| File name: | cmd_20052019.zip |
| Full analysis: | https://app.any.run/tasks/d259f79b-c3b2-480a-9d64-17cf66de183c |
| Verdict: | Malicious activity |
| Analysis date: | May 24, 2019, 18:44:42 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/zip |
| File info: | Zip archive data, at least v2.0 to extract |
| MD5: | C52DB13403D3E999B0CA495F13077CA4 |
| SHA1: | E21AE2DCAD11CF377C885E04581F168F5AF575CD |
| SHA256: | 63F530B6B916EC55BDD1515101D048955142CDD7340BE778027EC3F634EB80D1 |
| SSDEEP: | 96:JBPlhsJBpbBwHH7RILDOSlPhdSwaYPM4AXSPaQjkU3Rzh9y:nPEJFEbSxBhdSDYPMq7AUBzh9y |
MALICIOUS
Runs PING.EXE for delay simulation
- cmd.exe (PID: 2336)
Writes to a start menu file
- wscript.exe (PID: 2044)
SUSPICIOUS
Starts CMD.EXE for commands execution
- WinRAR.exe (PID: 3300)
- cmd.exe (PID: 3332)
Starts application with an unusual extension
- cmd.exe (PID: 2692)
- cmd.exe (PID: 3332)
Executes scripts
- cmd.exe (PID: 2336)
Executable content was dropped or overwritten
- wscript.exe (PID: 2044)
Drop AutoIt3 executable file
- wscript.exe (PID: 2044)
Creates files in the user directory
- wscript.exe (PID: 2044)
INFO
No info indicators.
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
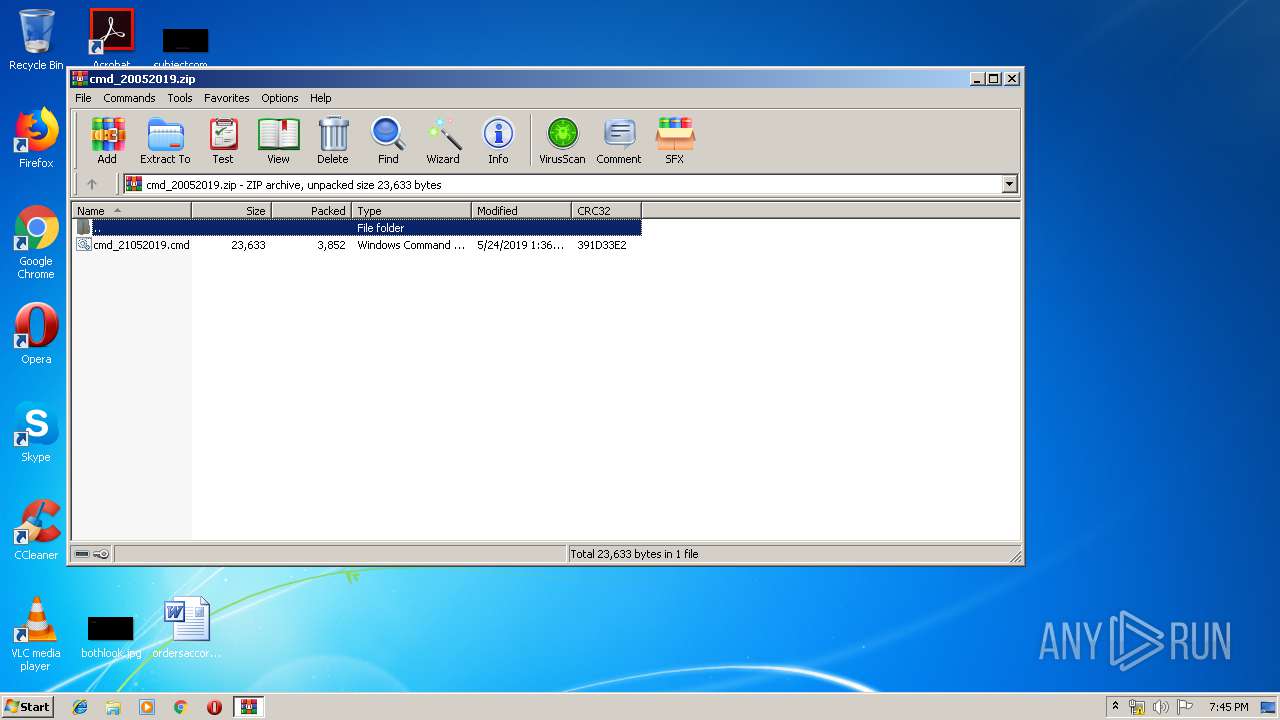
| .zip | | | ZIP compressed archive (100) |
|---|
EXIF
ZIP
| ZipRequiredVersion: | 20 |
|---|---|
| ZipBitFlag: | - |
| ZipCompression: | Deflated |
| ZipModifyDate: | 2019:05:24 09:36:00 |
| ZipCRC: | 0x391d33e2 |
| ZipCompressedSize: | 3852 |
| ZipUncompressedSize: | 23633 |
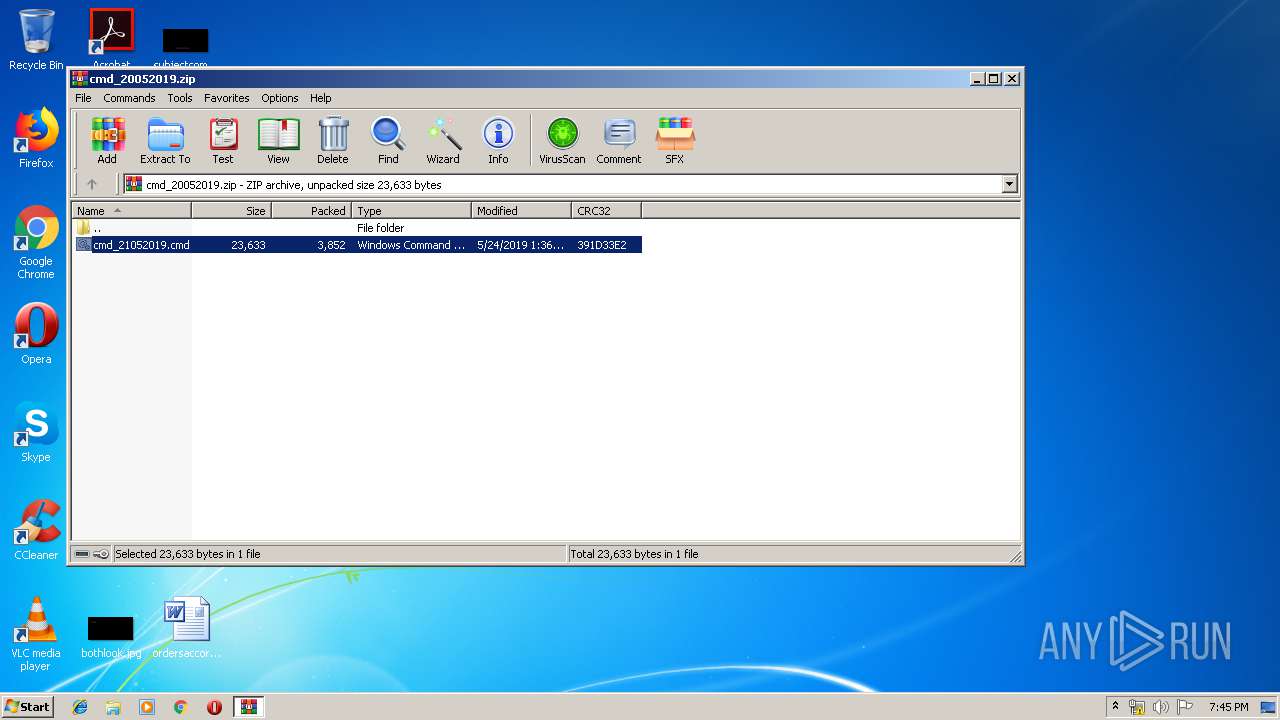
| ZipFileName: | cmd_21052019.cmd |
Total processes
41
Monitored processes
9
Malicious processes
2
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 2044 | wscript //Nologo "C:\Users\admin\admin.vbs" EQCJW6YlHHvx5vQ8SP2FtSBu4gcGjeJExuuEgYxbpAEAEJc | C:\Windows\system32\wscript.exe | cmd.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft ® Windows Based Script Host Exit code: 0 Version: 5.8.7600.16385 Modules
| |||||||||||||||
| 2140 | ping 127.0.0.1 -n 1 | C:\Windows\system32\PING.EXE | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: TCP/IP Ping Command Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2336 | cmd /c ""C:\Users\admin\AppData\Local\Temp\Rar$DIa3300.2118\cmd_21052019.cmd" " | C:\Windows\system32\cmd.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 2512 | chcp 708 | C:\Windows\system32\chcp.com | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Change CodePage Utility Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2584 | chcp 437 | C:\Windows\system32\chcp.com | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Change CodePage Utility Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2692 | C:\Windows\system32\cmd.exe /c chcp | C:\Windows\system32\cmd.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 3300 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\AppData\Local\Temp\cmd_20052019.zip" | C:\Program Files\WinRAR\WinRAR.exe | — | explorer.exe | |||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.60.0 Modules
| |||||||||||||||
| 3332 | cmd /c ""C:\Users\admin\AppData\Local\Temp\Rar$DIa3300.2118\cmd_21052019.cmd" " | C:\Windows\system32\cmd.exe | — | WinRAR.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 6.1.7601.17514 (win7sp1_rtm.101119-1850) Modules
| |||||||||||||||
| 3604 | chcp | C:\Windows\system32\chcp.com | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Change CodePage Utility Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
Total events
891
Read events
857
Write events
34
Delete events
0
Modification events
| (PID) Process: | (3300) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (3300) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
| (PID) Process: | (3300) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\62\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (3300) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\AppData\Local\Temp\cmd_20052019.zip | |||
| (PID) Process: | (3300) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (3300) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (3300) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (3300) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (3300) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\62\52C64B7E |
| Operation: | write | Name: | @C:\Windows\System32\acppage.dll,-6003 |
Value: Windows Command Script | |||
| (PID) Process: | (3300) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
Executable files
3
Suspicious files
2
Text files
109
Unknown types
3
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 3300 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$DIa3300.2118\cmd_21052019.cmd | text | |
MD5:— | SHA256:— | |||
| 2336 | cmd.exe | C:\Users\admin\admin.vbs | text | |
MD5:— | SHA256:— | |||
| 2044 | wscript.exe | C:\Users\admin\admin\PZHE9G8EA81U1LP301H70BP9W9A9T | — | |
MD5:— | SHA256:— | |||
| 2044 | wscript.exe | C:\Users\admin\admin\MNNB86Q893QOBF4PGHMX9KA9H5WBN9WMOB | a3x | |
MD5:— | SHA256:— | |||
| 2044 | wscript.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\H6QNMHE9\y213[1].zip | compressed | |
MD5:— | SHA256:— | |||
| 2044 | wscript.exe | C:\Users\admin\fhfj5nriop.zip | compressed | |
MD5:— | SHA256:— | |||
| 2044 | wscript.exe | C:\Users\admin\admin\htHDBLx_357097 | a3x | |
MD5:— | SHA256:— | |||
| 2044 | wscript.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Start Menu\Programs\Startup\aCNbAFfU9KI50004a06H0M12aNHDK4F8NNFKD2.LNK | lnk | |
MD5:— | SHA256:— | |||
| 2044 | wscript.exe | C:\Users\admin\admin\iEfEVMmT_3592827.dll | executable | |
MD5:— | SHA256:— | |||
| 2044 | wscript.exe | C:\Users\admin\admin\XUGDGKS020OUMV29FG06Q8WH9B63 | executable | |
MD5:B06E67F9767E5023892D9698703AD098 | SHA256:8498900E57A490404E7EC4D8159BEE29AED5852AE88BD484141780EAADB727BB | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
2
TCP/UDP connections
1
DNS requests
1
Threats
1
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
2044 | wscript.exe | GET | 200 | 192.99.34.204:80 | http://docseguridads.com/y213/y213.zip | CA | compressed | 8.34 Mb | malicious |
2044 | wscript.exe | POST | 200 | 192.99.34.204:80 | http://docseguridads.com/y213/ZCorpqhV432BJDA5Ca0JCE7BEaL5C3M5782H9a.txt | CA | text | 519 b | malicious |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
2044 | wscript.exe | 192.99.34.204:80 | docseguridads.com | OVH SAS | CA | malicious |
DNS requests
Domain | IP | Reputation |
|---|---|---|
docseguridads.com |
| malicious |
Threats
PID | Process | Class | Message |
|---|---|---|---|
2044 | wscript.exe | A Network Trojan was detected | MALWARE [PTsecurity] Virus.vbs.qexvmc (N40/KLBanker) |