| File name: | NetworkDistribution-svchost.exe |
| Full analysis: | https://app.any.run/tasks/c46b0735-0963-4f2d-ab05-fcfd9ef0fced |
| Verdict: | Suspicious activity |
| Analysis date: | June 29, 2019, 12:23:12 |
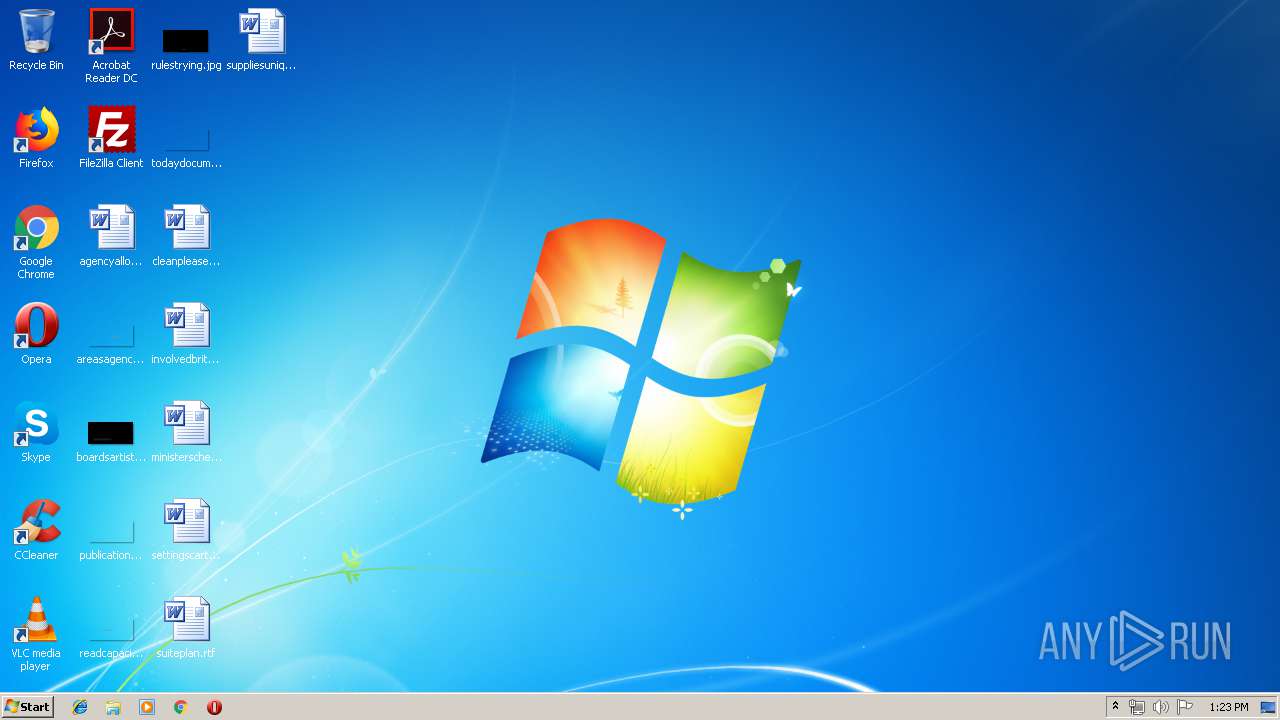
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/x-dosexec |
| File info: | PE32 executable (GUI) Intel 80386, for MS Windows, RAR self-extracting archive |
| MD5: | 46E88D1D97461C21FA12024E9D646C68 |
| SHA1: | 34F6B5671AF935392FCB87819B6A5D1BB174B2C6 |
| SHA256: | 63CA0F631BB662A9C255999FE0747A9586833776318AC2EB6389A82EF307F822 |
| SSDEEP: | 98304:RtvpSIzaW8DUcOqDtNszu9Z/LIFGGf5rsh:zvHanDU9qDUze/U8Gxa |
MALICIOUS
Uses SVCHOST.EXE for hidden code execution
- NetworkDistribution-svchost.exe (PID: 1336)
SUSPICIOUS
Executable content was dropped or overwritten
- NetworkDistribution-svchost.exe (PID: 1336)
Creates files in the Windows directory
- NetworkDistribution-svchost.exe (PID: 1336)
Application launched itself
- NetworkDistribution-svchost.exe (PID: 3632)
Creates executable files which already exist in Windows
- NetworkDistribution-svchost.exe (PID: 1336)
INFO
No info indicators.
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .exe | | | Win32 Executable MS Visual C++ (generic) (42.2) |
|---|---|---|
| .exe | | | Win64 Executable (generic) (37.3) |
| .dll | | | Win32 Dynamic Link Library (generic) (8.8) |
| .exe | | | Win32 Executable (generic) (6) |
| .exe | | | Generic Win/DOS Executable (2.7) |
EXIF
EXE
| MachineType: | Intel 386 or later, and compatibles |
|---|---|
| TimeStamp: | 2013:08:22 15:00:50+02:00 |
| PEType: | PE32 |
| LinkerVersion: | 9 |
| CodeSize: | 152064 |
| InitializedDataSize: | 175104 |
| UninitializedDataSize: | - |
| EntryPoint: | 0x1d348 |
| OSVersion: | 5 |
| ImageVersion: | - |
| SubsystemVersion: | 5 |
| Subsystem: | Windows GUI |
Summary
| Architecture: | IMAGE_FILE_MACHINE_I386 |
|---|---|
| Subsystem: | IMAGE_SUBSYSTEM_WINDOWS_GUI |
| Compilation Date: | 22-Aug-2013 13:00:50 |
| Detected languages: |
|
| Debug artifacts: |
|
DOS Header
| Magic number: | MZ |
|---|---|
| Bytes on last page of file: | 0x0090 |
| Pages in file: | 0x0003 |
| Relocations: | 0x0000 |
| Size of header: | 0x0004 |
| Min extra paragraphs: | 0x0000 |
| Max extra paragraphs: | 0xFFFF |
| Initial SS value: | 0x0000 |
| Initial SP value: | 0x00B8 |
| Checksum: | 0x0000 |
| Initial IP value: | 0x0000 |
| Initial CS value: | 0x0000 |
| Overlay number: | 0x0000 |
| OEM identifier: | 0x0000 |
| OEM information: | 0x0000 |
| Address of NE header: | 0x000000E0 |
PE Headers
| Signature: | PE |
|---|---|
| Machine: | IMAGE_FILE_MACHINE_I386 |
| Number of sections: | 4 |
| Time date stamp: | 22-Aug-2013 13:00:50 |
| Pointer to Symbol Table: | 0x00000000 |
| Number of symbols: | 0 |
| Size of Optional Header: | 0x00E0 |
| Characteristics: |
|
Sections
Name | Virtual Address | Virtual Size | Raw Size | Charateristics | Entropy |
|---|---|---|---|---|---|
.text | 0x00001000 | 0x0002517E | 0x00025200 | IMAGE_SCN_CNT_CODE, IMAGE_SCN_MEM_EXECUTE, IMAGE_SCN_MEM_READ | 6.70052 |
.rdata | 0x00027000 | 0x00004F43 | 0x00005000 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 5.32562 |
.data | 0x0002C000 | 0x000215E0 | 0x00001400 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ, IMAGE_SCN_MEM_WRITE | 2.53948 |
.rsrc | 0x0004E000 | 0x00004470 | 0x00004600 | IMAGE_SCN_CNT_INITIALIZED_DATA, IMAGE_SCN_MEM_READ | 4.60998 |
Resources
Title | Entropy | Size | Codepage | Language | Type |
|---|---|---|---|---|---|
1 | 5.22792 | 1600 | UNKNOWN | English - United States | RT_MANIFEST |
2 | 3.88998 | 1384 | UNKNOWN | English - United States | RT_ICON |
3 | 4.12176 | 744 | UNKNOWN | English - United States | RT_ICON |
4 | 4.68705 | 2216 | UNKNOWN | English - United States | RT_ICON |
7 | 3.1586 | 482 | UNKNOWN | English - United States | RT_STRING |
8 | 3.11685 | 460 | UNKNOWN | English - United States | RT_STRING |
9 | 3.18906 | 536 | UNKNOWN | English - United States | RT_STRING |
10 | 2.99727 | 326 | UNKNOWN | English - United States | RT_STRING |
11 | 3.2036 | 1094 | UNKNOWN | English - United States | RT_STRING |
12 | 3.12889 | 358 | UNKNOWN | English - United States | RT_STRING |
Imports
ADVAPI32.dll |
COMCTL32.dll |
COMDLG32.dll |
GDI32.dll |
KERNEL32.dll |
OLEAUT32.dll |
SHELL32.dll |
SHLWAPI.dll |
USER32.dll |
ole32.dll |
Total processes
37
Monitored processes
3
Malicious processes
2
Suspicious processes
0
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1336 | "C:\Users\admin\AppData\Local\Temp\NetworkDistribution-svchost.exe" -el -s2 "-dC:\Windows" "-p" "-sp" | C:\Users\admin\AppData\Local\Temp\NetworkDistribution-svchost.exe | NetworkDistribution-svchost.exe | ||||||||||||
User: admin Integrity Level: HIGH Exit code: 0 Modules
| |||||||||||||||
| 3348 | "C:\Windows\System32\svchost.exe" | C:\Windows\System32\svchost.exe | — | NetworkDistribution-svchost.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Host Process for Windows Services Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3632 | "C:\Users\admin\AppData\Local\Temp\NetworkDistribution-svchost.exe" | C:\Users\admin\AppData\Local\Temp\NetworkDistribution-svchost.exe | — | explorer.exe | |||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
Total events
425
Read events
416
Write events
9
Delete events
0
Modification events
| (PID) Process: | (3632) NetworkDistribution-svchost.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR SFX |
| Operation: | write | Name: | C%%Windows |
Value: C:\Windows | |||
| (PID) Process: | (3632) NetworkDistribution-svchost.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (3632) NetworkDistribution-svchost.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (1336) NetworkDistribution-svchost.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (1336) NetworkDistribution-svchost.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
Executable files
52
Suspicious files
0
Text files
6
Unknown types
1
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 1336 | NetworkDistribution-svchost.exe | C:\Windows\NetworkDistribution\etch-0.dll | executable | |
MD5:3E5D06DC6E7890E1800CF24C9F599856 | SHA256:3FCFFE9EAE90EC365EFB361674613AC95DE50B2CCFD634C24491923F85C309A5 | |||
| 1336 | NetworkDistribution-svchost.exe | C:\Windows\NetworkDistribution\adfw-2.dll | executable | |
MD5:31D696F93EC84E635C4560034340E171 | SHA256:F06D02359666B763E189402B7FBF9DFA83BA6F4DA2E7D037B3F9AEBEFD2D5A45 | |||
| 1336 | NetworkDistribution-svchost.exe | C:\Windows\NetworkDistribution\crli-0.dll | executable | |
MD5:F82FA69BFE0522163EB0CF8365497DA2 | SHA256:B556B5C077E38DCB65D21A707C19618D02E0A65FF3F9887323728EC078660CC3 | |||
| 1336 | NetworkDistribution-svchost.exe | C:\Windows\NetworkDistribution\cnli-0.dll | executable | |
MD5:EE2D6E1D976A3A92FB1C2524278922AE | SHA256:D3DB1E56360B25E7F36ABB822E03C18D23A19A9B5F198E16C16E06785FC8C5FA | |||
| 1336 | NetworkDistribution-svchost.exe | C:\Windows\NetworkDistribution\Eternalchampion-2.0.0.fb | xml | |
MD5:5B18E38E2B99EBD24937751E936B2161 | SHA256:C00DED23530A99CE053DC63B71D99462D358B2A07EE34065B5AFF489357420DE | |||
| 1336 | NetworkDistribution-svchost.exe | C:\Windows\NetworkDistribution\dmgd-4.dll | executable | |
MD5:A05C7011AB464E6C353A057973F5A06E | SHA256:50F329E034DB96BA254328CD1E0F588AF6126C341ED92DDF4AEB96BC76835937 | |||
| 1336 | NetworkDistribution-svchost.exe | C:\Windows\NetworkDistribution\coli-0.dll | executable | |
MD5:3C2FE2DBDF09CFA869344FDB53307CB2 | SHA256:0439628816CABE113315751E7113A9E9F720D7E499FFDD78ACBAC1ED8BA35887 | |||
| 1336 | NetworkDistribution-svchost.exe | C:\Windows\NetworkDistribution\etebCore-2.x64.dll | executable | |
MD5:24AA99837D14BEE5DA2E2339B07F9D4C | SHA256:8A5CCE25F1BF60E716709C724B96630B95E55CC0E488D74D60EA50FFBA7D6946 | |||
| 1336 | NetworkDistribution-svchost.exe | C:\Windows\NetworkDistribution\etchCore-0.x64.dll | executable | |
MD5:4FF94C163565A38A27CF997AD07B3D69 | SHA256:FE4640FEFA4BEF02041A771A206F9184ADB38DE051F0D8726C4579736FE13BB6 | |||
| 1336 | NetworkDistribution-svchost.exe | C:\Windows\NetworkDistribution\dmgd-1.dll | executable | |
MD5:1CA9E6EB86036DAEA4DFA3297F70D542 | SHA256:9B8EC5D0C10CCDD3933B7712BA40065D1B0DD3FFA7968FB28AD426CD5EEE5001 | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
0
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report