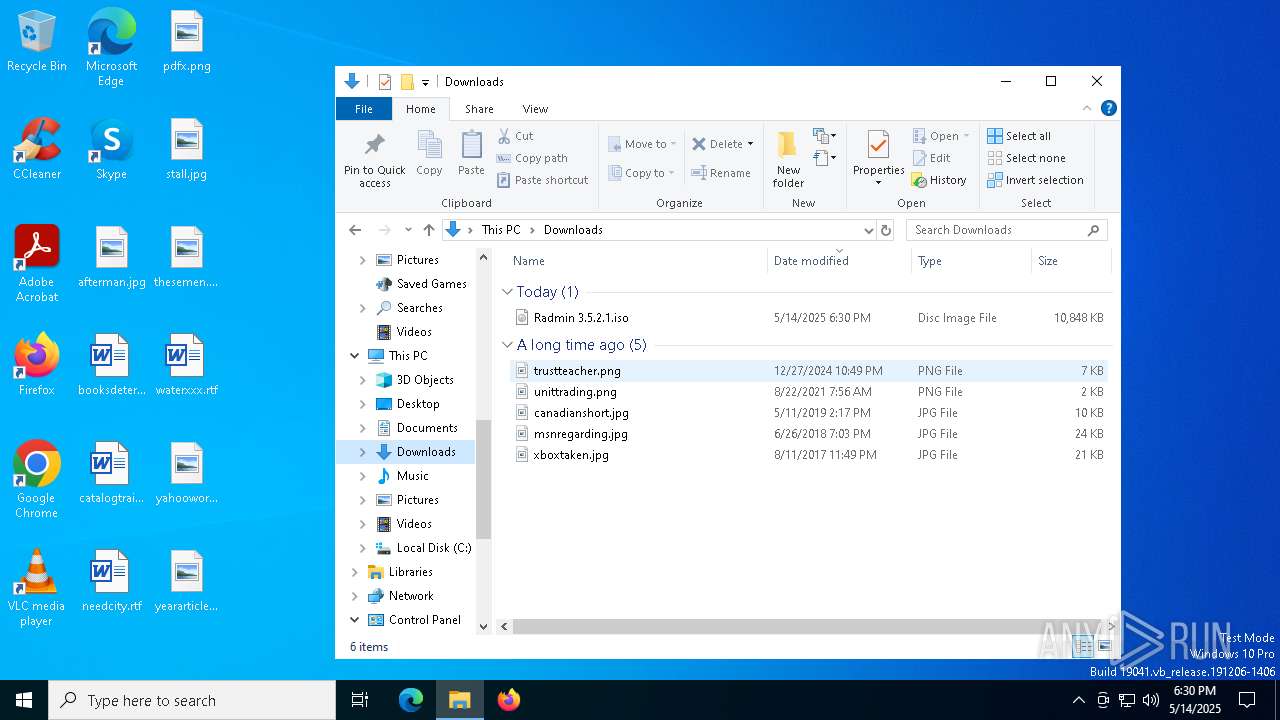
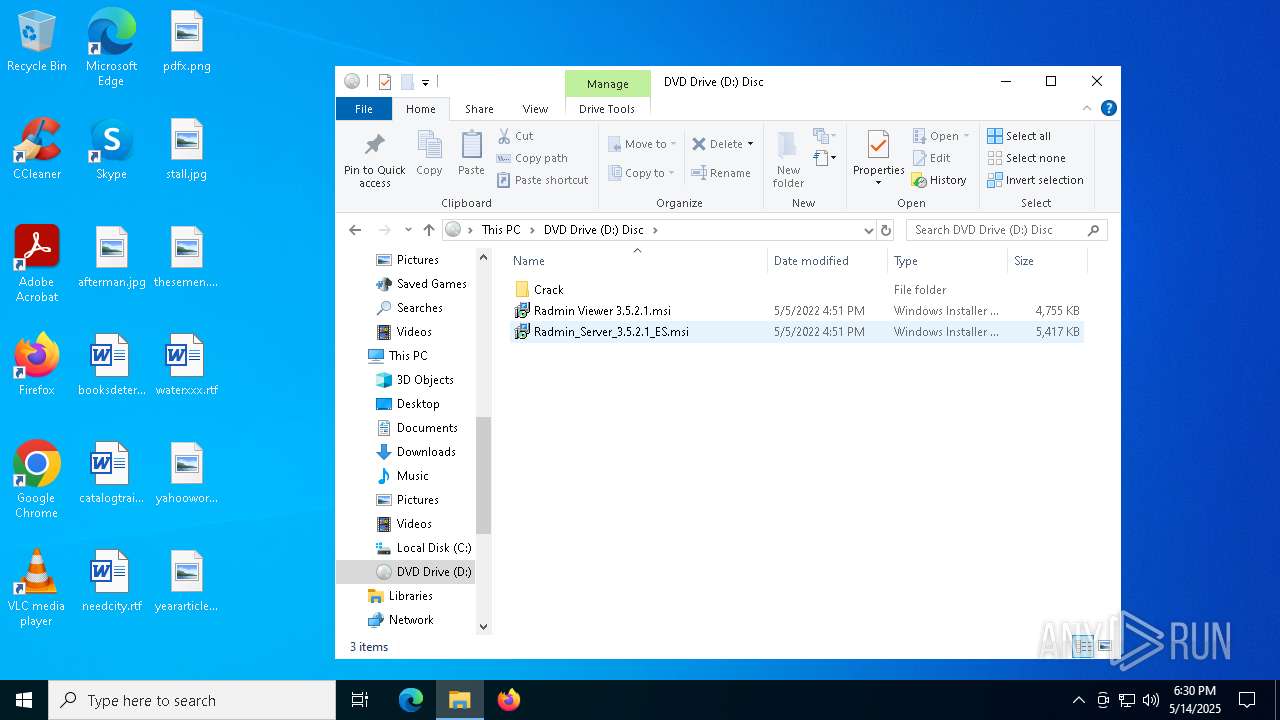
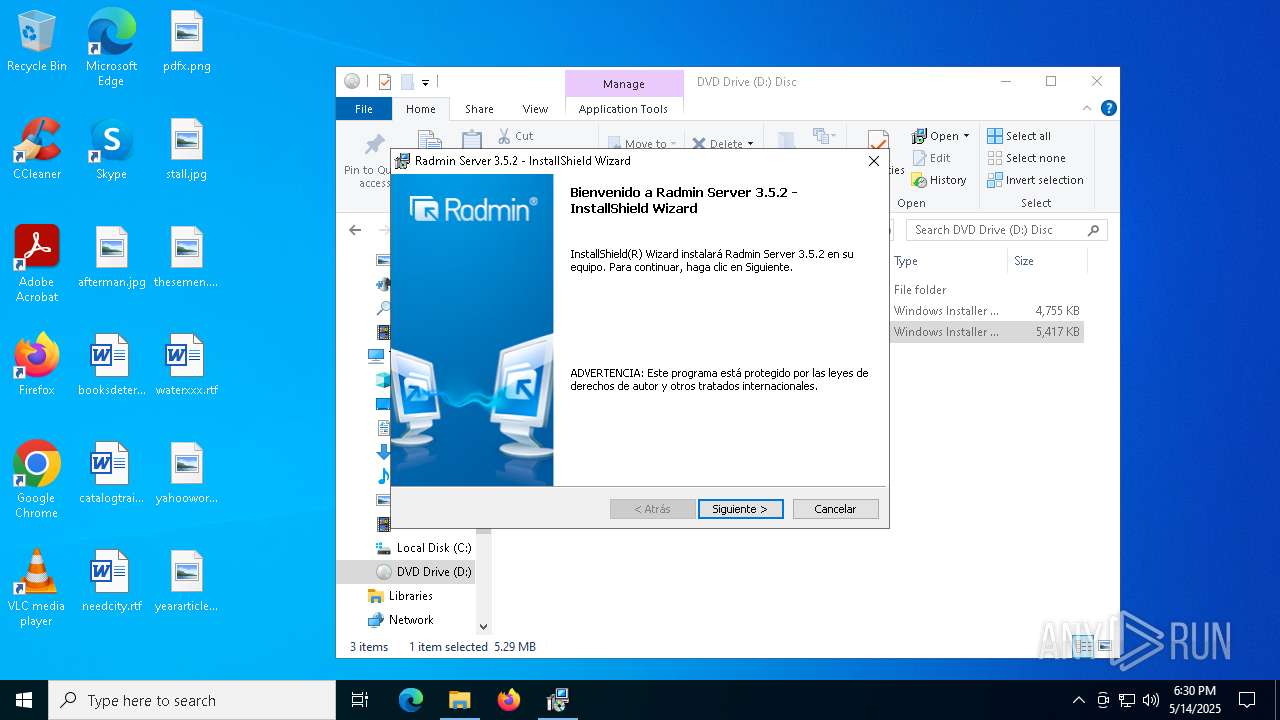
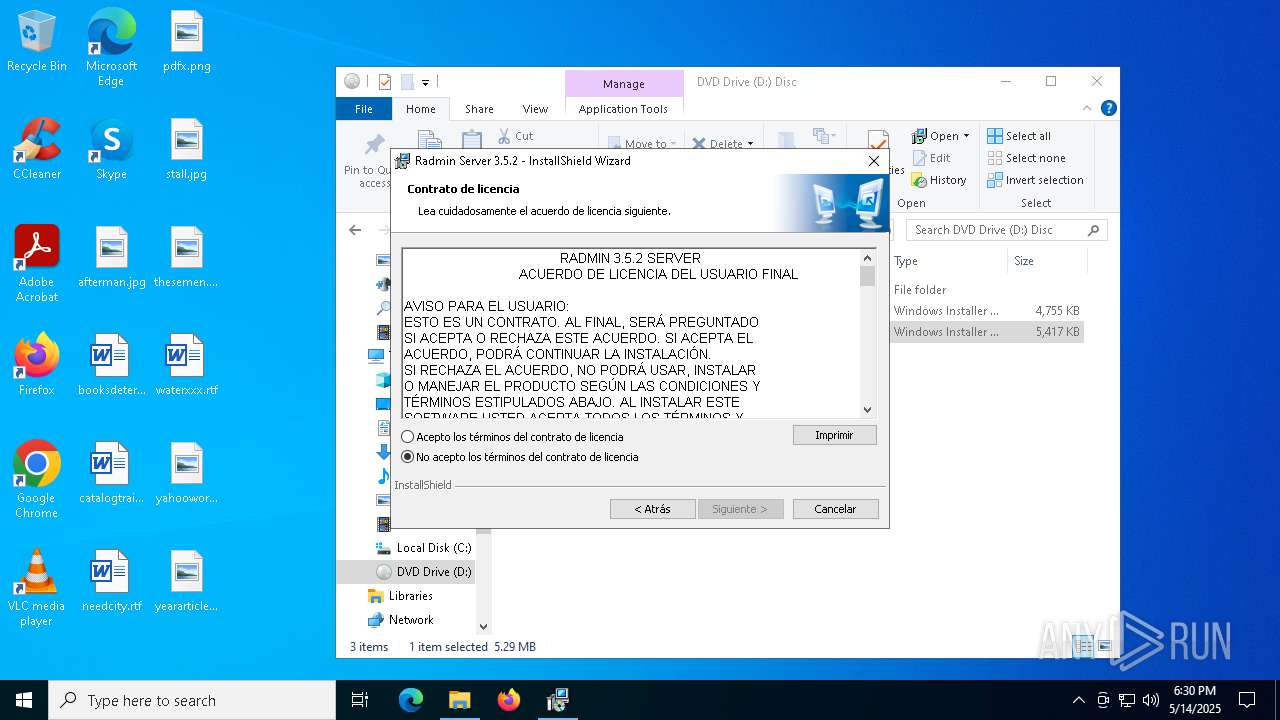
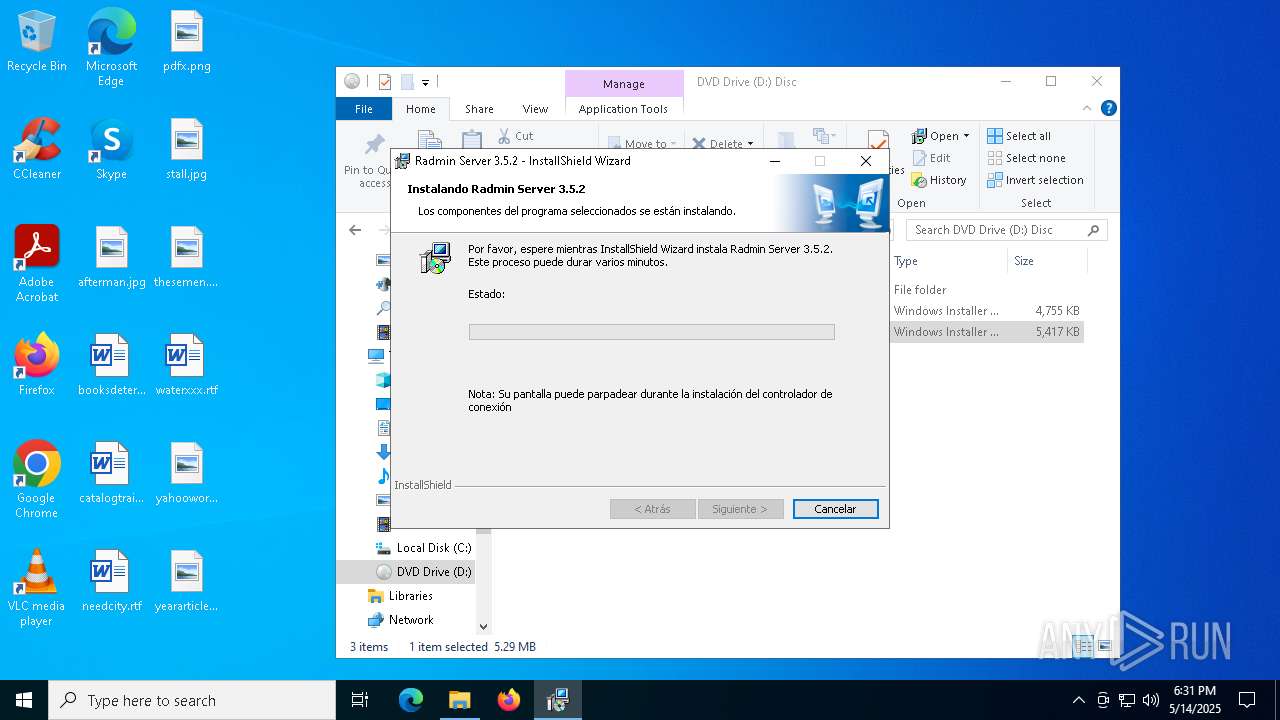
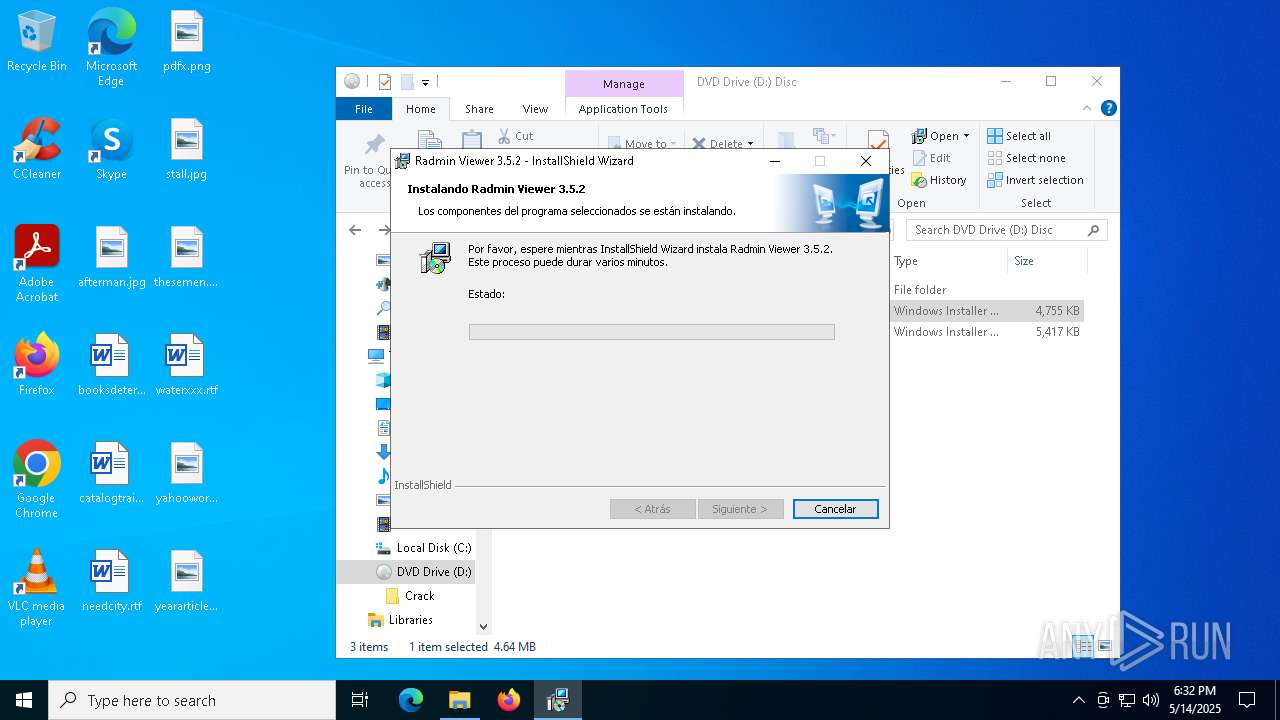
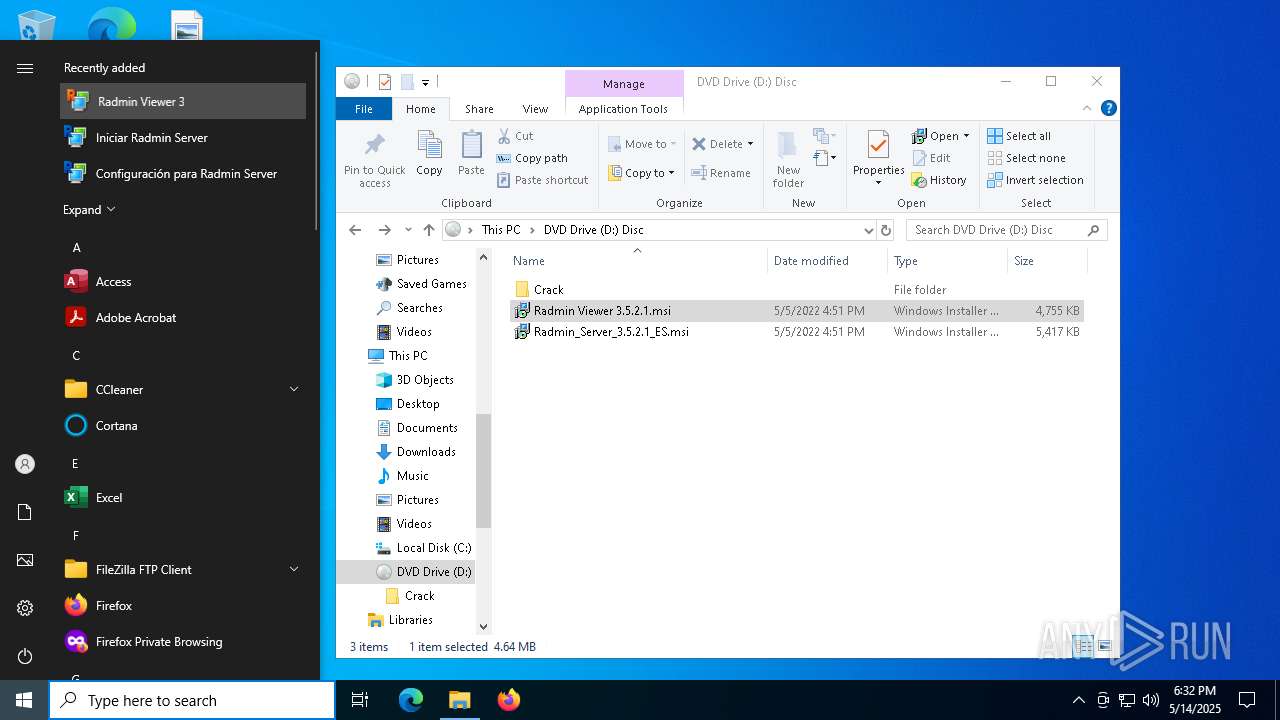
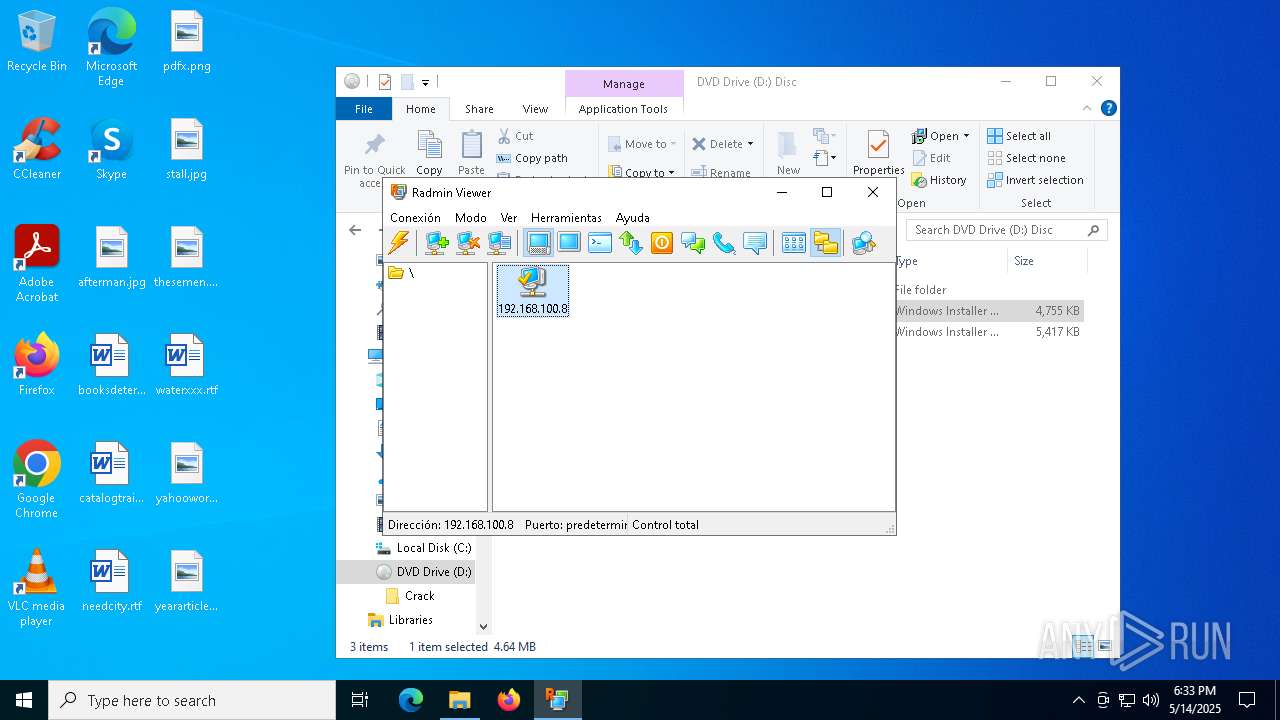
| File name: | Radmin 3.5.2.1.iso |
| Full analysis: | https://app.any.run/tasks/7deaf239-e8a3-4481-a772-aa83cf4a1b6f |
| Verdict: | Malicious activity |
| Analysis date: | May 14, 2025, 18:30:18 |
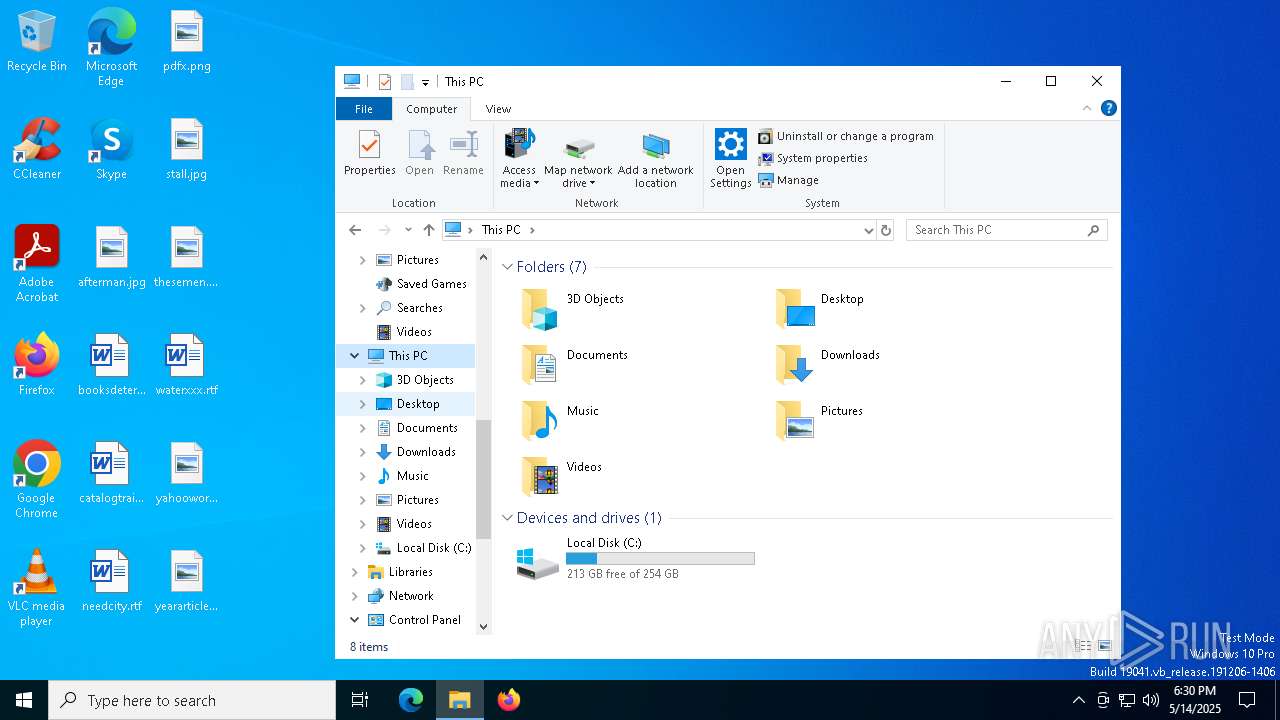
| OS: | Windows 10 Professional (build: 19044, 64 bit) |
| Tags: | |
| Indicators: | |
| MIME: | application/x-iso9660-image |
| File info: | ISO 9660 CD-ROM filesystem data 'DISC' |
| MD5: | BD4BA1A6D20BC7EB9A540EFFF03AEBDC |
| SHA1: | 43EAFDD39C32C86C72D581555159584AFC568324 |
| SHA256: | 6397A45051A6C36126E5B076D2B46A9F49D5D529070AE955434E3D40ADE232D5 |
| SSDEEP: | 98304:C9rHf8BPqG2Az7weWrlxTQB2zB4vSCzHmvIRjrNONUfVorZoqx8oloQPHj/R8dU1:1vnoDbHoOOMd8mC4s |
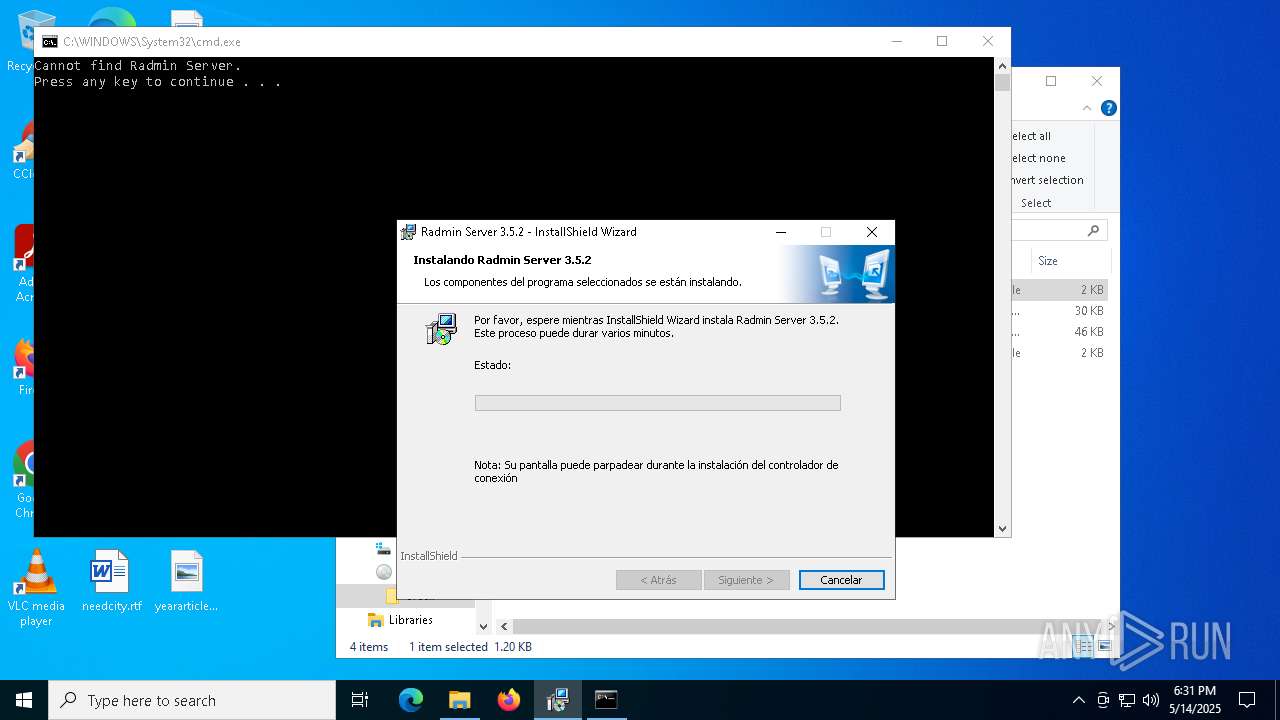
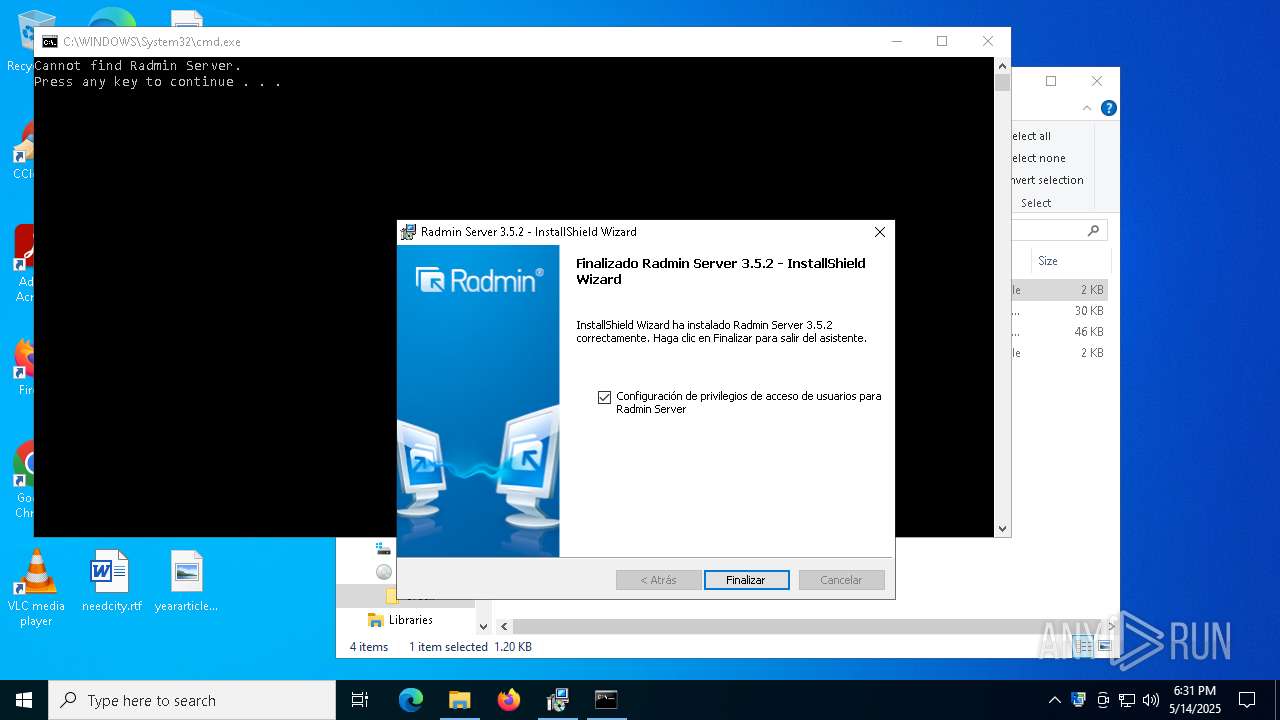
MALICIOUS
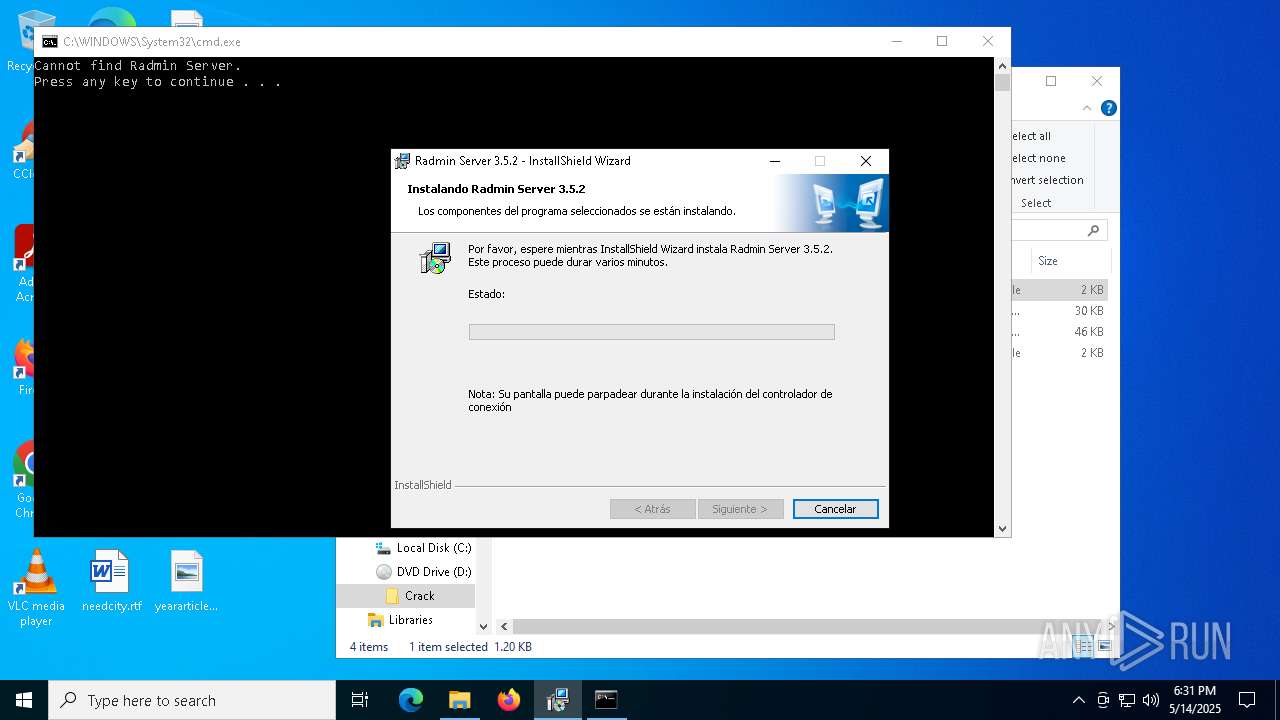
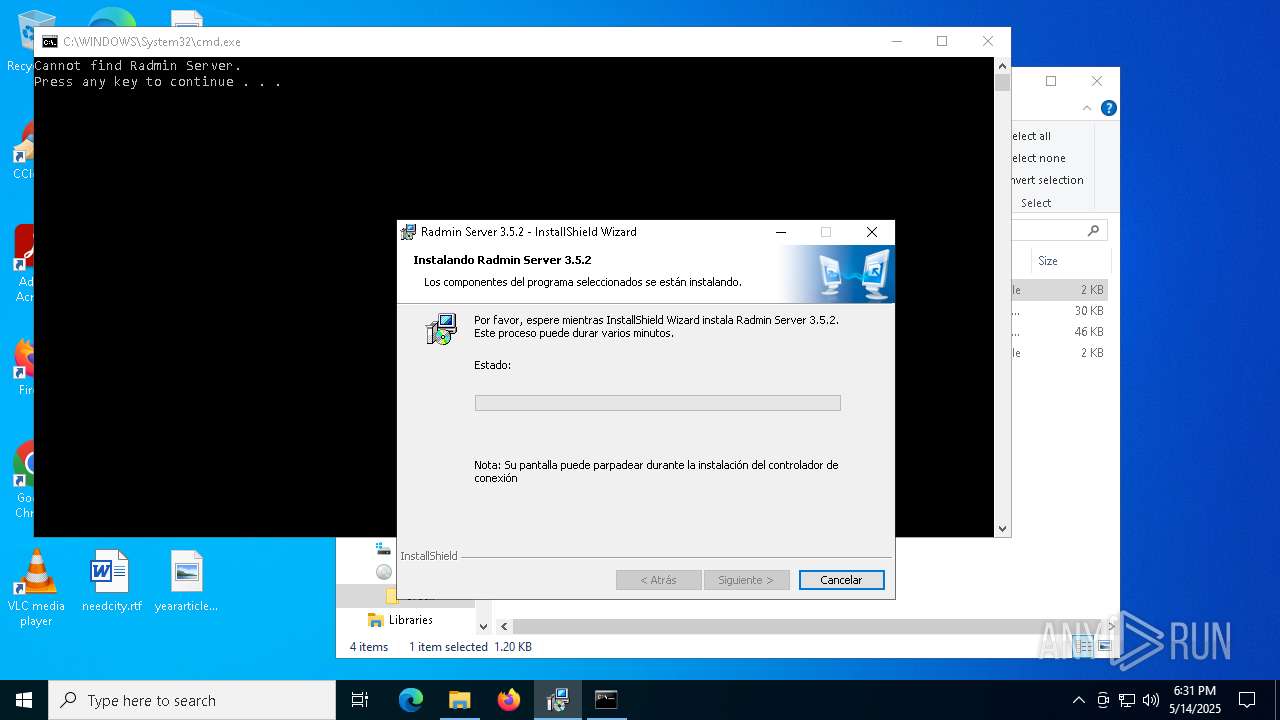
Executing a file with an untrusted certificate
- rsetup64.exe (PID: 2644)
- rsetup64.exe (PID: 7732)
- FamItrfc.Exe (PID: 7612)
- rserver3.exe (PID: 6940)
- rsetup64.exe (PID: 6800)
- FamItrfc.Exe (PID: 3396)
- FamItrfc.Exe (PID: 5344)
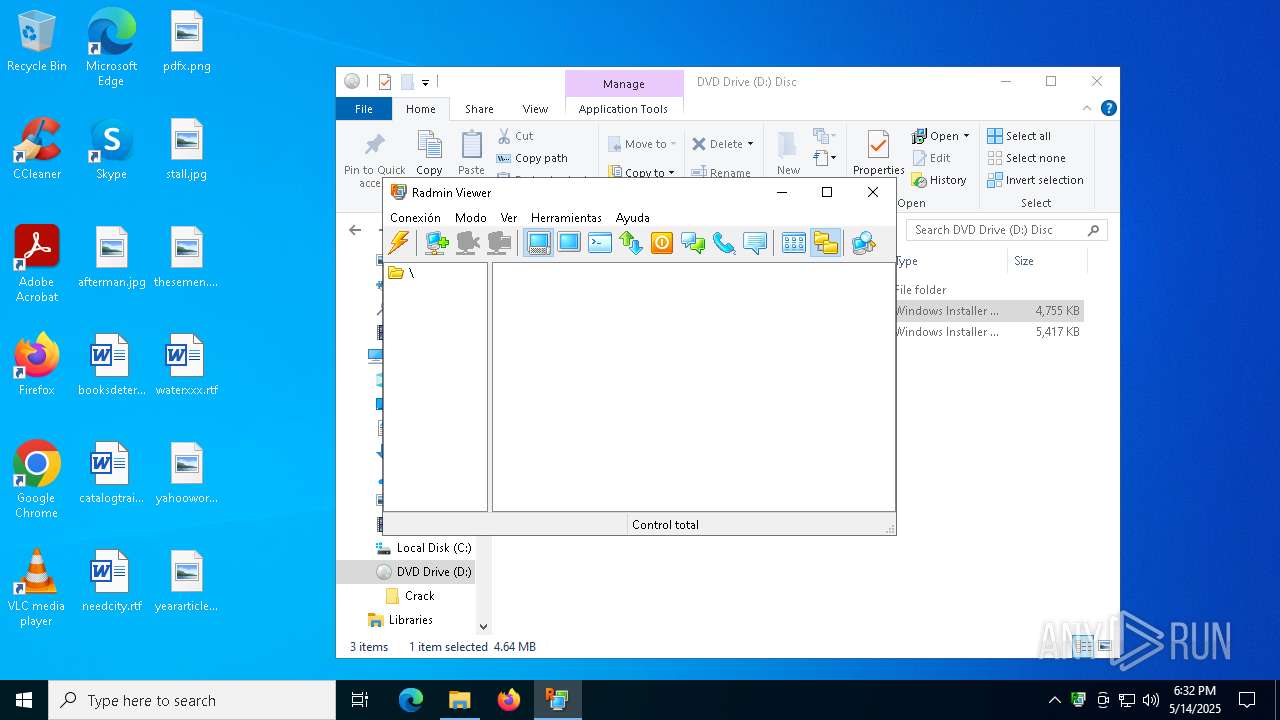
- Radmin.exe (PID: 3012)
- rserver3.exe (PID: 6572)
- rsl.exe (PID: 4108)
- rserver3.exe (PID: 7828)
- rserver3.exe (PID: 644)
- FamItrf2.Exe (PID: 1020)
- FamItrfc.Exe (PID: 3768)
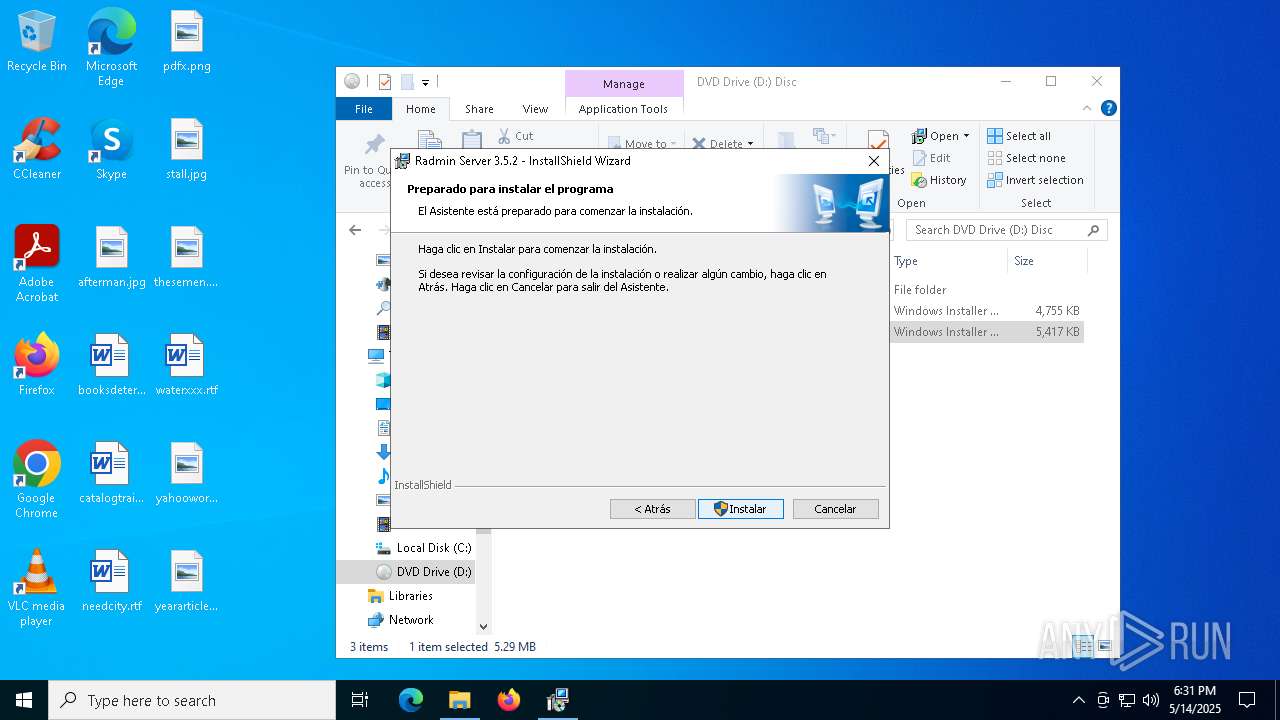
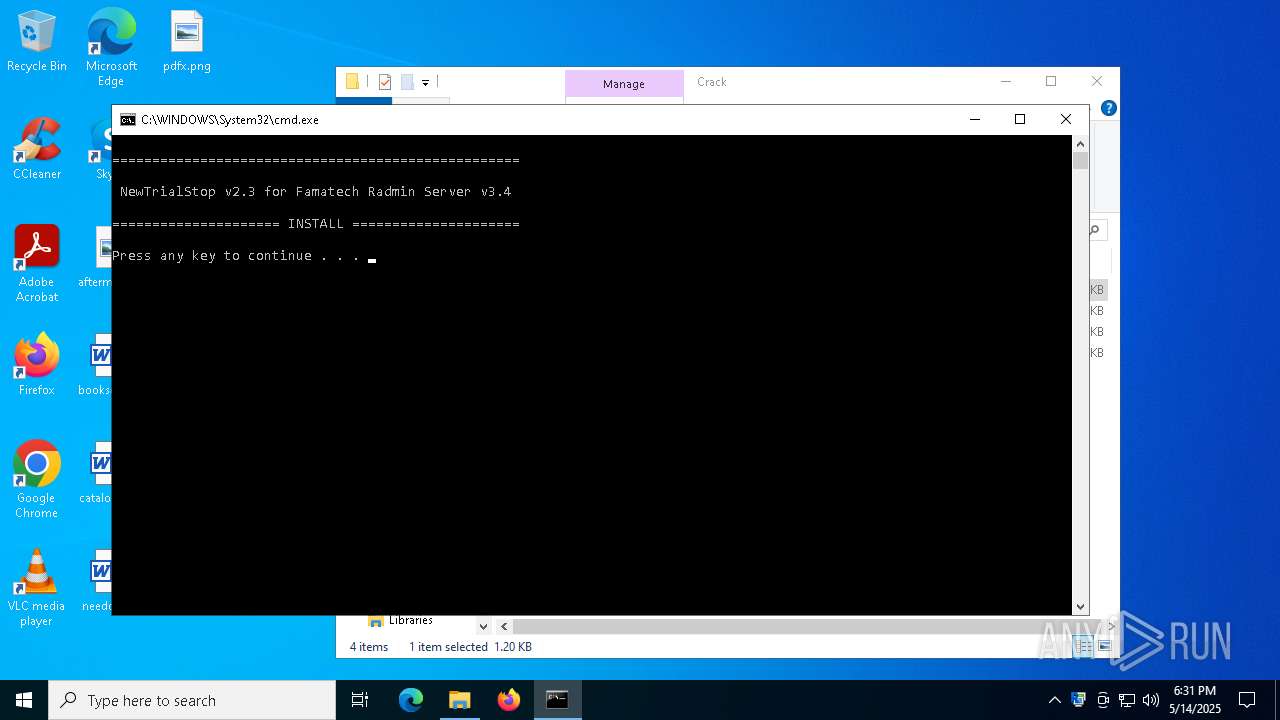
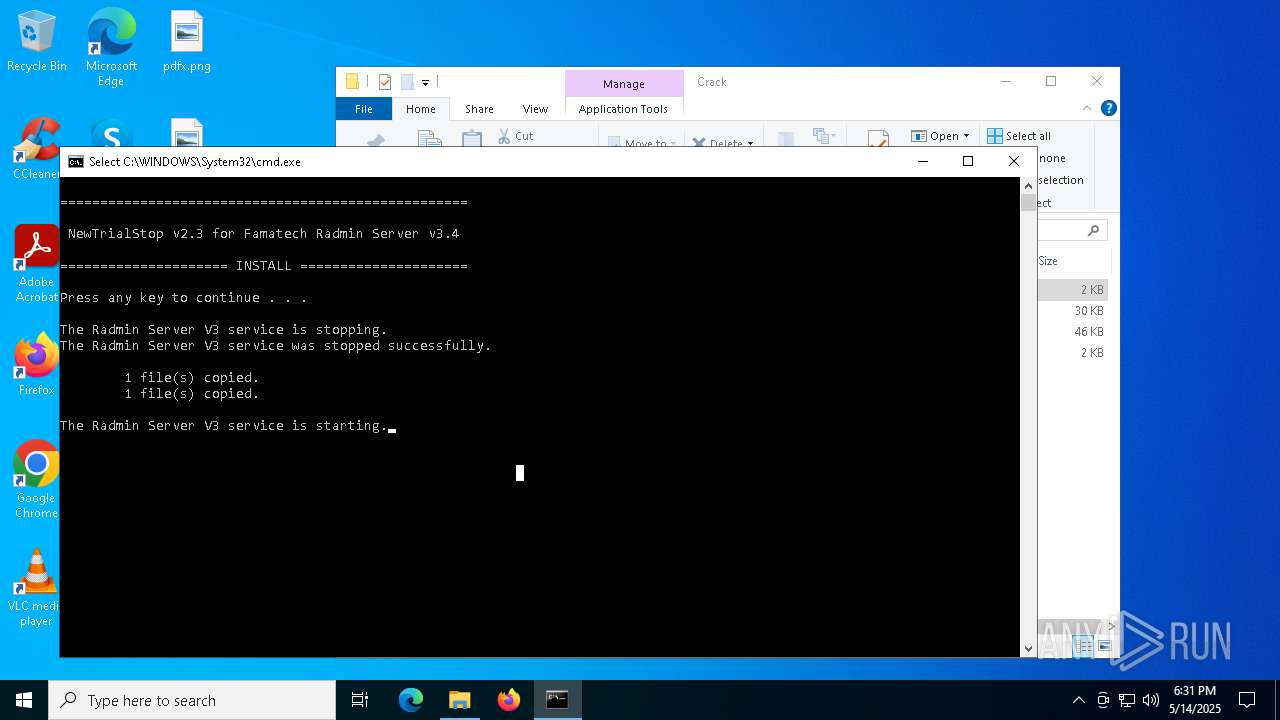
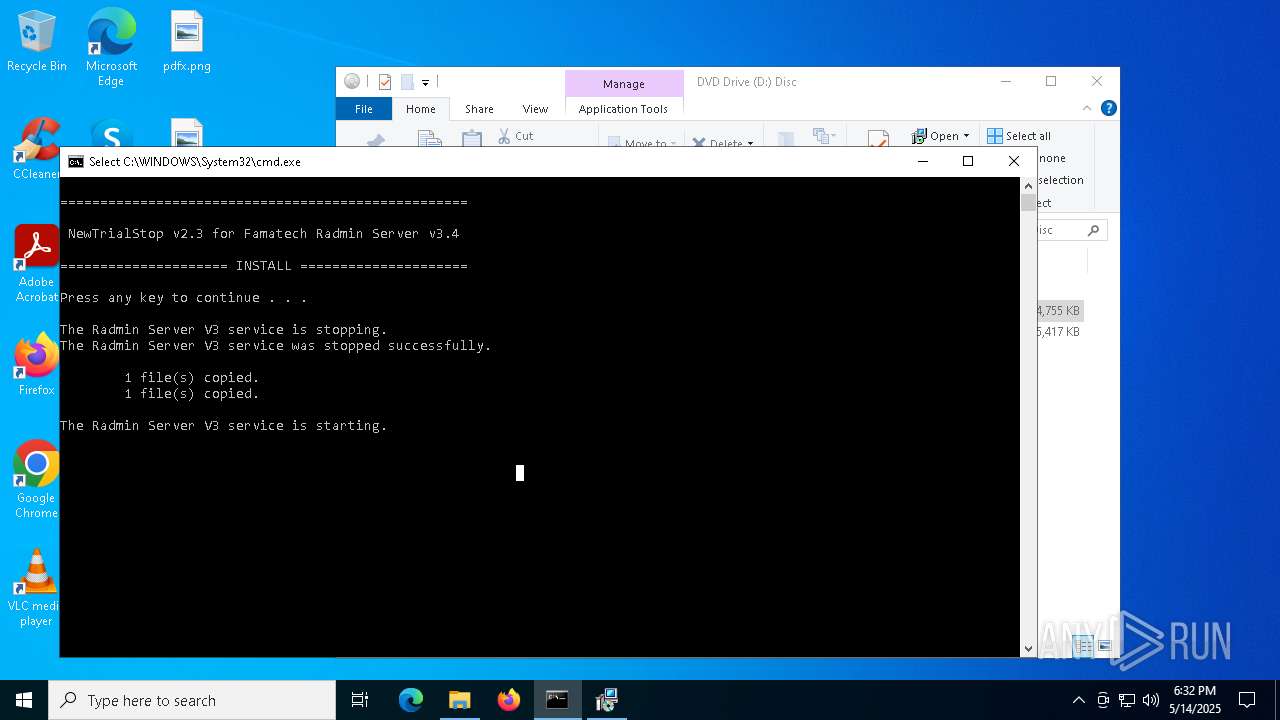
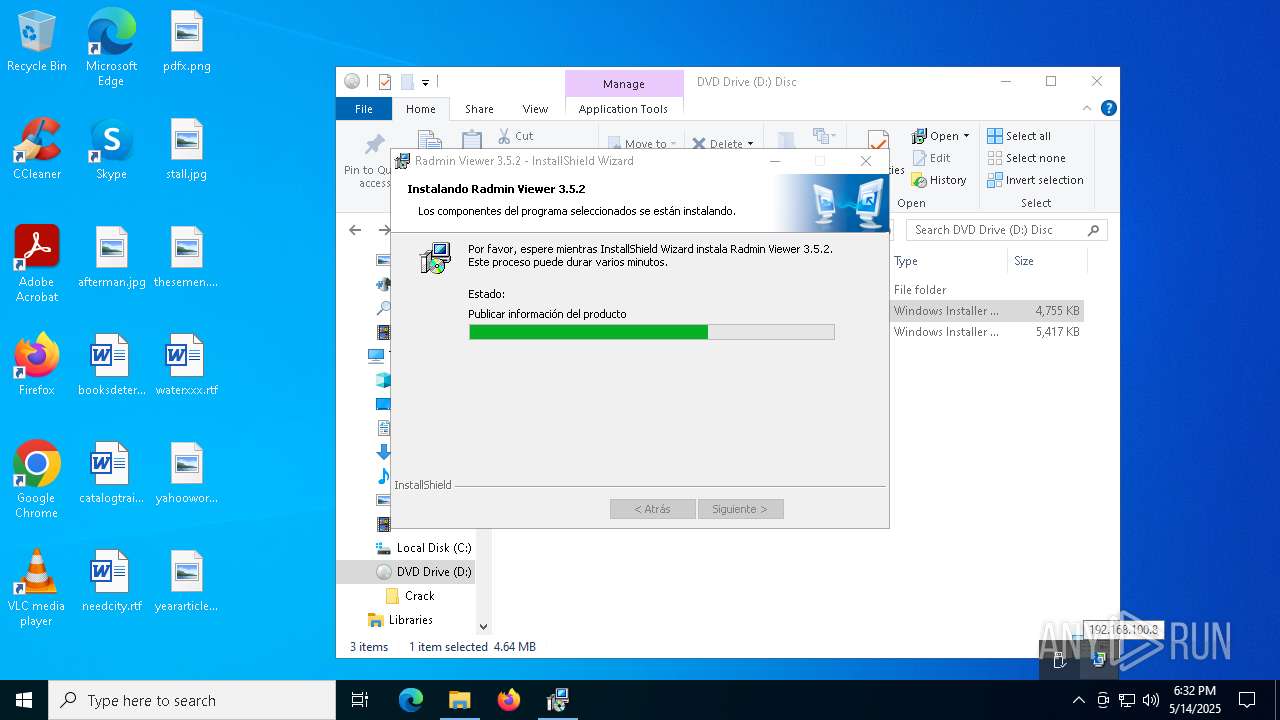
Starts NET.EXE for service management
- cmd.exe (PID: 5360)
- net.exe (PID: 4172)
- net.exe (PID: 208)
SUSPICIOUS
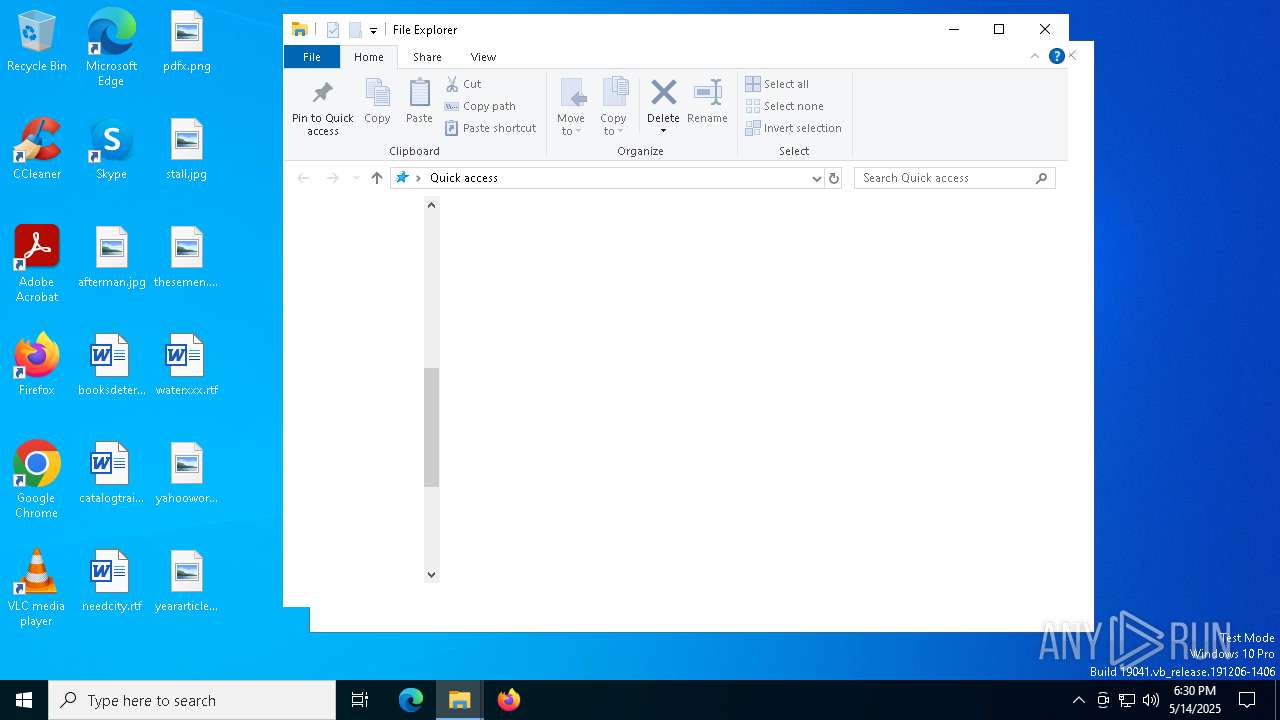
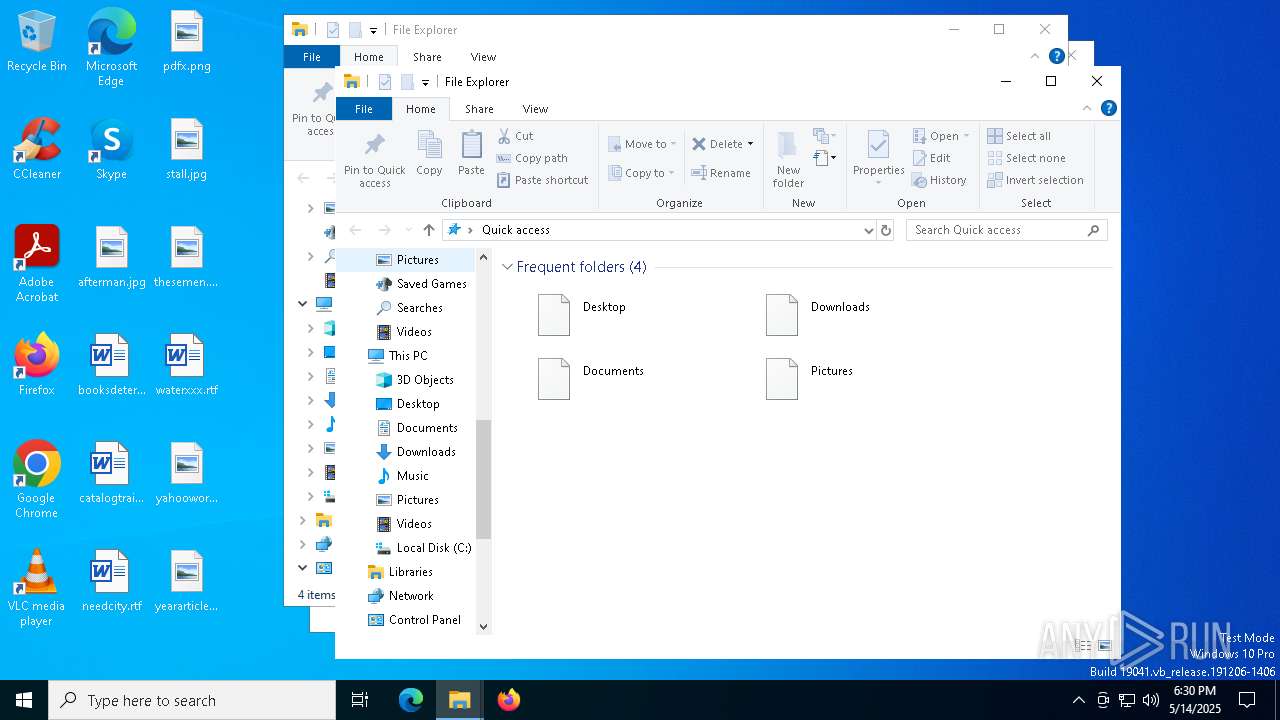
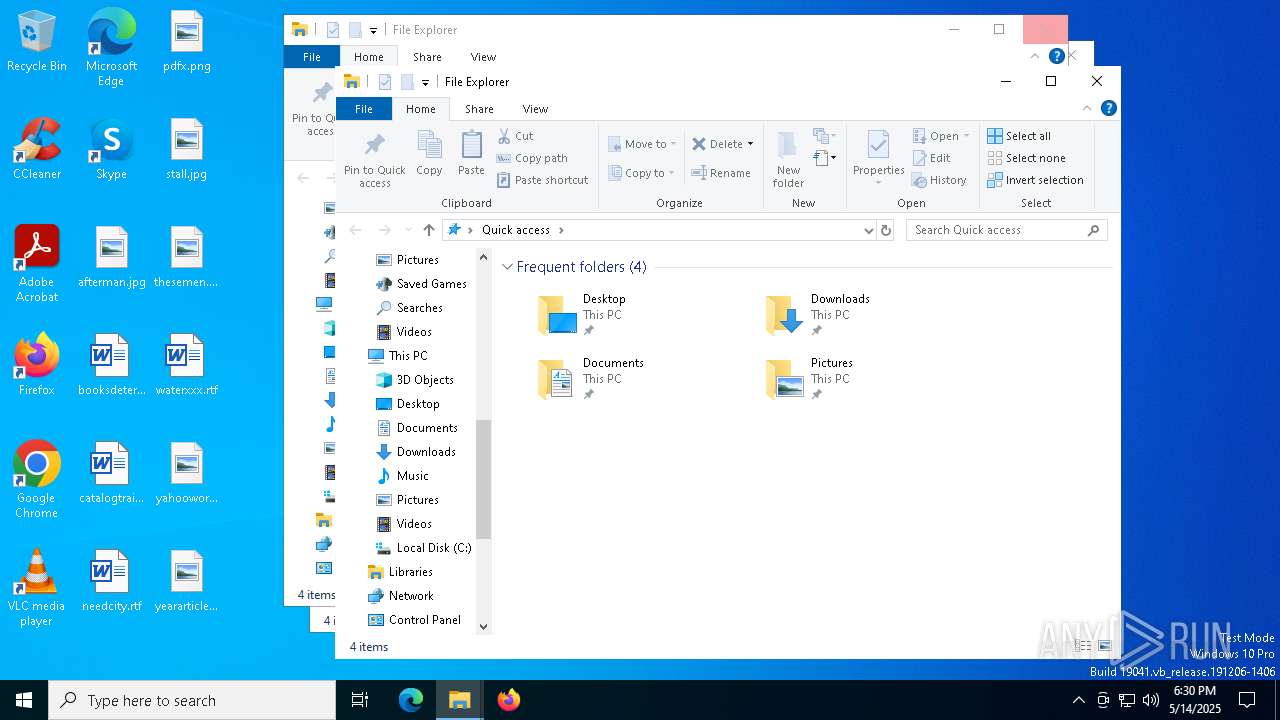
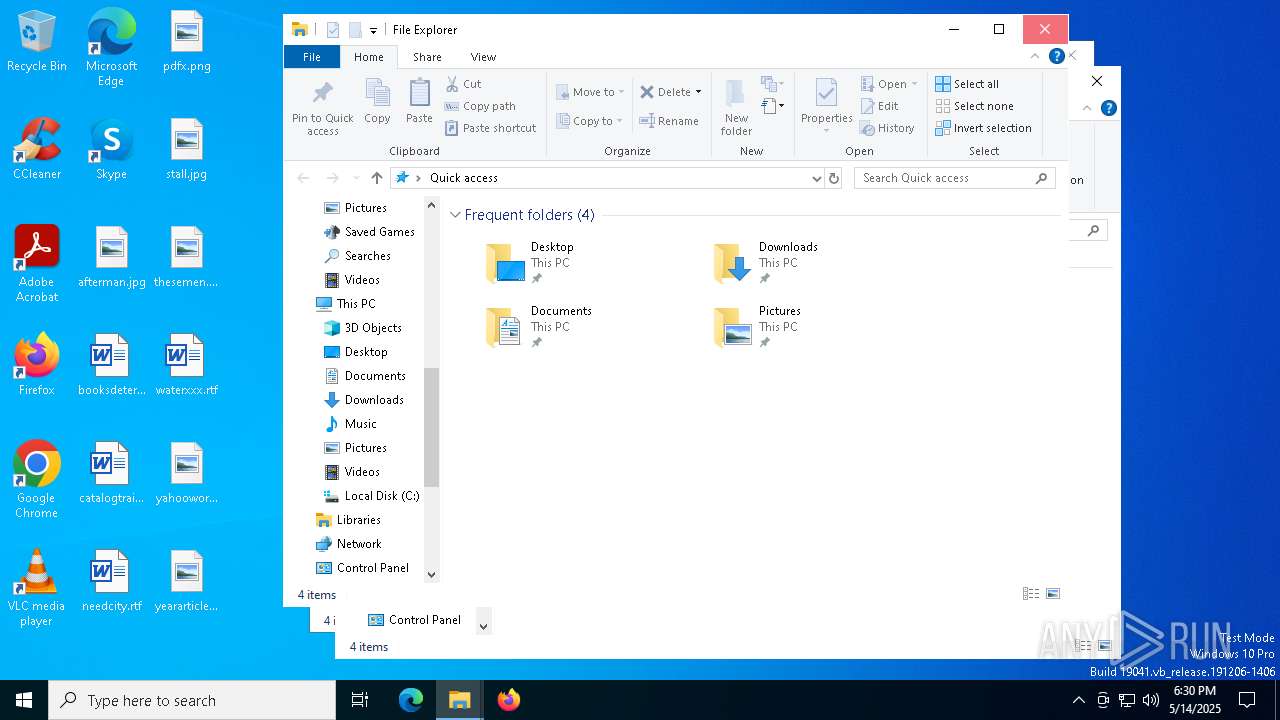
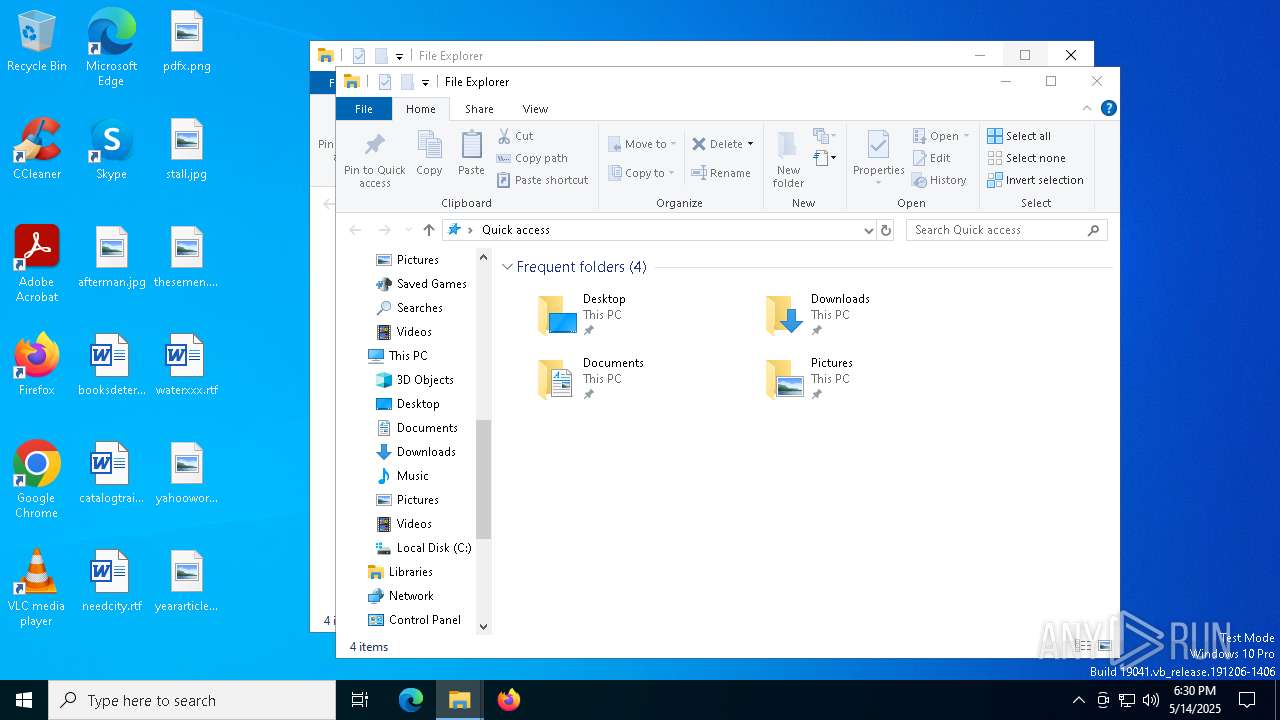
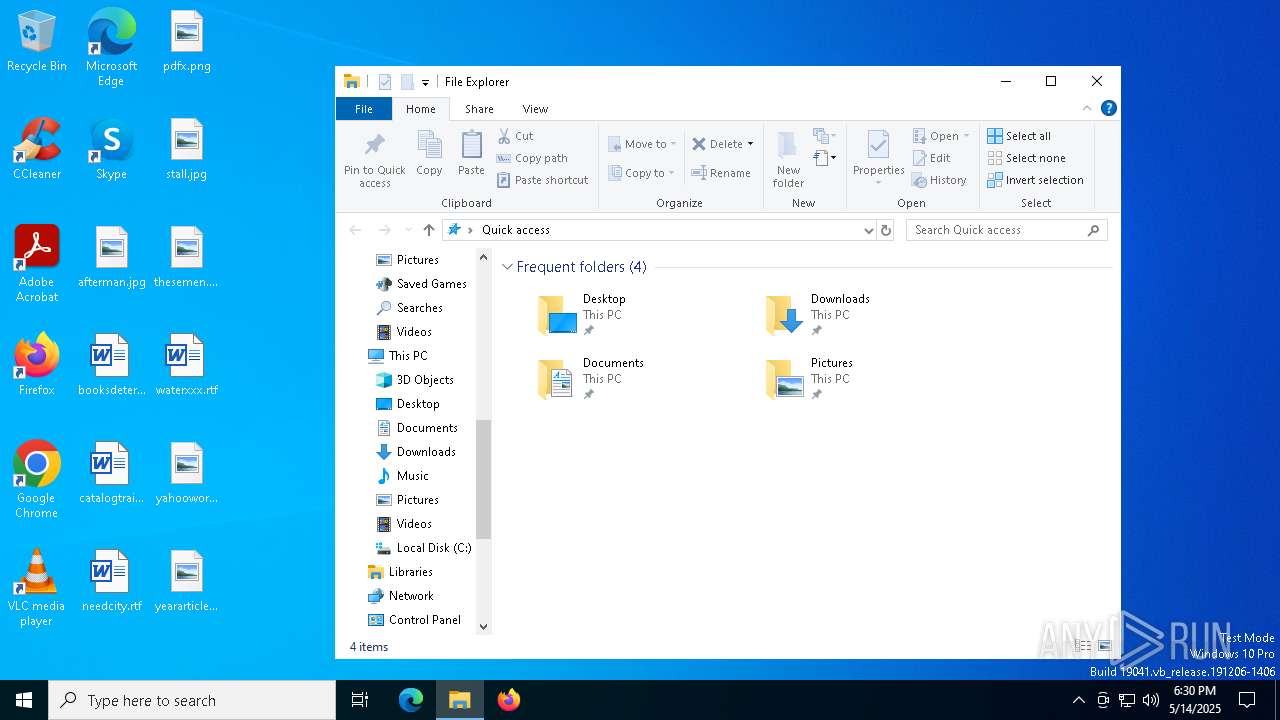
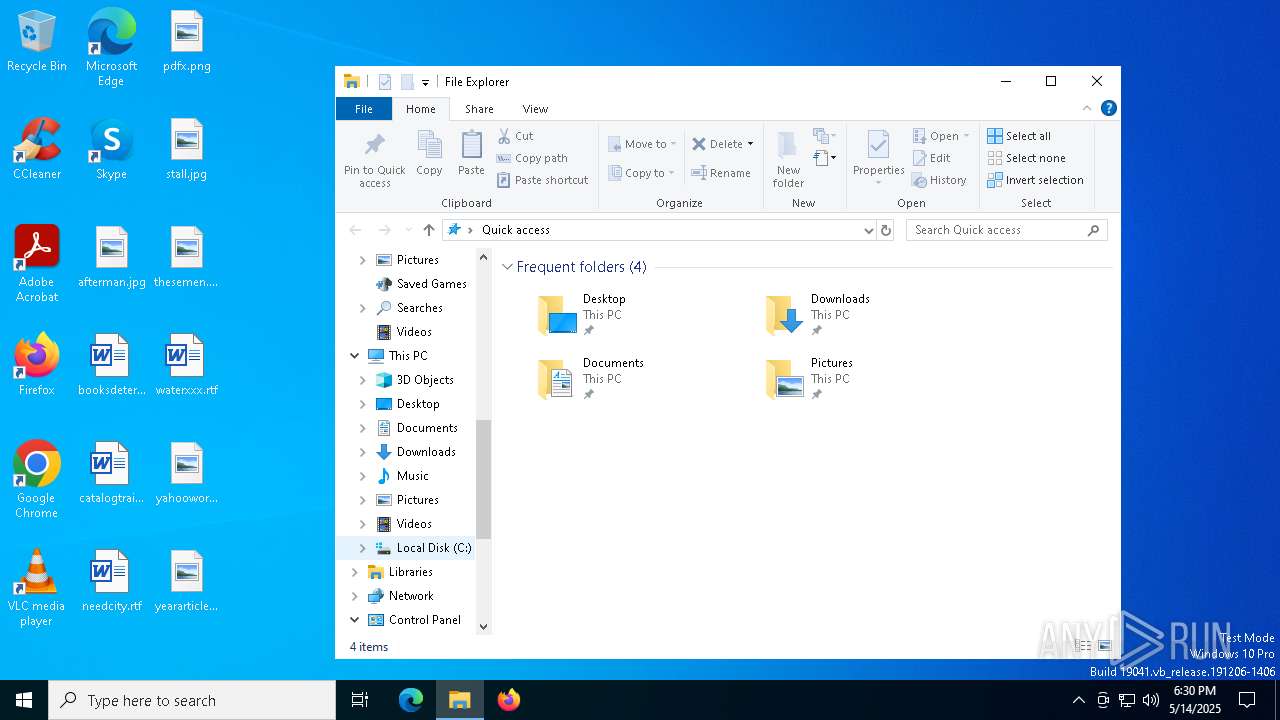
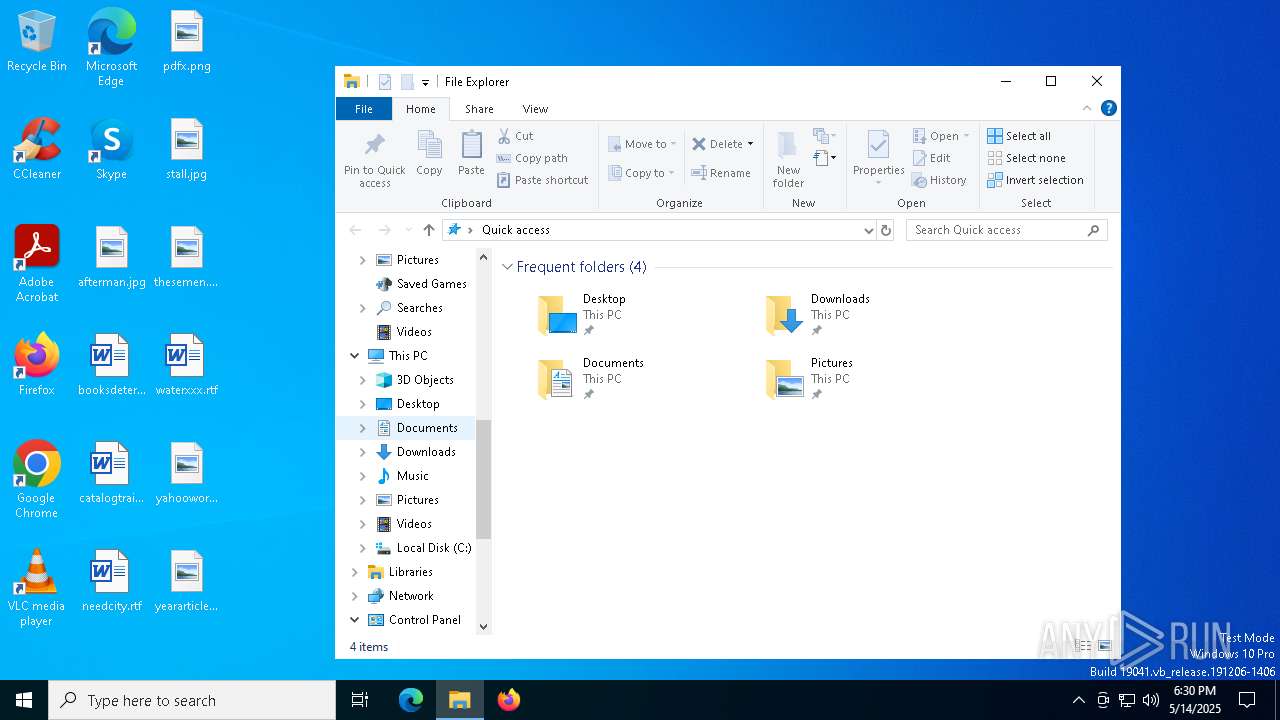
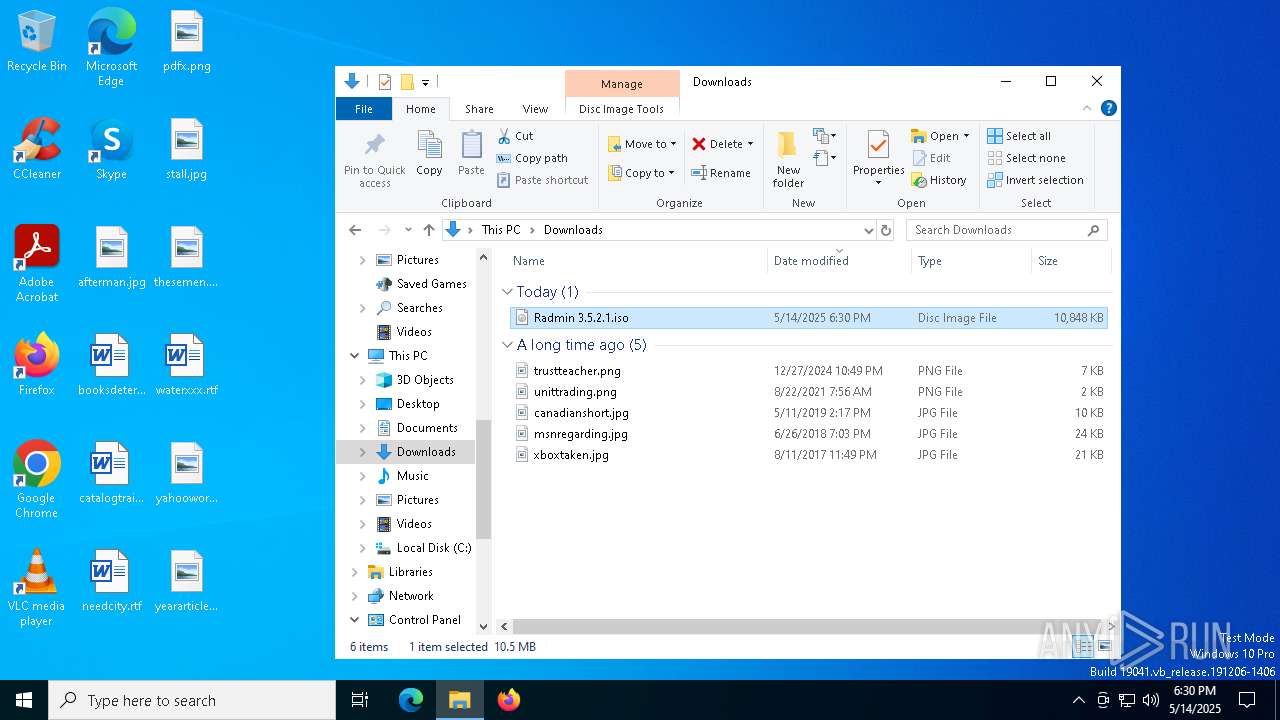
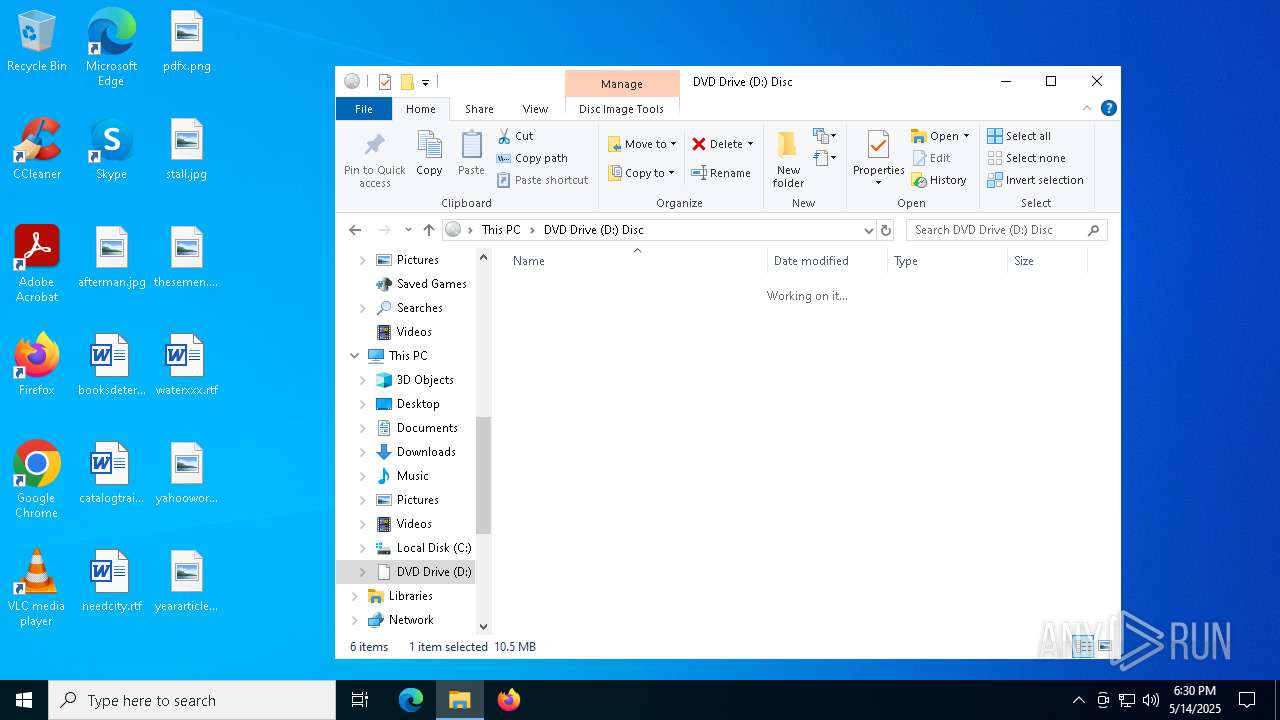
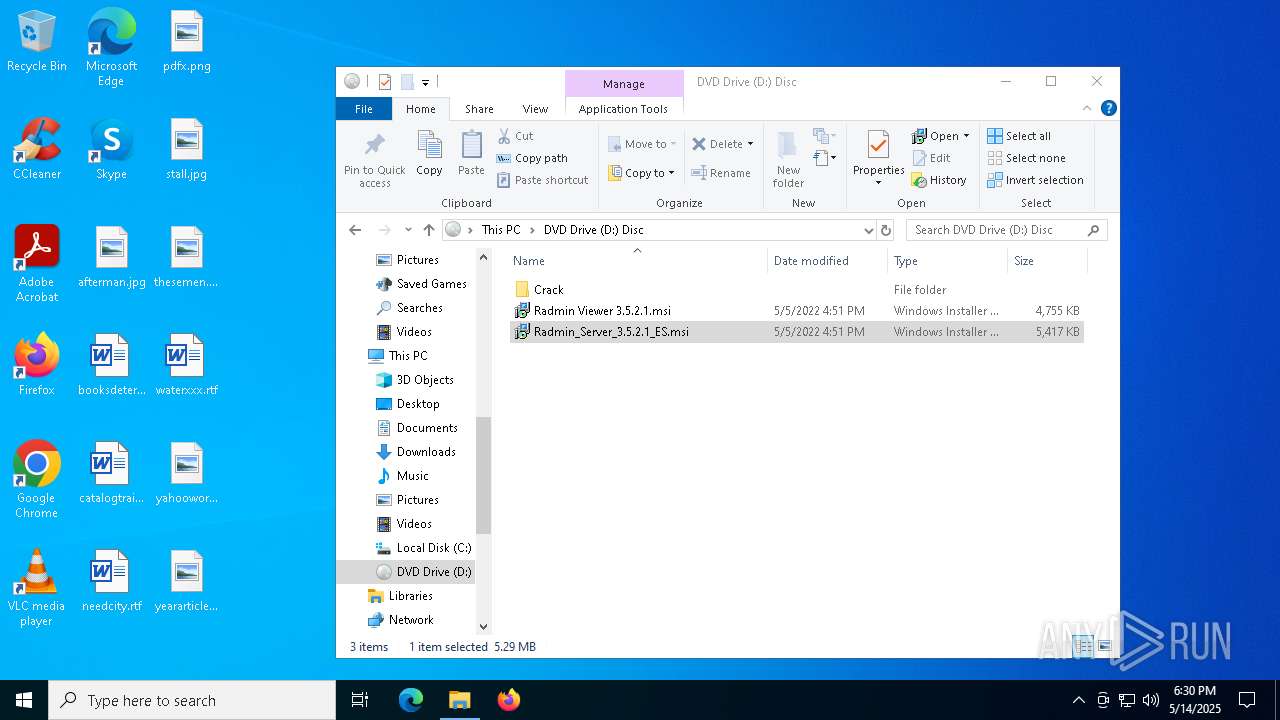
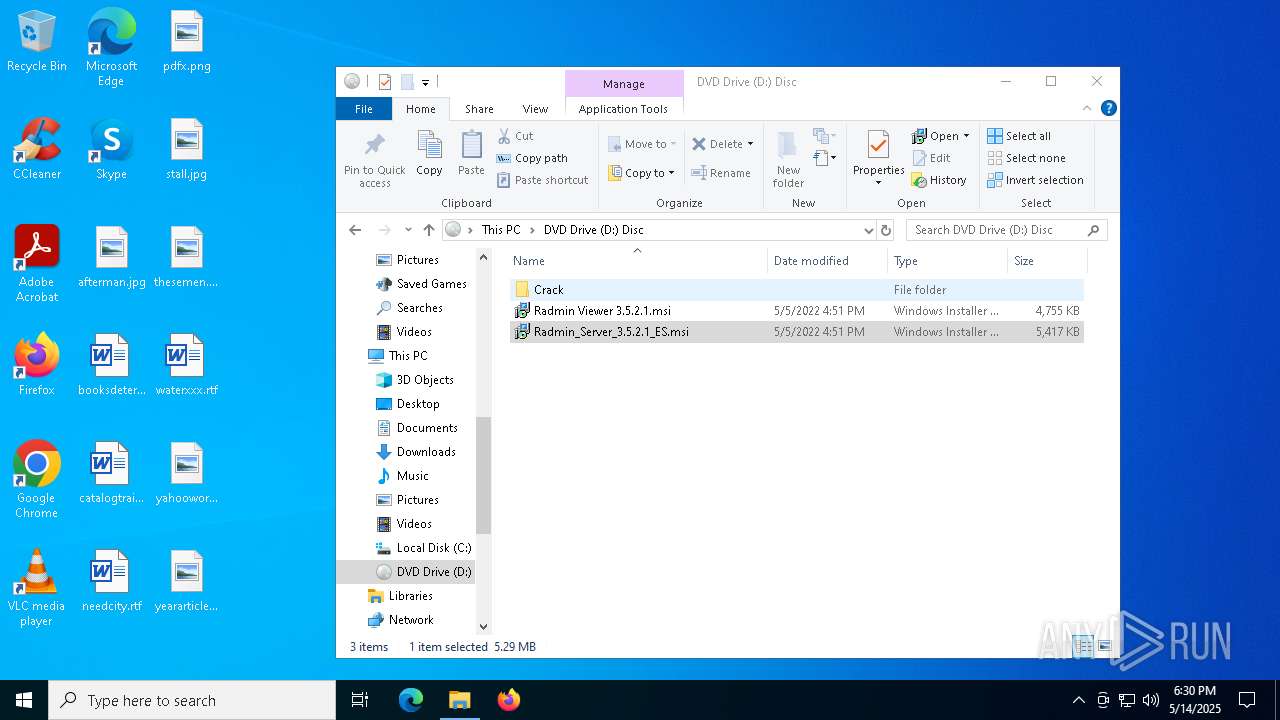
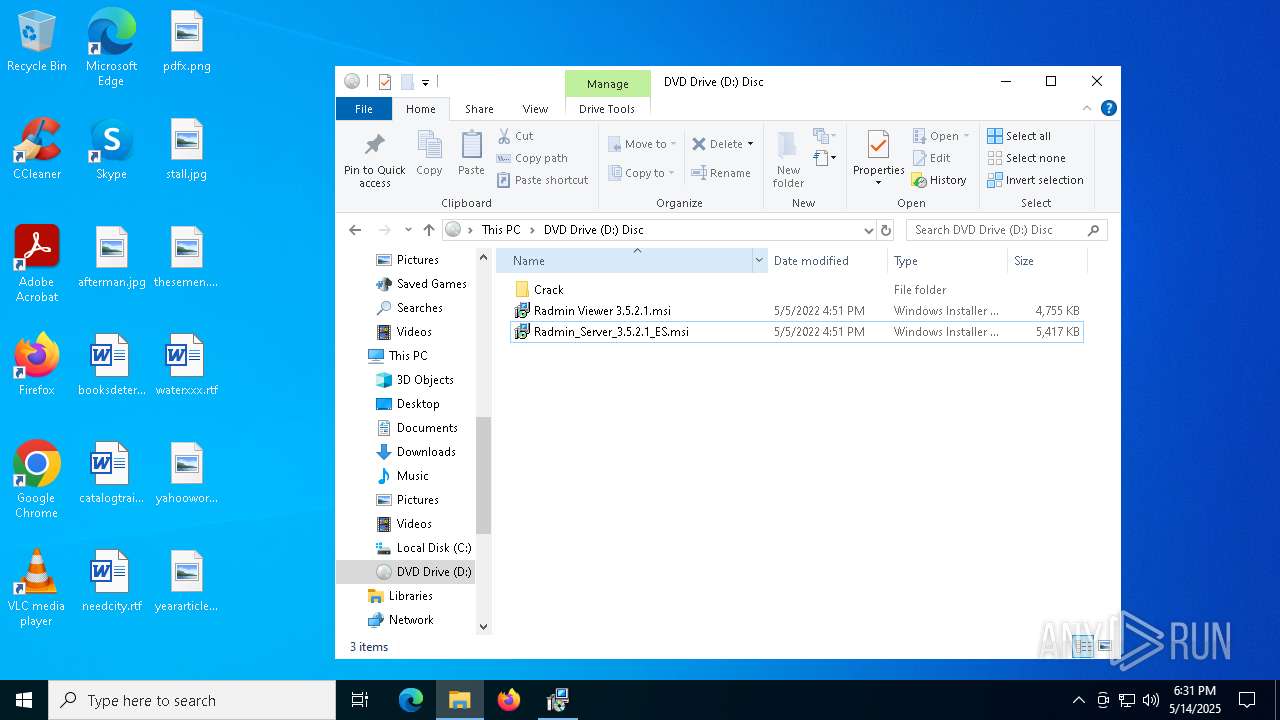
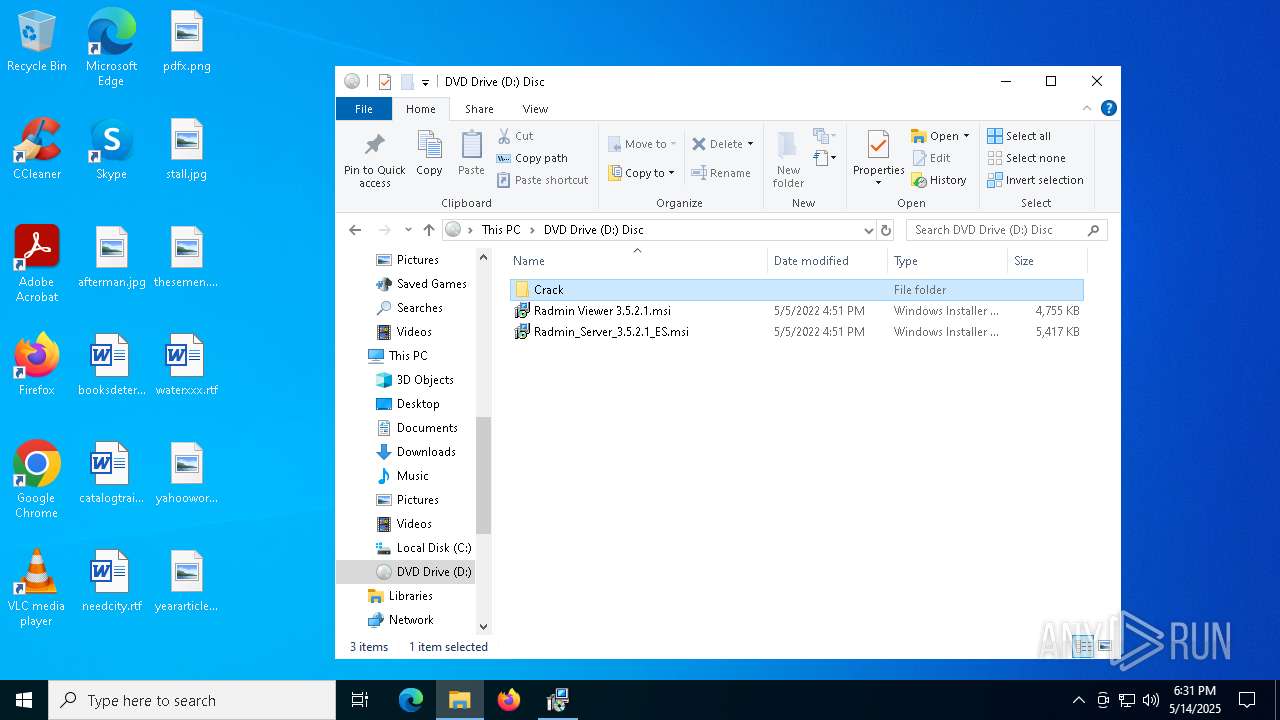
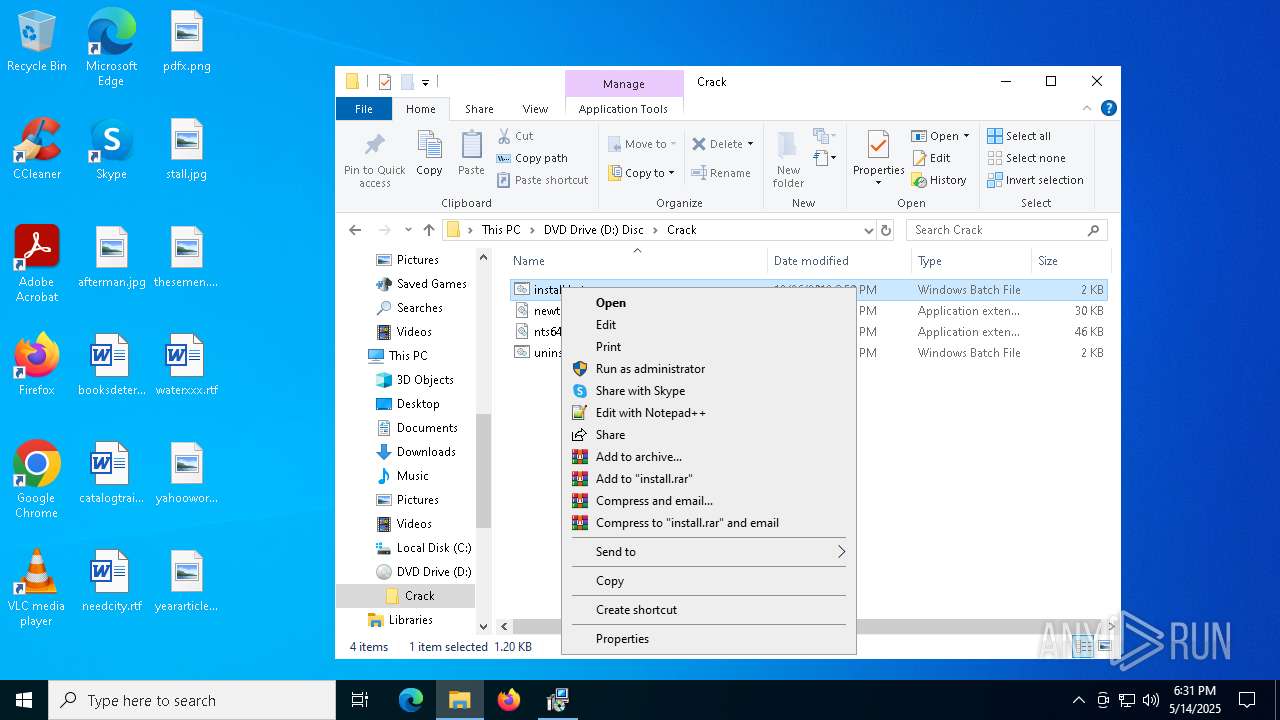
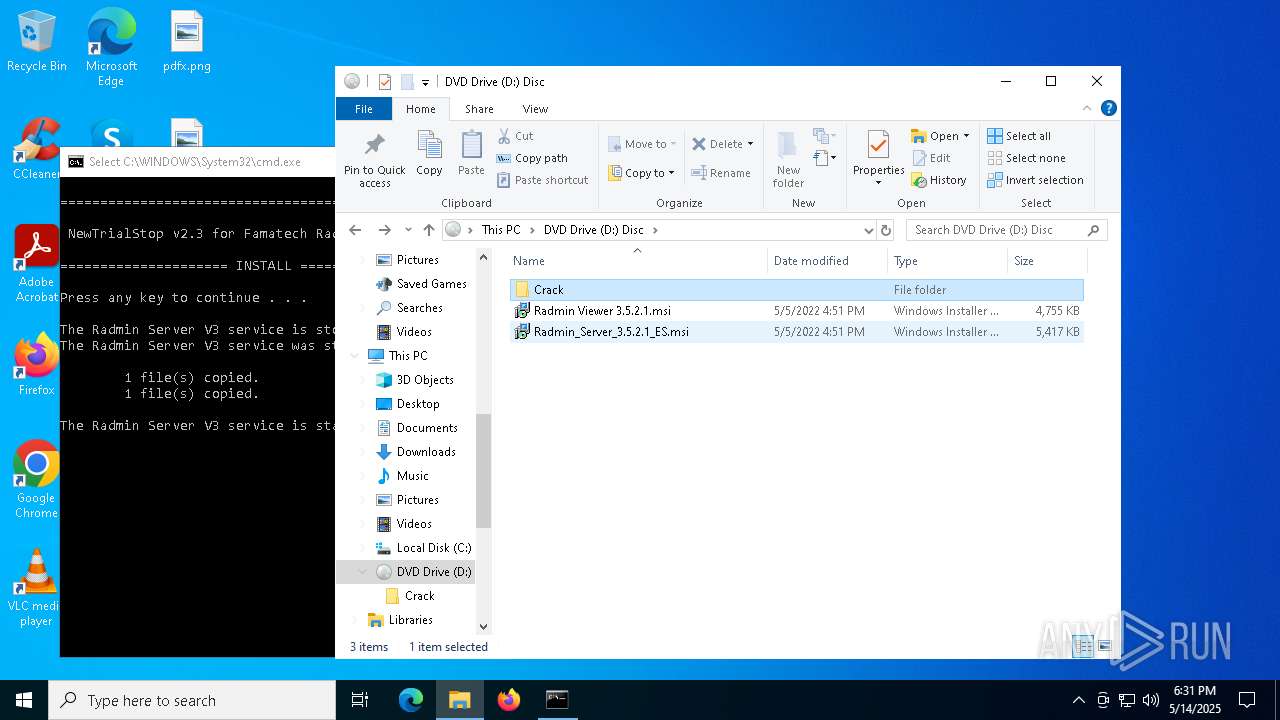
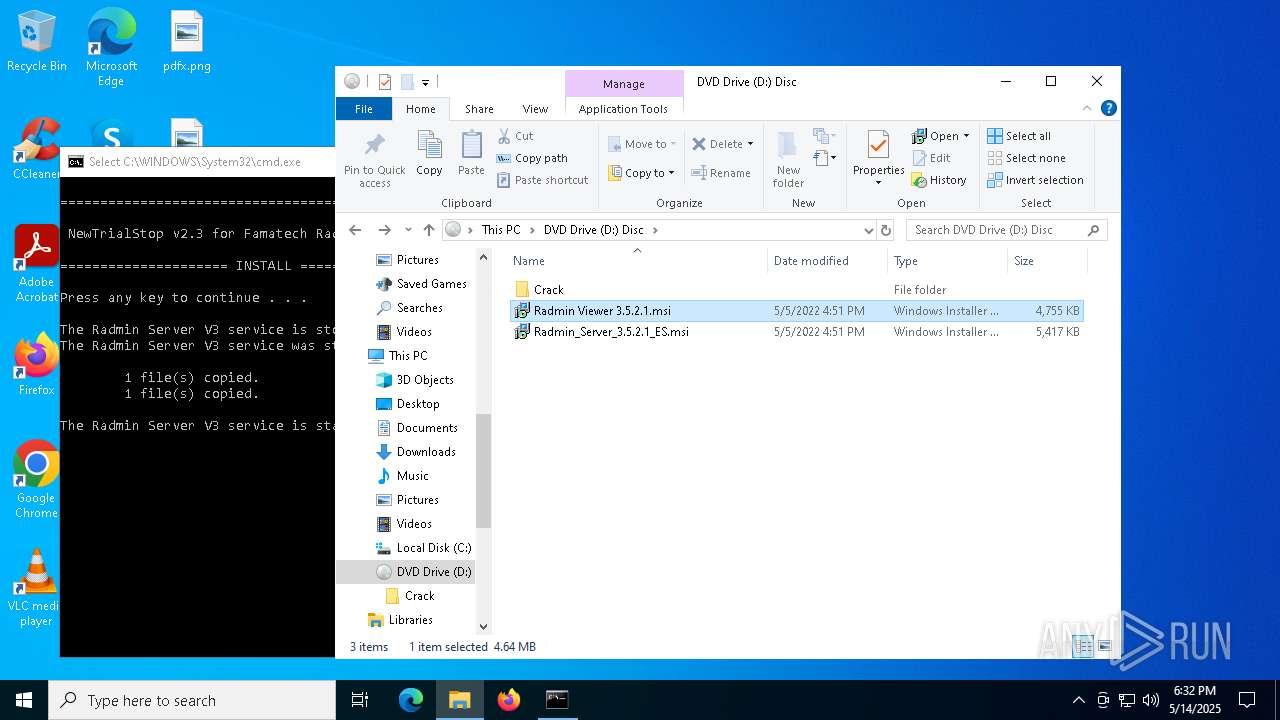
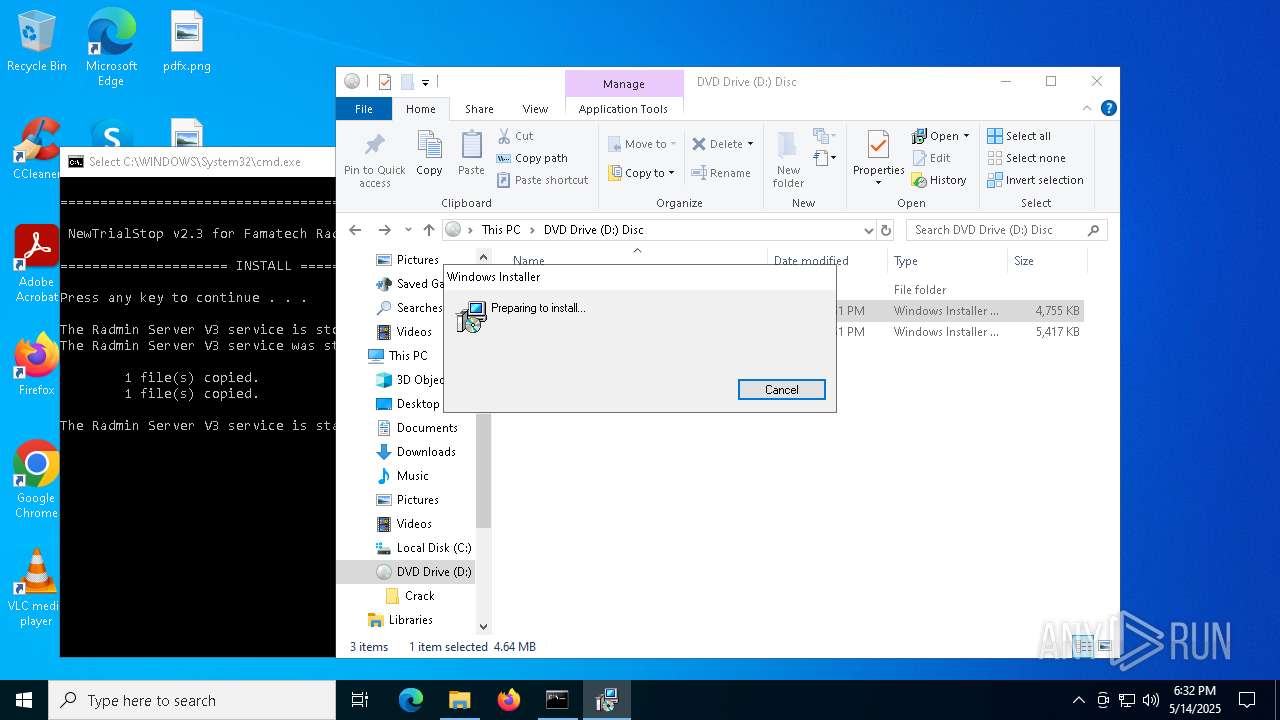
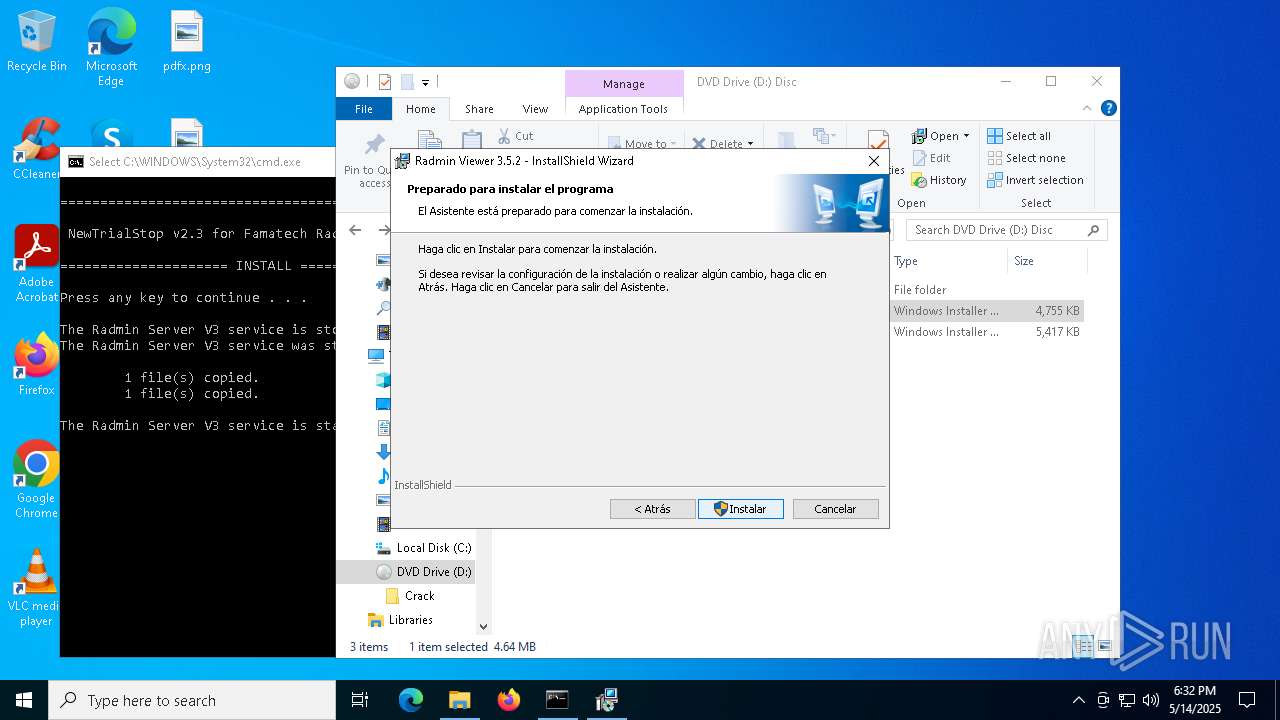
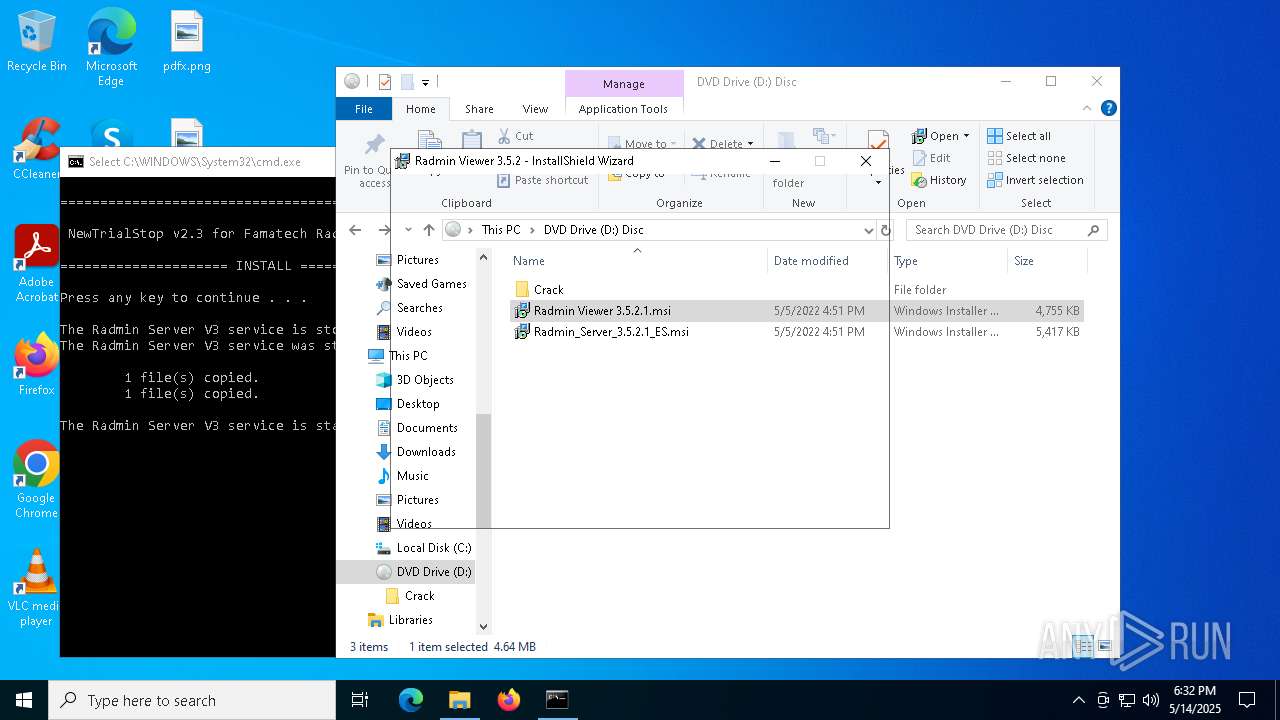
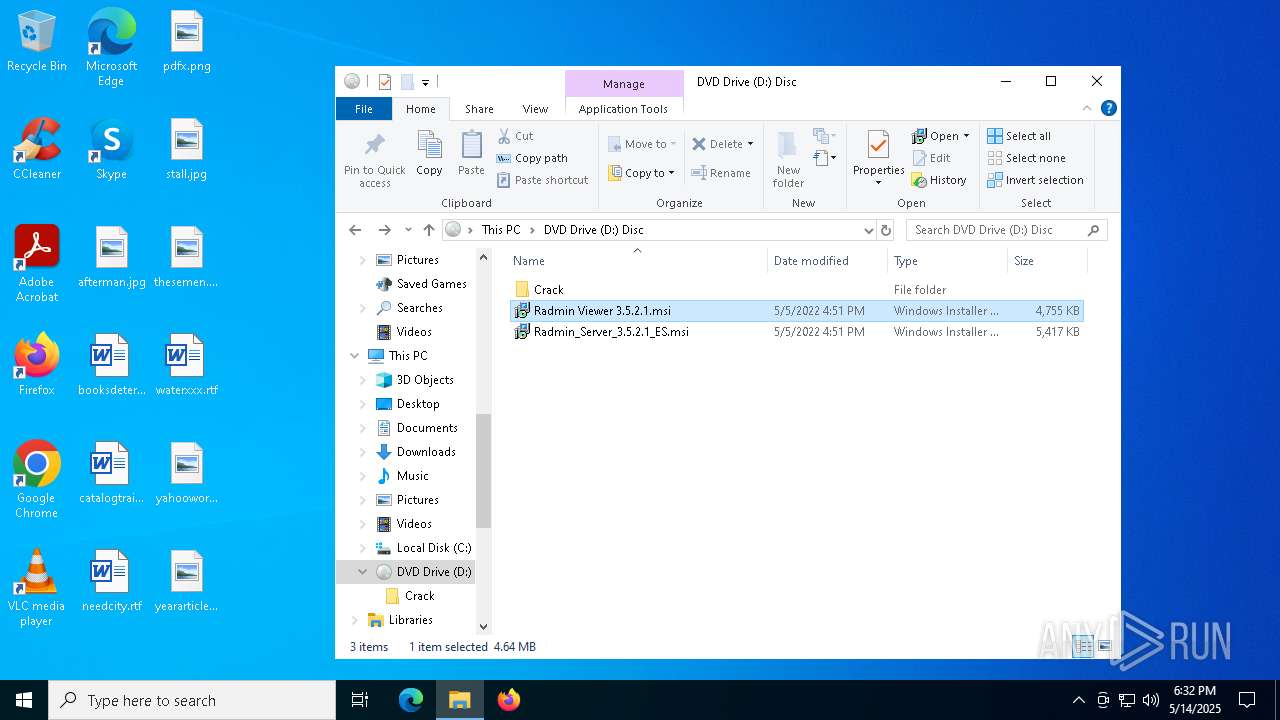
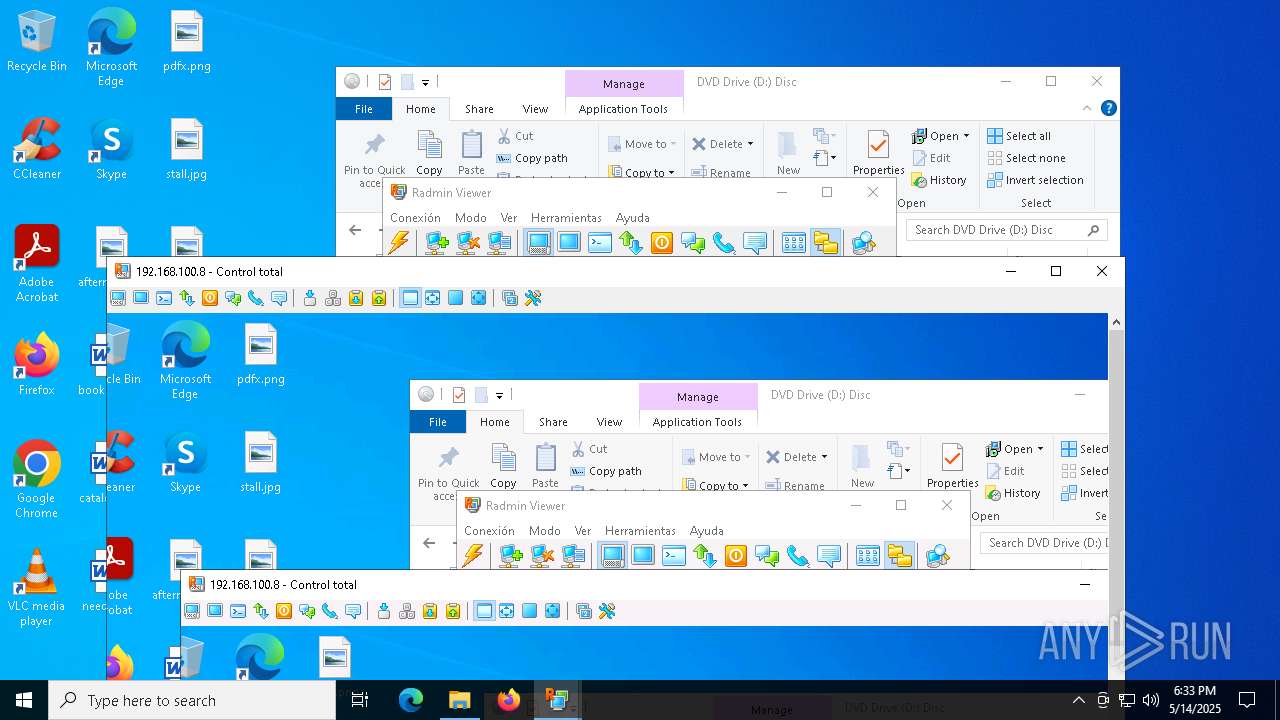
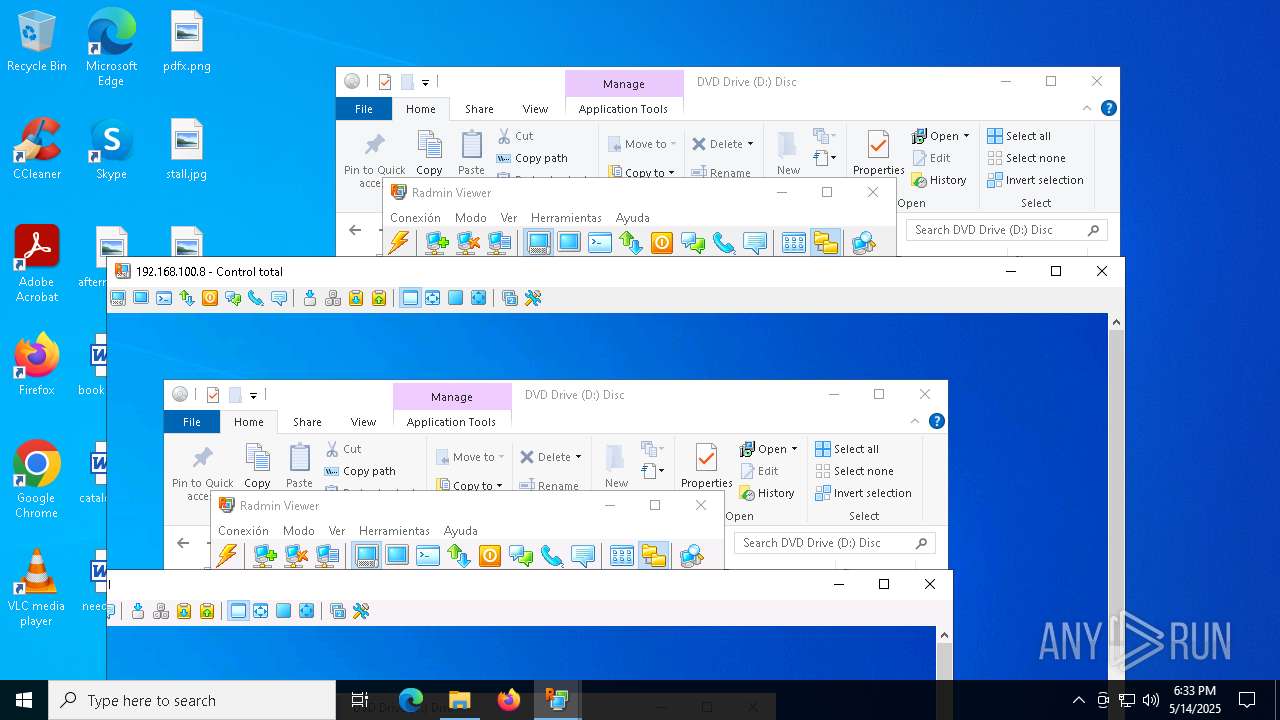
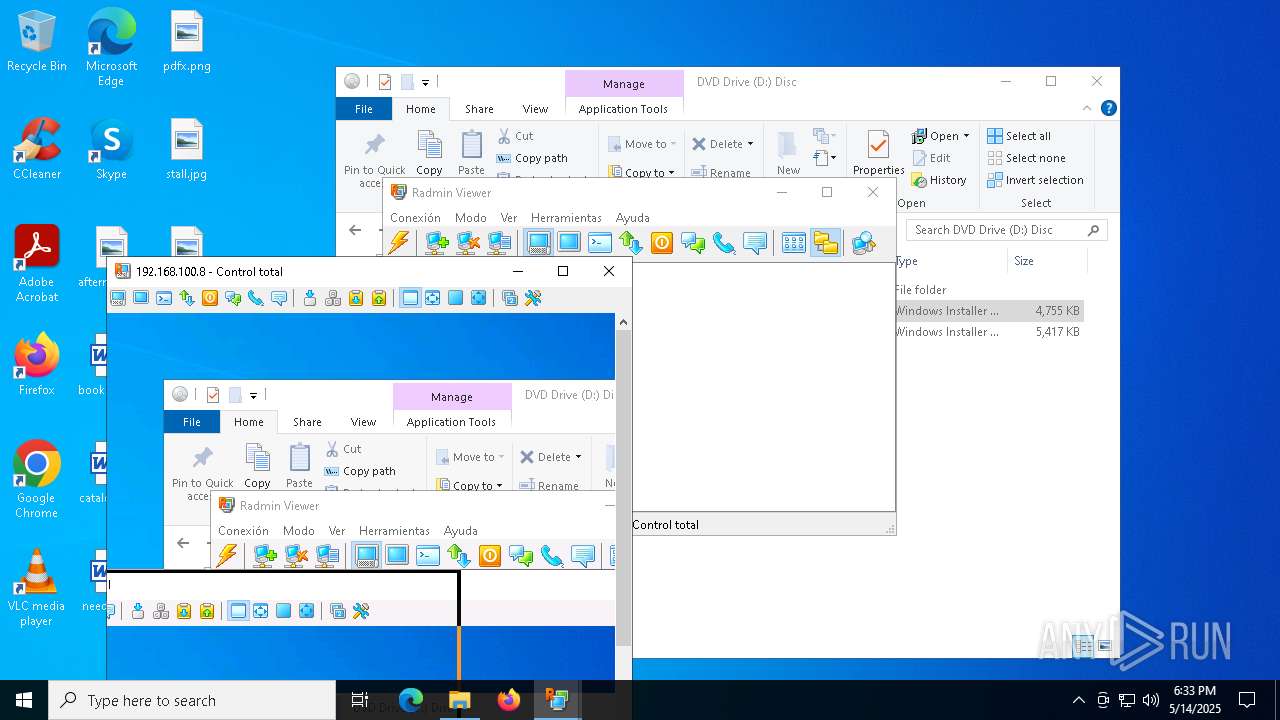
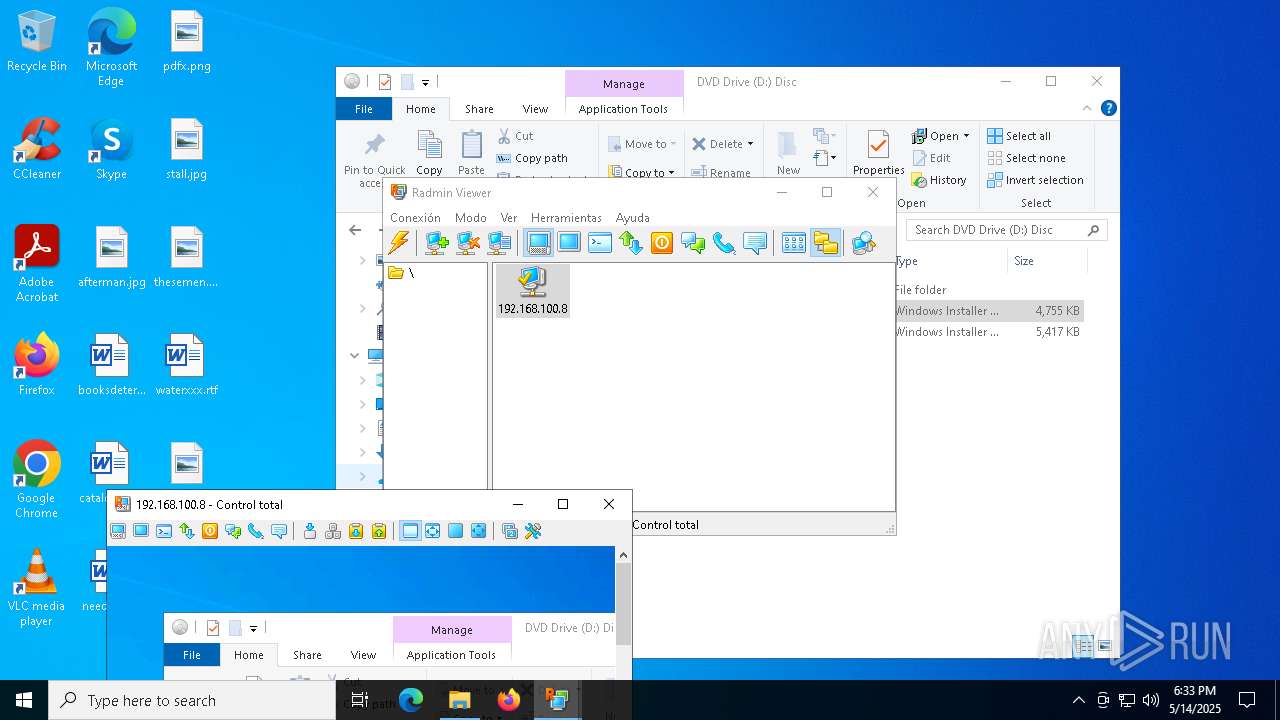
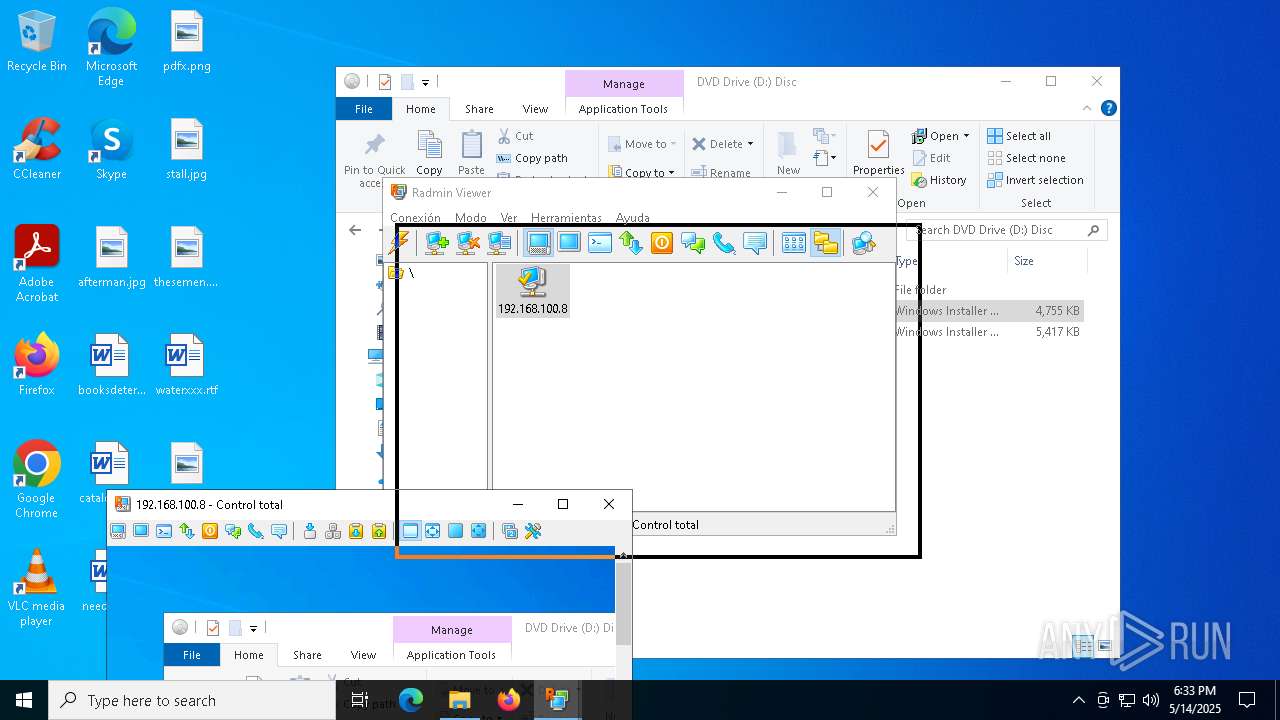
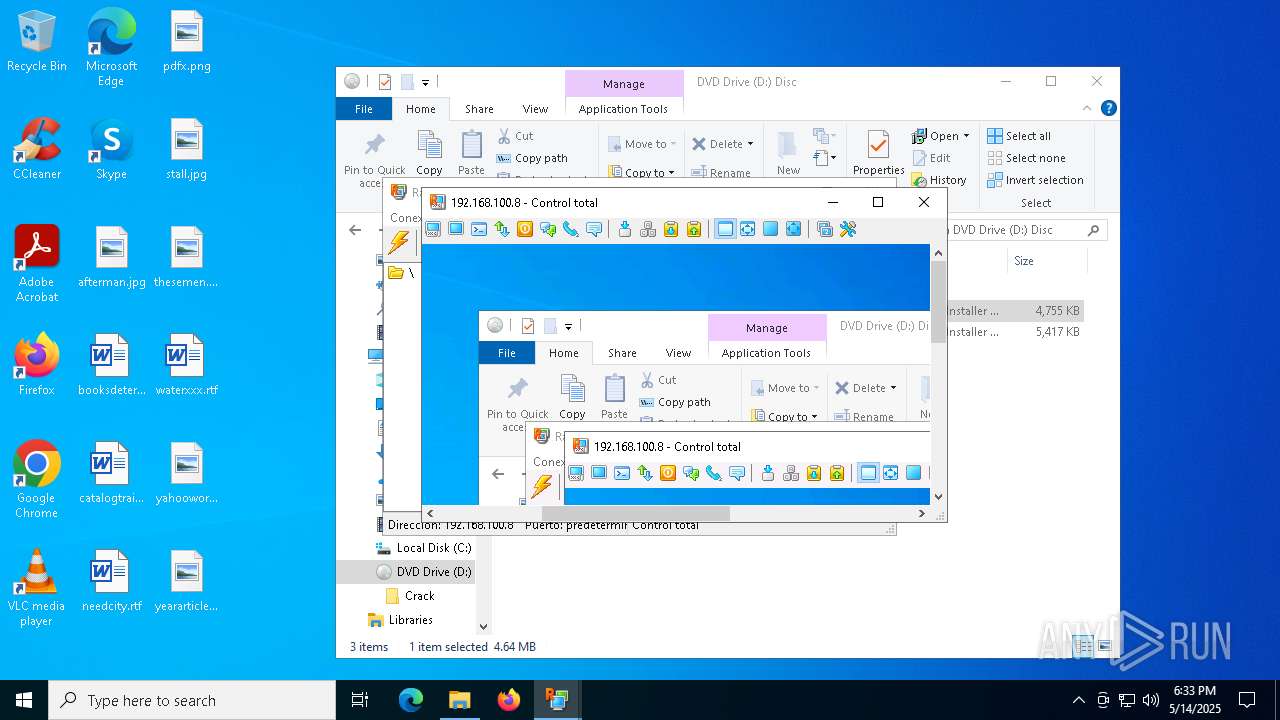
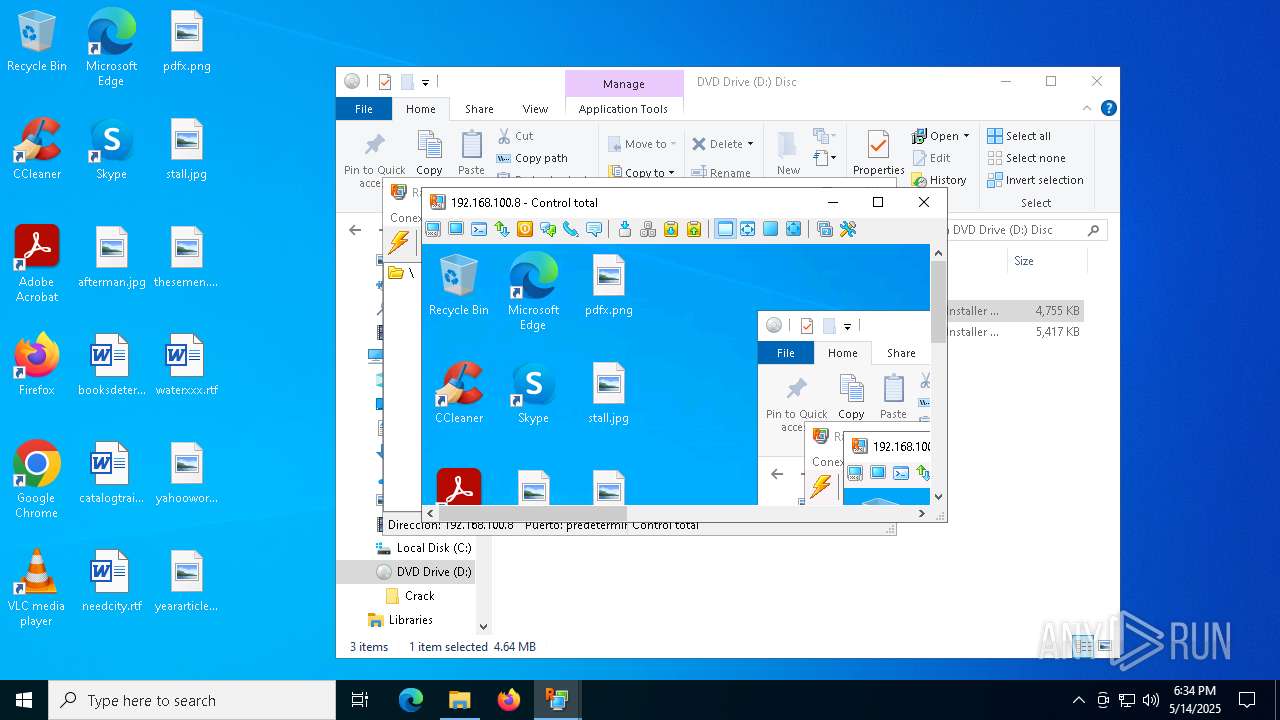
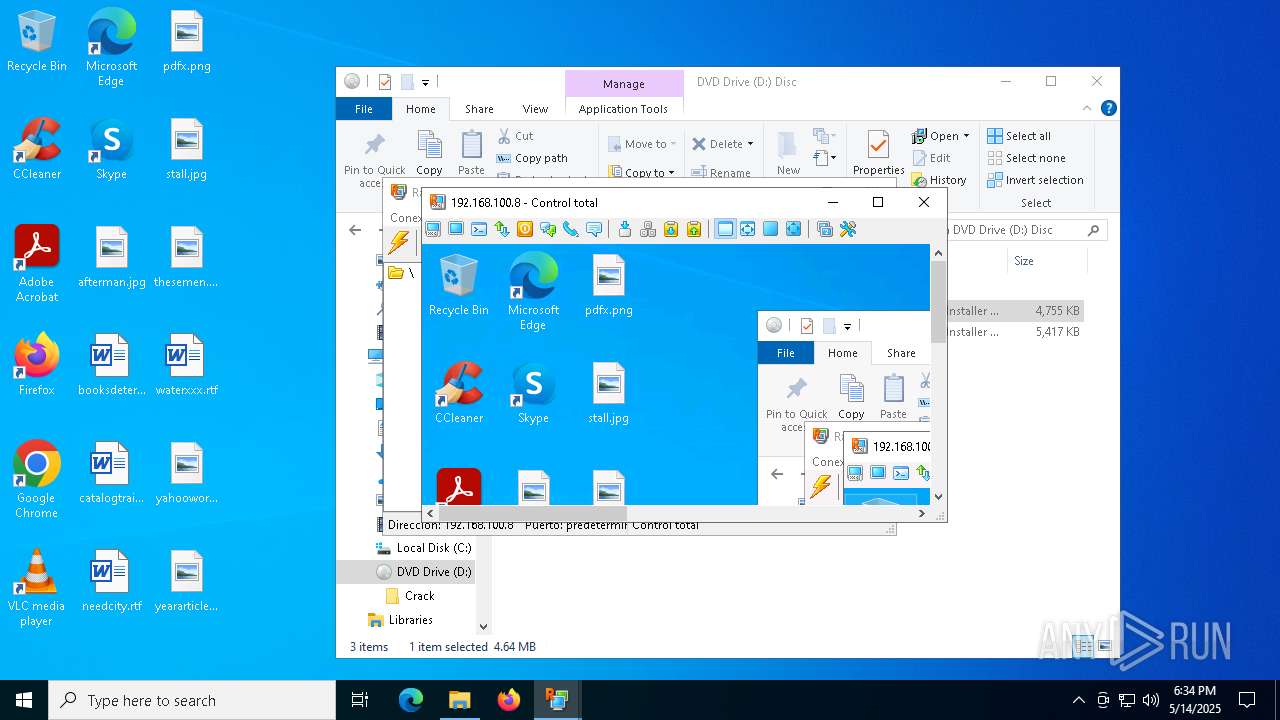
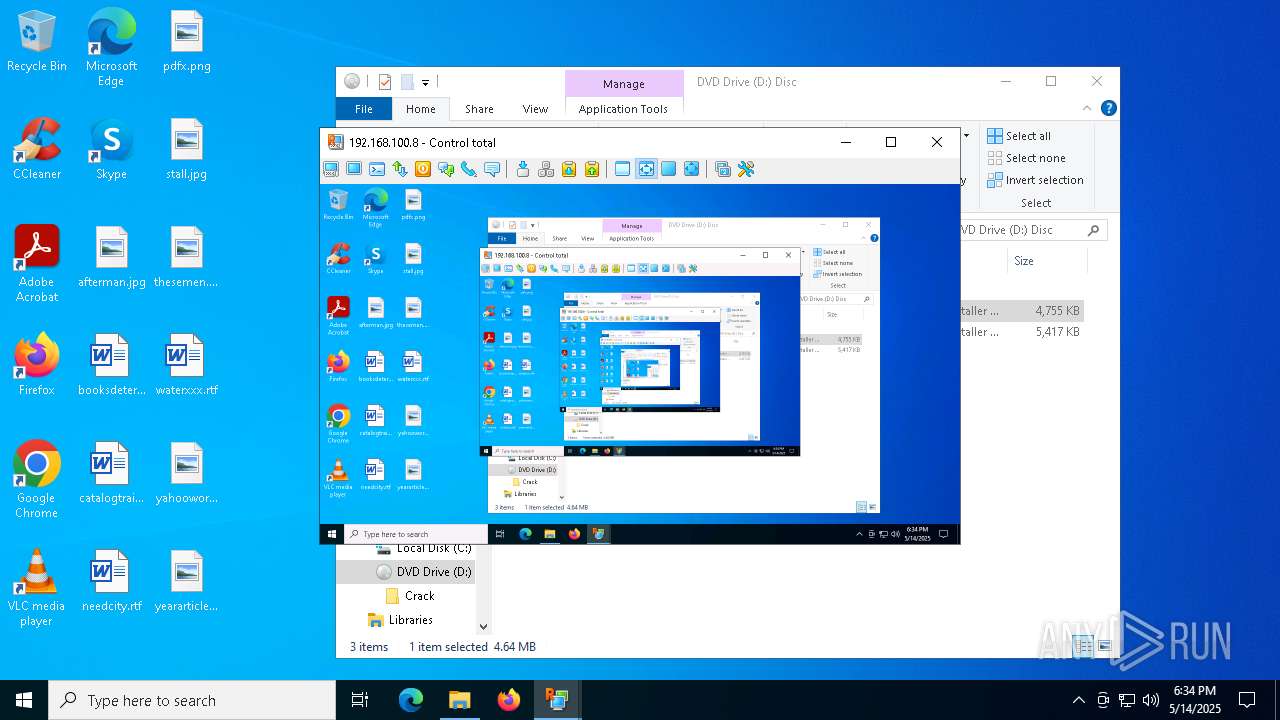
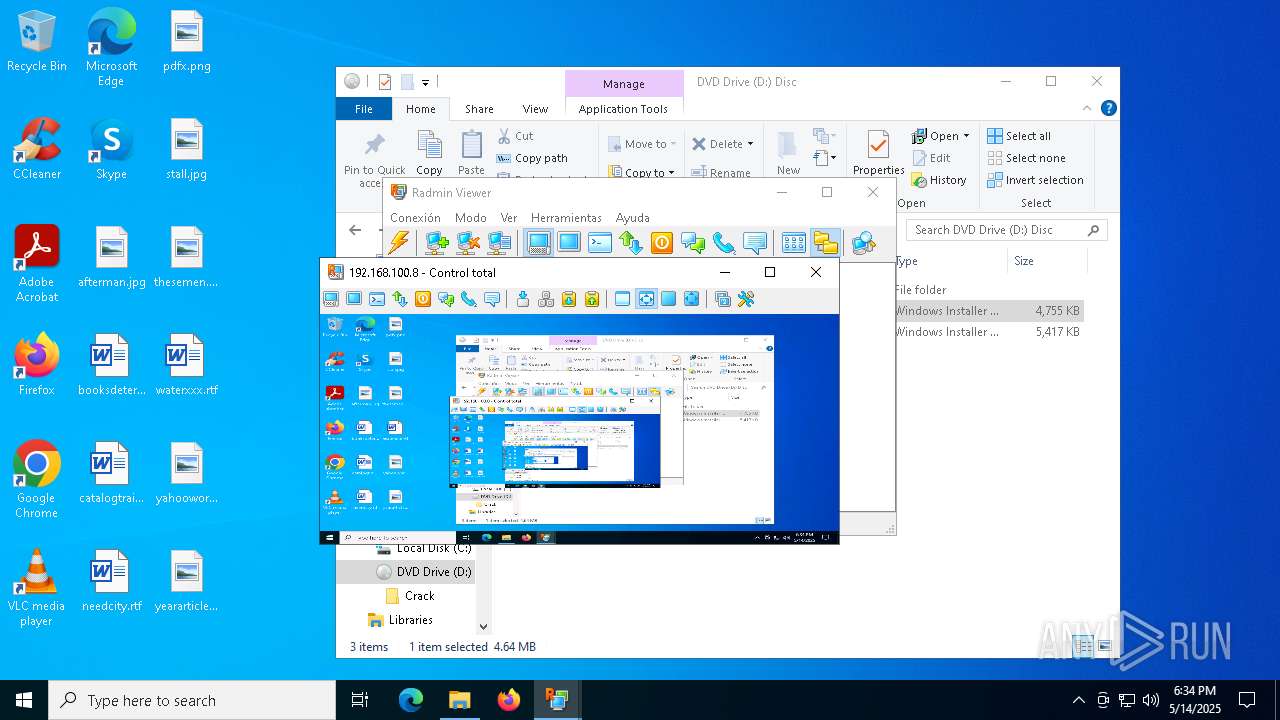
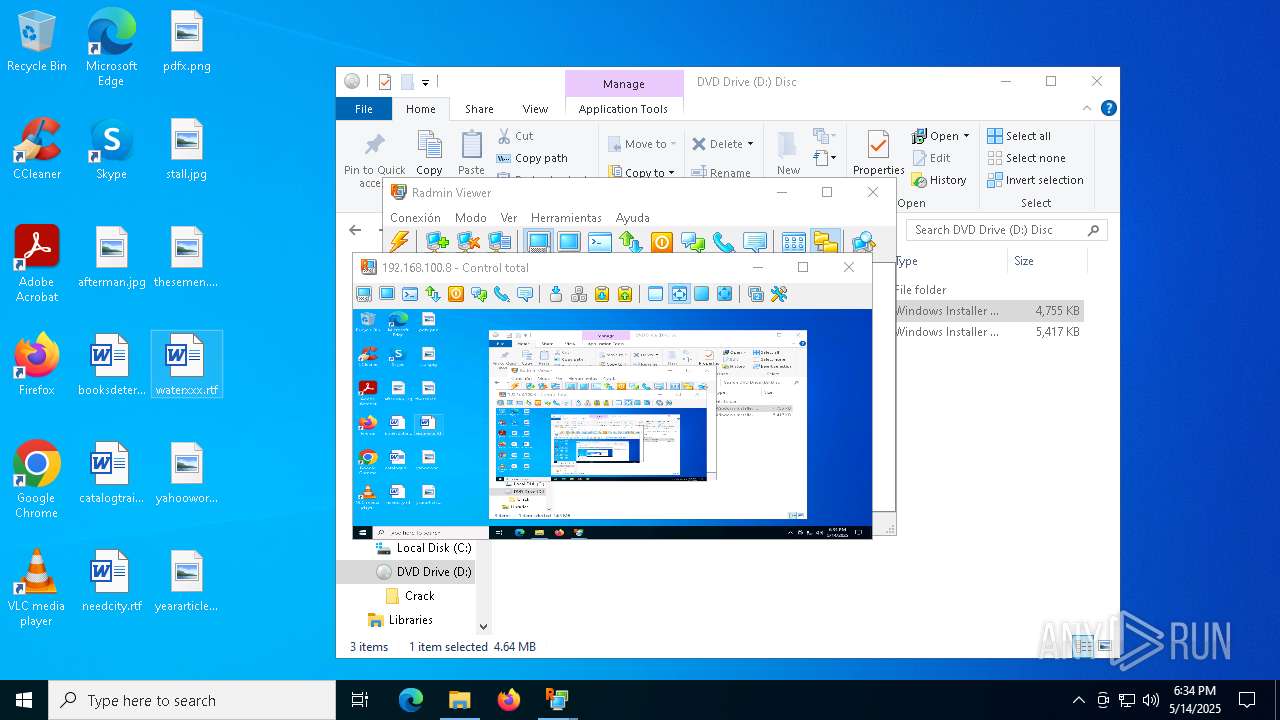
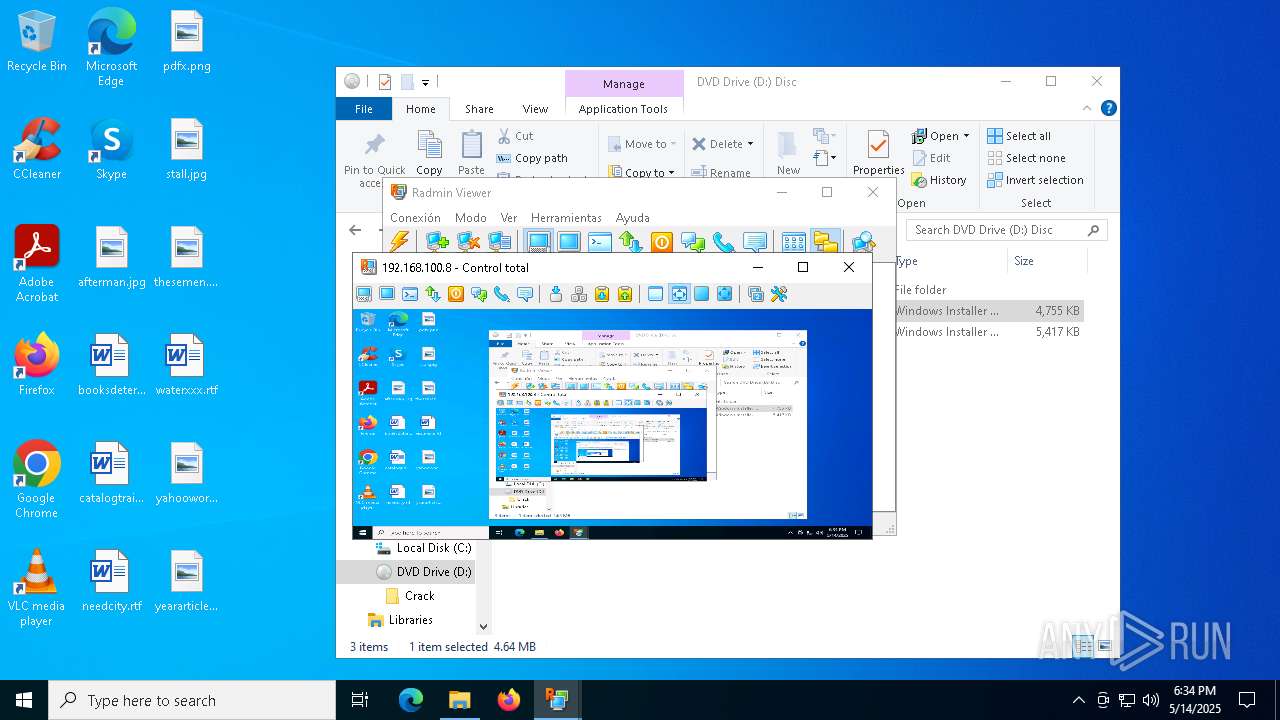
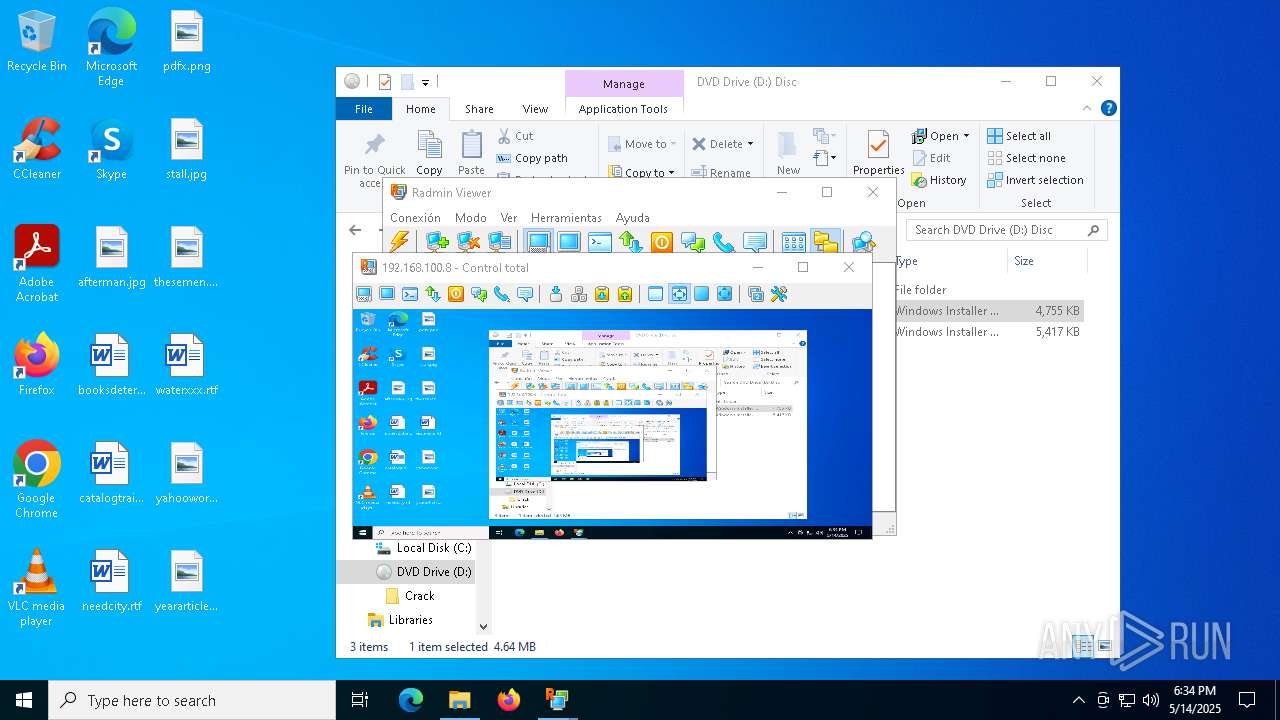
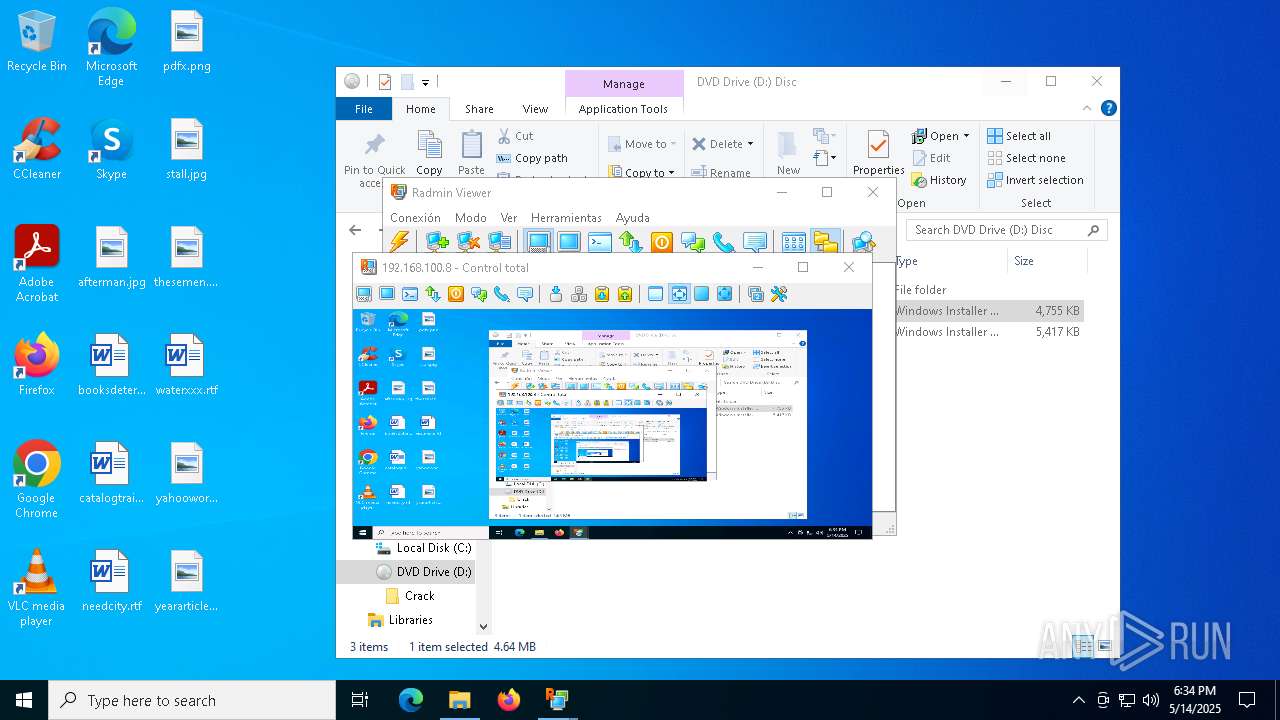
Image mount has been detect
- explorer.exe (PID: 5492)
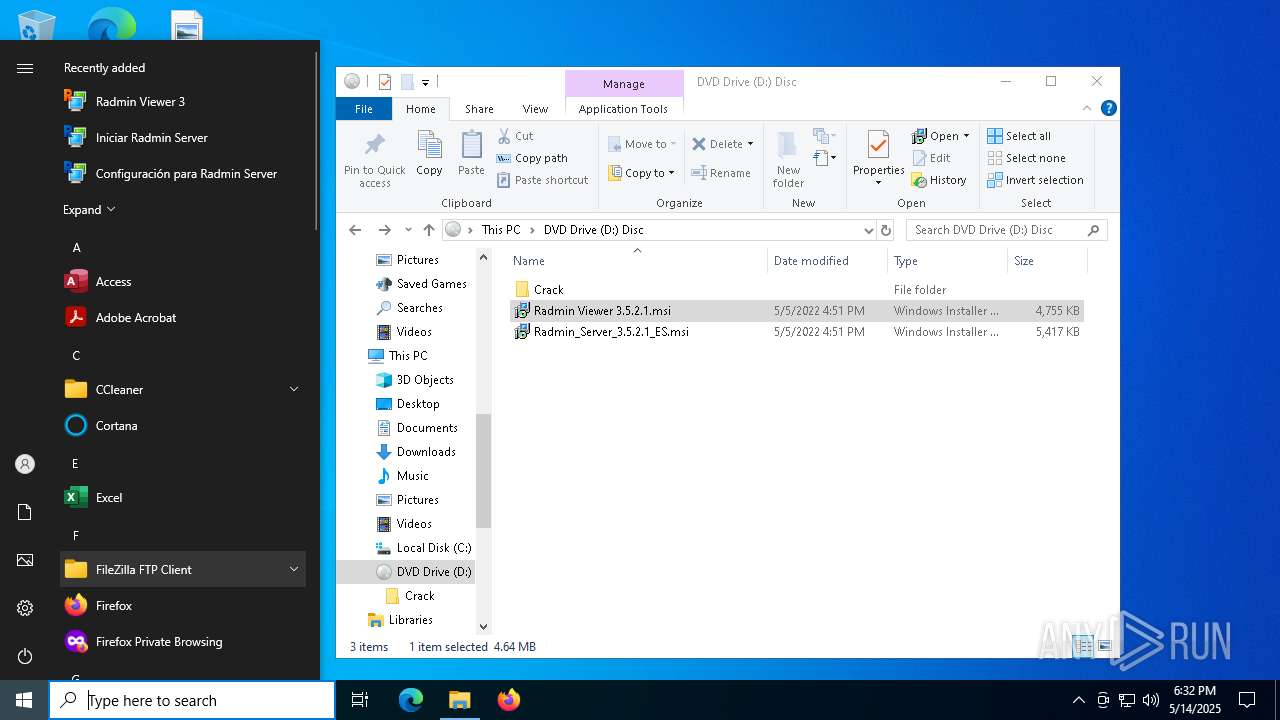
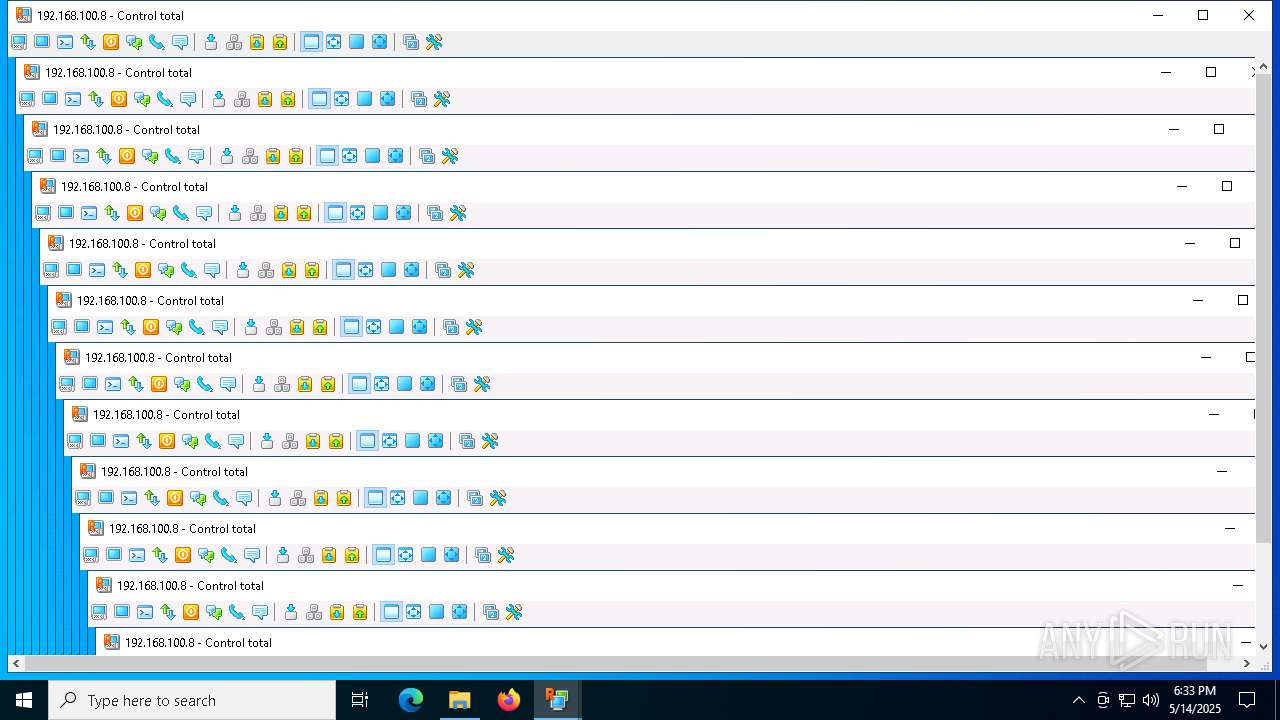
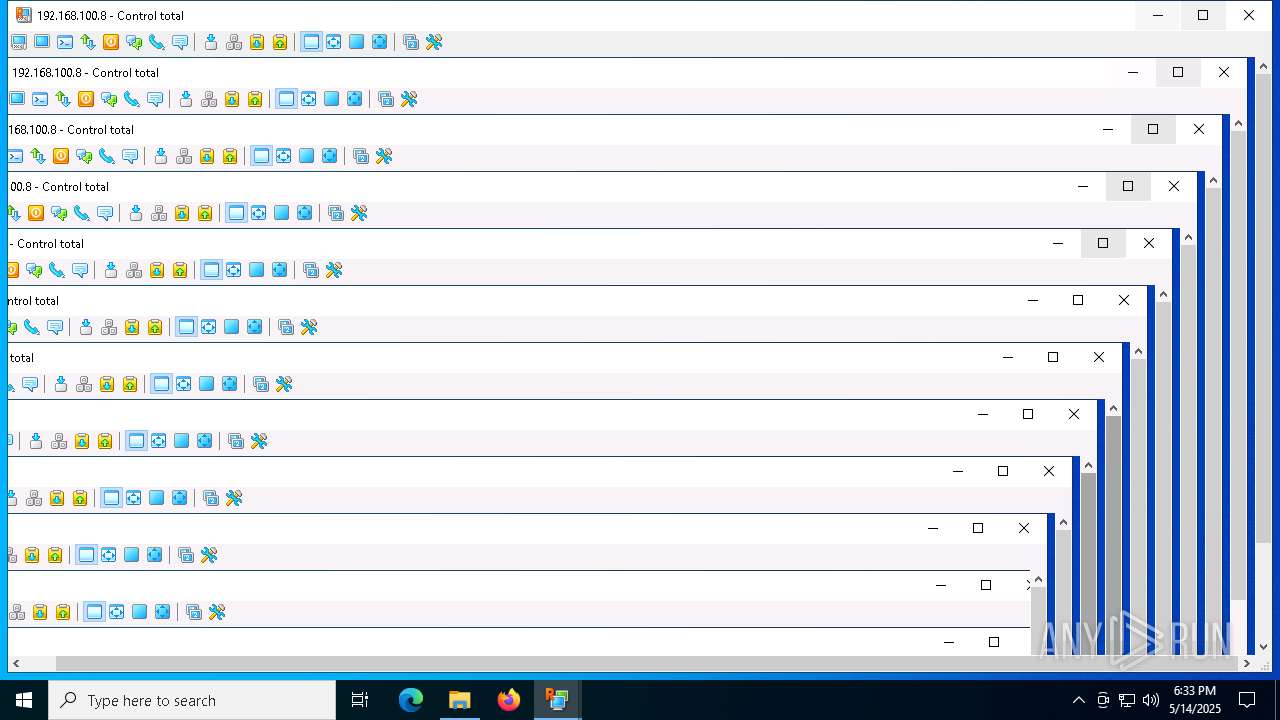
Application launched itself
- explorer.exe (PID: 5492)
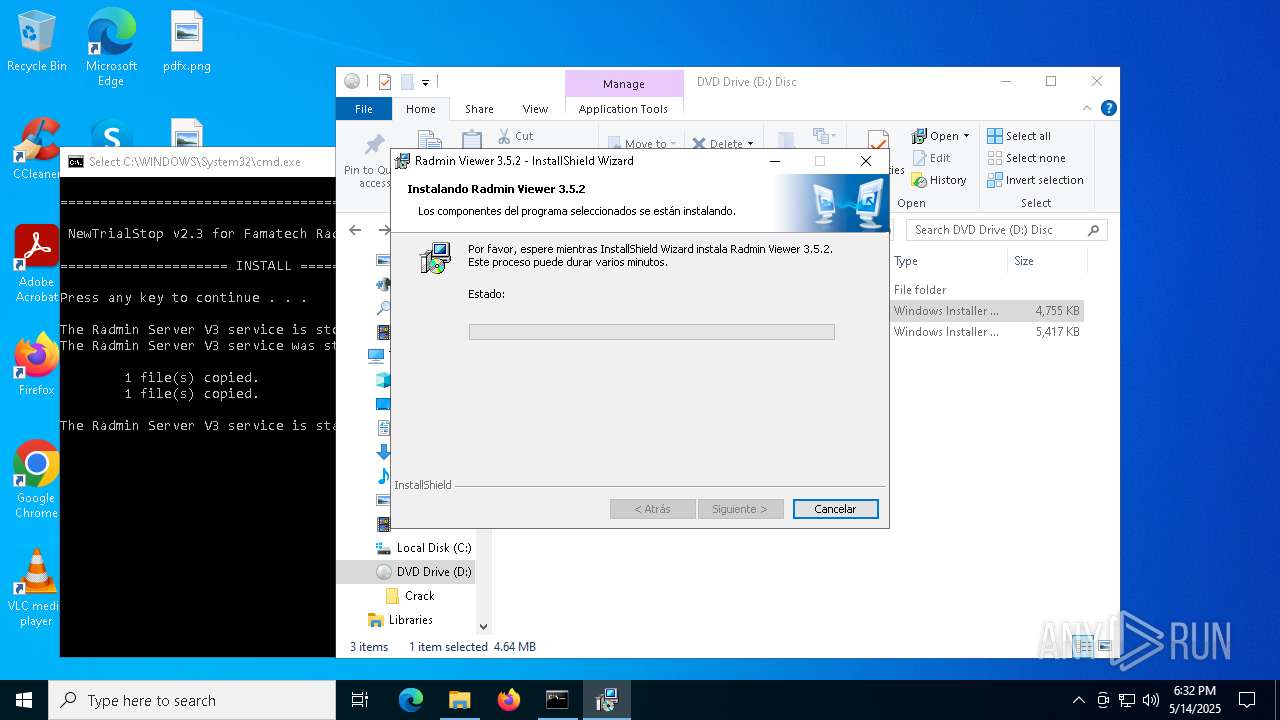
- msiexec.exe (PID: 8124)
- FamItrfc.Exe (PID: 3768)
- FamItrfc.Exe (PID: 3396)
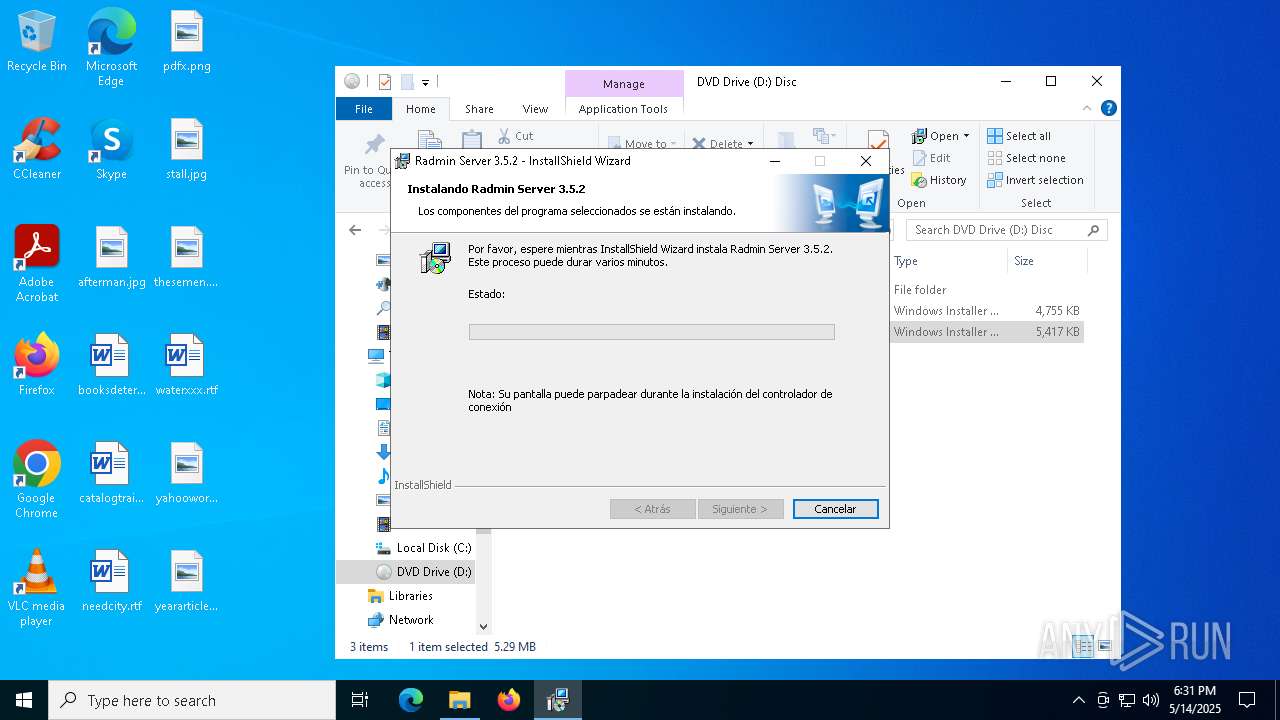
Executes as Windows Service
- VSSVC.exe (PID: 736)
- rserver3.exe (PID: 644)
- rserver3.exe (PID: 6940)
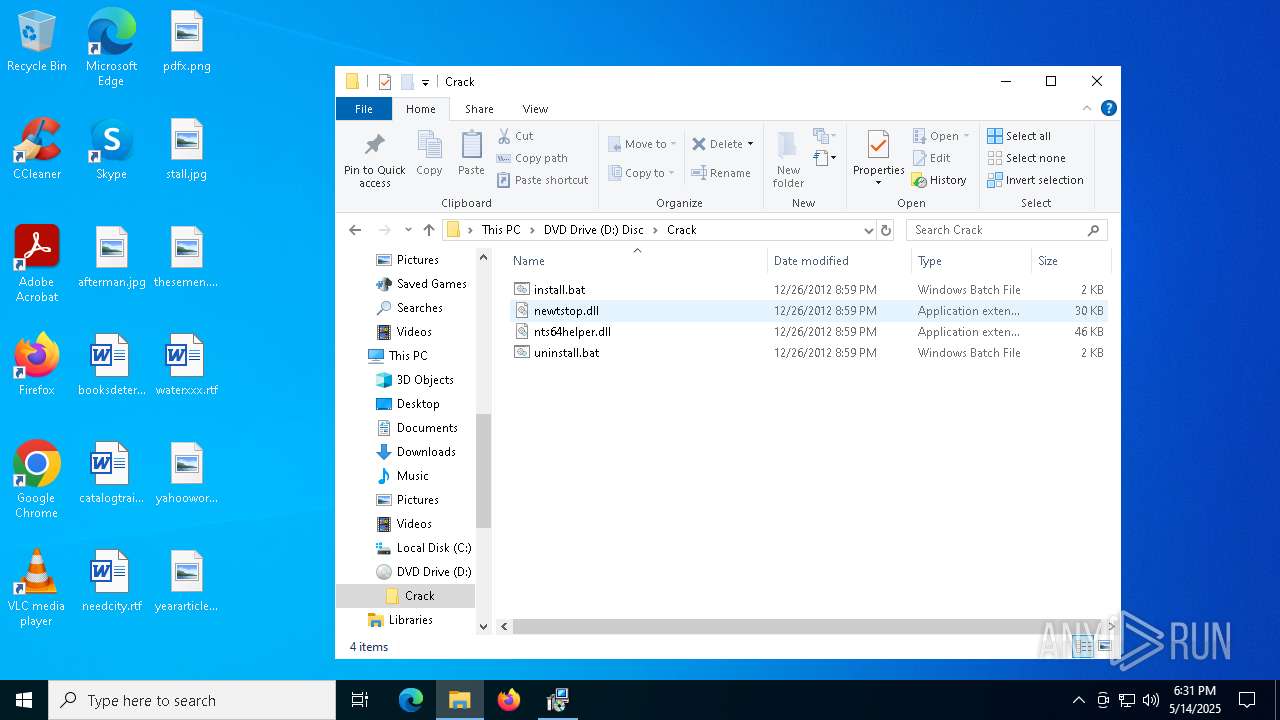
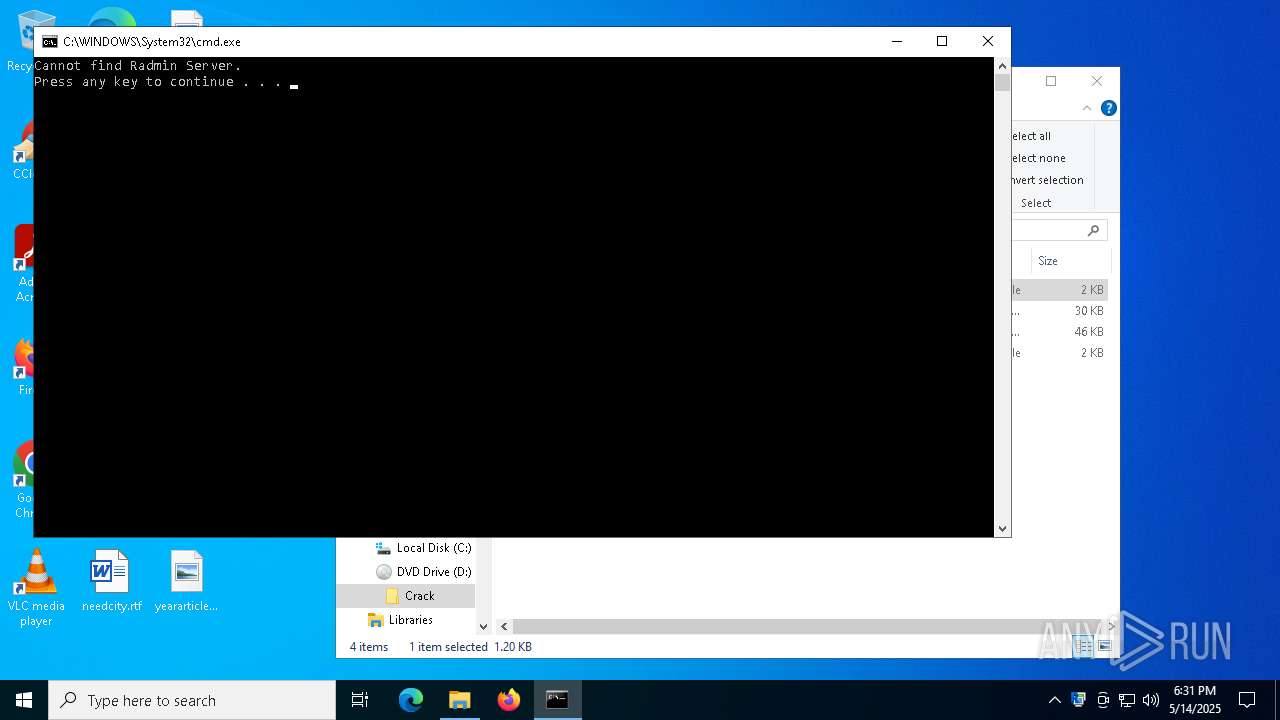
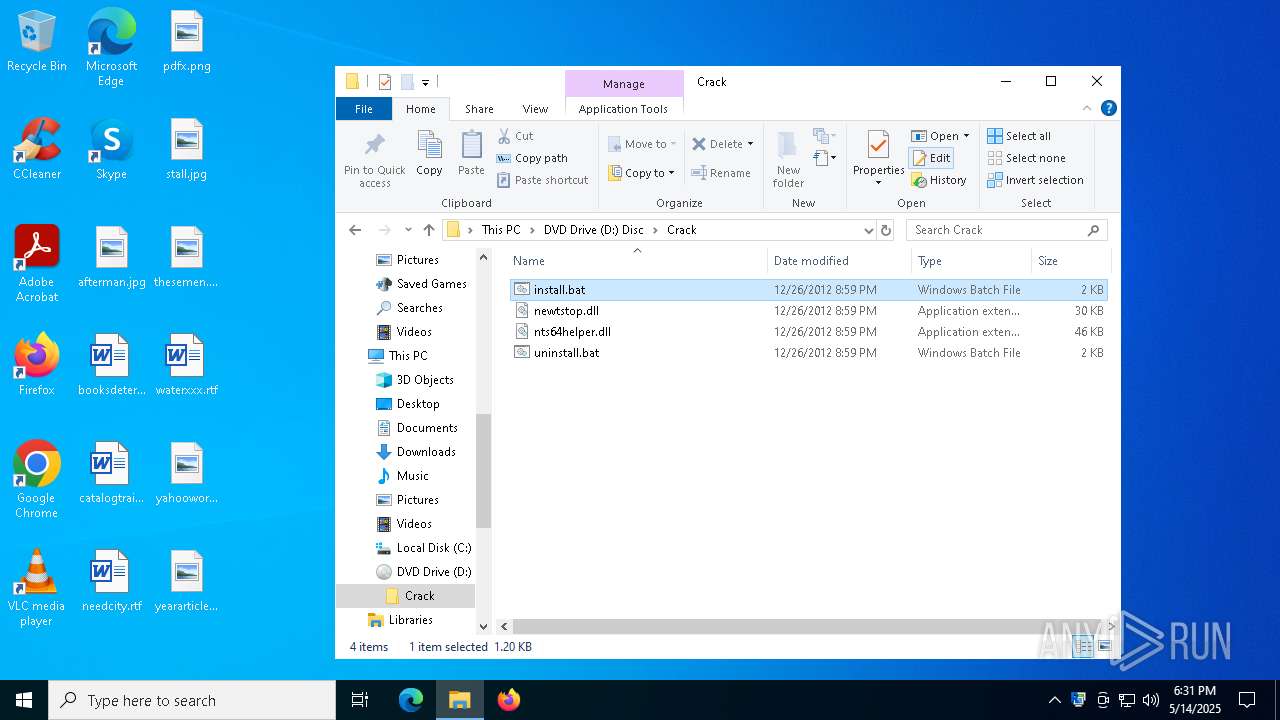
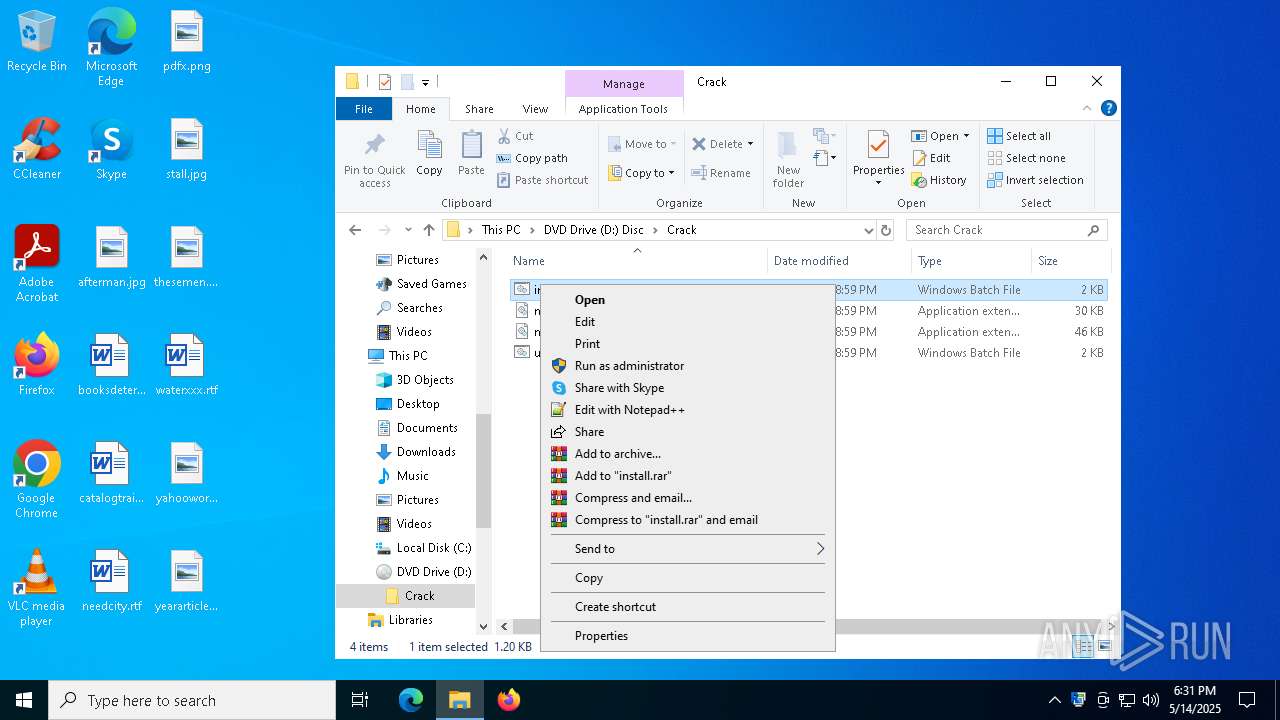
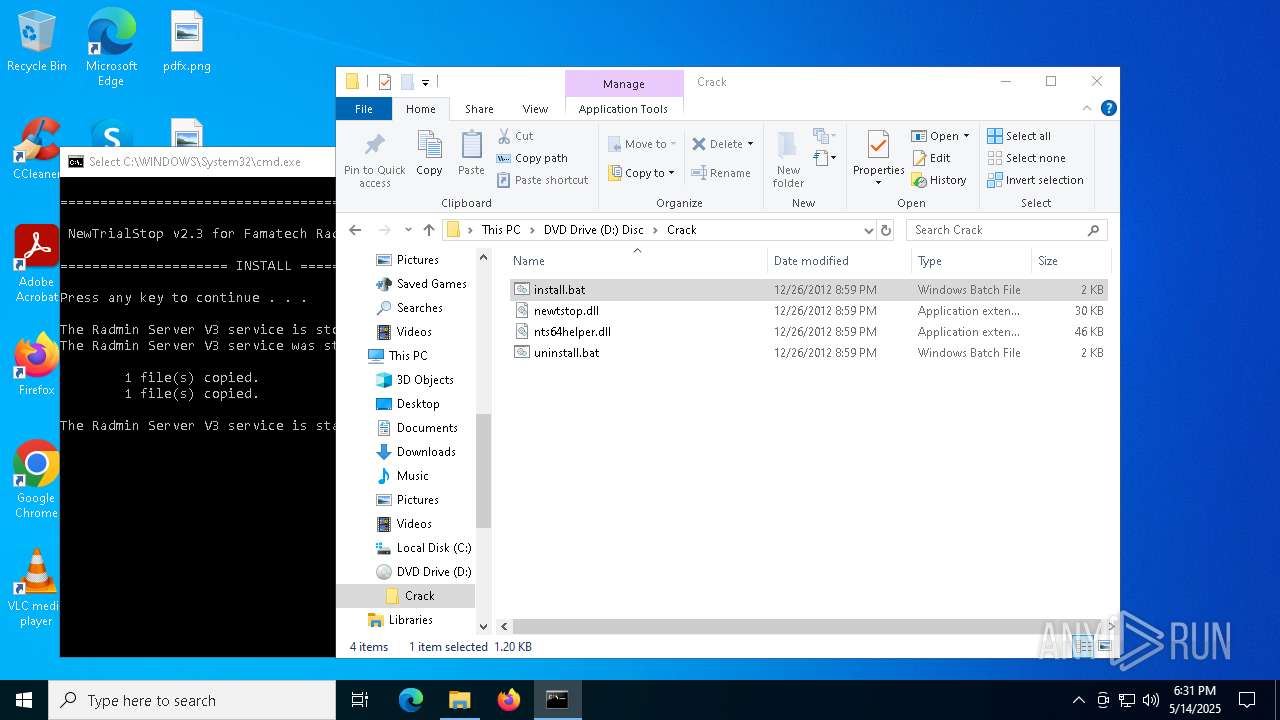
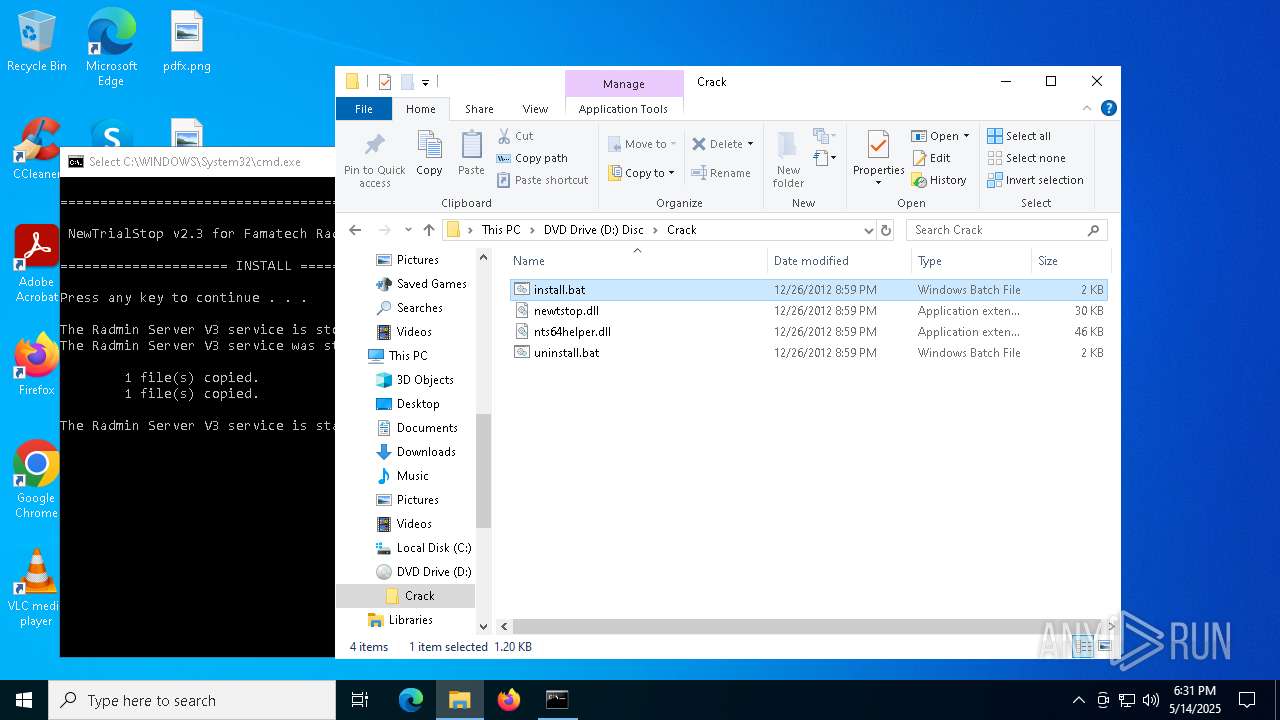
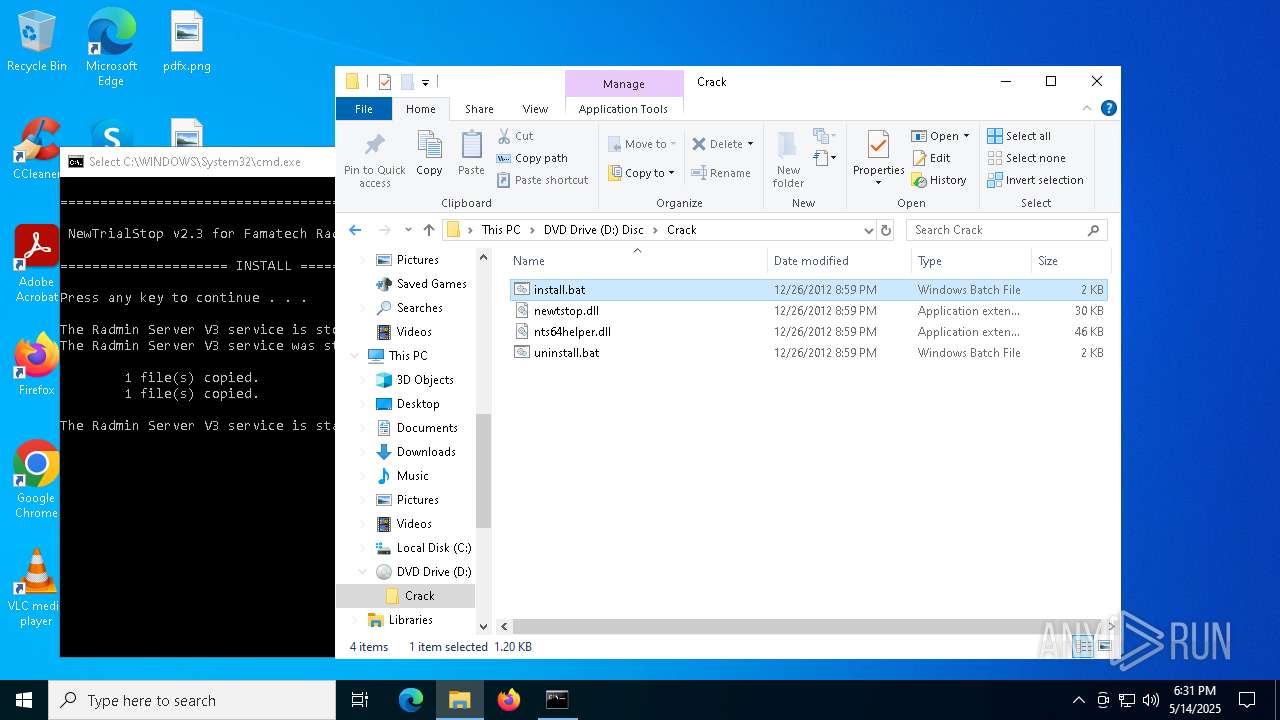
Executing commands from a ".bat" file
- explorer.exe (PID: 5492)
Starts CMD.EXE for commands execution
- explorer.exe (PID: 5492)
Process drops legitimate windows executable
- msiexec.exe (PID: 632)
- msiexec.exe (PID: 8124)
Uses NETSH.EXE to add a firewall rule or allowed programs
- msiexec.exe (PID: 7480)
Drops a system driver (possible attempt to evade defenses)
- msiexec.exe (PID: 8124)
Uses RUNDLL32.EXE to load library
- cmd.exe (PID: 5360)
Executable content was dropped or overwritten
- cmd.exe (PID: 5360)
INFO
Reads security settings of Internet Explorer
- explorer.exe (PID: 5492)
- msiexec.exe (PID: 7904)
Reads Microsoft Office registry keys
- explorer.exe (PID: 5492)
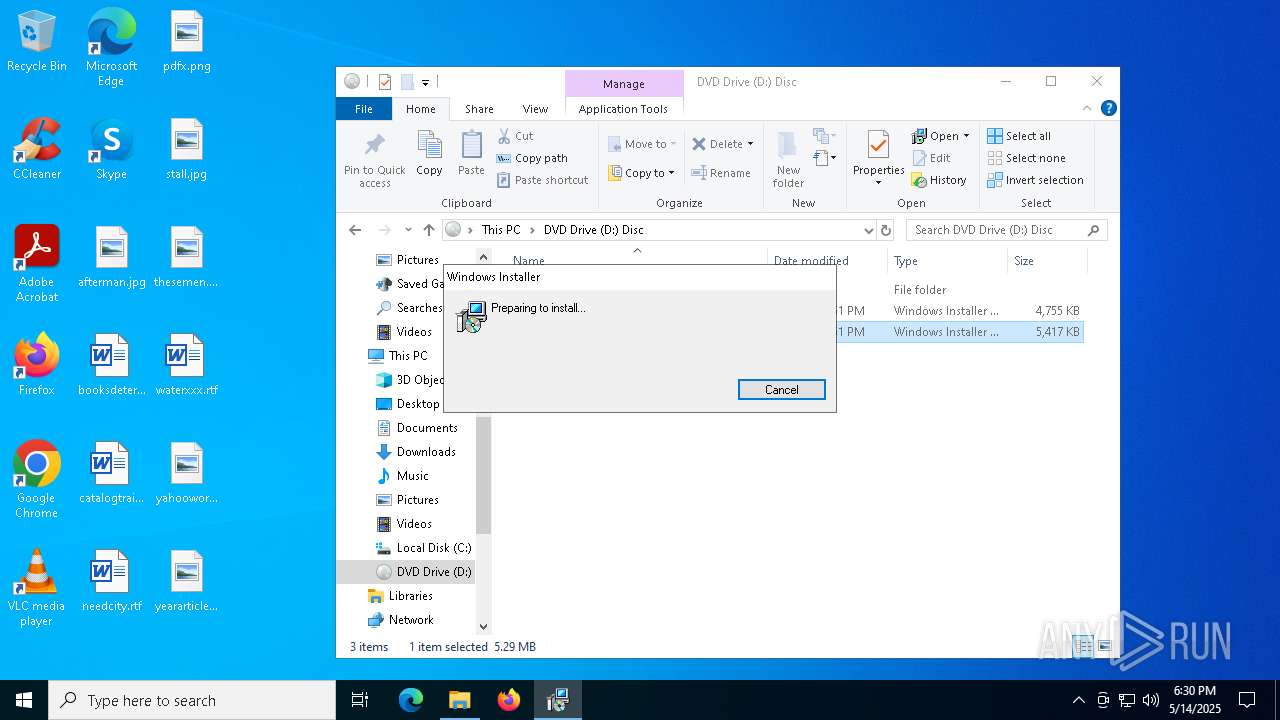
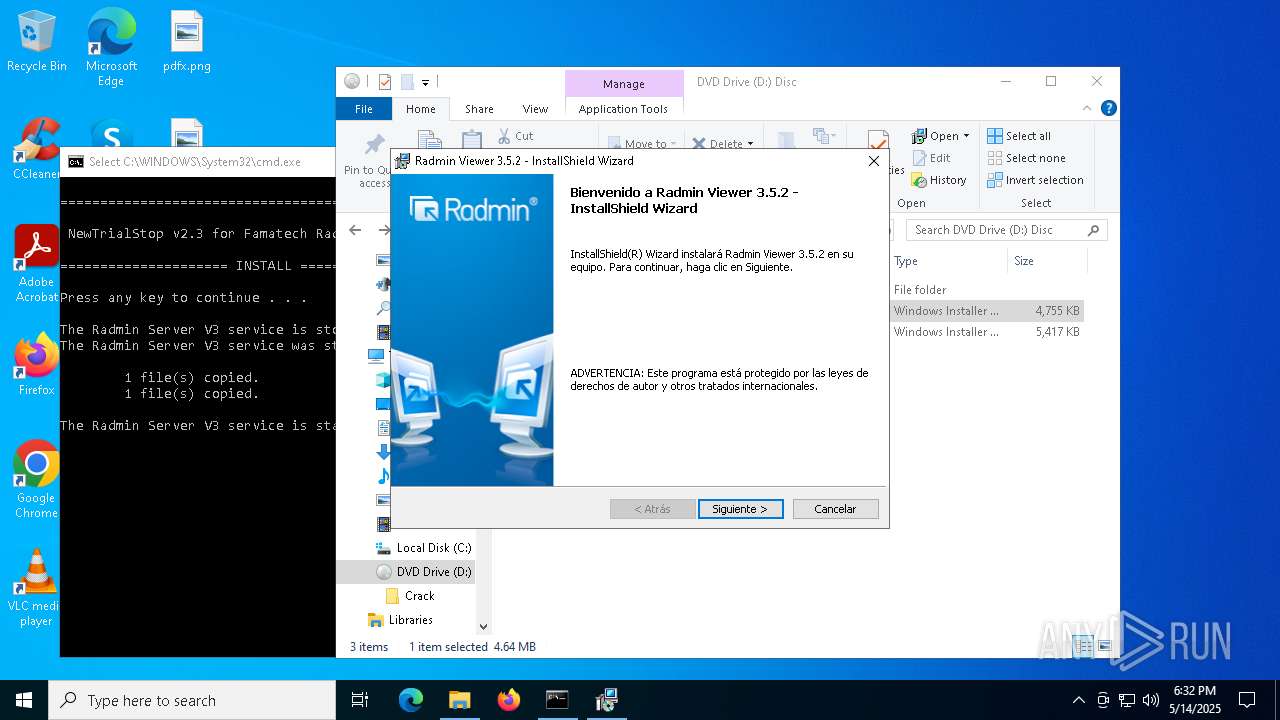
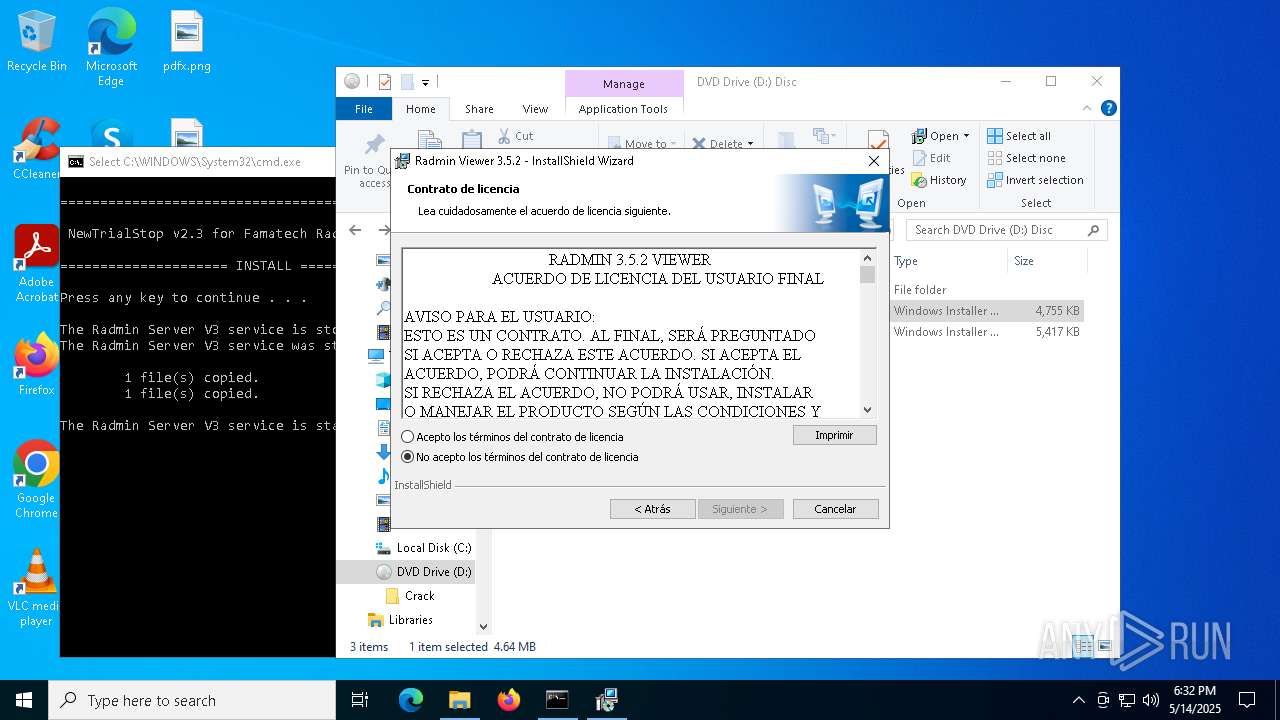
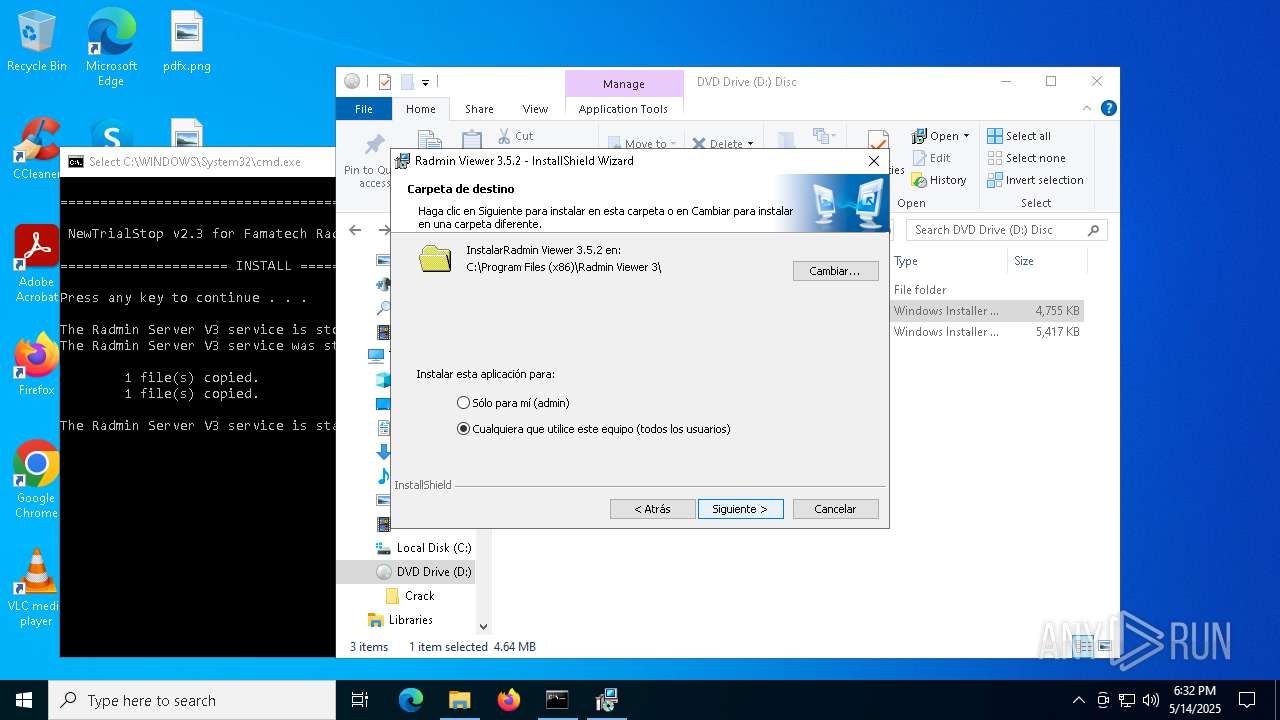
Manual execution by a user
- msiexec.exe (PID: 7904)
- cmd.exe (PID: 1188)
- cmd.exe (PID: 5360)
- msiexec.exe (PID: 840)
- Radmin.exe (PID: 3012)
Creates files or folders in the user directory
- msiexec.exe (PID: 7904)
Reads the software policy settings
- msiexec.exe (PID: 7904)
Checks proxy server information
- msiexec.exe (PID: 7904)
Checks supported languages
- msiexec.exe (PID: 8124)
- msiexec.exe (PID: 632)
Create files in a temporary directory
- msiexec.exe (PID: 7904)
- msiexec.exe (PID: 632)
Reads the computer name
- msiexec.exe (PID: 8124)
- msiexec.exe (PID: 632)
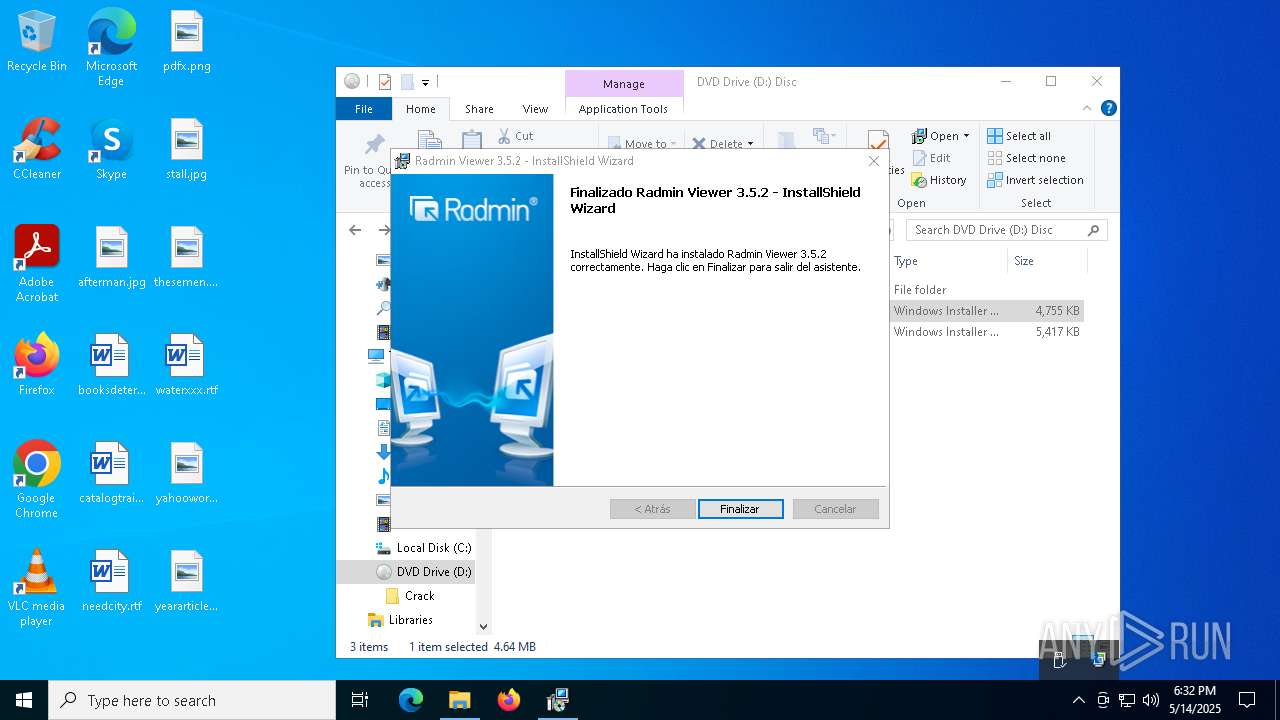
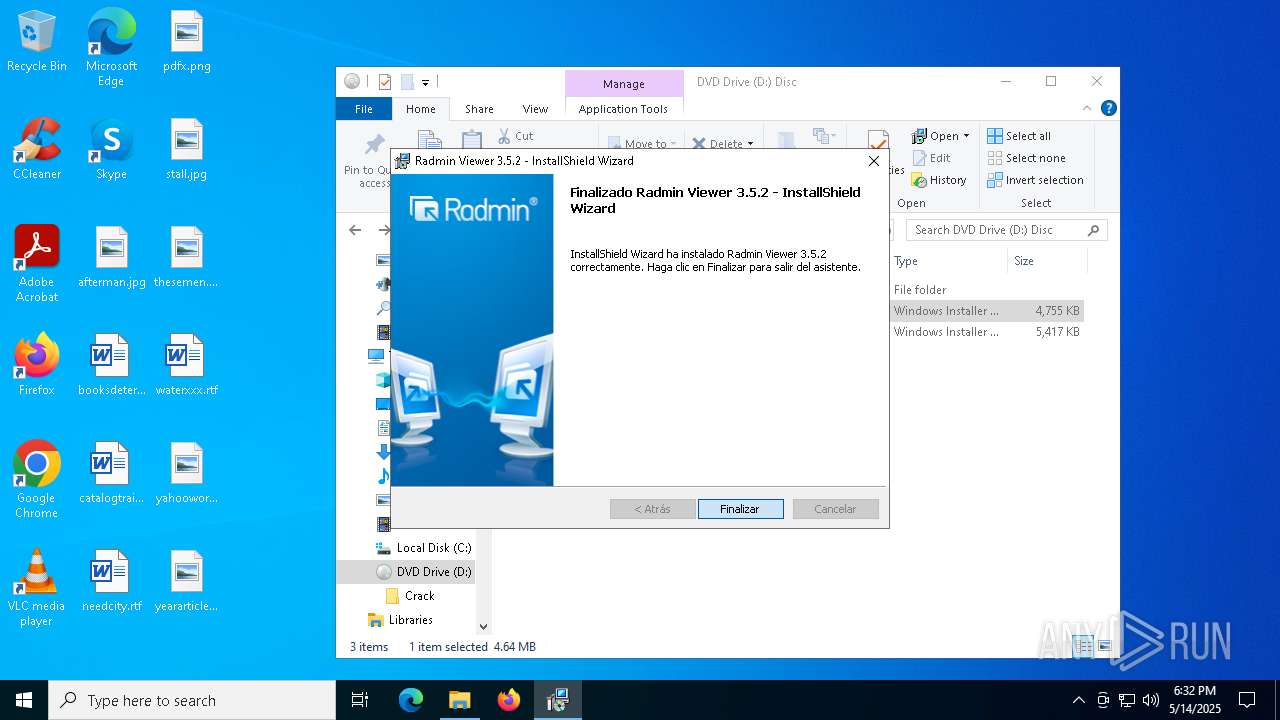
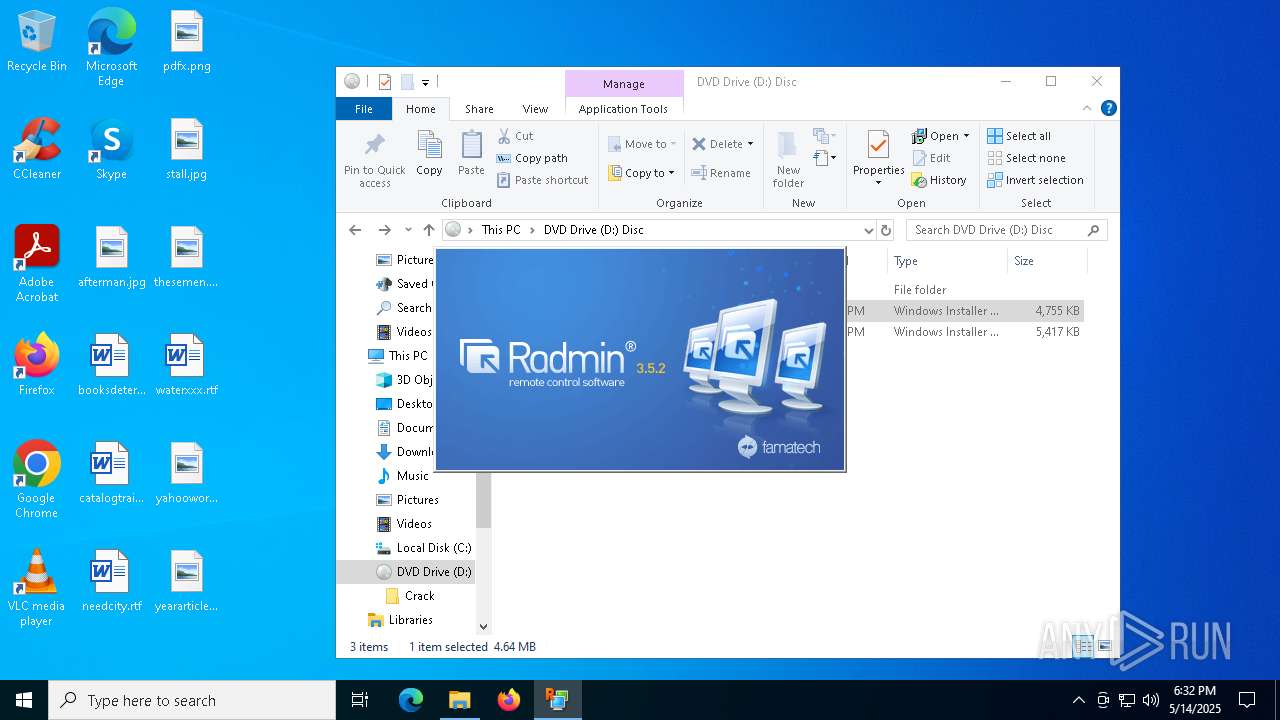
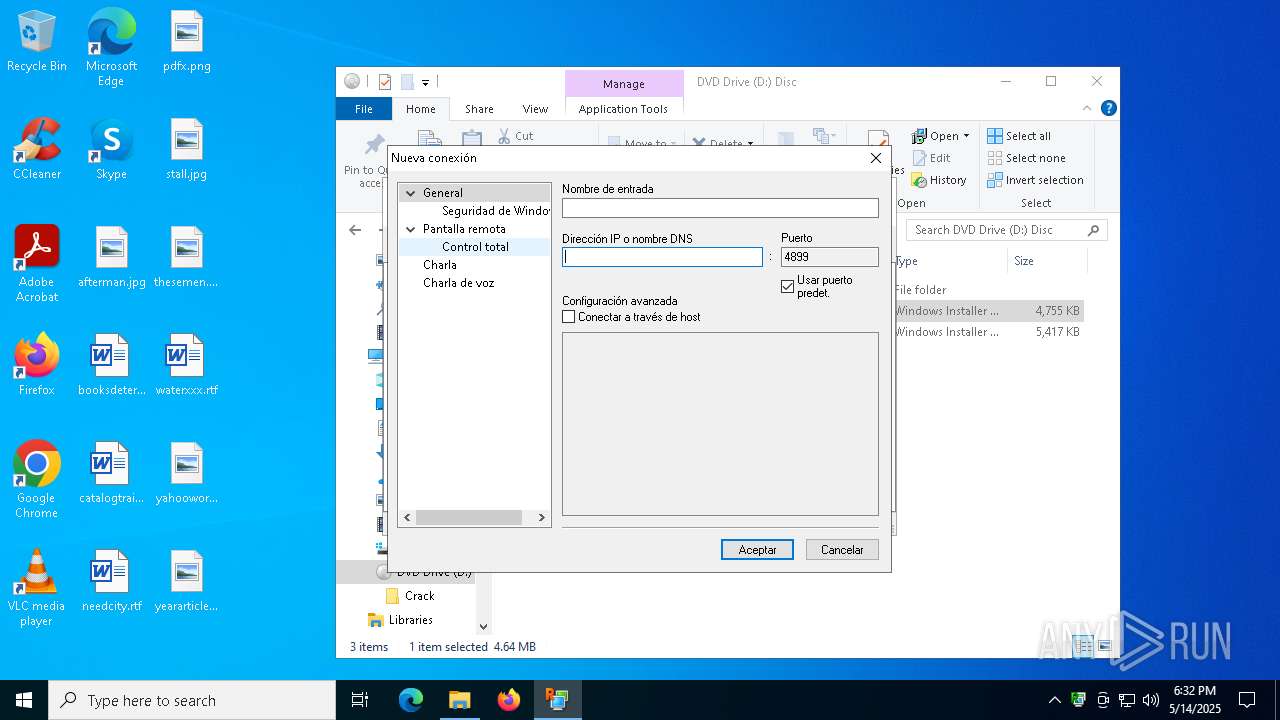
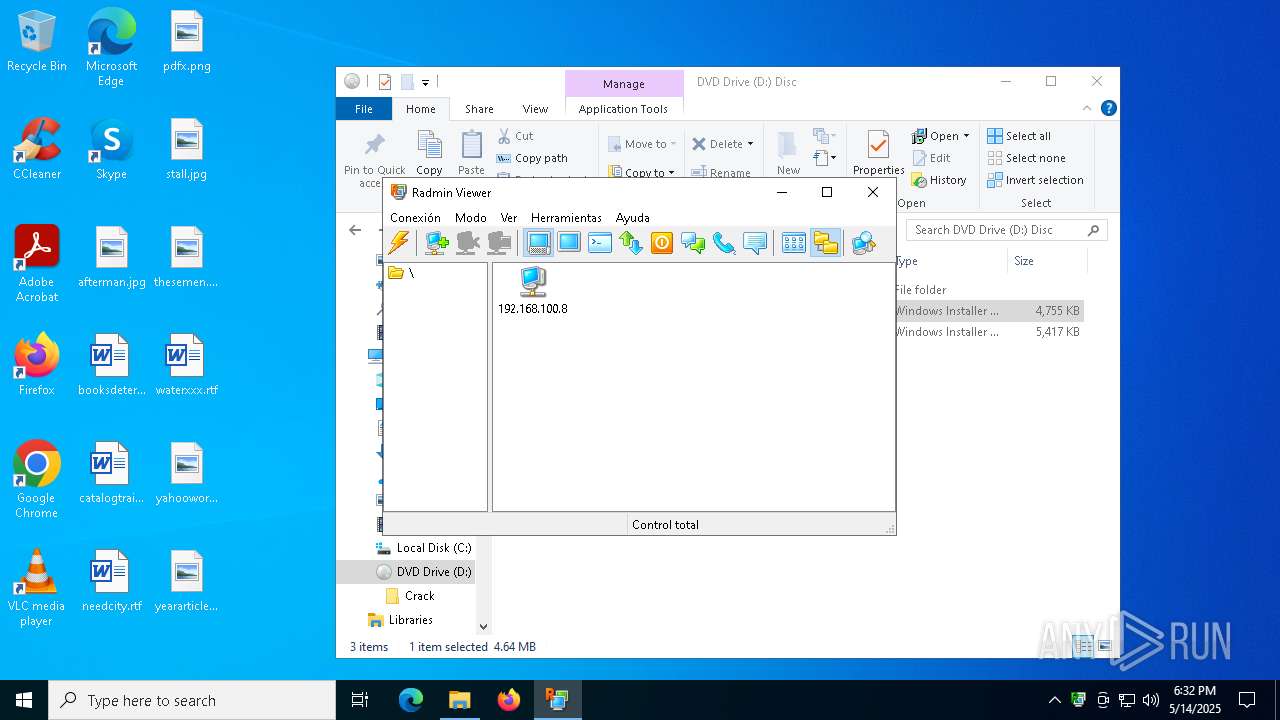
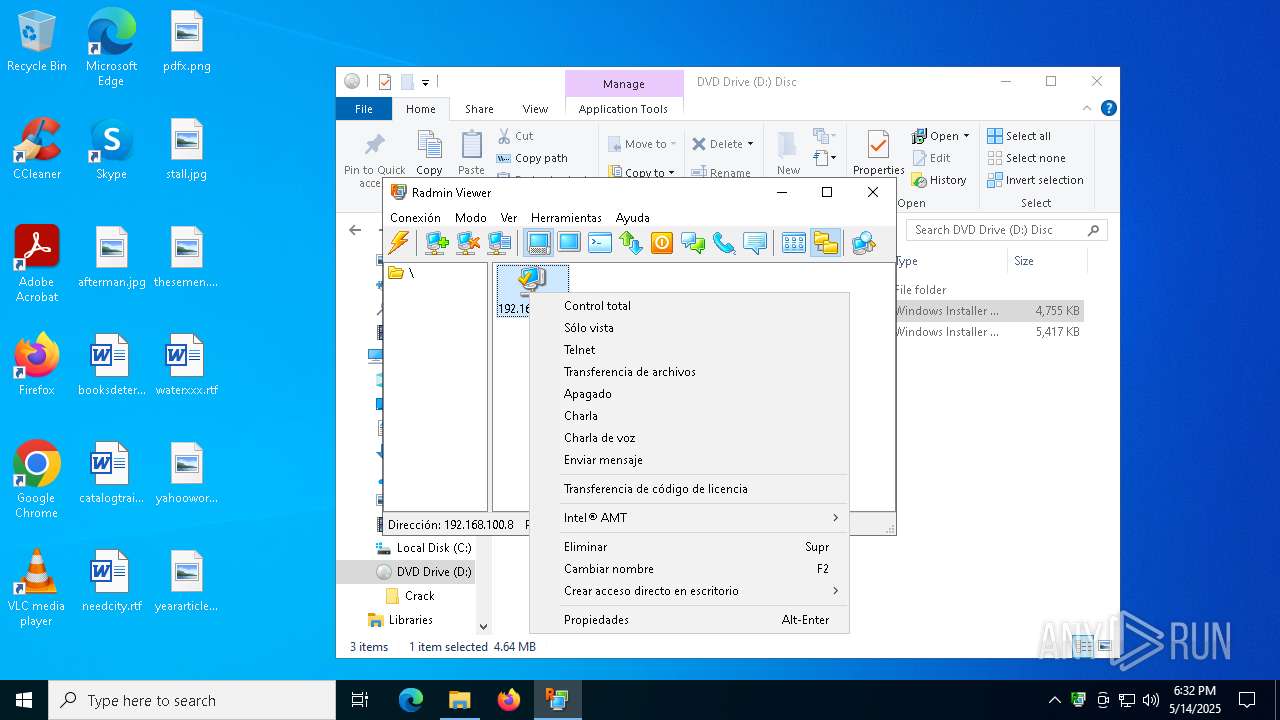
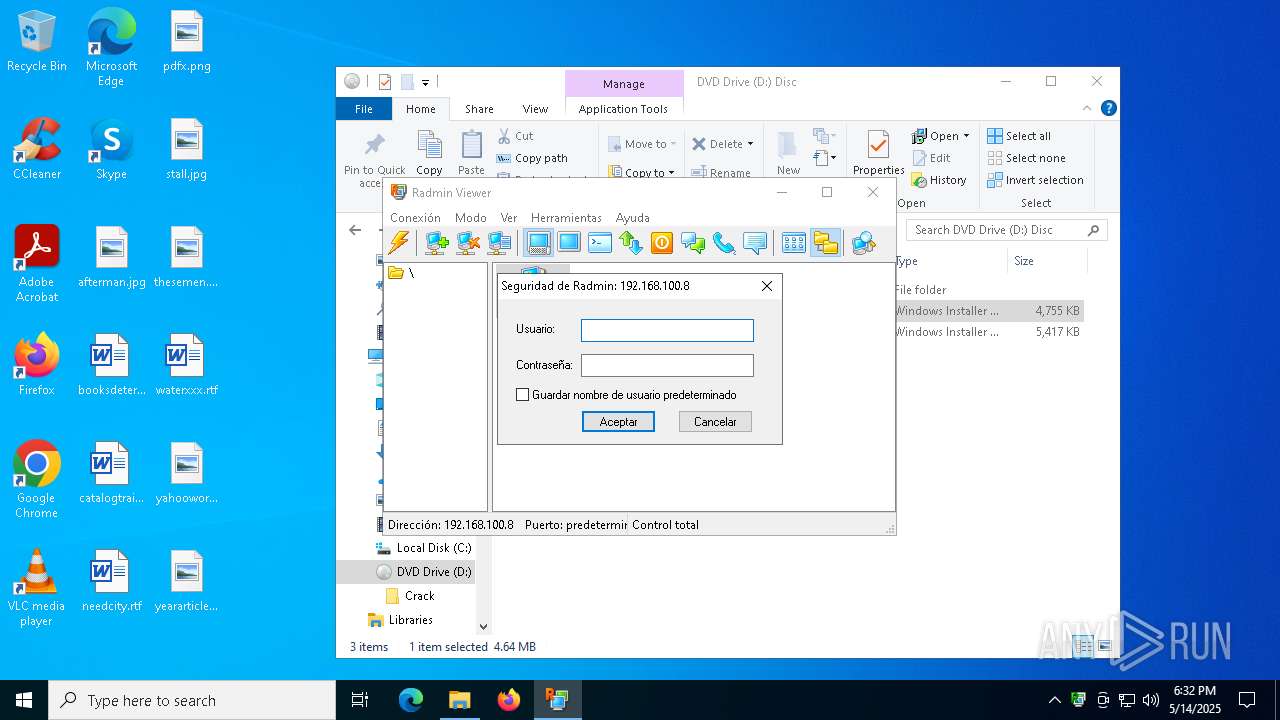
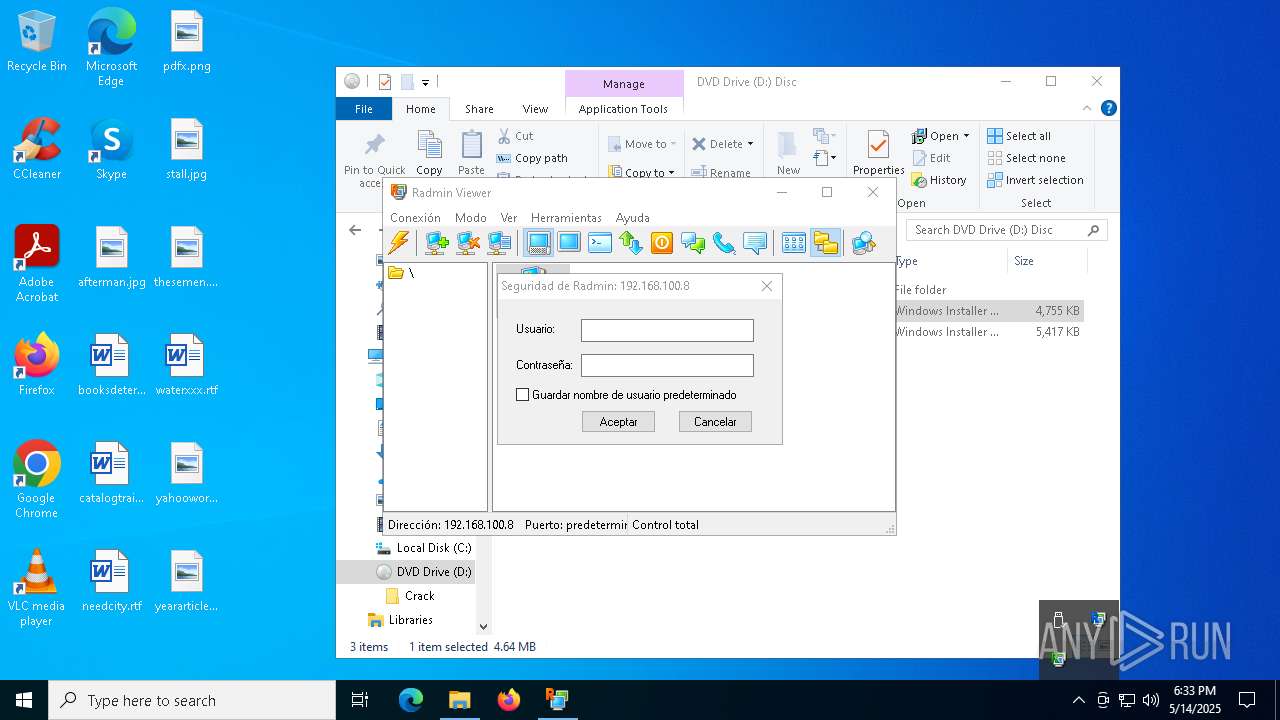
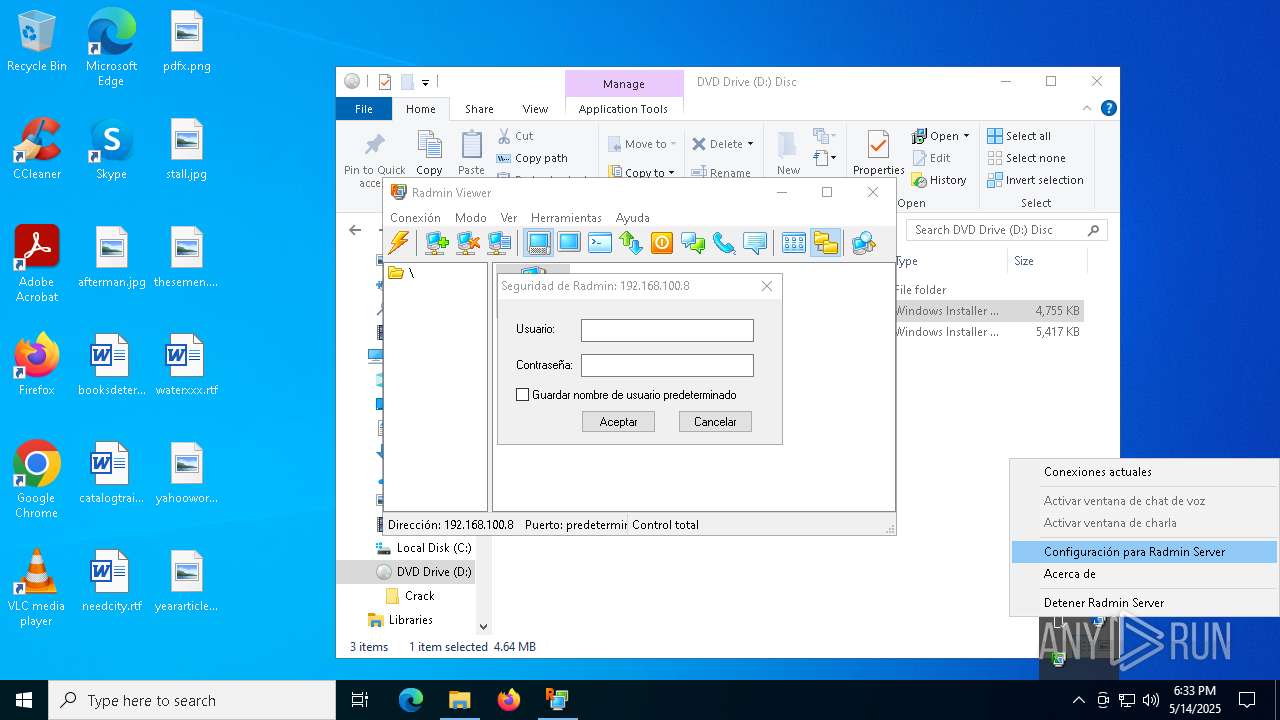
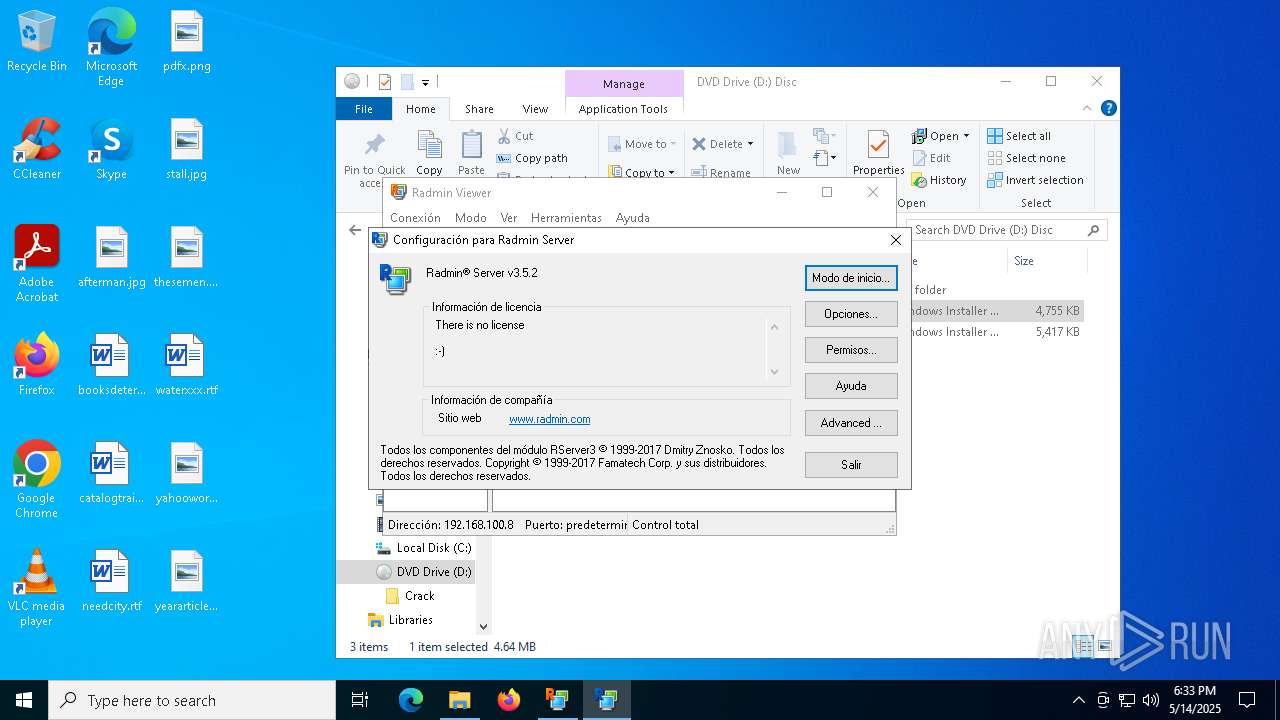
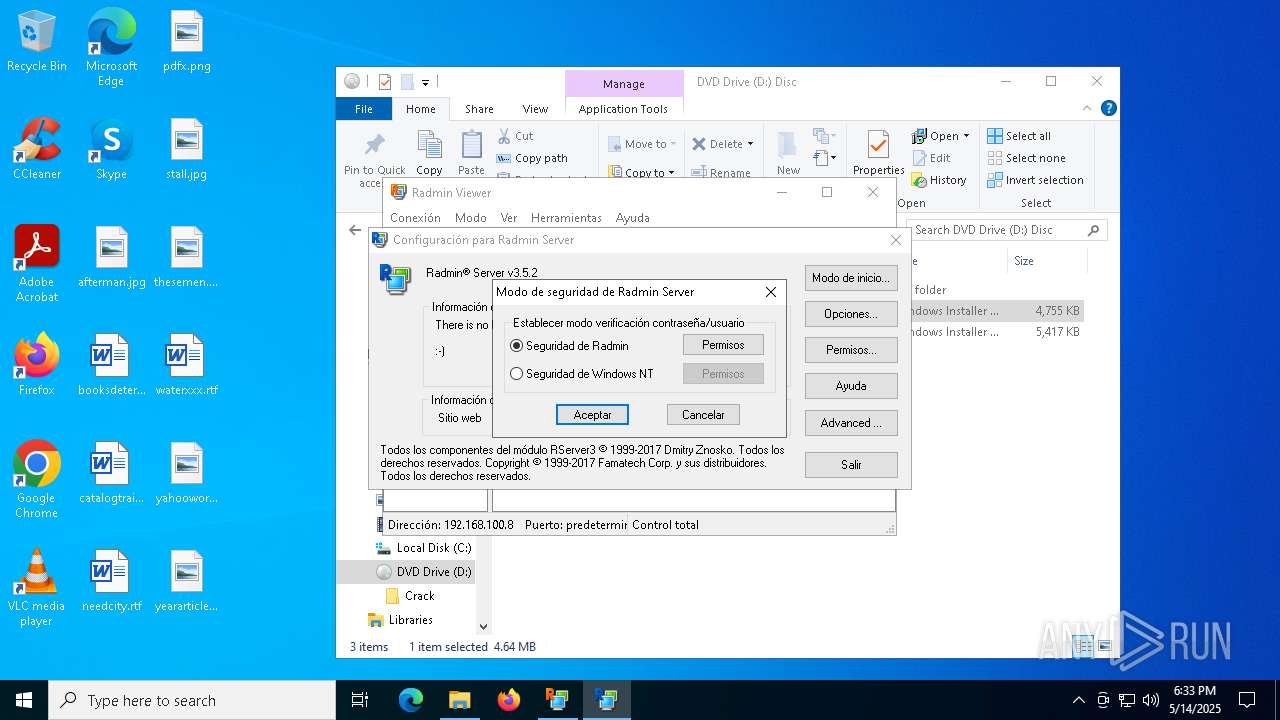
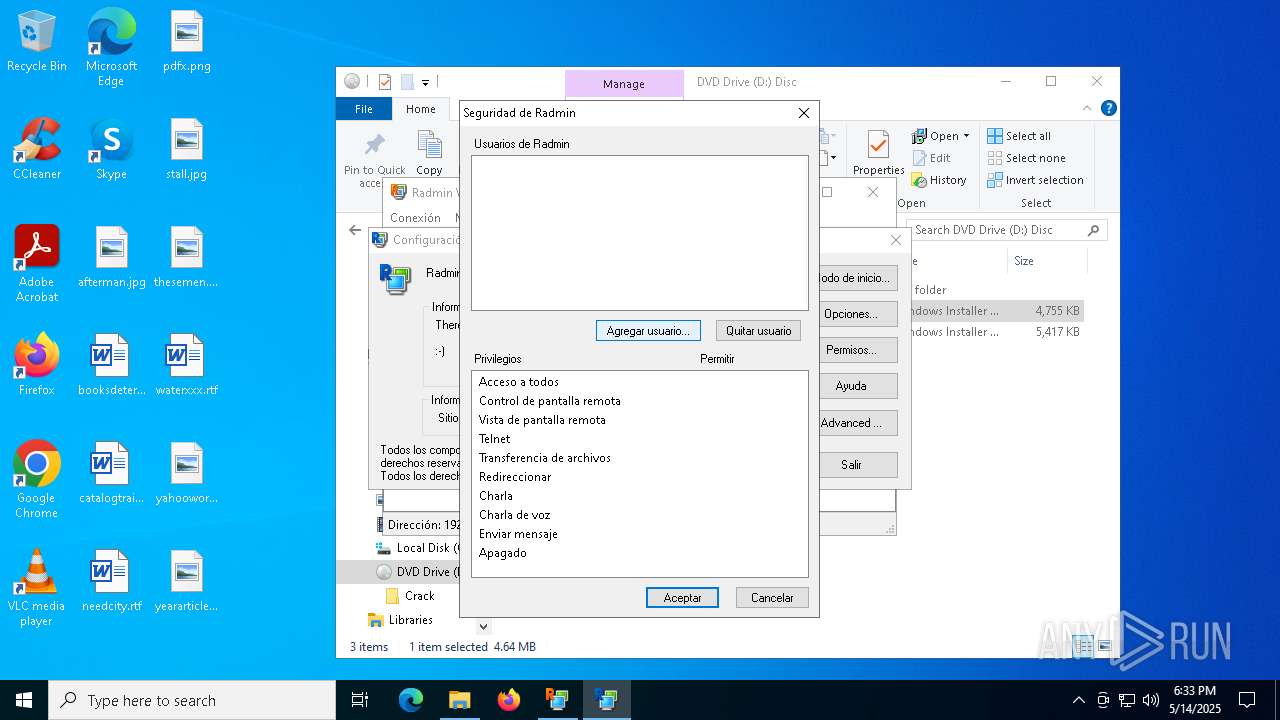
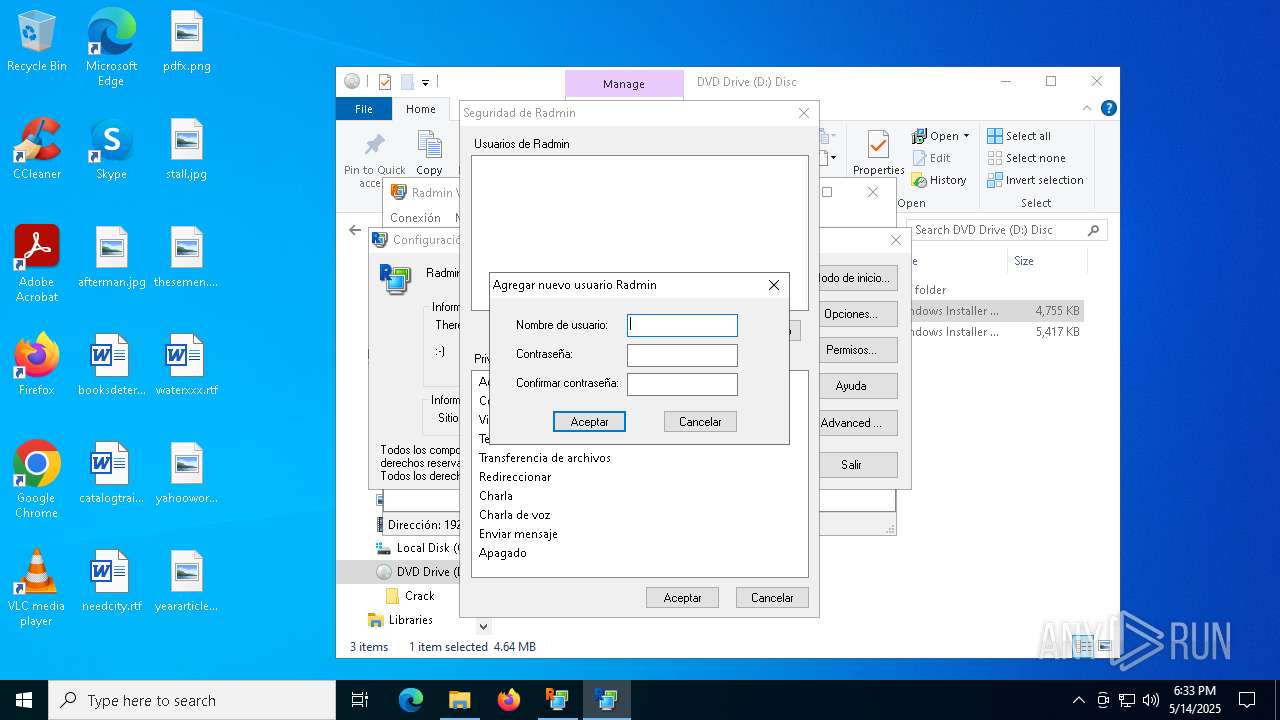
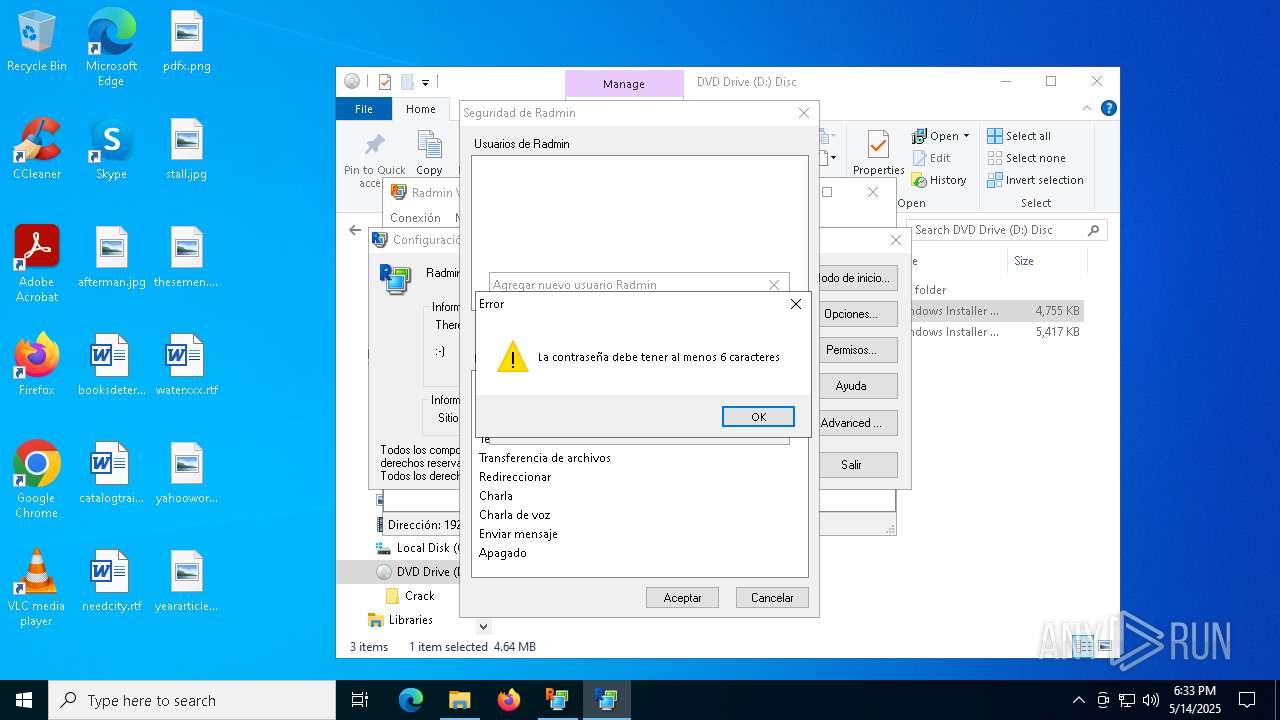
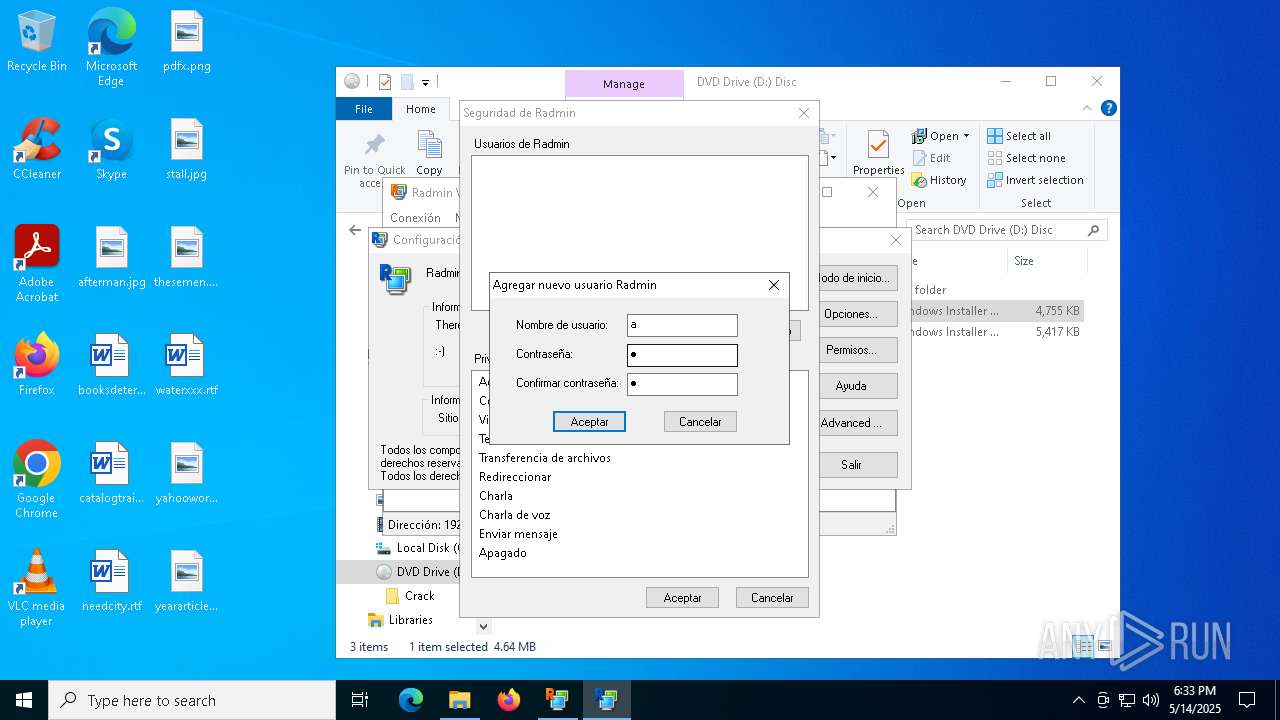
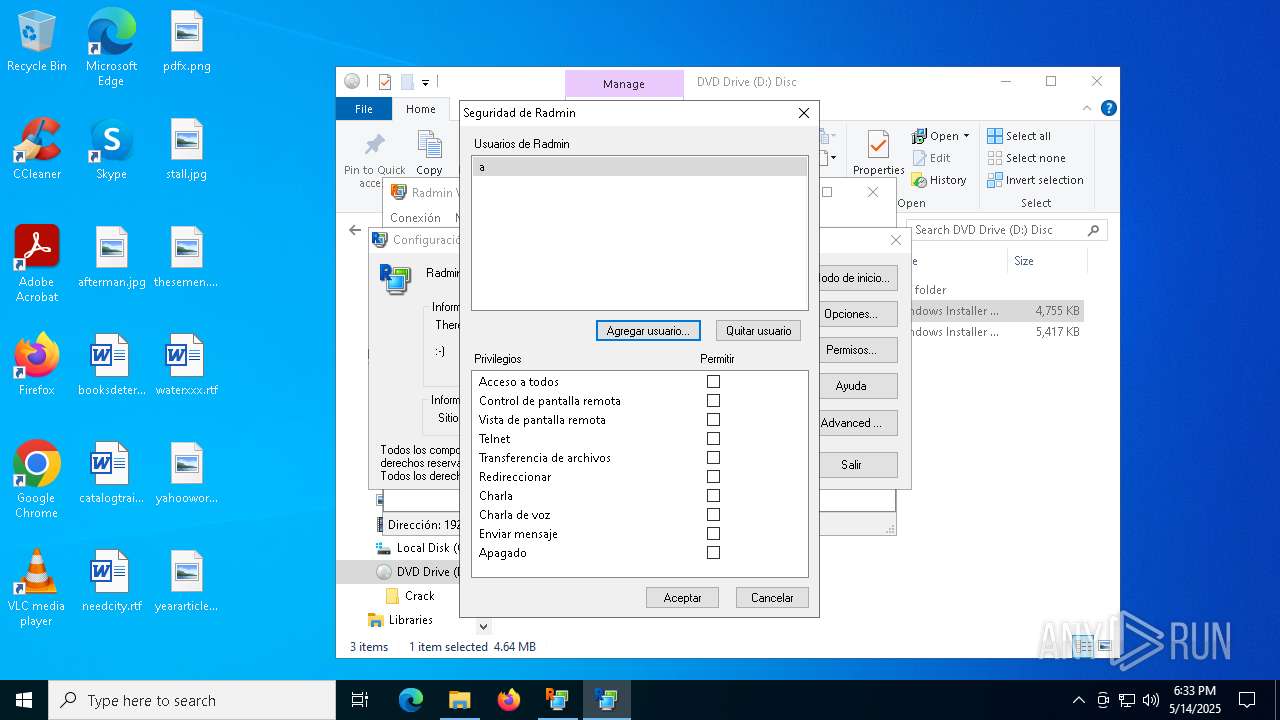
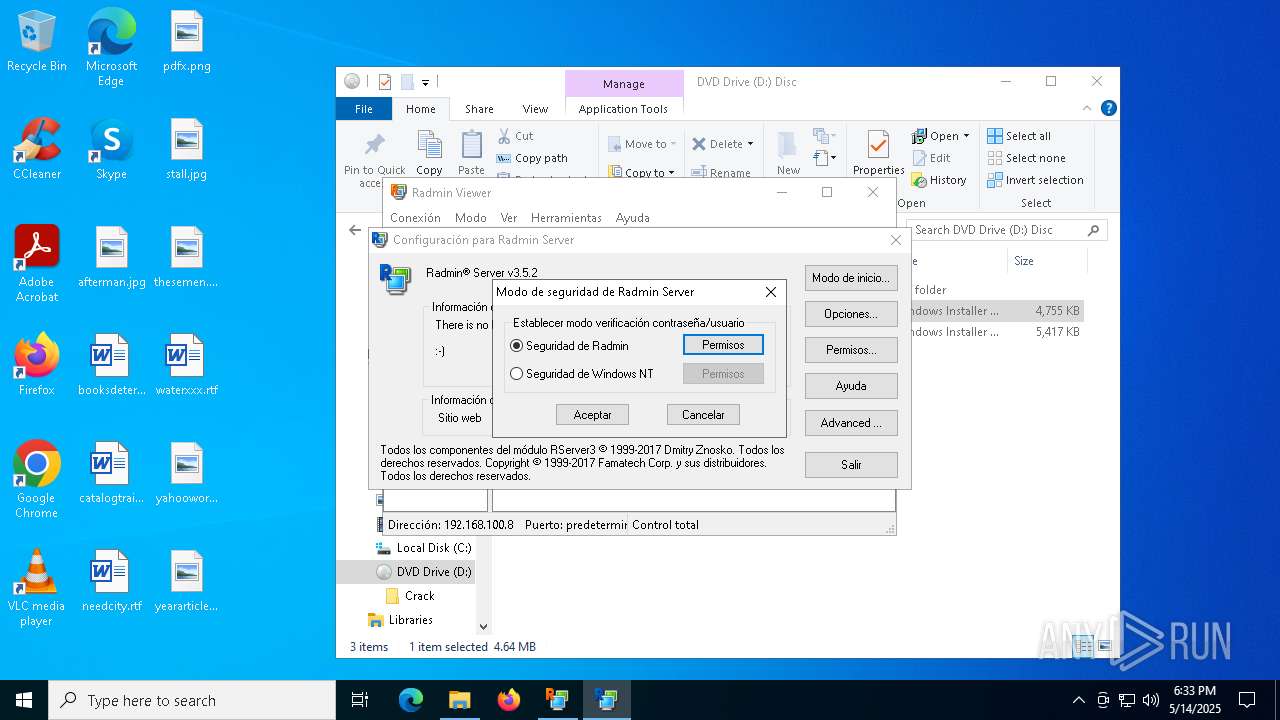
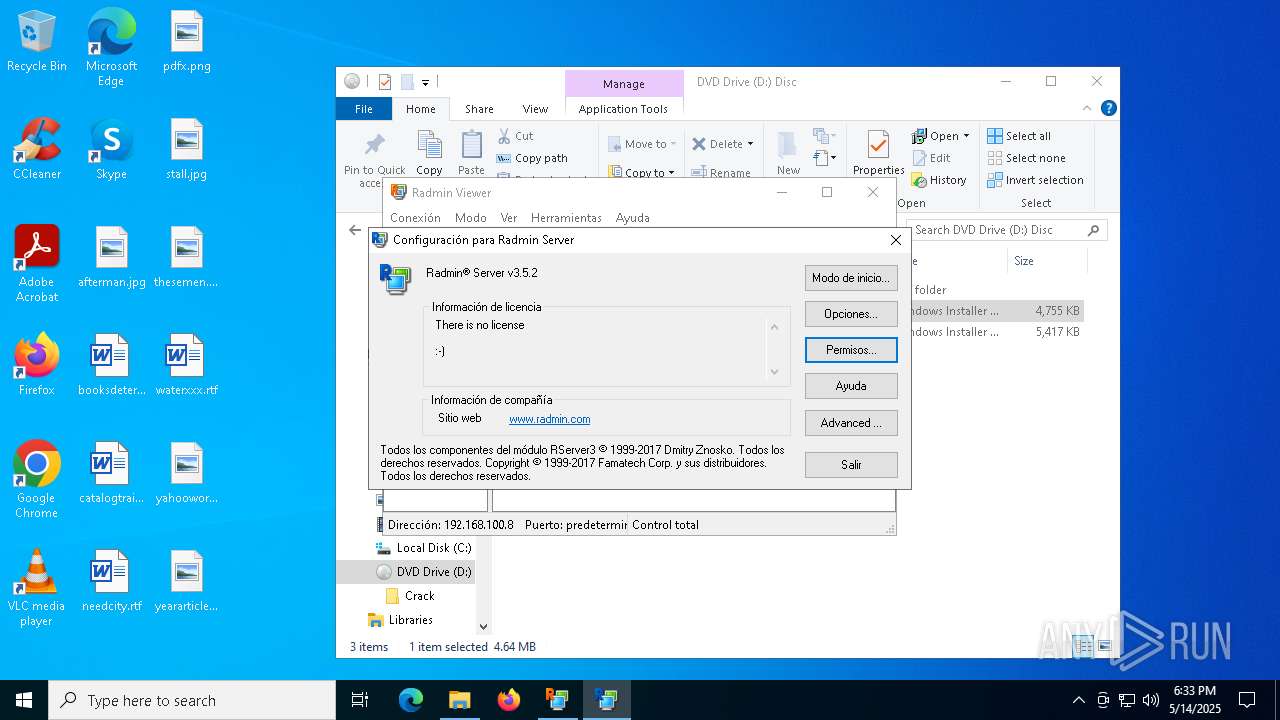
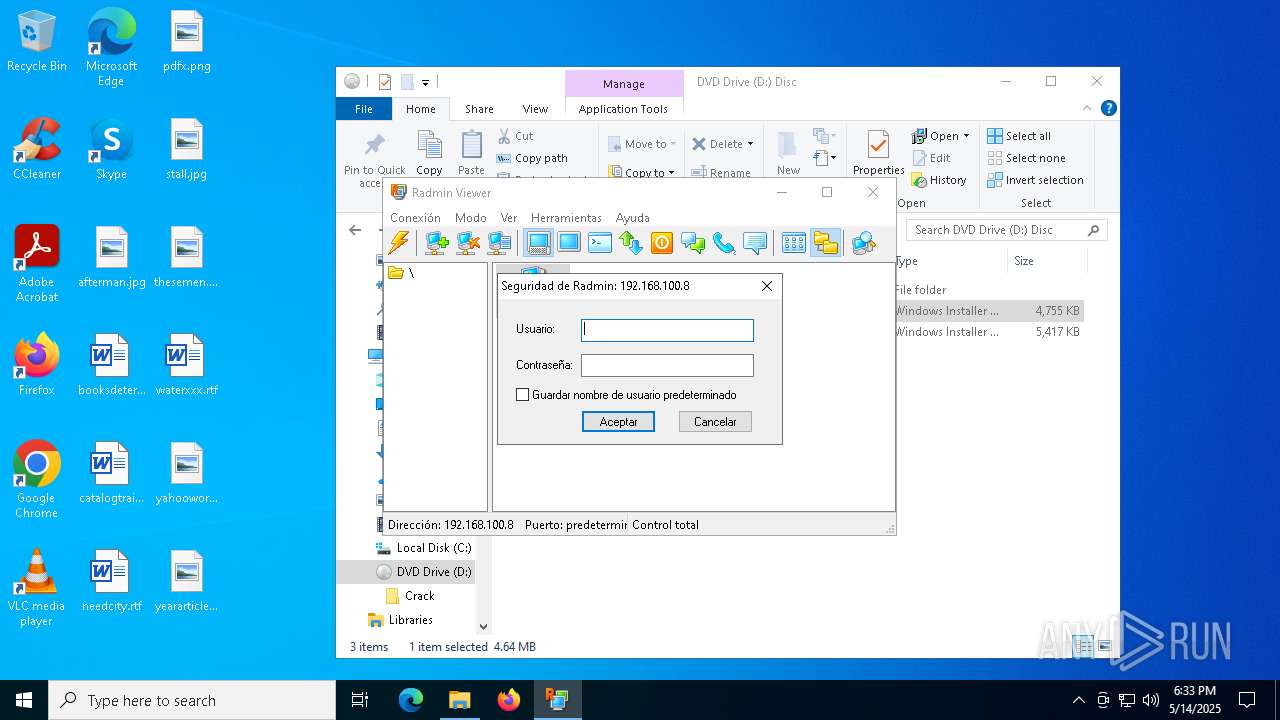
RADMIN has been detected
- msiexec.exe (PID: 7904)
Executable content was dropped or overwritten
- msiexec.exe (PID: 8124)
- msiexec.exe (PID: 632)
- msiexec.exe (PID: 7904)
- msiexec.exe (PID: 840)
Manages system restore points
- SrTasks.exe (PID: 6032)
- SrTasks.exe (PID: 6760)
The sample compiled with english language support
- msiexec.exe (PID: 632)
- msiexec.exe (PID: 7904)
- msiexec.exe (PID: 8124)
- msiexec.exe (PID: 840)
- cmd.exe (PID: 5360)
The sample compiled with russian language support
- msiexec.exe (PID: 8124)
Find more information about signature artifacts and mapping to MITRE ATT&CK™ MATRIX at the full report
TRiD
| .iso | | | ISO 9660 CD image (27.6) |
|---|---|---|
| .atn | | | Photoshop Action (27.1) |
| .gmc | | | Game Music Creator Music (6.1) |
EXIF
ISO
| VolumeName: | DISC |
|---|---|
| VolumeBlockCount: | 5424 |
| VolumeBlockSize: | 2048 |
| RootDirectoryCreateDate: | 1900:00:00 00:00:00+00:00 |
Composite
| VolumeSize: | 11 MB |
|---|
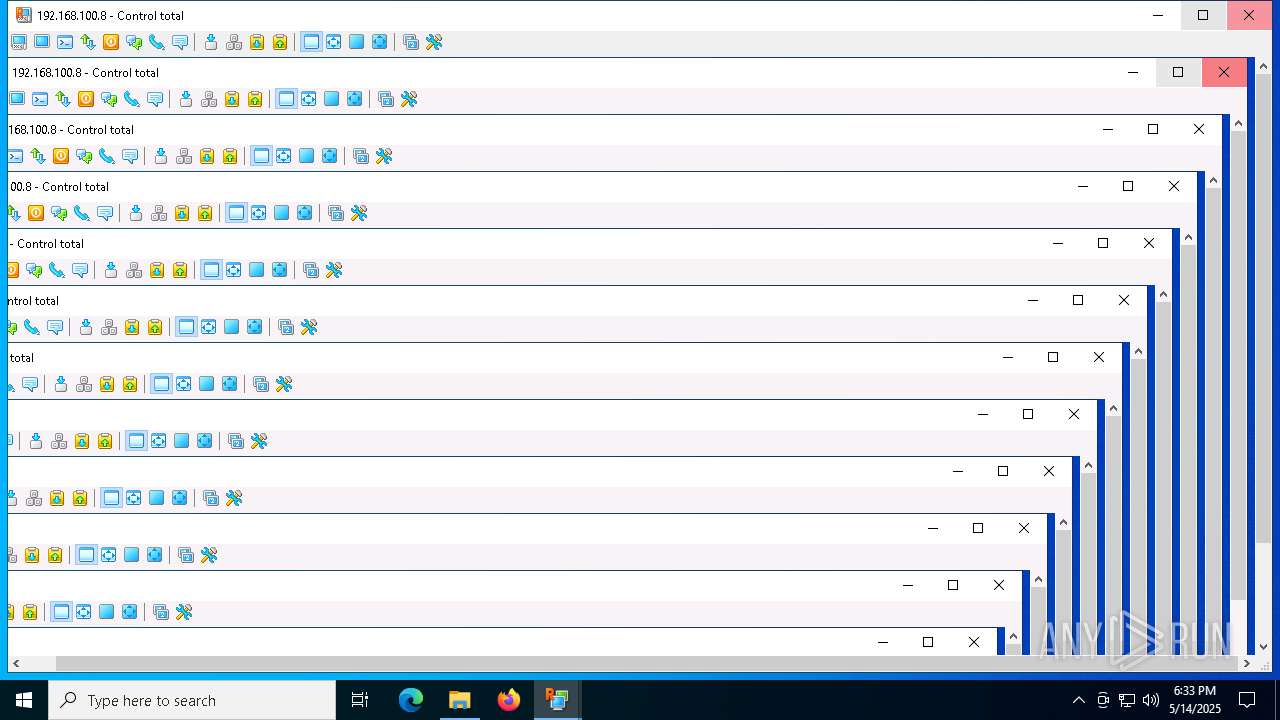
Total processes
189
Monitored processes
48
Malicious processes
10
Suspicious processes
8
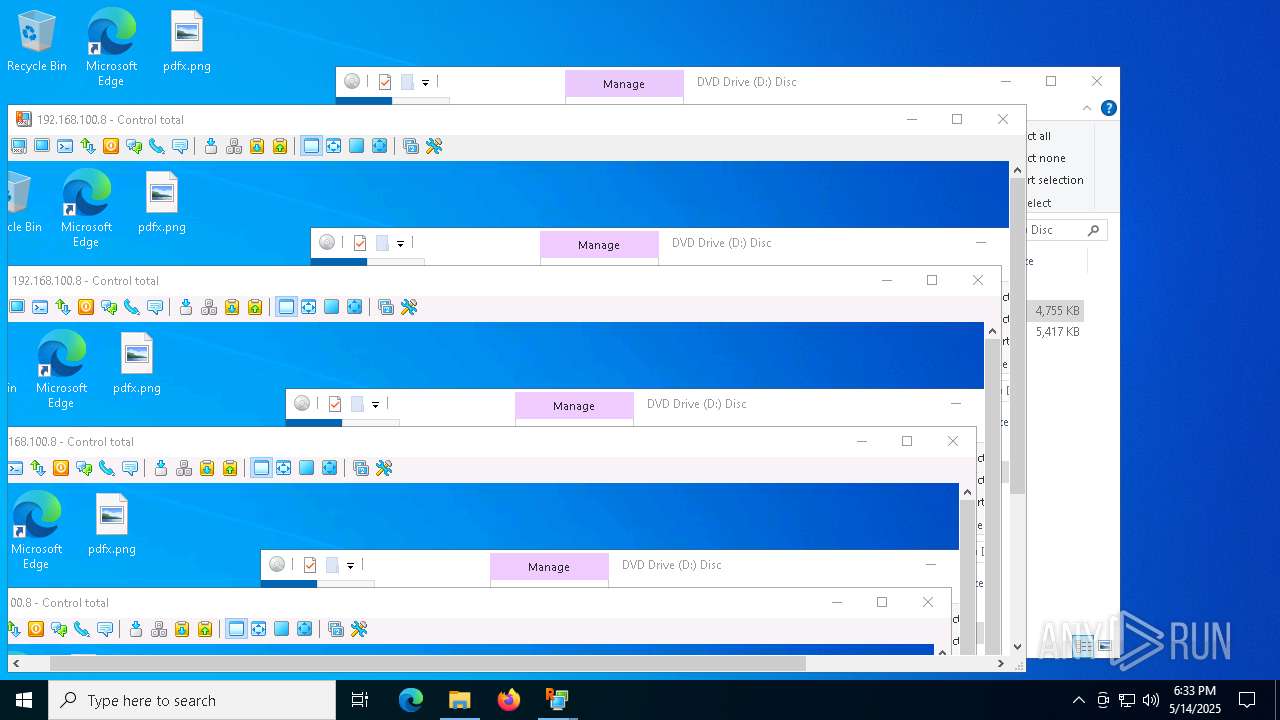
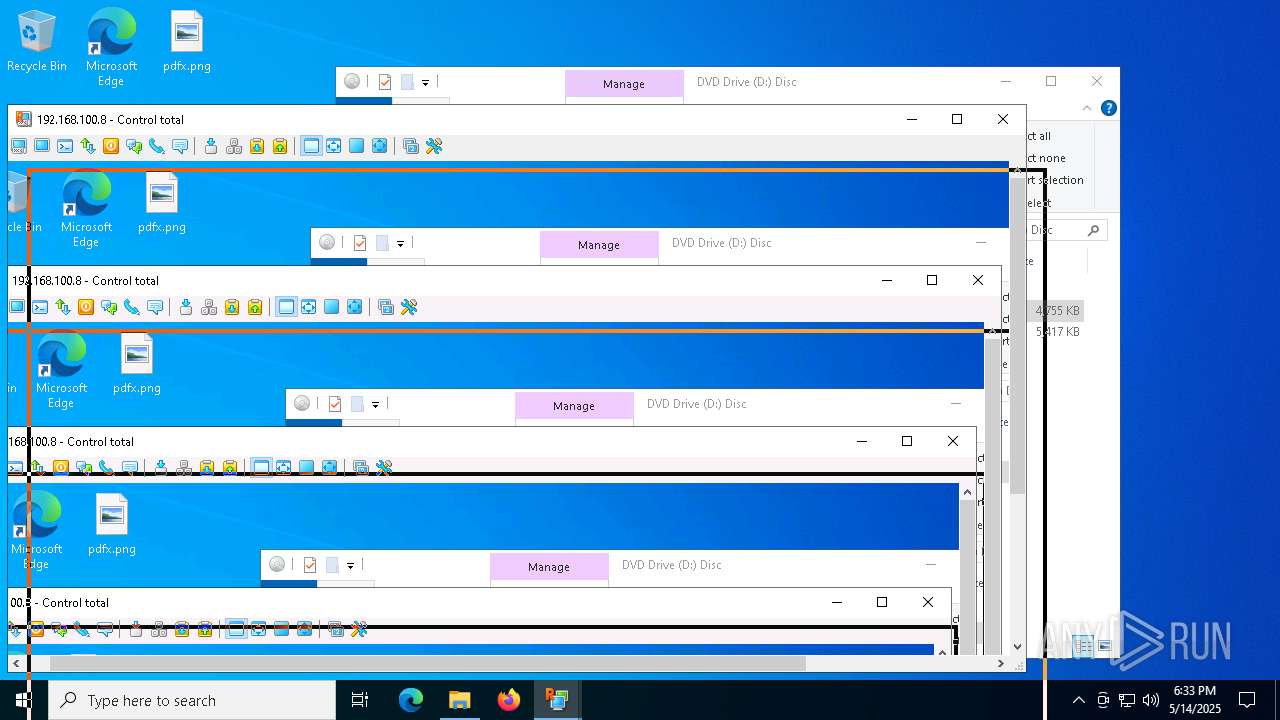
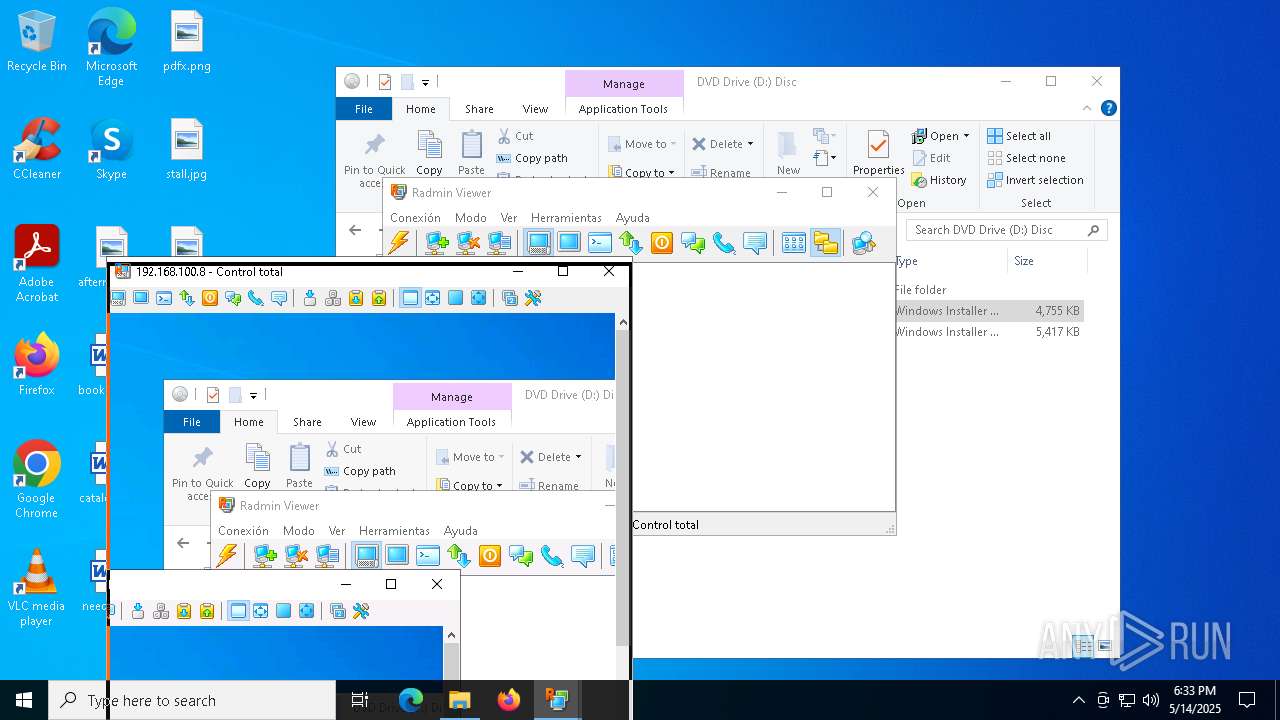
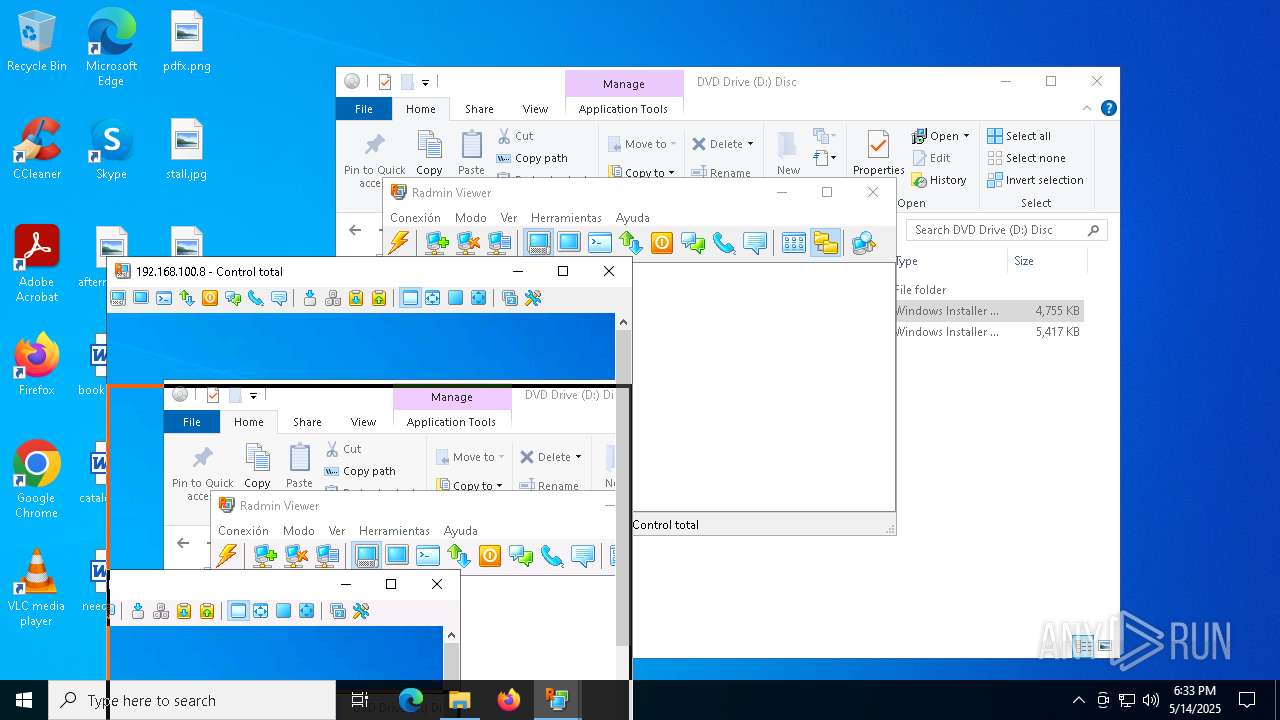
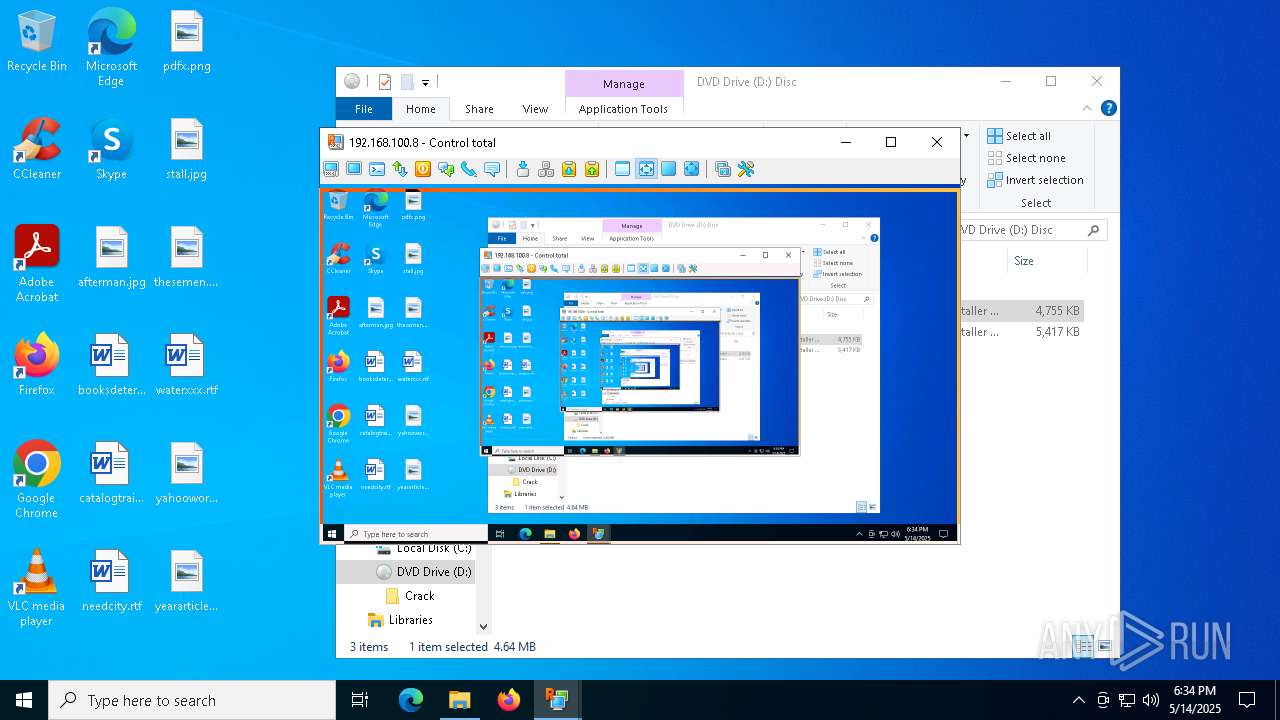
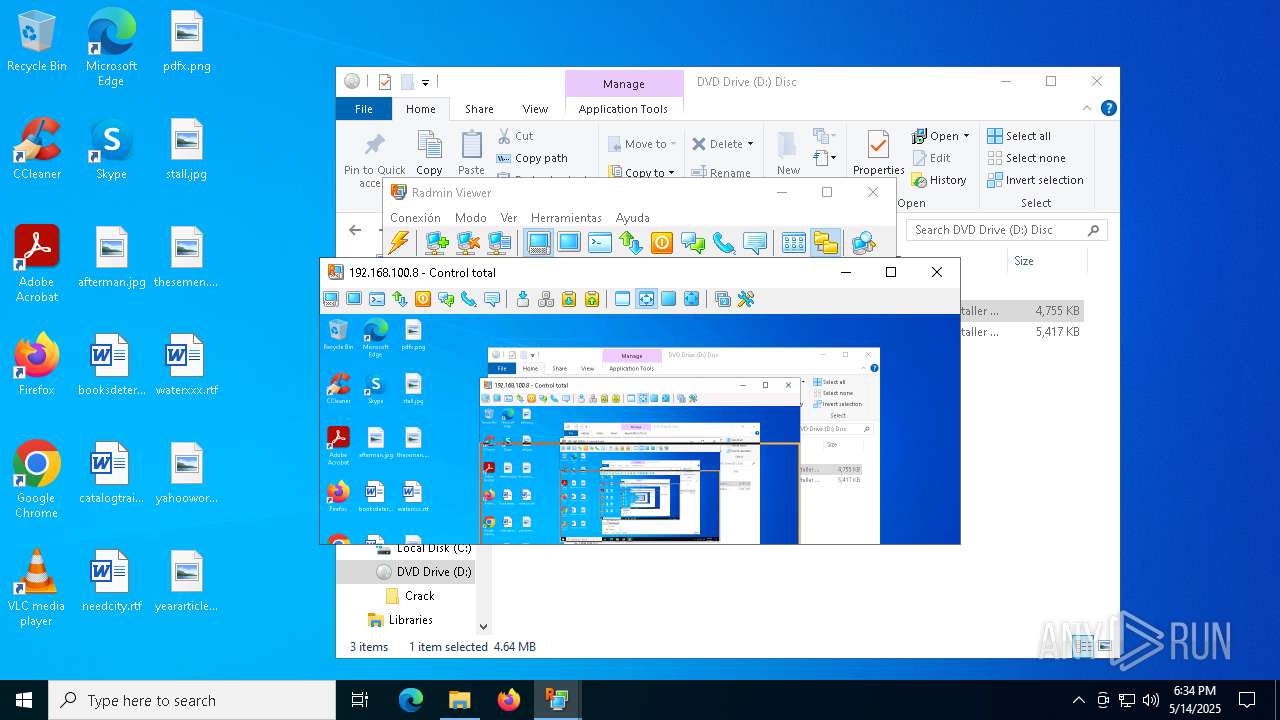
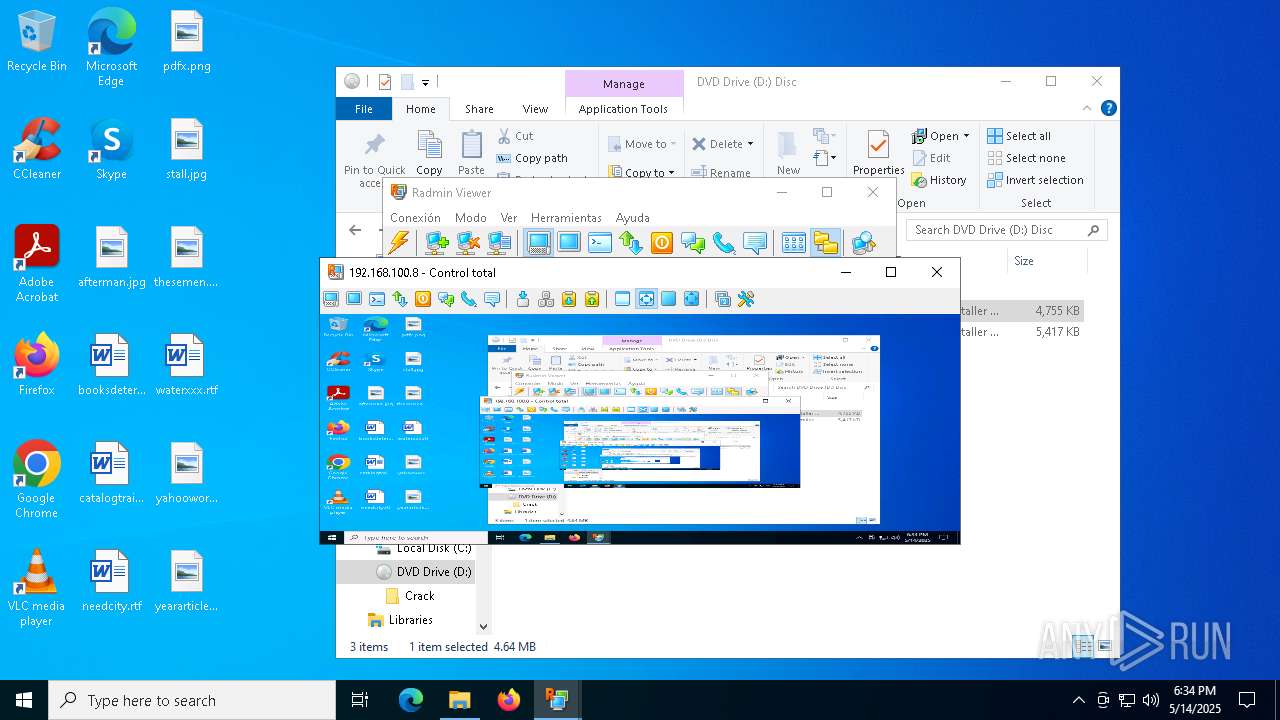
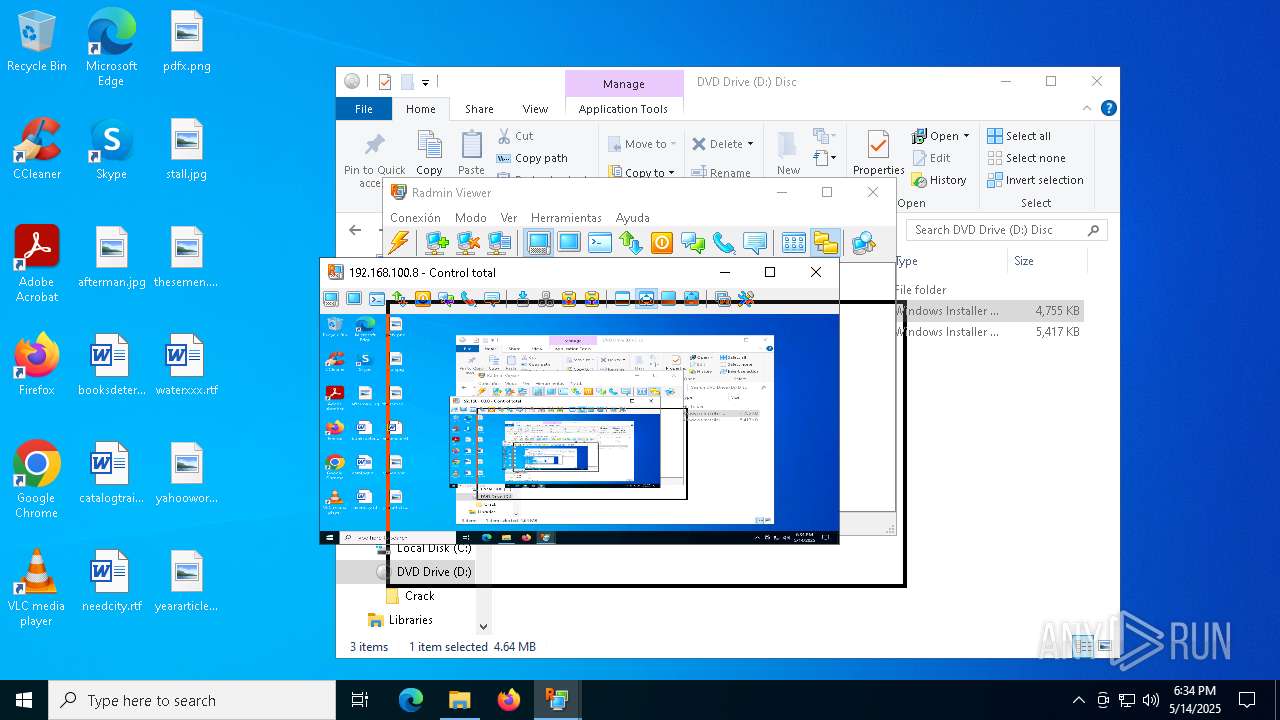
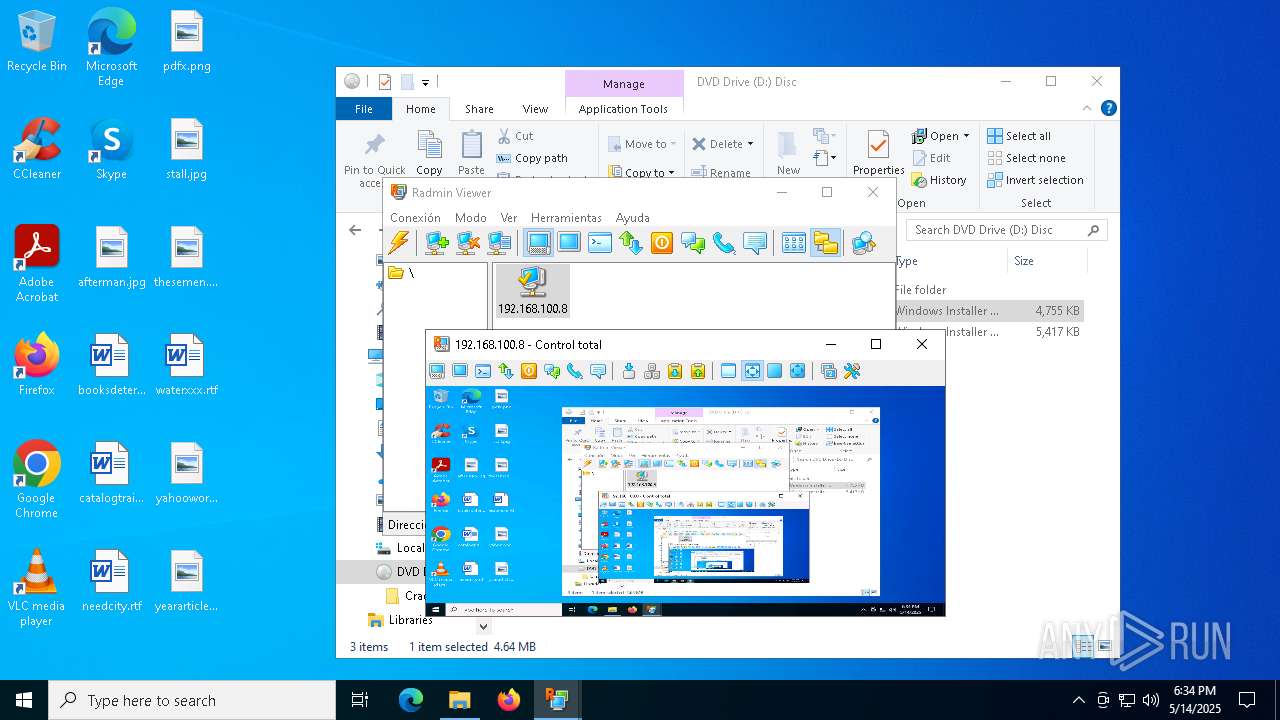
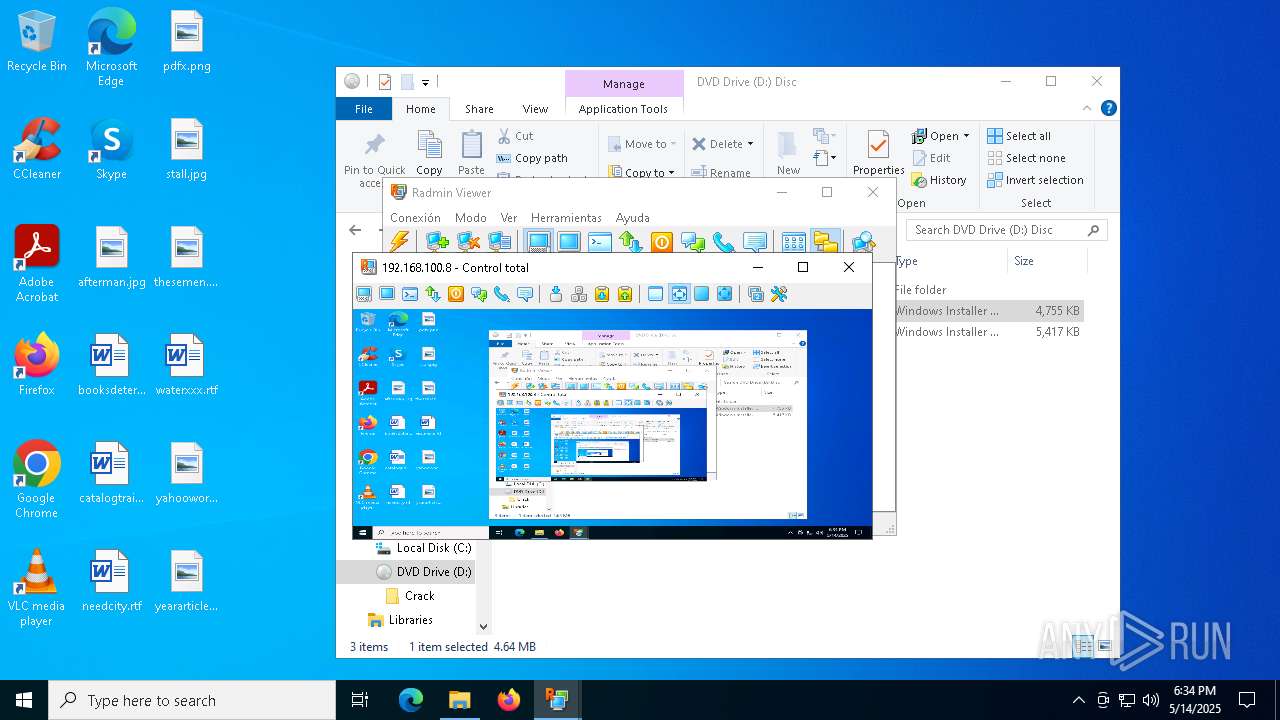
Behavior graph
Click at the process to see the details
Process information
PID | CMD | Path | Indicators | Parent process | |||||||||||
|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|---|
| 208 | net start rserver3 | C:\Windows\System32\net.exe | — | cmd.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Net Command Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 632 | C:\Windows\syswow64\MsiExec.exe -Embedding F51DDDA153E5CB95AC8123C964DED8CE C | C:\Windows\SysWOW64\msiexec.exe | msiexec.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows® installer Exit code: 0 Version: 5.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 644 | "C:\WINDOWS\SysWOW64\rserver30\RServer3.exe" /service | C:\Windows\SysWOW64\rserver30\rserver3.exe | services.exe | ||||||||||||
User: SYSTEM Company: Famatech Corp. Integrity Level: SYSTEM Description: Radmin Server Version: 3, 5, 2, 0 Modules
| |||||||||||||||
| 736 | C:\WINDOWS\system32\vssvc.exe | C:\Windows\System32\VSSVC.exe | — | services.exe | |||||||||||
User: SYSTEM Company: Microsoft Corporation Integrity Level: SYSTEM Description: Microsoft® Volume Shadow Copy Service Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 840 | "C:\WINDOWS\System32\msiexec.exe" /i "D:\Radmin Viewer 3.5.2.1.msi" | C:\Windows\System32\msiexec.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows® installer Exit code: 0 Version: 5.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1020 | "C:\WINDOWS\SysWOW64\rserver30\FamItrf2.Exe" | C:\Windows\SysWOW64\rserver30\FamItrf2.Exe | — | rserver3.exe | |||||||||||
User: SYSTEM Company: Famatech Corp. Integrity Level: SYSTEM Description: Radmin component Version: 3,5,2,1205 Modules
| |||||||||||||||
| 1132 | C:\WINDOWS\System32\slui.exe -Embedding | C:\Windows\System32\slui.exe | svchost.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: MEDIUM Description: Windows Activation Client Exit code: 0 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1188 | "C:\WINDOWS\System32\cmd.exe" /C "D:\Crack\install.bat" | C:\Windows\System32\cmd.exe | explorer.exe | ||||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Windows Command Processor Exit code: 3221225786 Version: 10.0.19041.1 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 1748 | C:\WINDOWS\system32\net1 stop rserver3 | C:\Windows\System32\net1.exe | — | net.exe | |||||||||||
User: admin Company: Microsoft Corporation Integrity Level: HIGH Description: Net Command Exit code: 0 Version: 10.0.19041.3636 (WinBuild.160101.0800) Modules
| |||||||||||||||
| 2644 | "C:\WINDOWS\SysWOW64\rserver30\rsetup64.exe" /intsetup | C:\Windows\SysWOW64\rserver30\rsetup64.exe | — | msiexec.exe | |||||||||||
User: SYSTEM Company: Famatech Corp. Integrity Level: SYSTEM Description: Radmin Setup Helper Exit code: 1 Version: 3, 5, 2, 0 Modules
| |||||||||||||||
Total events
72 052
Read events
70 997
Write events
987
Delete events
68
Modification events
| (PID) Process: | (5492) explorer.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\BagMRU |
| Operation: | write | Name: | NodeSlots |
Value: 02020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202020202 | |||
| (PID) Process: | (5492) explorer.exe | Key: | HKEY_CLASSES_ROOT\Local Settings\Software\Microsoft\Windows\Shell\BagMRU |
| Operation: | write | Name: | MRUListEx |
Value: 03000000040000000E00000000000000100000000F0000000C0000000D0000000B000000050000000A000000090000000800000001000000070000000600000002000000FFFFFFFF | |||
| (PID) Process: | (5492) explorer.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Internet Explorer\Toolbar |
| Operation: | write | Name: | Locked |
Value: 1 | |||
| (PID) Process: | (5492) explorer.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Explorer\FeatureUsage\AppLaunch |
| Operation: | write | Name: | Microsoft.Windows.Explorer |
Value: 52 | |||
| (PID) Process: | (5492) explorer.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\OneDrive\Accounts |
| Operation: | write | Name: | LastUpdate |
Value: 49E1246800000000 | |||
| (PID) Process: | (6036) explorer.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Explorer |
| Operation: | write | Name: | SlowContextMenuEntries |
Value: 6024B221EA3A6910A2DC08002B30309D0A010000BD0E0C47735D584D9CEDE91E22E23282770100000114020000000000C0000000000000468D0000006078A409B011A54DAFA526D86198A780390100009AD298B2EDA6DE11BA8CA68E55D895936E000000 | |||
| (PID) Process: | (5492) explorer.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Explorer\FeatureUsage\AppLaunch |
| Operation: | write | Name: | Microsoft.Windows.Explorer |
Value: 53 | |||
| (PID) Process: | (5492) explorer.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Explorer\Ribbon |
| Operation: | write | Name: | MinimizedStateTabletModeOff |
Value: 0 | |||
| (PID) Process: | (5492) explorer.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Windows\CurrentVersion\Explorer\Ribbon |
| Operation: | write | Name: | QatItems |
Value: 3C7369713A637573746F6D554920786D6C6E733A7369713D22687474703A2F2F736368656D61732E6D6963726F736F66742E636F6D2F77696E646F77732F323030392F726962626F6E2F716174223E3C7369713A726962626F6E206D696E696D697A65643D2266616C7365223E3C7369713A71617420706F736974696F6E3D2230223E3C7369713A736861726564436F6E74726F6C733E3C7369713A636F6E74726F6C206964513D227369713A3136313238222076697369626C653D2266616C73652220617267756D656E743D223022202F3E3C7369713A636F6E74726F6C206964513D227369713A3136313239222076697369626C653D2266616C73652220617267756D656E743D223022202F3E3C7369713A636F6E74726F6C206964513D227369713A3132333532222076697369626C653D2266616C73652220617267756D656E743D223022202F3E3C7369713A636F6E74726F6C206964513D227369713A3132333834222076697369626C653D22747275652220617267756D656E743D223022202F3E3C7369713A636F6E74726F6C206964513D227369713A3132333336222076697369626C653D22747275652220617267756D656E743D223022202F3E3C7369713A636F6E74726F6C206964513D227369713A3132333537222076697369626C653D2266616C73652220617267756D656E743D223022202F3E3C2F7369713A736861726564436F6E74726F6C733E3C2F7369713A7161743E3C2F7369713A726962626F6E3E3C2F7369713A637573746F6D55493E | |||
| (PID) Process: | (5492) explorer.exe | Key: | HKEY_CURRENT_USER\SOFTWARE\Microsoft\Internet Explorer\Toolbar\ShellBrowser |
| Operation: | write | Name: | ITBar7Layout |
Value: 13000000000000000000000020000000100000000000000001000000010700005E01000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000000 | |||
Executable files
69
Suspicious files
60
Text files
9
Unknown types
0
Dropped files
PID | Process | Filename | Type | |
|---|---|---|---|---|
| 7904 | msiexec.exe | C:\Users\admin\AppData\Local\Temp\112ecd.msi | — | |
MD5:— | SHA256:— | |||
| 8124 | msiexec.exe | C:\System Volume Information\SPP\metadata-2 | — | |
MD5:— | SHA256:— | |||
| 8124 | msiexec.exe | C:\Windows\Installer\119edd.msi | — | |
MD5:— | SHA256:— | |||
| 7904 | msiexec.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\C46E7B0F942663A1EDC8D9D6D7869173_6043FC604A395E1485AF7AC16D16B7CE | binary | |
MD5:54A18D6BB01BAA8EFE49AD72359265A4 | SHA256:8C070771C463E1D94F2F44BC6643FD89FEA507B5C9490F841150B9C544A126C8 | |||
| 8124 | msiexec.exe | C:\Windows\Installer\MSIA16D.tmp | executable | |
MD5:30CD07918815CF3E6CFF4FE8BB17CE24 | SHA256:A6E414108CC3B33436A04D35815E41D5B6449AE78600BF24ADF7CA17B57B5138 | |||
| 7904 | msiexec.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\Content\EA618097E393409AFA316F0F87E2C202_6D6BF469D0BDEA697BA93FFAF1E0C5EA | binary | |
MD5:5BFA51F3A417B98E7443ECA90FC94703 | SHA256:BEBE2853A3485D1C2E5C5BE4249183E0DDAFF9F87DE71652371700A89D937128 | |||
| 7904 | msiexec.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\EA618097E393409AFA316F0F87E2C202_6D6BF469D0BDEA697BA93FFAF1E0C5EA | binary | |
MD5:CC2D8C38C89C1F15CBB6CC167EB747A8 | SHA256:64AC7B48986CE98CE27AD38398B517FAD01F6A7824BA82084C5B5878389BB795 | |||
| 632 | msiexec.exe | C:\Users\admin\AppData\Local\Temp\{1B704FD1-C00F-482F-8997-82F2F19E10E7}\rsetup.exe | executable | |
MD5:500DAE8E966486D84F7AFB21870B64CA | SHA256:5911DE9F97E664822FA3DCF485D3F1C5D5FE8FAC041C9BD07BE724884D6FD0FD | |||
| 7904 | msiexec.exe | C:\Users\admin\AppData\LocalLow\Microsoft\CryptnetUrlCache\MetaData\ECF3006D44DA211141391220EE5049F4 | binary | |
MD5:64C66EF019E296ECA50DECFF77853A08 | SHA256:870B40BF521662FE73BE5D8C46B582C4EB0AD2EB3CE2155B4FEB9697572FCBDF | |||
| 7904 | msiexec.exe | C:\Users\admin\AppData\Local\Temp\MSI34D8.tmp | executable | |
MD5:4A908EE9C6F2F4AAD63382CCCEE731E4 | SHA256:459F503FB8B4FC4A600261430AC77BF70118D41FA19F7B2620D43BA6E9C8FA5E | |||
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
HTTP(S) requests
13
TCP/UDP connections
41
DNS requests
28
Threats
0
HTTP requests
PID | Process | Method | HTTP Code | IP | URL | CN | Type | Size | Reputation |
|---|---|---|---|---|---|---|---|---|---|
6544 | svchost.exe | GET | 200 | 2.17.190.73:80 | http://ocsp.digicert.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBSAUQYBMq2awn1Rh6Doh%2FsBYgFV7gQUA95QNVbRTLtm8KPiGxvDl7I90VUCEAJ0LqoXyo4hxxe7H%2Fz9DKA%3D | unknown | — | — | whitelisted |
5496 | MoUsoCoreWorker.exe | GET | 200 | 23.48.23.138:80 | http://crl.microsoft.com/pki/crl/products/MicRooCerAut2011_2011_03_22.crl | unknown | — | — | whitelisted |
5496 | MoUsoCoreWorker.exe | GET | 200 | 23.52.120.96:80 | http://www.microsoft.com/pkiops/crl/MicSecSerCA2011_2011-10-18.crl | unknown | — | — | whitelisted |
7904 | msiexec.exe | GET | 200 | 2.23.79.3:80 | http://s2.symcb.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBS56bKHAoUD%2BOyl%2B0LhPg9JxyQm4gQUf9Nlp8Ld7LvwMAnzQzn6Aq8zMTMCED141%2Fl2SWCyYX308B7Khio%3D | unknown | — | — | whitelisted |
7904 | msiexec.exe | GET | 200 | 2.23.79.3:80 | http://s2.symcb.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBS56bKHAoUD%2BOyl%2B0LhPg9JxyQm4gQUf9Nlp8Ld7LvwMAnzQzn6Aq8zMTMCED141%2Fl2SWCyYX308B7Khio%3D | unknown | — | — | whitelisted |
7904 | msiexec.exe | GET | 200 | 2.23.79.3:80 | http://s1.symcb.com/pca3-g5.crl | unknown | — | — | whitelisted |
7904 | msiexec.exe | GET | 200 | 2.23.79.3:80 | http://sv.symcd.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQe6LNDJdqx%2BJOp7hVgTeaGFJ%2FCQgQUljtT8Hkzl699g%2B8uK8zKt4YecmYCEGqlk0afvjzQyYSvvrtcLpI%3D | unknown | — | — | whitelisted |
7904 | msiexec.exe | GET | 200 | 2.23.79.3:80 | http://sv.symcd.com/MFEwTzBNMEswSTAJBgUrDgMCGgUABBQe6LNDJdqx%2BJOp7hVgTeaGFJ%2FCQgQUljtT8Hkzl699g%2B8uK8zKt4YecmYCEGqlk0afvjzQyYSvvrtcLpI%3D | unknown | — | — | whitelisted |
7904 | msiexec.exe | GET | 200 | 2.17.189.192:80 | http://sv.symcb.com/sv.crl | unknown | — | — | whitelisted |
7932 | SIHClient.exe | GET | 200 | 23.219.150.101:80 | http://www.microsoft.com/pkiops/crl/Microsoft%20ECC%20Product%20Root%20Certificate%20Authority%202018.crl | unknown | — | — | whitelisted |
Download PCAP, analyze network streams, HTTP content and a lot more at the full report
Connections
PID | Process | IP | Domain | ASN | CN | Reputation |
|---|---|---|---|---|---|---|
4 | System | 192.168.100.255:138 | — | — | — | whitelisted |
2104 | svchost.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
— | — | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
5496 | MoUsoCoreWorker.exe | 23.48.23.138:80 | crl.microsoft.com | Akamai International B.V. | DE | whitelisted |
5496 | MoUsoCoreWorker.exe | 23.52.120.96:80 | www.microsoft.com | AKAMAI-AS | DE | whitelisted |
6544 | svchost.exe | 20.190.160.66:443 | login.live.com | MICROSOFT-CORP-MSN-AS-BLOCK | NL | whitelisted |
6544 | svchost.exe | 2.17.190.73:80 | ocsp.digicert.com | AKAMAI-AS | DE | whitelisted |
— | — | 172.211.123.248:443 | client.wns.windows.com | MICROSOFT-CORP-MSN-AS-BLOCK | FR | whitelisted |
4 | System | 192.168.100.255:137 | — | — | — | whitelisted |
2112 | svchost.exe | 4.231.128.59:443 | settings-win.data.microsoft.com | MICROSOFT-CORP-MSN-AS-BLOCK | IE | whitelisted |
DNS requests
Domain | IP | Reputation |
|---|---|---|
settings-win.data.microsoft.com |
| whitelisted |
google.com |
| whitelisted |
crl.microsoft.com |
| whitelisted |
www.microsoft.com |
| whitelisted |
login.live.com |
| whitelisted |
ocsp.digicert.com |
| whitelisted |
client.wns.windows.com |
| whitelisted |
go.microsoft.com |
| whitelisted |
s2.symcb.com |
| whitelisted |
s1.symcb.com |
| whitelisted |
Threats
Process | Message |
|---|---|
rserver3.exe | %n%n%n%n%n%n%n%n%n |
rserver3.exe | %n%n%n%n%n%n%n%n%n |