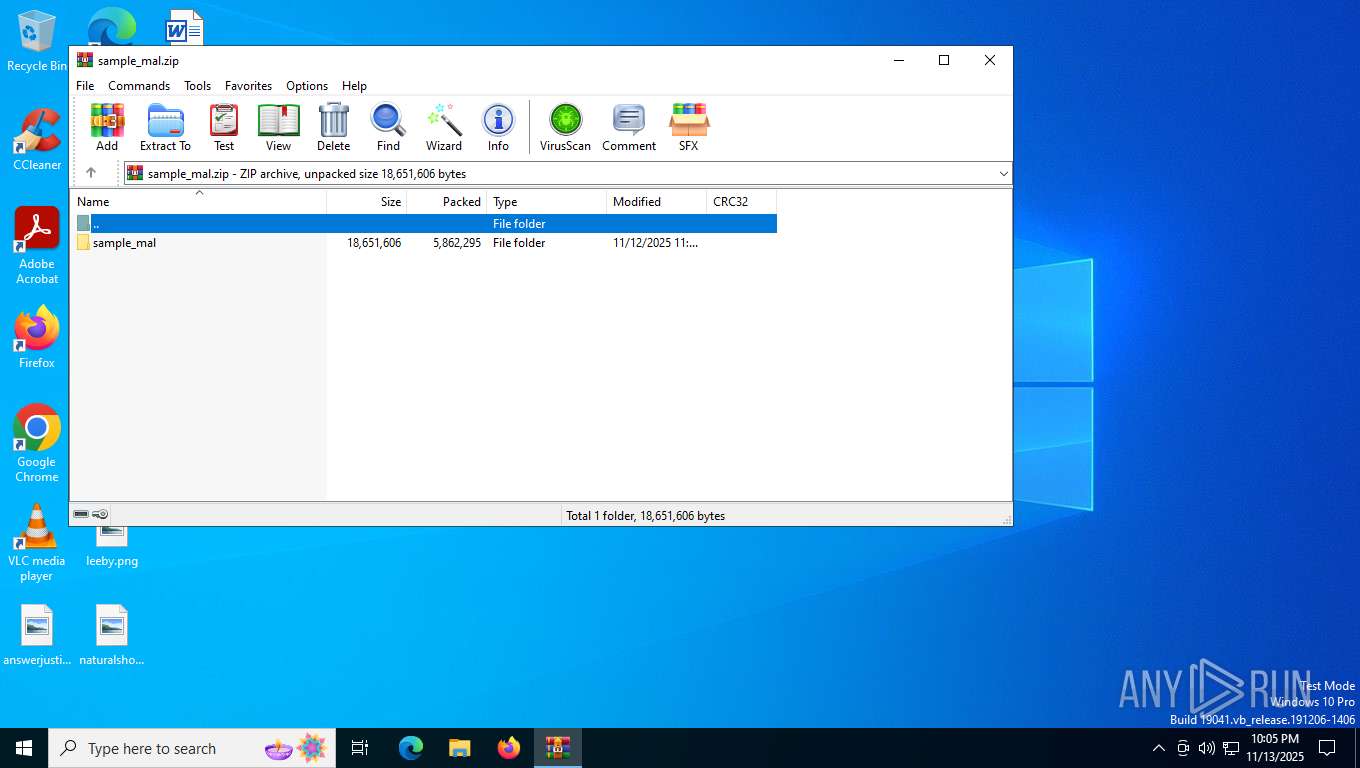
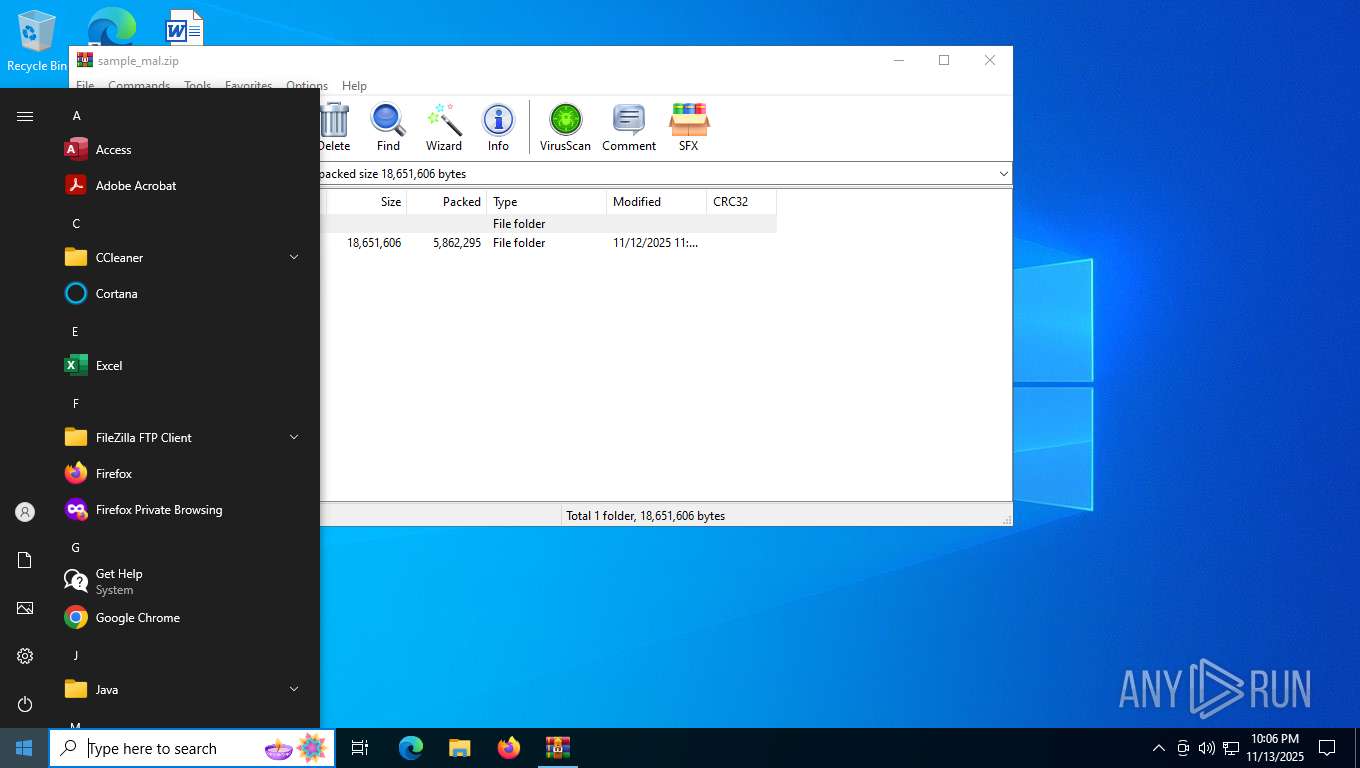
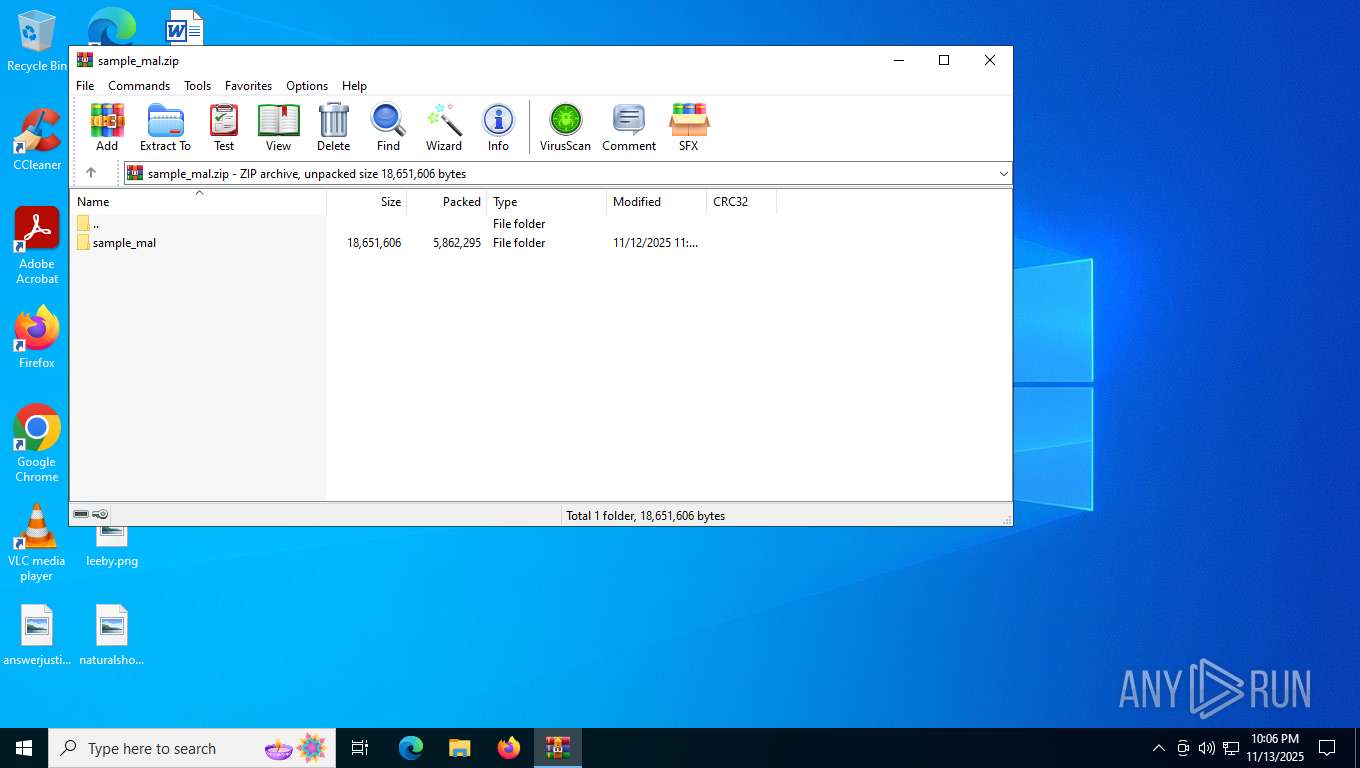
| File name: | sample_mal.zip |
| Full analysis: | https://app.any.run/tasks/4b3eb9b4-5307-432e-8f8b-4d766f42aed2 |
| Verdict: | Malicious activity |
| Analysis date: | November 13, 2025, 22:05:47 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/zip |
| File info: | Zip archive data, at least v2.0 to extract, compression method=store |
| MD5: | 03792C225BC250A16121F9FD0B21D2F2 |
| SHA1: | 1967654EF076371173681376DD6AFC8DEB60223D |
| SHA256: | 64081D577943AD608EECC77103F50053D6BCC2E2A5BD4518F3D4C96DA00813B0 |
| SSDEEP: | 98304:yM0OoKXoqLPQoeFoz63m7rkleR3Nu7Ab6BLzXlZN4vKK2qT5ThjwLLkNXs4gY/kI:kJ6K1GB+O/D |
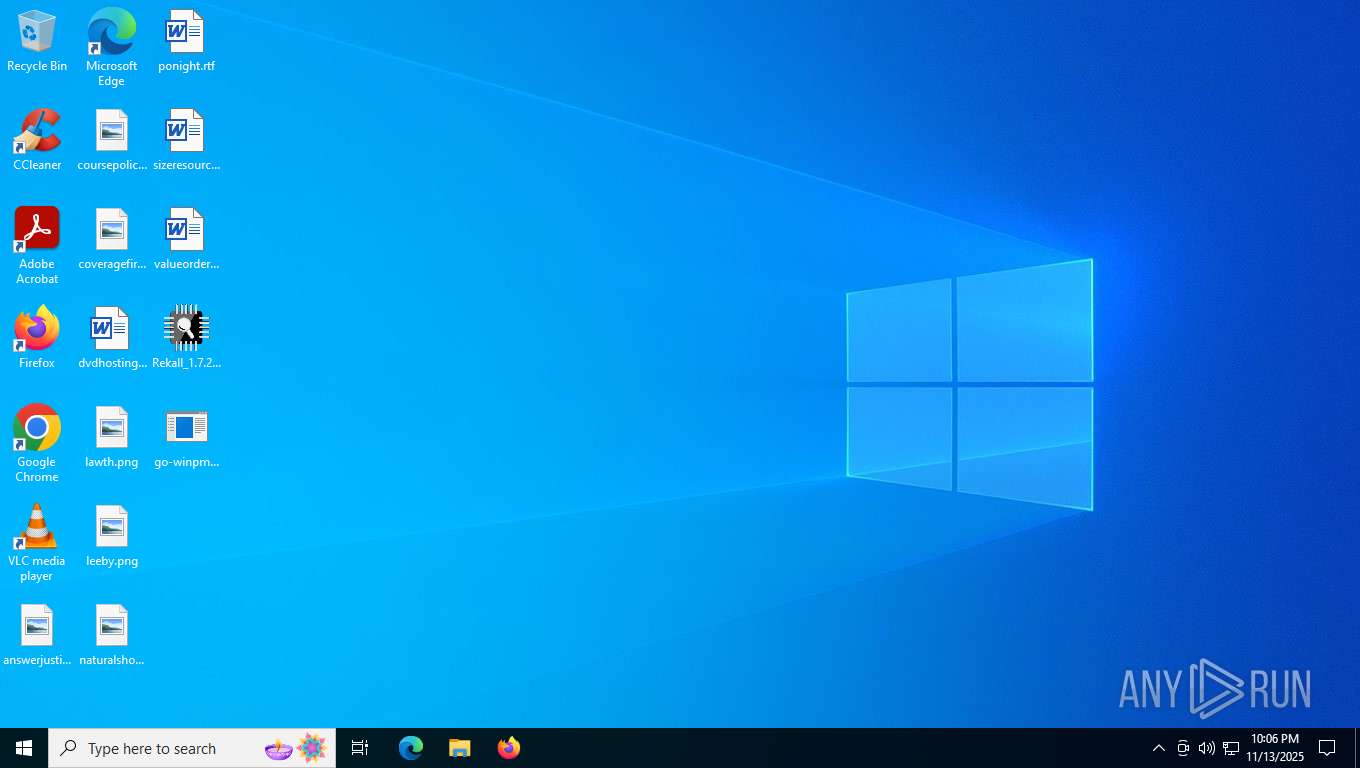
MALICIOUS
Generic archive extractor
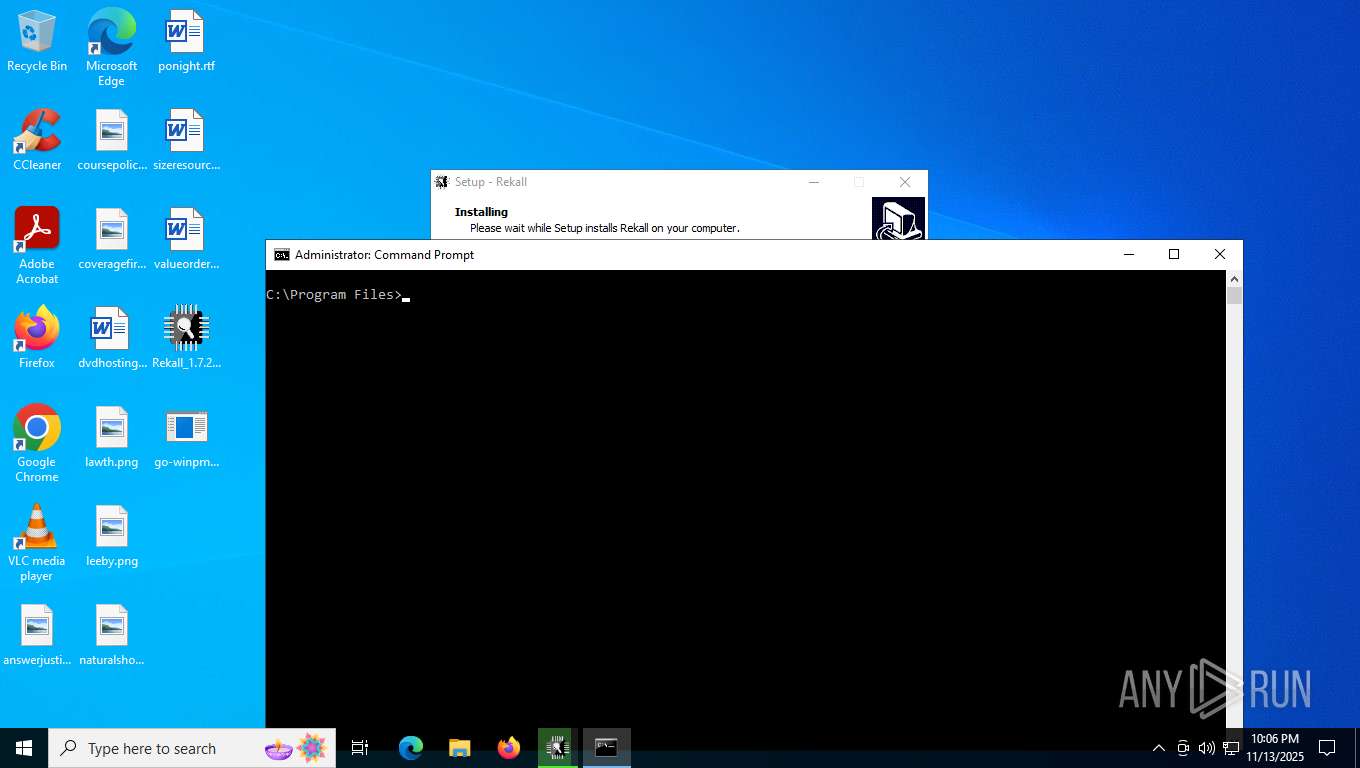
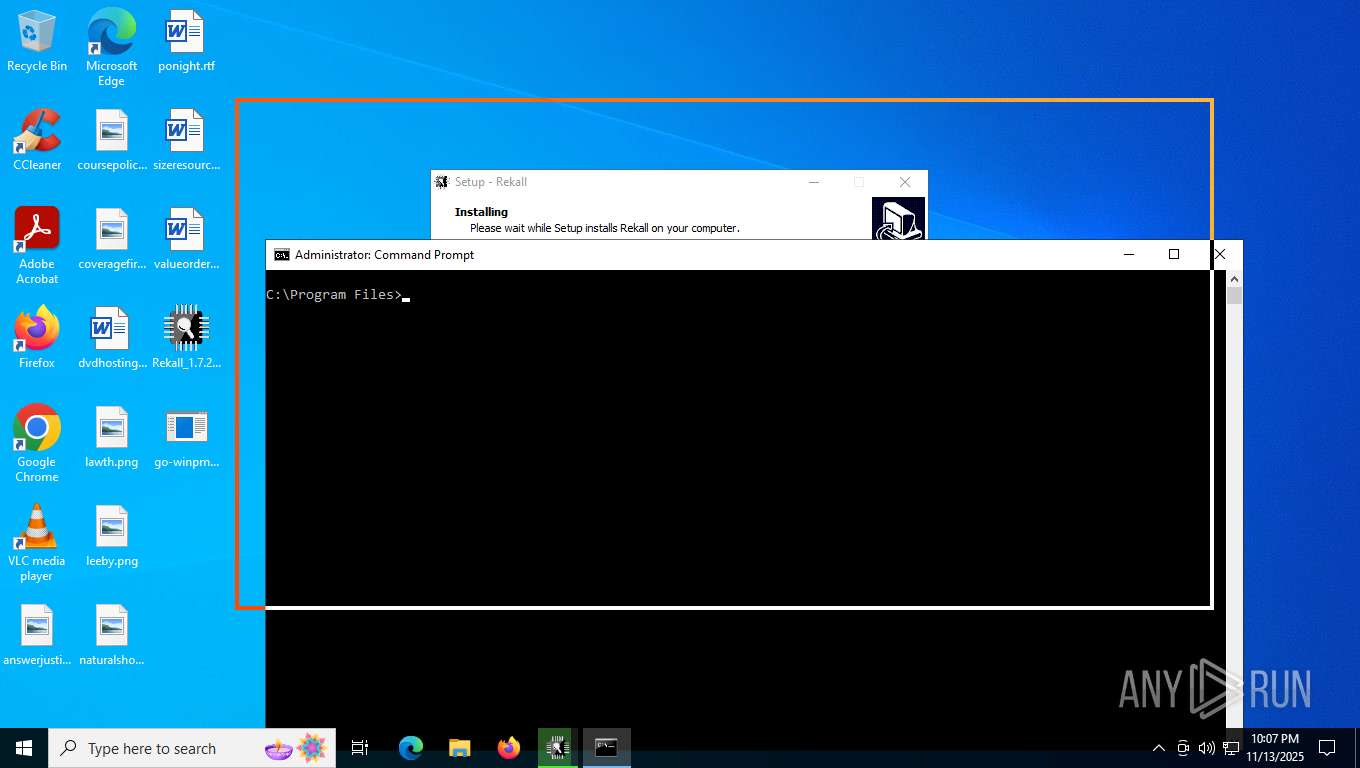
- WinRAR.exe (PID: 7348)
SUSPICIOUS
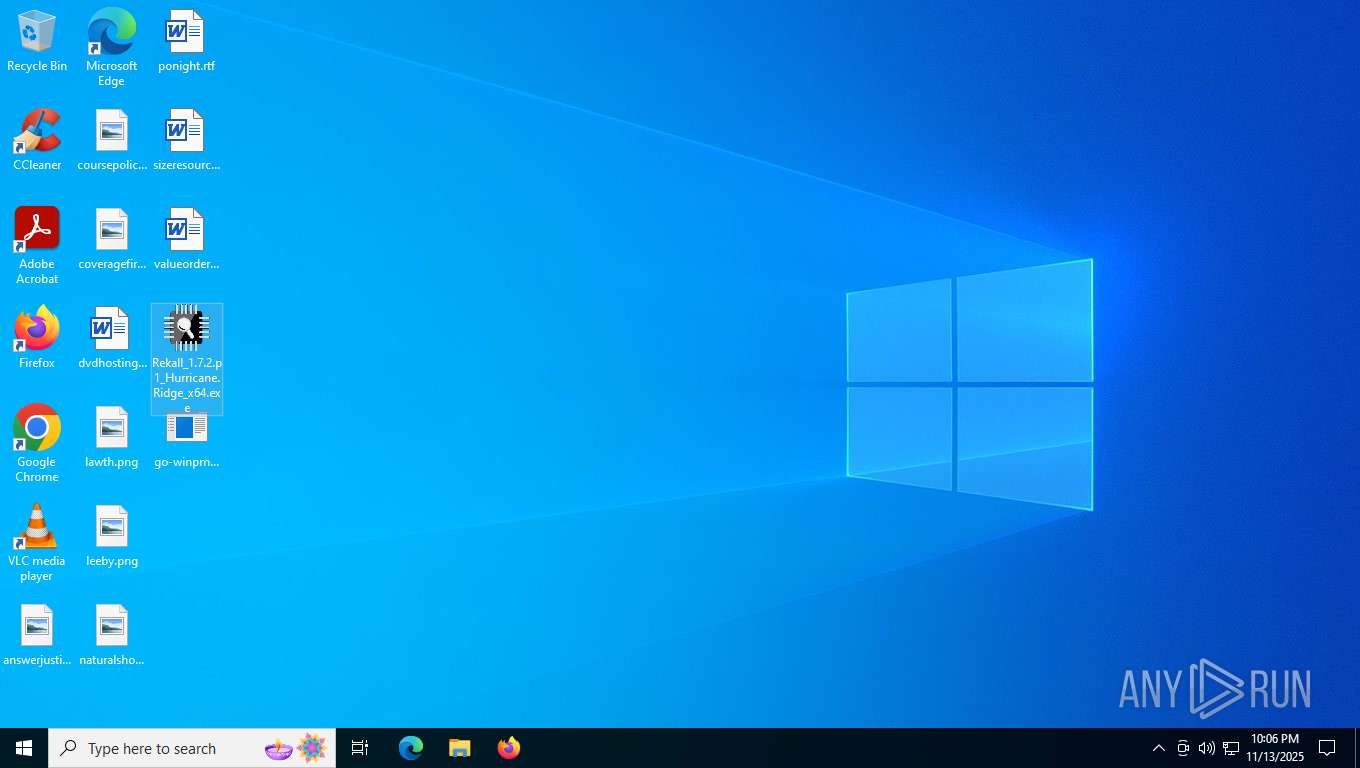
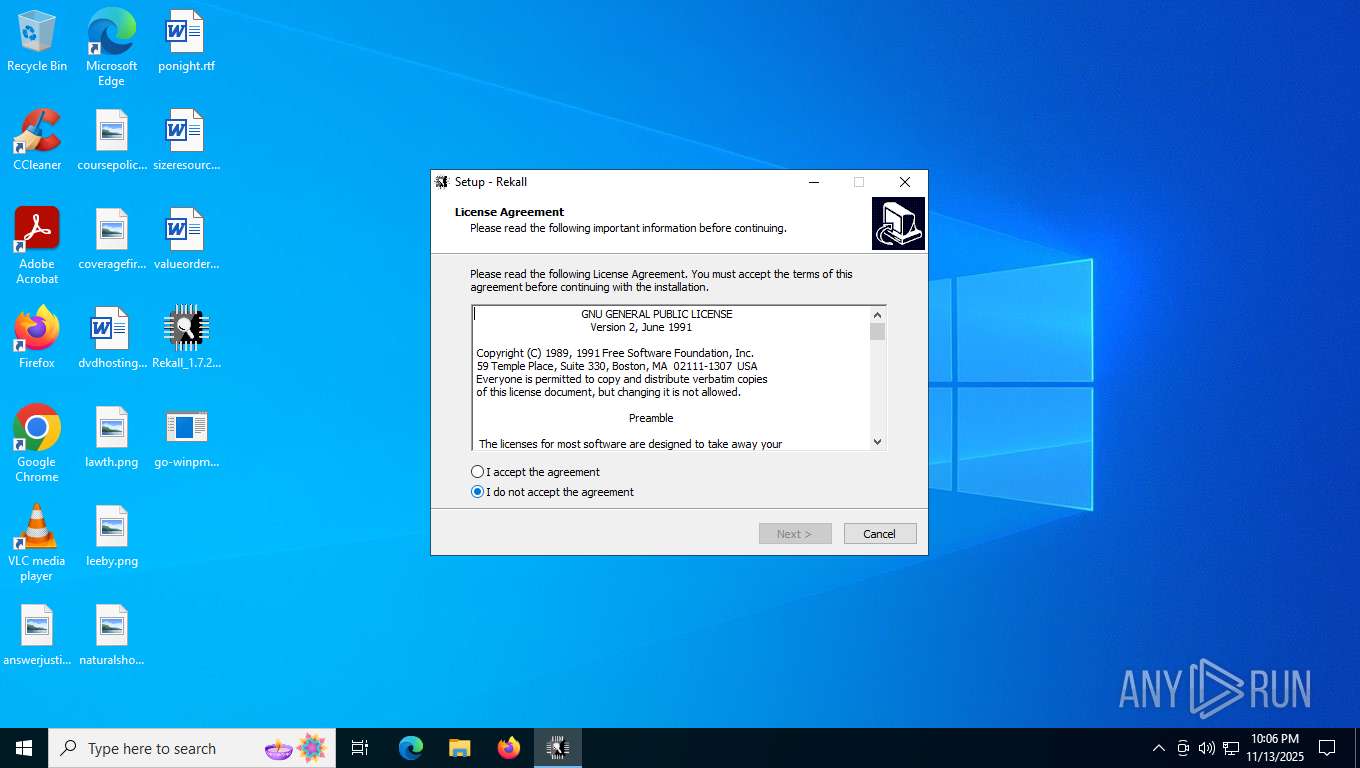
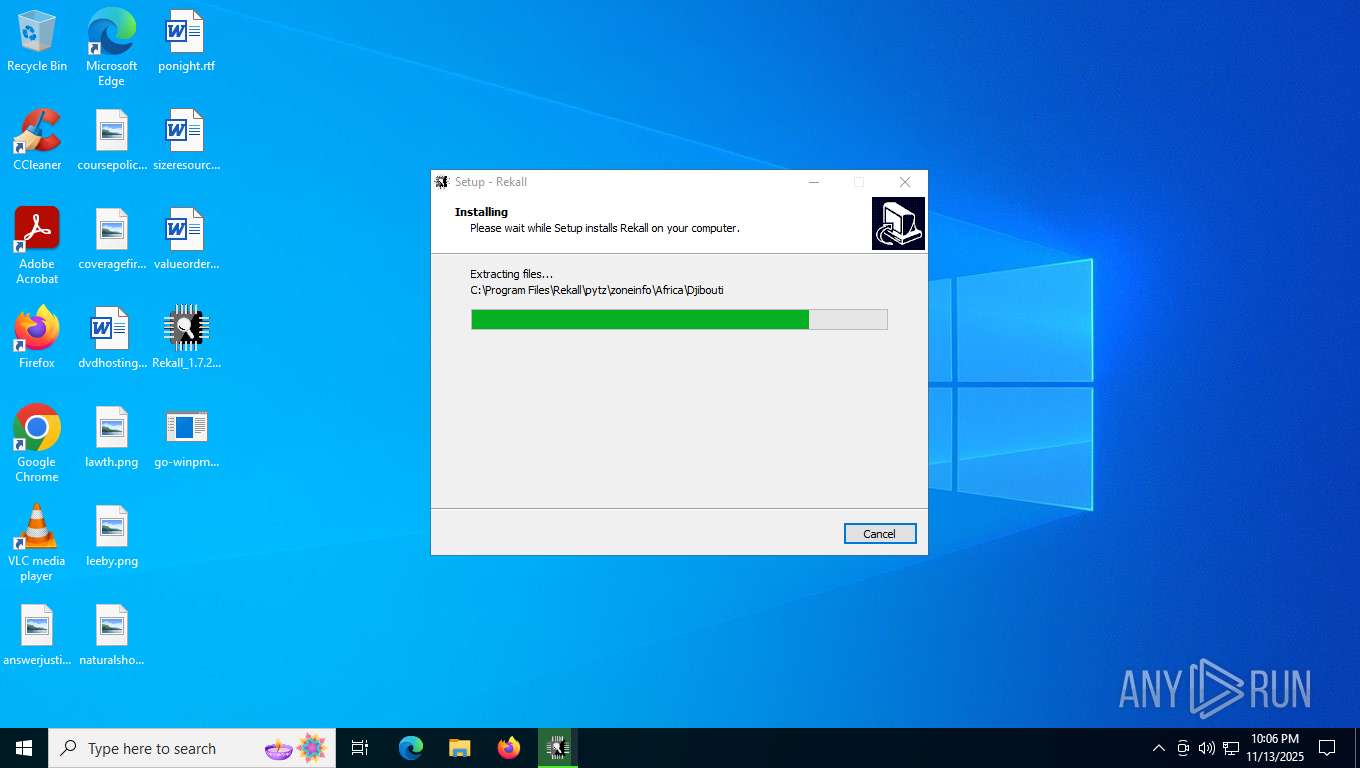
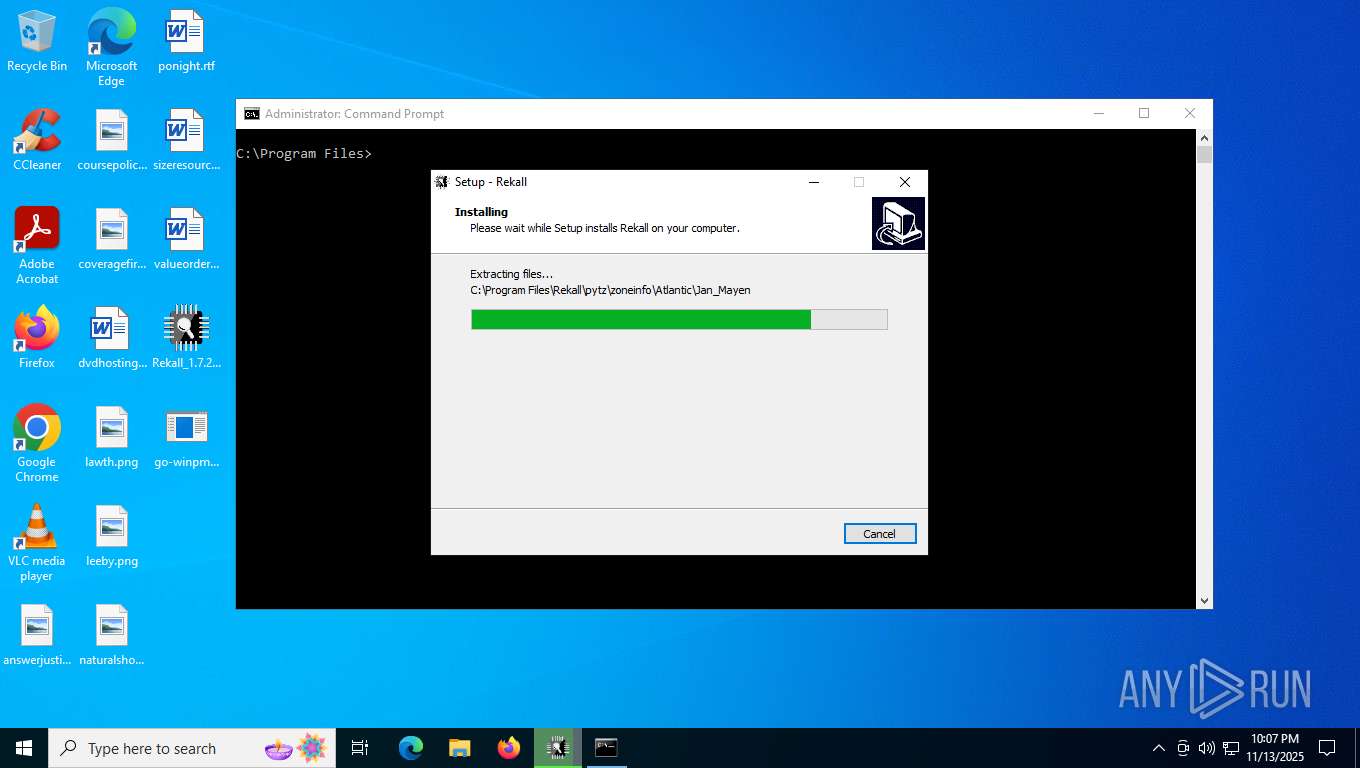
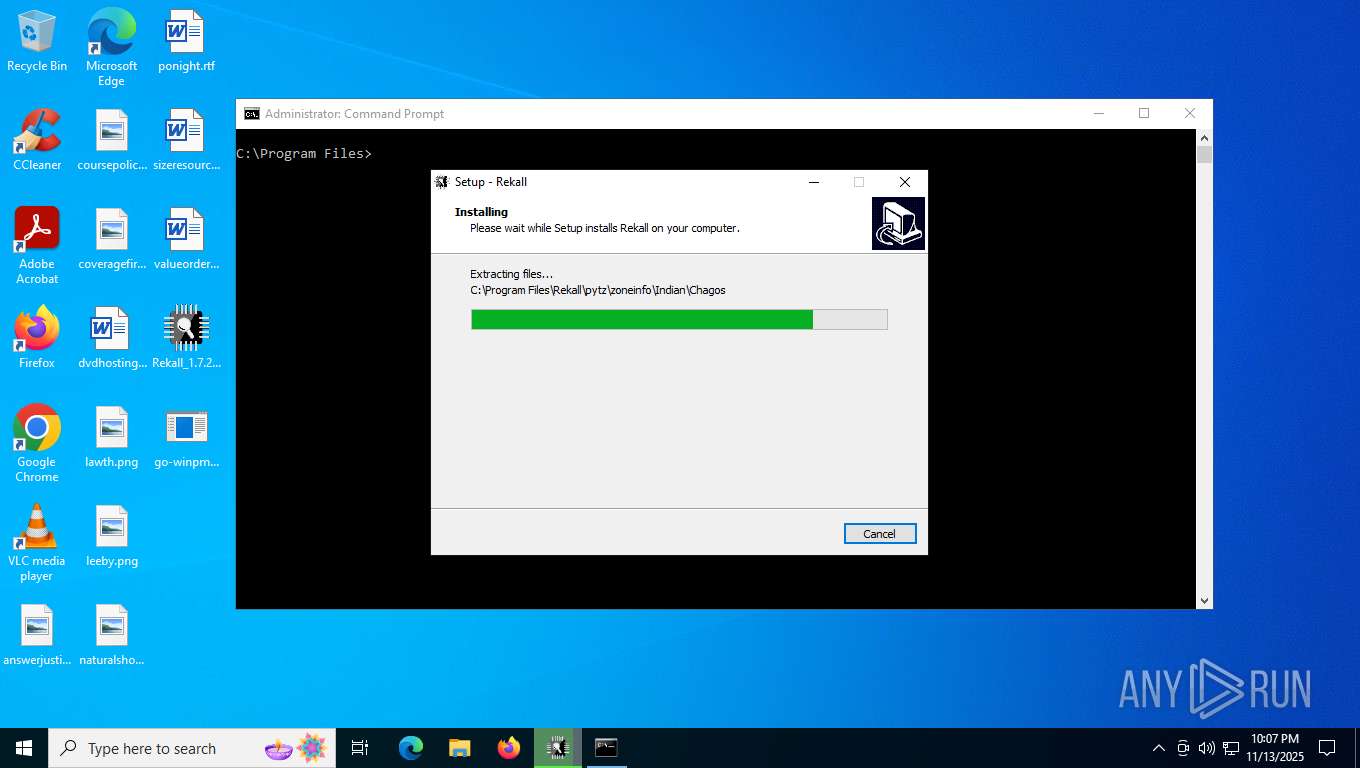
Executable content was dropped or overwritten
- Rekall_1.7.2.p1_Hurricane.Ridge_x64.exe (PID: 6212)
- Rekall_1.7.2.p1_Hurricane.Ridge_x64.exe (PID: 1308)
- Rekall_1.7.2.p1_Hurricane.Ridge_x64.tmp (PID: 2704)
- go-winpmem_amd64_1.0-rc2_signed.exe (PID: 6176)
Reads security settings of Internet Explorer
- Rekall_1.7.2.p1_Hurricane.Ridge_x64.tmp (PID: 2716)
Reads the Windows owner or organization settings
- Rekall_1.7.2.p1_Hurricane.Ridge_x64.tmp (PID: 2704)
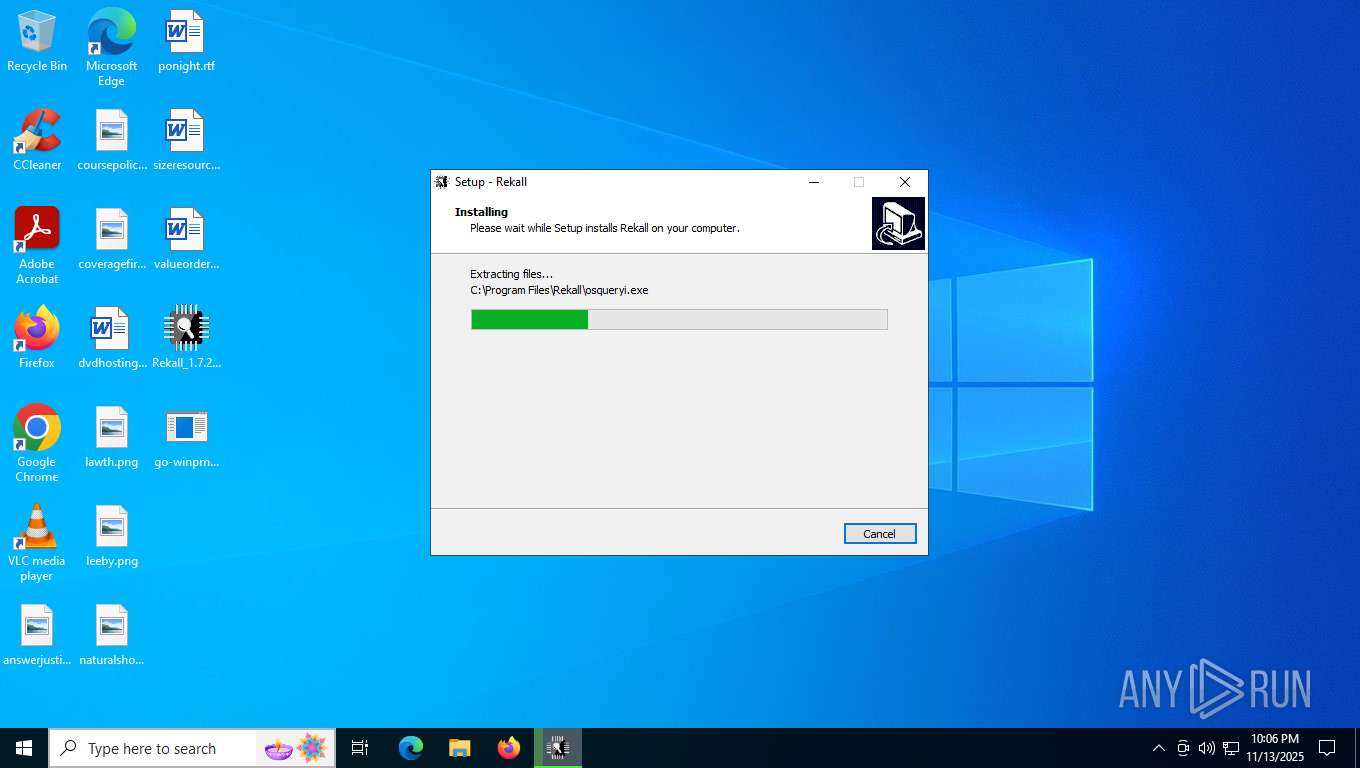
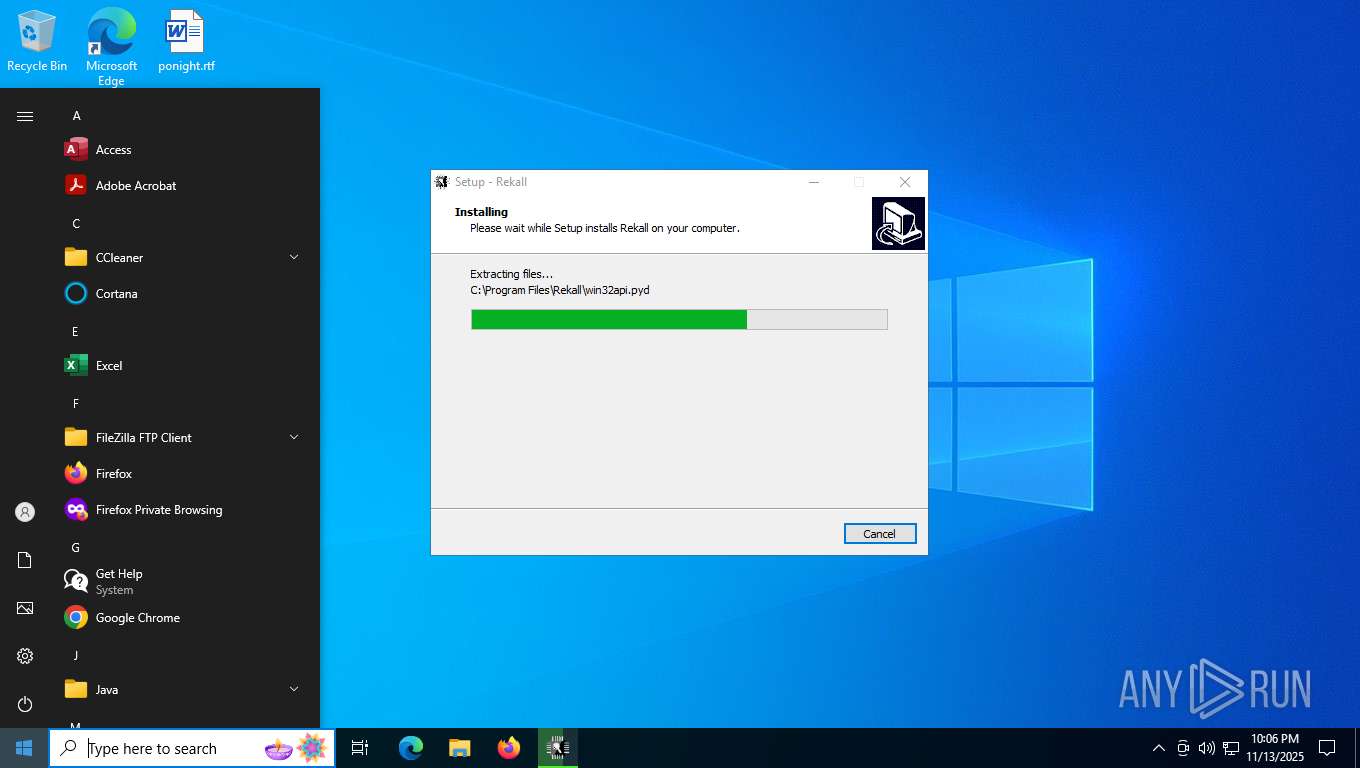
Process drops python dynamic module
- Rekall_1.7.2.p1_Hurricane.Ridge_x64.tmp (PID: 2704)
Process drops legitimate windows executable
- Rekall_1.7.2.p1_Hurricane.Ridge_x64.tmp (PID: 2704)
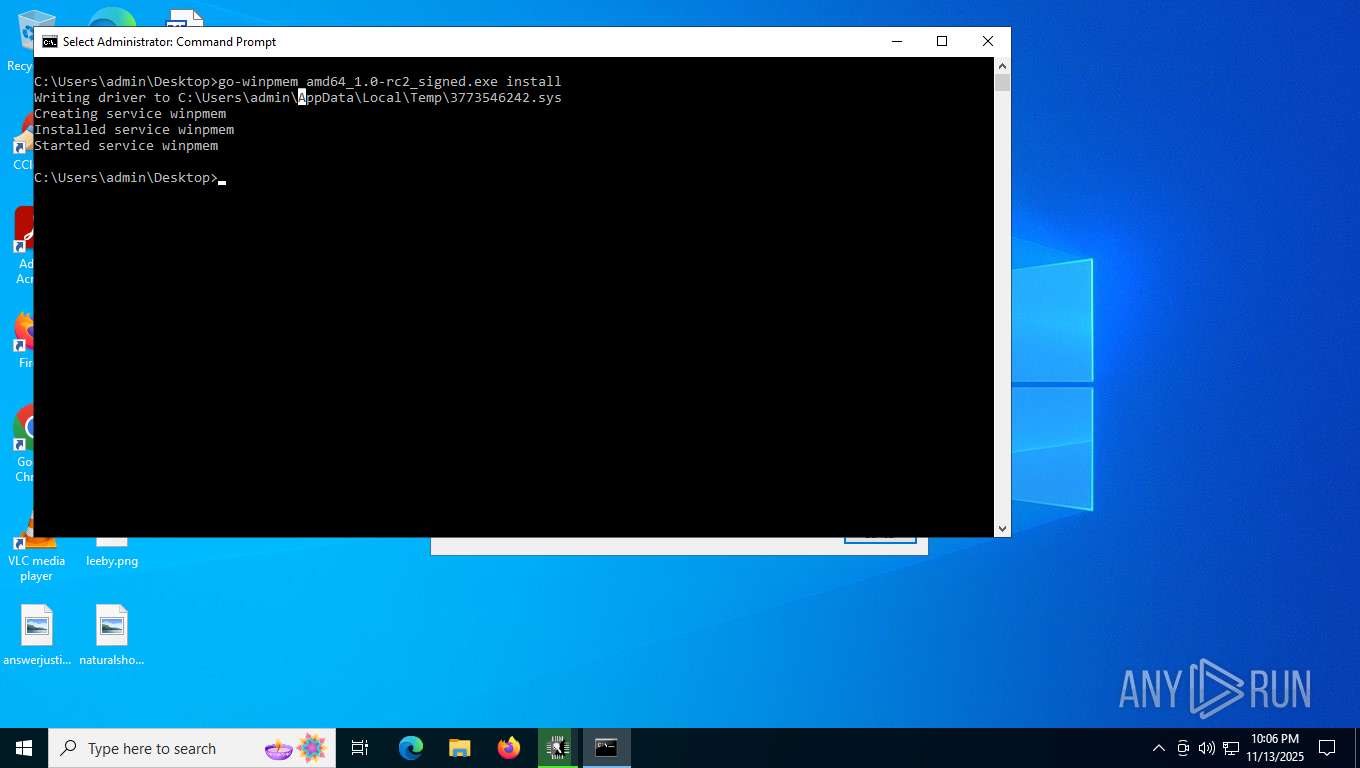
Drops a system driver (possible attempt to evade defenses)
- Rekall_1.7.2.p1_Hurricane.Ridge_x64.tmp (PID: 2704)
- go-winpmem_amd64_1.0-rc2_signed.exe (PID: 6176)
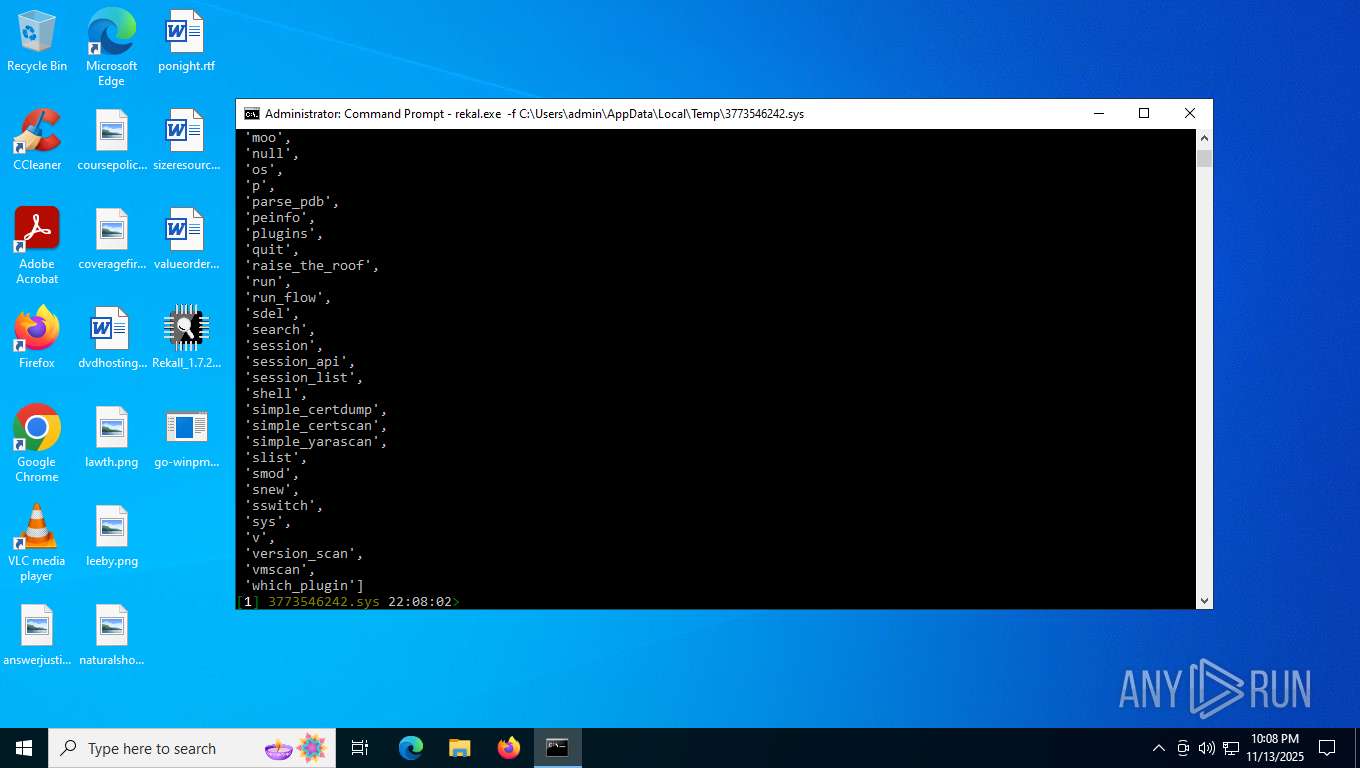
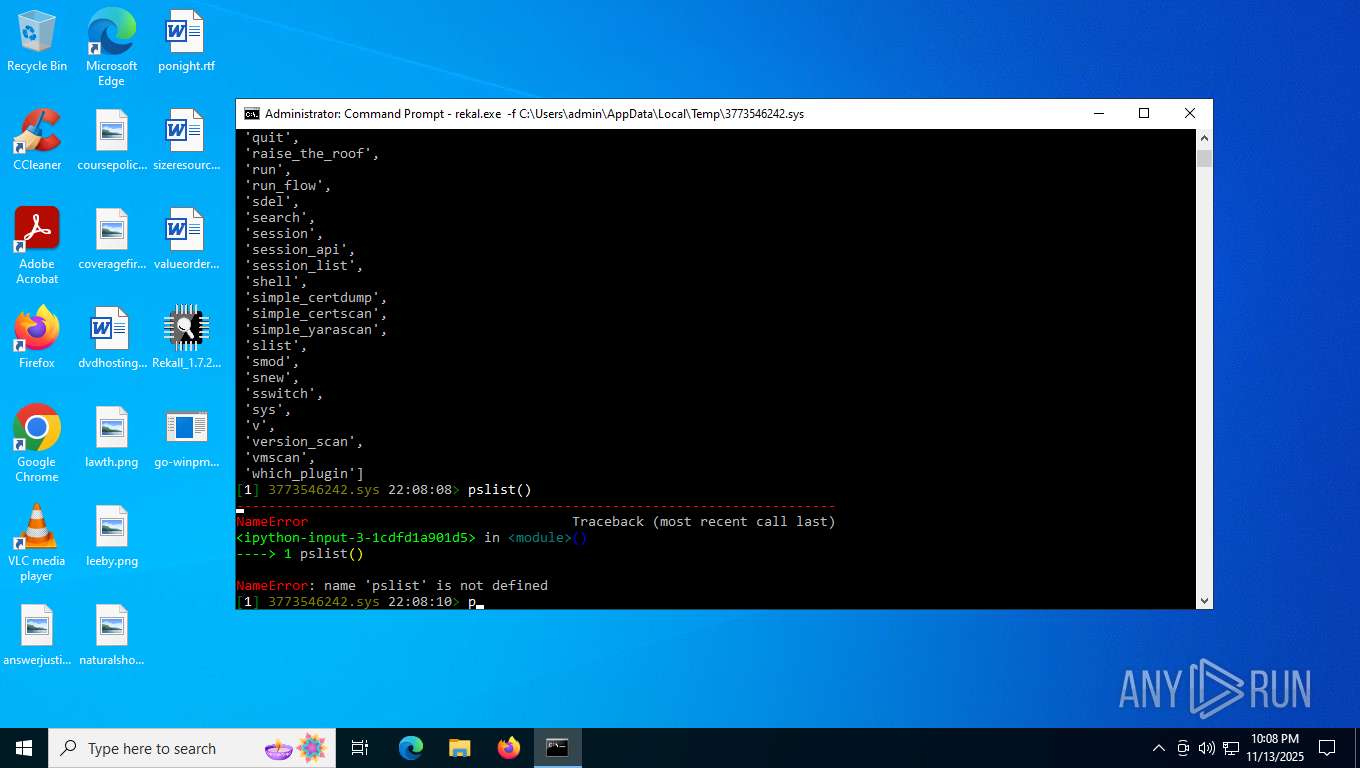
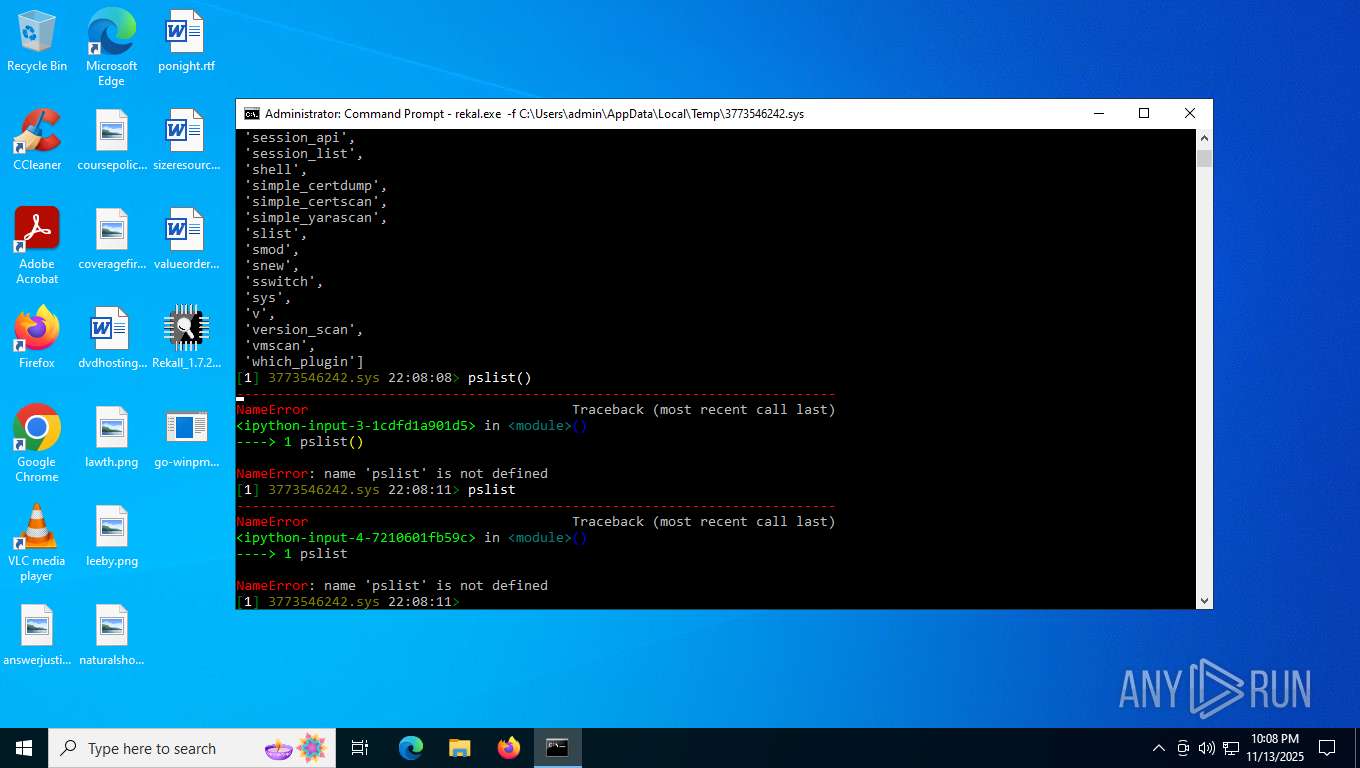
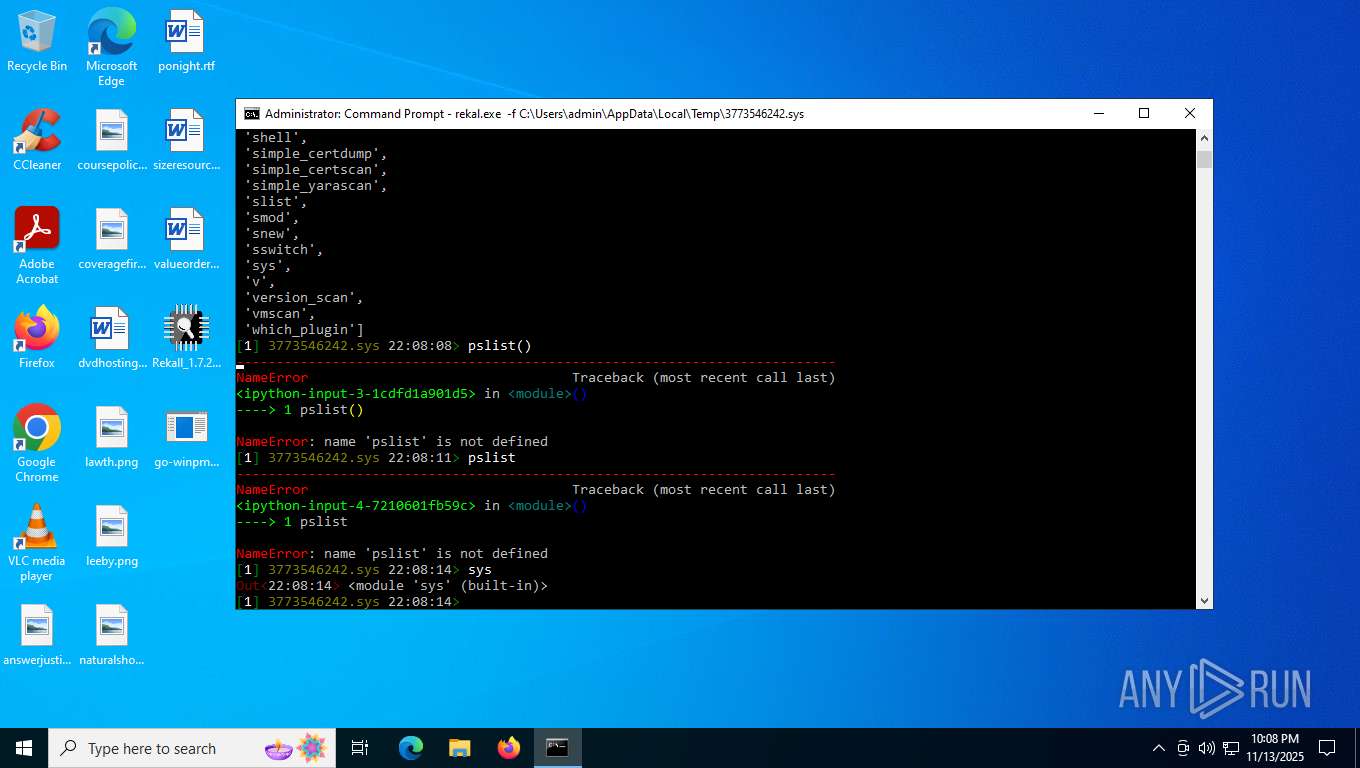
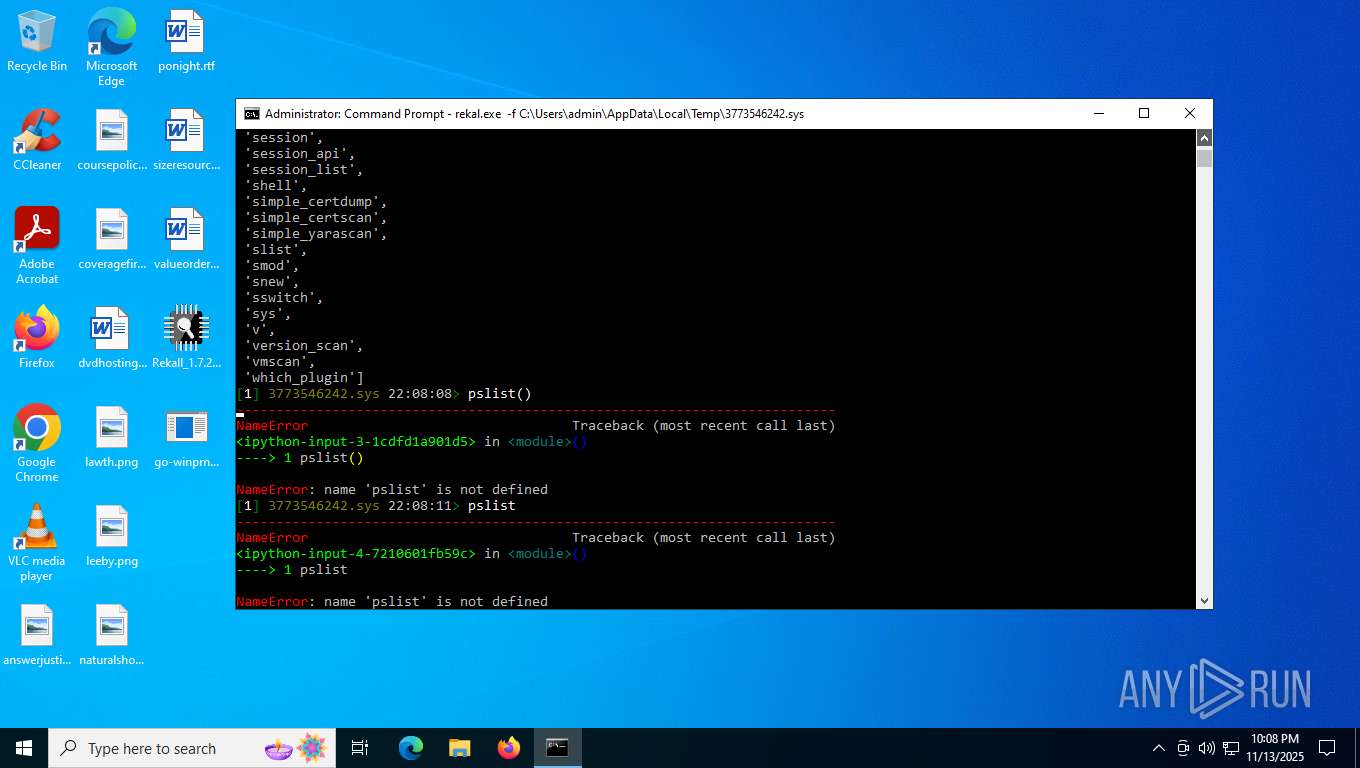
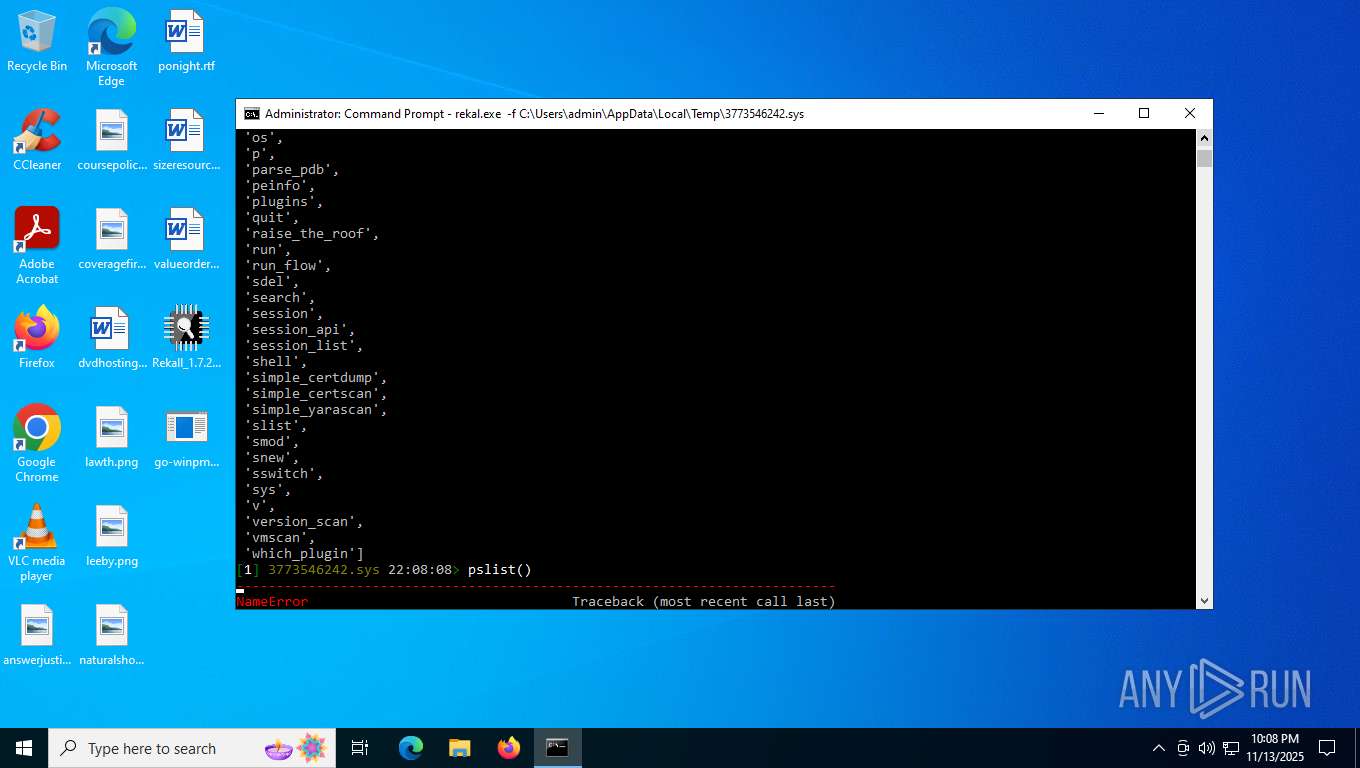
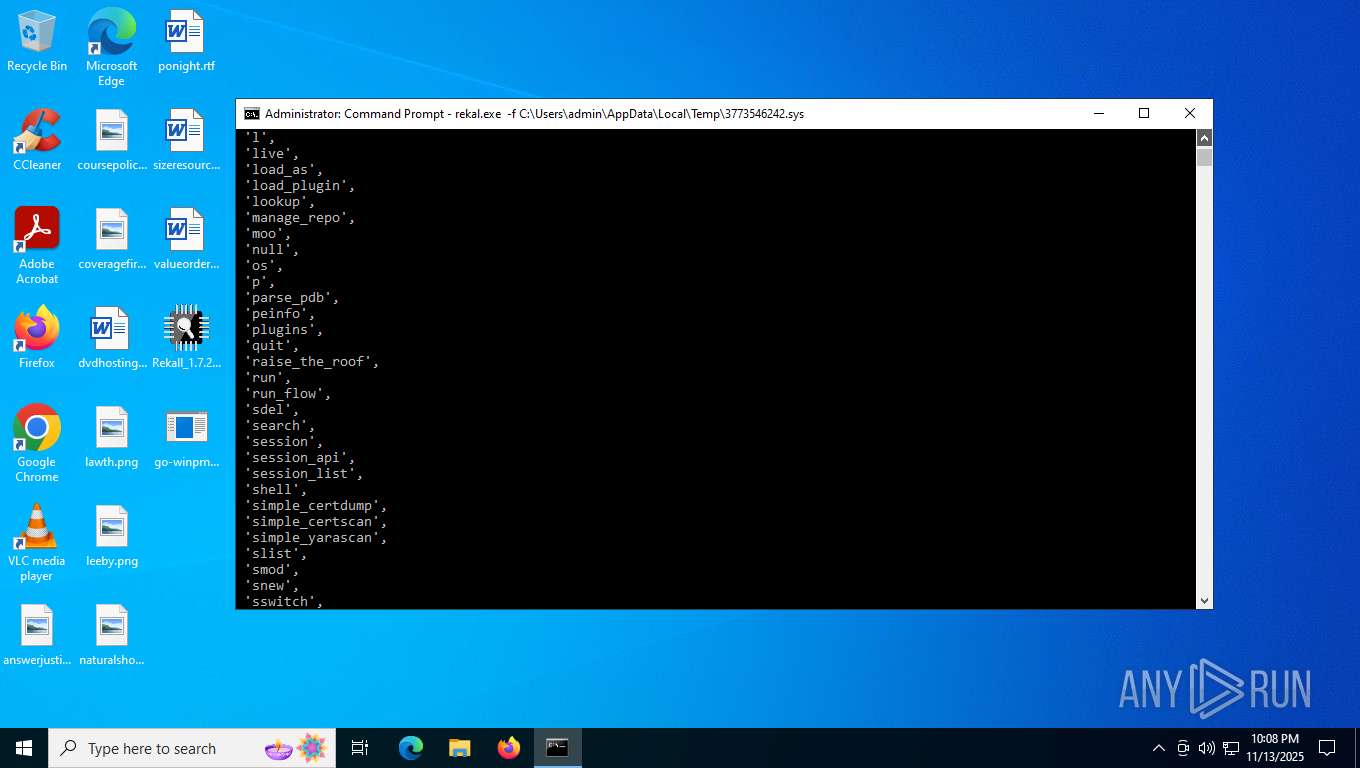
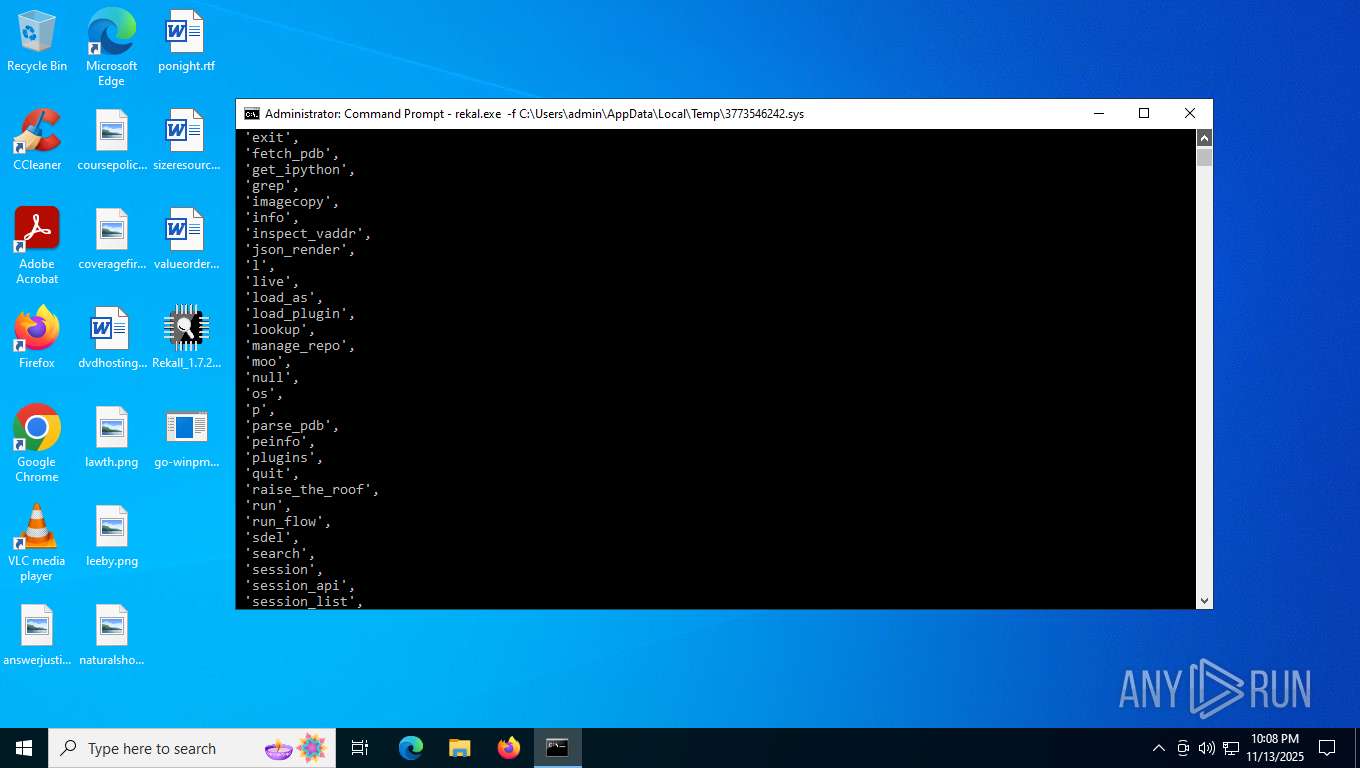
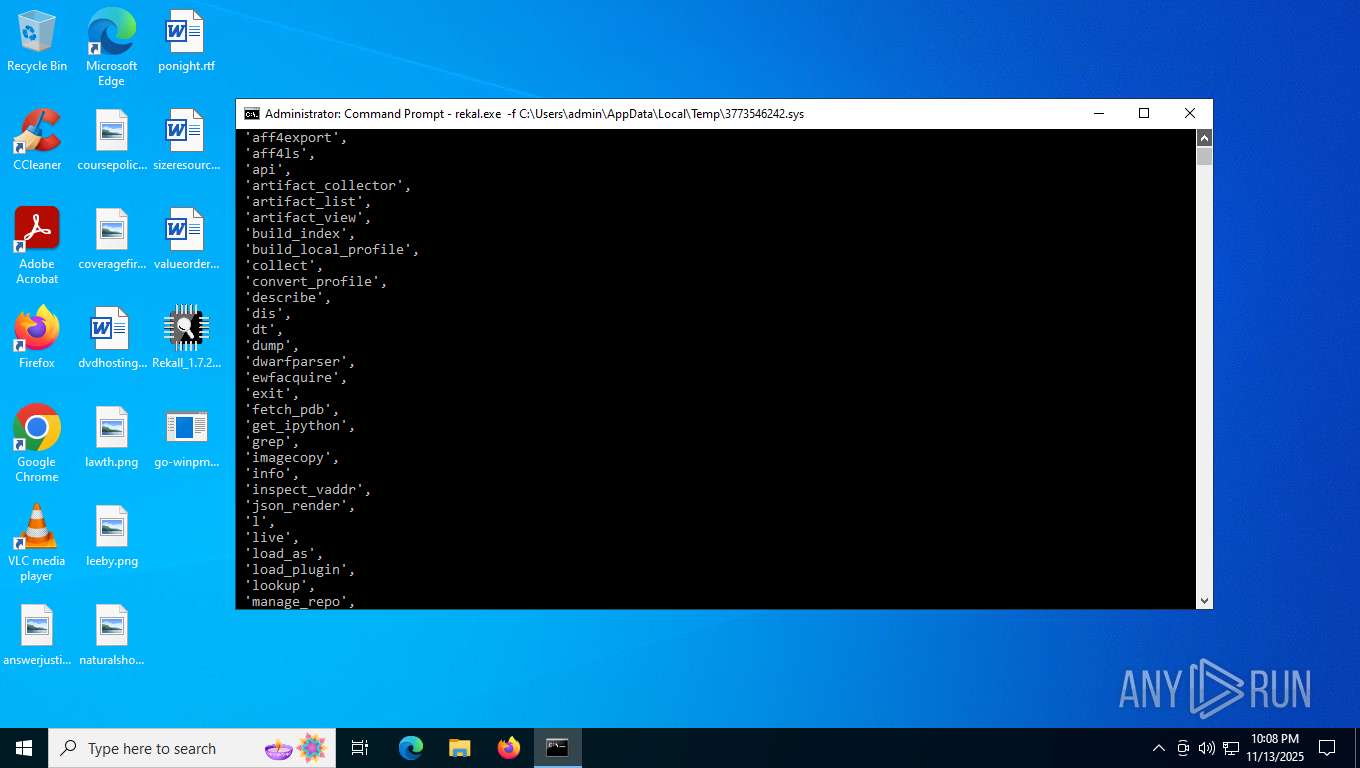
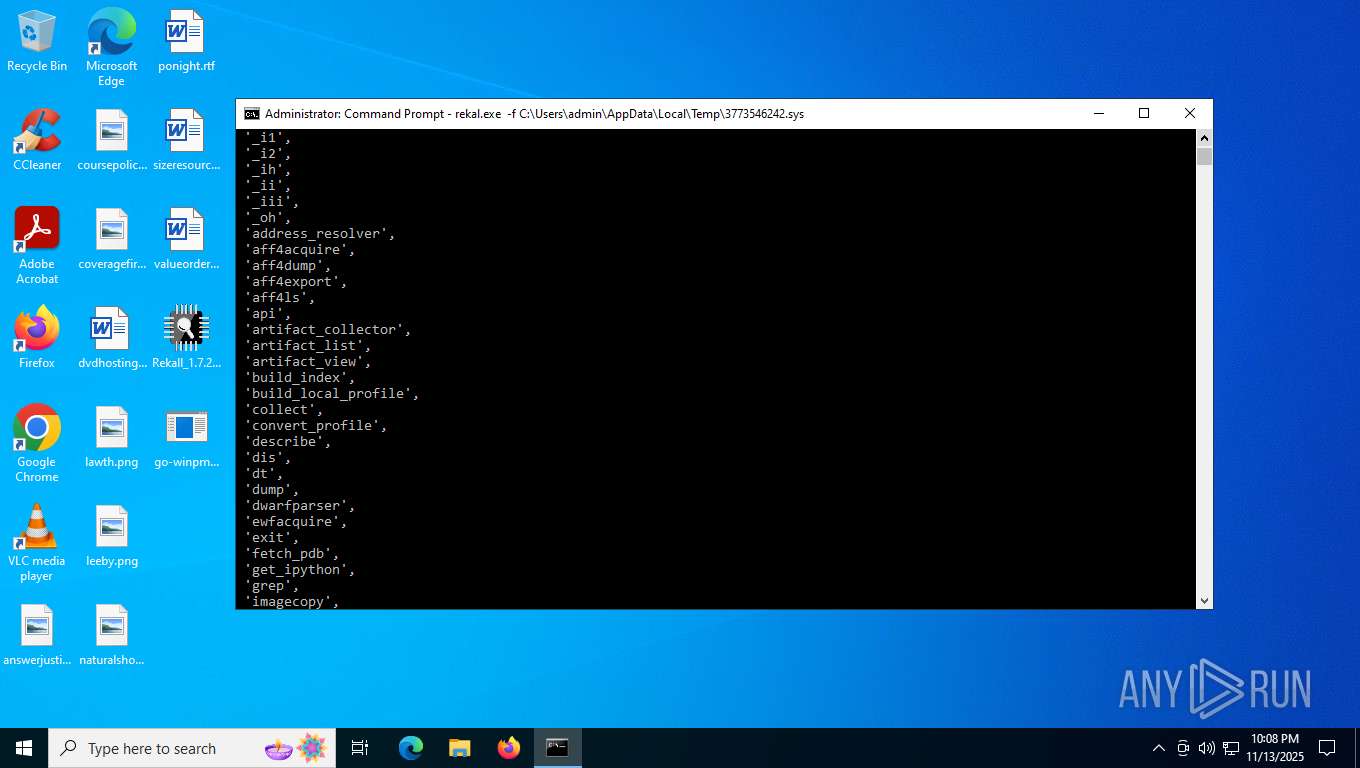
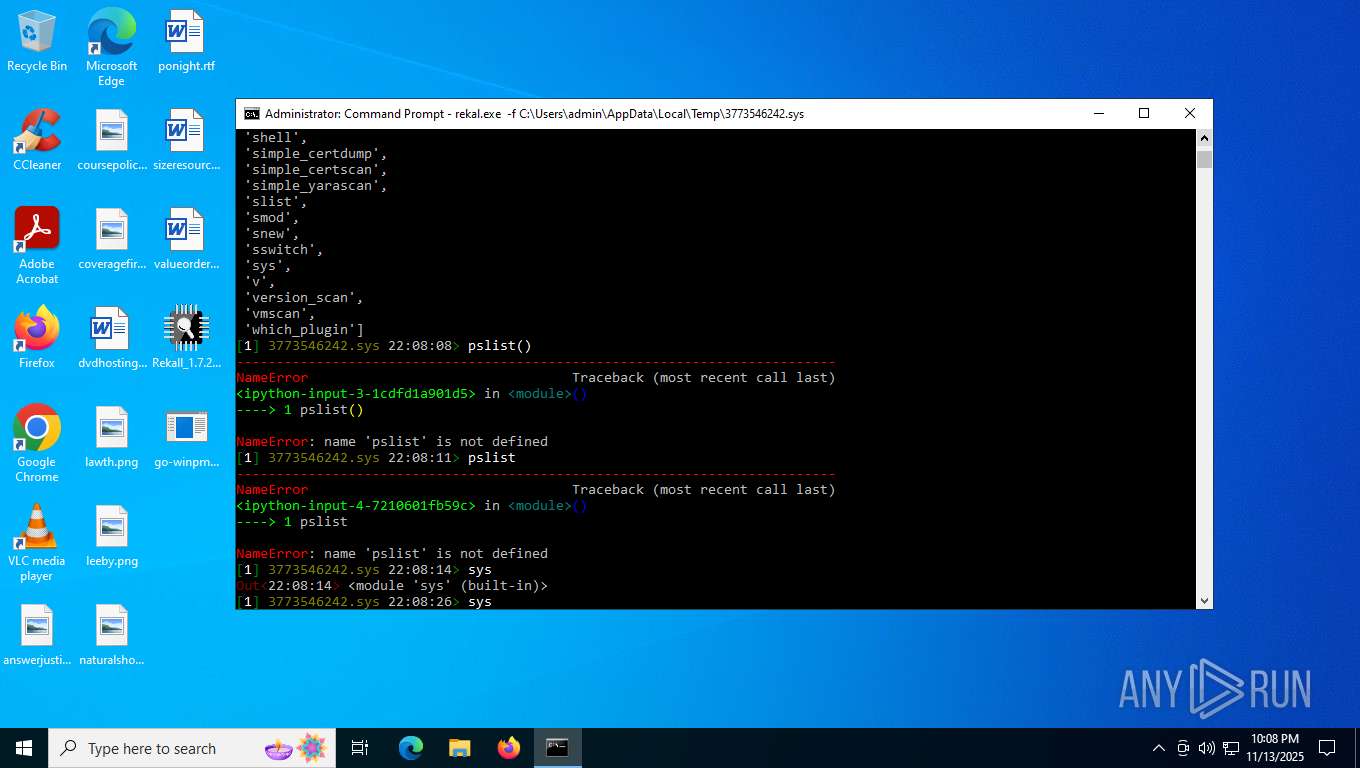
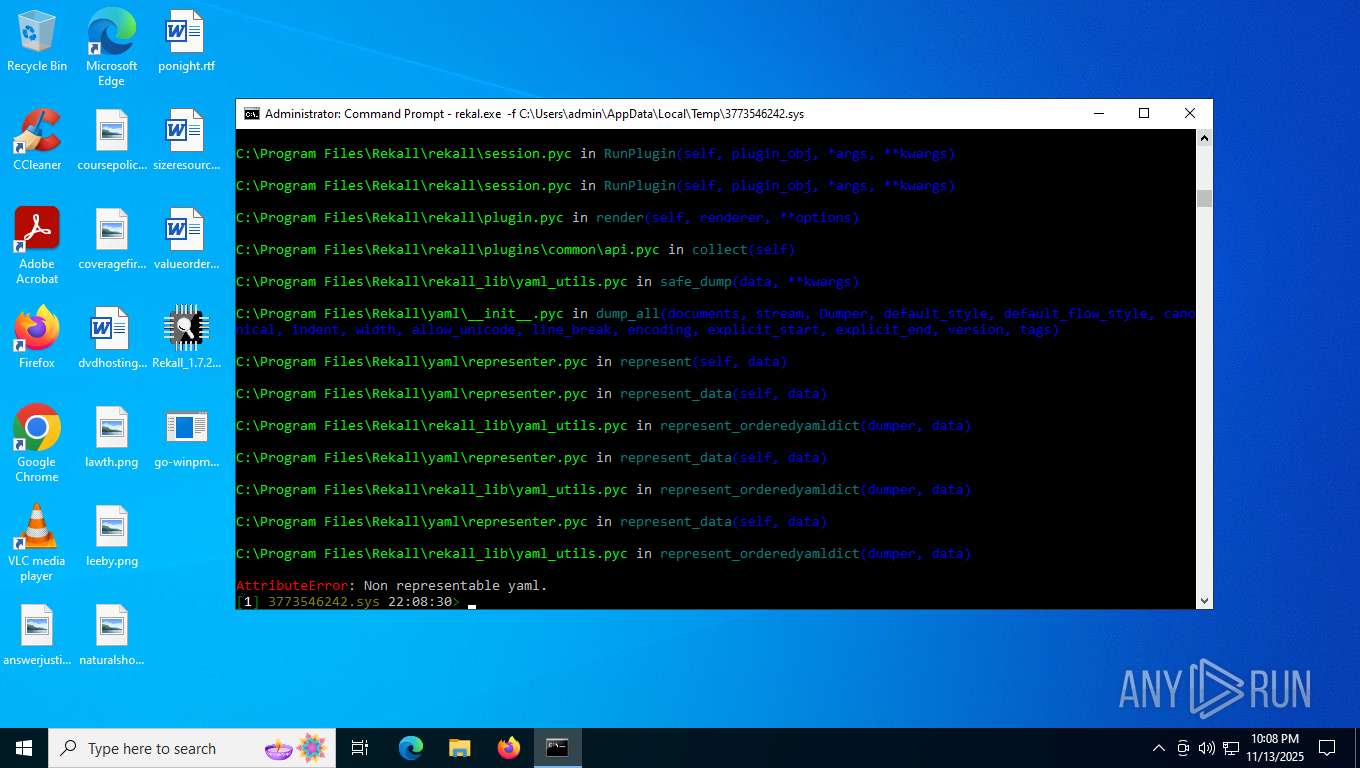
Loads Python modules
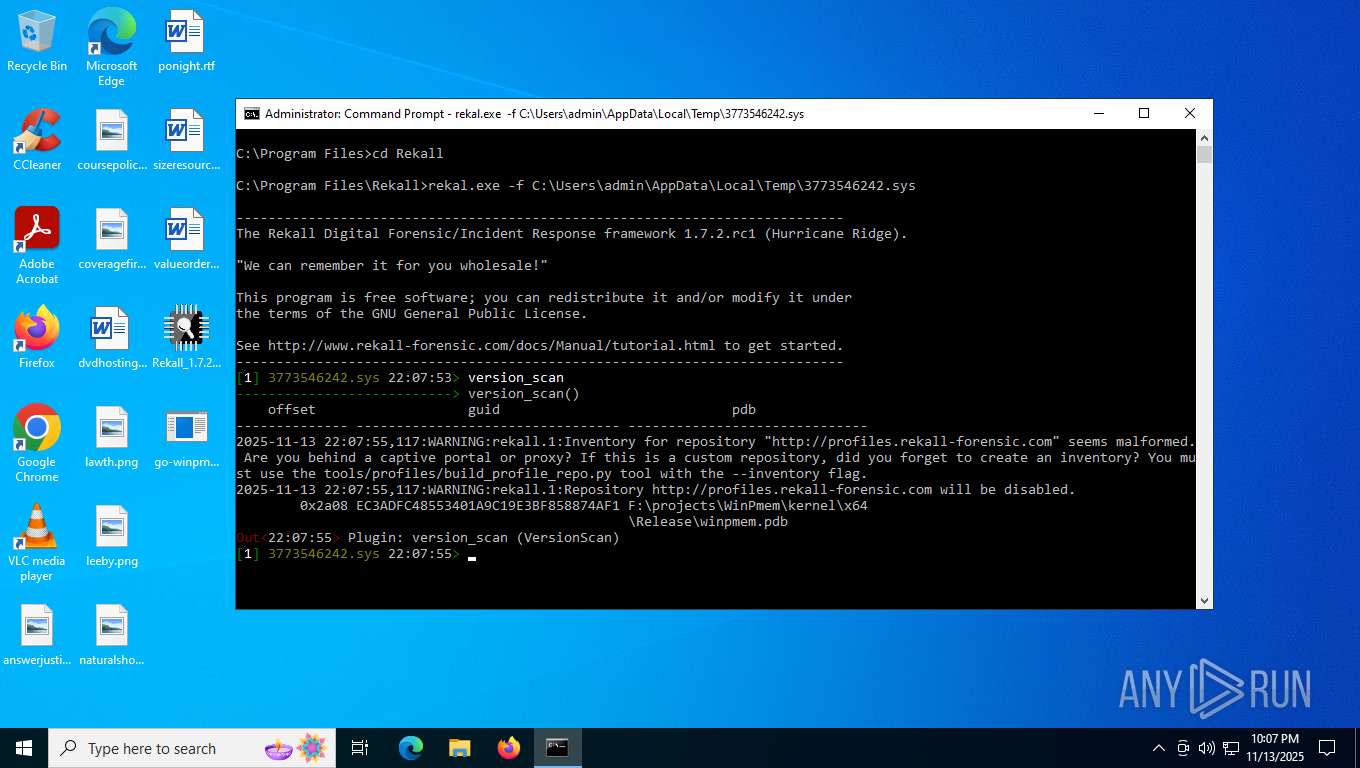
- rekal.exe (PID: 7860)
The process drops C-runtime libraries
- Rekall_1.7.2.p1_Hurricane.Ridge_x64.tmp (PID: 2704)
INFO
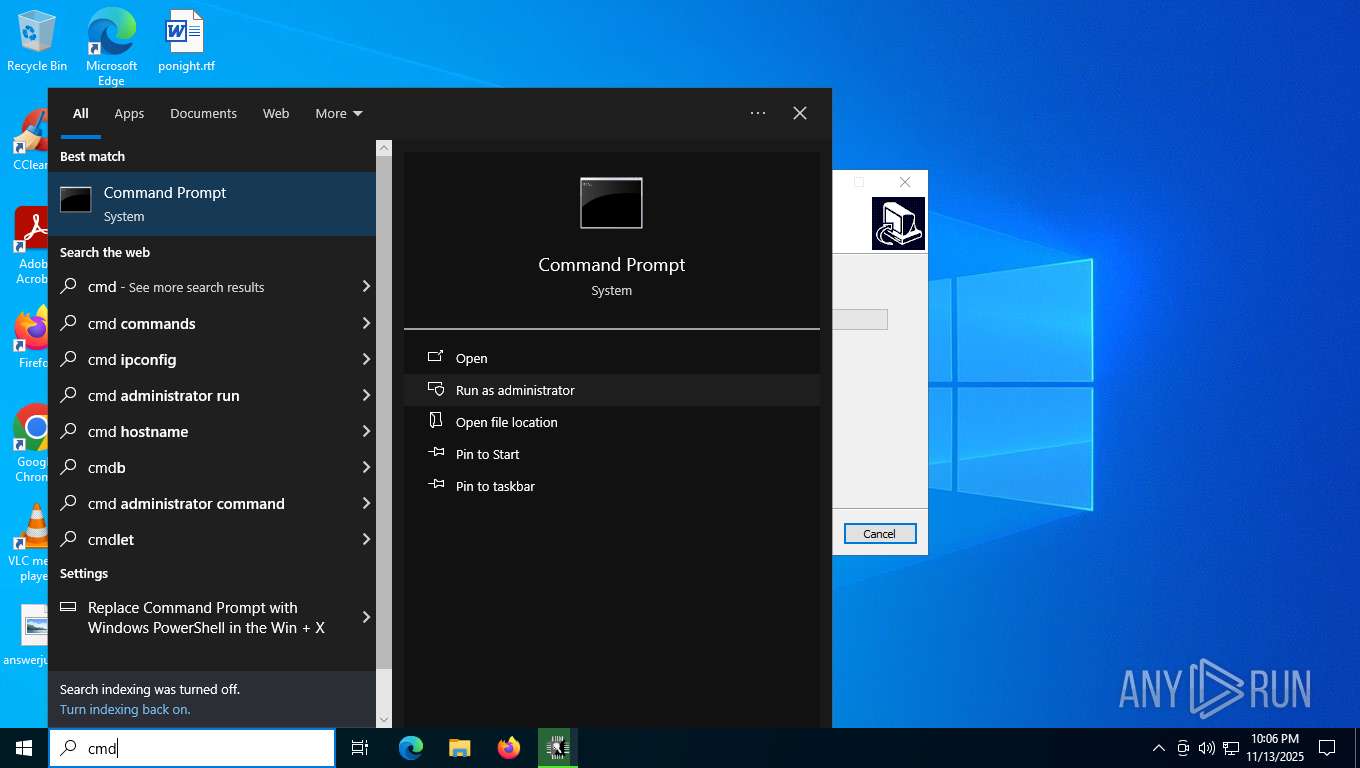
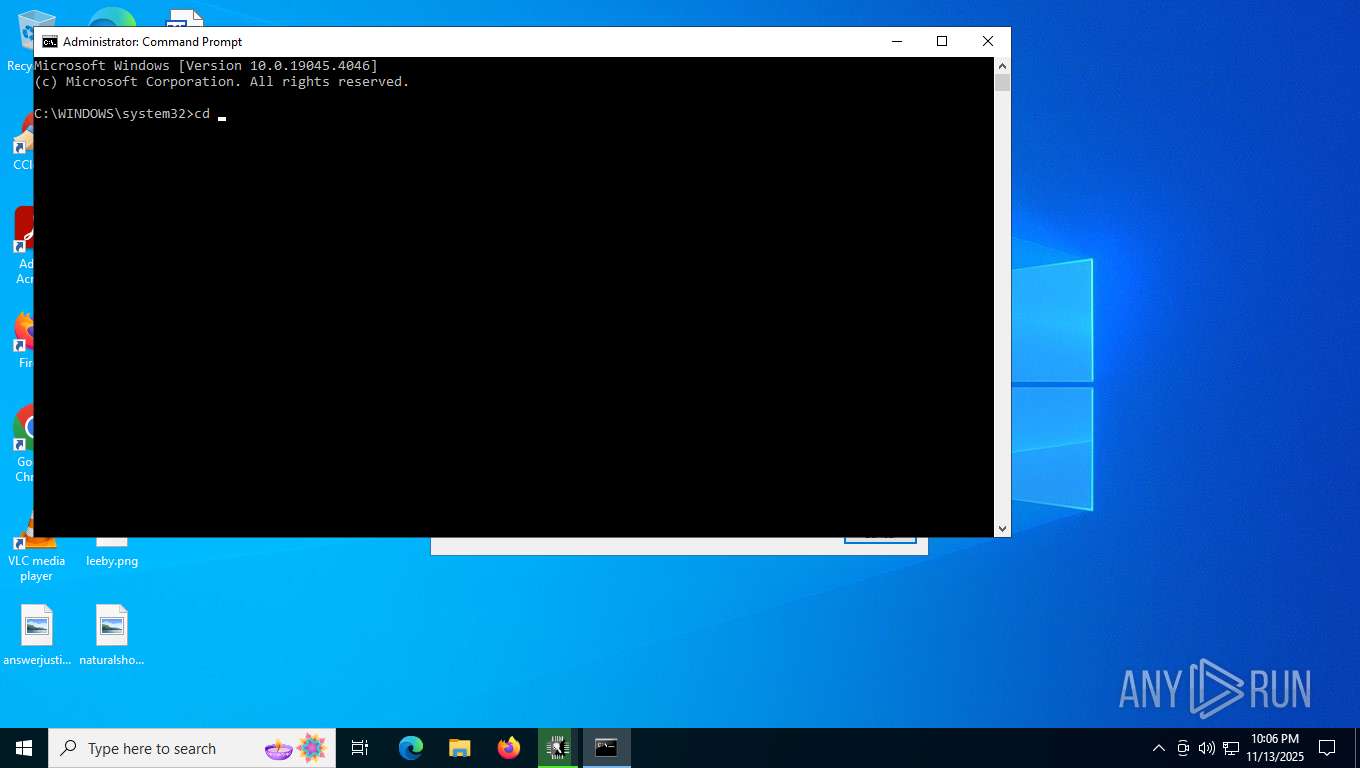
Manual execution by a user
- Rekall_1.7.2.p1_Hurricane.Ridge_x64.exe (PID: 6212)
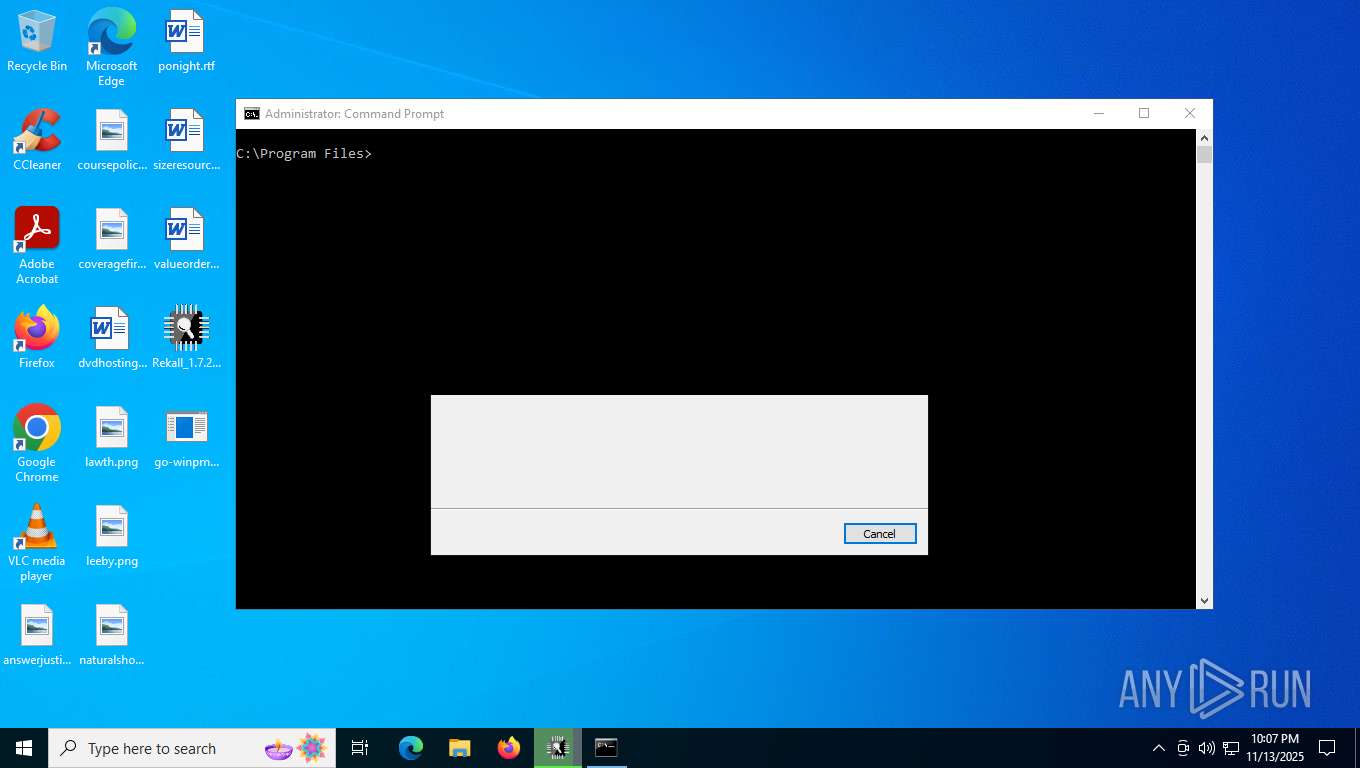
- cmd.exe (PID: 6140)
Checks supported languages
- Rekall_1.7.2.p1_Hurricane.Ridge_x64.tmp (PID: 2716)
- Rekall_1.7.2.p1_Hurricane.Ridge_x64.exe (PID: 6212)
- Rekall_1.7.2.p1_Hurricane.Ridge_x64.exe (PID: 1308)
- Rekall_1.7.2.p1_Hurricane.Ridge_x64.tmp (PID: 2704)
- go-winpmem_amd64_1.0-rc2_signed.exe (PID: 6176)
- rekal.exe (PID: 7860)
Create files in a temporary directory
- Rekall_1.7.2.p1_Hurricane.Ridge_x64.exe (PID: 6212)
- Rekall_1.7.2.p1_Hurricane.Ridge_x64.exe (PID: 1308)
- Rekall_1.7.2.p1_Hurricane.Ridge_x64.tmp (PID: 2704)
- rekal.exe (PID: 7860)
- go-winpmem_amd64_1.0-rc2_signed.exe (PID: 6176)
Process checks computer location settings
- Rekall_1.7.2.p1_Hurricane.Ridge_x64.tmp (PID: 2716)
Reads the computer name
- Rekall_1.7.2.p1_Hurricane.Ridge_x64.tmp (PID: 2716)
- Rekall_1.7.2.p1_Hurricane.Ridge_x64.tmp (PID: 2704)
- go-winpmem_amd64_1.0-rc2_signed.exe (PID: 6176)
- rekal.exe (PID: 7860)
The sample compiled with english language support
- Rekall_1.7.2.p1_Hurricane.Ridge_x64.tmp (PID: 2704)
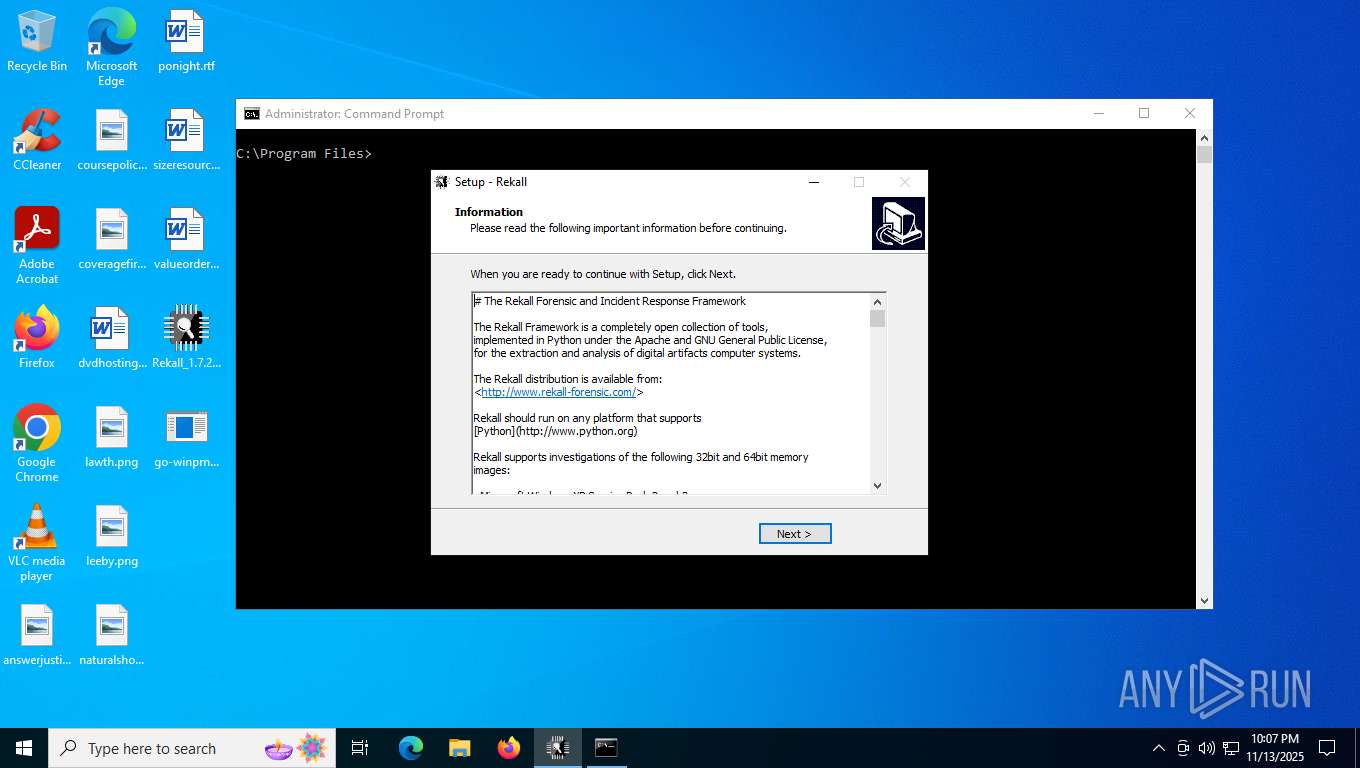
Detects InnoSetup installer (YARA)
- Rekall_1.7.2.p1_Hurricane.Ridge_x64.tmp (PID: 2716)
- Rekall_1.7.2.p1_Hurricane.Ridge_x64.exe (PID: 6212)
- Rekall_1.7.2.p1_Hurricane.Ridge_x64.tmp (PID: 2704)
- Rekall_1.7.2.p1_Hurricane.Ridge_x64.exe (PID: 1308)
Compiled with Borland Delphi (YARA)
- Rekall_1.7.2.p1_Hurricane.Ridge_x64.tmp (PID: 2716)
- Rekall_1.7.2.p1_Hurricane.Ridge_x64.tmp (PID: 2704)
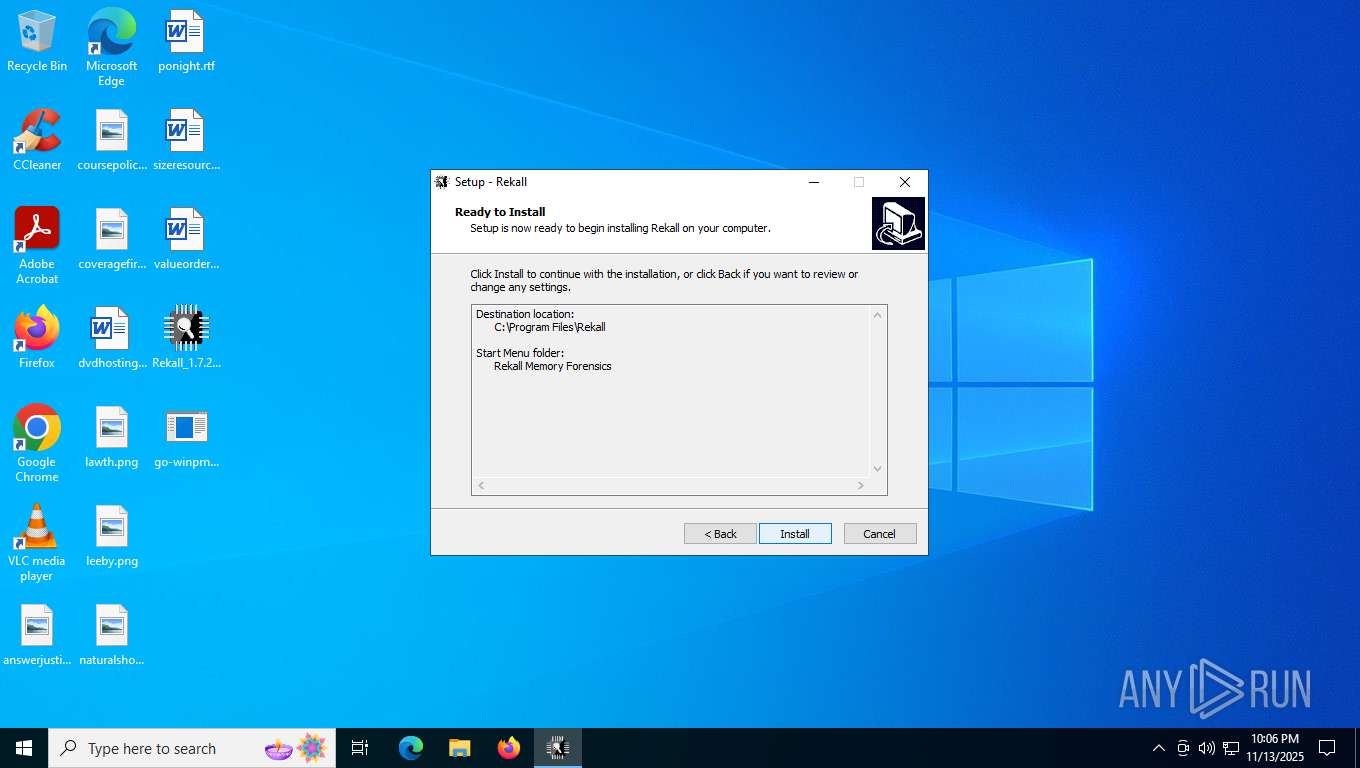
Creates files in the program directory
- Rekall_1.7.2.p1_Hurricane.Ridge_x64.tmp (PID: 2704)
Creates files or folders in the user directory
- Rekall_1.7.2.p1_Hurricane.Ridge_x64.tmp (PID: 2704)
Checks proxy server information
- slui.exe (PID: 5308)
- rekal.exe (PID: 7860)
Reads the machine GUID from the registry
- rekal.exe (PID: 7860)
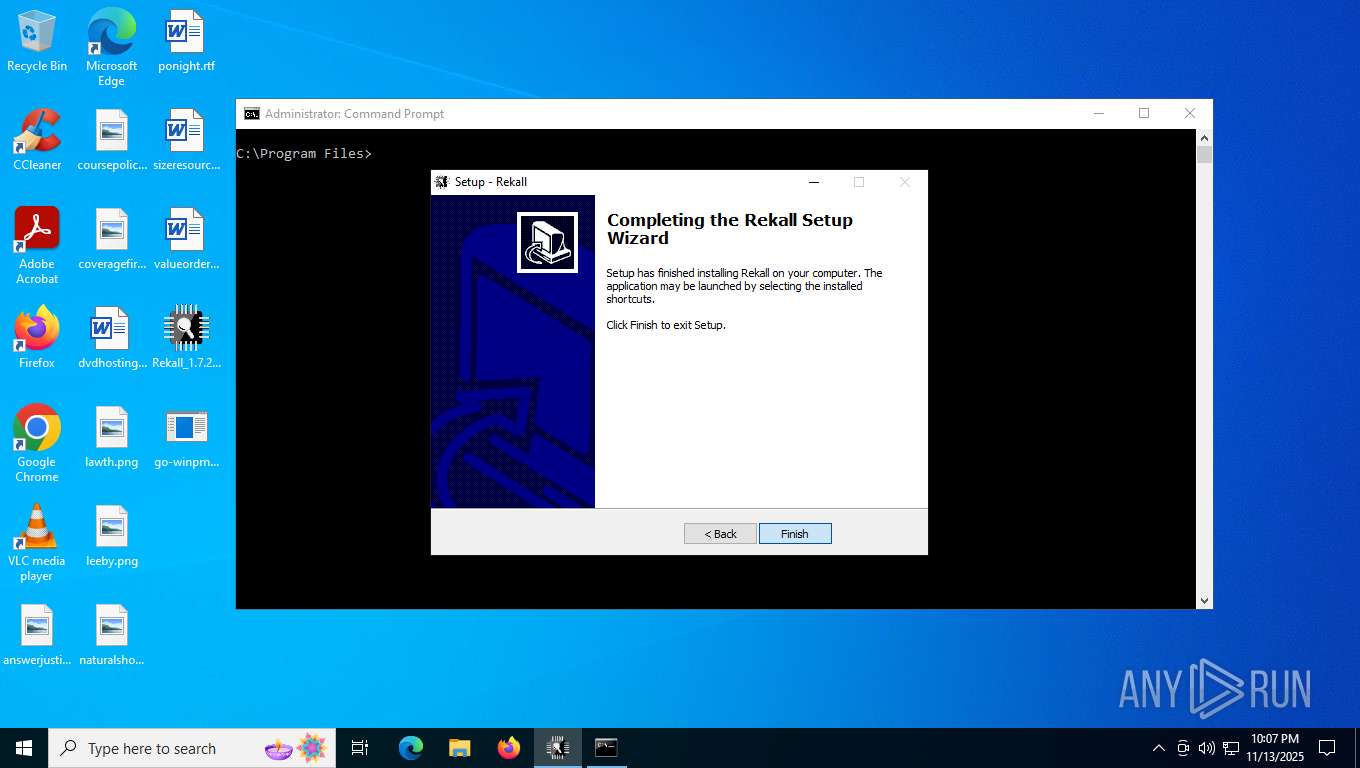
Creates a software uninstall entry
- Rekall_1.7.2.p1_Hurricane.Ridge_x64.tmp (PID: 2704)
Reads the software policy settings
- slui.exe (PID: 5308)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
EXIF
ZIP
| ZipRequiredVersion: | 20 |
|---|---|
| ZipBitFlag: | - |
| ZipCompression: | None |
| ZipModifyDate: | 2025:11:12 14:13:18 |
| ZipCRC: | 0x00000000 |
| ZipCompressedSize: | - |
| ZipUncompressedSize: | - |
| ZipFileName: | sample_mal/ |
Total processes
162
Monitored processes
10
Malicious processes
0
Suspicious processes
2
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1308 | "C:\Users\admin\Desktop\Rekall_1.7.2.p1_Hurricane.Ridge_x64.exe" /SPAWNWND=$901F8 /NOTIFYWND=$C02D0 | C:\Users\admin\Desktop\Rekall_1.7.2.p1_Hurricane.Ridge_x64.exe | Rekall_1.7.2.p1_Hurricane.Ridge_x64.tmp | ||||||||||||
User: admin Company: Rekall Inc. Integrity Level: HIGH Description: Rekall Memory Forensic Framework Exit code: 0 Version: Rekall Memory Forens Modules
| |||||||||||||||
| 2704 | "C:\Users\admin\AppData\Local\Temp\is-PTB1B.tmp\Rekall_1.7.2.p1_Hurricane.Ridge_x64.tmp" /SL5="$1401E8,30575895,119296,C:\Users\admin\Desktop\Rekall_1.7.2.p1_Hurricane.Ridge_x64.exe" /SPAWNWND=$901F8 /NOTIFYWND=$C02D0 | C:\Users\admin\AppData\Local\Temp\is-PTB1B.tmp\Rekall_1.7.2.p1_Hurricane.Ridge_x64.tmp | Rekall_1.7.2.p1_Hurricane.Ridge_x64.exe | ||||||||||||
User: admin Integrity Level: HIGH Description: Setup/Uninstall Exit code: 0 Version: 51.52.0.0 Modules
| |||||||||||||||
| 2716 | "C:\Users\admin\AppData\Local\Temp\is-C4PDO.tmp\Rekall_1.7.2.p1_Hurricane.Ridge_x64.tmp" /SL5="$C02D0,30575895,119296,C:\Users\admin\Desktop\Rekall_1.7.2.p1_Hurricane.Ridge_x64.exe" | C:\Users\admin\AppData\Local\Temp\is-C4PDO.tmp\Rekall_1.7.2.p1_Hurricane.Ridge_x64.tmp | — | Rekall_1.7.2.p1_Hurricane.Ridge_x64.exe | |||||||||||
User: admin Integrity Level: MEDIUM Description: Setup/Uninstall Exit code: 0 Version: 51.52.0.0 Modules
| |||||||||||||||
| 5308 | C:\WINDOWS\System32\slui.exe -Embedding | C:\Windows\System32\slui.exe | svchost.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Activation Client Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6140 | "C:\WINDOWS\system32\cmd.exe" | C:\Windows\System32\cmd.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 6176 | go-winpmem_amd64_1.0-rc2_signed.exe install | C:\Users\admin\Desktop\go-winpmem_amd64_1.0-rc2_signed.exe | cmd.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 6212 | "C:\Users\admin\Desktop\Rekall_1.7.2.p1_Hurricane.Ridge_x64.exe" | C:\Users\admin\Desktop\Rekall_1.7.2.p1_Hurricane.Ridge_x64.exe | explorer.exe | ||||||||||||
User: admin Company: Rekall Inc. Integrity Level: MEDIUM Description: Rekall Memory Forensic Framework Exit code: 0 Version: Rekall Memory Forens Modules
| |||||||||||||||
| 6376 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 7348 | "C:\Program Files\WinRAR\WinRAR.exe" C:\Users\admin\AppData\Local\Temp\sample_mal.zip | C:\Program Files\WinRAR\WinRAR.exe | — | explorer.exe | |||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.91.0 Modules
| |||||||||||||||
| 7860 | rekal.exe -f C:\Users\admin\AppData\Local\Temp\3773546242.sys | C:\Program Files\Rekall\rekal.exe | cmd.exe | ||||||||||||
User: admin Integrity Level: HIGH Modules
| |||||||||||||||
Total events
22 284
Read events
22 248
Write events
36
Delete events
0
Modification events
| (PID) Process: | (7348) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (7348) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
| (PID) Process: | (7348) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 3 |
Value: C:\Users\admin\Desktop\preferences.zip | |||
| (PID) Process: | (7348) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 2 |
Value: C:\Users\admin\Desktop\chromium_ext.zip | |||
| (PID) Process: | (7348) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 1 |
Value: C:\Users\admin\Desktop\omni_23_10_2024_.zip | |||
| (PID) Process: | (7348) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\sample_mal.zip | |||
| (PID) Process: | (7348) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (7348) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (7348) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (7348) WinRAR.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
Executable files
281
Suspicious files
1 252
Text files
84
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2704 | Rekall_1.7.2.p1_Hurricane.Ridge_x64.tmp | C:\Users\admin\AppData\Local\Temp\is-6K7CI.tmp\_isetup\_setup64.tmp | executable | |
MD5:E4211D6D009757C078A9FAC7FF4F03D4 | SHA256:388A796580234EFC95F3B1C70AD4CB44BFDDC7BA0F9203BF4902B9929B136F95 | |||
| 2704 | Rekall_1.7.2.p1_Hurricane.Ridge_x64.tmp | C:\Program Files\Rekall\is-HTRJP.tmp | executable | |
MD5:397AEDDCAEBABFAC8968D303AB10620A | SHA256:950B200F12B25F6A3977F6BC286570CFE00527EACAA269297D1E1DA5CC6B671E | |||
| 2704 | Rekall_1.7.2.p1_Hurricane.Ridge_x64.tmp | C:\Program Files\Rekall\acora._acora.pyd | executable | |
MD5:429B2154DD9DF796BAD21996021F7DA4 | SHA256:3A49C311B992AA28DF1D56C4F9F61CF24450B3ADAD14D78AC7505A1816769810 | |||
| 1308 | Rekall_1.7.2.p1_Hurricane.Ridge_x64.exe | C:\Users\admin\AppData\Local\Temp\is-PTB1B.tmp\Rekall_1.7.2.p1_Hurricane.Ridge_x64.tmp | executable | |
MD5:B956C0EE128F7F24A6BBB3959EEB0132 | SHA256:DFD4B4D7B07AF409D3347B06A2A5D2E8F3443A503ECB07C3DB7E32C86471024A | |||
| 2704 | Rekall_1.7.2.p1_Hurricane.Ridge_x64.tmp | C:\Program Files\Rekall\is-A5VK2.tmp | executable | |
MD5:429B2154DD9DF796BAD21996021F7DA4 | SHA256:3A49C311B992AA28DF1D56C4F9F61CF24450B3ADAD14D78AC7505A1816769810 | |||
| 2704 | Rekall_1.7.2.p1_Hurricane.Ridge_x64.tmp | C:\Program Files\Rekall\unins000.exe | executable | |
MD5:397AEDDCAEBABFAC8968D303AB10620A | SHA256:950B200F12B25F6A3977F6BC286570CFE00527EACAA269297D1E1DA5CC6B671E | |||
| 2704 | Rekall_1.7.2.p1_Hurricane.Ridge_x64.tmp | C:\Users\admin\AppData\Local\Temp\is-6K7CI.tmp\_isetup\_isdecmp.dll | executable | |
MD5:77D6D961F71A8C558513BED6FD0AD6F1 | SHA256:5DA7C8D33D3B7DB46277012D92875C0B850C8ABF1EB3C8C9C5B9532089A0BCF0 | |||
| 6212 | Rekall_1.7.2.p1_Hurricane.Ridge_x64.exe | C:\Users\admin\AppData\Local\Temp\is-C4PDO.tmp\Rekall_1.7.2.p1_Hurricane.Ridge_x64.tmp | executable | |
MD5:B956C0EE128F7F24A6BBB3959EEB0132 | SHA256:DFD4B4D7B07AF409D3347B06A2A5D2E8F3443A503ECB07C3DB7E32C86471024A | |||
| 2704 | Rekall_1.7.2.p1_Hurricane.Ridge_x64.tmp | C:\Program Files\Rekall\api-ms-win-core-datetime-l1-1-0.dll | executable | |
MD5:A00913A82561375C1A51F1C7A1FF354F | SHA256:D6105DF036FB1C5A8C997CABB36946AE627C4E6D25A037CE06E146CEB767658D | |||
| 2704 | Rekall_1.7.2.p1_Hurricane.Ridge_x64.tmp | C:\Program Files\Rekall\is-E3QED.tmp | executable | |
MD5:BE87532E70CC84D36849B11DB3BA7197 | SHA256:212512042CEC75CB3A51010BFD09961A8C1FB469565827319FB53B8EC5460E9B | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
8
TCP/UDP connections
44
DNS requests
26
Threats
2
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
4324 | svchost.exe | GET | 200 | 184.30.131.245:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | US | binary | 471 b | whitelisted |
7176 | SIHClient.exe | GET | 200 | 23.3.109.244:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20Update%20Signing%20CA%202.3.crl | DE | binary | 813 b | whitelisted |
7088 | SearchApp.exe | GET | 200 | 172.66.2.5:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | US | binary | 471 b | whitelisted |
7176 | SIHClient.exe | GET | 200 | 23.3.109.244:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20Time-Stamp%20PCA%202010(1).crl | DE | binary | 814 b | whitelisted |
7176 | SIHClient.exe | GET | 200 | 23.3.109.244:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Signing%20CA%202.3.crl | DE | binary | 401 b | whitelisted |
7176 | SIHClient.exe | GET | 200 | 23.3.109.244:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20Update%20Signing%20CA%202.2.crl | DE | binary | 813 b | whitelisted |
7176 | SIHClient.exe | GET | 200 | 23.3.109.244:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Signing%20CA%202.2.crl | DE | binary | 402 b | whitelisted |
2792 | svchost.exe | GET | 200 | 2.16.168.114:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | RU | binary | 825 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
2792 | svchost.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
5596 | MoUsoCoreWorker.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4204 | RUXIMICS.exe | 40.127.240.158:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
7088 | SearchApp.exe | 184.86.251.19:443 | www.bing.com | Akamai International B.V. | DE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
4324 | svchost.exe | 40.126.31.128:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4324 | svchost.exe | 184.30.131.245:80 | ocsp.digicert.com | AKAMAI-AS | US | whitelisted |
2792 | svchost.exe | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
2792 | svchost.exe | 2.16.168.114:80 | crl.microsoft.com | Akamai International B.V. | RU | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
www.bing.com |
| whitelisted |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
fp.msedge.net |
| whitelisted |
s-ring.msedge.net |
| whitelisted |
mcr-ring.msedge.net |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
— | — | Unknown Traffic | ET USER_AGENTS Microsoft Dr Watson User-Agent (MSDW) |
2276 | svchost.exe | Not Suspicious Traffic | INFO [ANY.RUN] Attempting to access raw user content on GitHub |