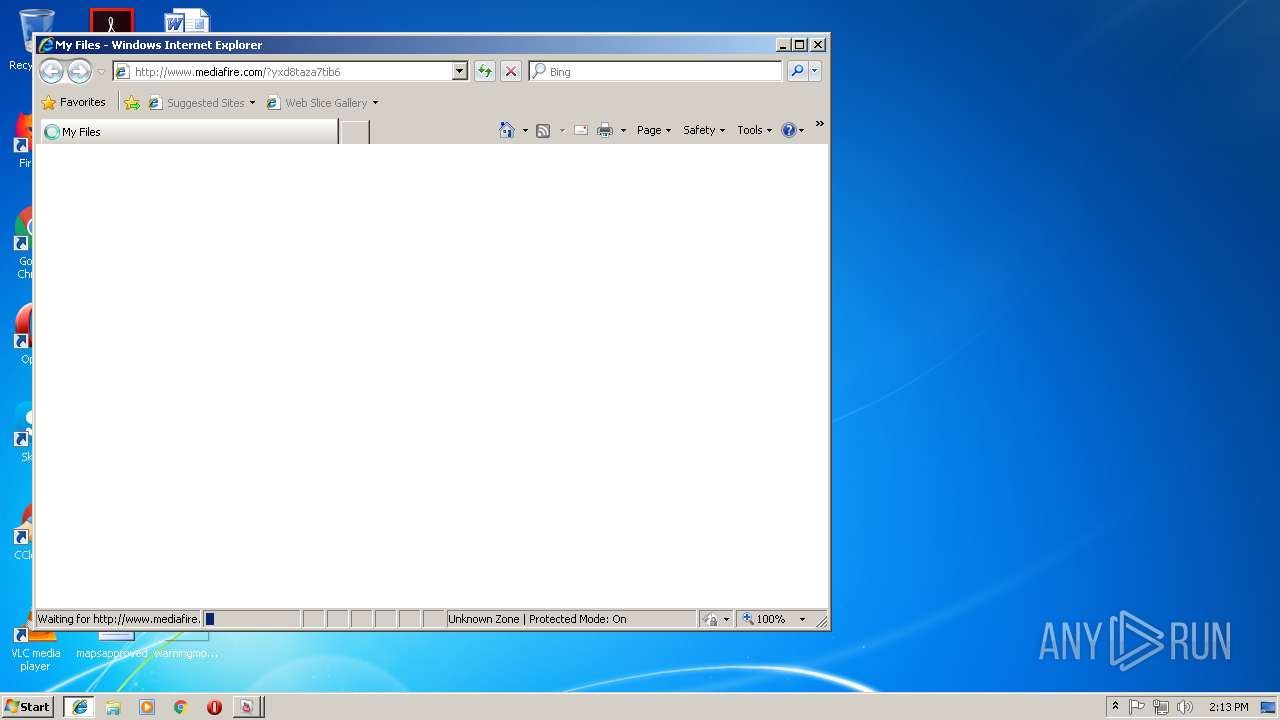
4016 | iexplore.exe | GET | — | 104.19.195.29:80 | http://static.mediafire.com/css/mfv4_120533.php?ver=nonssl&date=2018-09-10 | US | — | — | shared |
4016 | iexplore.exe | GET | — | 104.19.195.29:80 | http://static.mediafire.com/css/mfv3_120533.php?ver=nonssl | US | — | — | shared |
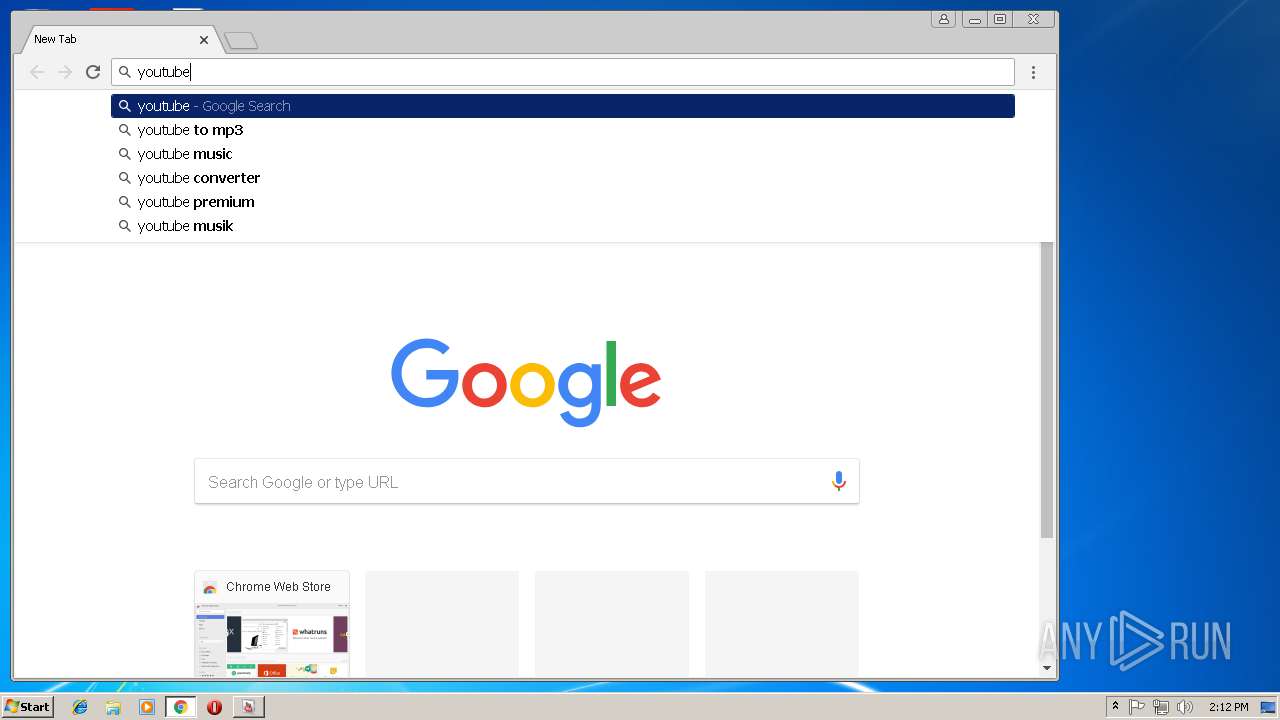
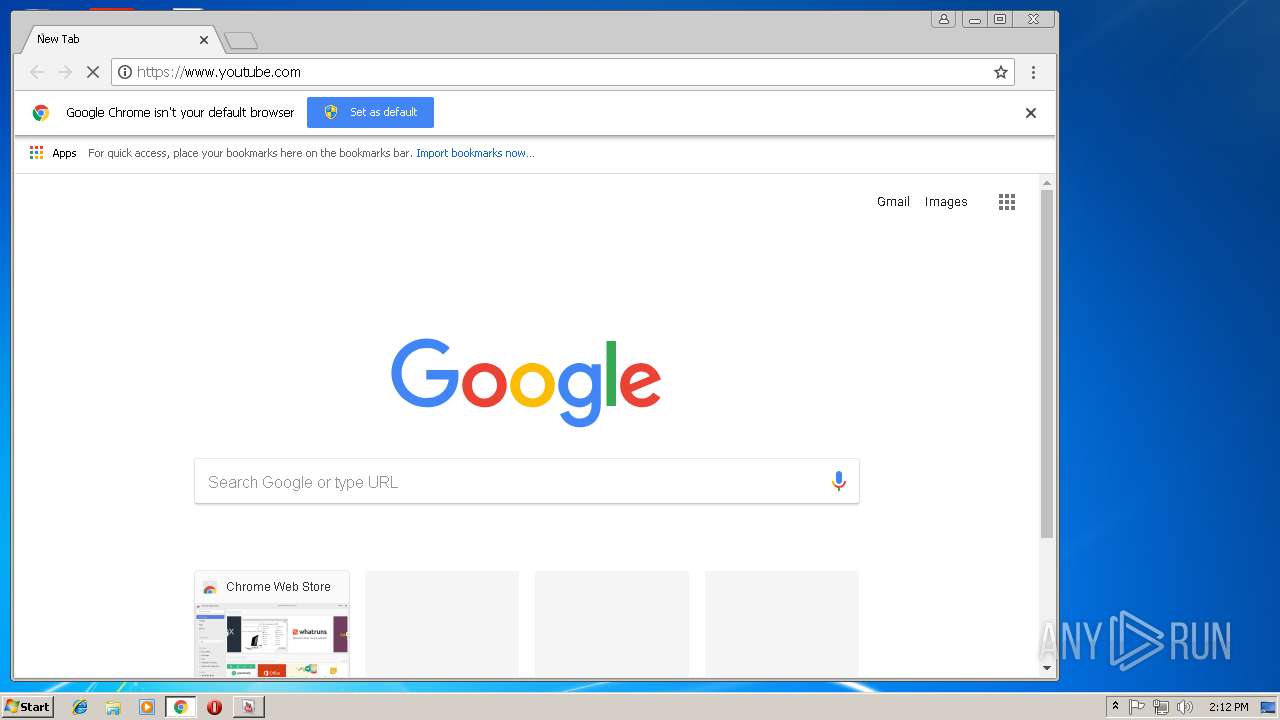
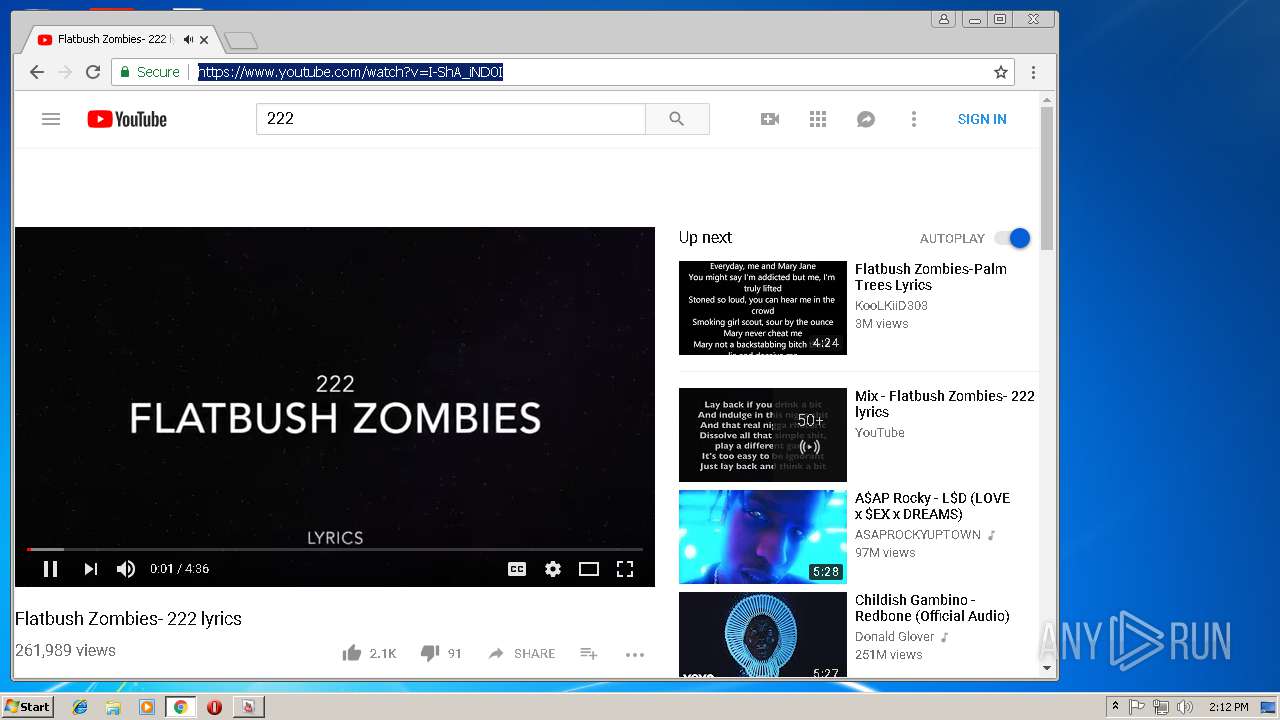
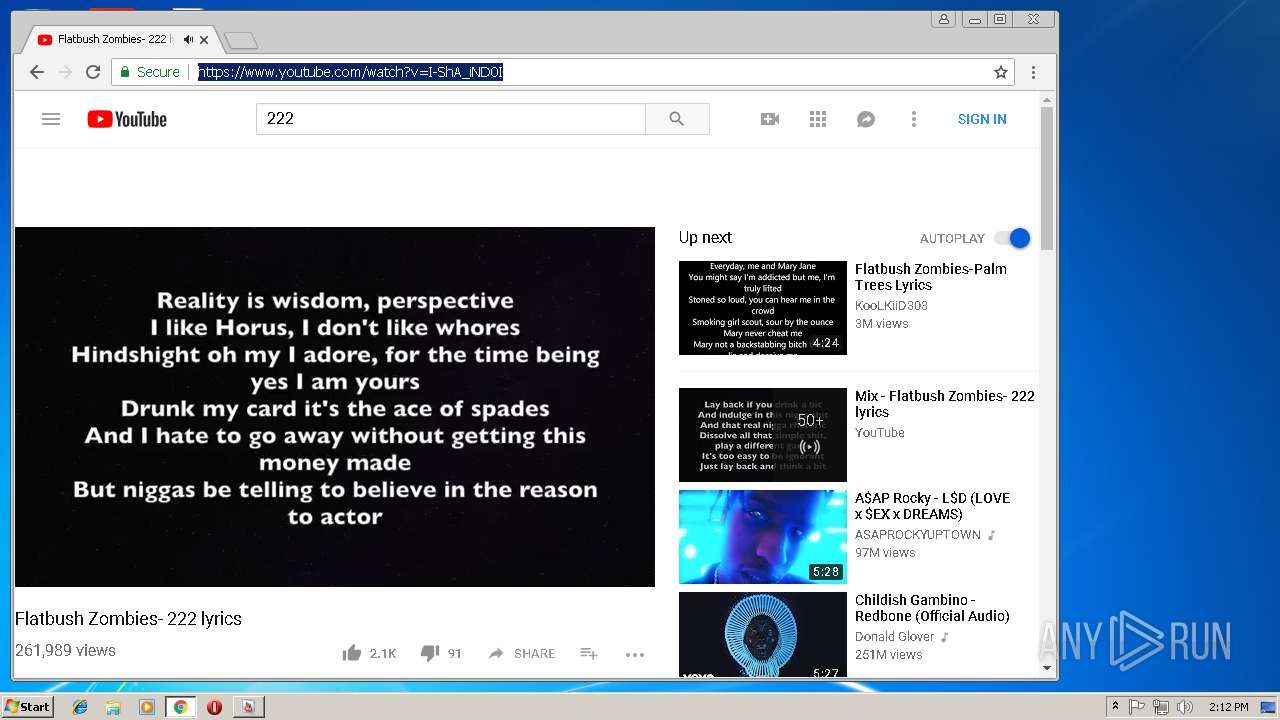
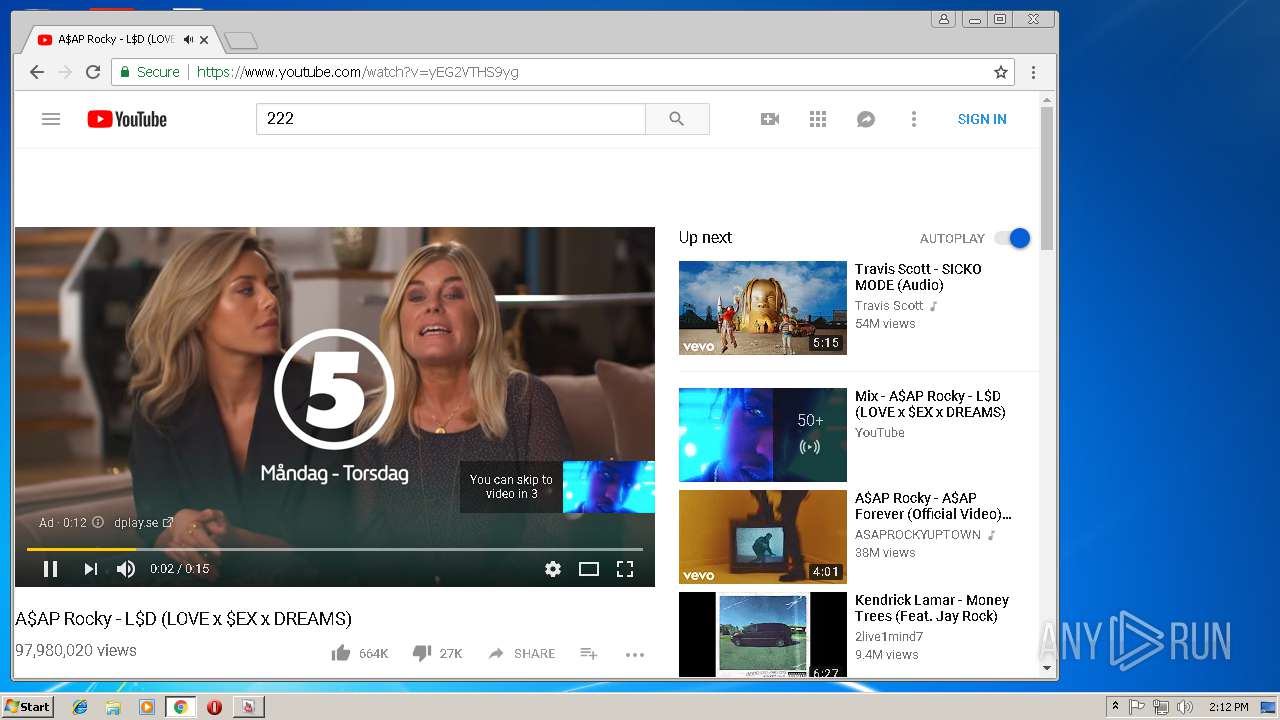
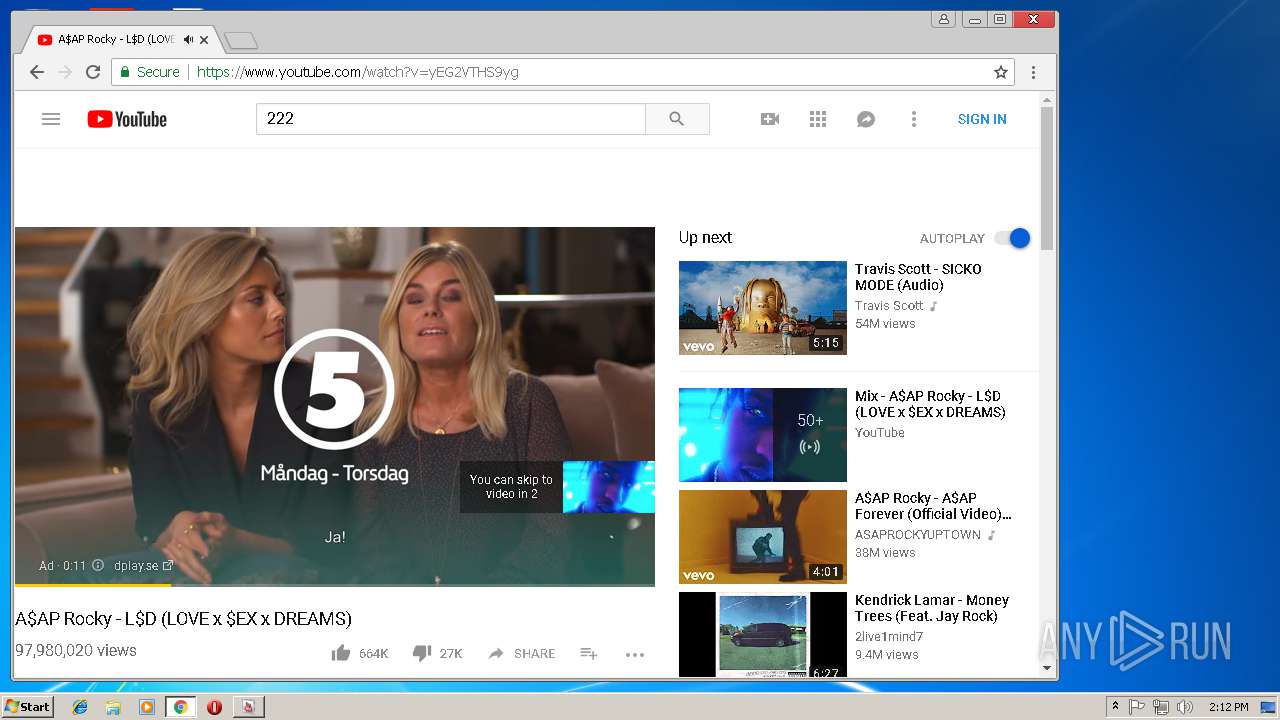
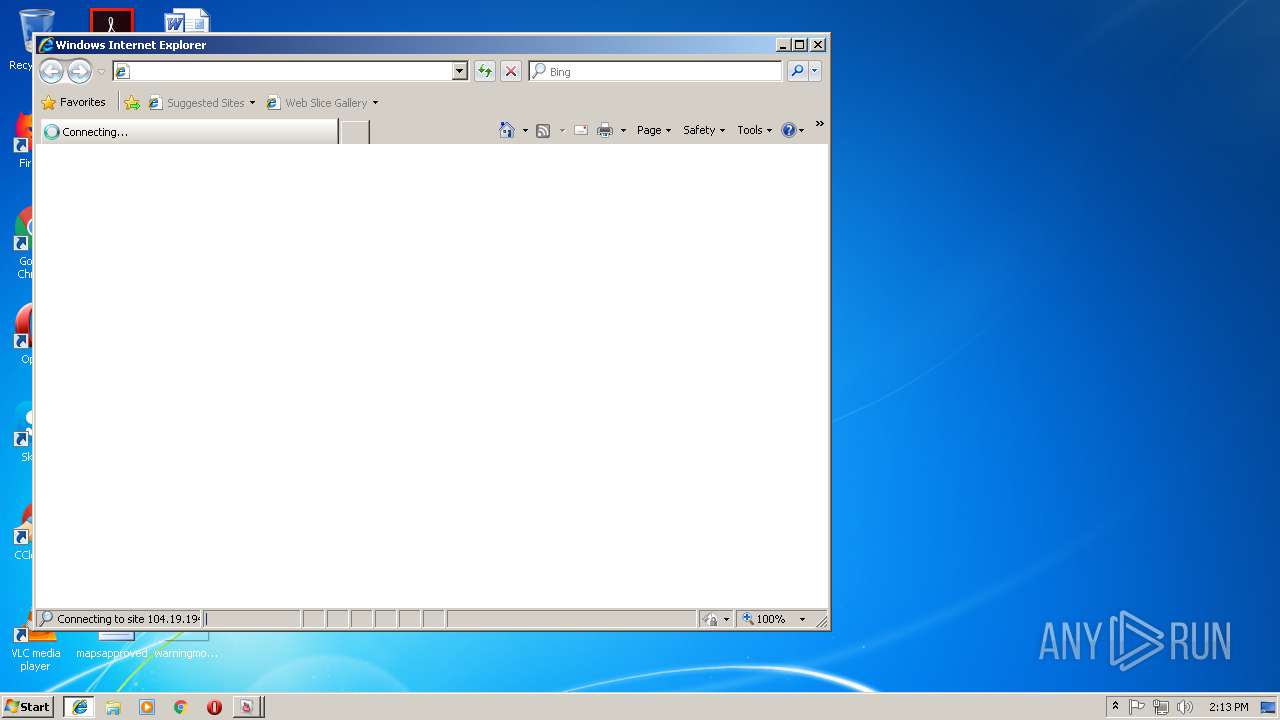
1072 | YouTube View Booster.exe | GET | 301 | 172.217.17.78:80 | http://www.youtube.com/user/idulkoan | US | — | — | whitelisted |
4016 | iexplore.exe | GET | 200 | 104.19.194.29:80 | http://www.mediafire.com/?yxd8taza7tib6 | US | html | 37.8 Kb | shared |
4016 | iexplore.exe | GET | — | 104.19.195.29:80 | http://static.mediafire.com/css/mfv3_120533.php?ver=nonssl | US | — | — | shared |
3348 | iexplore.exe | GET | 200 | 13.107.22.200:80 | http://www.bing.com/favicon.ico | US | image | 237 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
1072 | YouTube View Booster.exe | 172.217.17.78:443 | www.youtube.com | Google Inc. | US | whitelisted |
1072 | YouTube View Booster.exe | 172.217.17.35:443 | fonts.gstatic.com | Google Inc. | US | whitelisted |
1072 | YouTube View Booster.exe | 172.217.17.46:443 | www.youtube.com | Google Inc. | US | whitelisted |
1072 | YouTube View Booster.exe | 172.217.19.193:443 | yt3.ggpht.com | Google Inc. | US | whitelisted |
1072 | YouTube View Booster.exe | 172.217.17.33:443 | s2.googleusercontent.com | Google Inc. | US | whitelisted |
3128 | chrome.exe | 172.217.20.67:443 | fonts.gstatic.com | Google Inc. | US | whitelisted |
3128 | chrome.exe | 172.217.19.193:443 | yt3.ggpht.com | Google Inc. | US | whitelisted |
3128 | chrome.exe | 172.217.17.35:443 | fonts.gstatic.com | Google Inc. | US | whitelisted |
3128 | chrome.exe | 172.217.19.195:443 | www.google.com.ua | Google Inc. | US | whitelisted |
3128 | chrome.exe | 108.177.96.95:443 | fonts.googleapis.com | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.youtube.com |
| whitelisted |
s.ytimg.com |
| whitelisted |
fonts.gstatic.com |
| whitelisted |
yt3.ggpht.com |
| whitelisted |
accounts.google.com |
| shared |
s2.googleusercontent.com |
| whitelisted |
ssl.gstatic.com |
| whitelisted |
clientservices.googleapis.com |
| whitelisted |
www.google.com.ua |
| whitelisted |
www.gstatic.com |
| whitelisted |