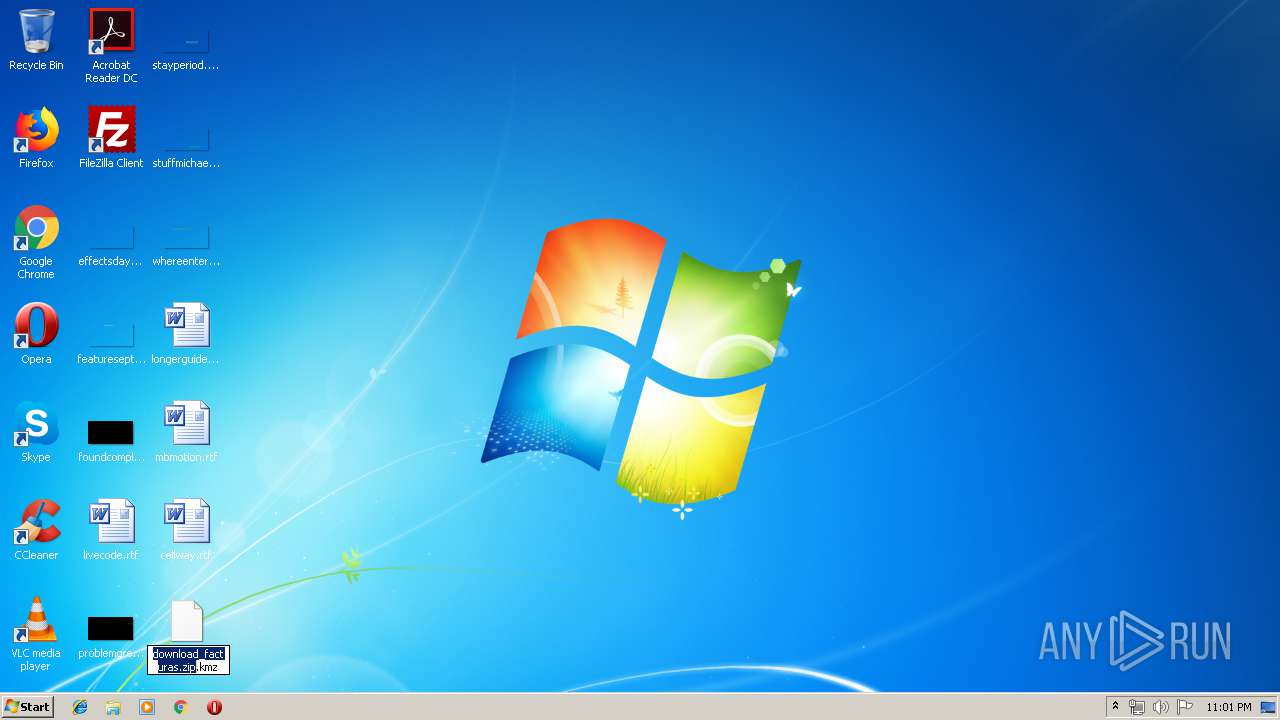
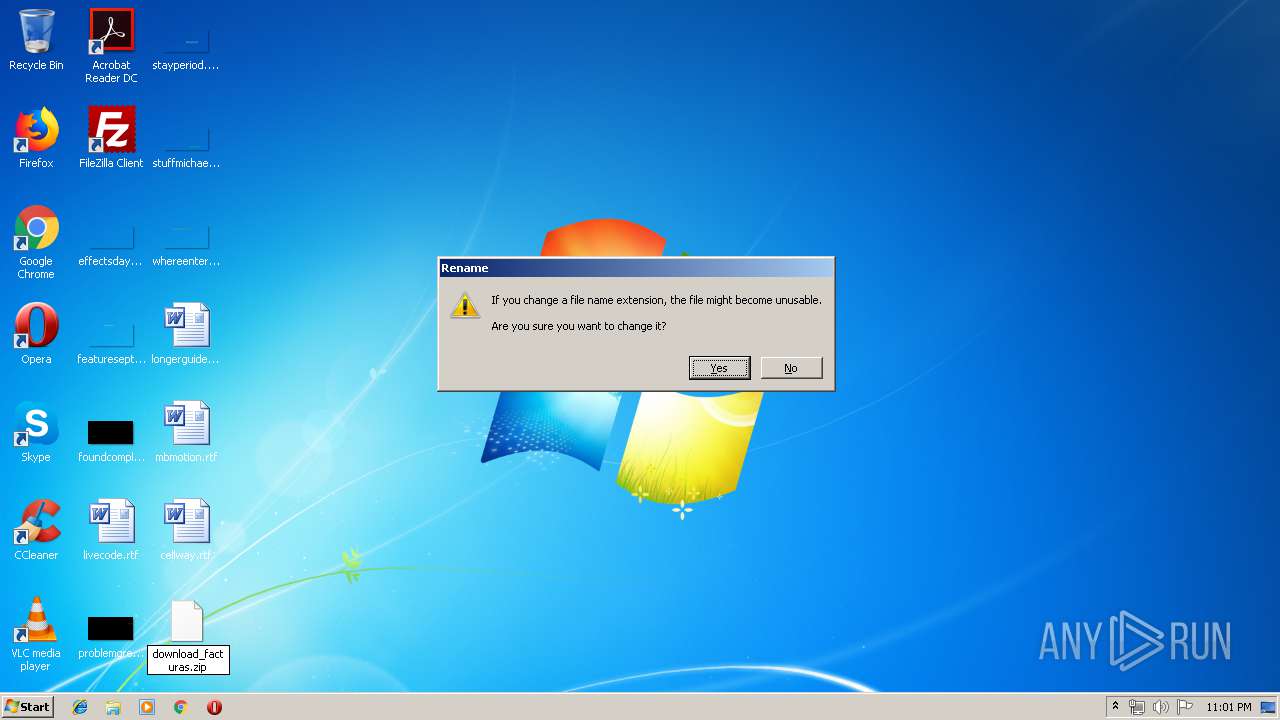
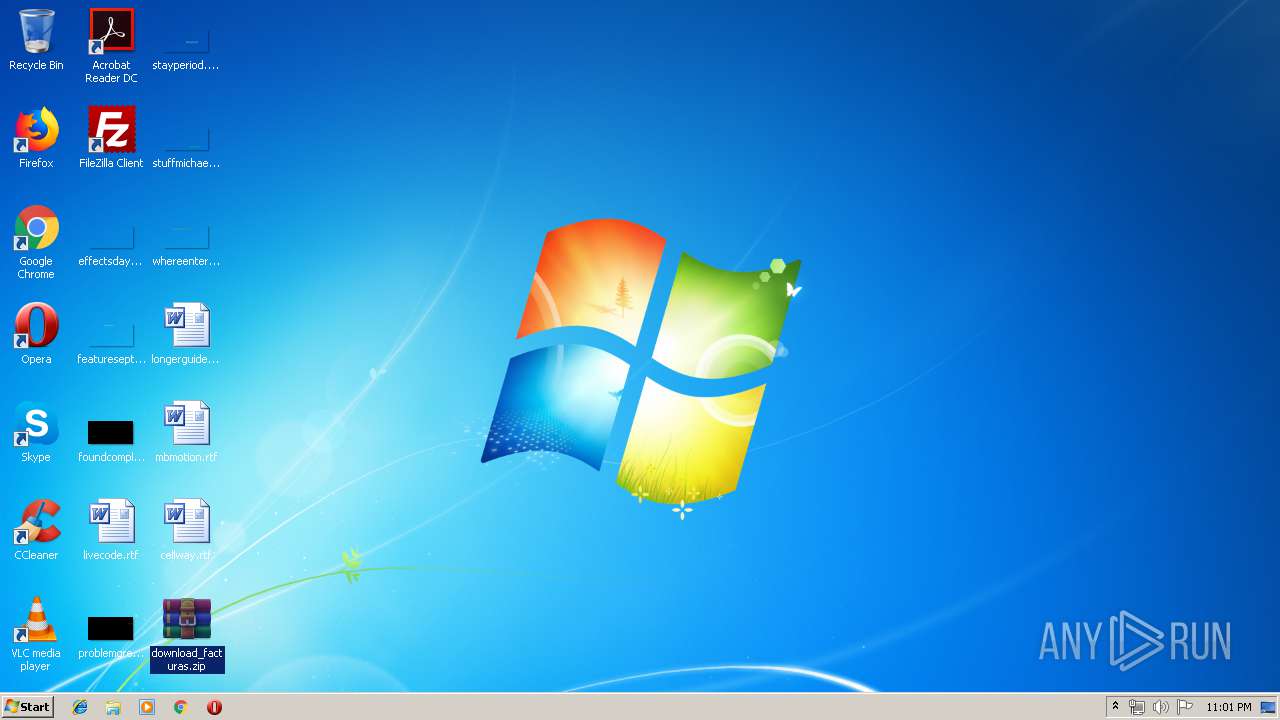
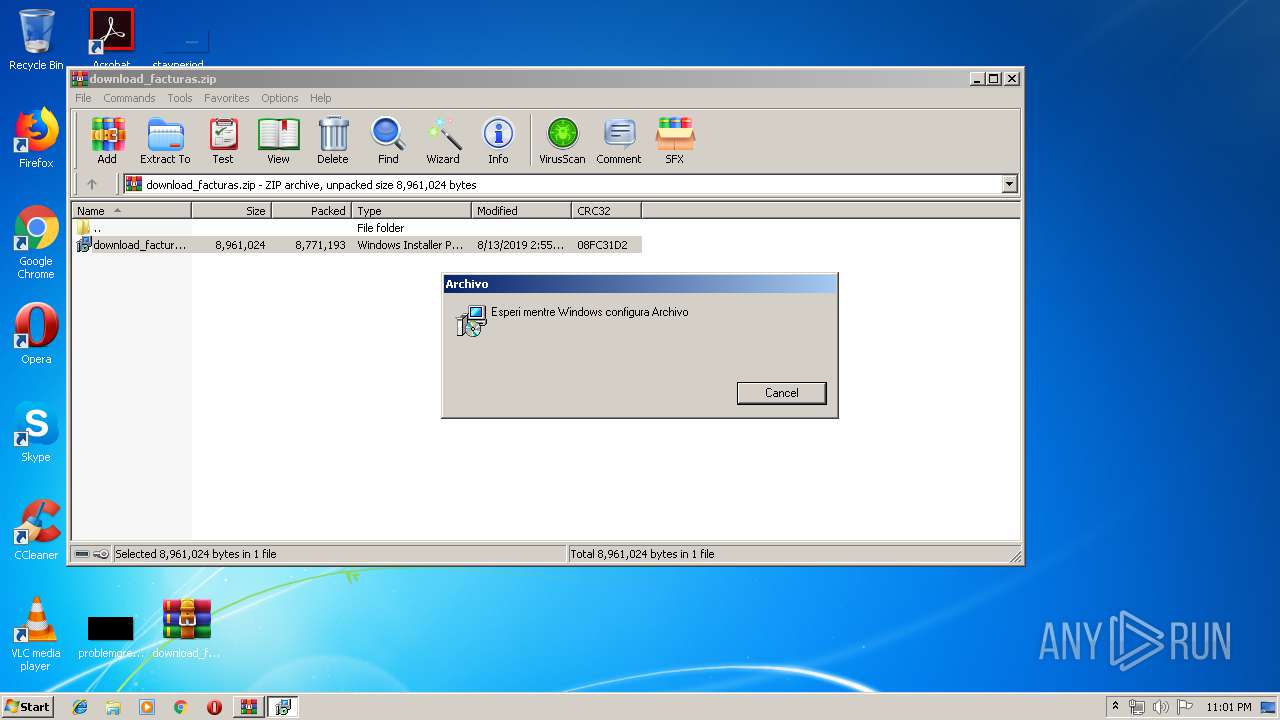
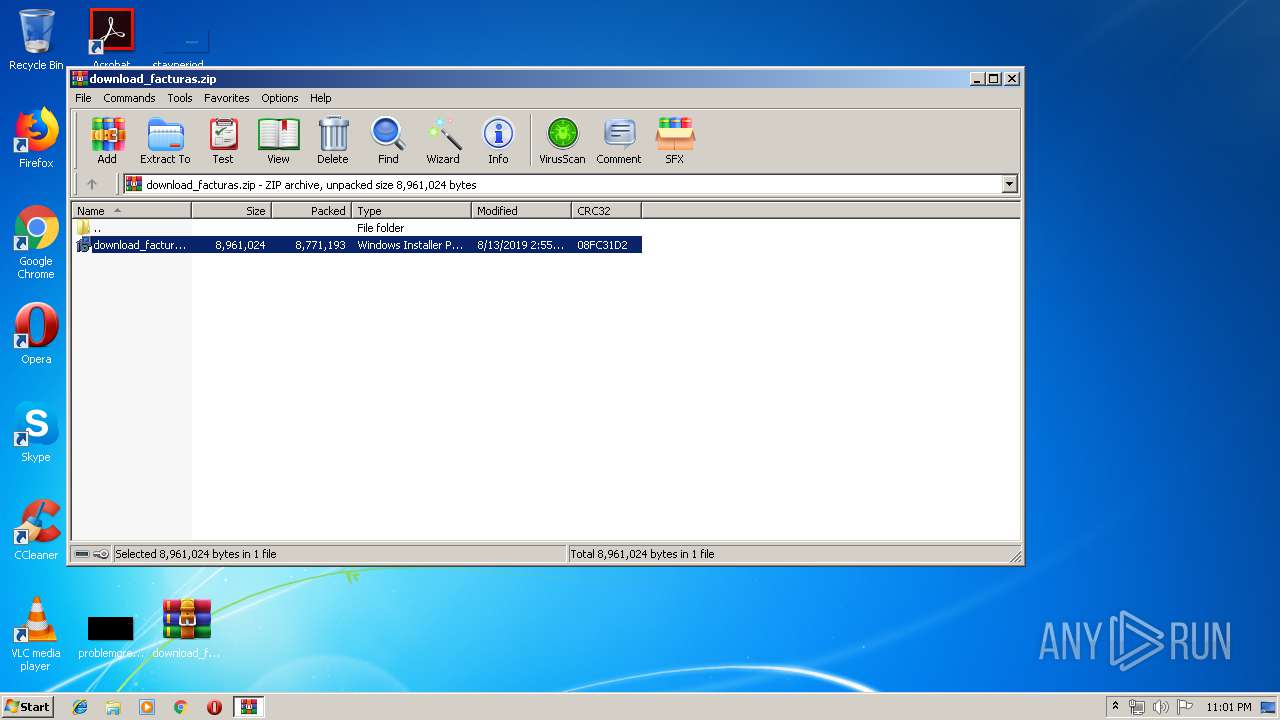
| File name: | download_facturas.zip |
| Full analysis: | https://app.any.run/tasks/ccb42ad9-4c39-45f2-b69e-3dfb7b8d9d58 |
| Verdict: | Malicious activity |
| Analysis date: | August 13, 2019, 22:00:43 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Indicators: | |
| MIME: | application/zip |
| File info: | Zip archive data, at least v2.0 to extract |
| MD5: | CF749FEA5CE8A857EF39EB2CEBCCE529 |
| SHA1: | 6FCA06EE3F46B0583282D4F9CB801317F6205CB9 |
| SHA256: | 639FC4CB43BF03B709C4912B64C8898B048330C6637B7290684023406C162C25 |
| SSDEEP: | 196608:5Gylekyrw+4QWmET+QSy4r0viDz/7QeDi7VZX0nYinxkiTh9bL:MySZ8+OvGgX43xpTh1L |
MALICIOUS
Loads dropped or rewritten executable
- SearchProtocolHost.exe (PID: 3744)
- VASG054BF4Z4CZ9.exe (PID: 2364)
Application was dropped or rewritten from another process
- VASG054BF4Z4CZ9.exe (PID: 2364)
Changes the autorun value in the registry
- VASG054BF4Z4CZ9.exe (PID: 2364)
SUSPICIOUS
Starts Microsoft Installer
- WinRAR.exe (PID: 4052)
Executable content was dropped or overwritten
- msiexec.exe (PID: 2324)
Disables Form Suggestion in IE
- VASG054BF4Z4CZ9.exe (PID: 2364)
Executed as Windows Service
- vssvc.exe (PID: 2452)
Executed via COM
- DrvInst.exe (PID: 3368)
INFO
Application launched itself
- msiexec.exe (PID: 2324)
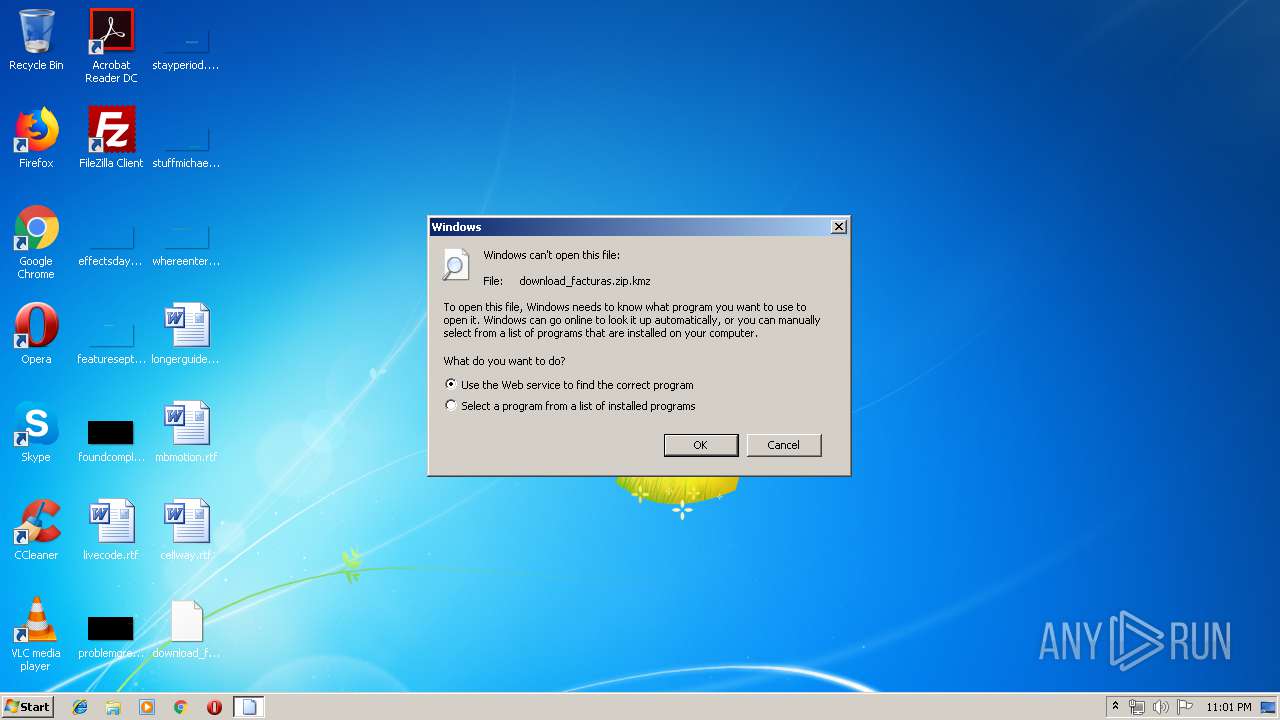
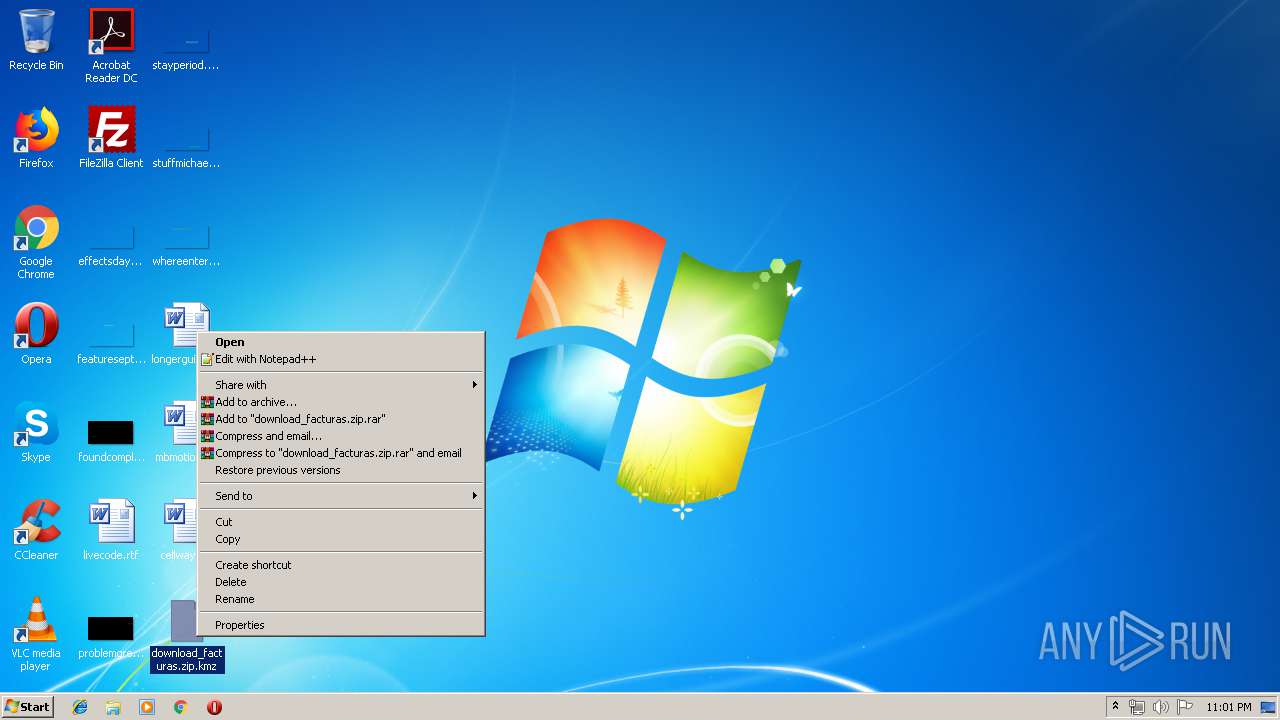
Manual execution by user
- WinRAR.exe (PID: 4052)
Searches for installed software
- msiexec.exe (PID: 2324)
Low-level read access rights to disk partition
- vssvc.exe (PID: 2452)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .kmz | | | Google Earth saved working session (60) |
|---|---|---|
| .zip | | | ZIP compressed archive (40) |
EXIF
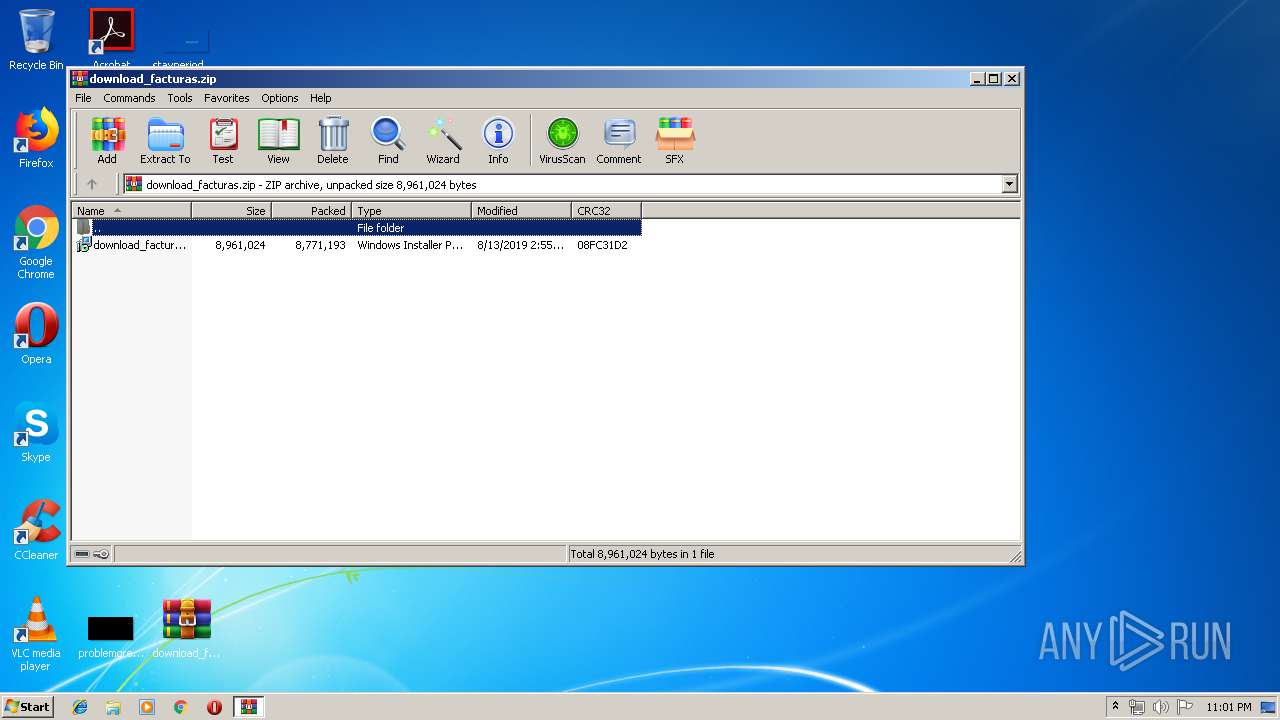
ZIP
| ZipRequiredVersion: | 20 |
|---|---|
| ZipBitFlag: | - |
| ZipCompression: | Deflated |
| ZipModifyDate: | 2019:08:13 10:55:17 |
| ZipCRC: | 0x08fc31d2 |
| ZipCompressedSize: | 8771193 |
| ZipUncompressedSize: | 8961024 |
| ZipFileName: | download_facturas.msi |
Total processes
45
Monitored processes
9
Malicious processes
1
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 1840 | "C:\Windows\system32\rundll32.exe" C:\Windows\system32\shell32.dll,OpenAs_RunDLL C:\Users\admin\Desktop\download_facturas.zip.kmz | C:\Windows\system32\rundll32.exe | — | explorer.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows host process (Rundll32) Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2272 | "C:\Windows\System32\msiexec.exe" /i "C:\Users\admin\AppData\Local\Temp\Rar$EXa4052.19122\download_facturas.msi" | C:\Windows\System32\msiexec.exe | — | WinRAR.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows® installer Exit code: 0 Version: 5.0.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2324 | C:\Windows\system32\msiexec.exe /V | C:\Windows\system32\msiexec.exe | services.exe | ||||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Windows® installer Exit code: 0 Version: 5.0.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2364 | "C:\Users\admin\Documents\VASG054BF4Z4CZ9.exe" | C:\Users\admin\Documents\VASG054BF4Z4CZ9.exe | msiexec.exe | ||||||||||||
User: admin Company: VMware, Inc. Integrity Level: MEDIUM Description: VMware NAT Service Exit code: 0 Version: 12.5.6 build-5528349 Modules
| |||||||||||||||
| 2452 | C:\Windows\system32\vssvc.exe | C:\Windows\system32\vssvc.exe | — | services.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Microsoft® Volume Shadow Copy Service Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 2904 | C:\Windows\system32\MsiExec.exe -Embedding C186D0F50334C90F29DF033849A7A7DC | C:\Windows\system32\MsiExec.exe | — | msiexec.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows® installer Exit code: 0 Version: 5.0.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3368 | DrvInst.exe "1" "200" "STORAGE\VolumeSnapshot\HarddiskVolumeSnapshot22" "" "" "695c3f483" "00000000" "00000578" "00000580" | C:\Windows\system32\DrvInst.exe | — | svchost.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Driver Installation Module Exit code: 0 Version: 6.1.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 3744 | "C:\Windows\system32\SearchProtocolHost.exe" Global\UsGthrFltPipeMssGthrPipe13_ Global\UsGthrCtrlFltPipeMssGthrPipe13 1 -2147483646 "Software\Microsoft\Windows Search" "Mozilla/4.0 (compatible; MSIE 6.0; Windows NT; MS Search 4.0 Robot)" "C:\ProgramData\Microsoft\Search\Data\Temp\usgthrsvc" "DownLevelDaemon" | C:\Windows\System32\SearchProtocolHost.exe | — | SearchIndexer.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Microsoft Windows Search Protocol Host Exit code: 0 Version: 7.00.7600.16385 (win7_rtm.090713-1255) Modules
| |||||||||||||||
| 4052 | "C:\Program Files\WinRAR\WinRAR.exe" "C:\Users\admin\Desktop\download_facturas.zip" | C:\Program Files\WinRAR\WinRAR.exe | — | explorer.exe | |||||||||||
User: admin Company: Alexander Roshal Integrity Level: MEDIUM Description: WinRAR archiver Exit code: 0 Version: 5.60.0 Modules
| |||||||||||||||
Total events
932
Read events
738
Write events
182
Delete events
12
Modification events
| (PID) Process: | (4052) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtBMP |
Value: | |||
| (PID) Process: | (4052) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\Interface\Themes |
| Operation: | write | Name: | ShellExtIcon |
Value: | |||
| (PID) Process: | (4052) WinRAR.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\MuiCache\72\52C64B7E |
| Operation: | write | Name: | LanguageList |
Value: en-US | |||
| (PID) Process: | (4052) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\ArcHistory |
| Operation: | write | Name: | 0 |
Value: C:\Users\admin\Desktop\download_facturas.zip | |||
| (PID) Process: | (4052) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | name |
Value: 120 | |||
| (PID) Process: | (4052) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | size |
Value: 80 | |||
| (PID) Process: | (4052) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | type |
Value: 120 | |||
| (PID) Process: | (4052) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\WinRAR\FileList\FileColumnWidths |
| Operation: | write | Name: | mtime |
Value: 100 | |||
| (PID) Process: | (4052) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (4052) WinRAR.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
Executable files
2
Suspicious files
4
Text files
30
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 4052 | WinRAR.exe | C:\Users\admin\AppData\Local\Temp\Rar$EXa4052.19122\download_facturas.msi | — | |
MD5:— | SHA256:— | |||
| 2324 | msiexec.exe | C:\System Volume Information\SPP\metadata-2 | — | |
MD5:— | SHA256:— | |||
| 2324 | msiexec.exe | C:\Windows\Installer\376e6e.msi | — | |
MD5:— | SHA256:— | |||
| 2324 | msiexec.exe | C:\Windows\Installer\MSI7071.tmp | — | |
MD5:— | SHA256:— | |||
| 2324 | msiexec.exe | C:\Windows\Installer\MSI71E9.tmp | — | |
MD5:— | SHA256:— | |||
| 2324 | msiexec.exe | C:\Users\admin\AppData\Local\Temp\~DFB9244FBC62666F7B.TMP | — | |
MD5:— | SHA256:— | |||
| 2324 | msiexec.exe | C:\Windows\Installer\376e70.ipi | — | |
MD5:— | SHA256:— | |||
| 2324 | msiexec.exe | C:\Windows\Installer\MSI7277.tmp | — | |
MD5:— | SHA256:— | |||
| 2324 | msiexec.exe | C:\Config.Msi\376e71.rbs | — | |
MD5:— | SHA256:— | |||
| 2324 | msiexec.exe | C:\Users\admin\AppData\Local\Temp\~DFFA21F0BB335877C3.TMP | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
0
TCP/UDP connections
0
DNS requests
0
Threats
0
HTTP requests
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
DNS requests
Threats
Process | Message |
|---|---|
VASG054BF4Z4CZ9.exe | CodeSet_Init: no ICU
|