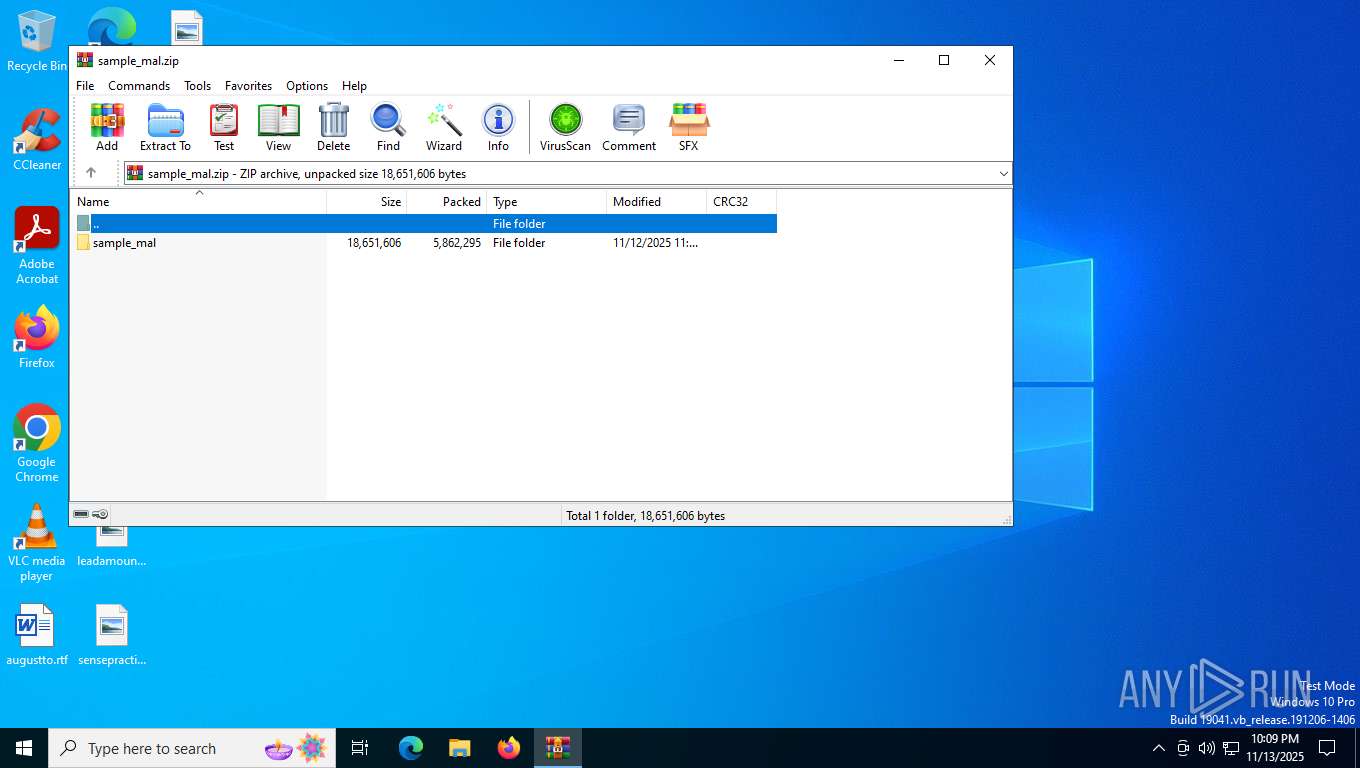
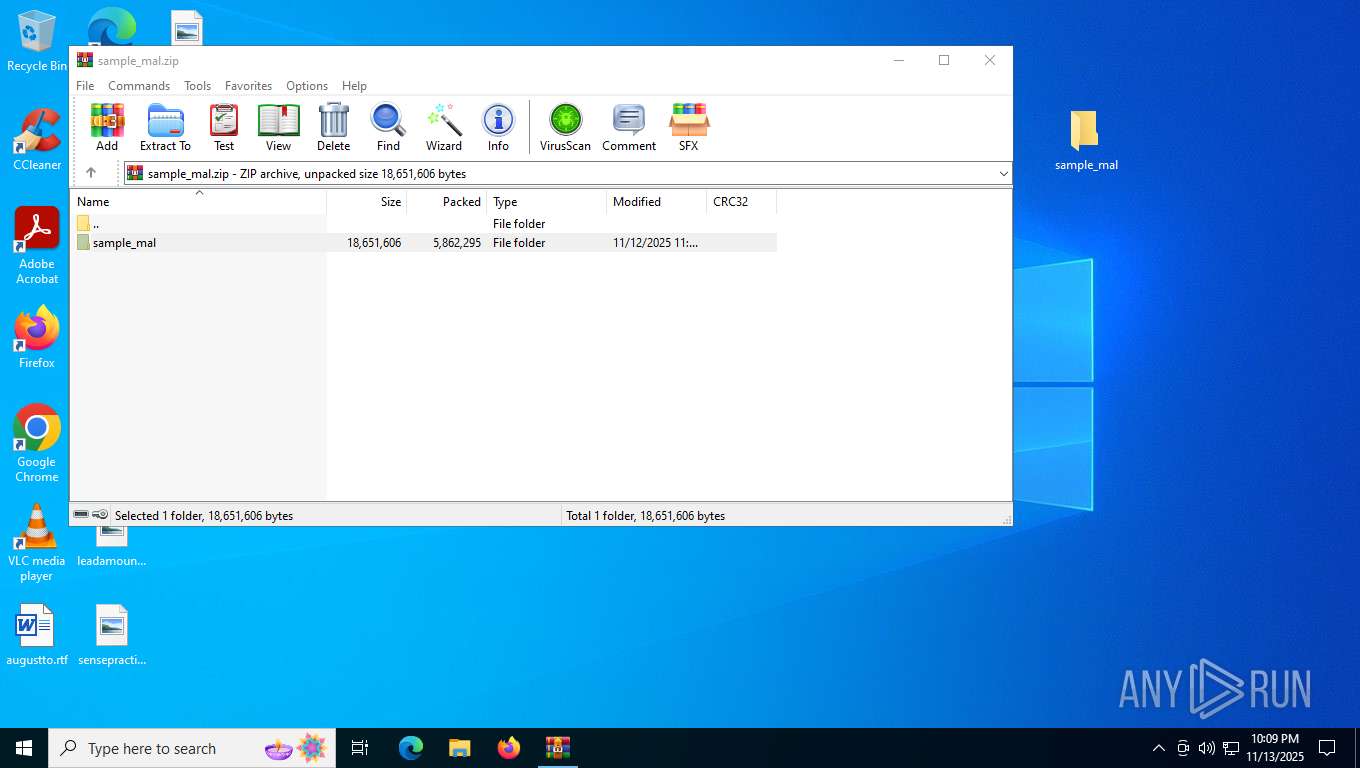
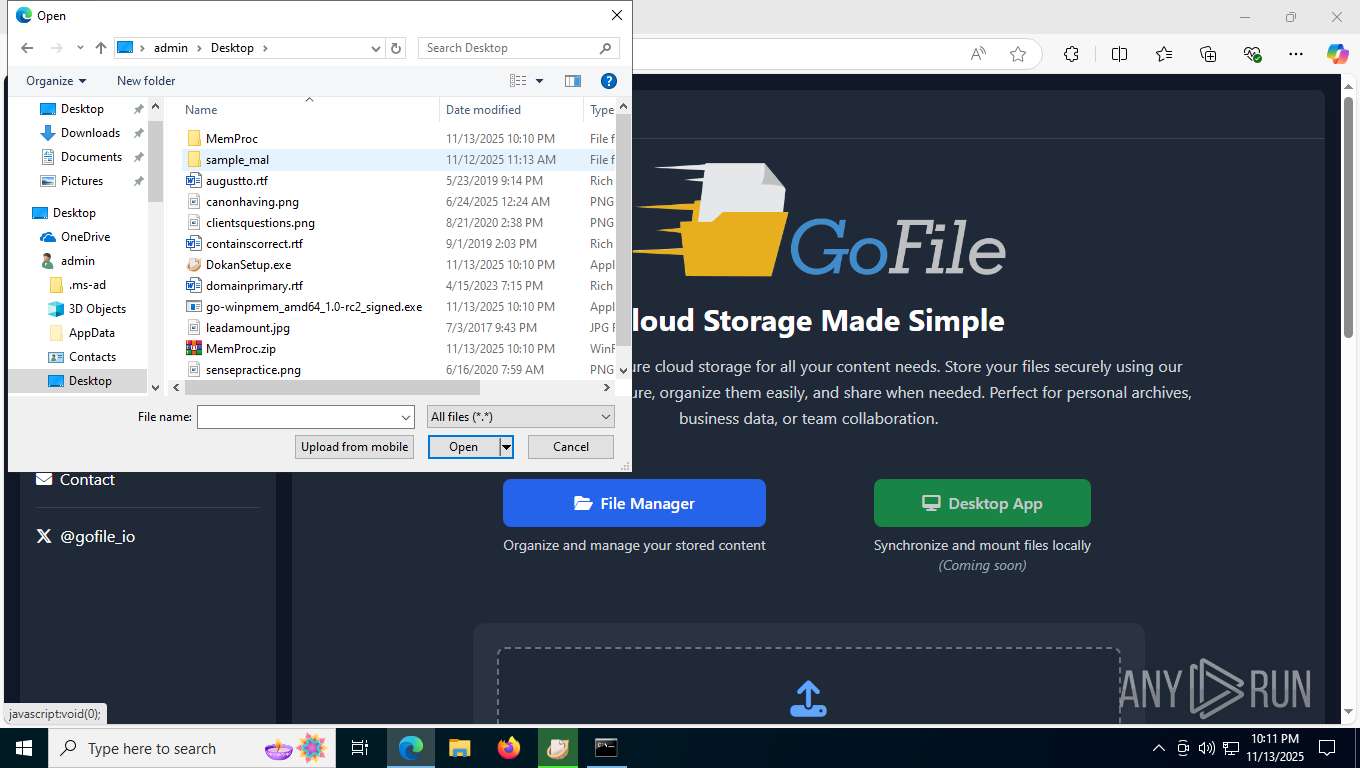
| File name: | sample_mal.zip |
| Full analysis: | https://app.any.run/tasks/50c52822-ab6d-4b47-9113-44b46cefcb6c |
| Verdict: | Malicious activity |
| Analysis date: | November 13, 2025, 22:09:23 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/zip |
| File info: | Zip archive data, at least v2.0 to extract, compression method=store |
| MD5: | 03792C225BC250A16121F9FD0B21D2F2 |
| SHA1: | 1967654EF076371173681376DD6AFC8DEB60223D |
| SHA256: | 64081D577943AD608EECC77103F50053D6BCC2E2A5BD4518F3D4C96DA00813B0 |
| SSDEEP: | 98304:yM0OoKXoqLPQoeFoz63m7rkleR3Nu7Ab6BLzXlZN4vKK2qT5ThjwLLkNXs4gY/kI:kJ6K1GB+O/D |
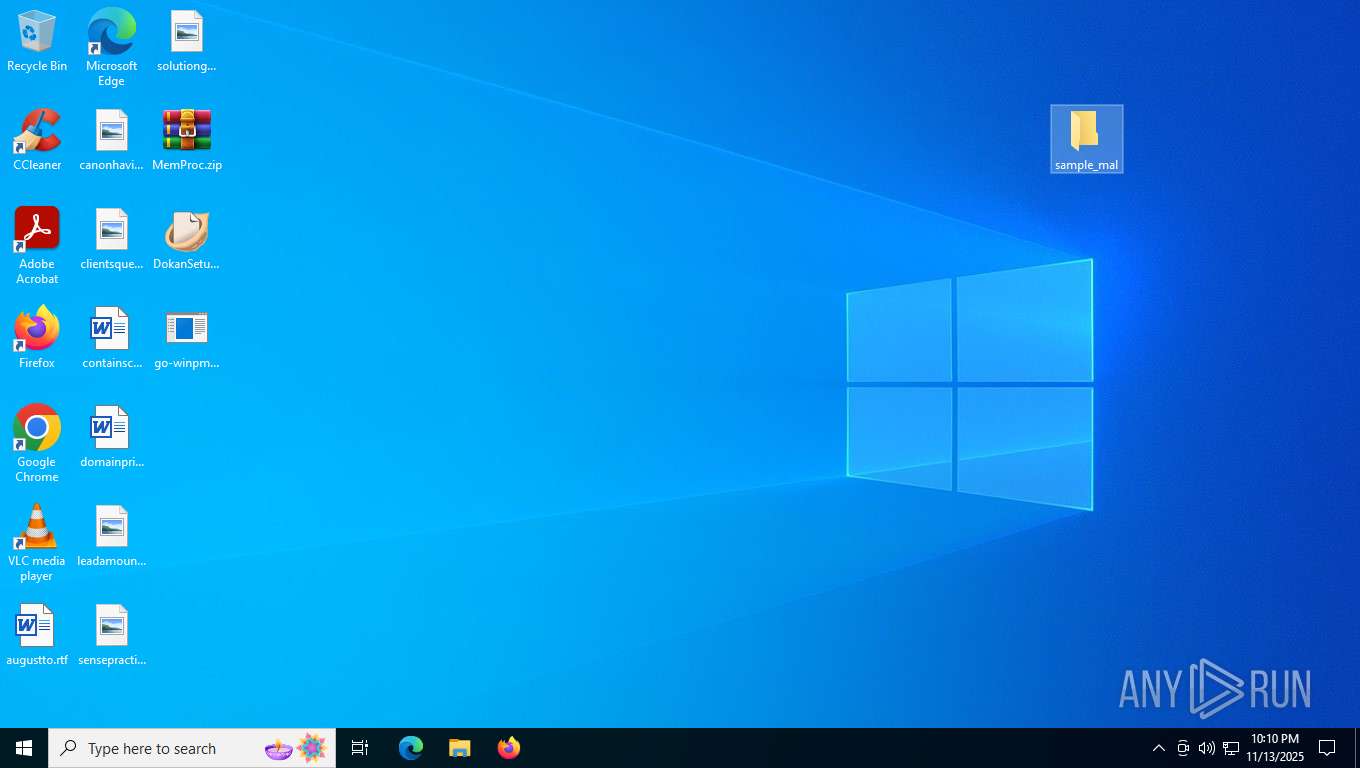
MALICIOUS
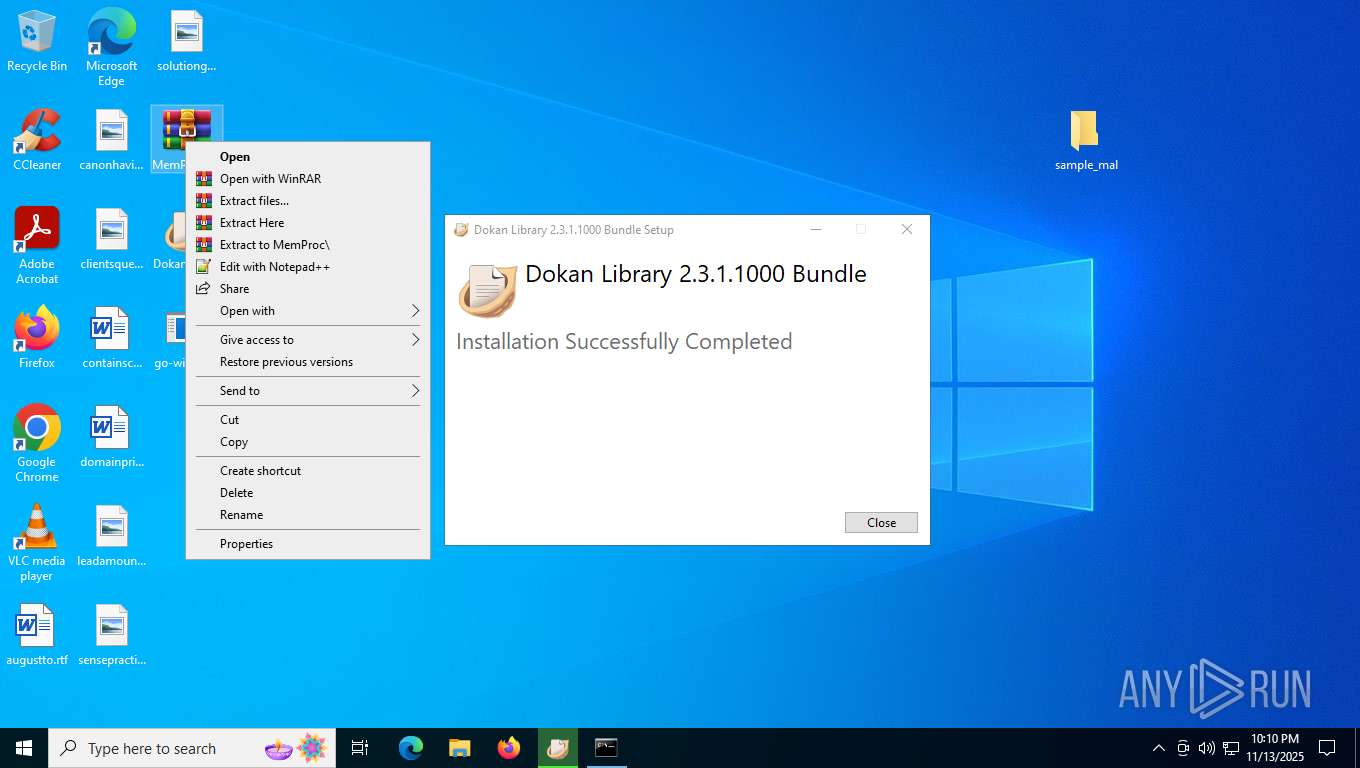
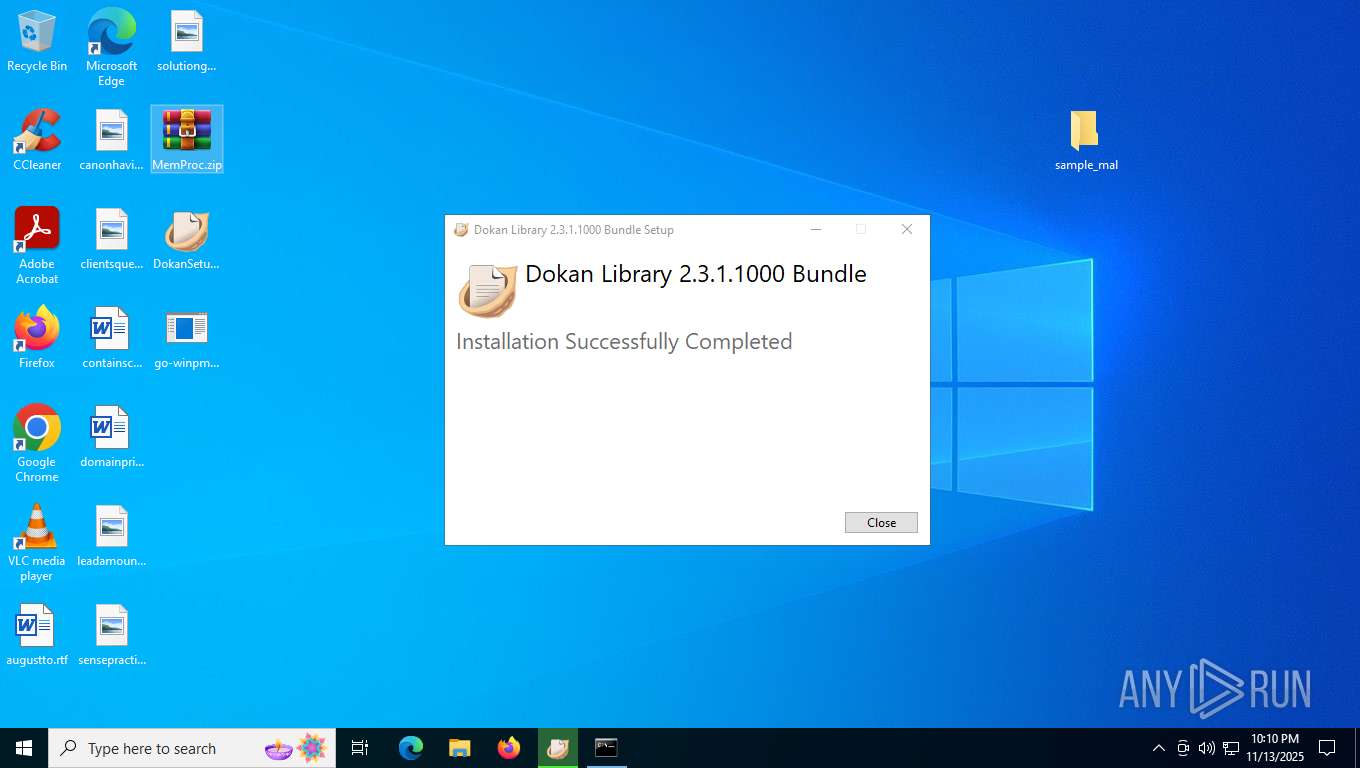
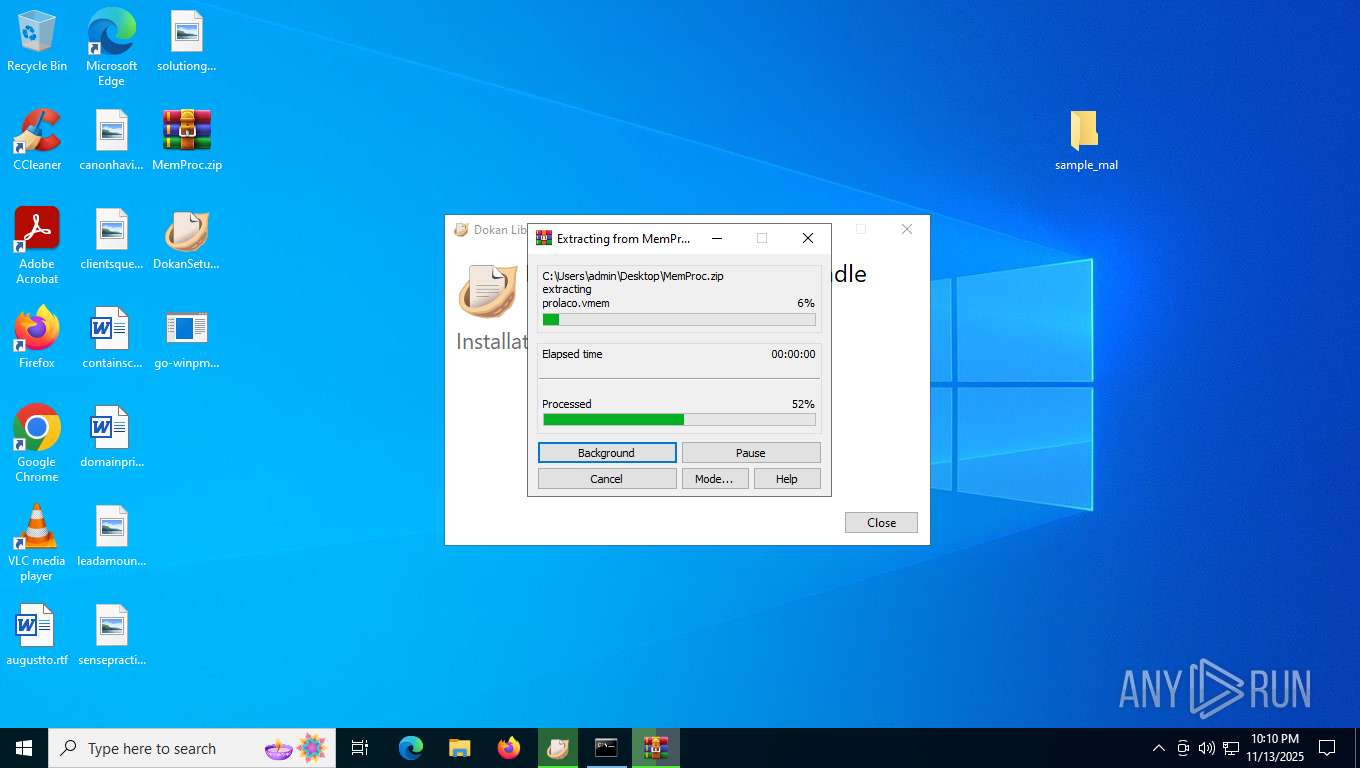
Generic archive extractor
- WinRAR.exe (PID: 7256)
Changes the autorun value in the registry
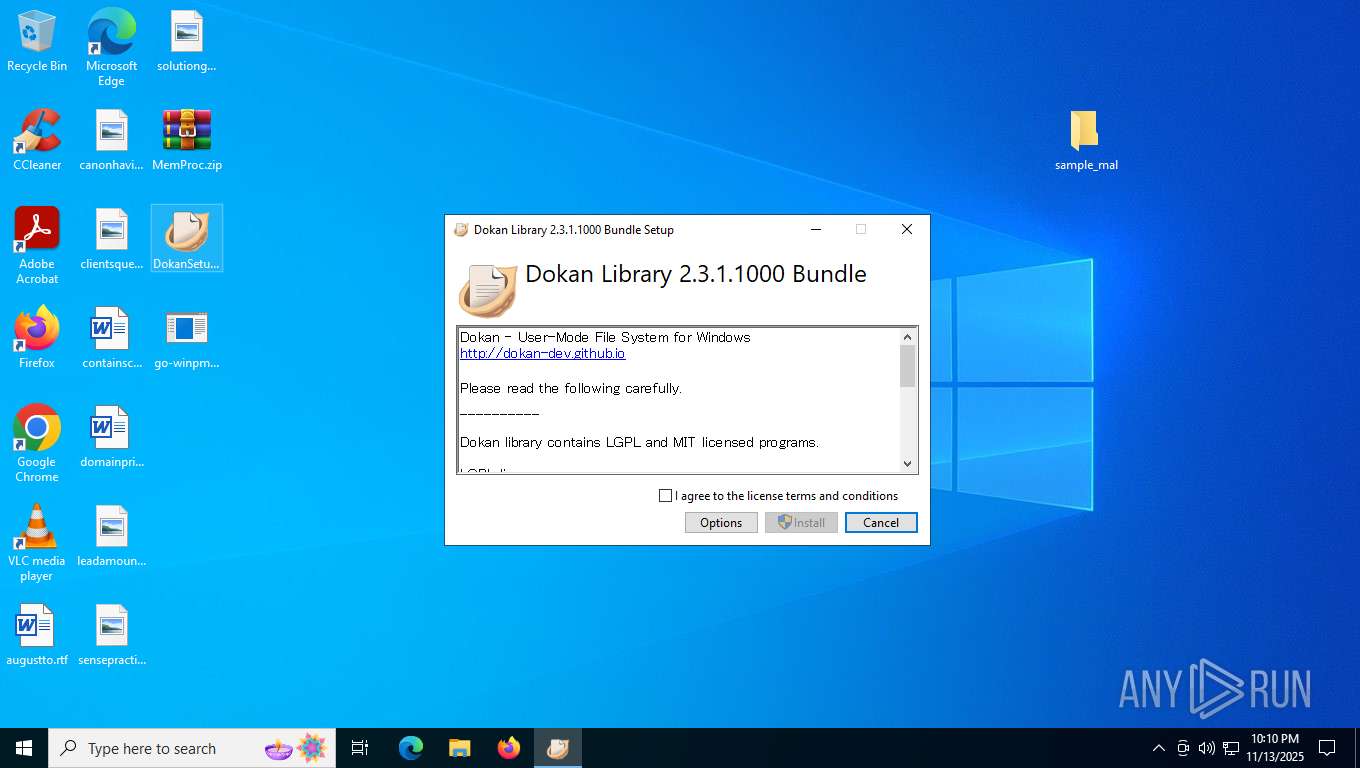
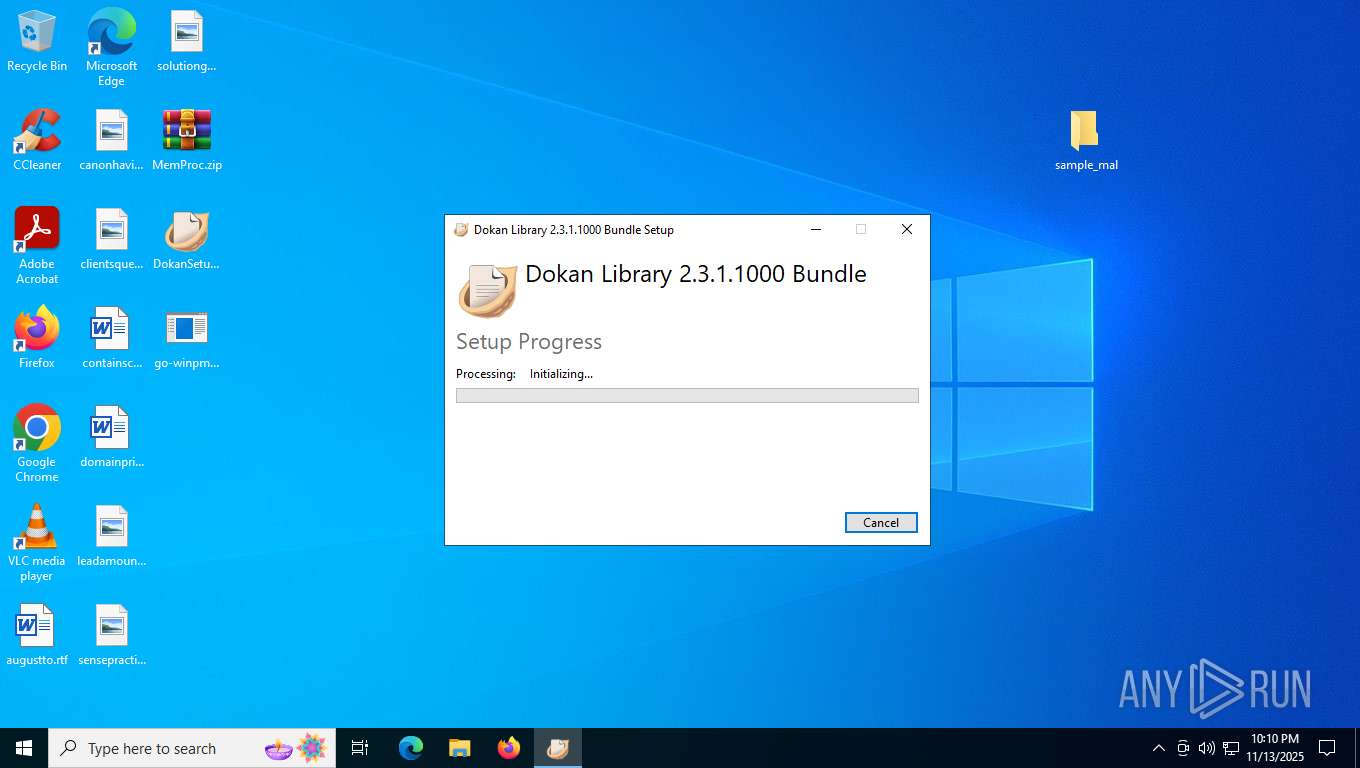
- DokanSetup.exe (PID: 8188)
Changes settings of System certificates
- msiexec.exe (PID: 1144)
SUSPICIOUS
Searches for installed software
- DokanSetup.exe (PID: 8068)
- DokanSetup.exe (PID: 8188)
- dllhost.exe (PID: 1152)
Reads security settings of Internet Explorer
- DokanSetup.exe (PID: 8068)
- MemProcFS.exe (PID: 1252)
Executable content was dropped or overwritten
- DokanSetup.exe (PID: 8068)
- DokanSetup.exe (PID: 8188)
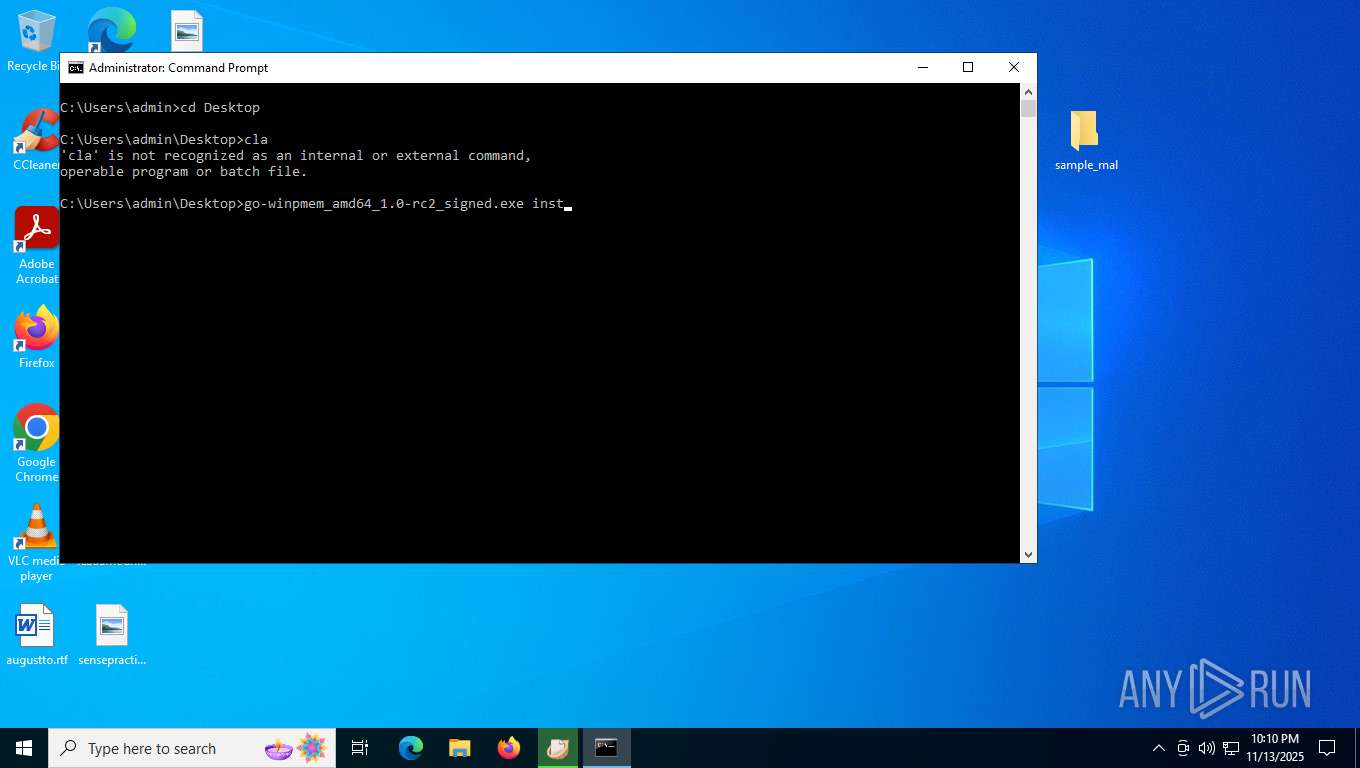
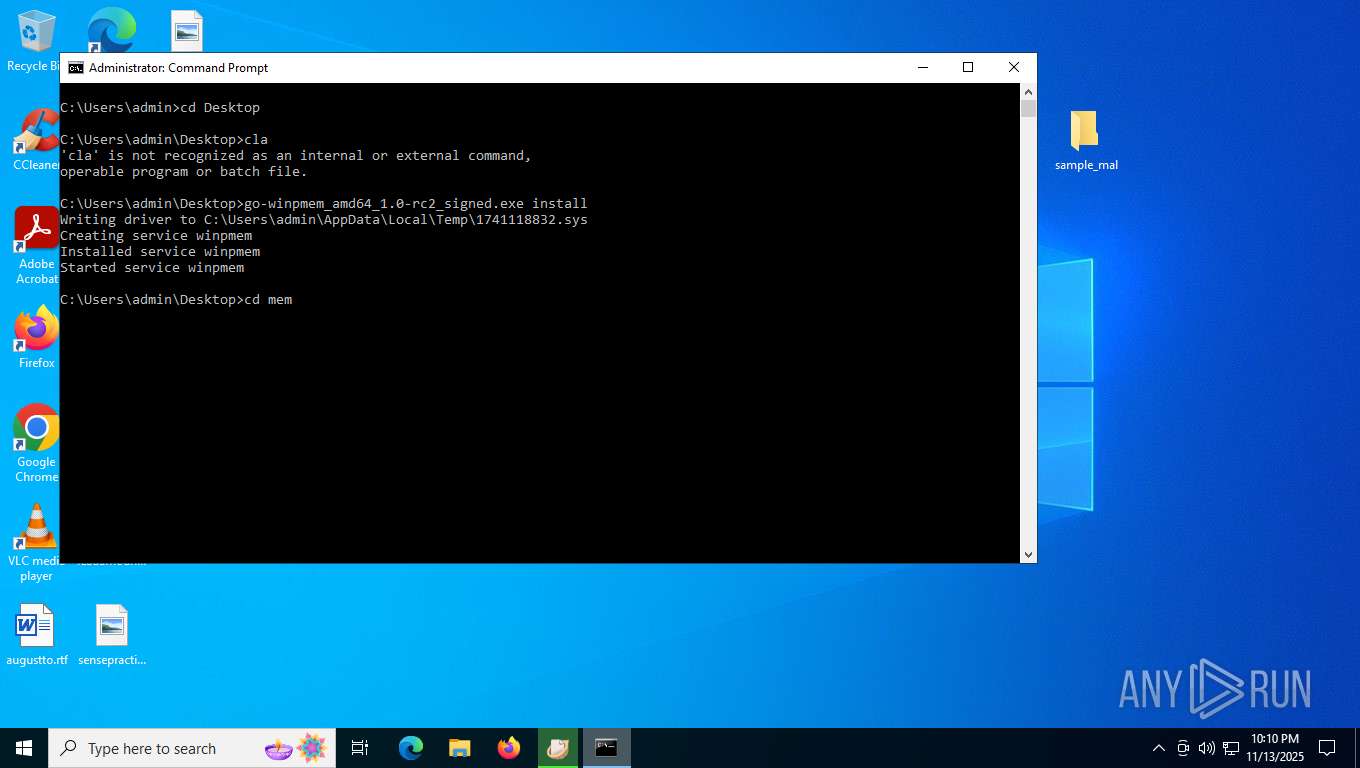
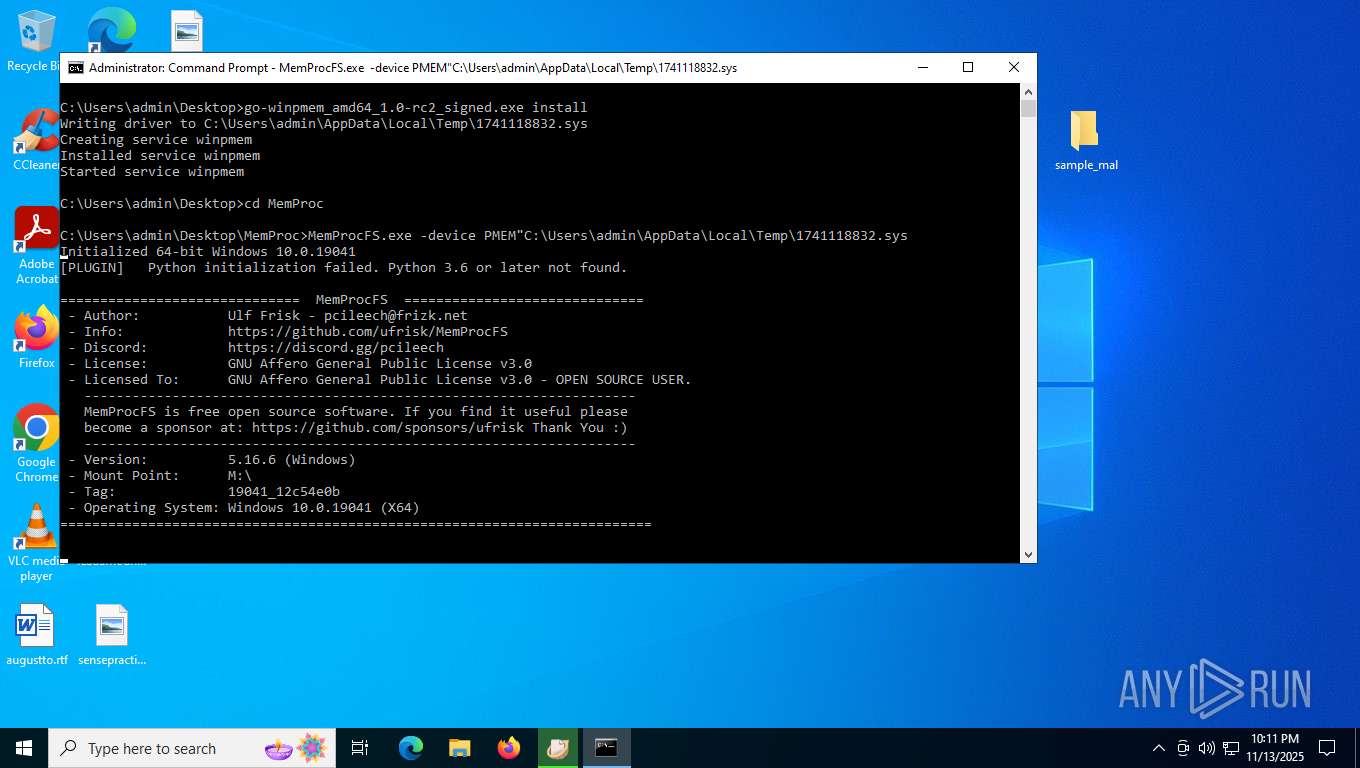
- go-winpmem_amd64_1.0-rc2_signed.exe (PID: 7416)
Executes as Windows Service
- VSSVC.exe (PID: 7220)
Adds/modifies Windows certificates
- msiexec.exe (PID: 1144)
Reads the Windows owner or organization settings
- msiexec.exe (PID: 1144)
Drops a system driver (possible attempt to evade defenses)
- msiexec.exe (PID: 1144)
- go-winpmem_amd64_1.0-rc2_signed.exe (PID: 7416)
- WinRAR.exe (PID: 8164)
Creates files in the driver directory
- msiexec.exe (PID: 1144)
Process drops legitimate windows executable
- WinRAR.exe (PID: 8164)
Process drops python dynamic module
- WinRAR.exe (PID: 8164)
INFO
Executable content was dropped or overwritten
- WinRAR.exe (PID: 7256)
- msiexec.exe (PID: 1144)
- WinRAR.exe (PID: 8164)
Drops encrypted VBS script (Microsoft Script Encoder)
- WinRAR.exe (PID: 7256)
Checks supported languages
- wixstdba.exe (PID: 8096)
- DokanSetup.exe (PID: 8068)
- DokanSetup.exe (PID: 8188)
- msiexec.exe (PID: 1144)
- msiexec.exe (PID: 2388)
- dokanctl.exe (PID: 2052)
- go-winpmem_amd64_1.0-rc2_signed.exe (PID: 7416)
- MemProcFS.exe (PID: 1252)
- identity_helper.exe (PID: 8224)
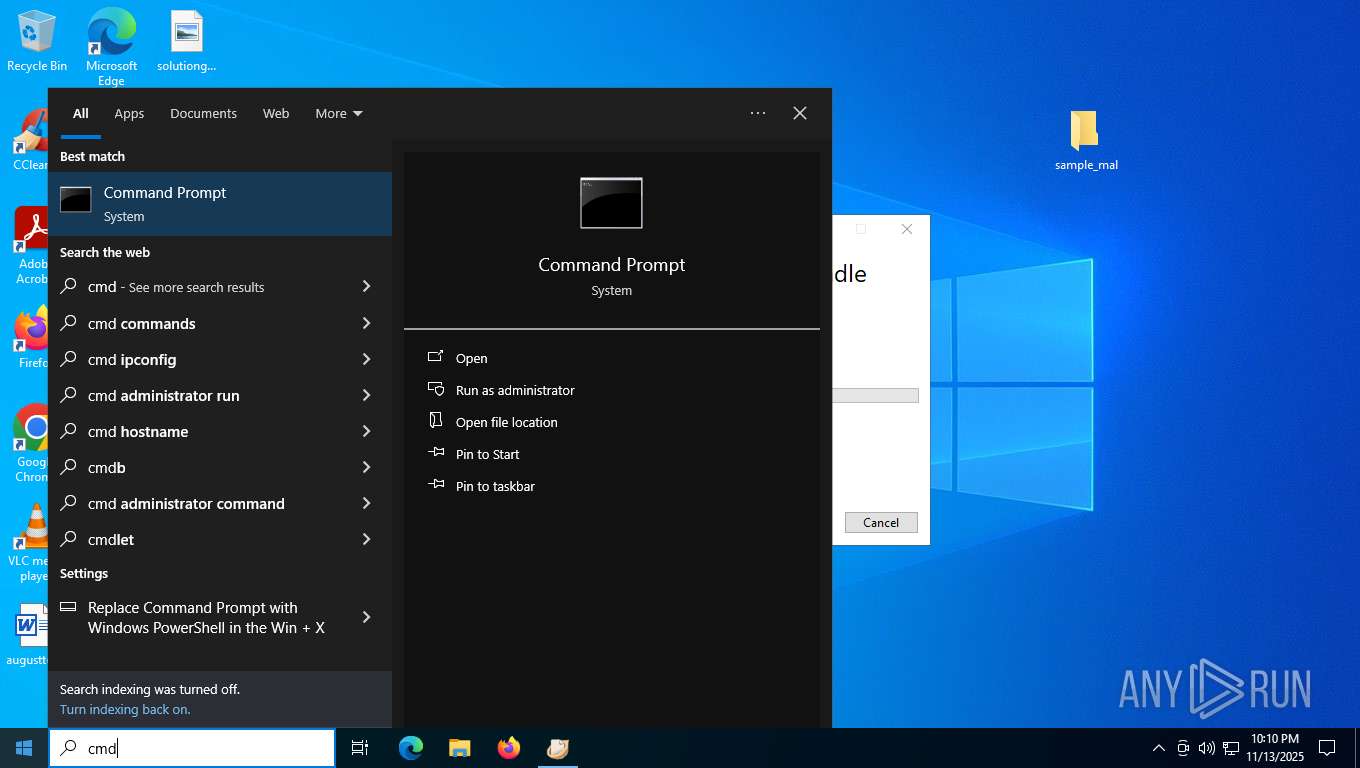
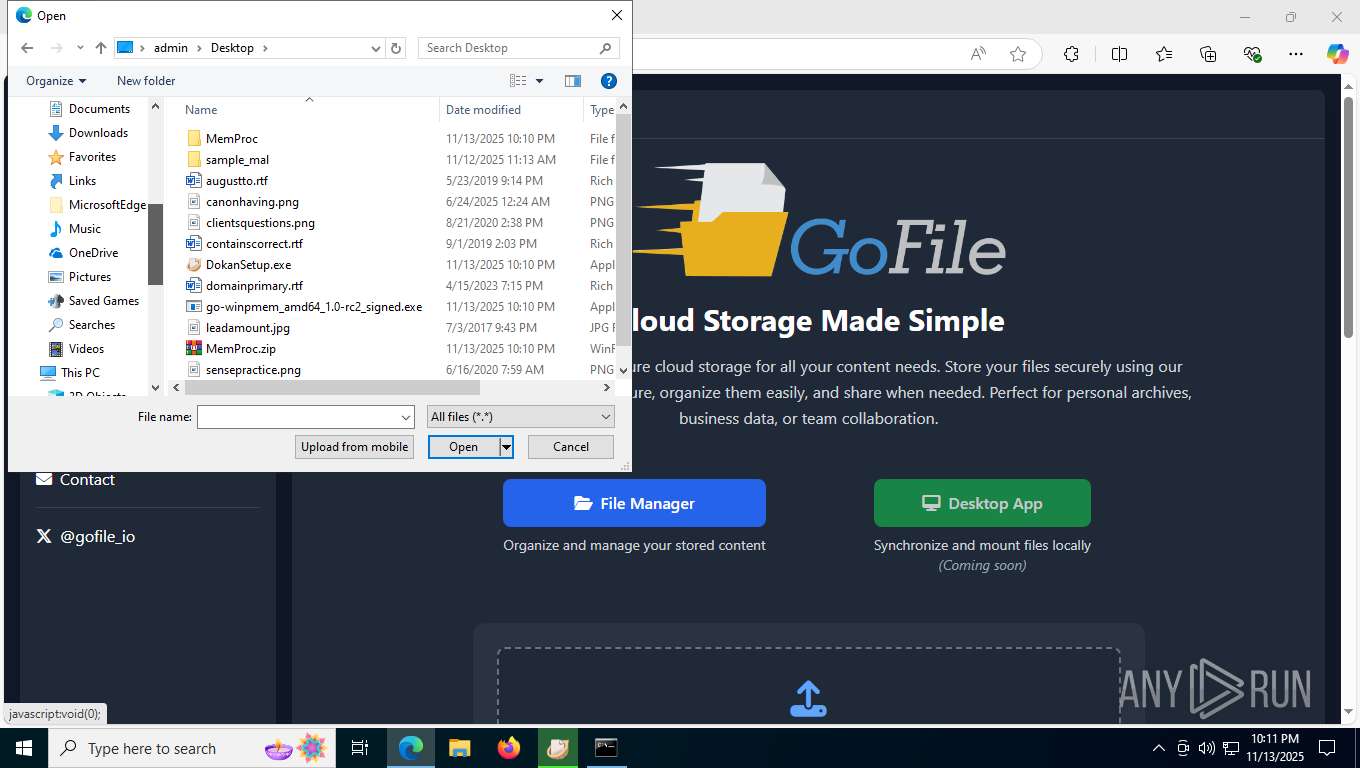
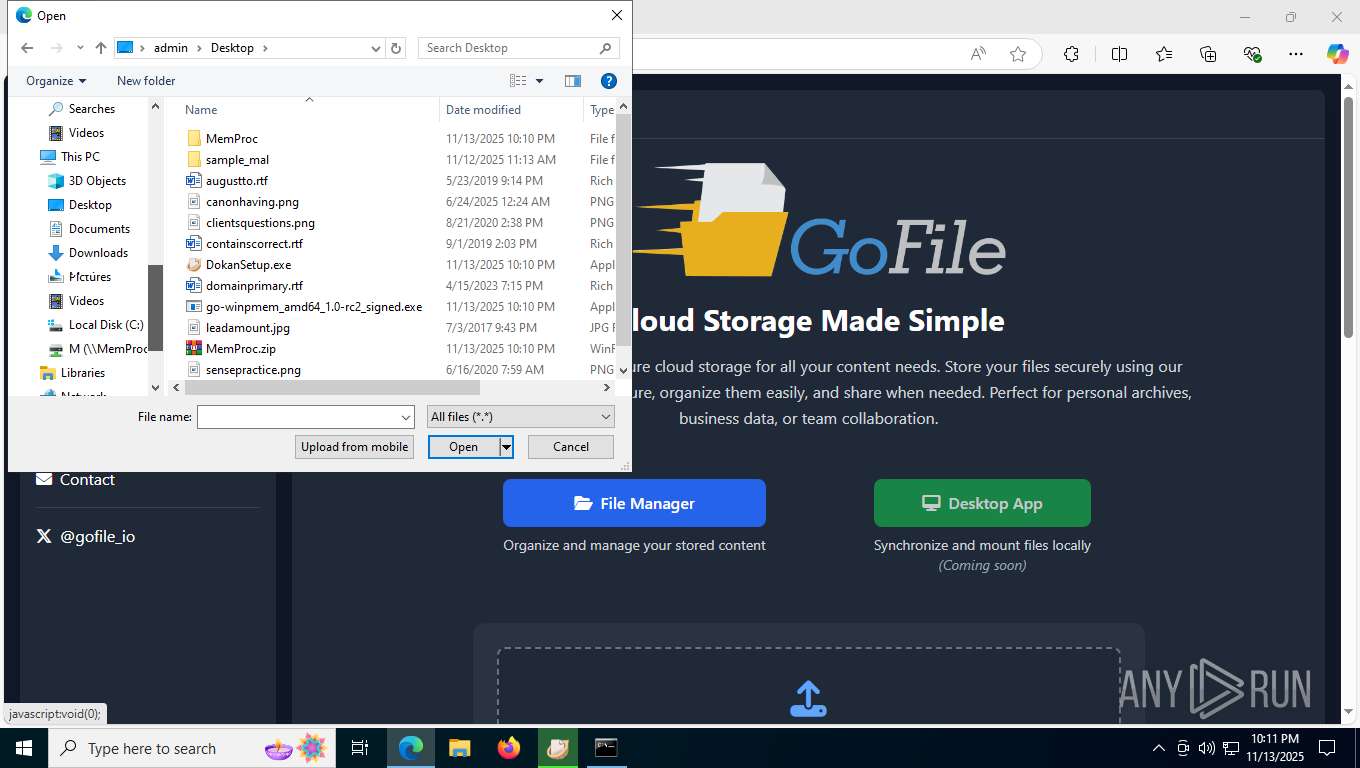
Manual execution by a user
- DokanSetup.exe (PID: 8068)
- cmd.exe (PID: 1284)
- WinRAR.exe (PID: 8164)
- msedge.exe (PID: 2188)
Reads the computer name
- wixstdba.exe (PID: 8096)
- DokanSetup.exe (PID: 8068)
- DokanSetup.exe (PID: 8188)
- msiexec.exe (PID: 2388)
- dokanctl.exe (PID: 2052)
- msiexec.exe (PID: 1144)
- go-winpmem_amd64_1.0-rc2_signed.exe (PID: 7416)
- MemProcFS.exe (PID: 1252)
- identity_helper.exe (PID: 8224)
The sample compiled with english language support
- DokanSetup.exe (PID: 8068)
- DokanSetup.exe (PID: 8188)
- WinRAR.exe (PID: 8164)
Creates files in the program directory
- DokanSetup.exe (PID: 8188)
Creates a software uninstall entry
- DokanSetup.exe (PID: 8188)
- msiexec.exe (PID: 1144)
Create files in a temporary directory
- DokanSetup.exe (PID: 8068)
- DokanSetup.exe (PID: 8188)
- go-winpmem_amd64_1.0-rc2_signed.exe (PID: 7416)
Process checks computer location settings
- DokanSetup.exe (PID: 8068)
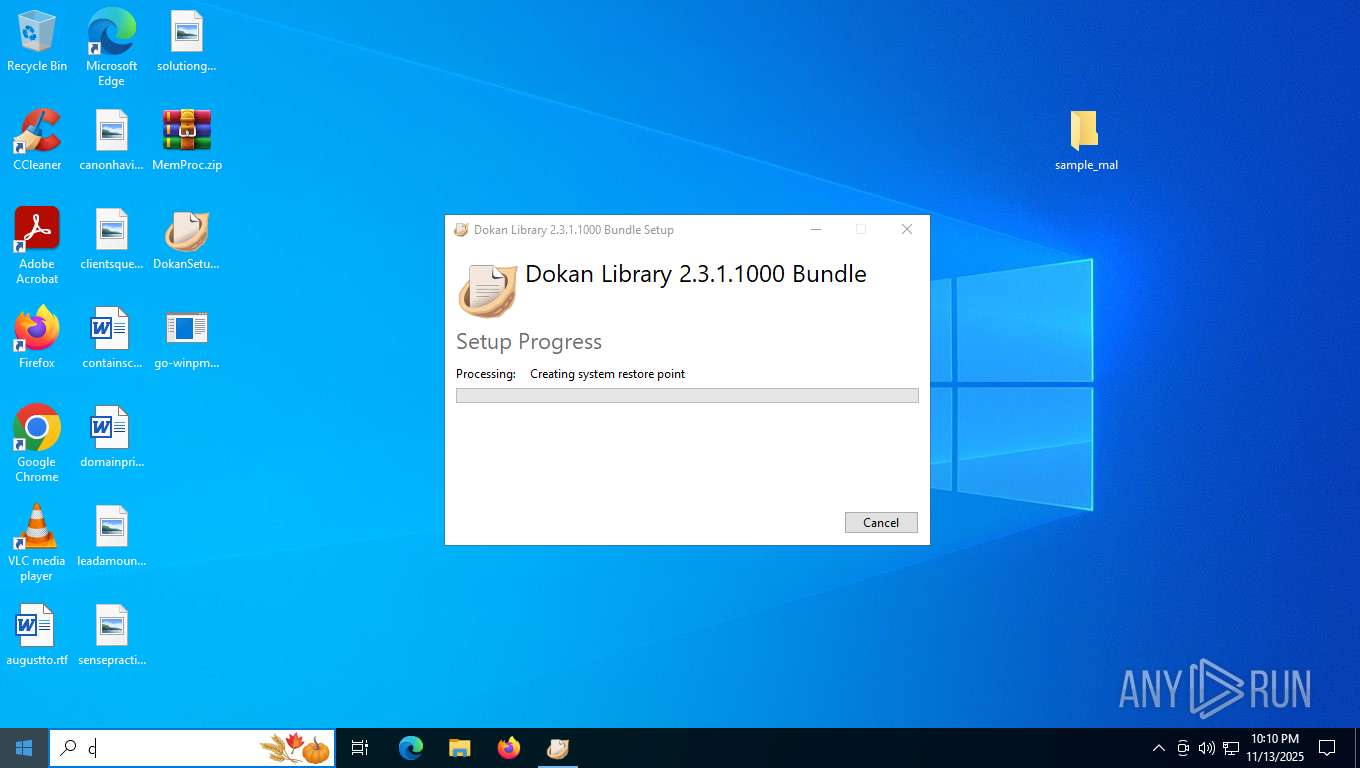
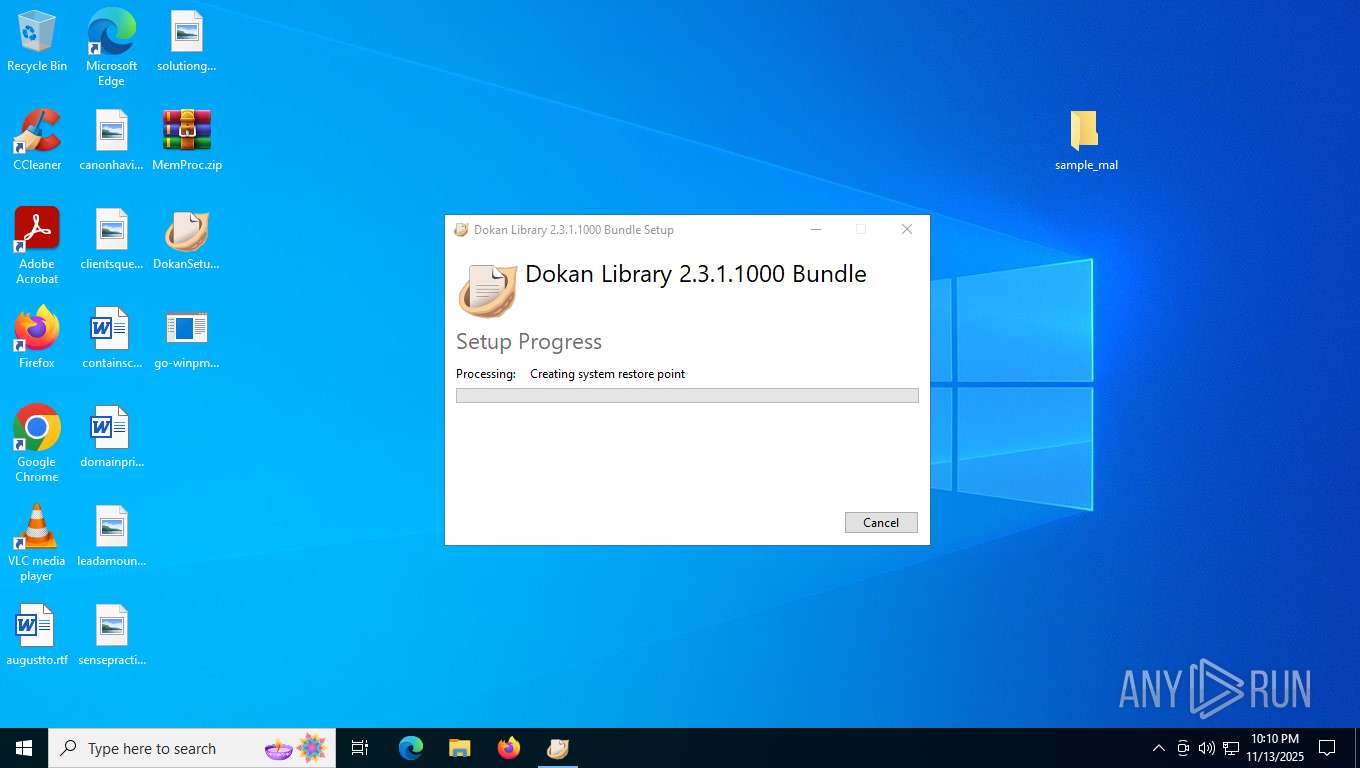
Manages system restore points
- SrTasks.exe (PID: 7804)
Launching a file from a Registry key
- DokanSetup.exe (PID: 8188)
Reads the software policy settings
- msiexec.exe (PID: 1144)
- slui.exe (PID: 4544)
- MemProcFS.exe (PID: 1252)
Creates files or folders in the user directory
- msiexec.exe (PID: 1144)
- MemProcFS.exe (PID: 1252)
Reads the machine GUID from the registry
- DokanSetup.exe (PID: 8188)
- msiexec.exe (PID: 1144)
- MemProcFS.exe (PID: 1252)
Checks proxy server information
- MemProcFS.exe (PID: 1252)
- slui.exe (PID: 4544)
Application launched itself
- msedge.exe (PID: 2188)
Reads Environment values
- identity_helper.exe (PID: 8224)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .zip | | | ZIP compressed archive (100) |
|---|
EXIF
ZIP
| ZipRequiredVersion: | 20 |
|---|---|
| ZipBitFlag: | - |
| ZipCompression: | None |
| ZipModifyDate: | 2025:11:12 14:13:18 |
| ZipCRC: | 0x00000000 |
| ZipCompressedSize: | - |
| ZipUncompressedSize: | - |
| ZipFileName: | sample_mal/ |
Total processes
195
Monitored processes
41
Malicious processes
0
Suspicious processes
3
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 148 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=renderer --string-annotations --extension-process --renderer-sub-type=extension --video-capture-use-gpu-memory-buffer --lang=en-US --js-flags=--ms-user-locale= --device-scale-factor=1 --num-raster-threads=3 --enable-main-frame-before-activation --renderer-client-id=7 --always-read-main-dll --field-trial-handle=4284,i,9960234184682204042,9459059618338895843,262144 --variations-seed-version --mojo-platform-channel-handle=4308 /prefetch:2 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 133.0.3065.92 Modules
| |||||||||||||||
| 1144 | C:\WINDOWS\system32\msiexec.exe /V | C:\Windows\System32\msiexec.exe | services.exe | ||||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows® installer Version: 5.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1152 | C:\WINDOWS\system32\DllHost.exe /Processid:{F32D97DF-E3E5-4CB9-9E3E-0EB5B4E49801} | C:\Windows\System32\dllhost.exe | — | svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: COM Surrogate Exit code: 0 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1152 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --type=utility --utility-sub-type=asset_store.mojom.AssetStoreService --lang=en-US --service-sandbox-type=asset_store_service --disable-quic --string-annotations --always-read-main-dll --field-trial-handle=3924,i,9960234184682204042,9459059618338895843,262144 --variations-seed-version --mojo-platform-channel-handle=3928 /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: LOW Description: Microsoft Edge Exit code: 0 Version: 133.0.3065.92 Modules
| |||||||||||||||
| 1220 | "C:\Program Files (x86)\Microsoft\Edge\Application\133.0.3065.92\identity_helper.exe" --type=utility --utility-sub-type=winrt_app_id.mojom.WinrtAppIdService --lang=en-US --service-sandbox-type=none --disable-quic --string-annotations --always-read-main-dll --field-trial-handle=3964,i,9960234184682204042,9459059618338895843,262144 --variations-seed-version --mojo-platform-channel-handle=6508 /prefetch:8 | C:\Program Files (x86)\Microsoft\Edge\Application\133.0.3065.92\identity_helper.exe | — | msedge.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: PWA Identity Proxy Host Exit code: 3221226029 Version: 133.0.3065.92 Modules
| |||||||||||||||
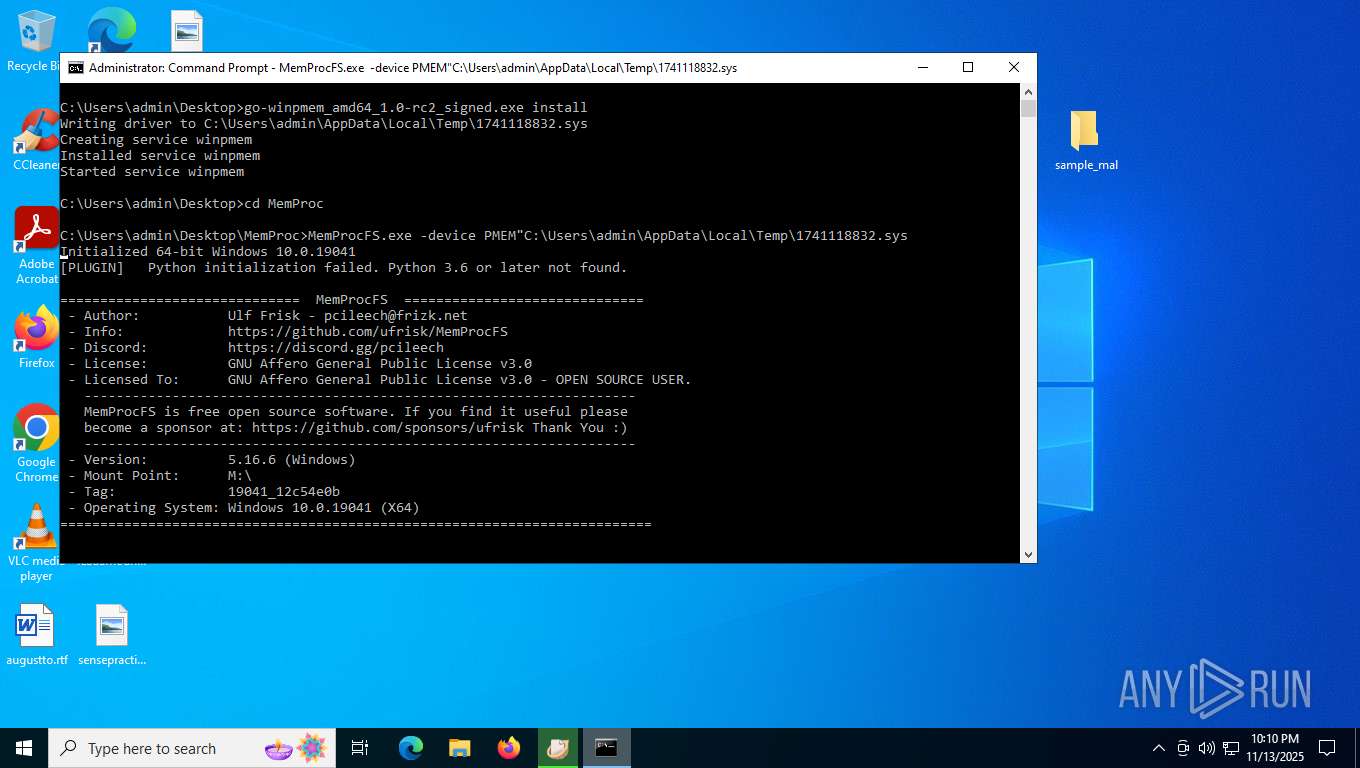
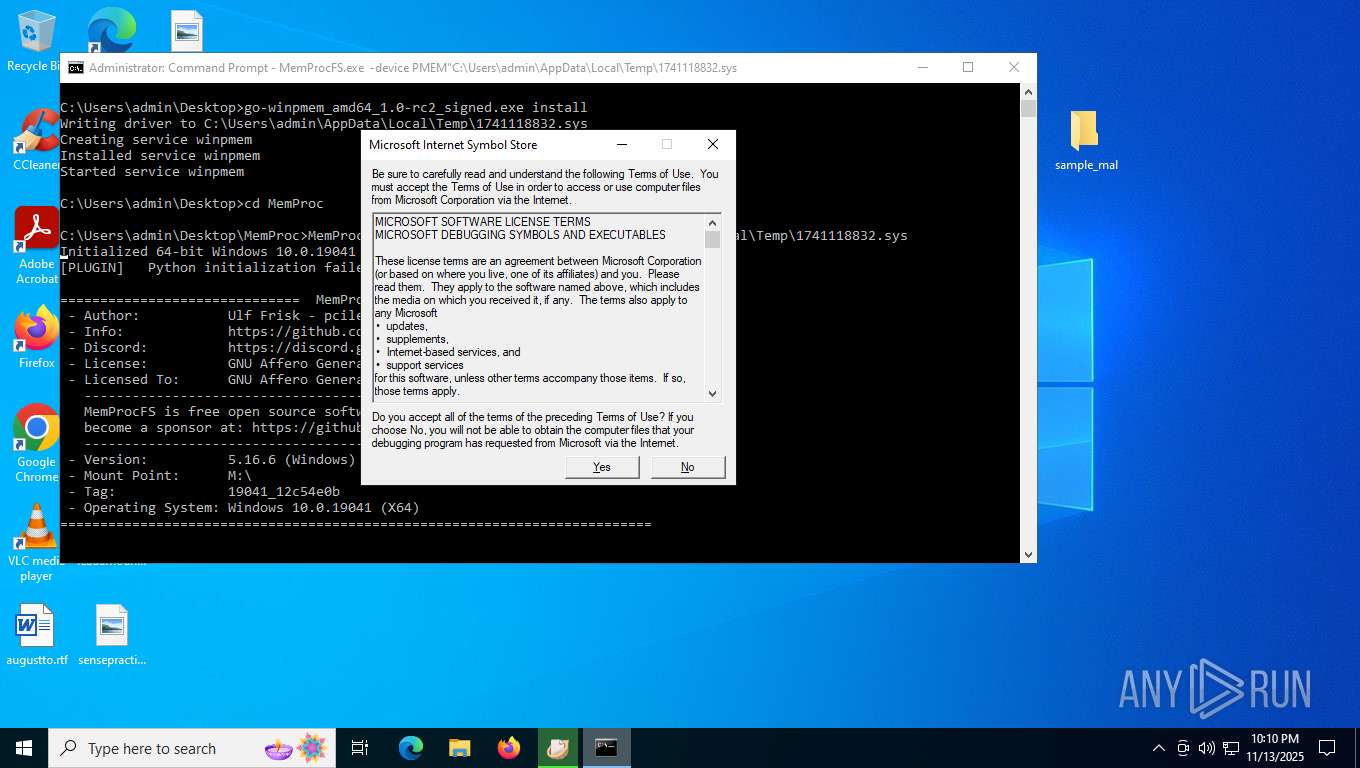
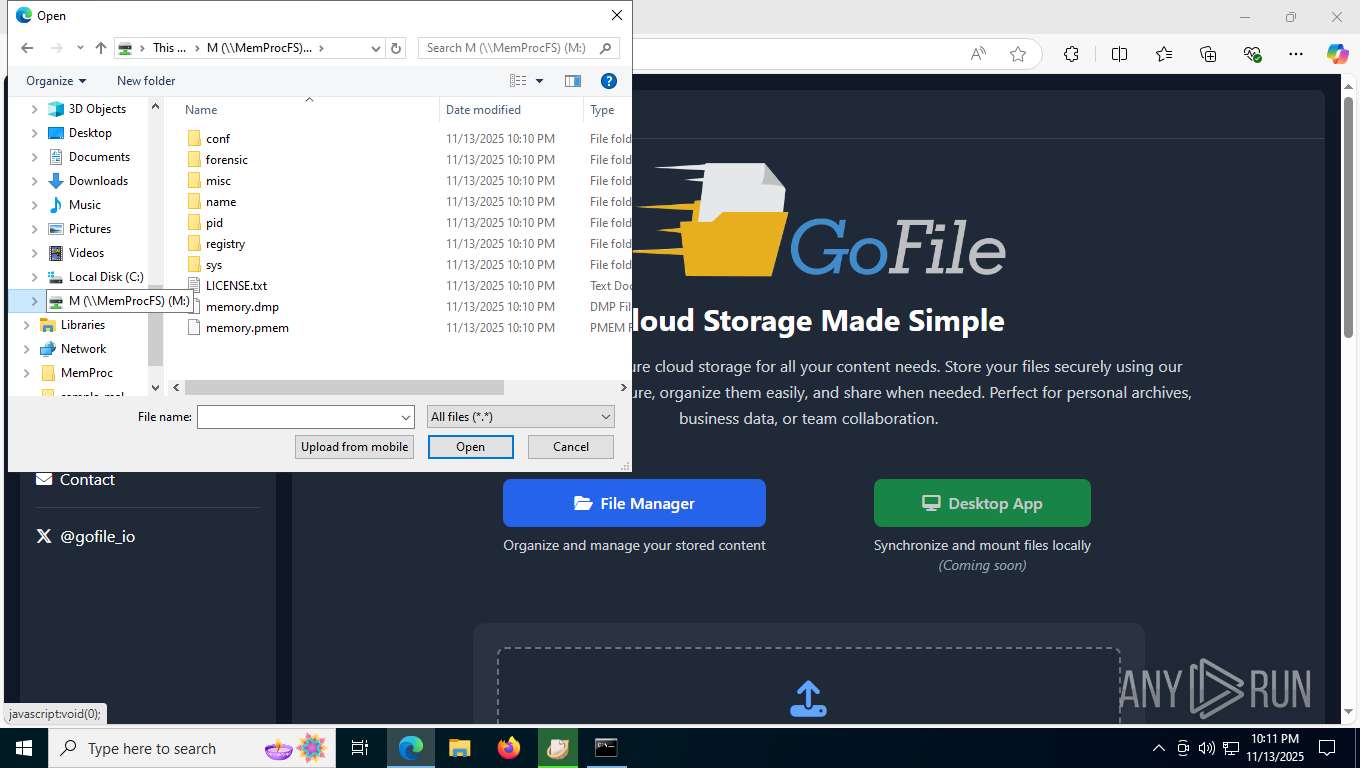
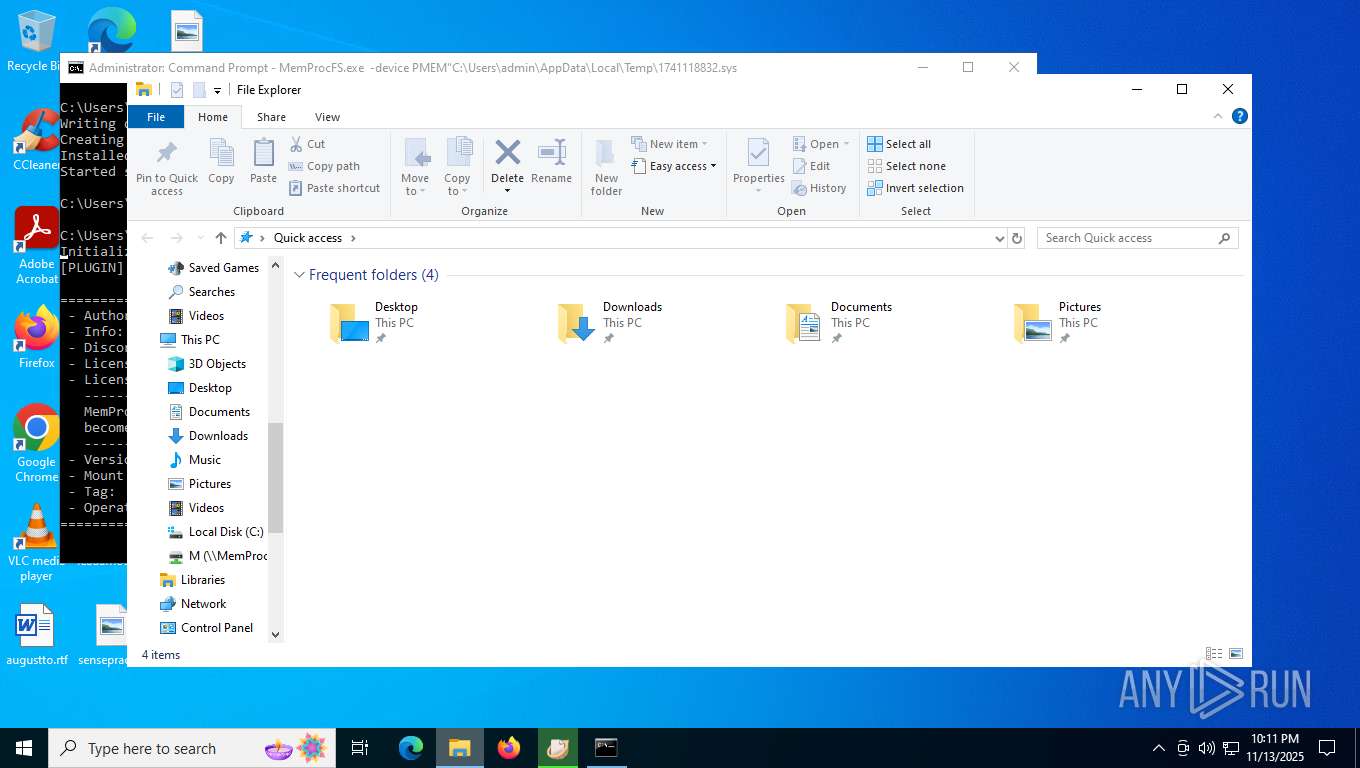
| 1252 | MemProcFS.exe -device PMEM"C:\Users\admin\AppData\Local\Temp\1741118832.sys | C:\Users\admin\Desktop\MemProc\MemProcFS.exe | cmd.exe | ||||||||||||
User: admin Integrity Level: HIGH Description: MemProcFS Version: 5.16.6.220 Modules
| |||||||||||||||
| 1284 | "C:\WINDOWS\system32\cmd.exe" | C:\Windows\System32\cmd.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2052 | "C:\Program Files\Dokan\Dokan Library-2.3.1\dokanctl.exe" /i a | C:\Program Files\Dokan\Dokan Library-2.3.1\dokanctl.exe | — | msiexec.exe | |||||||||||
User: SYSTEM Integrity Level: SYSTEM Exit code: 0 Modules
| |||||||||||||||
| 2188 | "C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe" --profile-directory=Default | C:\Program Files (x86)\Microsoft\Edge\Application\msedge.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft Edge Exit code: 0 Version: 133.0.3065.92 Modules
| |||||||||||||||
| 2388 | C:\Windows\syswow64\MsiExec.exe -Embedding FB831007D54832D248E29E4E2DA71641 E Global\MSI0000 | C:\Windows\SysWOW64\msiexec.exe | — | msiexec.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows® installer Exit code: 0 Version: 5.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
18 734
Read events
18 321
Write events
378
Delete events
35
Modification events
| (PID) Process: | (7256) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (7256) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
| (PID) Process: | (7256) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 3 |
Value: C:\Users\admin\Desktop\preferences.zip | |||
| (PID) Process: | (7256) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 2 |
Value: C:\Users\admin\Desktop\chromium_ext.zip | |||
| (PID) Process: | (7256) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 1 |
Value: C:\Users\admin\Desktop\omni_23_10_2024_.zip | |||
| (PID) Process: | (7256) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\sample_mal.zip | |||
| (PID) Process: | (7256) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (7256) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (7256) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (7256) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
Executable files
101
Suspicious files
630
Text files
186
Unknown types
2
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 7256 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa7256.41224\sample_mal\021a02dbe5a2258713659732552c3bbbb243c2ca1c07b18b2c46b47d4d40bbed.ps1 | — | |
MD5:— | SHA256:— | |||
| 7256 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa7256.41224\sample_mal\5b06edde6e27affef207ab14cca036946d5692fc9734e6d06175eb5942788a47.js | — | |
MD5:— | SHA256:— | |||
| 7256 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa7256.41224\sample_mal\2a93a3dd84f04f745620b491ccece930df4157037f710bac9020f1e7ca908ca1.bat | text | |
MD5:92F951511352307D262E52366BF9E7AB | SHA256:2A93A3DD84F04F745620B491CCECE930DF4157037F710BAC9020F1E7CA908CA1 | |||
| 7256 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa7256.41224\sample_mal\ac4928b95e1d016fa8941da5e0840870c97987a154d70c5ae0124055ffa07196.js | binary | |
MD5:500D2688ACB35207EC25816A3BB4E765 | SHA256:AC4928B95E1D016FA8941DA5E0840870C97987A154D70C5AE0124055FFA07196 | |||
| 7256 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa7256.41224\sample_mal\4efe3ebdbf79630bda1a3f0280d637613f9fd03f65773a9fa1d1fca183a61590.docx | binary | |
MD5:F96B5024B5C1752B6E169729C462B533 | SHA256:4EFE3EBDBF79630BDA1A3F0280D637613F9FD03F65773A9FA1D1FCA183A61590 | |||
| 7256 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa7256.41224\sample_mal\6493cb811a2860dcb1c3b9abb41b627fe7c8e7eb7af3dbbbb21c0291e400b0b9.vbs | text | |
MD5:5A9348168DADB75E91D71B9ED2C8318B | SHA256:6493CB811A2860DCB1C3B9ABB41B627FE7C8E7EB7AF3DBBBB21C0291E400B0B9 | |||
| 7256 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa7256.41224\sample_mal\56b96f91313684e0a54fef61c1e6bae76b314de7ab3b365a22f6c4f3c61ef5ad.vbe | binary | |
MD5:AB1A62C8C690111A88417F8C09A08838 | SHA256:56B96F91313684E0A54FEF61C1E6BAE76B314DE7AB3B365A22F6C4F3C61EF5AD | |||
| 7256 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa7256.41224\sample_mal\69eb4fca412201039105d862d5f2bf12085d41cb18a93398afef0be8dfb9c229.doc | binary | |
MD5:701270F377771368084D8A07857F3420 | SHA256:69EB4FCA412201039105D862D5F2BF12085D41CB18A93398AFEF0BE8DFB9C229 | |||
| 7256 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa7256.41224\sample_mal\d00af15162f27272d71c5be5617669c113426922dea30639b21166bd74e2849b.bat | text | |
MD5:8DE41A646DBE89D6427C9F7D9B0D4E85 | SHA256:D00AF15162F27272D71C5BE5617669C113426922DEA30639B21166BD74E2849B | |||
| 7256 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa7256.41224\sample_mal\70239684f01e37692087c05f6f355daae3bdcdbc4bfa2fcb786dbf8ddf1d2966.doc | binary | |
MD5:D6E7A65A344935376EB8AADC3A294DEB | SHA256:70239684F01E37692087C05F6F355DAAE3BDCDBC4BFA2FCB786DBF8DDF1D2966 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
12
TCP/UDP connections
131
DNS requests
93
Threats
25
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2016 | svchost.exe | GET | 200 | 184.30.131.245:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | US | binary | 471 b | whitelisted |
5596 | MoUsoCoreWorker.exe | GET | 200 | 2.16.168.124:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | RU | binary | 825 b | whitelisted |
7912 | SIHClient.exe | GET | 200 | 104.79.89.142:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20Update%20Signing%20CA%202.3.crl | DE | binary | 813 b | whitelisted |
7912 | SIHClient.exe | GET | 200 | 104.79.89.142:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20Time-Stamp%20PCA%202010(1).crl | DE | binary | 814 b | whitelisted |
7912 | SIHClient.exe | GET | 200 | 104.79.89.142:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Signing%20CA%202.3.crl | DE | binary | 401 b | whitelisted |
7912 | SIHClient.exe | GET | 200 | 104.79.89.142:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20Update%20Signing%20CA%202.2.crl | DE | binary | 813 b | whitelisted |
7912 | SIHClient.exe | GET | 200 | 104.79.89.142:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Signing%20CA%202.2.crl | DE | binary | 402 b | whitelisted |
1144 | msiexec.exe | GET | 200 | 2.19.120.91:80 | http://cevcsca2021.ocsp-certum.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBR2rKuShFxBxX%2BVZ%2F8jiOwbsyptXQQUrFfKCBbcP8UxHApN2%2Fvx3pknLTQCECXKBE7TioV4cMIHvdBfYTg%3D | DE | binary | 2.25 Kb | whitelisted |
1144 | msiexec.exe | GET | 200 | 23.11.206.115:80 | http://subca.ocsp-certum.com/MFIwUDBOMEwwSjAJBgUrDgMCGgUABBRIH1V64SBkA%2BzJQVQ6VFBAcvLB3wQUtqFUOQLDoD%2BOirz61PgcptE6Dv0CEQC78My1t7gx%2FSGuMneK5AyJ | DE | binary | 1.80 Kb | whitelisted |
1252 | MemProcFS.exe | GET | 200 | 184.30.131.245:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEA77flR%2B3w%2FxBpruV2lte6A%3D | US | binary | 471 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
6456 | svchost.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
5596 | MoUsoCoreWorker.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
2016 | svchost.exe | 20.190.160.64:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
5192 | RUXIMICS.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
2016 | svchost.exe | 20.190.160.131:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
2016 | svchost.exe | 184.30.131.245:80 | ocsp.digicert.com | AKAMAI-AS | US | whitelisted |
5596 | MoUsoCoreWorker.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
5596 | MoUsoCoreWorker.exe | 2.16.168.124:80 | crl.microsoft.com | Akamai International B.V. | RU | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
login.live.com |
| whitelisted |
google.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
slscr.update.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
fe3cr.delivery.mp.microsoft.com |
| whitelisted |
www.bing.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
— | — | Unknown Traffic | ET USER_AGENTS Microsoft Dr Watson User-Agent (MSDW) |
2276 | svchost.exe | Not Suspicious Traffic | INFO [ANY.RUN] Azure Blob Storage (.blob .core .windows .net) |
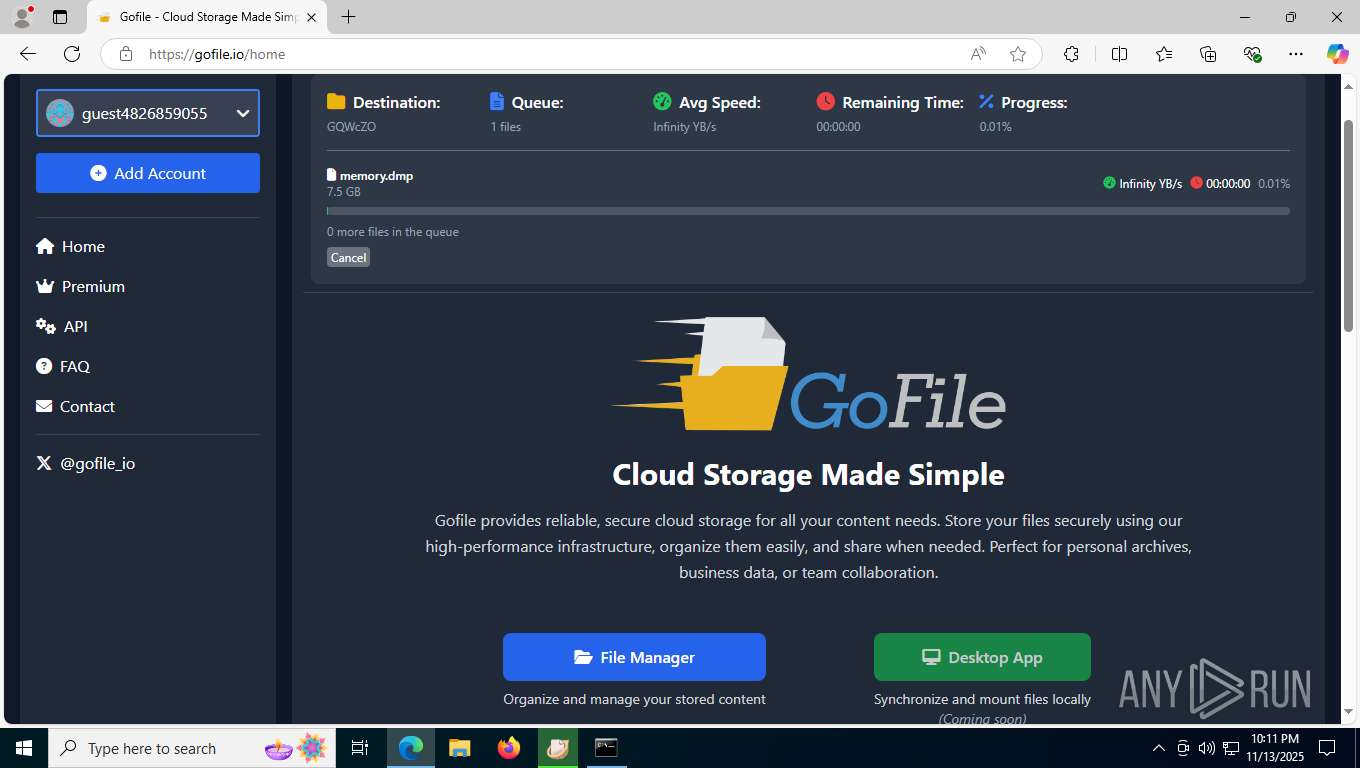
4360 | msedge.exe | Potentially Bad Traffic | ET FILE_SHARING Online File Storage Domain in DNS Lookup (gofile .io) |
4360 | msedge.exe | Potentially Bad Traffic | ET FILE_SHARING Online File Storage Domain in DNS Lookup (gofile .io) |
4360 | msedge.exe | Potentially Bad Traffic | ET FILE_SHARING Online File Storage Domain in DNS Lookup (gofile .io) |
4360 | msedge.exe | Potentially Bad Traffic | ET FILE_SHARING Online File Storage Domain in DNS Lookup (gofile .io) |
4360 | msedge.exe | Misc activity | ET FILE_SHARING File Sharing Related Domain in TLS SNI (gofile .io) |
4360 | msedge.exe | Potentially Bad Traffic | ET FILE_SHARING Online File Storage Domain in DNS Lookup (gofile .io) |
4360 | msedge.exe | Potentially Bad Traffic | ET FILE_SHARING Online File Storage Domain in DNS Lookup (gofile .io) |
4360 | msedge.exe | Misc activity | ET FILE_SHARING File Sharing Related Domain in TLS SNI (gofile .io) |
Process | Message |
|---|---|
msedge.exe | WNNC_ENUMERATION
|
msedge.exe | WNNC_NET_TYPE
|
msedge.exe | NPOpenEnum: dwScope 0x00000001, dwType 0x00000001, dwUsage 0x00000000, lpNetResource 0000000000000000
|
msedge.exe | NPEnumResource SesstionID: 4294967295
|
msedge.exe | WNC_CONNECTION
|
msedge.exe | NPGetCaps 13
|
msedge.exe | NPOpenEnum: pCtx 000001B4882ABA80
|
msedge.exe | NPEnumResource: *lpcCount 0xffffffff, *lpBufferSize 0x4000, pCtx->index 0
|
msedge.exe | NPEnumResource: RESOURCE_CONNECTED
|
msedge.exe | NPEnumResource: lpRemoteName: \\MemProcFS\M
|