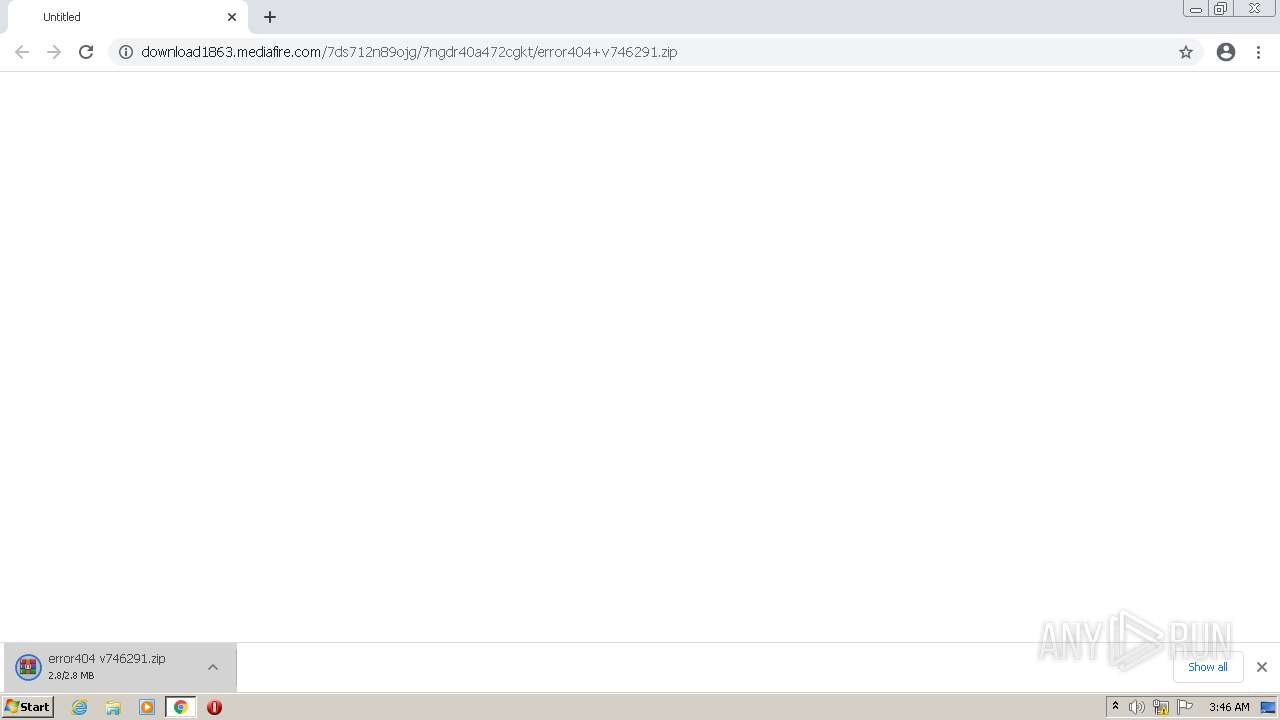
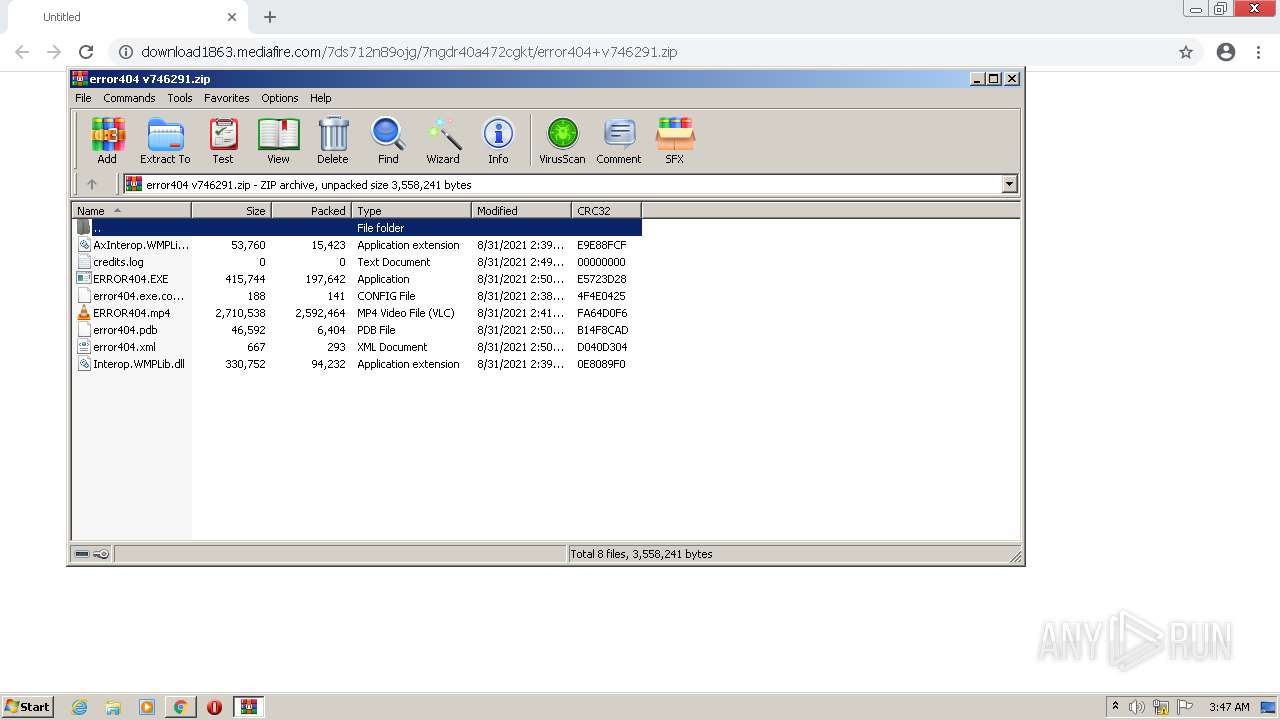
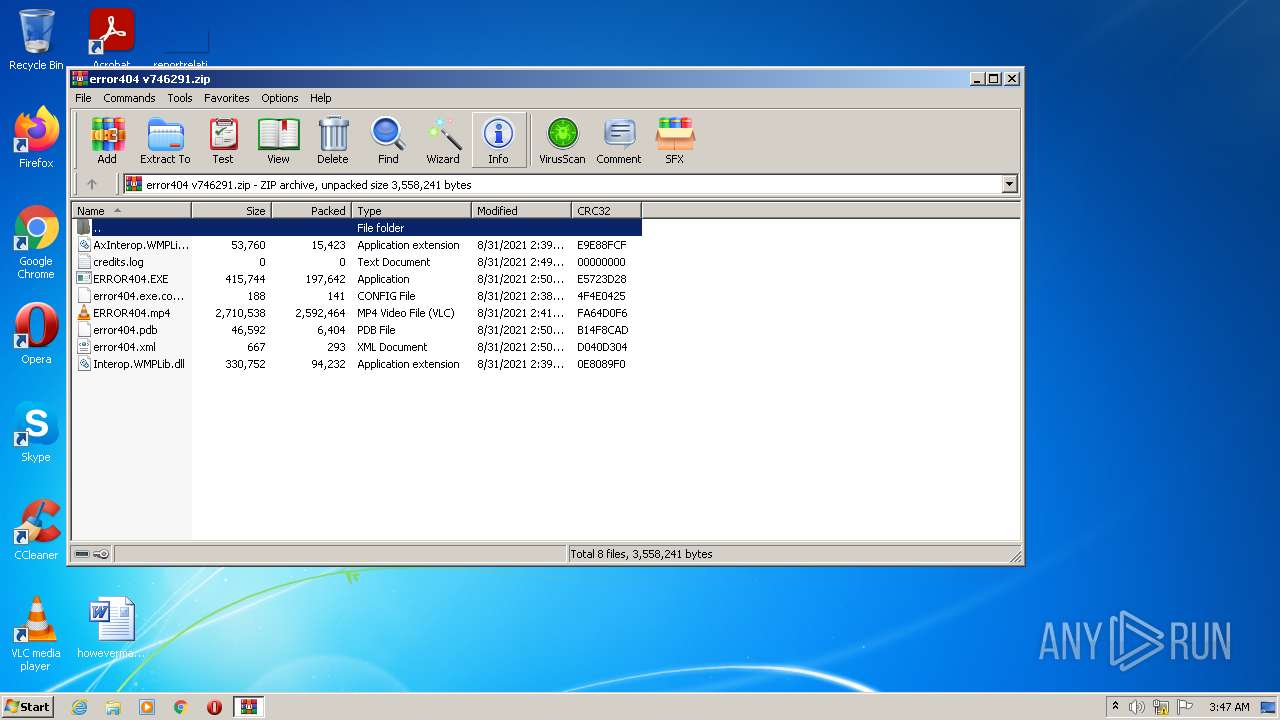
| URL: | https://download1863.mediafire.com/7ds712n89ojg/7ngdr40a472cgkt/error404+v746291.zip |
| Full analysis: | https://app.any.run/tasks/252e152e-9fd0-4135-bc9f-03540c081ab5 |
| Verdict: | Malicious activity |
| Analysis date: | July 03, 2022, 02:46:42 |
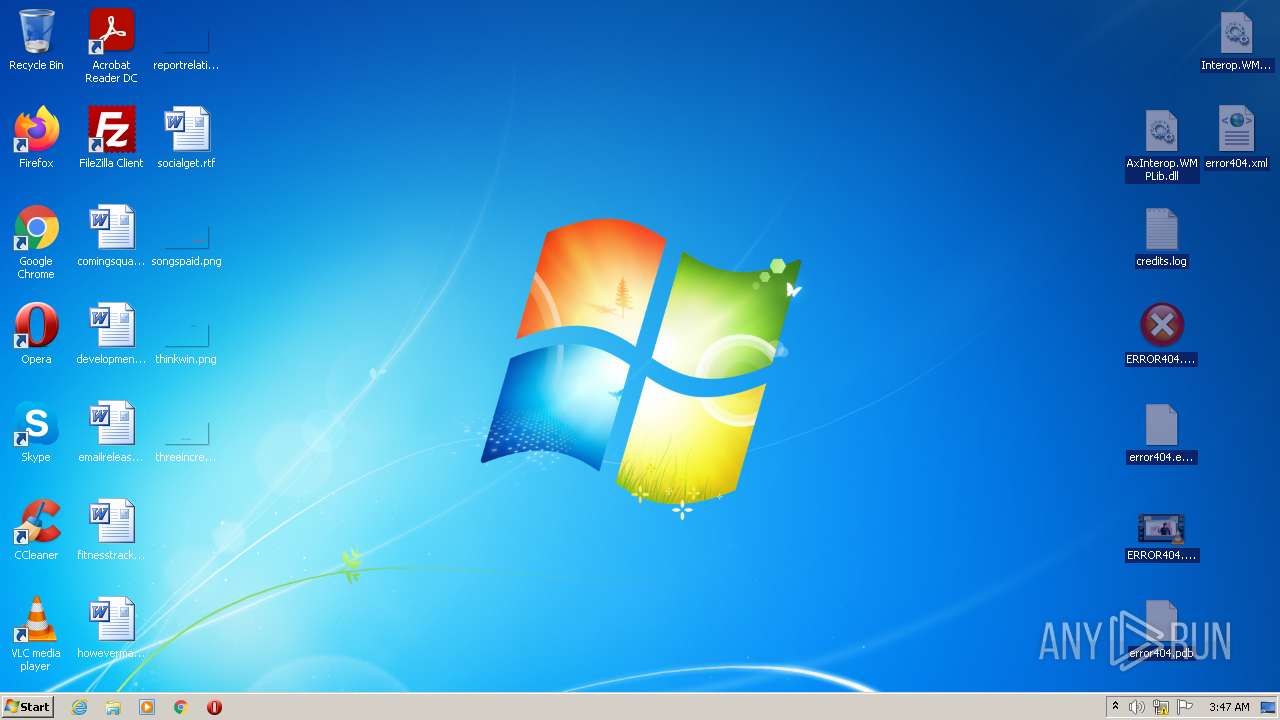
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MD5: | 065084BF25AACAB504CAA213CC28BBC1 |
| SHA1: | 149B96FC11859A99AB9EF66E0416202658FF6421 |
| SHA256: | 6419BEF30216466F210D3080C04C955733E0BE479606699EA6B320D836BA44BB |
| SSDEEP: | 3:N8SE6danMEQeGSnFrAXO4UrMV:2SqnMEQeGSnFoUrU |
MALICIOUS
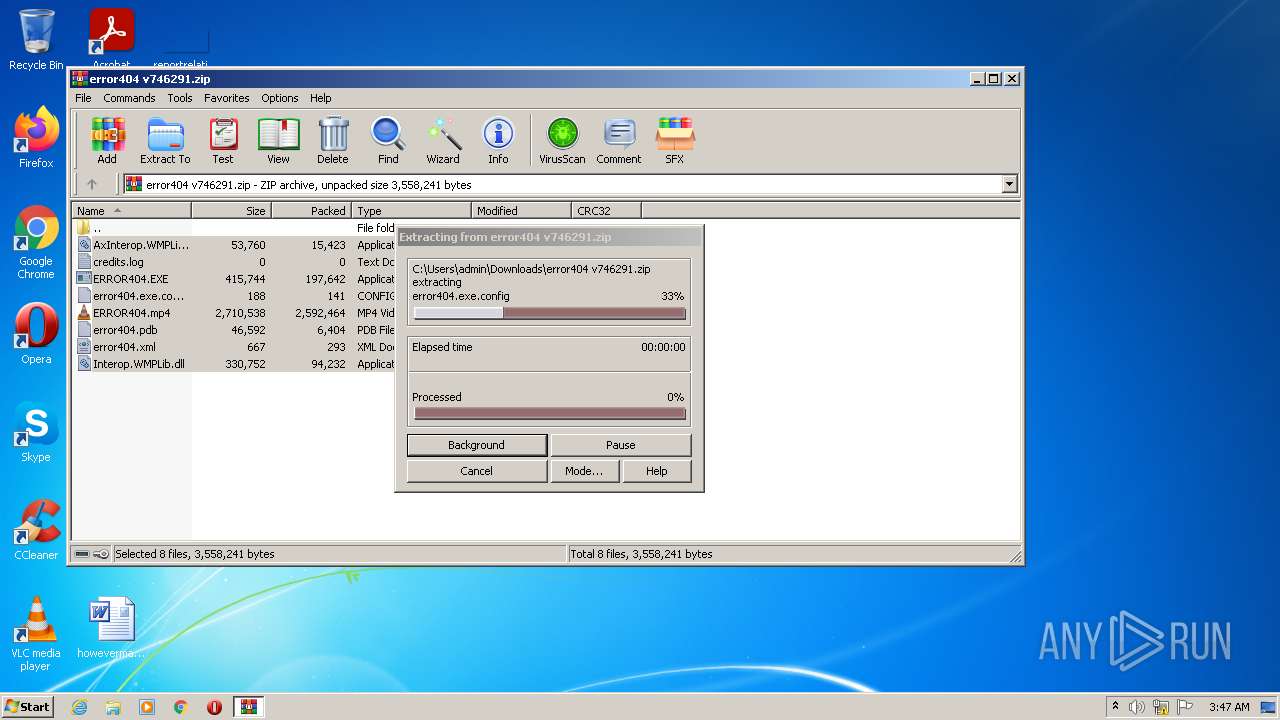
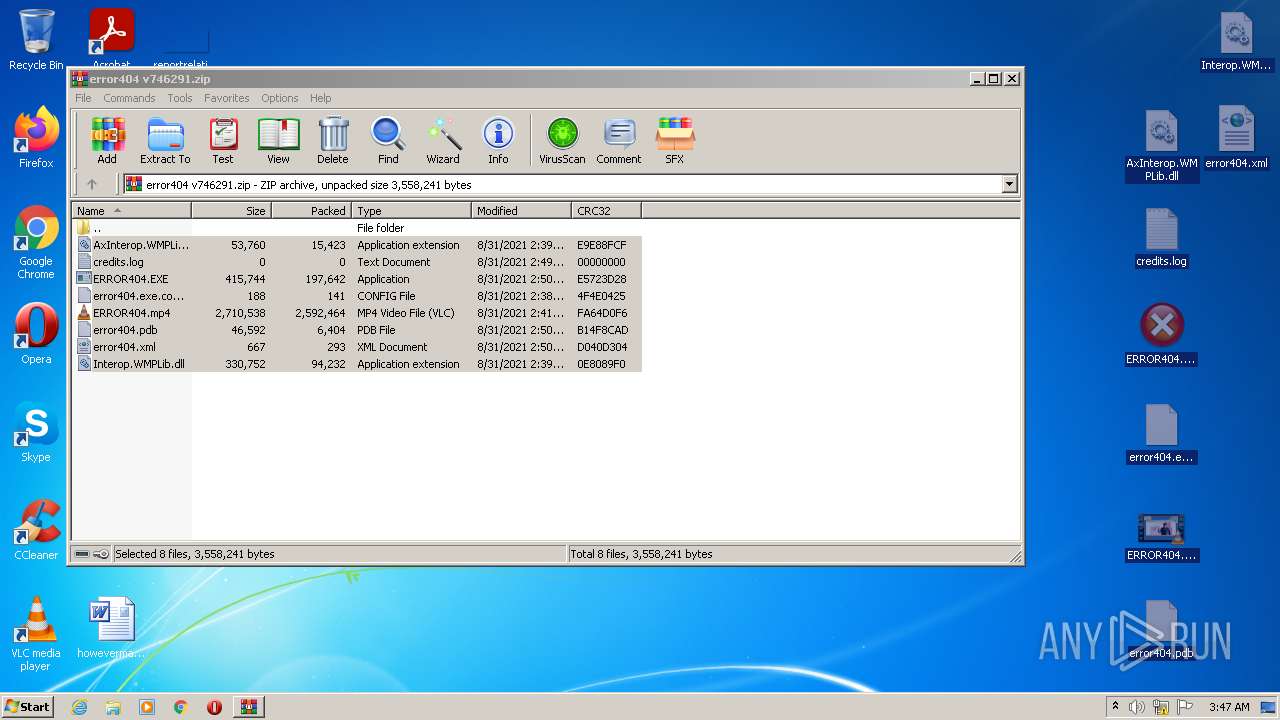
Drops executable file immediately after starts
- chrome.exe (PID: 2148)
- WinRAR.exe (PID: 2948)
- iexplore.exe (PID: 2844)
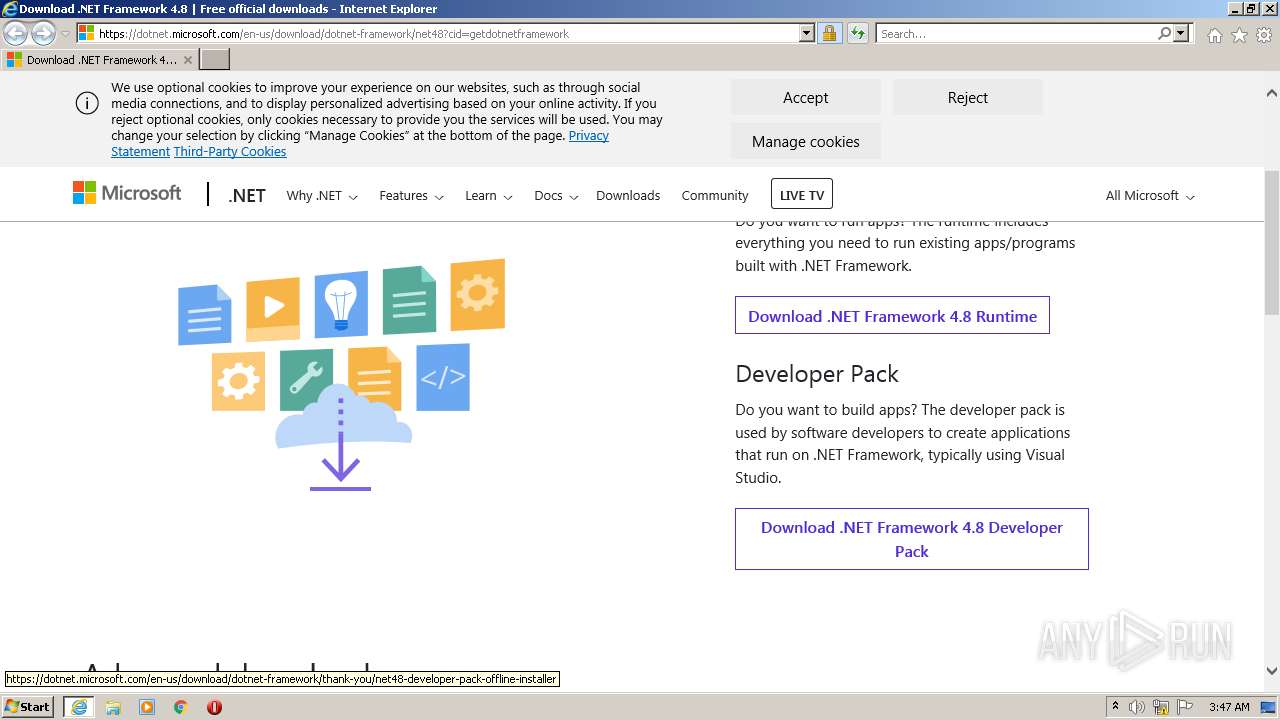
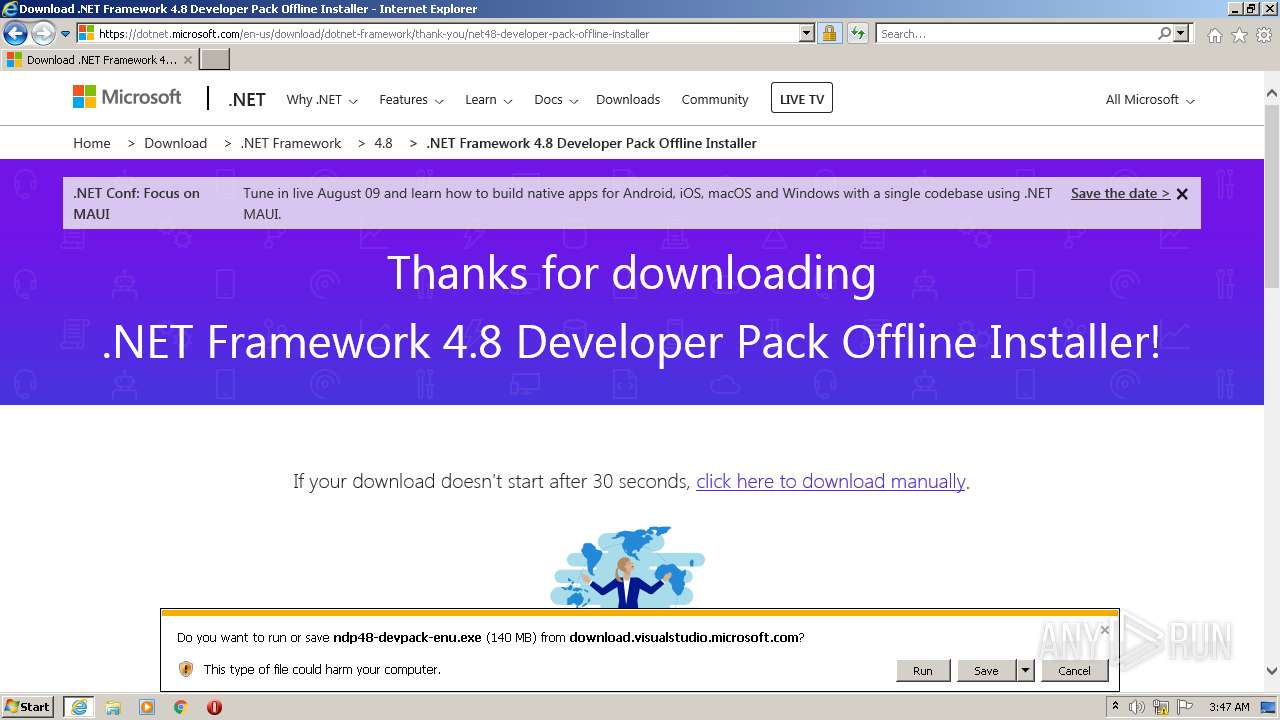
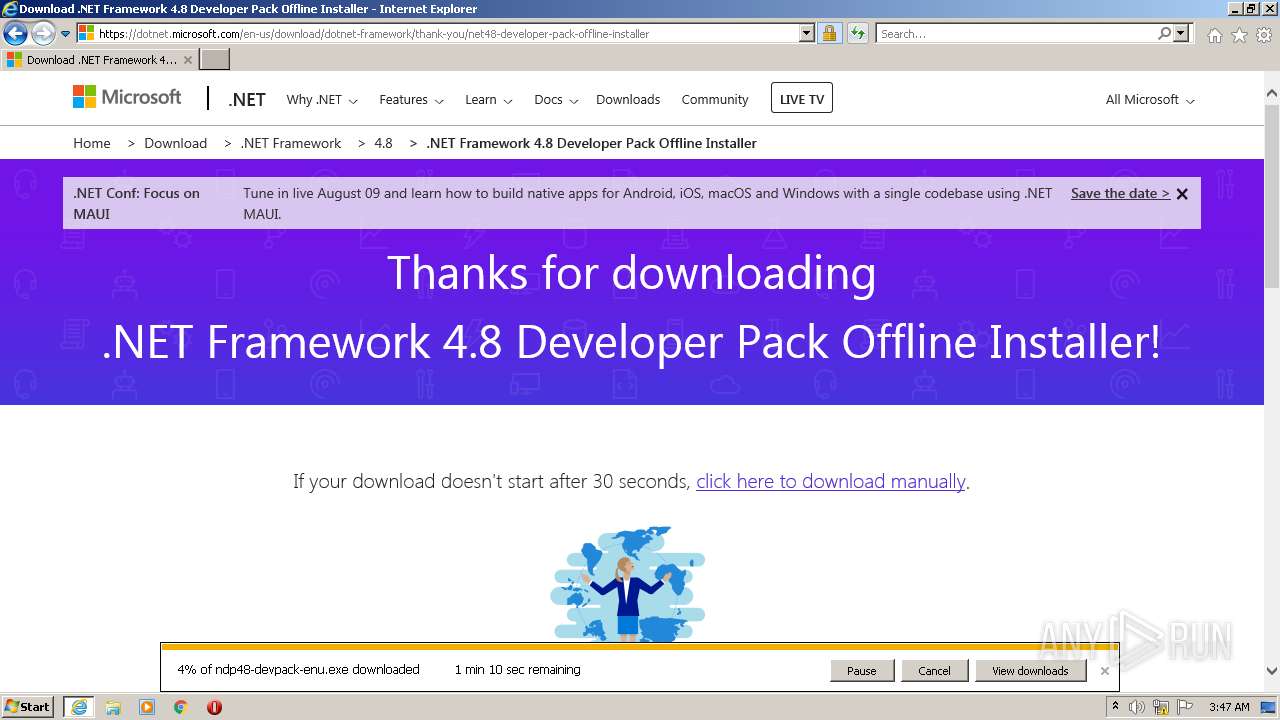
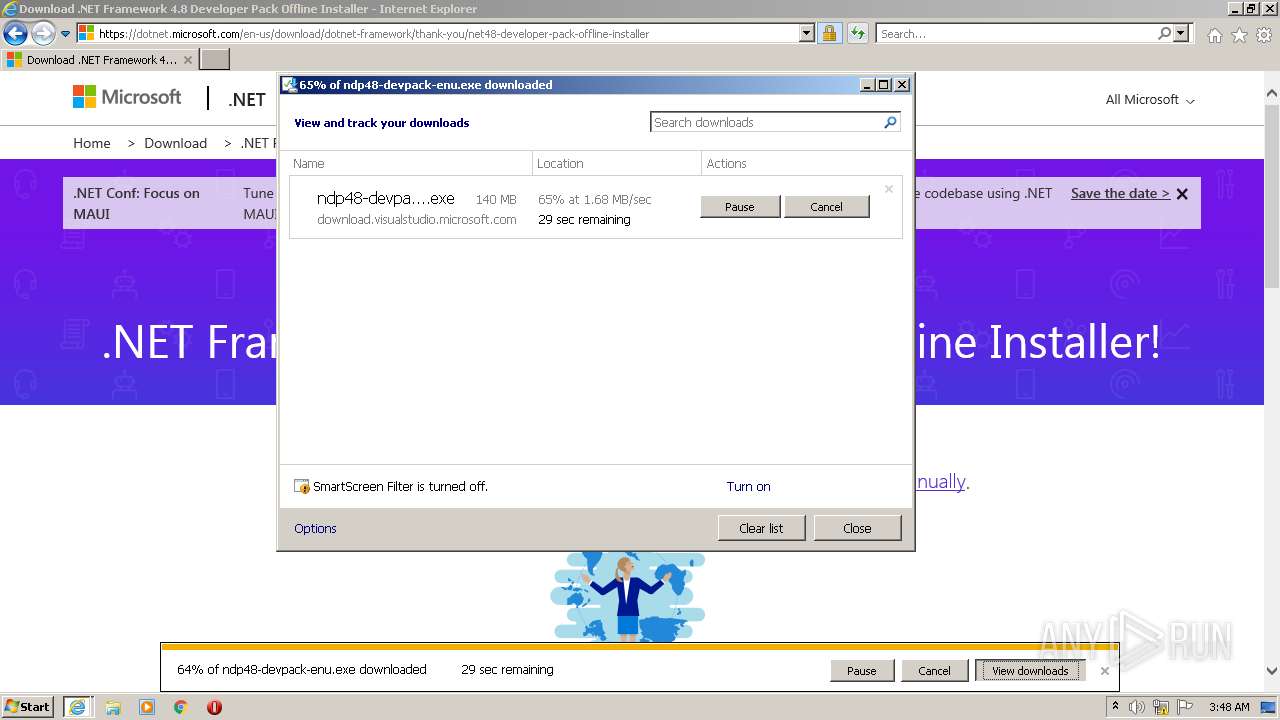
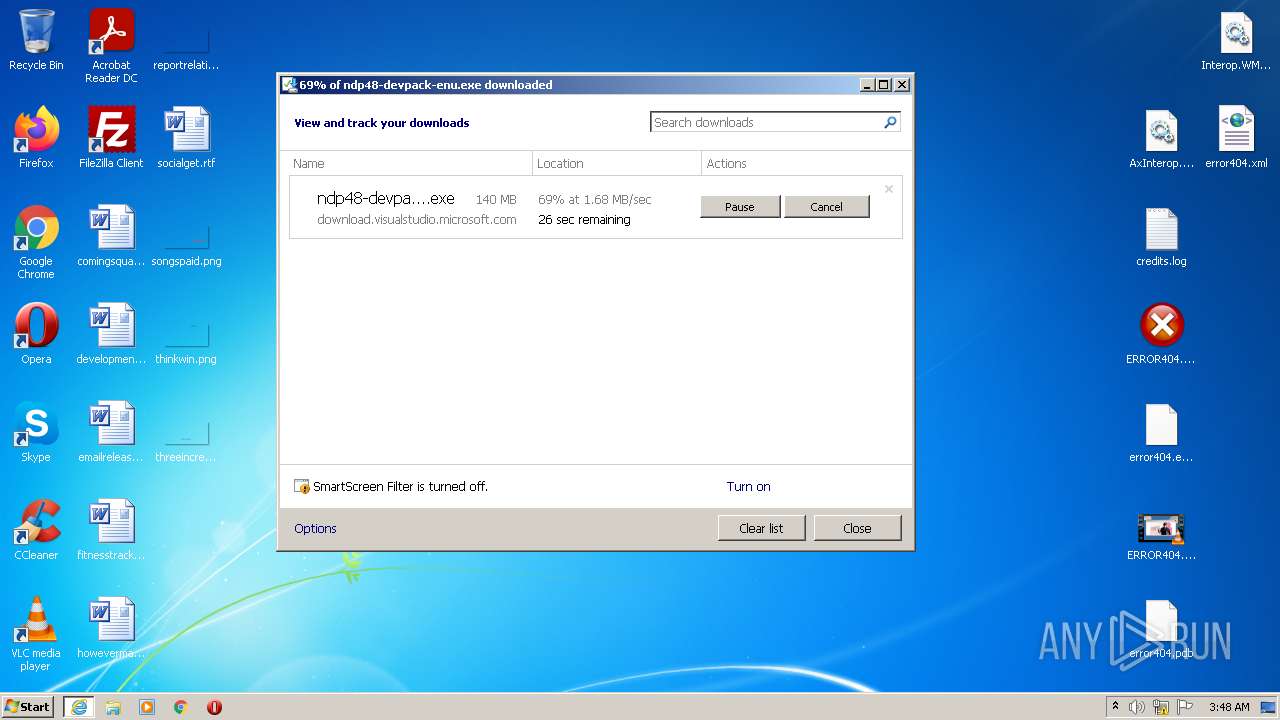
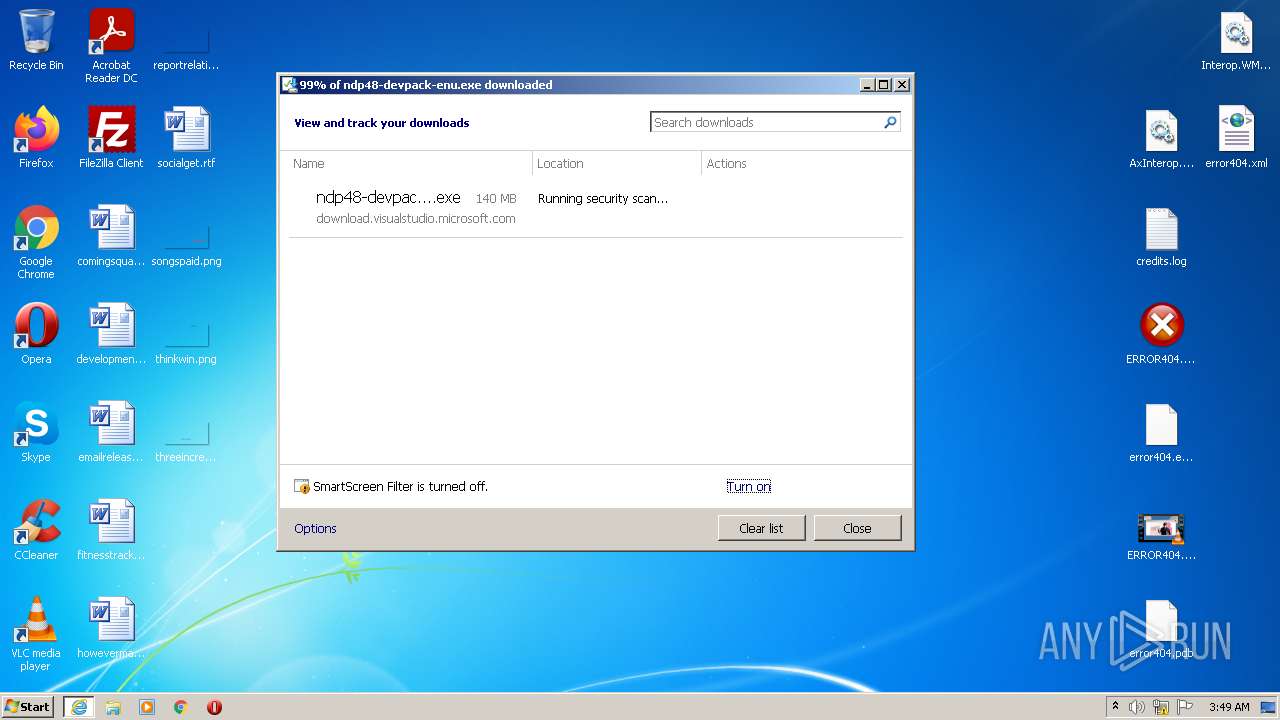
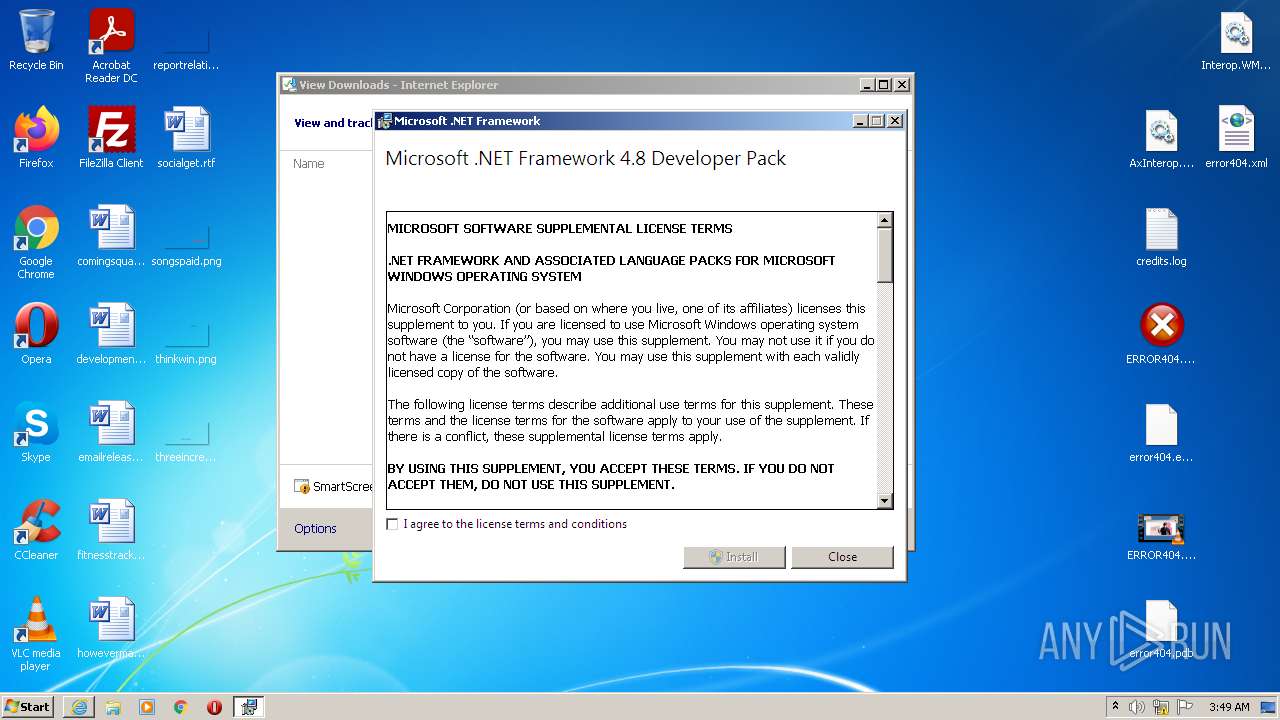
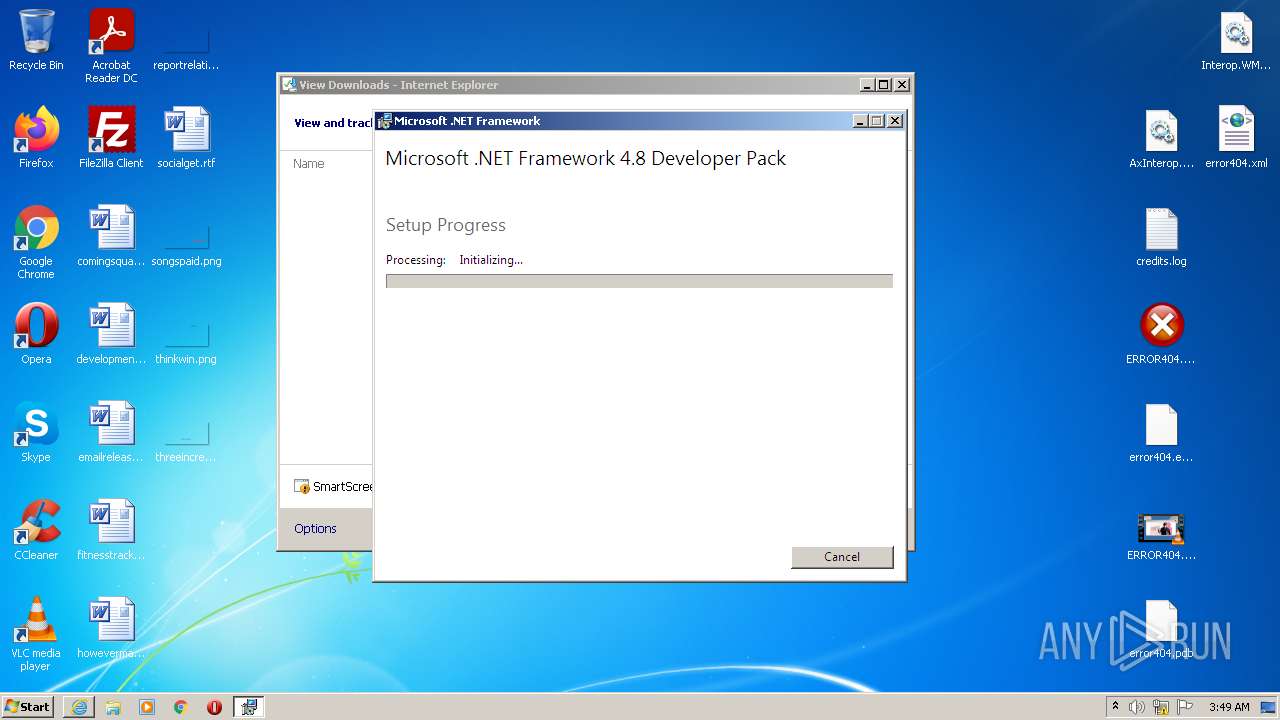
- ndp48-devpack-enu.exe (PID: 2588)
- ndp48-devpack-enu.exe (PID: 2868)
- NDP48-DevPack-ENU.exe (PID: 1852)
- NDP48-x86-x64-AllOS-ENU.exe (PID: 3628)
- msiexec.exe (PID: 3128)
Loads dropped or rewritten executable
- SearchProtocolHost.exe (PID: 3088)
- ndp48-devpack-enu.exe (PID: 2868)
- Setup.exe (PID: 2392)
Application was dropped or rewritten from another process
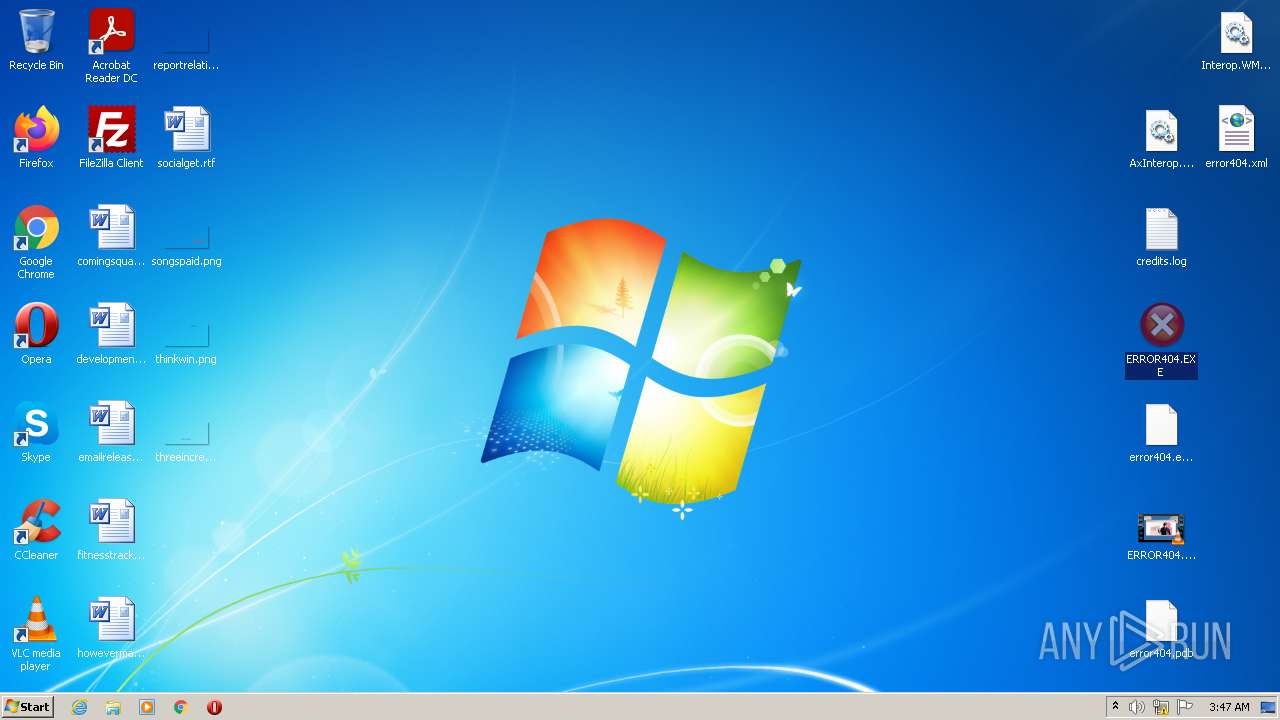
- ERROR404.EXE (PID: 3748)
- ndp48-devpack-enu.exe (PID: 2588)
- ndp48-devpack-enu.exe (PID: 2868)
- NDP48-DevPack-ENU.exe (PID: 1852)
- Setup.exe (PID: 2392)
- SetupUtility.exe (PID: 1908)
- SetupUtility.exe (PID: 840)
Changes the autorun value in the registry
- NDP48-DevPack-ENU.exe (PID: 1852)
Actions looks like stealing of personal data
- NDP48-x86-x64-AllOS-ENU.exe (PID: 3628)
Changes settings of System certificates
- Setup.exe (PID: 2392)
SUSPICIOUS
Executable content was dropped or overwritten
- chrome.exe (PID: 2148)
- WinRAR.exe (PID: 2948)
- iexplore.exe (PID: 2844)
- ndp48-devpack-enu.exe (PID: 2588)
- ndp48-devpack-enu.exe (PID: 2868)
- NDP48-DevPack-ENU.exe (PID: 1852)
- NDP48-x86-x64-AllOS-ENU.exe (PID: 3628)
- msiexec.exe (PID: 3128)
Modifies files in Chrome extension folder
- chrome.exe (PID: 2568)
Drops a file with a compile date too recent
- chrome.exe (PID: 2148)
- WinRAR.exe (PID: 2948)
- iexplore.exe (PID: 2844)
- ndp48-devpack-enu.exe (PID: 2588)
- ndp48-devpack-enu.exe (PID: 2868)
- NDP48-x86-x64-AllOS-ENU.exe (PID: 3628)
- NDP48-DevPack-ENU.exe (PID: 1852)
- msiexec.exe (PID: 3128)
Reads the computer name
- WinRAR.exe (PID: 2948)
- ERROR404.EXE (PID: 3748)
- ndp48-devpack-enu.exe (PID: 2868)
- NDP48-DevPack-ENU.exe (PID: 1852)
- NDP48-x86-x64-AllOS-ENU.exe (PID: 3628)
- Setup.exe (PID: 2392)
- SetupUtility.exe (PID: 1908)
- SetupUtility.exe (PID: 840)
- msiexec.exe (PID: 3128)
- MsiExec.exe (PID: 2664)
- MsiExec.exe (PID: 3940)
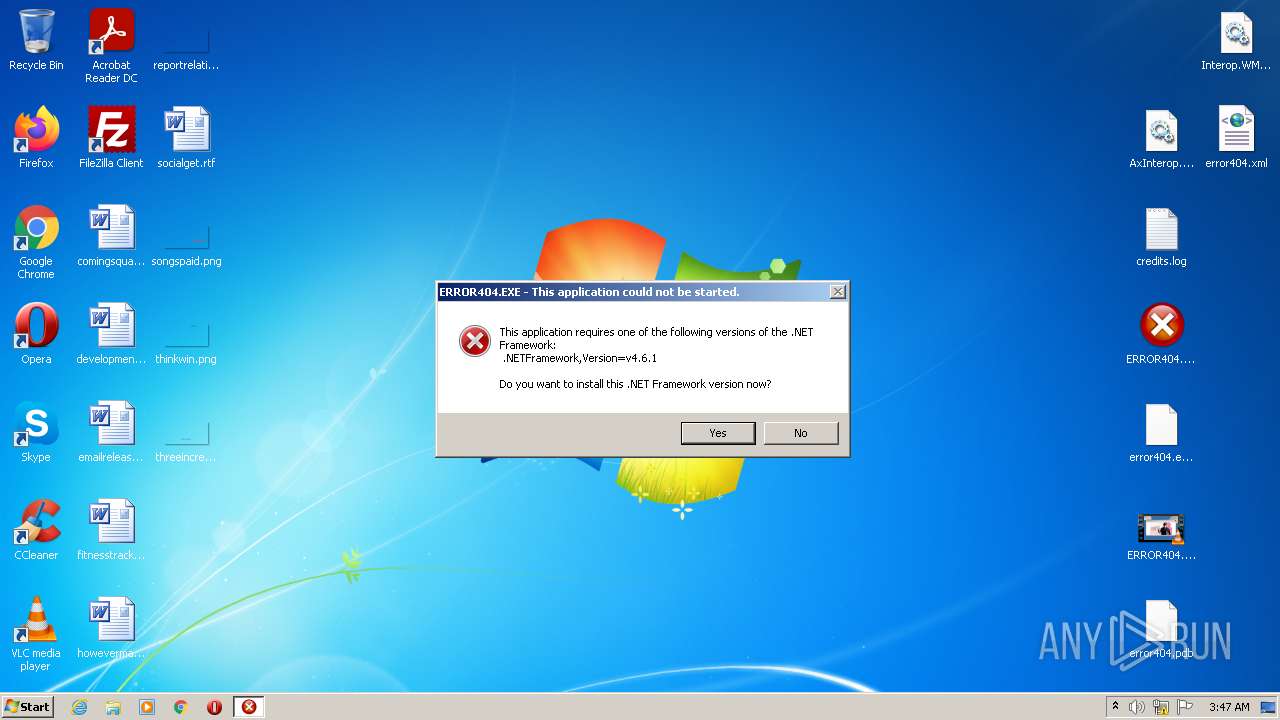
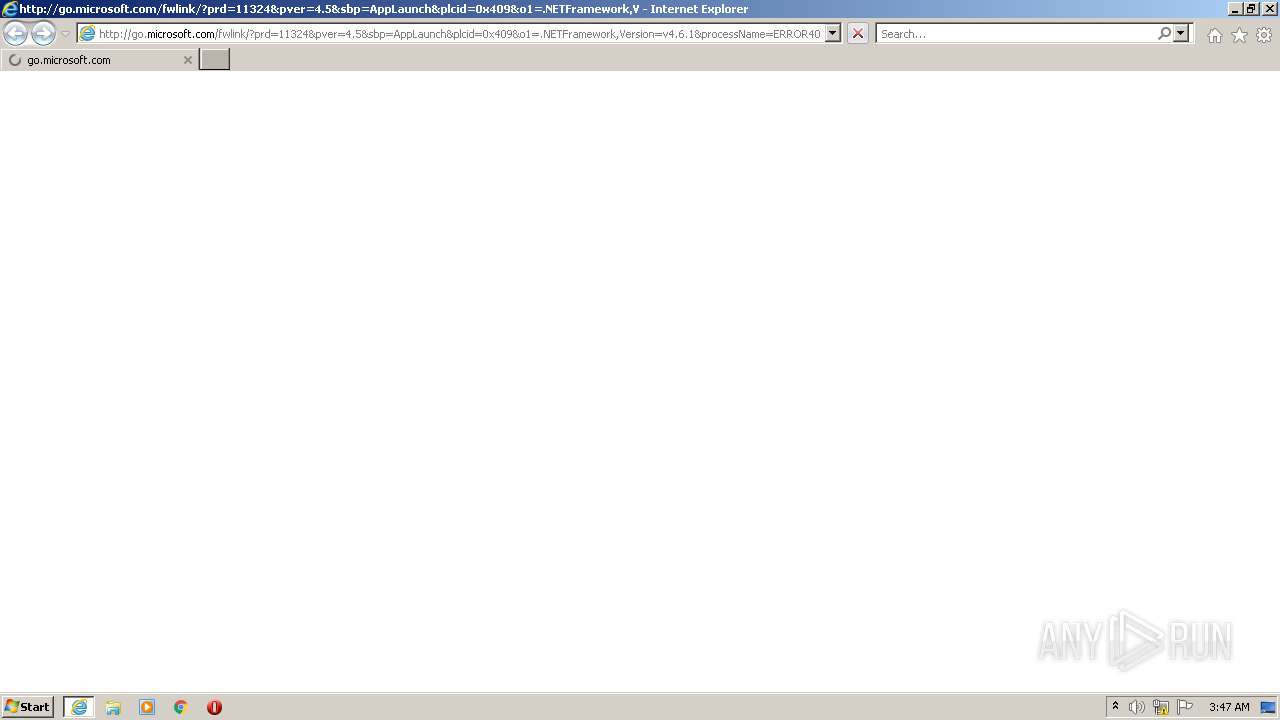
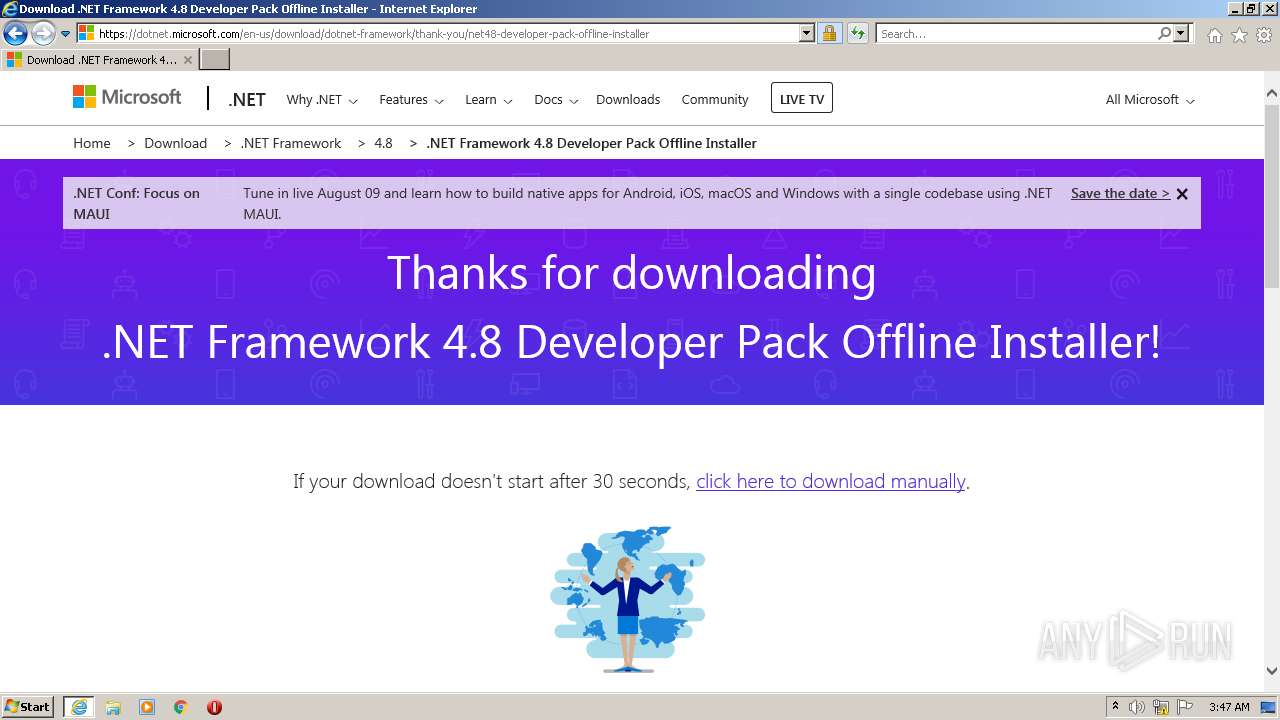
Starts Internet Explorer
- ERROR404.EXE (PID: 3748)
Checks supported languages
- WinRAR.exe (PID: 2948)
- ERROR404.EXE (PID: 3748)
- ndp48-devpack-enu.exe (PID: 2588)
- ndp48-devpack-enu.exe (PID: 2868)
- NDP48-DevPack-ENU.exe (PID: 1852)
- NDP48-x86-x64-AllOS-ENU.exe (PID: 3628)
- Setup.exe (PID: 2392)
- SetupUtility.exe (PID: 1908)
- SetupUtility.exe (PID: 840)
- msiexec.exe (PID: 3128)
- MsiExec.exe (PID: 2664)
- MsiExec.exe (PID: 3940)
Reads Microsoft Outlook installation path
- iexplore.exe (PID: 2844)
Searches for installed software
- ndp48-devpack-enu.exe (PID: 2868)
- NDP48-DevPack-ENU.exe (PID: 1852)
Reads Environment values
- ndp48-devpack-enu.exe (PID: 2868)
- vssvc.exe (PID: 1296)
- Setup.exe (PID: 2392)
Starts itself from another location
- ndp48-devpack-enu.exe (PID: 2868)
Creates a software uninstall entry
- NDP48-DevPack-ENU.exe (PID: 1852)
Creates files in the program directory
- NDP48-DevPack-ENU.exe (PID: 1852)
Executed as Windows Service
- vssvc.exe (PID: 1296)
Reads CPU info
- Setup.exe (PID: 2392)
Reads the Windows organization settings
- msiexec.exe (PID: 3128)
Reads Windows owner or organization settings
- msiexec.exe (PID: 3128)
Removes files from Windows directory
- msiexec.exe (PID: 3128)
Creates files in the Windows directory
- msiexec.exe (PID: 3128)
INFO
Application launched itself
- chrome.exe (PID: 2568)
- iexplore.exe (PID: 1184)
- msiexec.exe (PID: 3128)
Checks supported languages
- chrome.exe (PID: 2132)
- chrome.exe (PID: 3268)
- chrome.exe (PID: 3744)
- chrome.exe (PID: 3524)
- chrome.exe (PID: 2568)
- chrome.exe (PID: 3320)
- chrome.exe (PID: 2148)
- chrome.exe (PID: 2980)
- chrome.exe (PID: 3908)
- chrome.exe (PID: 3640)
- chrome.exe (PID: 3276)
- iexplore.exe (PID: 1184)
- iexplore.exe (PID: 2844)
- vssvc.exe (PID: 1296)
Reads the computer name
- chrome.exe (PID: 3268)
- chrome.exe (PID: 3320)
- chrome.exe (PID: 2568)
- chrome.exe (PID: 3524)
- chrome.exe (PID: 3640)
- chrome.exe (PID: 3276)
- iexplore.exe (PID: 1184)
- iexplore.exe (PID: 2844)
- vssvc.exe (PID: 1296)
Reads the hosts file
- chrome.exe (PID: 2568)
- chrome.exe (PID: 3320)
Reads settings of System Certificates
- chrome.exe (PID: 3320)
- iexplore.exe (PID: 2844)
- iexplore.exe (PID: 1184)
- Setup.exe (PID: 2392)
- msiexec.exe (PID: 3128)
Manual execution by user
- ERROR404.EXE (PID: 3748)
Checks Windows Trust Settings
- iexplore.exe (PID: 2844)
- iexplore.exe (PID: 1184)
- Setup.exe (PID: 2392)
- msiexec.exe (PID: 3128)
Adds / modifies Windows certificates
- iexplore.exe (PID: 1184)
Creates files in the user directory
- iexplore.exe (PID: 2844)
- iexplore.exe (PID: 1184)
Reads internet explorer settings
- iexplore.exe (PID: 2844)
Changes settings of System certificates
- iexplore.exe (PID: 1184)
Dropped object may contain Bitcoin addresses
- iexplore.exe (PID: 1184)
- NDP48-x86-x64-AllOS-ENU.exe (PID: 3628)
- Setup.exe (PID: 2392)
- msiexec.exe (PID: 3128)
Modifies the phishing filter of IE
- iexplore.exe (PID: 1184)
Reads the date of Windows installation
- iexplore.exe (PID: 1184)
Changes internet zones settings
- iexplore.exe (PID: 1184)
Loads dropped or rewritten executable
- MsiExec.exe (PID: 2664)
- MsiExec.exe (PID: 3940)
- msiexec.exe (PID: 3128)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
69
Monitored processes
27
Malicious processes
11
Suspicious processes
2
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 840 | SetupUtility.exe /screboot | C:\e6faded18db9ed6a1e09665fa6ec22\SetupUtility.exe | — | Setup.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft .NET Framework 4.5 Setup Exit code: 0 Version: 14.8.4110.0 built by: NET48REL1LAST_B Modules
| |||||||||||||||
| 1184 | "C:\Program Files\Internet Explorer\iexplore.exe" http://go.microsoft.com/fwlink/?prd=11324&pver=4.5&sbp=AppLaunch&plcid=0x409&o1=.NETFramework,Version=v4.6.1&processName=ERROR404.EXE&platform=0000&osver=5&isServer=0&shimver=4.0.30319.34209 | C:\Program Files\Internet Explorer\iexplore.exe | ERROR404.EXE | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Internet Explorer Exit code: 1 Version: 11.00.9600.16428 (winblue_gdr.131013-1700) Modules
| |||||||||||||||
| 1296 | C:\Windows\system32\vssvc.exe | C:\Windows\system32\vssvc.exe | — | services.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Microsoft® Volume Shadow Copy Service Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1852 | "C:\Users\admin\AppData\Local\Temp\{7A856899-0845-4363-BFBF-3BC35642825D}\.be\NDP48-DevPack-ENU.exe" -q -burn.elevated BurnPipe.{500F11B1-516C-4414-AE7C-F9D1FDC89AAC} {8625F62C-883E-4929-8753-C2F1AC008E63} 2868 | C:\Users\admin\AppData\Local\Temp\{7A856899-0845-4363-BFBF-3BC35642825D}\.be\NDP48-DevPack-ENU.exe | ndp48-devpack-enu.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft .NET Framework 4.8 Developer Pack Exit code: 0 Version: 4.8.3928 Modules
| |||||||||||||||
| 1908 | SetupUtility.exe /aupause | C:\e6faded18db9ed6a1e09665fa6ec22\SetupUtility.exe | — | Setup.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft .NET Framework 4.5 Setup Exit code: 0 Version: 14.8.4110.0 built by: NET48REL1LAST_B Modules
| |||||||||||||||
| 2132 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=crashpad-handler "--user-data-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" /prefetch:7 --monitor-self-annotation=ptype=crashpad-handler "--database=C:\Users\admin\AppData\Local\Google\Chrome\User Data\Crashpad" "--metrics-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" --url=https://clients2.google.com/cr/report --annotation=channel= --annotation=plat=Win32 --annotation=prod=Chrome --annotation=ver=86.0.4240.198 --initial-client-data=0xc8,0xcc,0xd0,0x9c,0xd4,0x6f64d988,0x6f64d998,0x6f64d9a4 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 2148 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=chrome.mojom.FileUtilService --field-trial-handle=1044,6494888289819464258,4636735122758509971,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --mojo-platform-channel-handle=2696 /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | chrome.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 2392 | C:\e6faded18db9ed6a1e09665fa6ec22\\Setup.exe /q /x86 /x64 /norestart /skipenucheck /keepaupaused /chainingpackage "Microsoft .NET Framework 4.8 Developer Pack" /log "C:\Users\admin\AppData\Local\Temp\Microsoft_.NET_Framework_4.8_Developer_Pack_20220703034904_000_netfxfullrefreshisv.log.html" /pipe NetFxSection.{34E587CF-66EC-4D81-A44F-8A44FB27C13F} /x86 /x64 /redist | C:\e6faded18db9ed6a1e09665fa6ec22\Setup.exe | NDP48-x86-x64-AllOS-ENU.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Setup Installer Exit code: 0 Version: 14.8.4110.0 built by: NET48REL1LAST_B Modules
| |||||||||||||||
| 2568 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --disk-cache-dir=null --disk-cache-size=1 --media-cache-size=1 --disable-gpu-shader-disk-cache --disable-background-networking "https://download1863.mediafire.com/7ds712n89ojg/7ngdr40a472cgkt/error404+v746291.zip" | C:\Program Files\Google\Chrome\Application\chrome.exe | Explorer.EXE | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 3221225547 Version: 86.0.4240.198 Modules
| |||||||||||||||
| 2588 | "C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\6Z2BCOUL\ndp48-devpack-enu.exe" | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\6Z2BCOUL\ndp48-devpack-enu.exe | iexplore.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft .NET Framework 4.8 Developer Pack Exit code: 0 Version: 4.8.3928 Modules
| |||||||||||||||
Total events
48 388
Read events
39 407
Write events
8 969
Delete events
12
Modification events
| (PID) Process: | (2568) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (2568) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (2568) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: | |||
| (PID) Process: | (2568) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\ThirdParty |
| Operation: | write | Name: | StatusCodes |
Value: 01000000 | |||
| (PID) Process: | (2568) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (2568) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | dr |
Value: 1 | |||
| (PID) Process: | (2568) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Chrome |
| Operation: | write | Name: | UsageStatsInSample |
Value: 0 | |||
| (PID) Process: | (2568) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
| (PID) Process: | (2568) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | metricsid |
Value: | |||
| (PID) Process: | (2568) chrome.exe | Key: | HKEY_CURRENT_USER\Software\Google\Update\ClientState\{8A69D345-D564-463c-AFF1-A69D9E530F96} |
| Operation: | write | Name: | metricsid_installdate |
Value: 0 | |||
Executable files
1 445
Suspicious files
63
Text files
376
Unknown types
26
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2568 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\BrowserMetrics\BrowserMetrics-62C10315-A08.pma | — | |
MD5:— | SHA256:— | |||
| 2568 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Preferences | text | |
MD5:— | SHA256:— | |||
| 2568 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\47686f8e-3e89-4f3d-8f01-a98d317d4e53.tmp | text | |
MD5:— | SHA256:— | |||
| 2132 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\CrashpadMetrics.pma | binary | |
MD5:03C4F648043A88675A920425D824E1B3 | SHA256:F91DBB7C64B4582F529C968C480D2DCE1C8727390482F31E4355A27BB3D9B450 | |||
| 2568 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Last Version | text | |
MD5:00046F773EFDD3C8F8F6D0F87A2B93DC | SHA256:593EDE11D17AF7F016828068BCA2E93CF240417563FB06DC8A579110AEF81731 | |||
| 2568 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Platform Notifications\LOG.old~RFf5e05.TMP | text | |
MD5:109A25C32EE1132ECD6D9F3ED9ADF01A | SHA256:DA6028DB9485C65E683643658326F02B1D0A1566DE14914EF28E5248EB94F0DD | |||
| 2568 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Site Characteristics Database\LOG.old | text | |
MD5:8FF312A95D60ED89857FEB720D80D4E1 | SHA256:946A57FAFDD28C3164D5AB8AB4971B21BD5EC5BFFF7554DBF832CB58CC37700B | |||
| 2568 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Session Storage\LOG.old~RFf5e34.TMP | text | |
MD5:B628564B8042F6E2CC2F53710AAECDC0 | SHA256:1D3B022BDEE9F48D79E3EC1E93F519036003642D3D72D10B05CFD47F43EFBF13 | |||
| 2568 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\Session Storage\LOG.old | text | |
MD5:995C92837E4775CAFFE387D51ADBA520 | SHA256:51247C3464FD988B72670002D01A57FBFF1348704D325DC8FF8817ED2459D0D9 | |||
| 2568 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Crashpad\settings.dat | binary | |
MD5:9C016064A1F864C8140915D77CF3389A | SHA256:0E7265D4A8C16223538EDD8CD620B8820611C74538E420A88E333BE7F62AC787 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
13
TCP/UDP connections
59
DNS requests
29
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2844 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTBL0V27RVZ7LBduom%2FnYB45SPUEwQU5Z1ZMIJHWMys%2BghUNoZ7OrUETfACEA8Ull8gIGmZT9XHrHiJQeI%3D | US | der | 1.47 Kb | whitelisted |
2844 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAbY2QTVWENG9oovp1QifsQ%3D | US | der | 471 b | whitelisted |
2844 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTBL0V27RVZ7LBduom%2FnYB45SPUEwQU5Z1ZMIJHWMys%2BghUNoZ7OrUETfACEA9bw6F2y3ieICDHiTyBZ7Q%3D | US | der | 1.47 Kb | whitelisted |
2844 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTBL0V27RVZ7LBduom%2FnYB45SPUEwQU5Z1ZMIJHWMys%2BghUNoZ7OrUETfACEA%2BnRyLFPYjID1ie%2Bx%2BdSjo%3D | US | der | 1.47 Kb | whitelisted |
2392 | Setup.exe | GET | 200 | 72.246.169.155:80 | http://www.microsoft.com/pkiops/crl/MicCodSigPCA2011_2011-07-08.crl | NL | der | 1.05 Kb | whitelisted |
2392 | Setup.exe | GET | 200 | 92.123.194.154:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | der | 1.11 Kb | whitelisted |
2844 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEALnkXH7gCHpP%2BLZg4NMUMA%3D | US | der | 471 b | whitelisted |
2844 | iexplore.exe | GET | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | US | der | 471 b | whitelisted |
2392 | Setup.exe | GET | 200 | 92.123.194.154:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut_2010-06-23.crl | unknown | der | 824 b | whitelisted |
2844 | iexplore.exe | GET | 200 | 67.26.139.254:80 | http://ctldl.windowsupdate.com/msdownload/update/v3/static/trustedr/en/disallowedcertstl.cab?b78e2c06a04ecf82 | US | compressed | 4.70 Kb | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
3320 | chrome.exe | 199.91.153.110:443 | download1863.mediafire.com | MediaFire, LLC | US | unknown |
3320 | chrome.exe | 142.250.181.238:443 | clients2.google.com | Google Inc. | US | whitelisted |
3320 | chrome.exe | 172.217.16.141:443 | accounts.google.com | Google Inc. | US | suspicious |
3320 | chrome.exe | 142.250.186.161:443 | clients2.googleusercontent.com | Google Inc. | US | whitelisted |
3320 | chrome.exe | 142.250.185.67:443 | ssl.gstatic.com | Google Inc. | US | whitelisted |
3320 | chrome.exe | 142.250.185.110:443 | sb-ssl.google.com | Google Inc. | US | whitelisted |
2844 | iexplore.exe | 104.92.93.19:443 | go.microsoft.com | Akamai Technologies, Inc. | NL | unknown |
2844 | iexplore.exe | 67.26.139.254:80 | ctldl.windowsupdate.com | Level 3 Communications, Inc. | US | suspicious |
2844 | iexplore.exe | 93.184.220.29:80 | ocsp.digicert.com | MCI Communications Services, Inc. d/b/a Verizon Business | US | whitelisted |
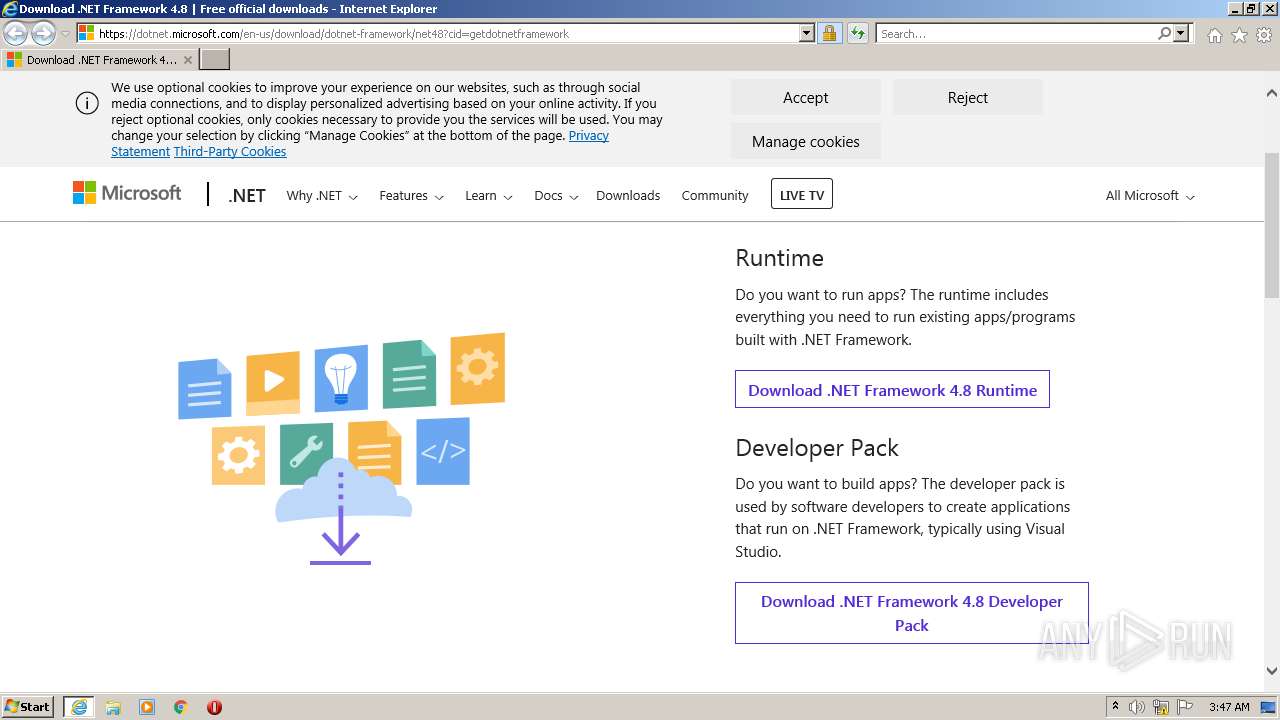
2844 | iexplore.exe | 13.107.246.45:443 | dotnet.microsoft.com | Microsoft Corporation | US | malicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
download1863.mediafire.com |
| unknown |
accounts.google.com |
| shared |
clients2.google.com |
| whitelisted |
clients2.googleusercontent.com |
| whitelisted |
ssl.gstatic.com |
| whitelisted |
sb-ssl.google.com |
| whitelisted |
go.microsoft.com |
| whitelisted |
ctldl.windowsupdate.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
dotnet.microsoft.com |
| whitelisted |