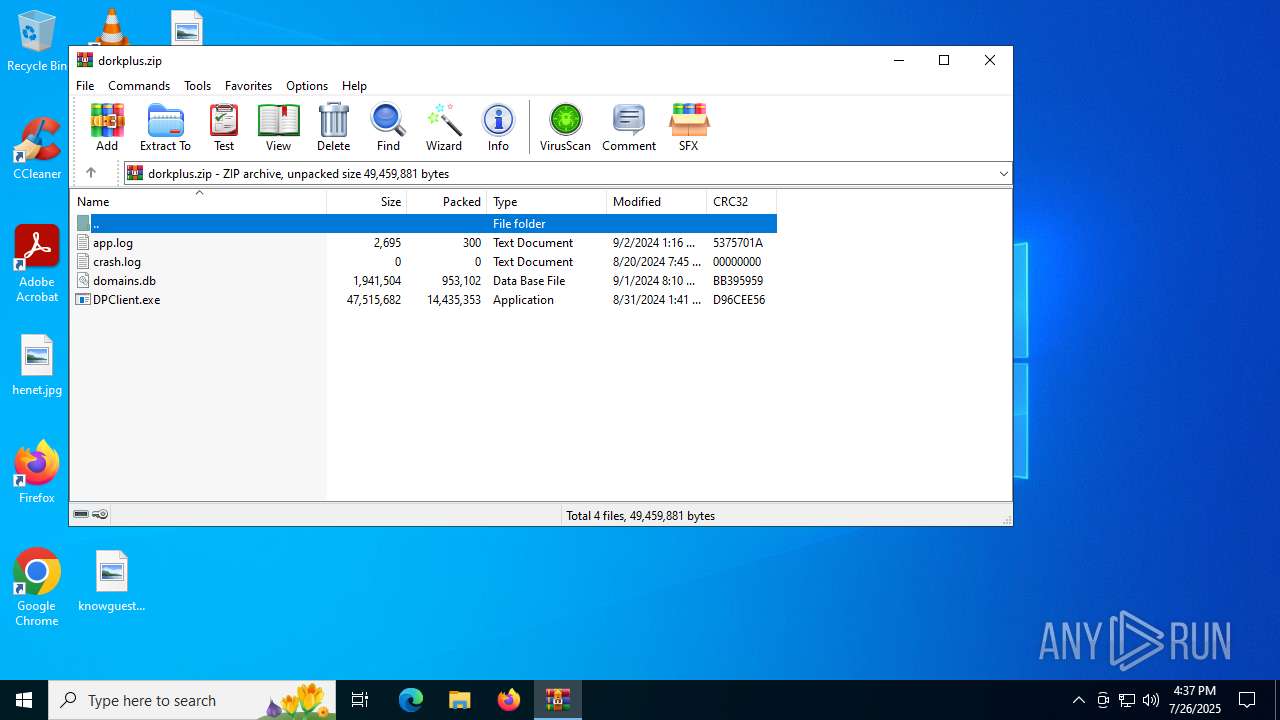
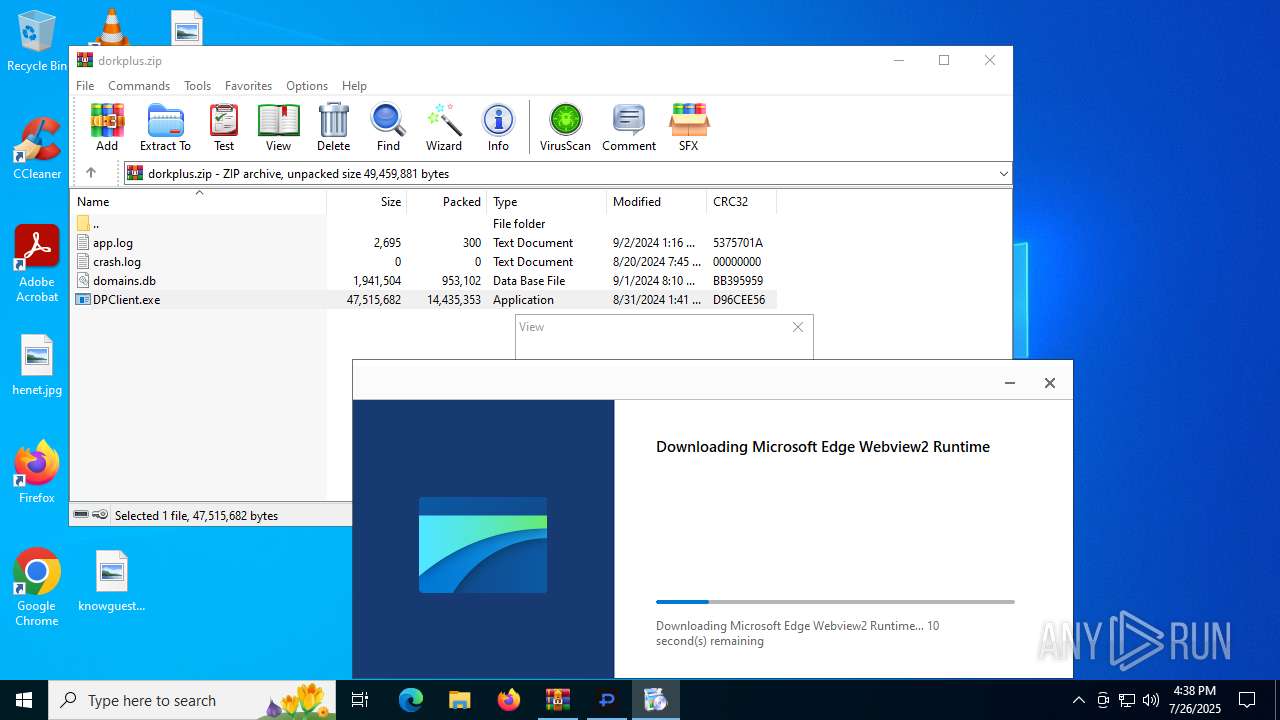
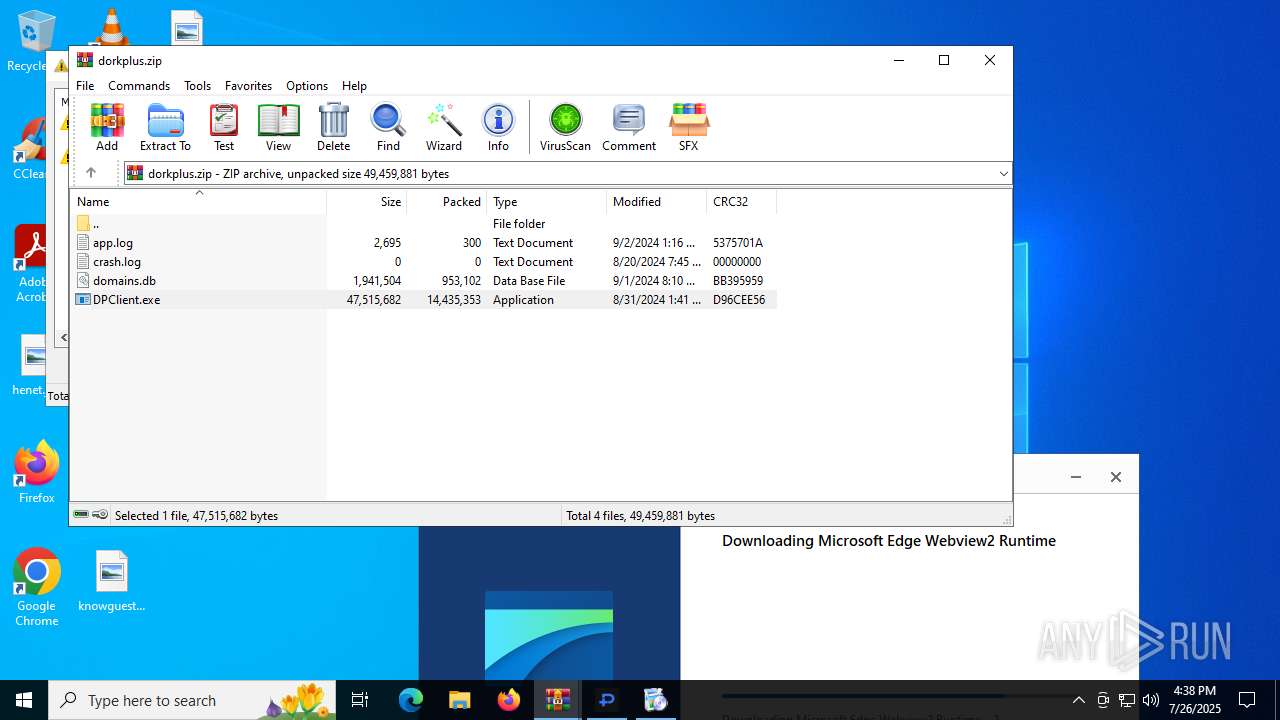
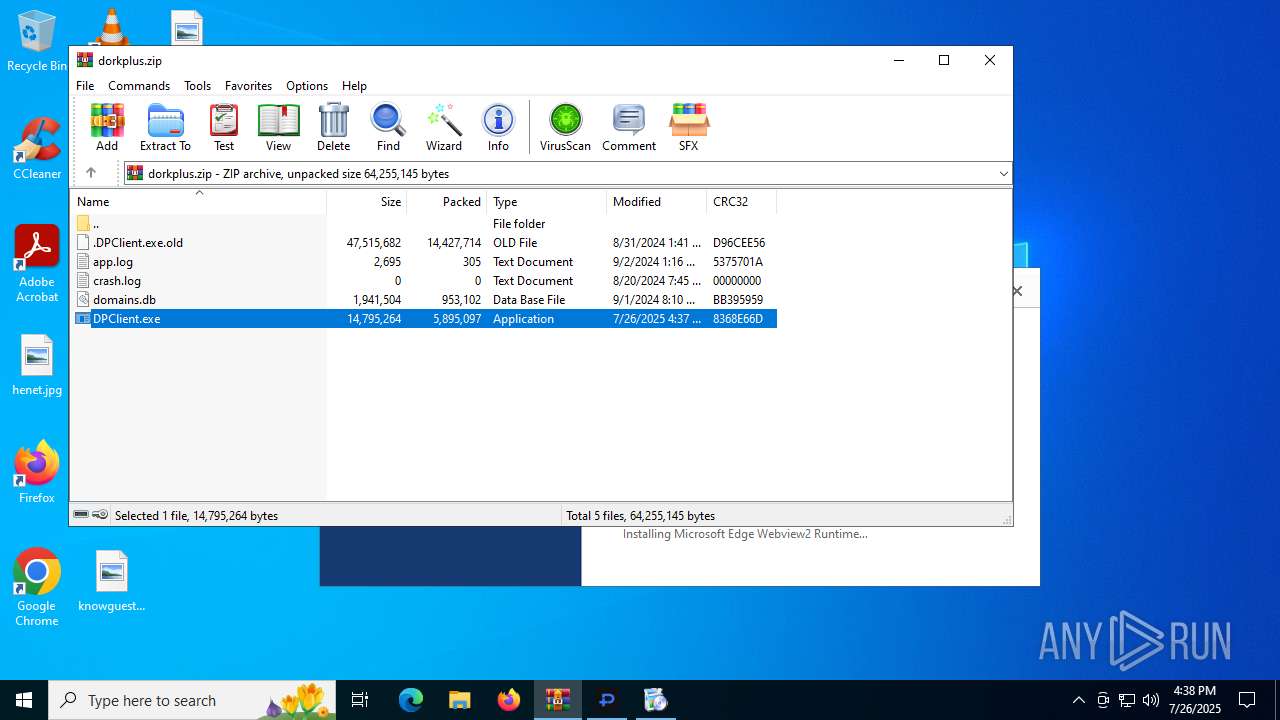
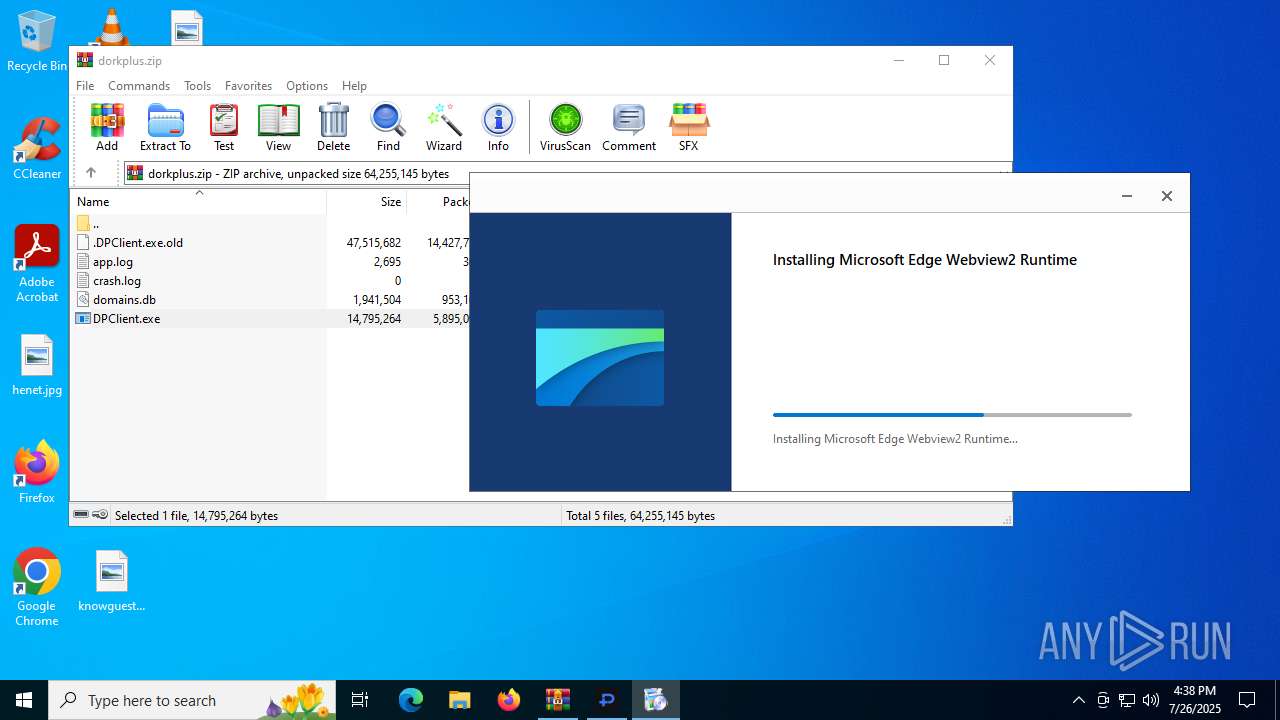
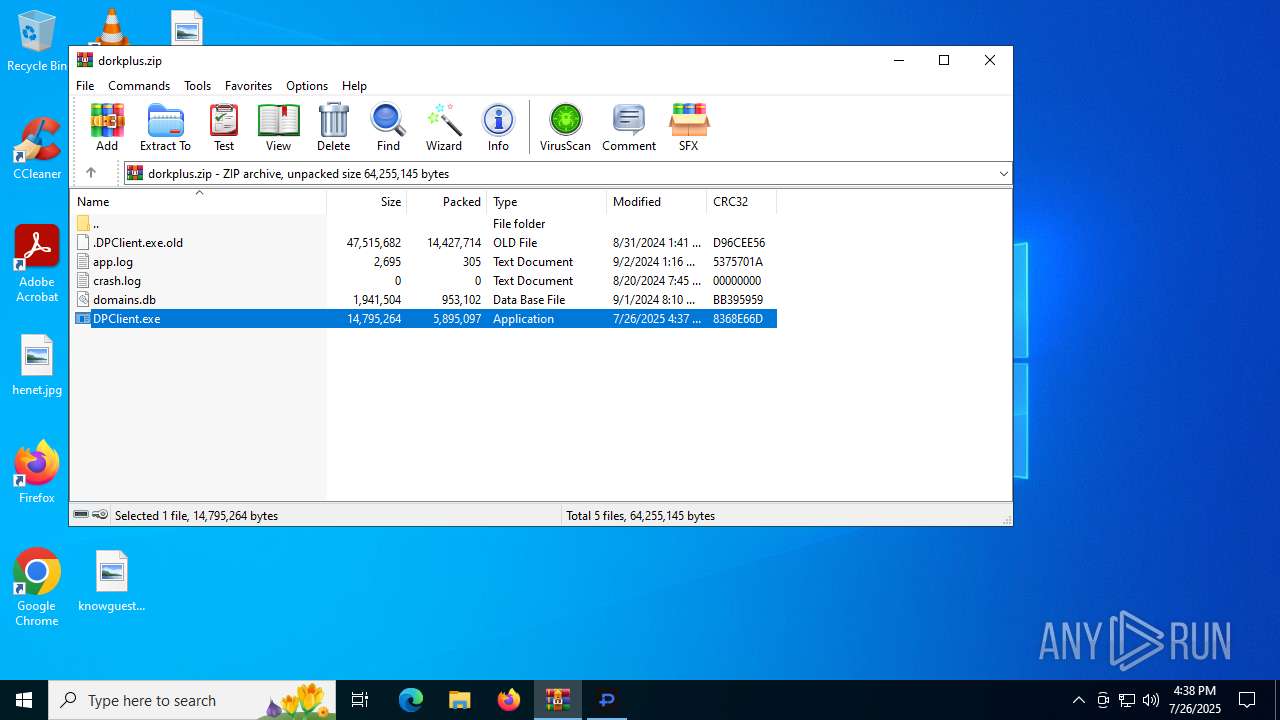
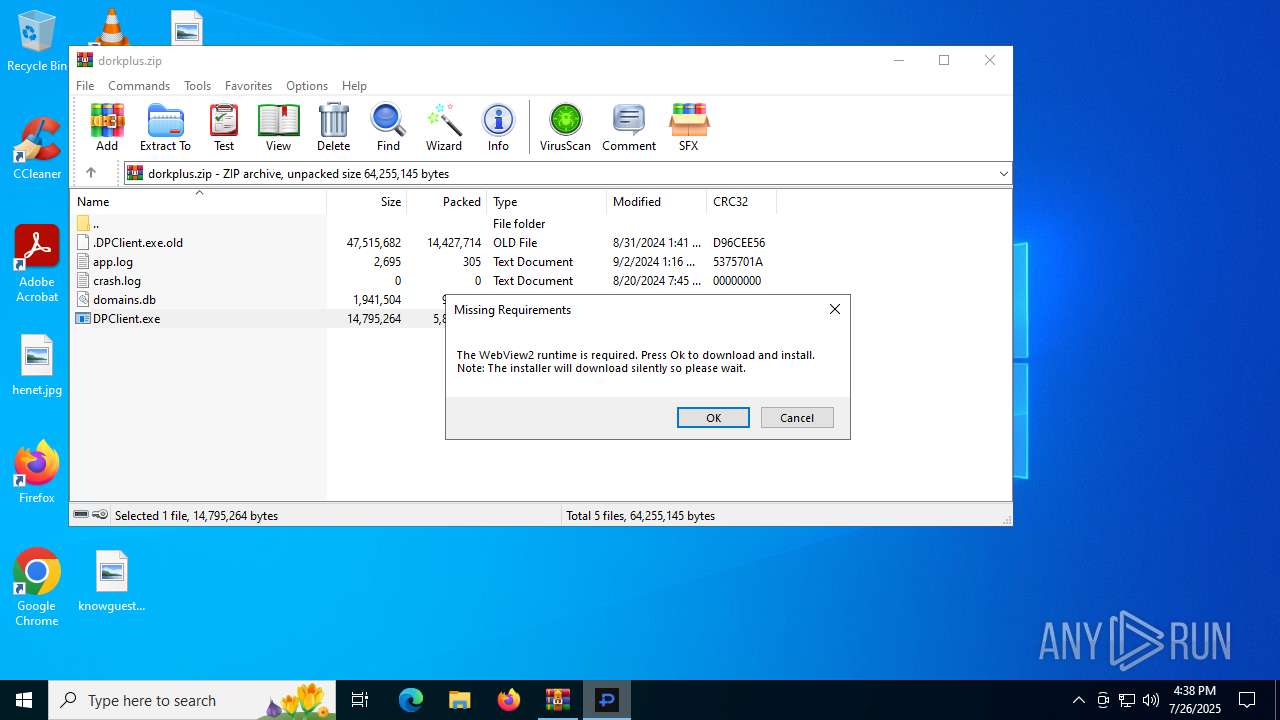
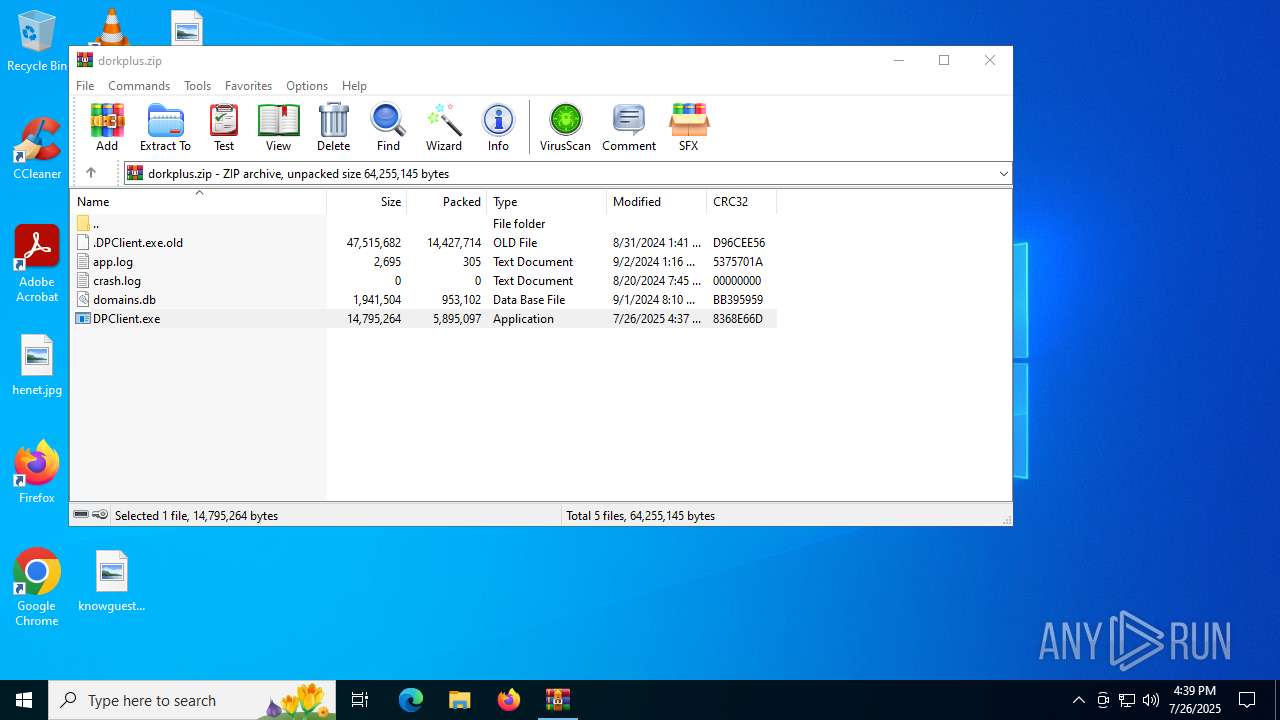
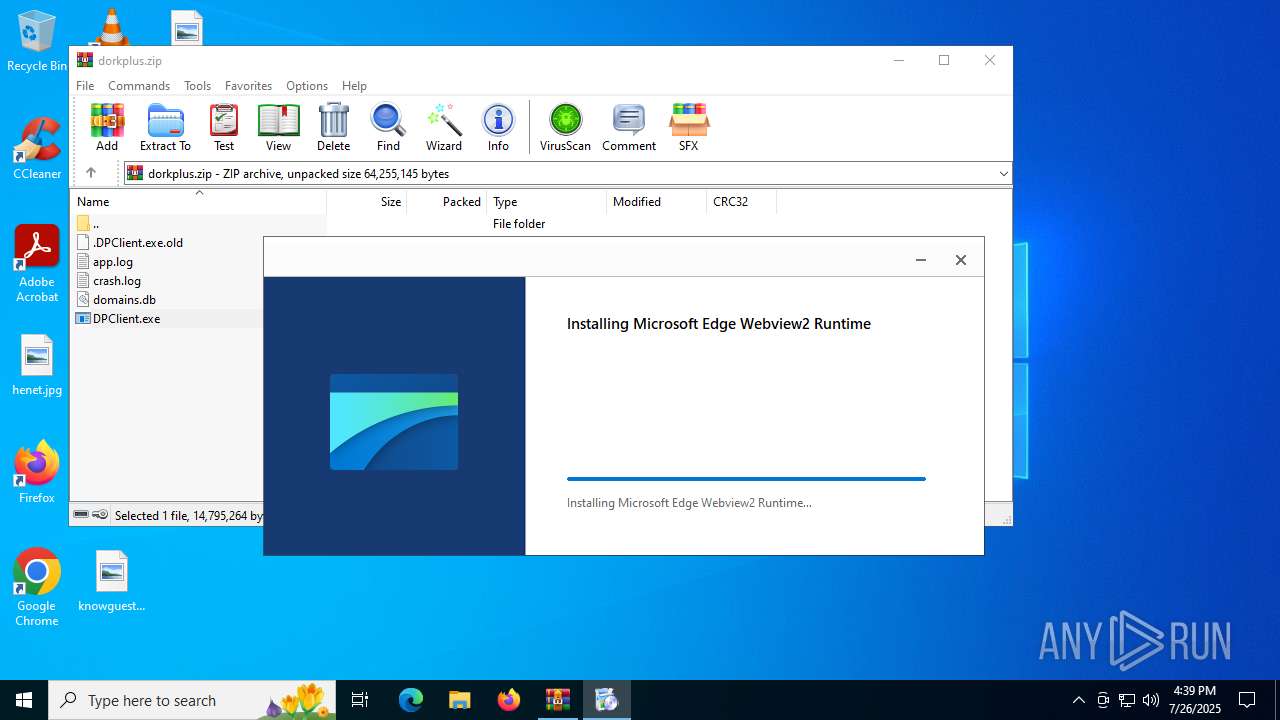
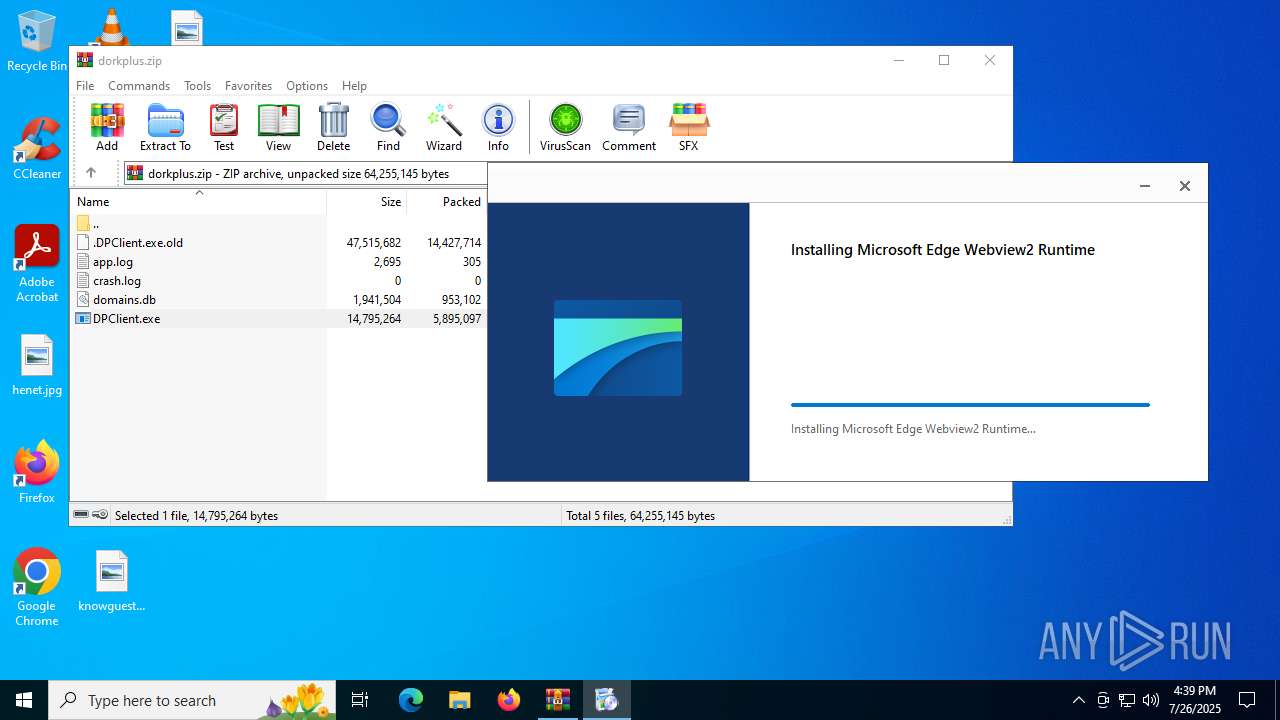
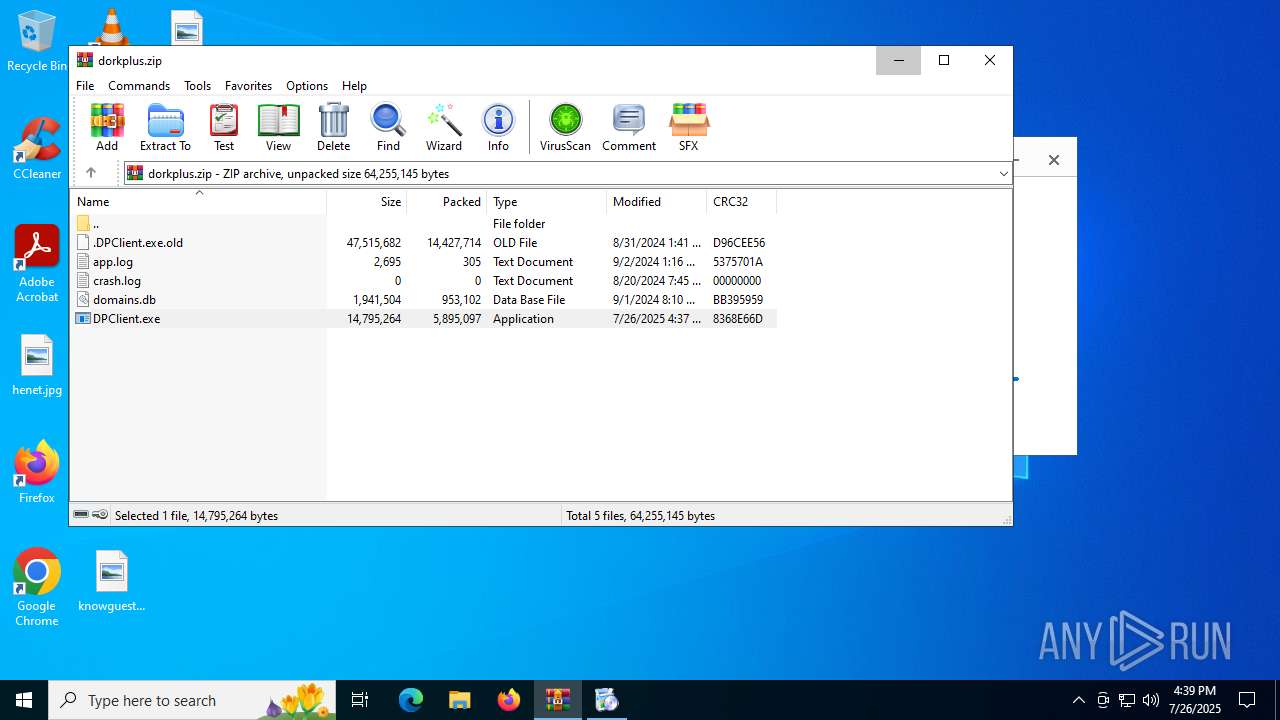
| File name: | dorkplus.zip |
| Full analysis: | https://app.any.run/tasks/01f4d9f9-288a-4b0a-9232-d3659c9ef2bc |
| Verdict: | Malicious activity |
| Analysis date: | July 26, 2025, 16:37:38 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/zip |
| File info: | Zip archive data, at least v2.0 to extract, compression method=deflate |
| MD5: | F27772112E6624BA667C7966AC9B7C17 |
| SHA1: | F38E6EB1A2761B45D197CE54BD4EE1F46ECEFE4C |
| SHA256: | 641F48B7F9B23D49C3AE86E047858CA127632B43E4FA9D0264BAB837AB43777C |
| SSDEEP: | 98304:27LoFP4ve9c93Je1UKQztKIGSwykCtFnaJyS3P2yvJLN/c5doHcJ2V1bcGWWaE1c:PH7N1ZAVnK+6FVkvTZwALdRto6P |
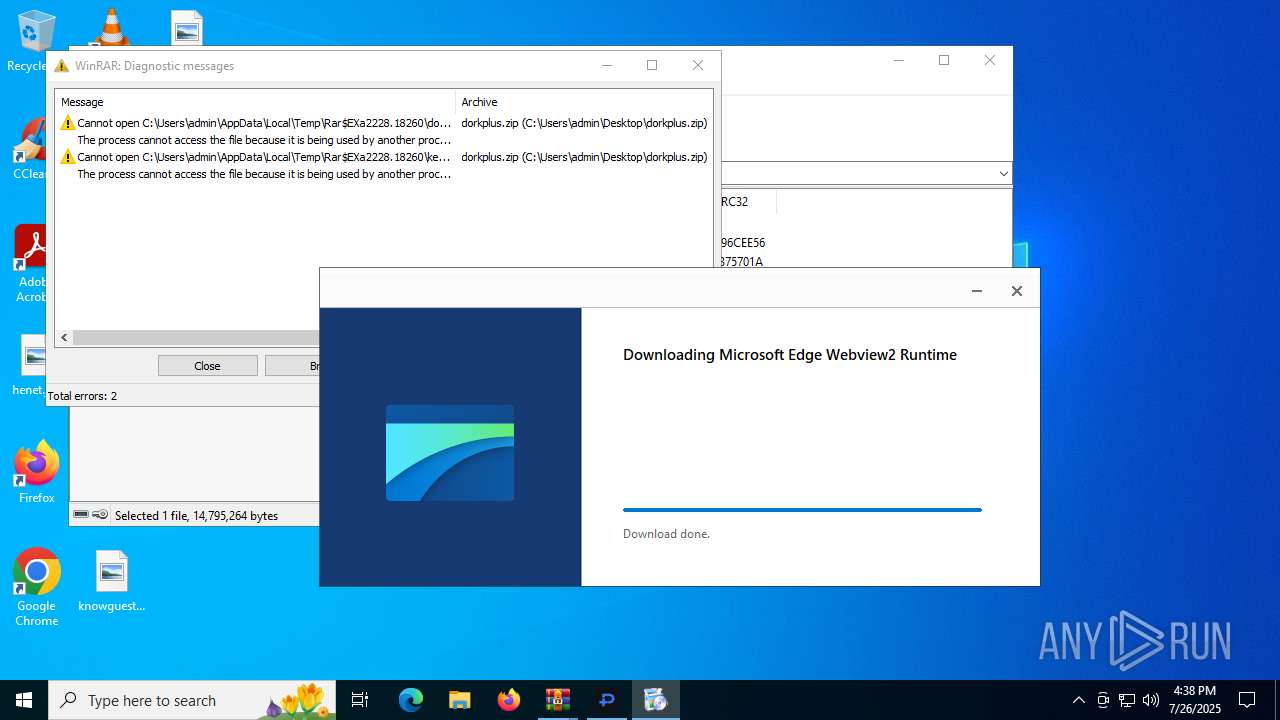
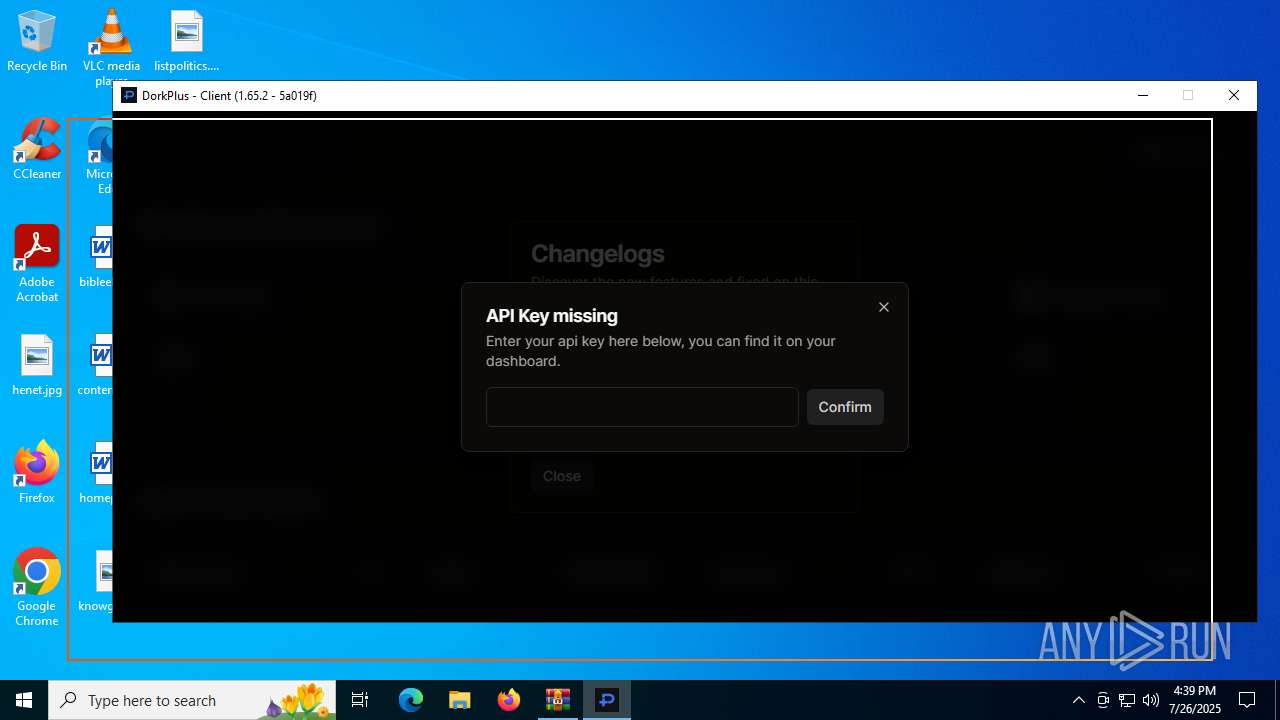
MALICIOUS
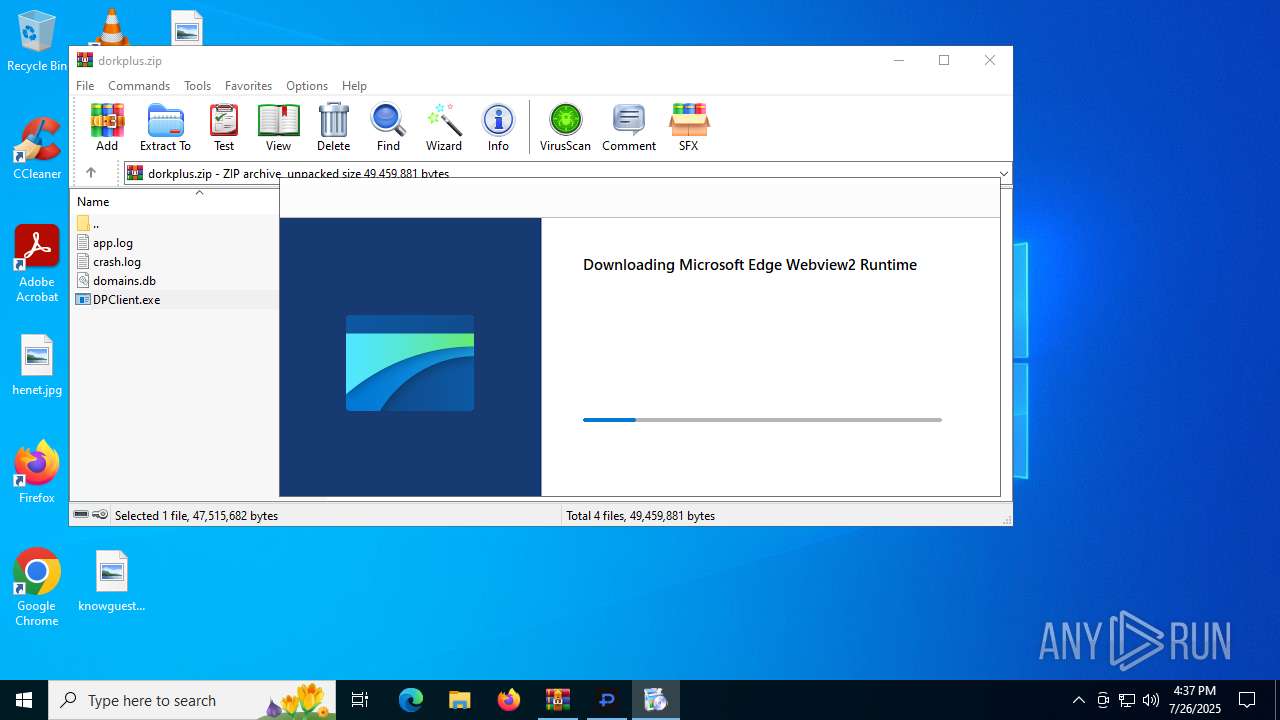
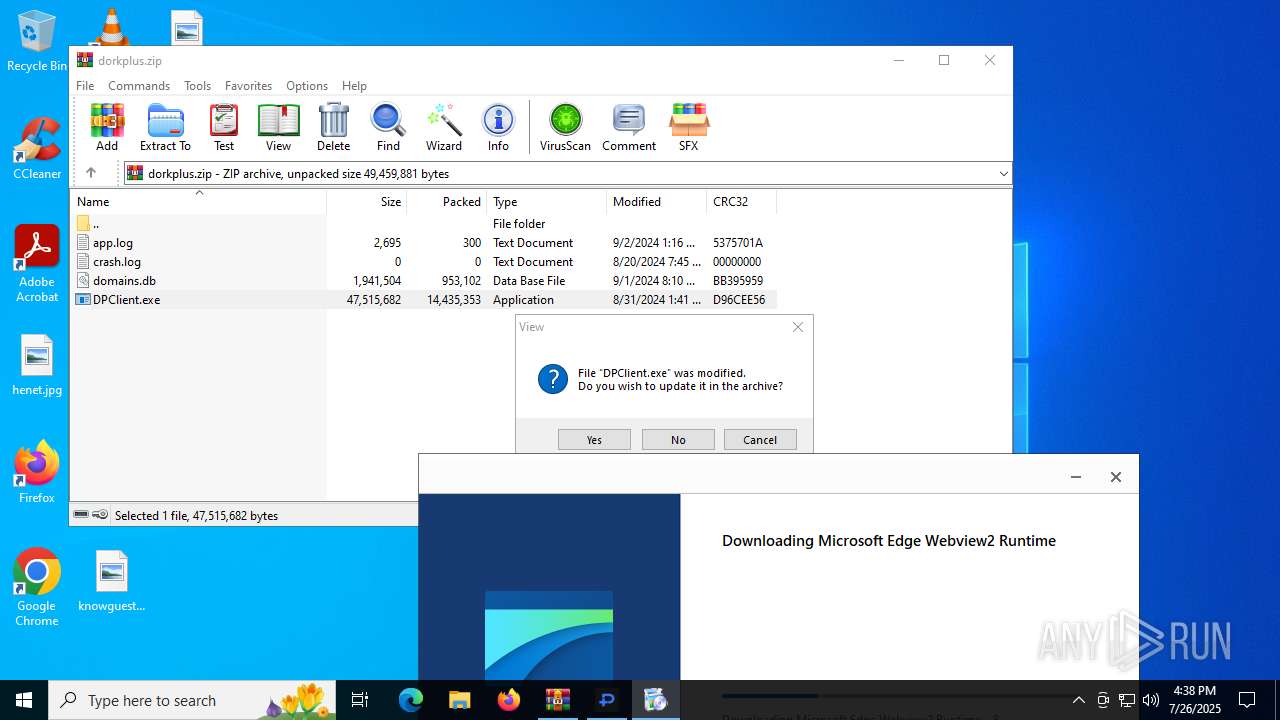
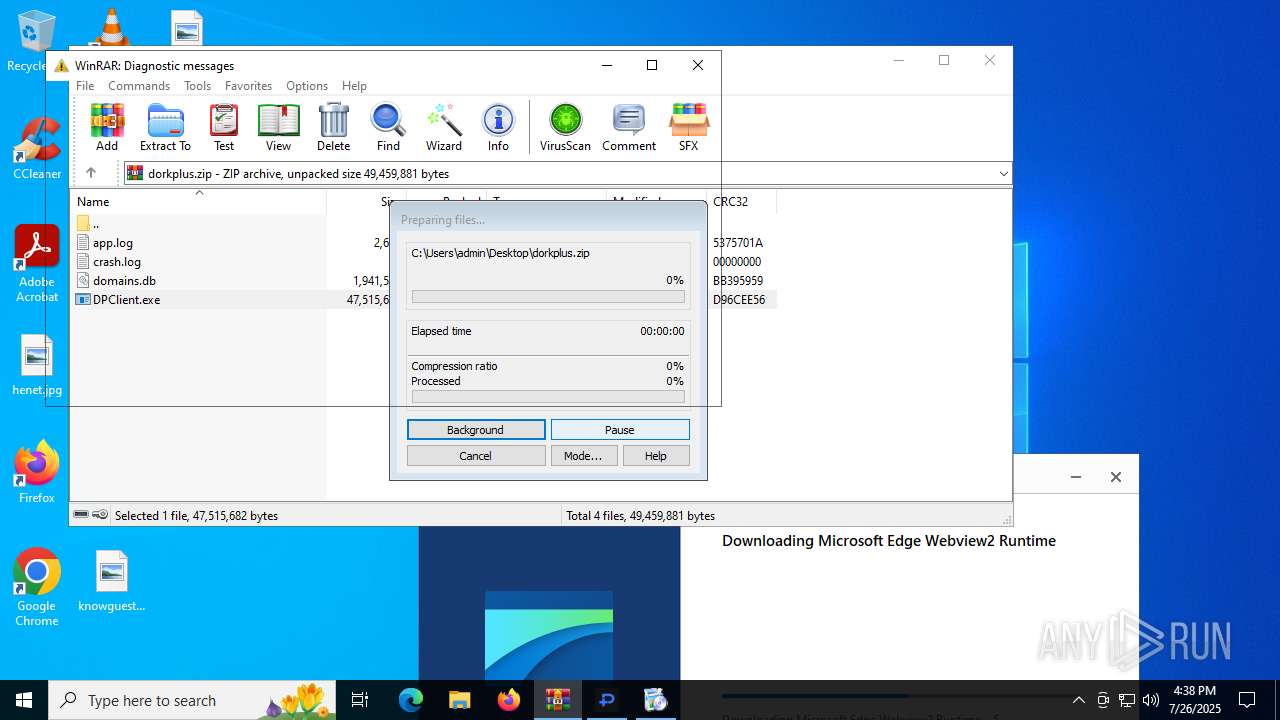
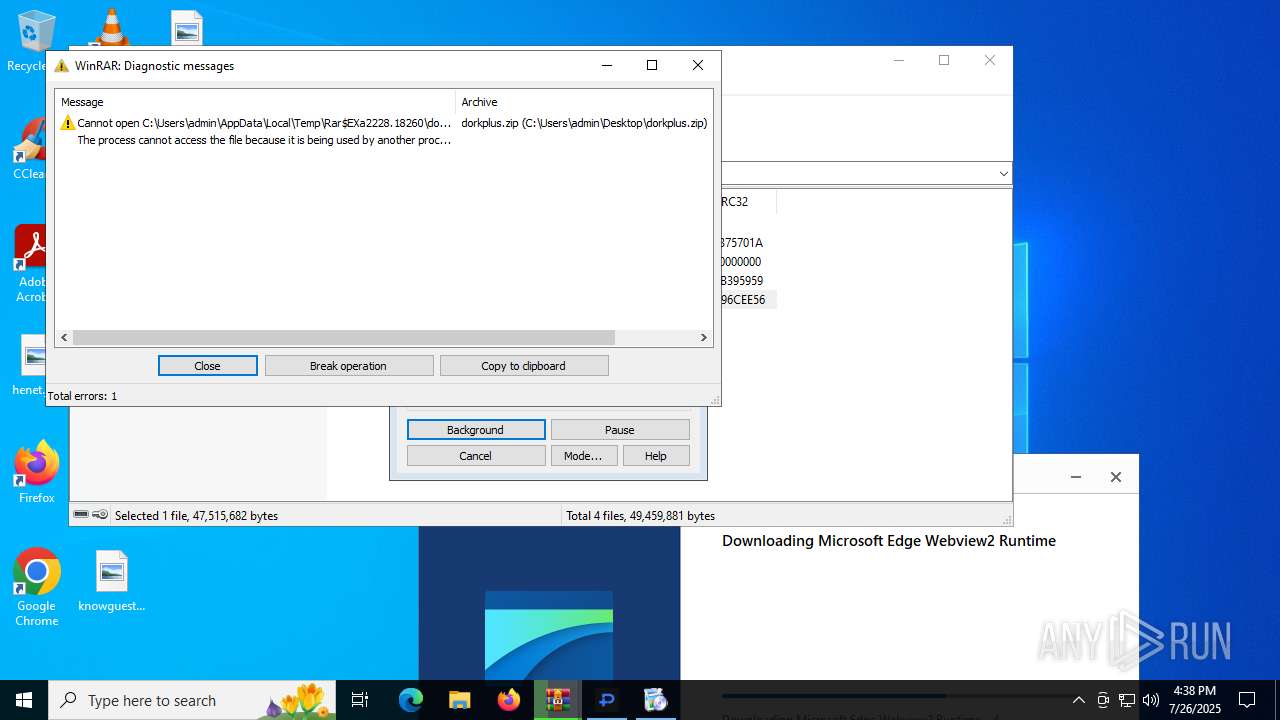
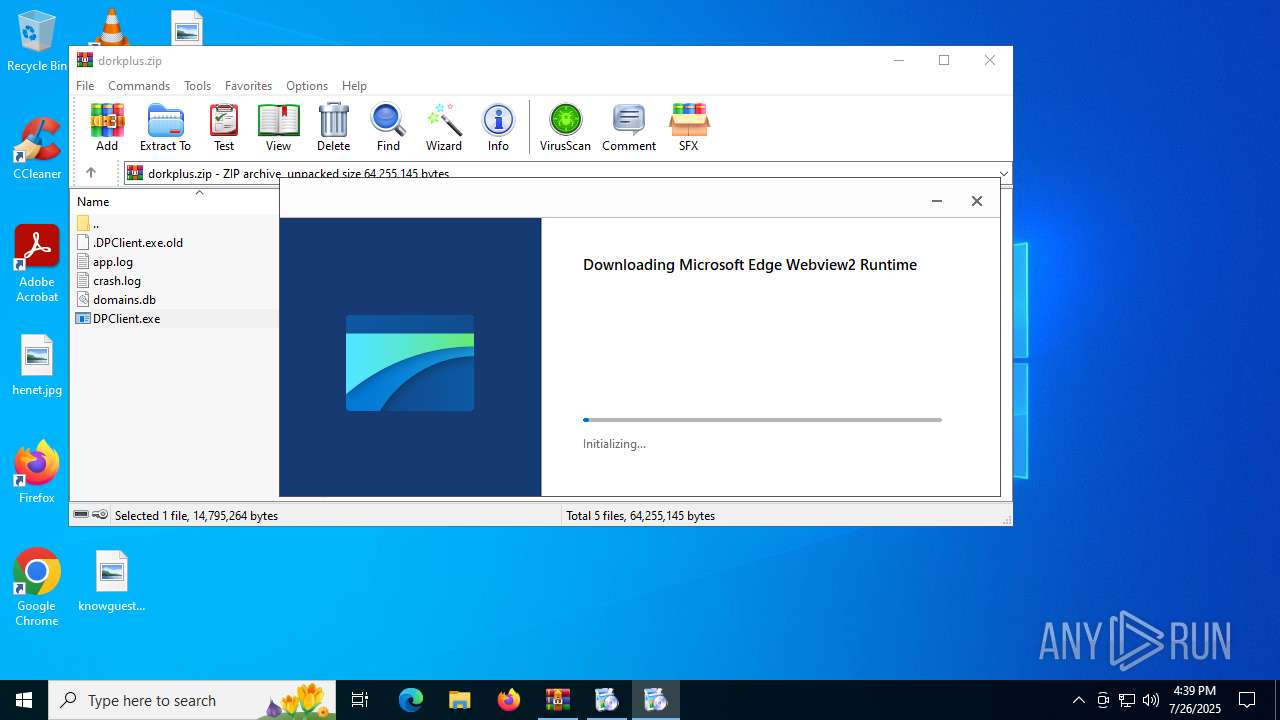
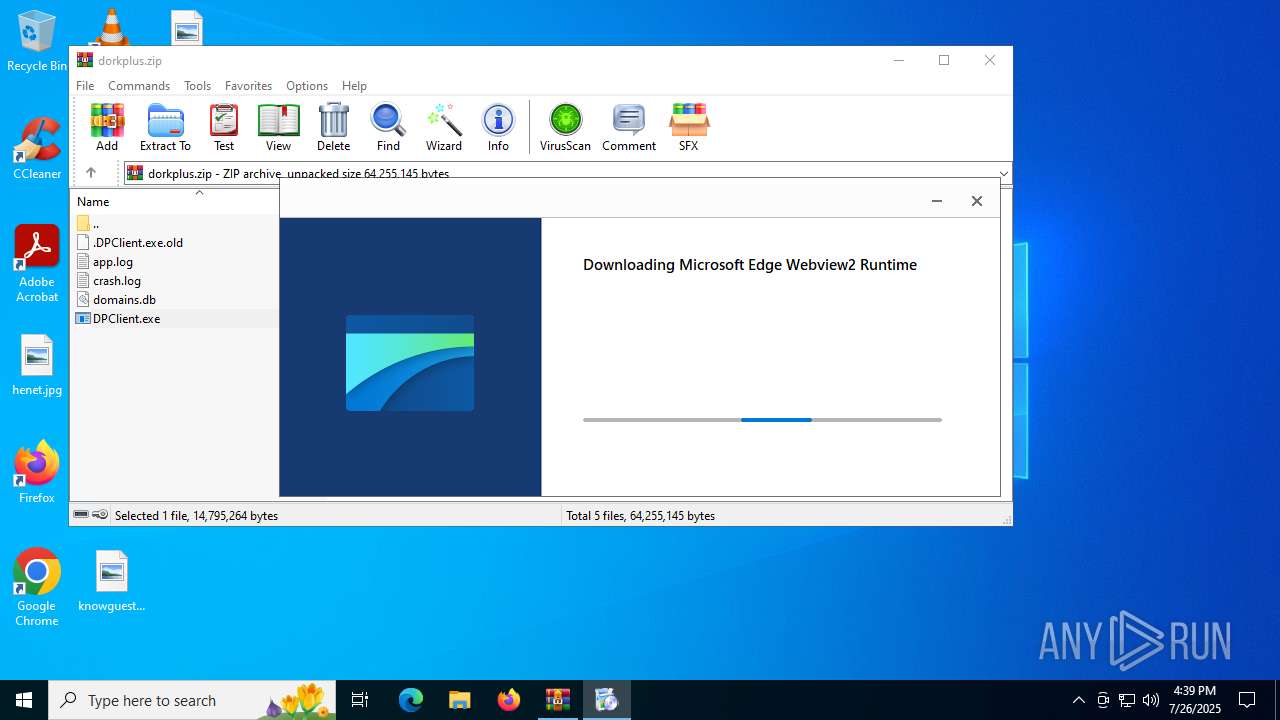
Generic archive extractor
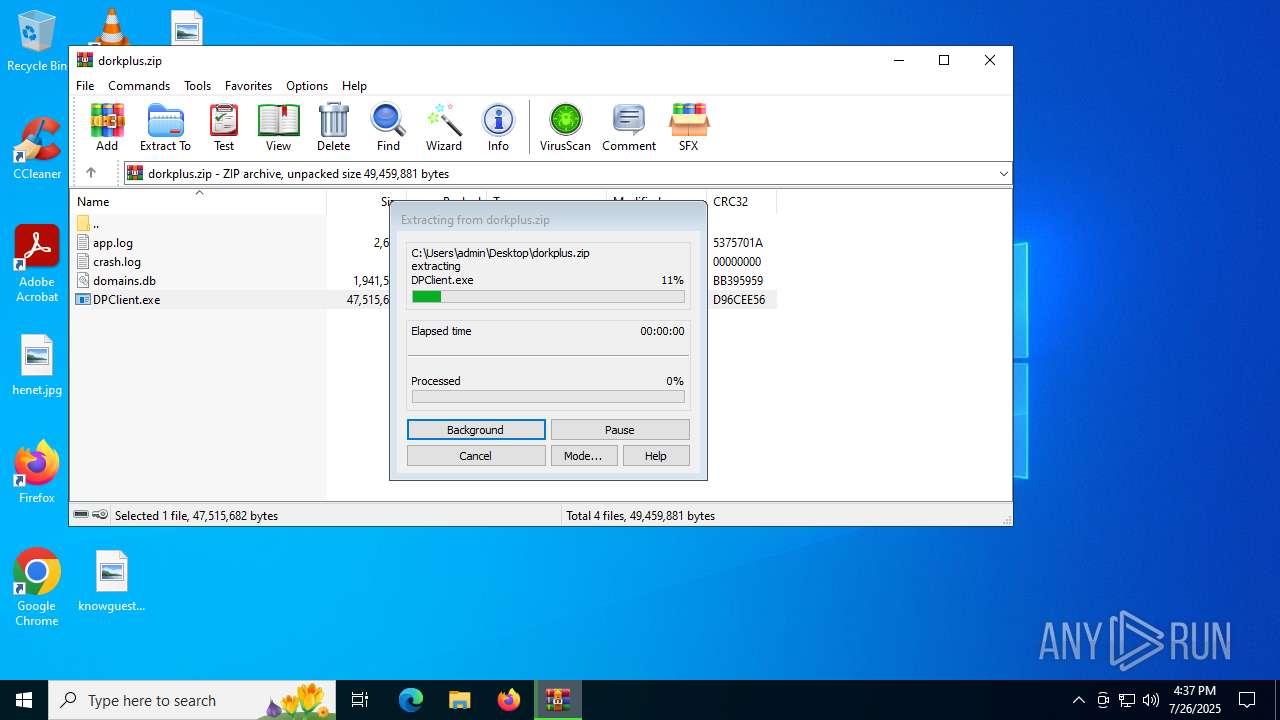
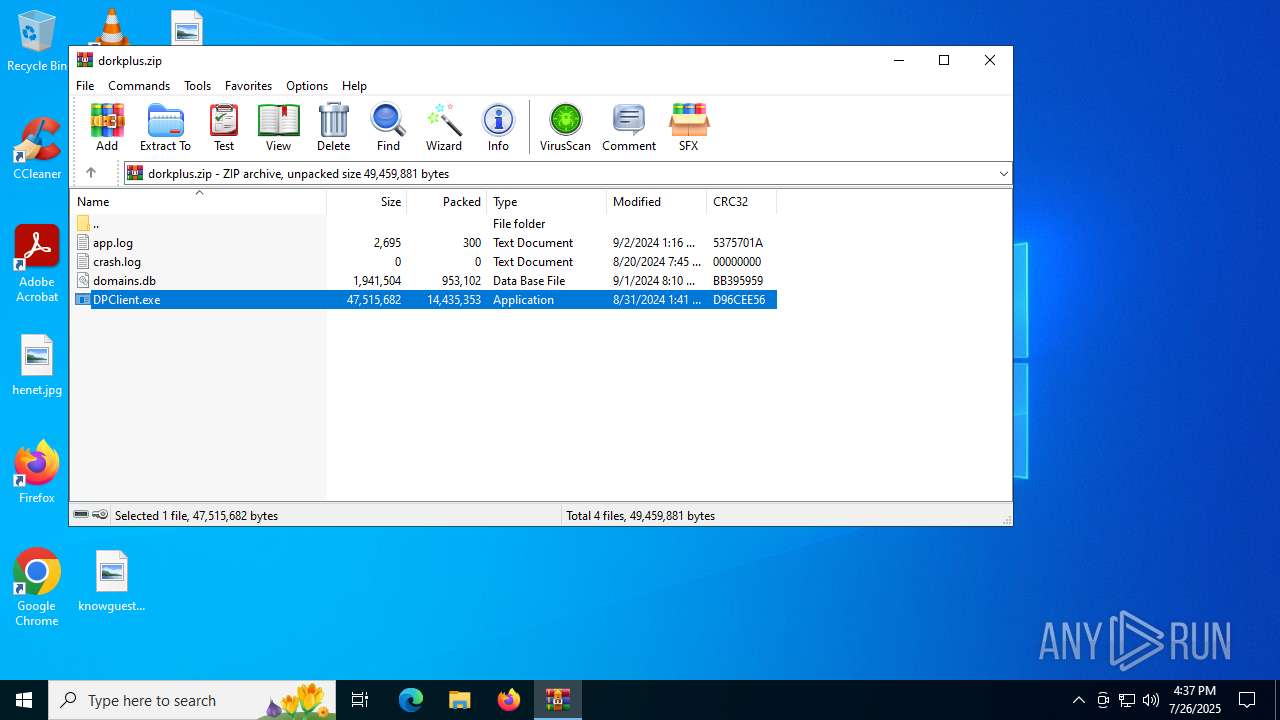
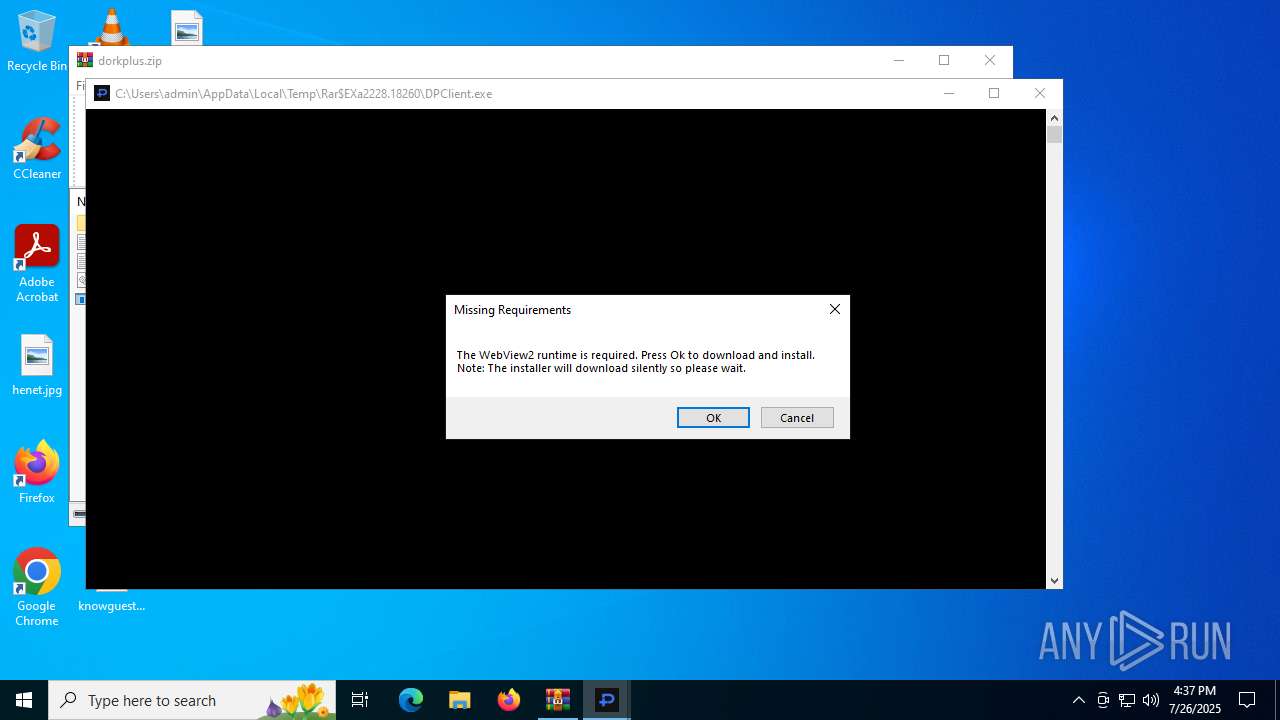
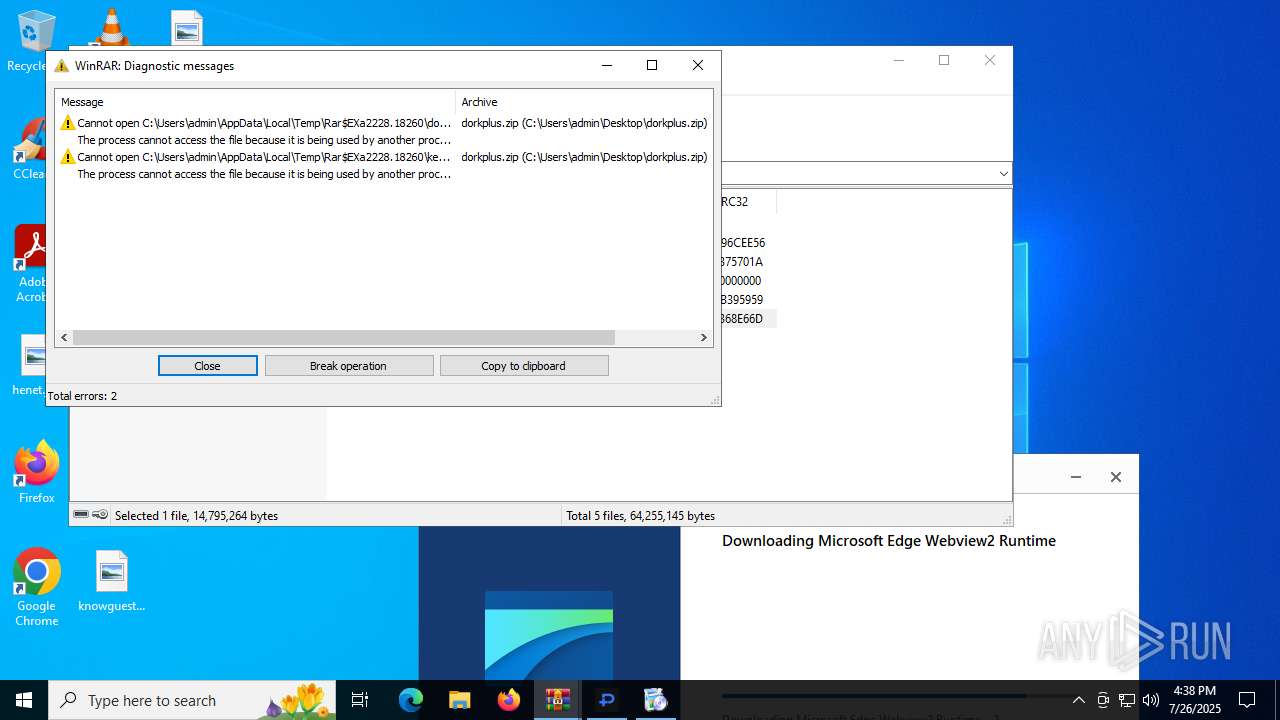
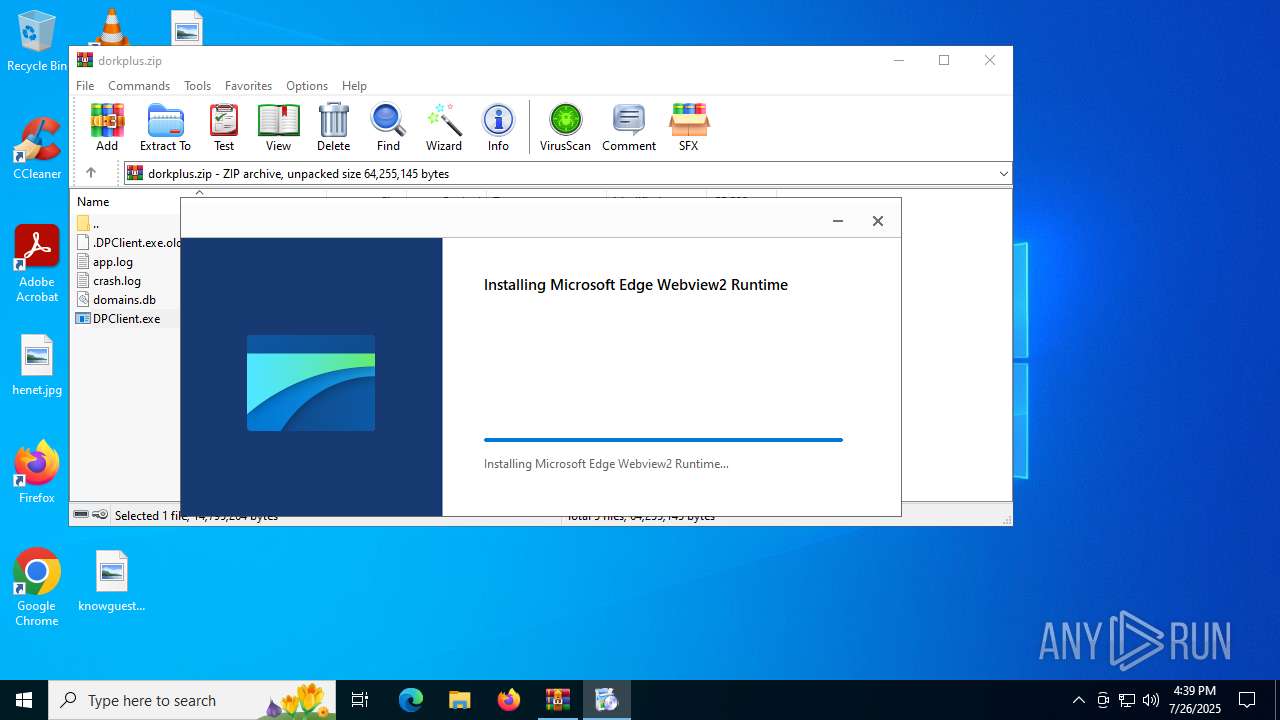
- WinRAR.exe (PID: 2228)
Changes the autorun value in the registry
- MicrosoftEdgeUpdate.exe (PID: 6812)
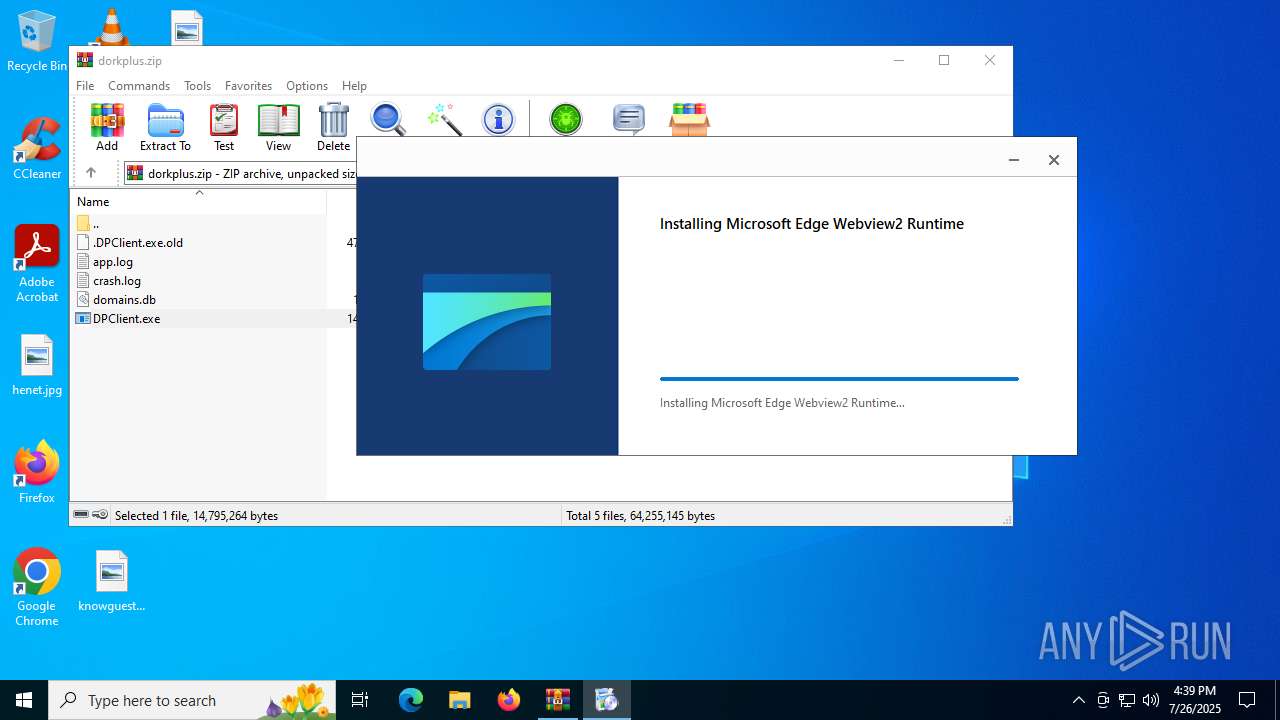
The DLL Hijacking
- msedgewebview2.exe (PID: 2692)
SUSPICIOUS
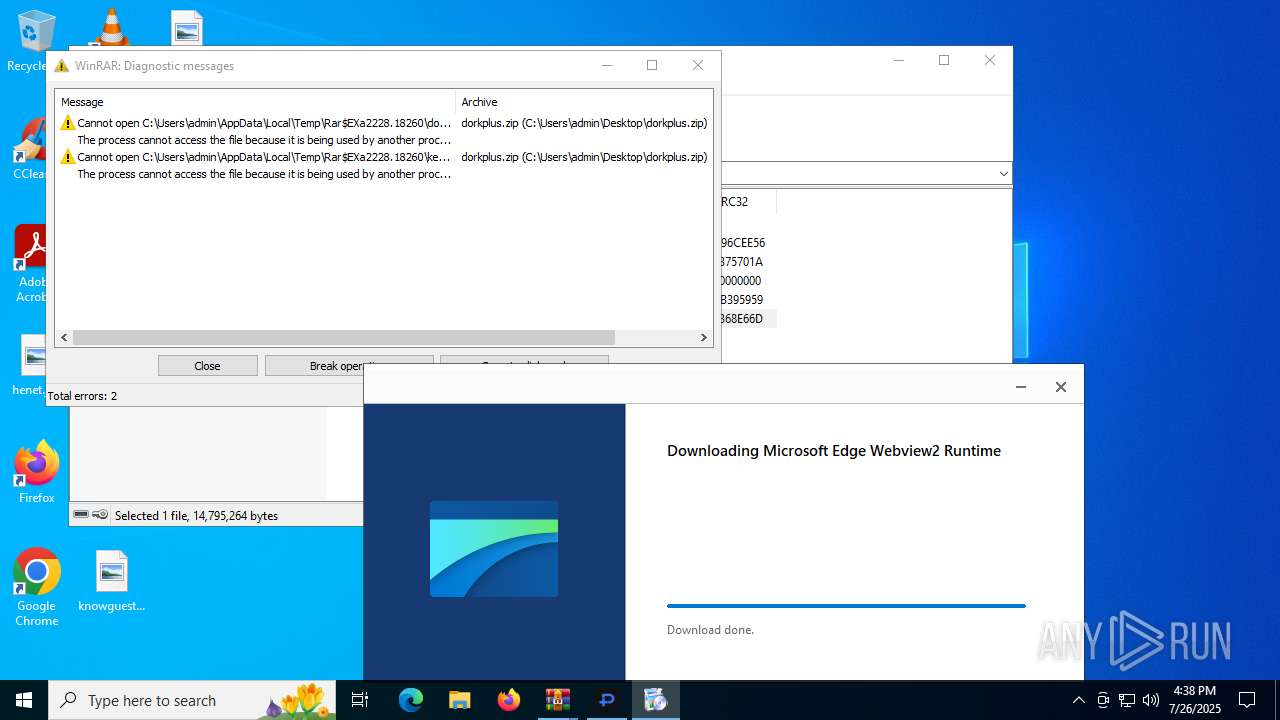
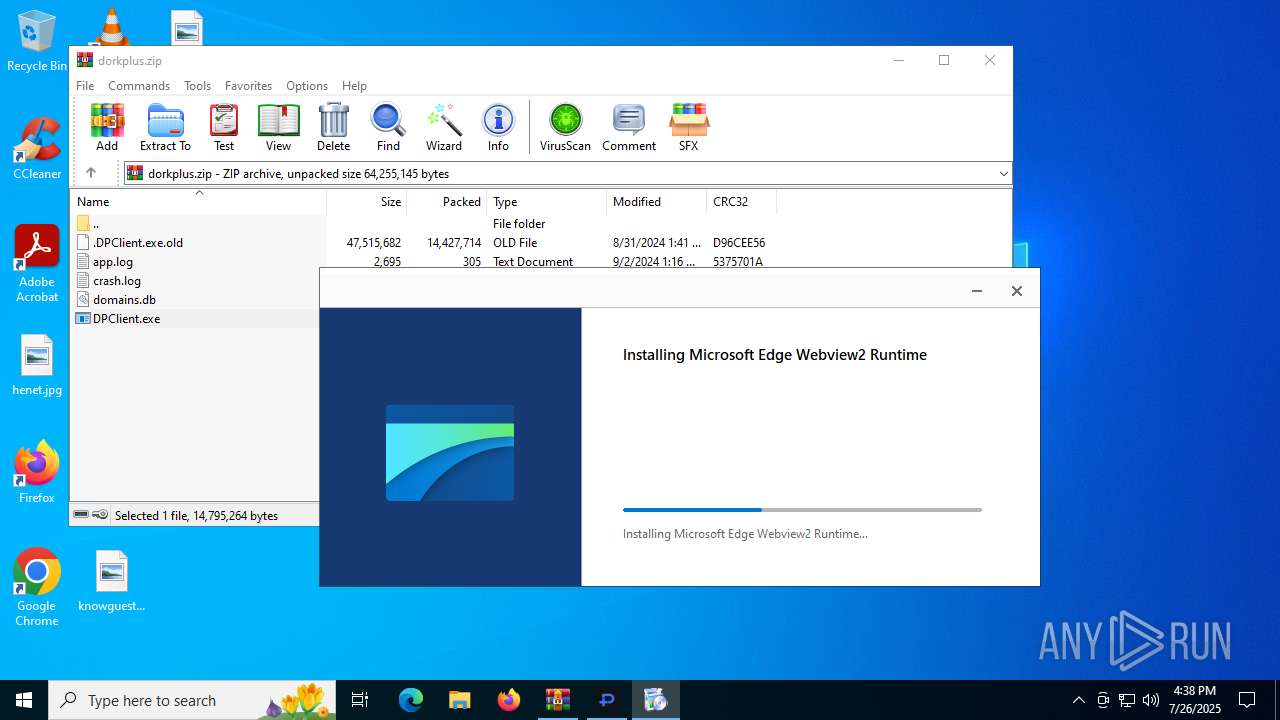
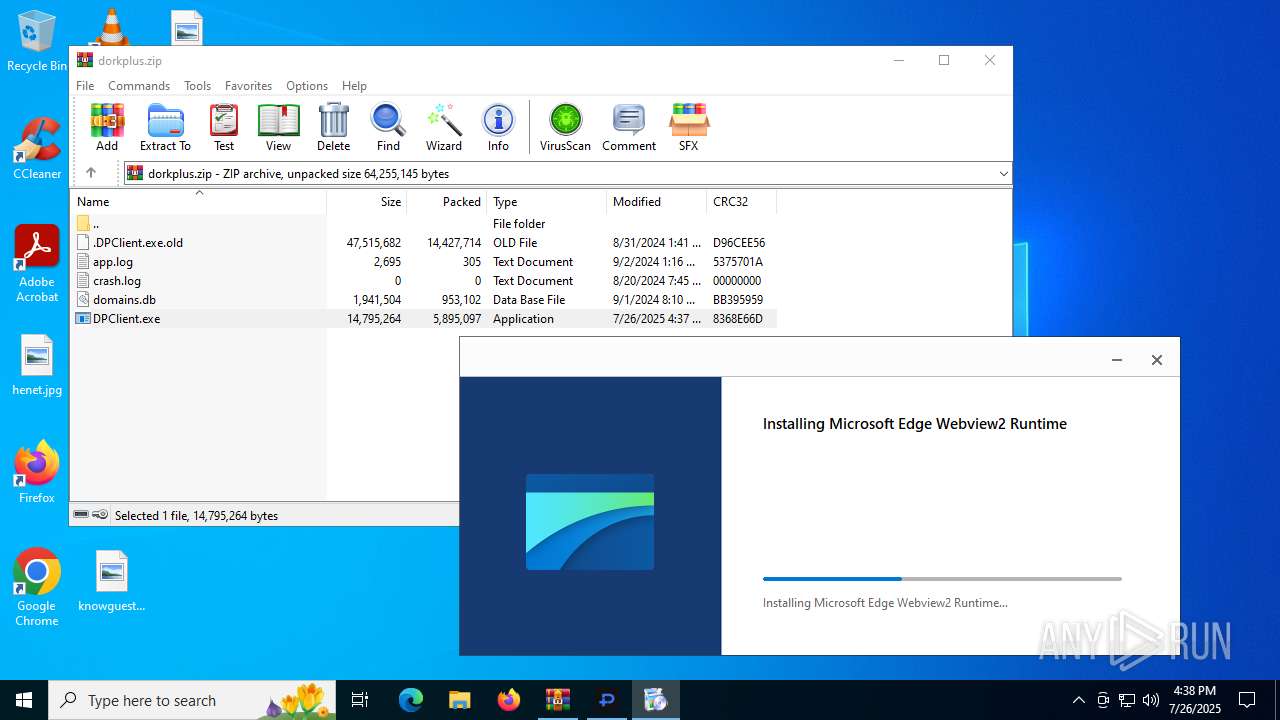
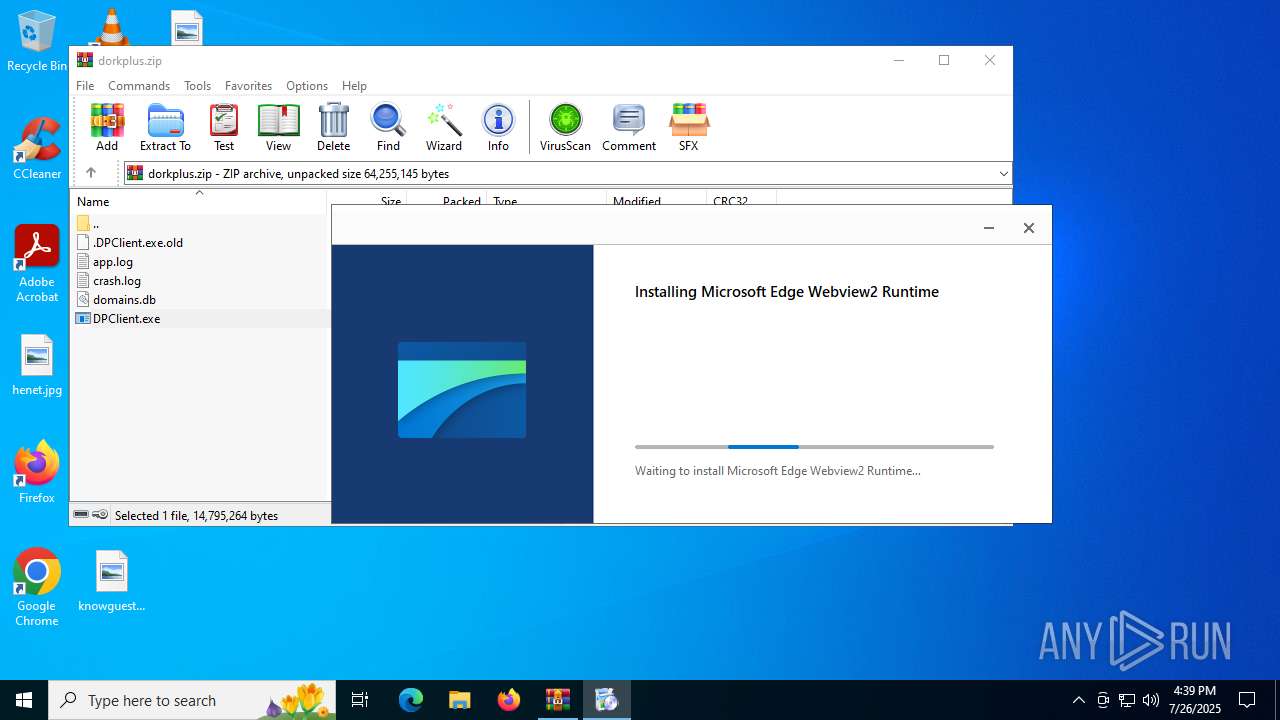
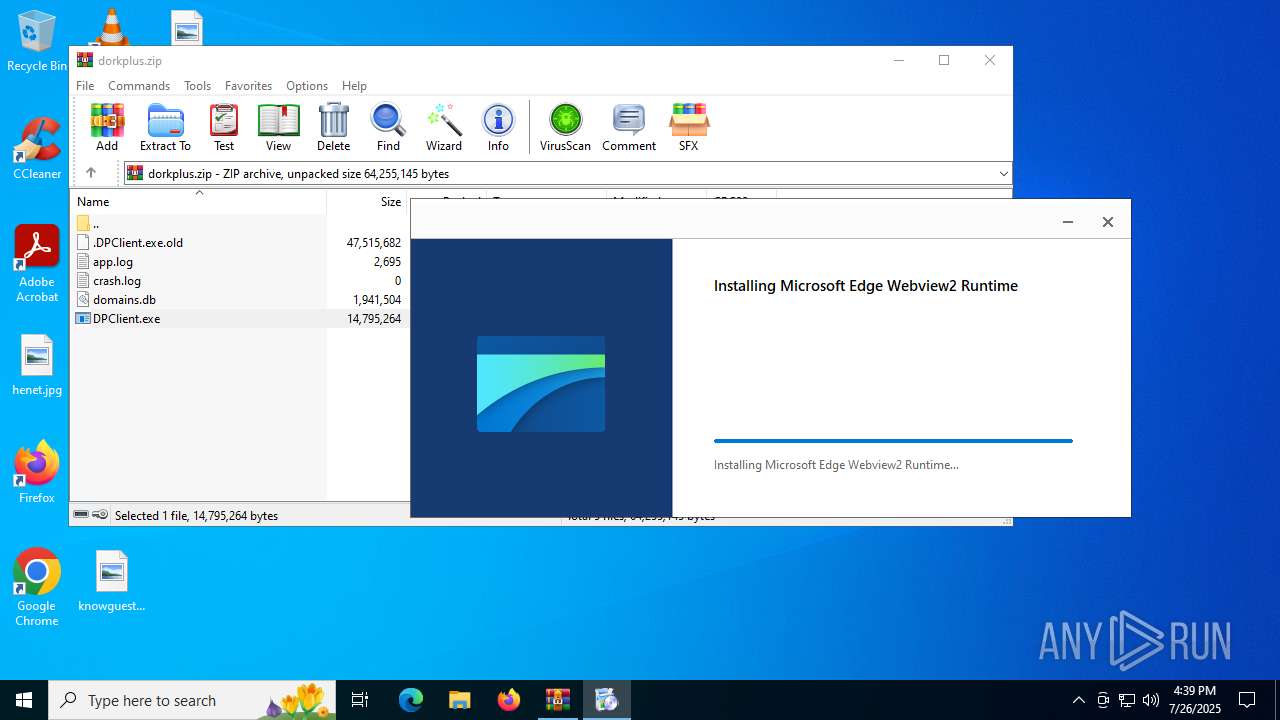
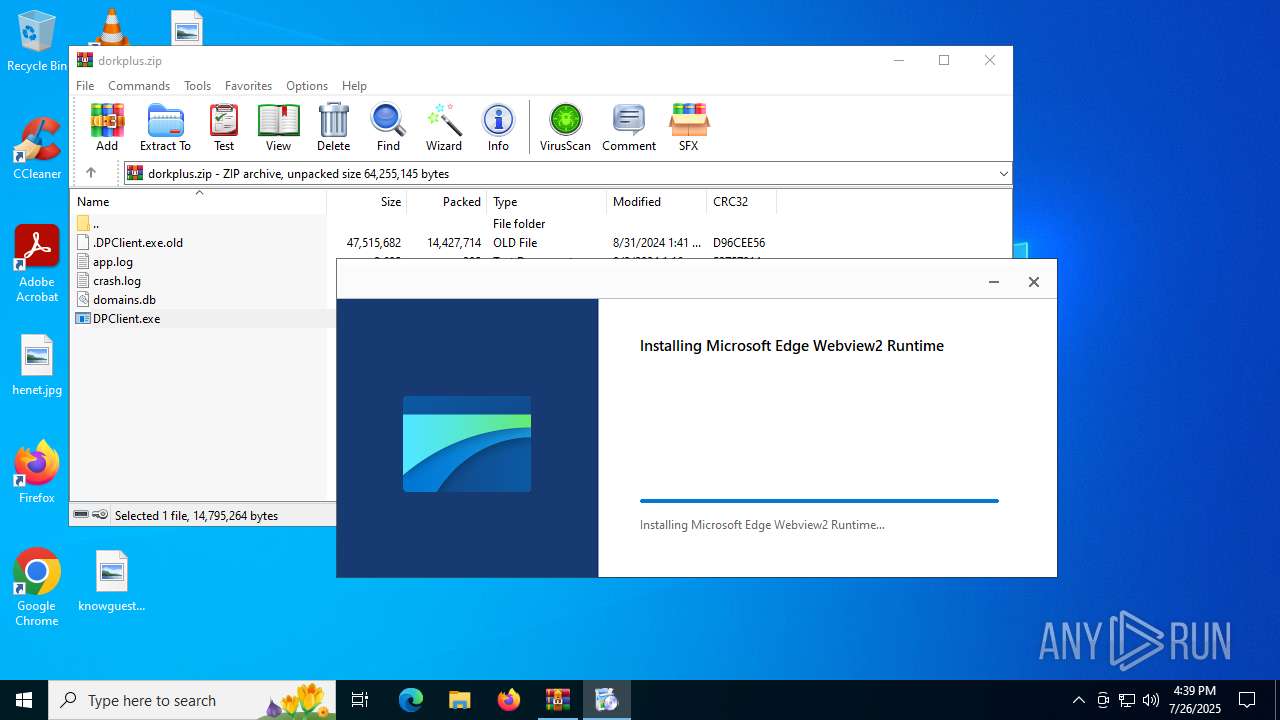
Executable content was dropped or overwritten
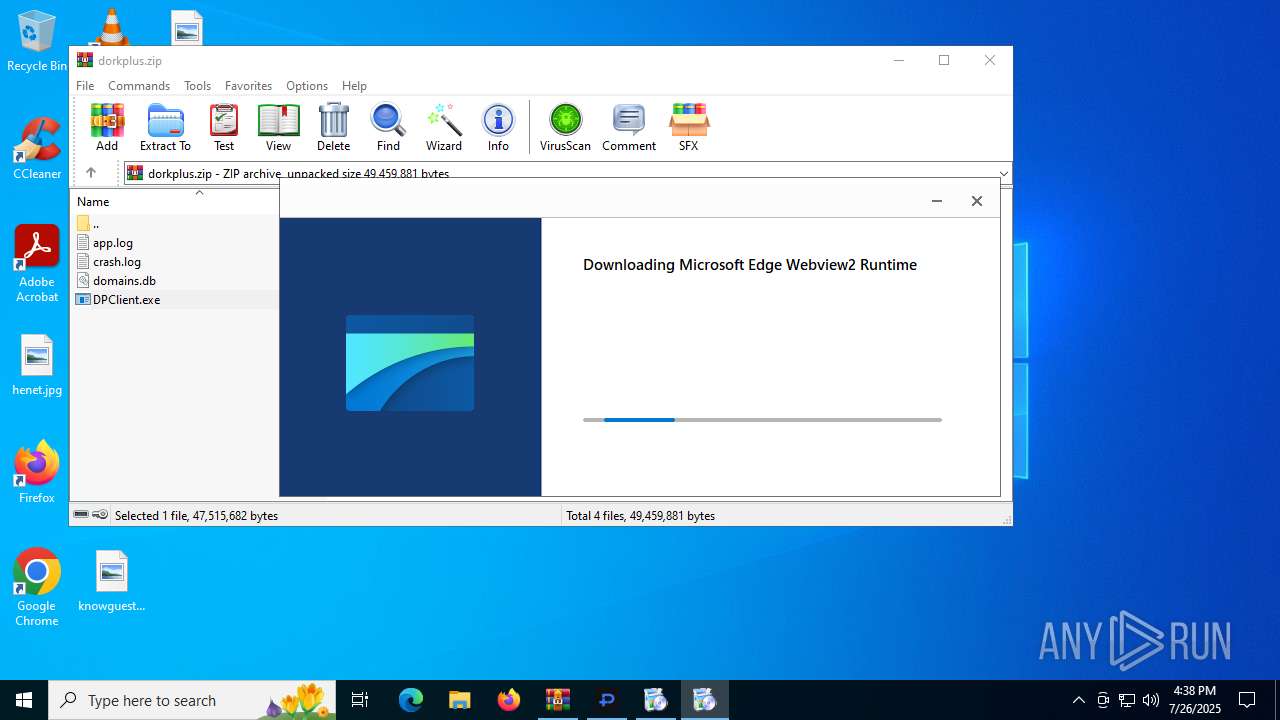
- DPClient.exe (PID: 2632)
- MicrosoftEdgeWebview2Setup.exe (PID: 4520)
- MicrosoftEdgeUpdate.exe (PID: 6812)
- setup.exe (PID: 6240)
- MicrosoftEdge_X64_138.0.3351.109.exe (PID: 4196)
- MicrosoftEdgeWebview2Setup.exe (PID: 5236)
- MicrosoftEdge_X64_138.0.3351.109.exe (PID: 6332)
Reads security settings of Internet Explorer
- WinRAR.exe (PID: 2228)
- MicrosoftEdgeUpdate.exe (PID: 7092)
- MicrosoftEdgeUpdate.exe (PID: 6812)
- MicrosoftEdgeUpdate.exe (PID: 6772)
- msedgewebview2.exe (PID: 7104)
Process drops legitimate windows executable
- DPClient.exe (PID: 2632)
- MicrosoftEdgeWebview2Setup.exe (PID: 4520)
- MicrosoftEdgeUpdate.exe (PID: 6812)
- MicrosoftEdge_X64_138.0.3351.109.exe (PID: 4196)
- setup.exe (PID: 6240)
- MicrosoftEdgeWebview2Setup.exe (PID: 5236)
- MicrosoftEdge_X64_138.0.3351.109.exe (PID: 6332)
Starts a Microsoft application from unusual location
- MicrosoftEdgeWebview2Setup.exe (PID: 4520)
- MicrosoftEdgeUpdate.exe (PID: 6812)
- MicrosoftEdgeWebview2Setup.exe (PID: 5236)
- MicrosoftEdgeUpdate.exe (PID: 6772)
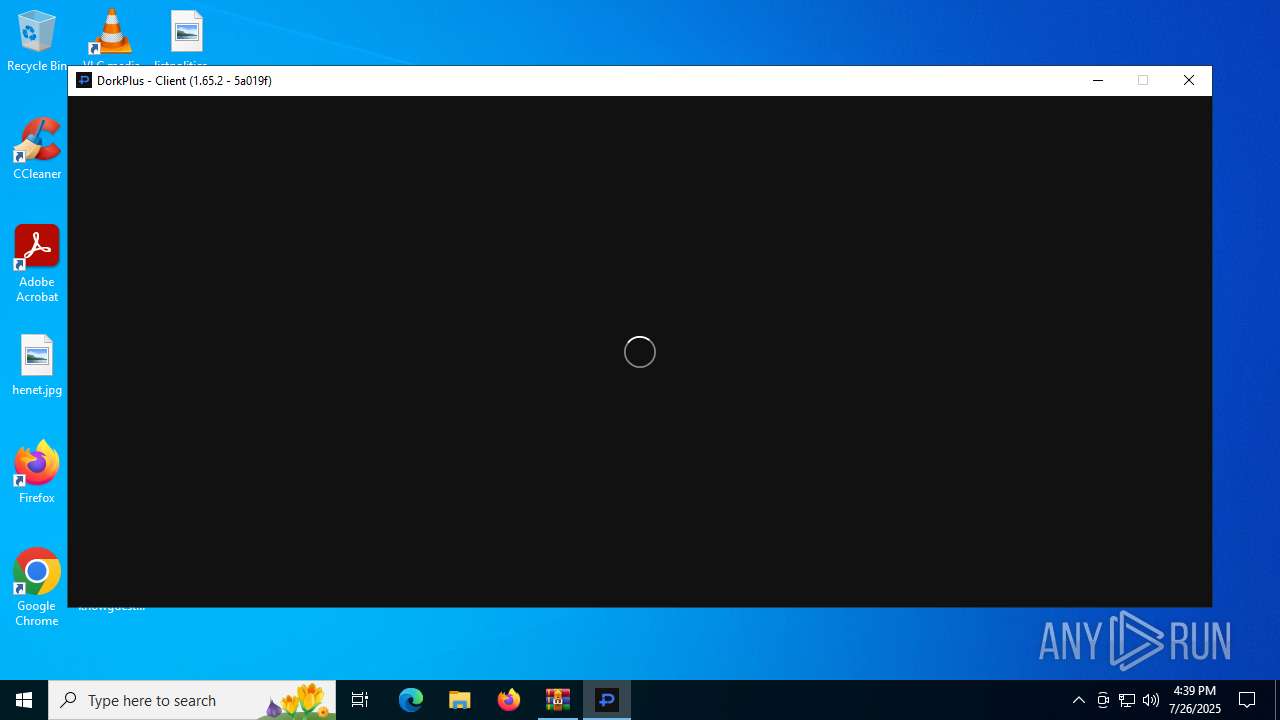
Application launched itself
- DPClient.exe (PID: 2632)
- setup.exe (PID: 6240)
- MicrosoftEdgeUpdate.exe (PID: 7092)
- setup.exe (PID: 5460)
- MicrosoftEdgeUpdate.exe (PID: 5476)
- msedgewebview2.exe (PID: 7104)
Starts itself from another location
- MicrosoftEdgeUpdate.exe (PID: 6812)
- MicrosoftEdgeUpdate.exe (PID: 6772)
Creates/Modifies COM task schedule object
- MicrosoftEdgeUpdateComRegisterShell64.exe (PID: 6236)
- MicrosoftEdgeUpdateComRegisterShell64.exe (PID: 5780)
- MicrosoftEdgeUpdate.exe (PID: 1588)
- MicrosoftEdgeUpdateComRegisterShell64.exe (PID: 5232)
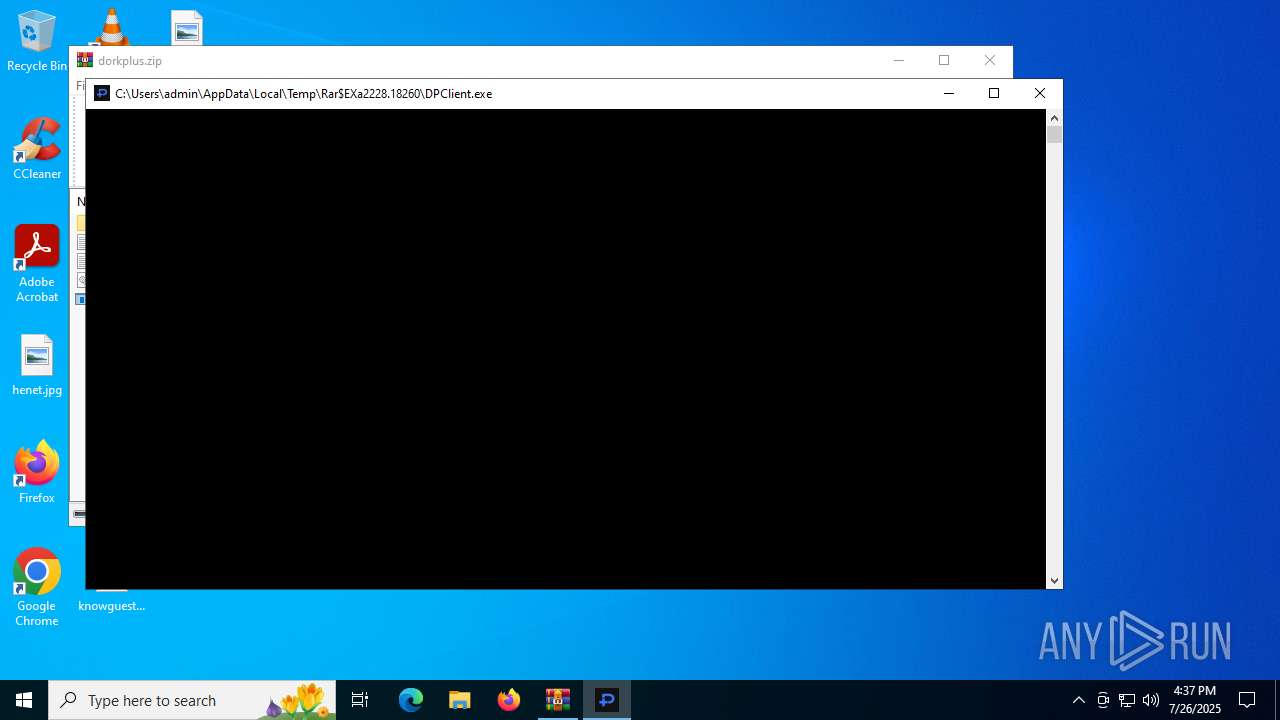
There is functionality for taking screenshot (YARA)
- DPClient.exe (PID: 2580)
Searches for installed software
- setup.exe (PID: 6240)
- setup.exe (PID: 5460)
Creates a software uninstall entry
- setup.exe (PID: 6240)
- setup.exe (PID: 5460)
Executes as Windows Service
- WmiApSrv.exe (PID: 4760)
Connects to unusual port
- DPClient.exe (PID: 2580)
INFO
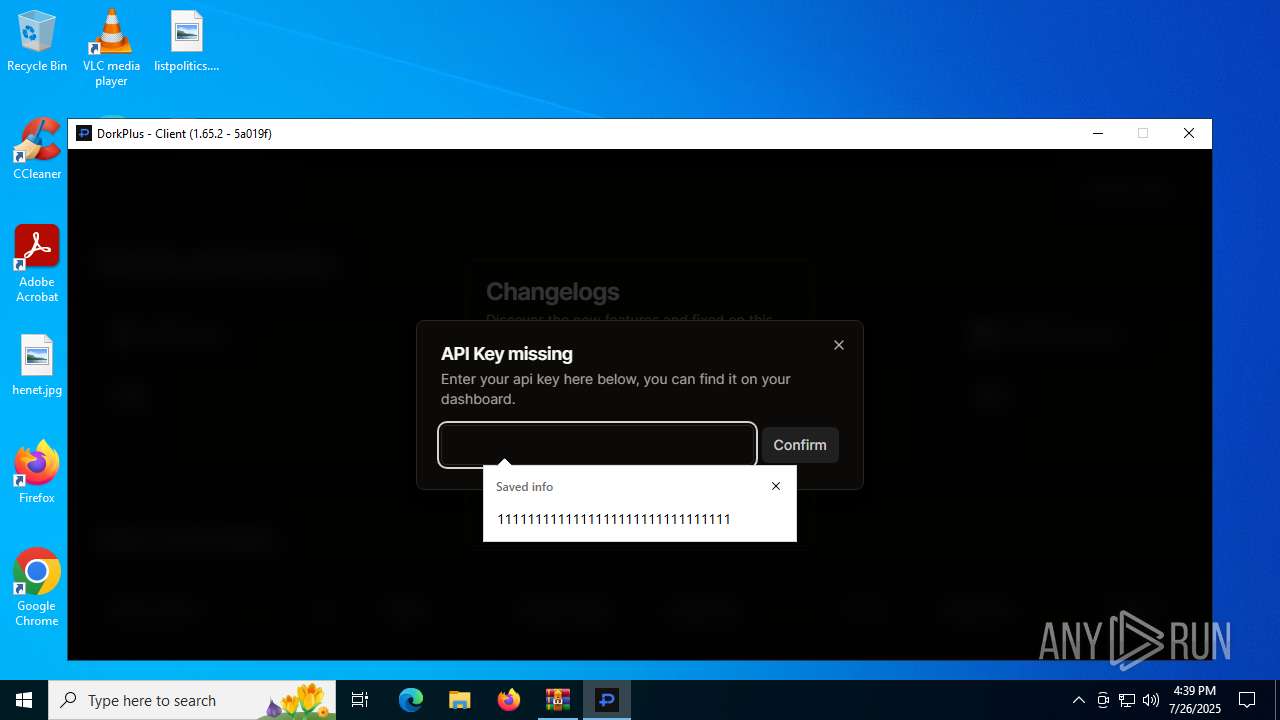
Reads the machine GUID from the registry
- DPClient.exe (PID: 2632)
- DPClient.exe (PID: 2580)
- MicrosoftEdgeUpdate.exe (PID: 7092)
- msedgewebview2.exe (PID: 7104)
Checks supported languages
- DPClient.exe (PID: 2632)
- MicrosoftEdgeWebview2Setup.exe (PID: 4520)
- MicrosoftEdgeUpdate.exe (PID: 6812)
- MicrosoftEdgeUpdate.exe (PID: 1588)
- MicrosoftEdgeUpdateComRegisterShell64.exe (PID: 6236)
- MicrosoftEdgeUpdateComRegisterShell64.exe (PID: 5780)
- MicrosoftEdgeUpdateComRegisterShell64.exe (PID: 5232)
- MicrosoftEdgeUpdate.exe (PID: 6772)
- MicrosoftEdgeUpdate.exe (PID: 5188)
- MicrosoftEdgeUpdate.exe (PID: 7092)
- MicrosoftEdge_X64_138.0.3351.109.exe (PID: 4196)
- setup.exe (PID: 6240)
- setup.exe (PID: 2216)
- MicrosoftEdgeWebview2Setup.exe (PID: 5236)
- MicrosoftEdgeUpdate.exe (PID: 1712)
- MicrosoftEdgeUpdate.exe (PID: 4684)
- MicrosoftEdgeUpdate.exe (PID: 4832)
- MicrosoftEdgeUpdate.exe (PID: 6772)
- DPClient.exe (PID: 2580)
- MicrosoftEdgeUpdate.exe (PID: 6392)
- MicrosoftEdgeUpdate.exe (PID: 5476)
- MicrosoftEdge_X64_138.0.3351.109.exe (PID: 6332)
- MicrosoftEdgeUpdate.exe (PID: 6788)
- setup.exe (PID: 5460)
- setup.exe (PID: 6668)
- msedgewebview2.exe (PID: 7104)
- msedgewebview2.exe (PID: 2692)
- msedgewebview2.exe (PID: 4264)
- msedgewebview2.exe (PID: 7048)
- msedgewebview2.exe (PID: 5372)
- msedgewebview2.exe (PID: 1864)
Reads the computer name
- DPClient.exe (PID: 2632)
- DPClient.exe (PID: 2580)
- MicrosoftEdgeUpdate.exe (PID: 6812)
- MicrosoftEdgeUpdate.exe (PID: 1588)
- MicrosoftEdgeUpdateComRegisterShell64.exe (PID: 5780)
- MicrosoftEdgeUpdate.exe (PID: 6772)
- MicrosoftEdgeUpdateComRegisterShell64.exe (PID: 5232)
- MicrosoftEdgeUpdate.exe (PID: 5188)
- MicrosoftEdgeUpdateComRegisterShell64.exe (PID: 6236)
- MicrosoftEdge_X64_138.0.3351.109.exe (PID: 4196)
- MicrosoftEdgeUpdate.exe (PID: 7092)
- setup.exe (PID: 6240)
- MicrosoftEdgeUpdate.exe (PID: 4832)
- MicrosoftEdgeUpdate.exe (PID: 6772)
- MicrosoftEdgeUpdate.exe (PID: 1712)
- MicrosoftEdgeUpdate.exe (PID: 4684)
- MicrosoftEdgeUpdate.exe (PID: 6392)
- MicrosoftEdgeUpdate.exe (PID: 5476)
- MicrosoftEdge_X64_138.0.3351.109.exe (PID: 6332)
- setup.exe (PID: 5460)
- msedgewebview2.exe (PID: 7104)
- MicrosoftEdgeUpdate.exe (PID: 6788)
- msedgewebview2.exe (PID: 2692)
- msedgewebview2.exe (PID: 4264)
Reads the software policy settings
- DPClient.exe (PID: 2632)
- MicrosoftEdgeUpdate.exe (PID: 7092)
- MicrosoftEdgeUpdate.exe (PID: 6772)
- MicrosoftEdgeUpdate.exe (PID: 4832)
- DPClient.exe (PID: 2580)
- MicrosoftEdgeUpdate.exe (PID: 5476)
- MicrosoftEdgeUpdate.exe (PID: 6788)
- slui.exe (PID: 892)
Reads Environment values
- DPClient.exe (PID: 2632)
- DPClient.exe (PID: 2580)
- MicrosoftEdgeUpdate.exe (PID: 6772)
- MicrosoftEdgeUpdate.exe (PID: 4832)
- MicrosoftEdgeUpdate.exe (PID: 4684)
- MicrosoftEdgeUpdate.exe (PID: 6788)
- msedgewebview2.exe (PID: 7104)
Create files in a temporary directory
- DPClient.exe (PID: 2632)
- DPClient.exe (PID: 2580)
- MicrosoftEdgeWebview2Setup.exe (PID: 5236)
- MicrosoftEdgeWebview2Setup.exe (PID: 4520)
- msedgewebview2.exe (PID: 7104)
The sample compiled with english language support
- DPClient.exe (PID: 2632)
- MicrosoftEdgeWebview2Setup.exe (PID: 4520)
- MicrosoftEdgeUpdate.exe (PID: 6812)
- MicrosoftEdge_X64_138.0.3351.109.exe (PID: 4196)
- setup.exe (PID: 6240)
- MicrosoftEdgeWebview2Setup.exe (PID: 5236)
- MicrosoftEdge_X64_138.0.3351.109.exe (PID: 6332)
Creates files or folders in the user directory
- MicrosoftEdgeUpdate.exe (PID: 6812)
- MicrosoftEdgeUpdate.exe (PID: 7092)
- setup.exe (PID: 2216)
- setup.exe (PID: 6240)
- MicrosoftEdge_X64_138.0.3351.109.exe (PID: 4196)
- MicrosoftEdgeUpdate.exe (PID: 5476)
- MicrosoftEdge_X64_138.0.3351.109.exe (PID: 6332)
- setup.exe (PID: 5460)
- msedgewebview2.exe (PID: 7104)
- msedgewebview2.exe (PID: 1864)
- msedgewebview2.exe (PID: 4264)
Launching a file from a Registry key
- MicrosoftEdgeUpdate.exe (PID: 6812)
Checks proxy server information
- MicrosoftEdgeUpdate.exe (PID: 7092)
- MicrosoftEdgeUpdate.exe (PID: 6772)
- MicrosoftEdgeUpdate.exe (PID: 4832)
- MicrosoftEdgeUpdate.exe (PID: 5476)
- MicrosoftEdgeUpdate.exe (PID: 6788)
- msedgewebview2.exe (PID: 7104)
- slui.exe (PID: 892)
Detects GO elliptic curve encryption (YARA)
- DPClient.exe (PID: 2580)
Application based on Golang
- DPClient.exe (PID: 2580)
Process checks computer location settings
- MicrosoftEdgeUpdate.exe (PID: 6812)
- setup.exe (PID: 6240)
- MicrosoftEdgeUpdate.exe (PID: 6772)
- setup.exe (PID: 5460)
- msedgewebview2.exe (PID: 7104)
- msedgewebview2.exe (PID: 5372)
Reads CPU info
- msedgewebview2.exe (PID: 7104)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .zip | | | ZIP compressed archive (100) |
|---|
EXIF
ZIP
| ZipRequiredVersion: | 20 |
|---|---|
| ZipBitFlag: | - |
| ZipCompression: | Deflated |
| ZipModifyDate: | 2024:09:02 04:16:10 |
| ZipCRC: | 0x5375701a |
| ZipCompressedSize: | 300 |
| ZipUncompressedSize: | 2695 |
| ZipFileName: | app.log |
Total processes
178
Monitored processes
35
Malicious processes
10
Suspicious processes
6
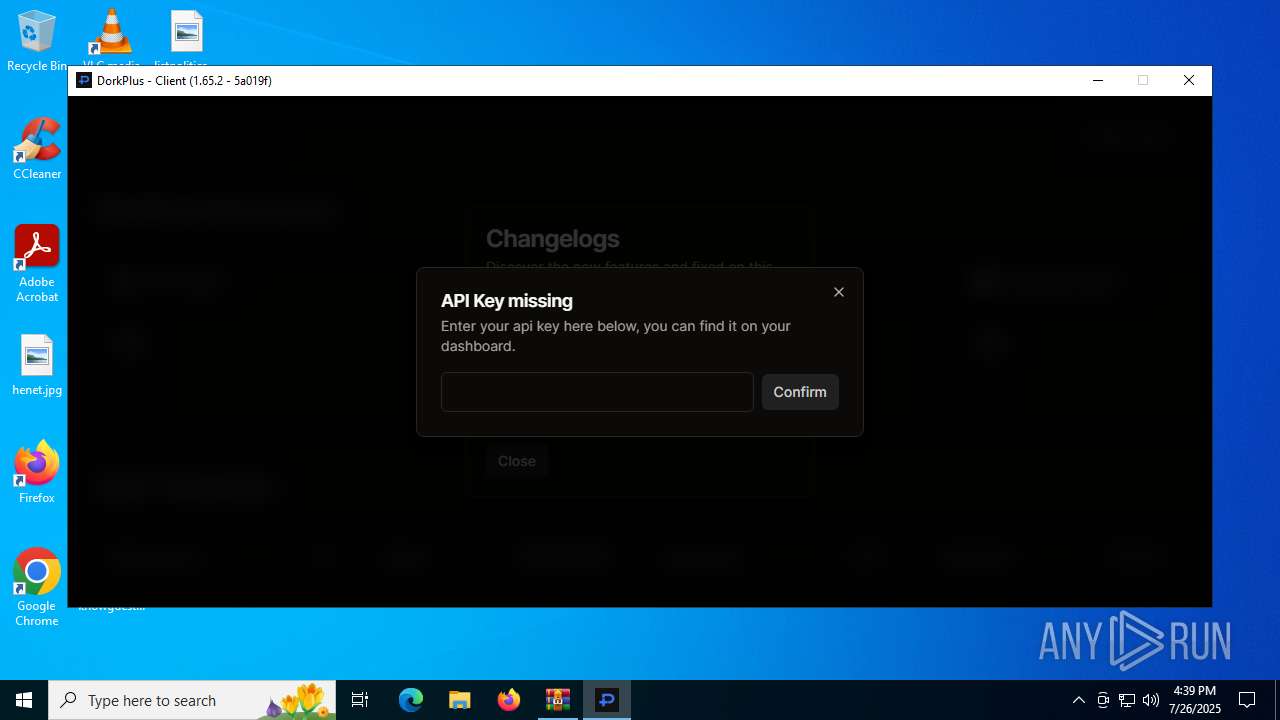
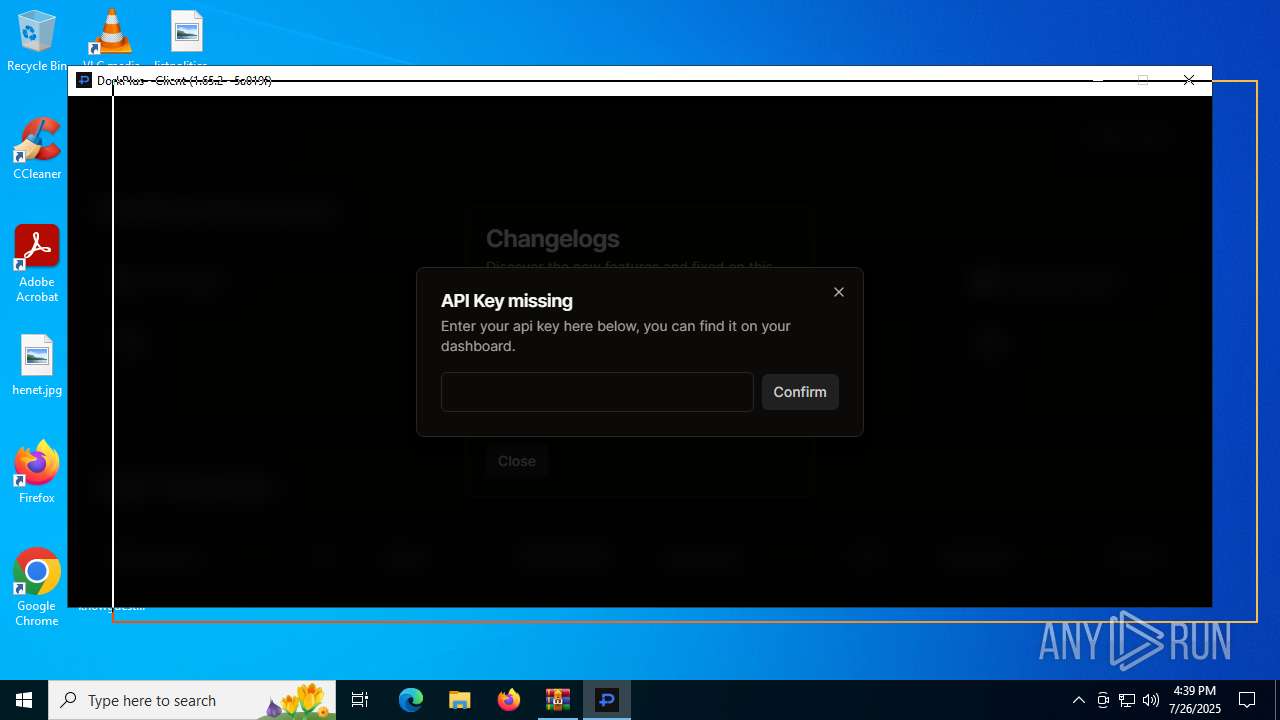
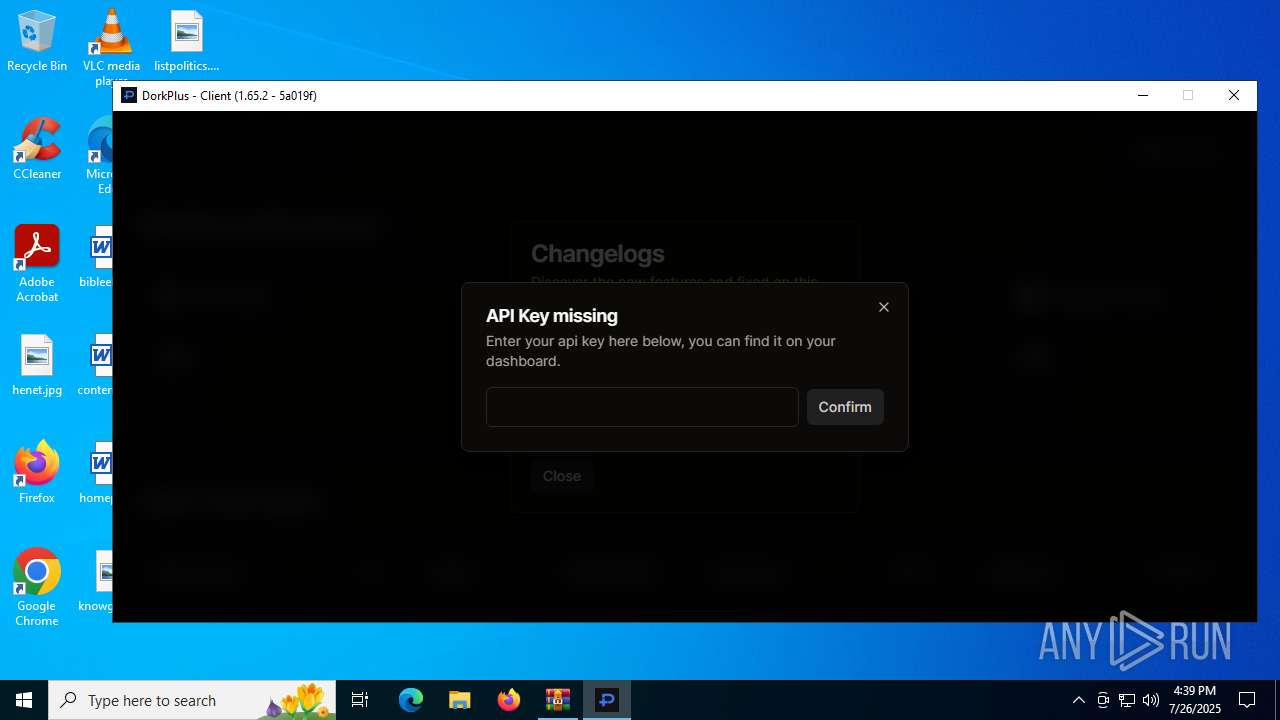
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 892 | C:\WINDOWS\System32\slui.exe -Embedding | C:\Windows\System32\slui.exe | svchost.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Activation Client Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1588 | "C:\Users\admin\AppData\Local\Microsoft\EdgeUpdate\MicrosoftEdgeUpdate.exe" /regserver | C:\Users\admin\AppData\Local\Microsoft\EdgeUpdate\MicrosoftEdgeUpdate.exe | — | MicrosoftEdgeUpdate.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Update Exit code: 0 Version: 1.3.195.61 Modules
| |||||||||||||||
| 1712 | "C:\Users\admin\AppData\Local\Microsoft\EdgeUpdate\MicrosoftEdgeUpdate.exe" /healthcheck | C:\Users\admin\AppData\Local\Microsoft\EdgeUpdate\MicrosoftEdgeUpdate.exe | — | MicrosoftEdgeUpdate.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Update Exit code: 0 Version: 1.3.195.61 Modules
| |||||||||||||||
| 1864 | C:\Users\admin\AppData\Local\Microsoft\EdgeWebView\Application\138.0.3351.109\msedgewebview2.exe --type=crashpad-handler --user-data-dir=C:\Users\admin\AppData\Roaming\DPClient.exe\EBWebView /prefetch:4 --monitor-self-annotation=ptype=crashpad-handler --database=C:\Users\admin\AppData\Roaming\DPClient.exe\EBWebView\Crashpad --annotation=IsOfficialBuild=1 --annotation=channel= --annotation=chromium-version=138.0.7204.169 --annotation=exe=C:\Users\admin\AppData\Local\Microsoft\EdgeWebView\Application\138.0.3351.109\msedgewebview2.exe --annotation=plat=Win64 "--annotation=prod=Edge WebView2" --annotation=ver=138.0.3351.109 --initial-client-data=0x188,0x18c,0x190,0x184,0x160,0x7ffc44afa178,0x7ffc44afa184,0x7ffc44afa190 | C:\Users\admin\AppData\Local\Microsoft\EdgeWebView\Application\138.0.3351.109\msedgewebview2.exe | — | msedgewebview2.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge WebView2 Version: 138.0.3351.109 Modules
| |||||||||||||||
| 2216 | C:\Users\admin\AppData\Local\Microsoft\EdgeUpdate\Install\{8FE852B6-4875-444B-A1DA-F5E18FCDA828}\EDGEMITMP_D3967.tmp\setup.exe --type=crashpad-handler /prefetch:4 --monitor-self-annotation=ptype=crashpad-handler "--database=C:\Users\admin\AppData\Local\Microsoft\EdgeWebView\User Data\Crashpad" --annotation=IsOfficialBuild=1 --annotation=channel= --annotation=chromium-version=138.0.7204.169 --annotation=exe=C:\Users\admin\AppData\Local\Microsoft\EdgeUpdate\Install\{8FE852B6-4875-444B-A1DA-F5E18FCDA828}\EDGEMITMP_D3967.tmp\setup.exe --annotation=plat=Win64 --annotation=prod=Edge --annotation=ver=138.0.3351.109 --initial-client-data=0x298,0x29c,0x2a0,0x274,0x2a4,0x7ff65349d4c8,0x7ff65349d4d4,0x7ff65349d4e0 | C:\Users\admin\AppData\Local\Microsoft\EdgeUpdate\Install\{8FE852B6-4875-444B-A1DA-F5E18FCDA828}\EDGEMITMP_D3967.tmp\setup.exe | — | setup.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Installer Exit code: 0 Version: 138.0.3351.109 Modules
| |||||||||||||||
| 2228 | "C:\Program Files\WinRAR\WinRAR.exe" C:\Users\admin\Desktop\dorkplus.zip | C:\Program Files\WinRAR\WinRAR.exe | — | explorer.exe | |||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Version: 5.91.0 Modules
| |||||||||||||||
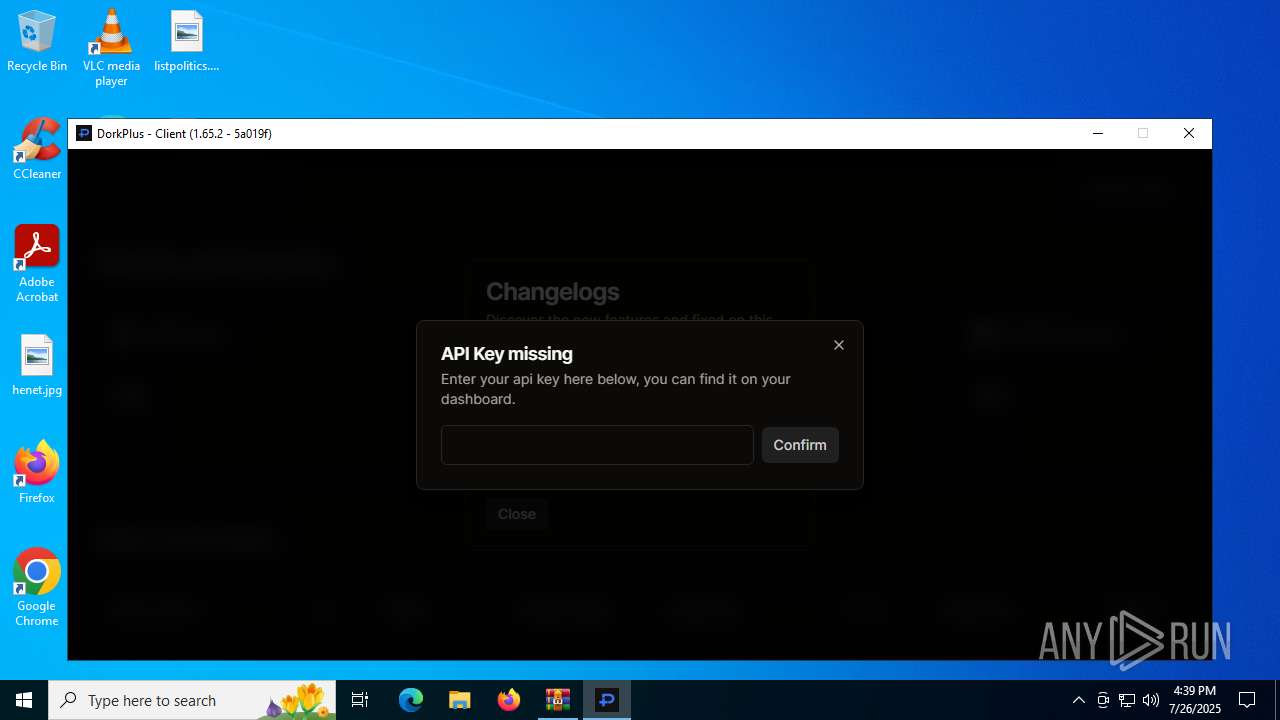
| 2580 | C:\Users\admin\AppData\Local\Temp\Rar$EXa2228.18260\DPClient.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXa2228.18260\DPClient.exe | DPClient.exe | ||||||||||||
User: admin Company: DPClient Integrity Level: MEDIUM Description: DPClient Modules
| |||||||||||||||
| 2632 | "C:\Users\admin\AppData\Local\Temp\Rar$EXa2228.18260\DPClient.exe" | C:\Users\admin\AppData\Local\Temp\Rar$EXa2228.18260\DPClient.exe | WinRAR.exe | ||||||||||||
User: admin Company: DPClient Integrity Level: MEDIUM Description: DPClient Exit code: 0 Modules
| |||||||||||||||
| 2692 | "C:\Users\admin\AppData\Local\Microsoft\EdgeWebView\Application\138.0.3351.109\msedgewebview2.exe" --type=gpu-process --noerrdialogs --user-data-dir="C:\Users\admin\AppData\Roaming\DPClient.exe\EBWebView" --webview-exe-name=DPClient.exe --webview-exe-version=1.0.0 --embedded-browser-webview=1 --embedded-browser-webview-dpi-awareness=2 --no-pre-read-main-dll --force-high-res-timeticks=disabled --gpu-preferences=UAAAAAAAAADgAAAEAAAAAAAAAAAAAAAAAABgAAEAAAAAAAAAAAAAAAAAAAACAAAAAAAAAAAAAAAAAAAAAAAAABAAAAAAAAAAEAAAAAAAAAAIAAAAAAAAAAgAAAAAAAAA --always-read-main-dll --field-trial-handle=1852,i,12989967321678785483,13469627126571284186,262144 --enable-features=ForceSWDCompWhenDCompFallbackRequired,msAggressiveCacheTrimming,msCustomDataPartition,msWebView2NoTabForScreenShare,msWindowsTaskManager --disable-features=BackForwardCache,BackgroundTabLoadingFromPerformanceManager,CloseOmniboxPopupOnInactiveAreaClick,CollectAVProductsInfo,CollectCodeIntegrityInfo,EnableHangWatcher,FilterAdsOnAbusiveSites,GetWifiProtocol,LoginDetection,MediaFoundationCameraUsageMonitoring,PreconnectToSearch,SafetyHub,SegmentationPlatform,SpareRendererForSitePerProcess,Ukm,WebPayments,msAITrackerClassification,msAbydosForWindowlessWV2,msAffirmVirtualCard,msAllowChromeWebstore,msAllowMSAPrtSSOForNonMSAProfile,msApplicationGuard,msAskBeforeClosingMultipleTabs,msAutoToggleAADPrtSSOForNonAADProfile,msAutofillEdgeCoupons,msAutofillEdgeCouponsAutoApply,msAutofillEdgeServiceRequest,msAutofillEnableEdgeSuggestions,msAutomaticTabFreeze,msBrowserSettingsSupported,msCoarseGeolocationService,msDataProtection,msDesktopMode,msDesktopRewards,msDisableVariationsSeedFetchThrottling,msEEProactiveHistory,msETFOffstoreExtensionFileDataCollection,msETFPasswordTheftDNRActionSignals,msEdgeAdPlatformUI,msEdgeAddWebCapturetoCollections,msEdgeAutofillShowDeployedPassword,msEdgeCaptureSelectionInPDF,msEdgeCloudConfigService,msEdgeCloudConfigServiceV2,msEdgeCohorts,msEdgeCollectionsPrismExperiment1,msEdgeCollectionsPrismOverallMigration,msEdgeComposeNext,msEdgeEnableNurturingFramework,msEdgeEnclavePrefsBasic,msEdgeEnclavePrefsNotification,msEdgeFaviconService,msEdgeHJTelemetry,msEdgeHubAppSkype,msEdgeImageEditorUI,msEdgeLinkDoctor,msEdgeMouseGestureDefaultEnabled,msEdgeMouseGestureSupported,msEdgeNewDeviceFre,msEdgeOnRampFRE,msEdgeOnRampImport,msEdgePDFCMHighlightUX,msEdgePasswordIris,msEdgePasswordIrisSaveBubble,msEdgeProngPersonalization,msEdgeReadingView,msEdgeRose,msEdgeScreenshotUI,msEdgeSendTabToSelf,msEdgeSettingsImport,msEdgeSettingsImportV2,msEdgeShoppingPersistentStorage,msEdgeShoppingUI,msEdgeSmartFind,msEdgeSuperDragDefaultEnabled,msEdgeSuperDragDropSupported,msEdgeTipping,msEdgeTranslate,msEdgeUseCaptivePortalService,msEdgeWebCapture,msEdgeWebCaptureUniformExperience,msEdgeWebContentFilteringFeedback,msEdgeWorkSearchBanner,msEnableCustomJobMemoryLimitsOnXbox,msEnableMIPForPDF,msEnablePdfUpsell,msEnableThirdPartyScanning,msEnableWebSignInCta,msEnableWebToBrowserSignIn,msEndpointDlp,msEntityExtraction,msExtensionTelemetryFramework,msExternalTaskManager,msFileSystemAccessDirectoryIterationBlocklistCheck,msForceBrowserSignIn,msForeignSessionsPage,msGeolocationAccessService,msGeolocationOSLocationPermissionFallback,msGeolocationSQMService,msGeolocationService,msGrowthInfraLaunchSourceLogging,msGuidedSwitchAllowed,msHubPinPersist,msImplicitSignin,msIrm,msIrmv2,msKlarnaVirtualCard,msLlmConsumerDlpPurview,msLoadStatistics,msLogIsEdgePinnedToTaskbarOnLaunch,msMIPCrossTenantPdfViewSupport,msMdatpWebSiteDlp,msNotificationPermissionForPWA,msNumberOfSitesToPin,msNurturingSitePinningWithWindowsConsent,msOnHoverSearchInSidebar,msOpenOfficeDocumentsInWebViewer,msPasswordBreachDetection,msPdfAnnotationsVisibility,msPdfDataRecovery,msPdfDigitalSignatureRead,msPdfFreeText,msPdfFreeTextForCJK,msPdfHighlightMode,msPdfInking,msPdfKeyphraseSupport,msPdfOOUI,msPdfPopupMarkerRenderer,msPdfShare,msPdfSharedLibrary,msPdfTextNote,msPdfTextNoteMoreMenu,msPdfThumbnailCache,msPdfUnderside,msPdfViewRestore,msPersonalizationUMA,msPriceComparison,msPromptDefaultHandlerForPDF,msReactiveSearch,msReadAloud,msReadAloudPdf,msRedirectToShoreline,msRevokeExtensions,msSaasDlp,msShoppingTrigger,msShorelineSearch,msShorelineSearchFindOnPageWebUI,msShowOfflineGameEntrance,msShowReadAloudIconInAddressBar,msShowUXForAADPrtSSOForNonAADProfile,msSitePinningWithoutUi,msSmartScreenProtection,msSuspendMessageForNewSessionWhenHavingPendingNavigation,msSyncEdgeCollections,msTabResourceStats,msTokenizationAutofillInlineEnabled,msTouchMode,msTriggeringSignalGenerator,msUserUnderstanding,msVideoSuperResolutionUI,msWalletBuyNow,msWalletCheckout,msWalletDiagnosticDataLogger,msWalletHubEntry,msWalletHubIntlP3,msWalletPartialCard,msWalletPasswordCategorization,msWalletPasswordCategorizationPlatformExpansion,msWalletTokenizationCardMetadata,msWalletTokenizedAutofill,msWebAssist,msWebAssistHistorySearchService,msWebOOUI,msWindowsUserActivities,msZipPayVirtualCard --variations-seed-version --mojo-platform-channel-handle=1848 /prefetch:2 | C:\Users\admin\AppData\Local\Microsoft\EdgeWebView\Application\138.0.3351.109\msedgewebview2.exe | — | msedgewebview2.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge WebView2 Version: 138.0.3351.109 Modules
| |||||||||||||||
| 4196 | "C:\Users\admin\AppData\Local\Microsoft\EdgeUpdate\Install\{8FE852B6-4875-444B-A1DA-F5E18FCDA828}\MicrosoftEdge_X64_138.0.3351.109.exe" --msedgewebview --verbose-logging --do-not-launch-msedge --user-level | C:\Users\admin\AppData\Local\Microsoft\EdgeUpdate\Install\{8FE852B6-4875-444B-A1DA-F5E18FCDA828}\MicrosoftEdge_X64_138.0.3351.109.exe | MicrosoftEdgeUpdate.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Installer Exit code: 0 Version: 138.0.3351.109 Modules
| |||||||||||||||
Total events
23 352
Read events
20 891
Write events
2 351
Delete events
110
Modification events
| (PID) Process: | (2228) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 3 |
Value: C:\Users\admin\Desktop\preferences.zip | |||
| (PID) Process: | (2228) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 2 |
Value: C:\Users\admin\Desktop\chromium_ext.zip | |||
| (PID) Process: | (2228) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 1 |
Value: C:\Users\admin\Desktop\omni_23_10_2024_.zip | |||
| (PID) Process: | (2228) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\Desktop\dorkplus.zip | |||
| (PID) Process: | (2228) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (2228) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (2228) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (2228) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (6812) MicrosoftEdgeUpdate.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\EdgeUpdate |
| Operation: | write | Name: | path |
Value: C:\Users\admin\AppData\Local\Microsoft\EdgeUpdate\MicrosoftEdgeUpdate.exe | |||
| (PID) Process: | (6812) MicrosoftEdgeUpdate.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\EdgeUpdate |
| Operation: | write | Name: | UninstallCmdLine |
Value: "C:\Users\admin\AppData\Local\Microsoft\EdgeUpdate\MicrosoftEdgeUpdate.exe" /uninstall | |||
Executable files
316
Suspicious files
130
Text files
29
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2228 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXa2228.18260\DPClient.exe | — | |
MD5:— | SHA256:— | |||
| 2632 | DPClient.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXa2228.18260\.DPClient.exe.old | — | |
MD5:— | SHA256:— | |||
| 2632 | DPClient.exe | C:\Users\admin\AppData\Local\Temp\MicrosoftEdgeWebview2Setup.exe | executable | |
MD5:5424BAC02DB3D21E75C21FF2049CD04F | SHA256:3C60FDBD71B468CF52FDE6F780740A910C9D190E7023B1AC1217D427D794CCB1 | |||
| 4520 | MicrosoftEdgeWebview2Setup.exe | C:\Users\admin\AppData\Local\Temp\EUF9DC.tmp\MicrosoftEdgeUpdate.exe | executable | |
MD5:570D4E78E4EF679C9435247685F8A8D3 | SHA256:5CDF1C3C7F72120CA88145D38E48C9E1E6A6BD4EF43021193FD76D98D2F05496 | |||
| 2228 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXa2228.18260\app.log | text | |
MD5:4BC4CE162B46A500CB58F9F4541EA7D2 | SHA256:FA1109185D4267E8FBD10B6B958D1959DDA923B84CB9D04EF5B77D0163CEFD80 | |||
| 2228 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXa2228.18260\domains.db | binary | |
MD5:7C44F232A2F8F49225DAFB0B51E0D276 | SHA256:9FACE0239ECE675E1EC2785C2837C80D0C8D8A93879D0FE5374D29595F55E27F | |||
| 2632 | DPClient.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXa2228.18260\.DPClient.exe.new | executable | |
MD5:4D3D1458A77C3B233E36252E6D4C4F9F | SHA256:5A019FE5656D38CAF2881F4754E14F8824CE78EE5231F292D6FD395CEA039391 | |||
| 4520 | MicrosoftEdgeWebview2Setup.exe | C:\Users\admin\AppData\Local\Temp\EUF9DC.tmp\msedgeupdate.dll | executable | |
MD5:750D6630199F17068FF1CE9F2F351DD8 | SHA256:36BBE422572AA67CD61CB6ACCFC0D68A8FCD32D72405B504C2FF576BEDB8E35C | |||
| 2632 | DPClient.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXa2228.18260\DPClient.exe | executable | |
MD5:4D3D1458A77C3B233E36252E6D4C4F9F | SHA256:5A019FE5656D38CAF2881F4754E14F8824CE78EE5231F292D6FD395CEA039391 | |||
| 4520 | MicrosoftEdgeWebview2Setup.exe | C:\Users\admin\AppData\Local\Temp\EUF9DC.tmp\MicrosoftEdgeUpdateBroker.exe | executable | |
MD5:7AE279F8F5FC1A139FC3FA06BF28BC59 | SHA256:9E259500EBA6A26384161A28A92F2DEDBDD6B1073DE46D8FEC74E03762E031D4 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
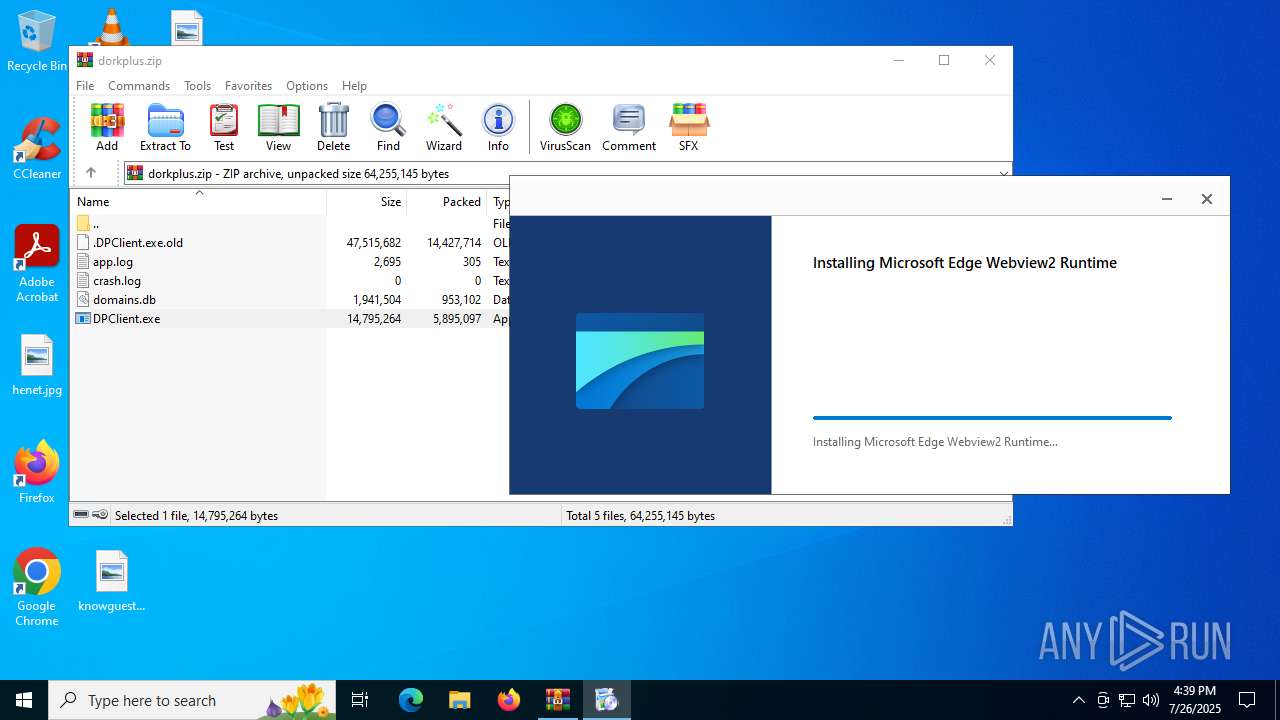
HTTP(S) requests
28
TCP/UDP connections
55
DNS requests
32
Threats
8
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
1268 | svchost.exe | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | DE | binary | 814 b | whitelisted |
1268 | svchost.exe | GET | 200 | 23.216.77.41:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | DE | binary | 825 b | whitelisted |
7084 | svchost.exe | HEAD | 200 | 23.48.23.56:80 | http://msedge.f.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/2914ef46-1278-4055-94b7-c97988099725?P1=1754152682&P2=404&P3=2&P4=gFCnQ%2fuT6R8OgzX9h7myZtb2Jkrmw5gqXfSxc0B%2fTwIhs5a8cwcpPrYET7N%2bwN8FBVNGajH%2feYSNCdDUri18%2fQ%3d%3d | DE | — | — | whitelisted |
7084 | svchost.exe | GET | — | 23.48.23.56:80 | http://msedge.f.tlu.dl.delivery.mp.microsoft.com/filestreamingservice/files/2914ef46-1278-4055-94b7-c97988099725?P1=1754152682&P2=404&P3=2&P4=gFCnQ%2fuT6R8OgzX9h7myZtb2Jkrmw5gqXfSxc0B%2fTwIhs5a8cwcpPrYET7N%2bwN8FBVNGajH%2feYSNCdDUri18%2fQ%3d%3d | DE | — | — | whitelisted |
4168 | svchost.exe | GET | 200 | 184.30.131.245:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | US | binary | 471 b | whitelisted |
5576 | SIHClient.exe | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | DE | binary | 420 b | whitelisted |
5576 | SIHClient.exe | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | DE | binary | 408 b | whitelisted |
2940 | svchost.exe | GET | 200 | 72.246.169.163:80 | http://x1.c.lencr.org/ | DE | binary | 734 b | whitelisted |
2580 | DPClient.exe | GET | 200 | 78.46.109.57:4657 | http://78.46.109.57:4657/api/ip?ver=1.65.2&source=client&t=1753547981 | DE | binary | 29 b | unknown |
2580 | DPClient.exe | POST | 500 | 78.46.109.57:4657 | http://78.46.109.57:4657/api/user/machines/add?ver=1.65.2&source=client&t=1753547982 | DE | binary | 241 b | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
5944 | MoUsoCoreWorker.exe | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
1268 | svchost.exe | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
5876 | RUXIMICS.exe | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
1268 | svchost.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
1268 | svchost.exe | 23.216.77.41:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
1268 | svchost.exe | 23.35.229.160:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
2632 | DPClient.exe | 104.21.10.128:443 | api.dorkplus.com | CLOUDFLARENET | — | unknown |
2632 | DPClient.exe | 23.35.238.131:443 | go.microsoft.com | AKAMAI-AS | DE | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
api.dorkplus.com |
| unknown |
go.microsoft.com |
| whitelisted |
msedge.sf.dl.delivery.mp.microsoft.com |
| whitelisted |
config.edge.skype.com |
| whitelisted |
msedge.api.cdp.microsoft.com |
| whitelisted |
msedge.f.tlu.dl.delivery.mp.microsoft.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
— | — | Unknown Traffic | ET USER_AGENTS Microsoft Dr Watson User-Agent (MSDW) |
7084 | svchost.exe | Misc activity | ET INFO Packed Executable Download |
4264 | msedgewebview2.exe | Not Suspicious Traffic | INFO [ANY.RUN] Requests to a free CDN for open source projects (jsdelivr .net) |
4264 | msedgewebview2.exe | Not Suspicious Traffic | INFO [ANY.RUN] Requests to a free CDN for open source projects (jsdelivr .net) |
4264 | msedgewebview2.exe | Generic Protocol Command Decode | SURICATA QUIC failed decrypt |
4264 | msedgewebview2.exe | Generic Protocol Command Decode | SURICATA QUIC failed decrypt |
4264 | msedgewebview2.exe | Generic Protocol Command Decode | SURICATA QUIC failed decrypt |
4264 | msedgewebview2.exe | Generic Protocol Command Decode | SURICATA QUIC failed decrypt |
Process | Message |
|---|---|
msedgewebview2.exe | RecursiveDirectoryCreate( C:\Users\admin\AppData\Roaming directory exists )
|
DPClient.exe | Warning: AddWebResourceRequestedFilter without SourceKind parameter is deprecated! It does not behave as expected for iframes.Please use AddWebResourceRequestedFilterWithRequestSourceKinds instead. For more information, please see https://go.microsoft.com/fwlink/?linkid=2286319 |