| File name: | 641d1e752250d27556de774dbb3692d24c4236595ee0e26cc055d4ab5e9cdbe0.doc |
| Full analysis: | https://app.any.run/tasks/eabff2e4-81bc-409b-a58d-94444f0b9b37 |
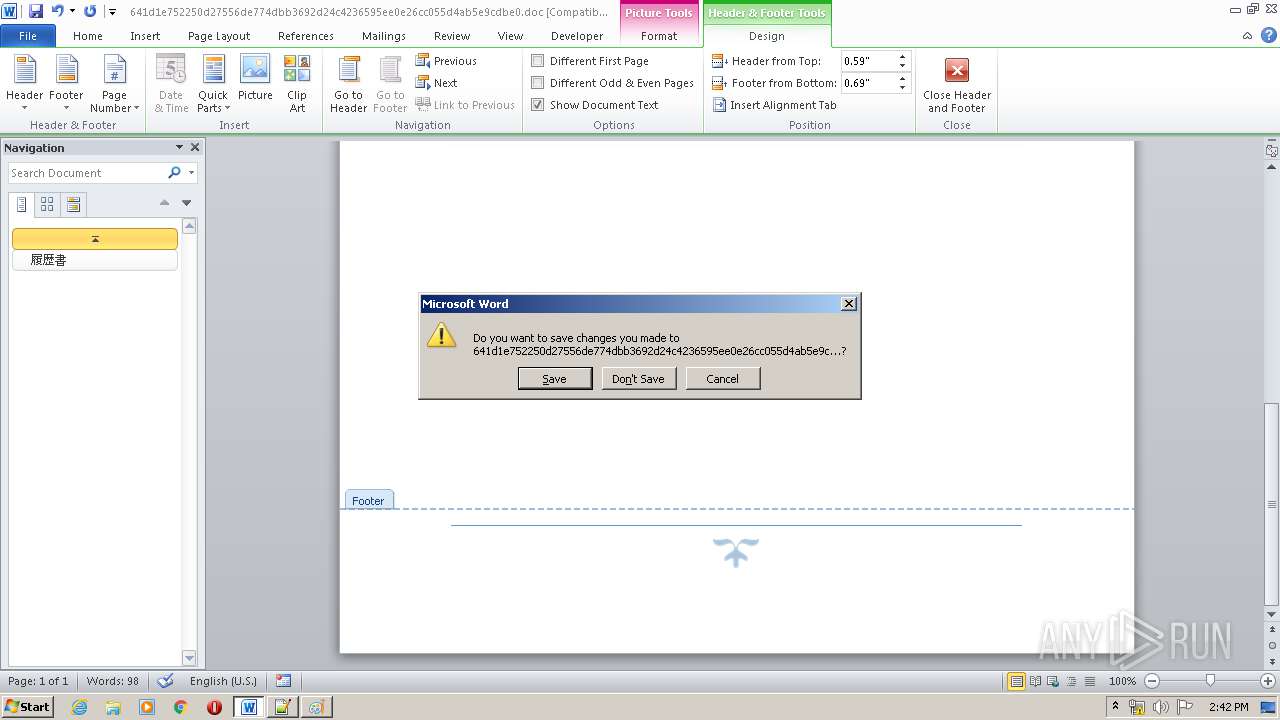
| Verdict: | Malicious activity |
| Analysis date: | May 20, 2020, 13:41:09 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/msword |
| File info: | Composite Document File V2 Document, Little Endian, Os: Windows, Version 10.0, Code page: 932, Template: Normal.dotm, Revision Number: 17, Total Editing Time: 01:39:00, Create Time/Date: Mon May 18 03:08:00 2020, Last Saved Time/Date: Tue May 19 04:07:00 2020, Number of Pages: 1, Number of Words: 21, Number of Characters: 121, Security: 0 |
| MD5: | C031B786CB0A7479CC72D299DAB2F0E3 |
| SHA1: | 10FA9313309A00955EC8F49B639909C4ED124AC4 |
| SHA256: | 641D1E752250D27556DE774DBB3692D24C4236595EE0E26CC055D4AB5E9CDBE0 |
| SSDEEP: | 12288:/esFbPMTAdMFfU6p+t2tLf26NB6Y6mAmh/pELQ/R0Vks/HT2ZIe4mbe8P:2sbPHj61Le6X6WEcRtF4i/P |
MALICIOUS
Loads dropped or rewritten executable
- SfsDllSample.exe (PID: 2296)
Application was dropped or rewritten from another process
- SfsDllSample.exe (PID: 2296)
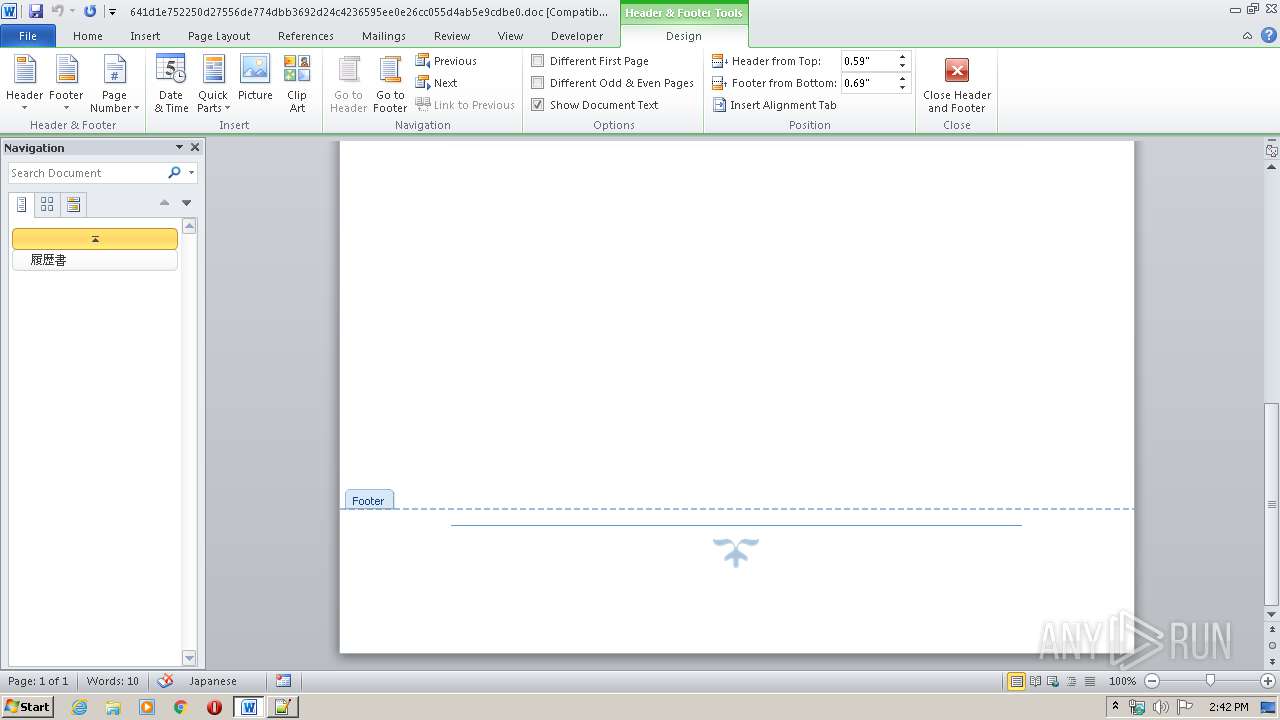
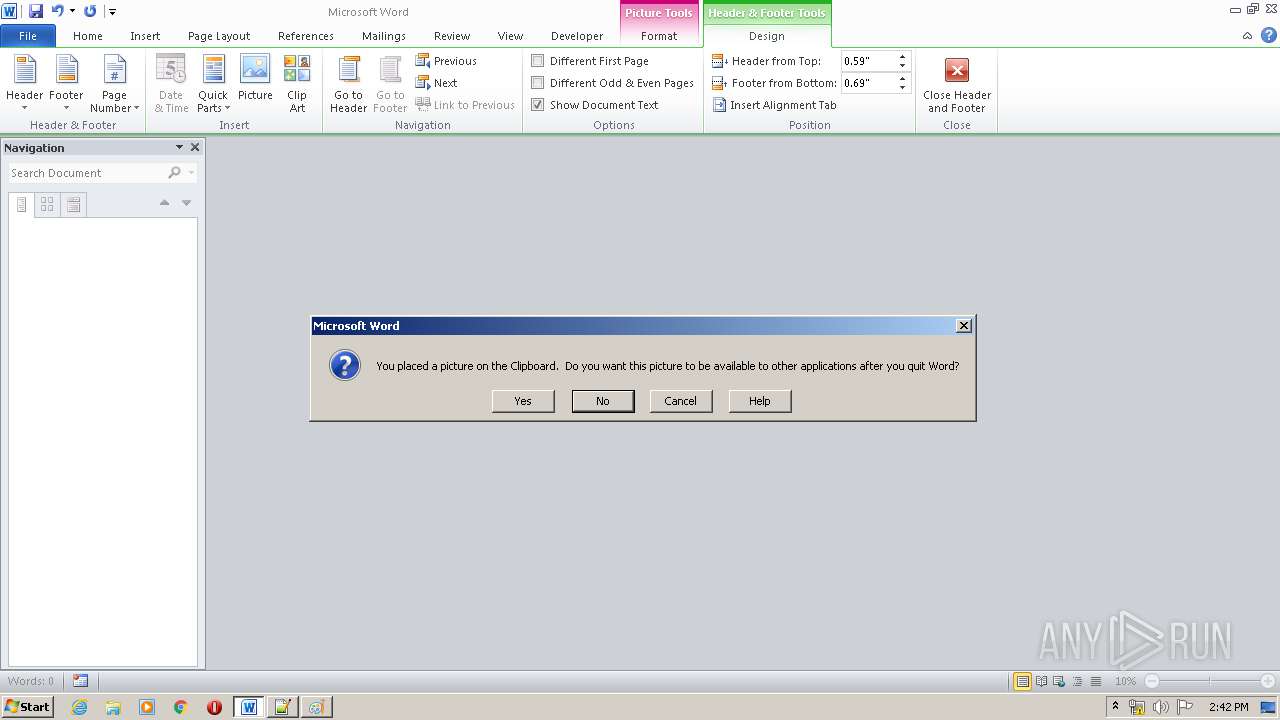
Unusual execution from Microsoft Office
- WINWORD.EXE (PID: 2836)
Changes the autorun value in the registry
- SfsDllSample.exe (PID: 2296)
Executable content was dropped or overwritten
- WINWORD.EXE (PID: 2836)
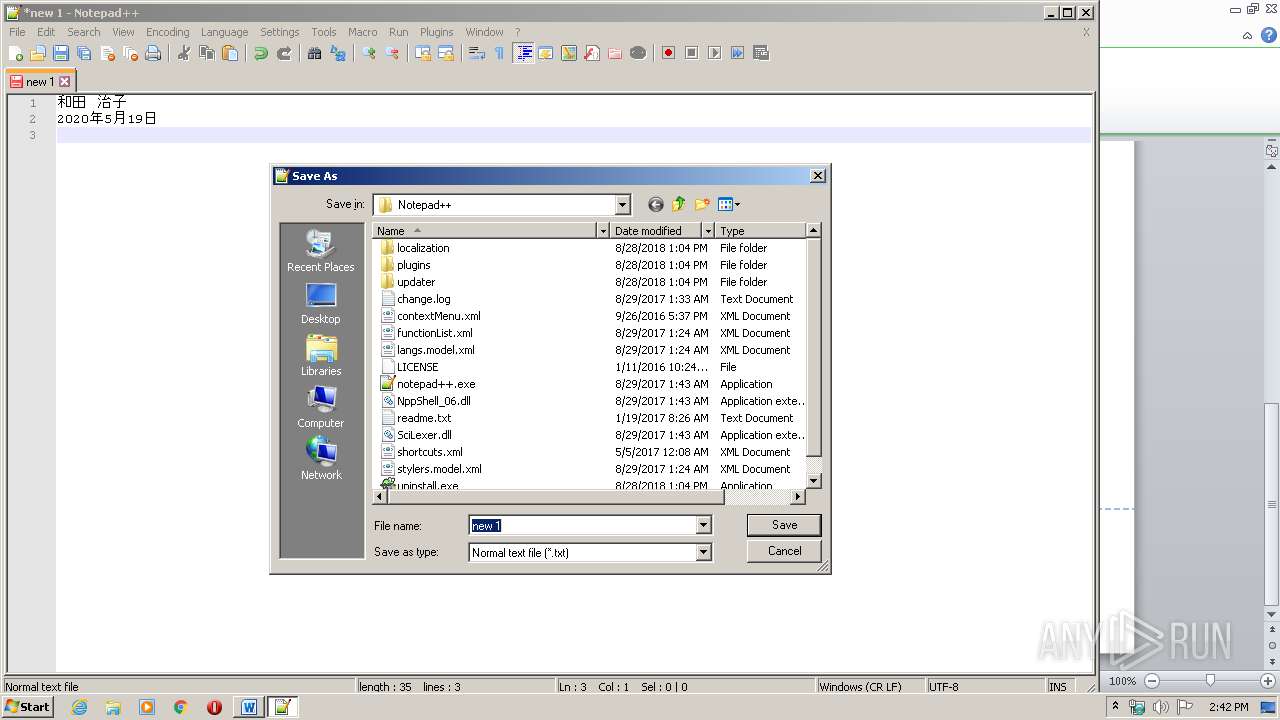
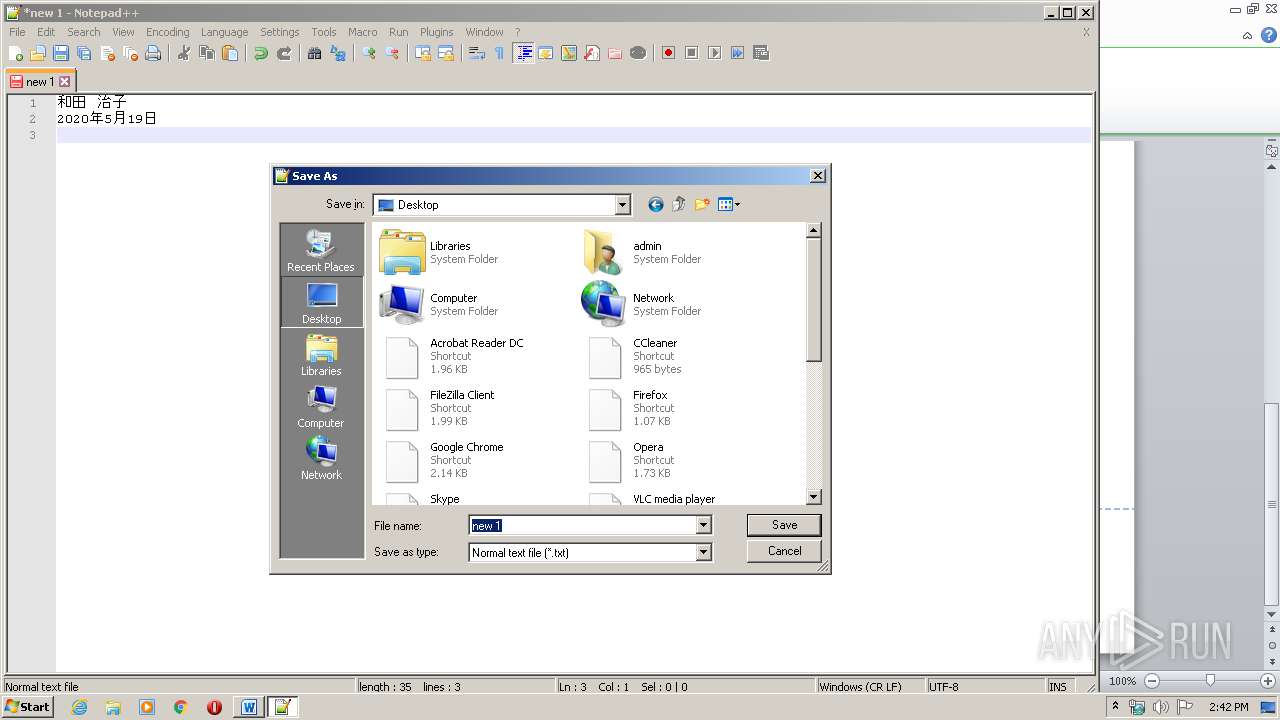
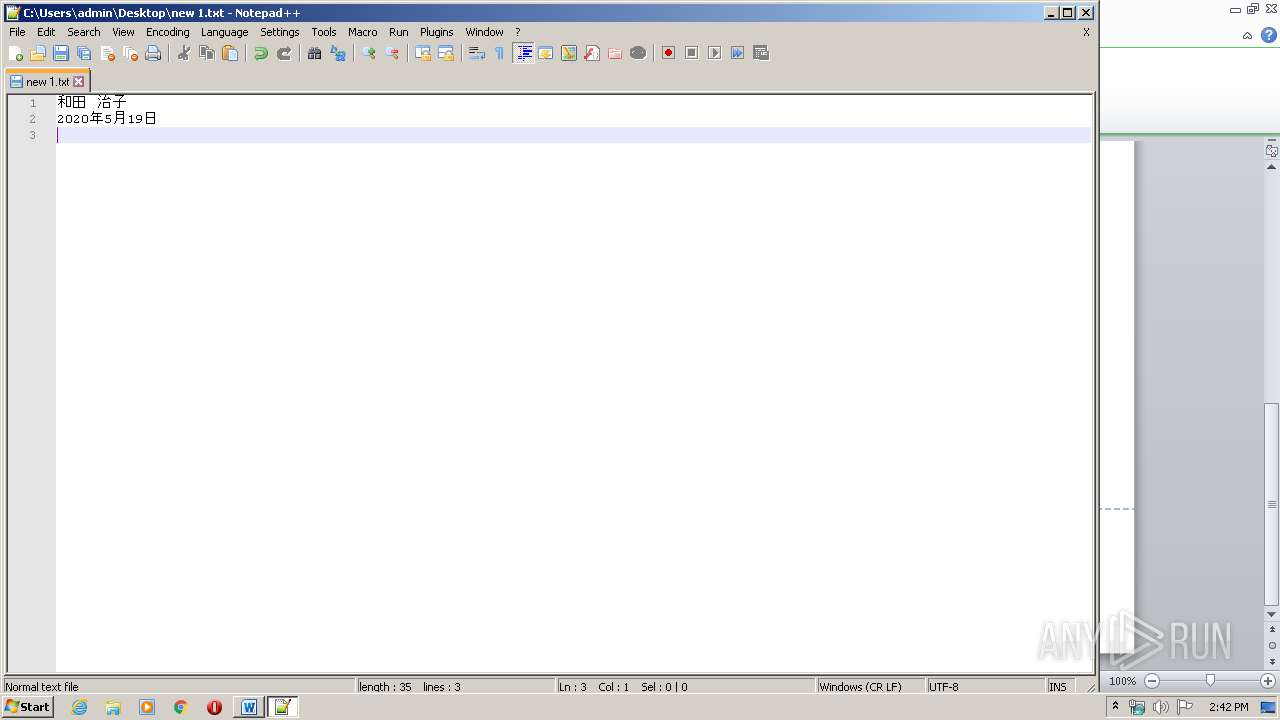
Actions looks like stealing of personal data
- notepad++.exe (PID: 2240)
SUSPICIOUS
Reads Internet Cache Settings
- SfsDllSample.exe (PID: 2296)
Creates files in the user directory
- notepad++.exe (PID: 2240)
INFO
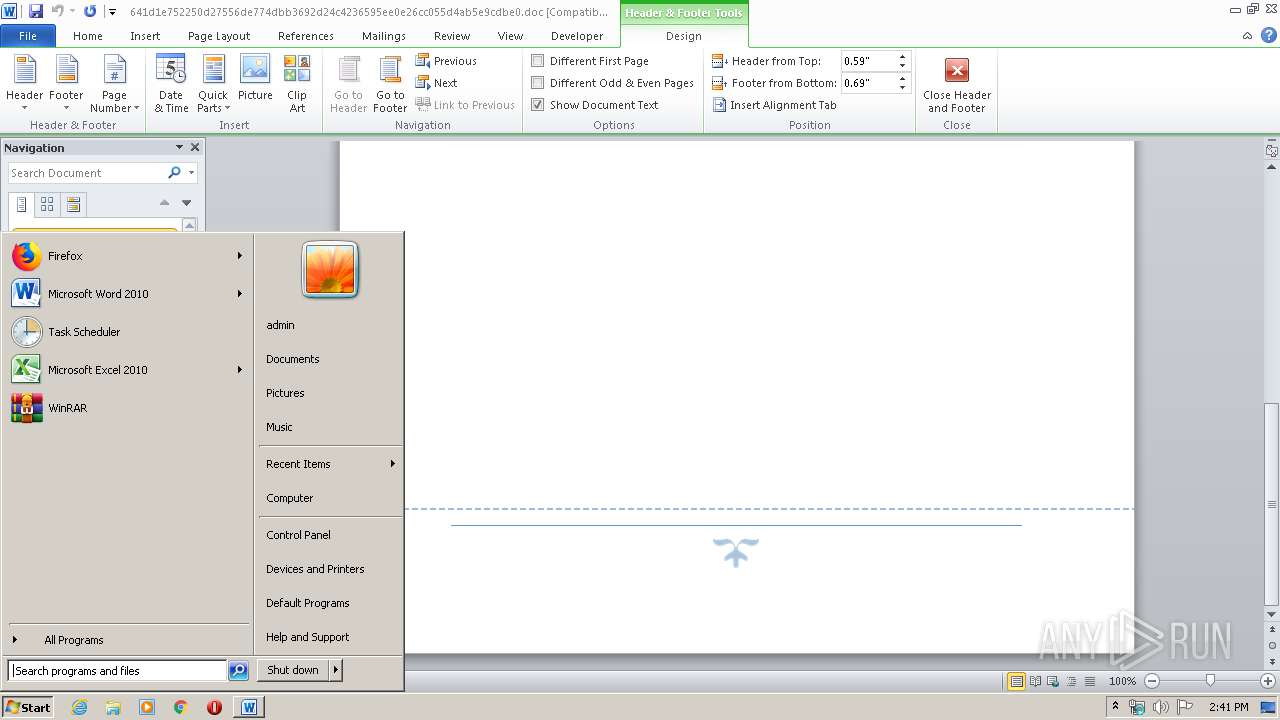
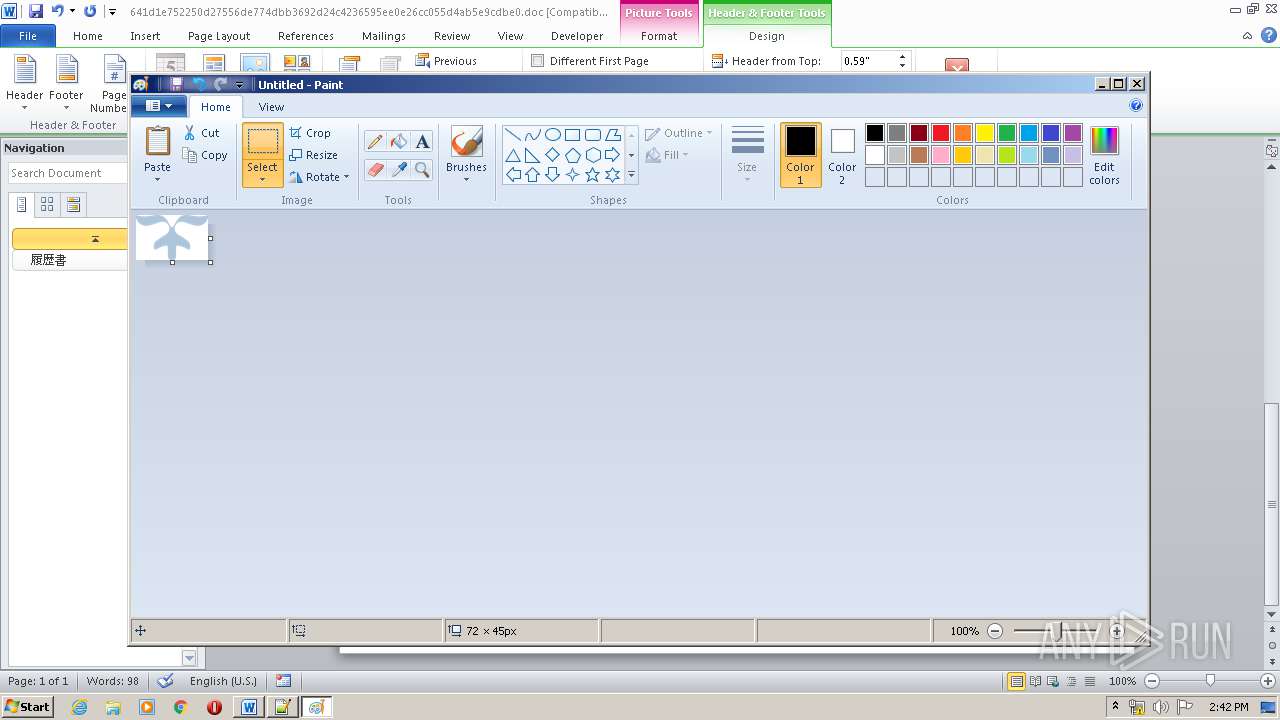
Manual execution by user
- notepad++.exe (PID: 2240)
- mspaint.exe (PID: 2316)
Creates files in the user directory
- WINWORD.EXE (PID: 2836)
Reads Microsoft Office registry keys
- WINWORD.EXE (PID: 2836)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .doc | | | Microsoft Word document (38.3) |
|---|---|---|
| .xls | | | Microsoft Excel sheet (alternate) (29.3) |
| .doc | | | Microsoft Word document (old ver.) (22.7) |
EXIF
FlashPix
| CompObjUserTypeLen: | 28 |
|---|---|
| CompObjUserType: | Microsoft Word 97-2003 ???? |
| Subject: | - |
| Keywords: | - |
| Comments: | - |
| Template: | Normal.dotm |
| RevisionNumber: | 17 |
| TotalEditTime: | 1.6 hours |
| CreateDate: | 2020:05:18 02:08:00 |
| ModifyDate: | 2020:05:19 03:07:00 |
| Pages: | 1 |
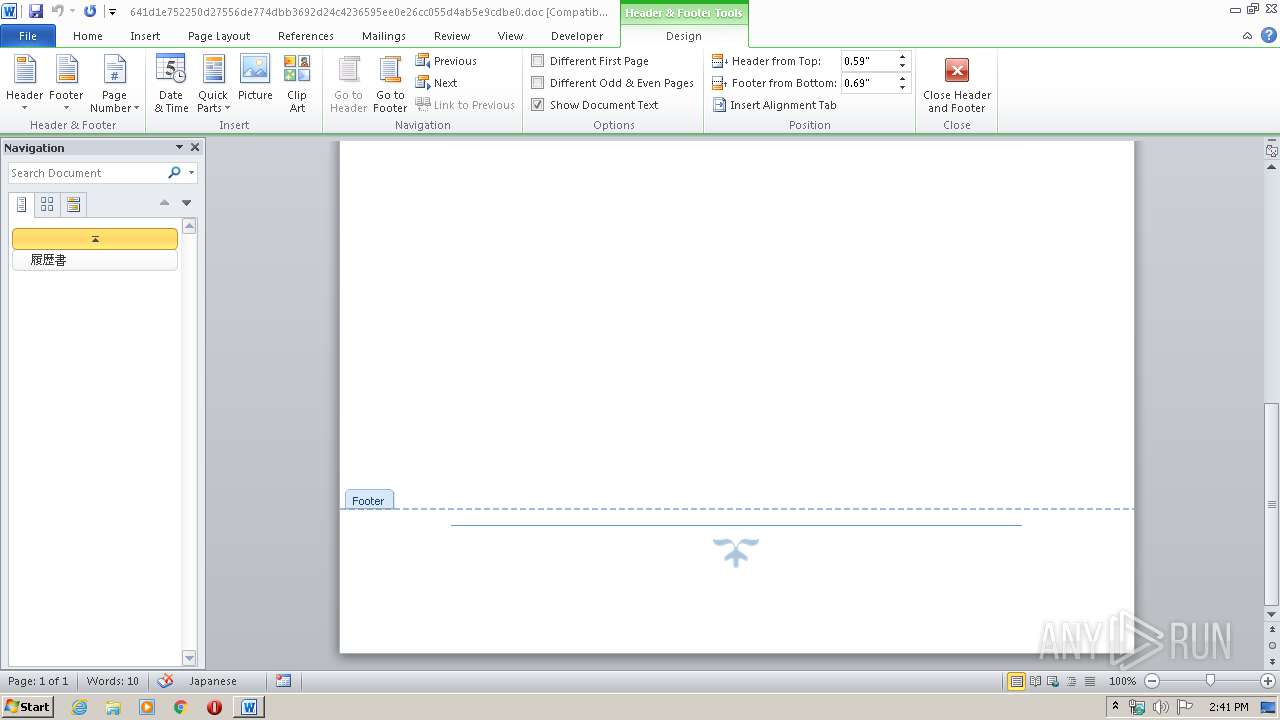
| Words: | 21 |
| Characters: | 121 |
| Security: | None |
| CodePage: | Windows Japanese (Shift-JIS) |
| Company: | - |
| Lines: | 1 |
| Paragraphs: | 1 |
| CharCountWithSpaces: | 141 |
| AppVersion: | 16 |
| ScaleCrop: | No |
| LinksUpToDate: | No |
| SharedDoc: | No |
| HyperlinksChanged: | No |
| TitleOfParts: | ?????? |
| HeadingPairs: |
|
Total processes
43
Monitored processes
5
Malicious processes
2
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1696 | "C:\Program Files\Notepad++\updater\gup.exe" -v7.51 | C:\Program Files\Notepad++\updater\gup.exe | notepad++.exe | ||||||||||||
User: admin Company: Don HO don.h@free.fr Integrity Level: MEDIUM Description: GUP : a free (LGPL) Generic Updater Exit code: 4294967295 Version: 4.1 Modules
| |||||||||||||||
| 2240 | "C:\Program Files\Notepad++\notepad++.exe" | C:\Program Files\Notepad++\notepad++.exe | explorer.exe | ||||||||||||
User: admin Company: Don HO don.h@free.fr Integrity Level: MEDIUM Description: Notepad++ : a free (GNU) source code editor Exit code: 0 Version: 7.51 Modules
| |||||||||||||||
| 2296 | "C:\Users\admin\AppData\Local\Temp\HFVREUI\SfsDllSample.exe" | C:\Users\admin\AppData\Local\Temp\HFVREUI\SfsDllSample.exe | WINWORD.EXE | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 2316 | "C:\Windows\system32\mspaint.exe" | C:\Windows\system32\mspaint.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Paint Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2836 | "C:\Program Files\Microsoft Office\Office14\WINWORD.EXE" /n "C:\Users\admin\AppData\Local\Temp\641d1e752250d27556de774dbb3692d24c4236595ee0e26cc055d4ab5e9cdbe0.doc" | C:\Program Files\Microsoft Office\Office14\WINWORD.EXE | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Word Exit code: 0 Version: 14.0.6024.1000 Modules
| |||||||||||||||
Total events
3 798
Read events
2 459
Write events
1 172
Delete events
167
Modification events
| (PID) Process: | (2836) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Word\Resiliency\StartupItems |
| Operation: | write | Name: | =5 |
Value: 3D352000140B0000010000000000000000000000 | |||
| (PID) Process: | (2836) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1033 |
Value: Off | |||
| (PID) Process: | (2836) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1041 |
Value: Off | |||
| (PID) Process: | (2836) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1046 |
Value: Off | |||
| (PID) Process: | (2836) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1036 |
Value: Off | |||
| (PID) Process: | (2836) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1031 |
Value: Off | |||
| (PID) Process: | (2836) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1040 |
Value: Off | |||
| (PID) Process: | (2836) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1049 |
Value: Off | |||
| (PID) Process: | (2836) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 3082 |
Value: Off | |||
| (PID) Process: | (2836) WINWORD.EXE | Key: | HKEY_CURRENT_USER\Software\Microsoft\Office\14.0\Common\LanguageResources\EnabledLanguages |
| Operation: | write | Name: | 1042 |
Value: Off | |||
Executable files
2
Suspicious files
1
Text files
10
Unknown types
3
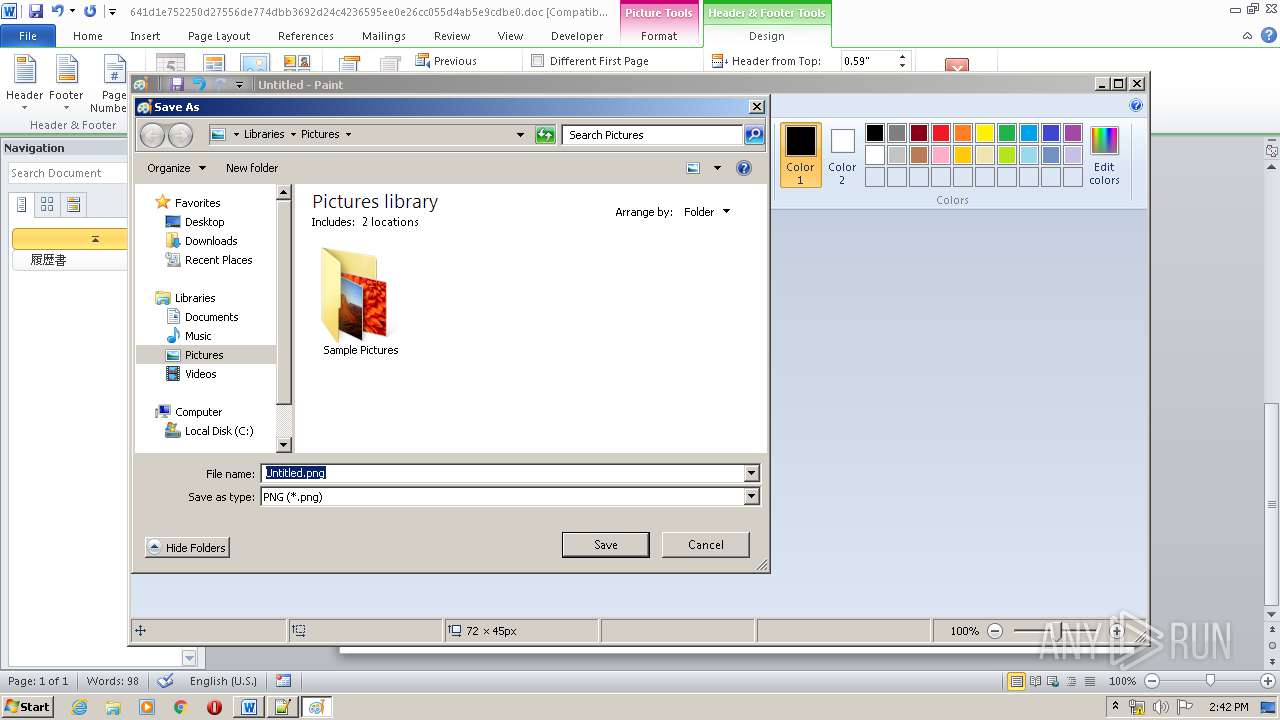
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2836 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\CVR991D.tmp.cvr | — | |
MD5:— | SHA256:— | |||
| 2836 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\~DF11CF9AE2F486D970.TMP | — | |
MD5:— | SHA256:— | |||
| 2836 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\~DF1C96B31EC8E3D002.TMP | — | |
MD5:— | SHA256:— | |||
| 2836 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\~DF8EFFF151766D944B.TMP | — | |
MD5:— | SHA256:— | |||
| 2836 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\~DF35DBE696E43C8479.TMP | — | |
MD5:— | SHA256:— | |||
| 2836 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\~DF058C955BF2D0B4E5.TMP | — | |
MD5:— | SHA256:— | |||
| 2836 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\~DF94642552F6F5CCEC.TMP | — | |
MD5:— | SHA256:— | |||
| 2836 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.Word\~WRS{3B27674A-D6F9-46DE-9FCF-D0A83462F0F4}.tmp | — | |
MD5:— | SHA256:— | |||
| 2836 | WINWORD.EXE | C:\Users\admin\AppData\Local\Temp\~DFB385B84F24EB8262.TMP | — | |
MD5:— | SHA256:— | |||
| 2836 | WINWORD.EXE | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.Word\~WRF{80E09FB5-69D1-4FA0-B51A-1C3CC2B56117}.tmp | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
1
DNS requests
1
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
1696 | gup.exe | 104.31.89.28:443 | notepad-plus-plus.org | Cloudflare Inc | US | shared |
DNS requests
Domain | IP | Reputation |
|---|---|---|
notepad-plus-plus.org |
| whitelisted |
Threats
Process | Message |
|---|---|
notepad++.exe | VerifyLibrary: C:\Program Files\Notepad++\SciLexer.dll
|
notepad++.exe | VerifyLibrary: certificate revocation checking is disabled
|
notepad++.exe | 42C4C5846BB675C74E2B2C90C69AB44366401093
|