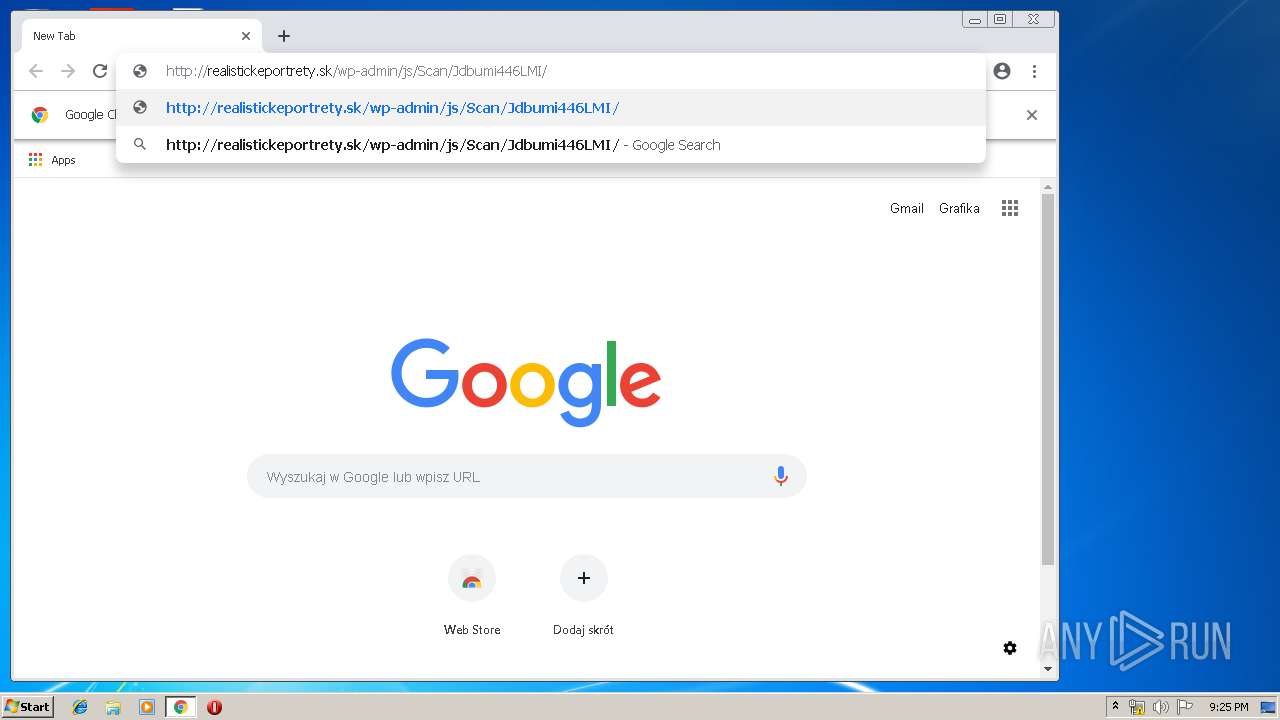
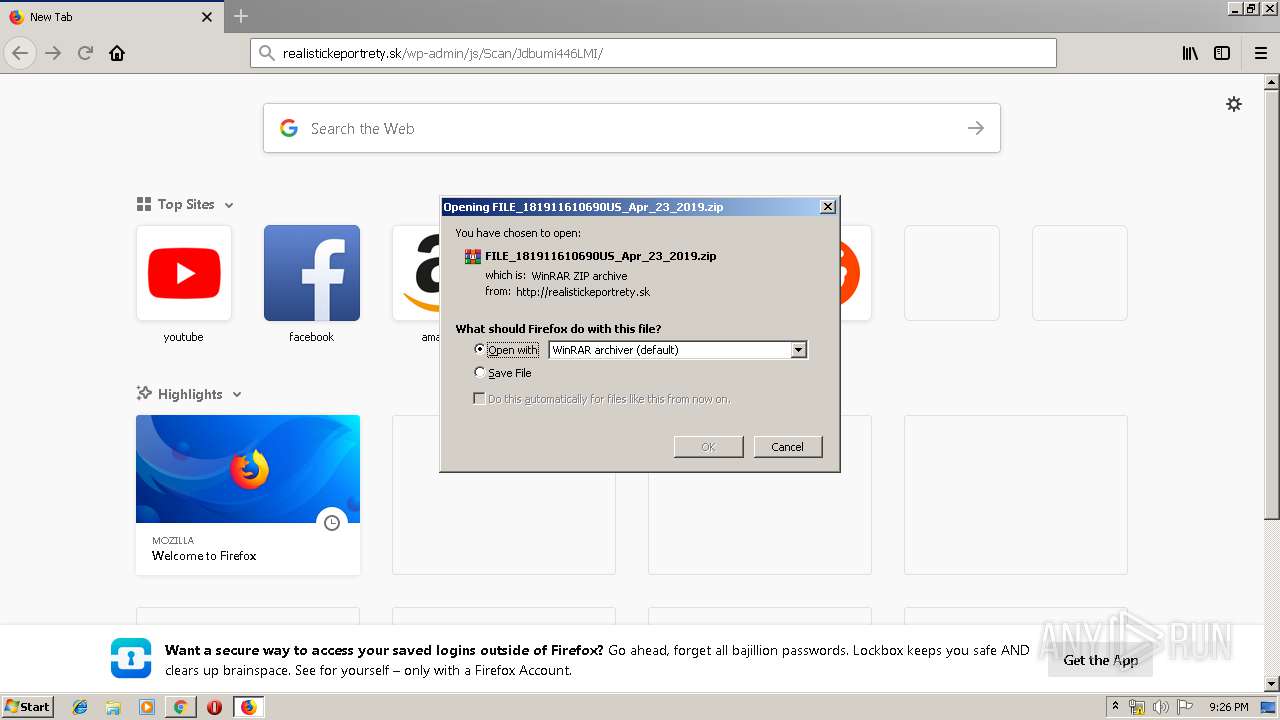
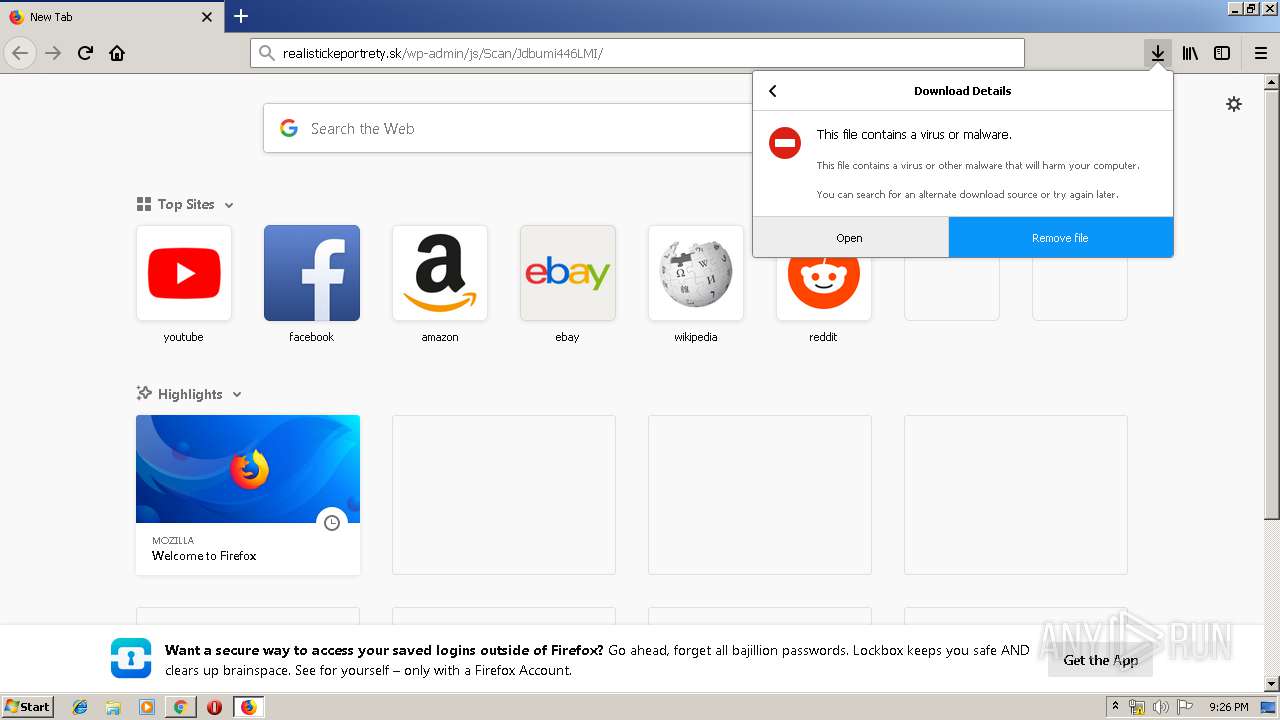
| URL: | http://realistickeportrety.sk/wp-admin/js/Scan/Jdbumi446LMI/ |
| Full analysis: | https://app.any.run/tasks/b687c41d-2209-4d3f-b020-a39f1d436278 |
| Verdict: | Malicious activity |
| Threats: | Emotet is one of the most dangerous trojans ever created. Over the course of its lifetime, it was upgraded to become a very destructive malware. It targets mostly corporate victims but even private users get infected in mass spam email campaigns. |
| Analysis date: | April 23, 2019, 20:24:18 |
| OS: | Windows 7 Professional Service Pack 1 (build: 7601, 32 bit) |
| Tags: | |
| Indicators: | |
| MD5: | 0C86D070AB5622FDFBC5C2A82DC648AF |
| SHA1: | EA68952C71E599CCA5AC1EC6ECA672916C5242B3 |
| SHA256: | 639EA51DAA9AF257652E903339CB834EFE8C56C3C39E197D22B4E5BE1DA8135B |
| SSDEEP: | 3:N1KMfMWtKXRX7sEBIH4KZlsKn:CMkNXRIVYKZt |
MALICIOUS
Application was dropped or rewritten from another process
- phawqkmdb.exe (PID: 3112)
- phawqkmdb.exe (PID: 1860)
- soundser.exe (PID: 2840)
- soundser.exe (PID: 272)
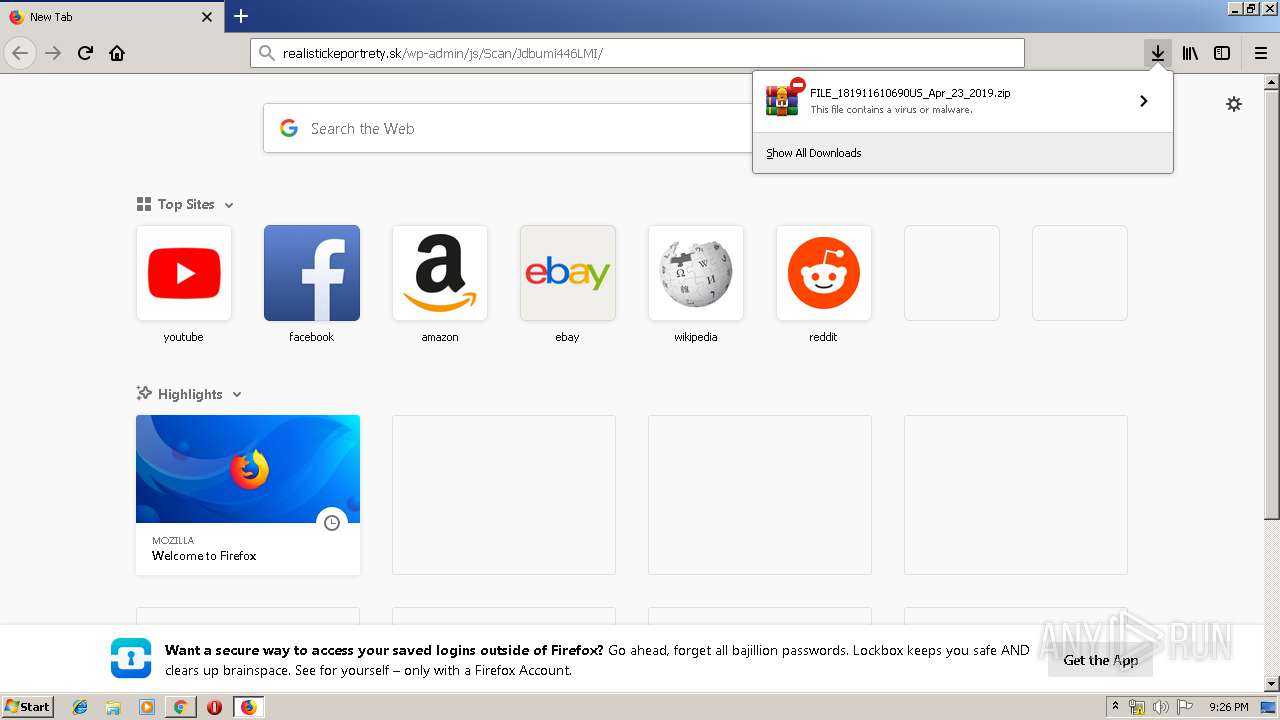
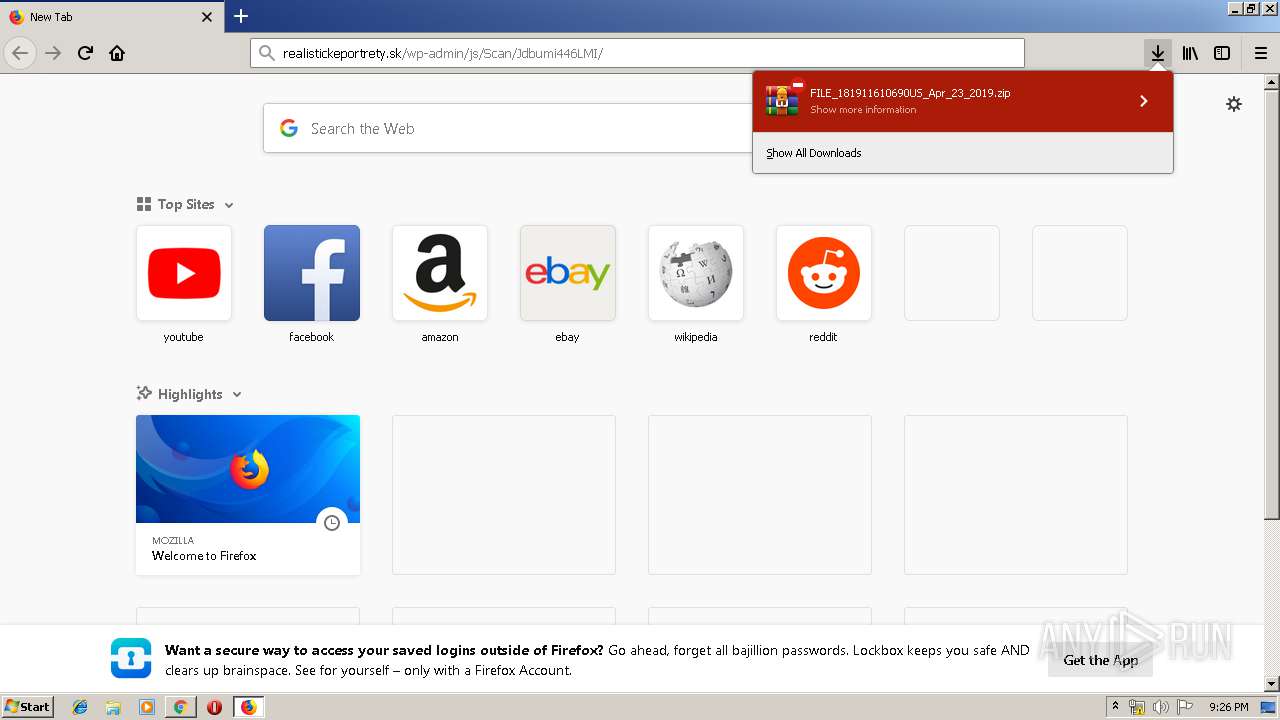
Downloads executable files from the Internet
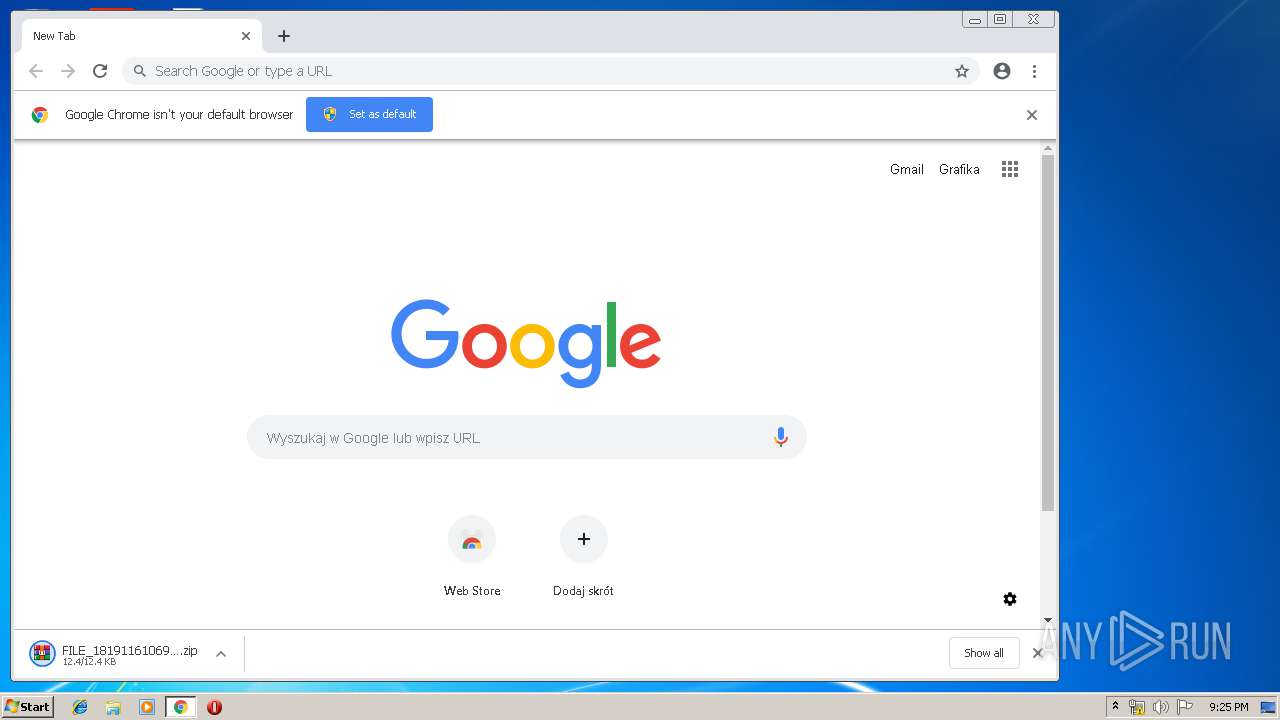
- WScript.exe (PID: 1088)
EMOTET was detected
- soundser.exe (PID: 272)
Emotet process was detected
- soundser.exe (PID: 2840)
Changes the autorun value in the registry
- soundser.exe (PID: 272)
Connects to CnC server
- soundser.exe (PID: 272)
SUSPICIOUS
Creates files in the user directory
- WScript.exe (PID: 1088)
Modifies files in Chrome extension folder
- chrome.exe (PID: 3332)
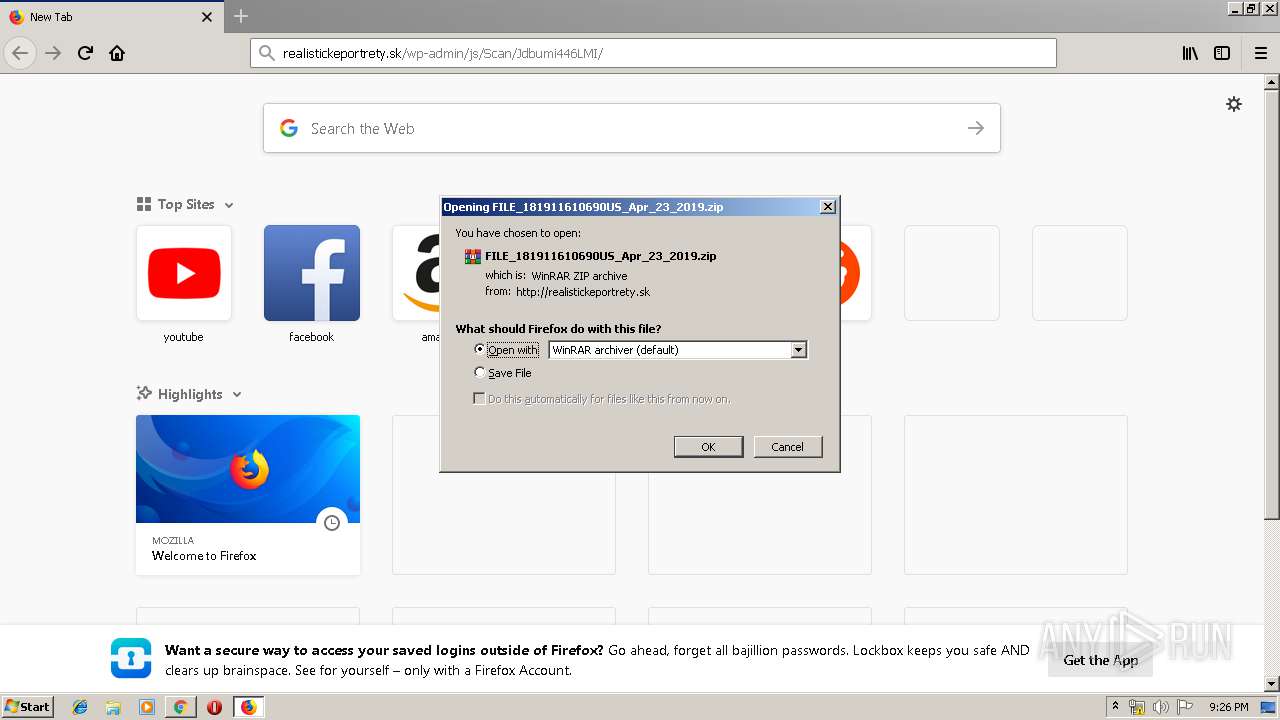
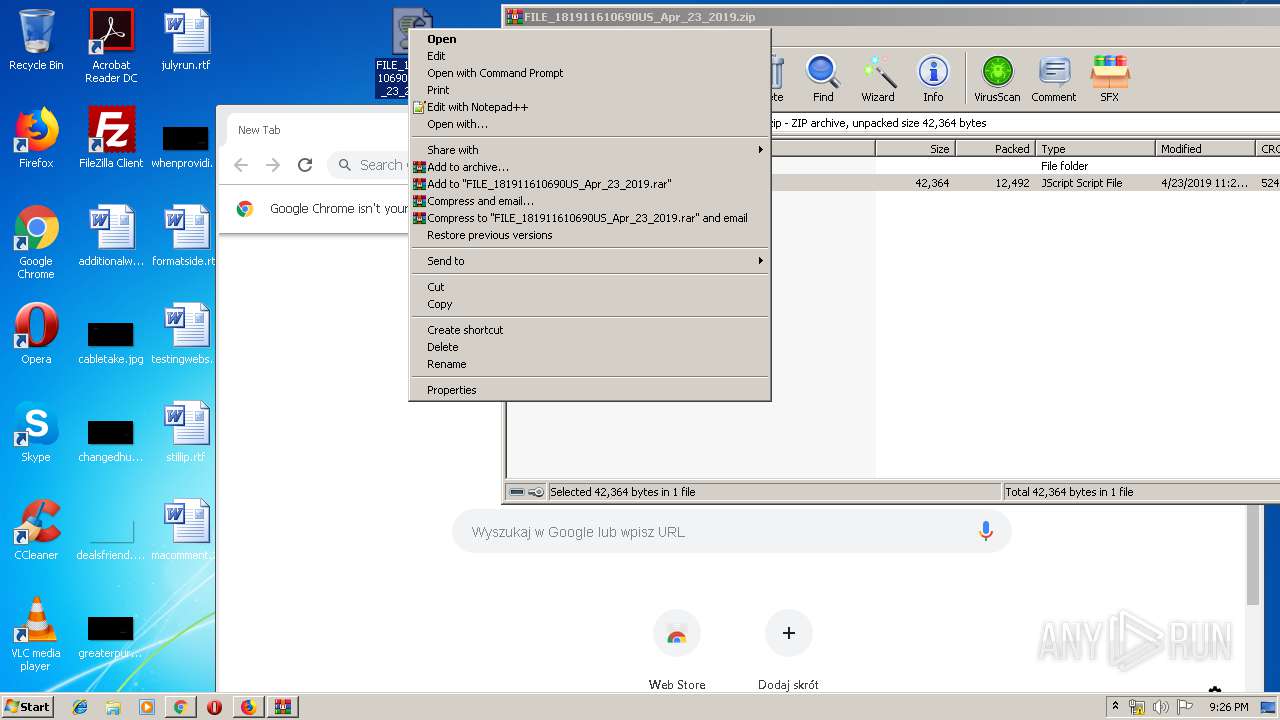
Executes scripts
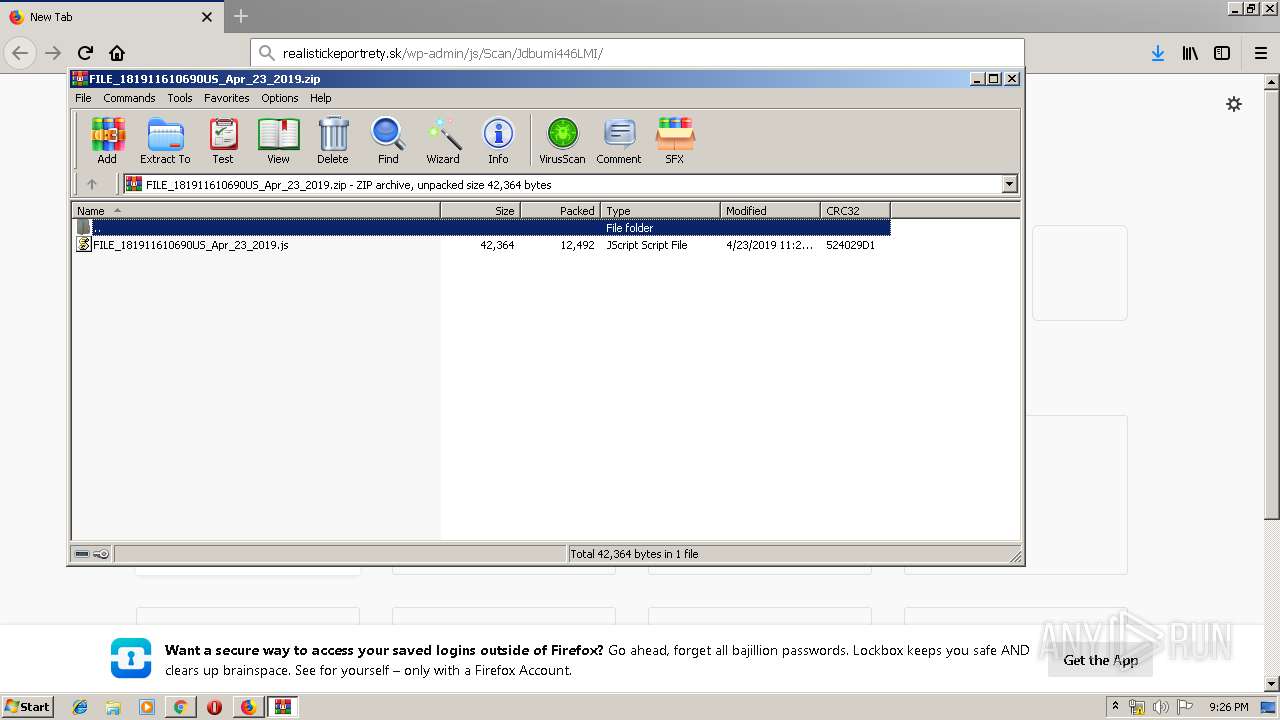
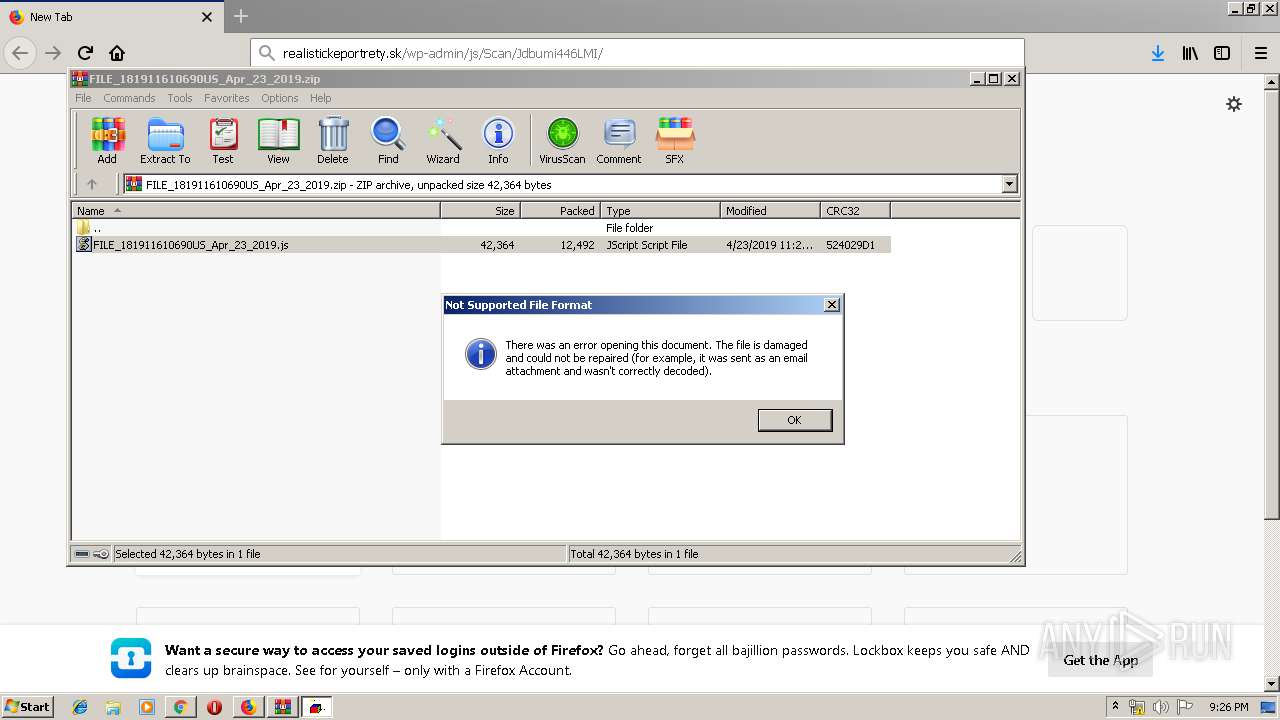
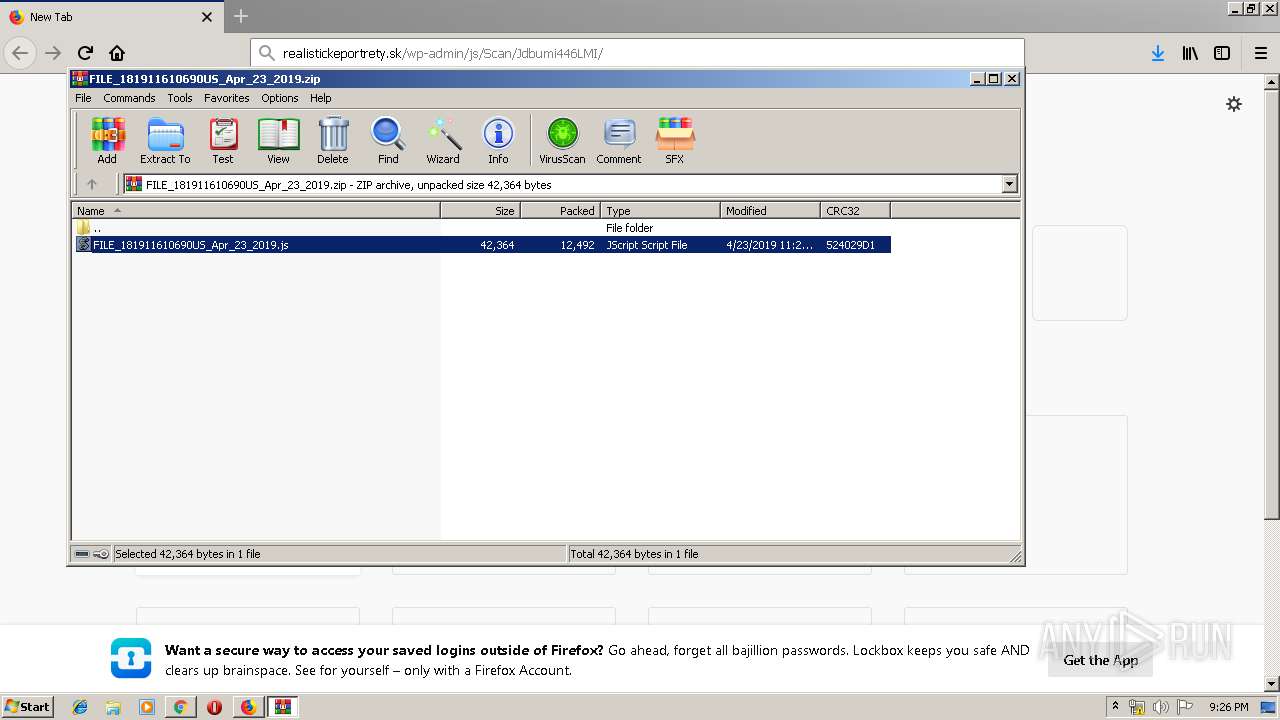
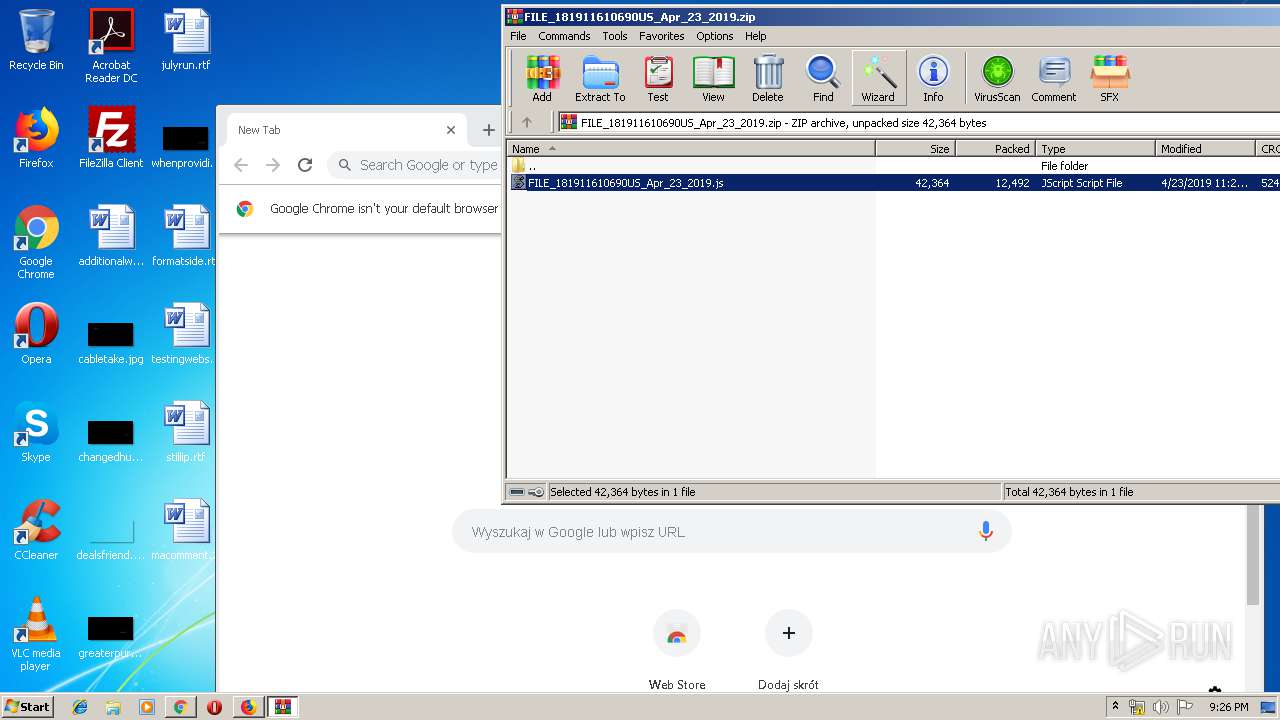
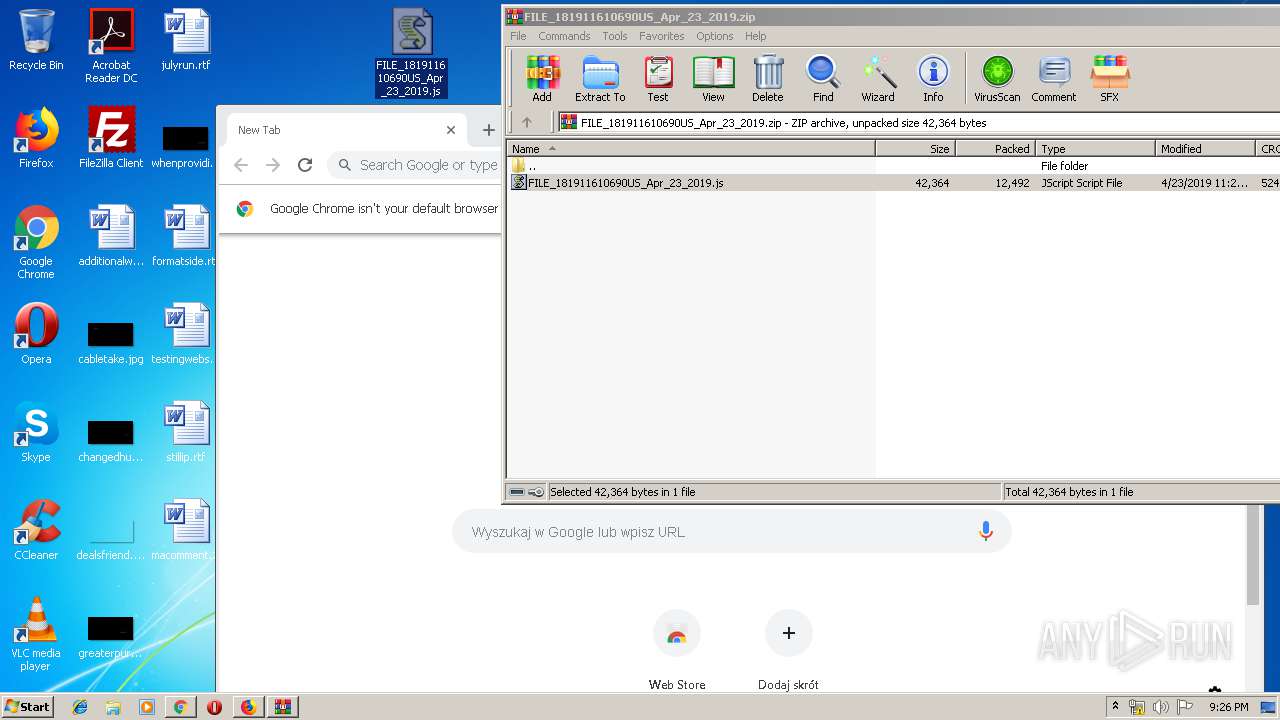
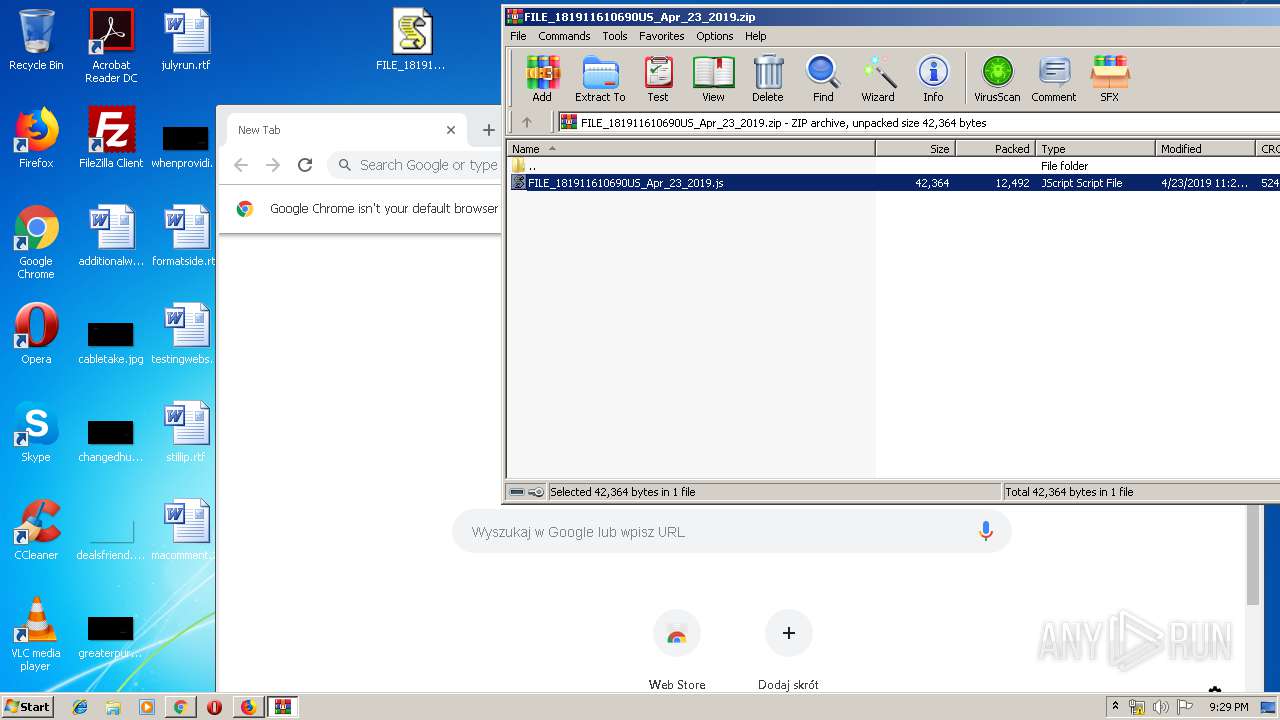
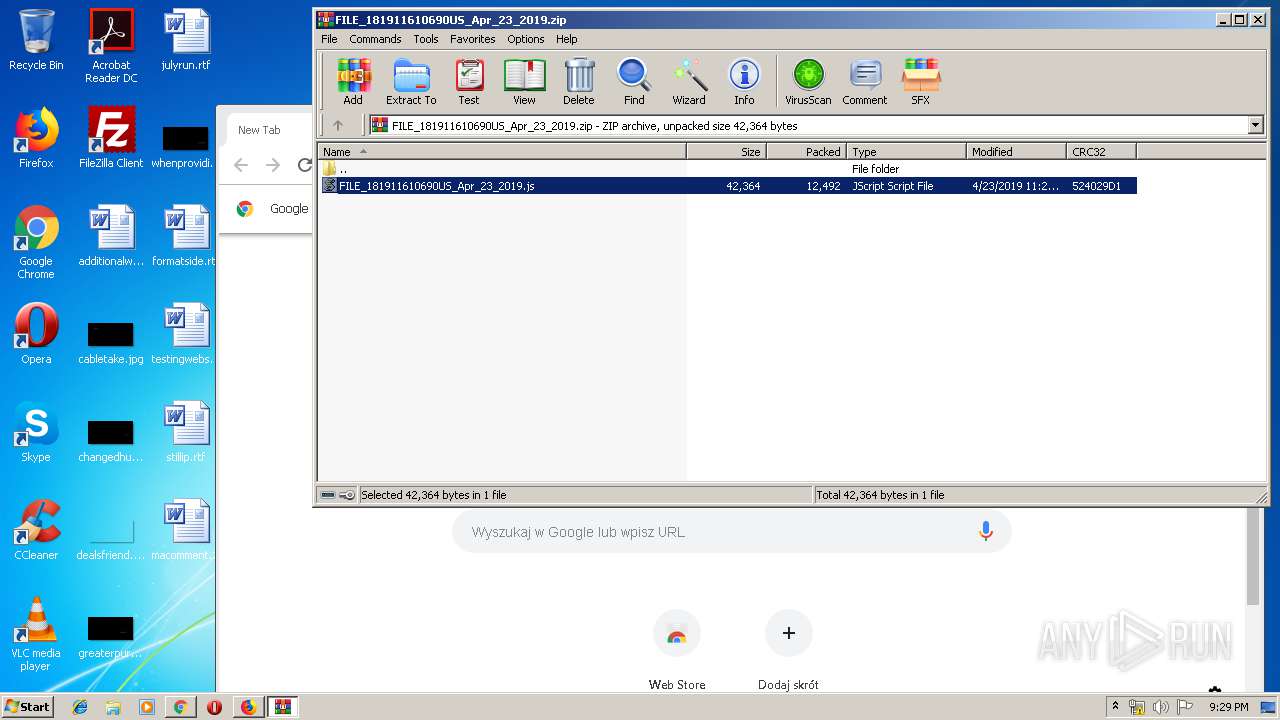
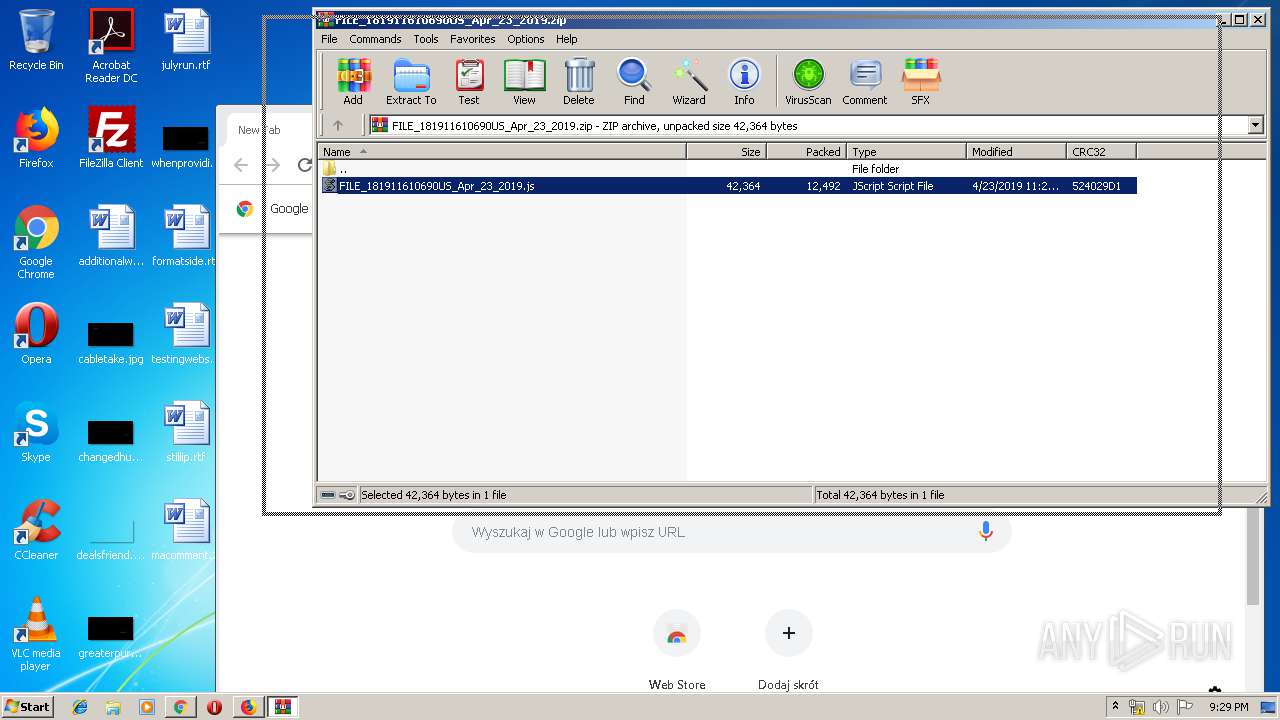
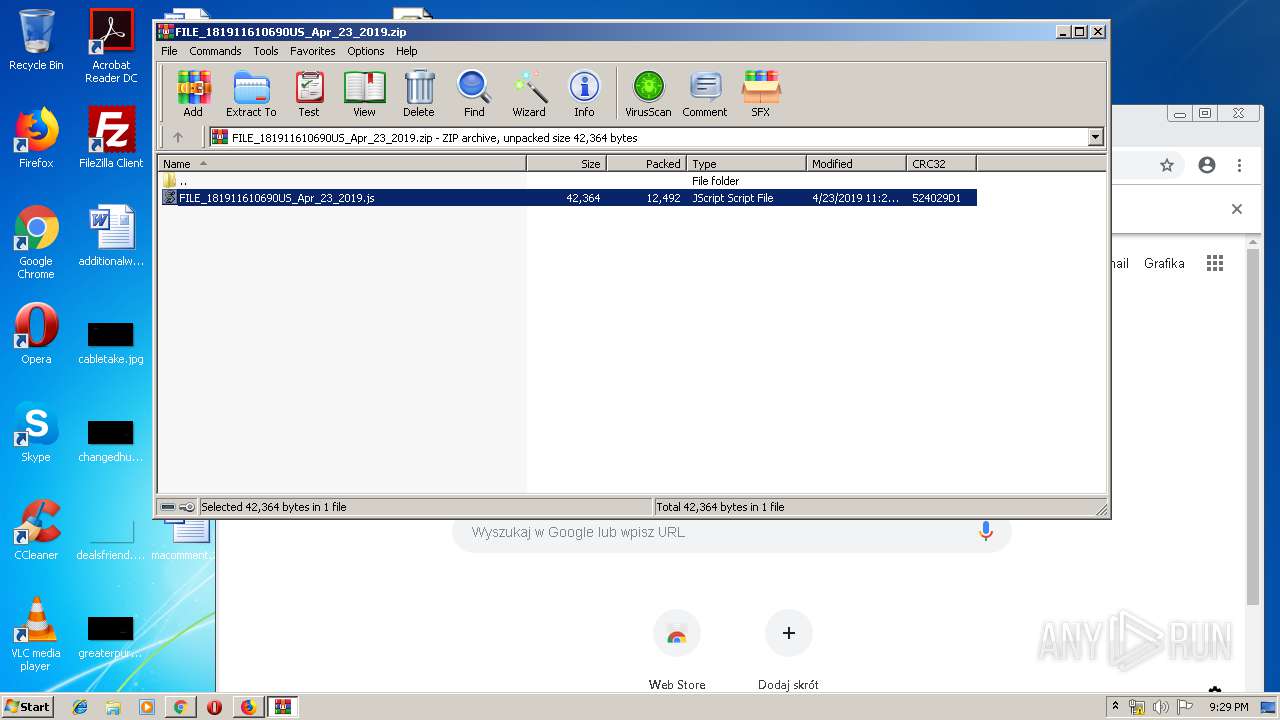
- WinRAR.exe (PID: 1404)
Executable content was dropped or overwritten
- WScript.exe (PID: 1088)
- phawqkmdb.exe (PID: 1860)
Starts itself from another location
- phawqkmdb.exe (PID: 1860)
Application launched itself
- phawqkmdb.exe (PID: 3112)
Connects to server without host name
- soundser.exe (PID: 272)
INFO
Changes internet zones settings
- iexplore.exe (PID: 2524)
Creates files in the user directory
- iexplore.exe (PID: 2524)
- firefox.exe (PID: 536)
- iexplore.exe (PID: 1564)
Application launched itself
- firefox.exe (PID: 536)
- iexplore.exe (PID: 2524)
- chrome.exe (PID: 3332)
Reads Internet Cache Settings
- iexplore.exe (PID: 1564)
Reads CPU info
- firefox.exe (PID: 536)
Reads settings of System Certificates
- firefox.exe (PID: 536)
Dropped object may contain Bitcoin addresses
- firefox.exe (PID: 536)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
Total processes
72
Monitored processes
38
Malicious processes
6
Suspicious processes
1
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 272 | --3ab57678 | C:\Users\admin\AppData\Local\soundser\soundser.exe | soundser.exe | ||||||||||||
User: admin Integrity Level: MEDIUM Exit code: 0 Modules
| |||||||||||||||
| 324 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=gpu-process --field-trial-handle=976,4033116576142292109,9482397887761321067,131072 --enable-features=PasswordImport --gpu-preferences=KAAAAAAAAACAAwAAAQAAAAAAAAAAAGAAAAAAAAEAAAAIAAAAAAAAACgAAAAEAAAAIAAAAAAAAAAoAAAAAAAAADAAAAAAAAAAOAAAAAAAAAAQAAAAAAAAAAAAAAAFAAAAEAAAAAAAAAAAAAAABgAAABAAAAAAAAAAAQAAAAUAAAAQAAAAAAAAAAEAAAAGAAAA --service-request-channel-token=2040312478867910334 --mojo-platform-channel-handle=996 --ignored=" --type=renderer " /prefetch:2 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 536 | "C:\Program Files\Mozilla Firefox\firefox.exe" | C:\Program Files\Mozilla Firefox\firefox.exe | explorer.exe | ||||||||||||
User: admin Company: Mozilla Corporation Integrity Level: MEDIUM Description: Firefox Exit code: 0 Version: 65.0.2 Modules
| |||||||||||||||
| 832 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=976,4033116576142292109,9482397887761321067,131072 --enable-features=PasswordImport --disable-gpu-compositing --service-pipe-token=753748858219430435 --lang=en-US --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=753748858219430435 --renderer-client-id=15 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=3932 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 936 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=976,4033116576142292109,9482397887761321067,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=14444580663317838143 --mojo-platform-channel-handle=4468 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 1024 | "C:\Program Files\Mozilla Firefox\firefox.exe" -contentproc --channel="536.13.984424665\959632965" -childID 2 -isForBrowser -prefsHandle 2536 -prefMapHandle 2540 -prefsLen 216 -prefMapSize 180950 -schedulerPrefs 0001,2 -parentBuildID 20190225143501 -greomni "C:\Program Files\Mozilla Firefox\omni.ja" -appomni "C:\Program Files\Mozilla Firefox\browser\omni.ja" -appdir "C:\Program Files\Mozilla Firefox\browser" - 536 "\\.\pipe\gecko-crash-server-pipe.536" 2552 tab | C:\Program Files\Mozilla Firefox\firefox.exe | firefox.exe | ||||||||||||
User: admin Company: Mozilla Corporation Integrity Level: LOW Description: Firefox Exit code: 0 Version: 65.0.2 Modules
| |||||||||||||||
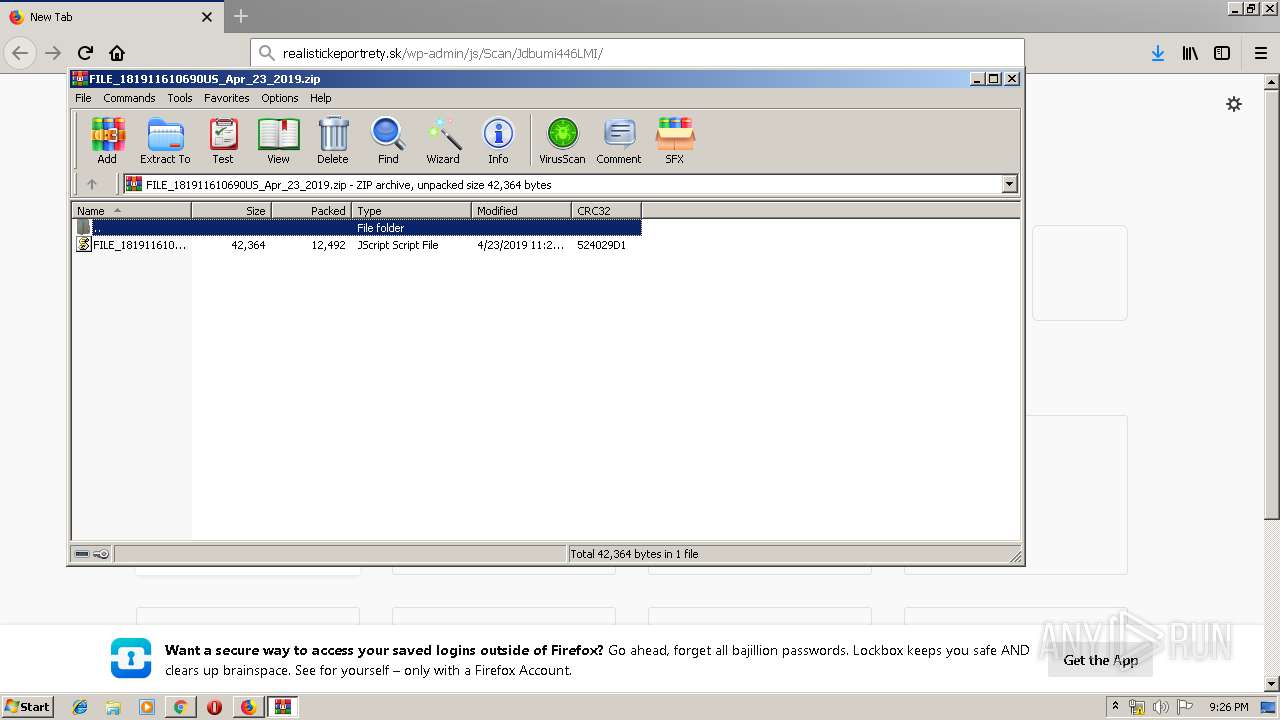
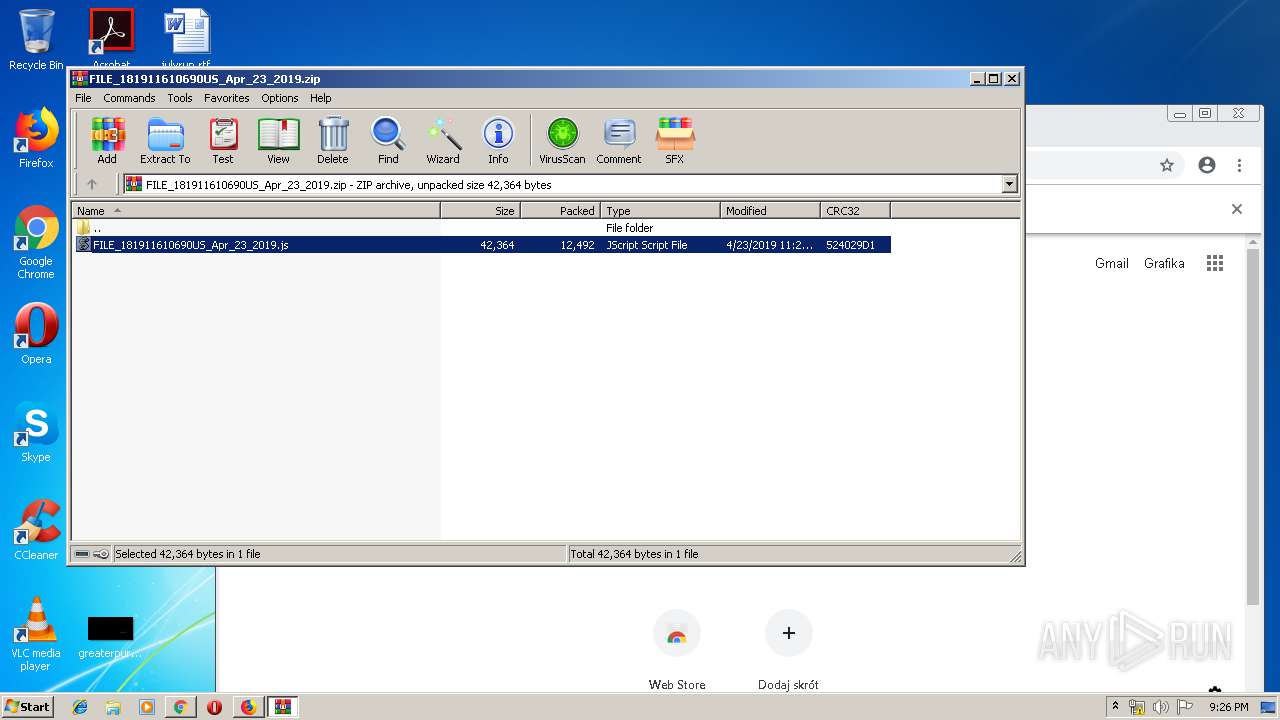
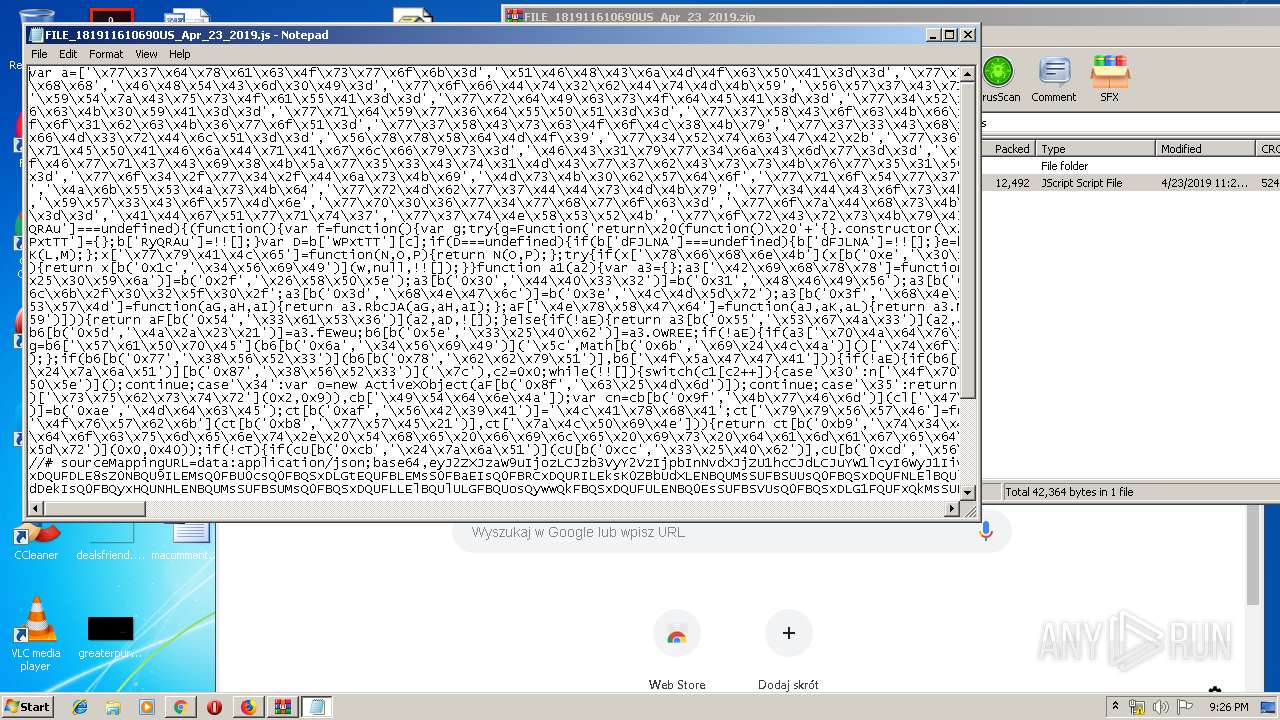
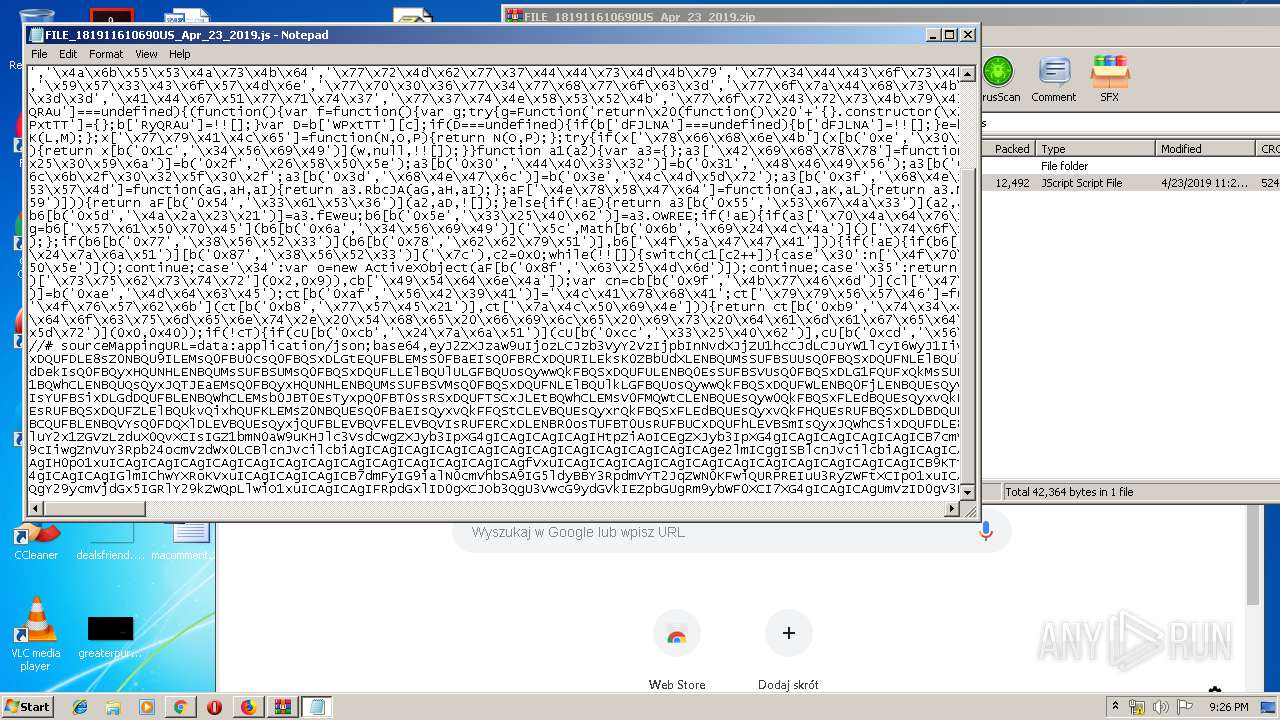
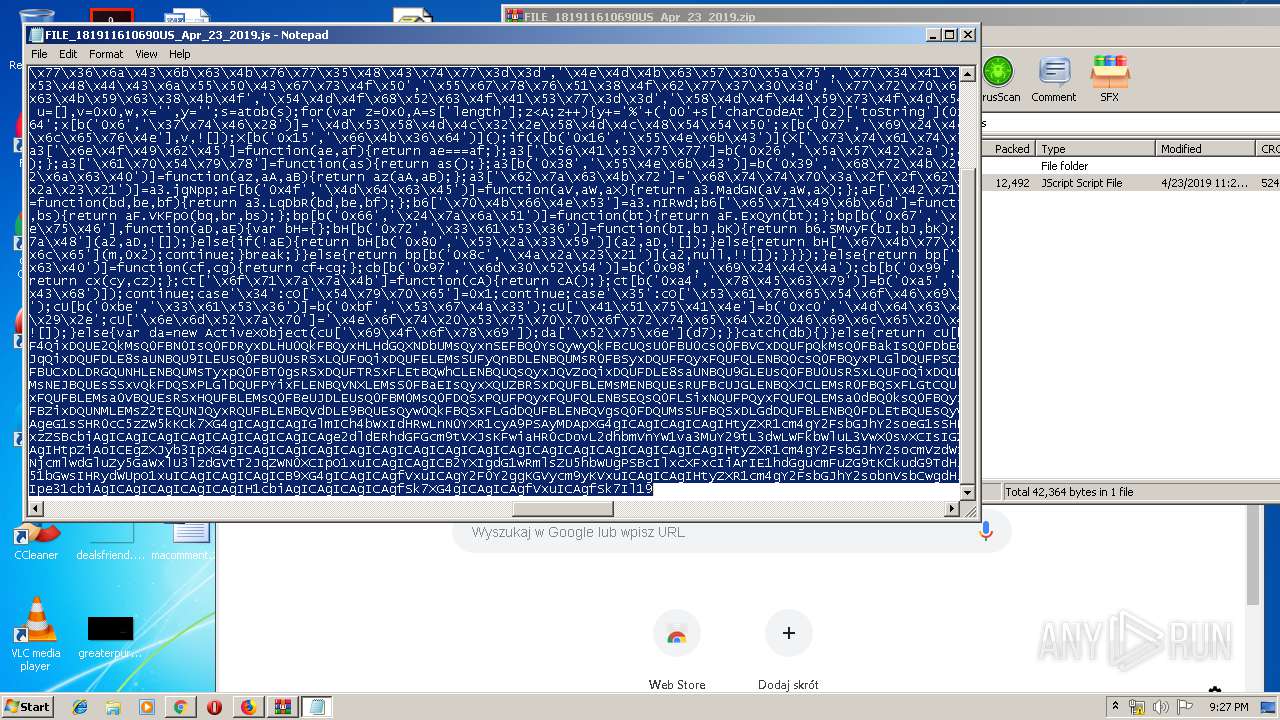
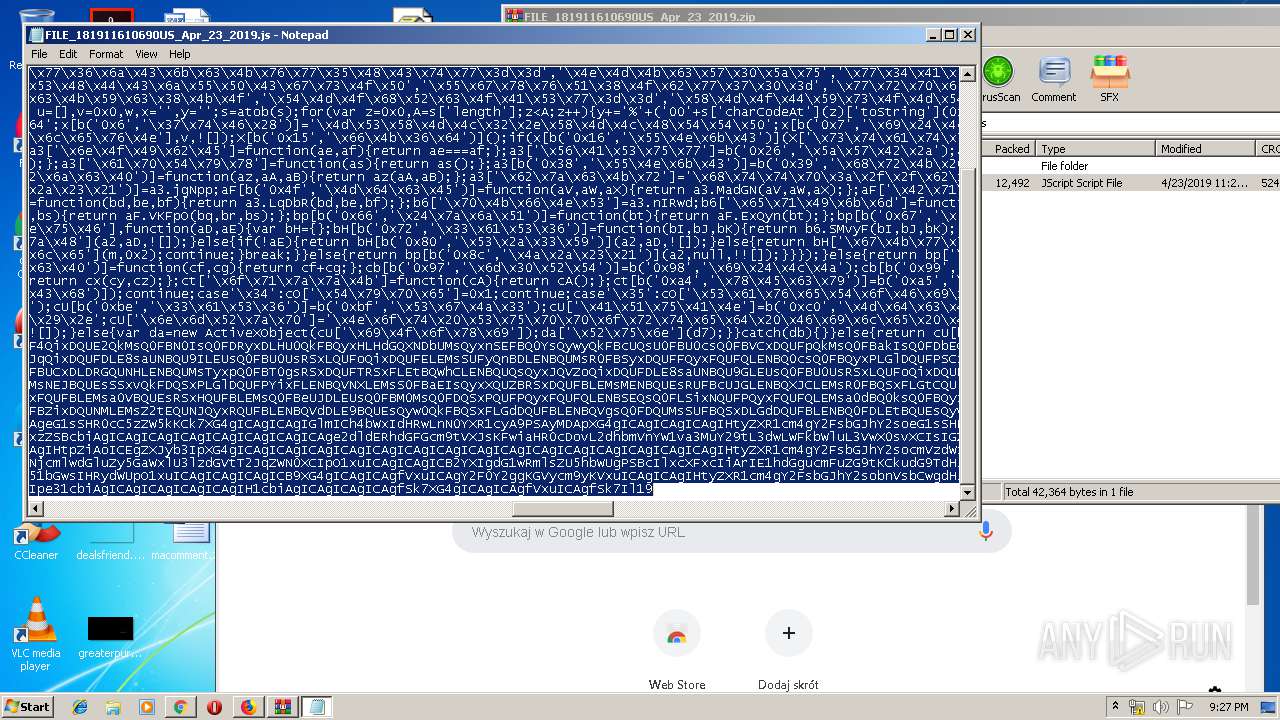
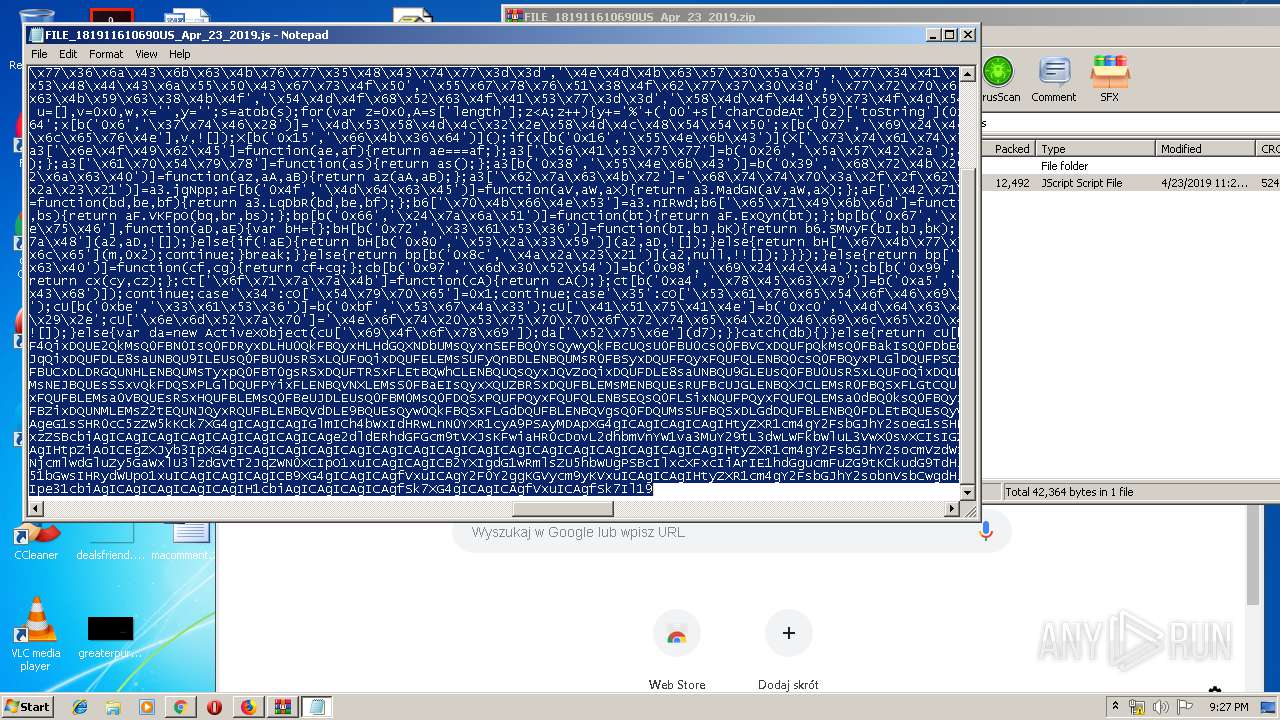
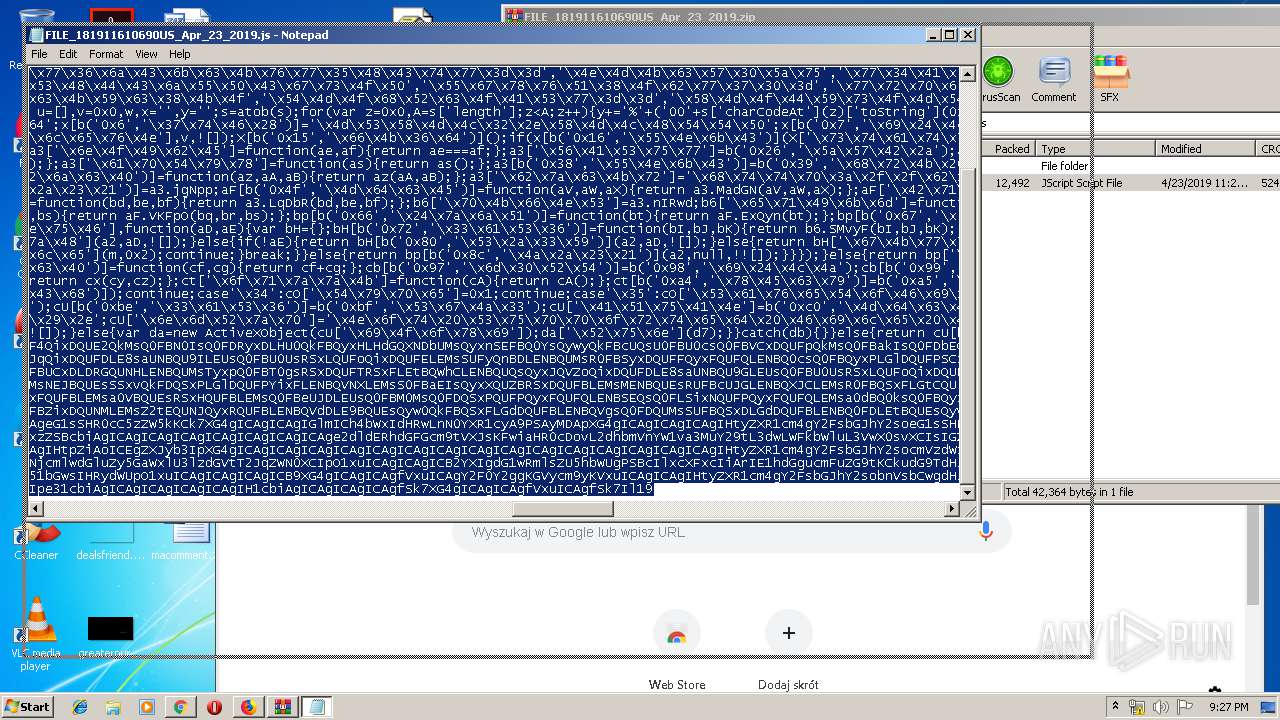
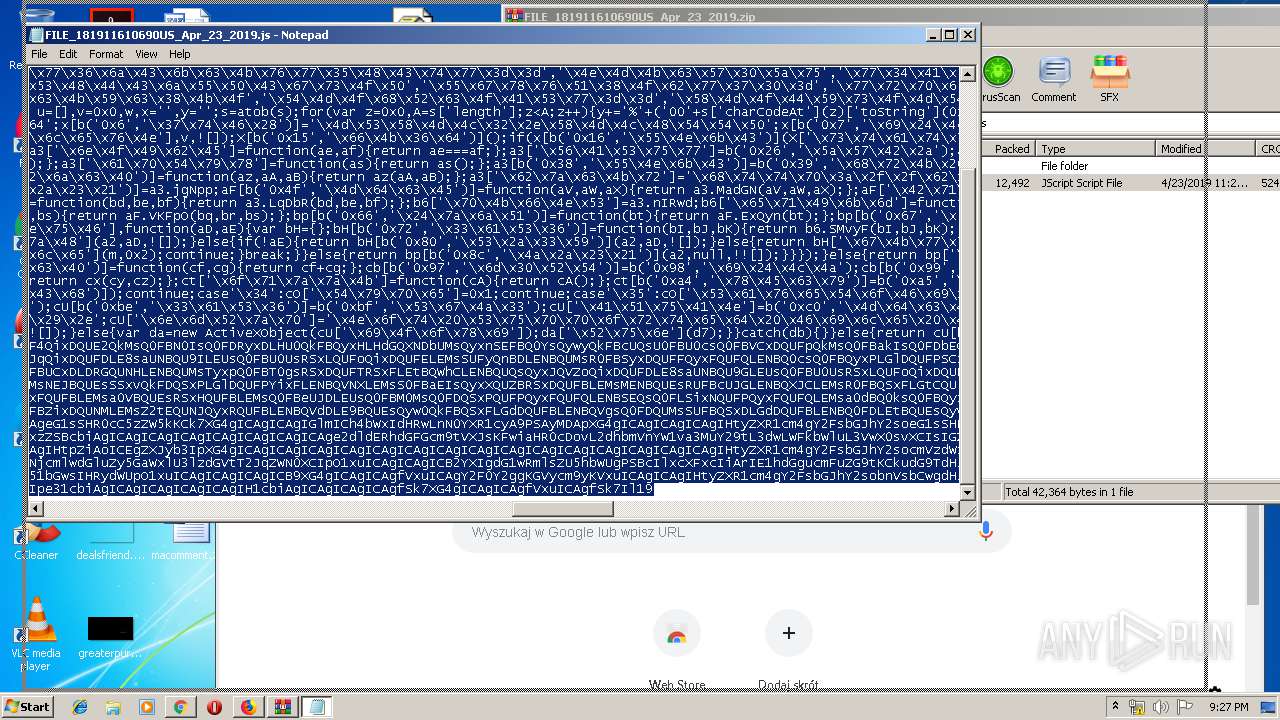
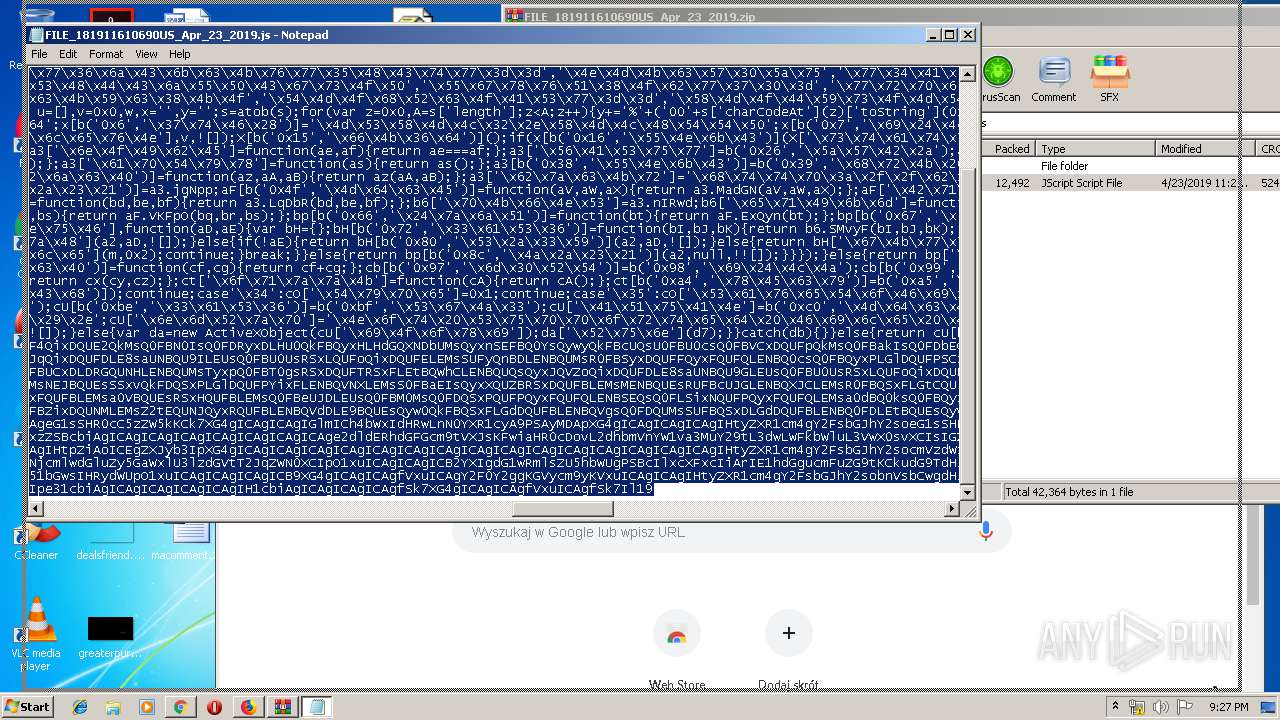
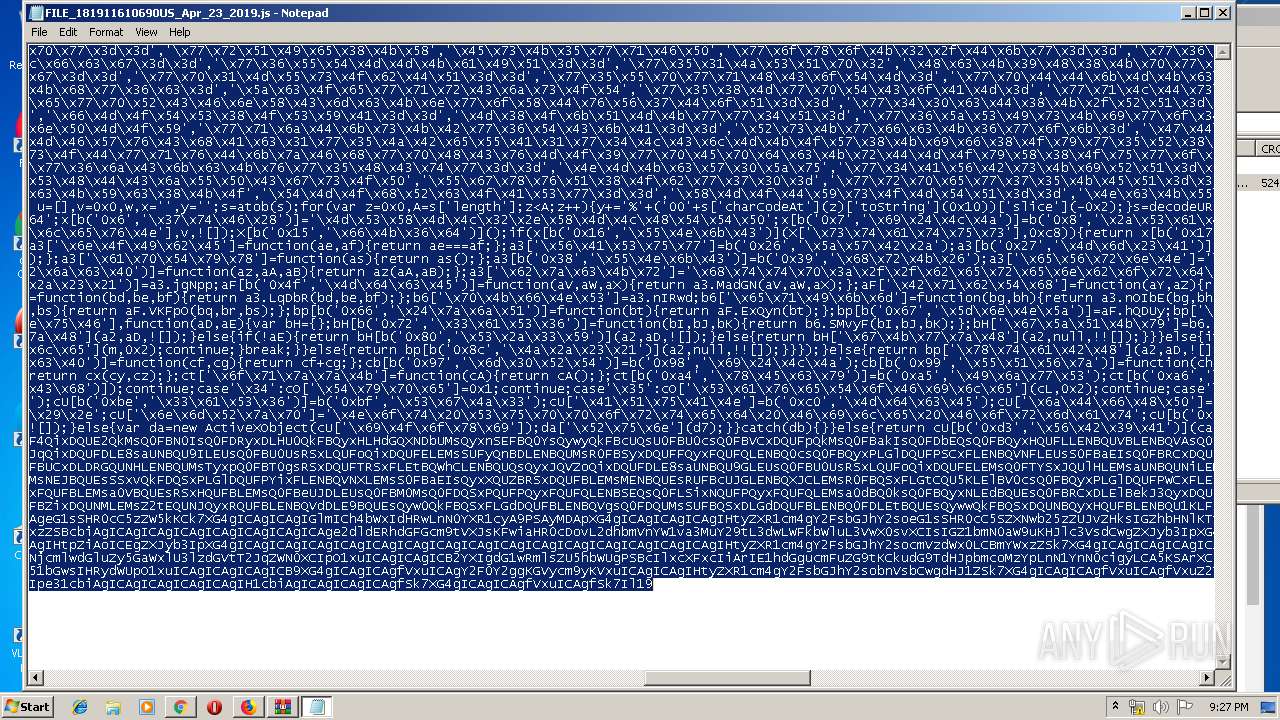
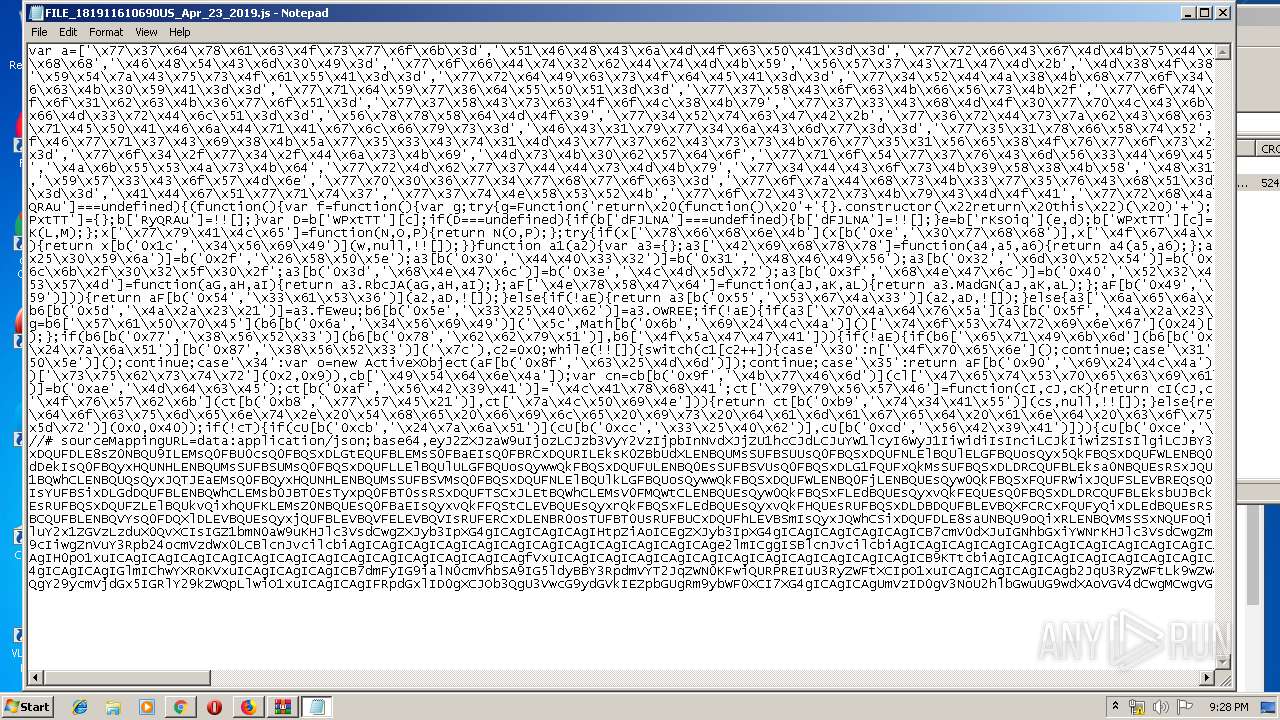
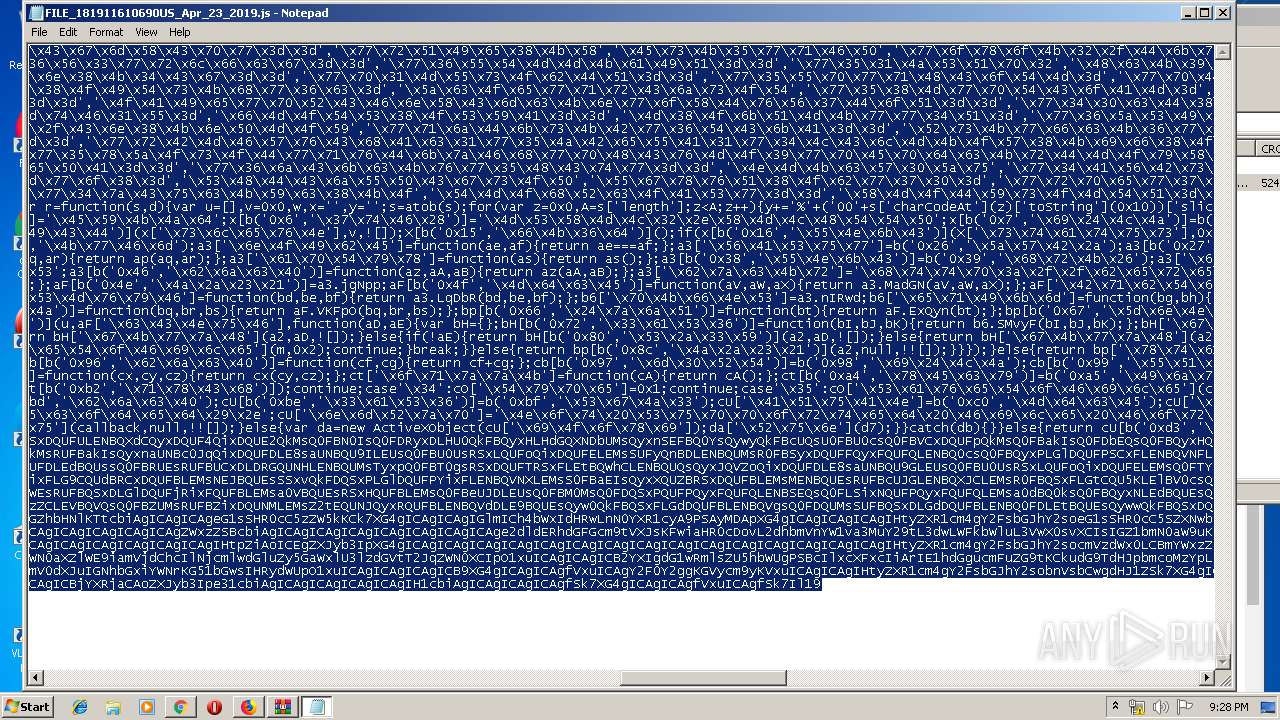
| 1088 | "C:\Windows\System32\WScript.exe" "C:\Users\admin\AppData\Local\Temp\Rar$DIa1404.19868\FILE_181911610690US_Apr_23_2019.js" | C:\Windows\System32\WScript.exe | WinRAR.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Microsoft ® Windows Based Script Host Exit code: 0 Version: 5.8.7600.16385 Modules
| |||||||||||||||
| 1160 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=renderer --field-trial-handle=976,4033116576142292109,9482397887761321067,131072 --enable-features=PasswordImport --service-pipe-token=3052934958760685620 --lang=en-US --instant-process --enable-offline-auto-reload --enable-offline-auto-reload-visible-only --device-scale-factor=1 --num-raster-threads=2 --enable-main-frame-before-activation --service-request-channel-token=3052934958760685620 --renderer-client-id=5 --no-v8-untrusted-code-mitigations --mojo-platform-channel-handle=2008 /prefetch:1 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
| 1248 | "C:\Program Files\Mozilla Firefox\firefox.exe" -contentproc --channel="536.0.1105382838\195522397" -parentBuildID 20190225143501 -greomni "C:\Program Files\Mozilla Firefox\omni.ja" -appomni "C:\Program Files\Mozilla Firefox\browser\omni.ja" -appdir "C:\Program Files\Mozilla Firefox\browser" - "C:\Users\admin\AppData\LocalLow\Mozilla\Temp-{ce348e4c-7d33-445e-89f9-60108c51bcaf}" 536 "\\.\pipe\gecko-crash-server-pipe.536" 1136 gpu | C:\Program Files\Mozilla Firefox\firefox.exe | — | firefox.exe | |||||||||||
User: admin Company: Mozilla Corporation Integrity Level: MEDIUM Description: Firefox Exit code: 0 Version: 65.0.2 Modules
| |||||||||||||||
| 1304 | "C:\Program Files\Google\Chrome\Application\chrome.exe" --type=utility --field-trial-handle=976,4033116576142292109,9482397887761321067,131072 --enable-features=PasswordImport --lang=en-US --service-sandbox-type=utility --service-request-channel-token=4175785668522791002 --mojo-platform-channel-handle=4116 --ignored=" --type=renderer " /prefetch:8 | C:\Program Files\Google\Chrome\Application\chrome.exe | — | chrome.exe | |||||||||||
User: admin Company: Google Inc. Integrity Level: LOW Description: Google Chrome Exit code: 0 Version: 73.0.3683.75 Modules
| |||||||||||||||
Total events
2 790
Read events
2 582
Write events
202
Delete events
6
Modification events
| (PID) Process: | (2524) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main |
| Operation: | write | Name: | CompatibilityFlags |
Value: 0 | |||
| (PID) Process: | (2524) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | UNCAsIntranet |
Value: 0 | |||
| (PID) Process: | (2524) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\ZoneMap |
| Operation: | write | Name: | AutoDetect |
Value: 1 | |||
| (PID) Process: | (2524) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Zones |
| Operation: | write | Name: | SecuritySafe |
Value: 1 | |||
| (PID) Process: | (2524) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings |
| Operation: | write | Name: | ProxyEnable |
Value: 0 | |||
| (PID) Process: | (2524) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Internet Settings\Connections |
| Operation: | write | Name: | SavedLegacySettings |
Value: 4600000071000000010000000000000000000000000000000000000000000000C0E333BBEAB1D301000000000000000000000000020000001700000000000000FE800000000000007D6CB050D9C573F70B000000000000006D00330032005C004D00530049004D004700330032002E0064006C000100000004AA400014AA4000040000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000002000000C0A8016400000000000000000000000000000000000000000800000000000000805D3F00983740000008000002000000000000600000002060040000B8A94000020000008802000060040000B8A9400004000000F8010000B284000088B64000B84B400043003A000000000000000000000000000000000000000000 | |||
| (PID) Process: | (2524) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Recovery\Active |
| Operation: | write | Name: | {D1B22B1B-6605-11E9-A09E-5254004A04AF} |
Value: 0 | |||
| (PID) Process: | (2524) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Ext\Stats\{2670000A-7350-4F3C-8081-5663EE0C6C49}\iexplore |
| Operation: | write | Name: | Type |
Value: 4 | |||
| (PID) Process: | (2524) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Ext\Stats\{2670000A-7350-4F3C-8081-5663EE0C6C49}\iexplore |
| Operation: | write | Name: | Count |
Value: 1 | |||
| (PID) Process: | (2524) iexplore.exe | Key: | HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Ext\Stats\{2670000A-7350-4F3C-8081-5663EE0C6C49}\iexplore |
| Operation: | write | Name: | Time |
Value: E3070400020017001400180028005402 | |||
Executable files
2
Suspicious files
121
Text files
255
Unknown types
54
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 2524 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Windows\Temporary Internet Files\Content.IE5\H6QNMHE9\favicon[1].ico | — | |
MD5:— | SHA256:— | |||
| 2524 | iexplore.exe | C:\Users\admin\AppData\LocalLow\Microsoft\Internet Explorer\Services\search_{0633EE93-D776-472f-A0FF-E1416B8B2E3A}.ico | — | |
MD5:— | SHA256:— | |||
| 2524 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\~DFBD79E507615D0DF3.TMP | — | |
MD5:— | SHA256:— | |||
| 2524 | iexplore.exe | C:\Users\admin\AppData\Local\Temp\~DF54A1F838576AF3E6.TMP | — | |
MD5:— | SHA256:— | |||
| 2524 | iexplore.exe | C:\Users\admin\AppData\Local\Microsoft\Internet Explorer\Recovery\Active\RecoveryStore.{D1B22B1B-6605-11E9-A09E-5254004A04AF}.dat | — | |
MD5:— | SHA256:— | |||
| 3332 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\index | — | |
MD5:— | SHA256:— | |||
| 3332 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\data_0 | — | |
MD5:— | SHA256:— | |||
| 3332 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\data_1 | — | |
MD5:— | SHA256:— | |||
| 3332 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\data_2 | — | |
MD5:— | SHA256:— | |||
| 3332 | chrome.exe | C:\Users\admin\AppData\Local\Google\Chrome\User Data\ShaderCache\GPUCache\data_3 | — | |
MD5:— | SHA256:— | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
18
TCP/UDP connections
46
DNS requests
86
Threats
17
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
3332 | chrome.exe | GET | 200 | 194.9.25.78:80 | http://r3---sn-5uh5o-f5fs.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvMjJlQUFXRC12Ny1ldUFnMXF3SDlXZDlFZw/7319.128.0.1_pkedcjkdefgpdelpbcmbmeomcjbeemfm.crx?cms_redirect=yes&mip=212.7.219.109&mm=28&mn=sn-5uh5o-f5fs&ms=nvh&mt=1556050731&mv=u&pl=24&shardbypass=yes | PL | crx | 842 Kb | whitelisted |
536 | firefox.exe | GET | 200 | 37.9.175.22:80 | http://realistickeportrety.sk/wp-admin/js/Scan/Jdbumi446LMI/ | SK | compressed | 12.3 Kb | suspicious |
1088 | WScript.exe | GET | 200 | 5.61.248.43:80 | http://berenbord.nl/wp-includes/7n_D/ | NL | executable | 67.5 Kb | suspicious |
3332 | chrome.exe | GET | 200 | 37.9.175.22:80 | http://realistickeportrety.sk/wp-admin/js/Scan/Jdbumi446LMI/ | SK | compressed | 12.3 Kb | suspicious |
536 | firefox.exe | POST | 200 | 93.184.220.29:80 | http://ocsp.digicert.com/ | US | der | 471 b | whitelisted |
272 | soundser.exe | POST | — | 68.229.130.39:80 | http://68.229.130.39/scripts/ | US | — | — | malicious |
272 | soundser.exe | POST | 200 | 190.112.228.47:443 | http://190.112.228.47:443/schema/acquire/ | CW | binary | 132 b | malicious |
272 | soundser.exe | POST | — | 70.116.68.186:80 | http://70.116.68.186/tpt/psec/ | US | — | — | malicious |
536 | firefox.exe | POST | 200 | 172.217.23.163:80 | http://ocsp.pki.goog/GTSGIAG3 | US | der | 471 b | whitelisted |
3332 | chrome.exe | GET | 302 | 172.217.18.14:80 | http://redirector.gvt1.com/edgedl/chromewebstore/L2Nocm9tZV9leHRlbnNpb24vYmxvYnMvMjJlQUFXRC12Ny1ldUFnMXF3SDlXZDlFZw/7319.128.0.1_pkedcjkdefgpdelpbcmbmeomcjbeemfm.crx | US | html | 508 b | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
1564 | iexplore.exe | 37.9.175.22:80 | realistickeportrety.sk | Websupport s.r.o. | SK | suspicious |
2524 | iexplore.exe | 204.79.197.200:80 | www.bing.com | Microsoft Corporation | US | whitelisted |
3332 | chrome.exe | 172.217.22.99:443 | clientservices.googleapis.com | Google Inc. | US | whitelisted |
3332 | chrome.exe | 172.217.21.195:443 | www.google.com.ua | Google Inc. | US | whitelisted |
3332 | chrome.exe | 216.58.208.46:443 | clients1.google.com | Google Inc. | US | whitelisted |
3332 | chrome.exe | 172.217.18.163:443 | www.gstatic.com | Google Inc. | US | whitelisted |
3332 | chrome.exe | 172.217.21.205:443 | accounts.google.com | Google Inc. | US | whitelisted |
3332 | chrome.exe | 37.9.175.22:80 | realistickeportrety.sk | Websupport s.r.o. | SK | suspicious |
3332 | chrome.exe | 172.217.16.196:443 | www.google.com | Google Inc. | US | whitelisted |
3332 | chrome.exe | 216.58.210.3:443 | ssl.gstatic.com | Google Inc. | US | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
www.bing.com |
| whitelisted |
realistickeportrety.sk |
| suspicious |
clientservices.googleapis.com |
| whitelisted |
www.google.com.ua |
| whitelisted |
accounts.google.com |
| shared |
clients1.google.com |
| whitelisted |
ssl.gstatic.com |
| whitelisted |
www.gstatic.com |
| whitelisted |
apis.google.com |
| whitelisted |
www.google.com |
| malicious |
Threats
PID | Process | Class | Message |
|---|---|---|---|
1564 | iexplore.exe | Misc activity | ET INFO SUSPICIOUS Single JS file inside of ZIP Download (Observed as lure in malspam campaigns) |
3332 | chrome.exe | Misc activity | ET INFO SUSPICIOUS Single JS file inside of ZIP Download (Observed as lure in malspam campaigns) |
536 | firefox.exe | Misc activity | ET INFO SUSPICIOUS Single JS file inside of ZIP Download (Observed as lure in malspam campaigns) |
1088 | WScript.exe | Misc activity | SUSPICIOUS [PTsecurity] Cmd.Powershell.Download HTTP UserAgent (Win7) |
1088 | WScript.exe | Potential Corporate Privacy Violation | ET POLICY PE EXE or DLL Windows file download HTTP |
1088 | WScript.exe | A Network Trojan was detected | ET CURRENT_EVENTS Likely Evil EXE download from MSXMLHTTP non-exe extension M2 |
1088 | WScript.exe | Misc activity | ET INFO EXE - Served Attached HTTP |
272 | soundser.exe | A Network Trojan was detected | MALWARE [PTsecurity] Feodo/Emotet |
272 | soundser.exe | A Network Trojan was detected | MALWARE [PTsecurity] Feodo/Emotet |
272 | soundser.exe | A Network Trojan was detected | MALWARE [PTsecurity] Feodo/Emotet |
6 ETPRO signatures available at the full report